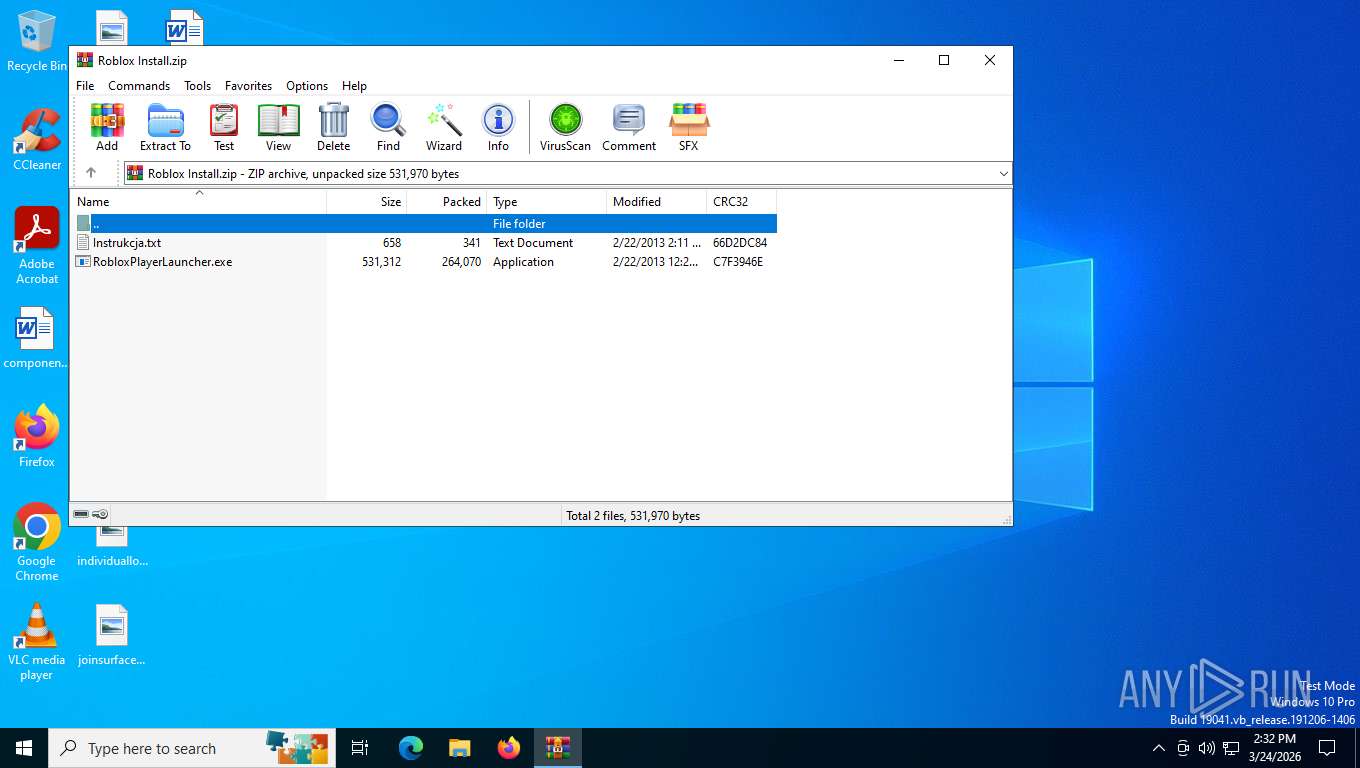
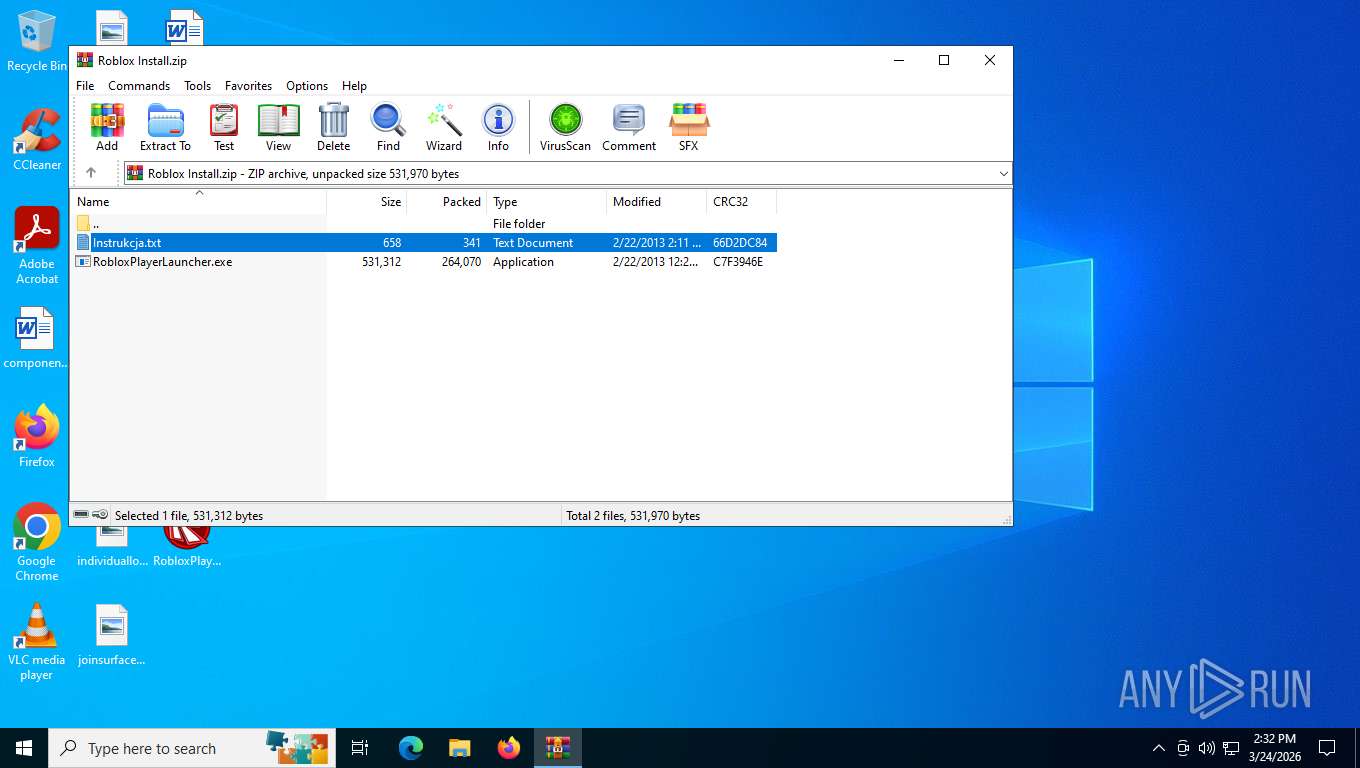
| File name: | Roblox Install.zip |
| Full analysis: | https://app.any.run/tasks/6062090a-bd58-445f-a282-5e8f12bcf0c2 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2026, 18:32:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A25508F7DA9EA8BDEA456AA11737932D |
| SHA1: | 691BD01DD903AFB6B4D0DB0C17D1D605BB656C41 |
| SHA256: | A4AB32209BC9235E27BEF06530F8E30738EF4CE295C3B373FF037F4ACC1280A5 |
| SSDEEP: | 12288:/XQOxDPQBI3yW2xoYA0nKI9HQ4AhAF3fnx84Y:/QOxrQ+3V2xfA0nKI9HQvaFvnx84Y |
MALICIOUS
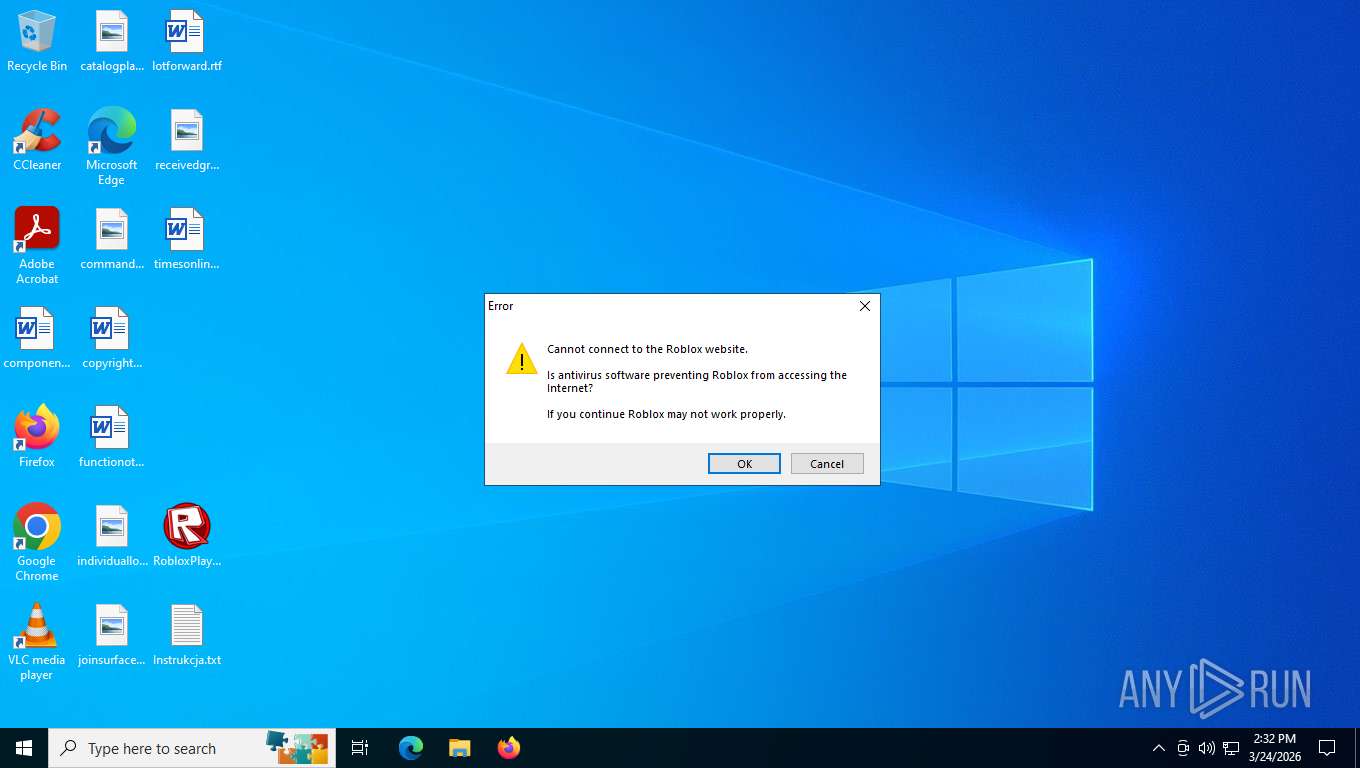
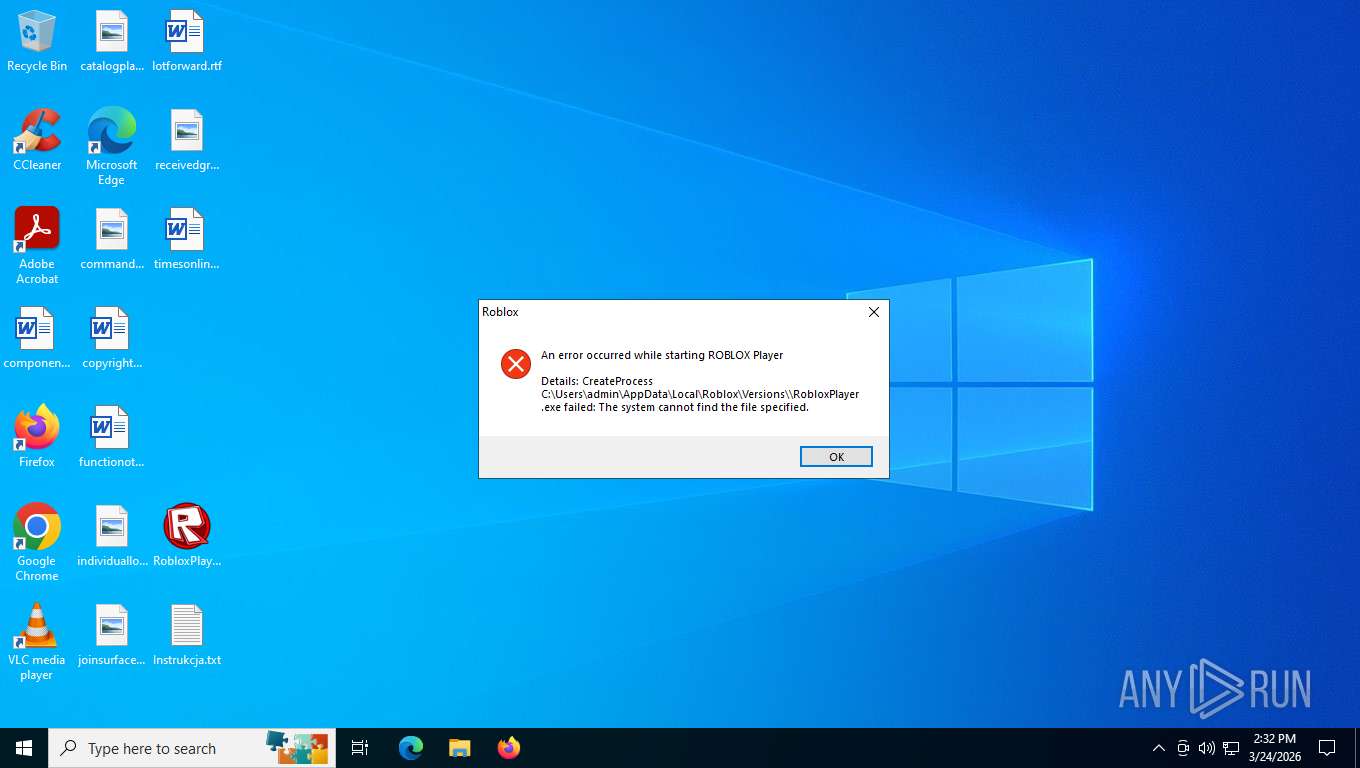
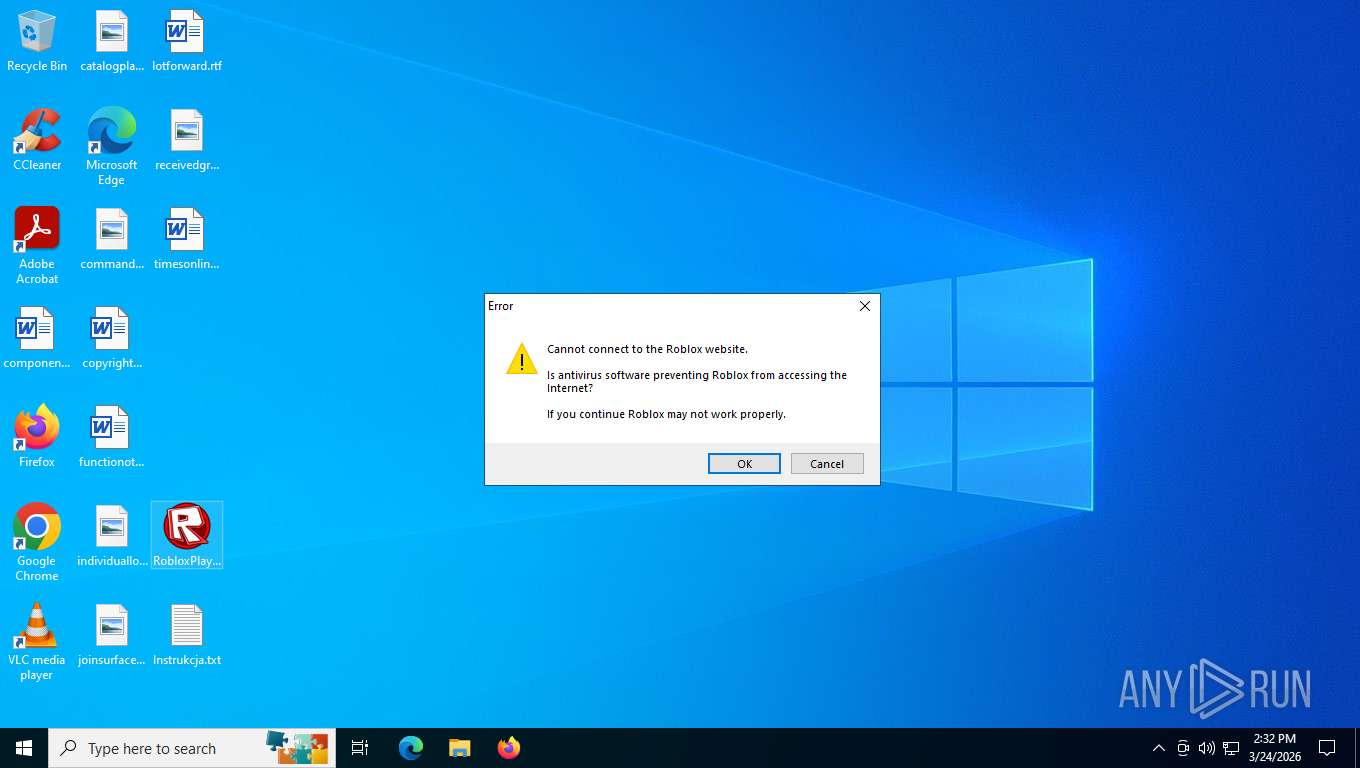
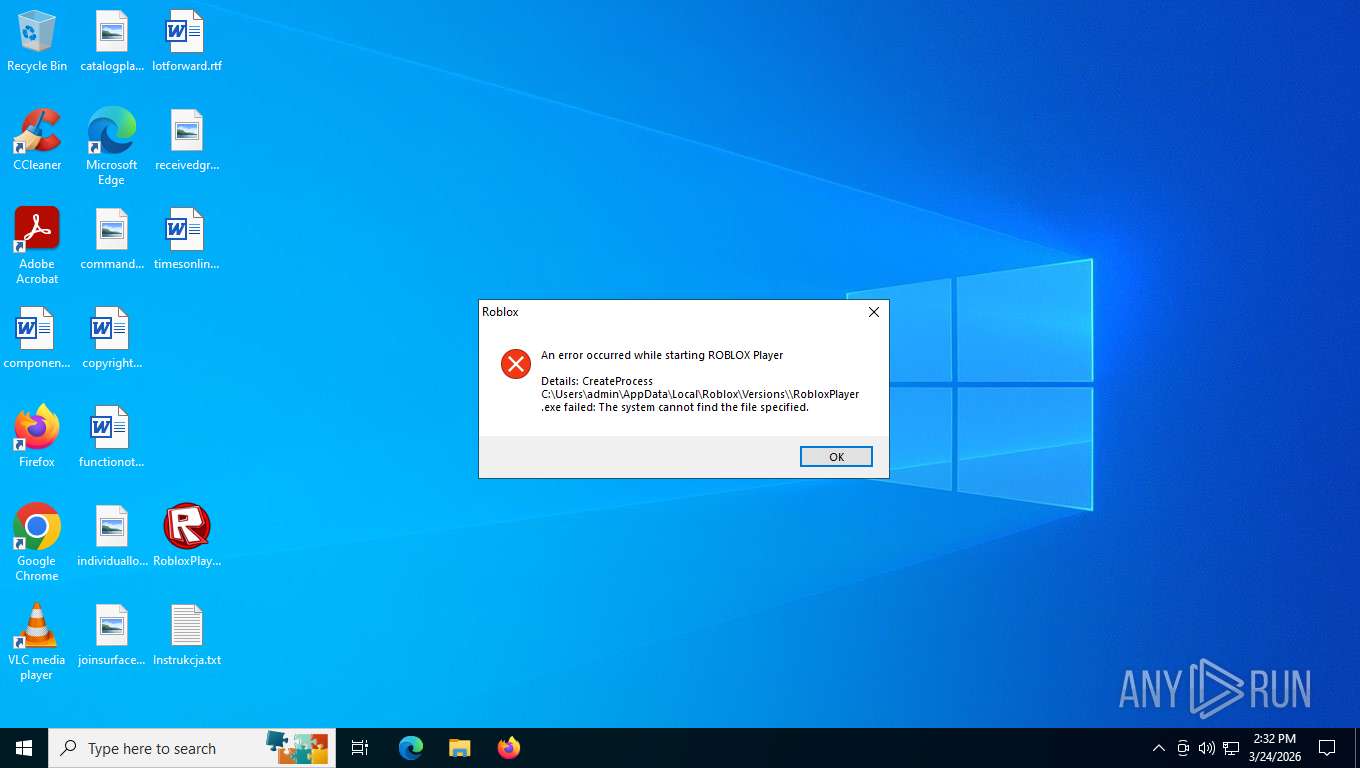
Executing a file with an untrusted certificate
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
SUSPICIOUS
No suspicious indicators.INFO
The sample compiled with english language support
- WinRAR.exe (PID: 3340)
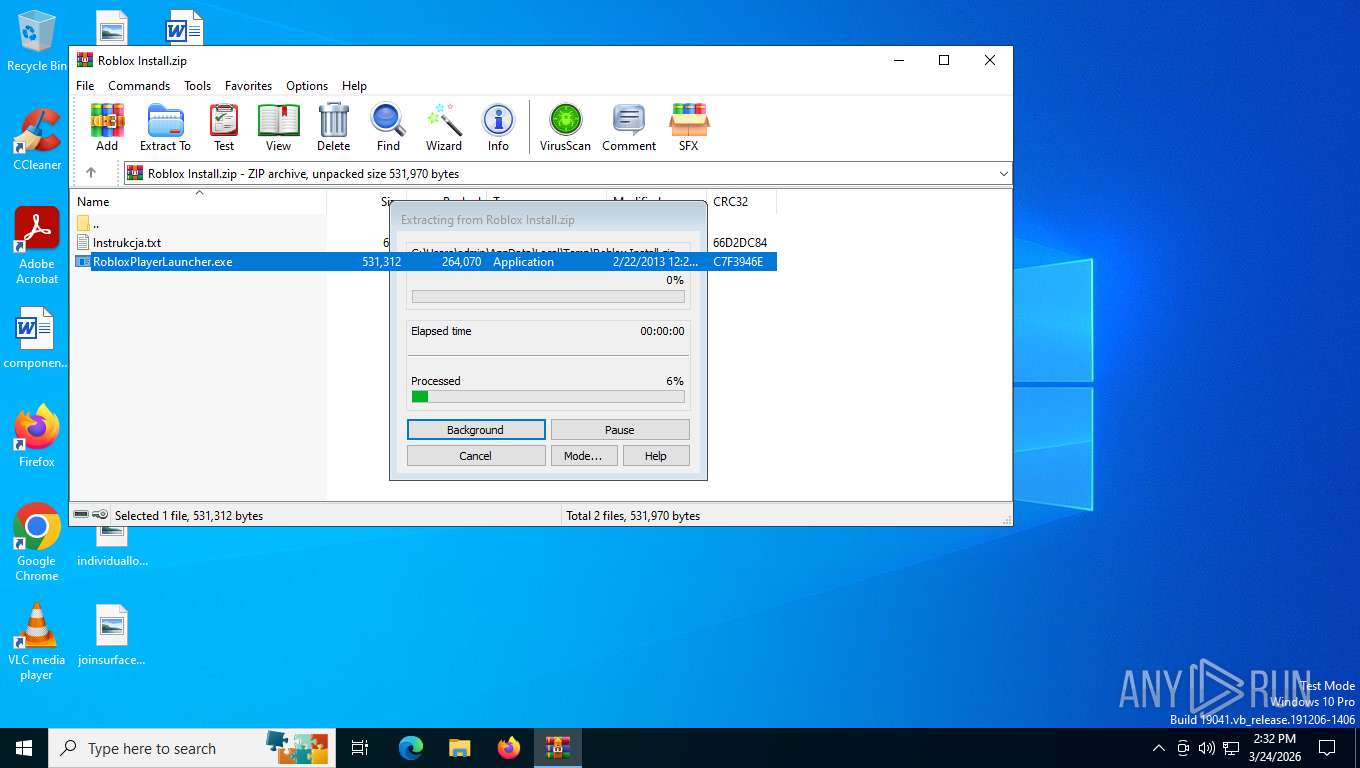
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3340)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4684)
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
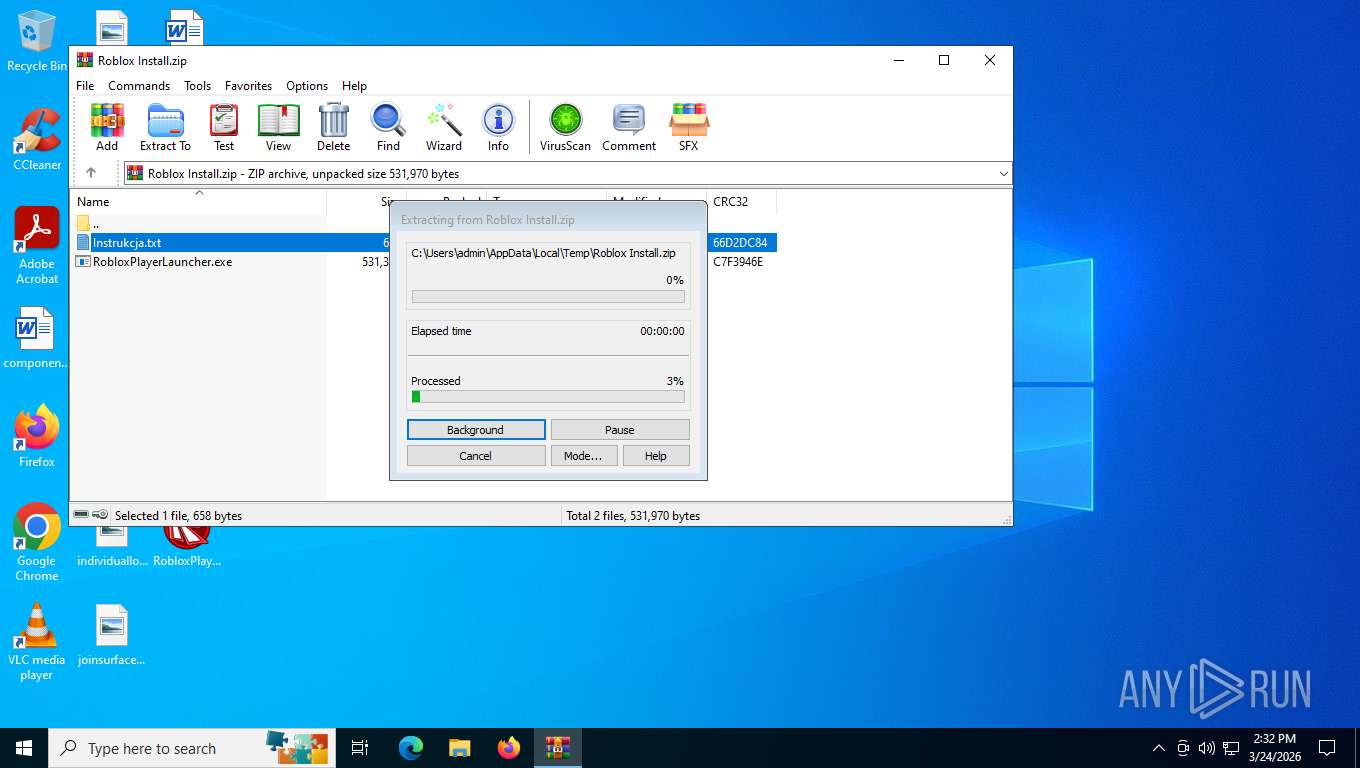
Generic archive extractor
- WinRAR.exe (PID: 3340)
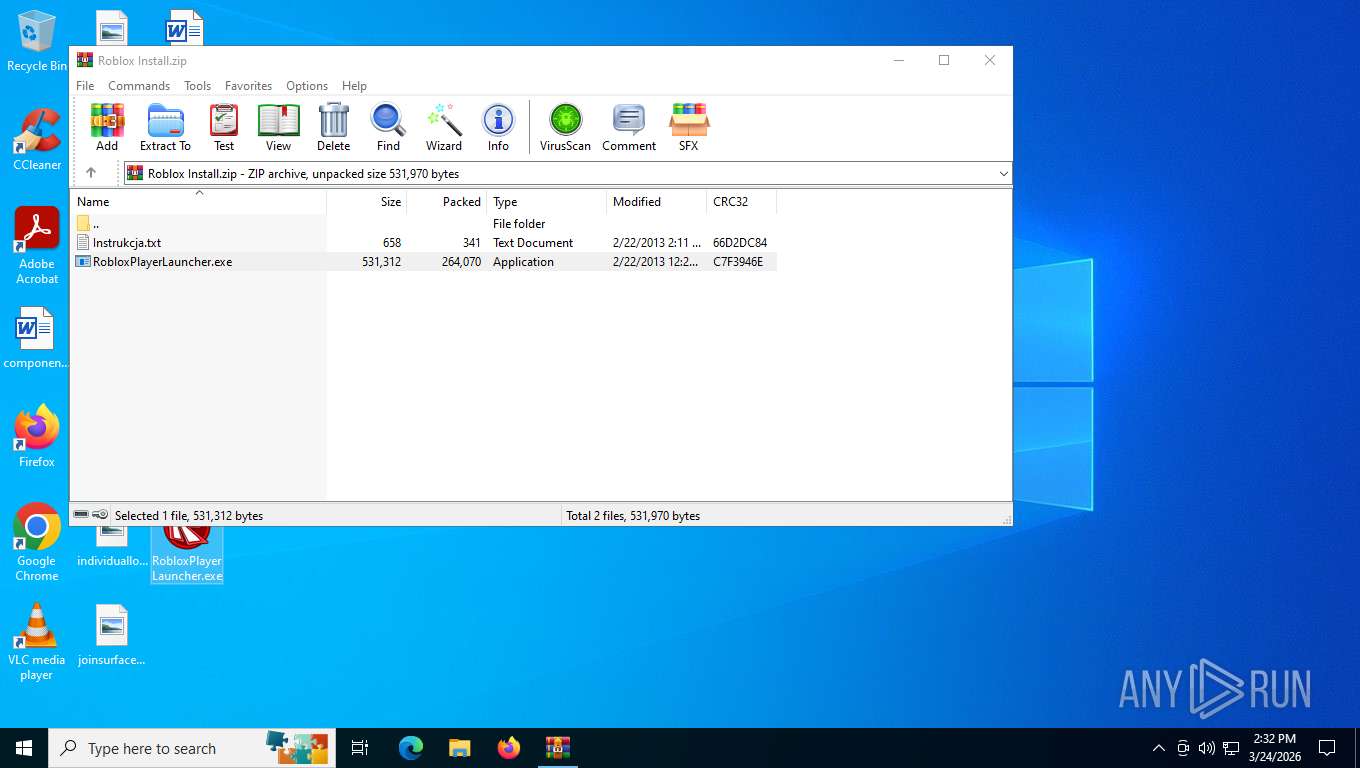
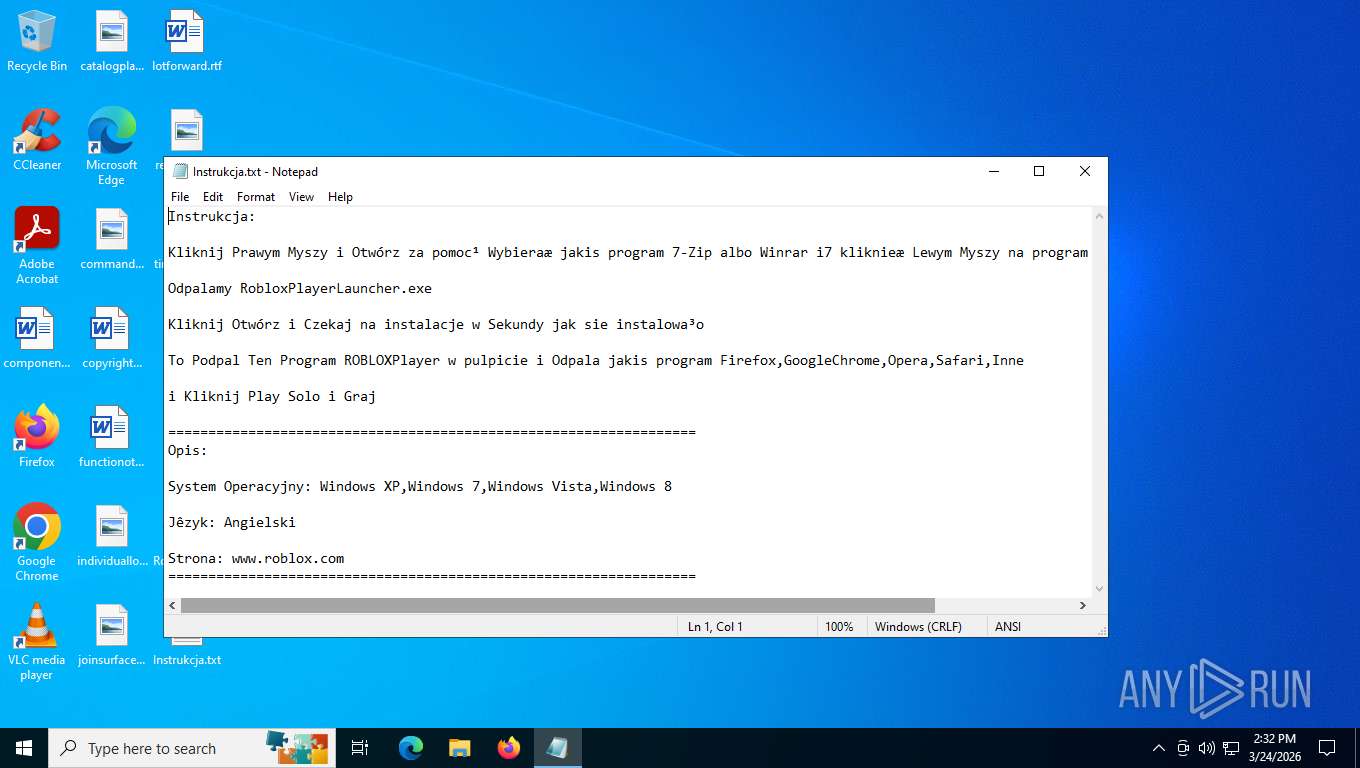
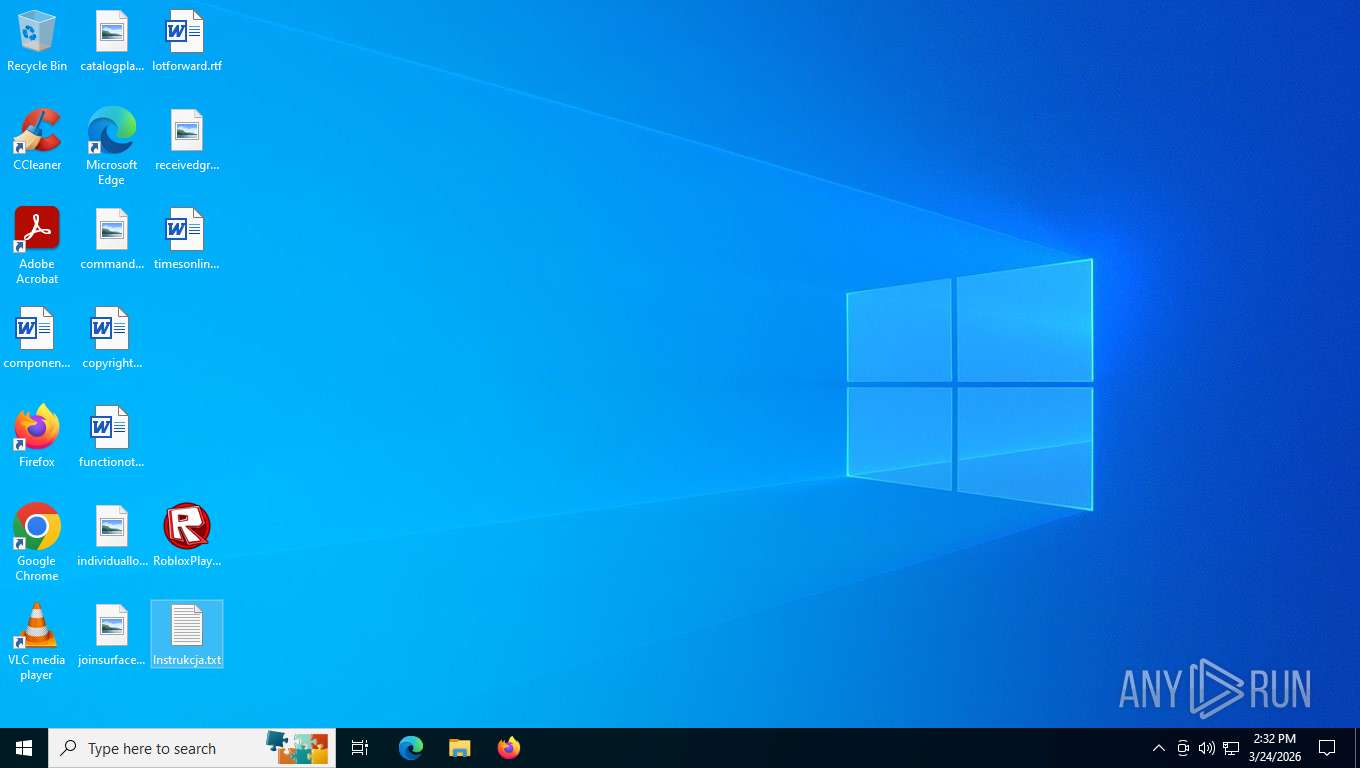
Manual execution by a user
- notepad.exe (PID: 4684)
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
Checks supported languages
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
Create files in a temporary directory
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
Reads the computer name
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
Reads the machine GUID from the registry
- RobloxPlayerLauncher.exe (PID: 1152)
- RobloxPlayerLauncher.exe (PID: 6632)
Creates files or folders in the user directory
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
ROBLOX mutex has been found
- RobloxPlayerLauncher.exe (PID: 6632)
- RobloxPlayerLauncher.exe (PID: 1152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2013:02:22 20:11:58 |
| ZipCRC: | 0x66d2dc84 |
| ZipCompressedSize: | 341 |
| ZipUncompressedSize: | 658 |
| ZipFileName: | Instrukcja.txt |
Total processes
132
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Users\admin\Desktop\RobloxPlayerLauncher.exe" | C:\Users\admin\Desktop\RobloxPlayerLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 3, 264 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Roblox Install.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4684 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Instrukcja.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6632 | "C:\Users\admin\Desktop\RobloxPlayerLauncher.exe" | C:\Users\admin\Desktop\RobloxPlayerLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 3, 264 Modules
| |||||||||||||||
Total events
6 311
Read events
6 280
Write events
27
Delete events
4
Modification events
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Roblox Install.zip | |||
Executable files
1
Suspicious files
4
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6632 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_44F84527B9D1A5107012929AC9B9BF7F | binary | |
MD5:DCB33499C11092FE880D54EB1F829FBA | SHA256:CE334CEA9F0E1E8731877B4C510FC09DCC630C9B5B7A9B1737C93704667C059C | |||
| 1152 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\RBX-486398AA.log | text | |
MD5:979D9A3626EAB3228DC73876EE72F47A | SHA256:9BBB3B1761E5AB65BFDD8B3C2FA9804CD8D2A207F8CB899EEA0D019E9A1EBE53 | |||
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3340.27127\RobloxPlayerLauncher.exe | executable | |
MD5:AF4936BAF093FD854C212CF8D059F41A | SHA256:C923854678869CCB09F16543CD7FA33953050ABEA08EF040FF08F57773B95370 | |||
| 6632 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_44F84527B9D1A5107012929AC9B9BF7F | binary | |
MD5:C901DA0EF911D81E5CD5A2BA740CA2F7 | SHA256:54CE0AF7BA58EA0D333A67B4F315EE8AAE92B1F51FD1E4F0A7DA3A6BBBC7D918 | |||
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3340.27637\Instrukcja.txt | text | |
MD5:4132644D932273EAE20E270739991DBB | SHA256:FBB3D492D5A196610703DF5CC76096B4BF1D479D35F725F18B01B16EFA287956 | |||
| 6632 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A1593701BD276673B04DEC503D761A9E_6705F5963FB7A51D452812C089BBDCD1 | binary | |
MD5:FB4B503B6B0C83935F76E0D33C0D0973 | SHA256:1D2A0FDE574FEF1BA5B8F65A0547A4D184CF5C89C0AEDBDBDB4CC33014509C63 | |||
| 6632 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A1593701BD276673B04DEC503D761A9E_6705F5963FB7A51D452812C089BBDCD1 | binary | |
MD5:1B58A1C8EBED8BBFA93AEEAEBB57E831 | SHA256:19DAD3A5E028EABD3DADE2D73DCE96E70876FBDAC1587039F5A52E1EDB2E30CF | |||
| 1152 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\WindowsBootstrapperSettings[1].json | text | |
MD5:99914B932BD37A50B983C5E7C90AE93B | SHA256:44136FA355B3678A1146AD16F7E8649E94FB4FC21FE77E8310C060F61CAAFF8A | |||
| 6632 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\RBX-20D1929A.log | text | |
MD5:B1B596AC74B507BEF2FB543263ACBB43 | SHA256:7E13EDE3049DA2A6F498E458640981ED230C21821C391B47272A8AD6803E330B | |||
| 6632 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\WindowsBootstrapperSettings[1].json | text | |
MD5:99914B932BD37A50B983C5E7C90AE93B | SHA256:44136FA355B3678A1146AD16F7E8649E94FB4FC21FE77E8310C060F61CAAFF8A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
47
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7984 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 200 | 135.232.92.97:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
4712 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.38:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 314 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
6632 | RobloxPlayerLauncher.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQDSf7vB3jWeUhatYUlYYJnE | US | binary | 2.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7984 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 184.24.77.38:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 2.16.204.143:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clientsettings.api.roblox.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7984 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |