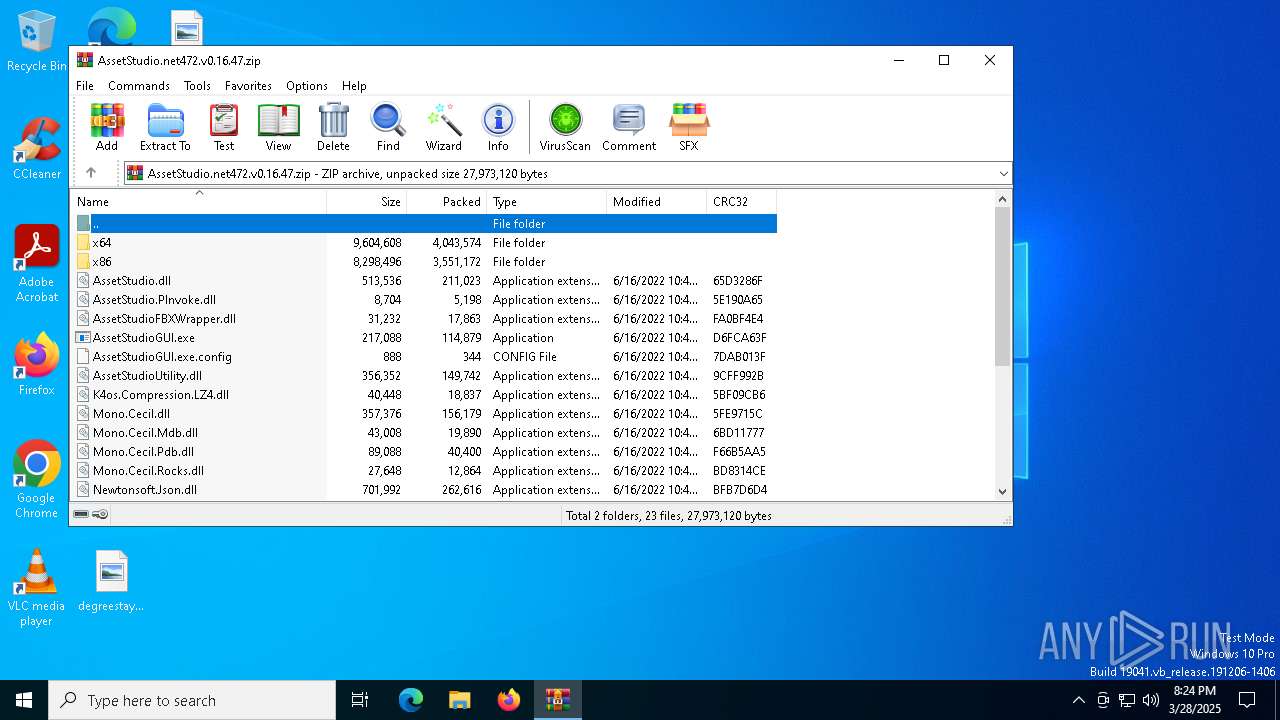
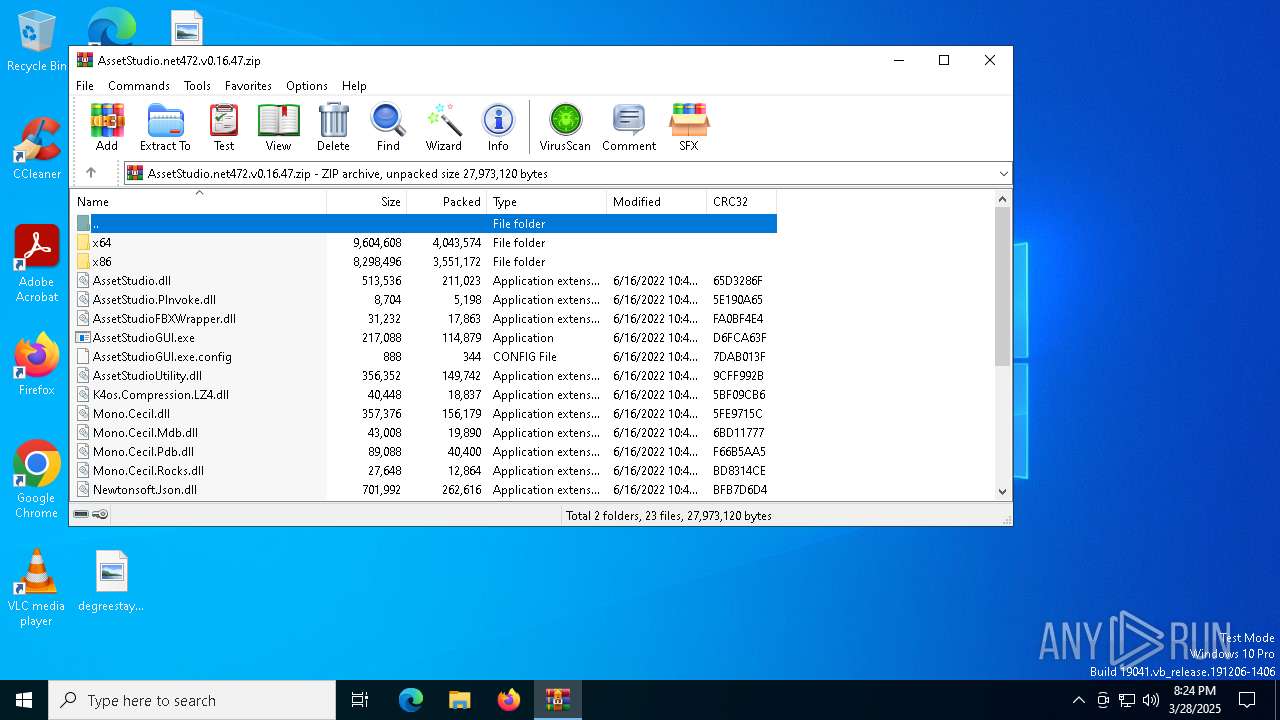
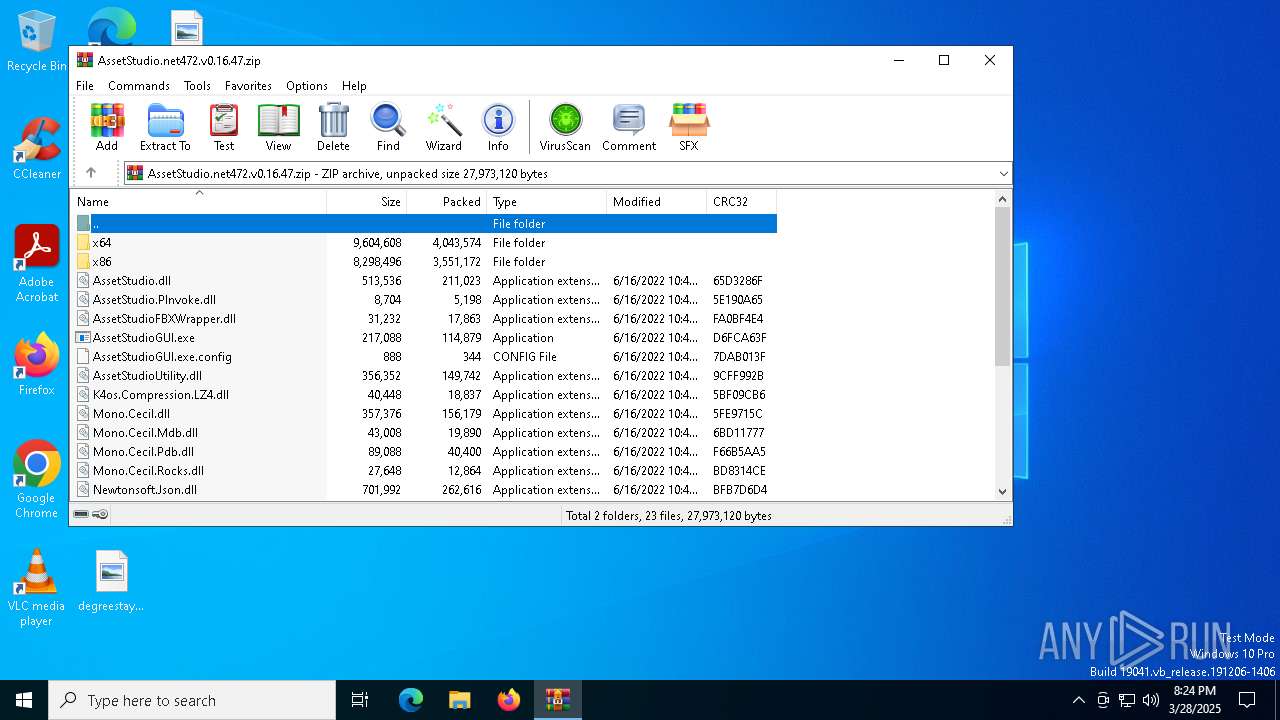
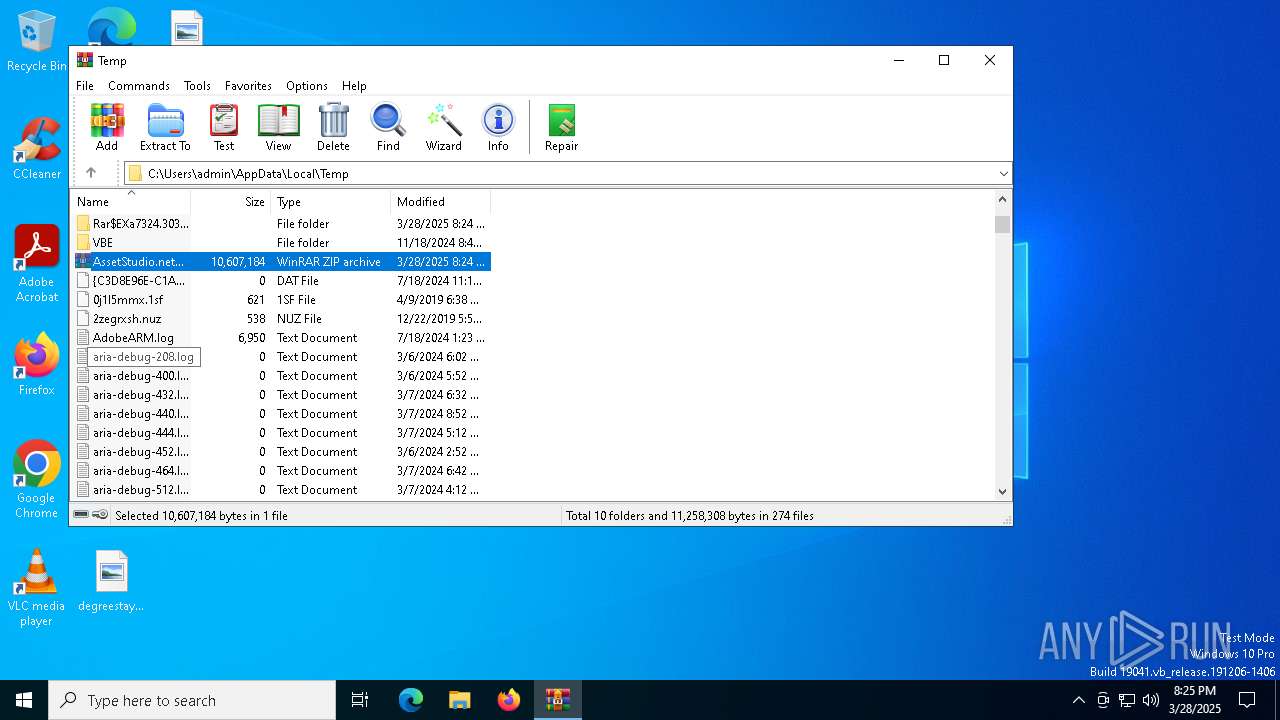
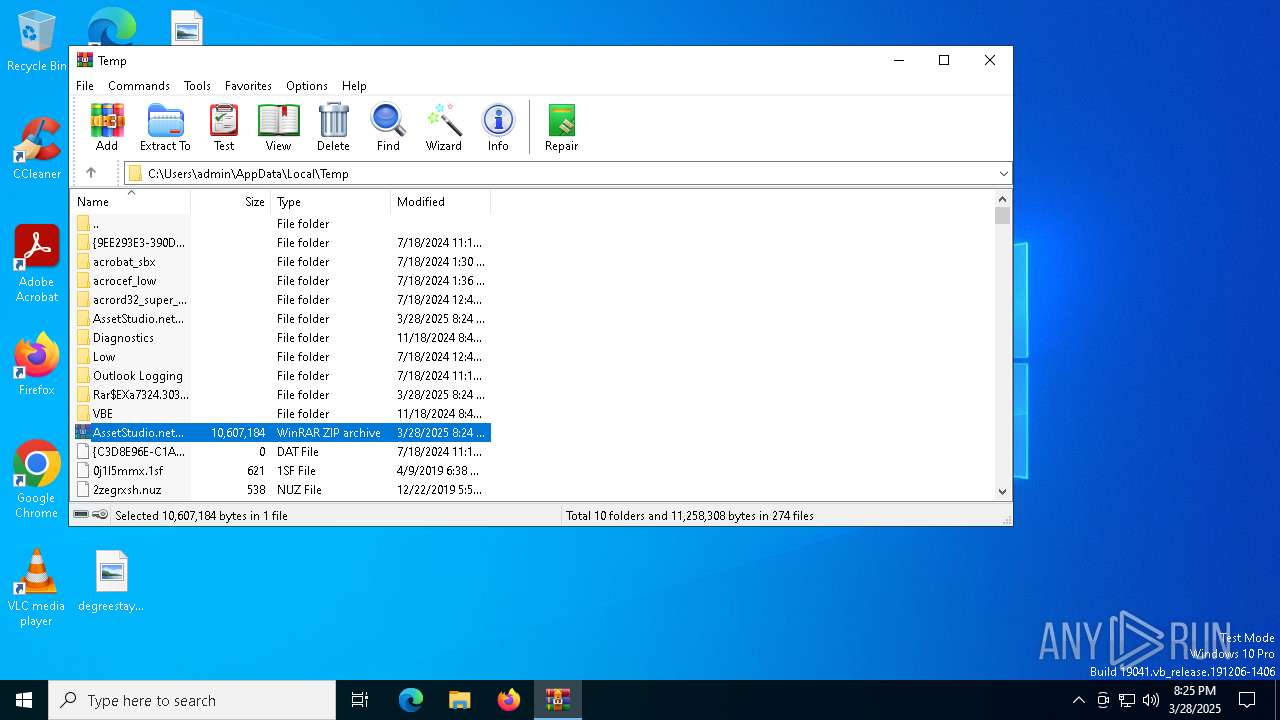
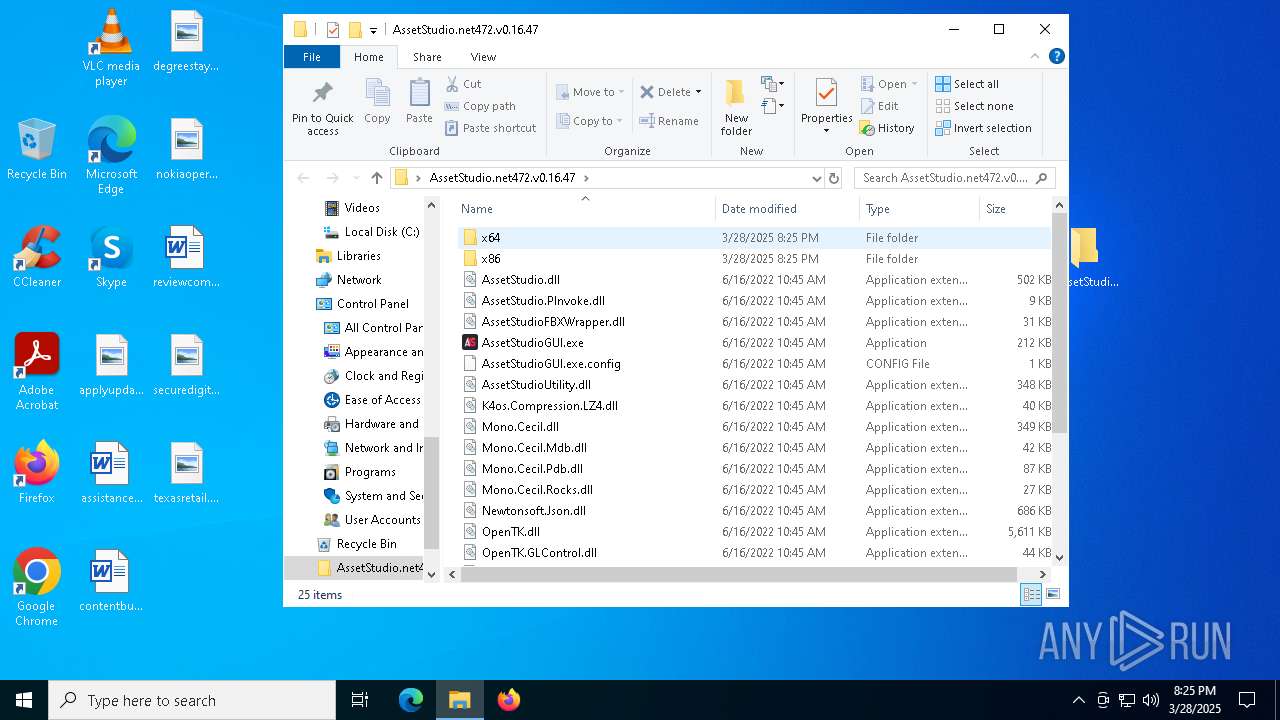
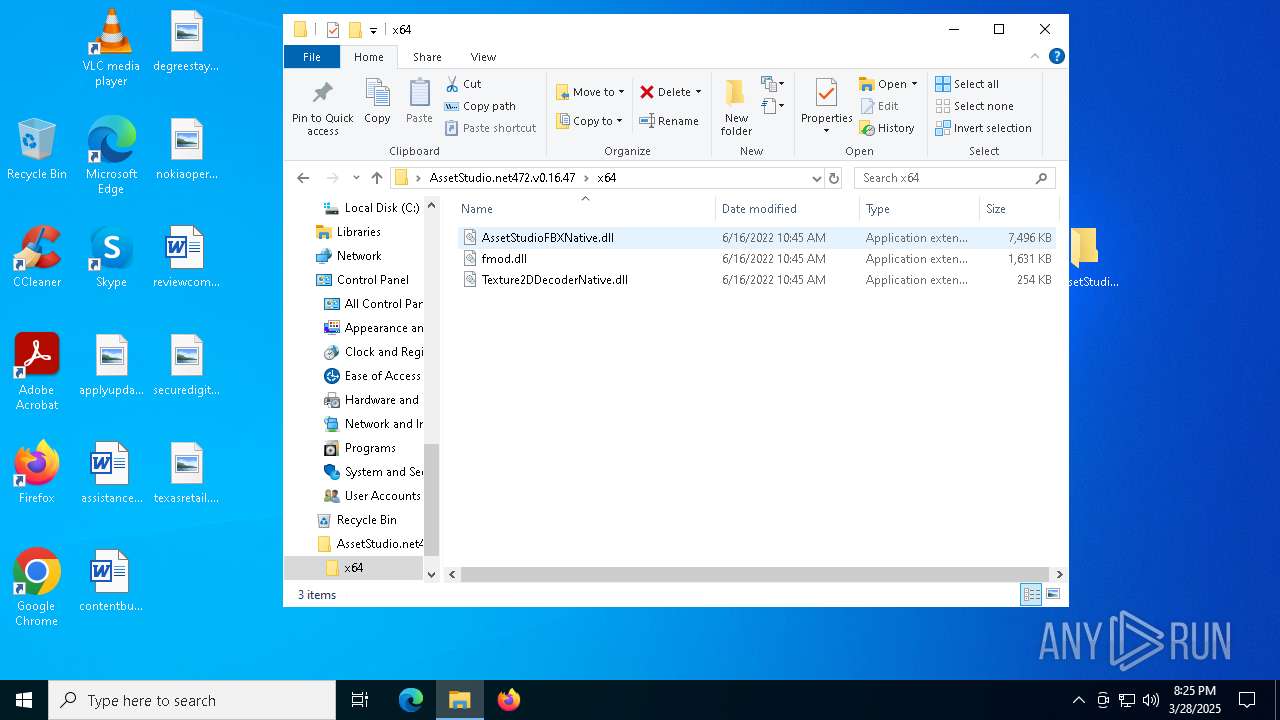
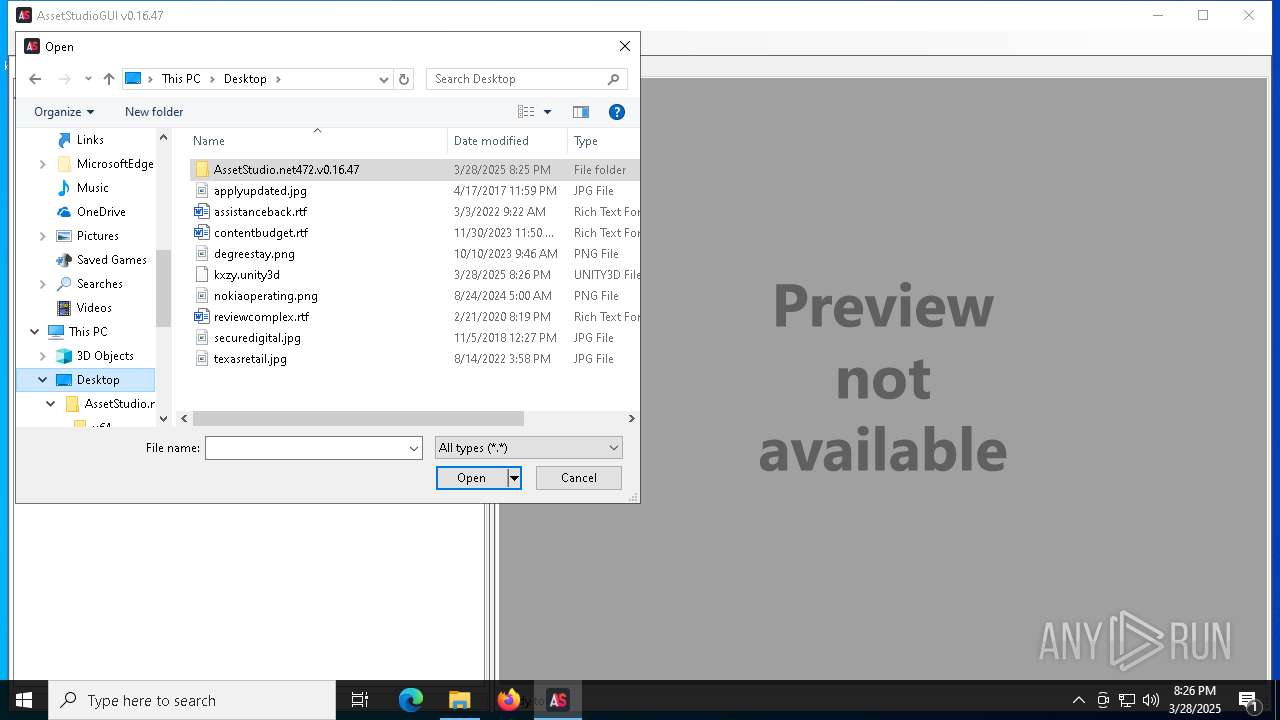
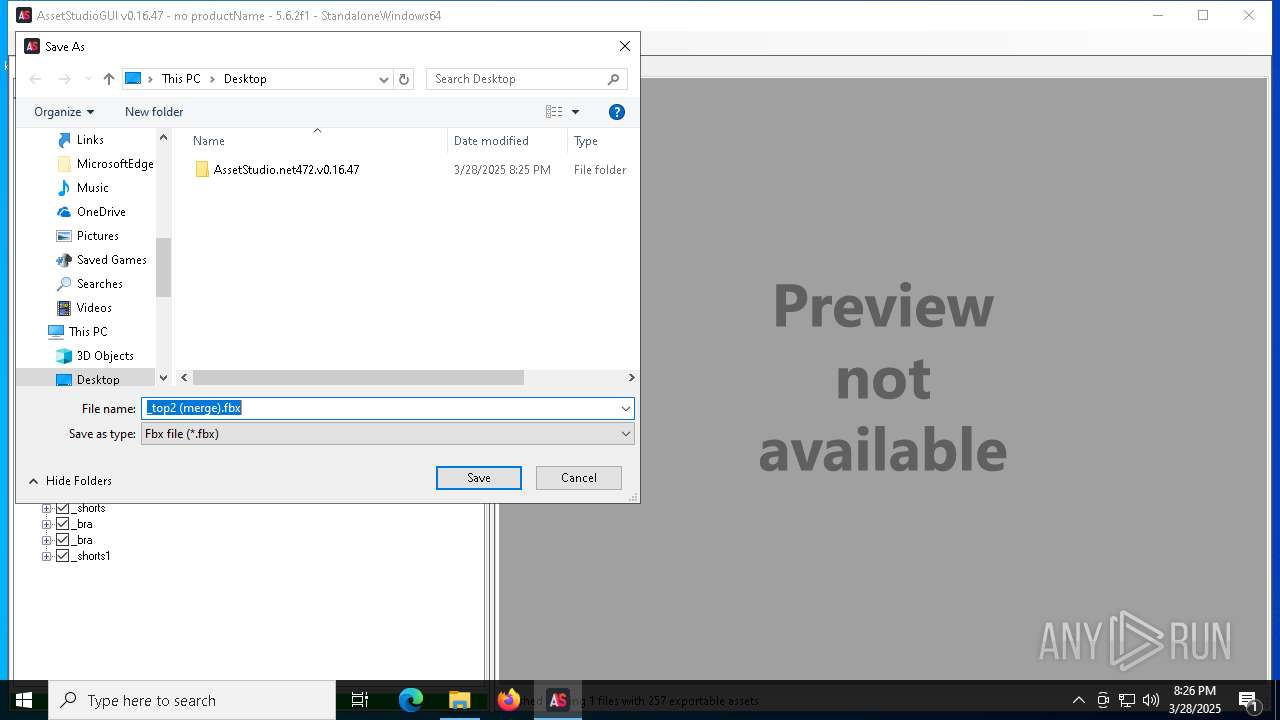
| File name: | AssetStudio.net472.v0.16.47.zip |
| Full analysis: | https://app.any.run/tasks/aa325d4e-aea6-4b34-a5ac-8cc26eedd645 |
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2025, 20:24:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 59D3A07ACA04580F984C855B54772C0D |
| SHA1: | B8D109237F52D4BB4DE906D82CD3D0B9162AC654 |
| SHA256: | A469F26742A5443A3216E01484A3A808608796FF22135F4D2F24F7B63AD356D8 |
| SSDEEP: | 98304:V+9K9+YMPz3av4jL98wM+zgN3DttdWYHyQZoiJGrndFF74cC1/twVWxyPlQ50V/G:aC/p7AWCWBd/AKmHD5Y |
MALICIOUS
No malicious indicators.SUSPICIOUS
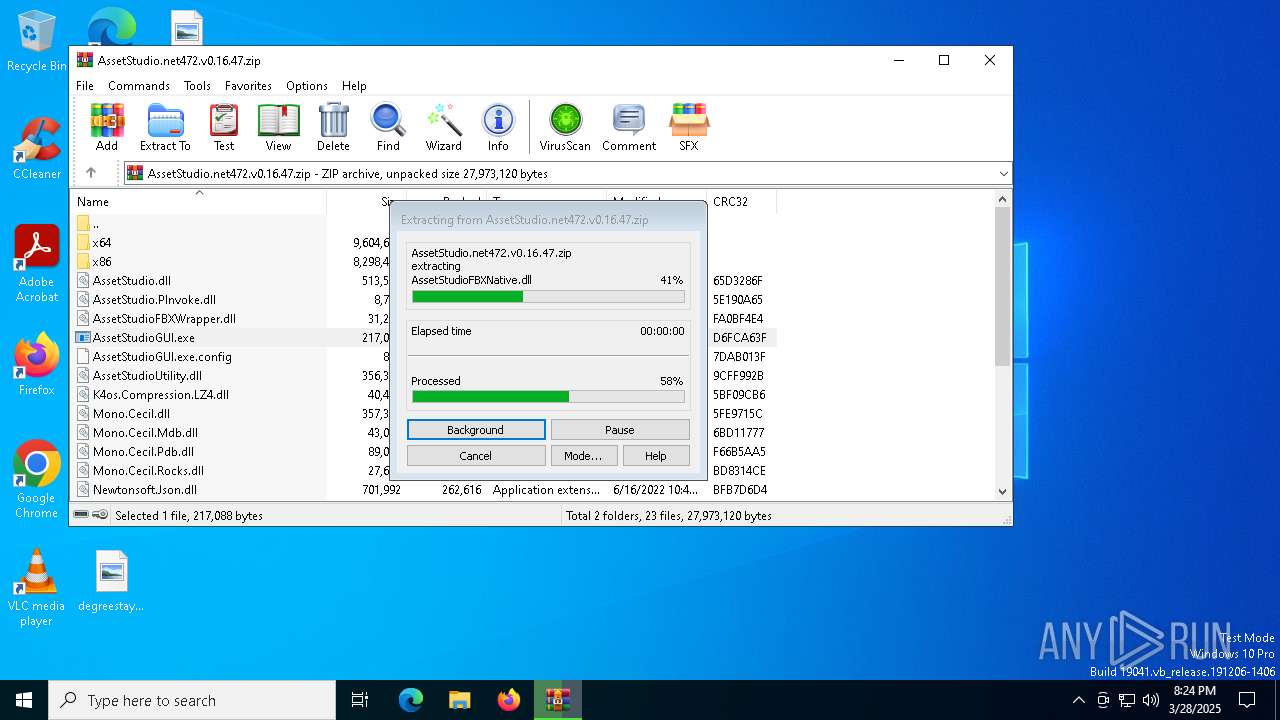
Process drops legitimate windows executable
- WinRAR.exe (PID: 7324)
Reads security settings of Internet Explorer
- AssetStudioGUI.exe (PID: 1568)
- WinRAR.exe (PID: 7324)
- AssetStudioGUI.exe (PID: 1676)
- ShellExperienceHost.exe (PID: 7784)
MeshAgent potential remote access (YARA)
- AssetStudioGUI.exe (PID: 1676)
There is functionality for taking screenshot (YARA)
- AssetStudioGUI.exe (PID: 1676)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7324)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7272)
- slui.exe (PID: 7444)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7272)
- BackgroundTransferHost.exe (PID: 8136)
- BackgroundTransferHost.exe (PID: 5544)
- BackgroundTransferHost.exe (PID: 7876)
- BackgroundTransferHost.exe (PID: 5392)
- BackgroundTransferHost.exe (PID: 7972)
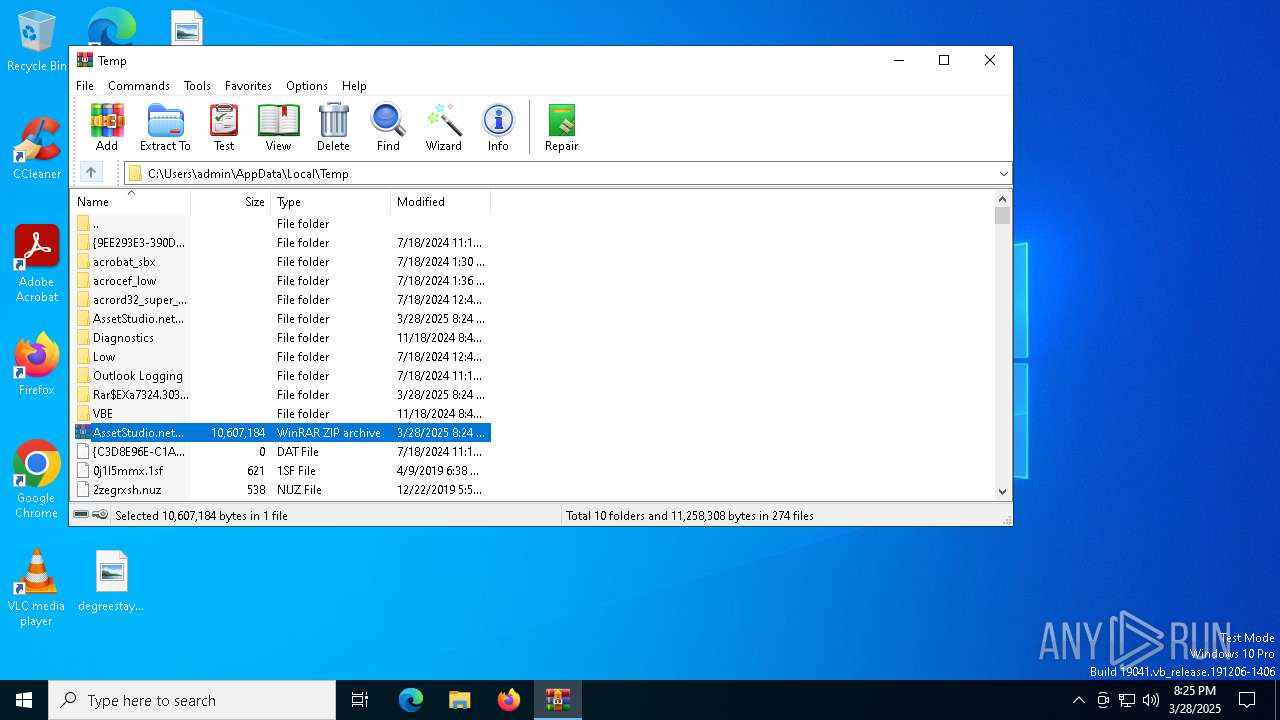
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7324)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7272)
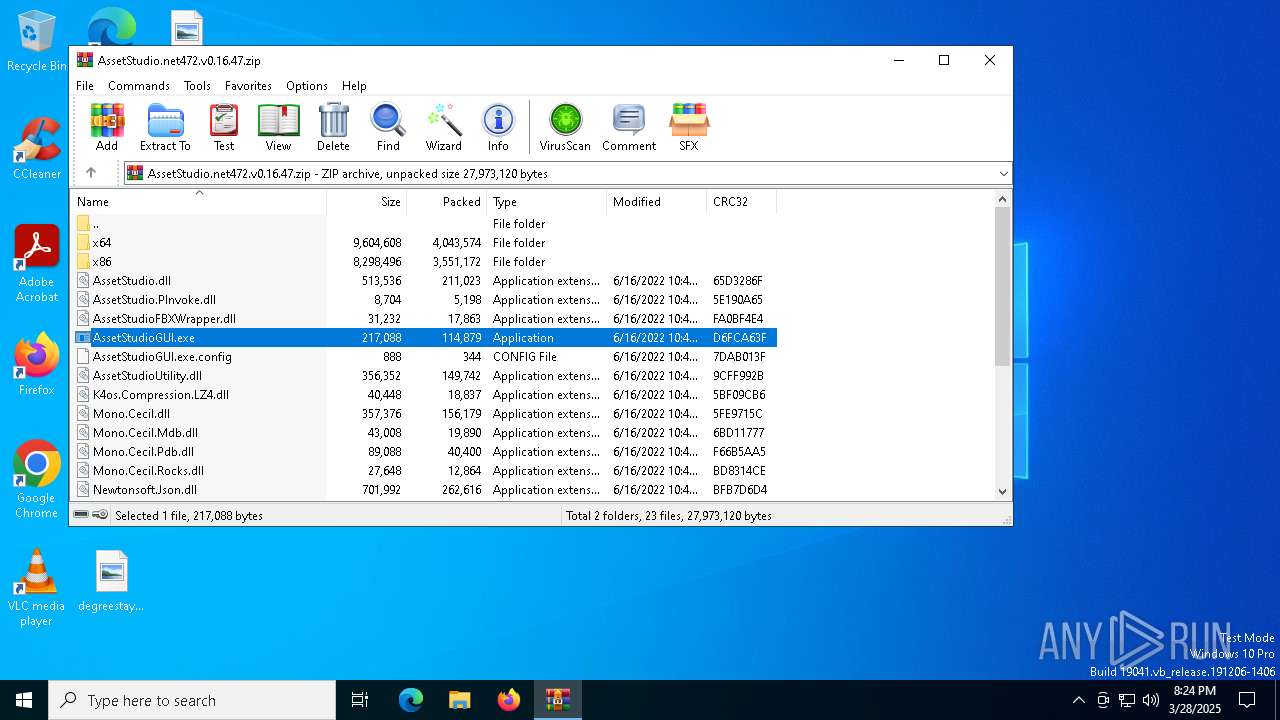
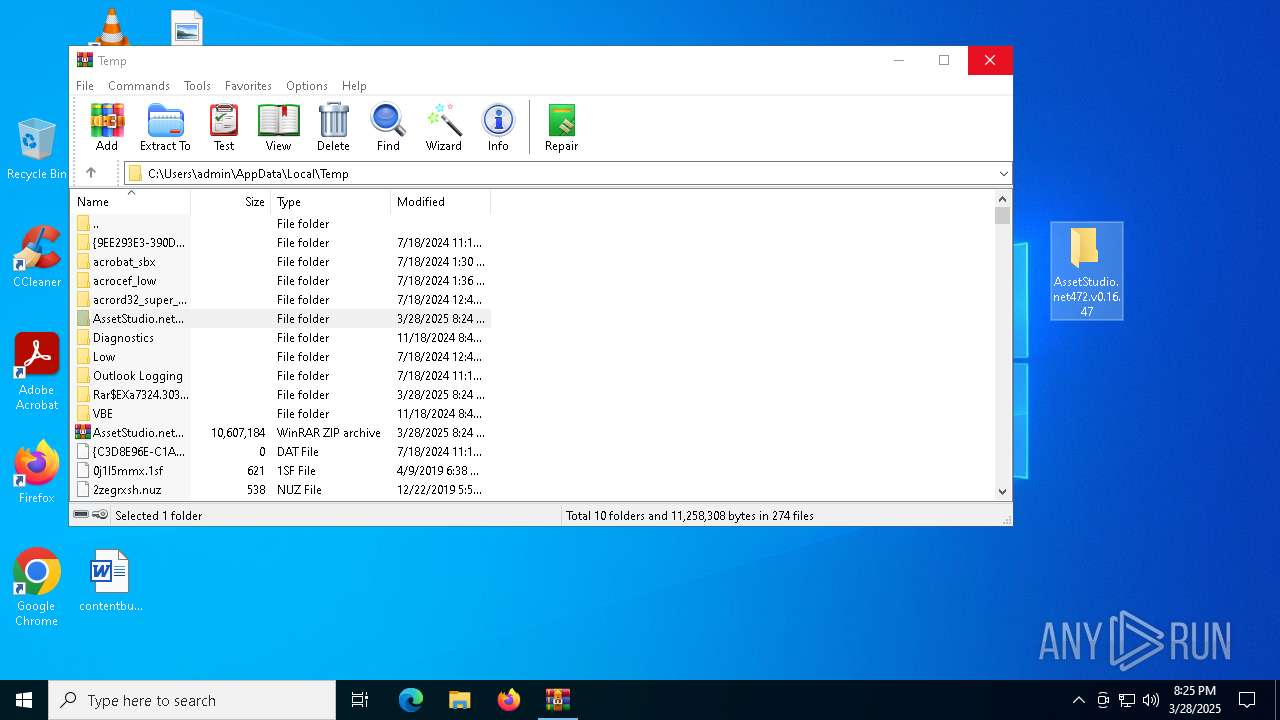
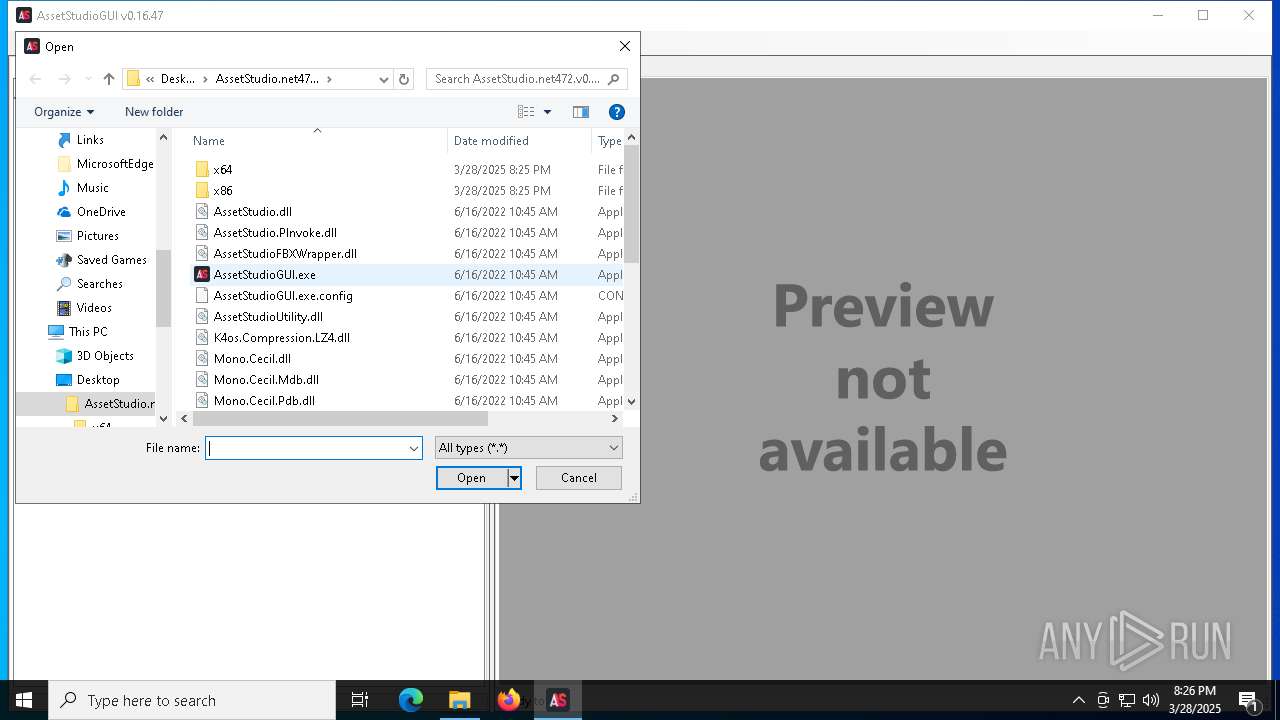
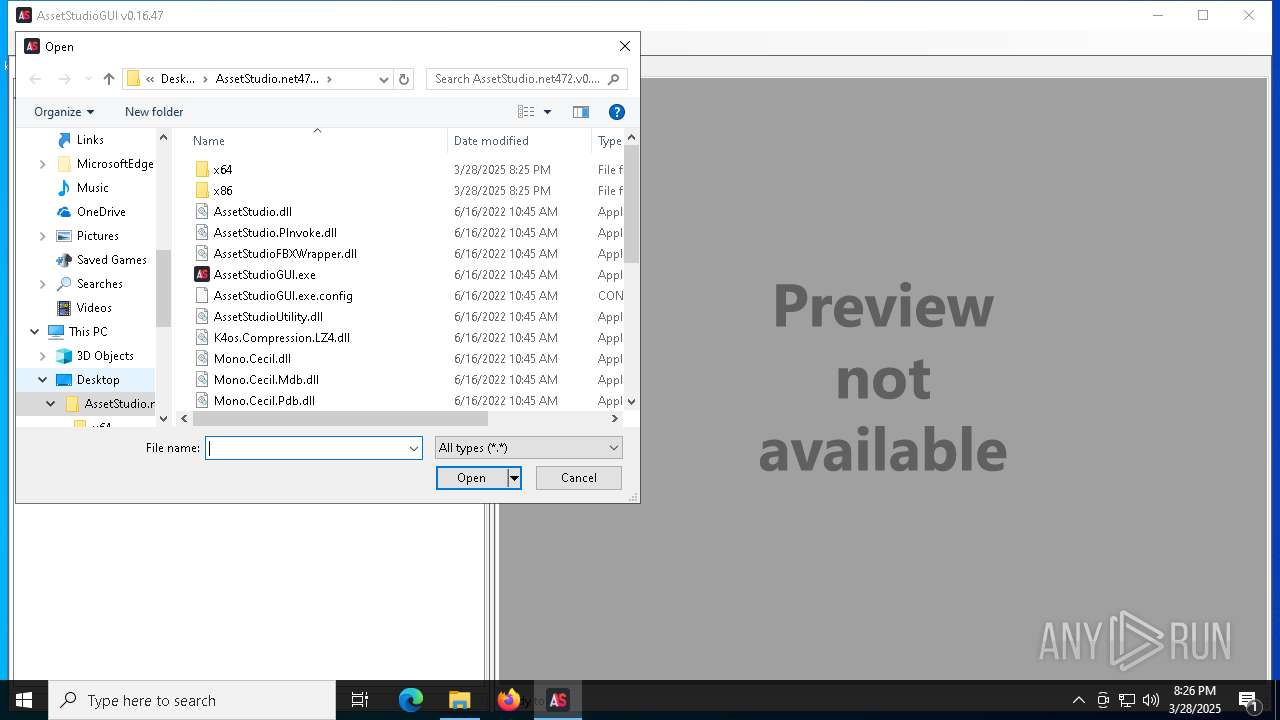
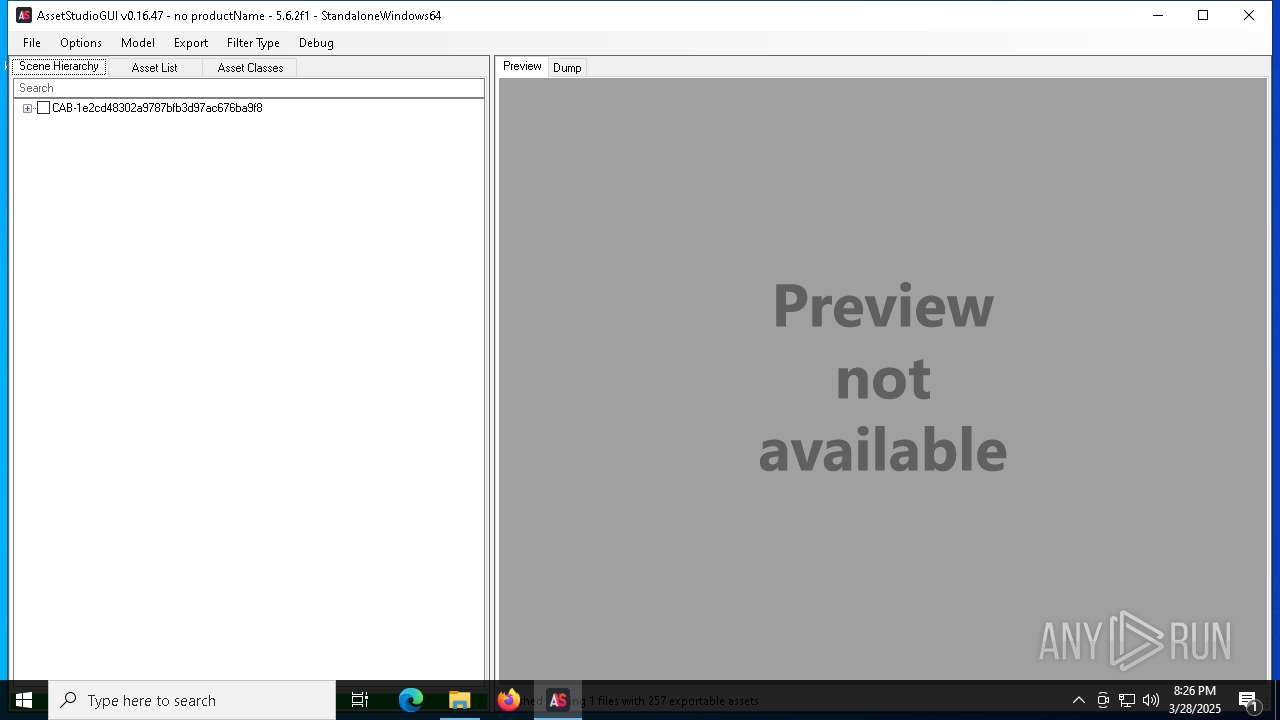
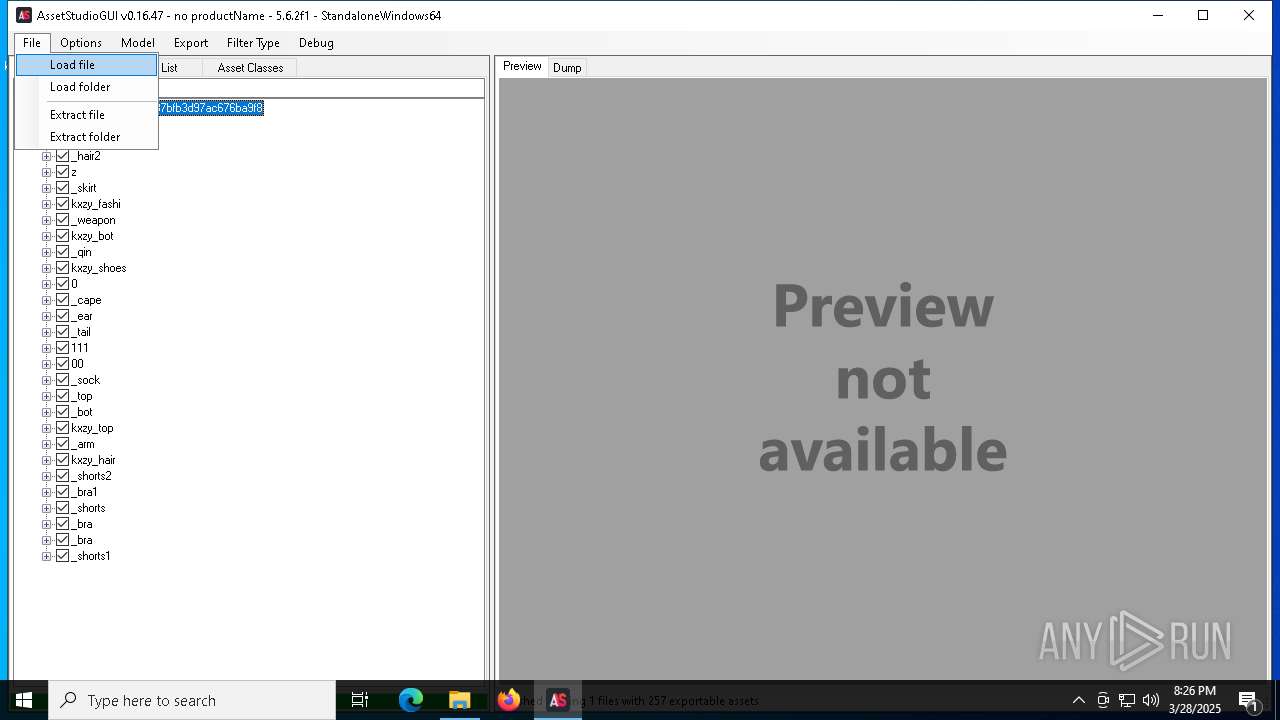
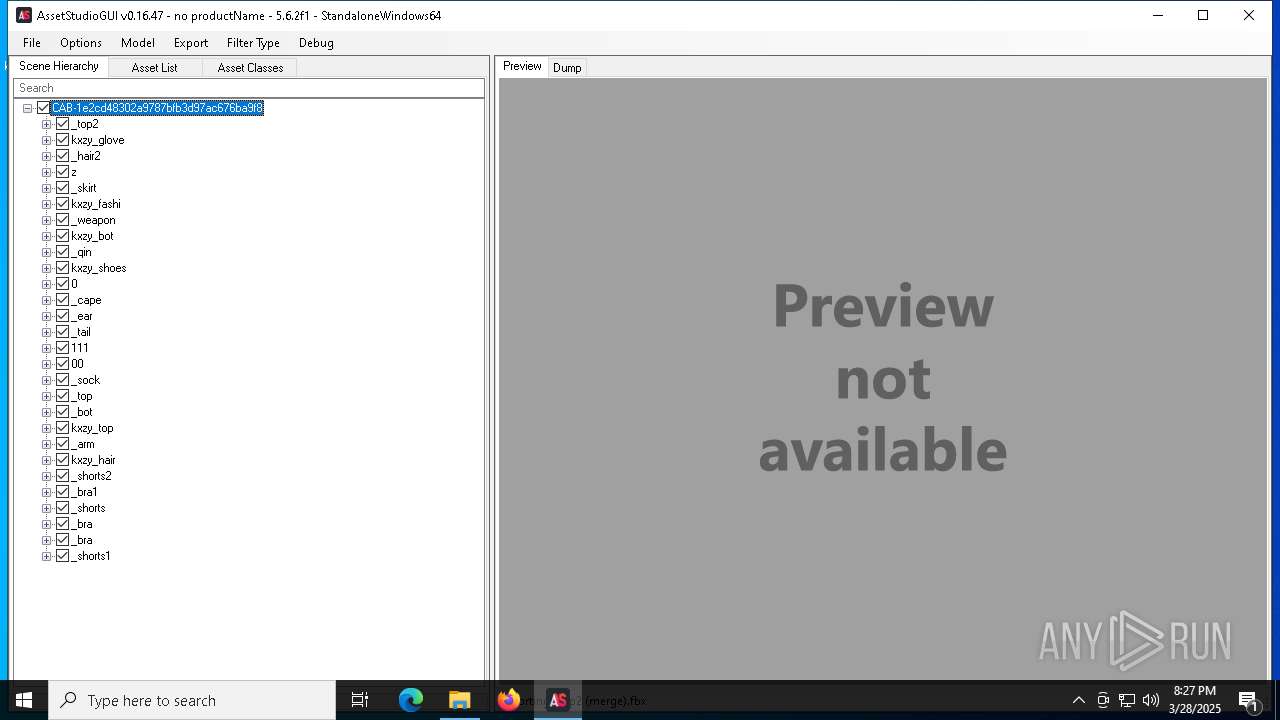
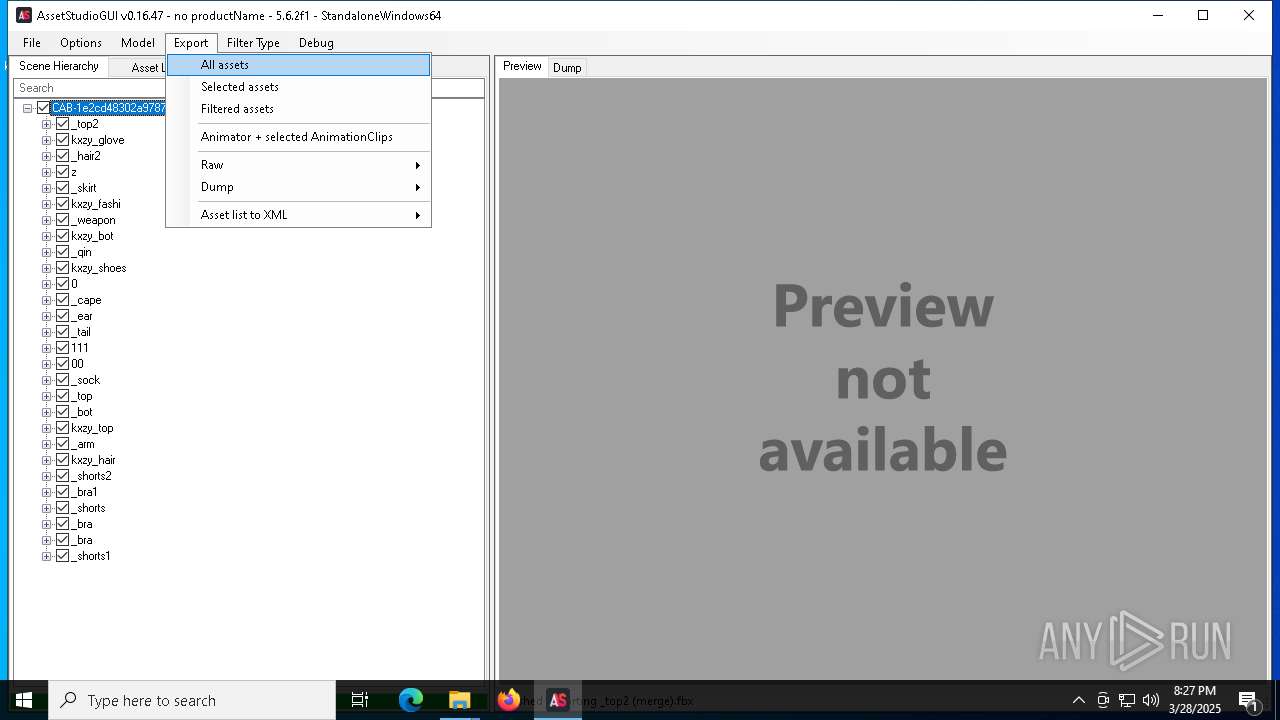
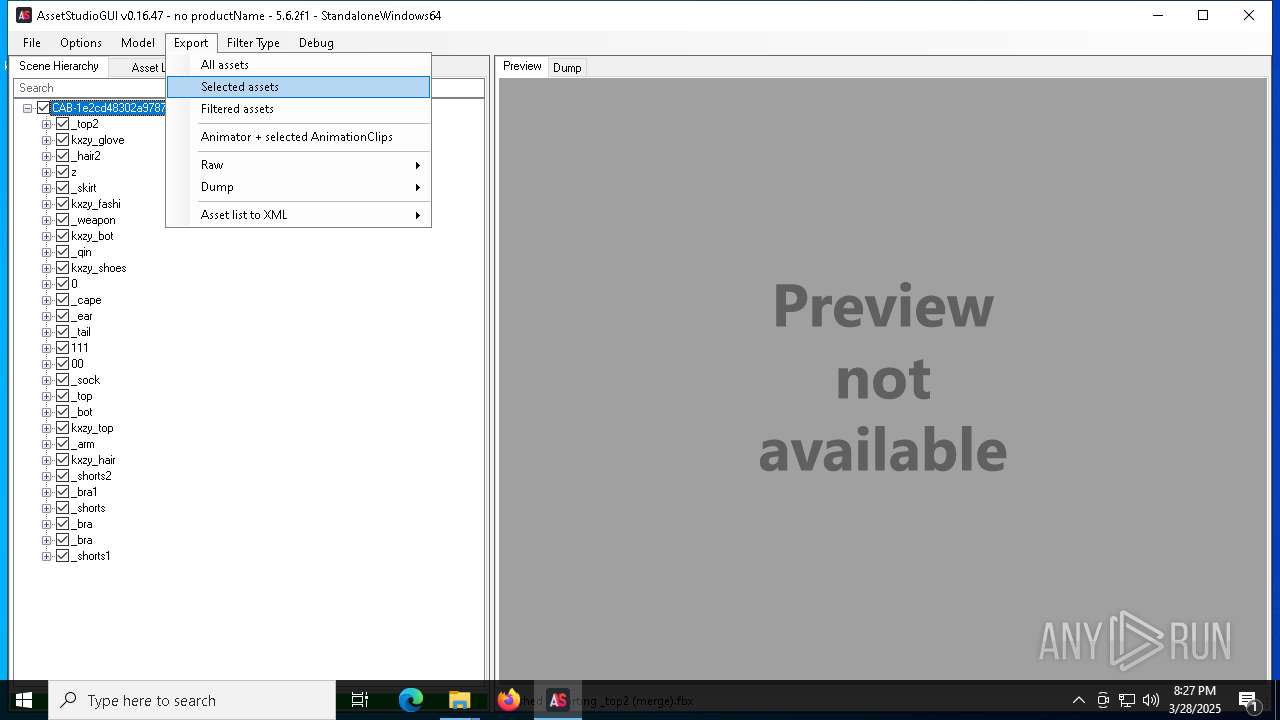
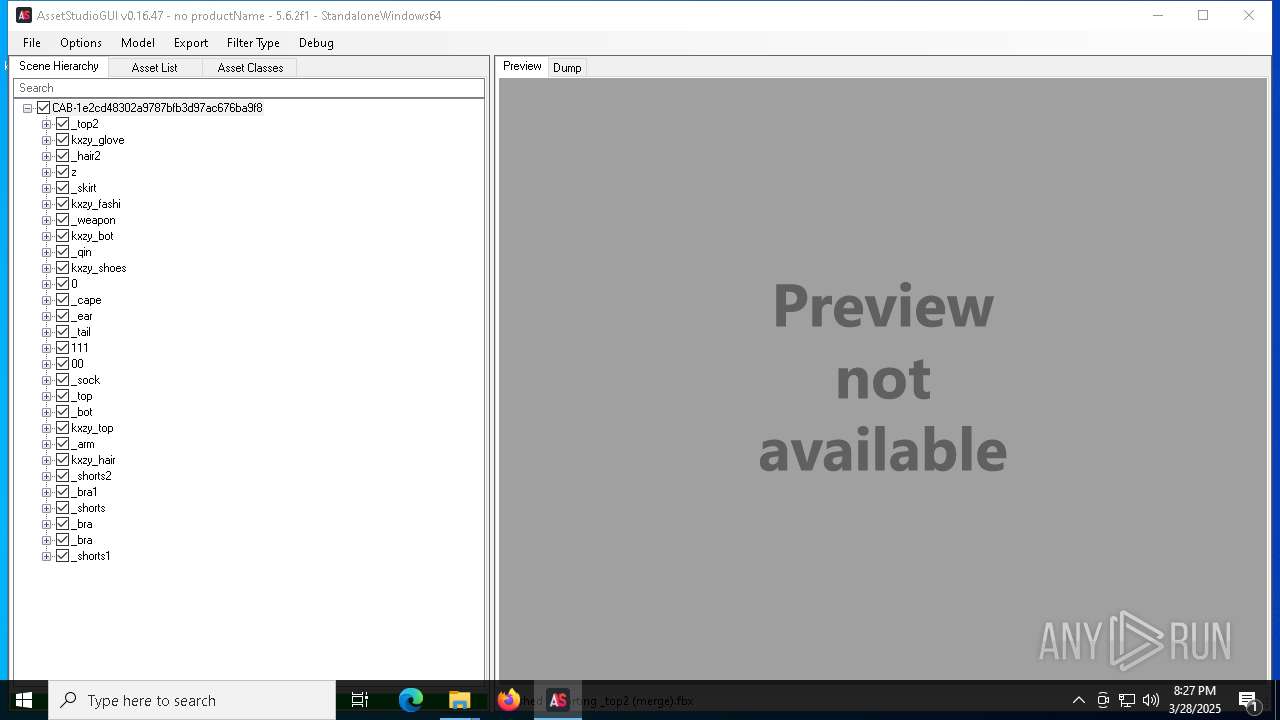
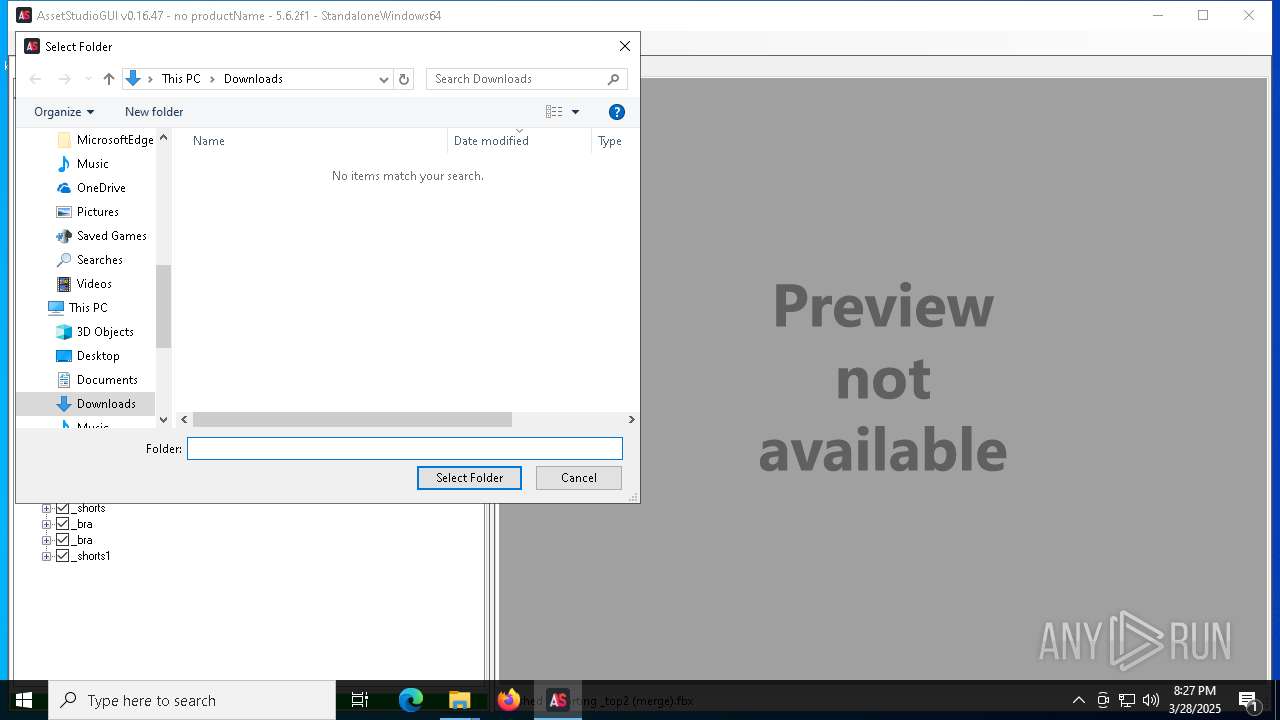
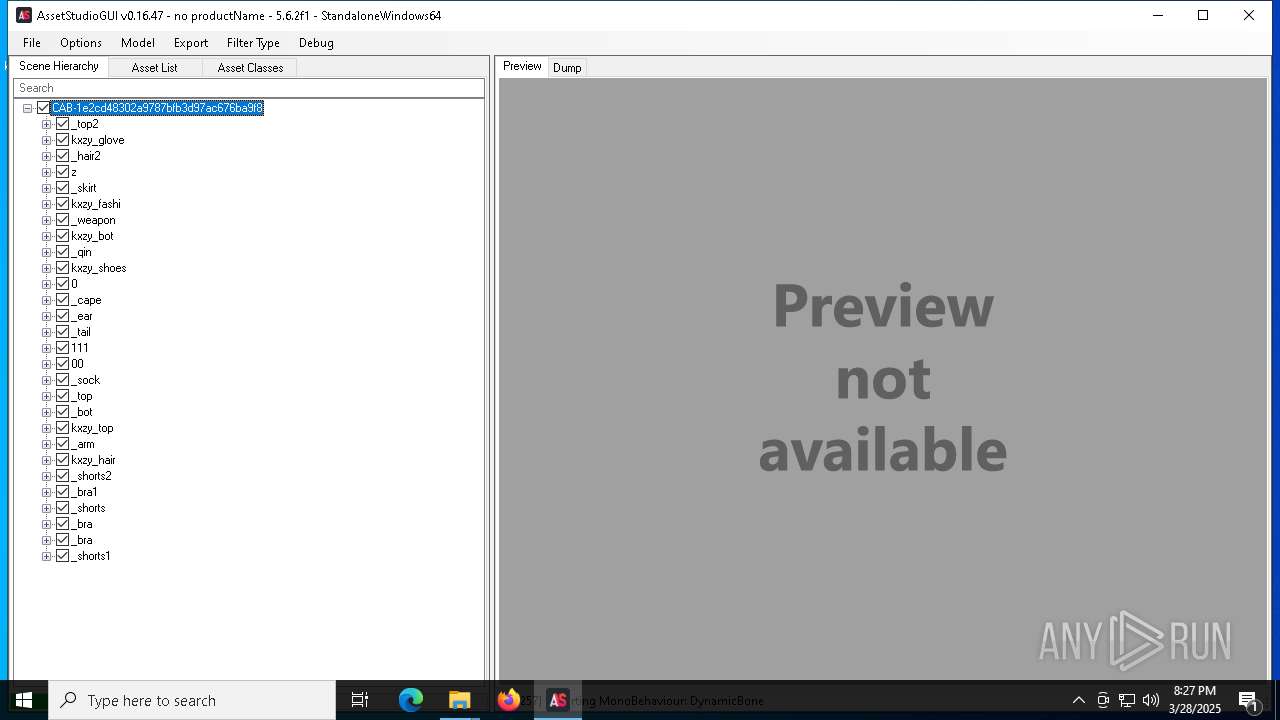
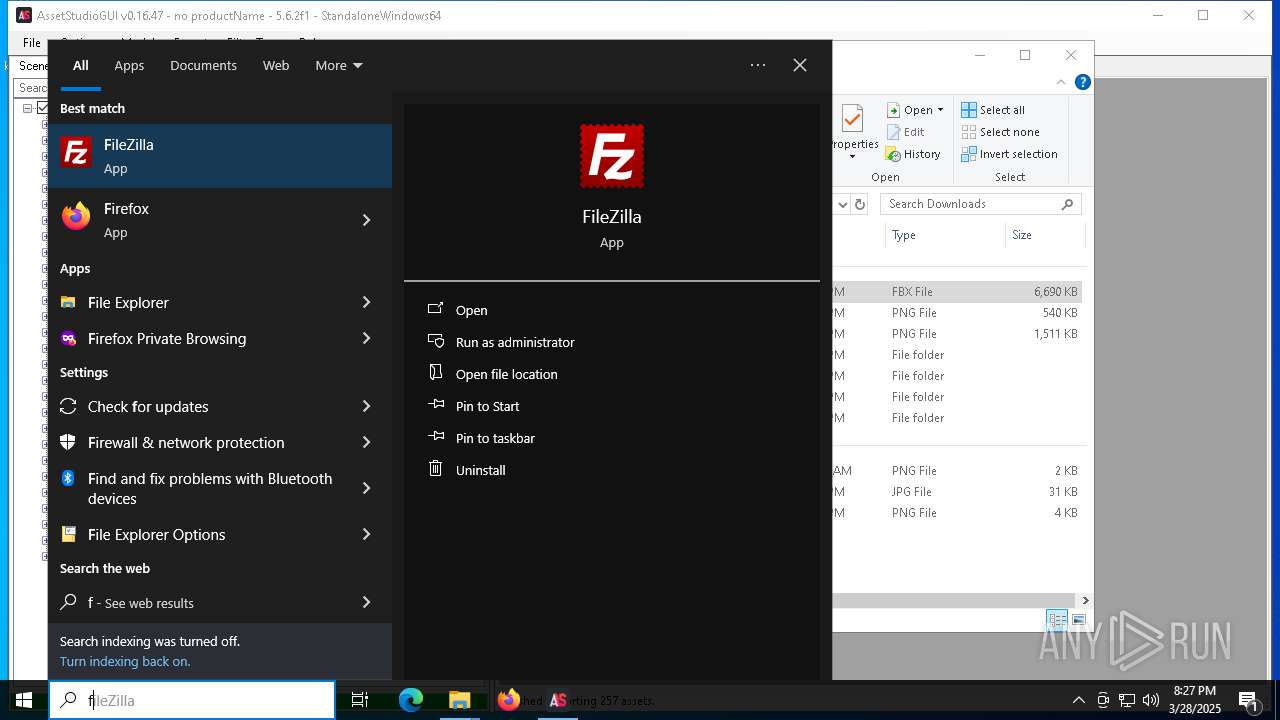
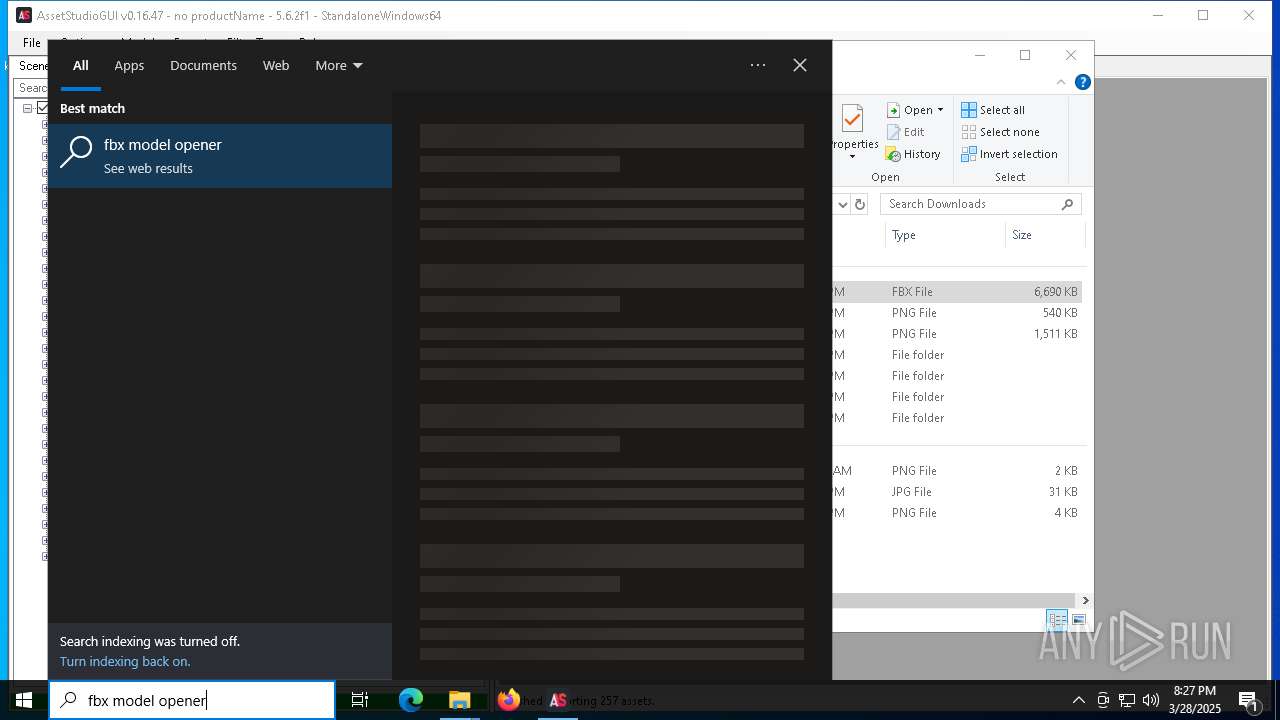
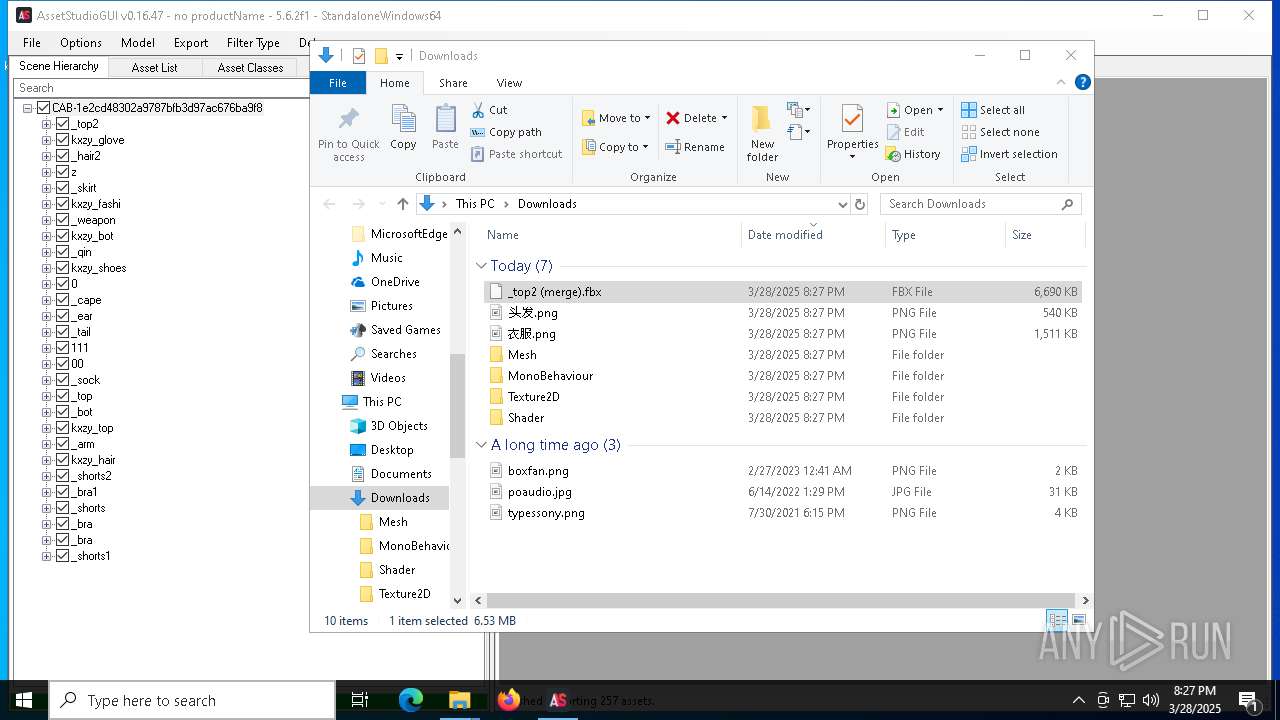
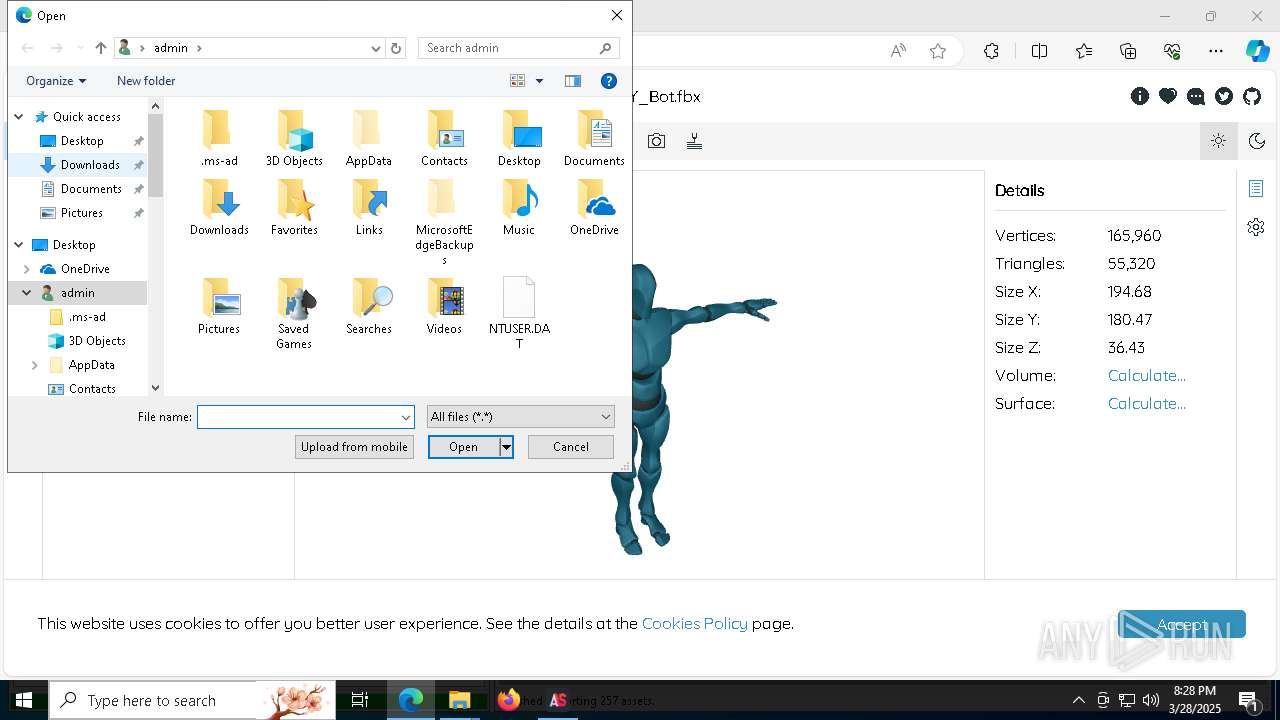
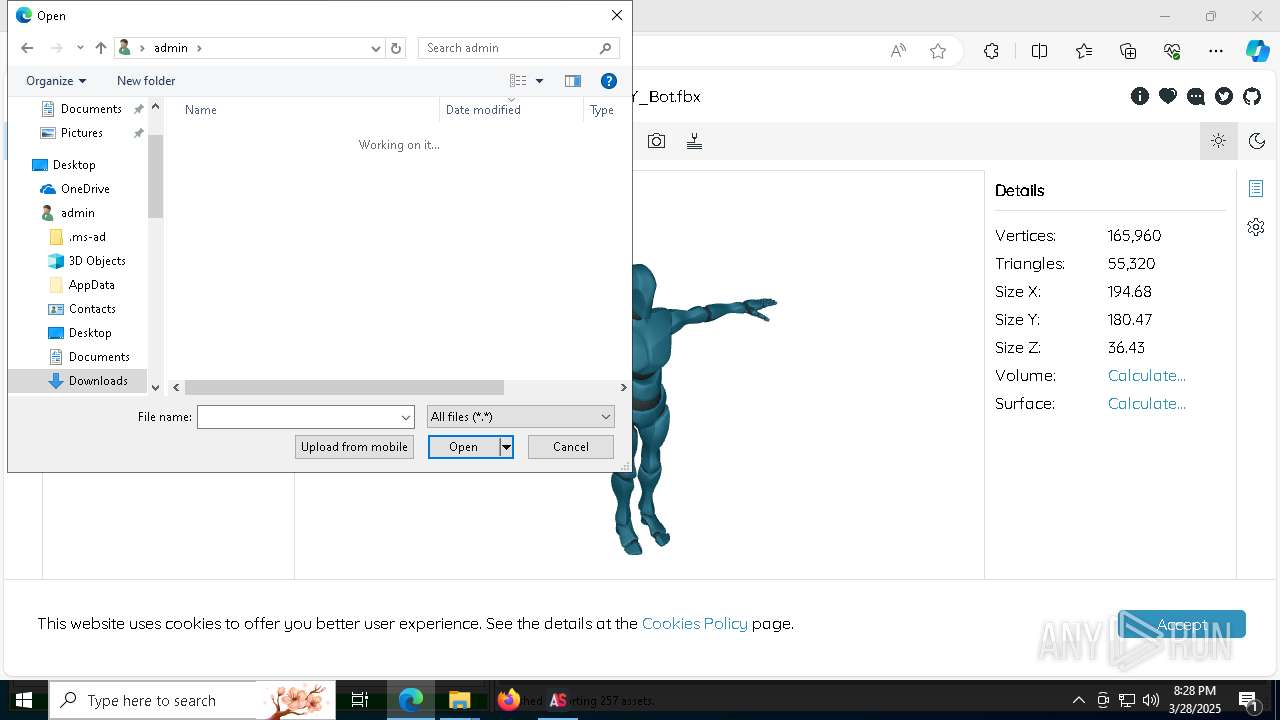
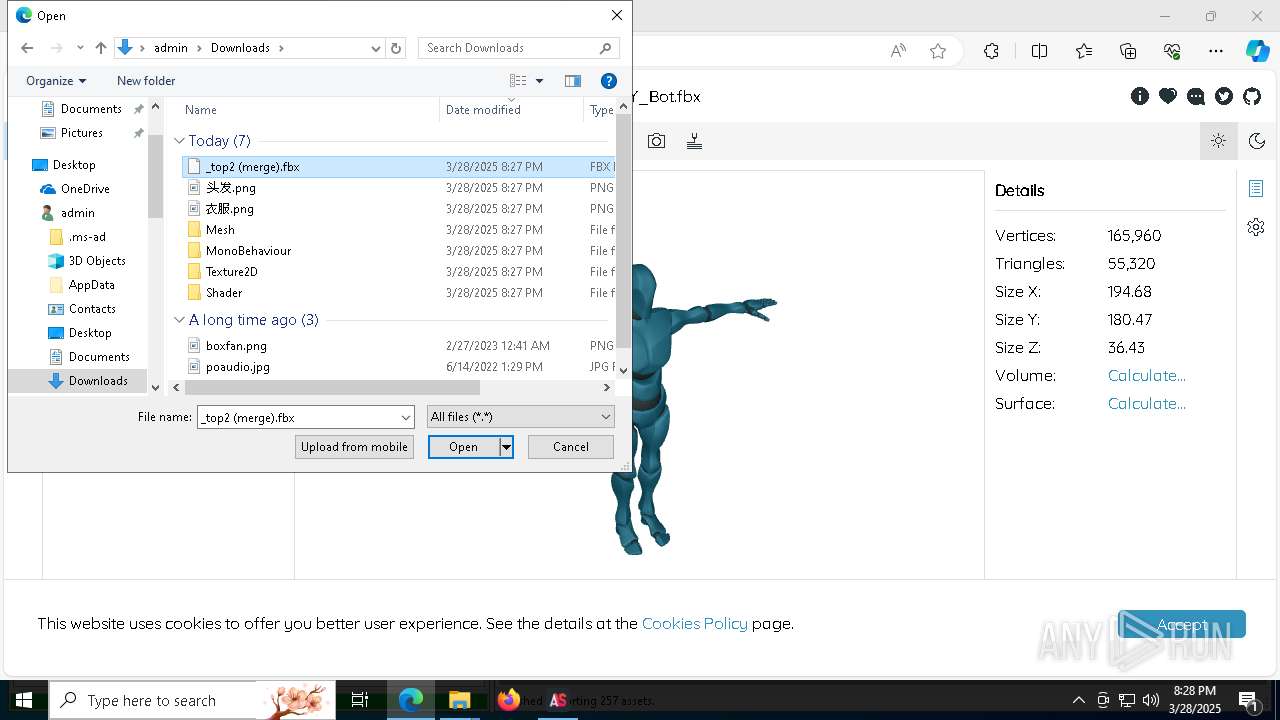
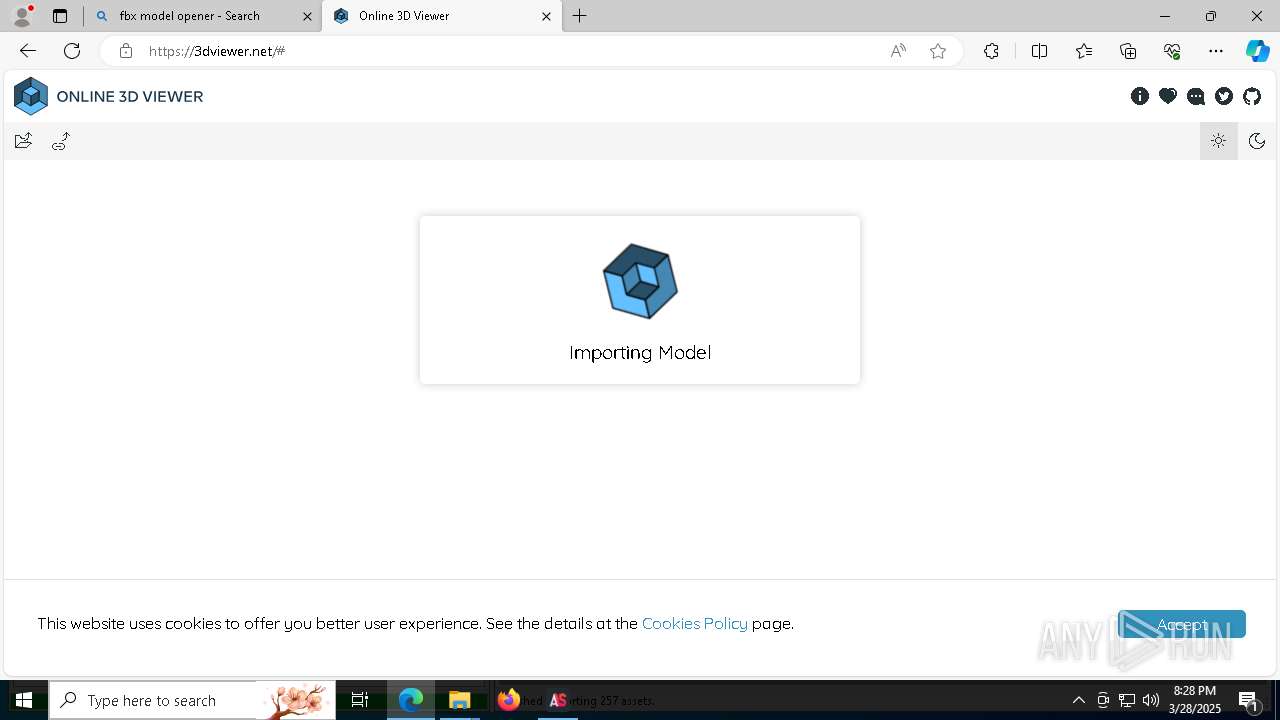
Manual execution by a user
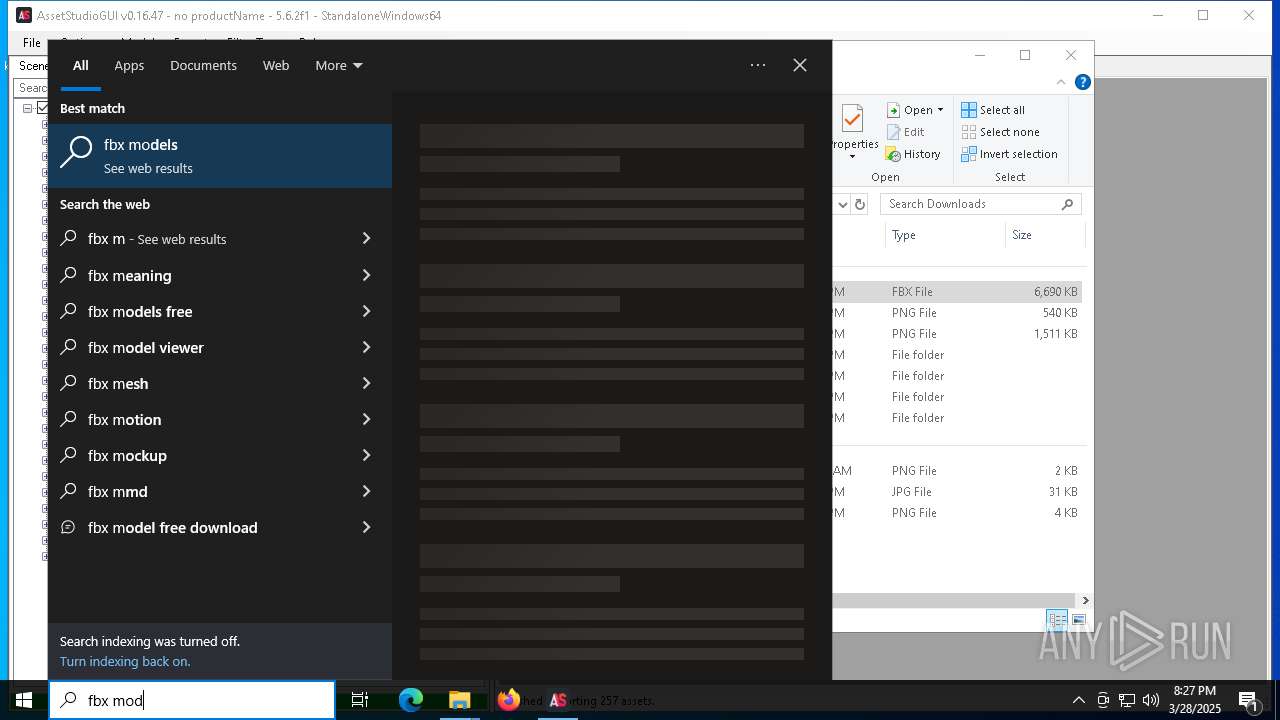
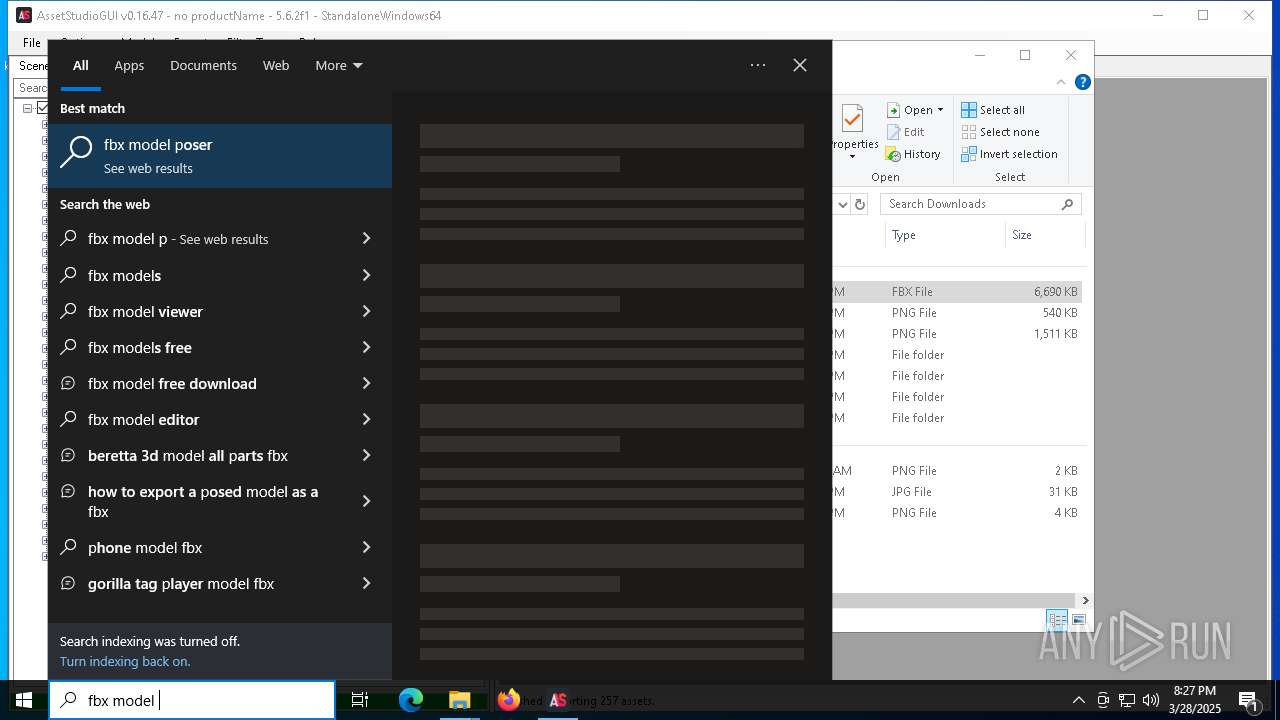
- AssetStudioGUI.exe (PID: 1676)
Reads the computer name
- AssetStudioGUI.exe (PID: 1676)
- AssetStudioGUI.exe (PID: 1568)
- ShellExperienceHost.exe (PID: 7784)
Checks supported languages
- AssetStudioGUI.exe (PID: 1568)
- AssetStudioGUI.exe (PID: 1676)
- ShellExperienceHost.exe (PID: 7784)
Reads the machine GUID from the registry
- AssetStudioGUI.exe (PID: 1568)
- AssetStudioGUI.exe (PID: 1676)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7272)
- slui.exe (PID: 7556)
- slui.exe (PID: 7444)
Creates files in the program directory
- AssetStudioGUI.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2022:06:16 10:45:26 |
| ZipCRC: | 0x65d3286f |
| ZipCompressedSize: | 211023 |
| ZipUncompressedSize: | 513536 |
| ZipFileName: | AssetStudio.dll |
Total processes
199
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
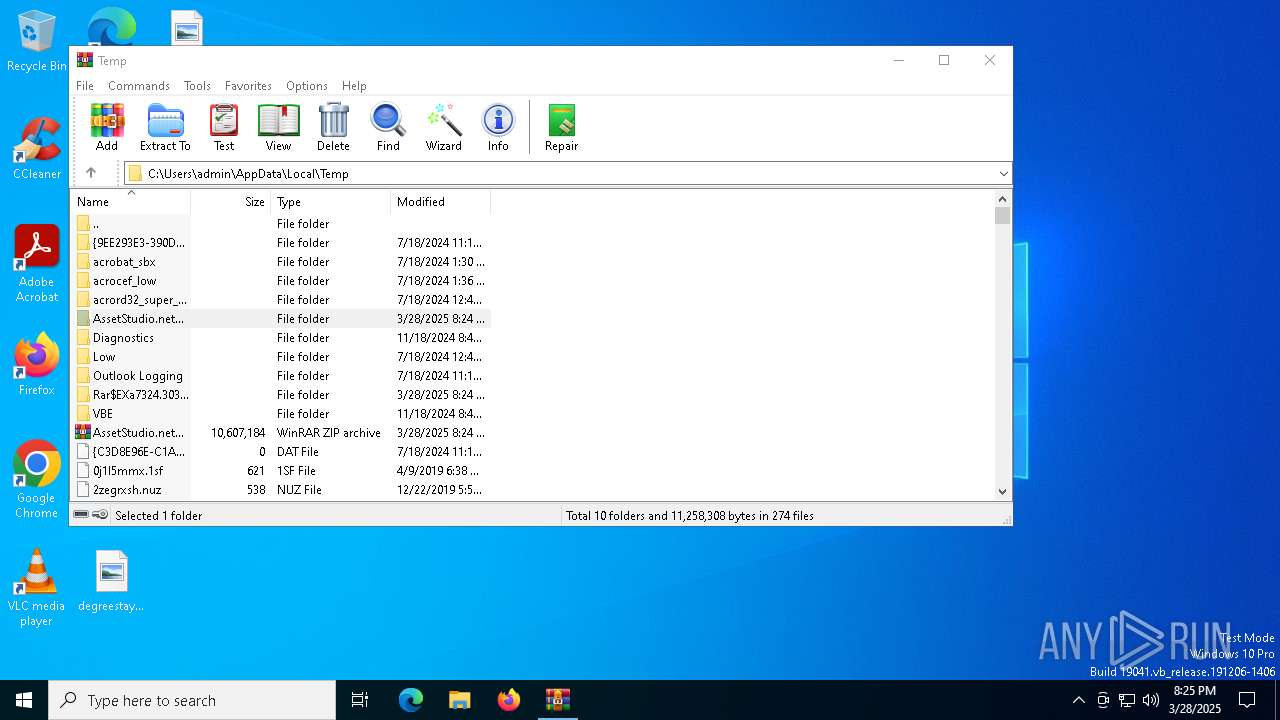
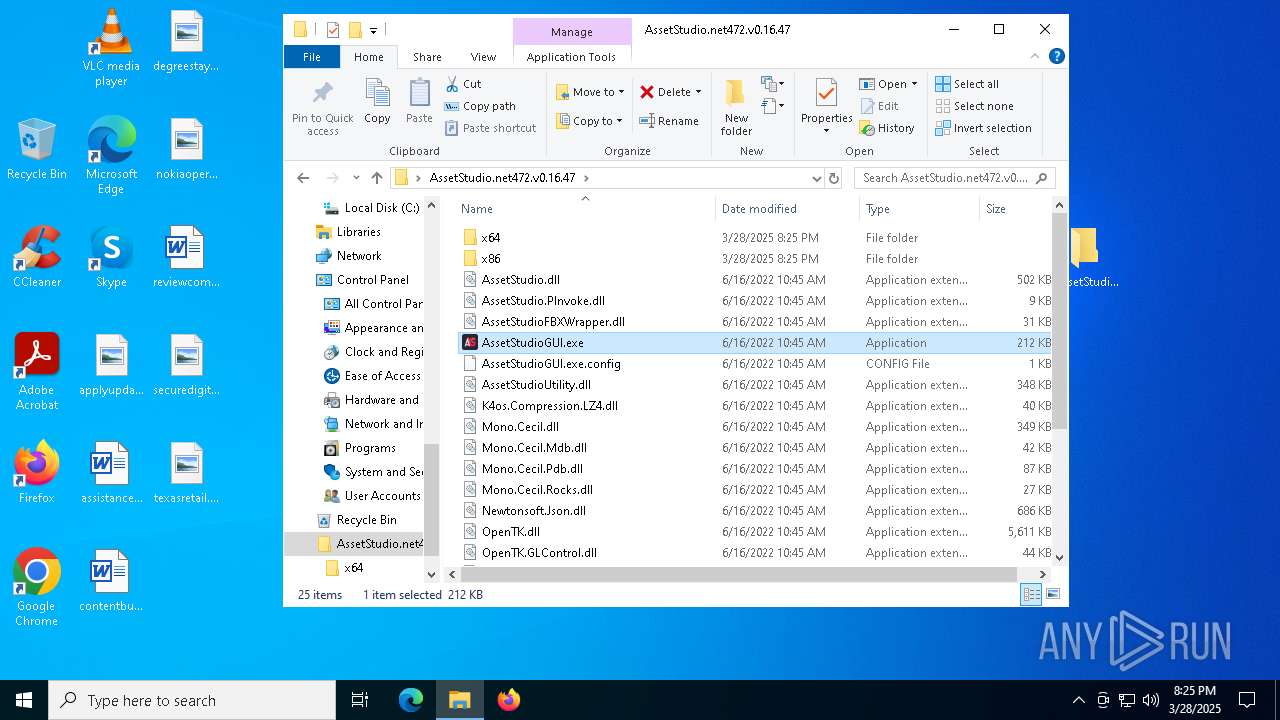
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
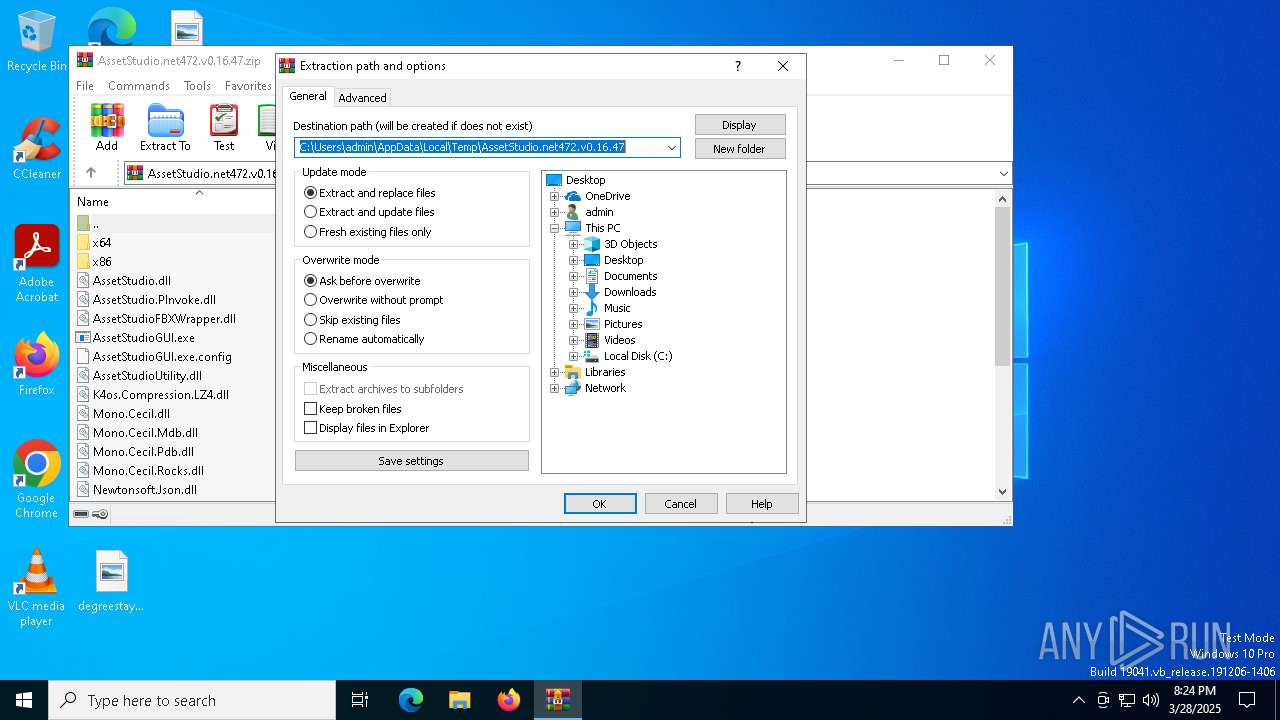
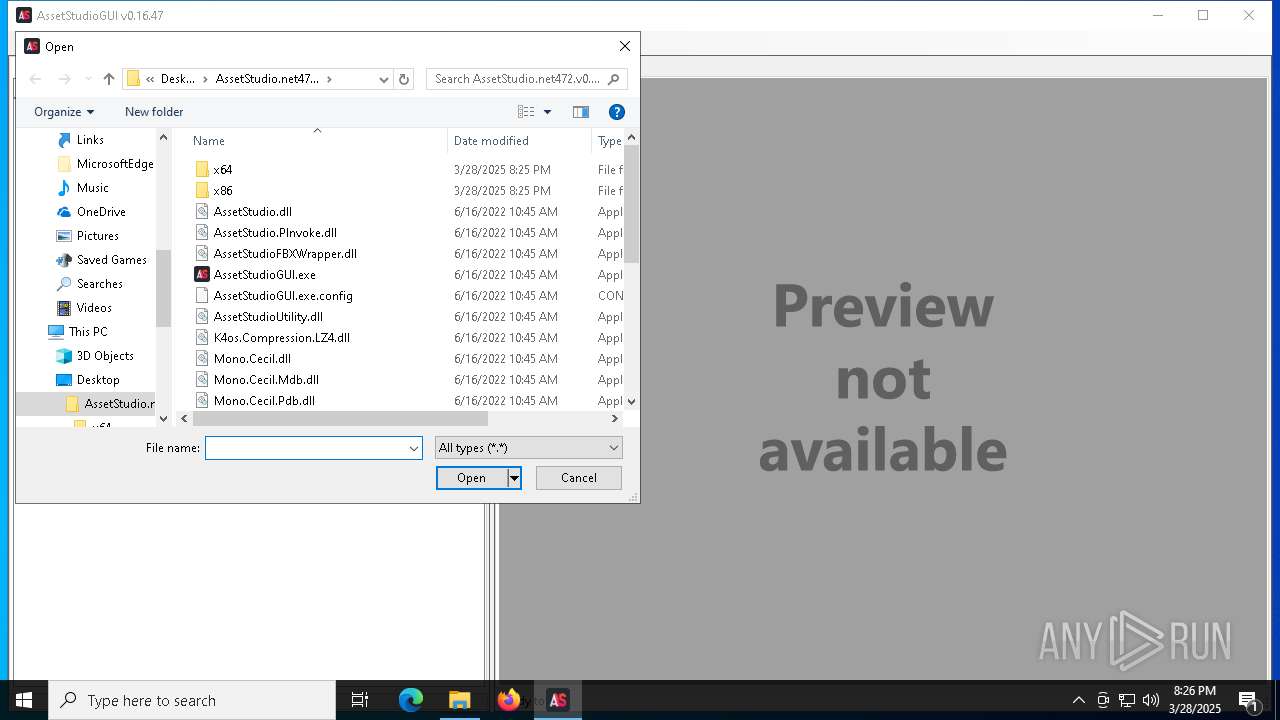
| 1568 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7324.30373\AssetStudioGUI.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7324.30373\AssetStudioGUI.exe | — | WinRAR.exe | |||||||||||
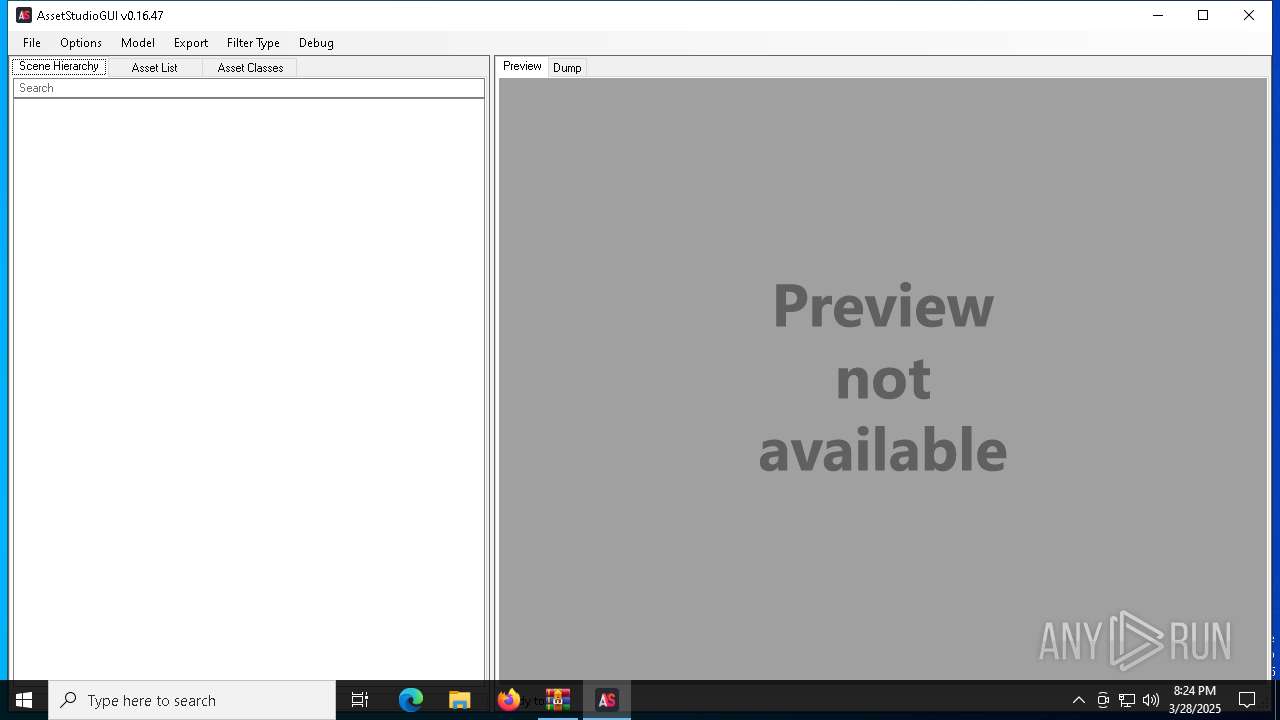
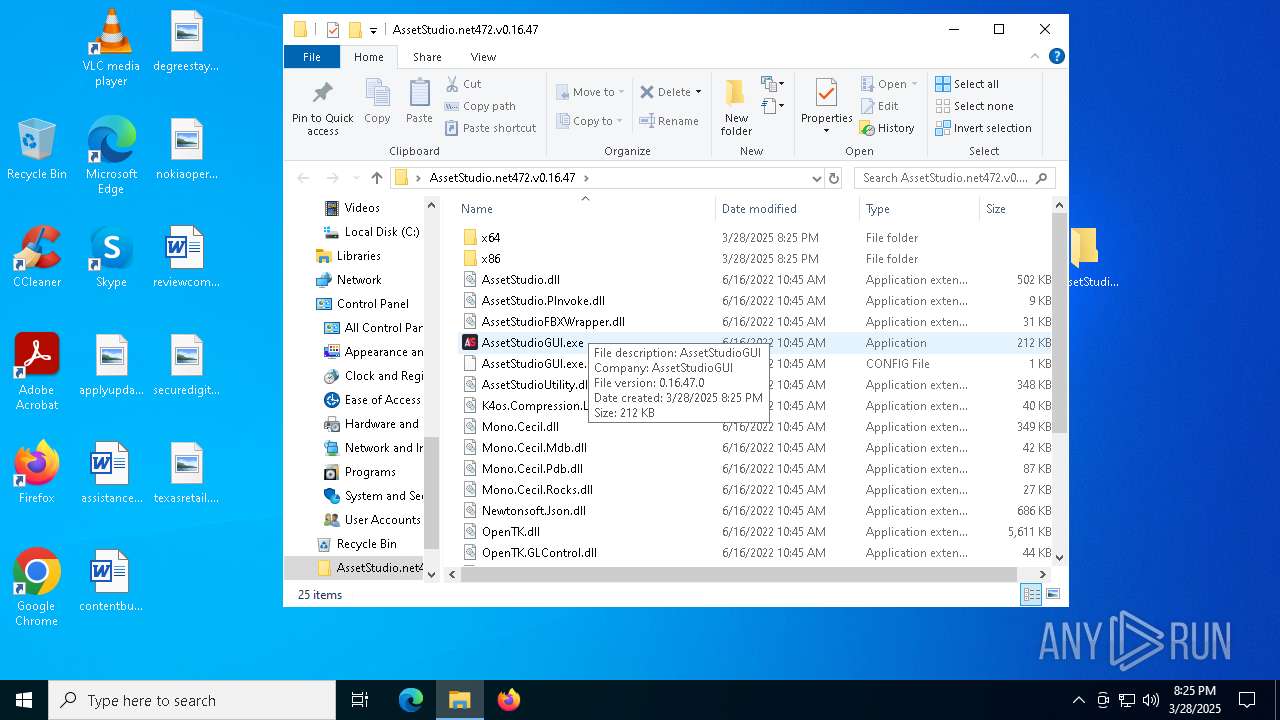
User: admin Company: AssetStudioGUI Integrity Level: MEDIUM Description: AssetStudioGUI Exit code: 0 Version: 0.16.47 Modules
| |||||||||||||||
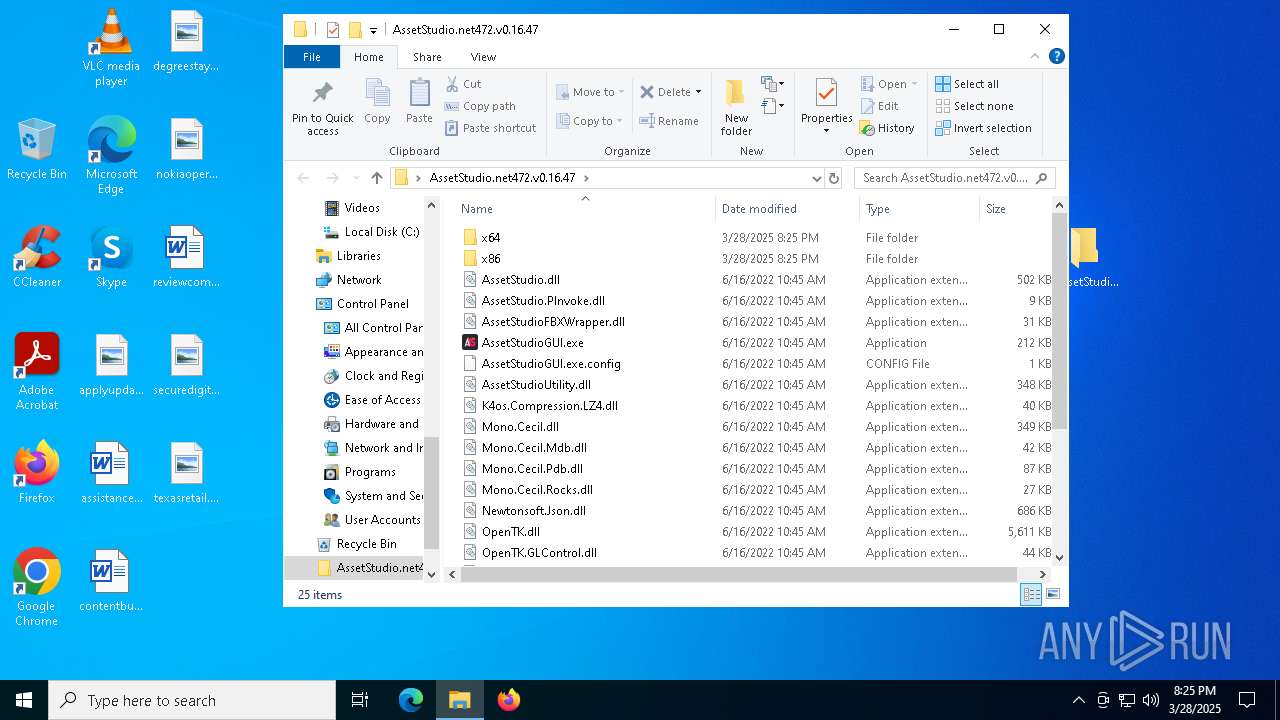
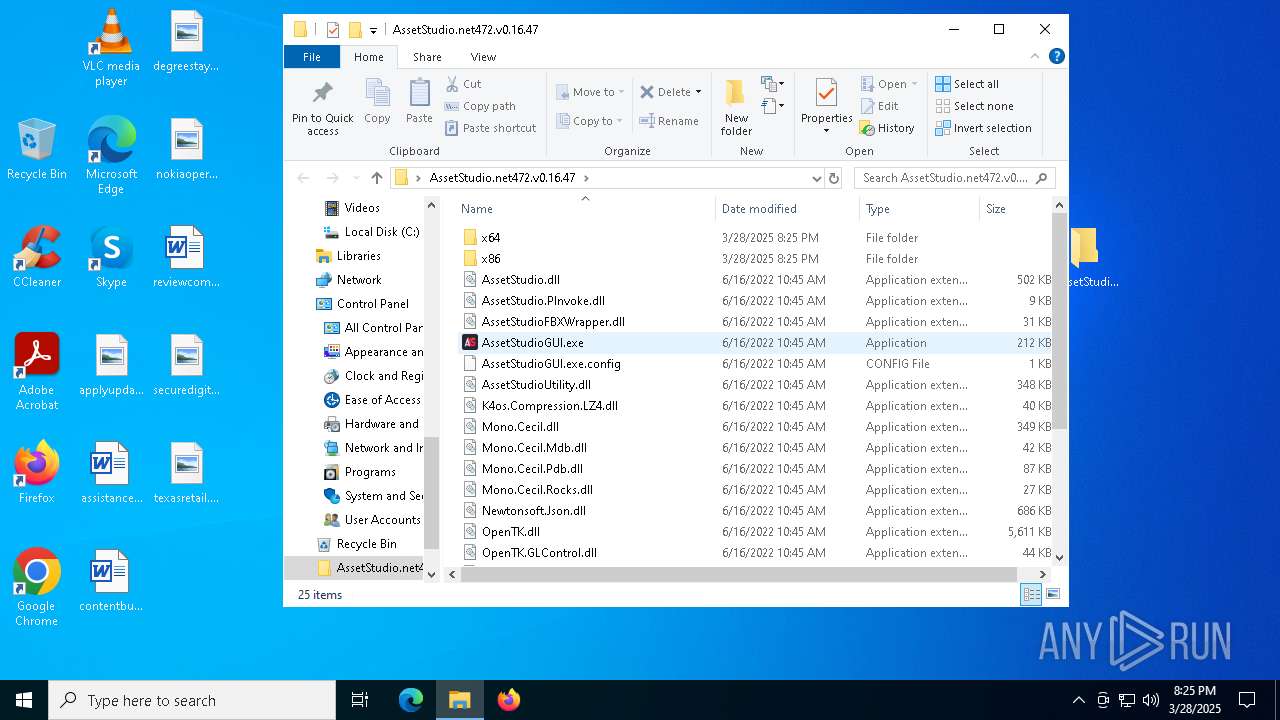
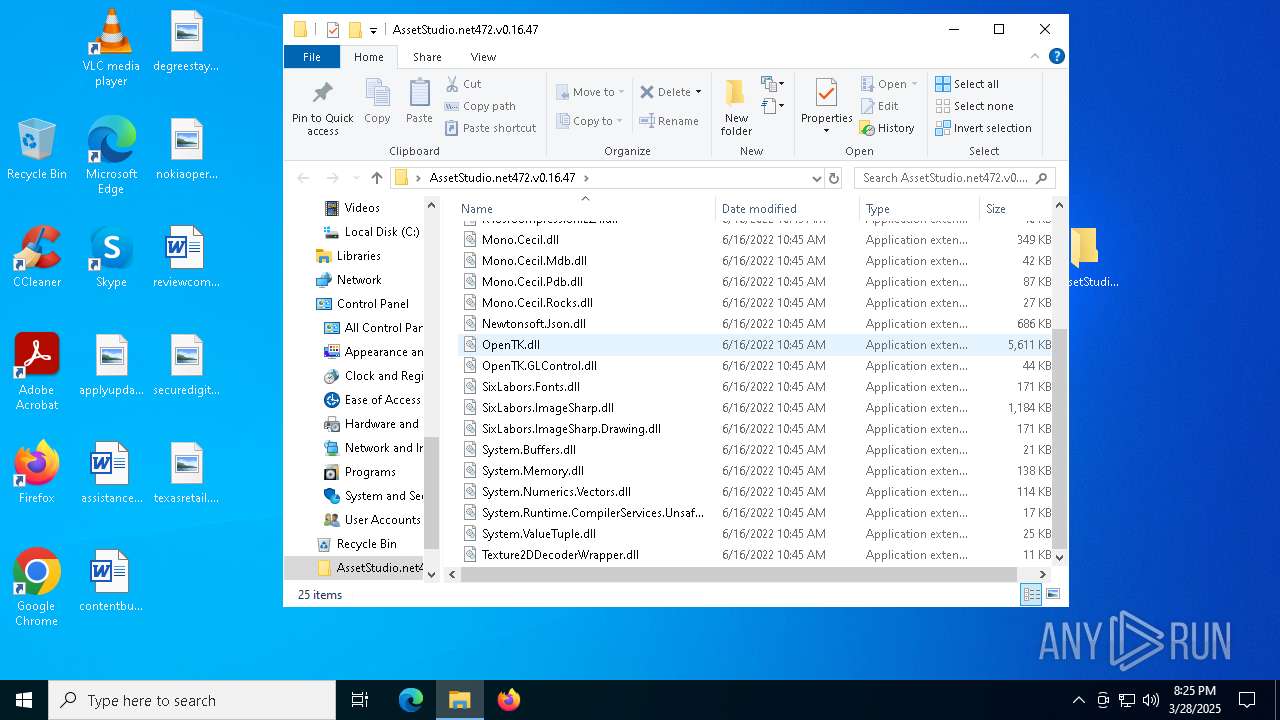
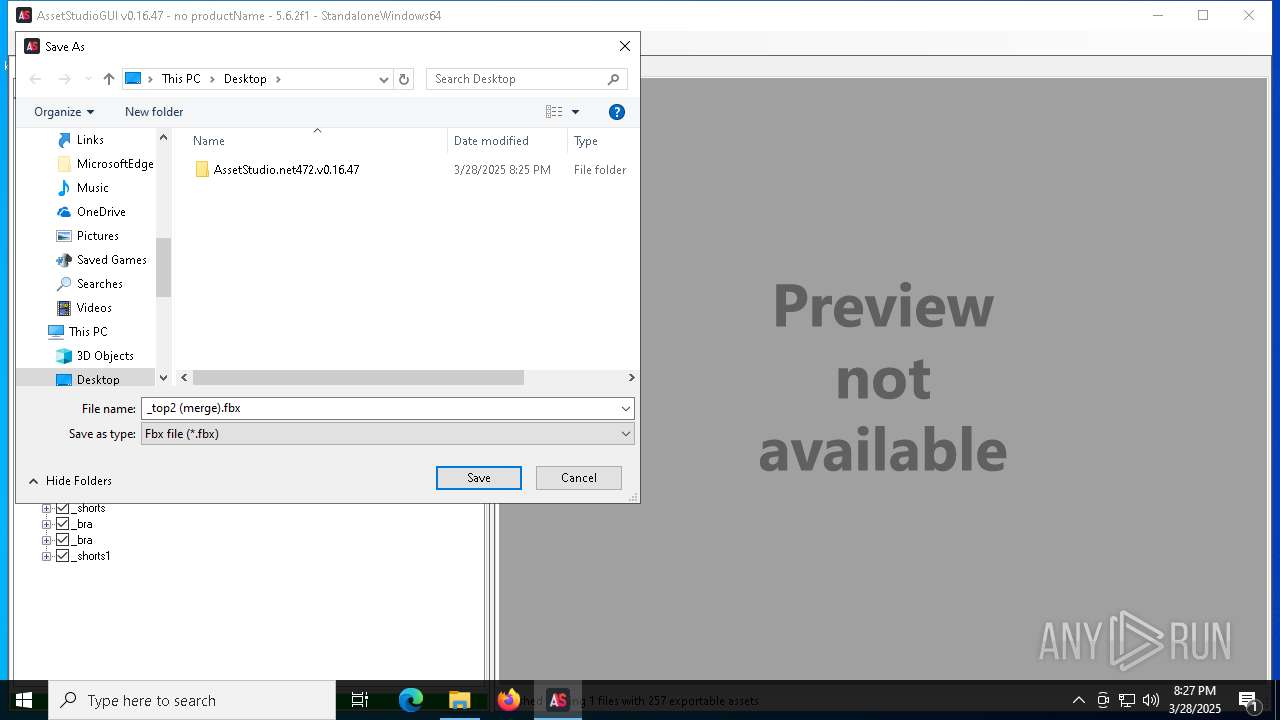
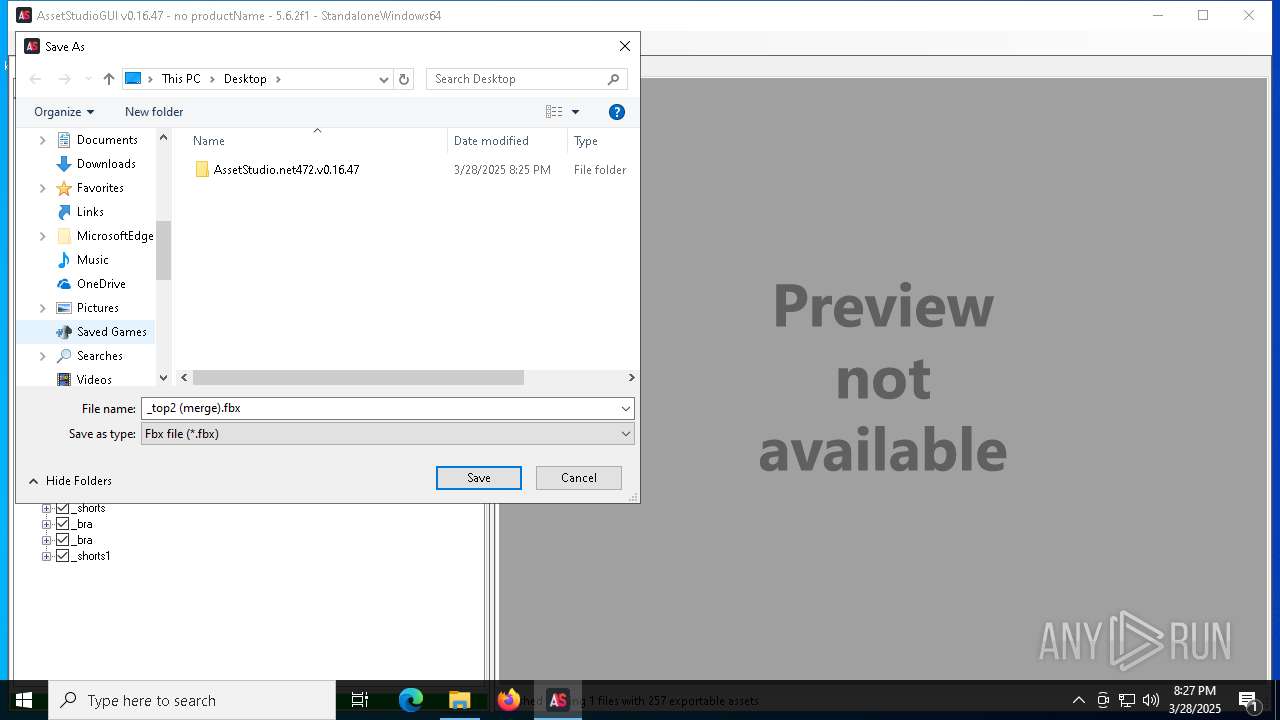
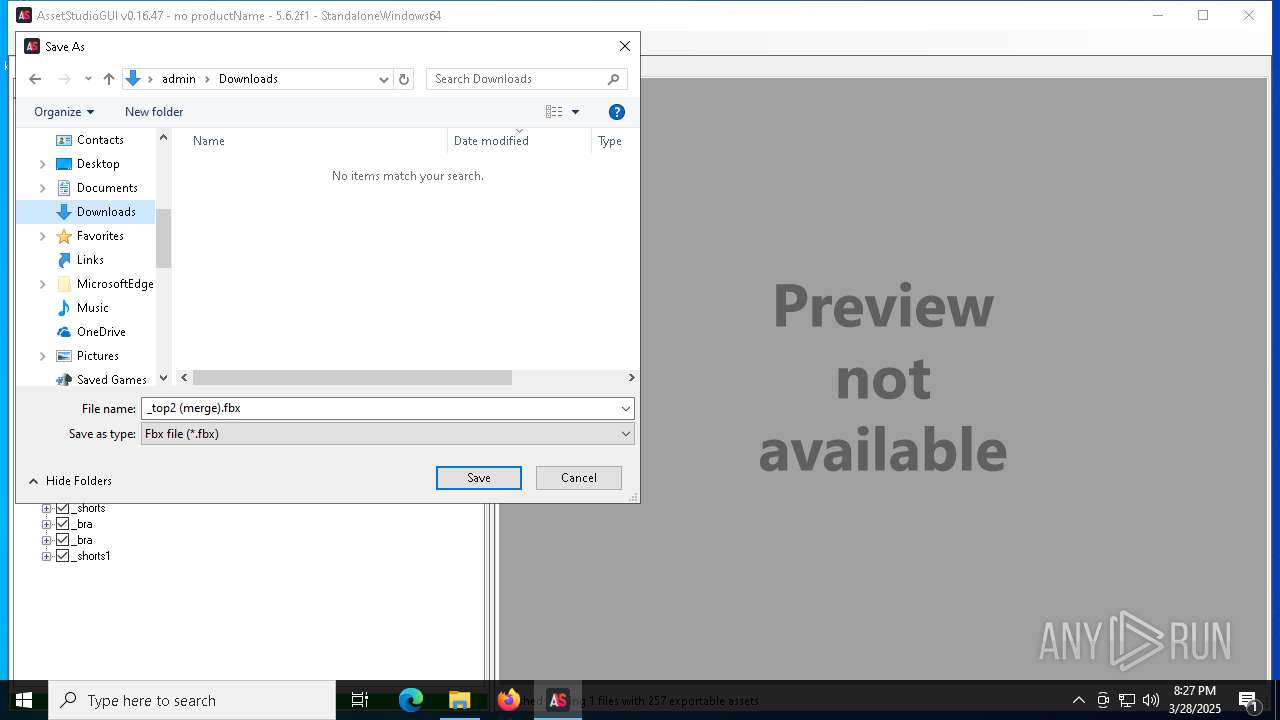
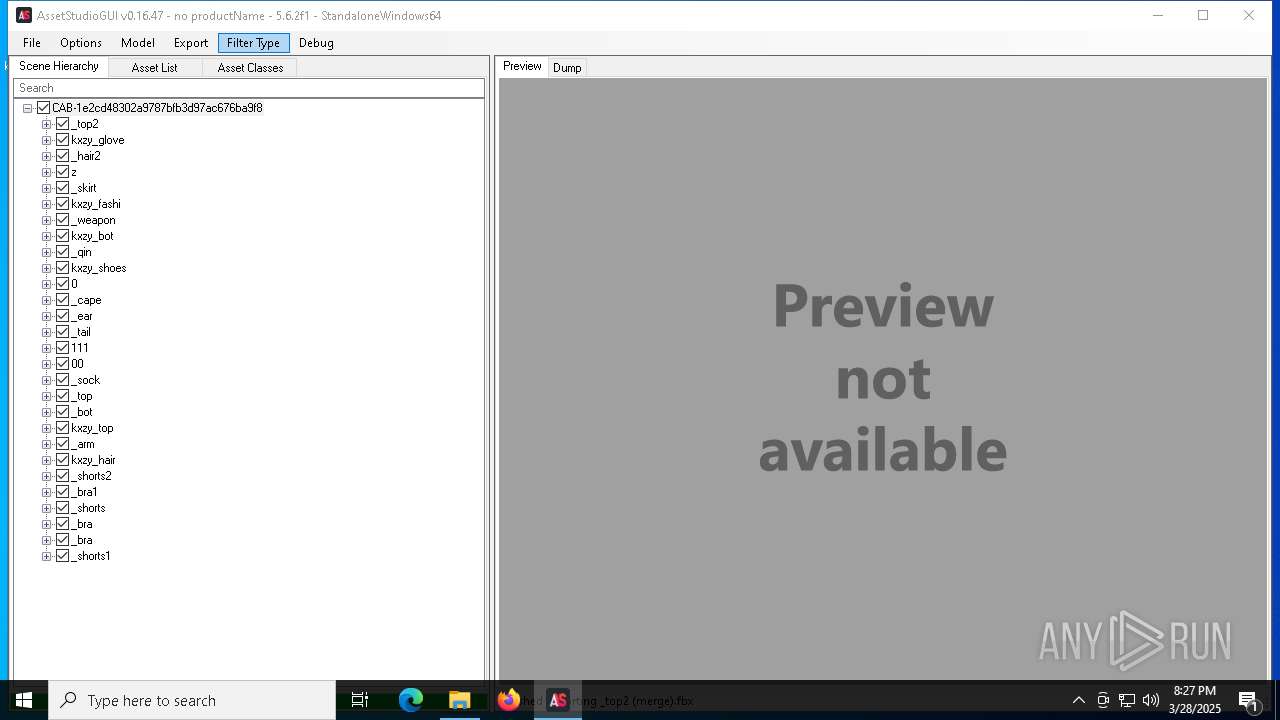
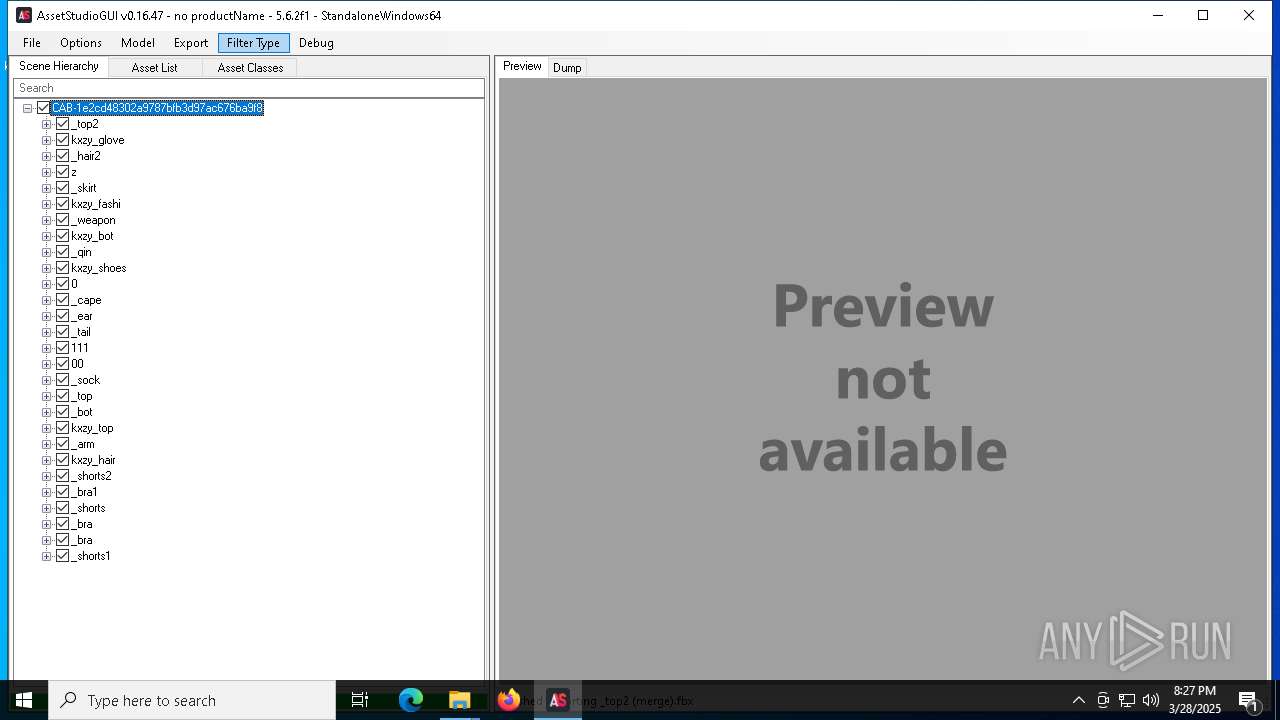
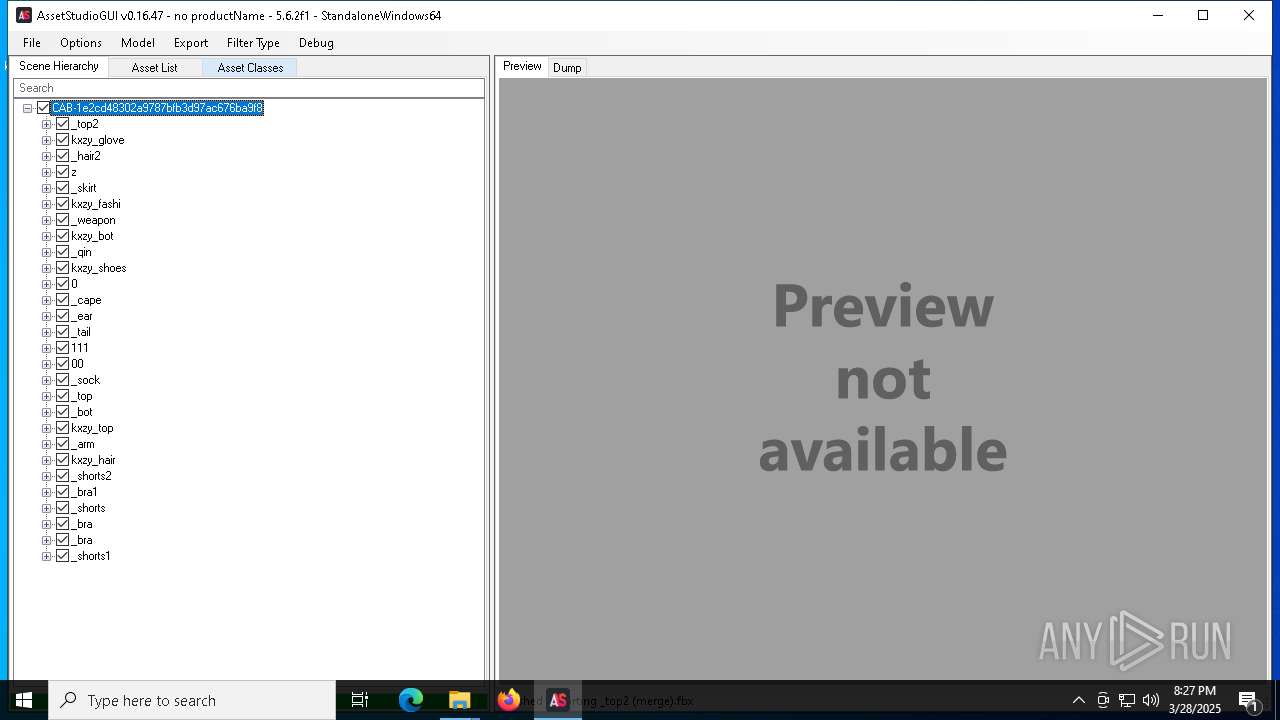
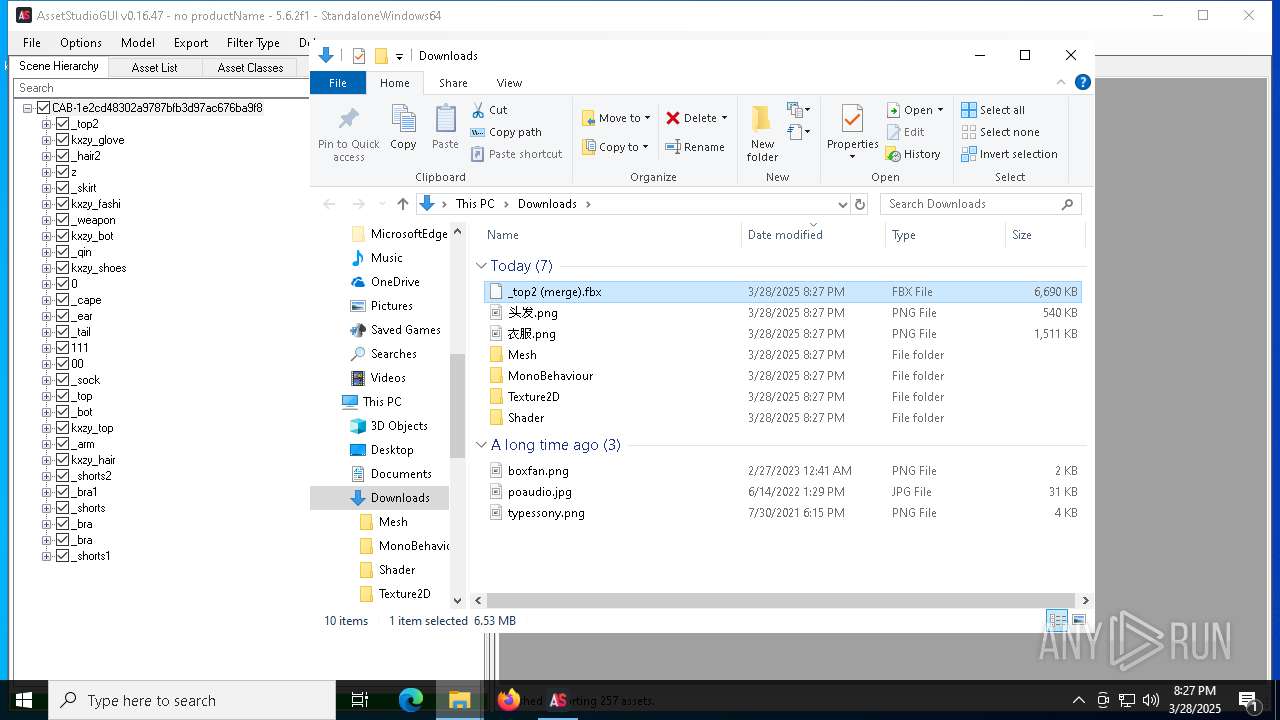
| 1676 | "C:\Users\admin\Desktop\AssetStudio.net472.v0.16.47\AssetStudioGUI.exe" | C:\Users\admin\Desktop\AssetStudio.net472.v0.16.47\AssetStudioGUI.exe | explorer.exe | ||||||||||||
User: admin Company: AssetStudioGUI Integrity Level: MEDIUM Description: AssetStudioGUI Version: 0.16.47 Modules
| |||||||||||||||
| 4608 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7272 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
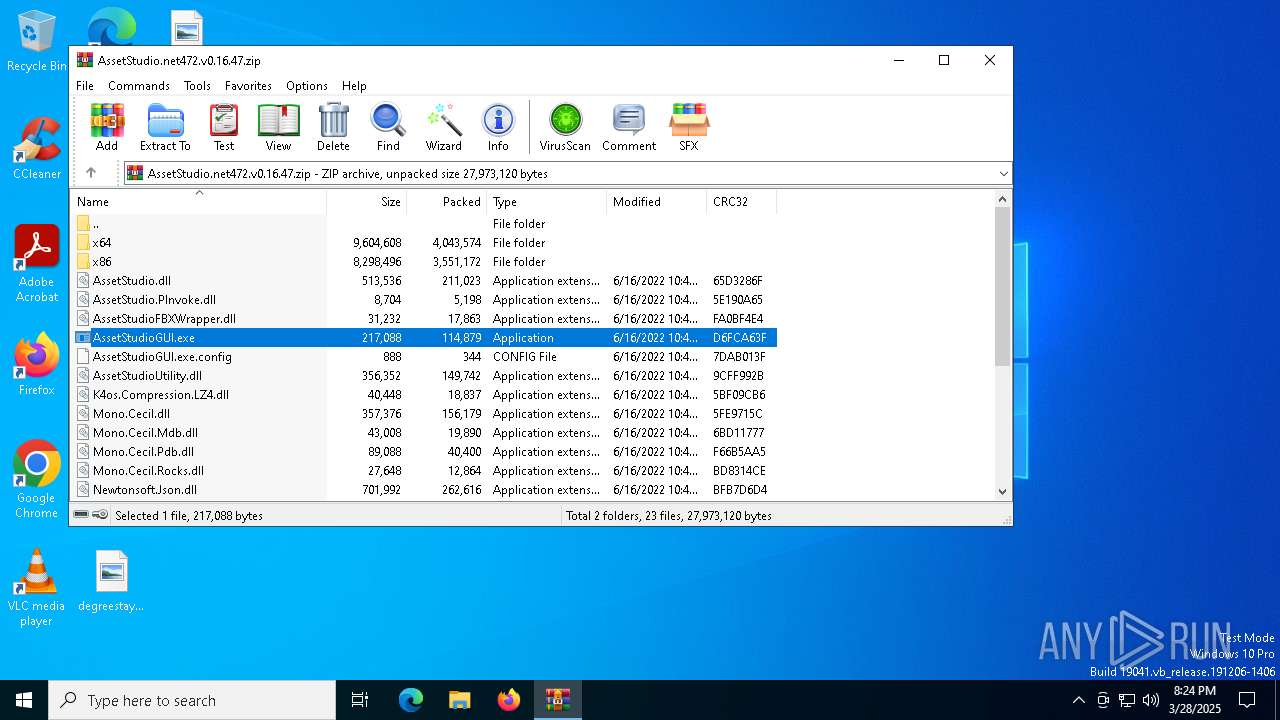
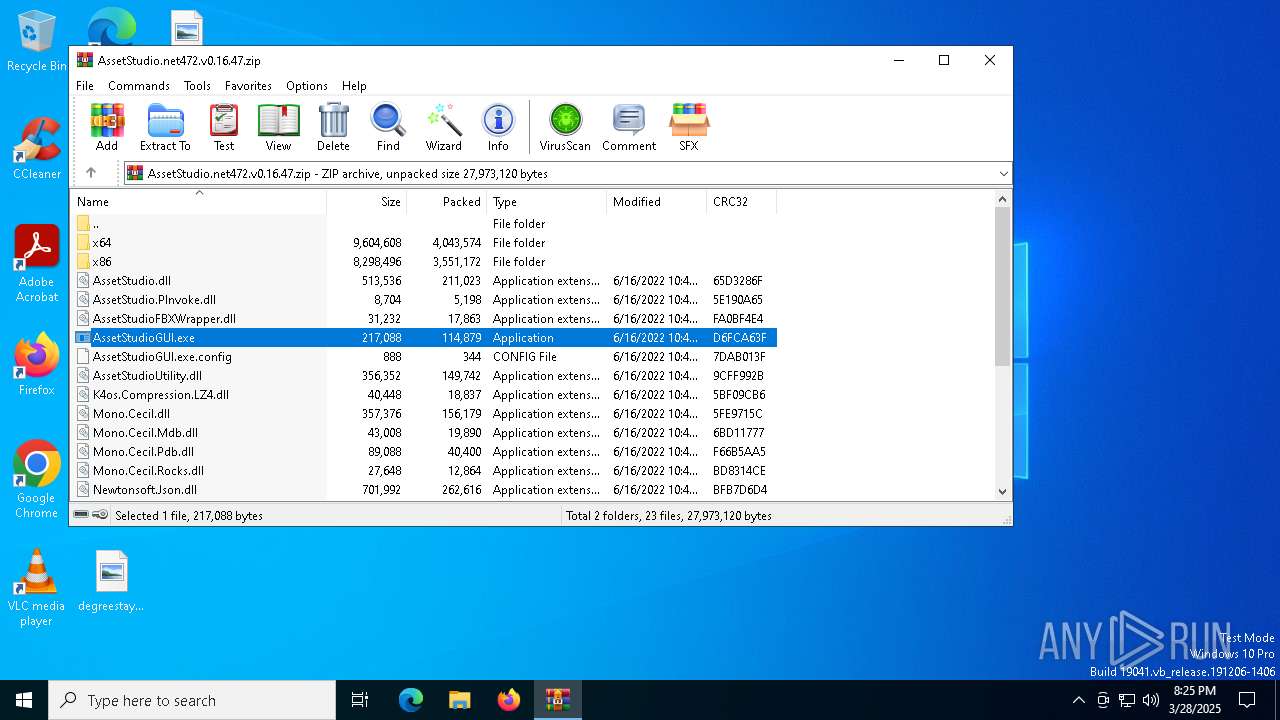
| 7324 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7444 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7520 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7556 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 644
Read events
17 408
Write events
214
Delete events
22
Modification events
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8136) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8136) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
56
Suspicious files
244
Text files
22
Unknown types
0
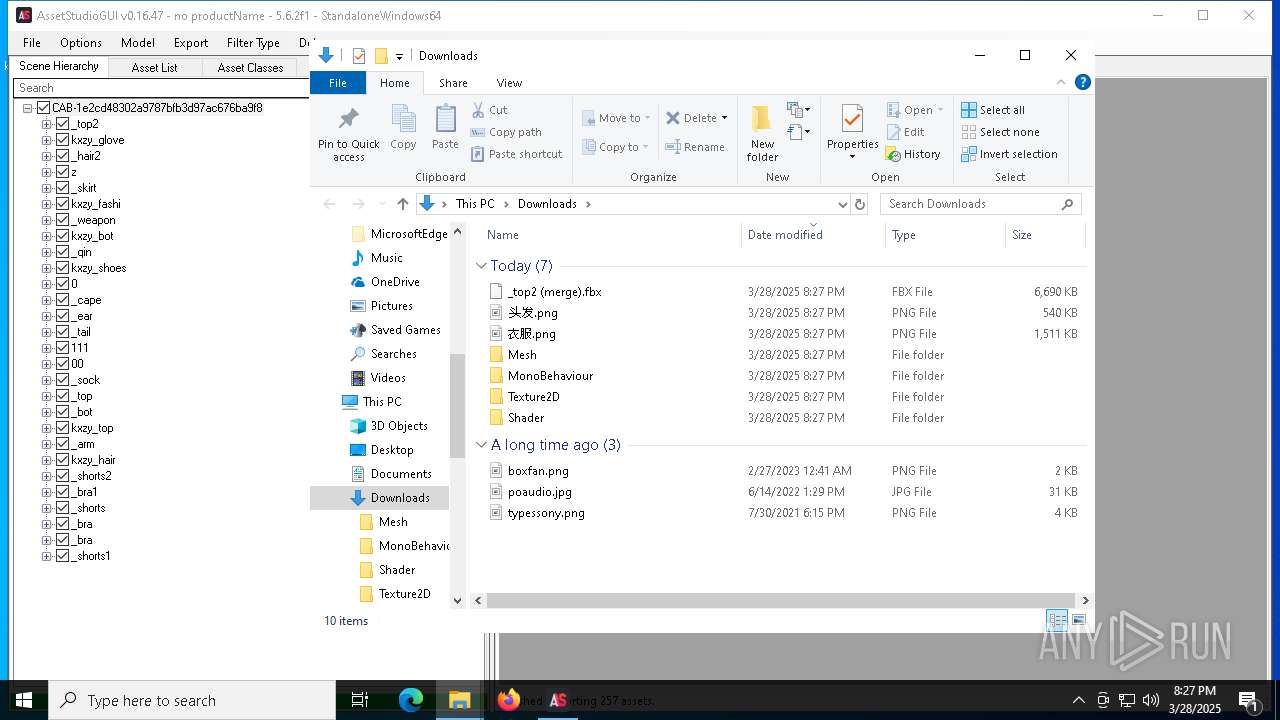
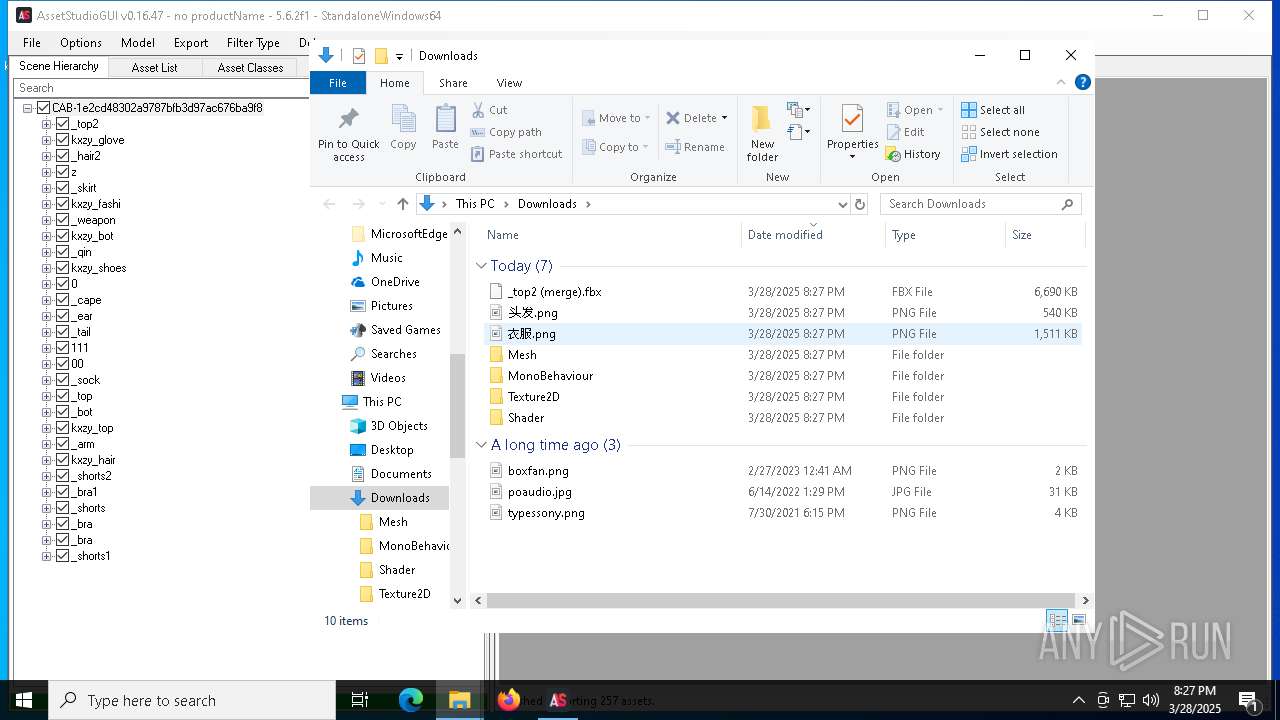
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7272 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\4b3909ea-dd26-4df2-914c-9f696480677d.down_data | — | |
MD5:— | SHA256:— | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\AssetStudio.PInvoke.dll | executable | |
MD5:4C09A52A71DFE595E2D0FC518858F916 | SHA256:2364B712984D460915772CD5E592F482B4EA7B9CC40CF04CE0338D52E69F5E12 | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\AssetStudio.dll | executable | |
MD5:6742DCC79E90F3EDA1D5DF6342546C19 | SHA256:79E1C82B483921C0C6B5C90759C418B7C7444E9754A7D8334E9B5322FC4314B1 | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\OpenTK.GLControl.dll | executable | |
MD5:35156489423C7BBB595337F64129B4A1 | SHA256:13763605654DC50B83844DCB23C4530CF8D1F443A4DADE3ABC485C1CC9A93318 | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\Mono.Cecil.Pdb.dll | executable | |
MD5:D1D8DE0281DA552F89729A148A316D3A | SHA256:4AE57A84BAF3A8191312A860ADB0AB65199C023F951BD739C6180965FD9B00D1 | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\AssetStudioUtility.dll | executable | |
MD5:4CA816201F39B1E0A8D2C445E738D6A6 | SHA256:4F05DFB689C6DEFBFE431C1EE961DDCA1B40051897BD38B389DF4FA083334B6B | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\AssetStudioFBXWrapper.dll | executable | |
MD5:44D6B367B579545C59280DE954D10A16 | SHA256:9AA8EC1188BC8C680C5E6B8FADE8504ABCDC088CE364034525BA1F5CF521EC34 | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\Mono.Cecil.dll | executable | |
MD5:272745086CB31748FBAB2347BF1B42FE | SHA256:96FA99D63CD84B76EB37505AFC603D404E12FD5CB27E8CAA1581AAD97B74AE69 | |||
| 7272 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:8A78D1AA05643657DF1D06D7CAA45C78 | SHA256:0FAF277AB6FA7DC6B72BA1F180F3BEE72EBF8608B5EED67043112E4B2CB72B95 | |||
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\AssetStudio.net472.v0.16.47\Mono.Cecil.Rocks.dll | executable | |
MD5:E479BE300CDE63F146E245E5BFBE87DC | SHA256:C1ED51D12A59EDF8B8F3D0A174A8C08DDC1B7E4032659EF983D071DB4E1D5230 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
120
DNS requests
97
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7272 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7468 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4300 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4300 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6988 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743715581&P2=404&P3=2&P4=aiohmVvB1VQvrslBhHSrr5oULKB02Iio1IQKBtkItzE0UJuBrzcb%2fn4%2bvhSz3Qpl0885xul%2b3mTUFaxh%2fl7JZw%3d%3d | unknown | — | — | whitelisted |
6988 | svchost.exe | GET | — | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743715581&P2=404&P3=2&P4=aiohmVvB1VQvrslBhHSrr5oULKB02Iio1IQKBtkItzE0UJuBrzcb%2fn4%2bvhSz3Qpl0885xul%2b3mTUFaxh%2fl7JZw%3d%3d | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6988 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743715581&P2=404&P3=2&P4=aiohmVvB1VQvrslBhHSrr5oULKB02Iio1IQKBtkItzE0UJuBrzcb%2fn4%2bvhSz3Qpl0885xul%2b3mTUFaxh%2fl7JZw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
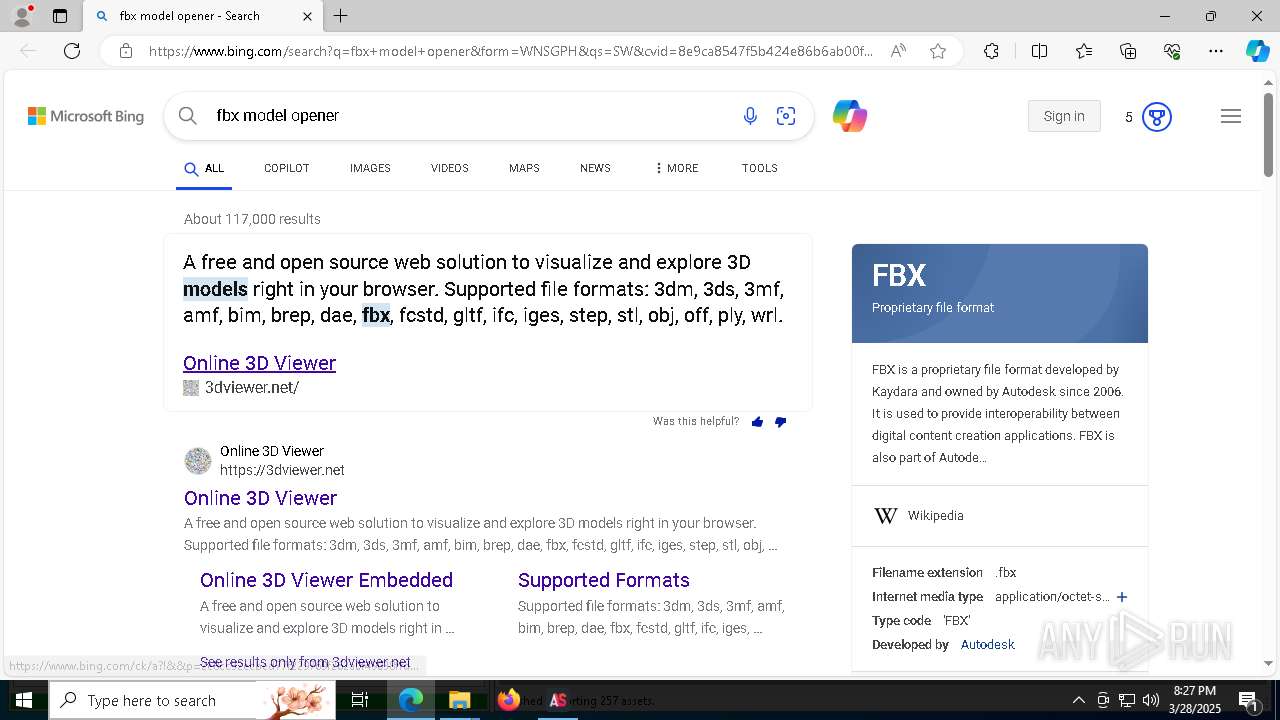
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |