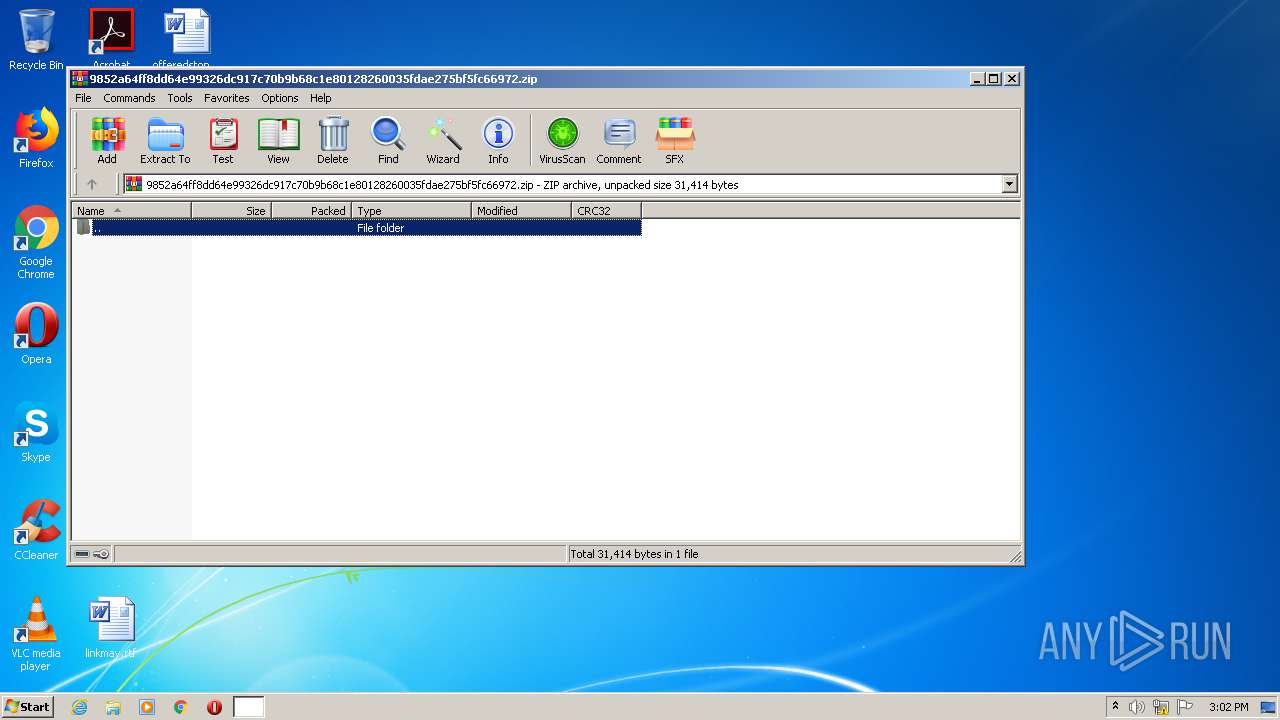
| File name: | 9852a64ff8dd64e99326dc917c70b9b68c1e80128260035fdae275bf5fc66972.zip |
| Full analysis: | https://app.any.run/tasks/717c535e-398b-4549-b71b-d1e27e62df6a |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 14:02:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | ADBBA3A078F4D086F21B9EE077FA1C37 |
| SHA1: | 9FA34DC06A1735D98BAF95696F58CA4AAF6DF734 |
| SHA256: | A4BF87286E2CCE6D057E0AB5CAFA52C29E5E0E0F77444E54E73FD4B11CAC5CF8 |
| SSDEEP: | 768:oE2qlD3/7ZNFbrMKS6qXteJd4Fq01tWCW3:oEBfZ7rMUNJeB1ts3 |
MALICIOUS
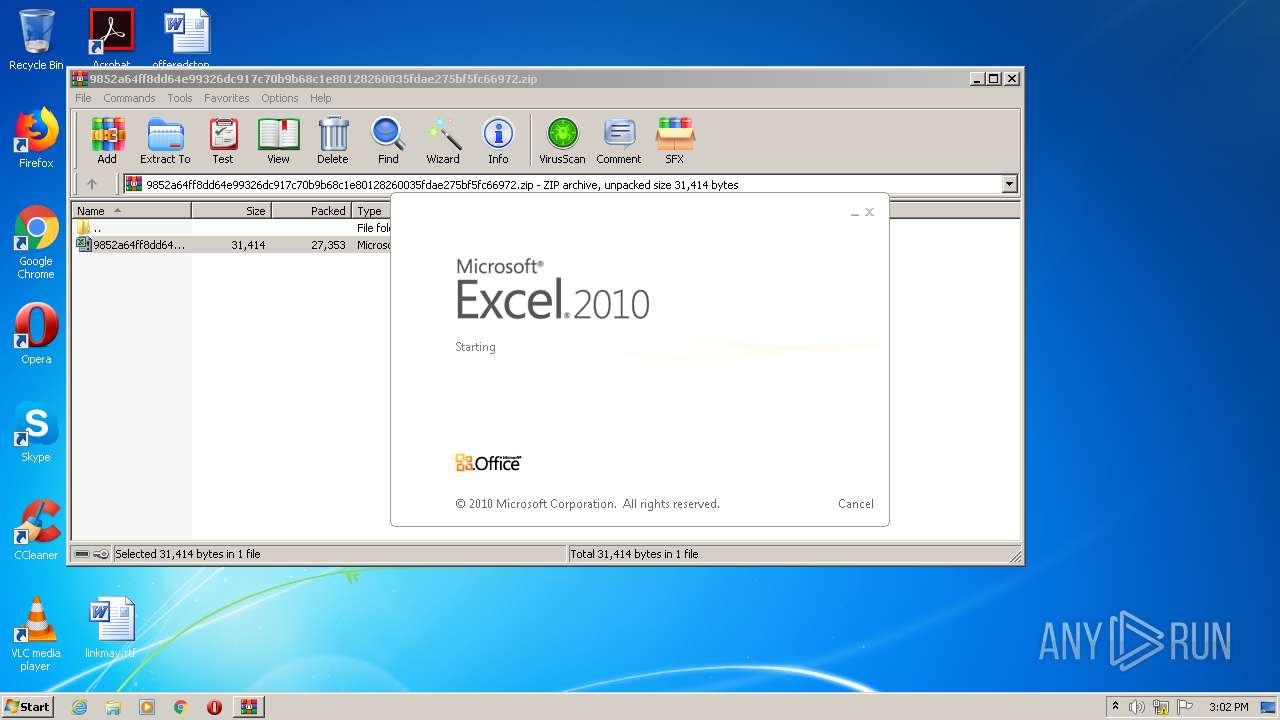
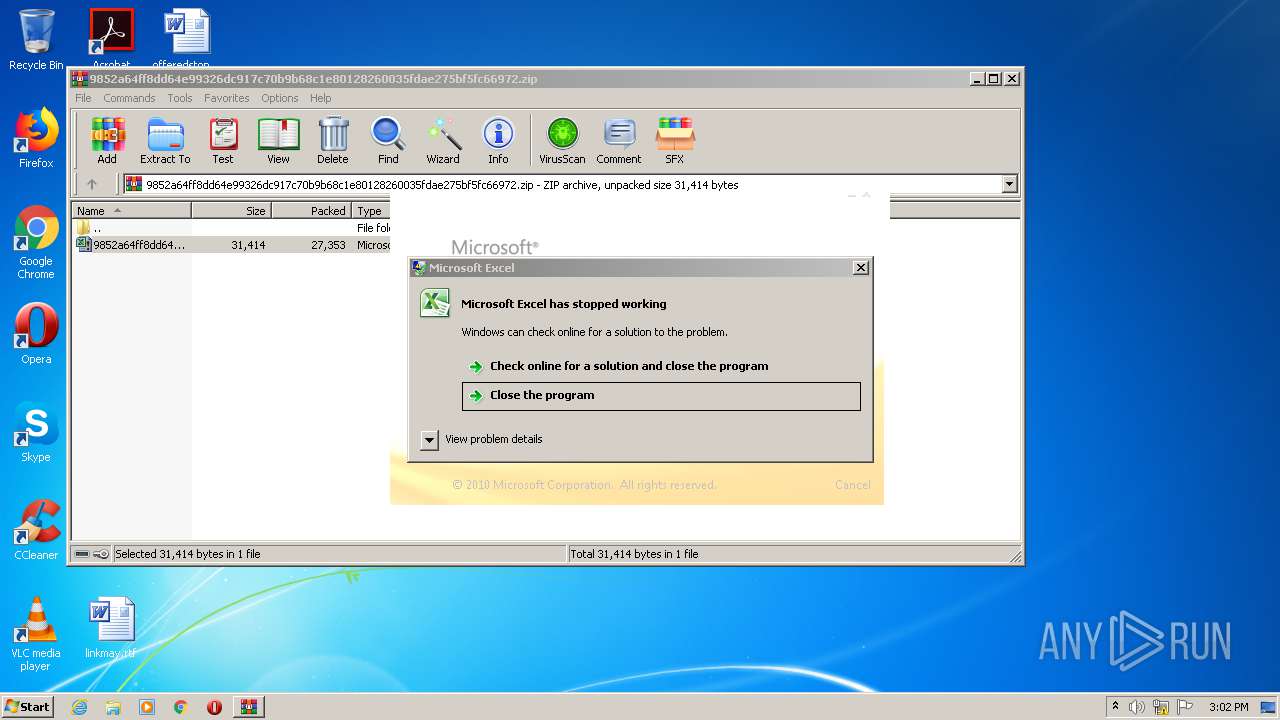
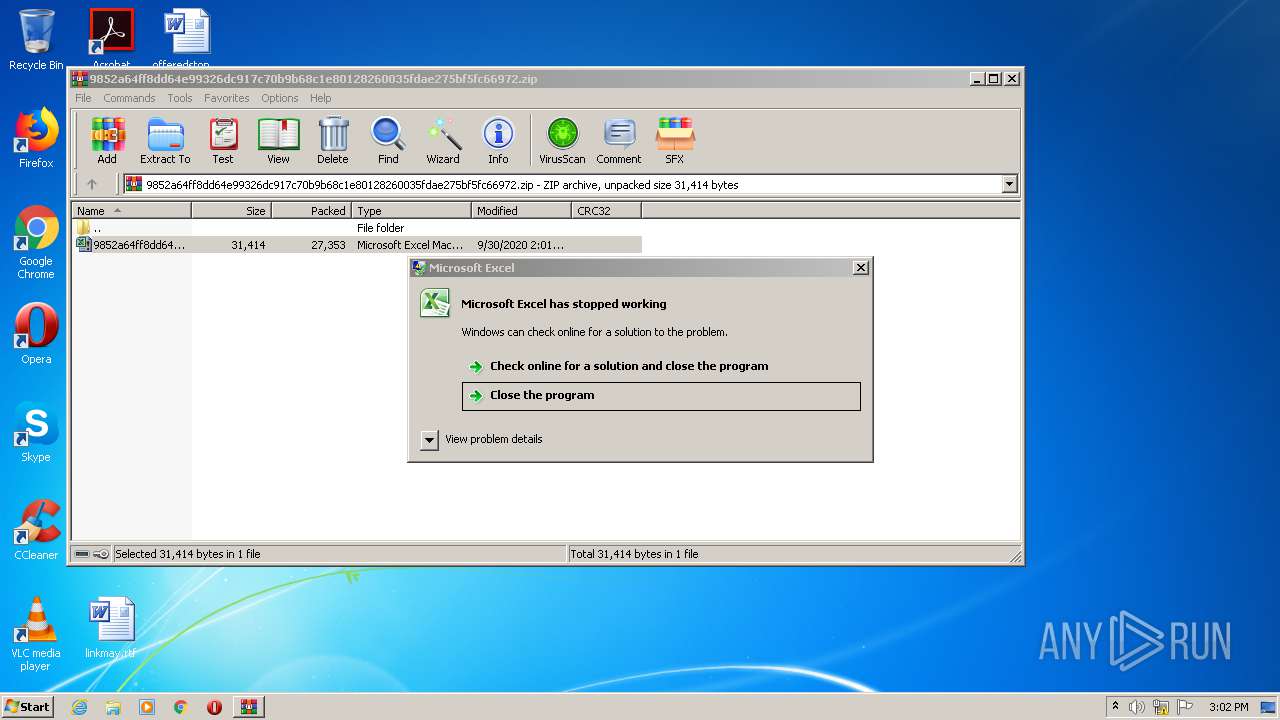
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2520)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2520)
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 2520)
SUSPICIOUS
Reads Internet Cache Settings
- regsvr32.exe (PID: 1700)
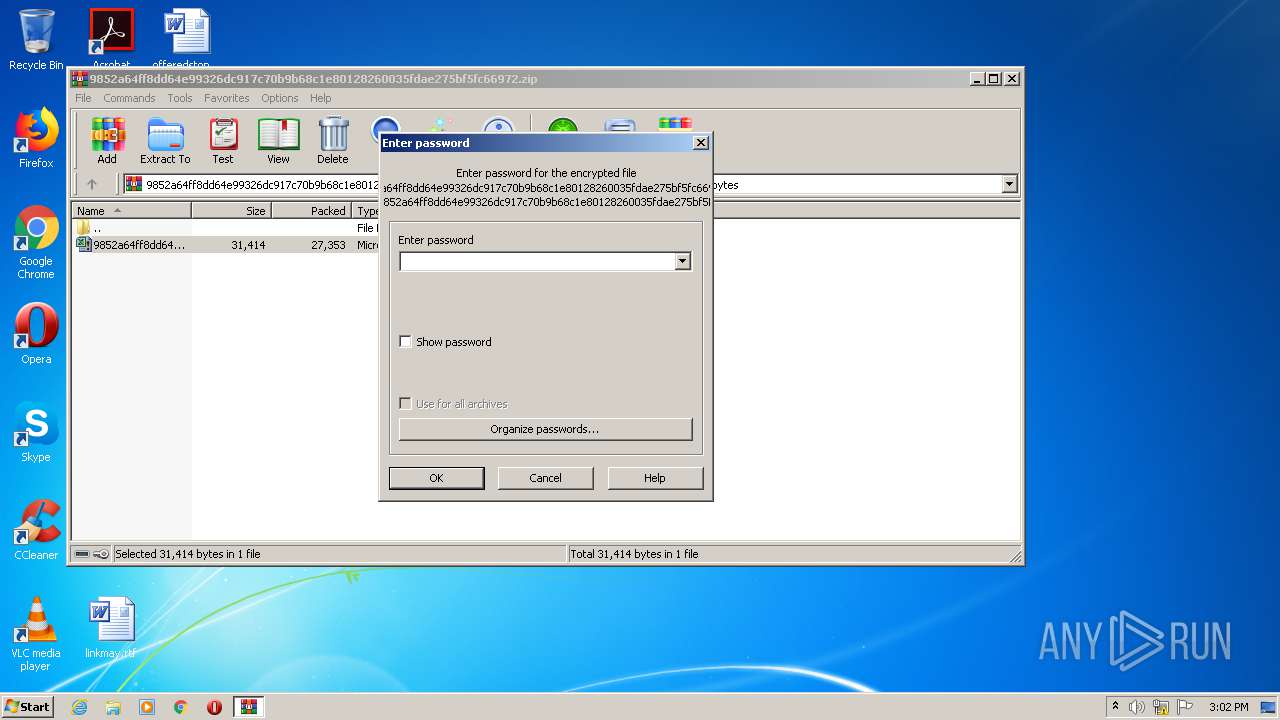
Starts Microsoft Office Application
- WinRAR.exe (PID: 2112)
Searches for installed software
- regsvr32.exe (PID: 1700)
INFO
Reads settings of System Certificates
- EXCEL.EXE (PID: 2520)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2520)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:30 14:01:15 |
| ZipCRC: | 0x51113bfc |
| ZipCompressedSize: | 27353 |
| ZipUncompressedSize: | 31414 |
| ZipFileName: | 9852a64ff8dd64e99326dc917c70b9b68c1e80128260035fdae275bf5fc66972.xlsm |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | "C:\Windows\System32\regsvr32.exe" -s C:\bQRmAmpj\YsnVxs\xVmDcR. | C:\Windows\System32\regsvr32.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 984 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
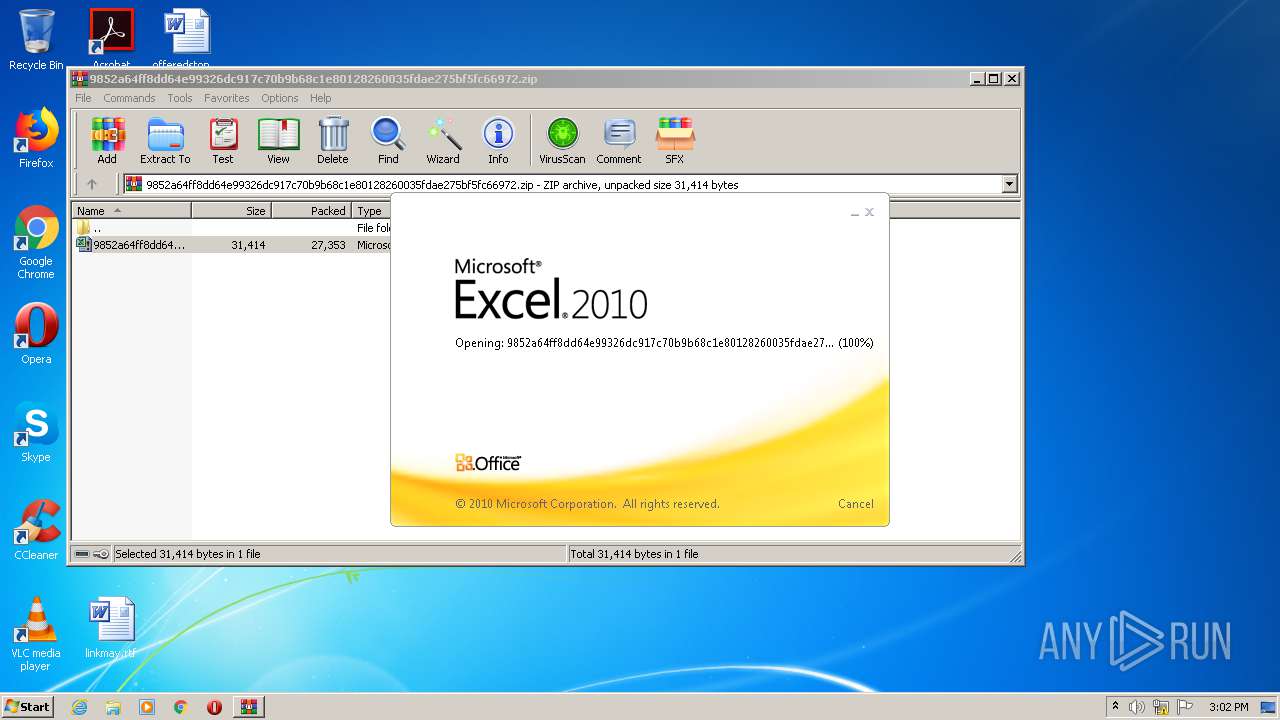
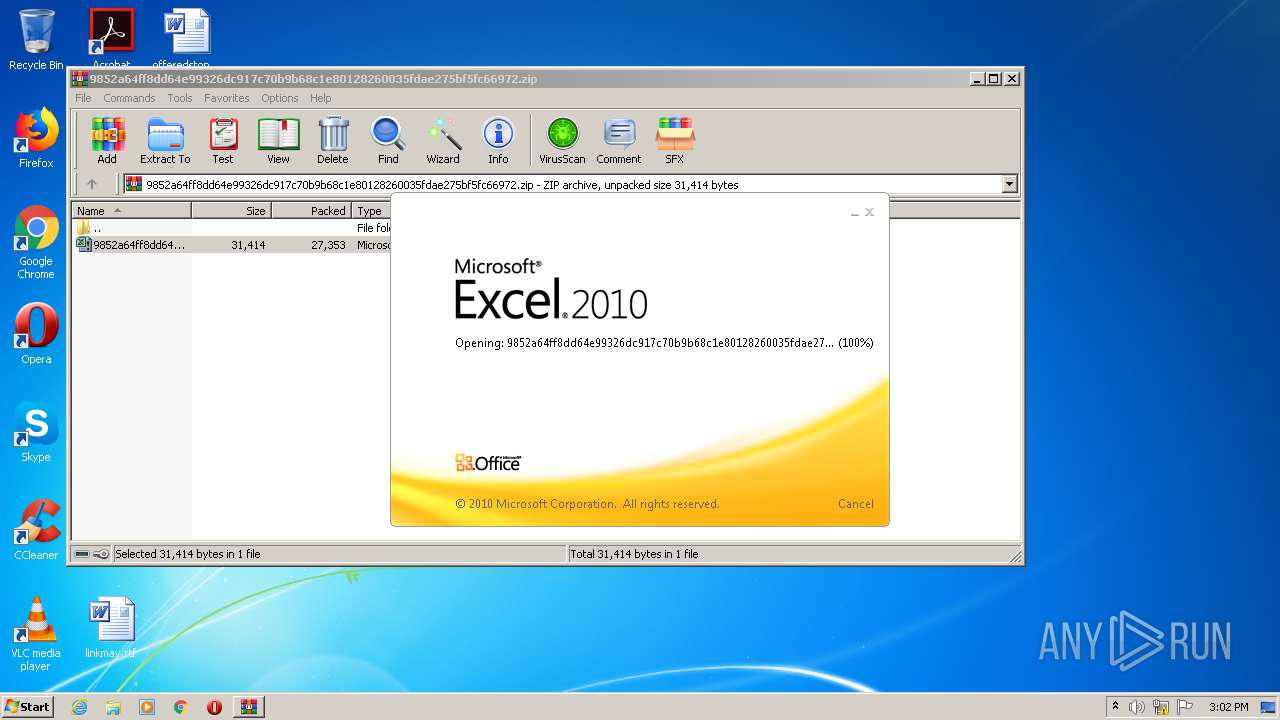
| 2112 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\9852a64ff8dd64e99326dc917c70b9b68c1e80128260035fdae275bf5fc66972.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2160 | C:\Windows\system32\dwwin.exe -x -s 984 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 446
Read events
1 285
Write events
145
Delete events
16
Modification events
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\9852a64ff8dd64e99326dc917c70b9b68c1e80128260035fdae275bf5fc66972.zip | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2112) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2520) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 3i$ |
Value: 33692400D8090000010000000000000000000000 | |||
Executable files
2
Suspicious files
5
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRD533.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CabED7F.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\TarED80.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D3E4A06F.png | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\855F5FA4.png | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1CF73355.png | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2112.37696\~$9852a64ff8dd64e99326dc917c70b9b68c1e80128260035fdae275bf5fc66972.xlsm | — | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Excel8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2520 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\1765390.cvr | sqm | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2520 | EXCEL.EXE | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPVY3MO9IytO9%2F4RrEnf12MMw%3D%3D | unknown | der | 527 b | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2520 | EXCEL.EXE | 83.166.138.121:443 | seminelogistics.com | Infomaniak Network SA | CH | unknown |
2520 | EXCEL.EXE | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
1052 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1700 | regsvr32.exe | 146.164.126.197:443 | — | Fundacao de Amparo a Pesquisa/RJ | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seminelogistics.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |