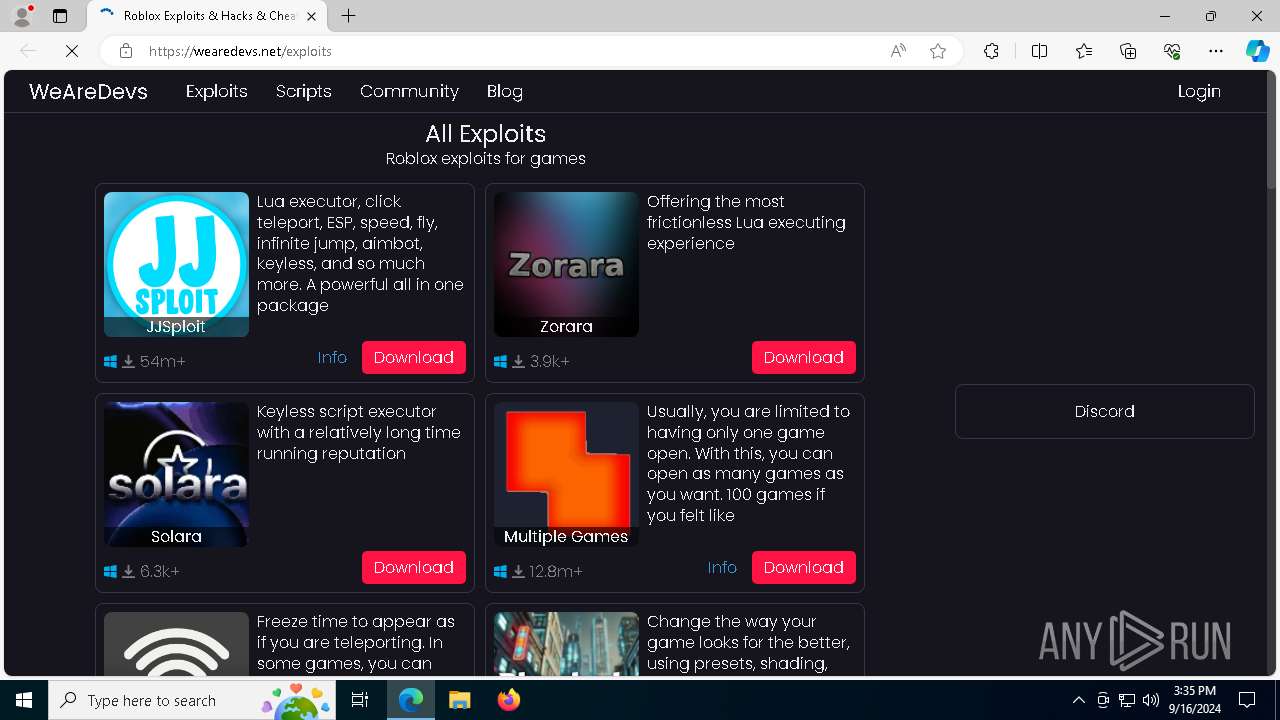
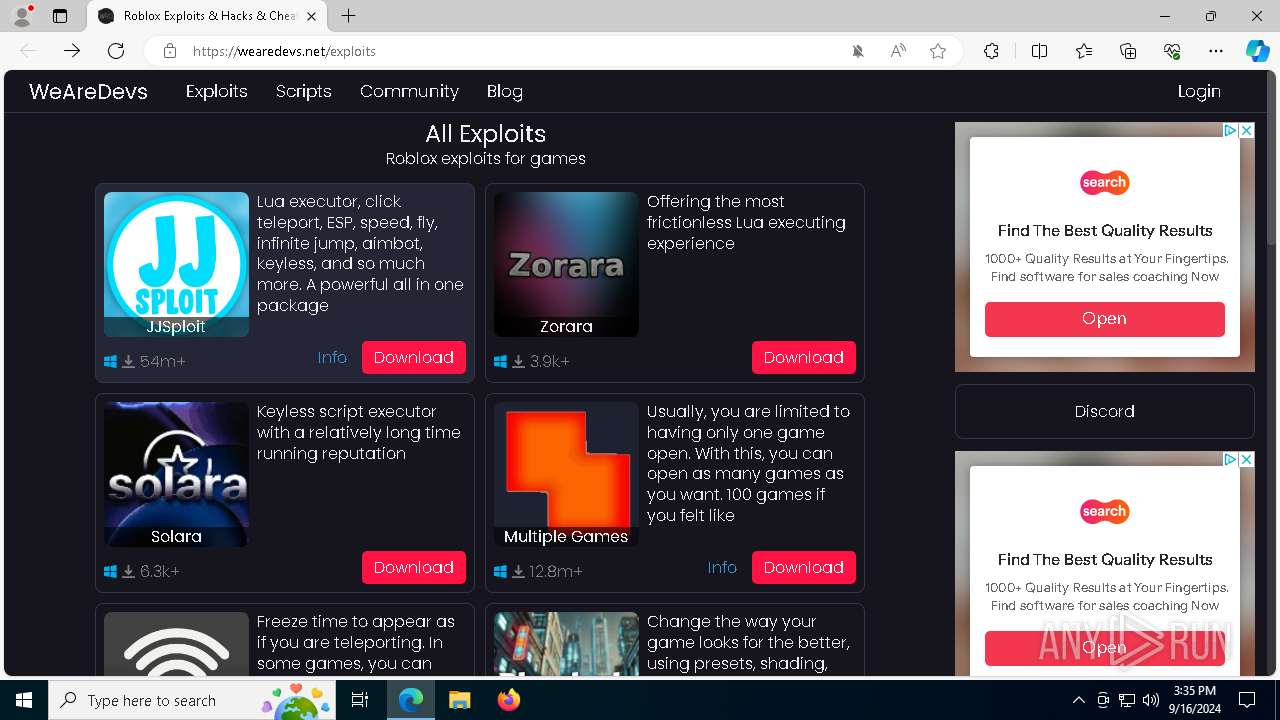
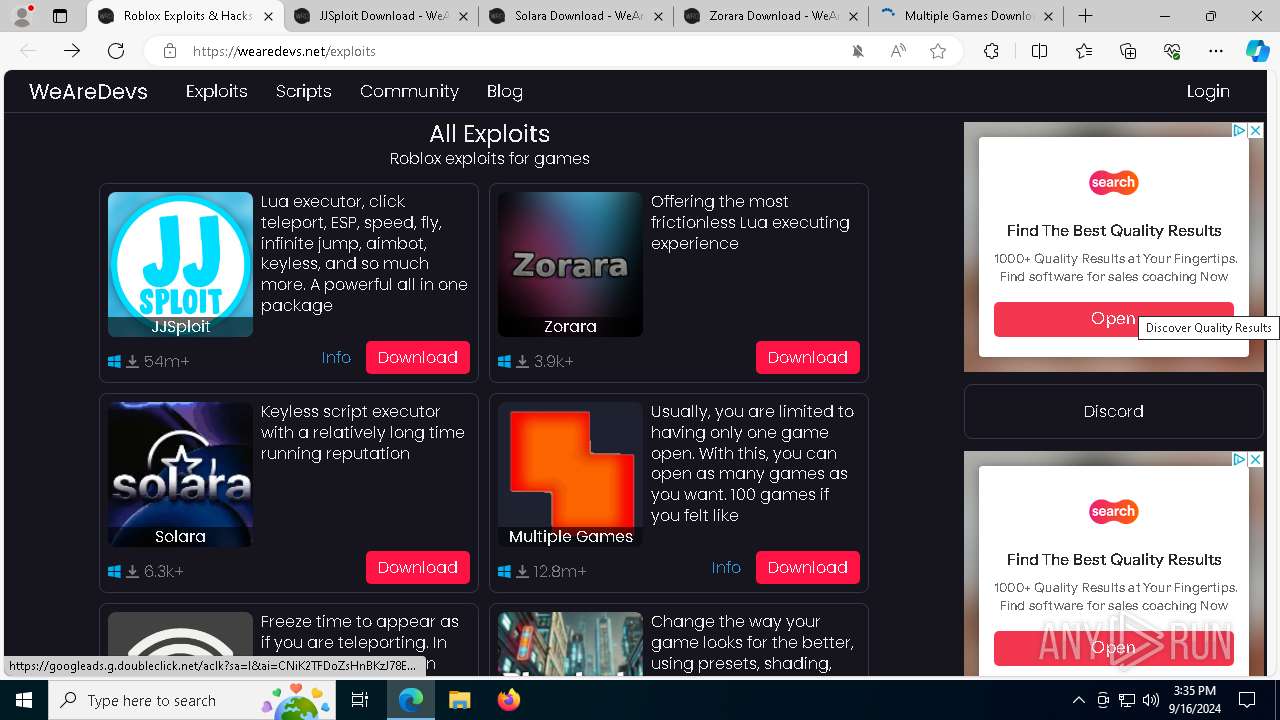
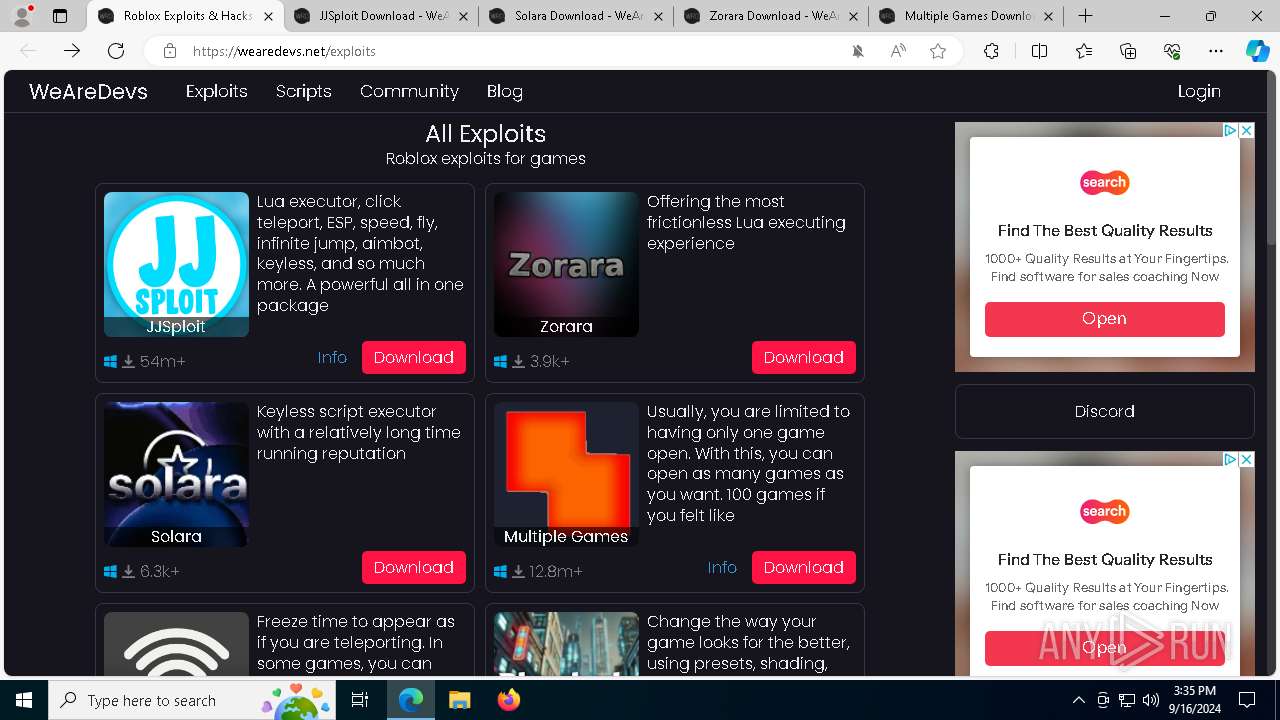
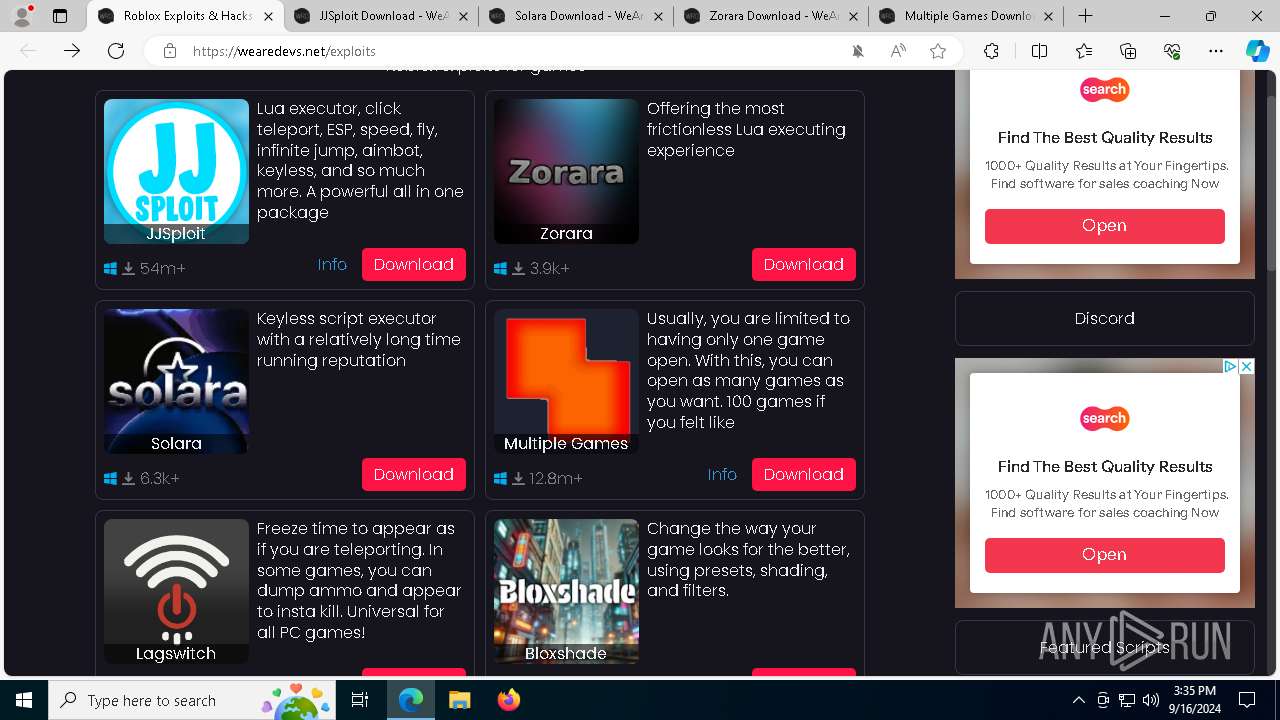
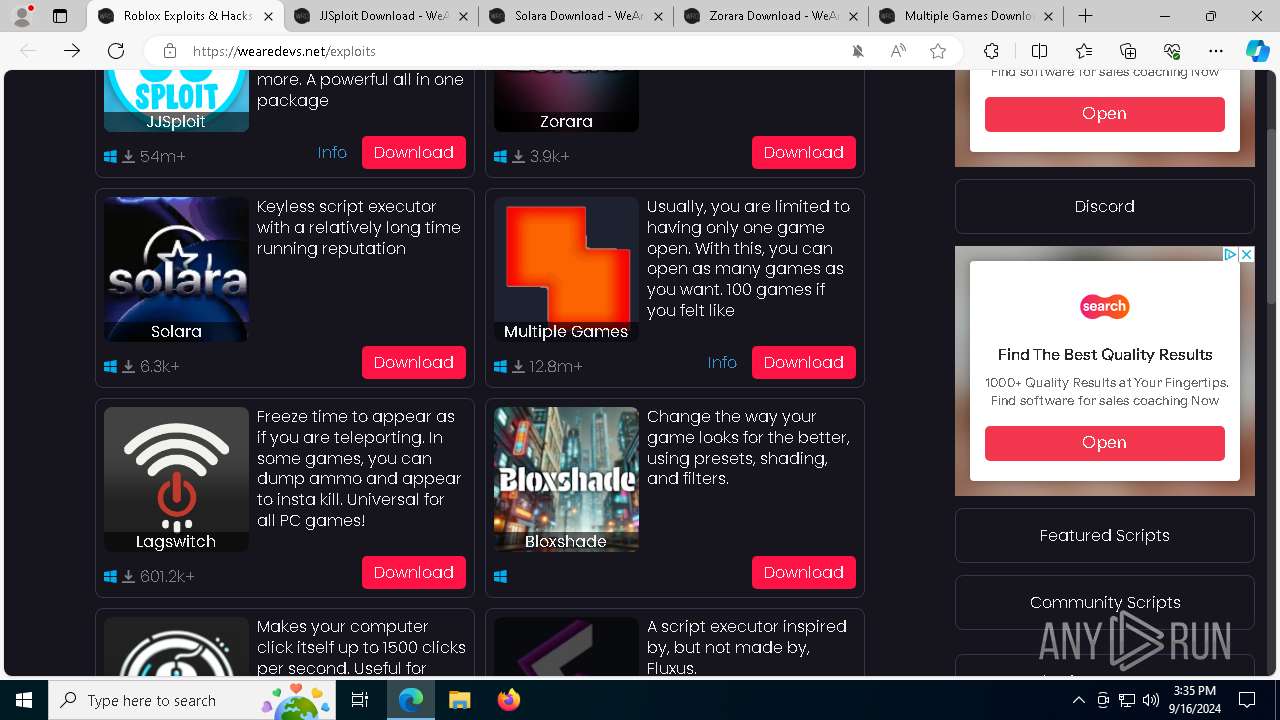
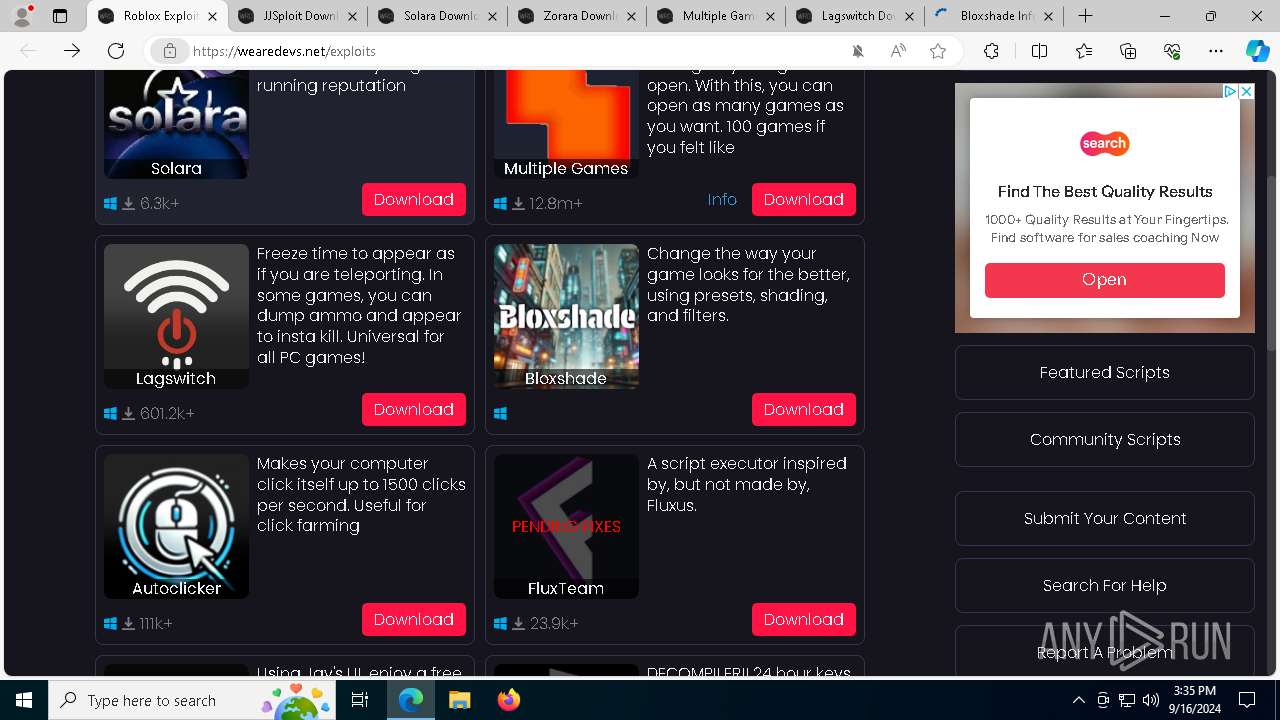
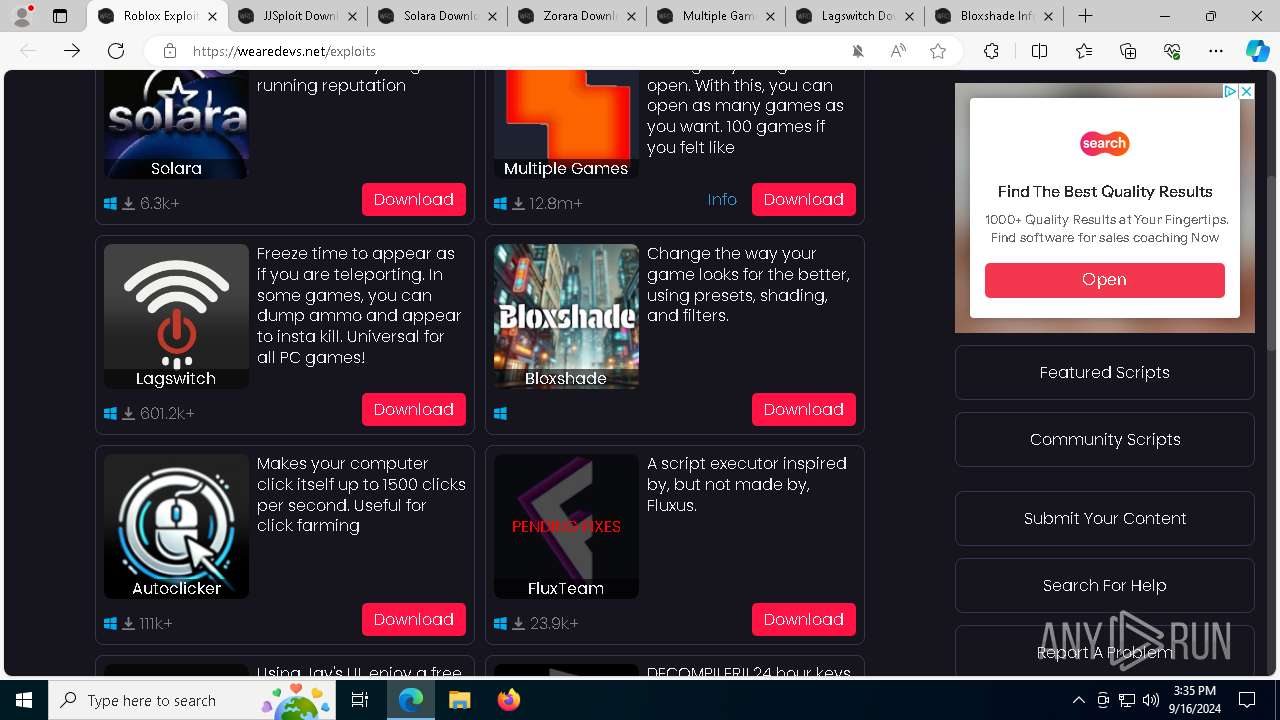
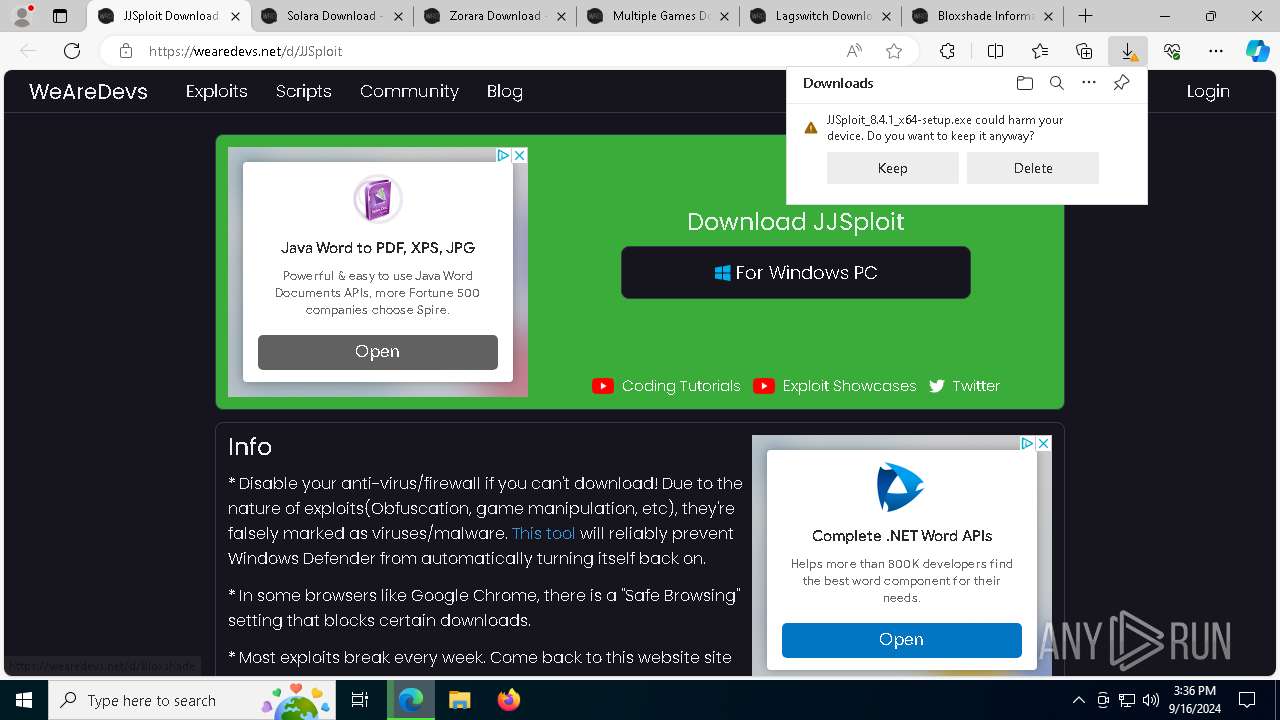
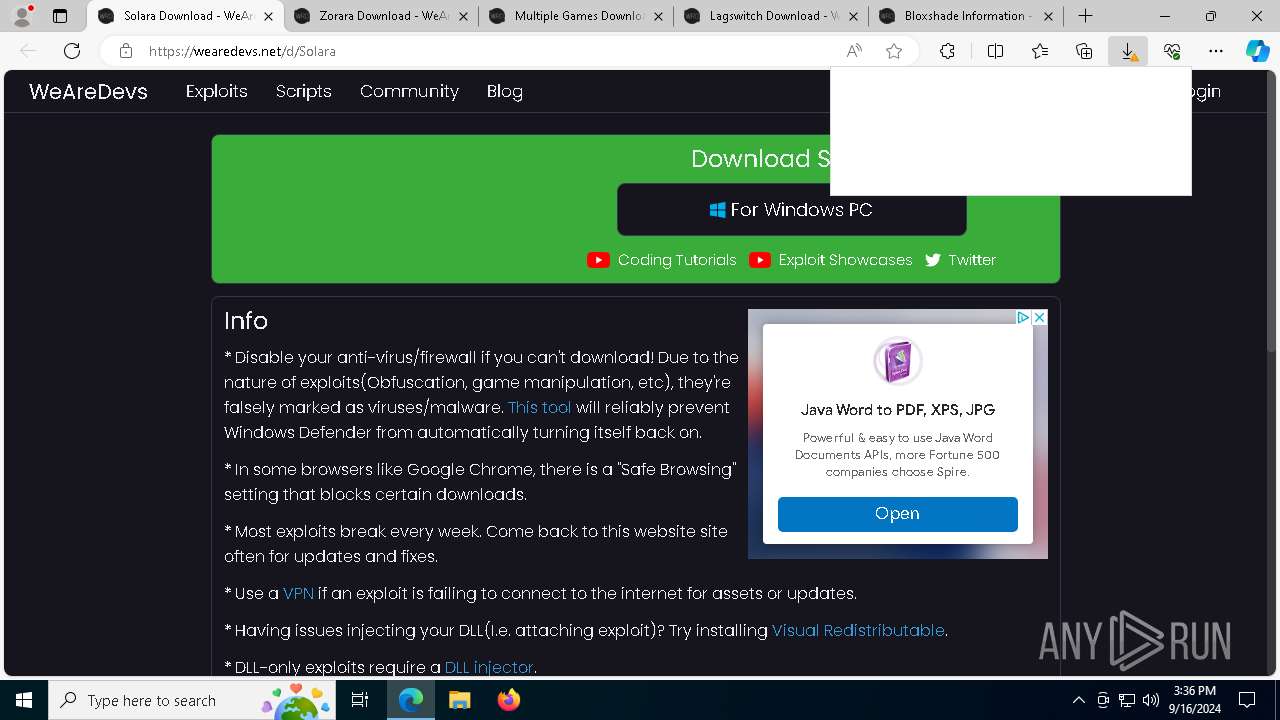
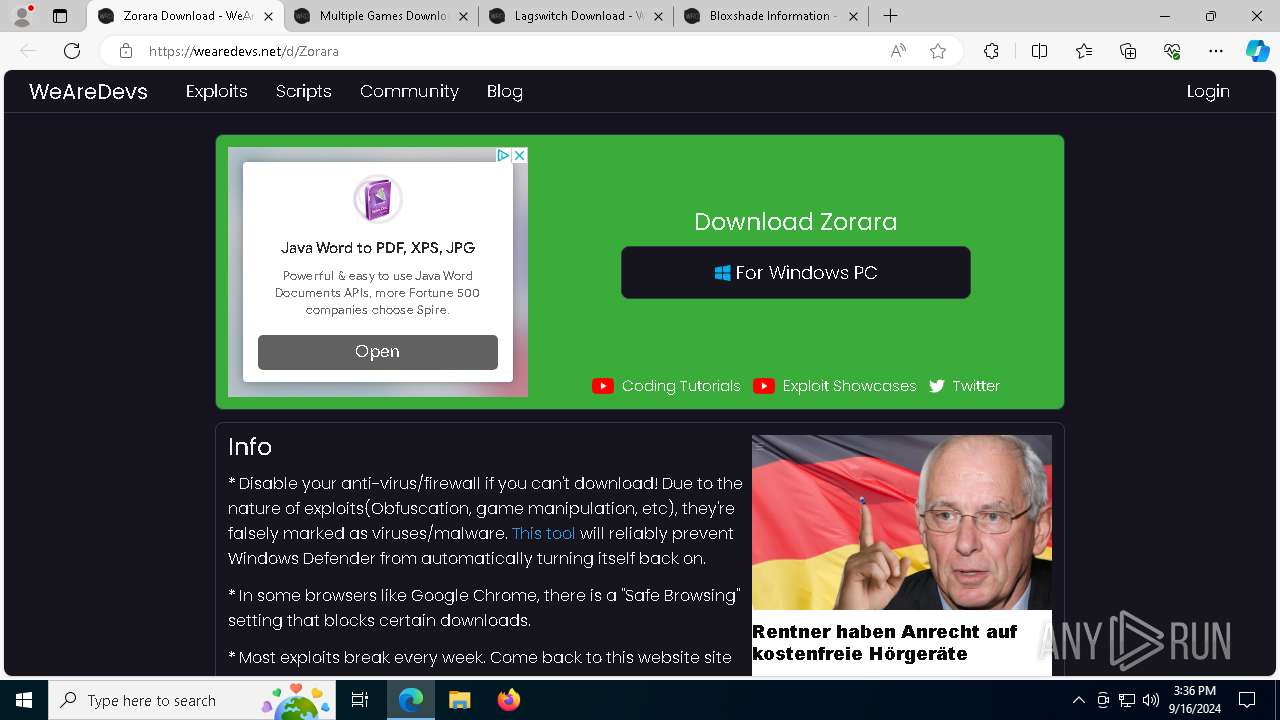
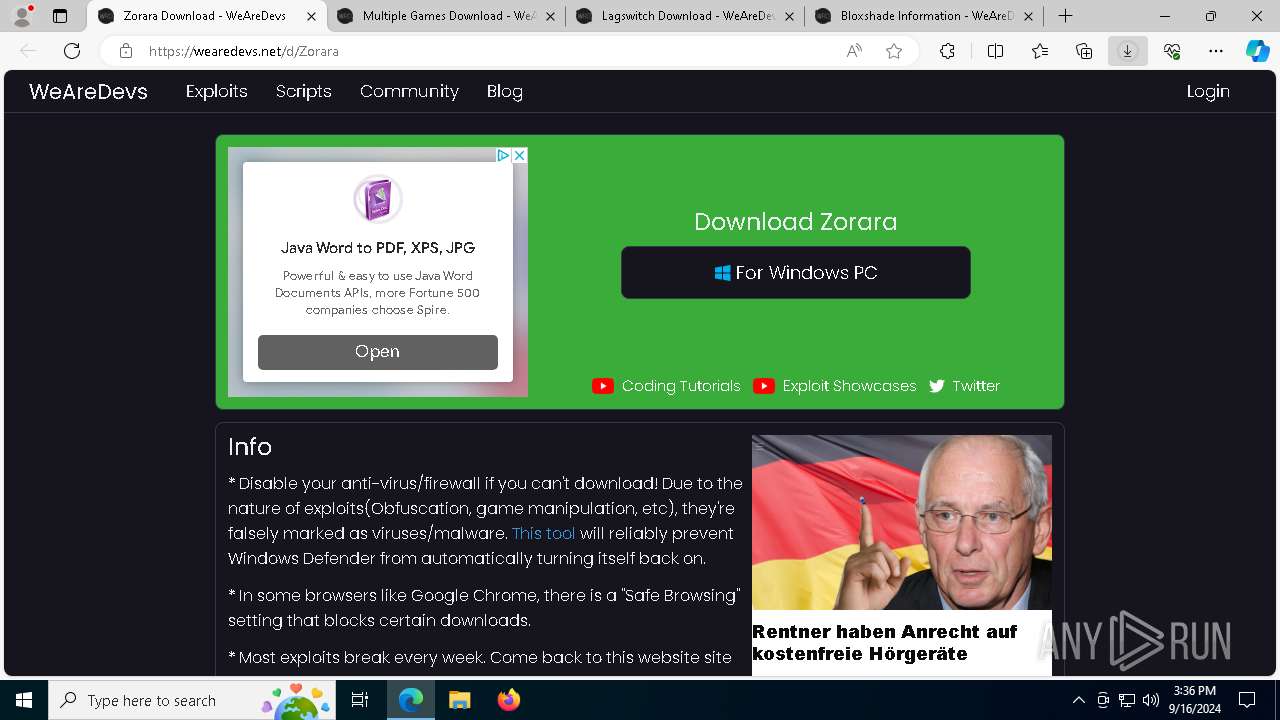
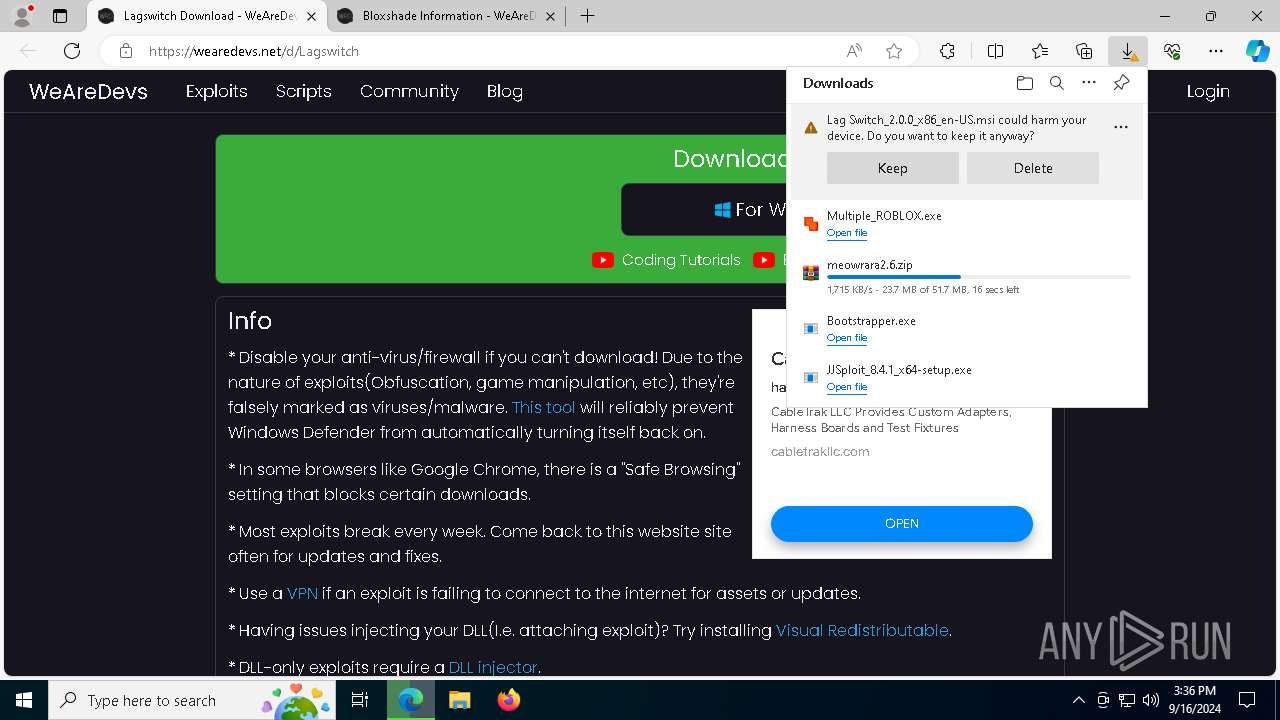
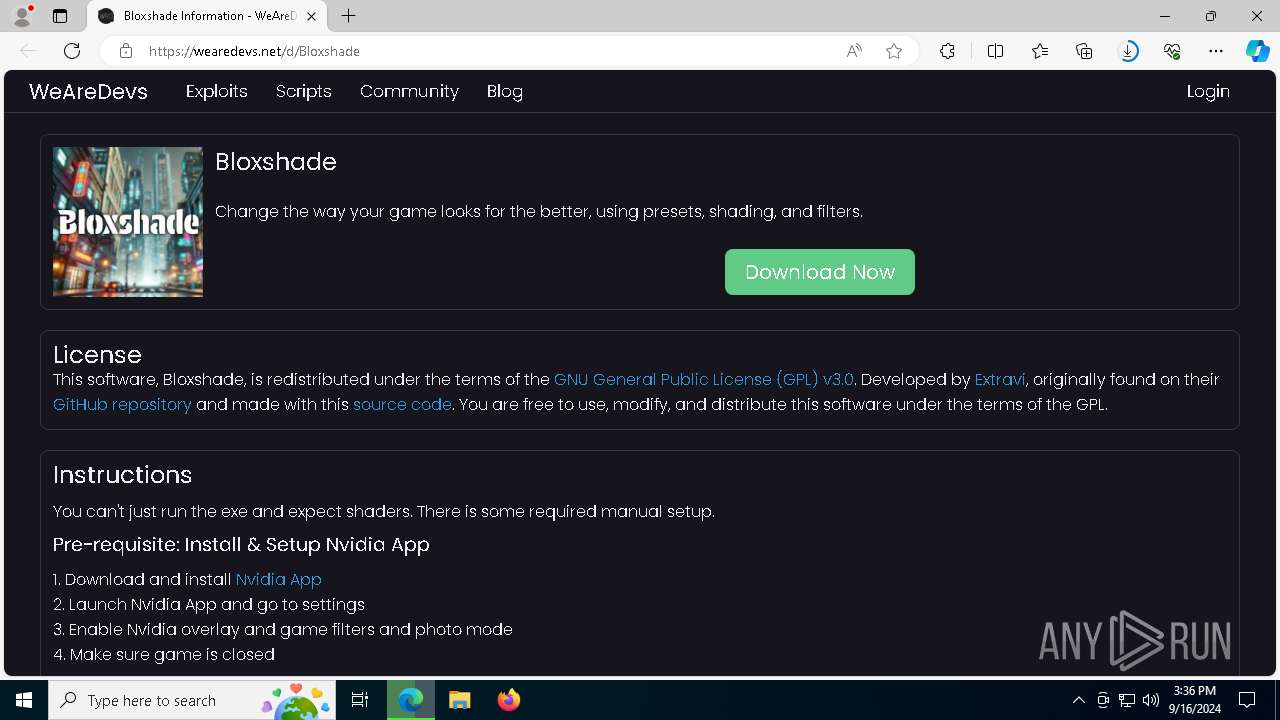
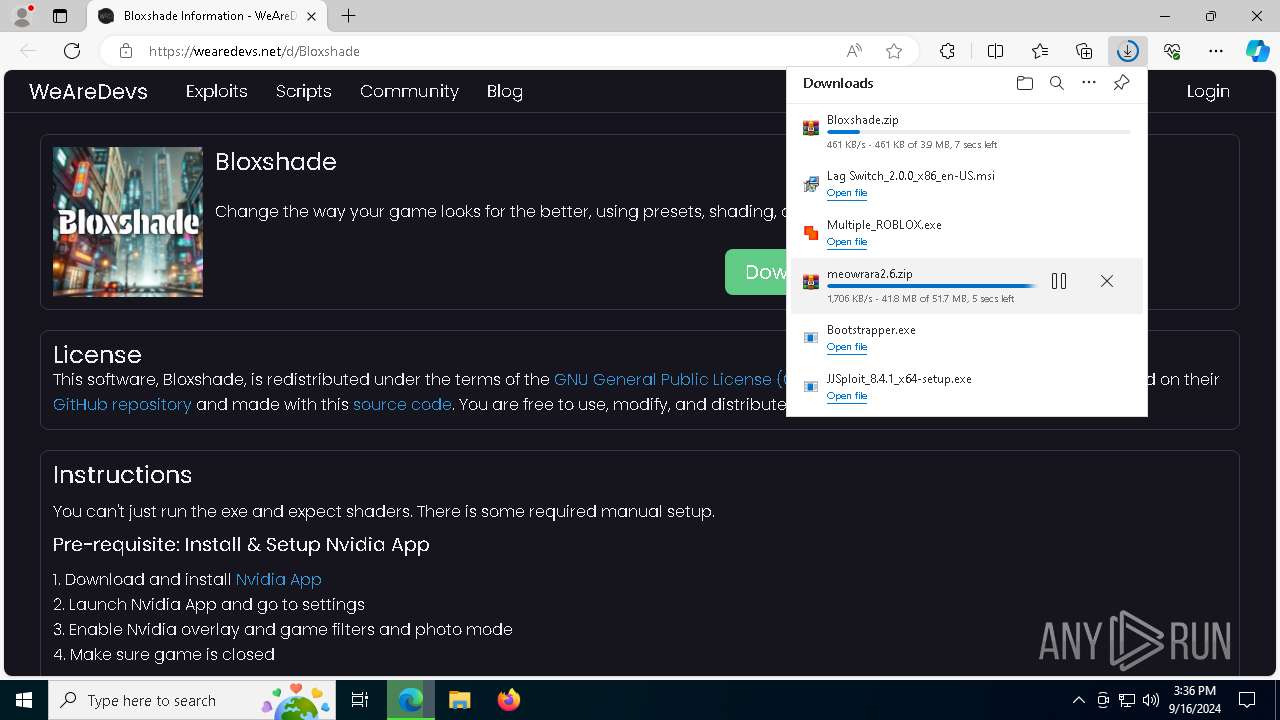
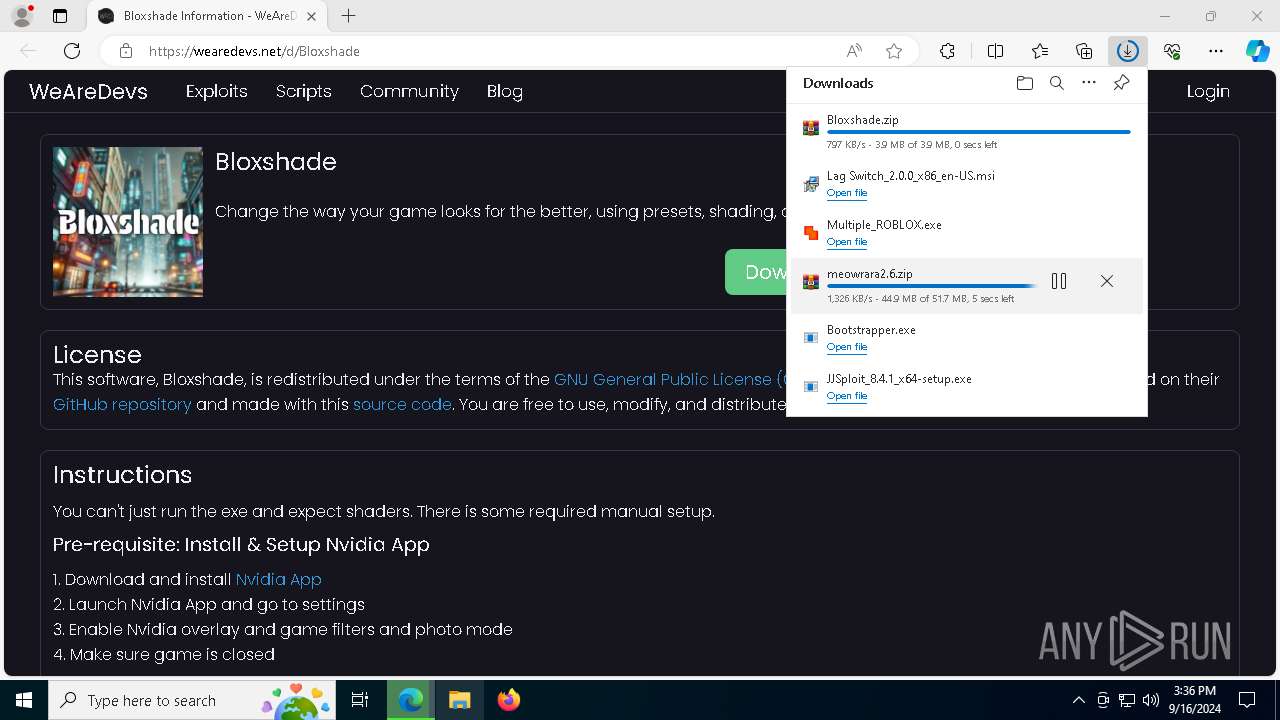
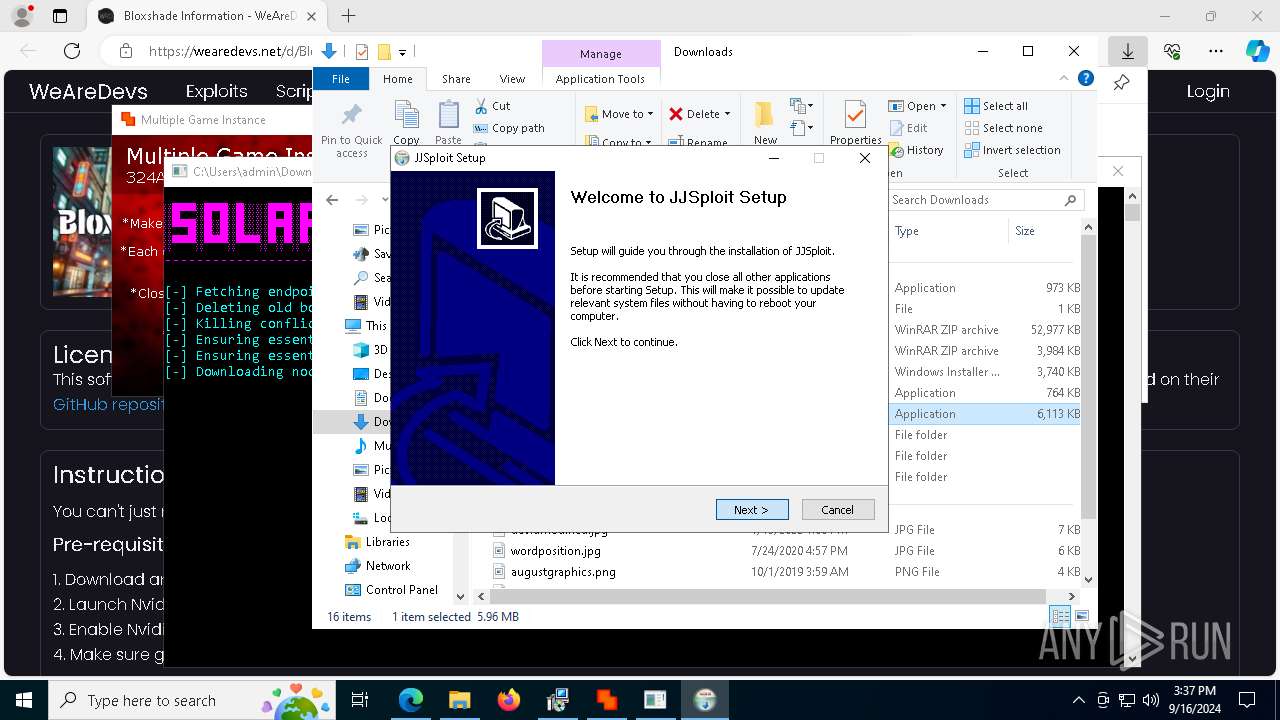
| URL: | wearedevs.net |
| Full analysis: | https://app.any.run/tasks/a08397d5-4a73-4071-8043-3c7242f4e2ef |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2024, 15:35:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7CD7530FFC18EECF81E924A5A2EA37DE |
| SHA1: | BA76E6E6B0B5DCD1AA30700F7EF36377458F7F39 |
| SHA256: | A4ABBB8EB051F9B4E769CD66297609E1C2C3A698C36718A6BE616C49B5BECCED |
| SSDEEP: | 3:b2pn:wn |
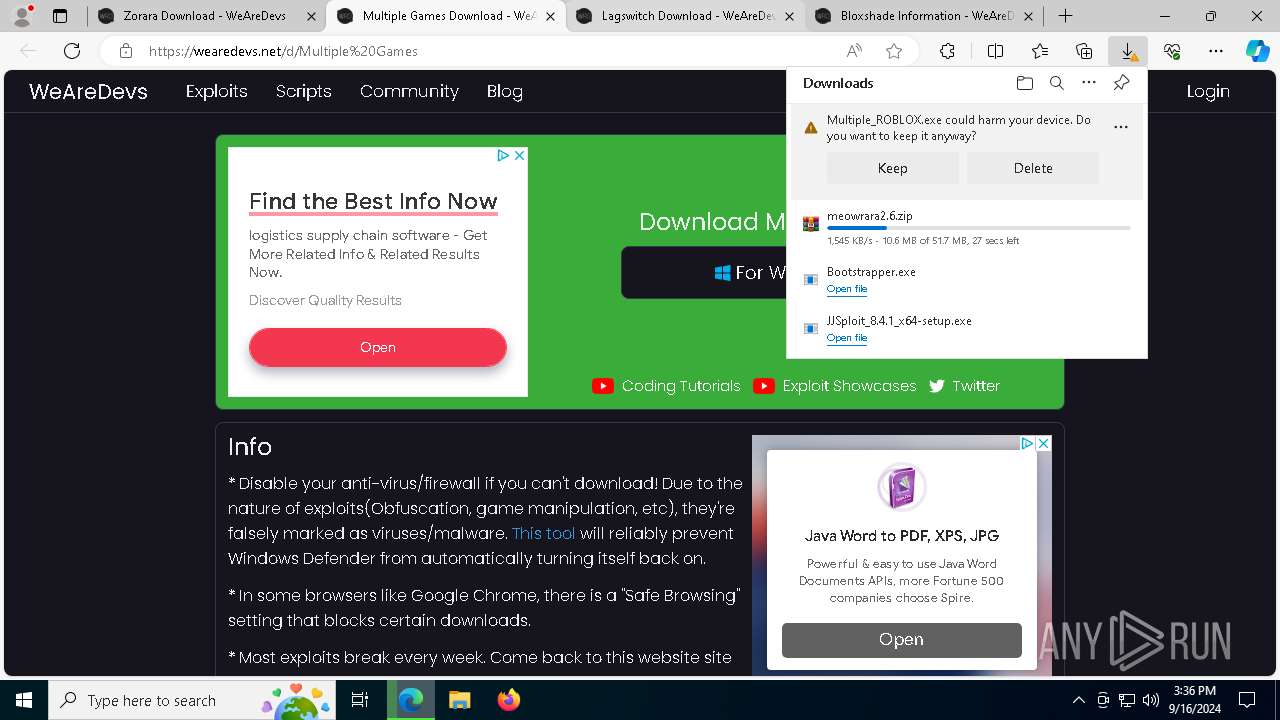
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7416)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 7340)
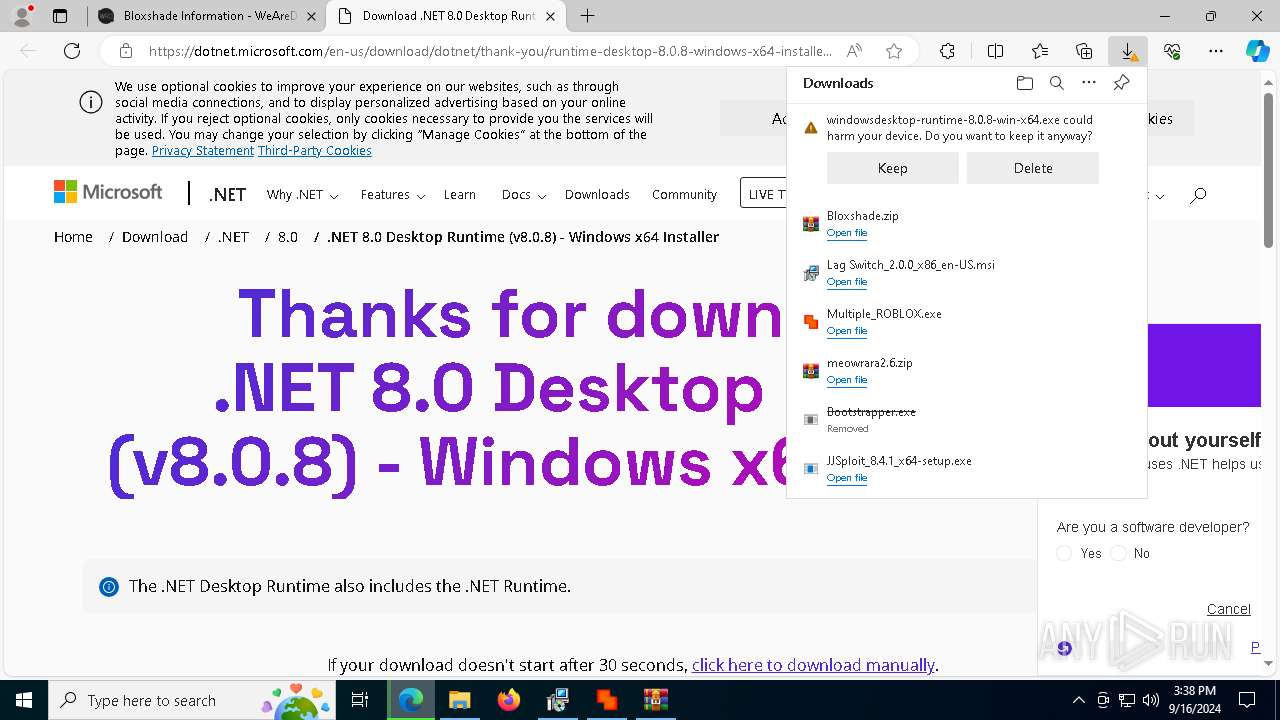
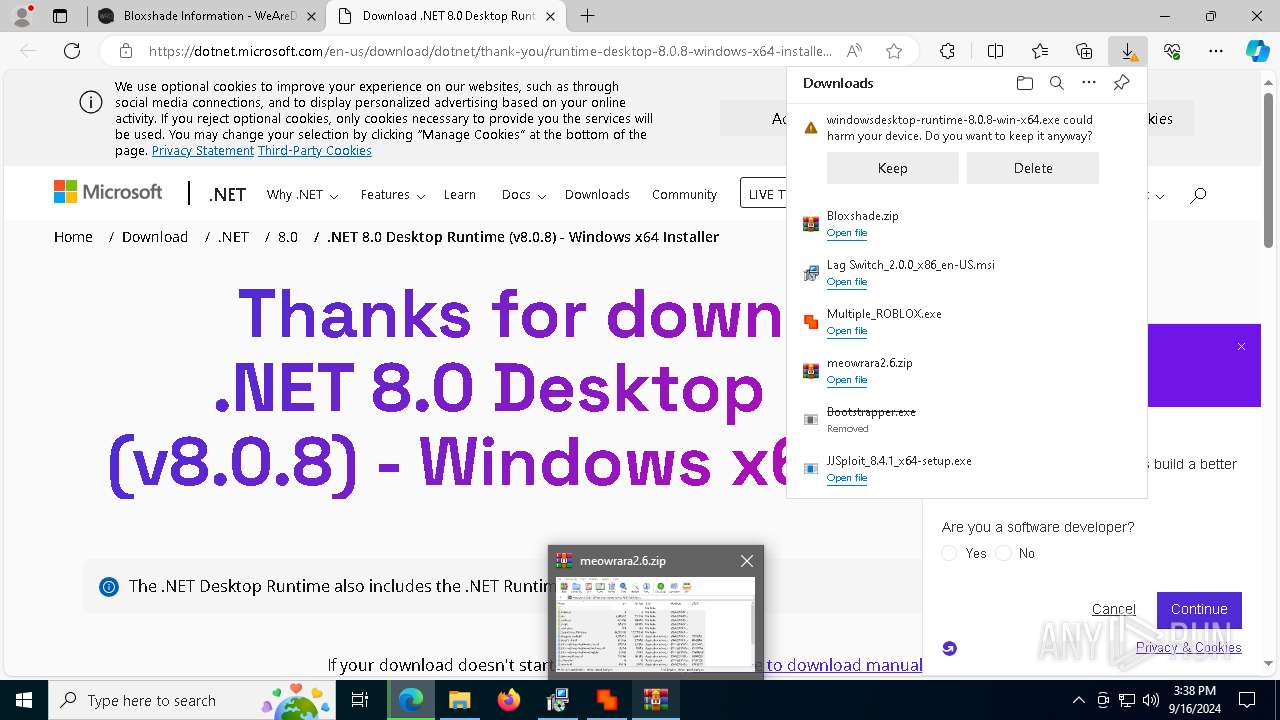
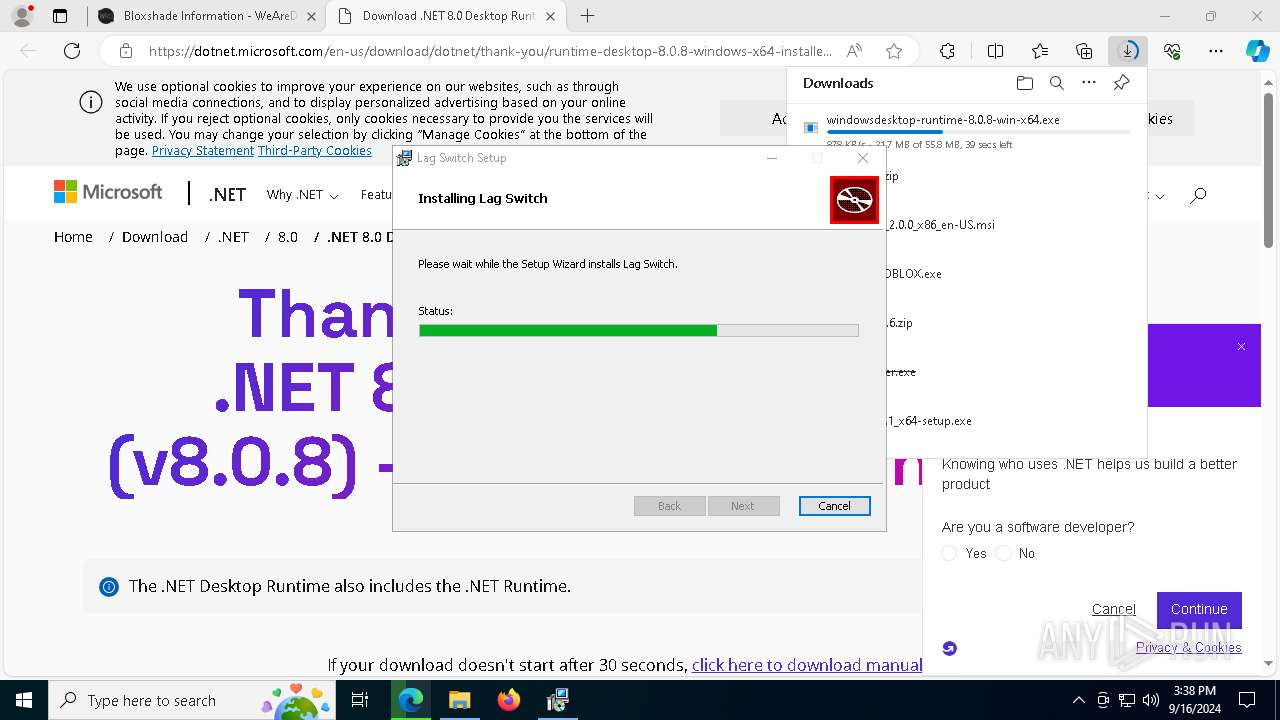
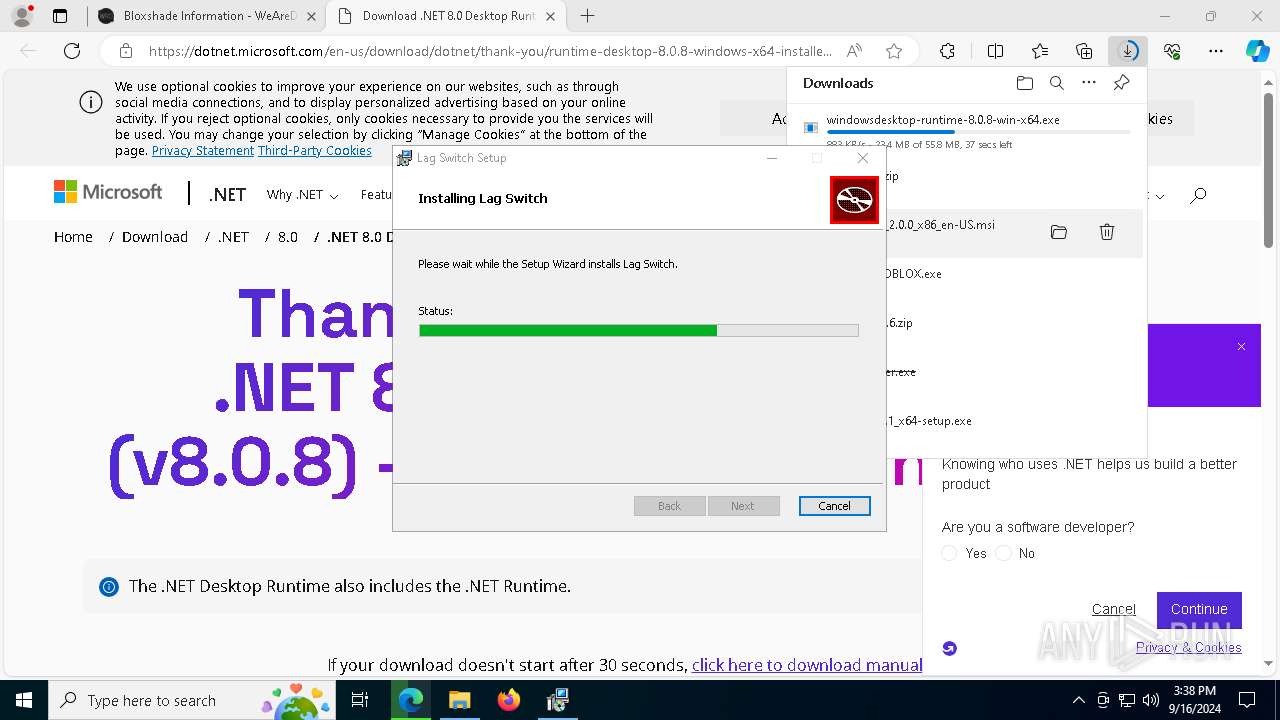
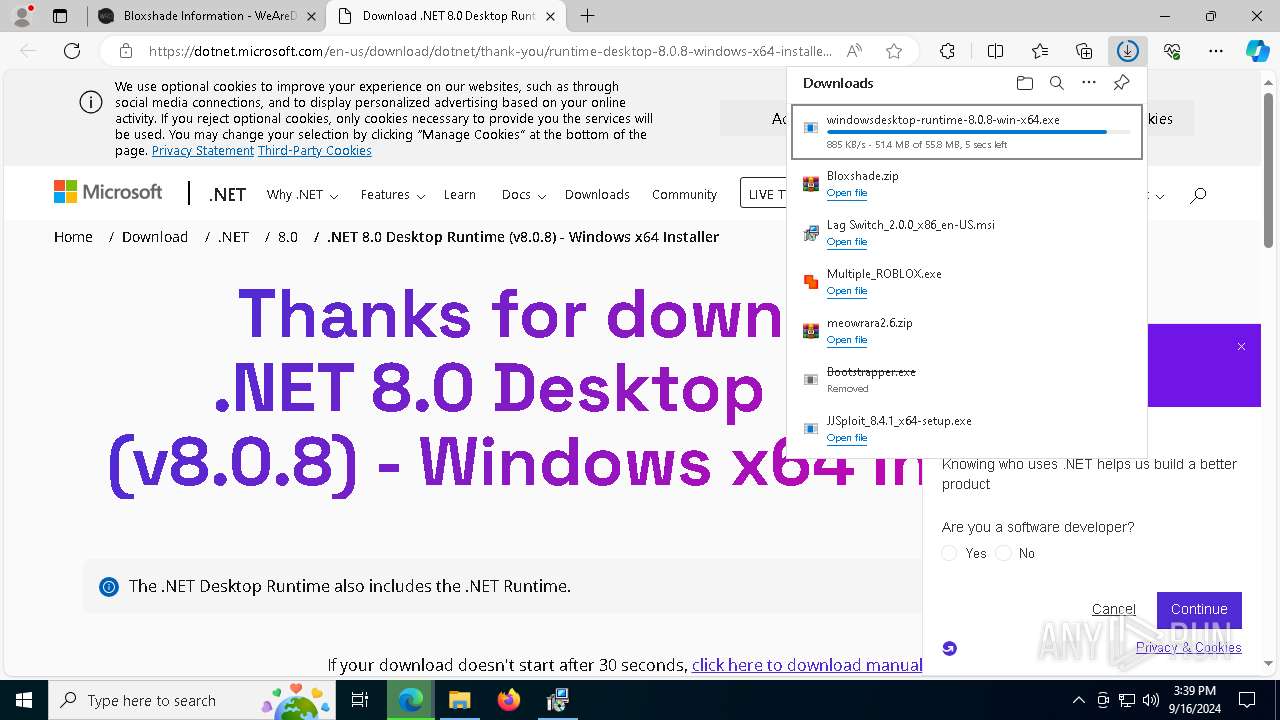
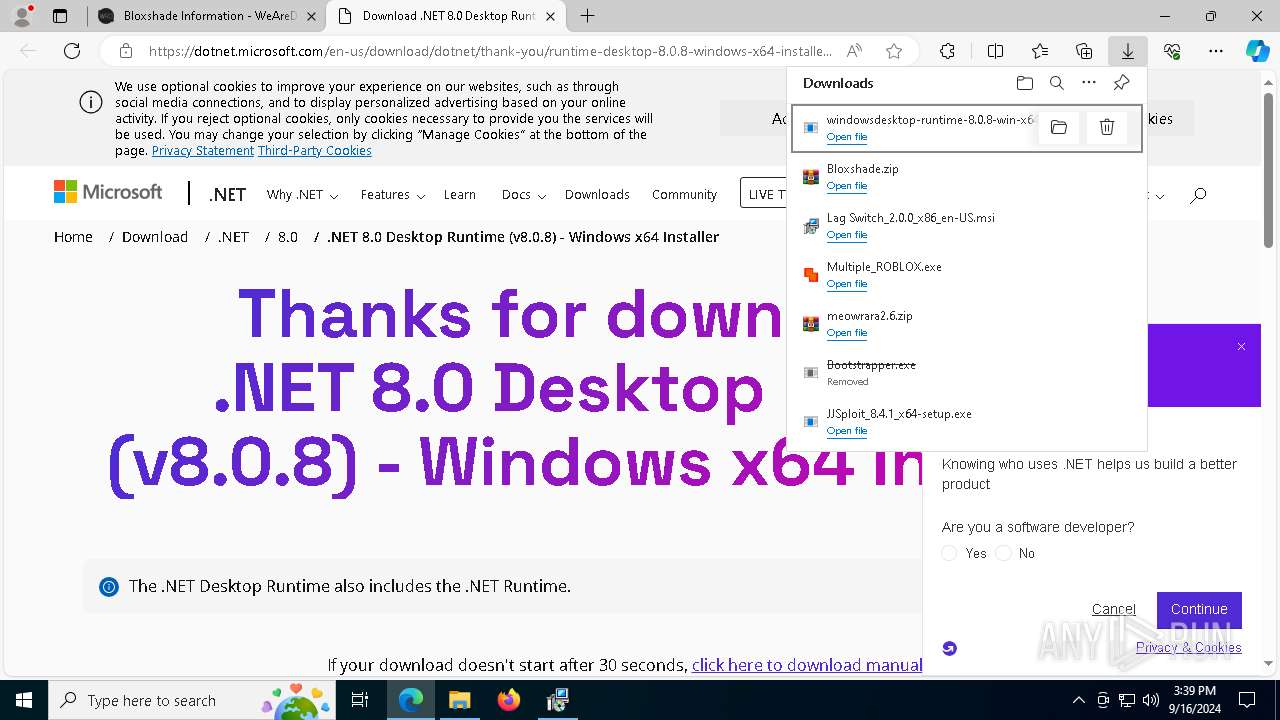
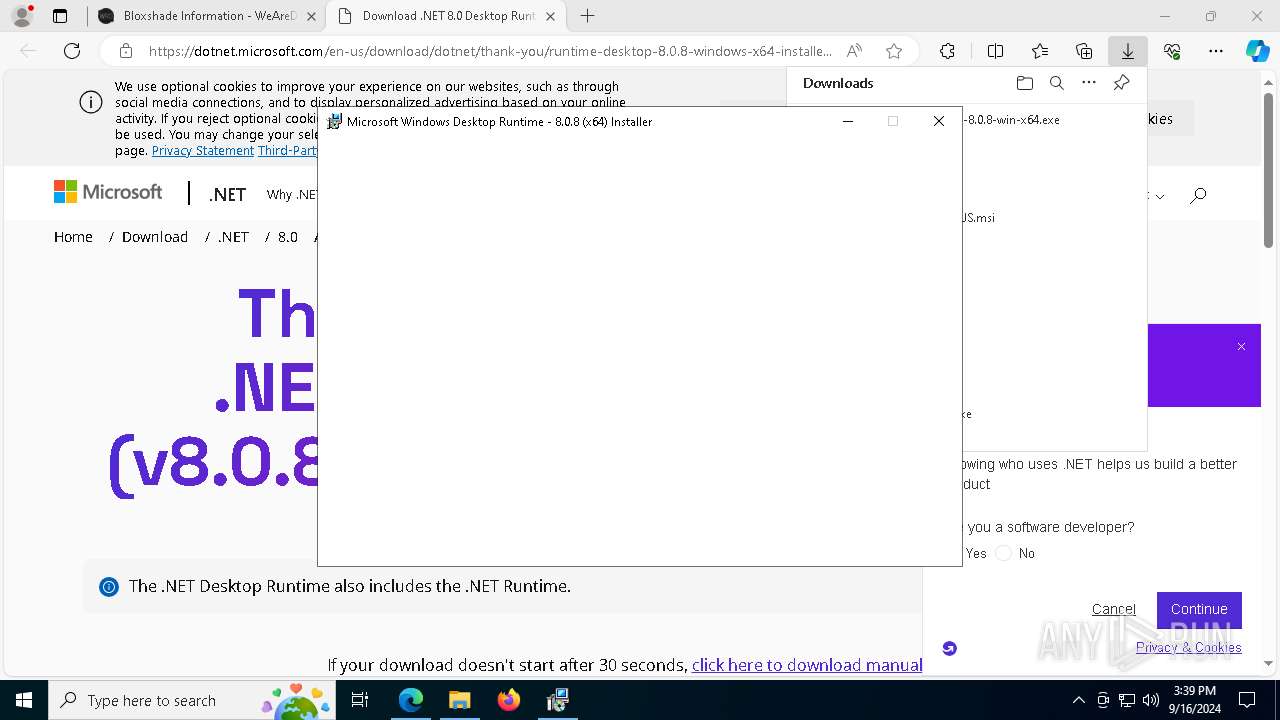
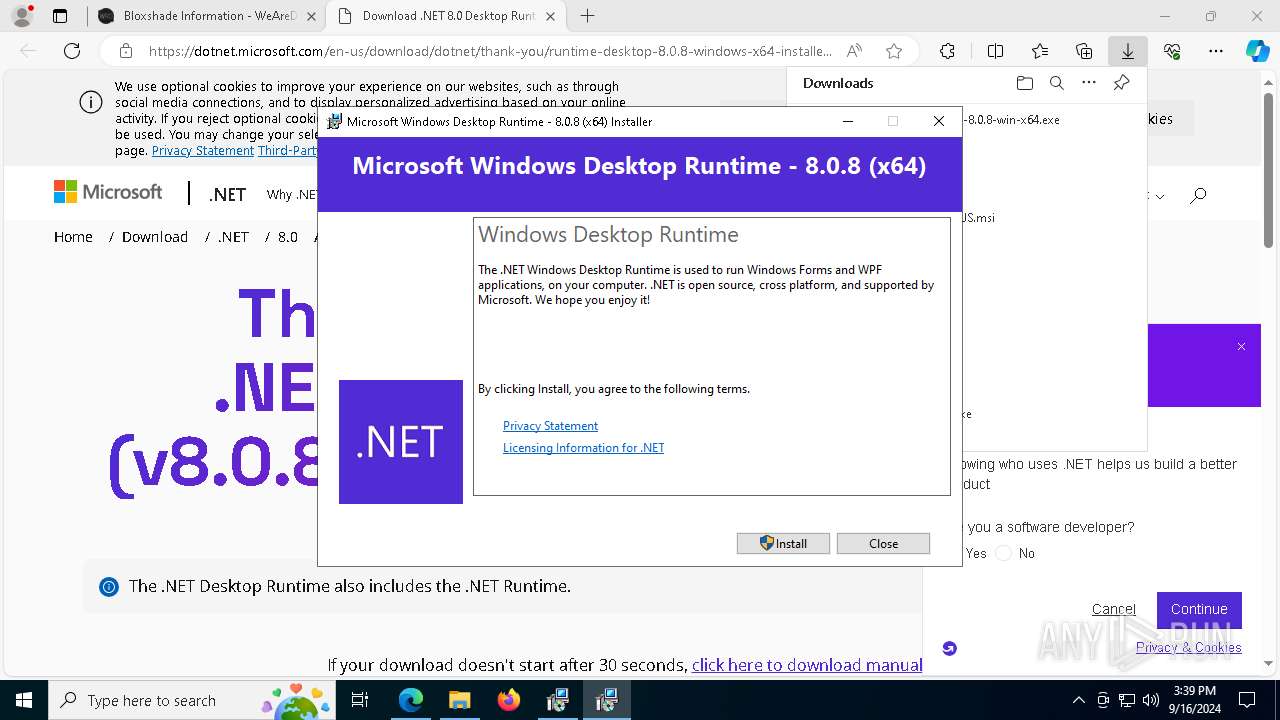
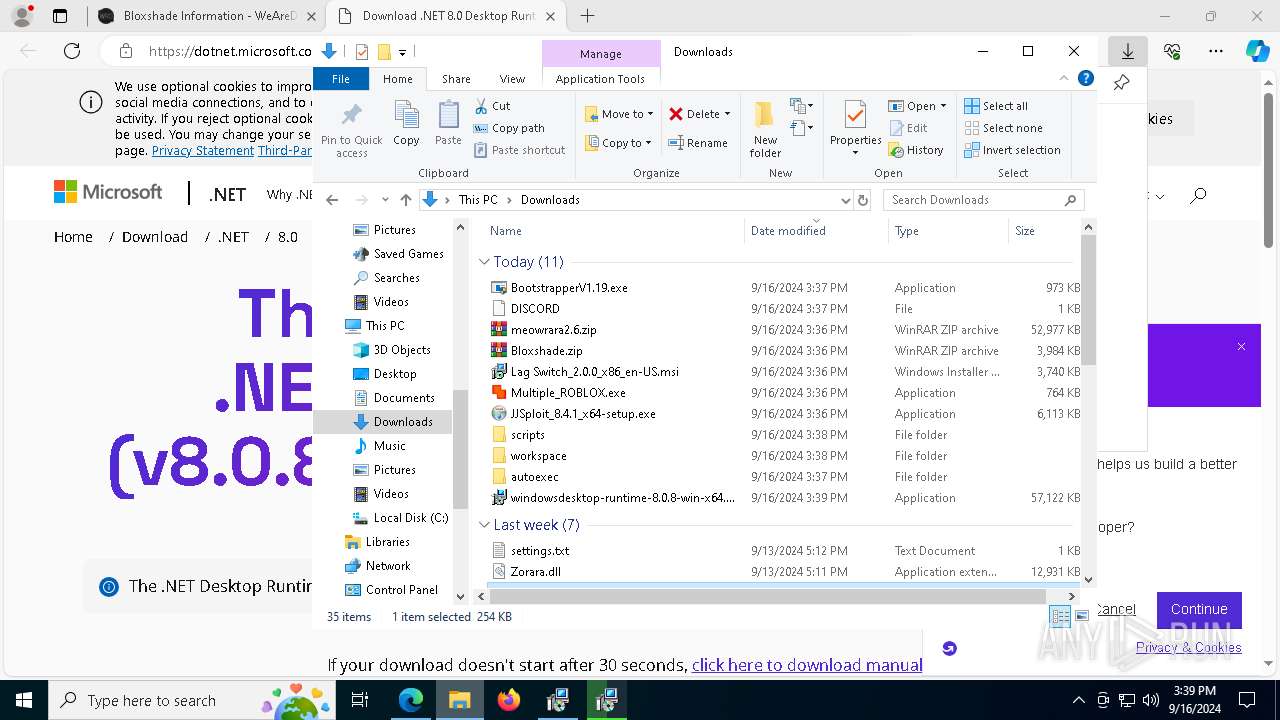
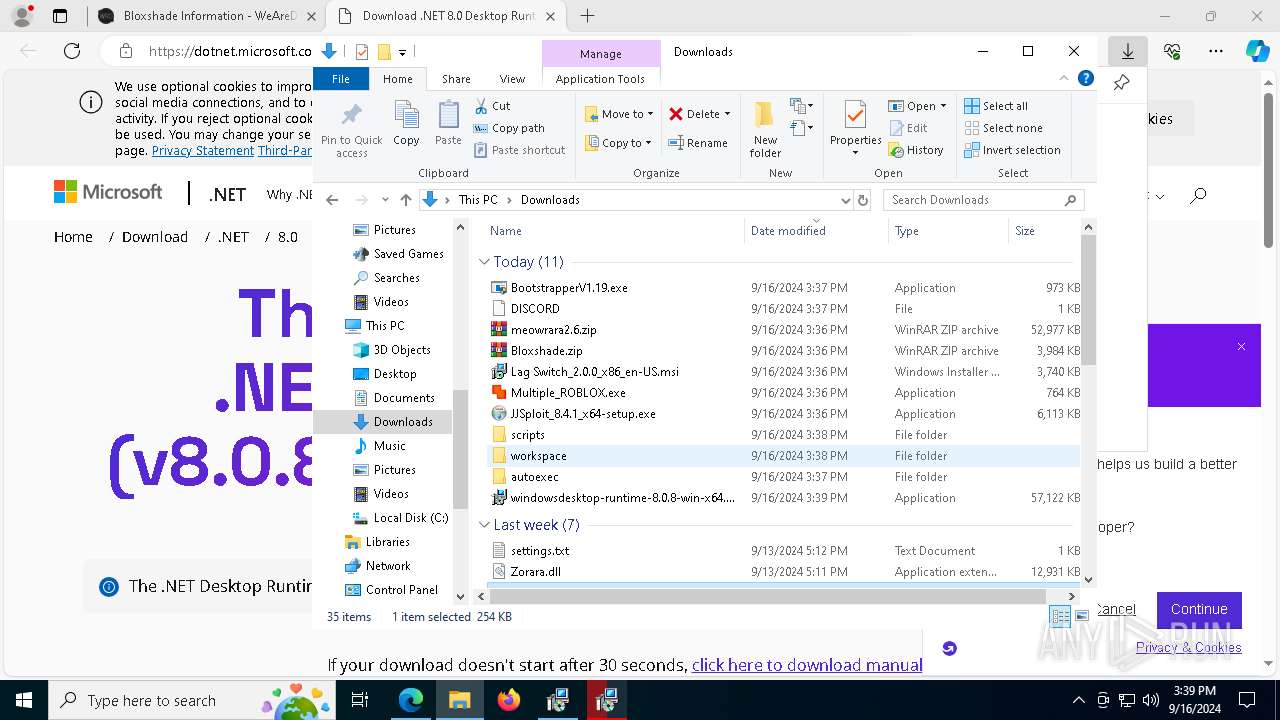
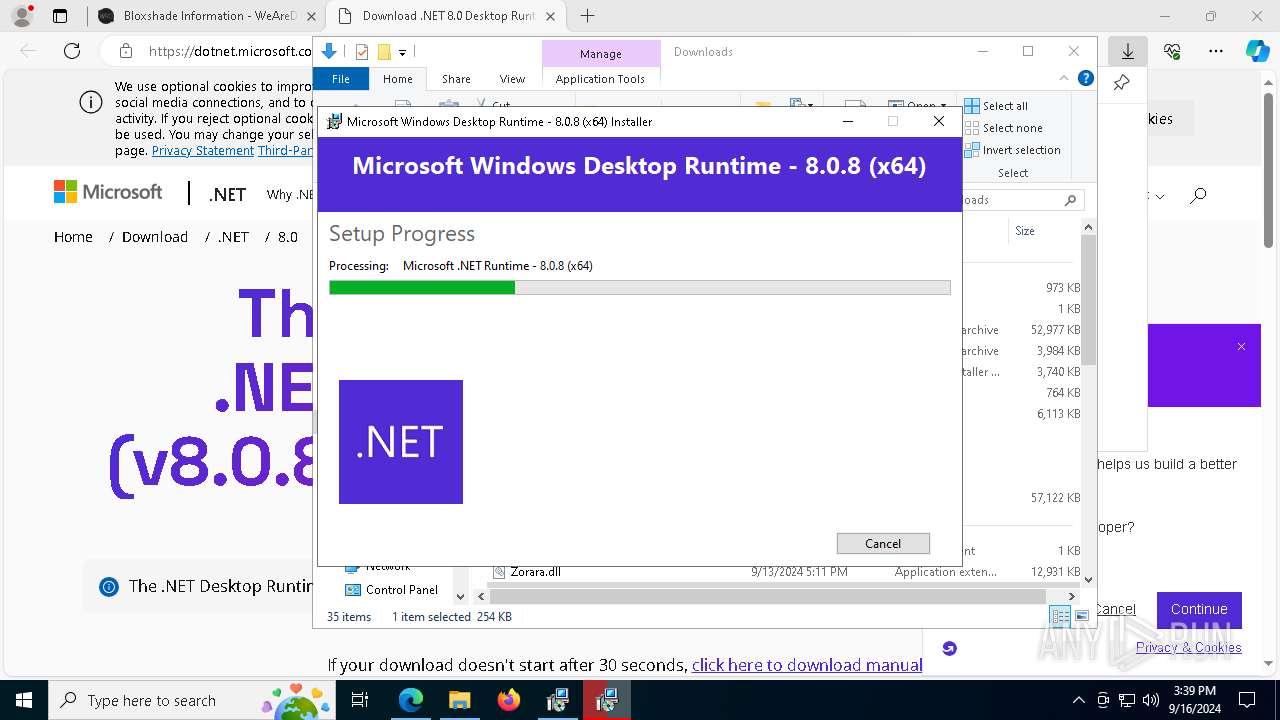
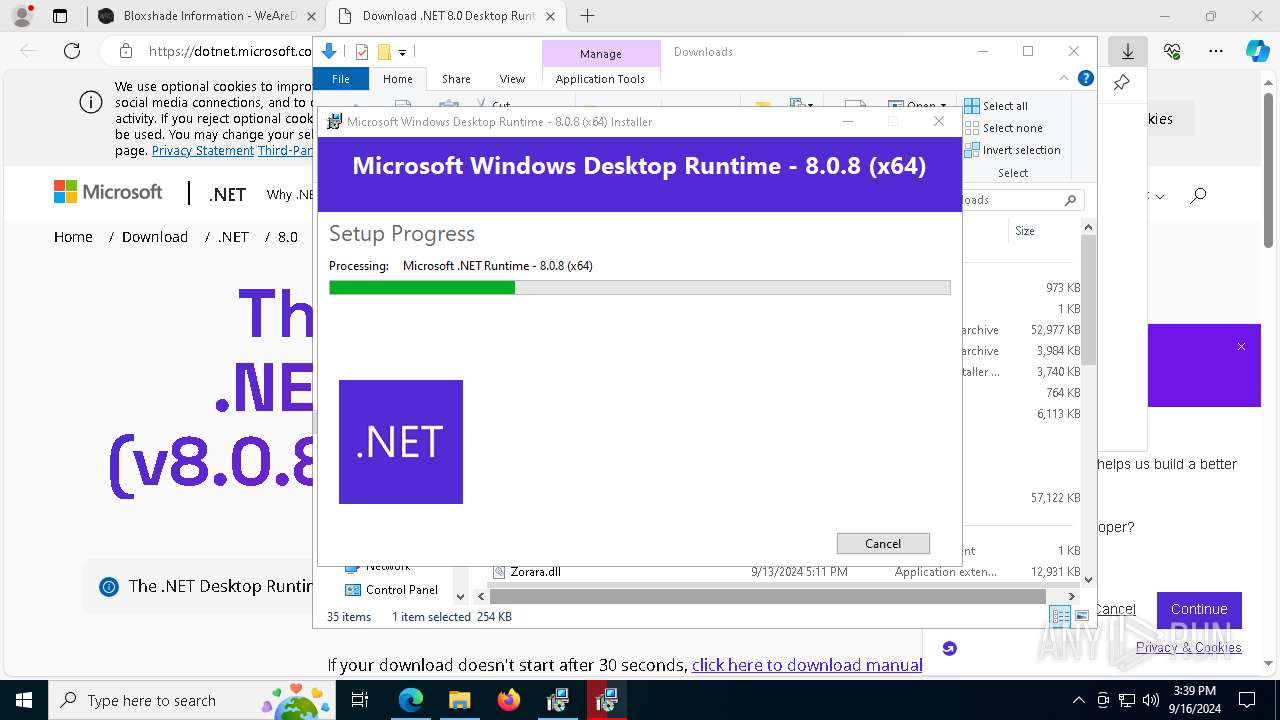
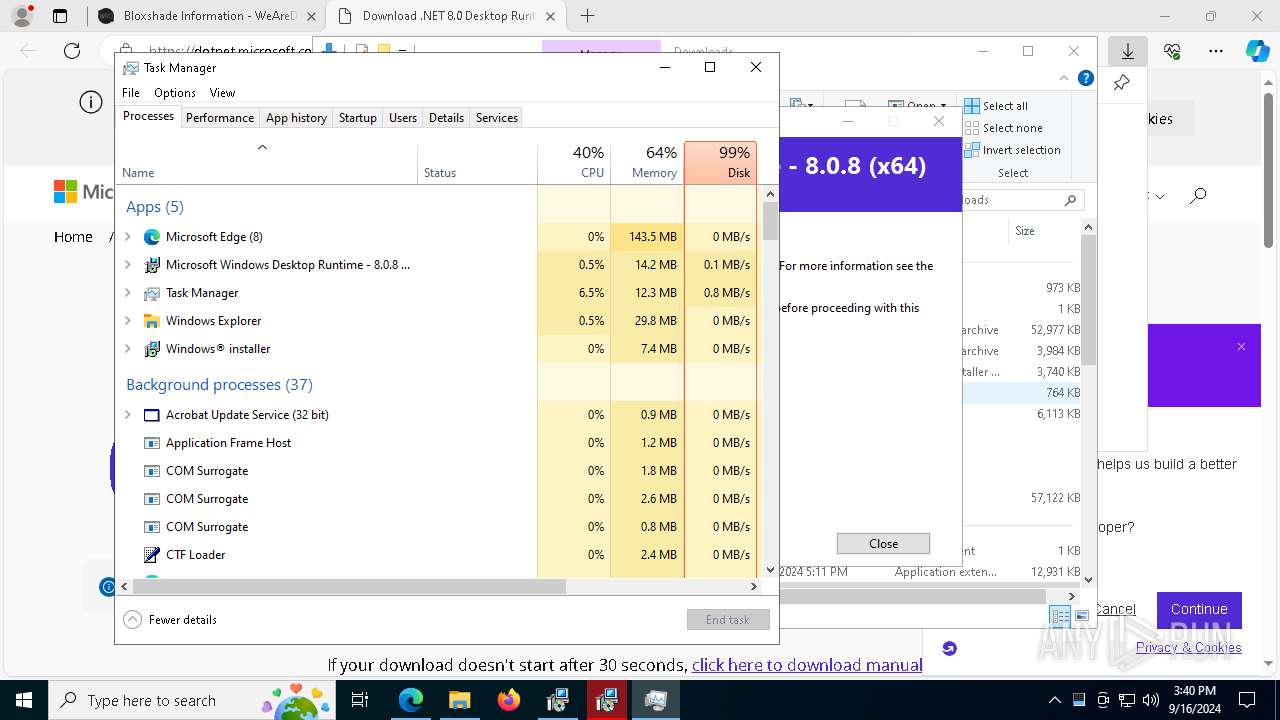
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6356)
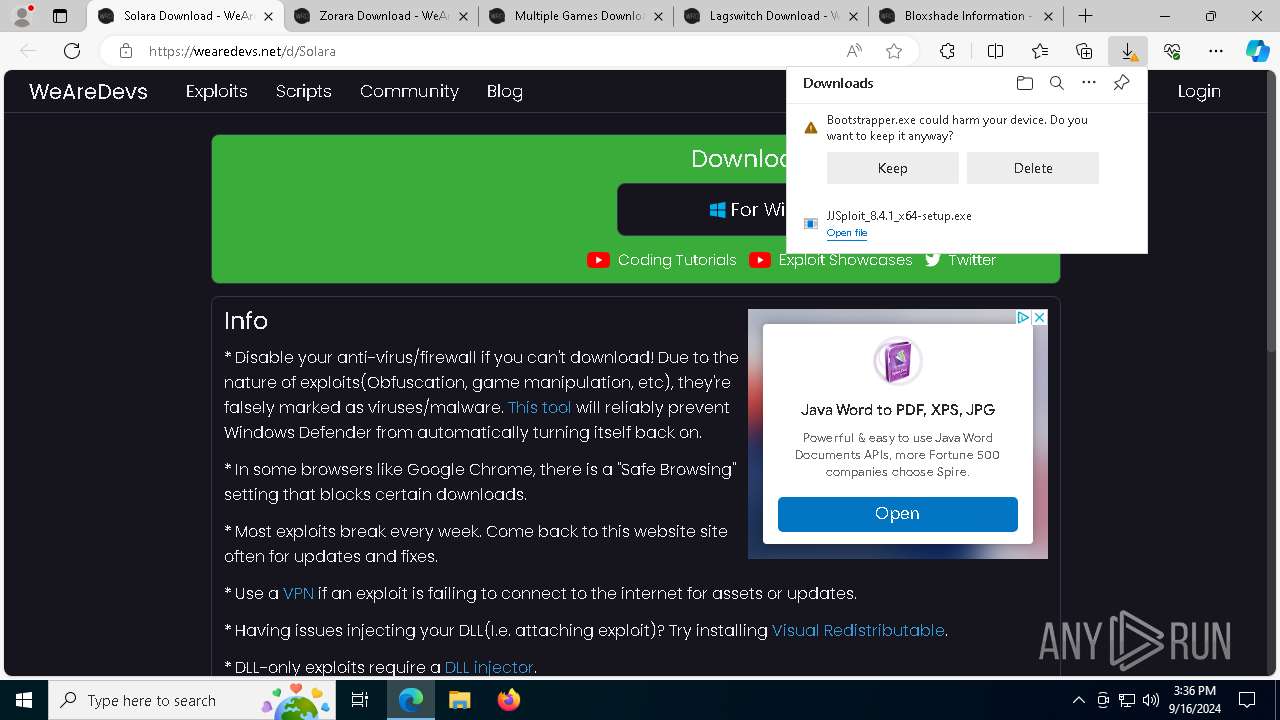
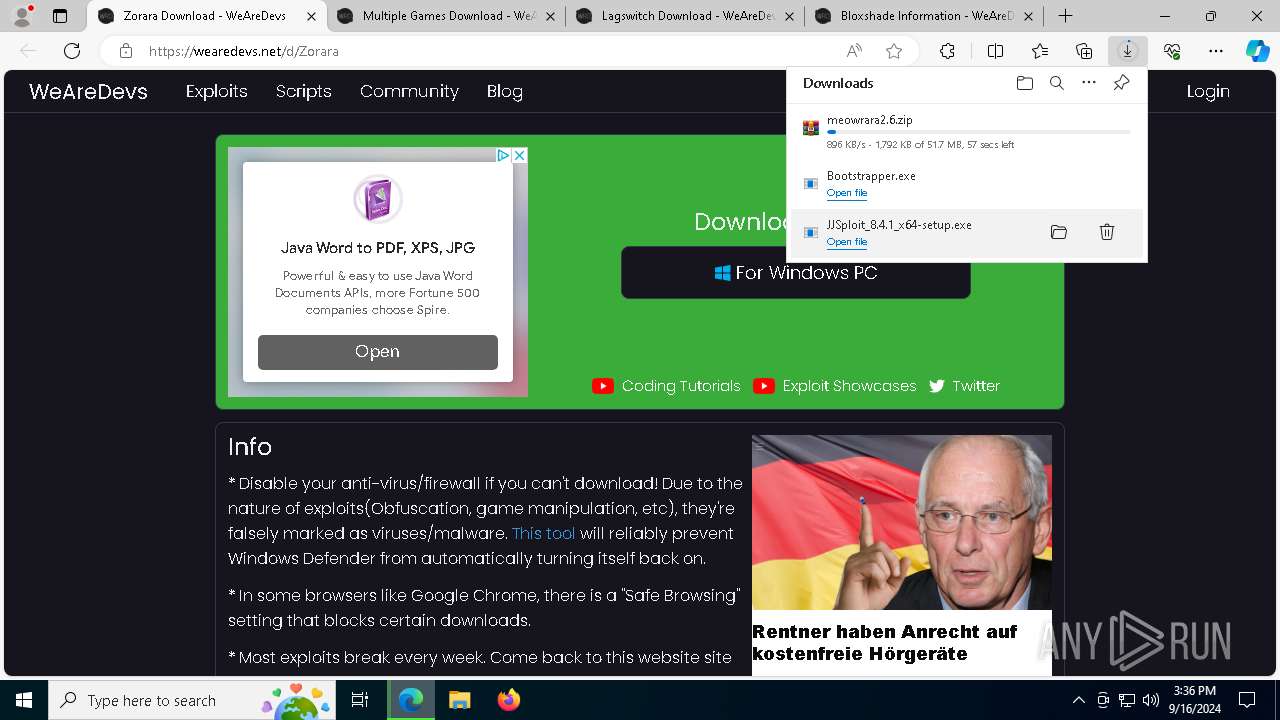
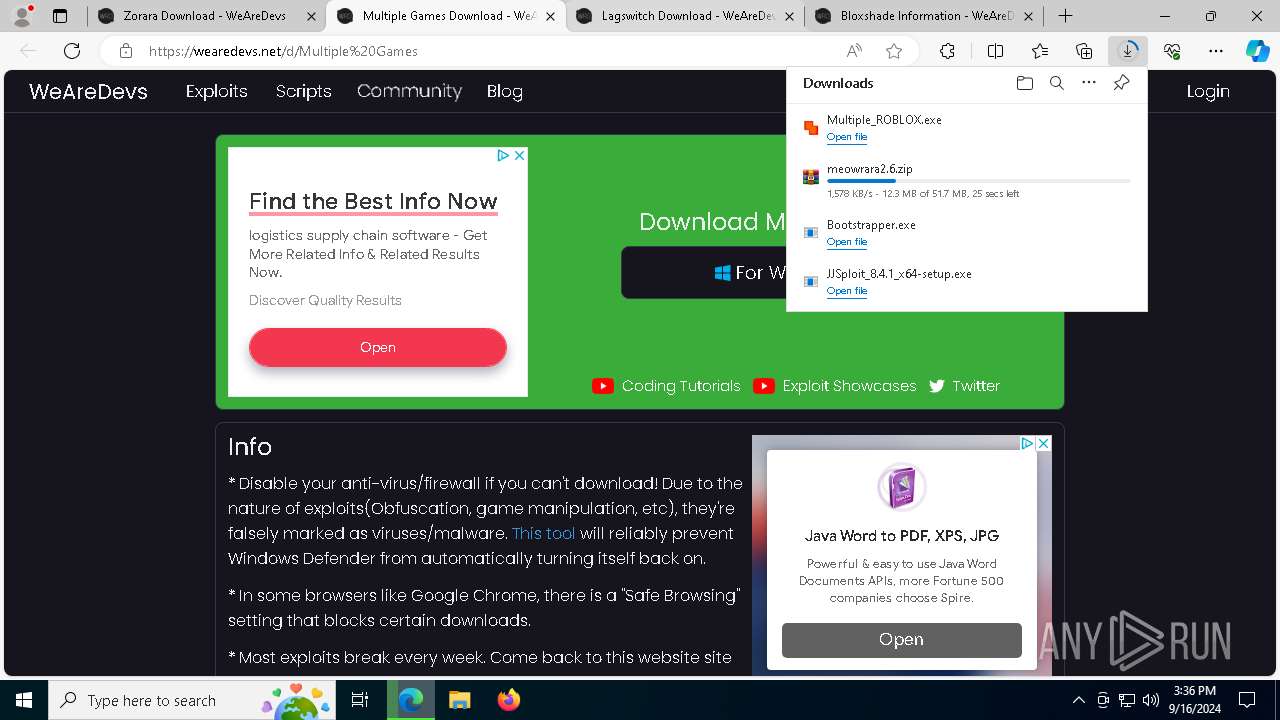
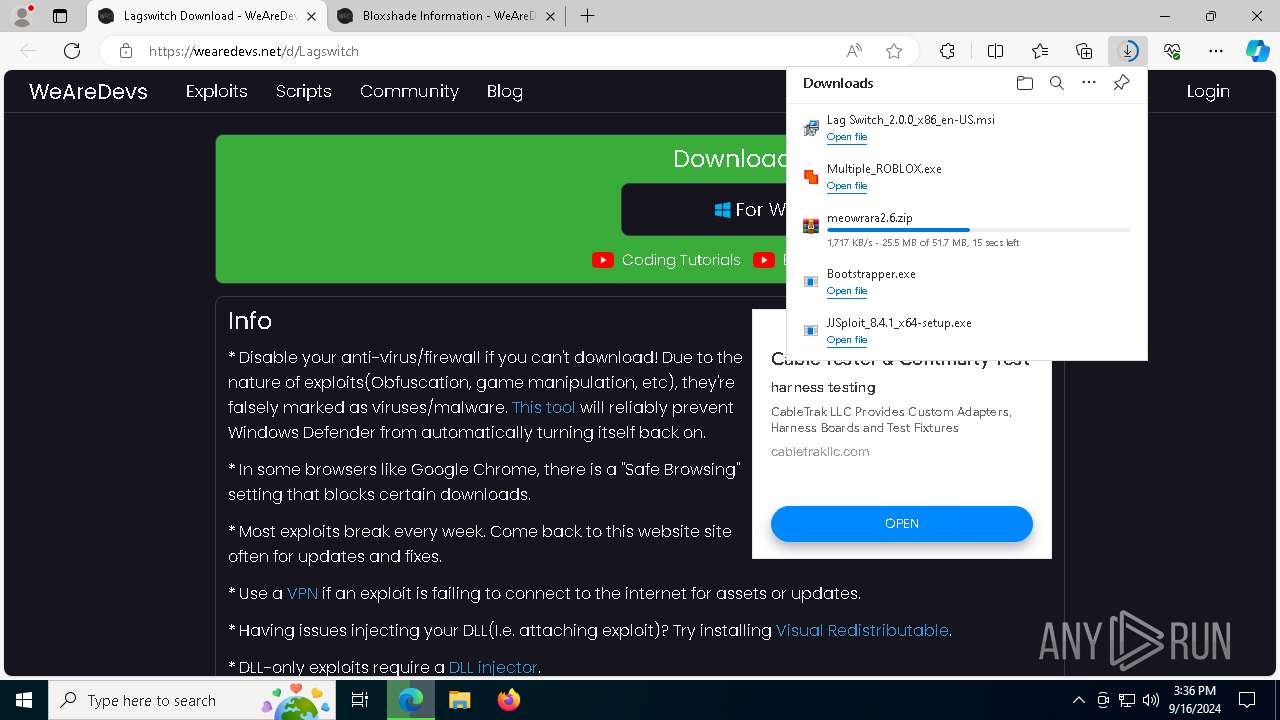
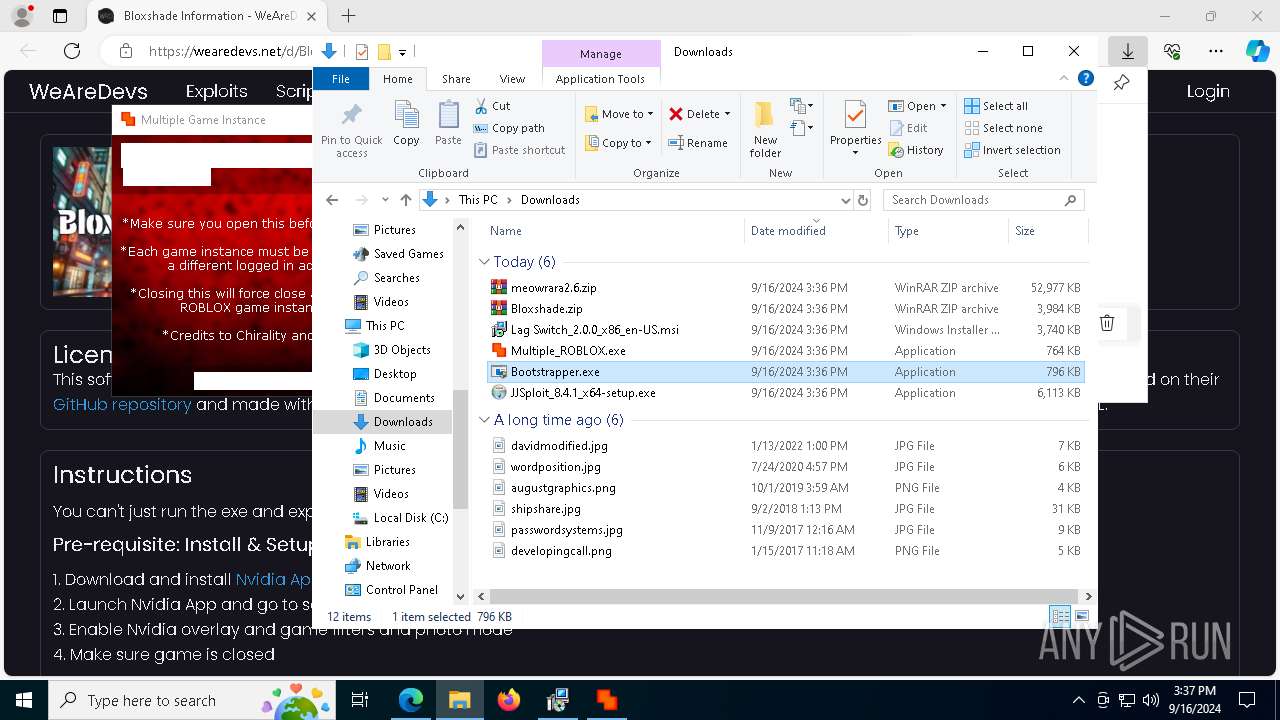
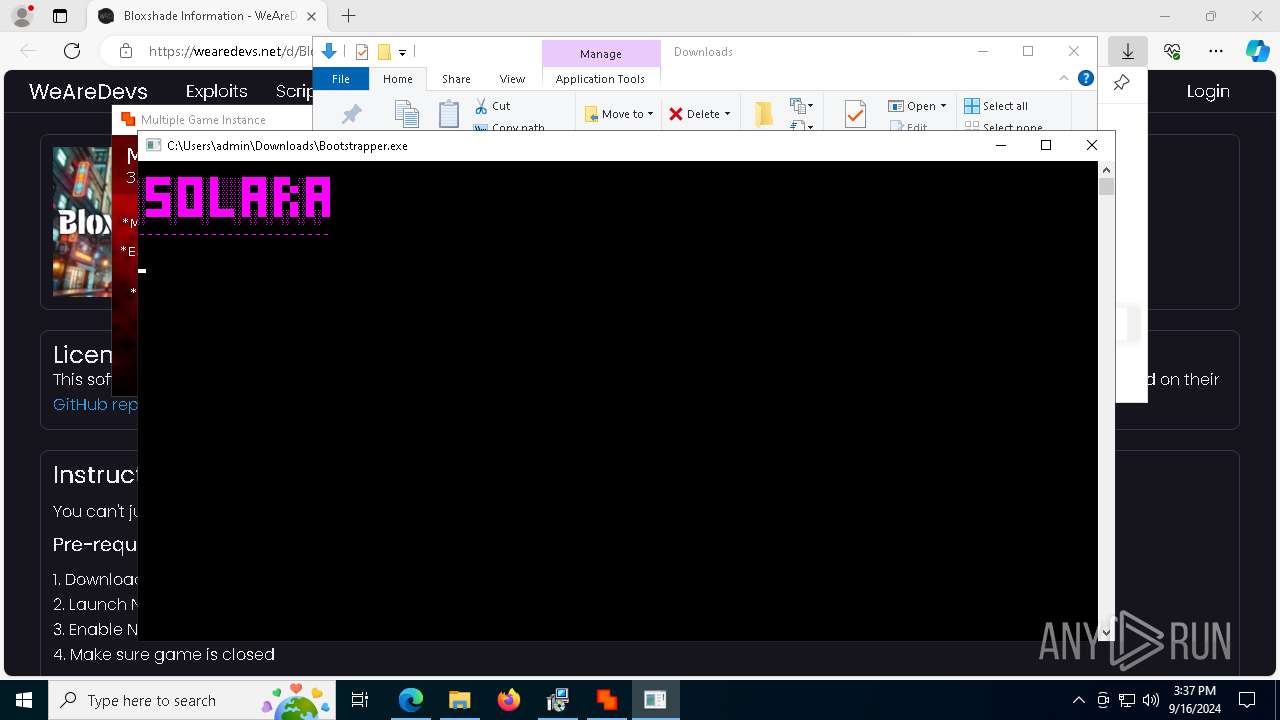
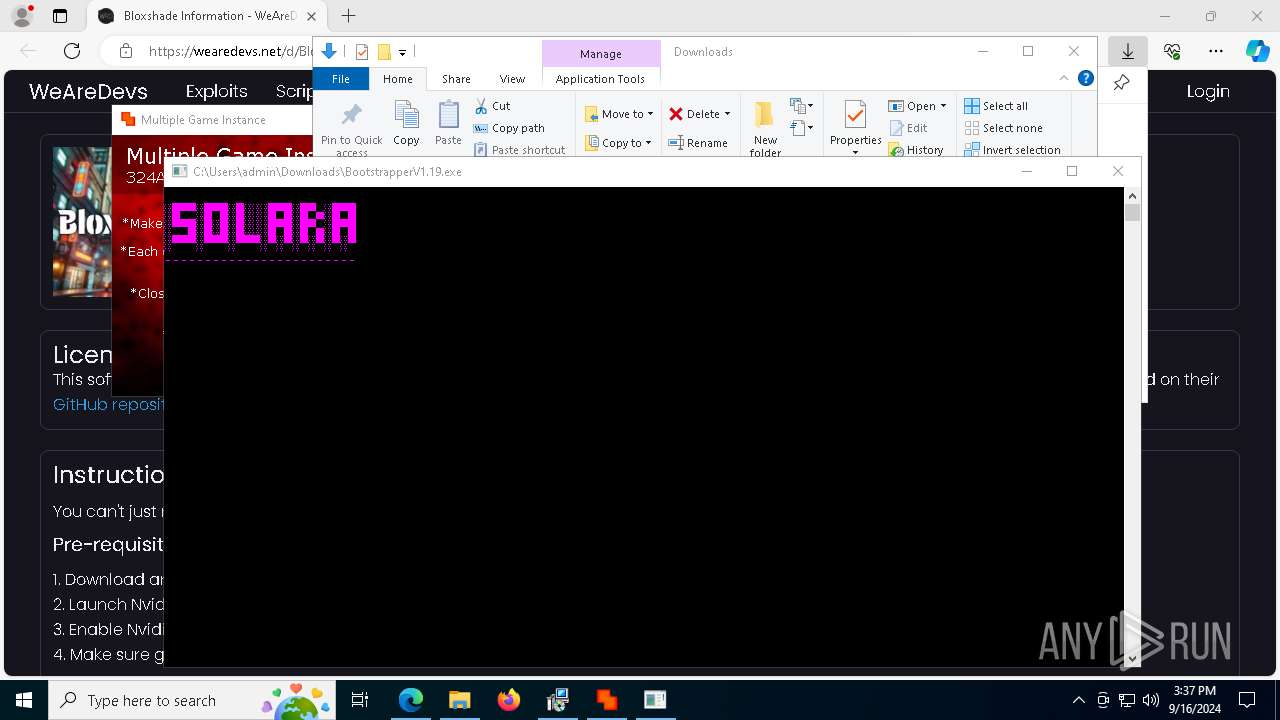
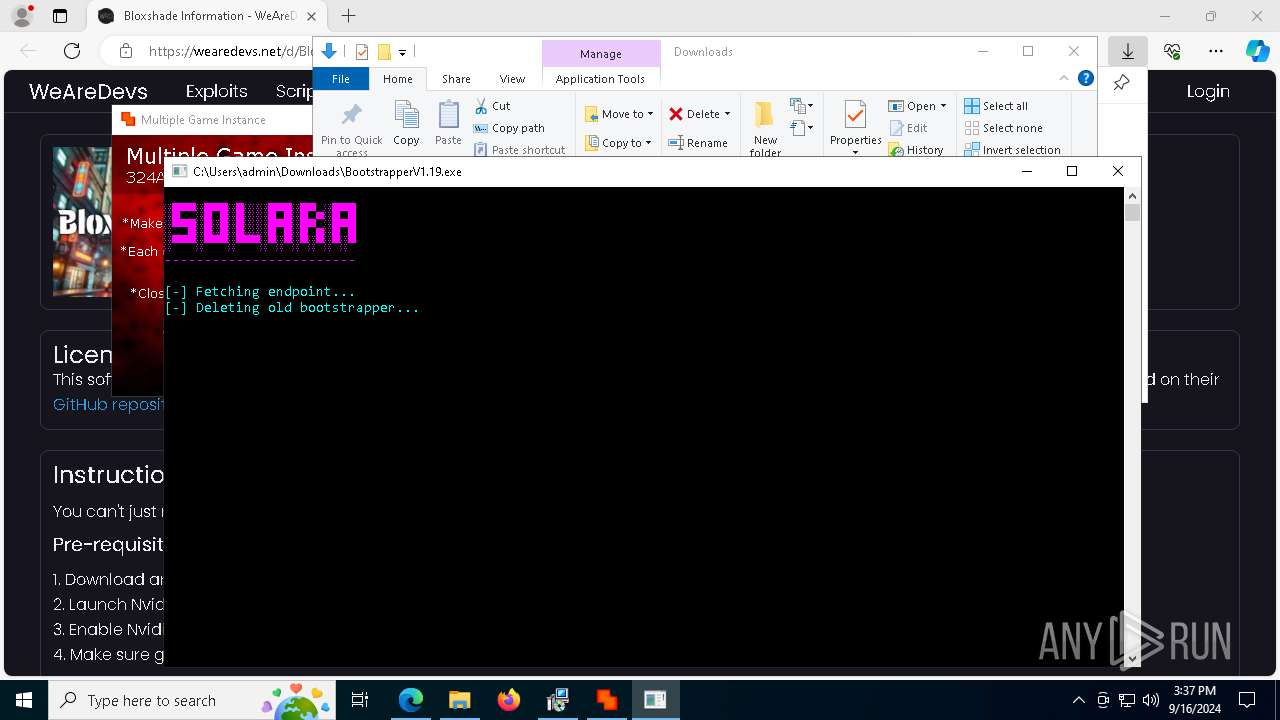
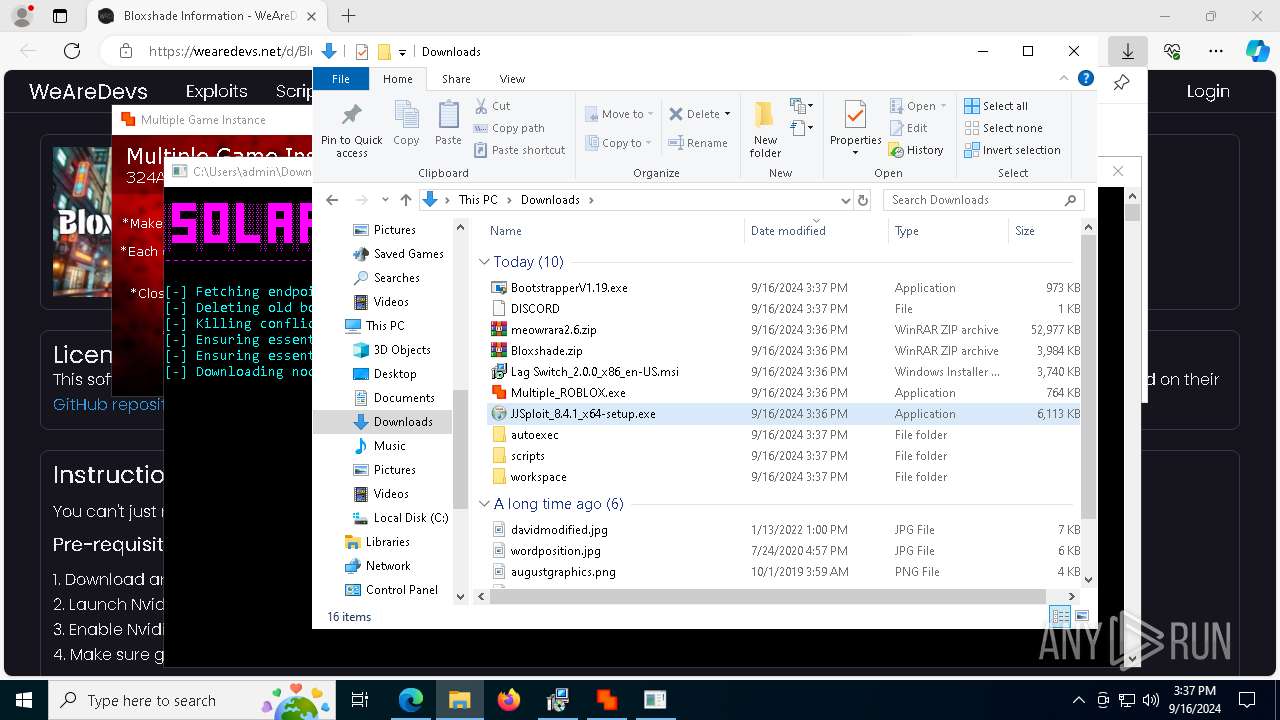
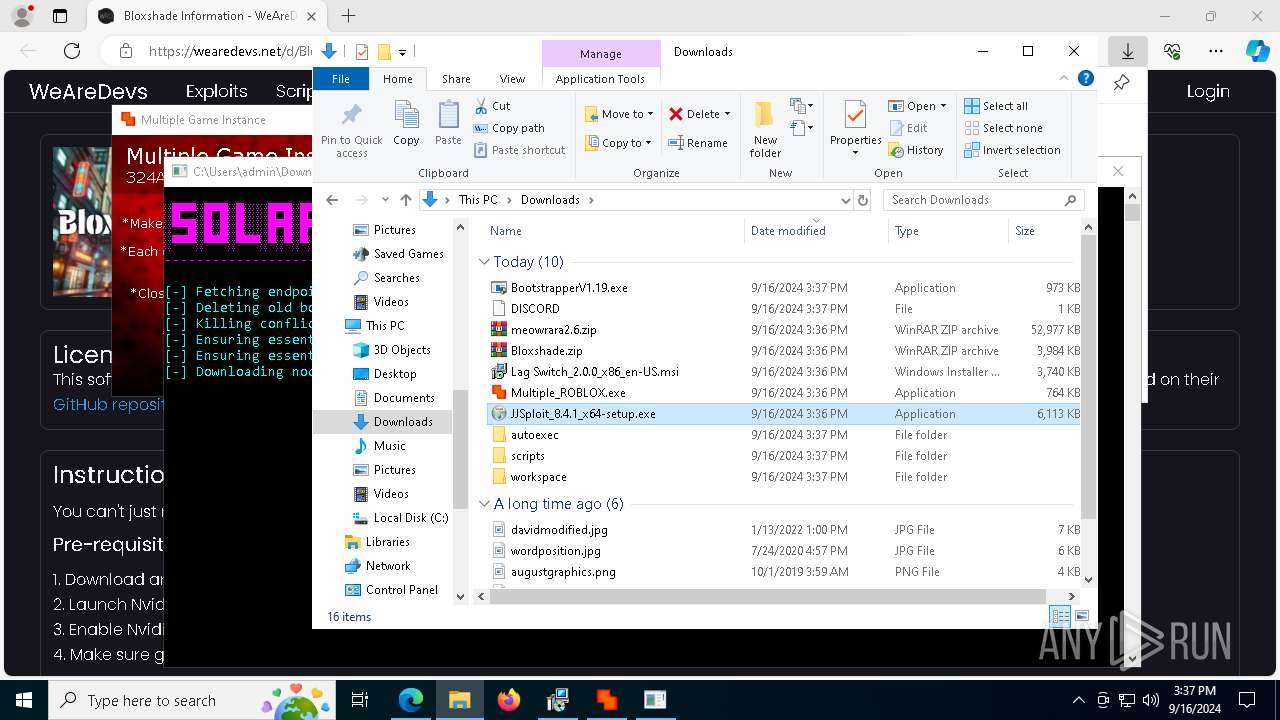
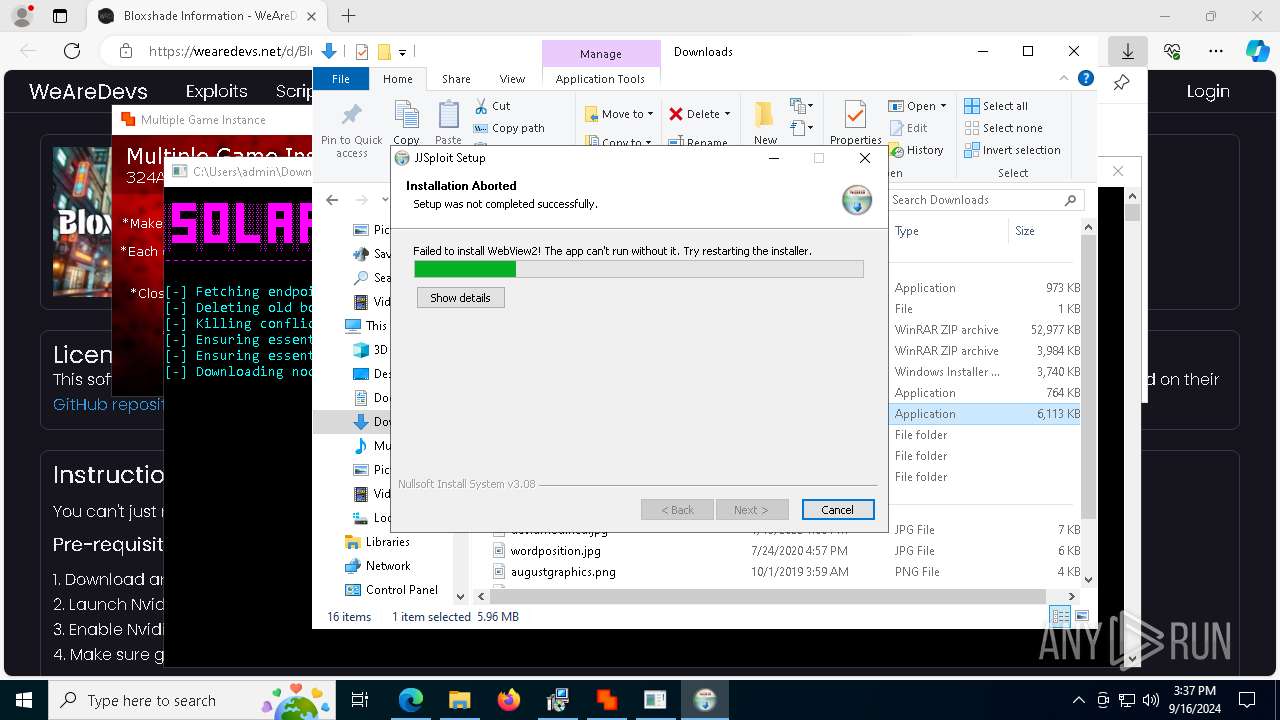
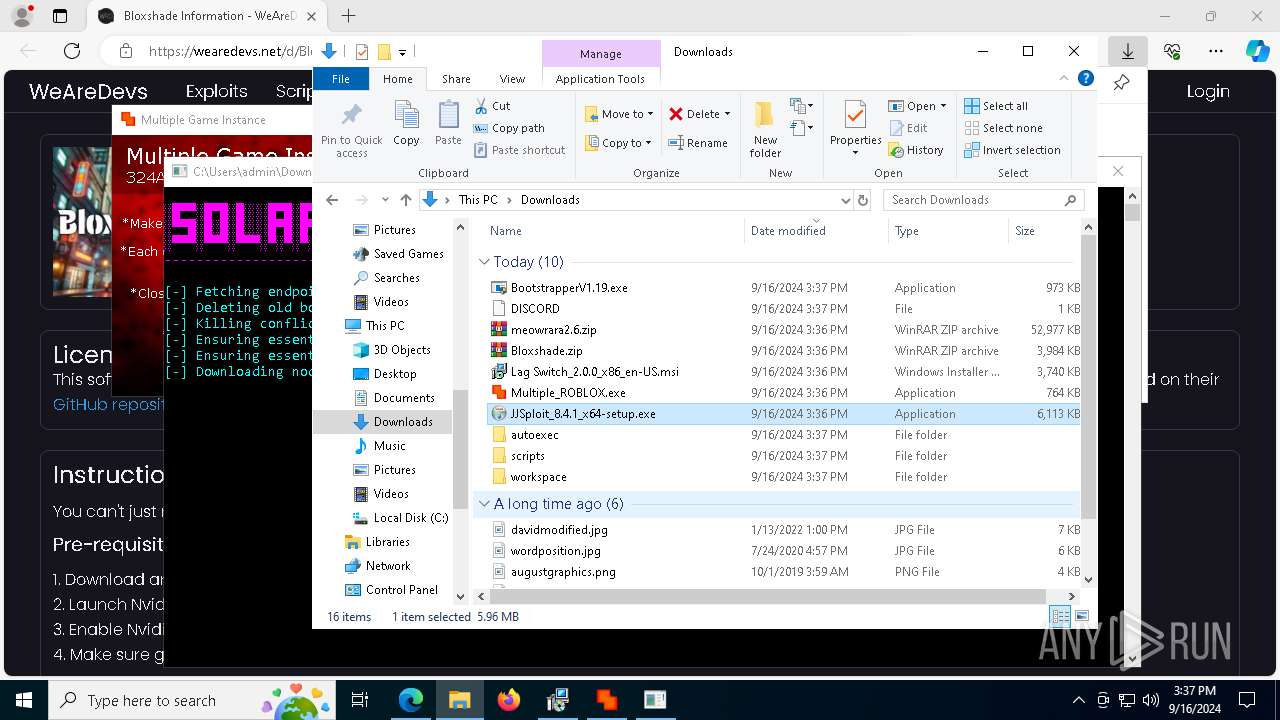
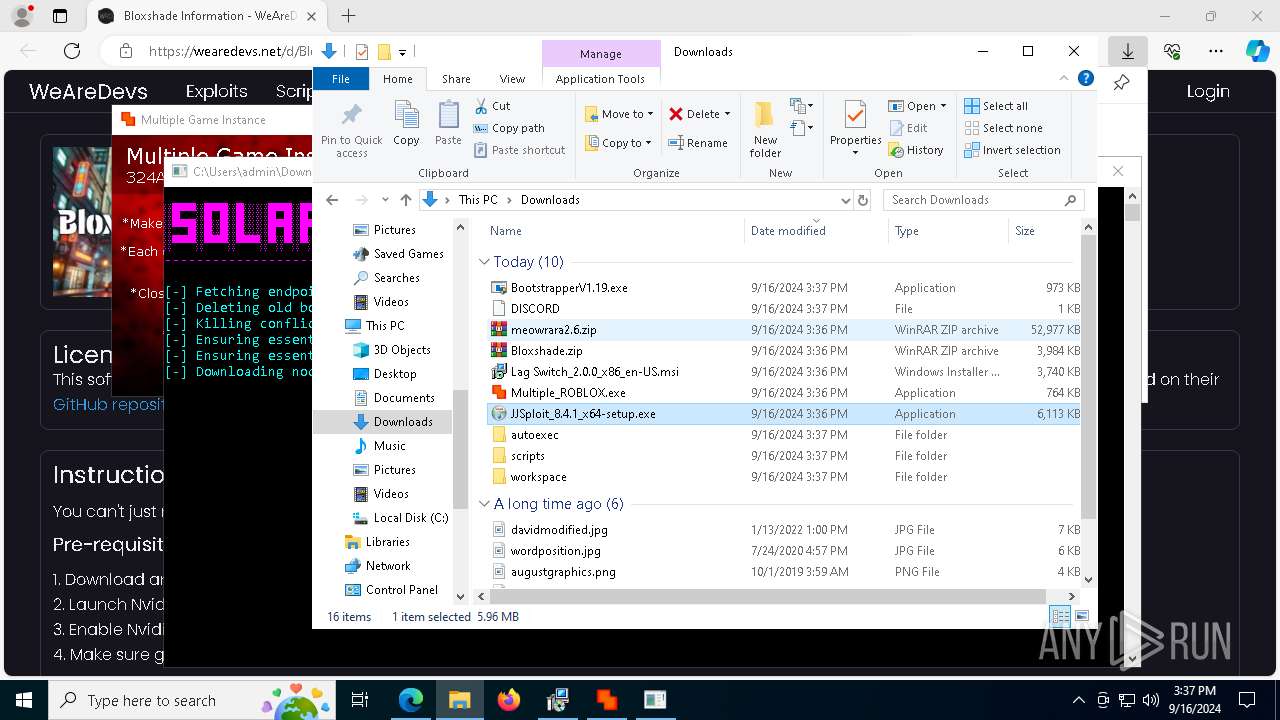
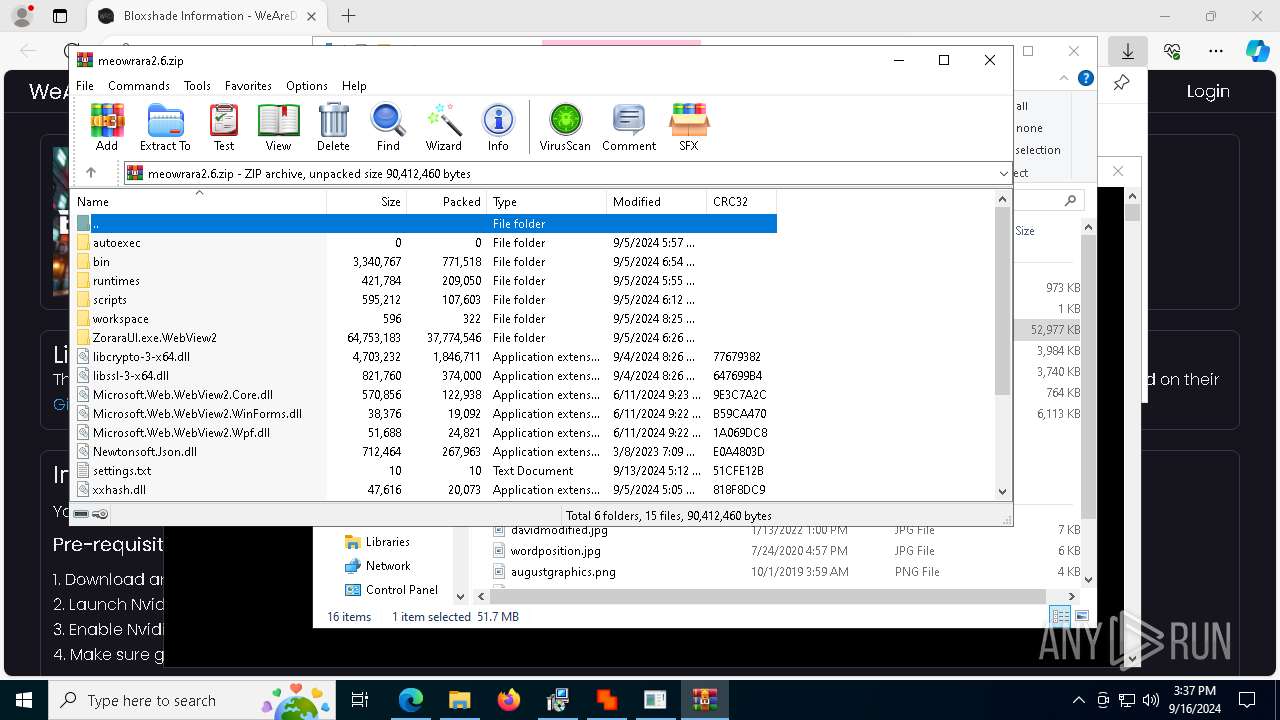
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 6728)
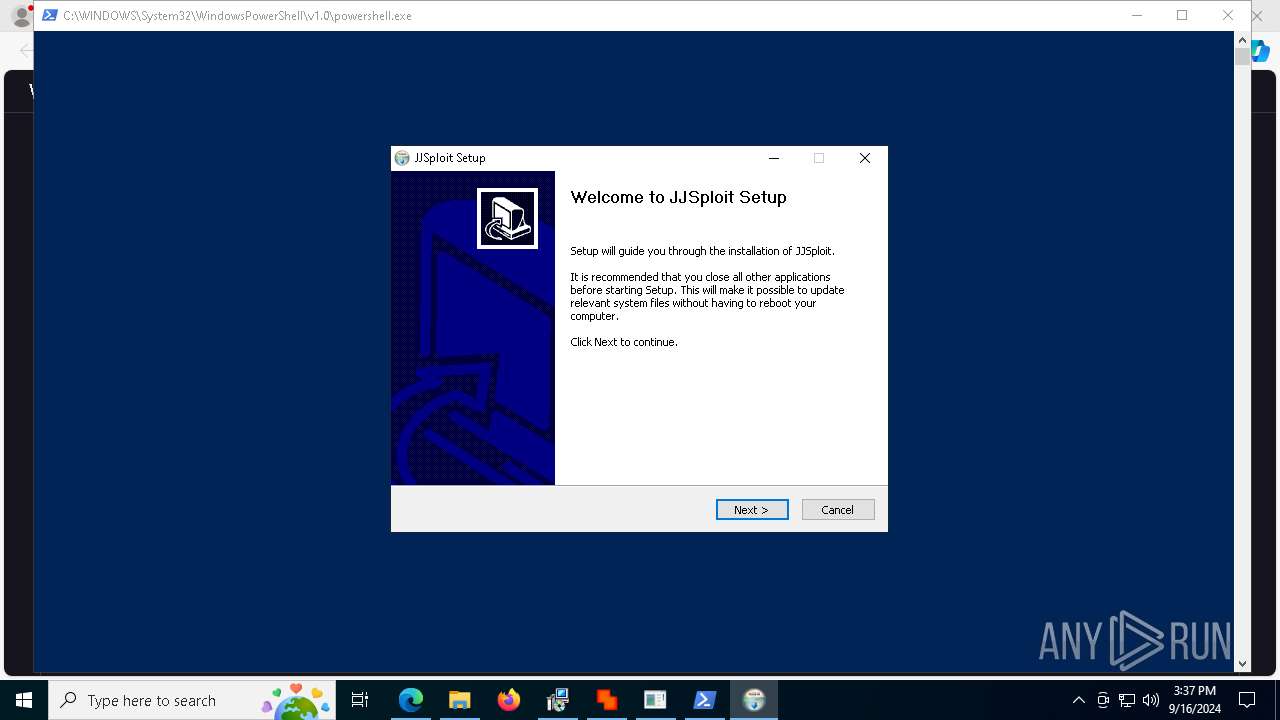
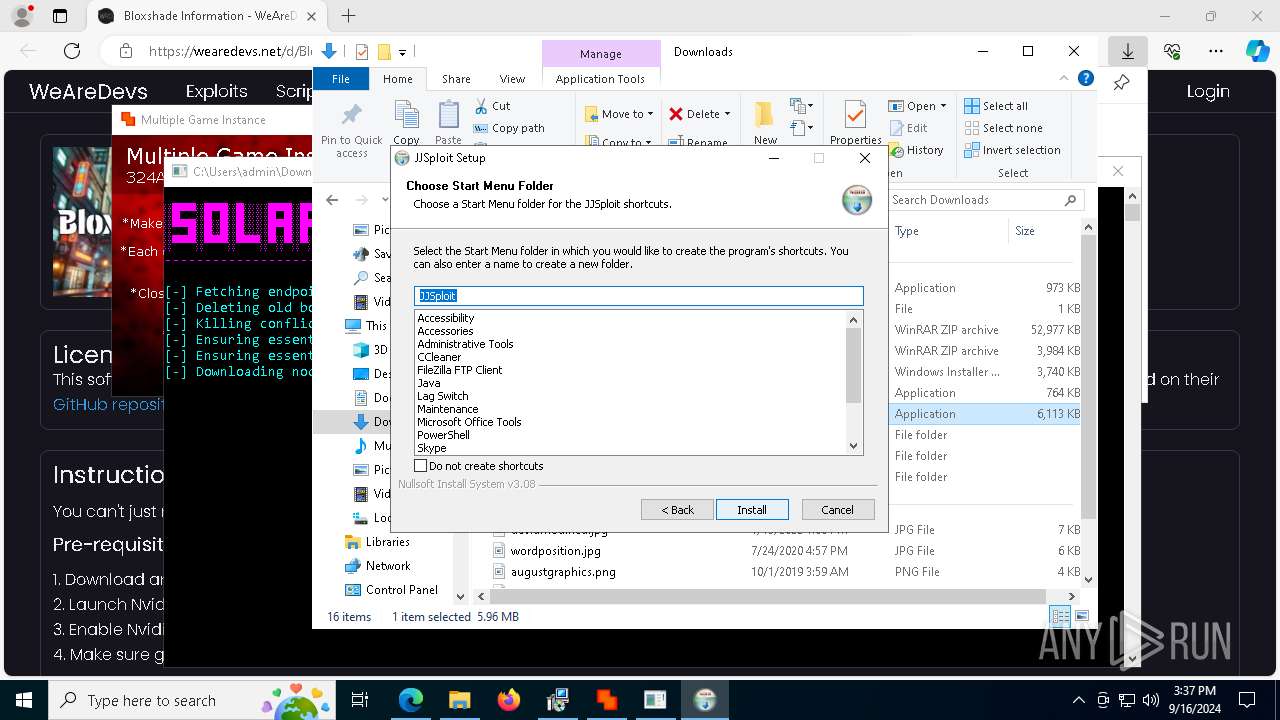
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
- MicrosoftEdgeWebview2Setup.exe (PID: 5900)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- BootstrapperV1.19.exe (PID: 6344)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7472)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 8116)
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- BootstrapperV1.19.exe (PID: 6344)
- ZoraraUI.exe (PID: 320)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- ShellExperienceHost.exe (PID: 4072)
- MicrosoftEdgeUpdate.exe (PID: 3176)
Reads the date of Windows installation
- Bootstrapper.exe (PID: 6728)
- BootstrapperV1.19.exe (PID: 6344)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4088)
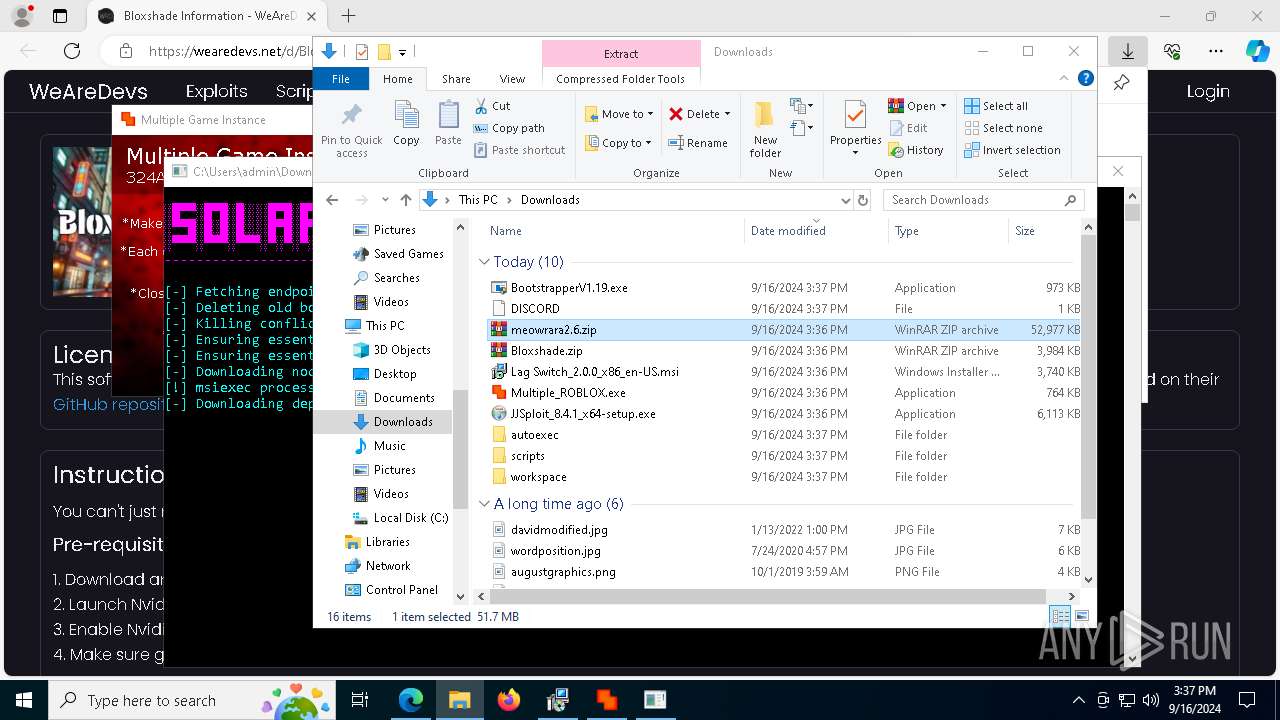
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 4088)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4088)
Downloads file from URI
- powershell.exe (PID: 7416)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4088)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 5900)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
The process creates files with name similar to system file names
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7416)
Powershell scripting: start process
- msiexec.exe (PID: 4088)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7416)
Searches for installed software
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7340)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3296)
- MicrosoftEdgeUpdate.exe (PID: 2524)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7976)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7972)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2360)
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
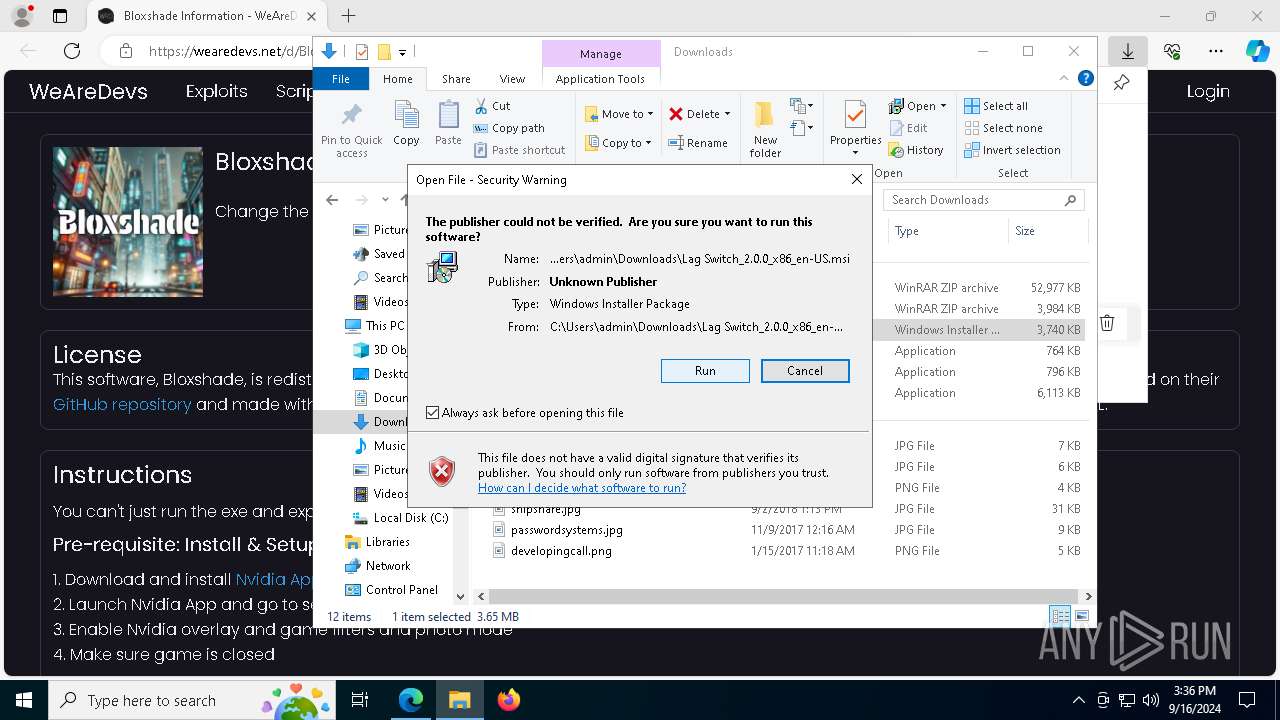
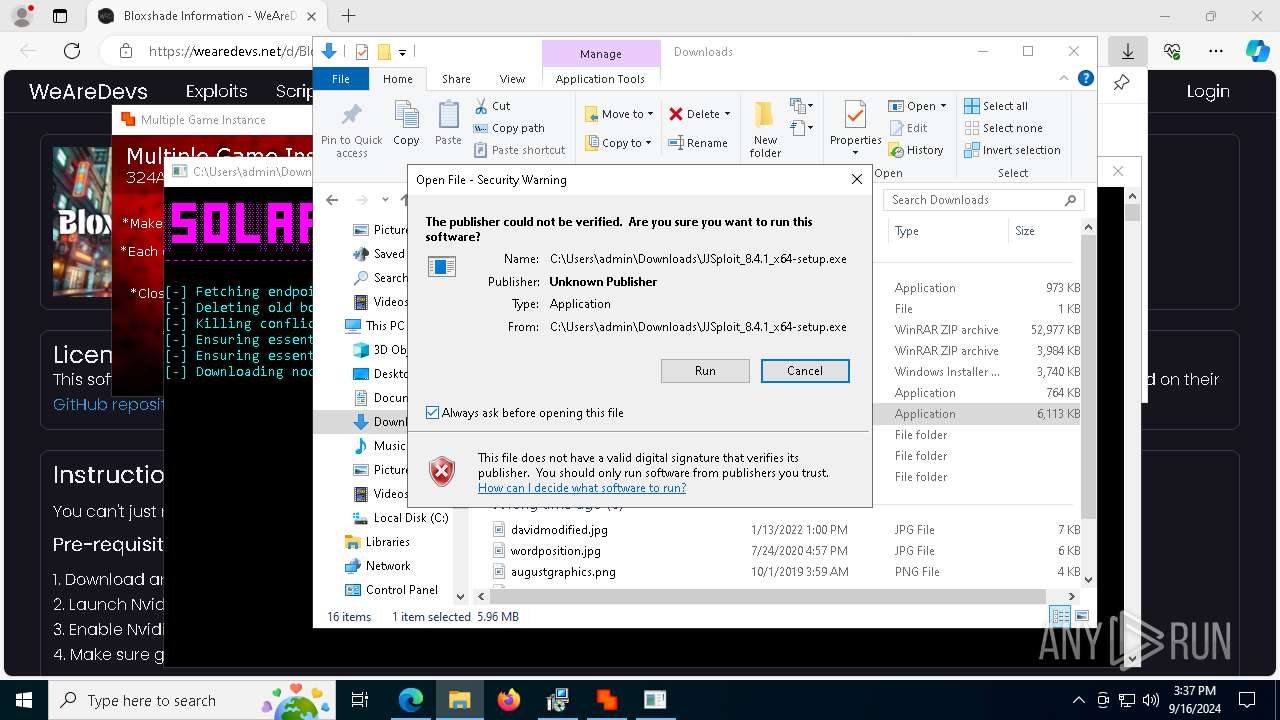
Checks Windows Trust Settings
- MicrosoftEdgeUpdate.exe (PID: 3176)
Application launched itself
- setup.exe (PID: 8004)
INFO
Checks supported languages
- identity_helper.exe (PID: 8132)
- msiexec.exe (PID: 4088)
- msiexec.exe (PID: 6052)
- Bootstrapper.exe (PID: 6728)
- Multiple_ROBLOX.exe (PID: 2112)
- BootstrapperV1.19.exe (PID: 6344)
- MicrosoftEdgeWebview2Setup.exe (PID: 5900)
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3296)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7976)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7972)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 2524)
- MicrosoftEdgeUpdate.exe (PID: 7964)
- MicrosoftEdgeUpdate.exe (PID: 6576)
- MicrosoftEdgeUpdate.exe (PID: 3176)
- ZoraraUI.exe (PID: 320)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7472)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
- ShellExperienceHost.exe (PID: 4072)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 8116)
- setup.exe (PID: 8004)
- setup.exe (PID: 2092)
Reads Environment values
- identity_helper.exe (PID: 8132)
- Bootstrapper.exe (PID: 6728)
- BootstrapperV1.19.exe (PID: 6344)
- MicrosoftEdgeUpdate.exe (PID: 7964)
Reads the computer name
- identity_helper.exe (PID: 8132)
- msiexec.exe (PID: 4088)
- msiexec.exe (PID: 6052)
- Bootstrapper.exe (PID: 6728)
- Multiple_ROBLOX.exe (PID: 2112)
- BootstrapperV1.19.exe (PID: 6344)
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 2524)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3296)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7976)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7972)
- MicrosoftEdgeUpdate.exe (PID: 7964)
- MicrosoftEdgeUpdate.exe (PID: 6576)
- MicrosoftEdgeUpdate.exe (PID: 3176)
- ZoraraUI.exe (PID: 320)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
- ShellExperienceHost.exe (PID: 4072)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 8116)
- setup.exe (PID: 8004)
Attempting to use instant messaging service
- msedge.exe (PID: 5092)
The process uses the downloaded file
- msedge.exe (PID: 7392)
- msedge.exe (PID: 6580)
- msedge.exe (PID: 7184)
- msedge.exe (PID: 1080)
- msedge.exe (PID: 7268)
- msedge.exe (PID: 1356)
- Bootstrapper.exe (PID: 6728)
- powershell.exe (PID: 7416)
- BootstrapperV1.19.exe (PID: 6344)
- WinRAR.exe (PID: 5304)
- msedge.exe (PID: 5000)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- msedge.exe (PID: 7864)
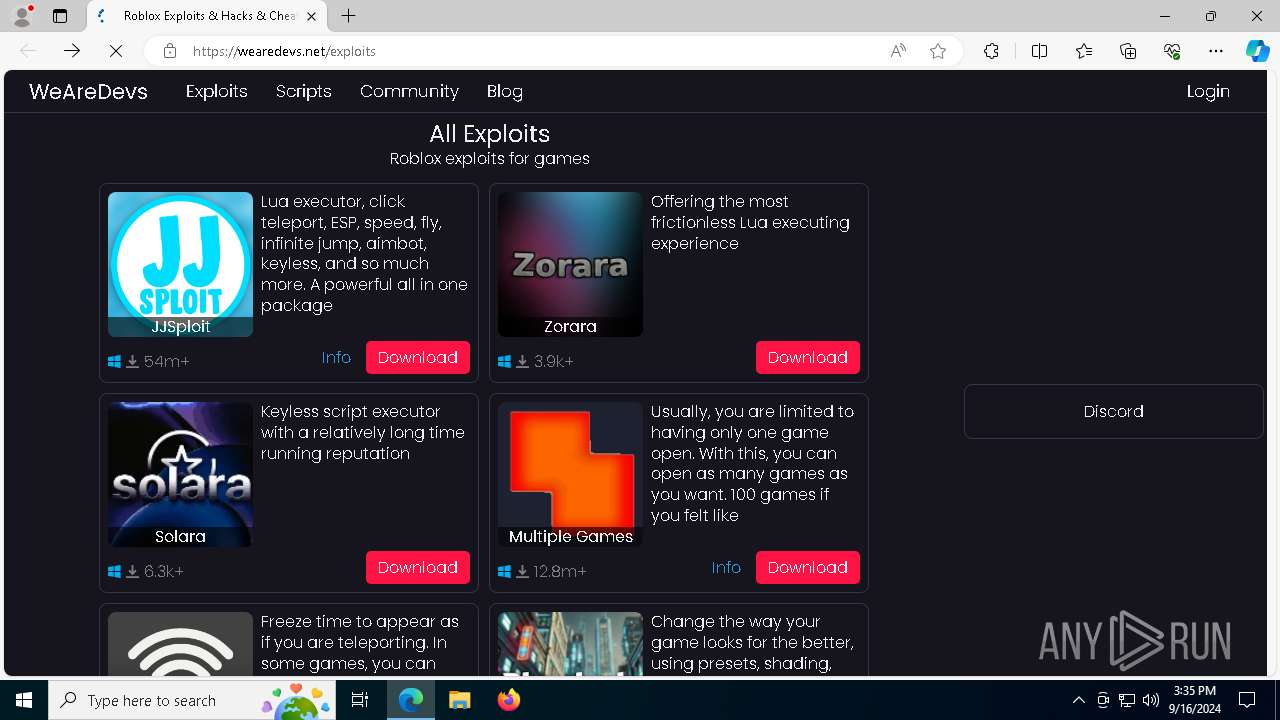
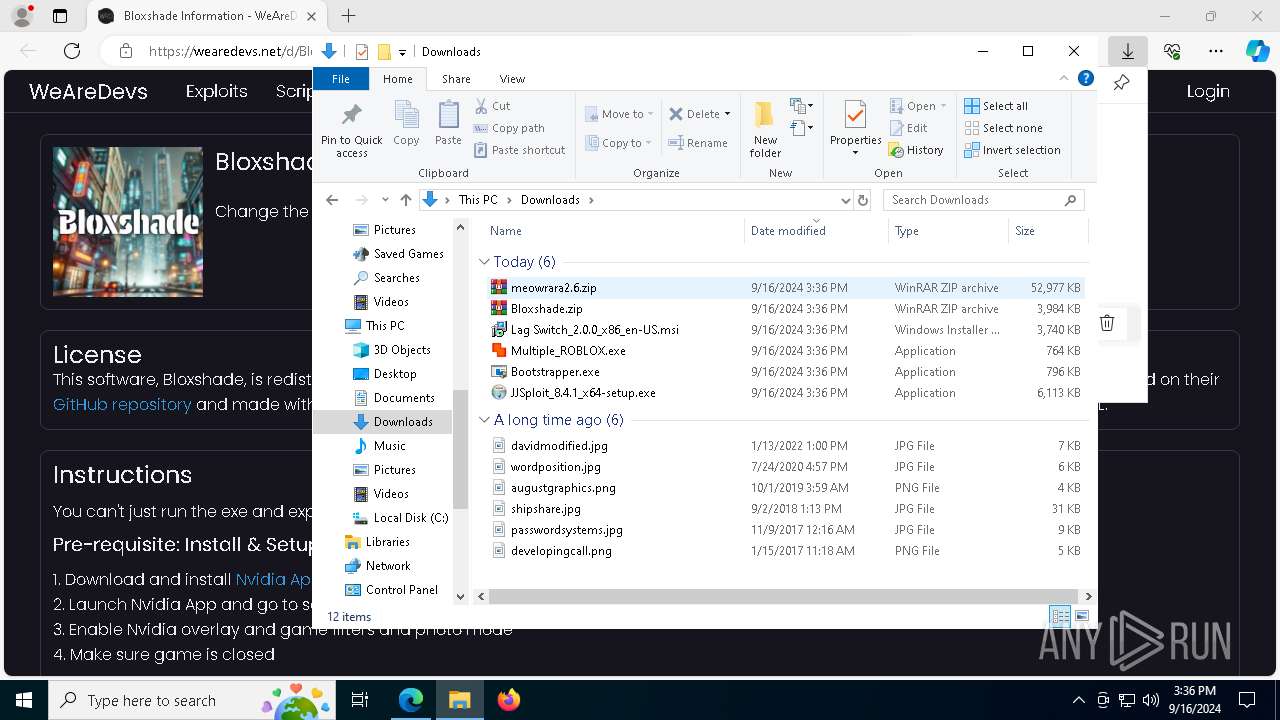
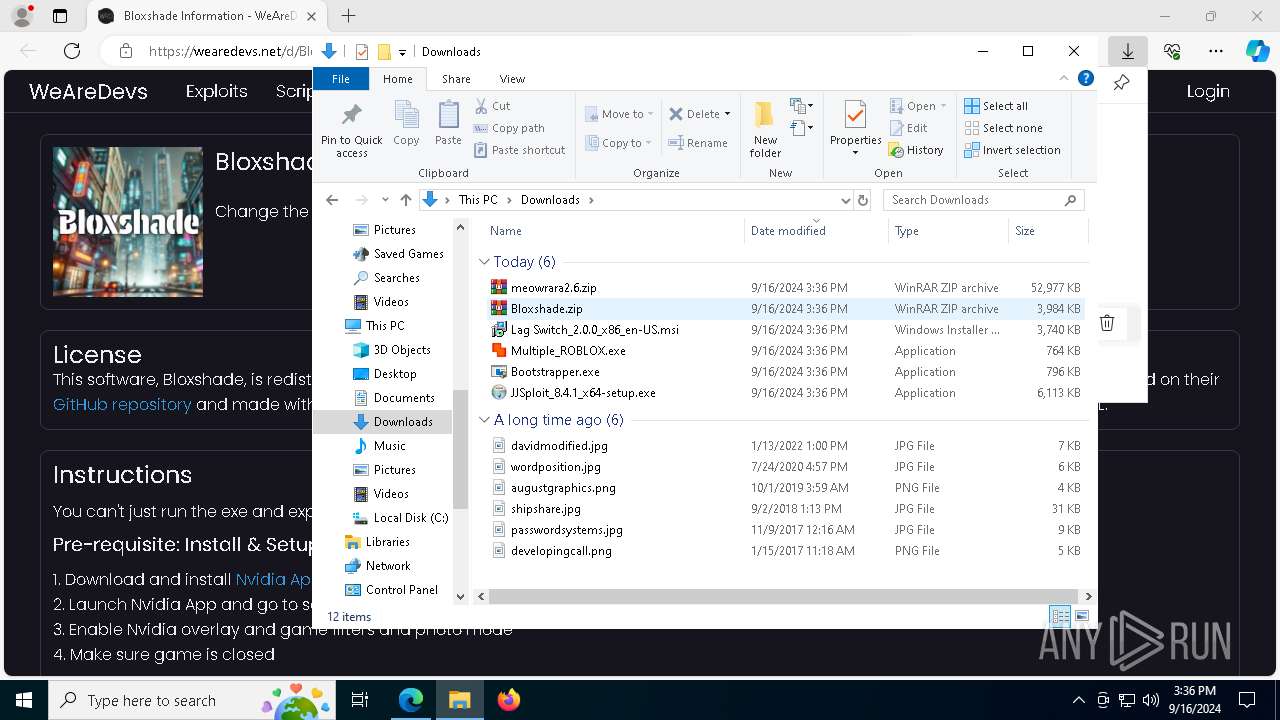
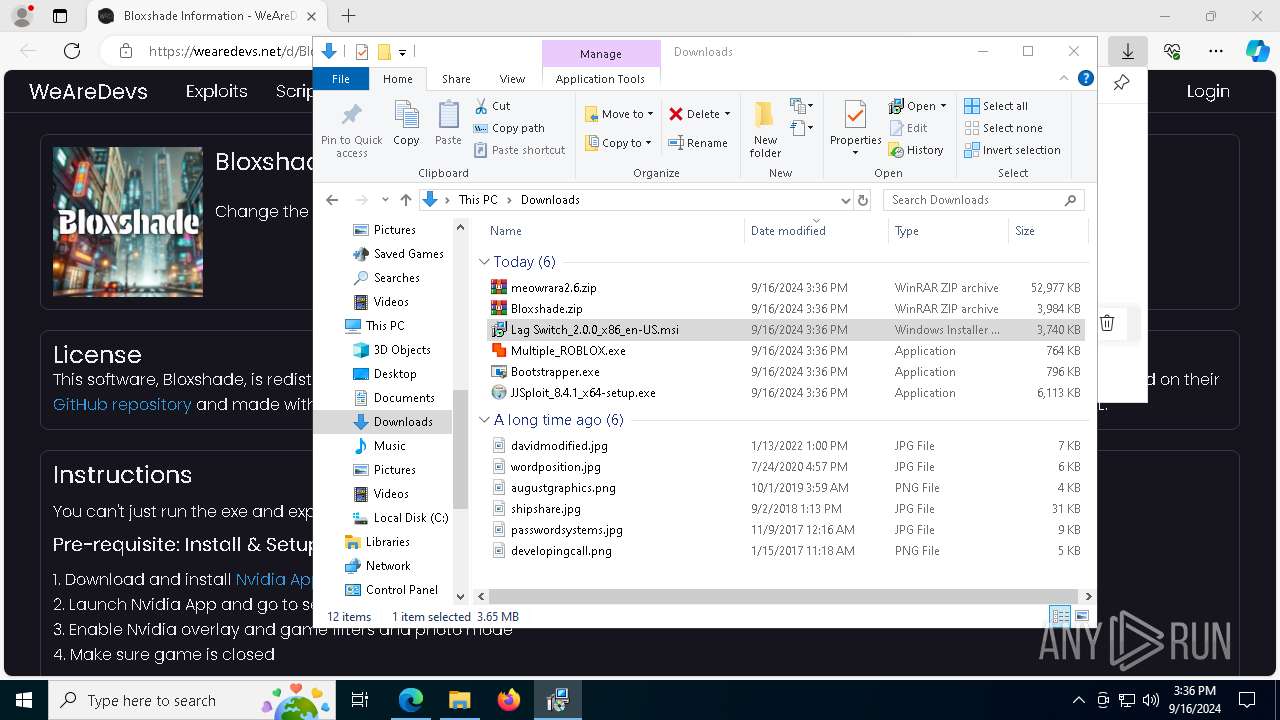
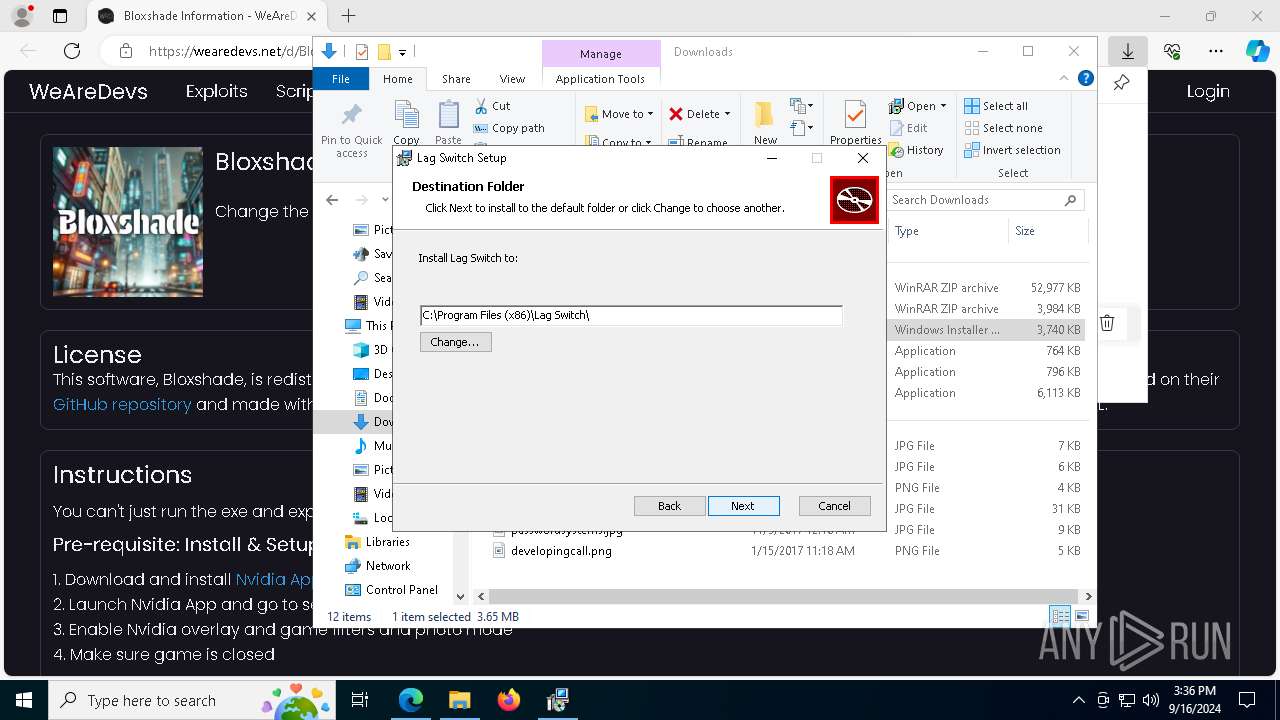
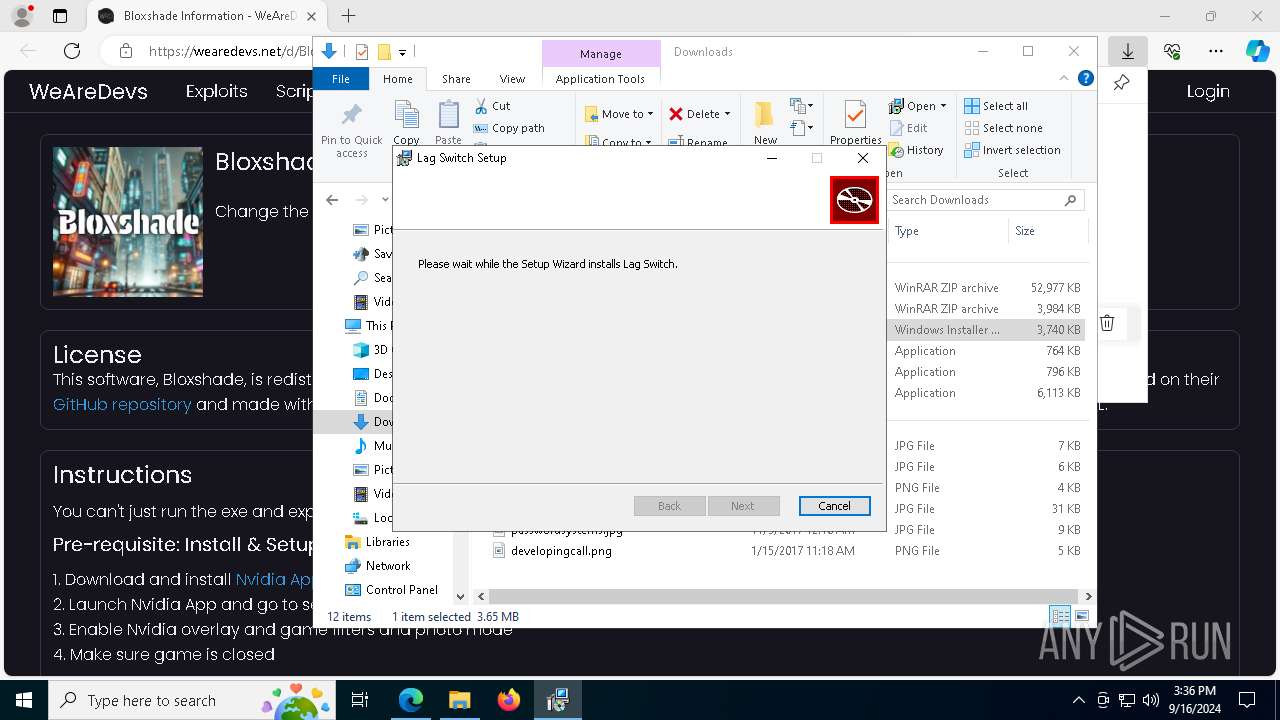
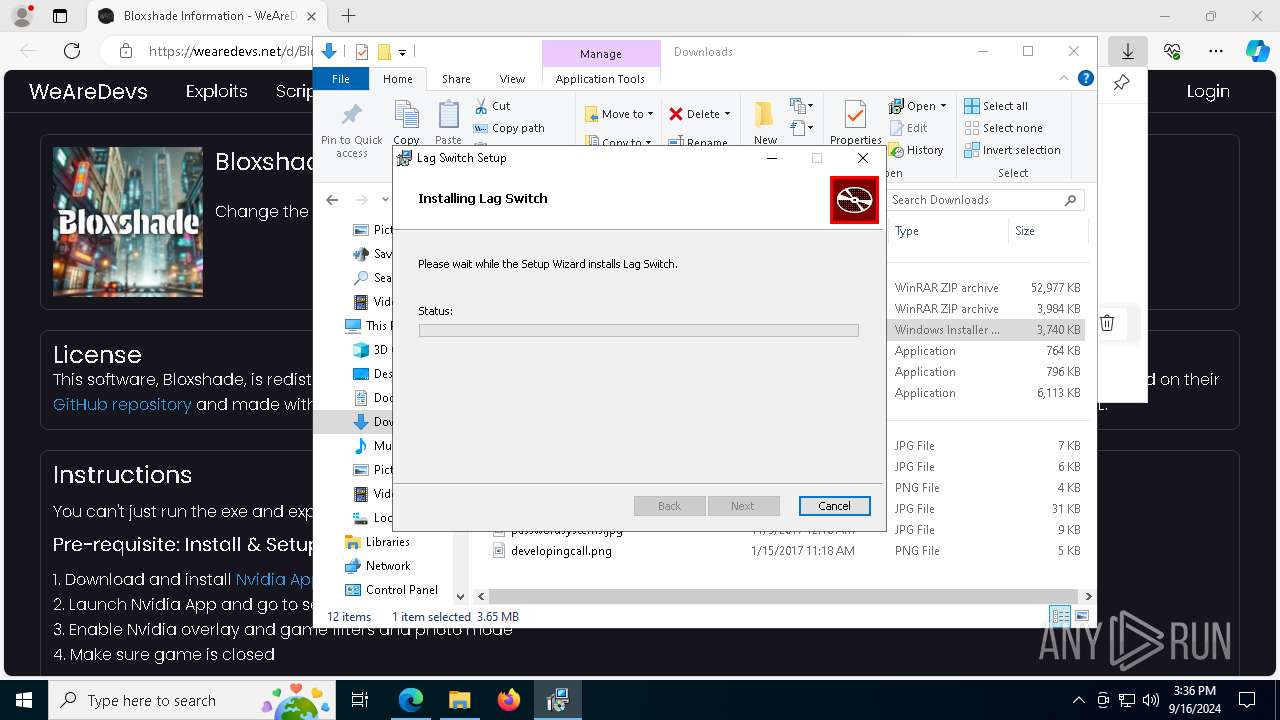
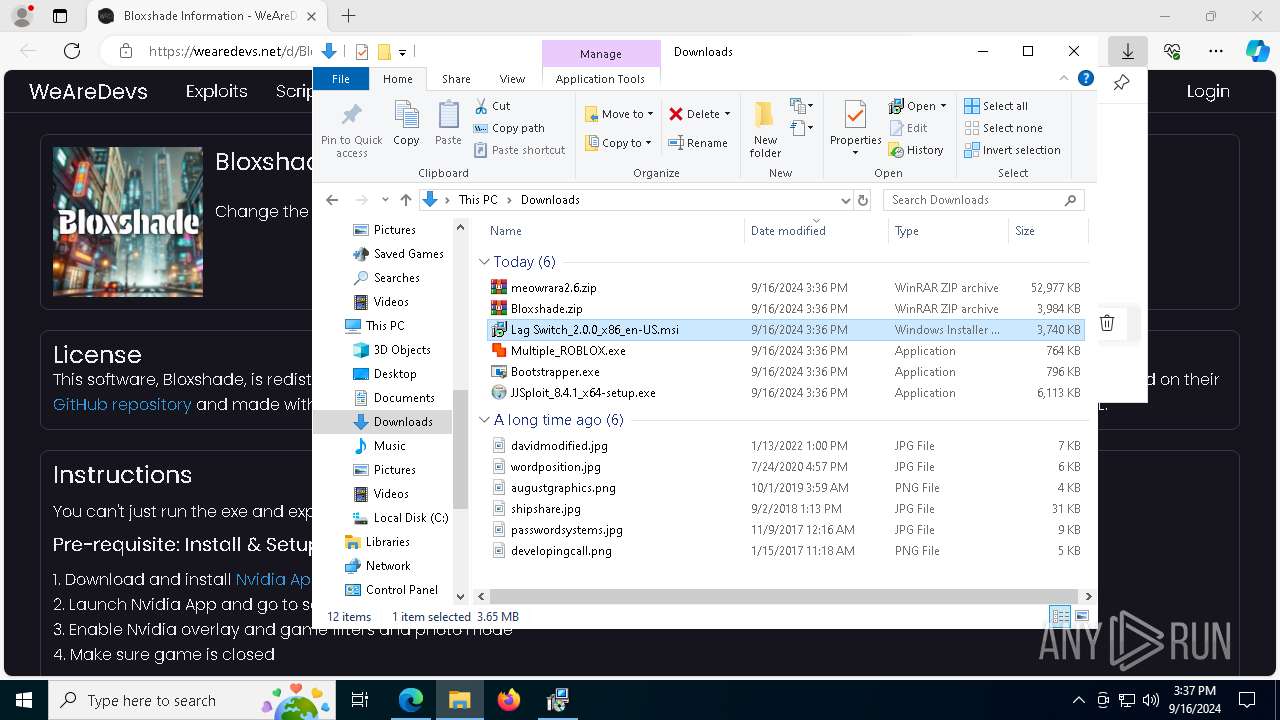
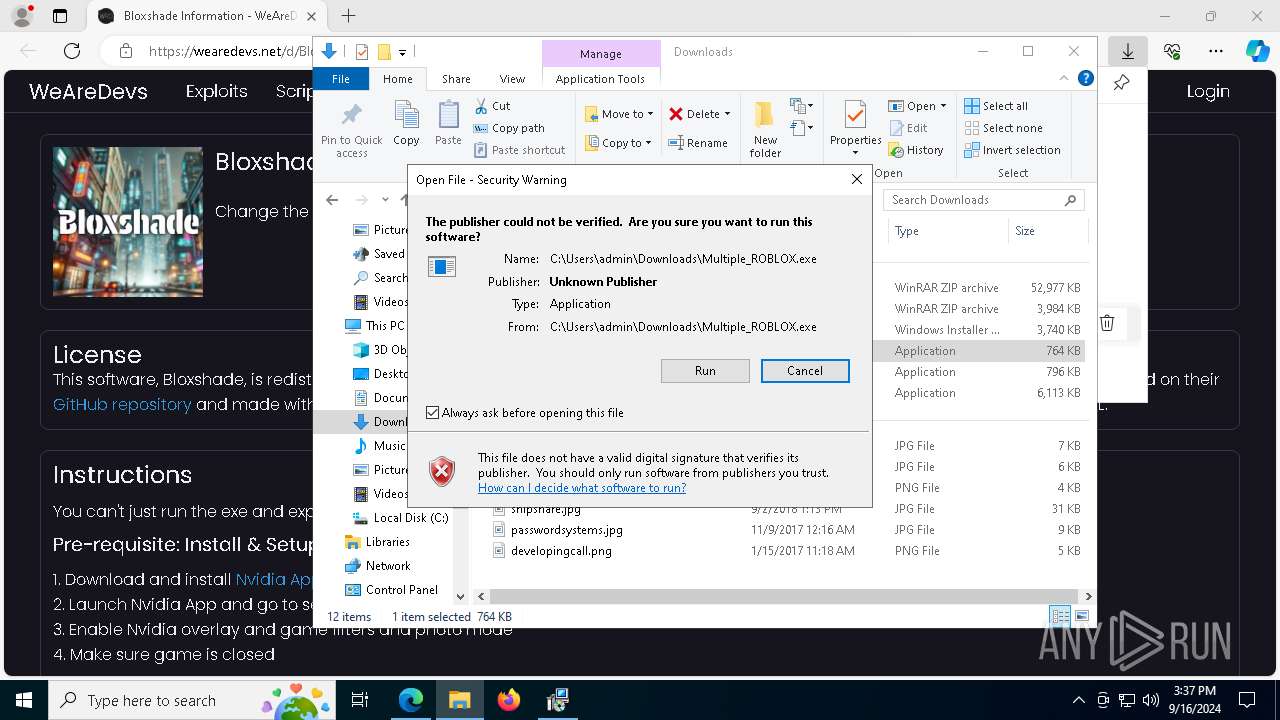
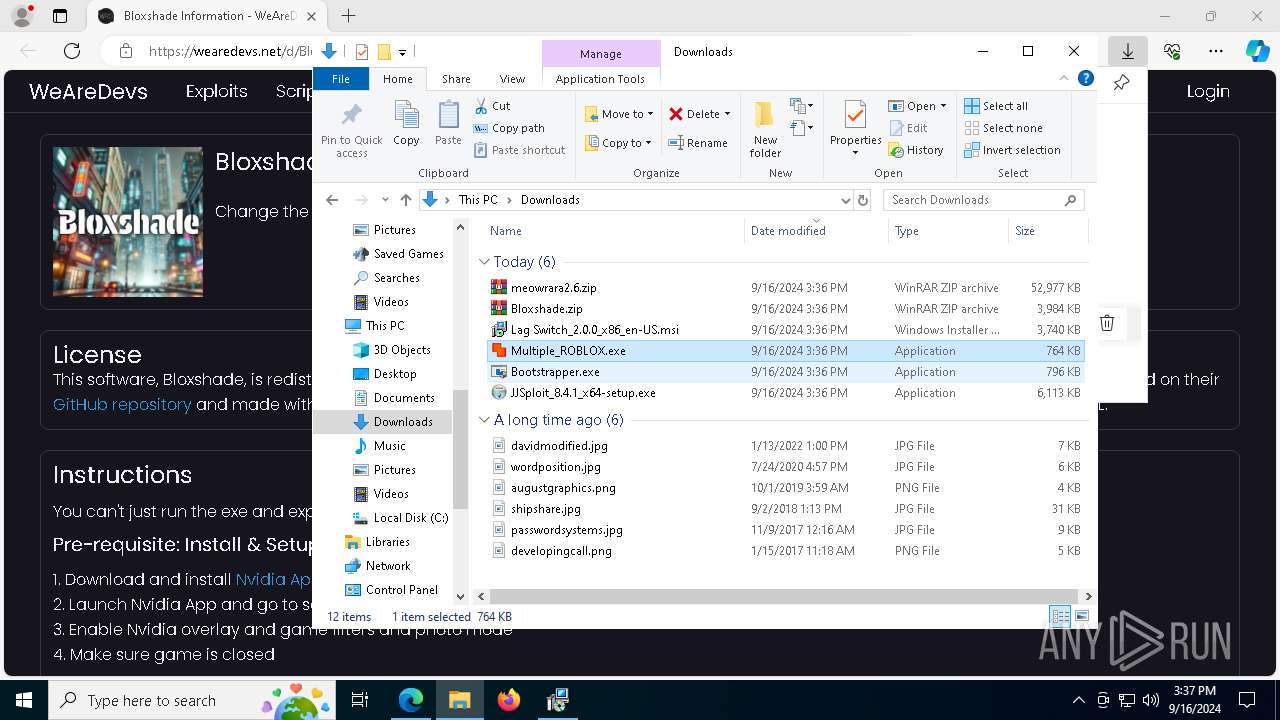
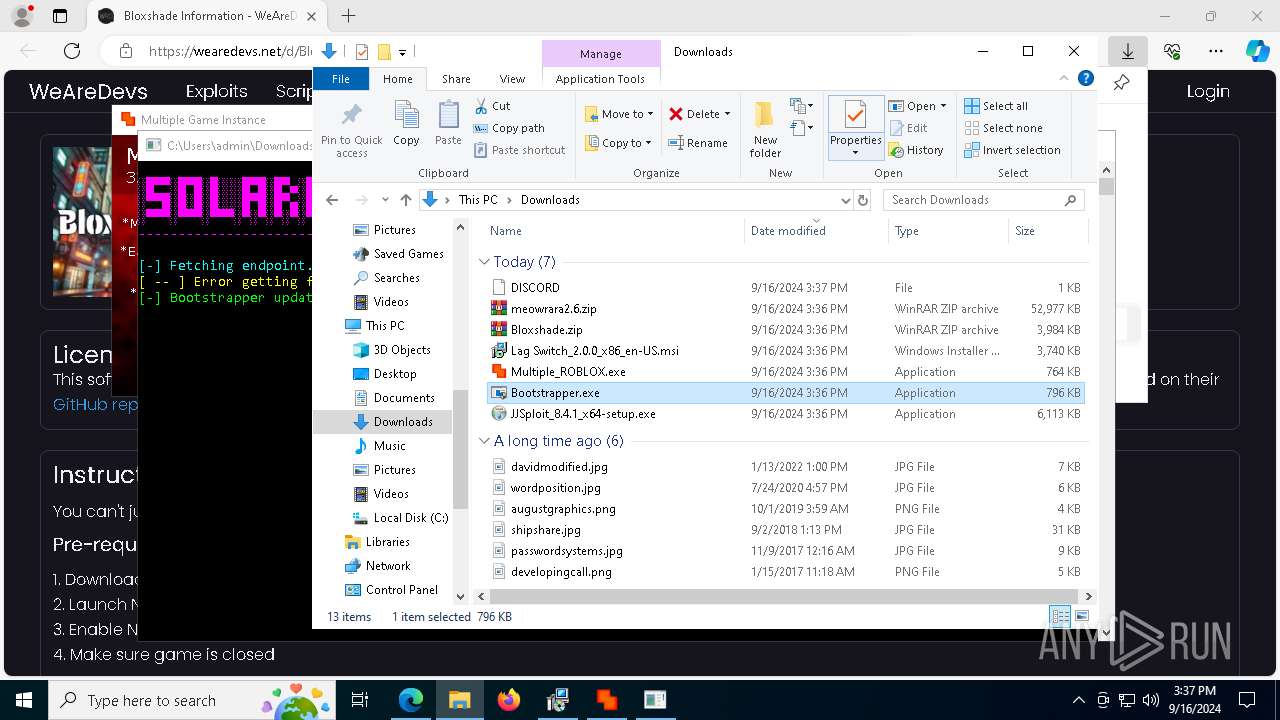
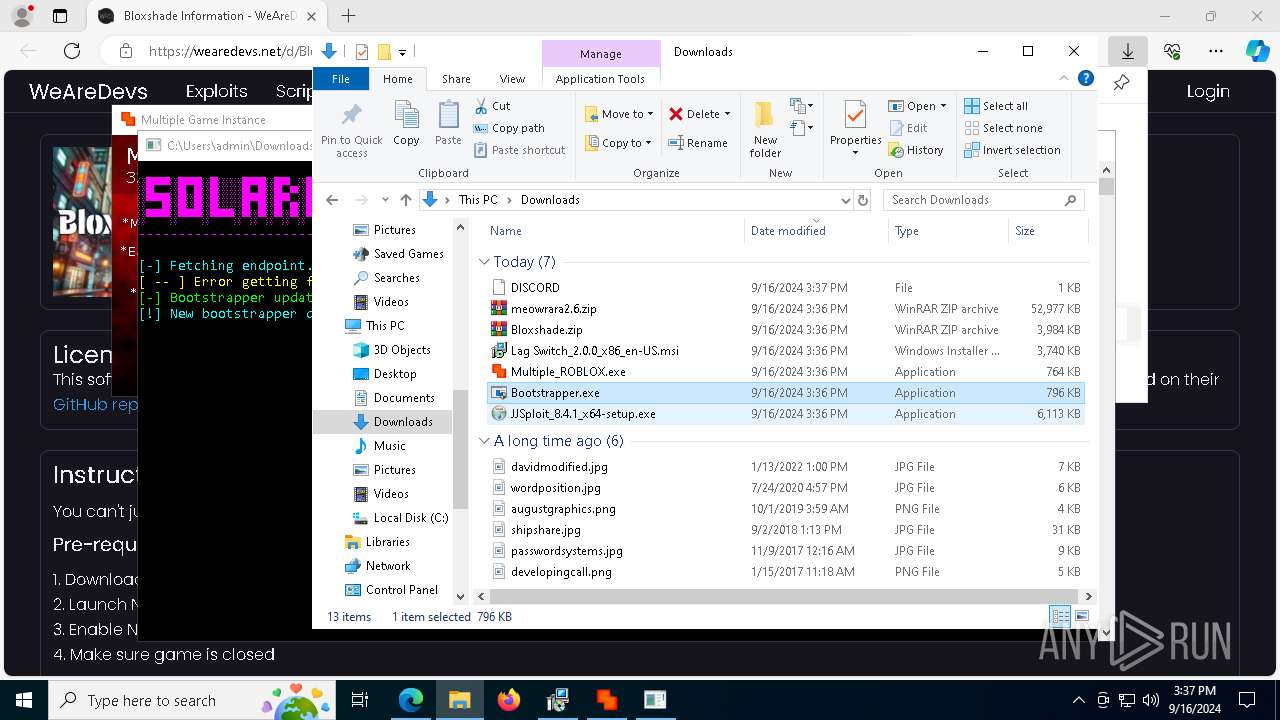
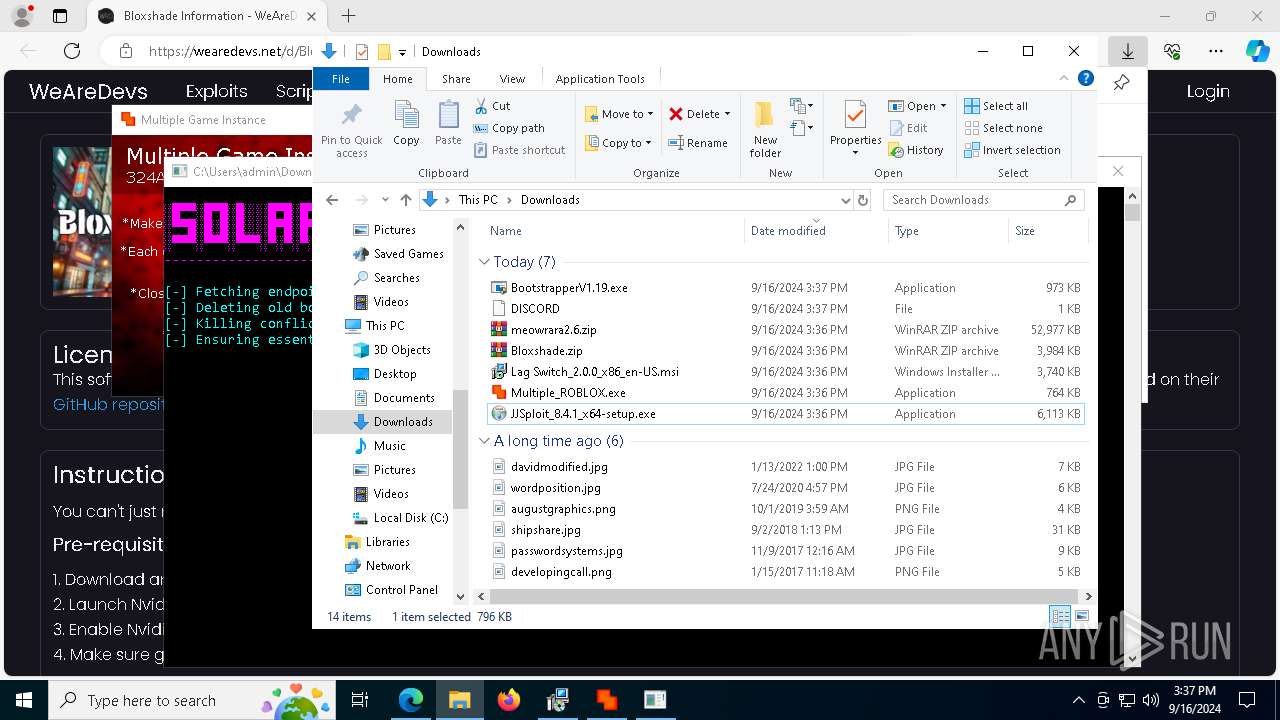
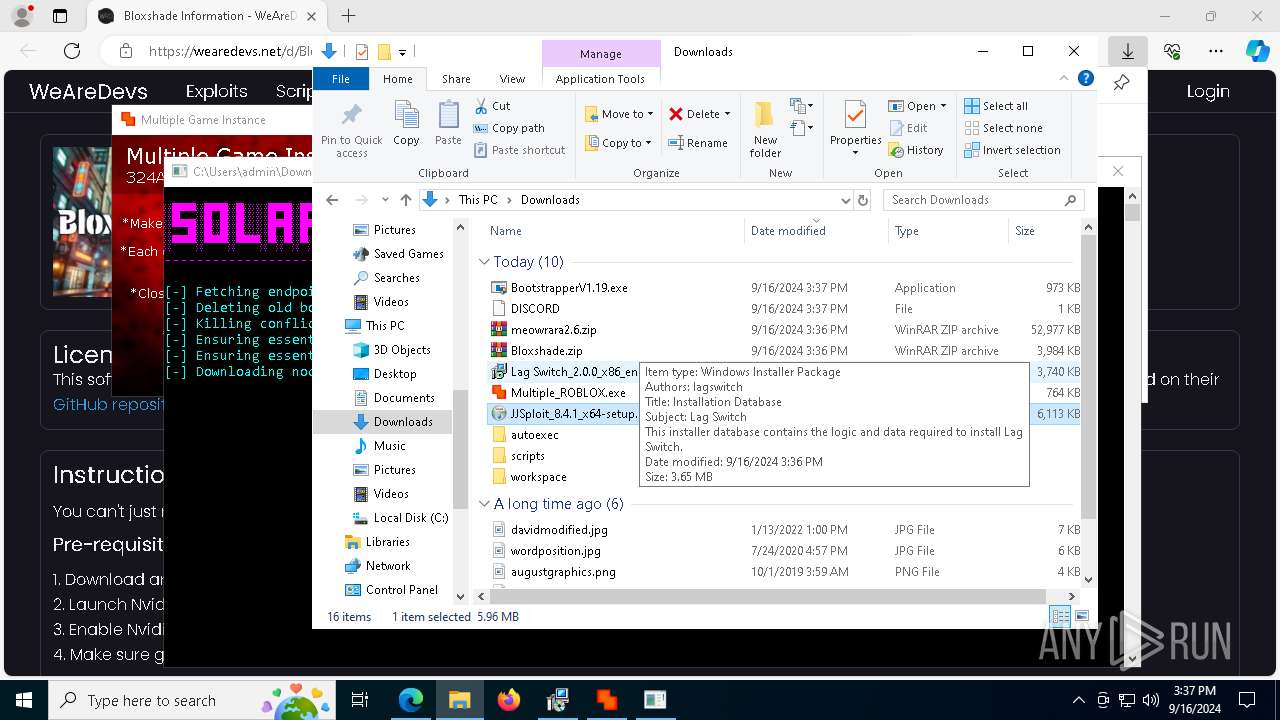
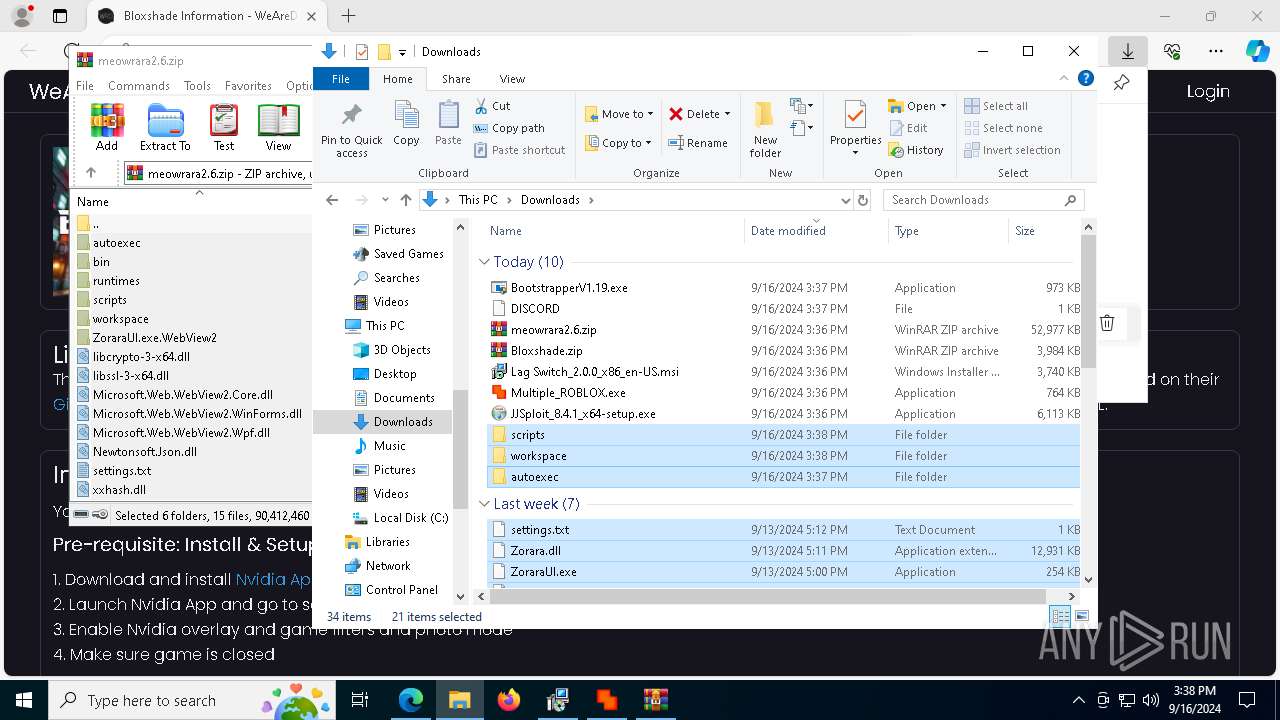
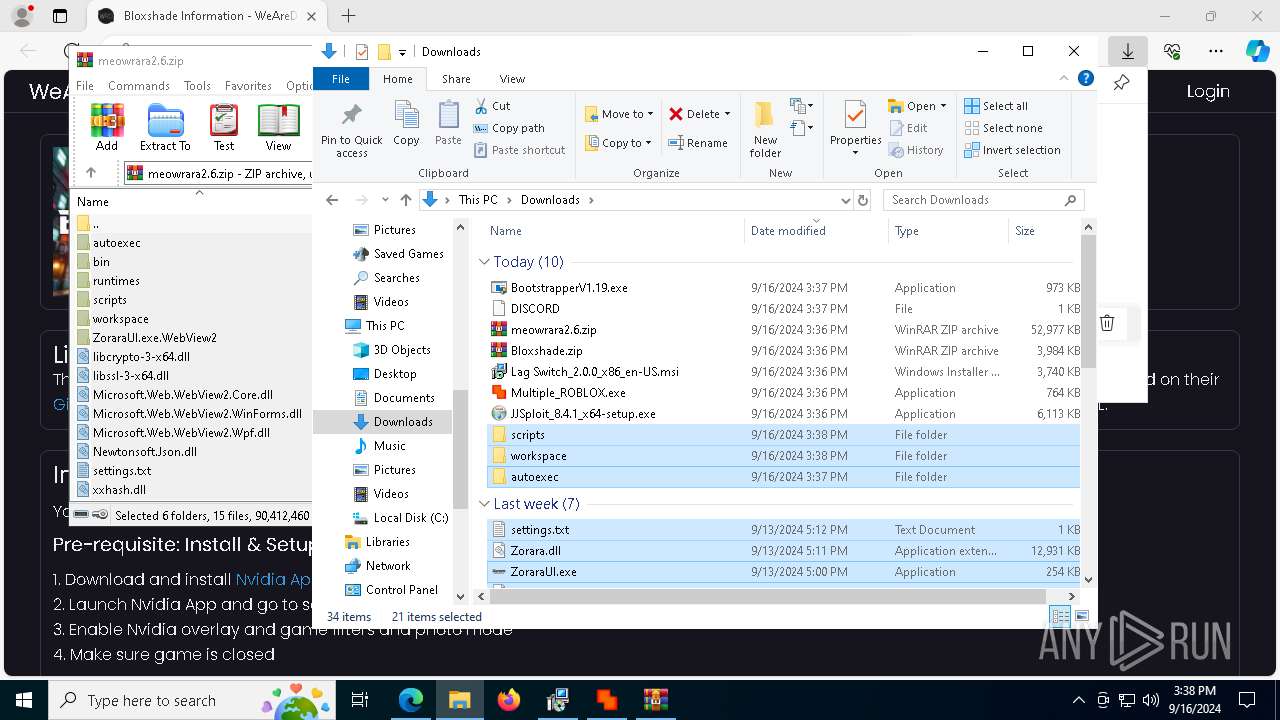
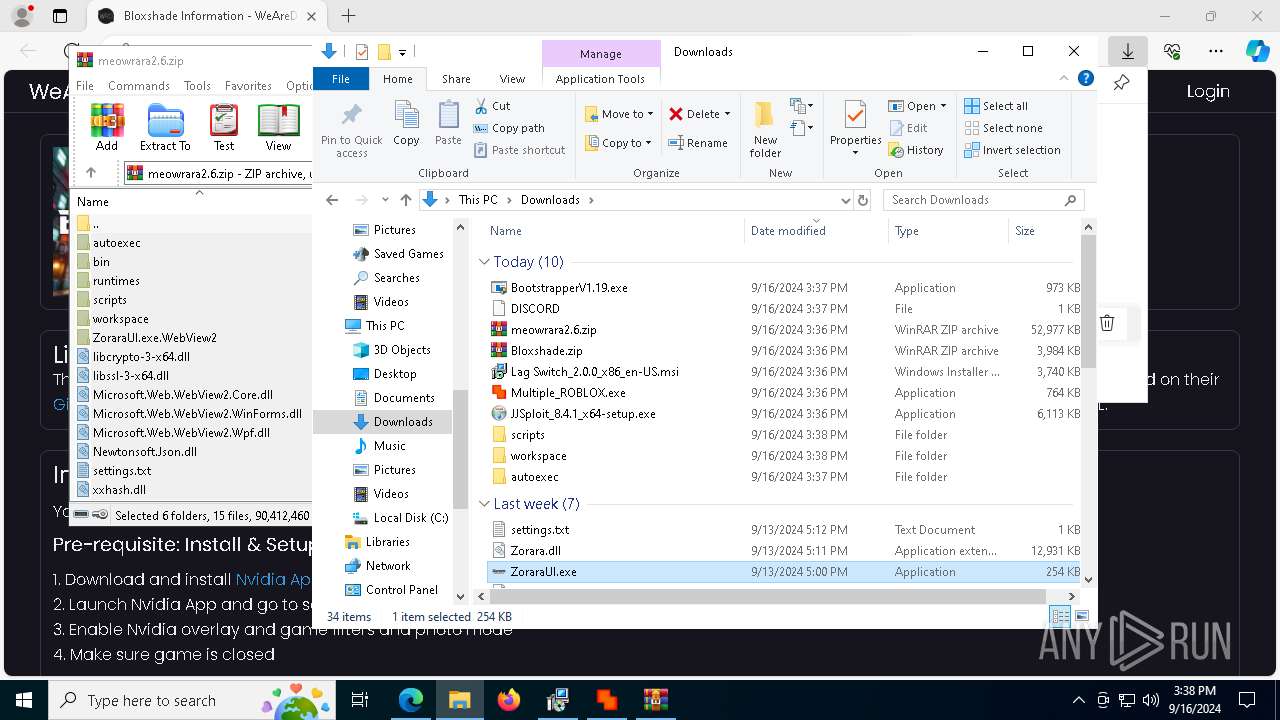
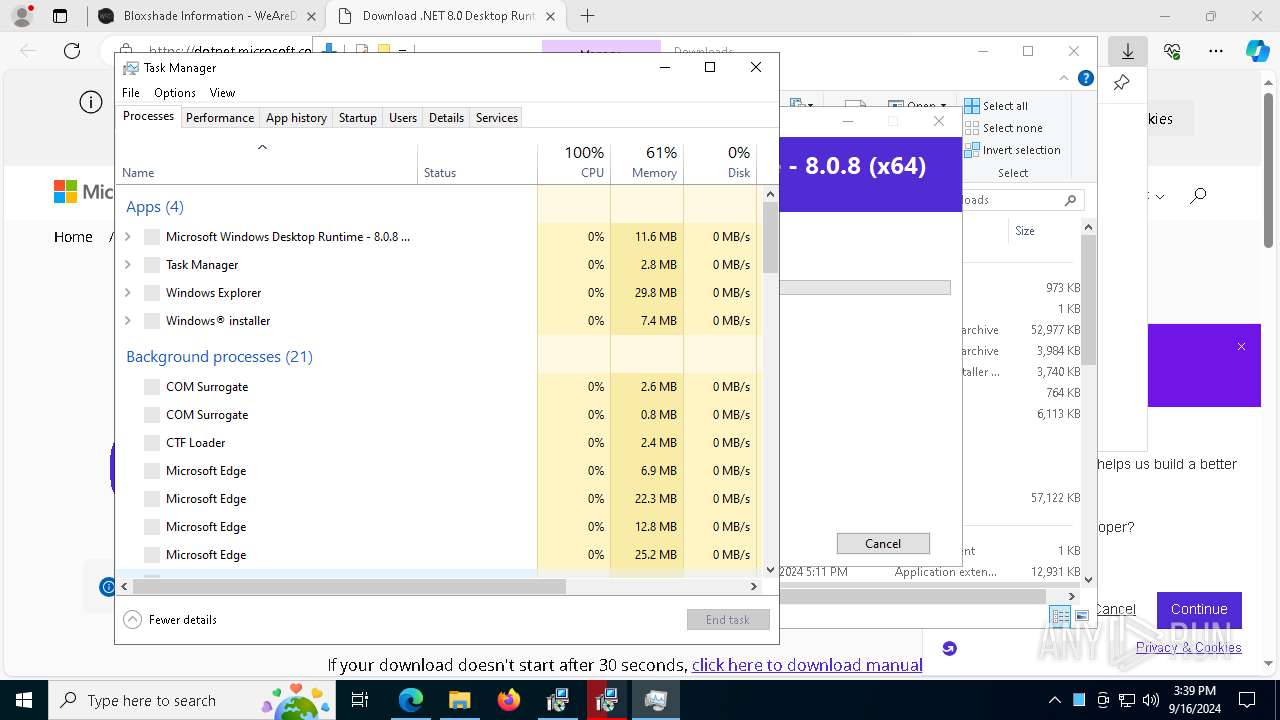
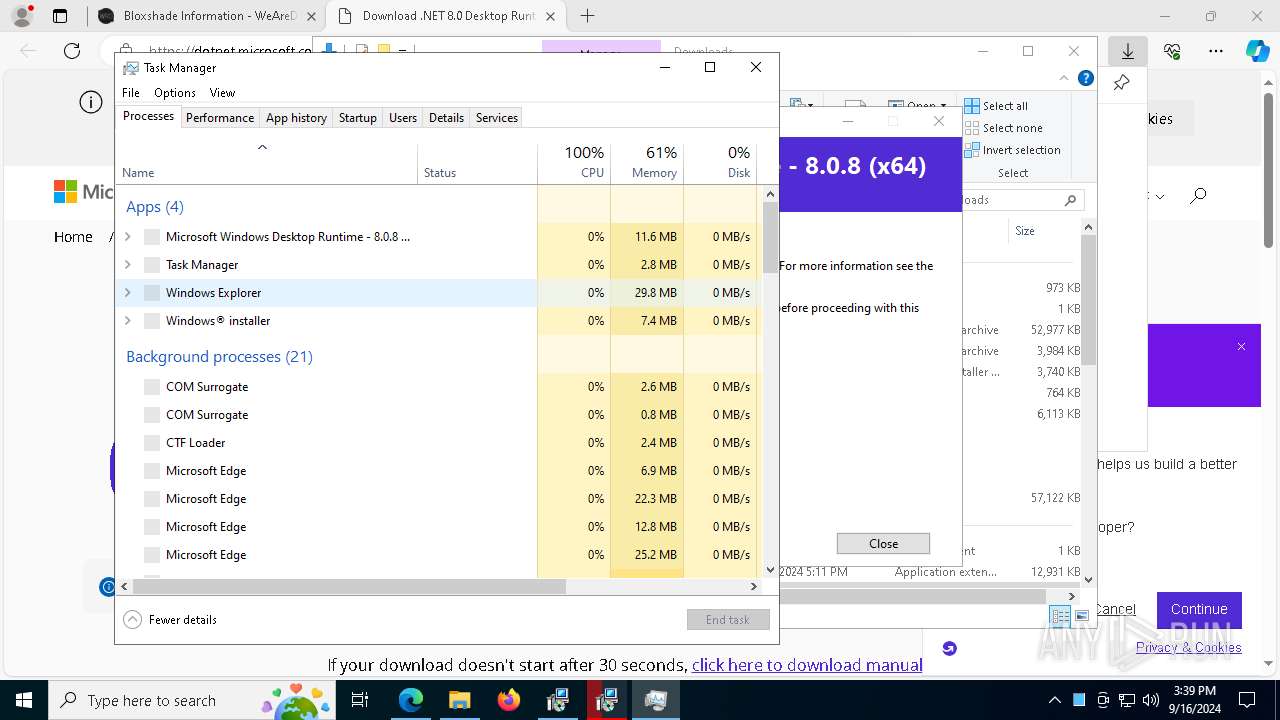
Manual execution by a user
- msiexec.exe (PID: 7936)
- Bootstrapper.exe (PID: 4132)
- Bootstrapper.exe (PID: 6728)
- Multiple_ROBLOX.exe (PID: 2112)
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
- WinRAR.exe (PID: 5304)
- ZoraraUI.exe (PID: 320)
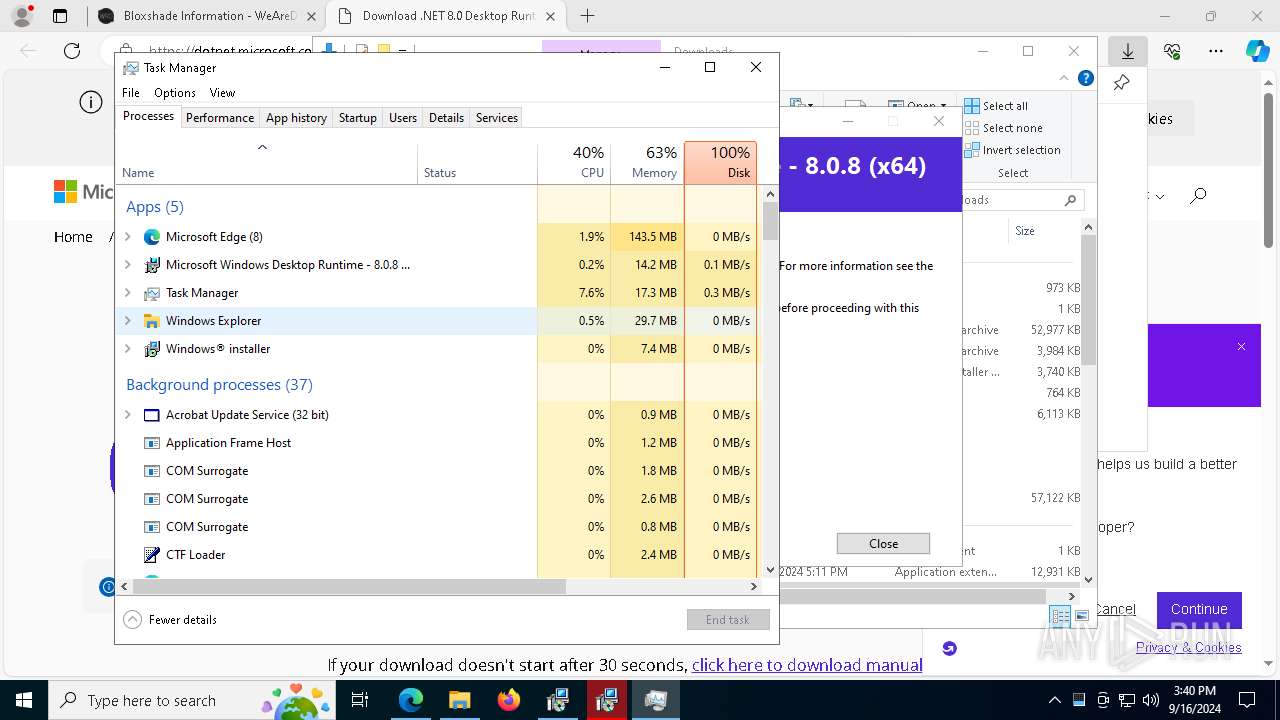
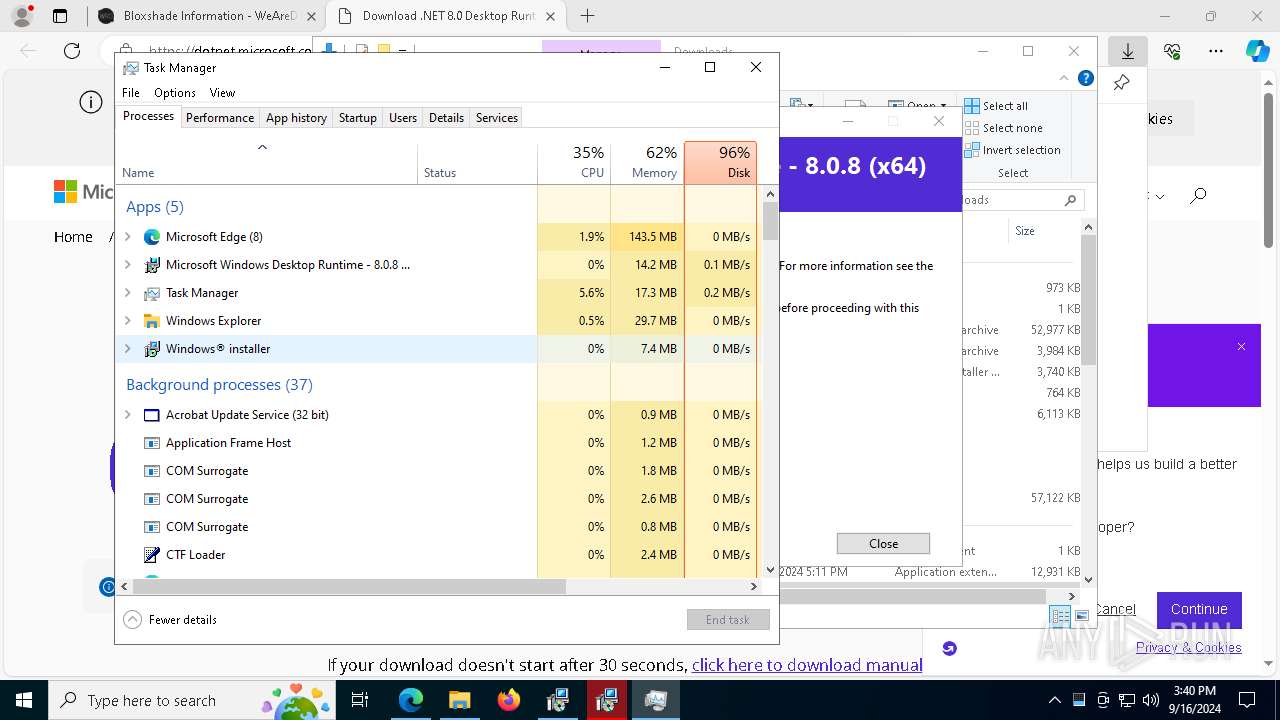
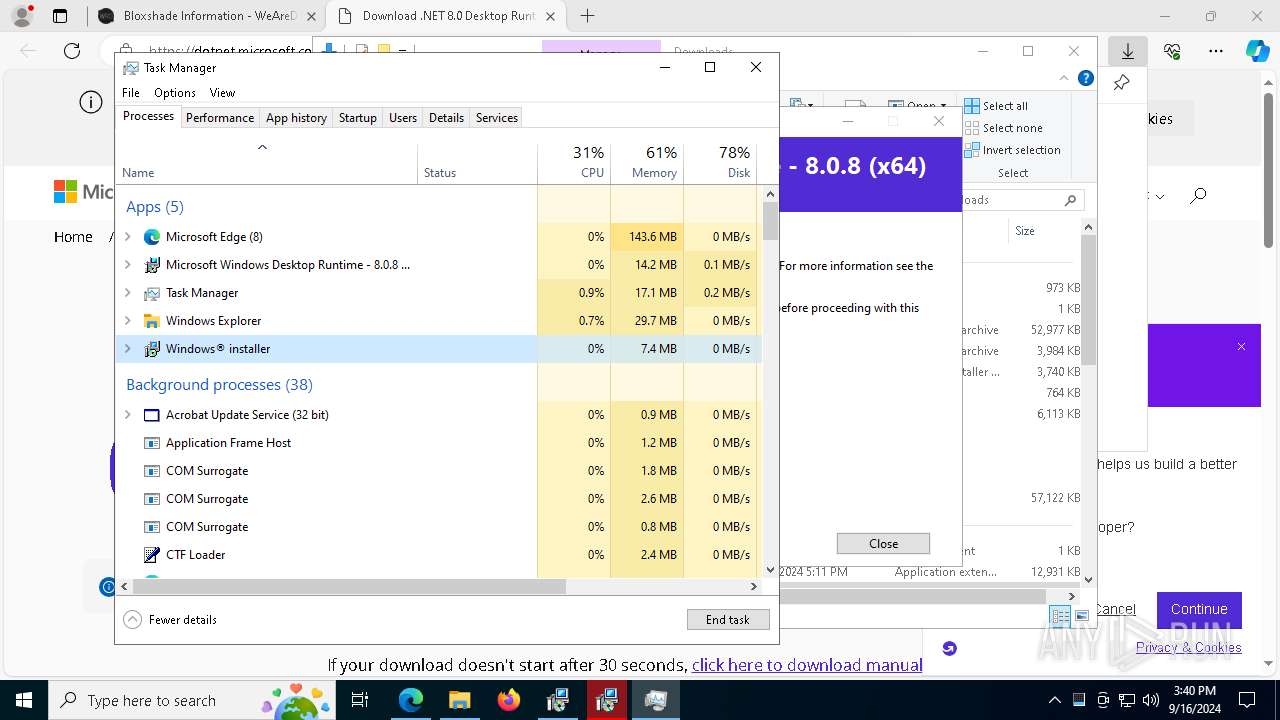
- Taskmgr.exe (PID: 3160)
- Taskmgr.exe (PID: 3040)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7936)
- msedge.exe (PID: 5092)
- msedge.exe (PID: 5000)
- msedge.exe (PID: 3652)
- msiexec.exe (PID: 4088)
- WinRAR.exe (PID: 5304)
Create files in a temporary directory
- svchost.exe (PID: 2360)
- BootstrapperV1.19.exe (PID: 6344)
- MicrosoftEdgeWebview2Setup.exe (PID: 5900)
- JJSploit_8.4.1_x64-setup.exe (PID: 2904)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7472)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
Application launched itself
- msedge.exe (PID: 5000)
Reads the machine GUID from the registry
- Multiple_ROBLOX.exe (PID: 2112)
- Bootstrapper.exe (PID: 6728)
- BootstrapperV1.19.exe (PID: 6344)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
- MicrosoftEdgeUpdate.exe (PID: 3176)
Reads the software policy settings
- Bootstrapper.exe (PID: 6728)
- BootstrapperV1.19.exe (PID: 6344)
- MicrosoftEdgeUpdate.exe (PID: 7964)
- MicrosoftEdgeUpdate.exe (PID: 3176)
Checks proxy server information
- Bootstrapper.exe (PID: 6728)
- BootstrapperV1.19.exe (PID: 6344)
- powershell.exe (PID: 7416)
- MicrosoftEdgeUpdate.exe (PID: 7964)
- MicrosoftEdgeUpdate.exe (PID: 3176)
Disables trace logs
- Bootstrapper.exe (PID: 6728)
- BootstrapperV1.19.exe (PID: 6344)
- powershell.exe (PID: 7416)
Process checks computer location settings
- Bootstrapper.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 7340)
- BootstrapperV1.19.exe (PID: 6344)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 6224)
Creates a software uninstall entry
- msiexec.exe (PID: 4088)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 5900)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 3176)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 8116)
- setup.exe (PID: 2092)
- setup.exe (PID: 8004)
Creates files in the program directory
- BootstrapperV1.19.exe (PID: 6344)
- windowsdesktop-runtime-8.0.8-win-x64.exe (PID: 7792)
Sends debugging messages
- ZoraraUI.exe (PID: 320)
- ShellExperienceHost.exe (PID: 4072)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
280
Monitored processes
141
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=99 --mojo-platform-channel-handle=4248 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 320 | "C:\Users\admin\Downloads\ZoraraUI.exe" | C:\Users\admin\Downloads\ZoraraUI.exe | explorer.exe | ||||||||||||
User: admin Company: XenoUI Integrity Level: MEDIUM Description: ZoraraUI Exit code: 2147516547 Version: 1.0.2 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=52 --mojo-platform-channel-handle=1332 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=9060 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6120 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7692 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=1352 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=8820 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=75 --mojo-platform-channel-handle=1548 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=6348 --field-trial-handle=2248,i,6830972971331056431,14164155213712704968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 610
Read events
35 814
Write events
4 732
Delete events
64
Modification events
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 371DF899D4802F00 | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EECD039AD4802F00 | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459424 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {27BDA2C6-0154-4D97-8780-C1B55B9EEC34} | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459424 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {556612CF-2A13-41A3-AAC3-CD73D8E00AB2} | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459424 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EBBF2BDC-A86B-49F5-A24C-65CBEF9B7E37} | |||
| (PID) Process: | (5000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459424 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {68A8CFB9-EF39-46F9-803C-0BB971131DC3} | |||
Executable files
270
Suspicious files
906
Text files
396
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12aa80.TMP | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12aa90.TMP | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12aa61.TMP | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12aabf.TMP | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12aaaf.TMP | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF12aade.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
198
DNS requests
213
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2360 | svchost.exe | HEAD | 200 | 23.48.23.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726546773&P2=404&P3=2&P4=AzuAGfI6rRTX3%2fupnMnHh4t6xL5Fxi63a1e7joNuwh4%2bpneKsLt%2bfeIirYjssn60WVHtIQNQpMAH5vGZ6byyow%3d%3d | unknown | — | — | whitelisted |
6484 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6484 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2036 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2360 | svchost.exe | GET | 206 | 23.48.23.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726546773&P2=404&P3=2&P4=AzuAGfI6rRTX3%2fupnMnHh4t6xL5Fxi63a1e7joNuwh4%2bpneKsLt%2bfeIirYjssn60WVHtIQNQpMAH5vGZ6byyow%3d%3d | unknown | — | — | whitelisted |
2360 | svchost.exe | GET | 206 | 23.48.23.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726546773&P2=404&P3=2&P4=AzuAGfI6rRTX3%2fupnMnHh4t6xL5Fxi63a1e7joNuwh4%2bpneKsLt%2bfeIirYjssn60WVHtIQNQpMAH5vGZ6byyow%3d%3d | unknown | — | — | whitelisted |
2360 | svchost.exe | GET | 206 | 23.48.23.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1726546771&P2=404&P3=2&P4=Gx6HwH6RHR%2bO9ZvOeRZxHOudEhuhxUAWH9CsE2DWk8ccdliakNZcaudALCOolqkSg5KzRmTjCF8TrsQd8YJYKA%3d%3d | unknown | — | — | whitelisted |
2360 | svchost.exe | GET | 206 | 23.48.23.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726546773&P2=404&P3=2&P4=AzuAGfI6rRTX3%2fupnMnHh4t6xL5Fxi63a1e7joNuwh4%2bpneKsLt%2bfeIirYjssn60WVHtIQNQpMAH5vGZ6byyow%3d%3d | unknown | — | — | whitelisted |
2360 | svchost.exe | GET | 206 | 23.48.23.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726546773&P2=404&P3=2&P4=AzuAGfI6rRTX3%2fupnMnHh4t6xL5Fxi63a1e7joNuwh4%2bpneKsLt%2bfeIirYjssn60WVHtIQNQpMAH5vGZ6byyow%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6652 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6164 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5000 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5092 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5092 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wearedevs.net |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5092 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5092 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5092 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
5092 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5092 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
5092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
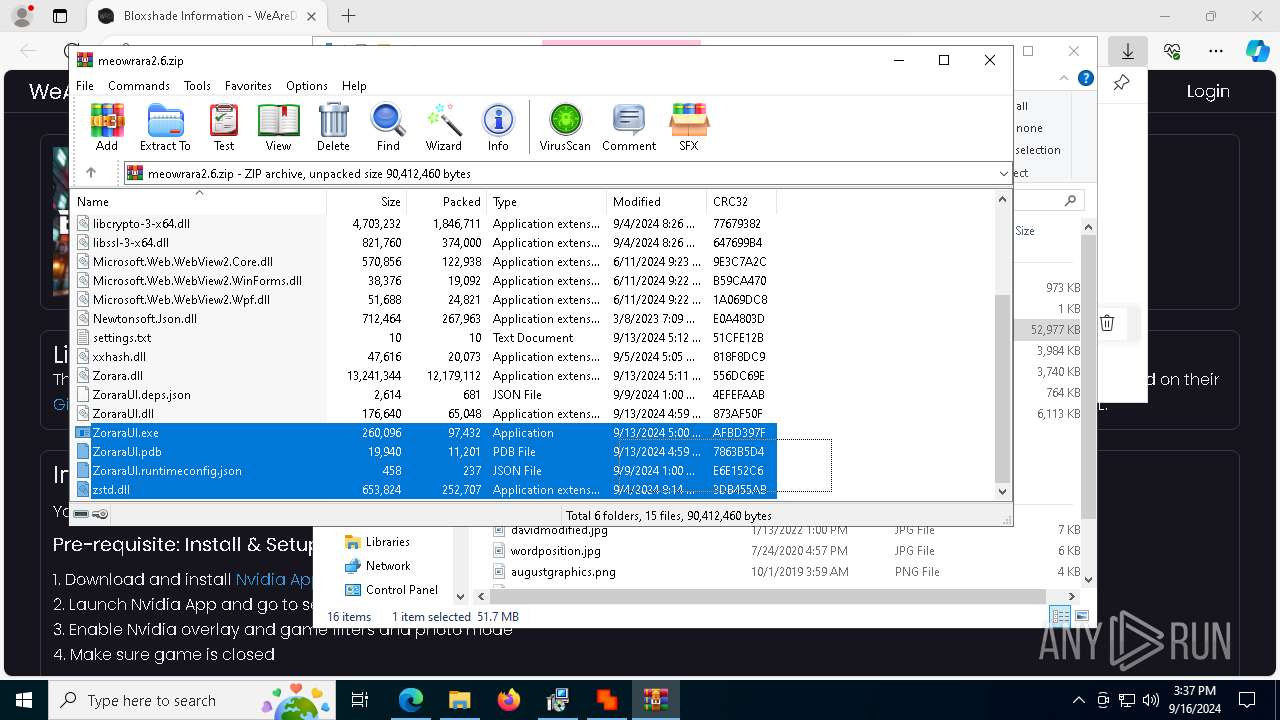
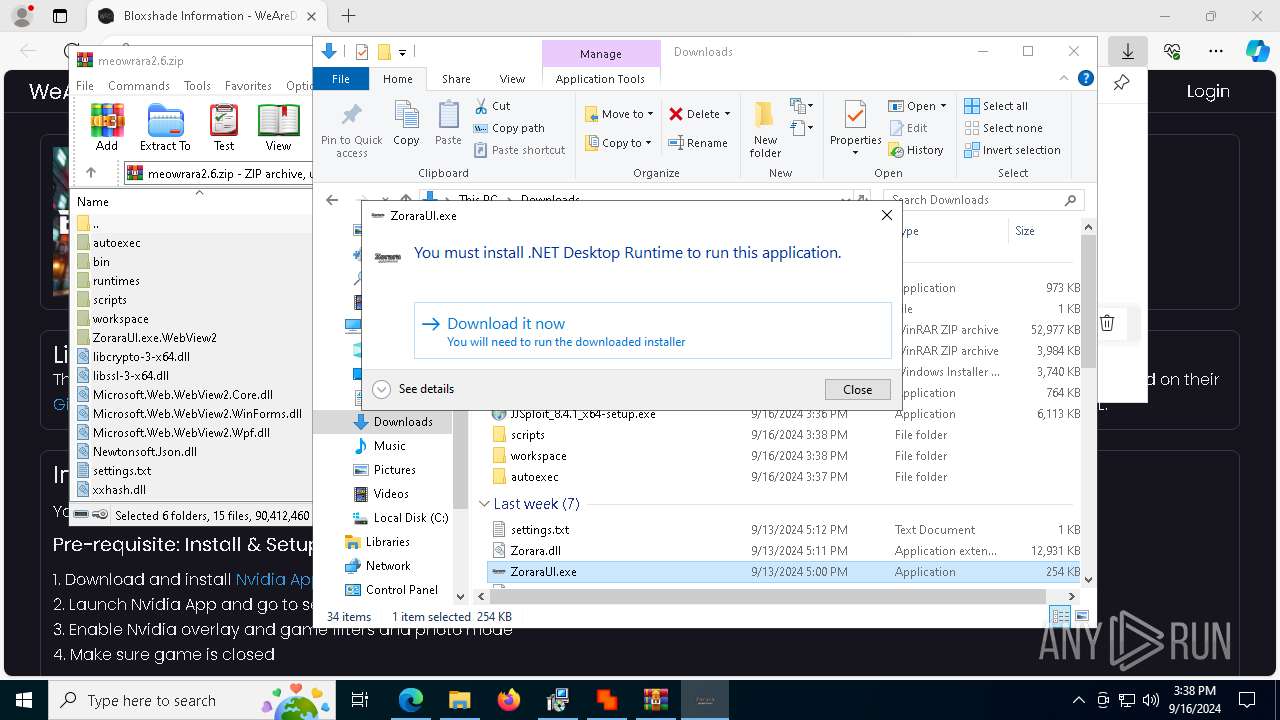
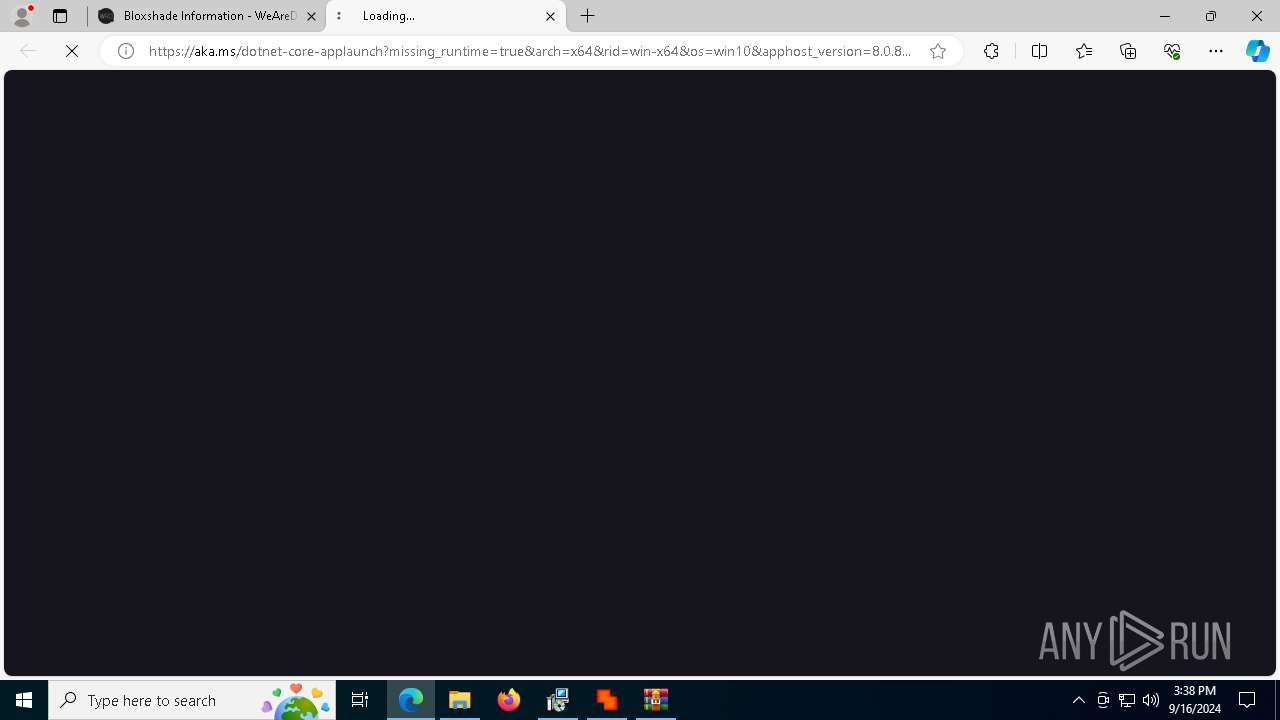
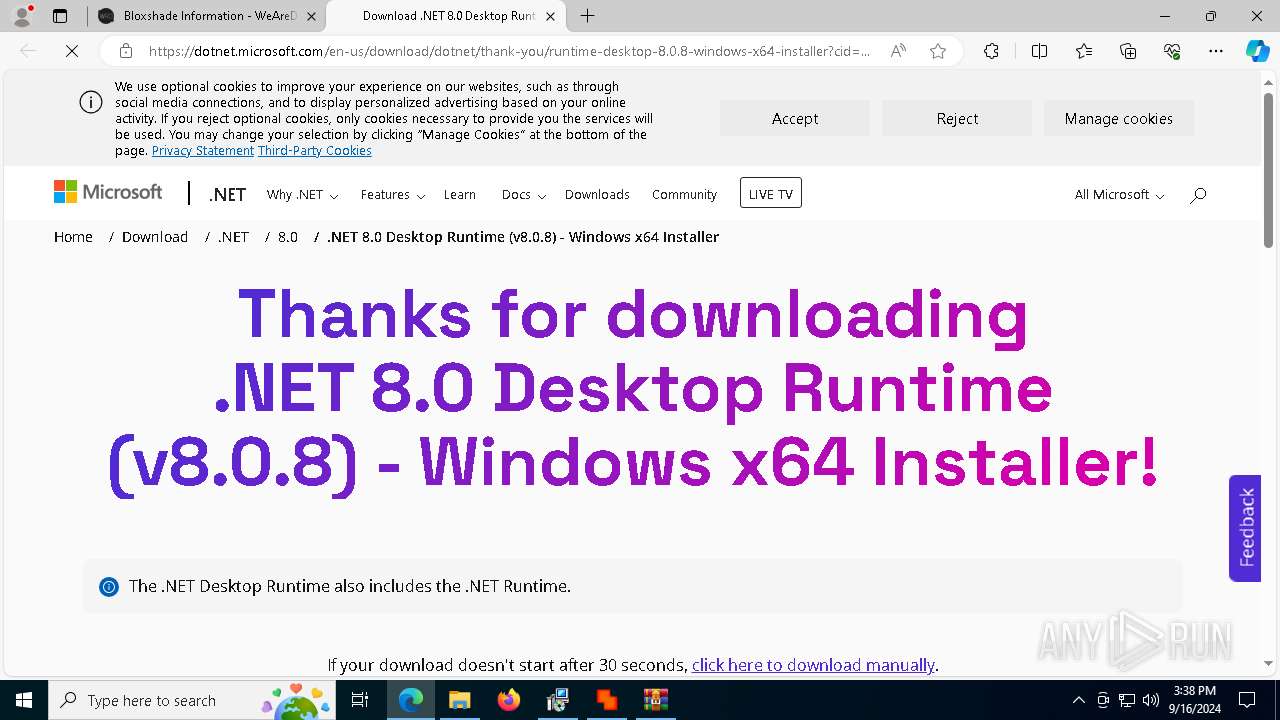
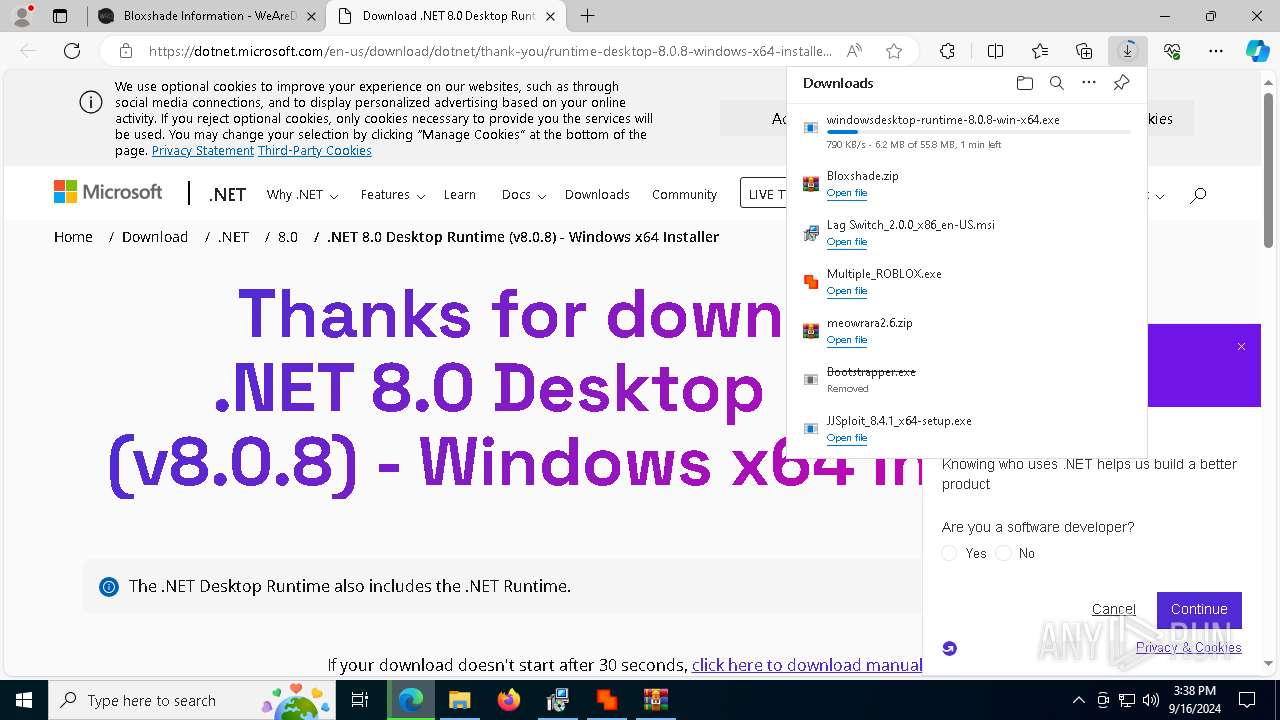
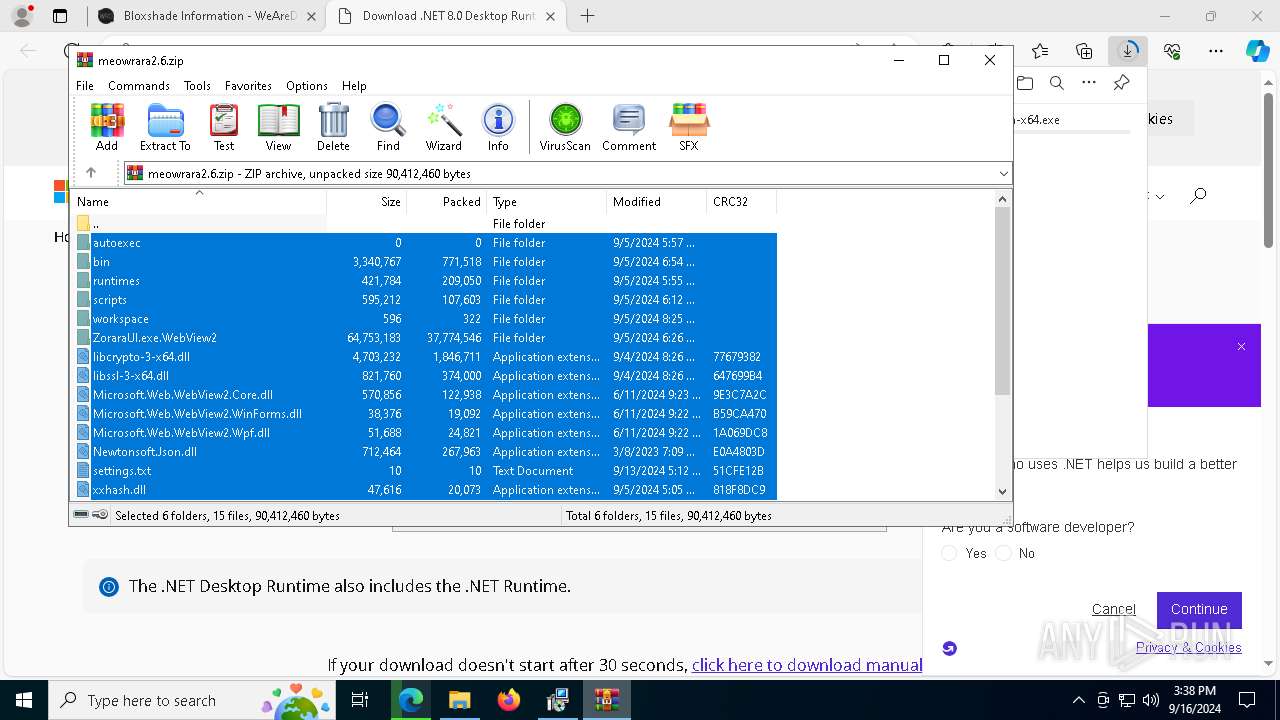
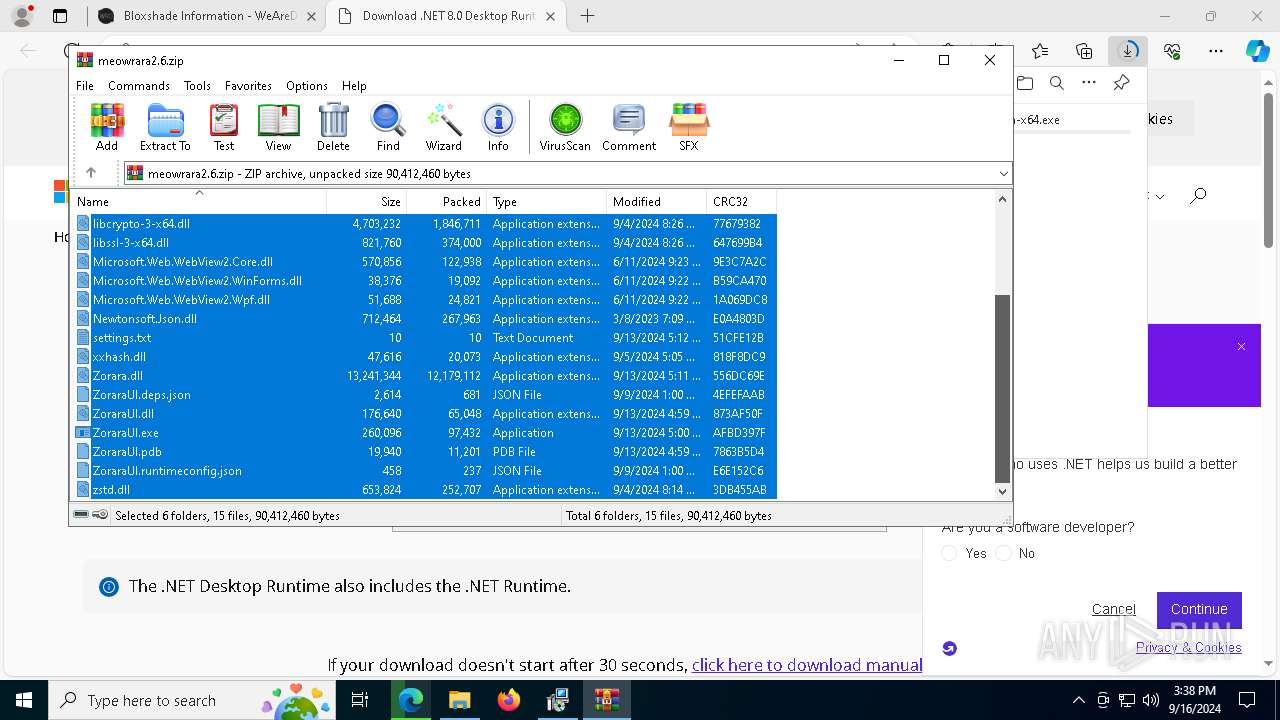
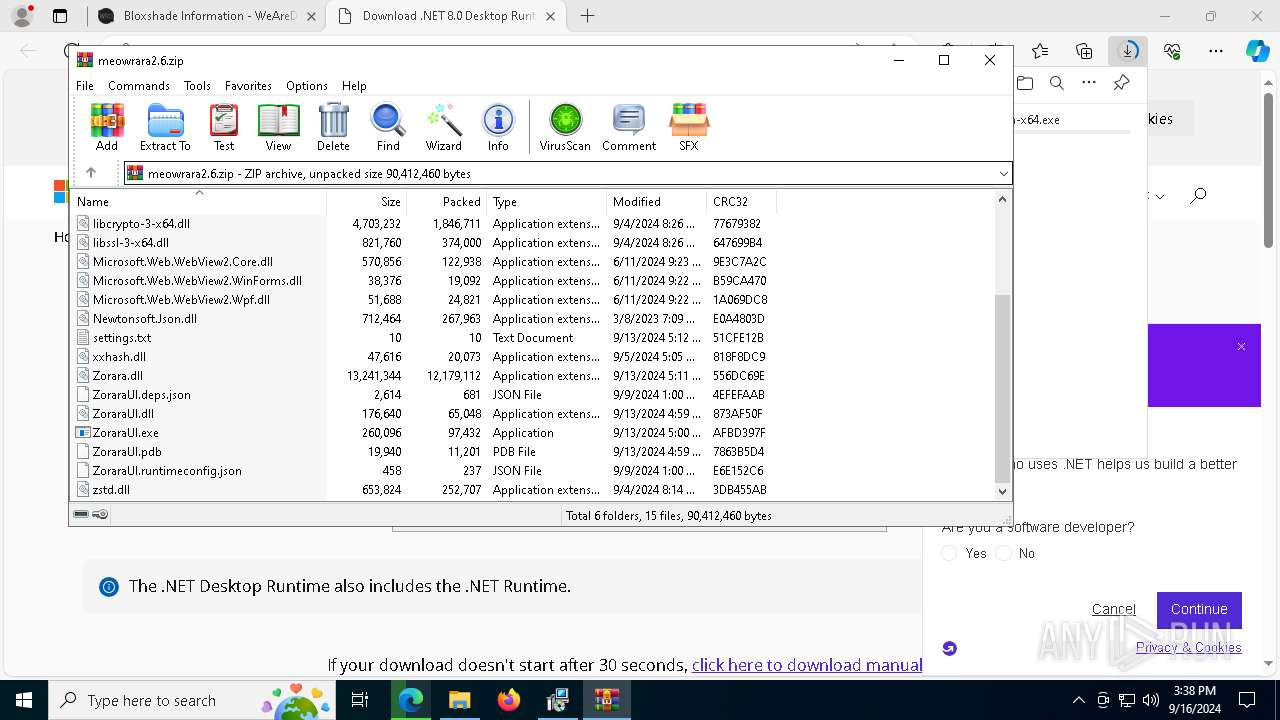
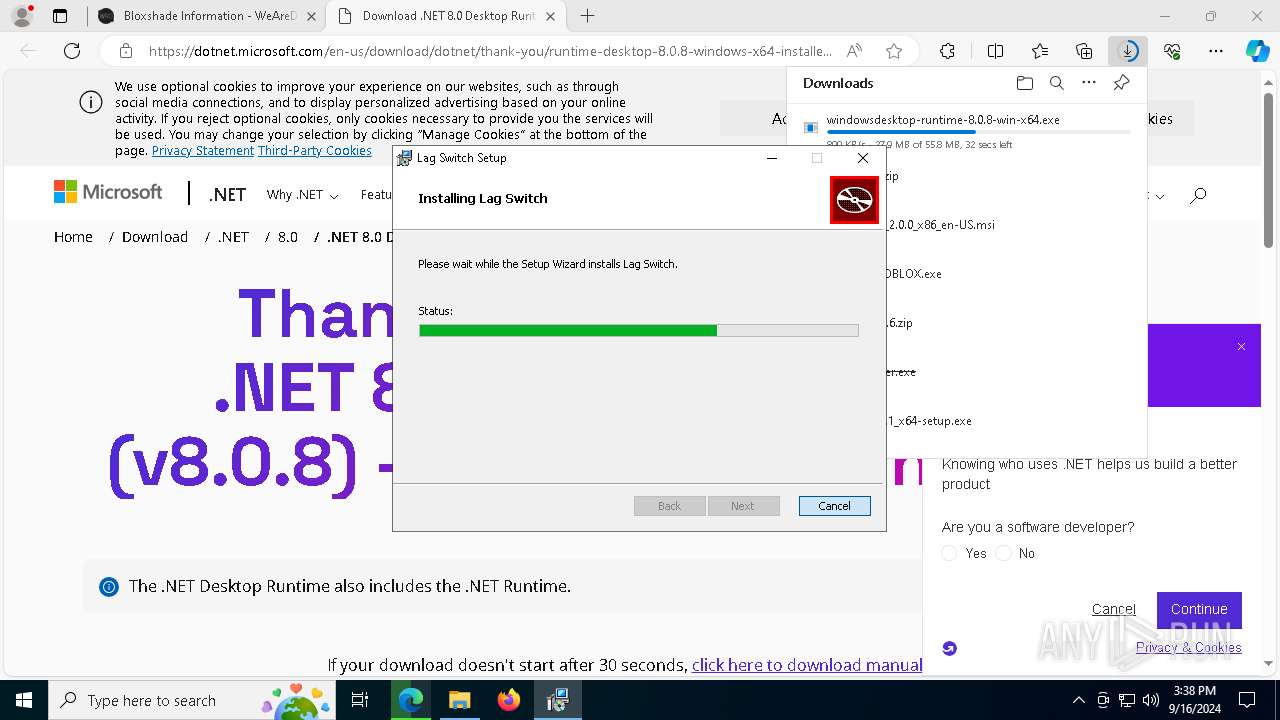
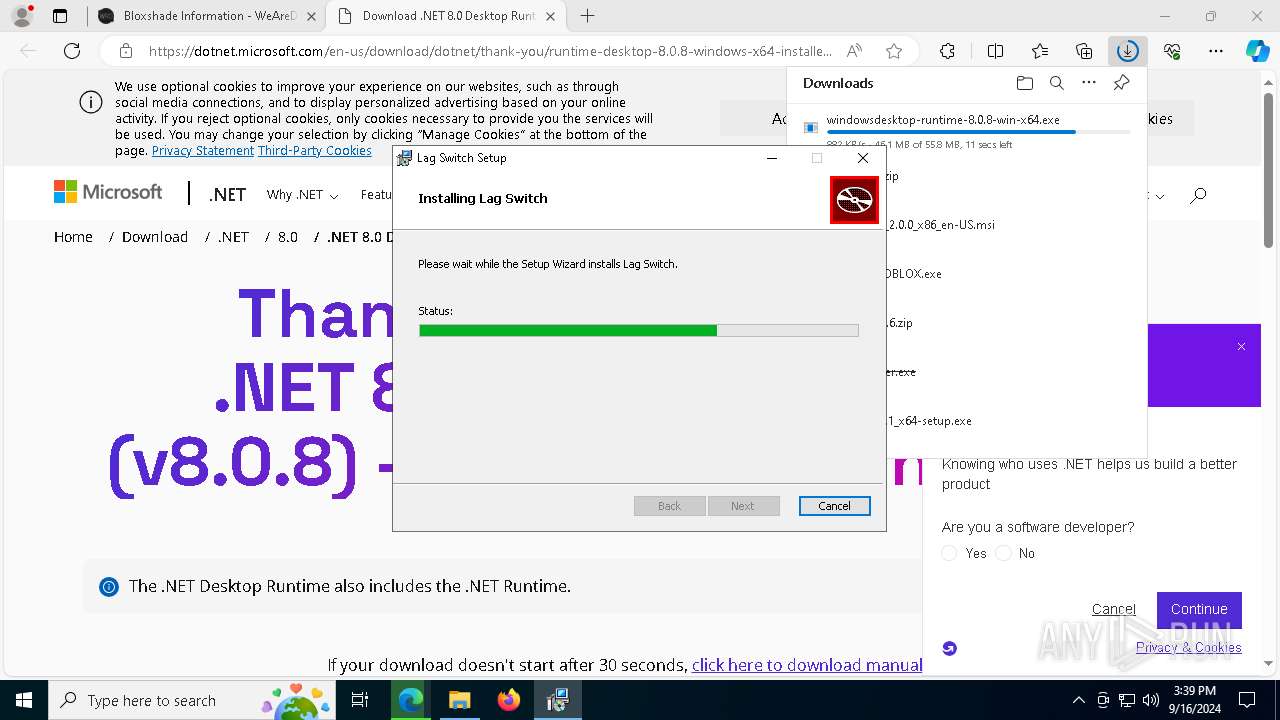
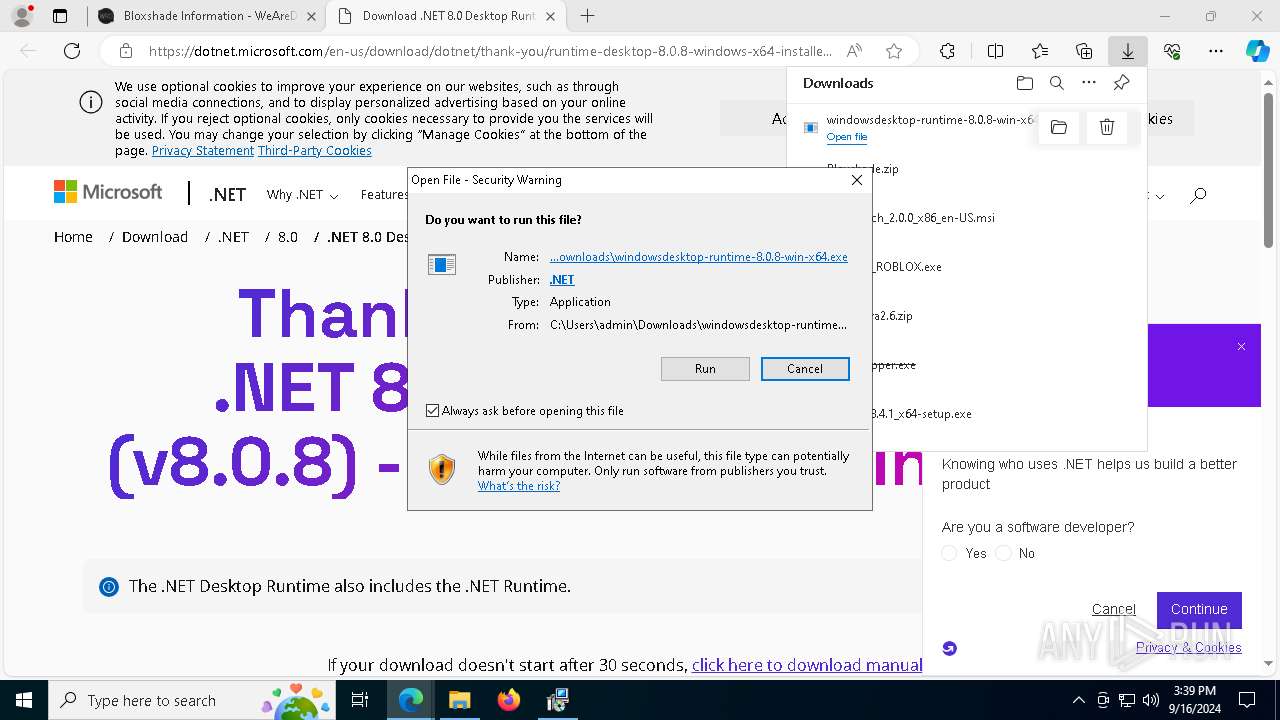
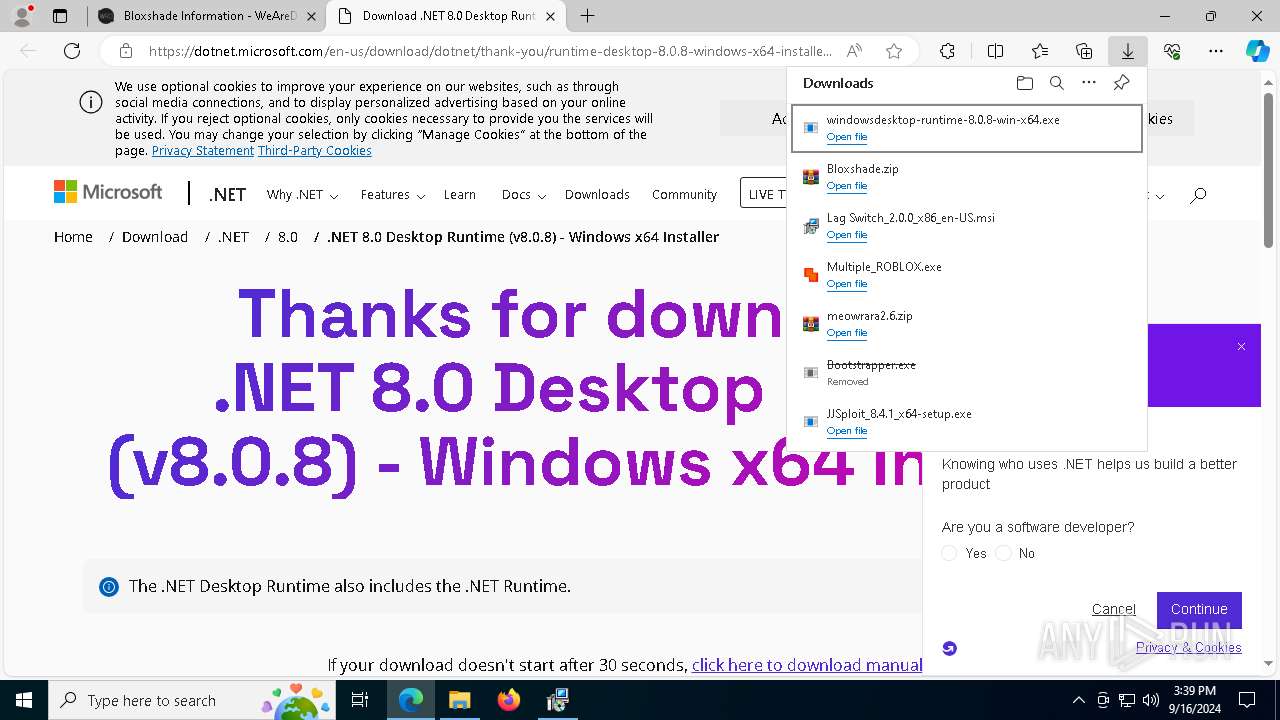
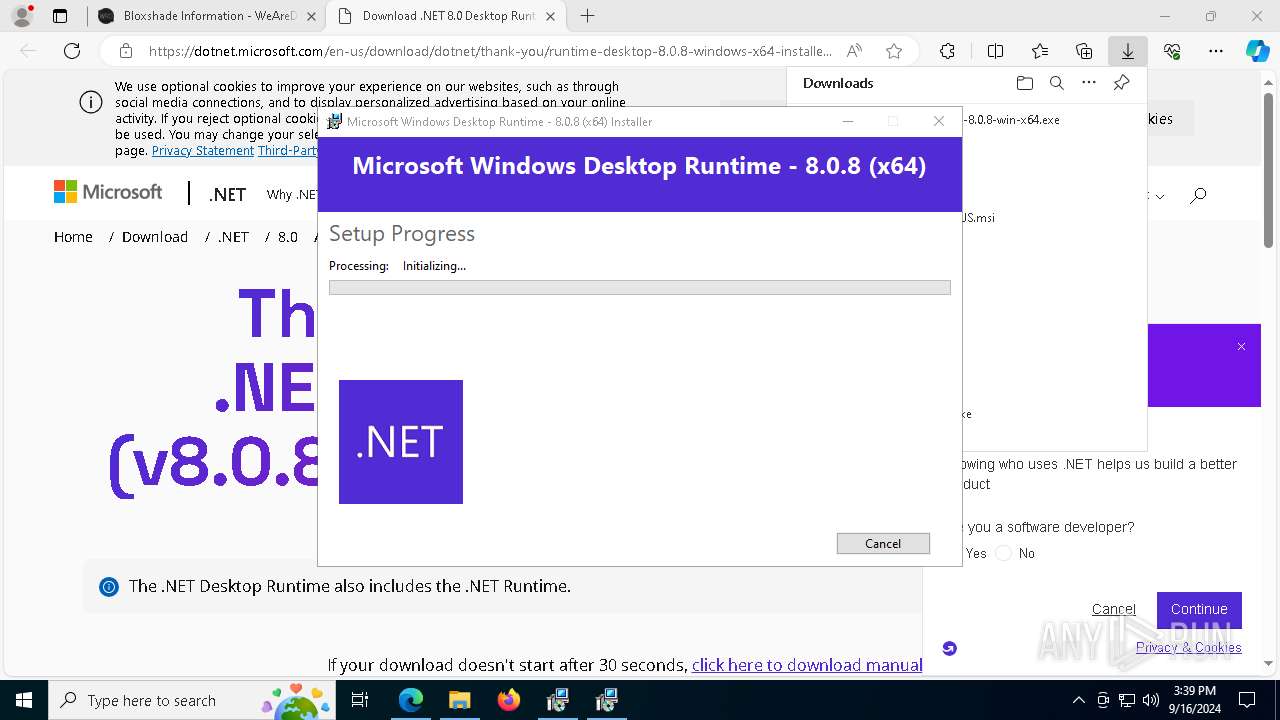
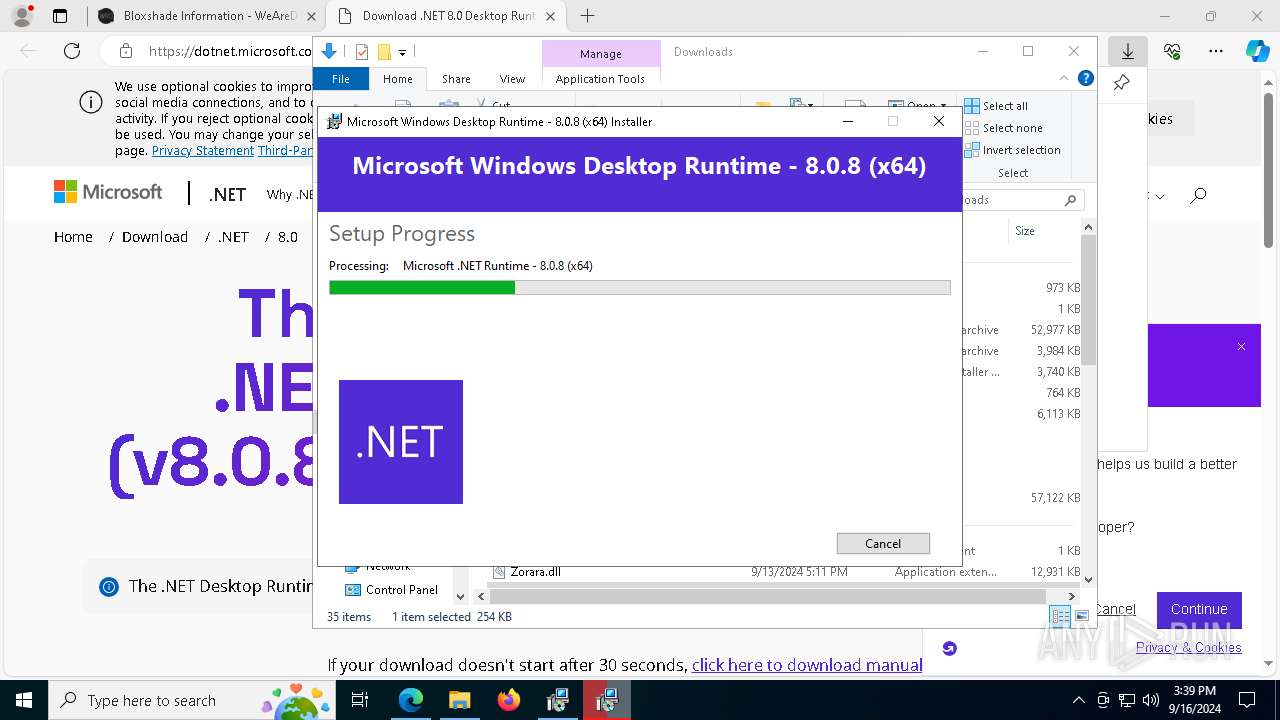
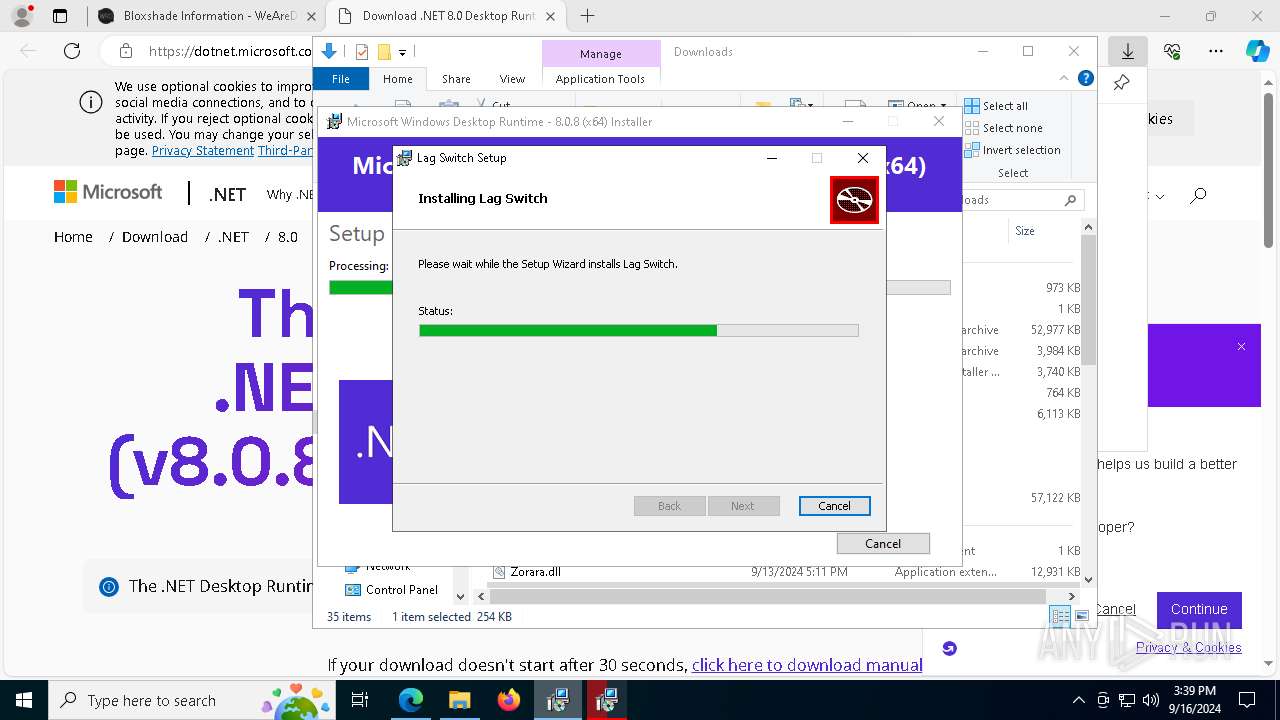
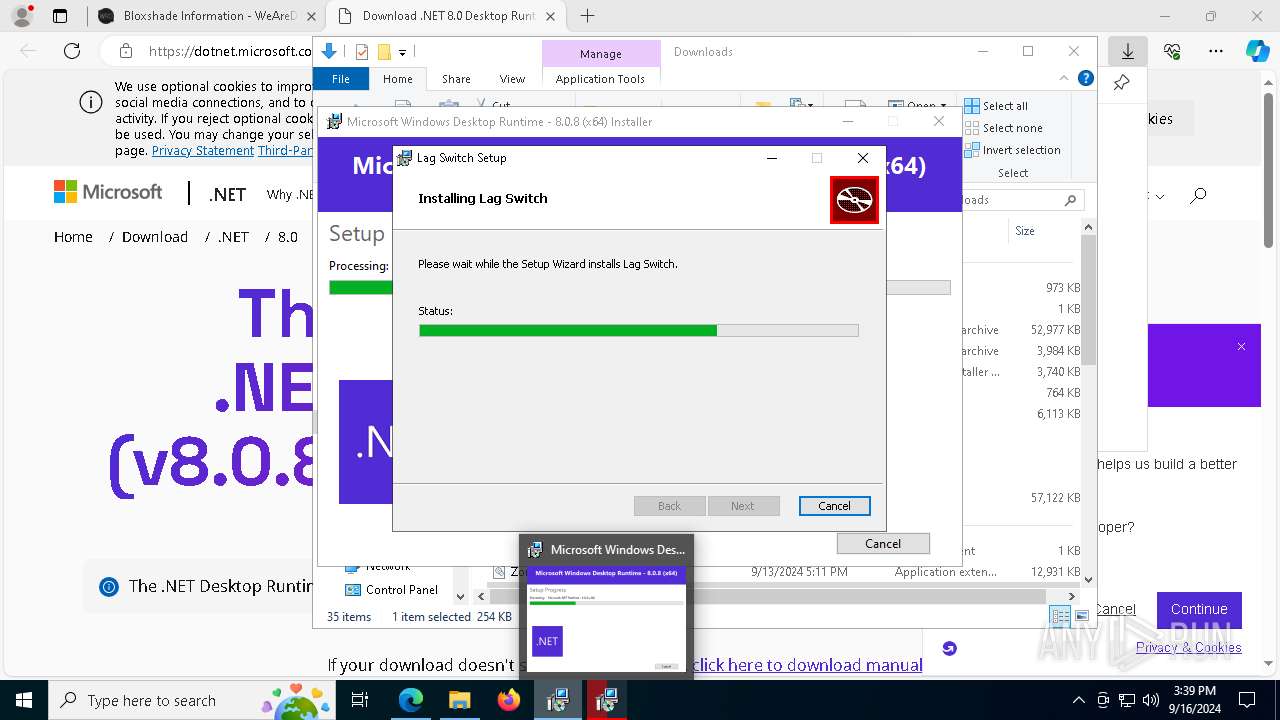
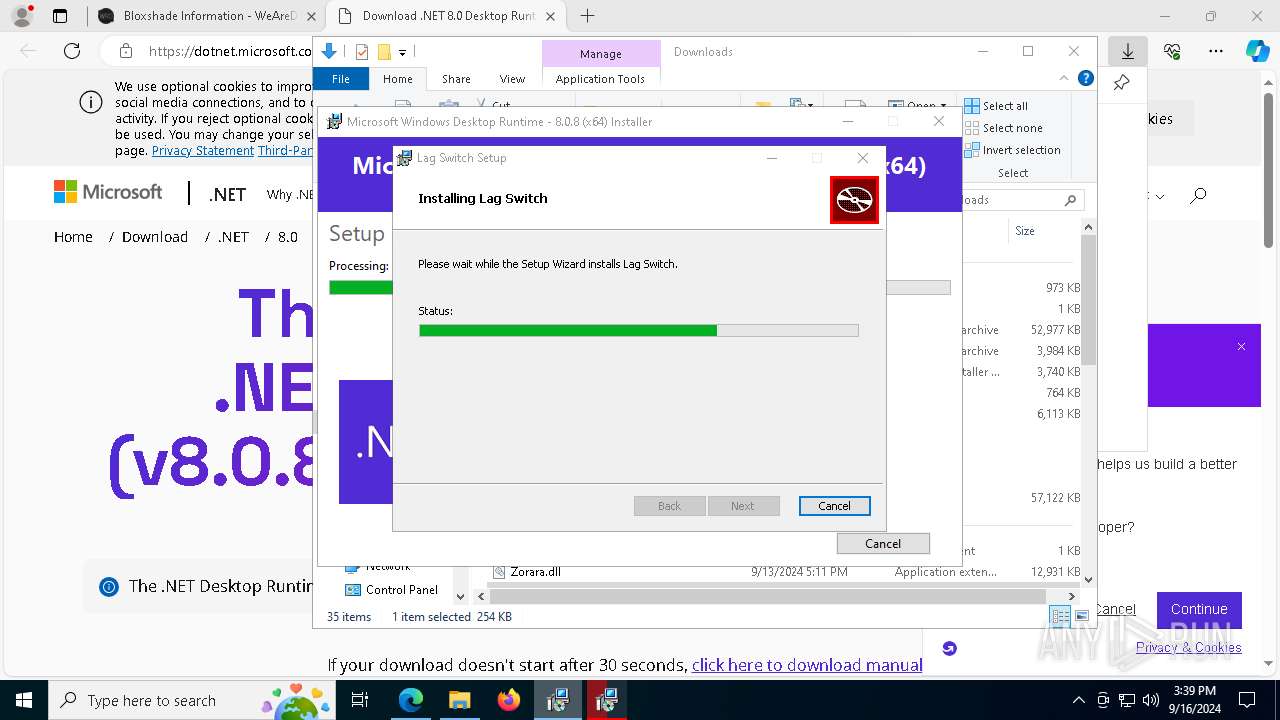
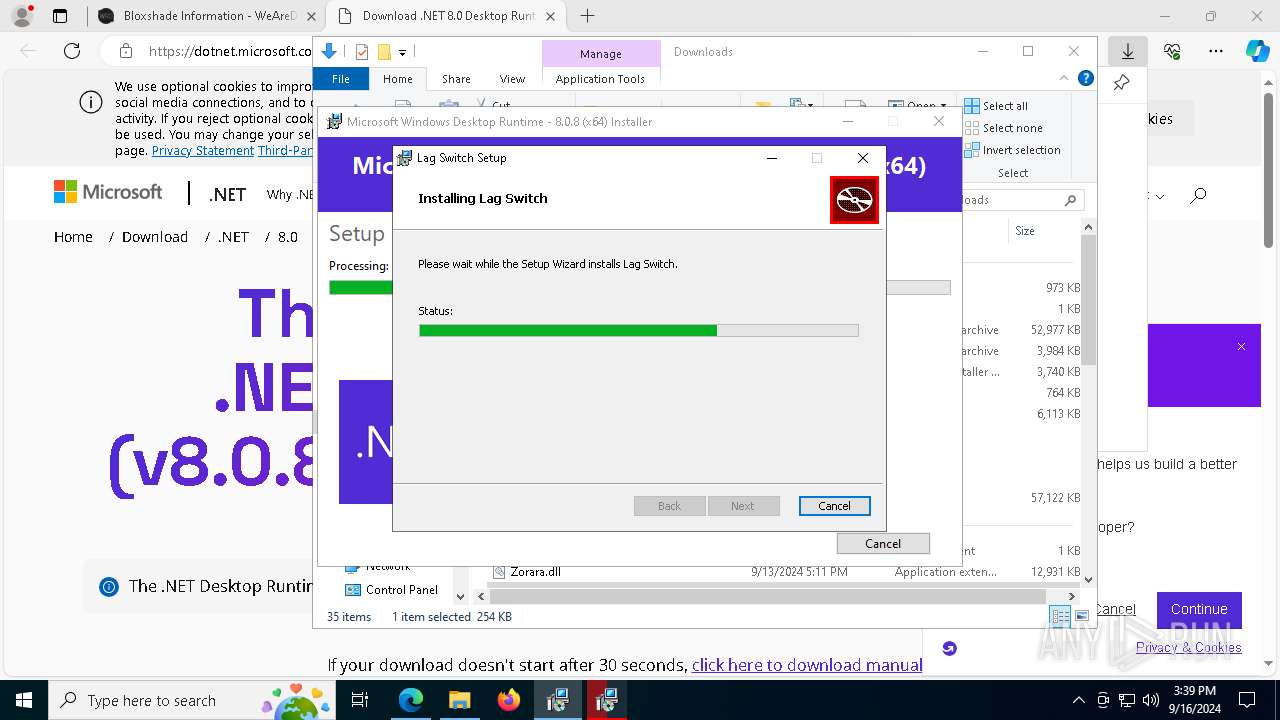
ZoraraUI.exe | You must install .NET to run this application.
App: C:\Users\admin\Downloads\ZoraraUI.exe
Architecture: x64
App host version: 8.0.8
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.8 |