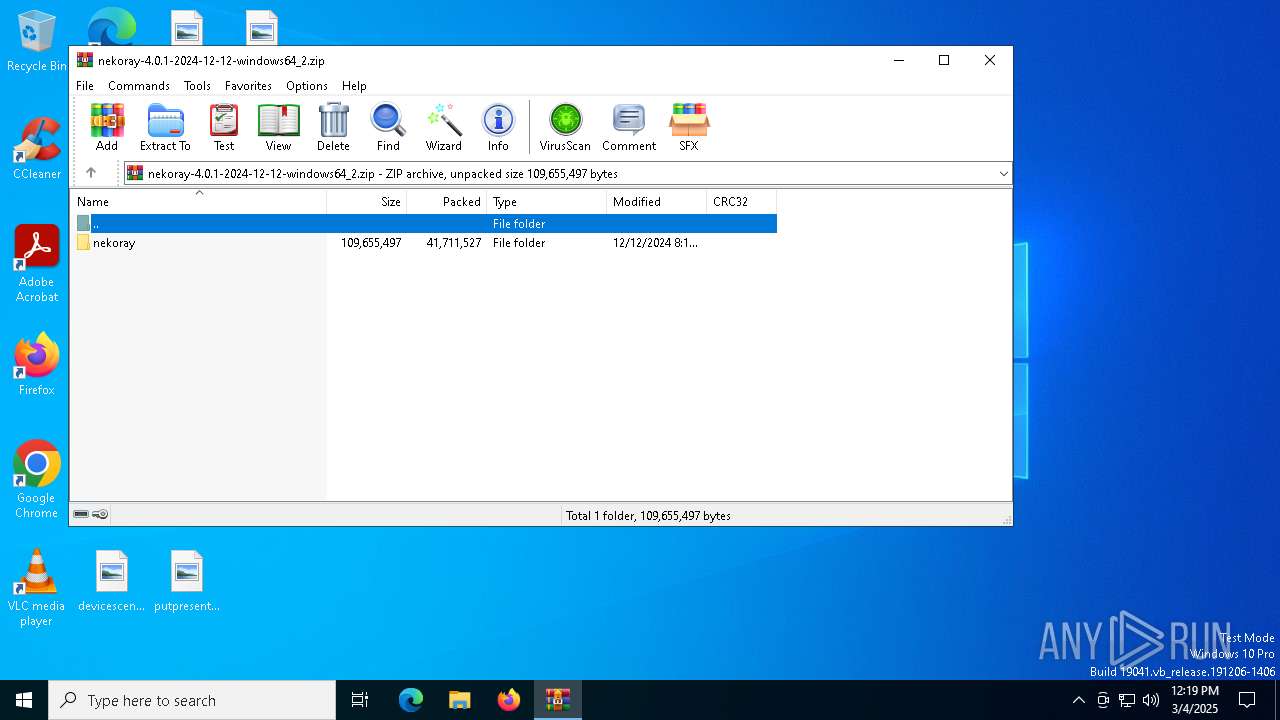
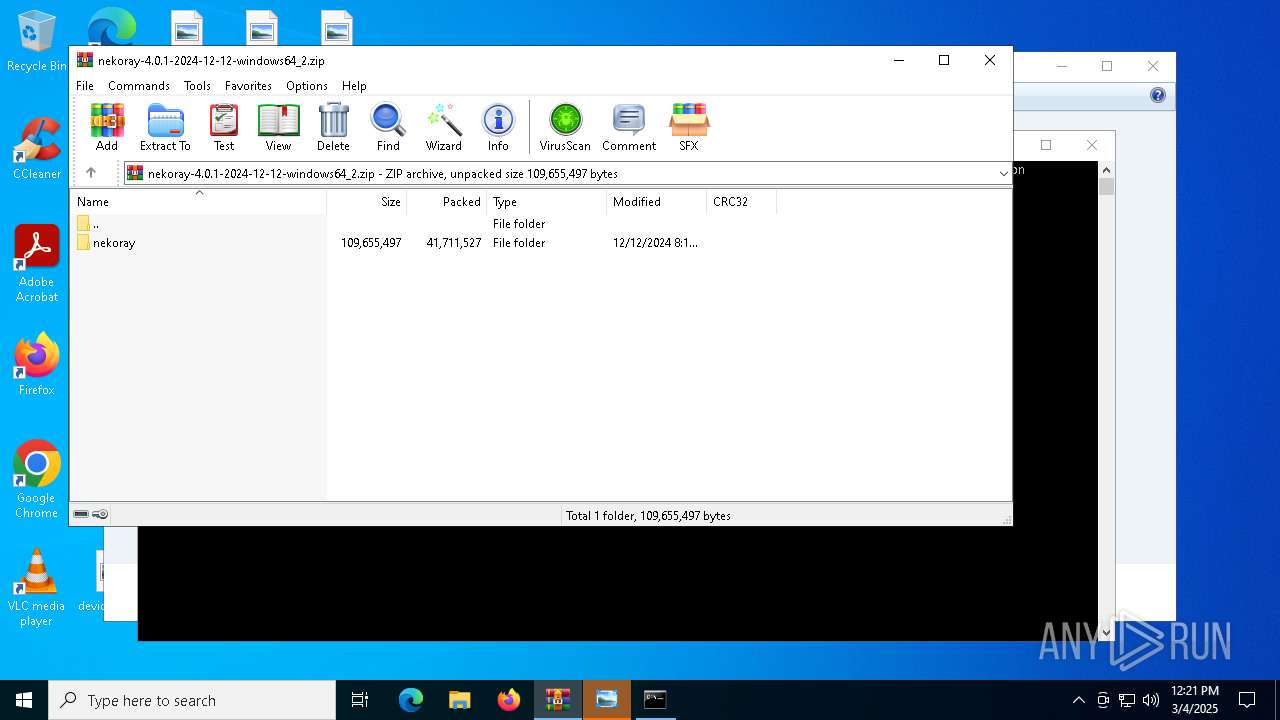
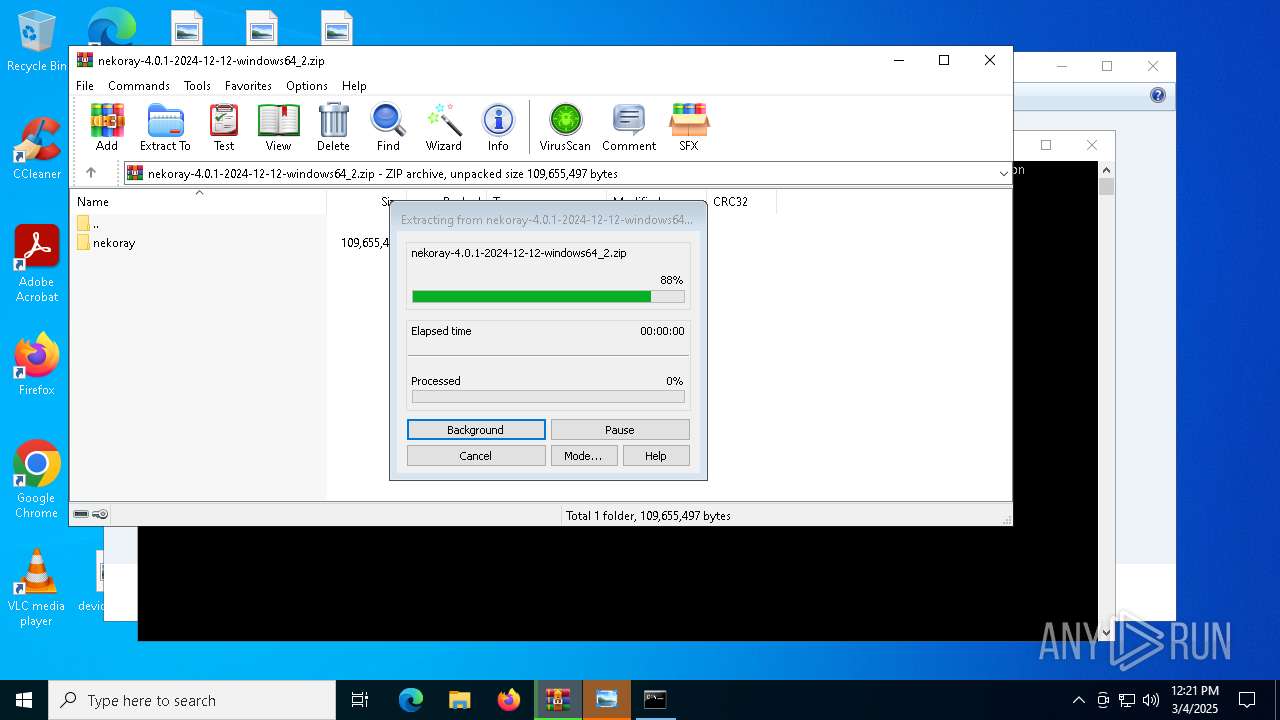
| File name: | nekoray-4.0.1-2024-12-12-windows64_2.zip |
| Full analysis: | https://app.any.run/tasks/9bd0691a-27e3-4dd2-ab42-2f97c512907d |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2025, 12:19:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | F57DADFAE7A4A0118119D3E9B152702A |
| SHA1: | F02D868A7209EB6AF67A99945C07A95C18C8A91E |
| SHA256: | A492224792C38BD1A3B7A5438B1431C5CB4260F55E9A121DB3B2CE1603F7664A |
| SSDEEP: | 393216:qzhaIieeypH1e1IvgbZSHjgTLc0JR+PaqHGJ2:H6pY1IQQDgs0JR+Pfy2 |
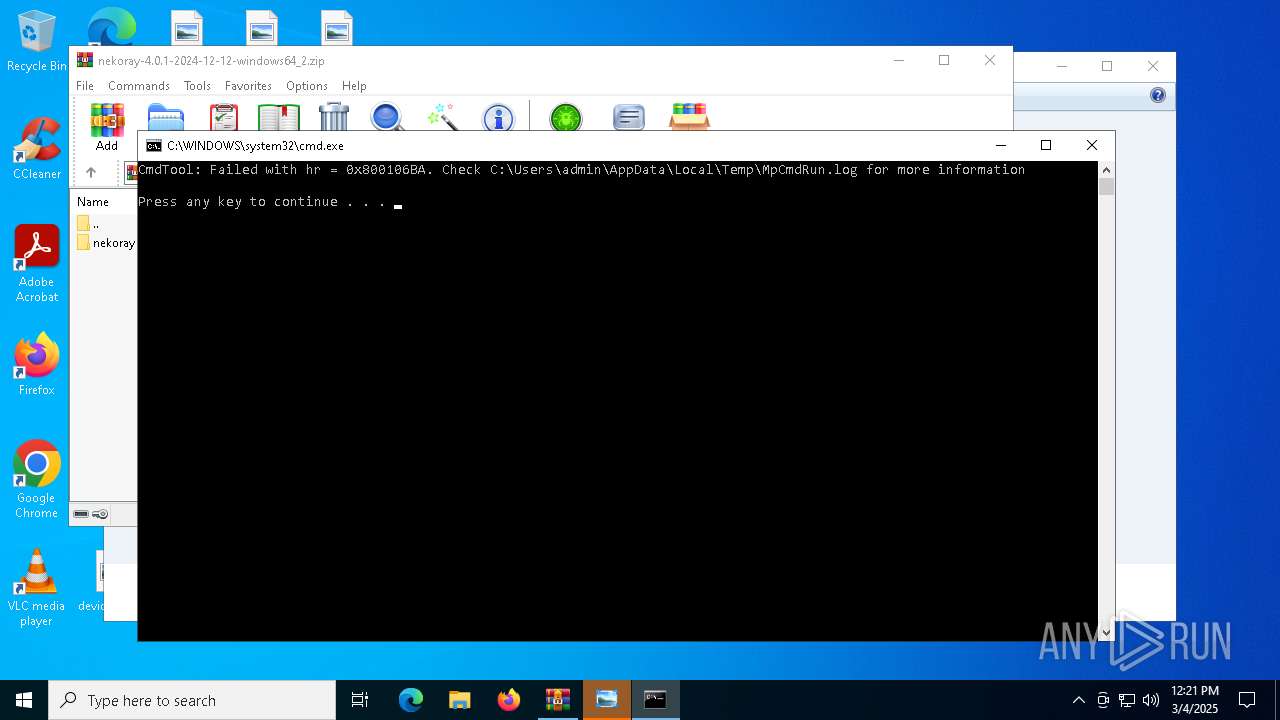
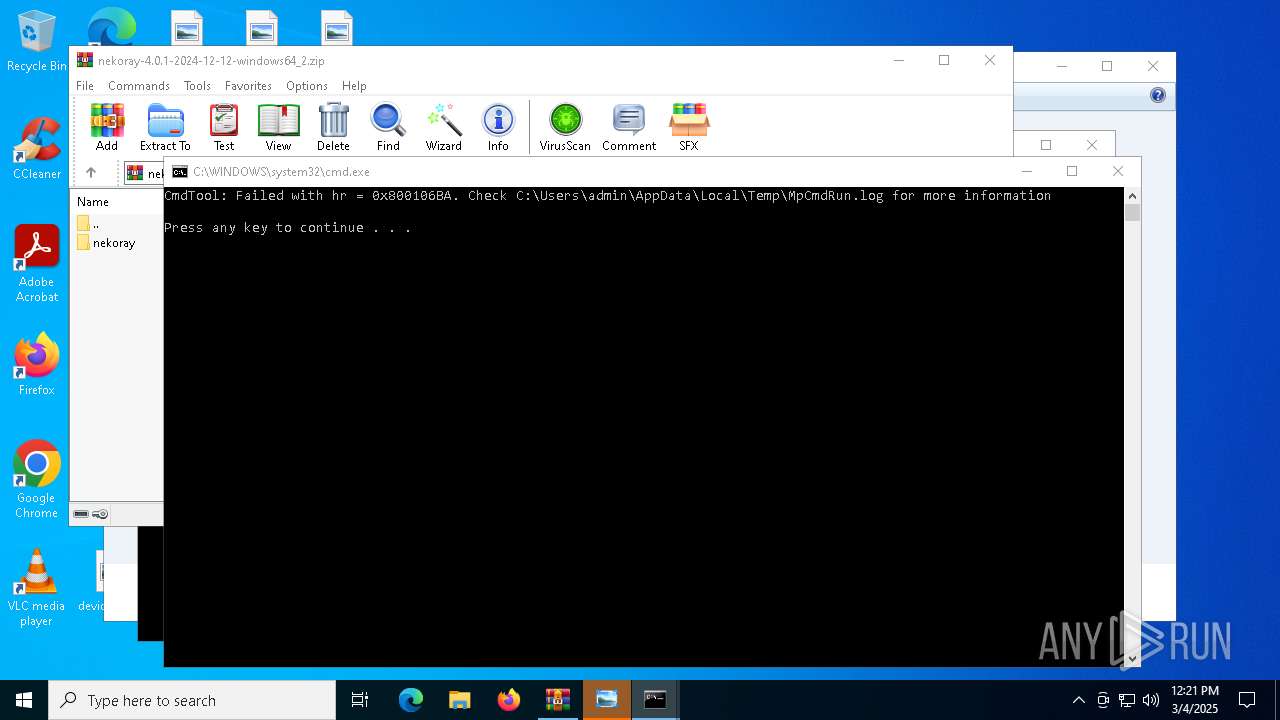
MALICIOUS
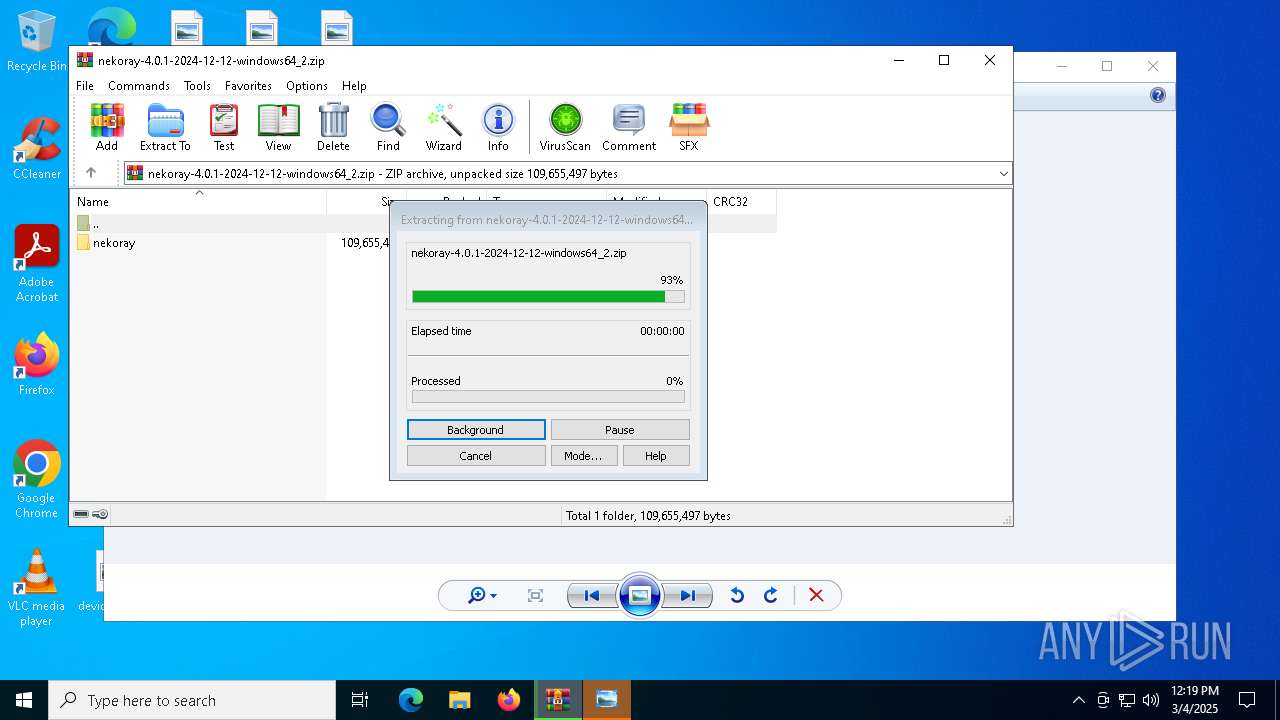
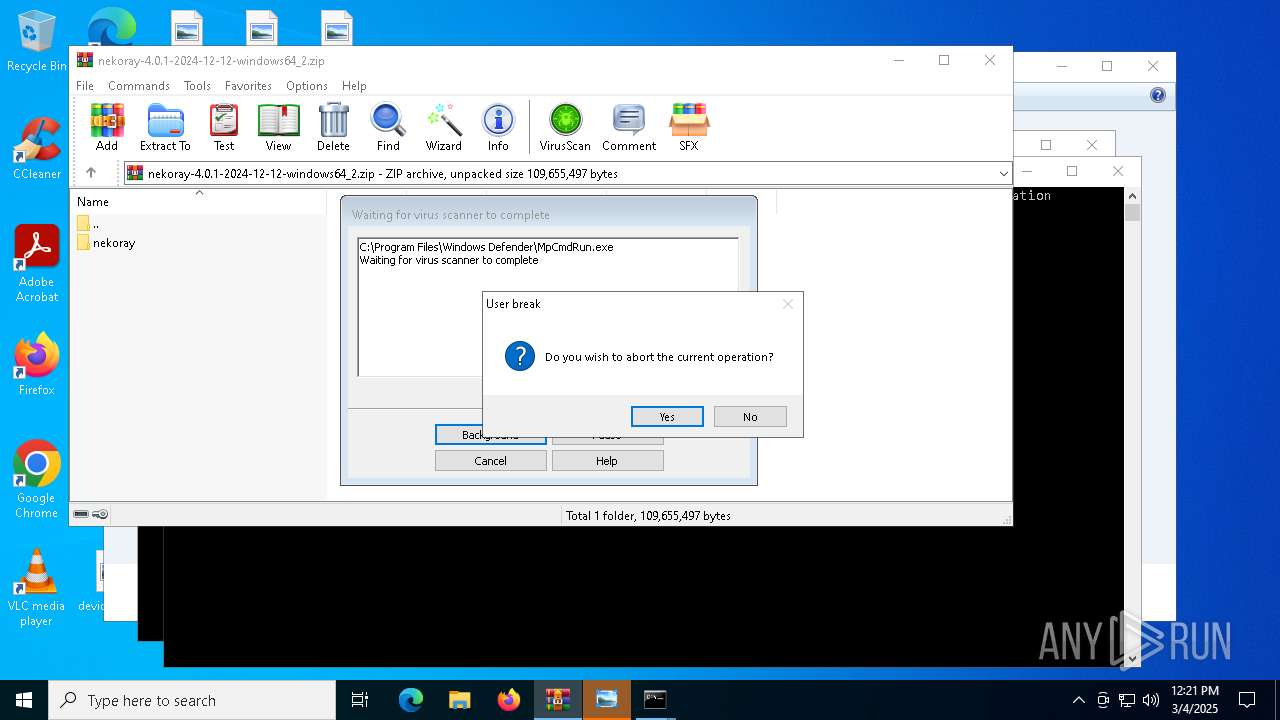
Generic archive extractor
- WinRAR.exe (PID: 7544)
SUSPICIOUS
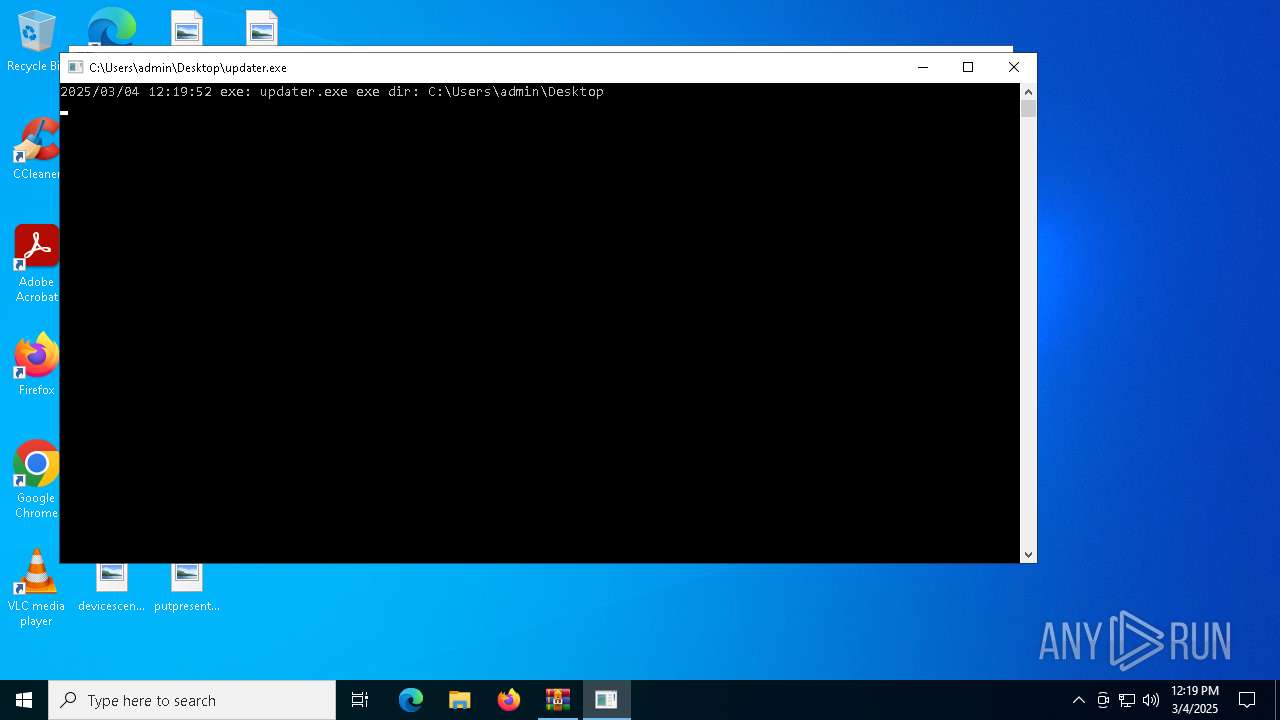
Starts itself from another location
- updater.exe (PID: 7700)
Executing commands from a ".bat" file
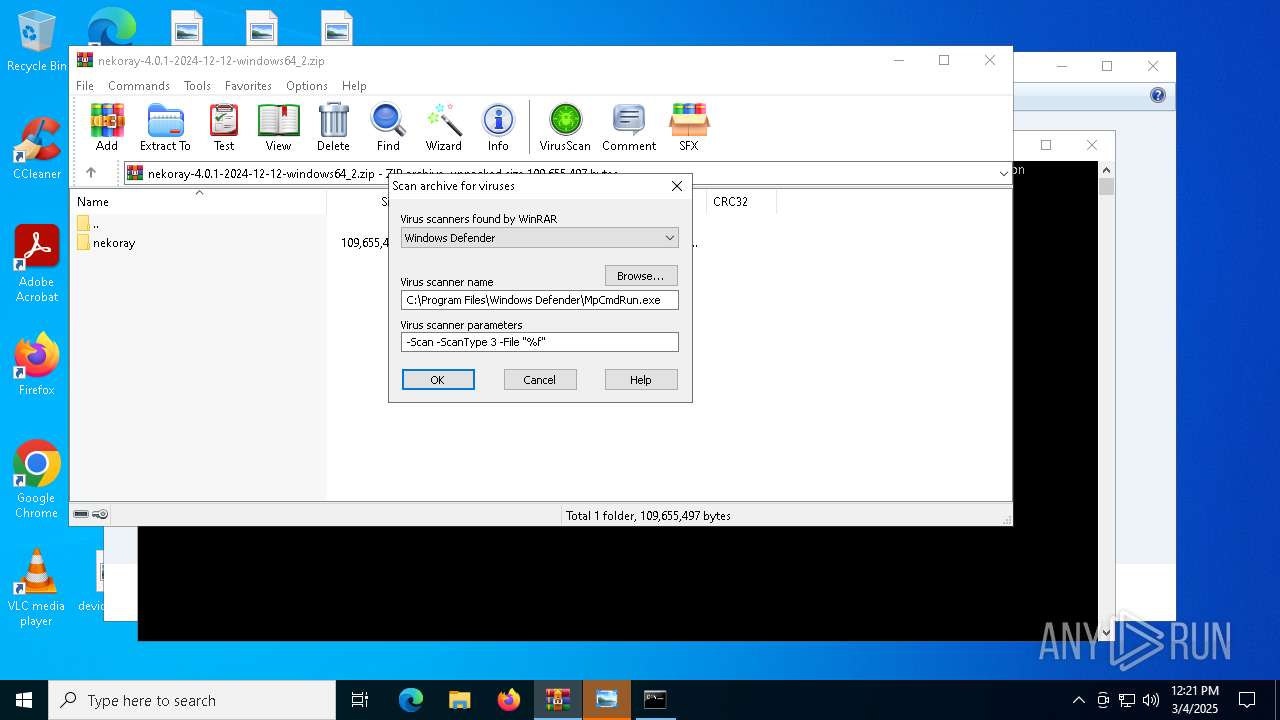
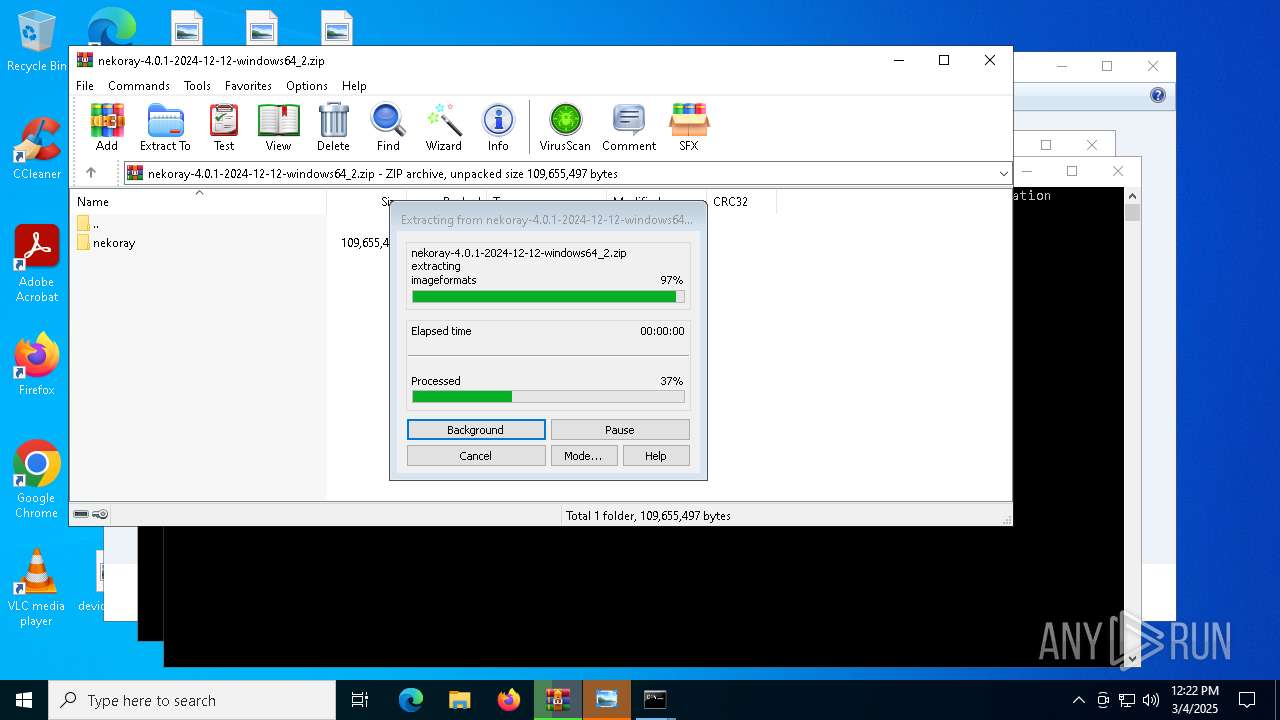
- WinRAR.exe (PID: 7544)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7544)
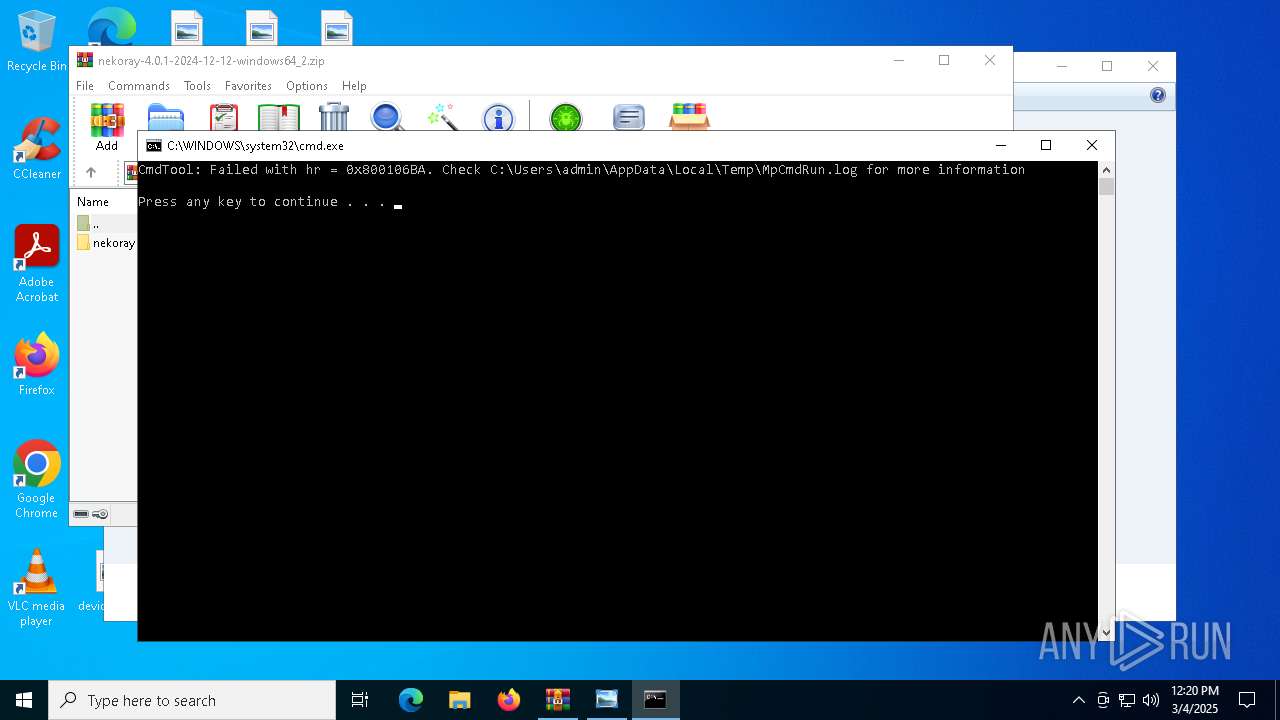
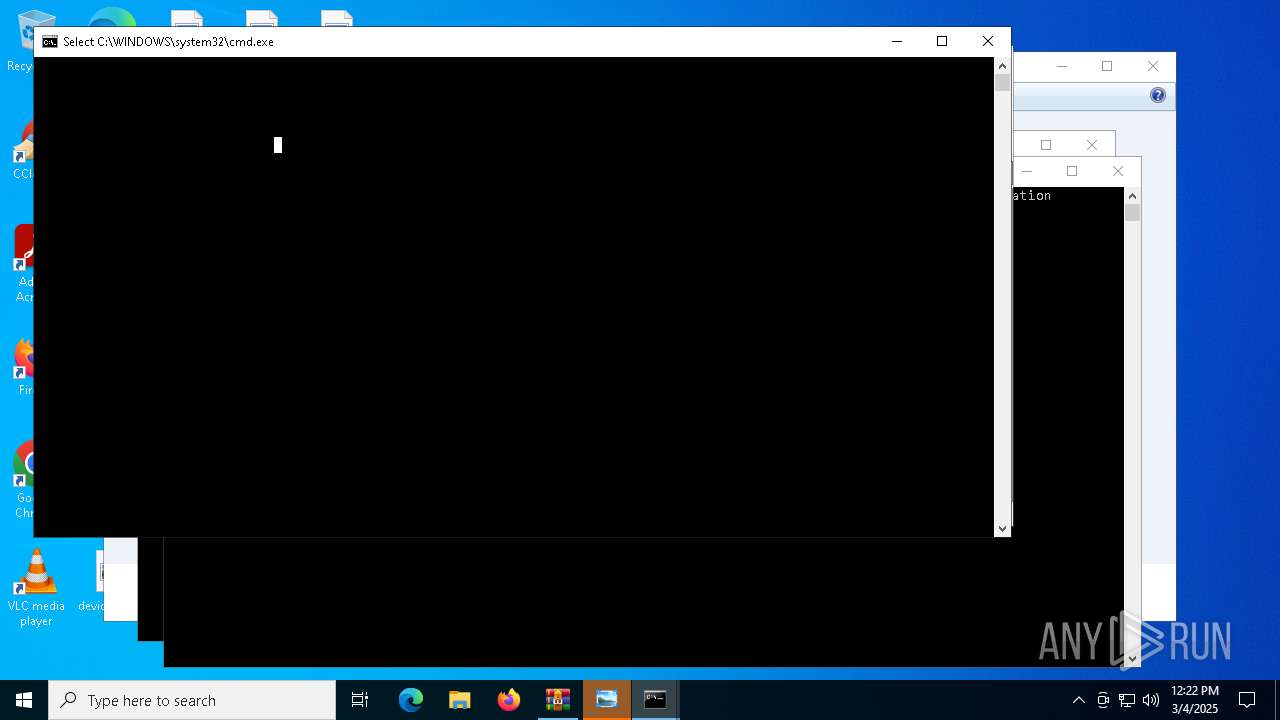
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7544)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7544)
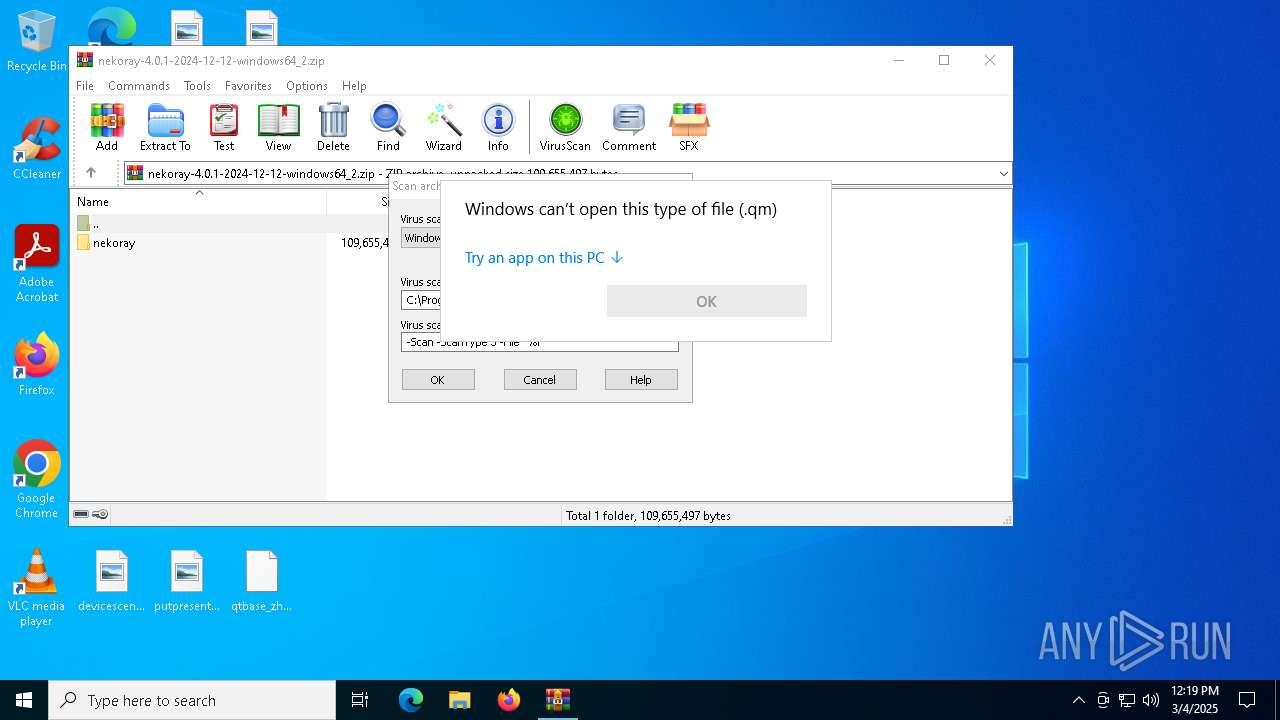
Starts application with an unusual extension
- updater.exe (PID: 7700)
Executable content was dropped or overwritten
- updater.exe (PID: 7700)
INFO
Checks supported languages
- updater.exe (PID: 7700)
- updater.old (PID: 7780)
- MpCmdRun.exe (PID: 8116)
- MpCmdRun.exe (PID: 5512)
- MpCmdRun.exe (PID: 6744)
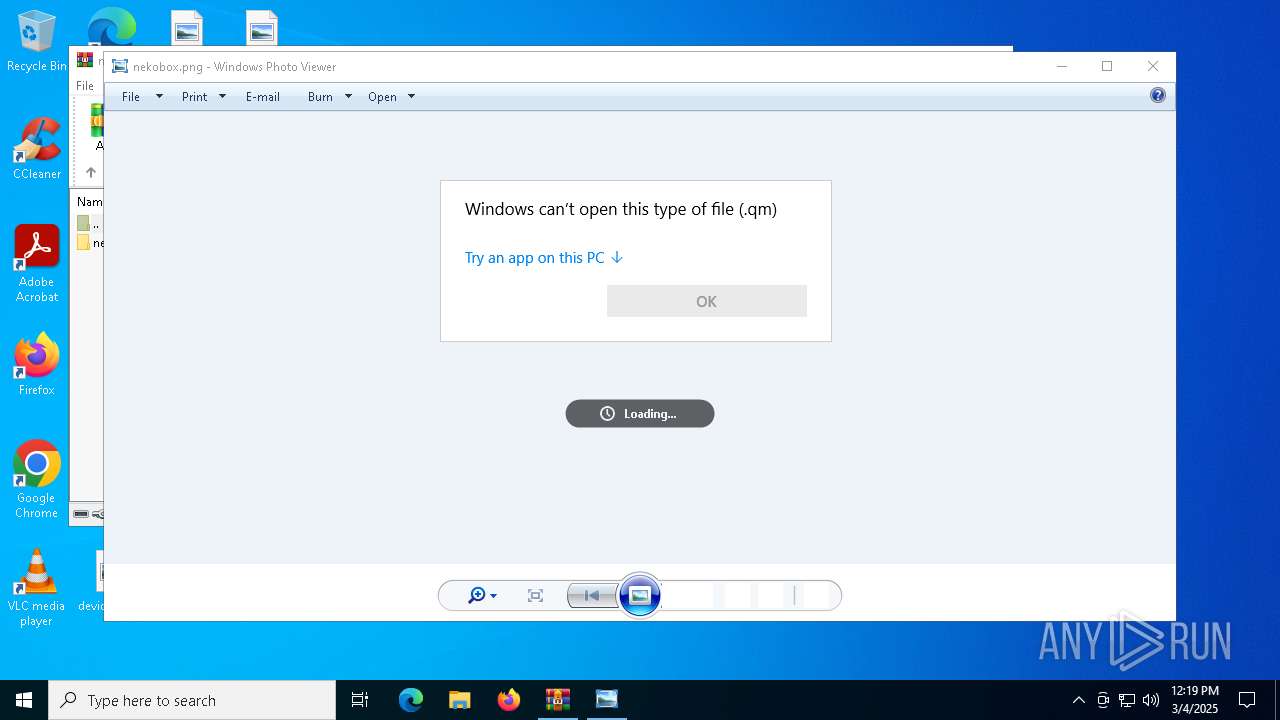
Manual execution by a user
- updater.exe (PID: 7700)
- OpenWith.exe (PID: 7840)
- rundll32.exe (PID: 7924)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7840)
The sample compiled with english language support
- WinRAR.exe (PID: 7544)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7544)
Reads the computer name
- MpCmdRun.exe (PID: 8116)
- MpCmdRun.exe (PID: 6744)
- MpCmdRun.exe (PID: 5512)
Checks proxy server information
- slui.exe (PID: 7208)
Create files in a temporary directory
- MpCmdRun.exe (PID: 8116)
Reads the software policy settings
- slui.exe (PID: 7208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
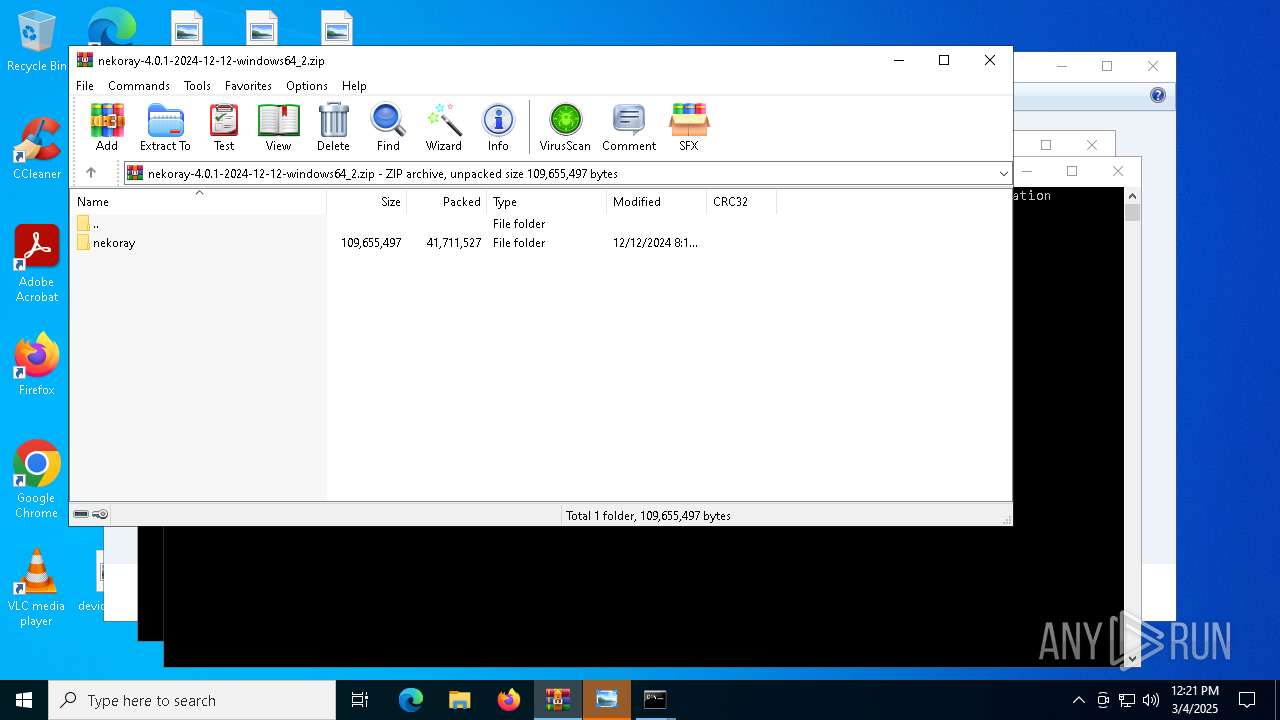
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:12:12 08:17:38 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | nekoray/ |
Total processes
132
Monitored processes
16
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7544.22008\Rar$Scan125300.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5204 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7544.23364\Rar$Scan140324.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
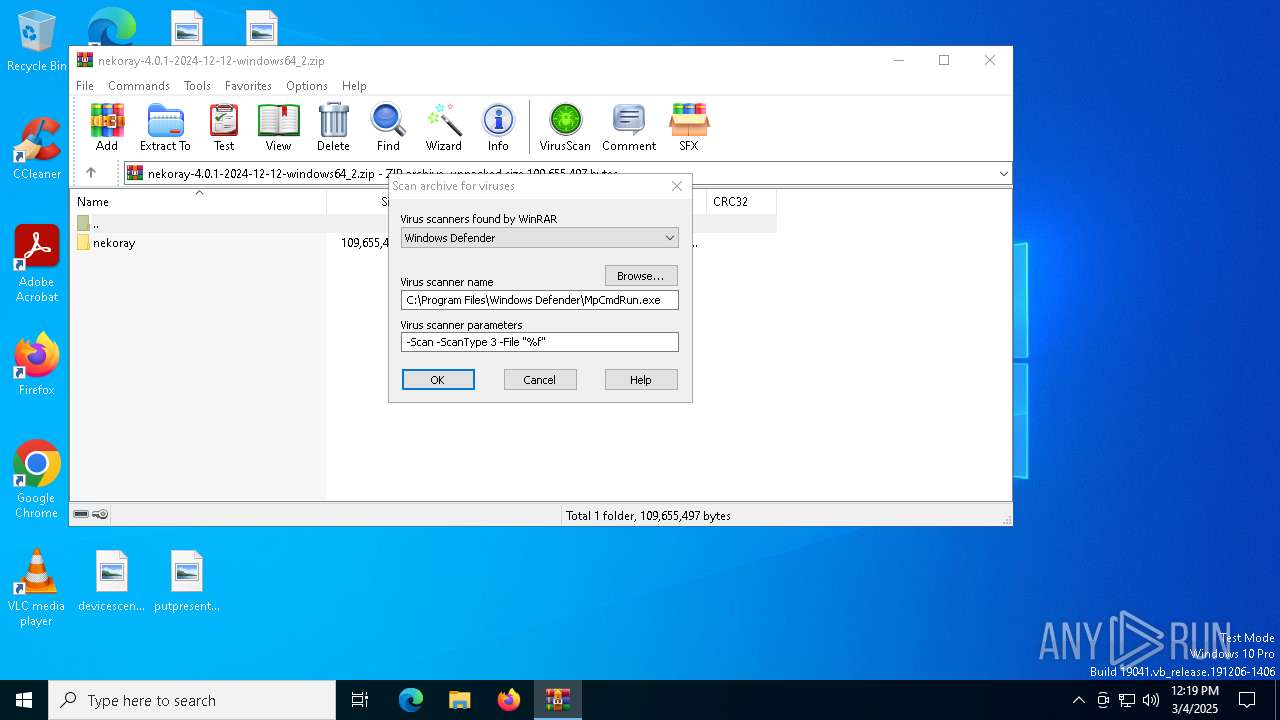
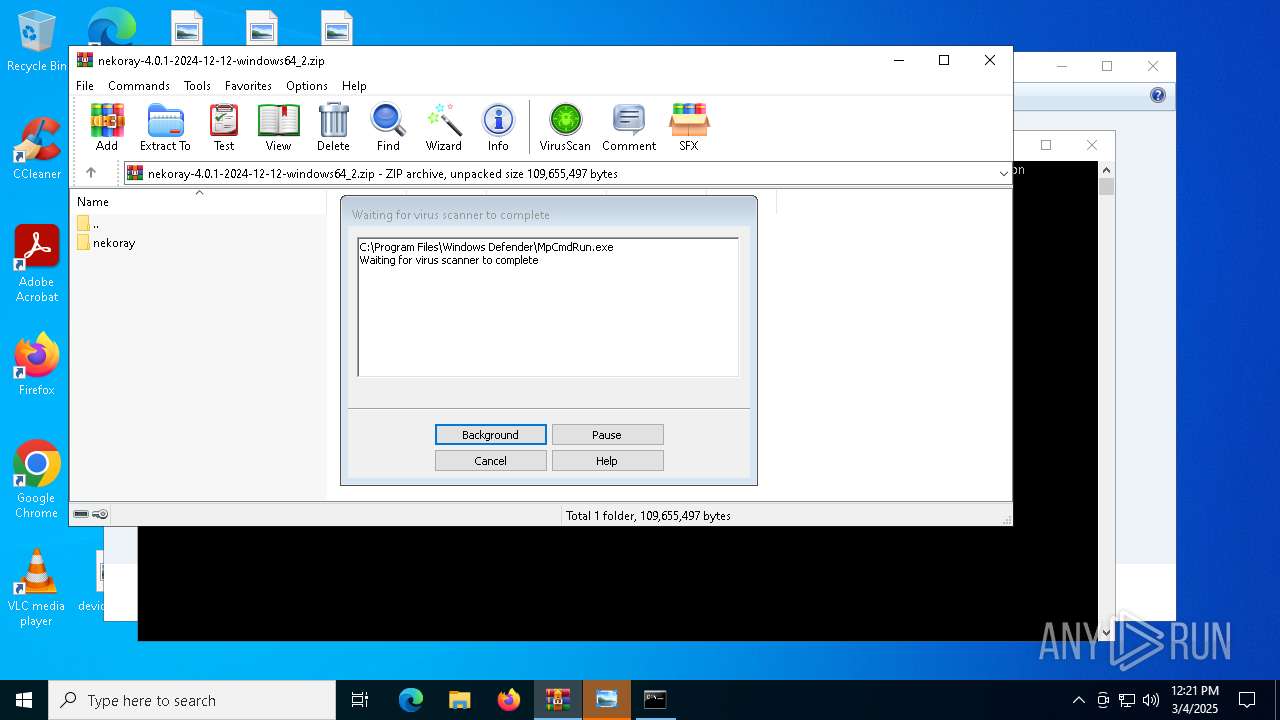
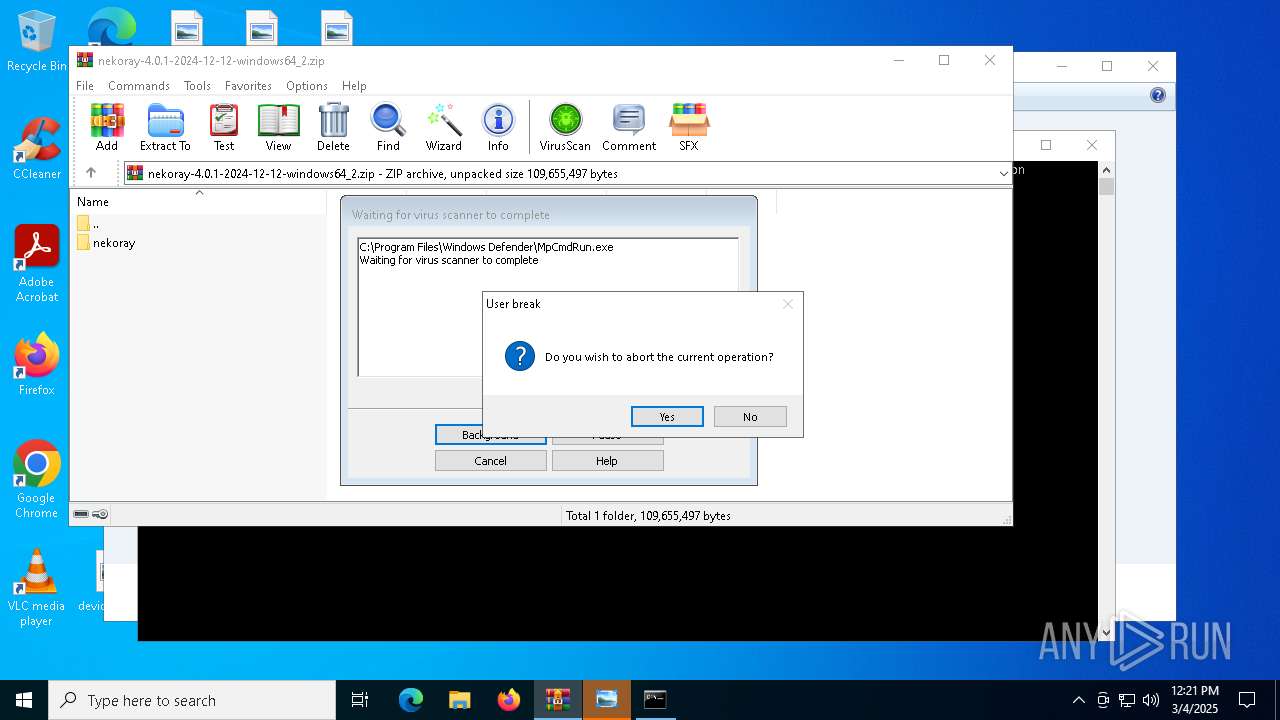
| 5512 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7544.23364" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6744 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7544.22008" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7208 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7544 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\nekoray-4.0.1-2024-12-12-windows64_2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7700 | "C:\Users\admin\Desktop\updater.exe" | C:\Users\admin\Desktop\updater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7708 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | updater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 428
Read events
8 417
Write events
11
Delete events
0
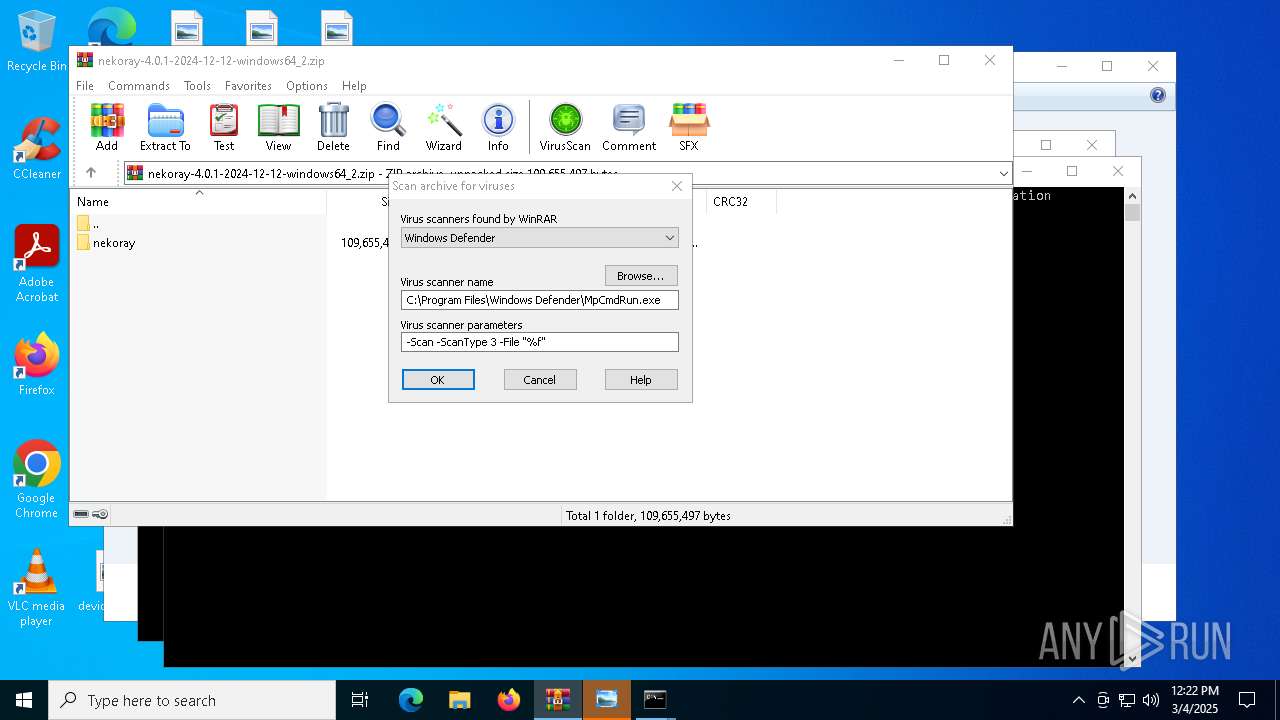
Modification events
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\nekoray-4.0.1-2024-12-12-windows64_2.zip | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
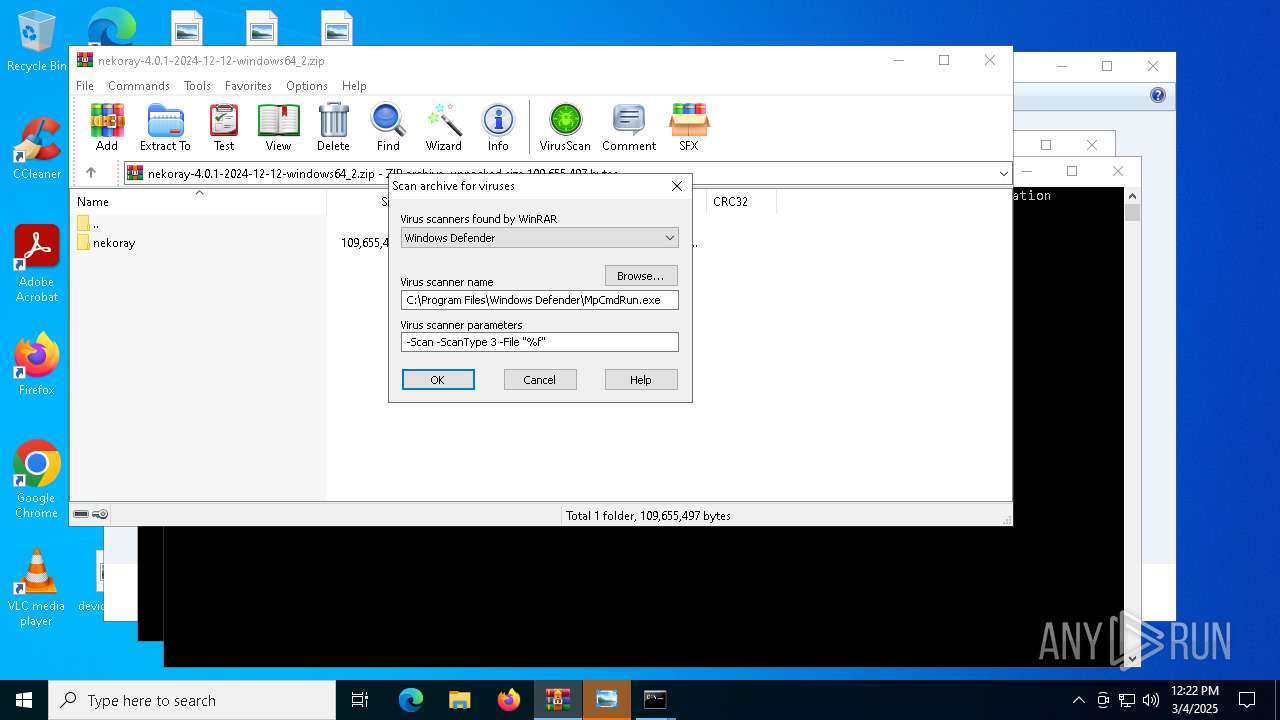
| (PID) Process: | (7544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
88
Suspicious files
13
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\geoip.dat | — | |
MD5:— | SHA256:— | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qwebp.dll | executable | |
MD5:CD33C23CB759AE9616FDF9EF5E65A381 | SHA256:5AF0237B83441ED3890A7E5E08A1925F47686B9F37F736F0FD10D9B859771A98 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\nekobox_core.exe | executable | |
MD5:157729C1176B28381CB2789CEB1E7209 | SHA256:B365388EE5F53EDD453A7A461E3F58E05C63EEBCC39C681070F05F2EACFD4C6D | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qwbmp.dll | executable | |
MD5:7BDE42A8B281B90B7BBC003A39BC398A | SHA256:B46A7AA7F3B5B8F9C7E3B2EB92060FC35C8446EA2F374D8FB74F872795FB0AF9 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qtga.dll | executable | |
MD5:5D9E2FF0FFD403BCB87350F3FBF43D04 | SHA256:881EF0545BE4C65109F5EA4BF34AD8D29EDE84905612C8A15E749565AFC810E1 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qgif.dll | executable | |
MD5:A25420B66E14B2E78089AA81128B9BE1 | SHA256:E147641921F15A8828C7A00EDC5AEF90D484407C5939CF39C07BA9F021CE4395 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qicns.dll | executable | |
MD5:761C10400FF3E9754FCE6E60B54F457D | SHA256:D9B97C5CC9016070CA1154947B844C351CD467ACEE88884B7455BB1391124882 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\updater.exe | executable | |
MD5:5D69070DA3EB2377374EA98F0353D710 | SHA256:D8CC758042FCDC989E8D678A79CD0A02CFF954902DA921EF797E23D040253048 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qsvg.dll | executable | |
MD5:EB36378AF3ED4007BD838B7FC50AA629 | SHA256:139212BD14F8295A33A2E3ABB02AEF23F3E1CD7691619A78C52721E22CCEC536 | |||
| 7544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7544.10672\nekoray-4.0.1-2024-12-12-windows64_2.zip\nekoray\imageformats\qico.dll | executable | |
MD5:85909D24C02E0183845ADEE807A86B2A | SHA256:2BA002A2C3AB1E0F06DB53D0B76306E2FD2730AAC99F881914A0E310A5BB51A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7348 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7208 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |