| File name: | a4b1ddf4fce066070e4c8c0c7dd8943e76b24f2a59d06f0120ad7649e320ad3e |
| Full analysis: | https://app.any.run/tasks/7a6e7d92-62de-4fdc-8ed7-81bda31c3072 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 15:20:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
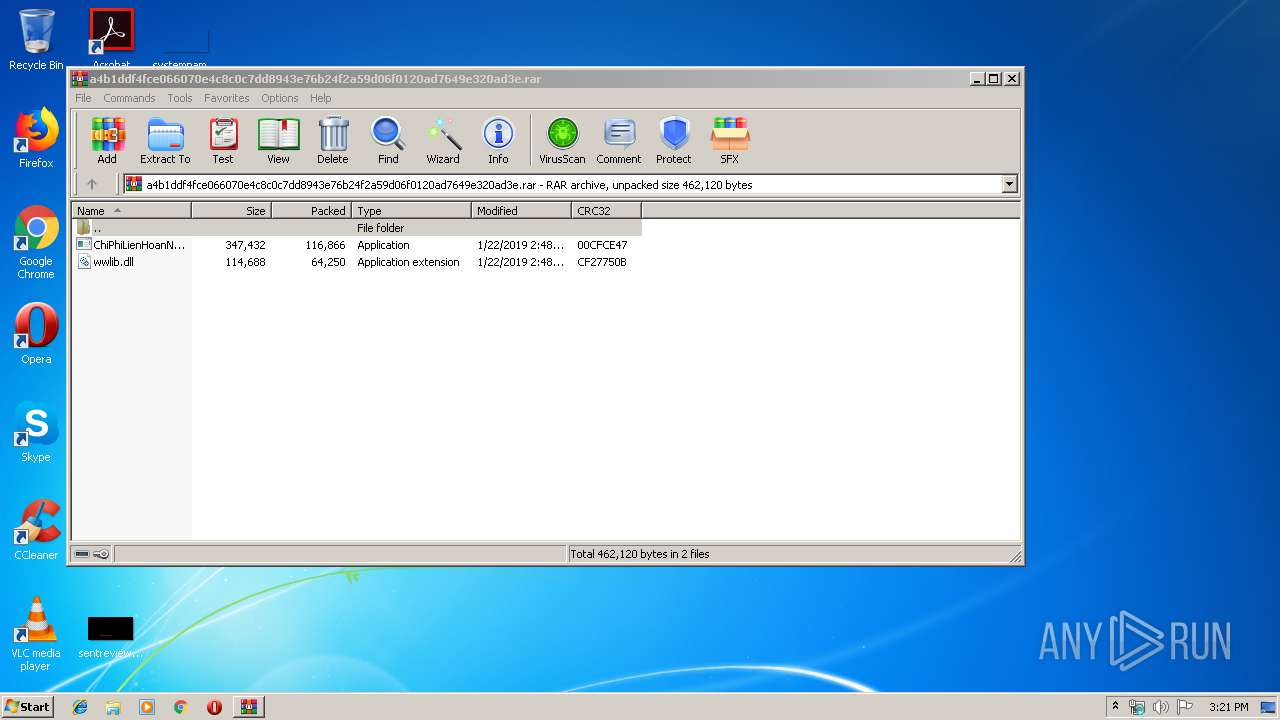
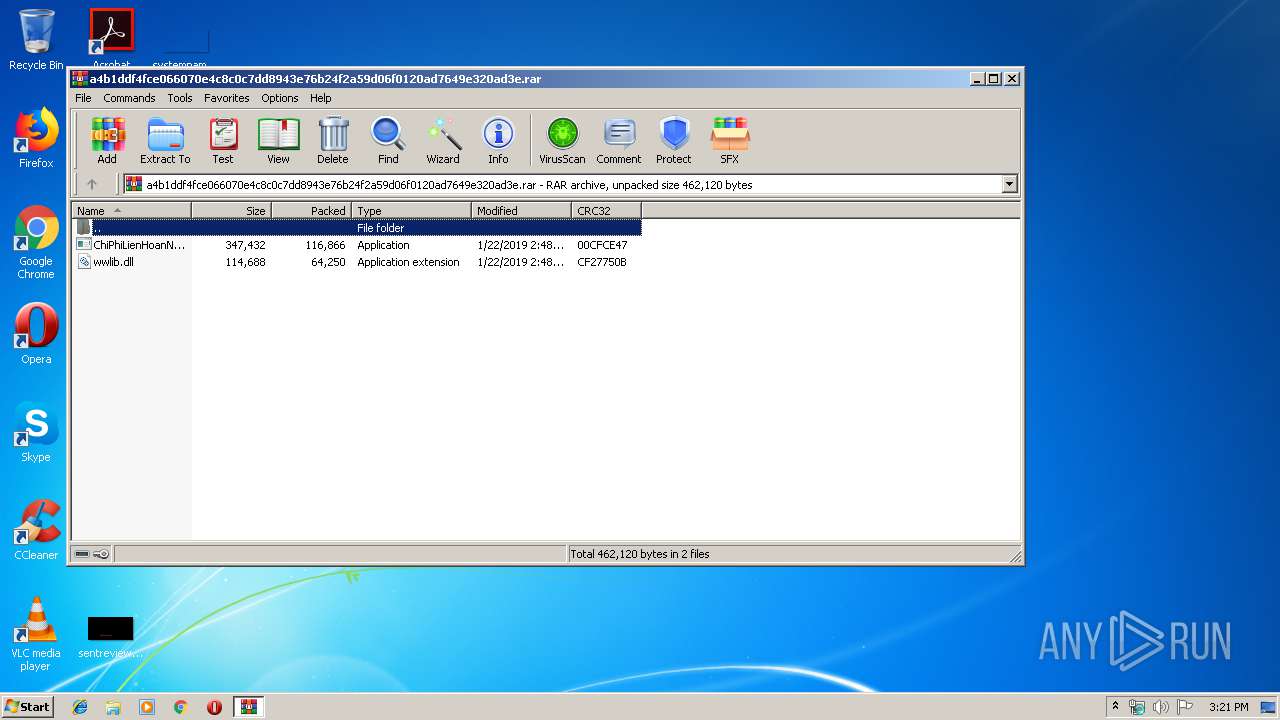
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2D3FB8D5B4CEFC9660D98E0AD46FF91A |
| SHA1: | 72ADE38861DAC1A720CA1F4E82B445E4F4379FE0 |
| SHA256: | A4B1DDF4FCE066070E4C8C0C7DD8943E76B24F2A59D06F0120AD7649E320AD3E |
| SSDEEP: | 3072:aIWzdBu9+0ZZHmdGHQgracn2mc9DXDmUpEJC6I6kD7kKdYc0+qXWC2n0Lkh:aIkjX0ZZHmd/Ujnzc9DXCxJCNDmsqXvG |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 752)
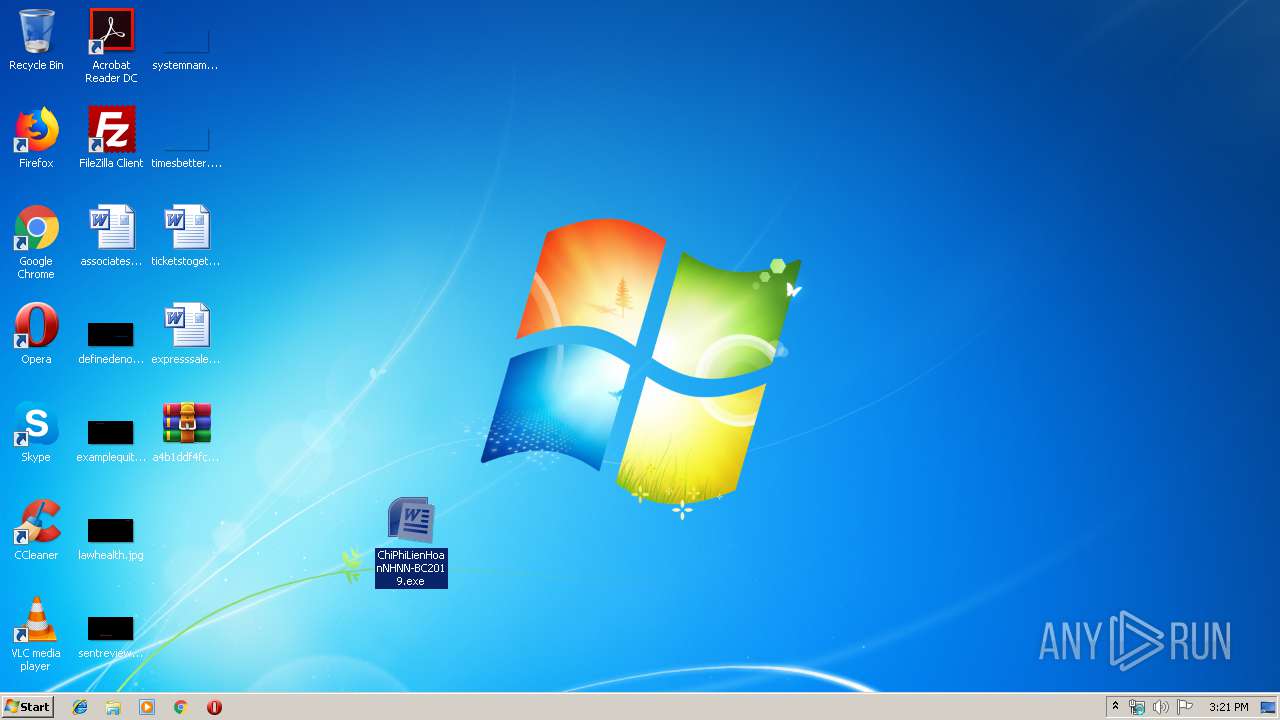
- ChiPhiLienHoanNHNN-BC2019.exe (PID: 2224)
Application was dropped or rewritten from another process
- ChiPhiLienHoanNHNN-BC2019.exe (PID: 2224)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2468)
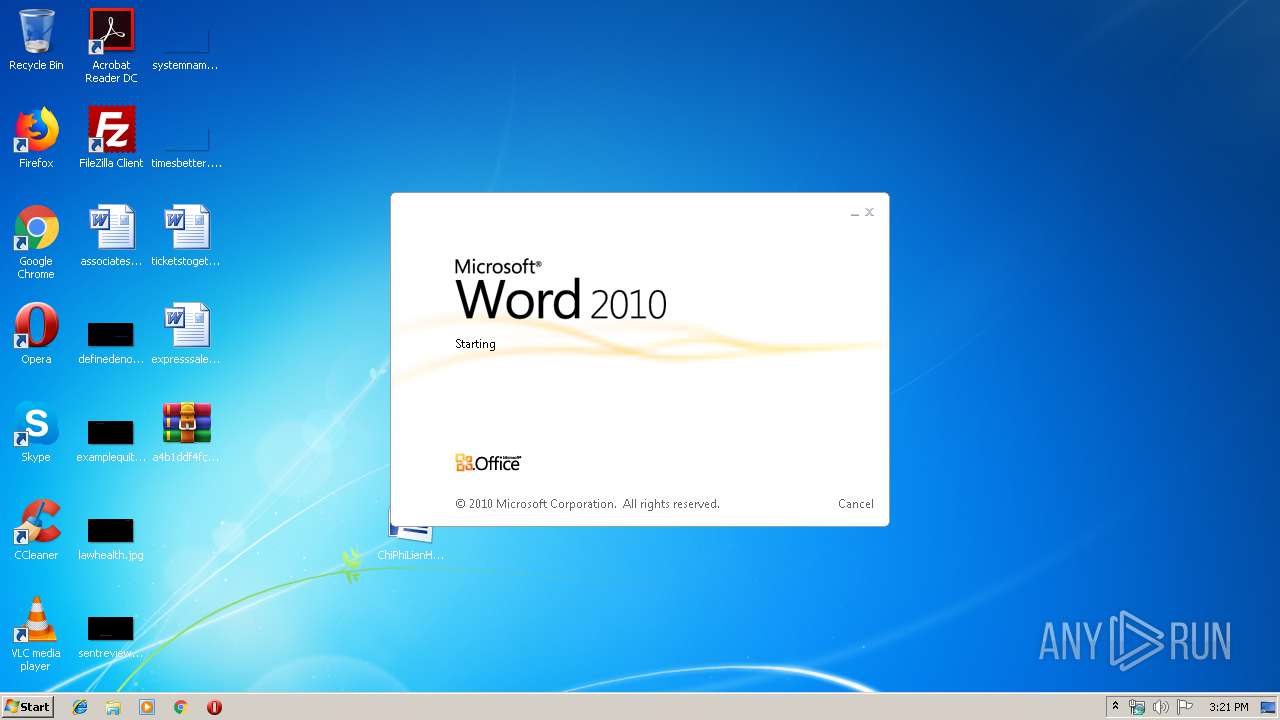
Starts Microsoft Office Application
- ChiPhiLienHoanNHNN-BC2019.exe (PID: 2224)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3780)
Creates files in the user directory
- WINWORD.EXE (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
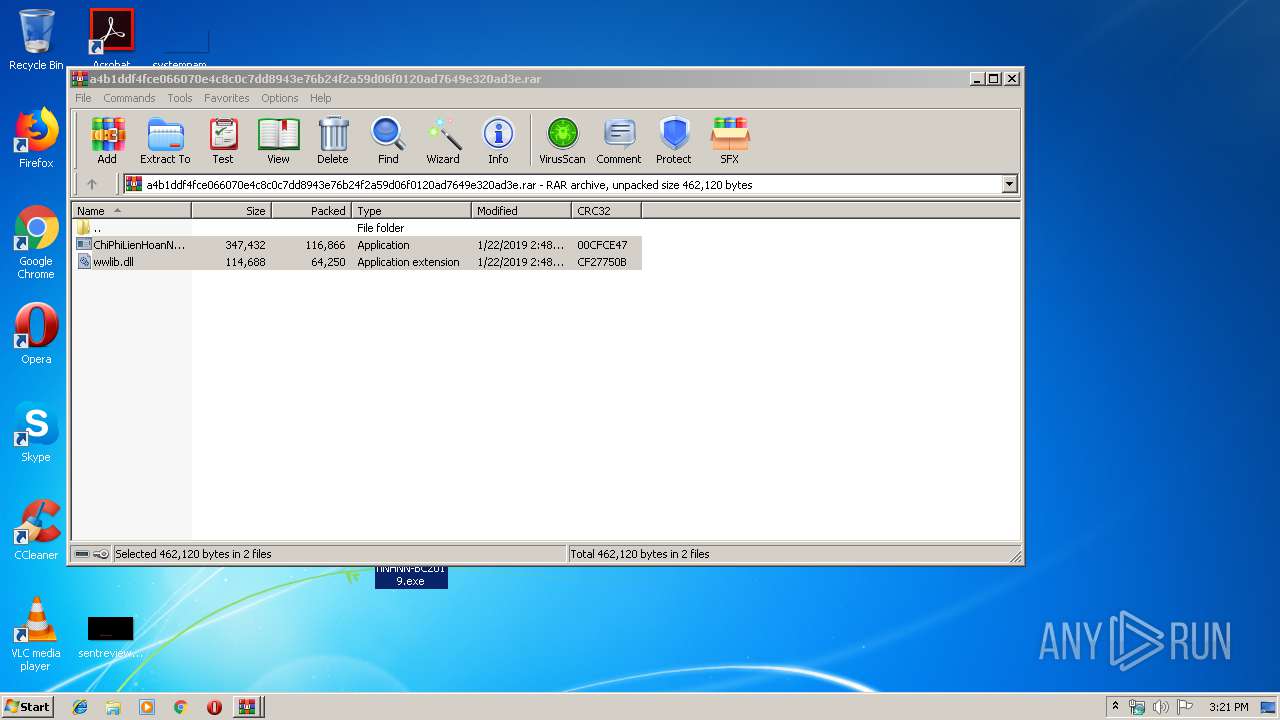
