| File name: | Lykaiz.exe |
| Full analysis: | https://app.any.run/tasks/19ff373a-3614-4f3f-95d0-e8f546b99e8e |
| Verdict: | Suspicious activity |
| Analysis date: | October 13, 2018, 15:48:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | 981730B3DDB0B17D95FC8833A7F1B465 |
| SHA1: | 8319AB427BE7FBC8BA3CFBCAE005B80D054623DB |
| SHA256: | A4810E49BF6F977AA755C4D64E494D509480C04B3A3E9282F3950125B099FF69 |
| SSDEEP: | 12288:fLoSy90OzZqoF+K+w6dGYDHQUeiqBk/NVjXIH4HEu1fqhBLEFY9ddNdCYaoXbFzP:3yEoF+KkdzDHWioOrIDCMLFwYaordu3 |
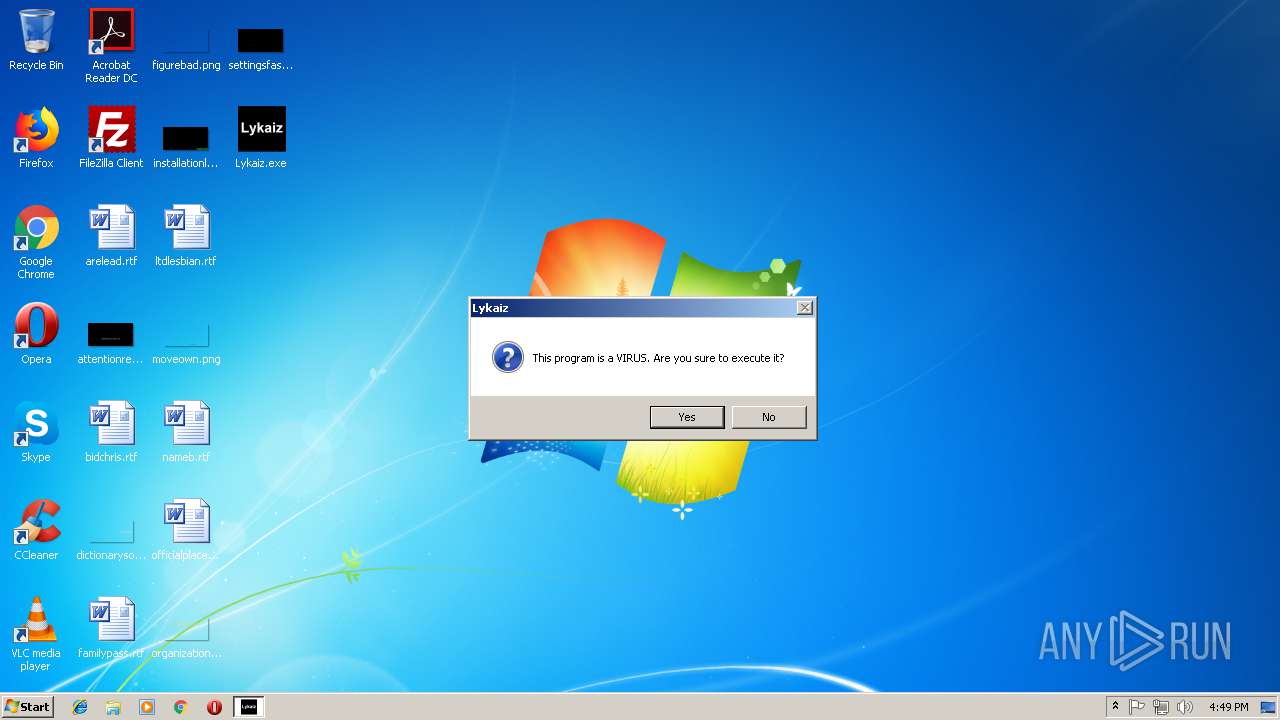
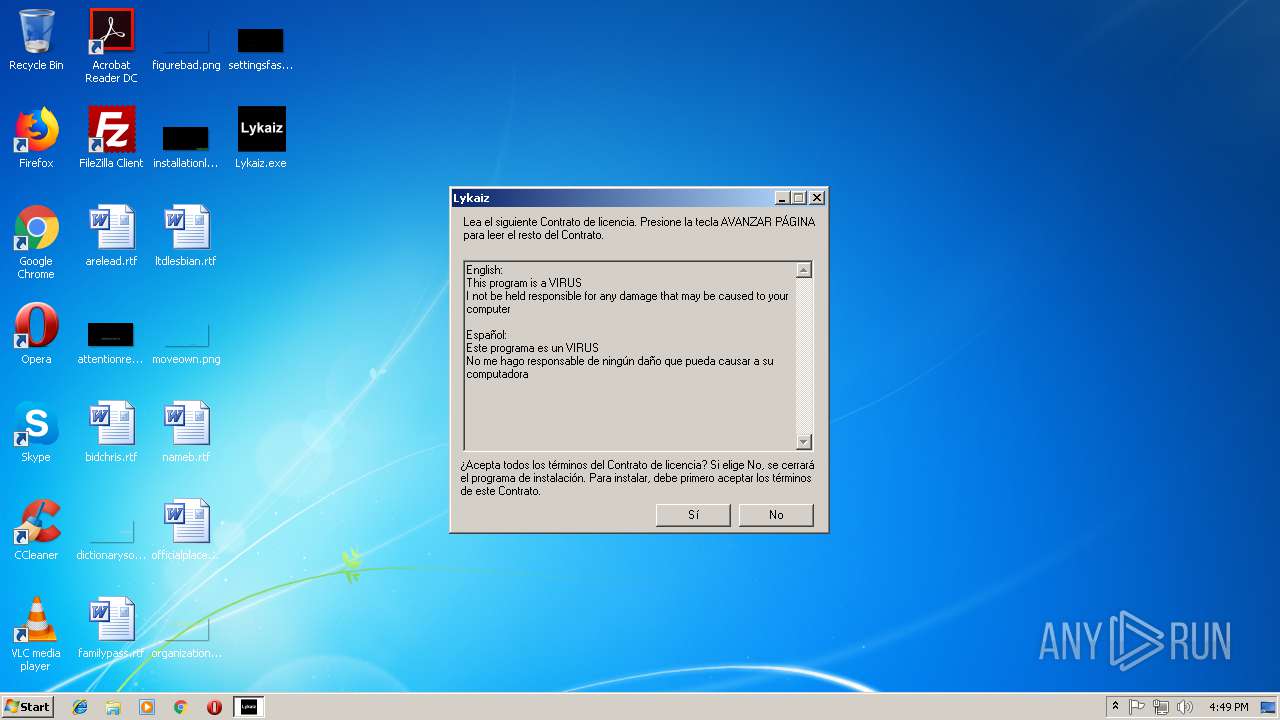
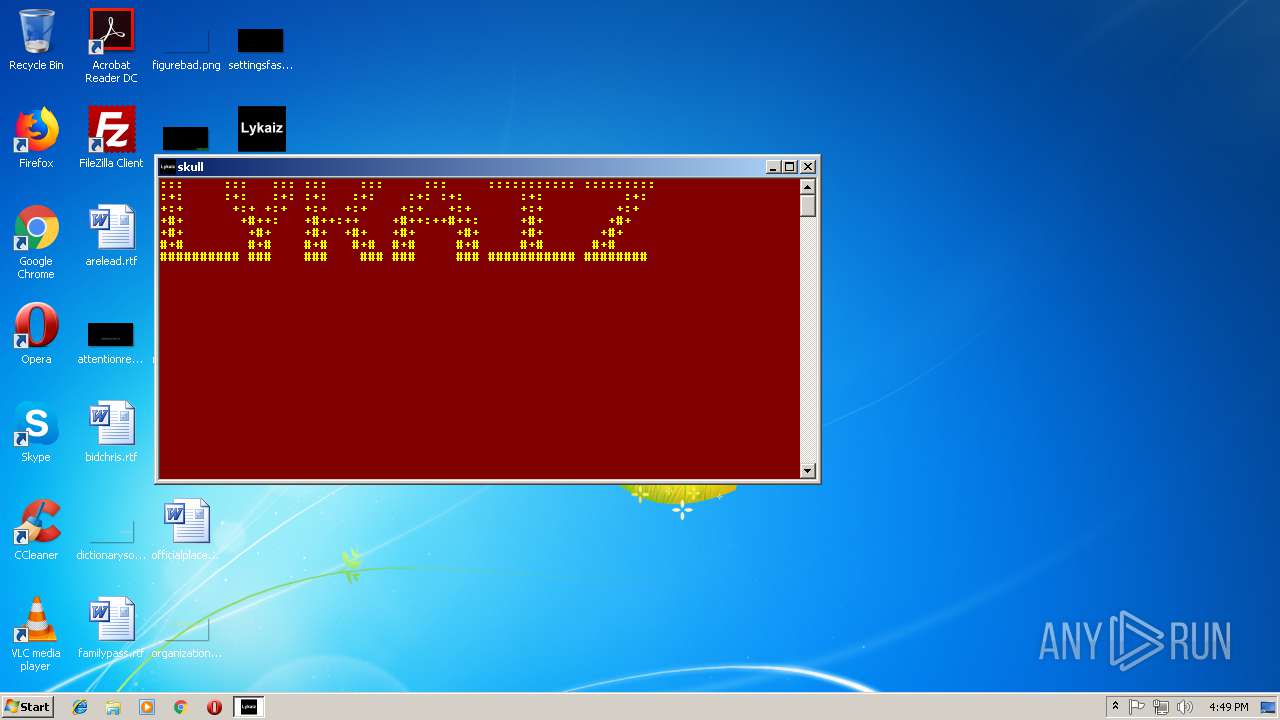
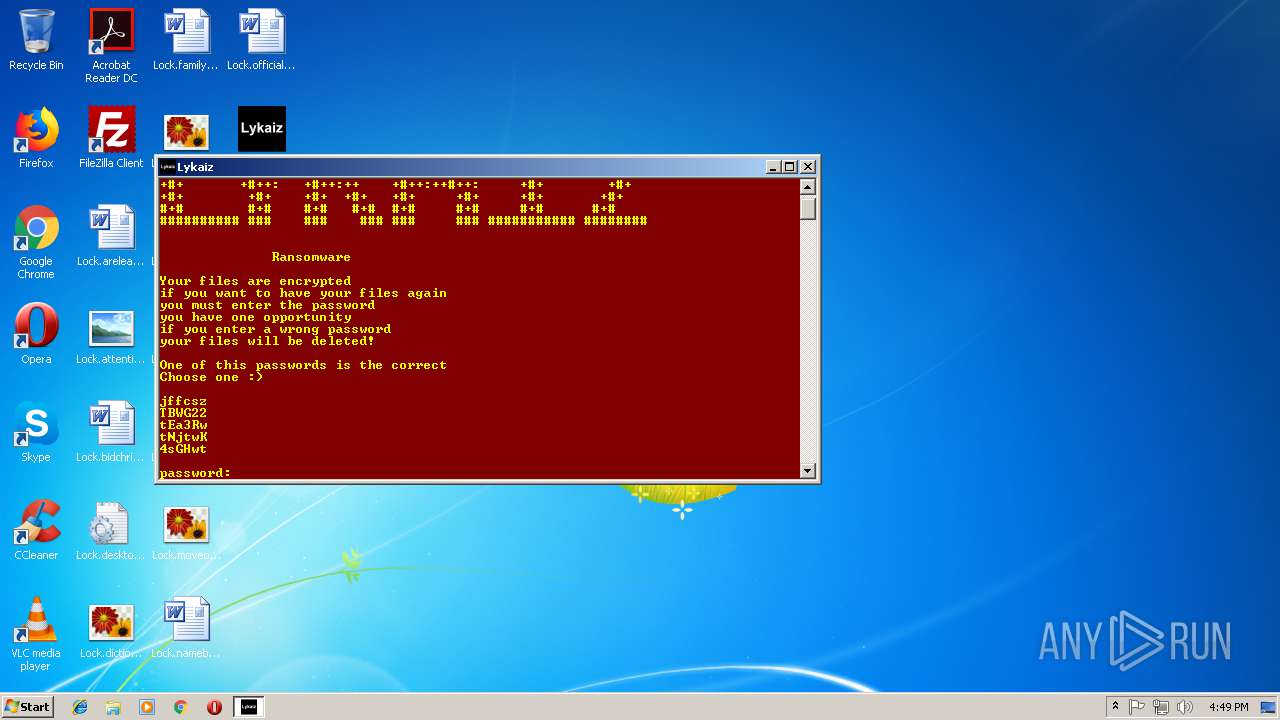
MALICIOUS
Application was dropped or rewritten from another process
- Lykaiz.exe (PID: 1972)
- ca.exe (PID: 3968)
Loads dropped or rewritten executable
- migwiz.exe (PID: 3340)
UAC/LUA settings modification
- reg.exe (PID: 1908)
Writes to a start menu file
- ca.exe (PID: 3968)
SUSPICIOUS
Executable content was dropped or overwritten
- Lykaiz.exe (PID: 1968)
- wusa.exe (PID: 1552)
- ca.exe (PID: 3968)
Executes scripts
- cmd.exe (PID: 3516)
- ca.exe (PID: 3968)
Creates files in the user directory
- WScript.exe (PID: 1180)
- ca.exe (PID: 3968)
Starts CMD.EXE for commands execution
- ca.exe (PID: 3968)
- Lykaiz.exe (PID: 1972)
- migwiz.exe (PID: 3340)
Creates files in the Windows directory
- wusa.exe (PID: 1552)
Removes files from Windows directory
- wusa.exe (PID: 1552)
Writes to a desktop.ini file (may be used to cloak folders)
- ca.exe (PID: 3968)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3112)
Changes the desktop background image
- ca.exe (PID: 3968)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:07:14 01:42:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 44032 |
| InitializedDataSize: | 774144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6af8 |
| OSVersion: | 6.1 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.7600.16385 |
| ProductVersionNumber: | 8.0.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jul-2009 23:42:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Archivo autoextractor de archivos CAB de Win32 |
| FileVersion: | 8.00.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. Reservados todos los derechos. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Windows® Internet Explorer |
| ProductVersion: | 8.00.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Jul-2009 23:42:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000AAE4 | 0x0000AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54415 |
.data | 0x0000C000 | 0x0000225C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.59775 |
.rsrc | 0x0000F000 | 0x000BBB74 | 0x000BBC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.44408 |
.reloc | 0x000CB000 | 0x00000D98 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.8066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.84816 | 1260 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
55
Monitored processes
15
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Windows\System32\migwiz\migwiz.exe" C:\Windows\System32\cmd.exe /c C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\migwiz\migwiz.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Easy Transfer Application Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\speak.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 3221225547 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1552 | "C:\Windows\system32\wusa.exe" C:\Users\admin\AppData\Local\Temp\32.cab /quiet /extract:C:\Windows\system32\migwiz\ | C:\Windows\system32\wusa.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | "C:\Users\admin\Desktop\Lykaiz.exe" | C:\Users\admin\Desktop\Lykaiz.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Lykaiz.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Lykaiz.exe | — | Lykaiz.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2436 | wusa C:\Users\admin\AppData\Local\Temp\32.cab /quiet /extract:C:\Windows\system32\migwiz\ | C:\Windows\system32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\888.vbs" | C:\Windows\System32\WScript.exe | — | ca.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3112 | C:\Windows\System32\cmd.exe /c C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\cmd.exe | — | migwiz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 281
Read events
952
Write events
329
Delete events
0
Modification events
| (PID) Process: | (3516) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3516) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1180) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | CLSID |
Value: {C9E37C15-DF92-4727-85D6-72E5EEB6995A} | |||
| (PID) Process: | (1180) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | |
Value: Current User Lexicon | |||
| (PID) Process: | (1180) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}\Files |
| Operation: | write | Name: | Datafile |
Value: %1a%\Microsoft\Speech\Files\UserLexicons\SP_5BBFF5F9D4EC4986A8AEE6284C0CBE49.dat | |||
| (PID) Process: | (1180) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | Generation |
Value: 0 | |||
| (PID) Process: | (1180) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\PhoneConverters |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech\PhoneConverters\Tokens\English | |||
| (PID) Process: | (3436) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3436) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1180) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | |
Value: Speakers (Realtek AC'97 Audio) | |||
Executable files
5
Suspicious files
34
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | ca.exe | C:\Users\admin\AppData\Local\Temp\aut3345.tmp | — | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\AppData\Local\Temp\xbcwvgi | — | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\AppData\Local\Temp\aut3356.tmp | — | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\AppData\Local\Temp\aut3366.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | wusa.exe | C:\Windows\system32\migwiz\$dpx$.tmp\7fd6a93a44294f41ba69810155de081c.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | wusa.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\Desktop\Lock.attentionreceive.jpg | binary | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\Desktop\Lock.arelead.rtf | binary | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\Desktop\Lock.bidchris.rtf | binary | |
MD5:— | SHA256:— | |||
| 3968 | ca.exe | C:\Users\admin\Desktop\Lock.dictionarysoon.png | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report