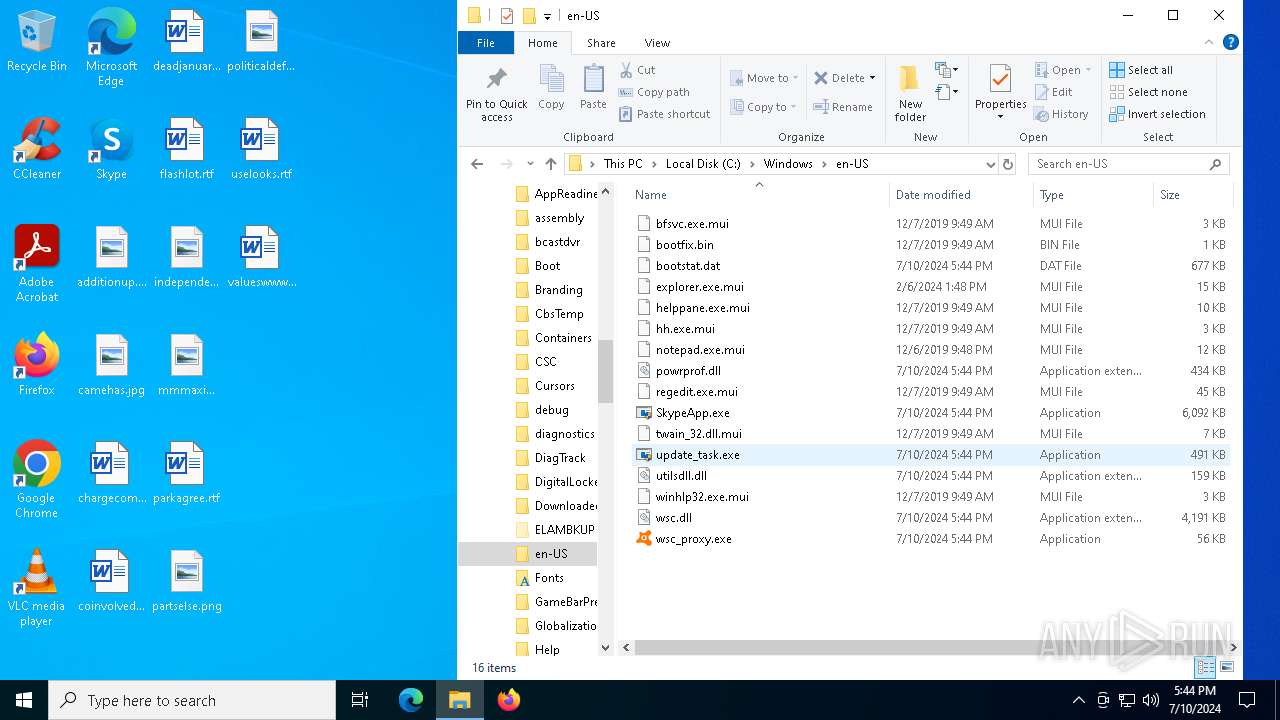
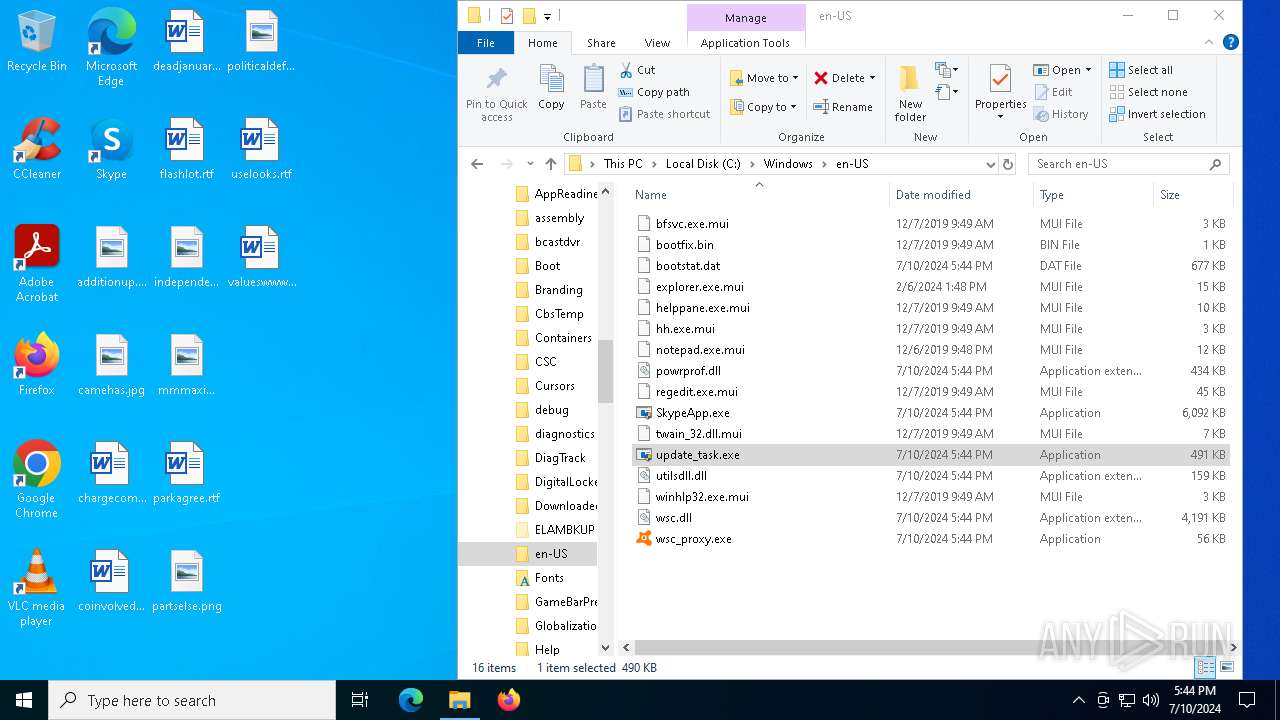
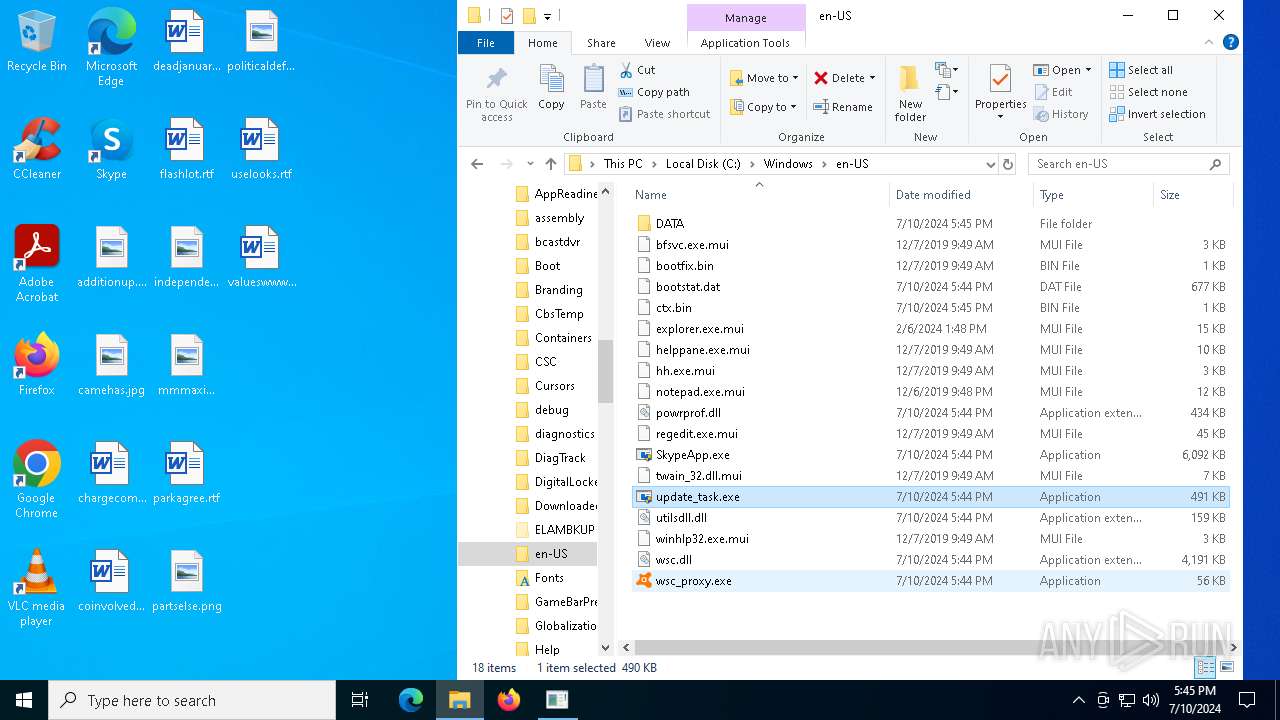
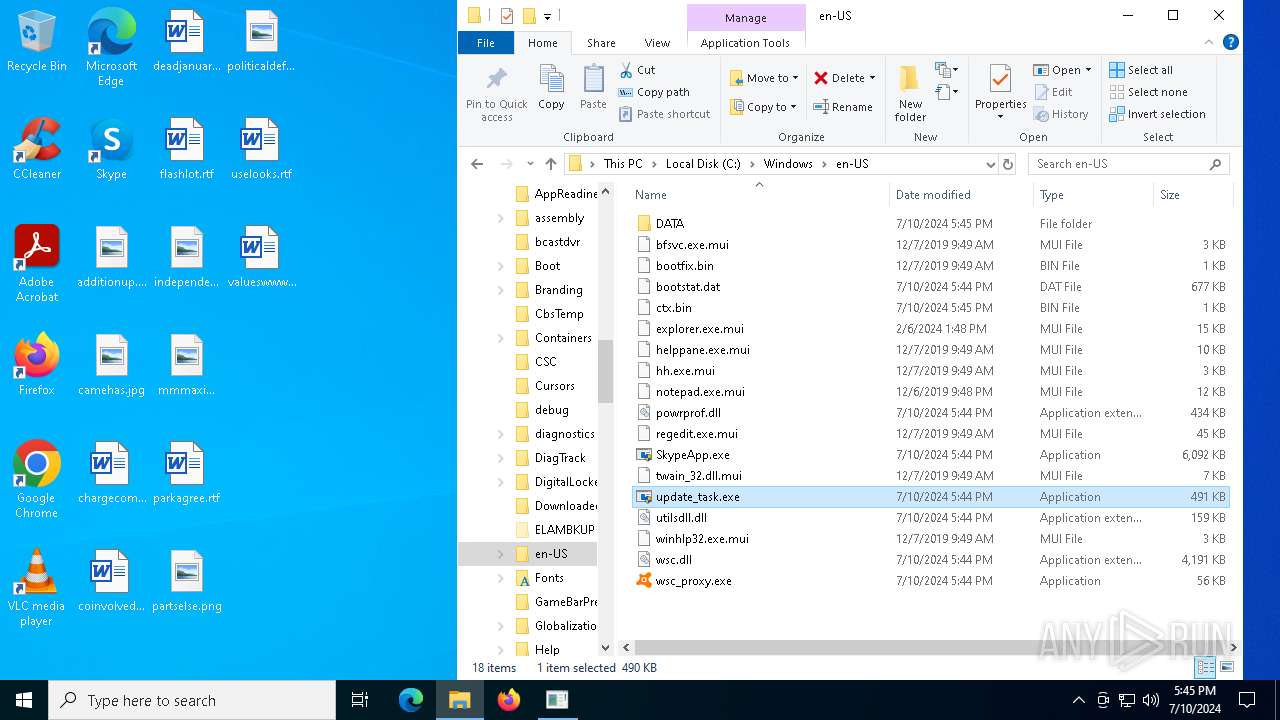
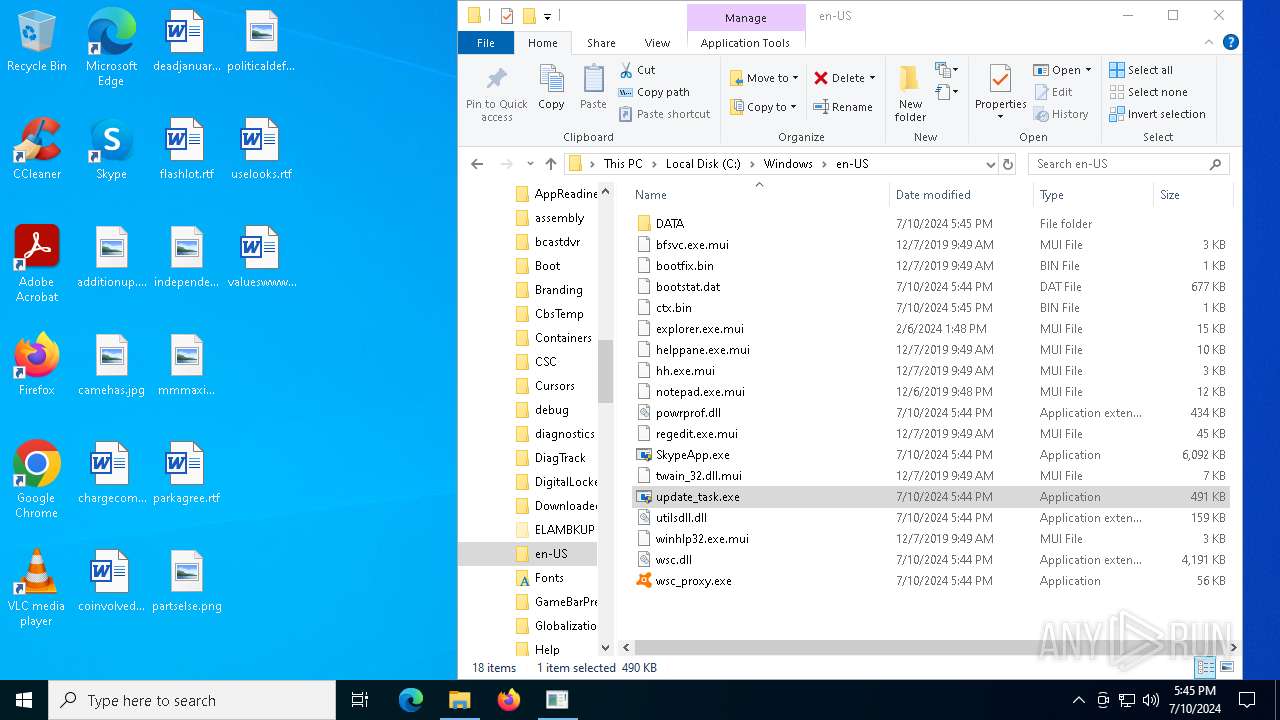
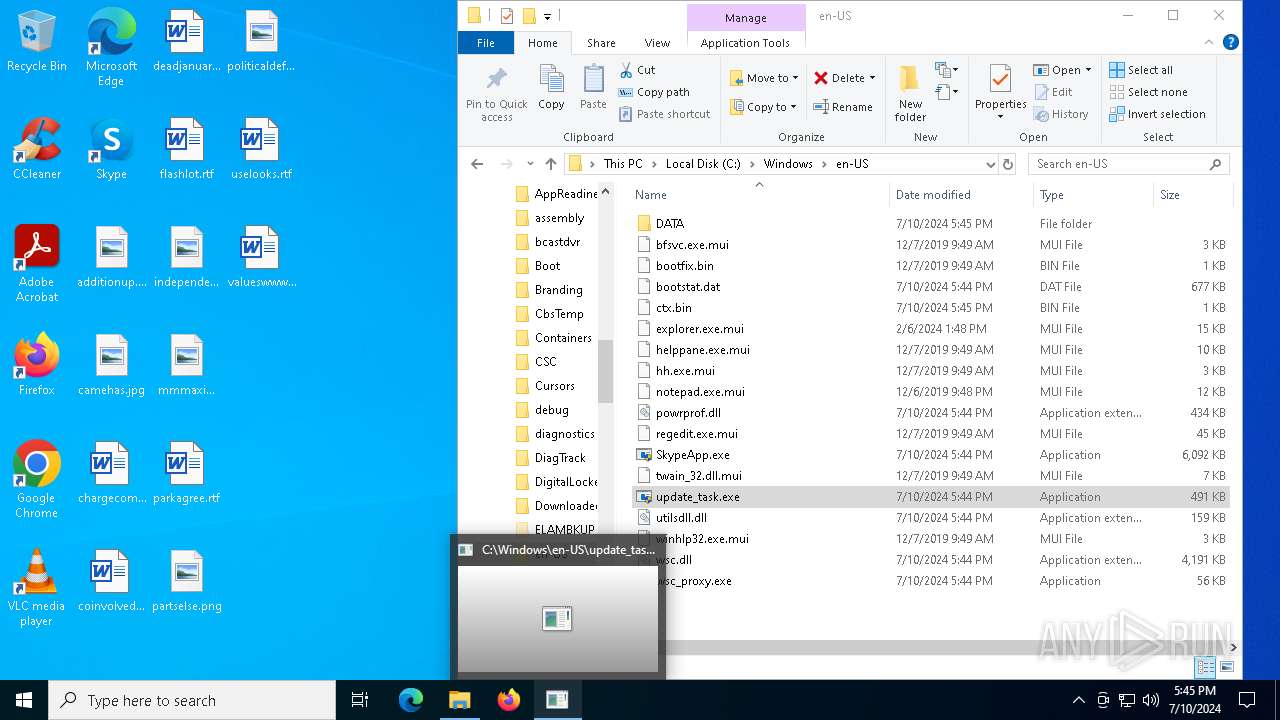
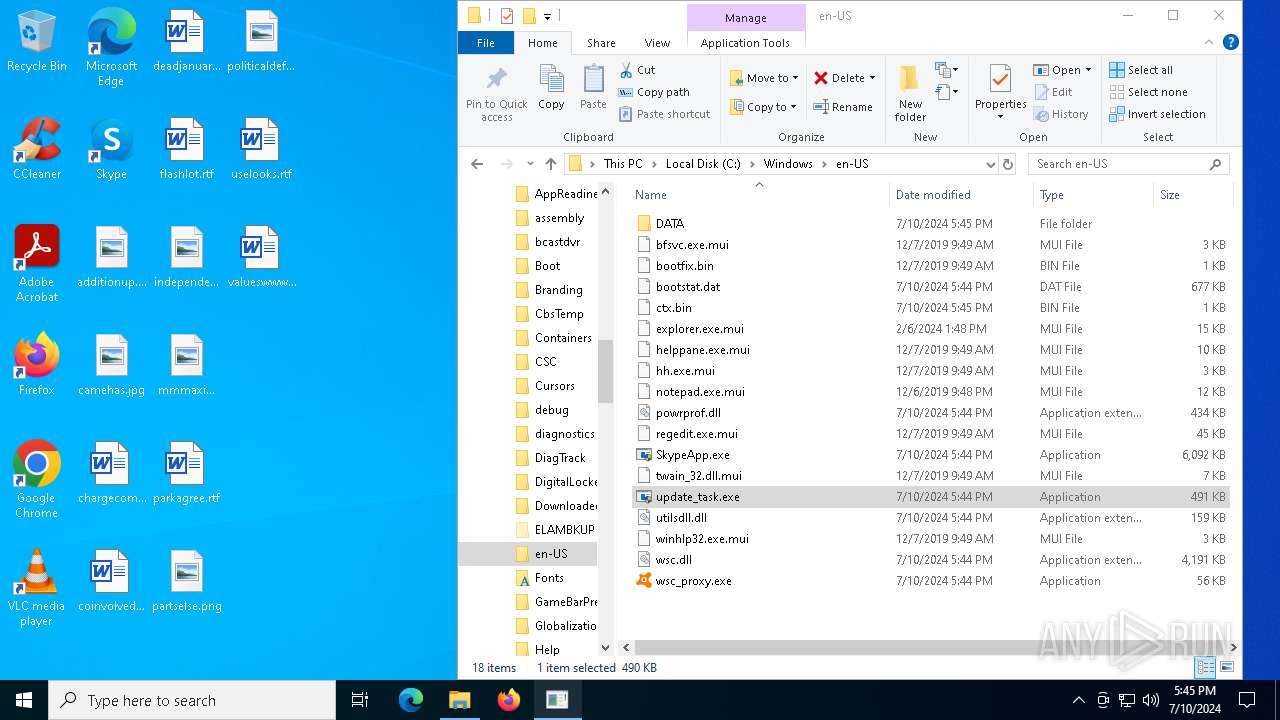
| File name: | update_task.exe |
| Full analysis: | https://app.any.run/tasks/8584c317-0490-427a-9024-4a1ee926b541 |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2024, 17:42:59 |
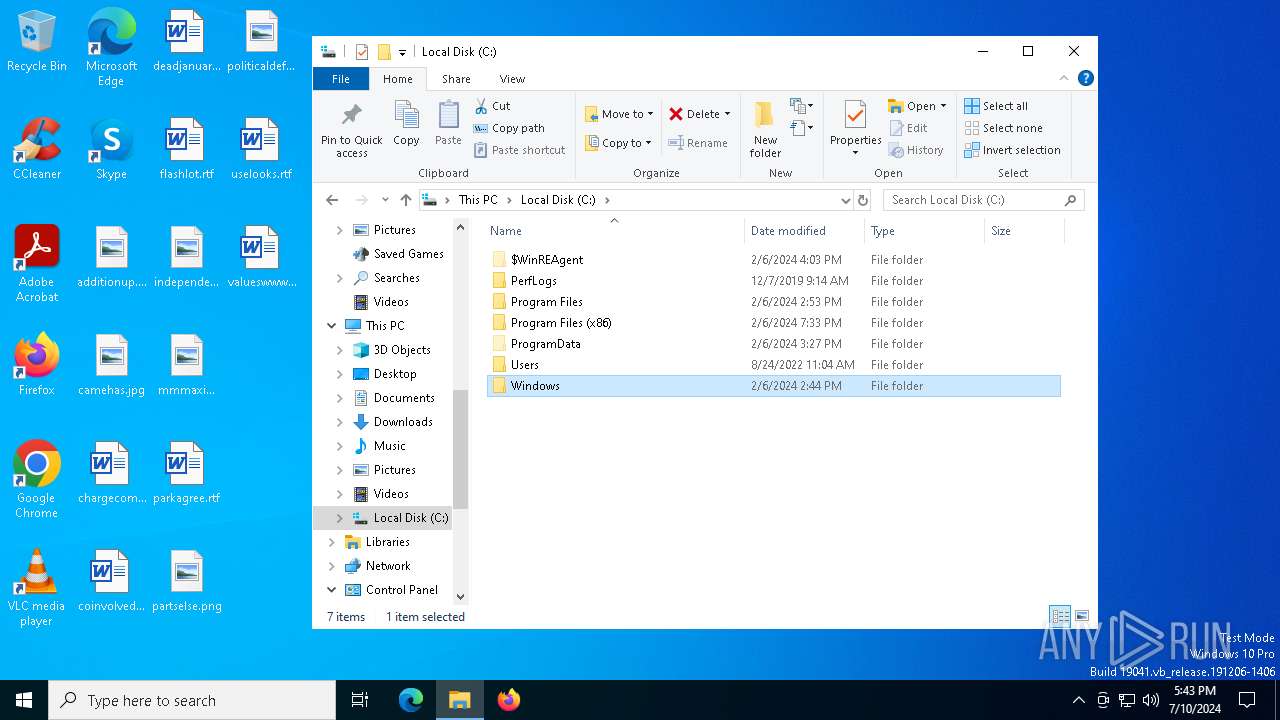
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 624A9592ECF9DC33A8F837DC5256A2BC |
| SHA1: | 4217D74F3DC4BAE644D3A847E1262C60F2AC90D5 |
| SHA256: | A4B2439027F2F45D95D6C9DF9979B76AB6B3252886CDDE436BF5F9AE88D79B13 |
| SSDEEP: | 12288:KvGvpKBvEKw8rPR+ABwiLyN/CoYYdg5DUq19LS95KBNvDhfBB4p2:KvGvKvbw8VwGYC59LS7KHhfcp2 |
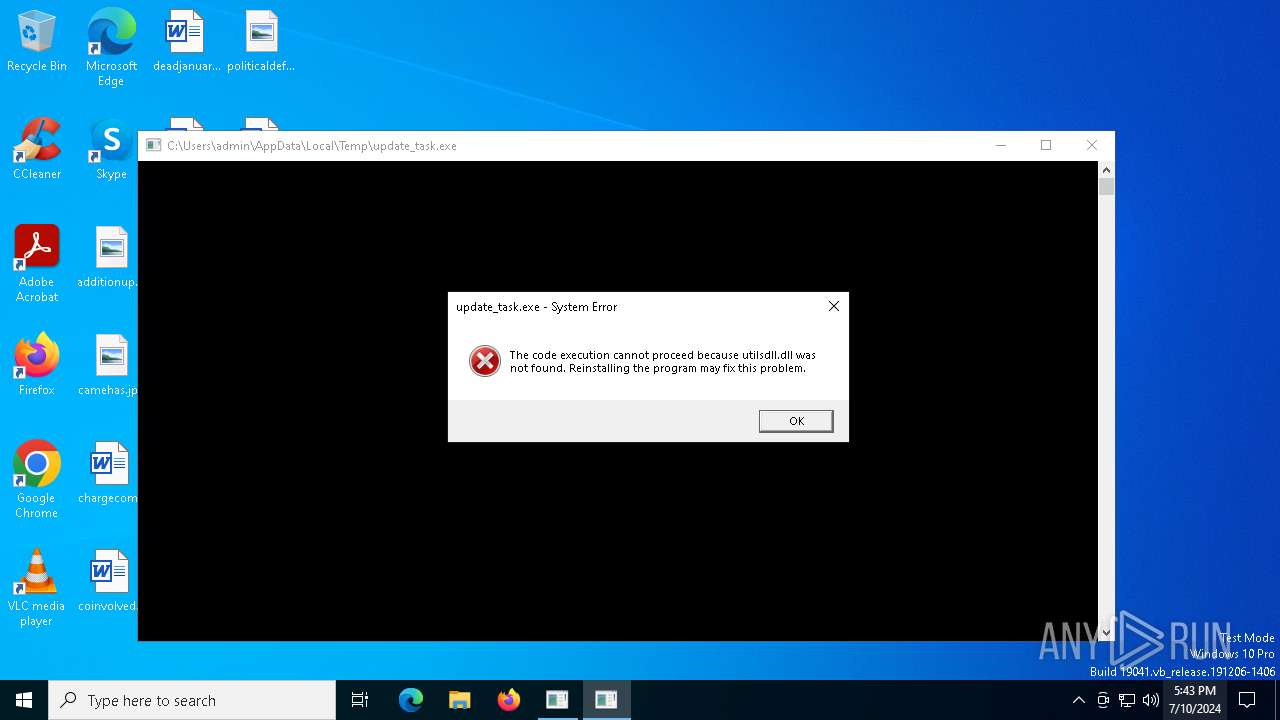
MALICIOUS
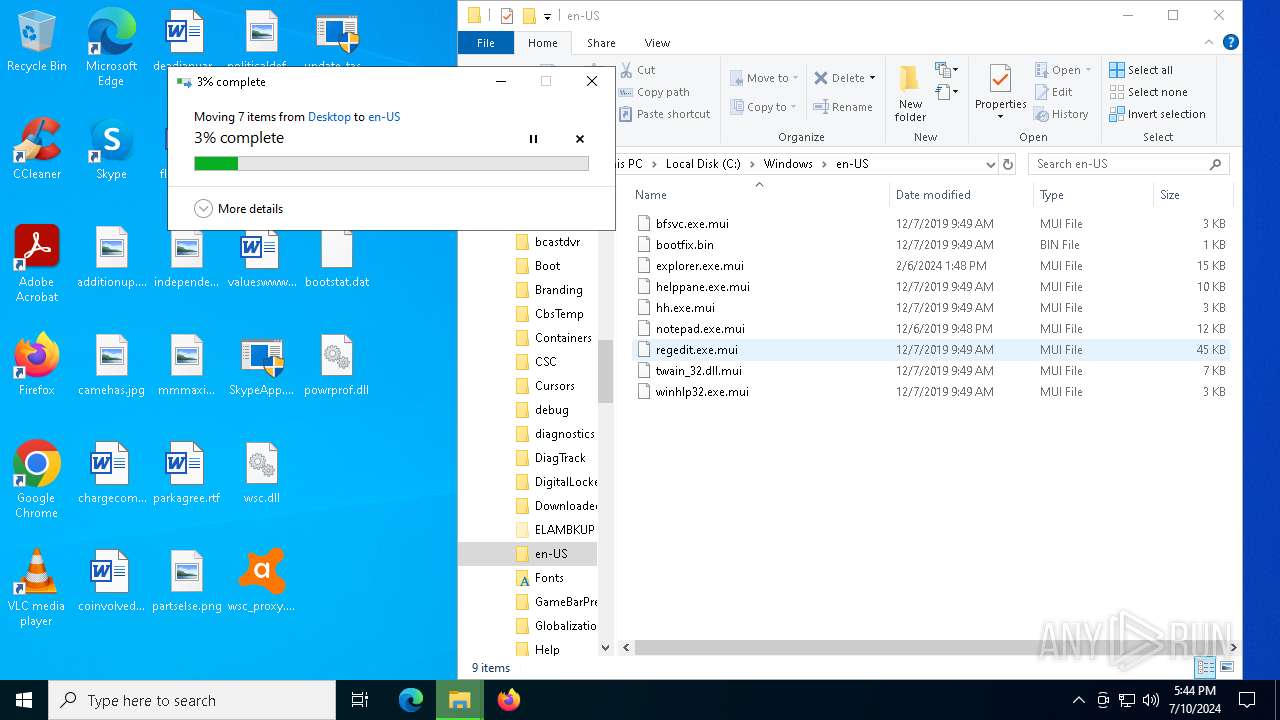
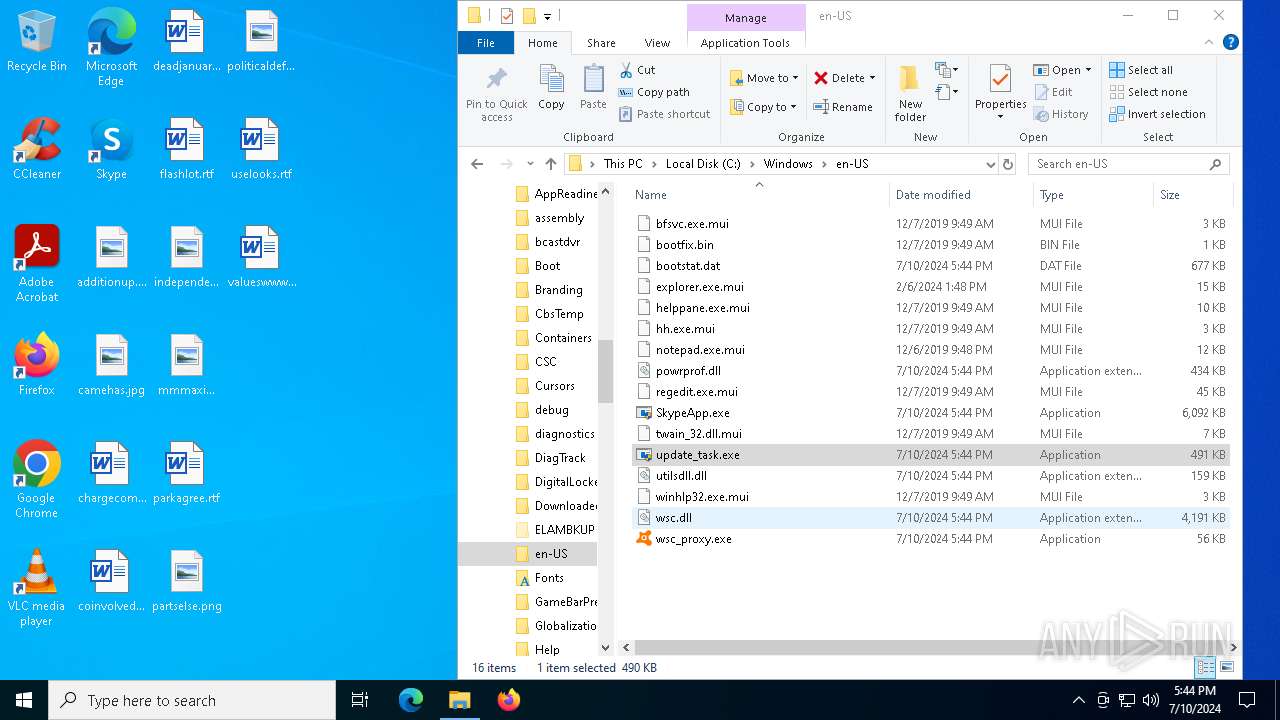
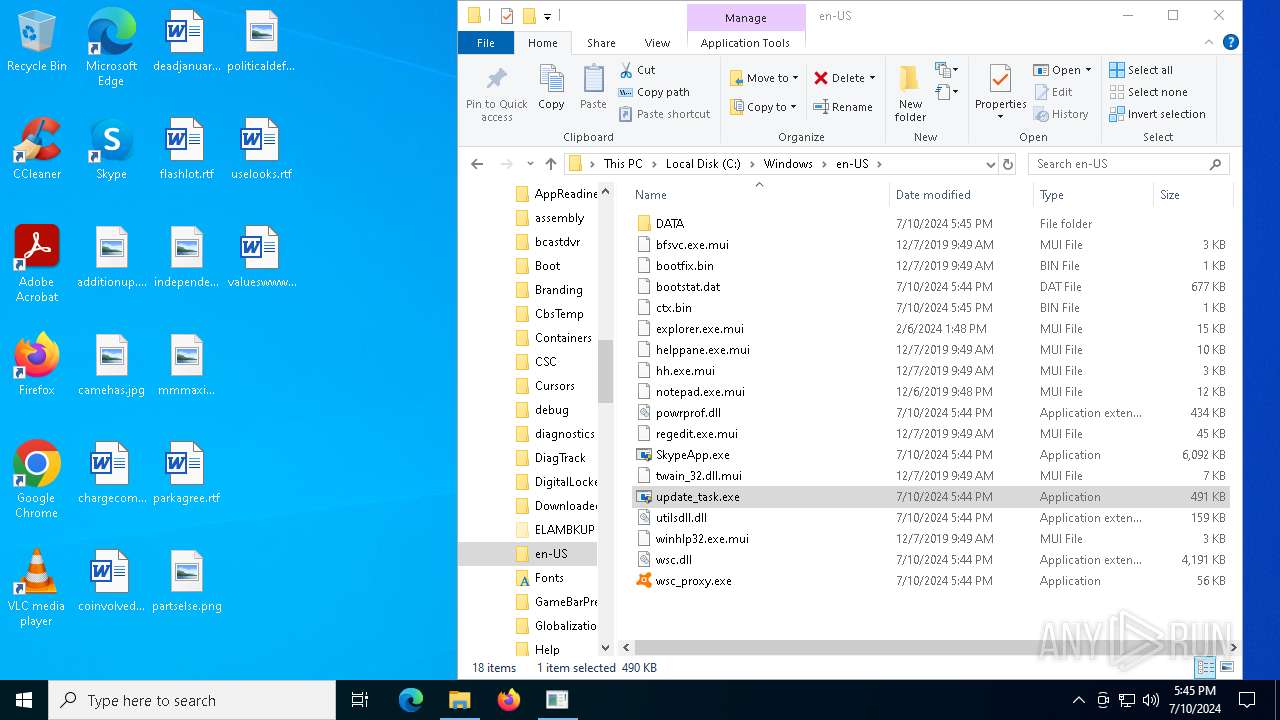
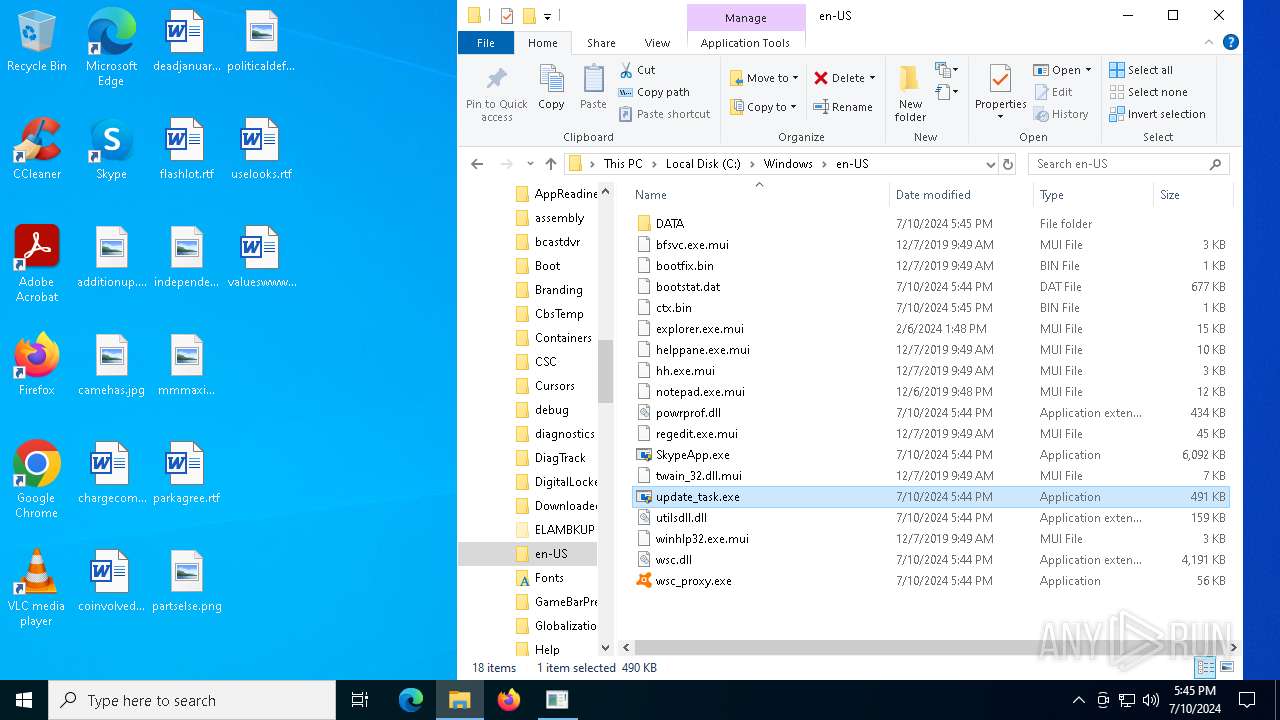
Drops the executable file immediately after the start
- update_task.exe (PID: 3848)
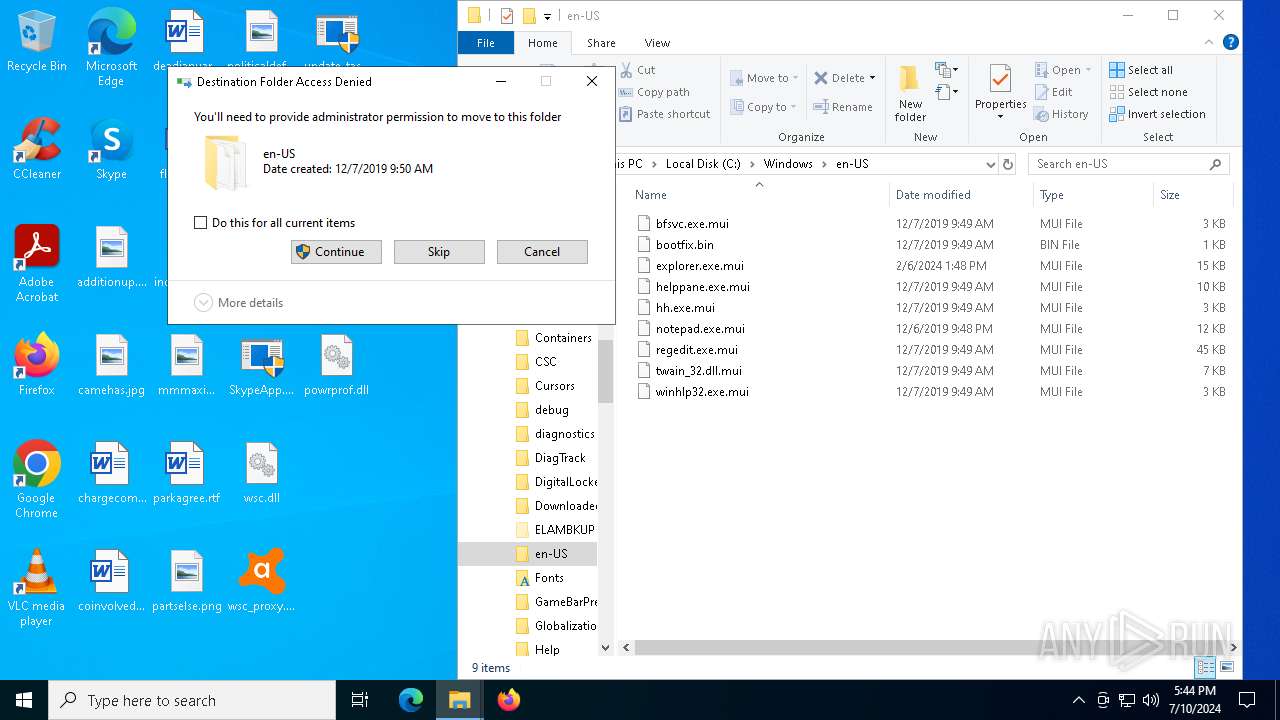
Creates a writable file in the system directory
- WerFault.exe (PID: 2972)
SUSPICIOUS
Reads security settings of Internet Explorer
- update_task.exe (PID: 7076)
- LockApp.exe (PID: 6796)
Reads the date of Windows installation
- update_task.exe (PID: 7076)
Executable content was dropped or overwritten
- dllhost.exe (PID: 6980)
Executes as Windows Service
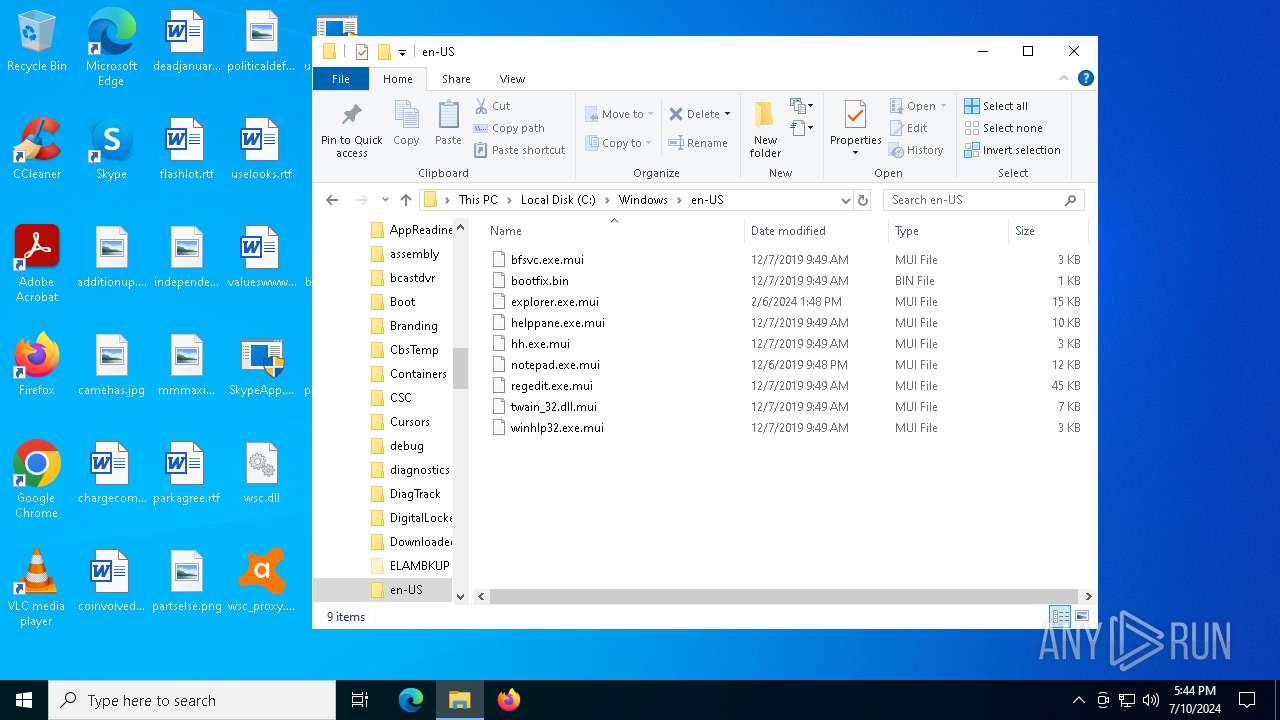
- wsc_proxy.exe (PID: 6612)
Executes application which crashes
- wsc_proxy.exe (PID: 6612)
INFO
Drops the executable file immediately after the start
- dllhost.exe (PID: 6980)
Reads the software policy settings
- slui.exe (PID: 6744)
- WerFault.exe (PID: 2972)
- slui.exe (PID: 6956)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6980)
Checks supported languages
- update_task.exe (PID: 7076)
- SkypeApp.exe (PID: 6444)
- LockApp.exe (PID: 6796)
- wsc_proxy.exe (PID: 6612)
Reads the computer name
- update_task.exe (PID: 7076)
- LockApp.exe (PID: 6796)
- SkypeApp.exe (PID: 6444)
- wsc_proxy.exe (PID: 6612)
Process checks computer location settings
- update_task.exe (PID: 7076)
Manual execution by a user
- update_task.exe (PID: 6896)
- update_task.exe (PID: 7076)
Reads the machine GUID from the registry
- wsc_proxy.exe (PID: 6612)
Reads CPU info
- wsc_proxy.exe (PID: 6612)
Creates files in the program directory
- wsc_proxy.exe (PID: 6612)
Checks proxy server information
- update_task.exe (PID: 7076)
- slui.exe (PID: 6956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:03:02 04:24:19+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 338944 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x22180 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 7.2.4.972 |
| ProductVersionNumber: | 7.2.4.972 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Fortinet Inc. |
| FileDescription: | FortiClient Virus Feedback Service |
| FileVersion: | 7.2.4.0972 |
| InternalName: | submitv.exe |
| LegalCopyright: | 2024 Fortinet Inc. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | submitv.exe |
| PrivateBuild: | - |
| ProductName: | FortiClient virus submit daemon |
| ProductVersion: | 7.2.4.0972 |
| SpecialBuild: | - |
Total processes
167
Monitored processes
16
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2972 | C:\WINDOWS\system32\WerFault.exe -u -p 6612 -s 1336 | C:\Windows\System32\WerFault.exe | wsc_proxy.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | "C:\Users\admin\AppData\Local\Temp\update_task.exe" | C:\Users\admin\AppData\Local\Temp\update_task.exe | explorer.exe | ||||||||||||
User: admin Company: Fortinet Inc. Integrity Level: HIGH Description: FortiClient Virus Feedback Service Exit code: 3221225781 Version: 7.2.4.0972 Modules
| |||||||||||||||
| 4320 | "C:\Users\admin\AppData\Local\Temp\update_task.exe" | C:\Users\admin\AppData\Local\Temp\update_task.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Virus Feedback Service Exit code: 3221226540 Version: 7.2.4.0972 Modules
| |||||||||||||||
| 5764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | update_task.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
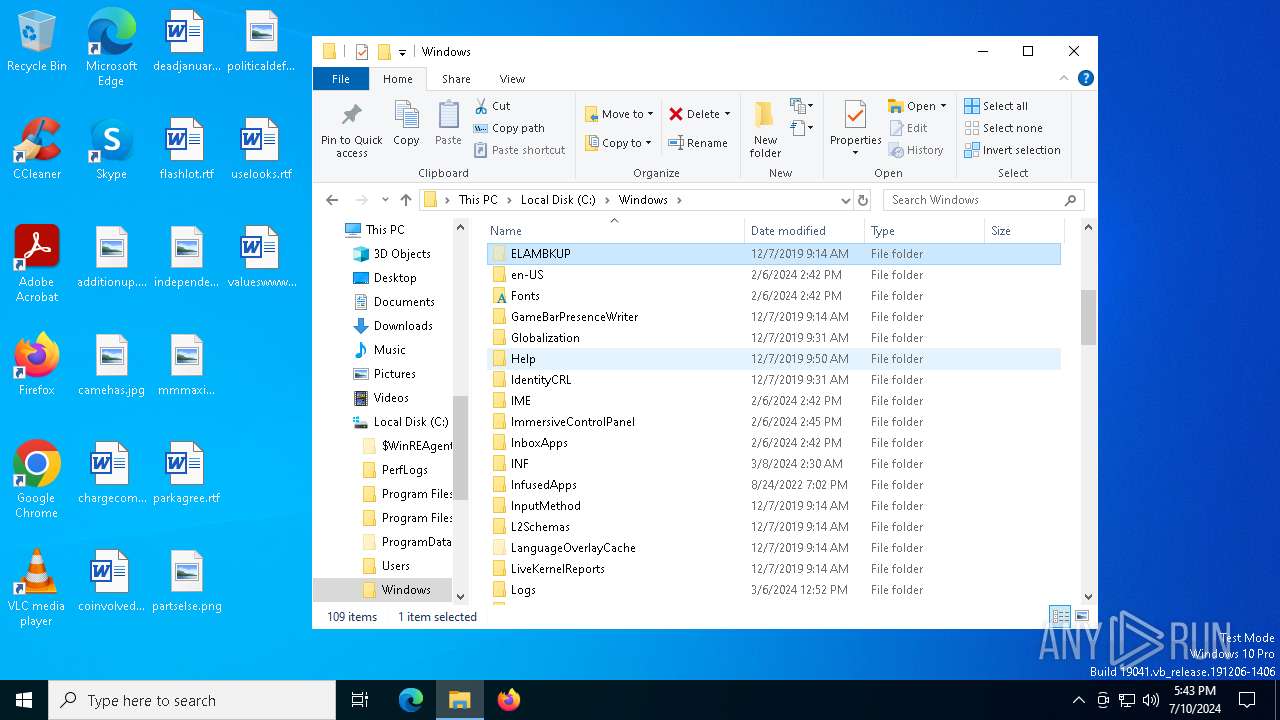
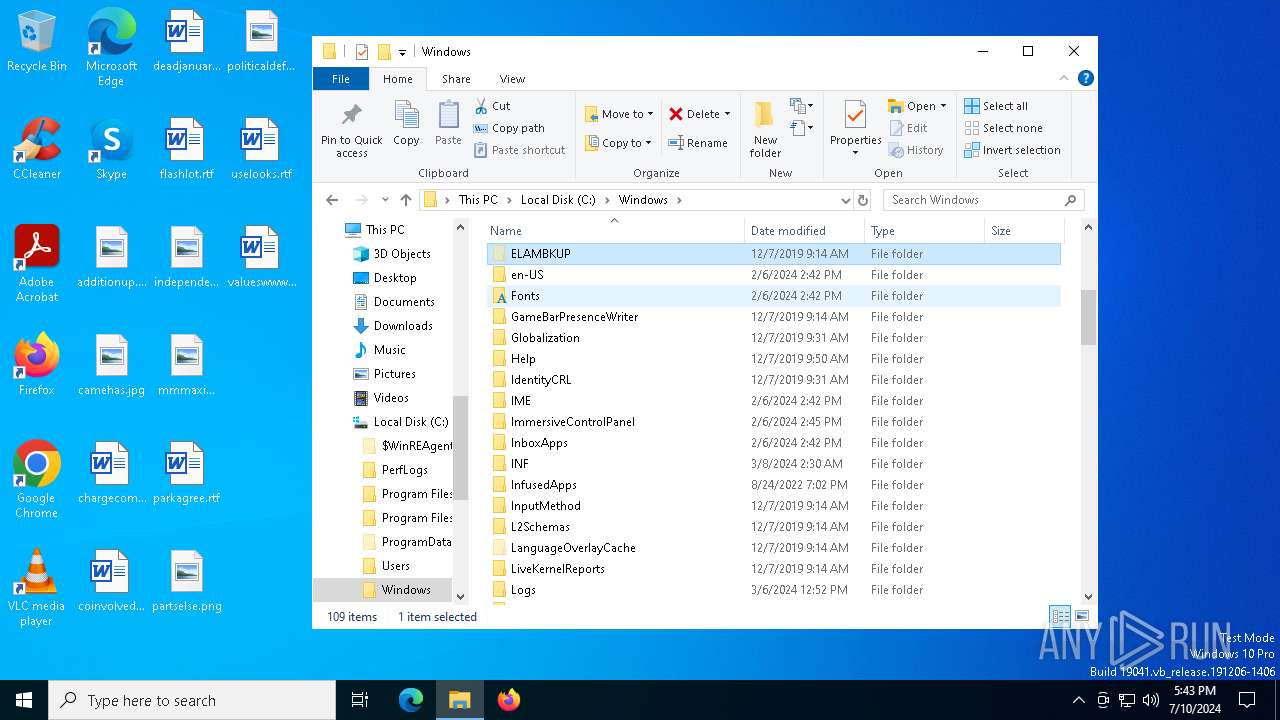
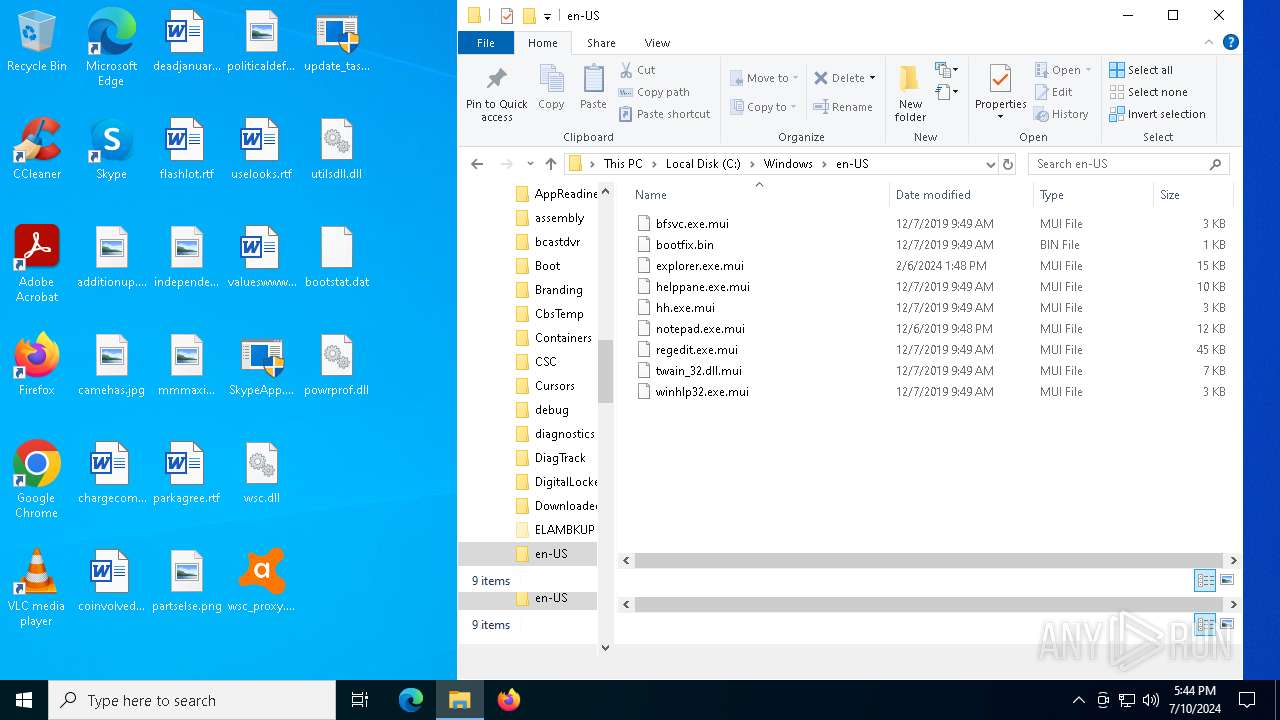
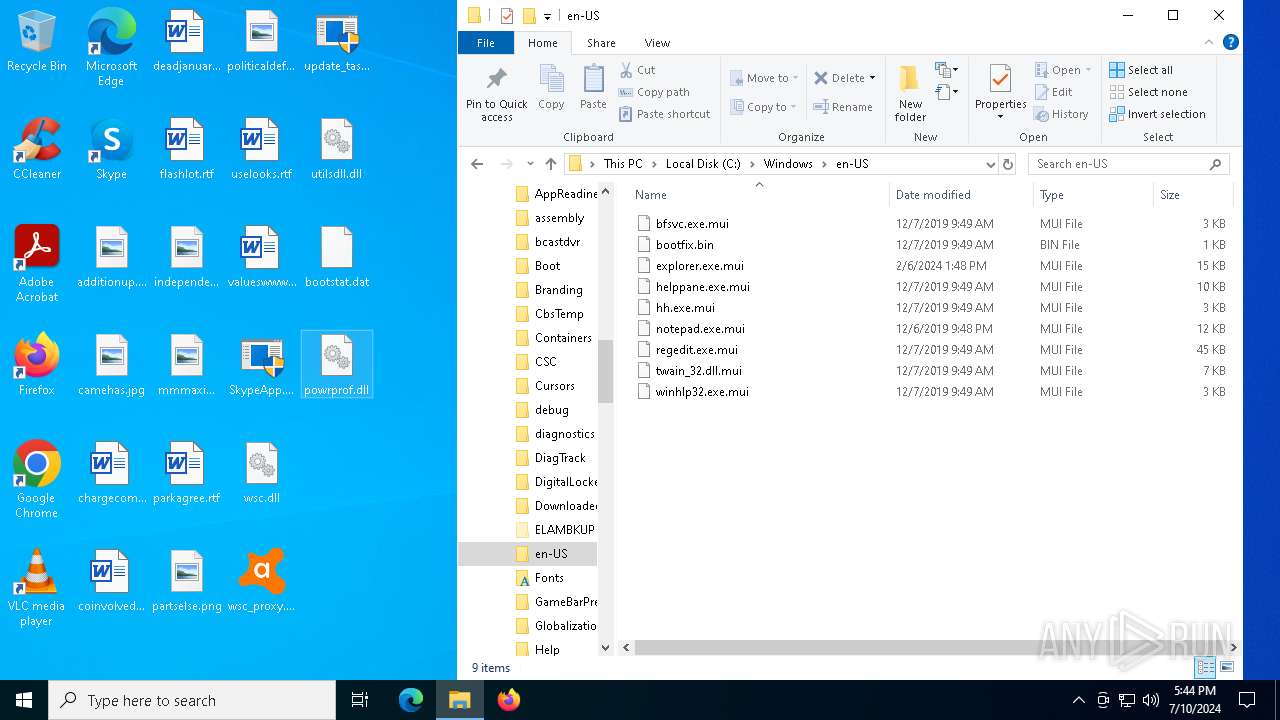
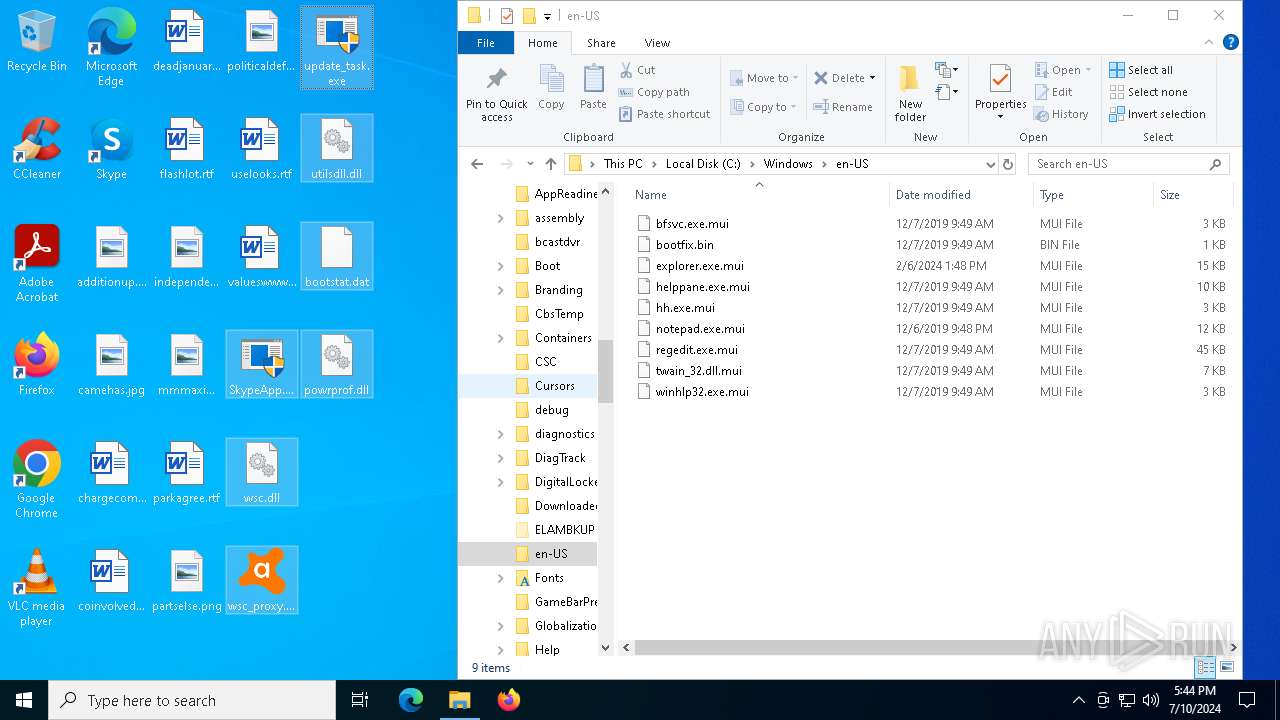
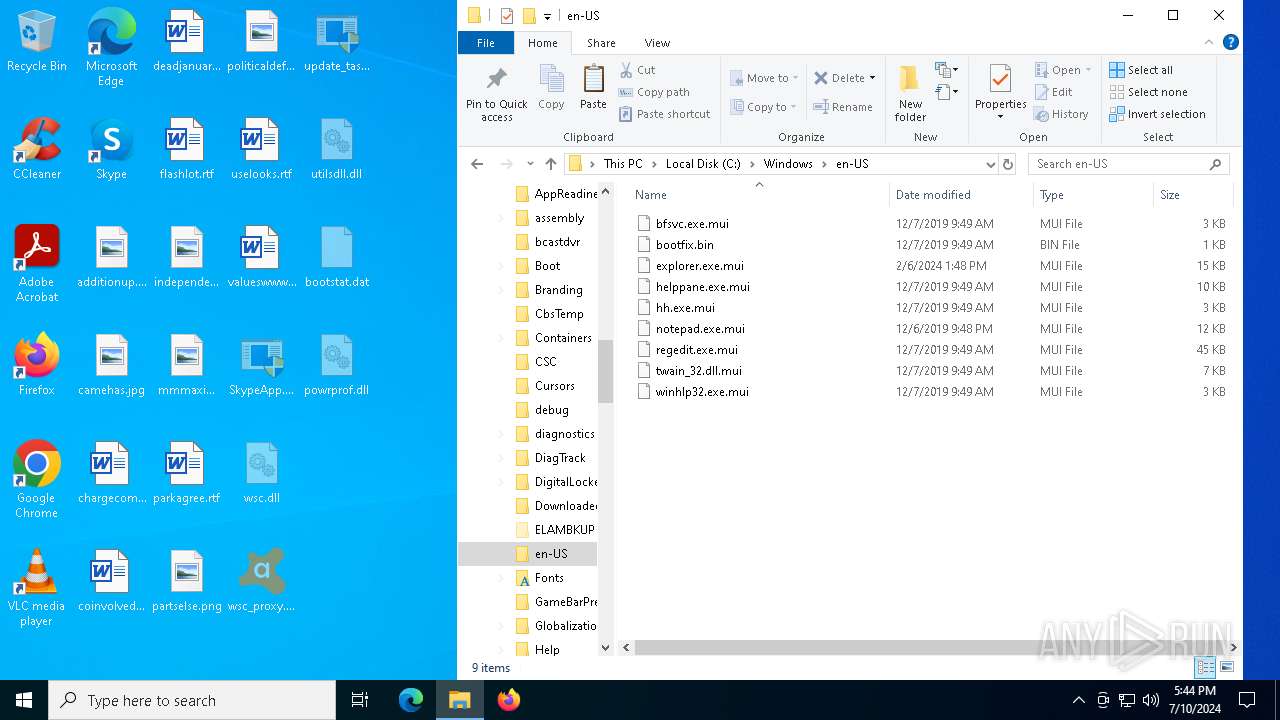
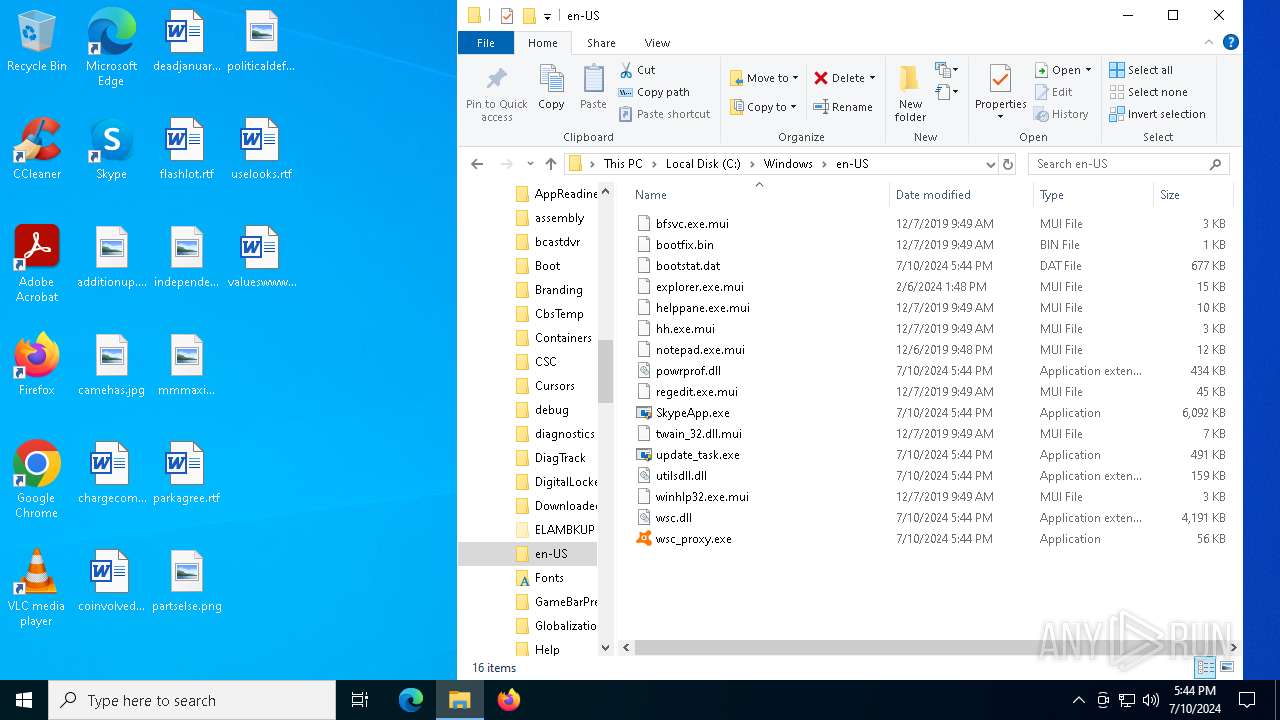
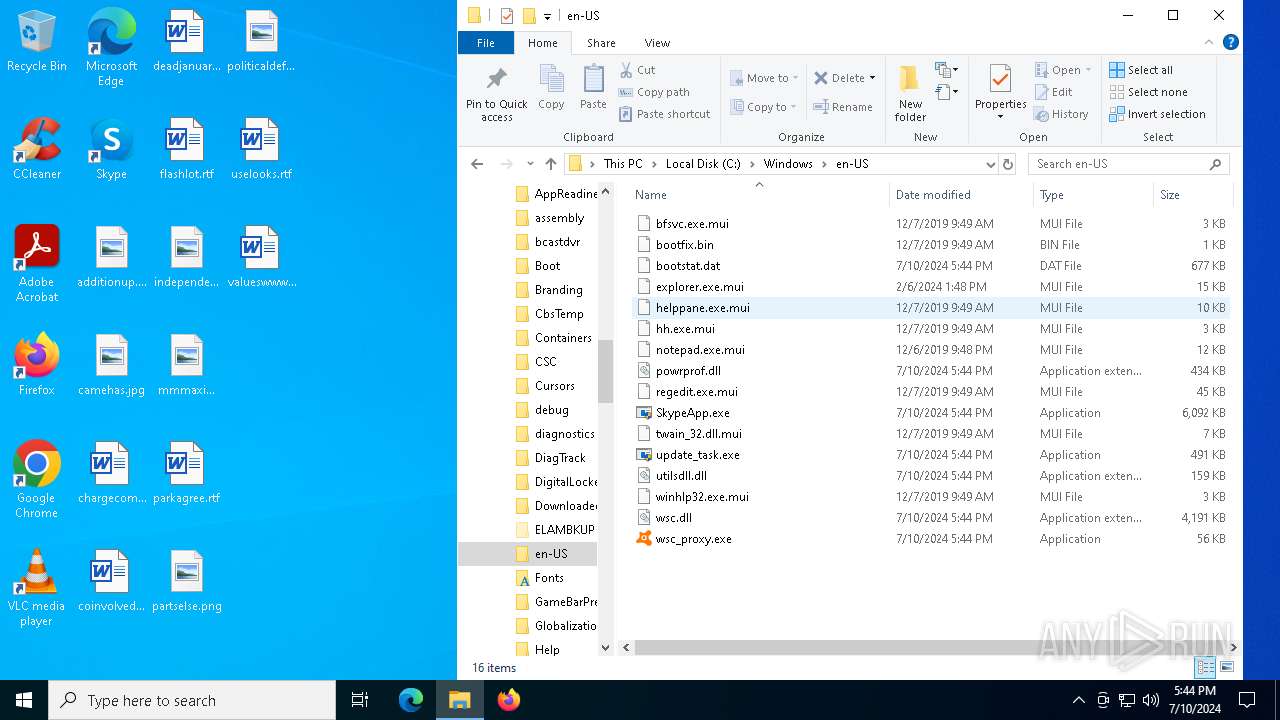
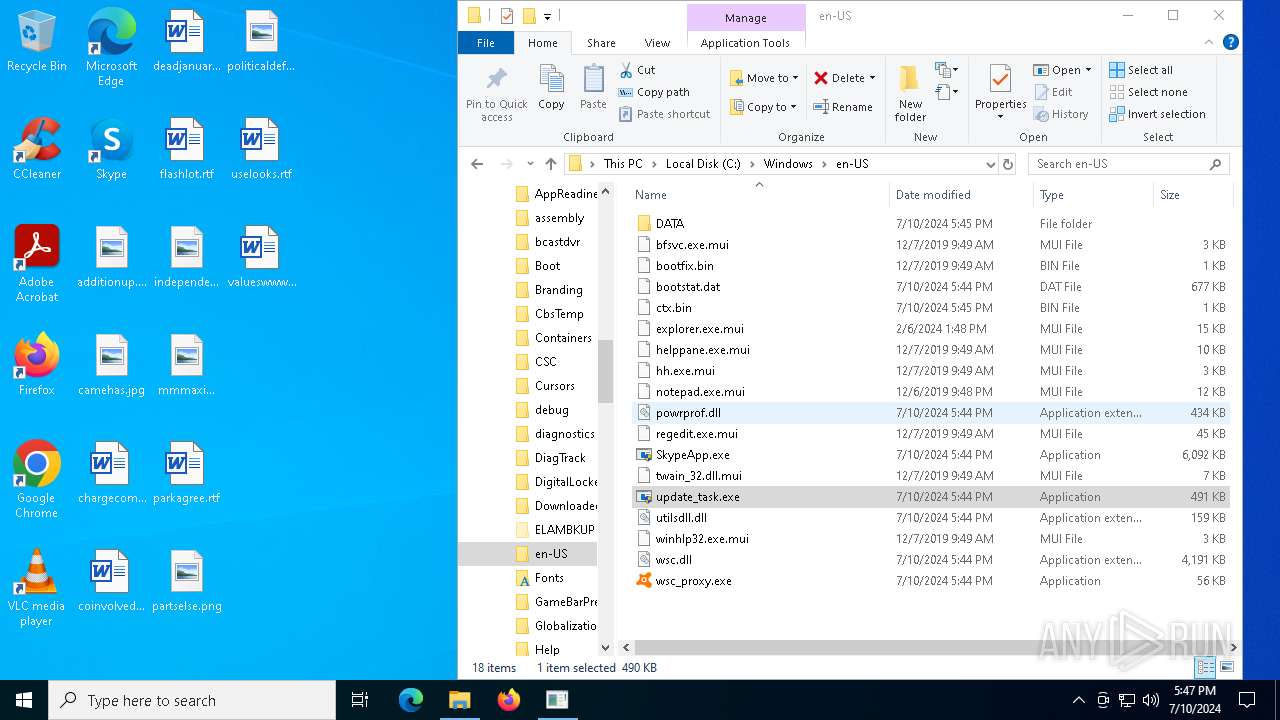
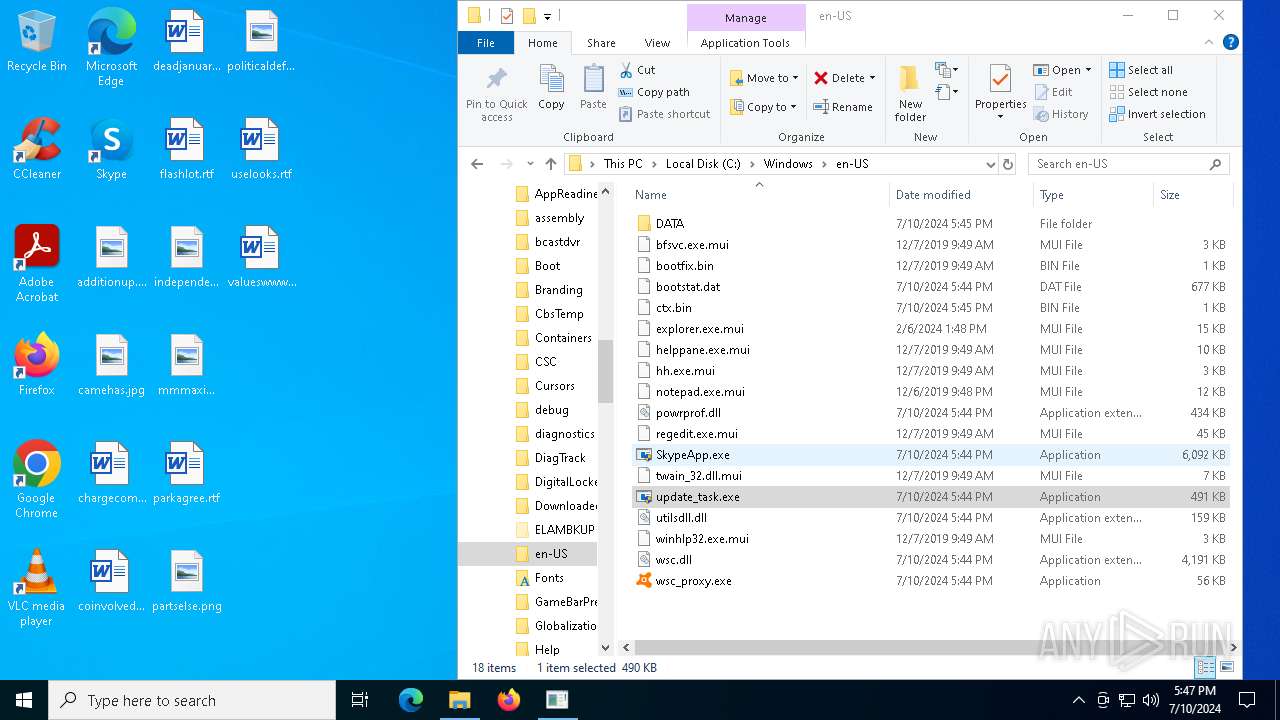
| 6444 | "C:\Windows\en-US\SkypeApp.exe" | C:\Windows\en-US\SkypeApp.exe | — | update_task.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SkypeApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6612 | "C:\Windows\en-US\wsc_proxy.exe" /runassvc /rpcserver /wsc_name:" " | C:\Windows\en-US\wsc_proxy.exe | services.exe | ||||||||||||
User: SYSTEM Company: AVAST Software Integrity Level: SYSTEM Description: Avast remediation exe Exit code: 3221226505 Version: 21.4.6162.0 Modules
| |||||||||||||||
| 6712 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6744 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6796 | "C:\WINDOWS\SystemApps\Microsoft.LockApp_cw5n1h2txyewy\LockApp.exe" -ServerName:WindowsDefaultLockScreen.AppX7y4nbzq37zn4ks9k7amqjywdat7d3j2z.mca | C:\Windows\SystemApps\Microsoft.LockApp_cw5n1h2txyewy\LockApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LockApp.exe Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 921
Read events
8 876
Write events
39
Delete events
6
Modification events
| (PID) Process: | (7076) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7076) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7076) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7076) update_task.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
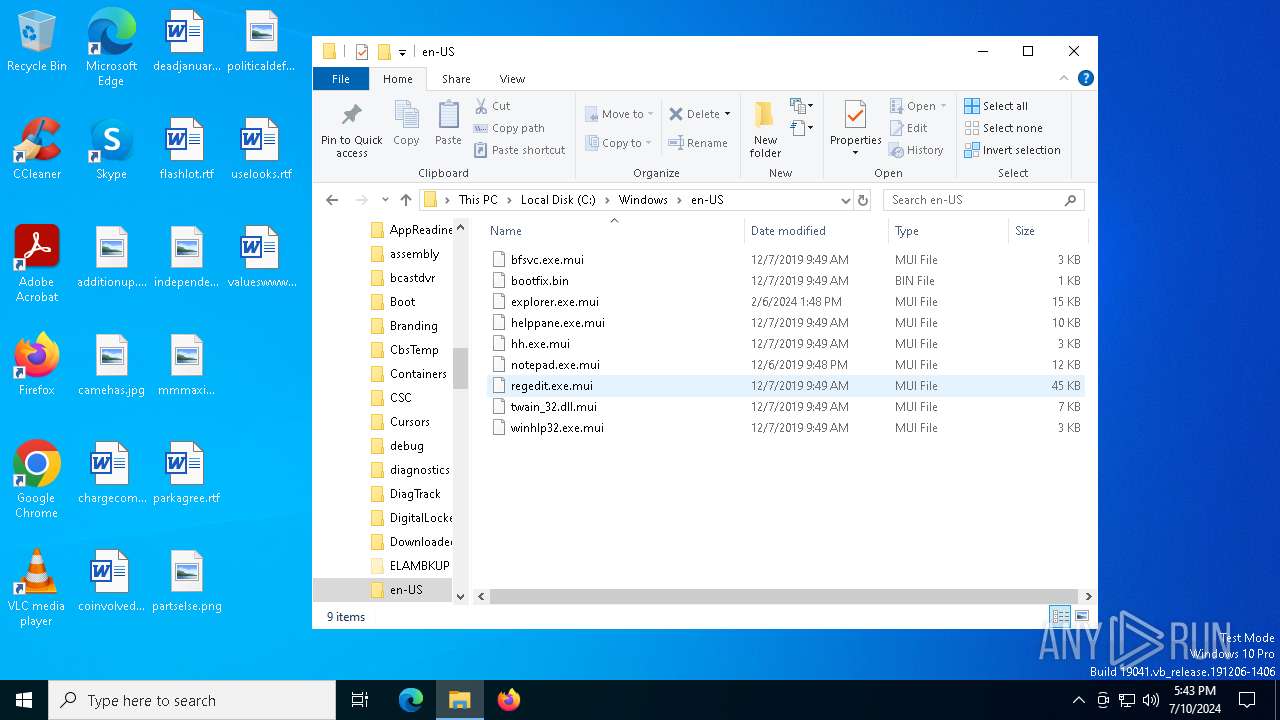
| (PID) Process: | (6444) SkypeApp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast |
| Operation: | write | Name: | ProgramFolder |
Value: C:\Windows\en-US | |||
| (PID) Process: | (6612) wsc_proxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast\properties |
| Operation: | write | Name: | UseRegistry |
Value: 1 | |||
| (PID) Process: | (6612) wsc_proxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast\Wsc |
| Operation: | write | Name: | IWscASStatus |
Value: | |||
| (PID) Process: | (6612) wsc_proxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Avast Software\Avast\Wsc |
| Operation: | write | Name: | IWscAVStatus4 |
Value: | |||
| (PID) Process: | (2972) WerFault.exe | Key: | \REGISTRY\A\{1bd03abe-a23b-a81f-ffa3-2fa15df675ea}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2972) WerFault.exe | Key: | \REGISTRY\A\{1bd03abe-a23b-a81f-ffa3-2fa15df675ea}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
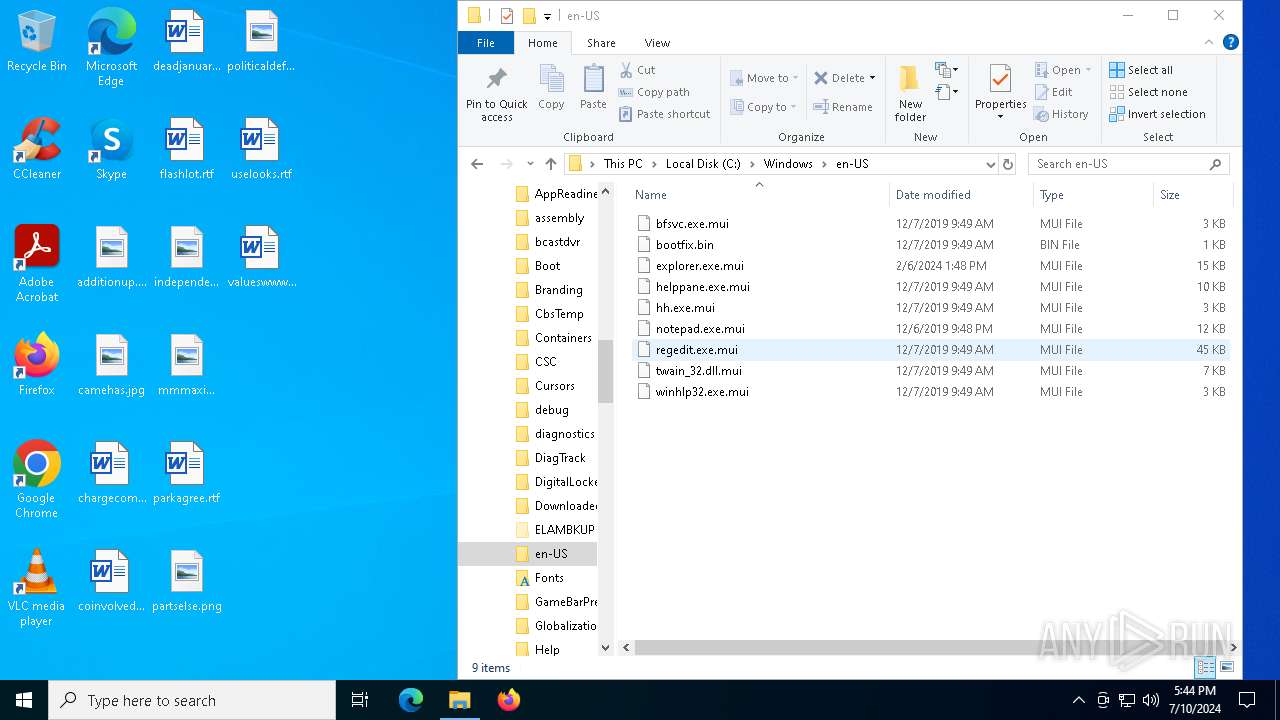
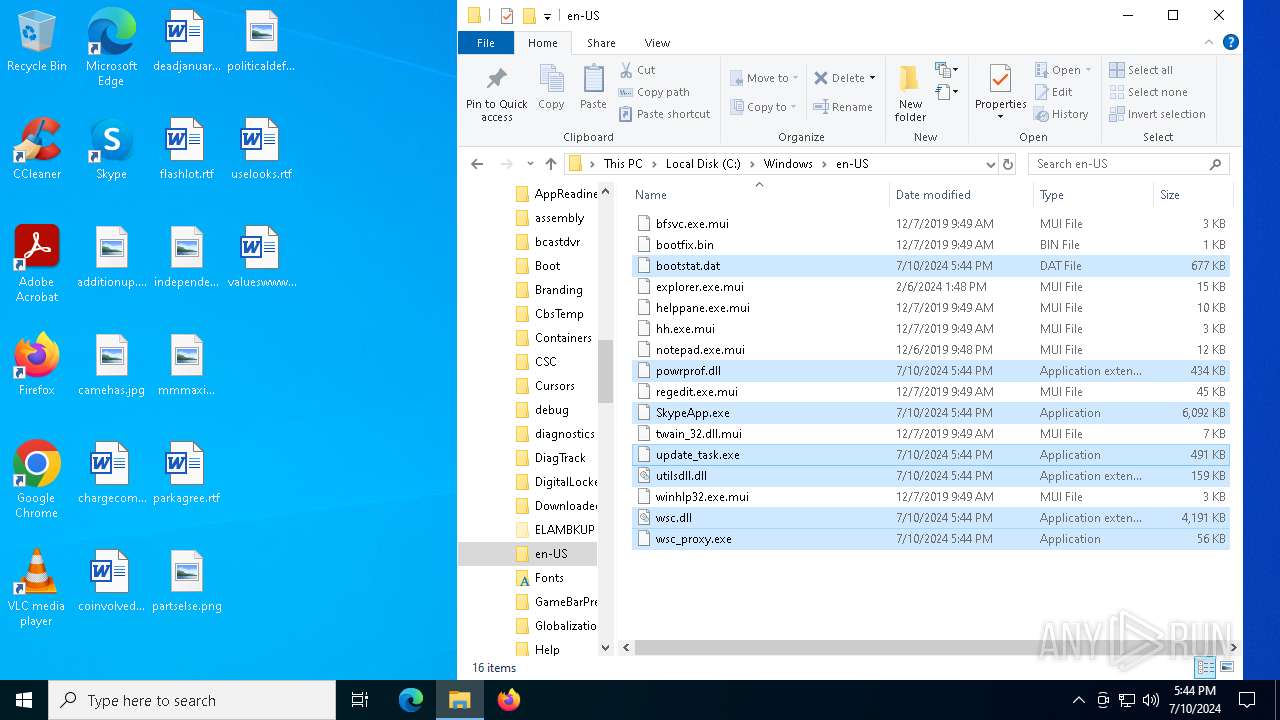
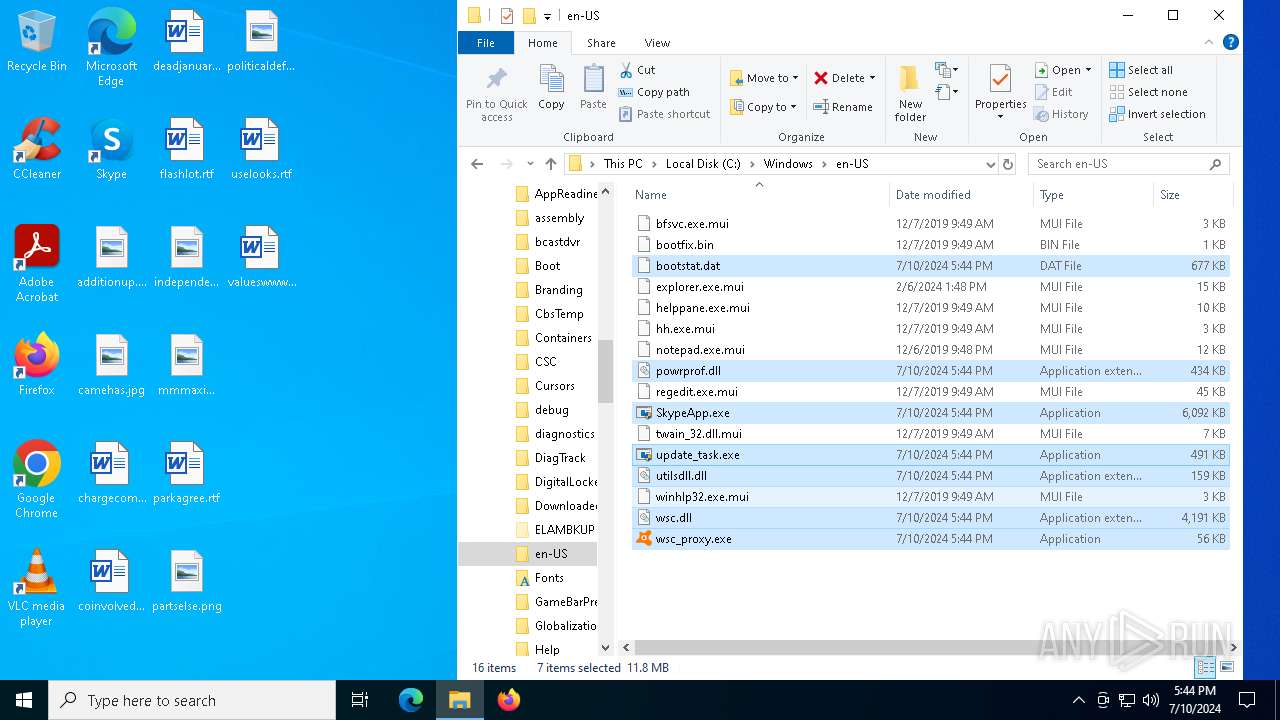
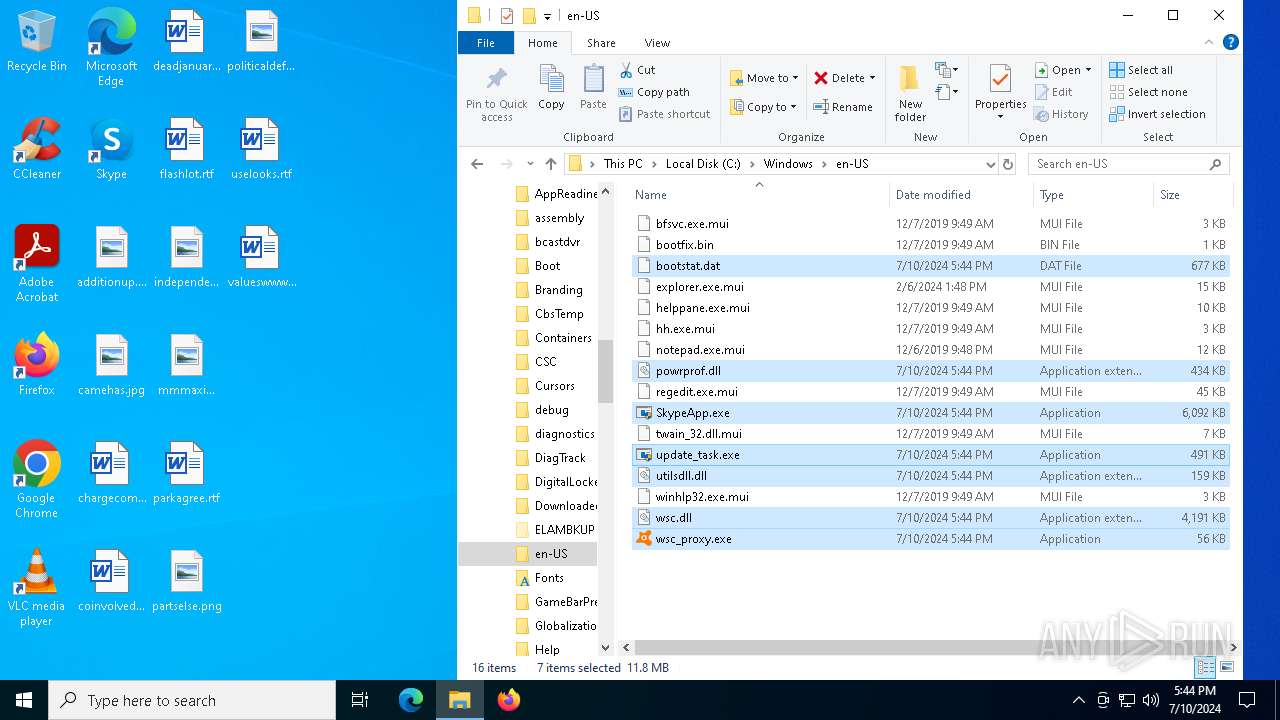
Executable files
6
Suspicious files
5
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_wsc_proxy.exe_8b25899f1fb3d5d2785872911ba1ea1fea2dfb1c_e2da83c0_9e393ef0-562e-41e5-a62e-b5985c08aedd\Report.wer | — | |
MD5:— | SHA256:— | |||
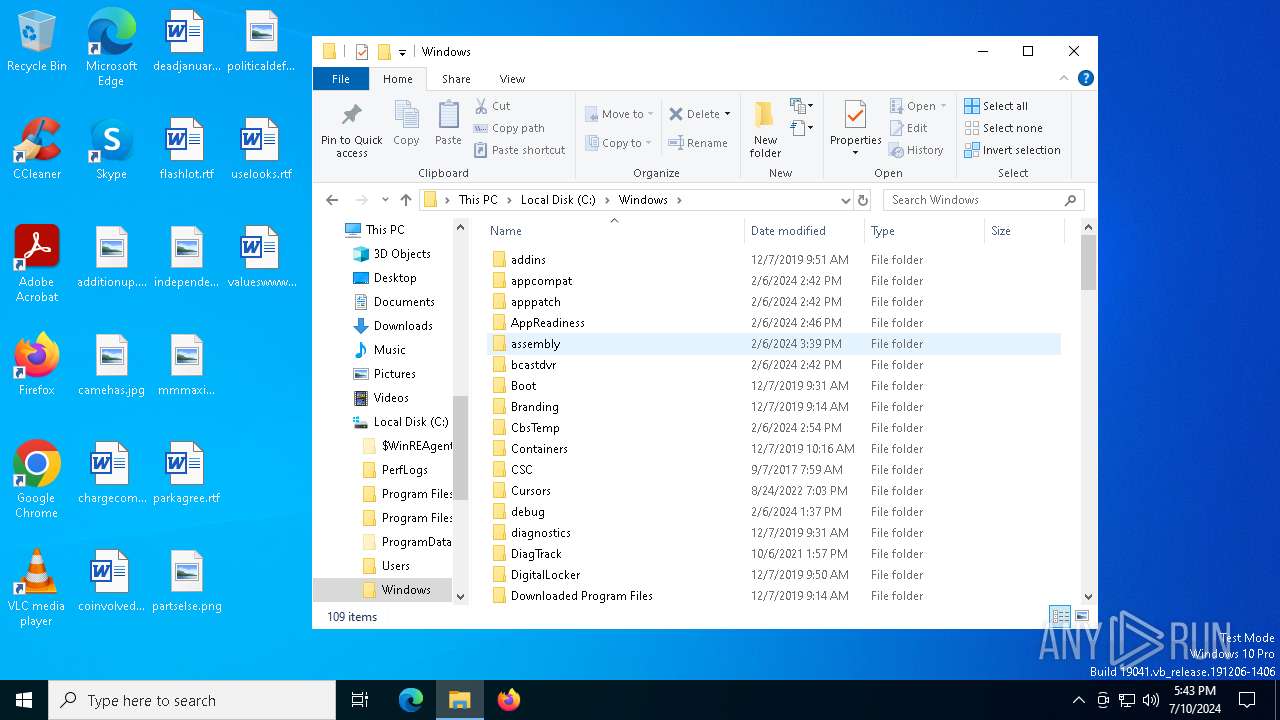
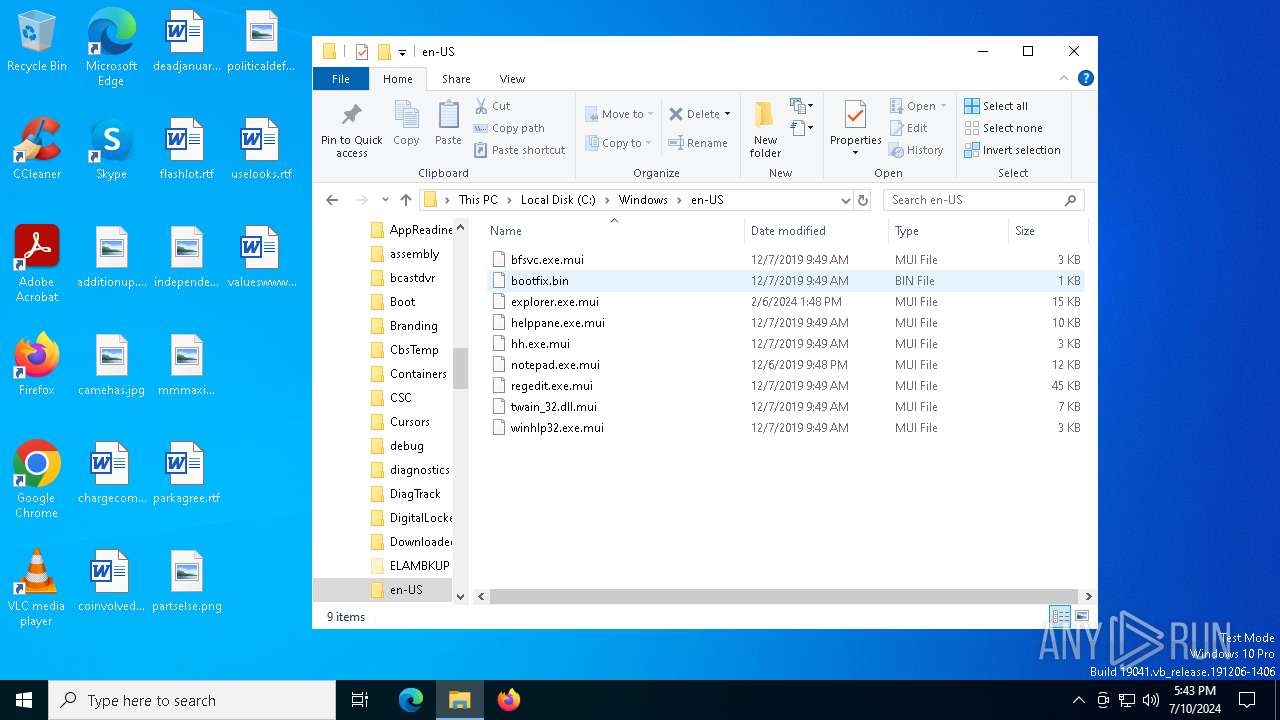
| 6980 | dllhost.exe | C:\Windows\en-US\SkypeApp.exe | executable | |
MD5:C0DCAE518FE65E407FDBB6F2A71B35C7 | SHA256:CB2FF159566E5D73EC3DF5C12ED502648F0F35D1917BEFCE39E9569B09CA4DCD | |||
| 6980 | dllhost.exe | C:\Windows\en-US\bootstat.dat | binary | |
MD5:CD92E4F79851F17ACF0719F3C9C12B39 | SHA256:7A510517252AA94DBD5E0C185F3B42C3AAA87292DA681ECF0B6B755B3C627754 | |||
| 6980 | dllhost.exe | C:\Windows\en-US\utilsdll.dll | executable | |
MD5:88118F697925A8DD74691B714AB8B4C9 | SHA256:E0EDE21DCEE0D47825D7B869395C0805EA9AF2797D1E7CED8F296D55E15DA9A0 | |||
| 6980 | dllhost.exe | C:\Windows\en-US\wsc_proxy.exe | executable | |
MD5:1B231B5C4D36DE4750A587F08338DEDE | SHA256:79E53D36A40951AB328E153BAC9C1E3ADF3330B45899345E645889B9046F06E0 | |||
| 6980 | dllhost.exe | C:\Windows\en-US\wsc.dll | executable | |
MD5:D60E8A632A3FF1F145F84C7231BAA6BD | SHA256:DE820B5E592CF456F6A4F8356195C4A335A51C6354CA7AC32CCD390E62D9BECC | |||
| 6444 | SkypeApp.exe | C:\Windows\en-US\ctx.bin | binary | |
MD5:441077CC9E57554DD476BDFB8B8B8102 | SHA256:B413F47D13EE2FE6C845B2EE141AF81DE858DF4EC549A58B7970BB96645BC8D2 | |||
| 2972 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC449.tmp.WERInternalMetadata.xml | xml | |
MD5:C5142C2249200DBE292AA5CE333A1339 | SHA256:830904333F2087E4937AF1349D5C309B4F064491A6AFC2006FFF2FA1E21C391C | |||
| 6980 | dllhost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:7AFD23CCED1529B2BC33F11B103130ED | SHA256:98E59FFF2EBA8B6361559385740419A80115D403F43CFDD4E0593EA6FB921A63 | |||
| 6612 | wsc_proxy.exe | C:\ProgramData\Avast Software\Avast\log\wsc.log | text | |
MD5:ECAA88F7FA0BF610A5A26CF545DCD3AA | SHA256:F1945CD6C19E56B3C1C78943EF5EC18116907A4CA1EFC40A57D48AB1DB7ADFC5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
80
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | unknown |
1436 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
1272 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
740 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
6176 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | unknown |
6176 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | unknown |
2032 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
2032 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2032 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2052 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3676 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4656 | SearchApp.exe | 92.123.104.43:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1436 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1436 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wsc_proxy.exe | [2024-07-10 17:45:04.721] [error ] [crashguard ] [ 6612: 4600] [E9669F: 103] Dump path 'C:\ProgramData\Avast Software\Avast\log' does not exist. Directory should be already created.
|