| 2224 | "C:\Users\admin\Desktop\ChiPhiLienHoanNHNN-BC2019.exe" | C:\Users\admin\Desktop\ChiPhiLienHoanNHNN-BC2019.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Word Exit code: 3221225477 Version: 12.0.4518.1014 Modules
| |||||||||||||||
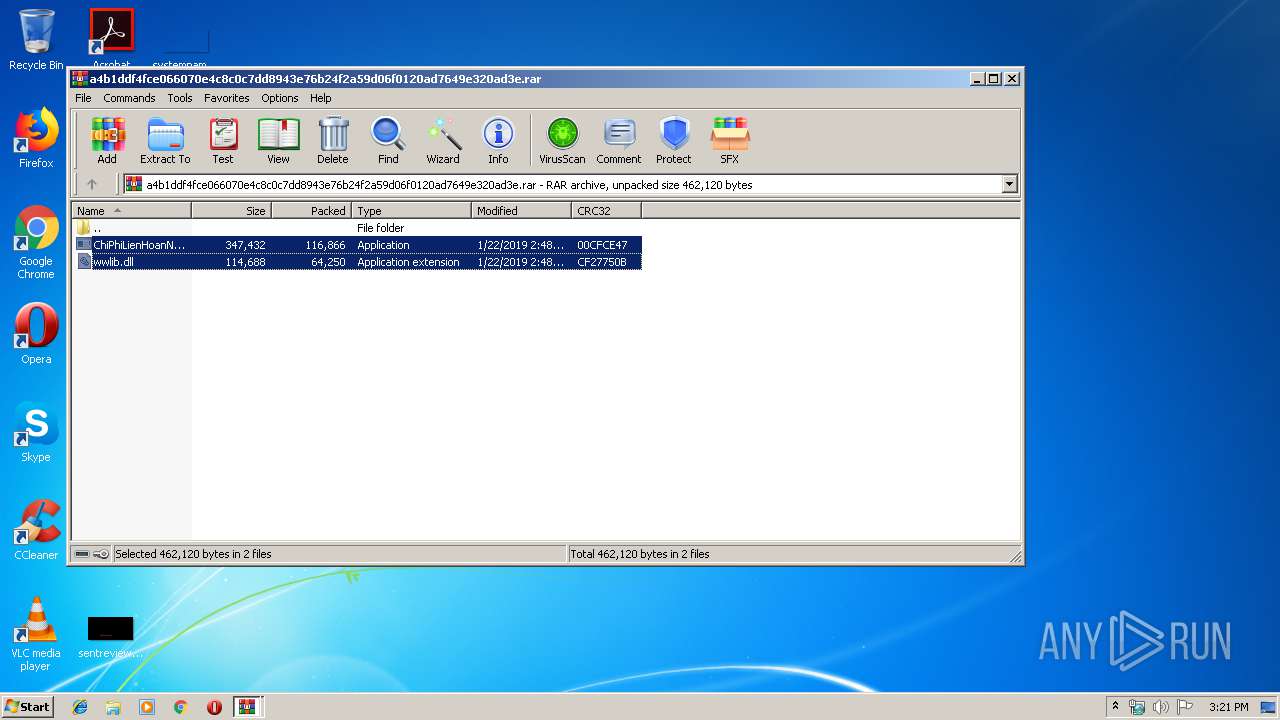
| 2468 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\a4b1ddf4fce066070e4c8c0c7dd8943e76b24f2a59d06f0120ad7649e320ad3e.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\a4b1ddf4fce066070e4c8c0c7dd8943e76b24f2a59d06f0120ad7649e320ad3e.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3780 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ChiPhiLienHoan.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | ChiPhiLienHoanNHNN-BC2019.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 388
Read events
1 717
Write events
666
Delete events
5
Modification events
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\a4b1ddf4fce066070e4c8c0c7dd8943e76b24f2a59d06f0120ad7649e320ad3e.rar | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
2
Suspicious files
1
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3780 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR66DA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3780 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso696B.tmp | — | |
MD5:— | SHA256:— | |||
| 3780 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$iPhiLienHoan.docx | pgc | |
MD5:— | SHA256:— | |||
| 2468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2468.19103\wwlib.dll | executable | |
MD5:— | SHA256:— | |||
| 2224 | ChiPhiLienHoanNHNN-BC2019.exe | C:\Users\admin\AppData\Local\Temp\ChiPhiLienHoan.docx | document | |
MD5:— | SHA256:— | |||
| 3780 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3780 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3780 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0c09.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2468.19103\ChiPhiLienHoanNHNN-BC2019.exe | executable | |
MD5:CEAA5817A65E914AA178B28F12359A46 | SHA256:6C959CFB001FBB900958441DFD8B262FB33E052342948BAB338775D3E83EF7F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
office.allsafebrowsing.com |
| unknown |