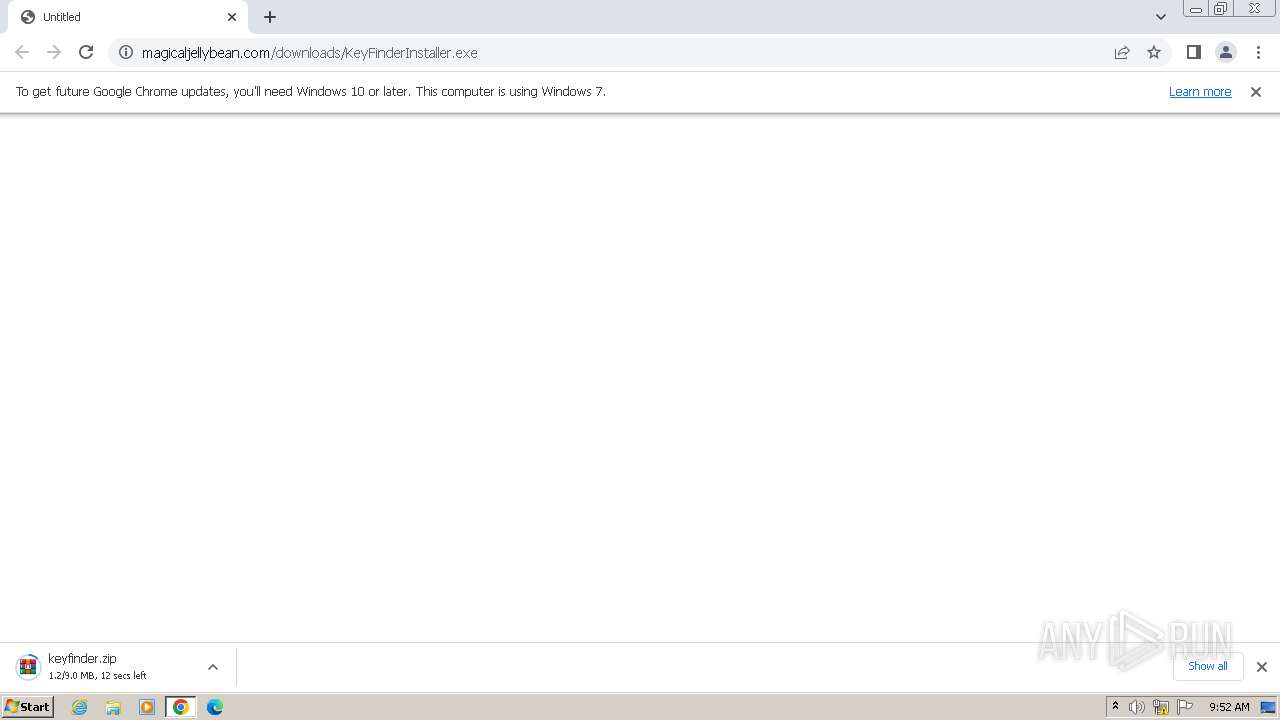
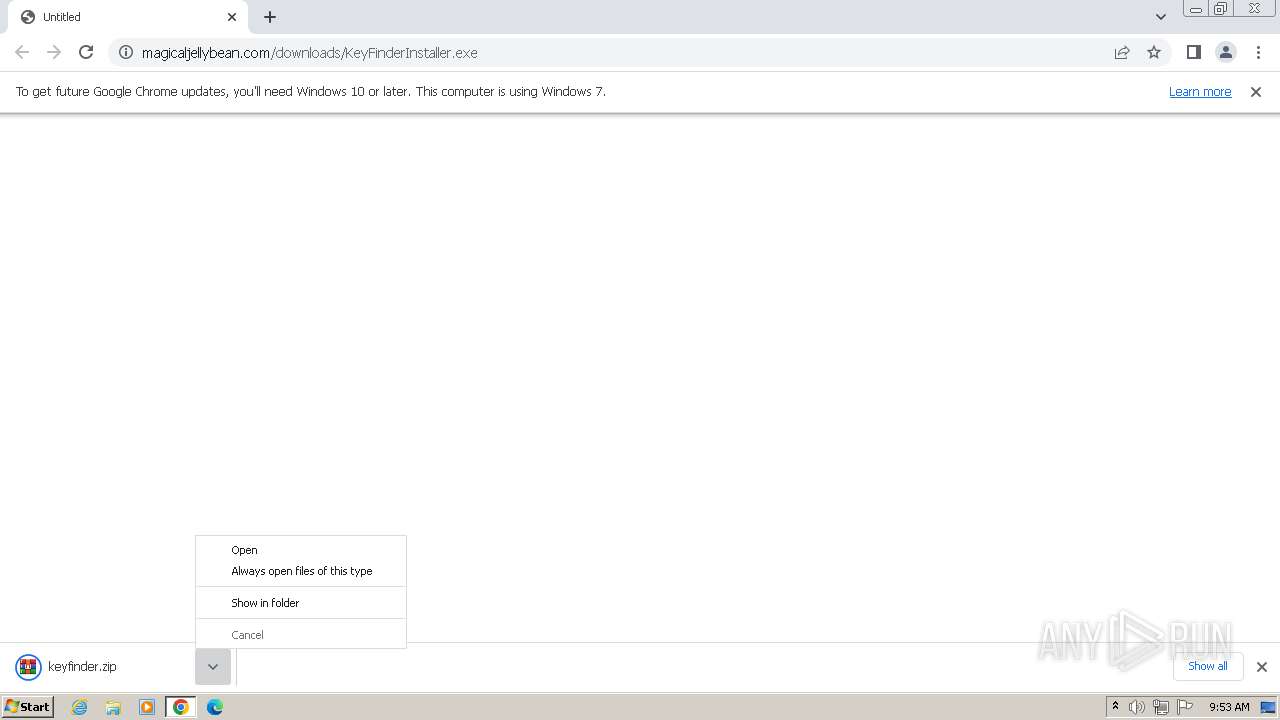
| URL: | http://www.magicaljellybean.com/downloads/KeyFinderInstaller.exe |
| Full analysis: | https://app.any.run/tasks/73857b0c-c031-4858-963e-2bc2b7f61e7f |
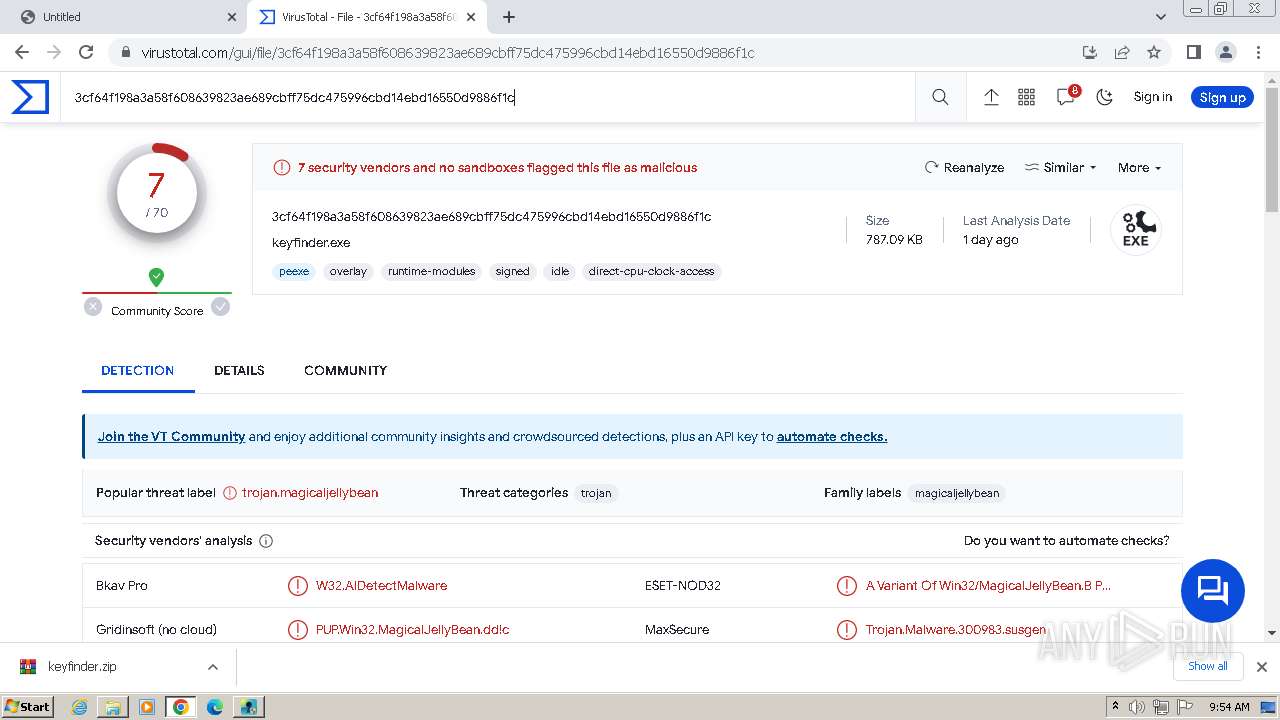
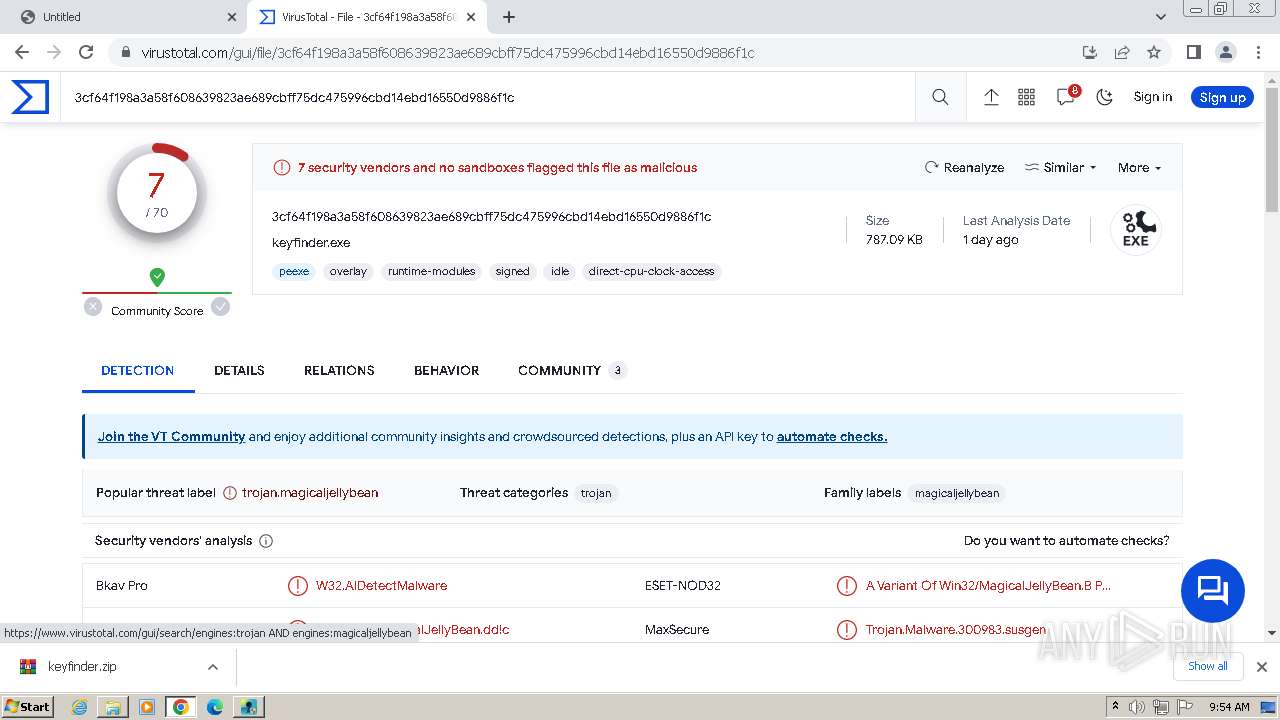
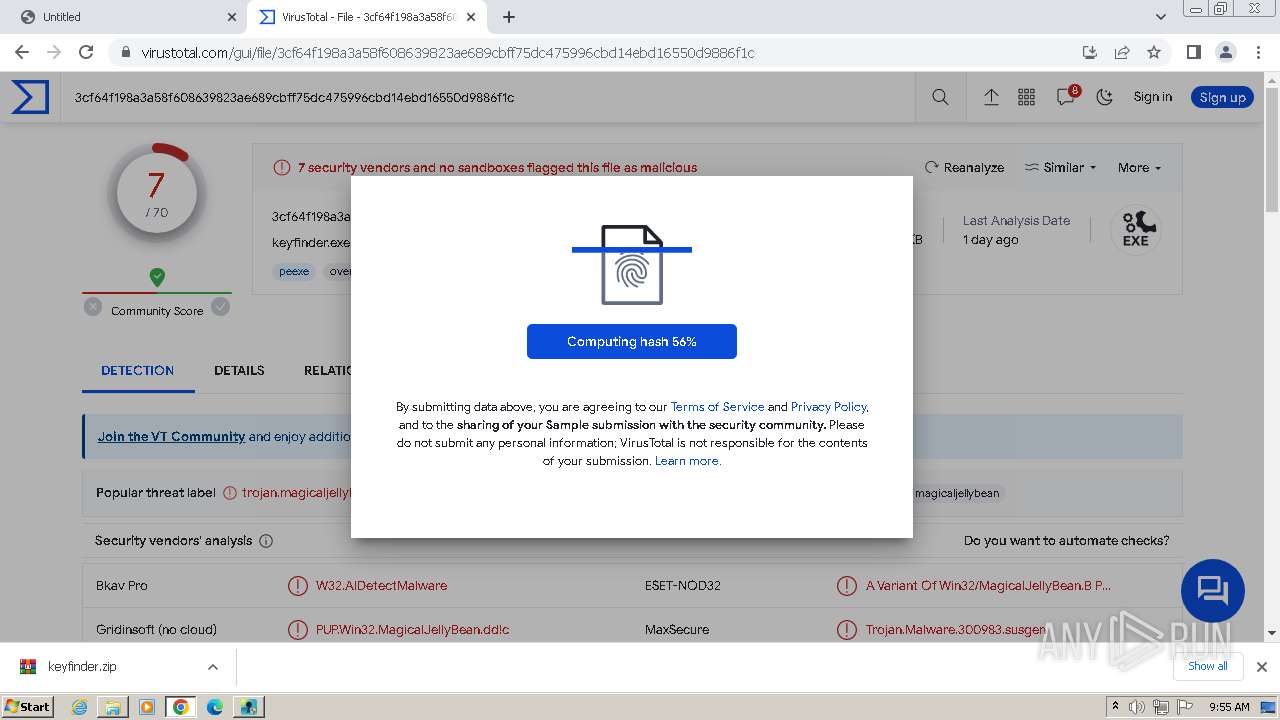
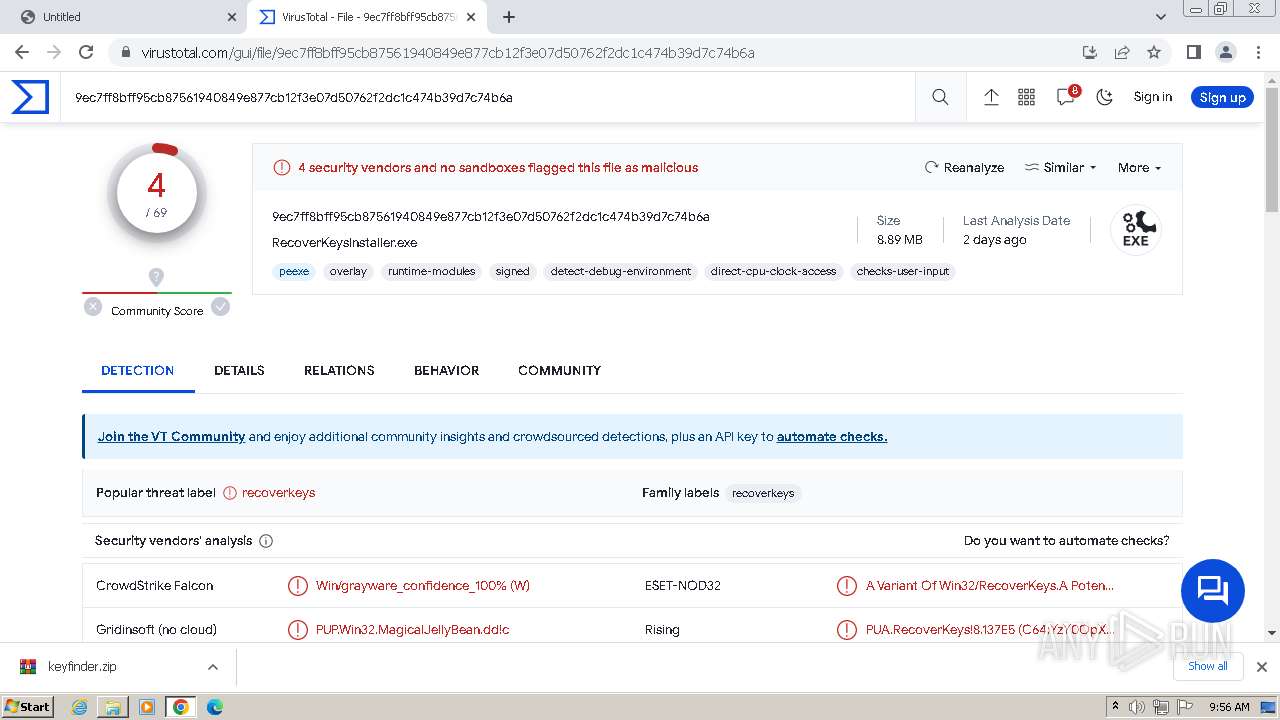
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 09:52:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | EC57EC5765EEF95F0D18D877DD5F6E6D2DB587FE |
| SHA256: | A49A5F6C13839A52EAE0E66CCCA7402C7C9A193B3EF95125B1978BD5AD982A35 |
| SSDEEP: | 3:N1KJS4kg4CyGBKXKkwL1WEgXLNn:Cc4kg4Ct8akwLgEgXLN |
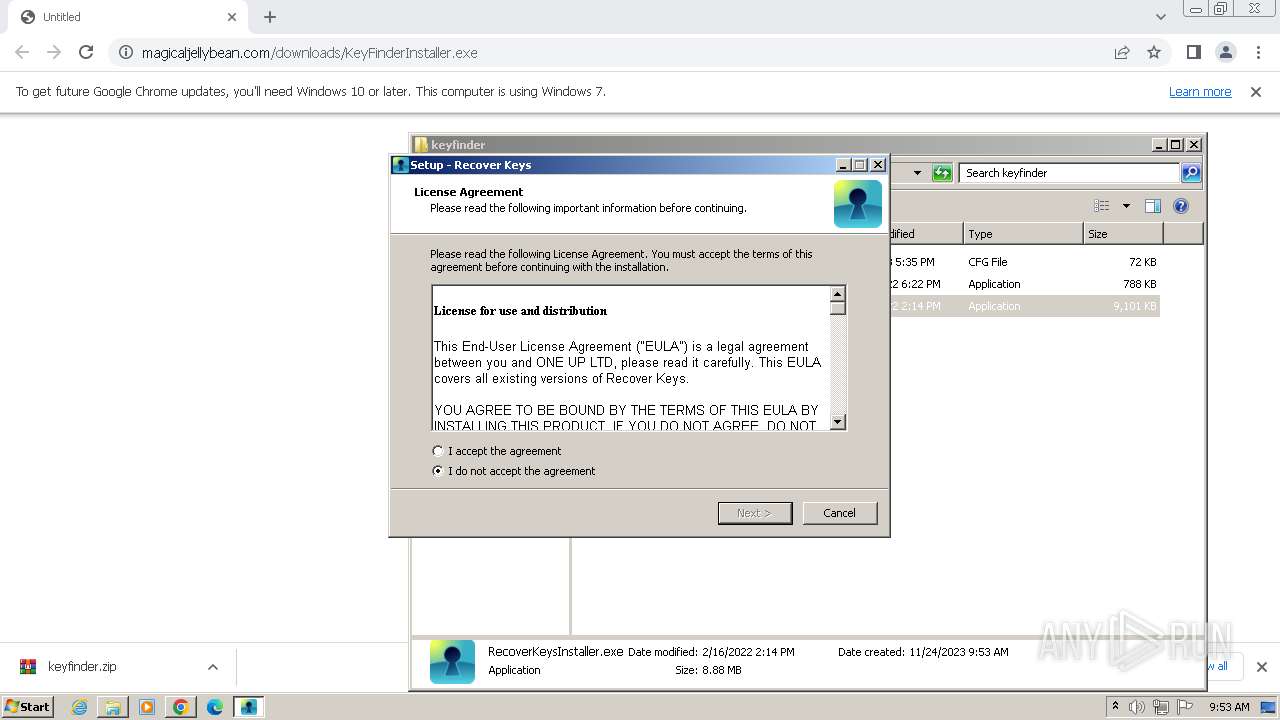
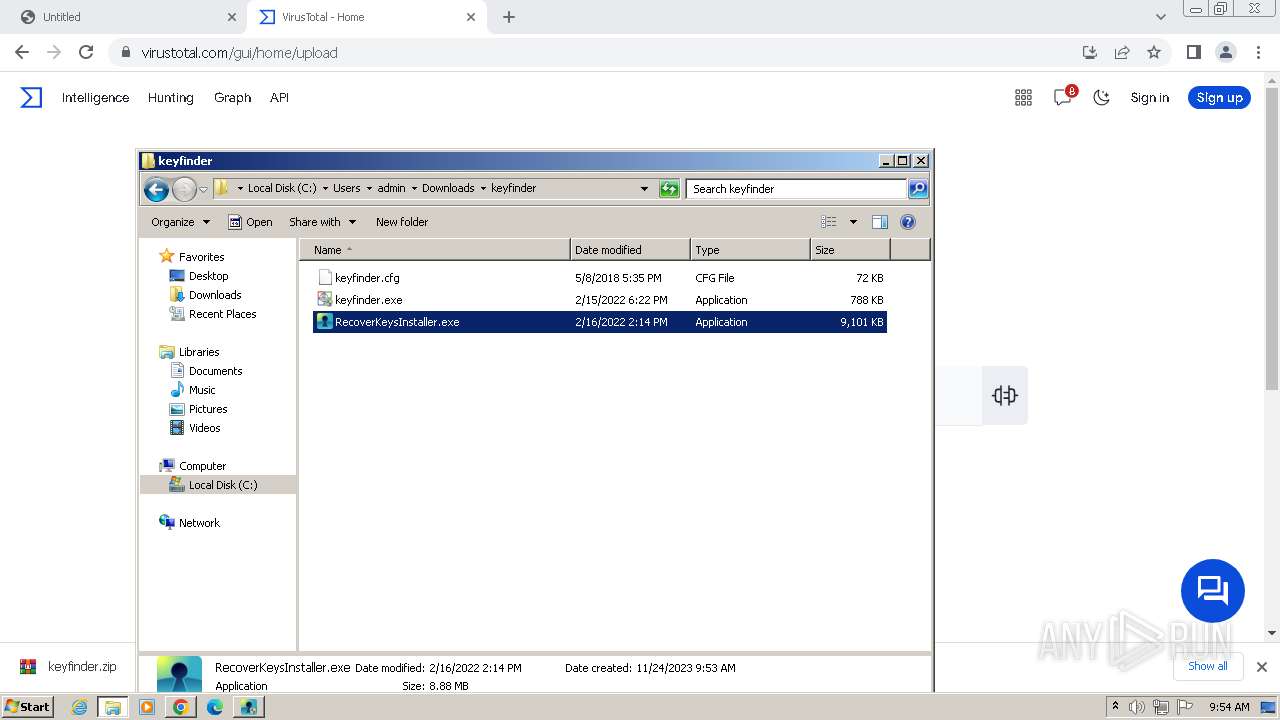
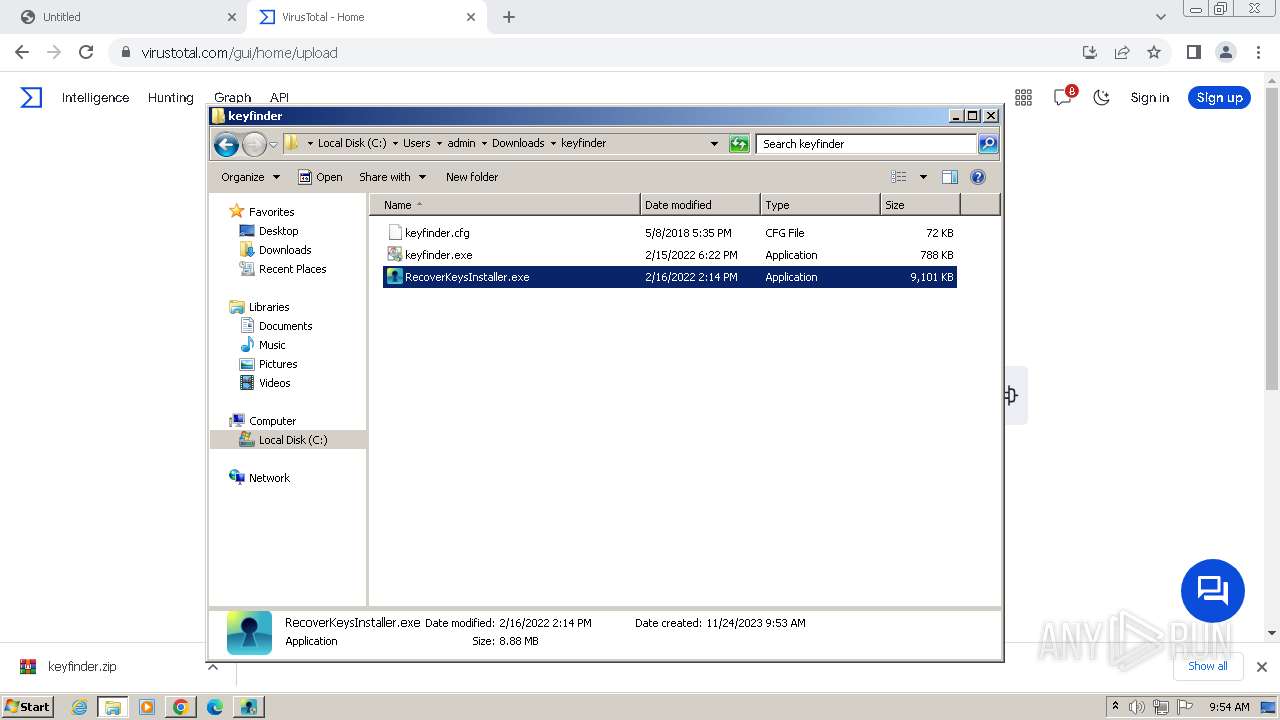
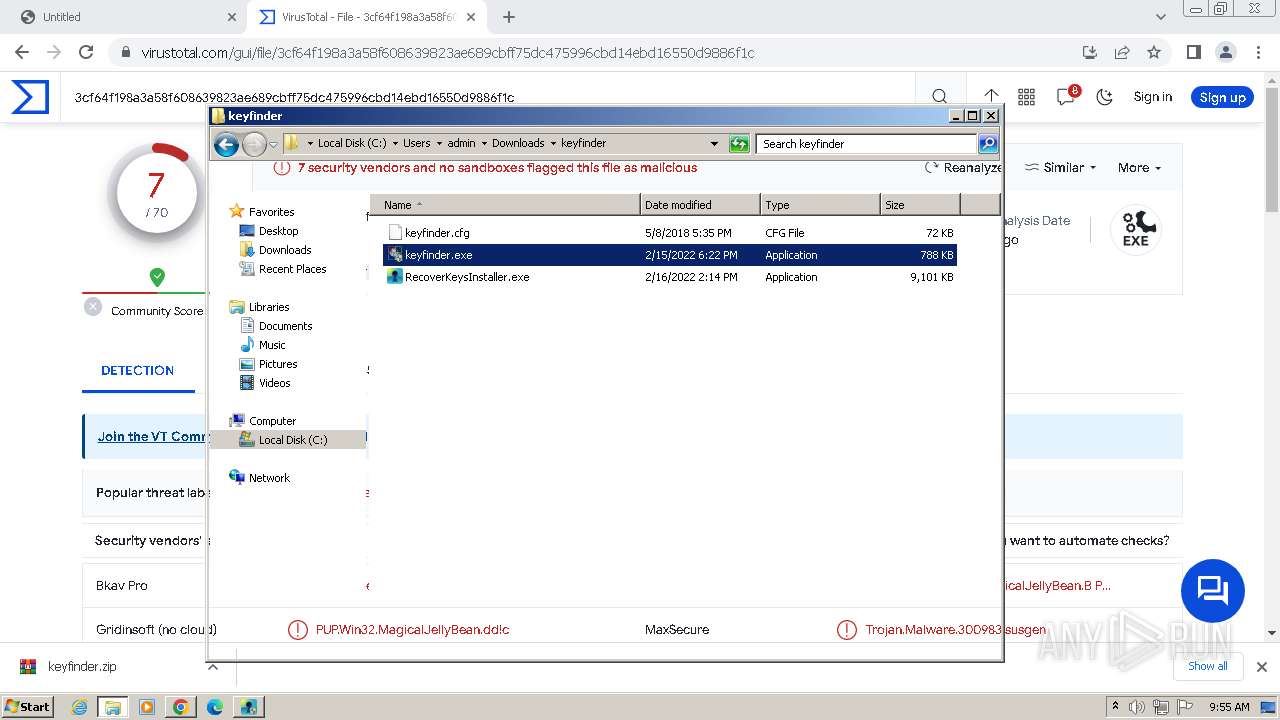
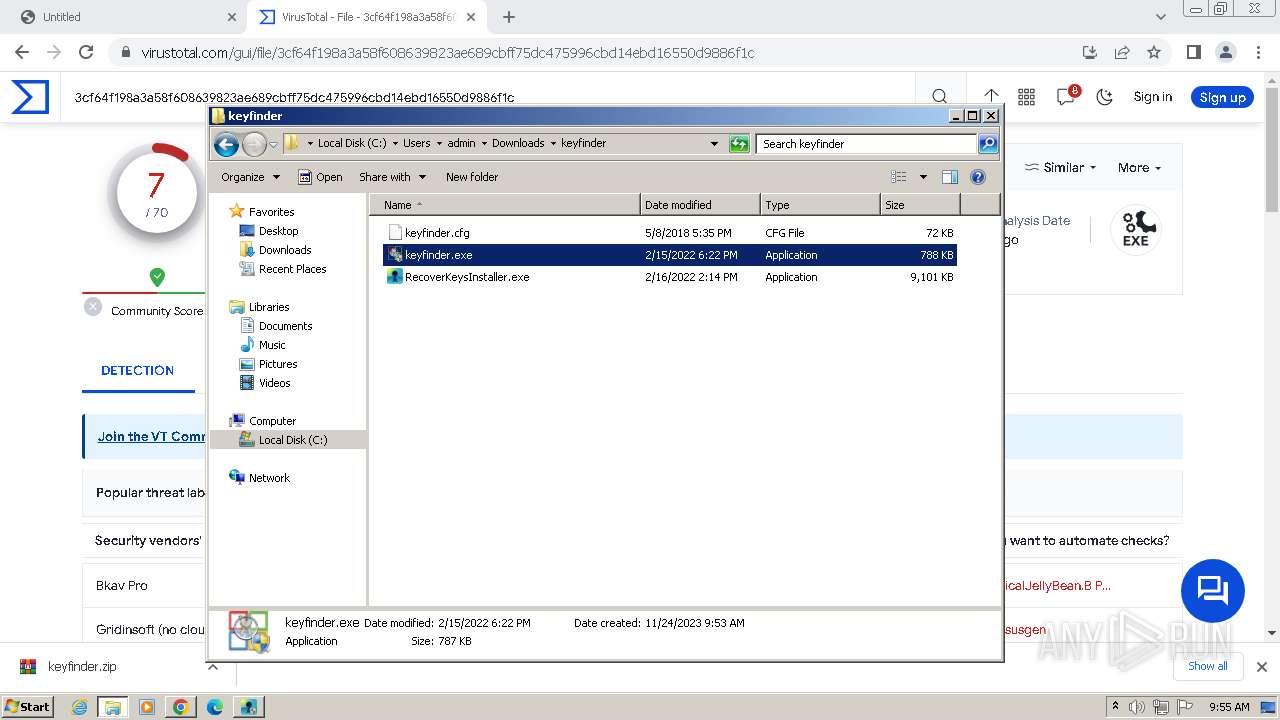
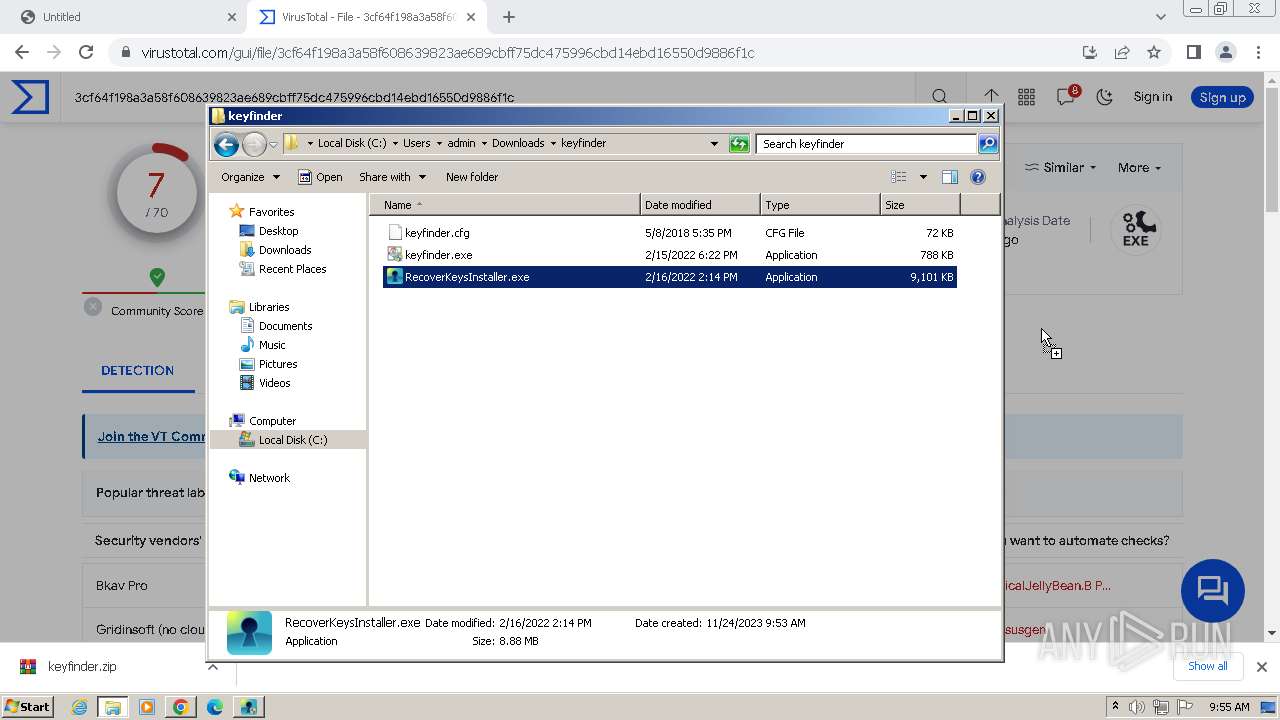
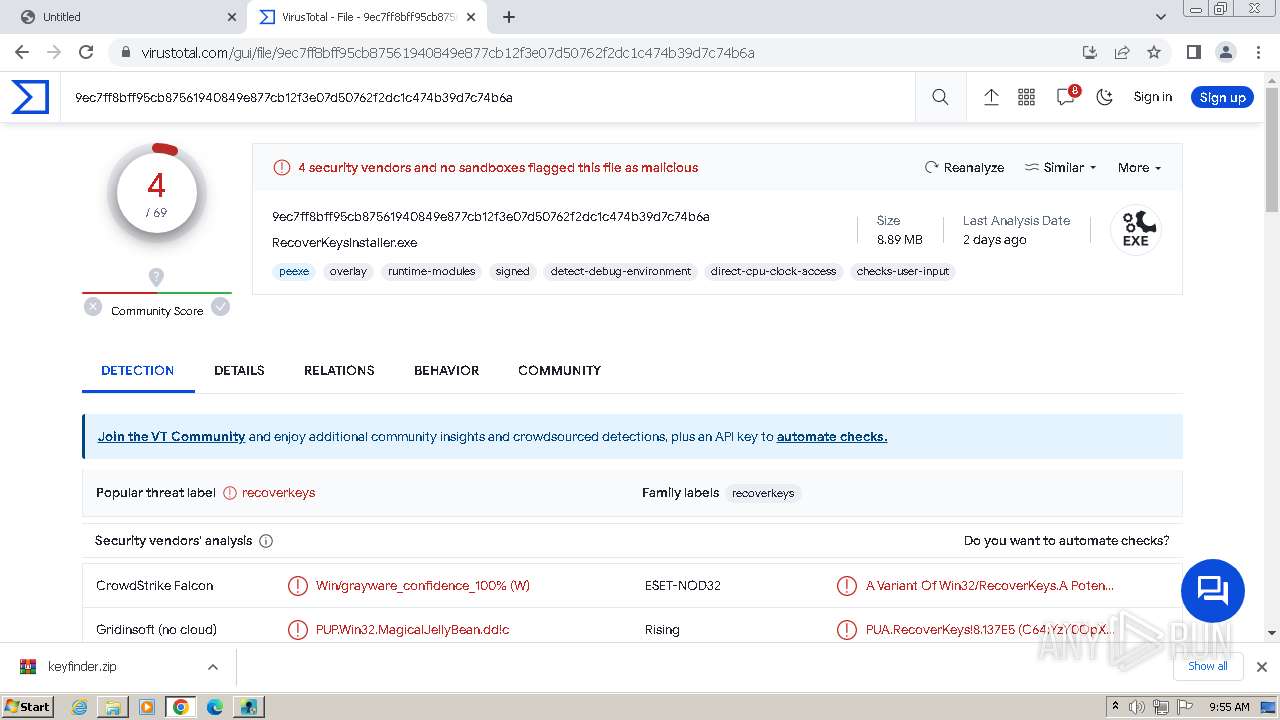
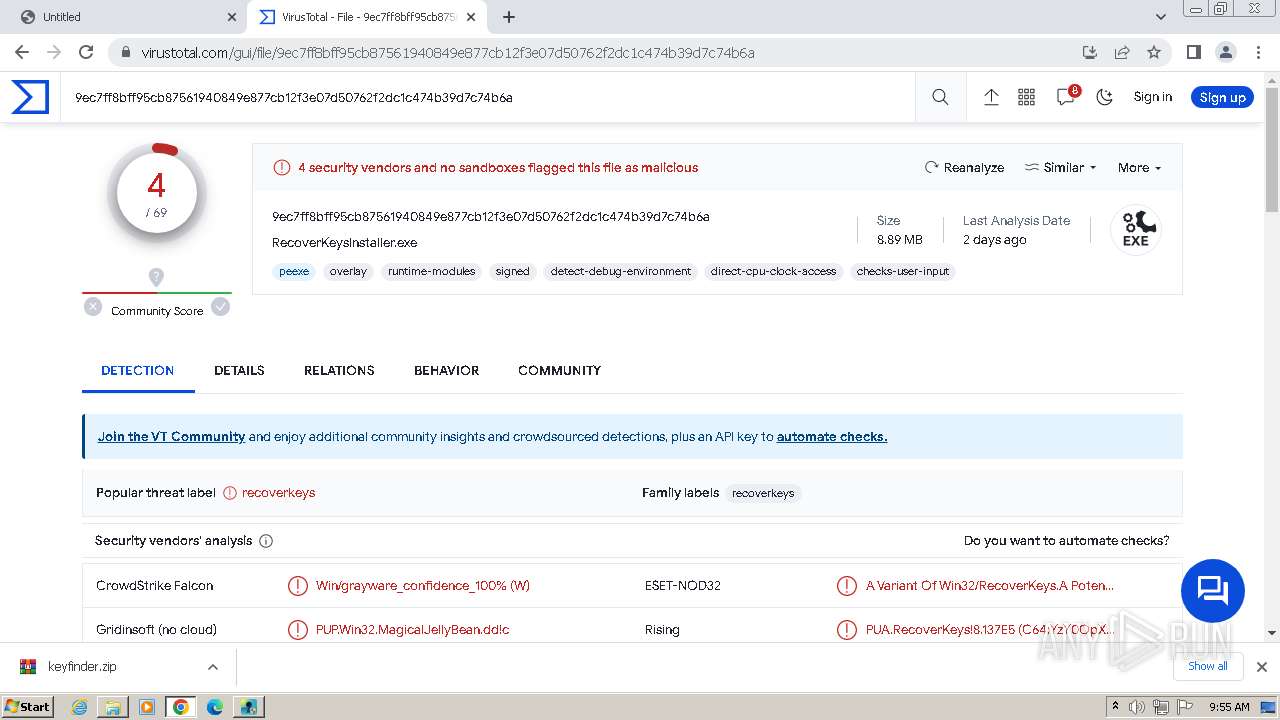
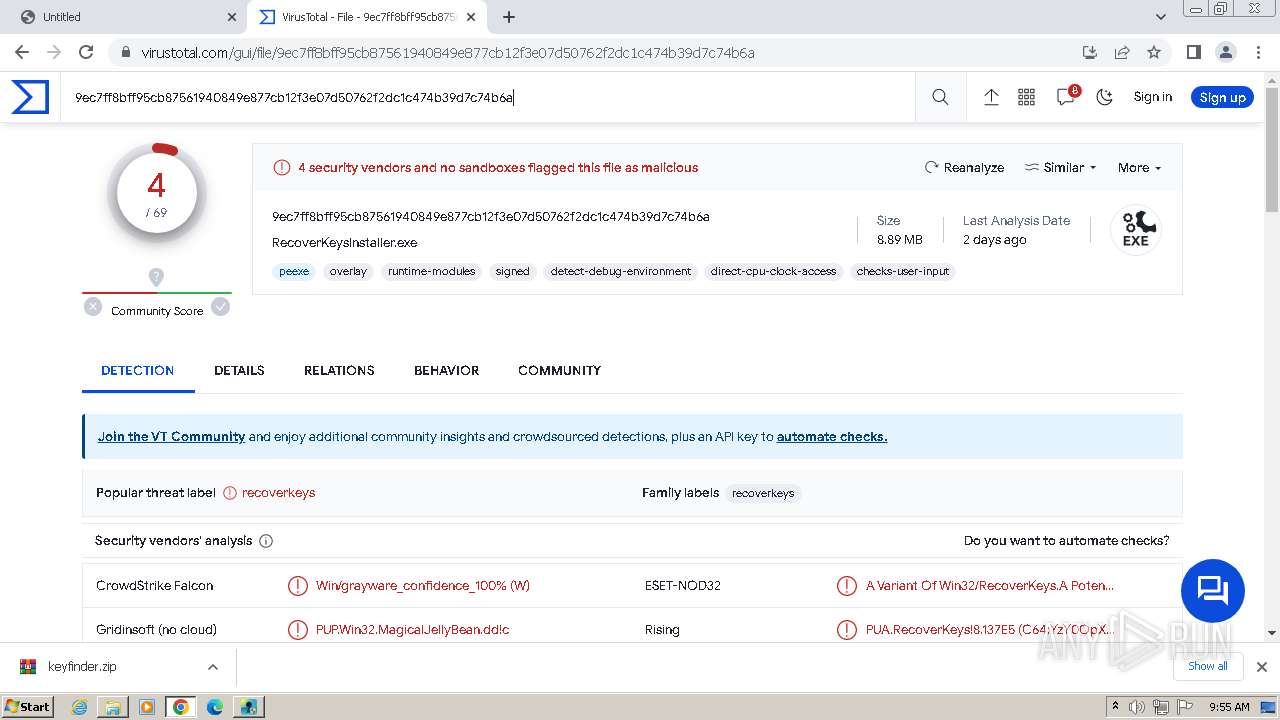
MALICIOUS
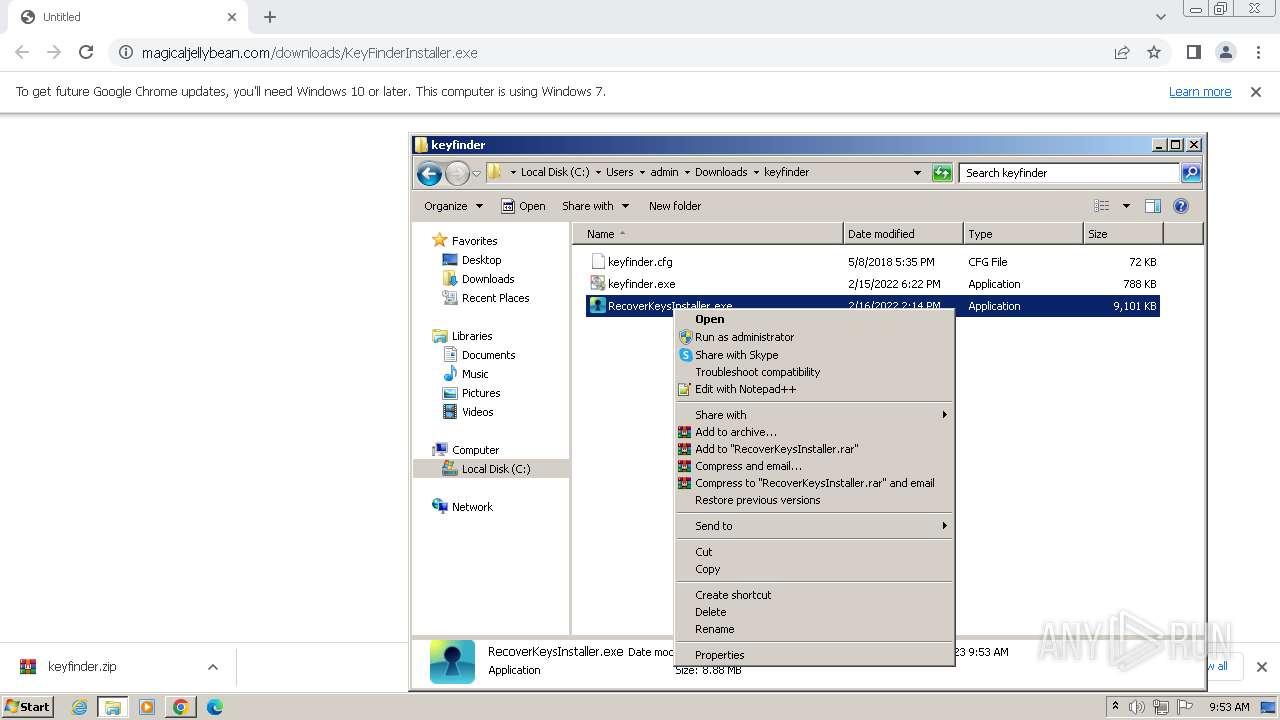
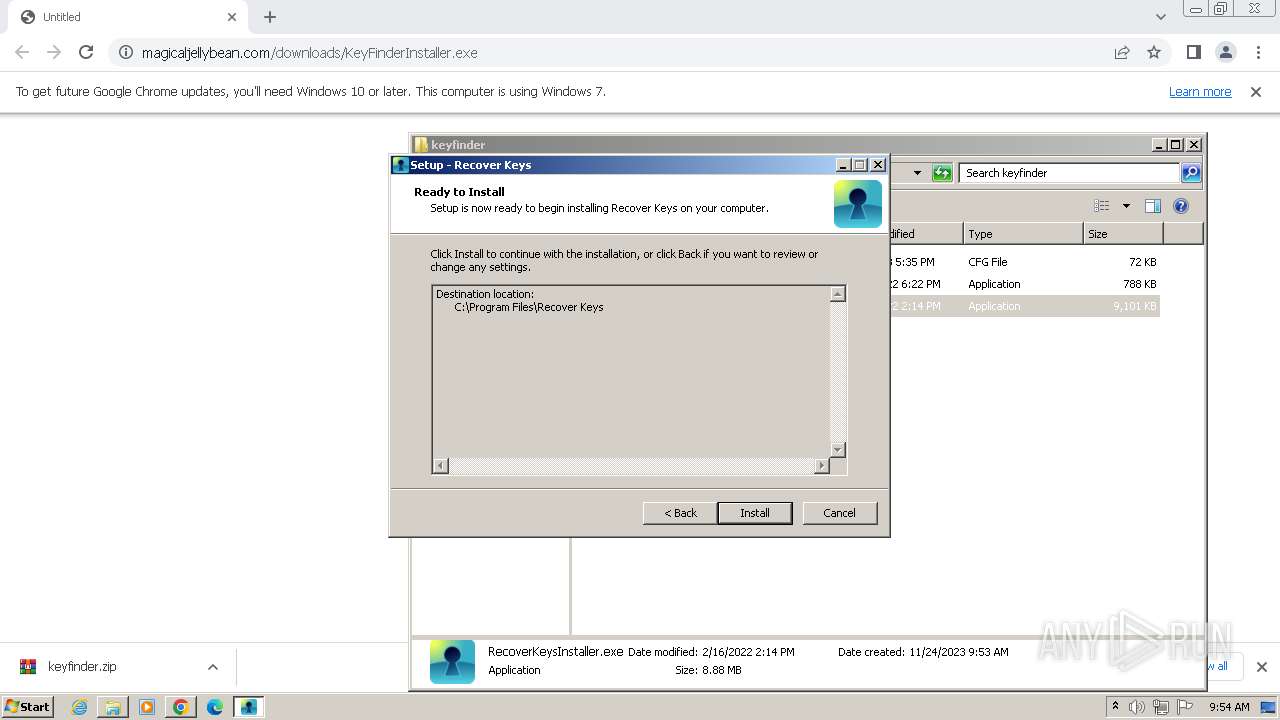
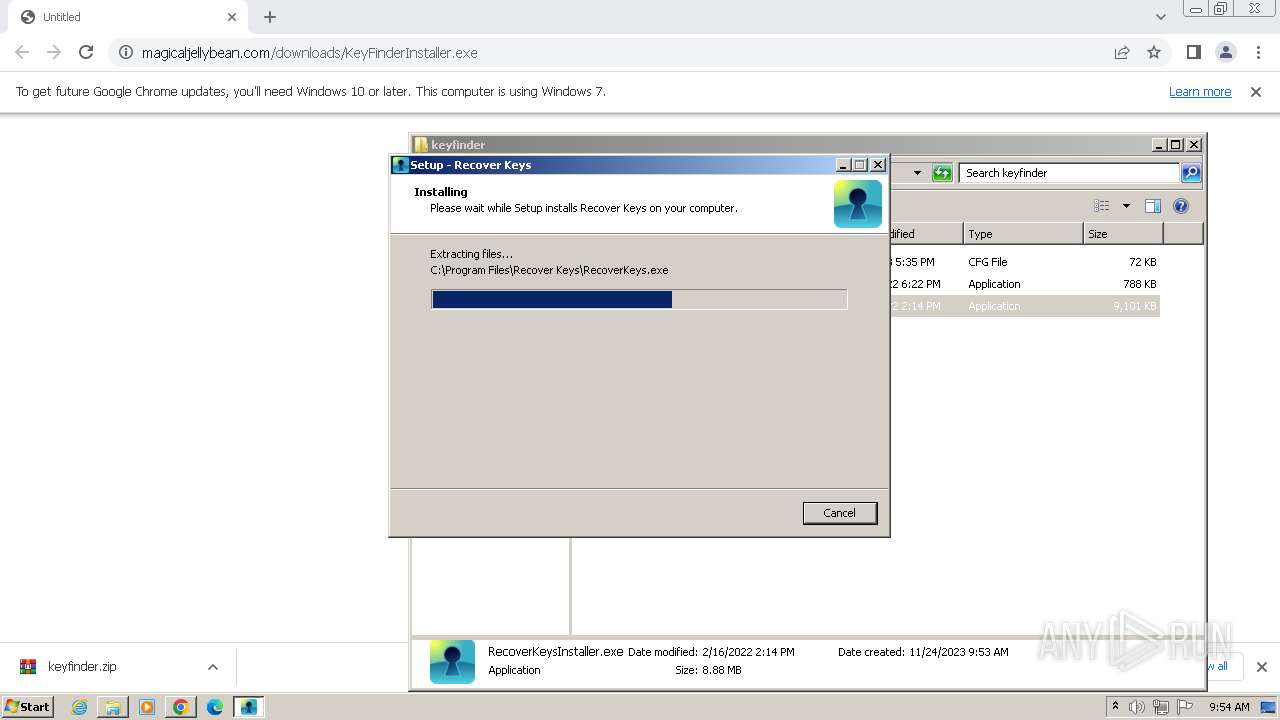
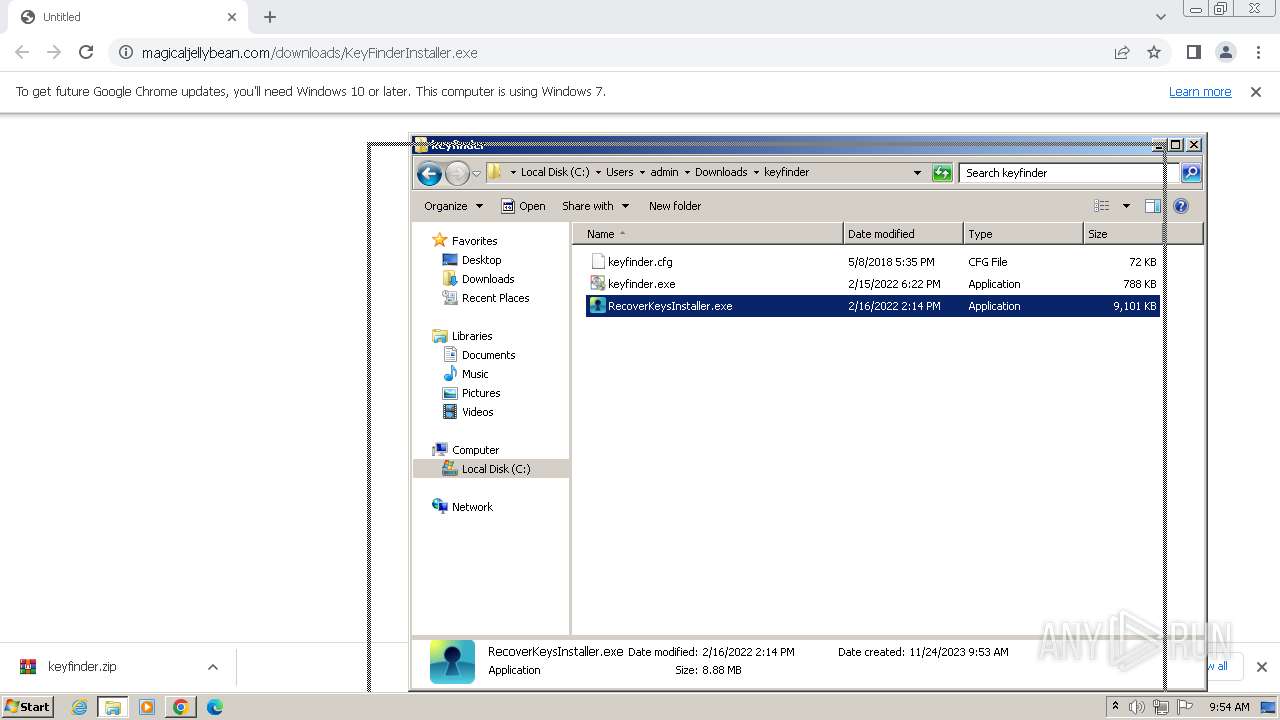
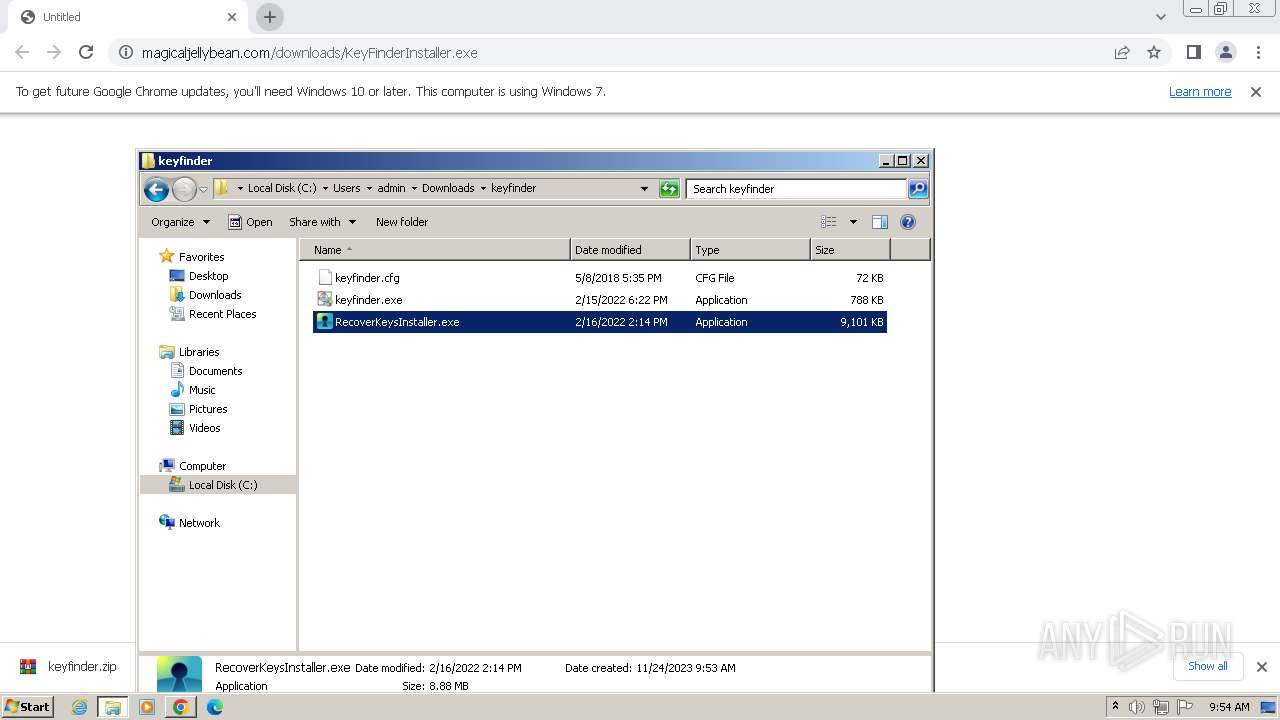
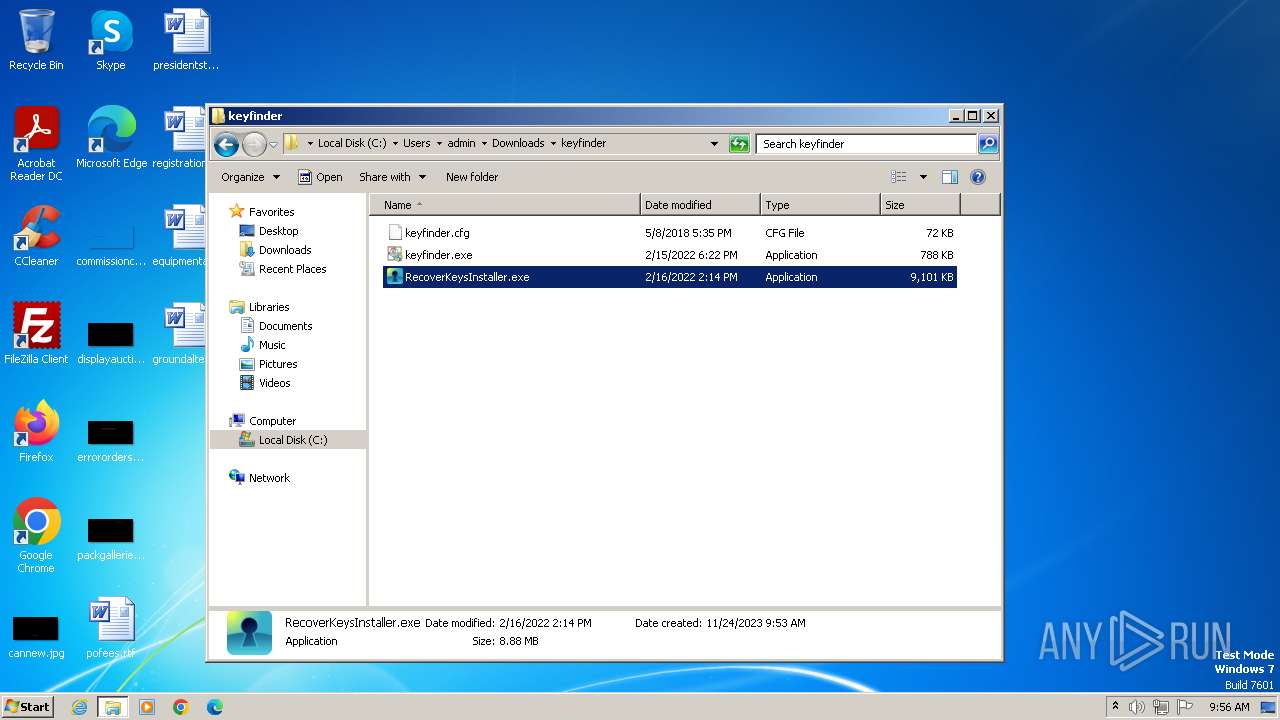
Drops the executable file immediately after the start
- RecoverKeysInstaller.exe (PID: 3700)
- RecoverKeysInstaller.tmp (PID: 1128)
- RecoverKeysInstaller.exe (PID: 120)
SUSPICIOUS
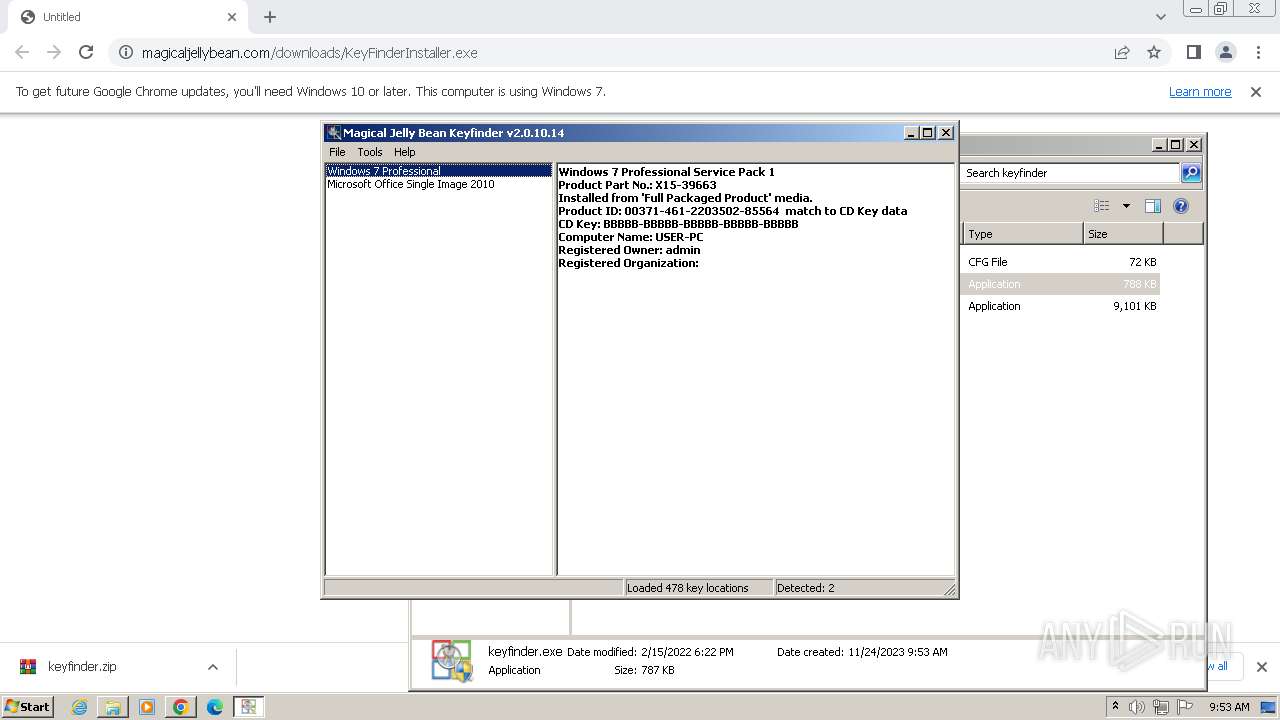
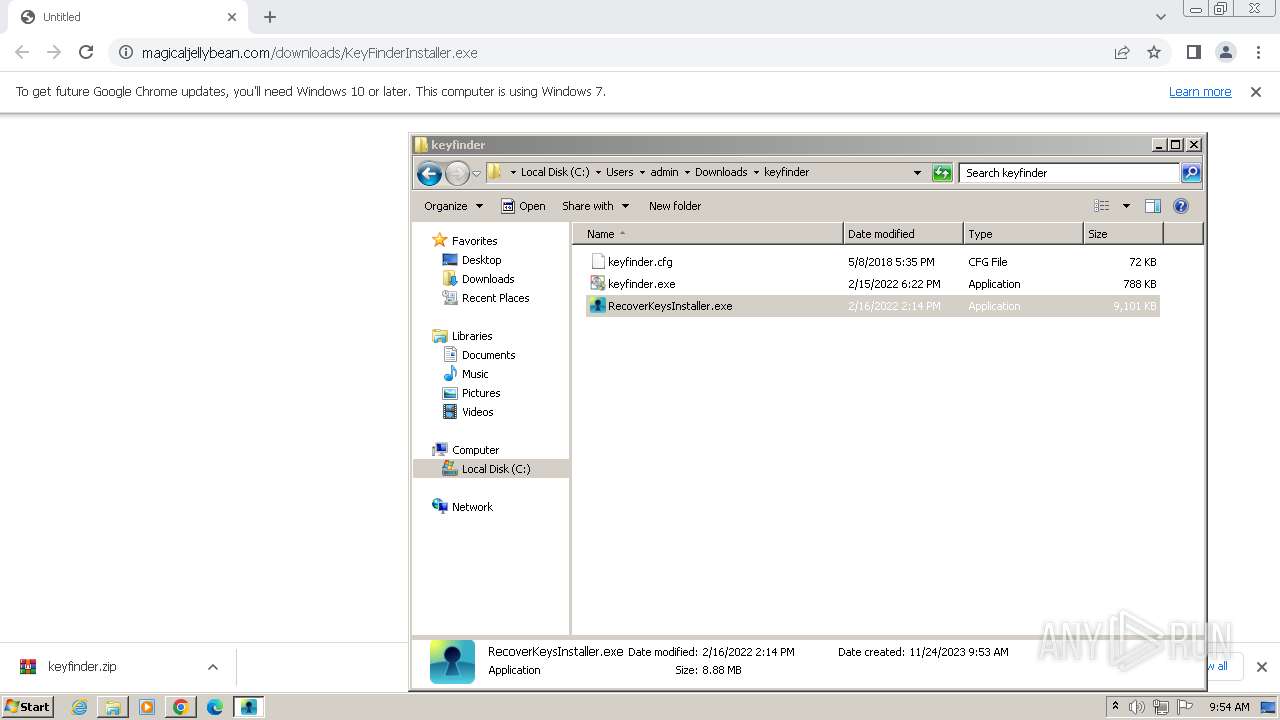
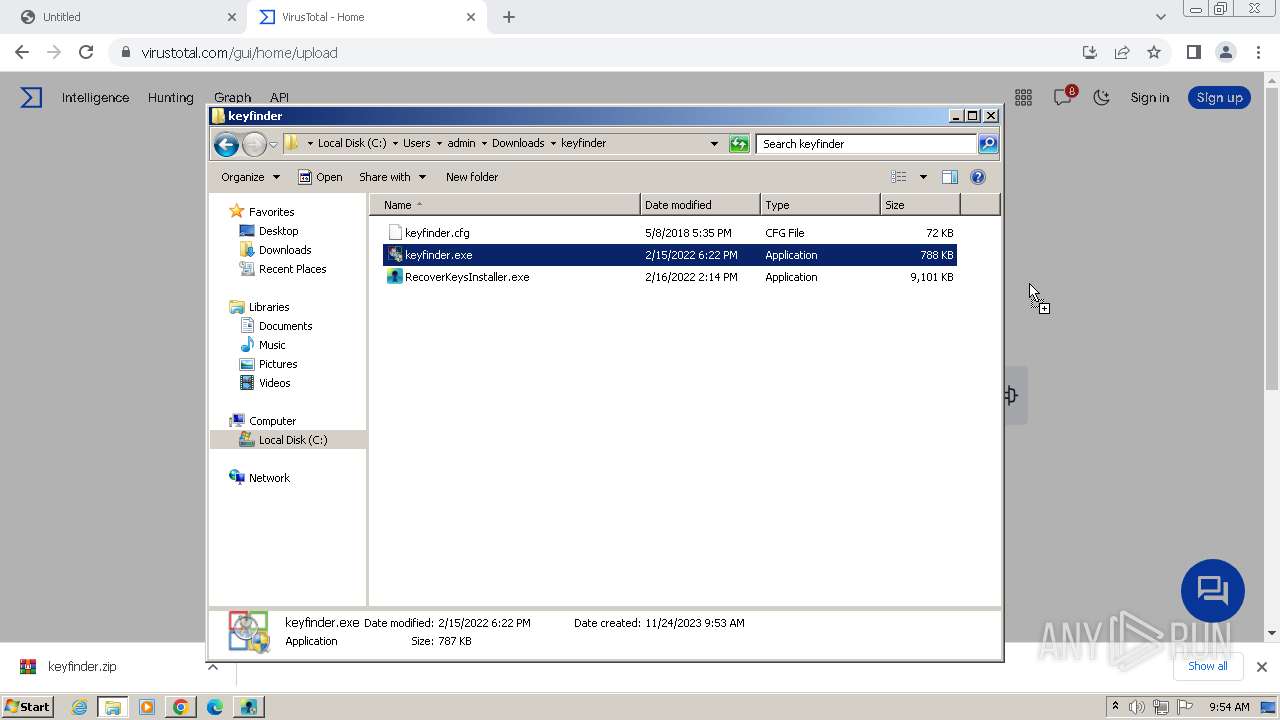
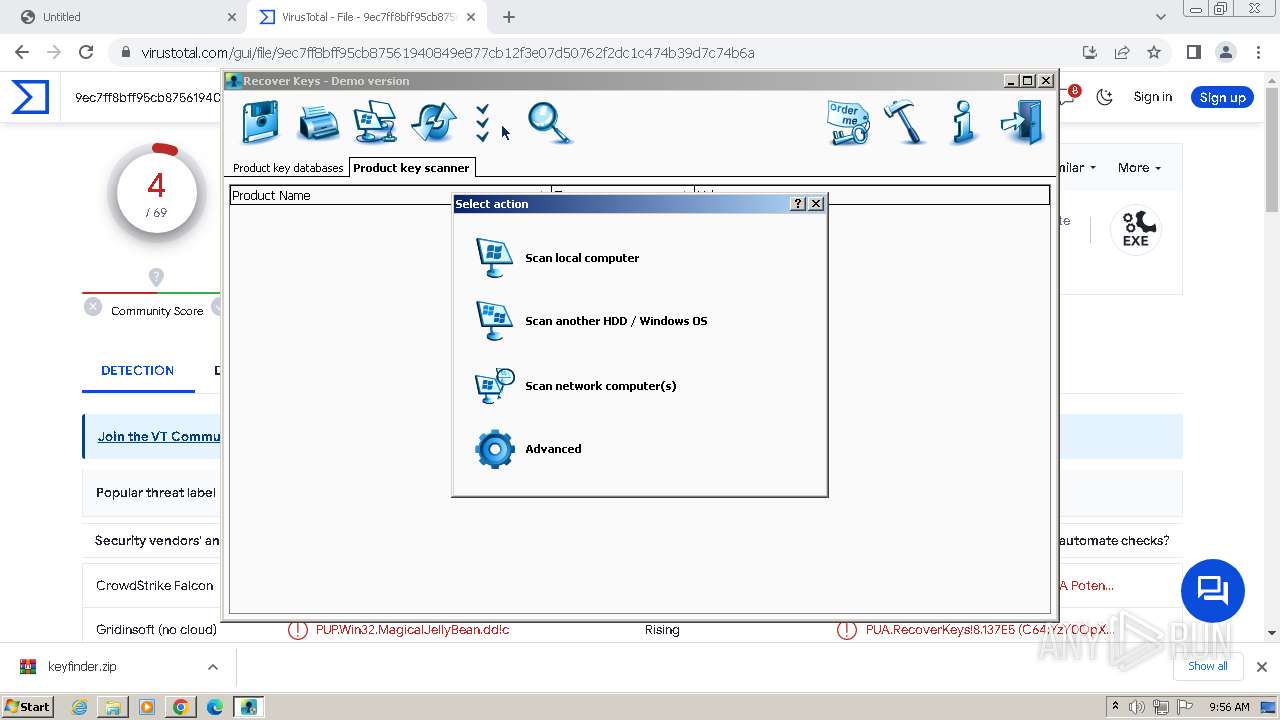
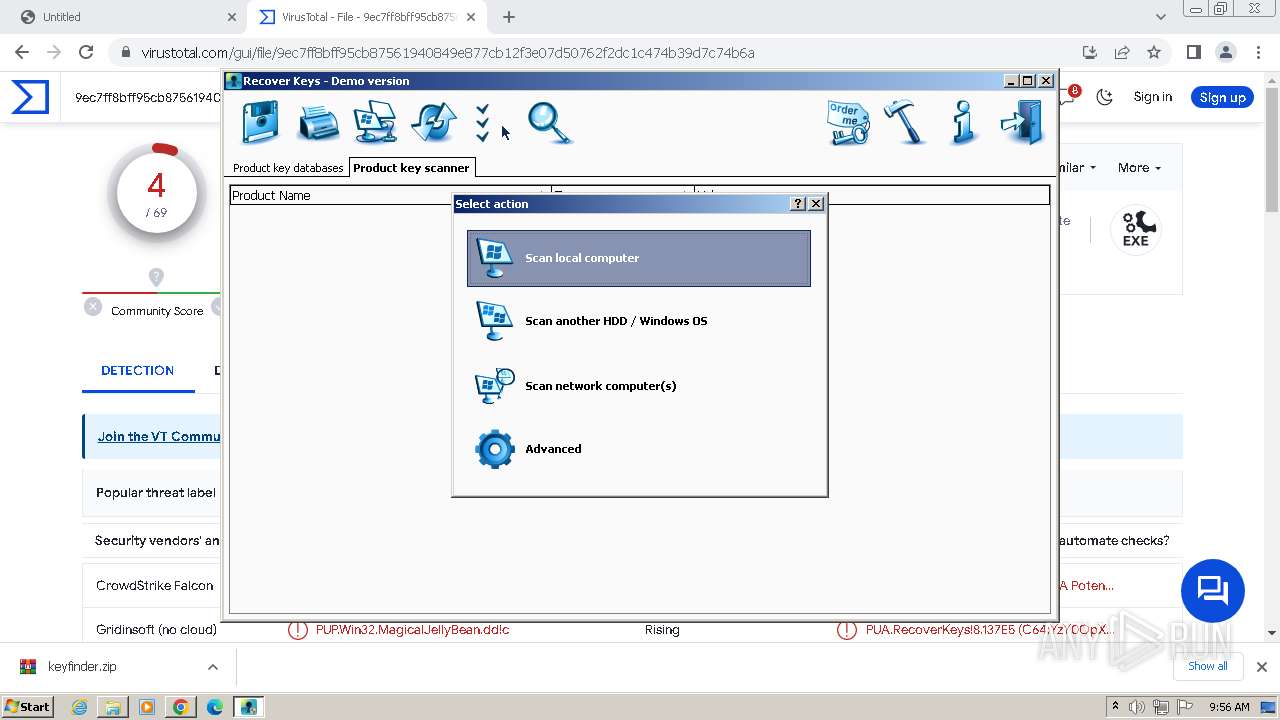
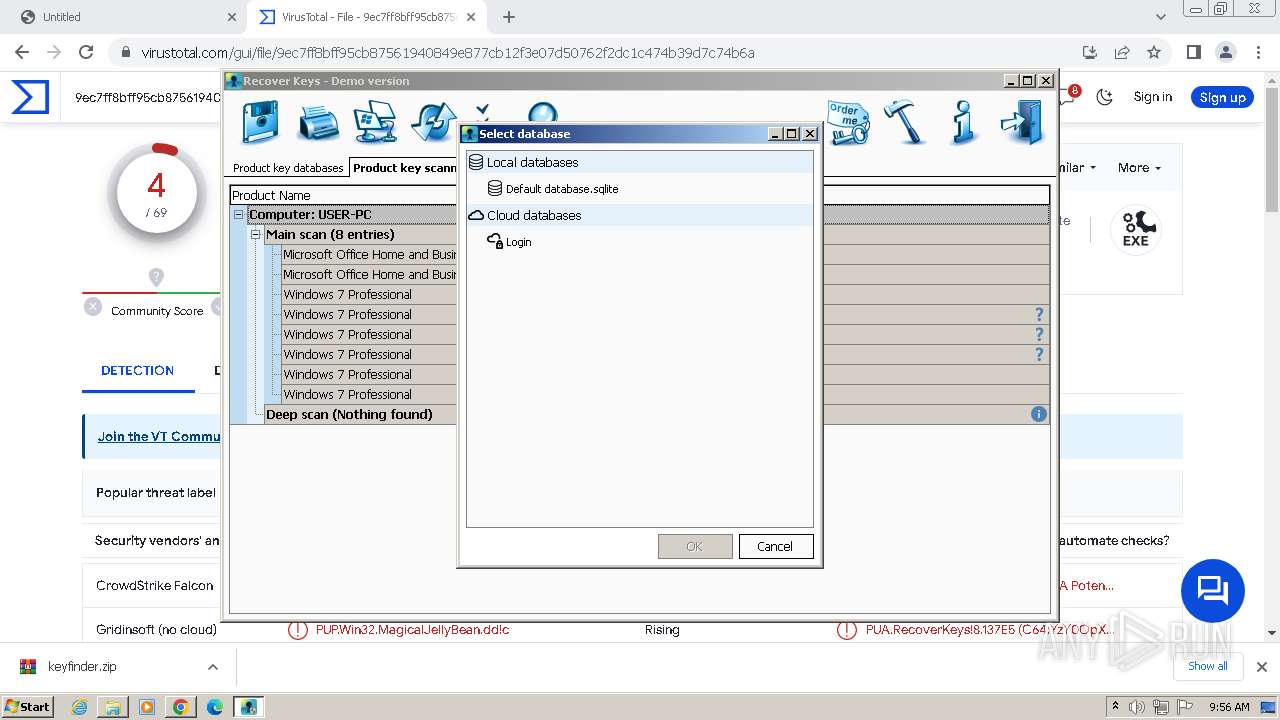
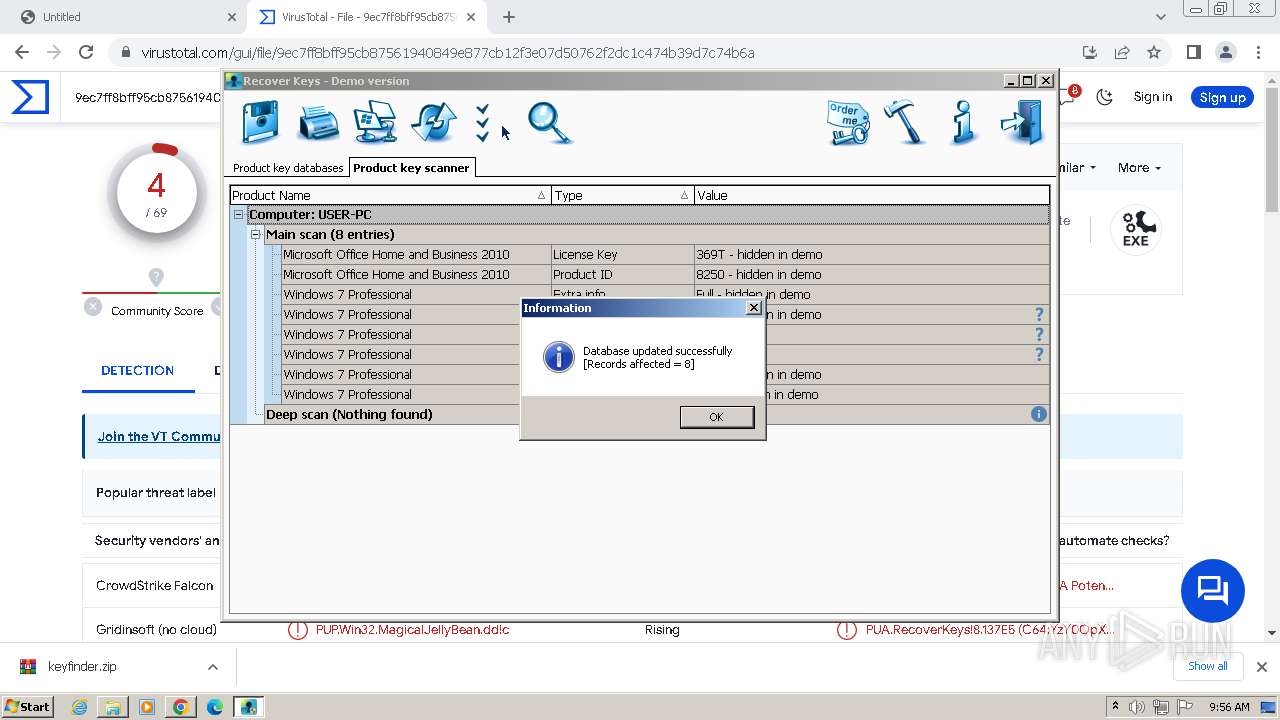
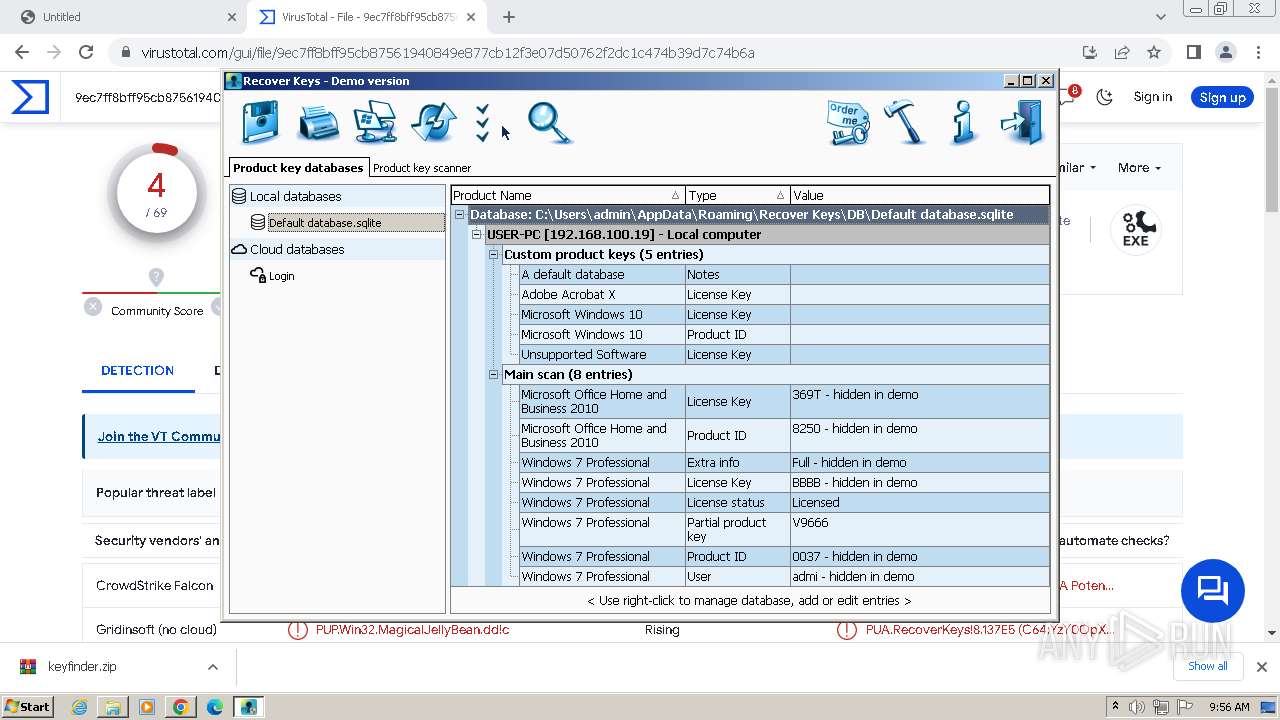
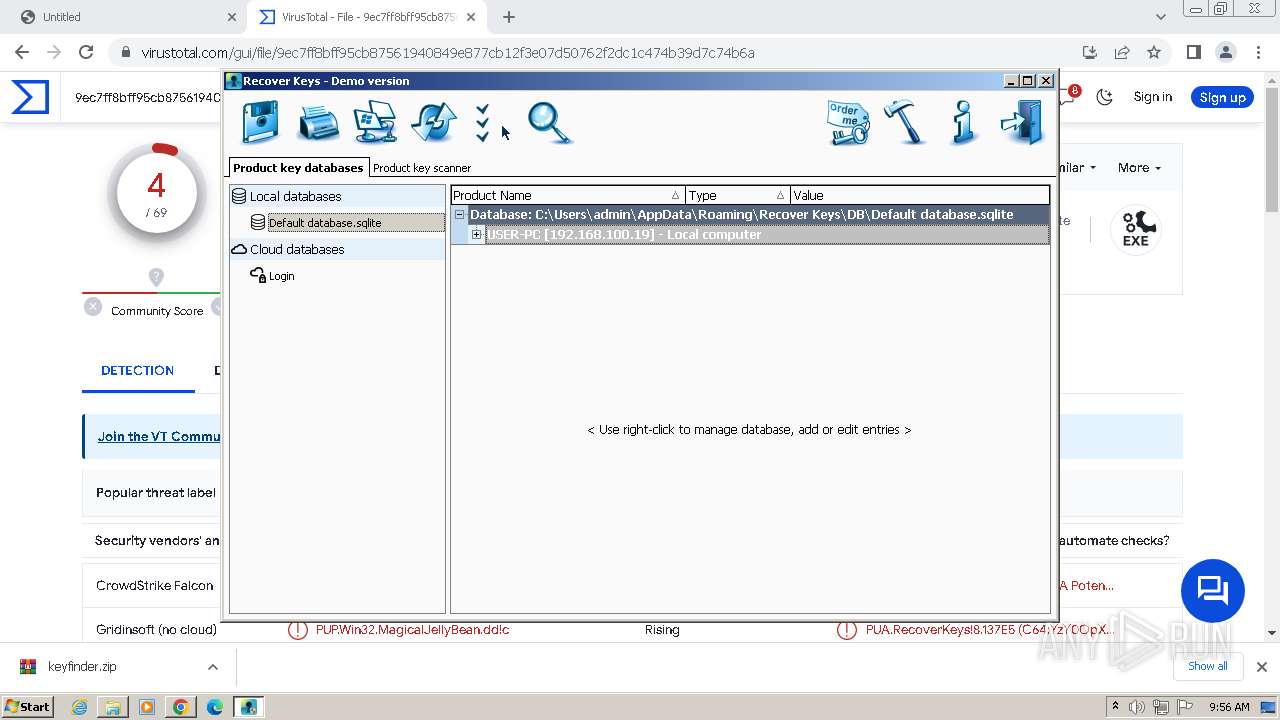
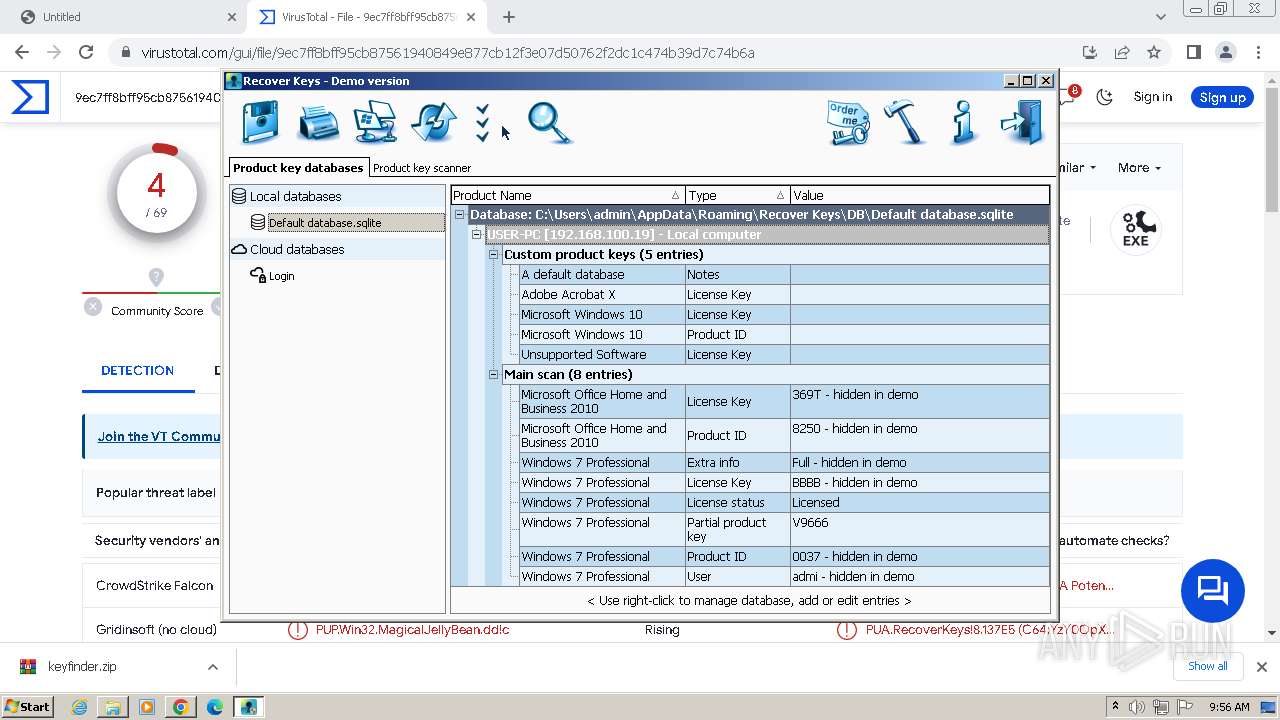
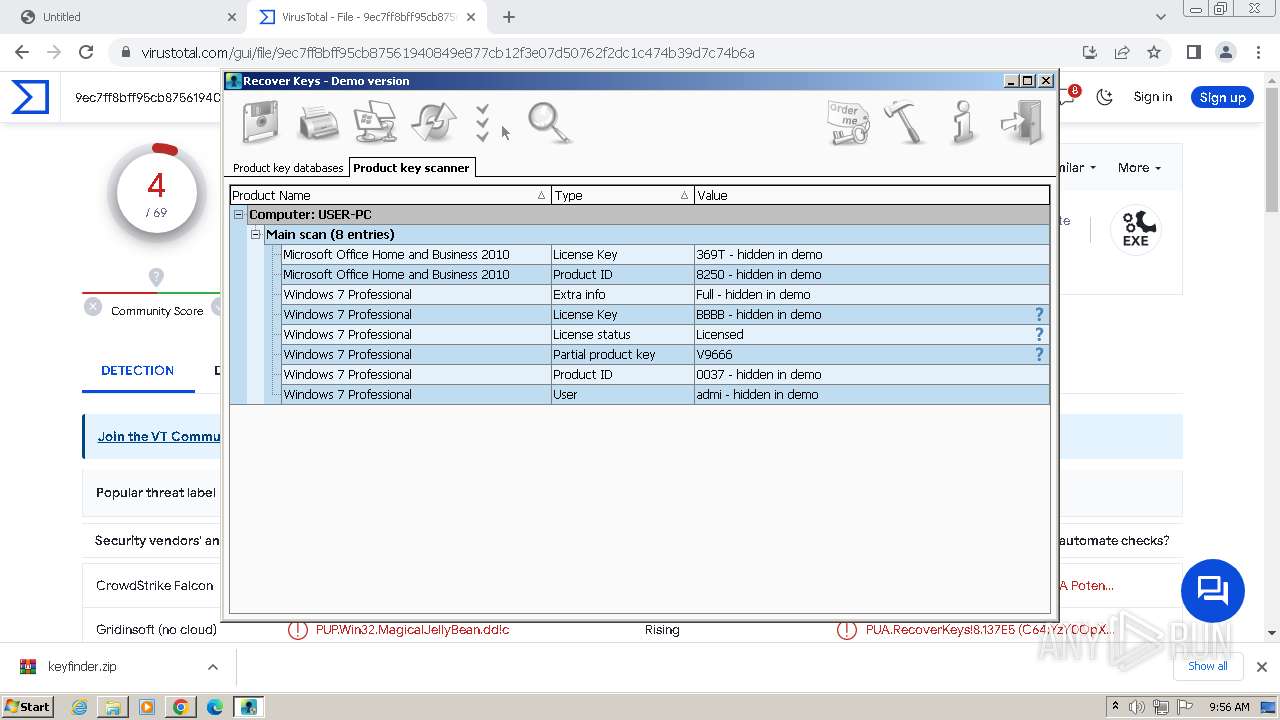
Searches for installed software
- keyfinder.exe (PID: 368)
- RecoverKeys.exe (PID: 3464)
Reads the Windows owner or organization settings
- RecoverKeysInstaller.tmp (PID: 1128)
- keyfinder.exe (PID: 368)
- RecoverKeys.exe (PID: 3464)
Reads the Internet Settings
- RecoverKeysInstaller.tmp (PID: 3708)
INFO
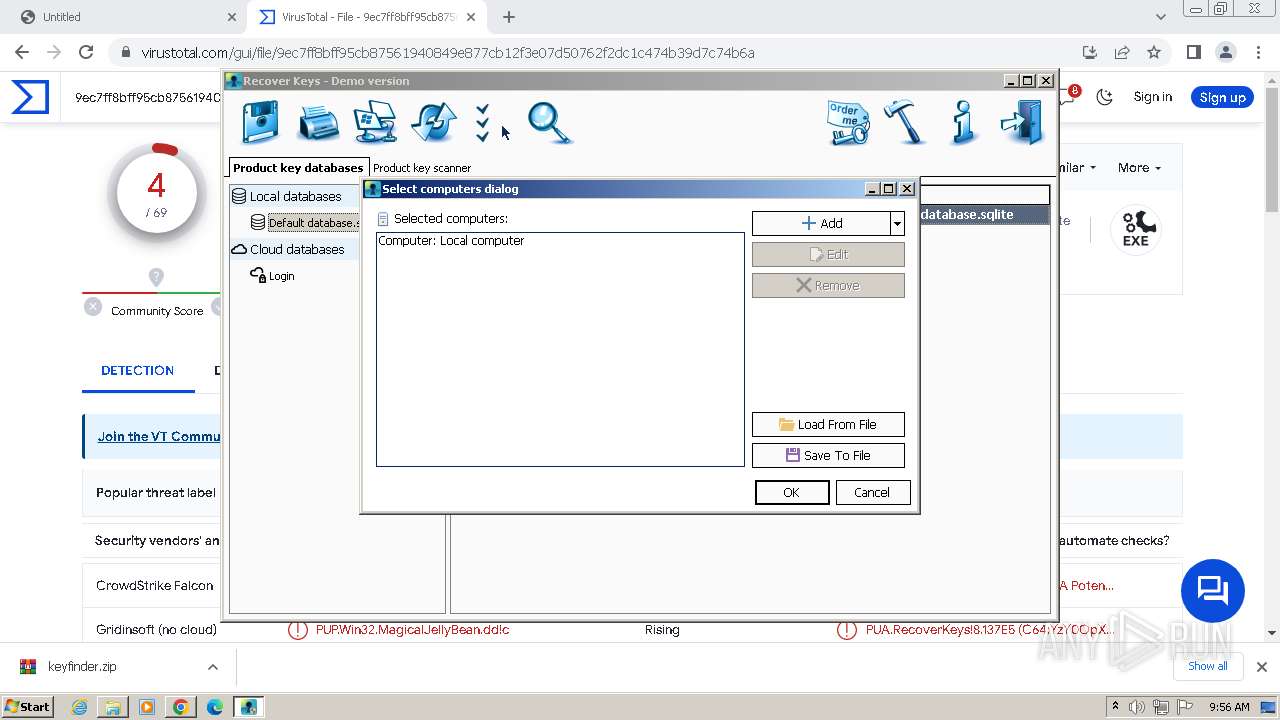
Reads the computer name
- wmpnscfg.exe (PID: 2484)
- keyfinder.exe (PID: 368)
- RecoverKeysInstaller.tmp (PID: 3708)
- RecoverKeysInstaller.tmp (PID: 1128)
- RecoverKeys.exe (PID: 3464)
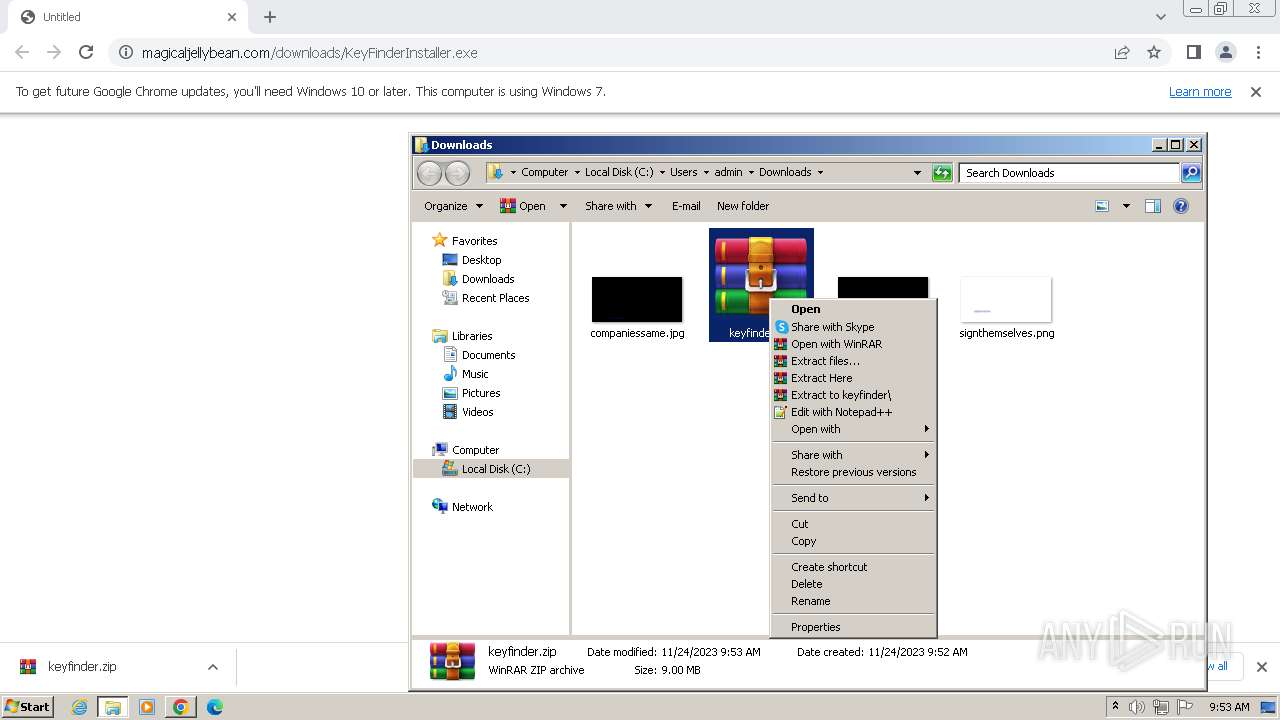
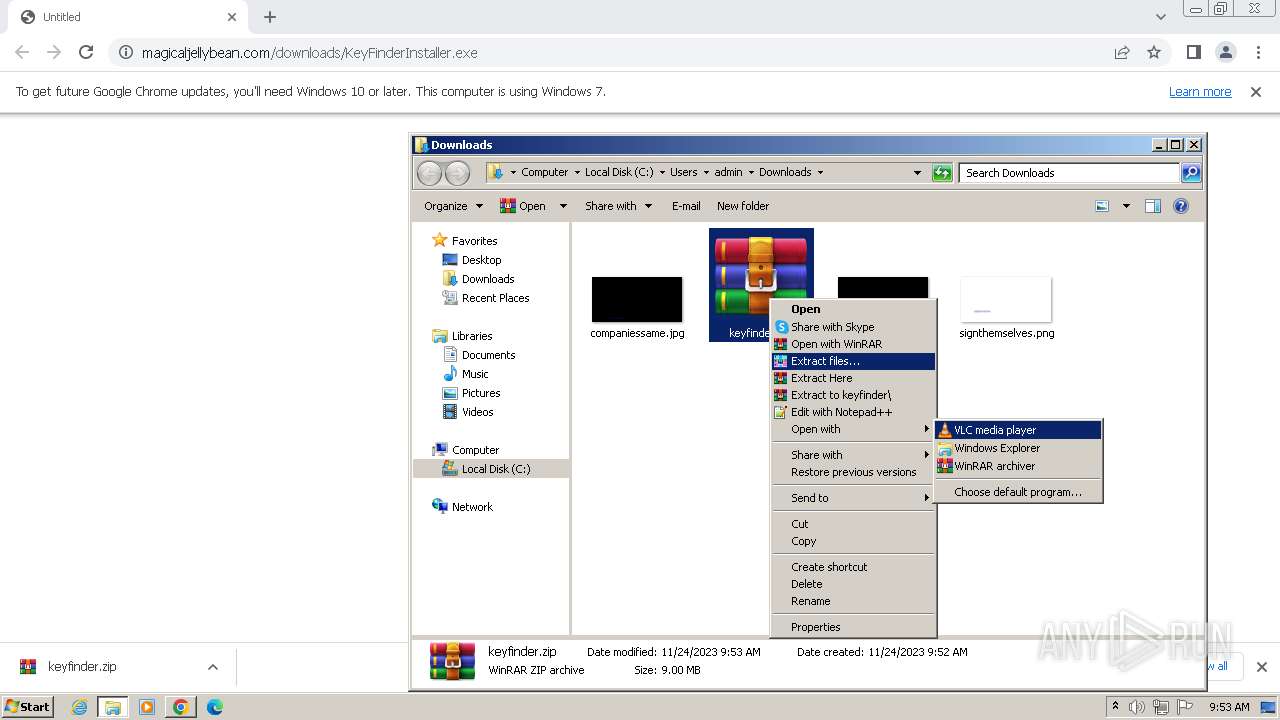
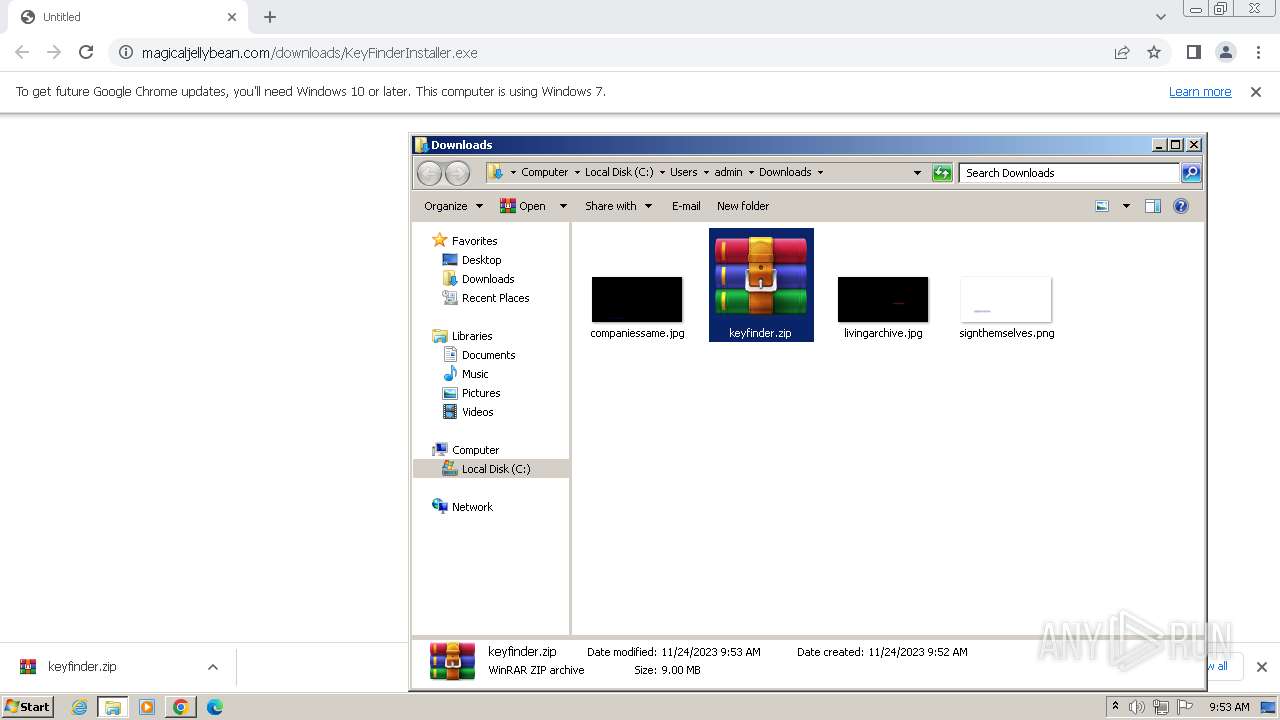
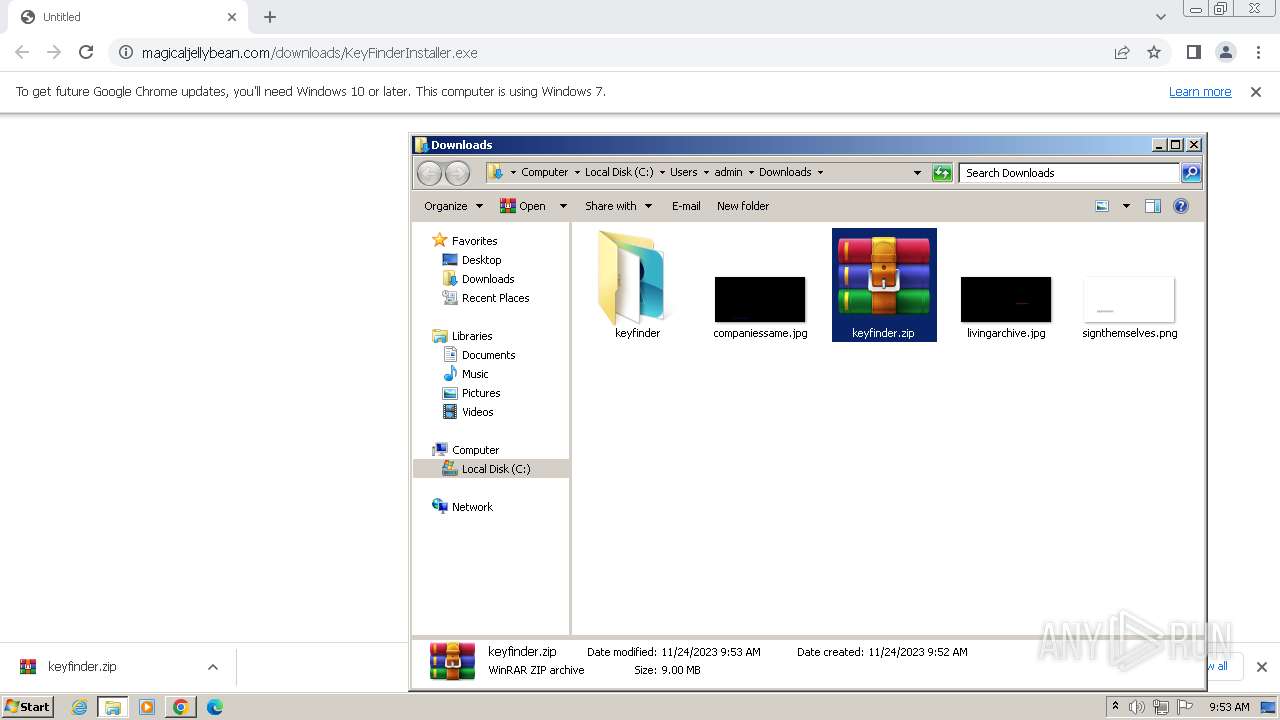
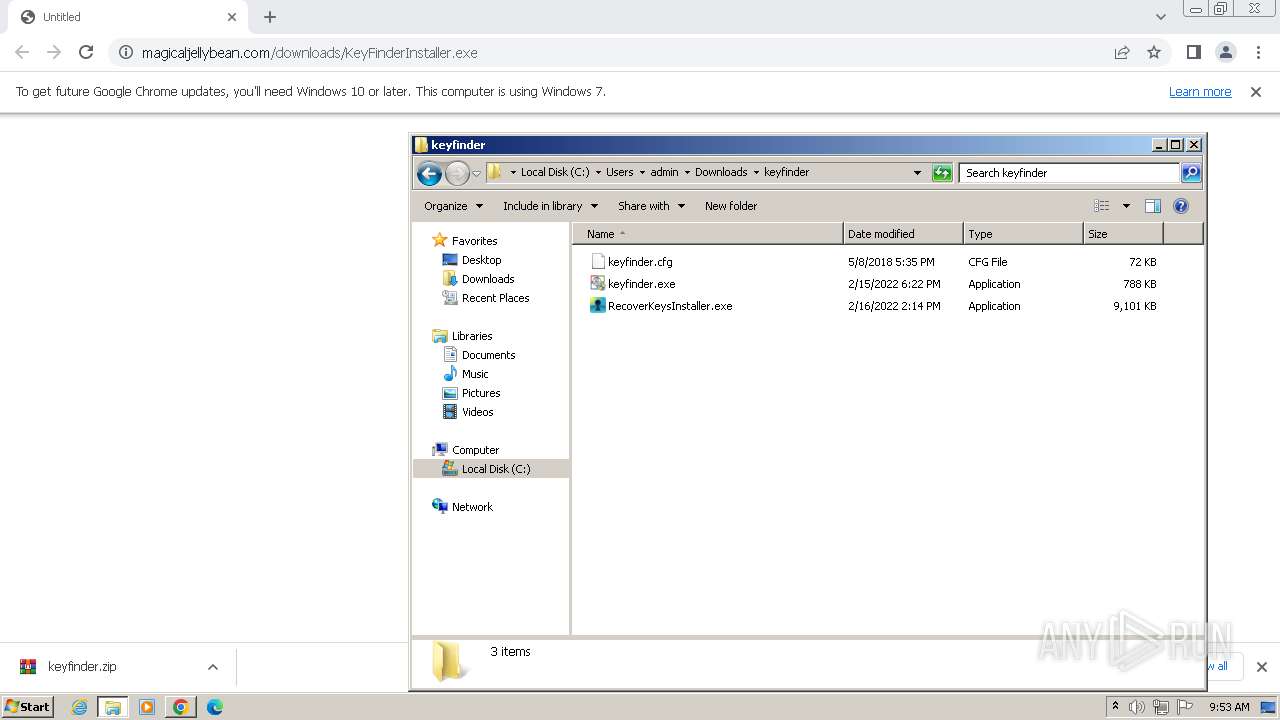
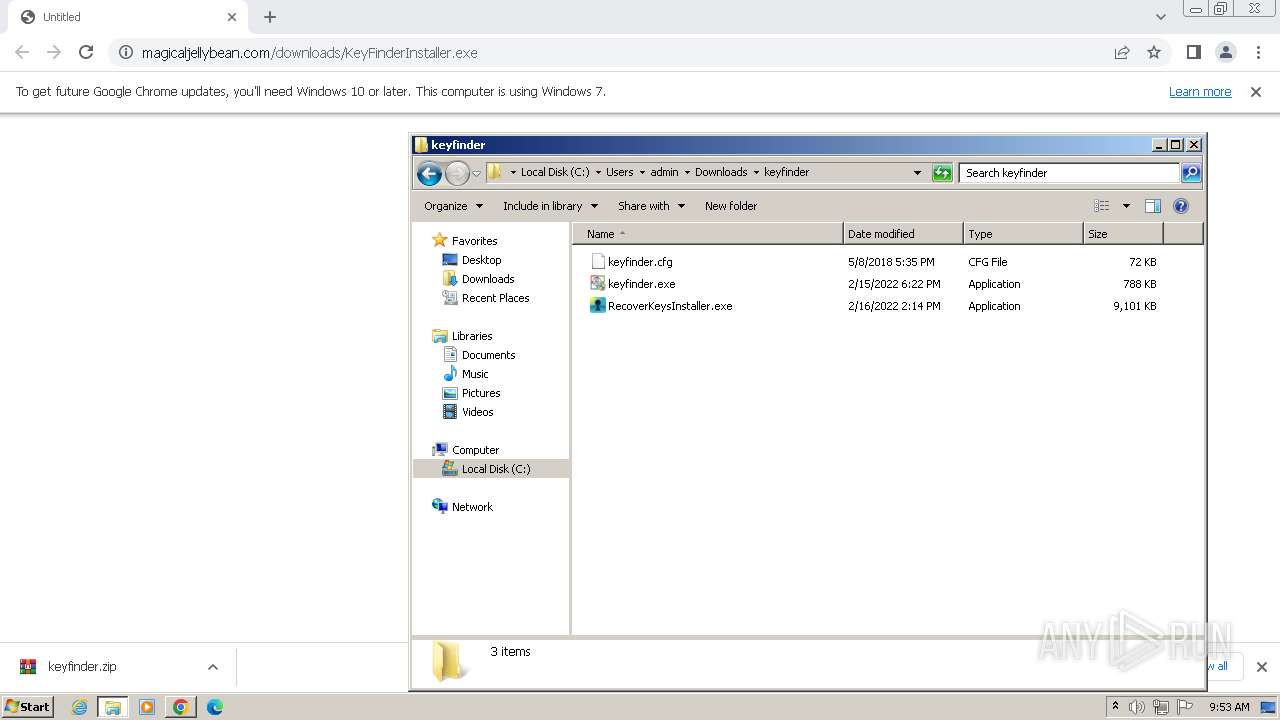
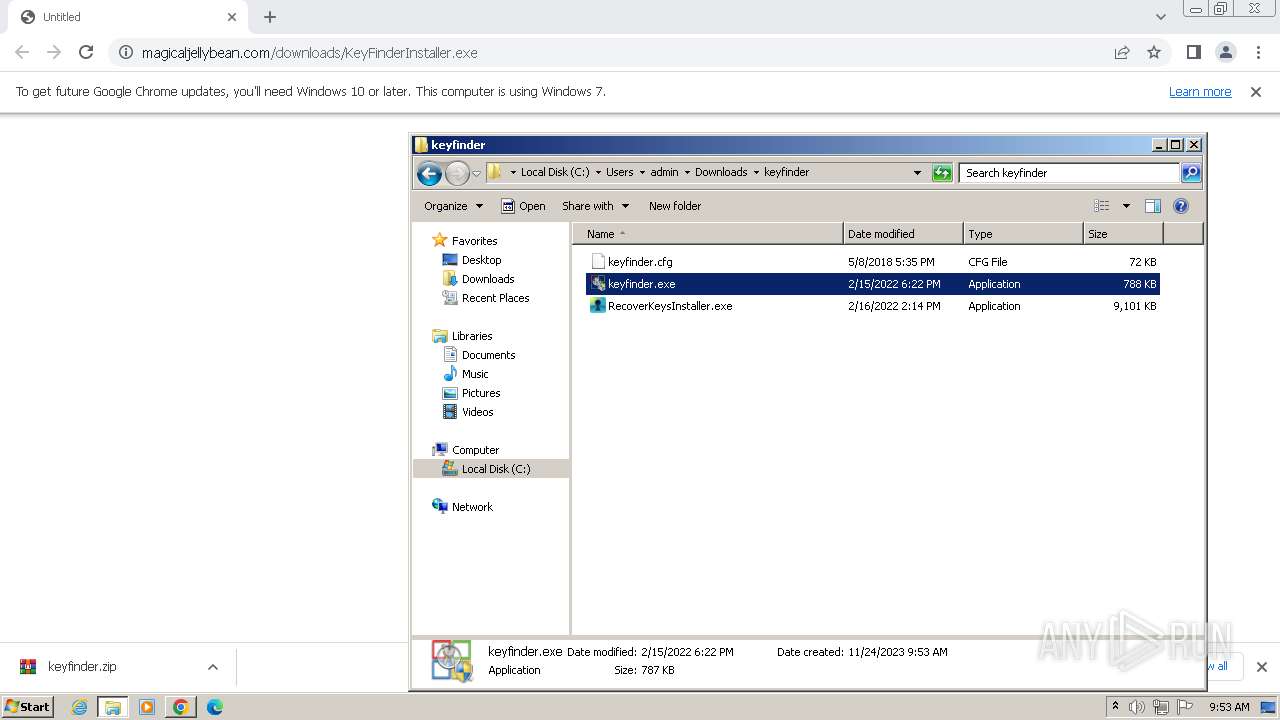
Manual execution by a user
- wmpnscfg.exe (PID: 2484)
- WinRAR.exe (PID: 3724)
- keyfinder.exe (PID: 2612)
- keyfinder.exe (PID: 368)
- RecoverKeysInstaller.exe (PID: 3700)
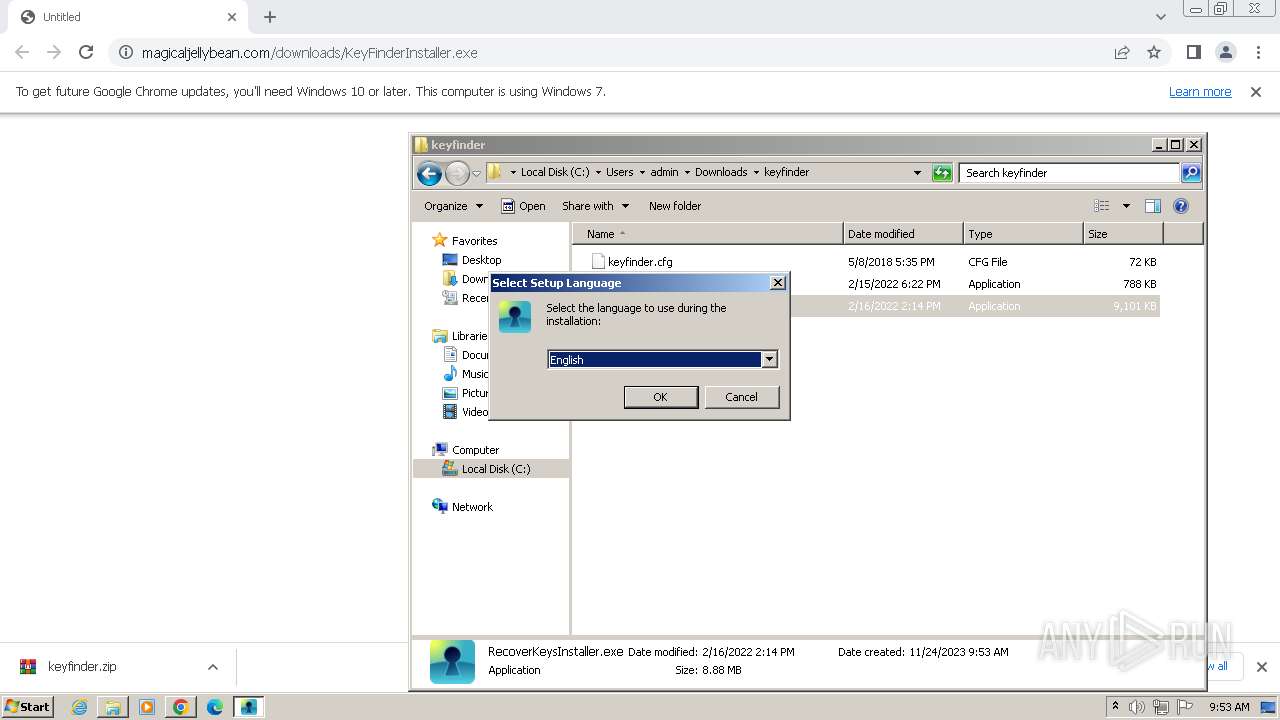
Checks supported languages
- wmpnscfg.exe (PID: 2484)
- keyfinder.exe (PID: 368)
- RecoverKeysInstaller.exe (PID: 3700)
- RecoverKeysInstaller.tmp (PID: 3708)
- RecoverKeysInstaller.exe (PID: 120)
- RecoverKeysInstaller.tmp (PID: 1128)
- RecoverKeys.exe (PID: 3464)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2484)
- RecoverKeys.exe (PID: 3464)
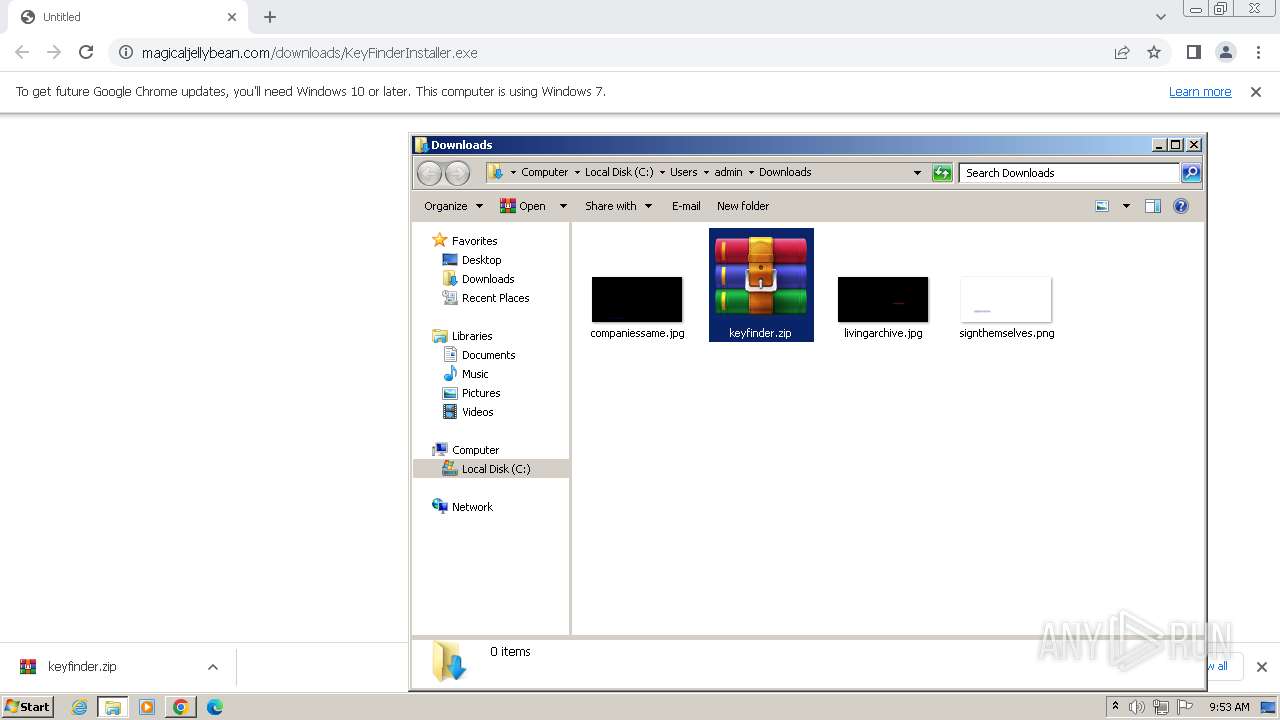
The process uses the downloaded file
- chrome.exe (PID: 3508)
- WinRAR.exe (PID: 3724)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 2440)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3724)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 3112)
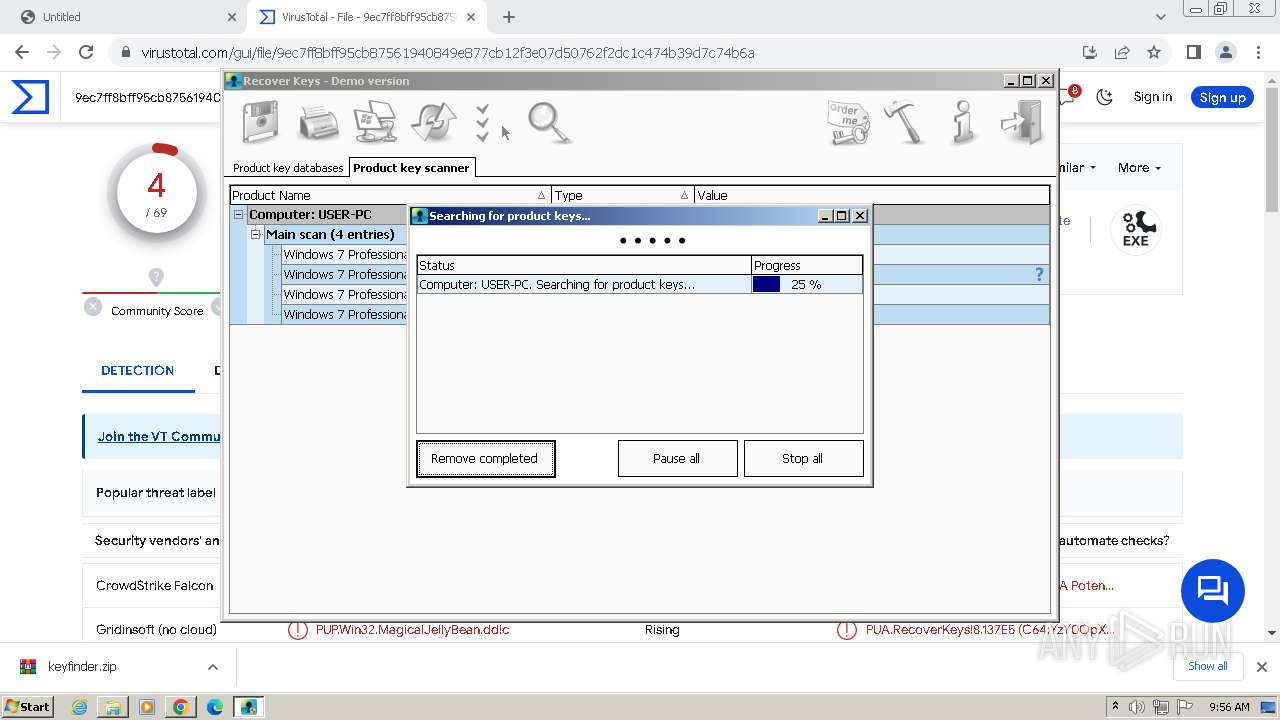
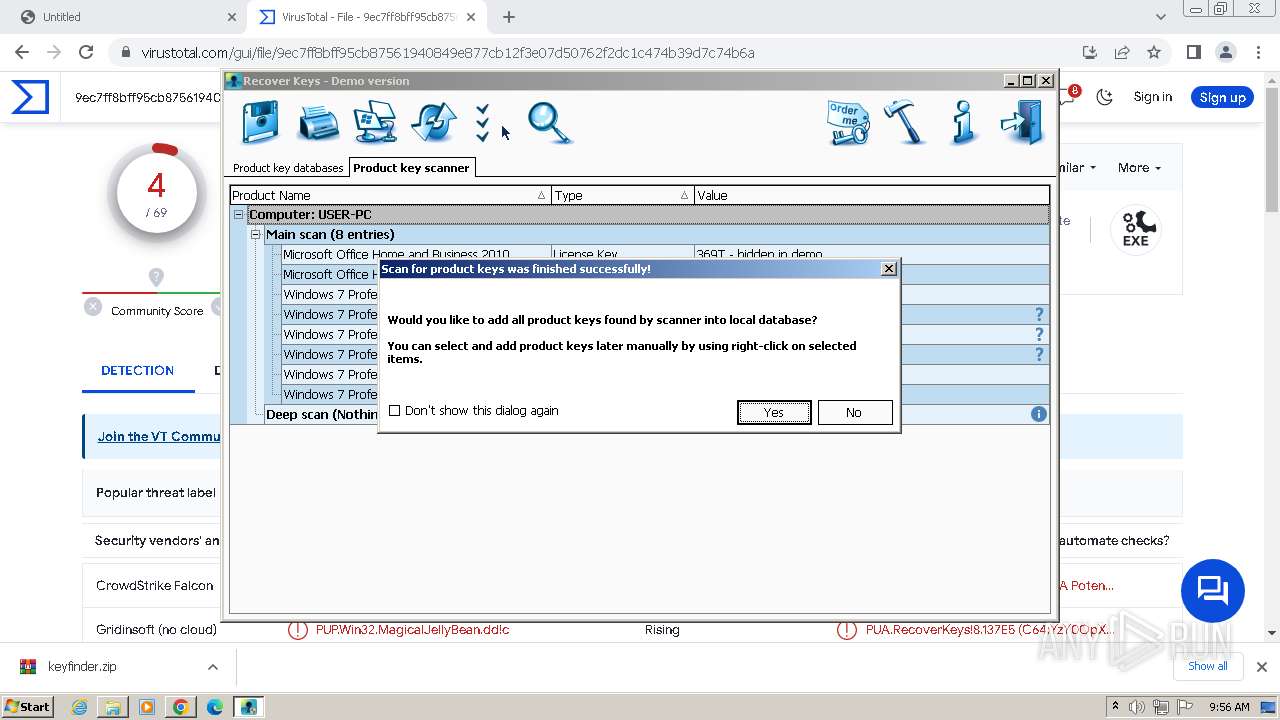
Reads Microsoft Office registry keys
- keyfinder.exe (PID: 368)
- RecoverKeys.exe (PID: 3464)
Reads product name
- keyfinder.exe (PID: 368)
- RecoverKeys.exe (PID: 3464)
Reads Environment values
- keyfinder.exe (PID: 368)
- RecoverKeys.exe (PID: 3464)
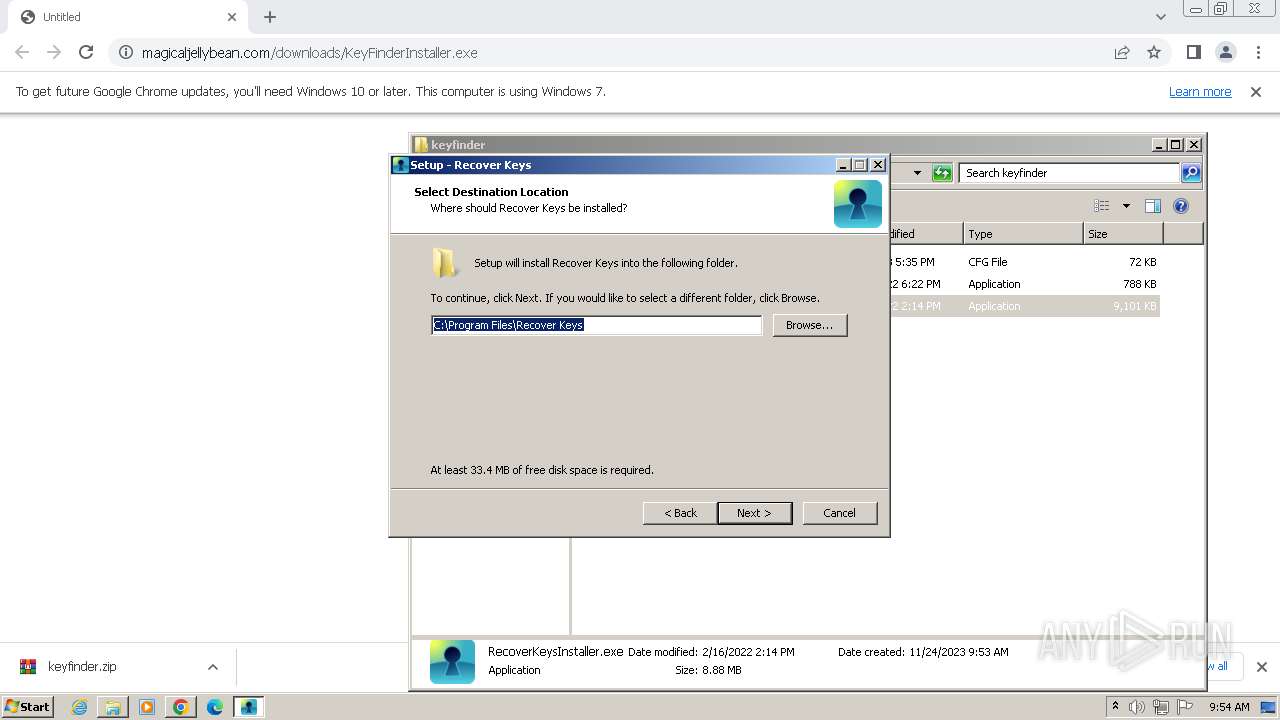
Create files in a temporary directory
- RecoverKeysInstaller.exe (PID: 3700)
- RecoverKeysInstaller.exe (PID: 120)
Creates files in the program directory
- RecoverKeysInstaller.tmp (PID: 1128)
Application launched itself
- chrome.exe (PID: 2168)
Reads Windows Product ID
- keyfinder.exe (PID: 368)
- RecoverKeys.exe (PID: 3464)
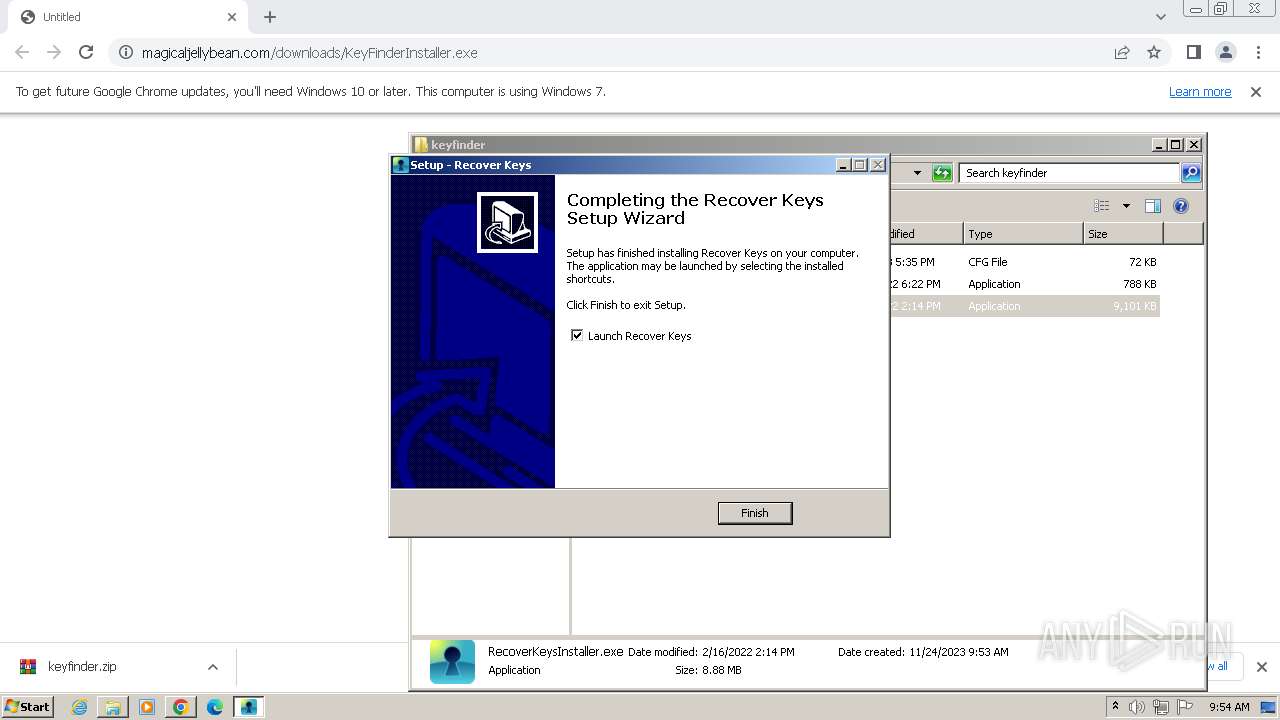
Creates files or folders in the user directory
- RecoverKeys.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
45
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\Downloads\keyfinder\RecoverKeysInstaller.exe" /SPAWNWND=$7021E /NOTIFYWND=$B0160 | C:\Users\admin\Downloads\keyfinder\RecoverKeysInstaller.exe | RecoverKeysInstaller.tmp | ||||||||||||
User: admin Company: Recover Keys Integrity Level: HIGH Description: Recover Keys Setup Exit code: 0 Version: 11.0.4.235 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3456 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 368 | "C:\Users\admin\Downloads\keyfinder\keyfinder.exe" | C:\Users\admin\Downloads\keyfinder\keyfinder.exe | explorer.exe | ||||||||||||
User: admin Company: ONE UP LTD. Integrity Level: HIGH Description: Magical Jelly Bean Keyfinder Exit code: 0 Version: 2.0.10.14 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\AppData\Local\Temp\is-G7KE6.tmp\RecoverKeysInstaller.tmp" /SL5="$A01EA,8764450,404480,C:\Users\admin\Downloads\keyfinder\RecoverKeysInstaller.exe" /SPAWNWND=$7021E /NOTIFYWND=$B0160 | C:\Users\admin\AppData\Local\Temp\is-G7KE6.tmp\RecoverKeysInstaller.tmp | — | RecoverKeysInstaller.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1156 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2020 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4056 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3872 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3816 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3716 --field-trial-handle=1176,i,9667679710392608857,8982371168231463713,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
15 384
Read events
15 257
Write events
116
Delete events
11
Modification events
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
17
Suspicious files
254
Text files
109
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bdf8f.TMP | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1bdfae.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1bdf8f.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1be490.TMP | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8d7d1a02-aa25-4582-a35e-ec2cd9d4f808.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1be125.TMP | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
65
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
3056 | chrome.exe | GET | 301 | 67.227.166.128:80 | http://www.magicaljellybean.com/downloads/KeyFinderInstaller.exe | unknown | html | 264 b | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 5.84 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.99 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 10.0 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 21.9 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 8.35 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 8.35 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 33.0 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 90.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3056 | chrome.exe | 67.227.166.128:80 | www.magicaljellybean.com | LIQUIDWEB | US | unknown |
2168 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3056 | chrome.exe | 172.217.16.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
3056 | chrome.exe | 67.227.166.128:443 | www.magicaljellybean.com | LIQUIDWEB | US | unknown |
2168 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3056 | chrome.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.magicaljellybean.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |