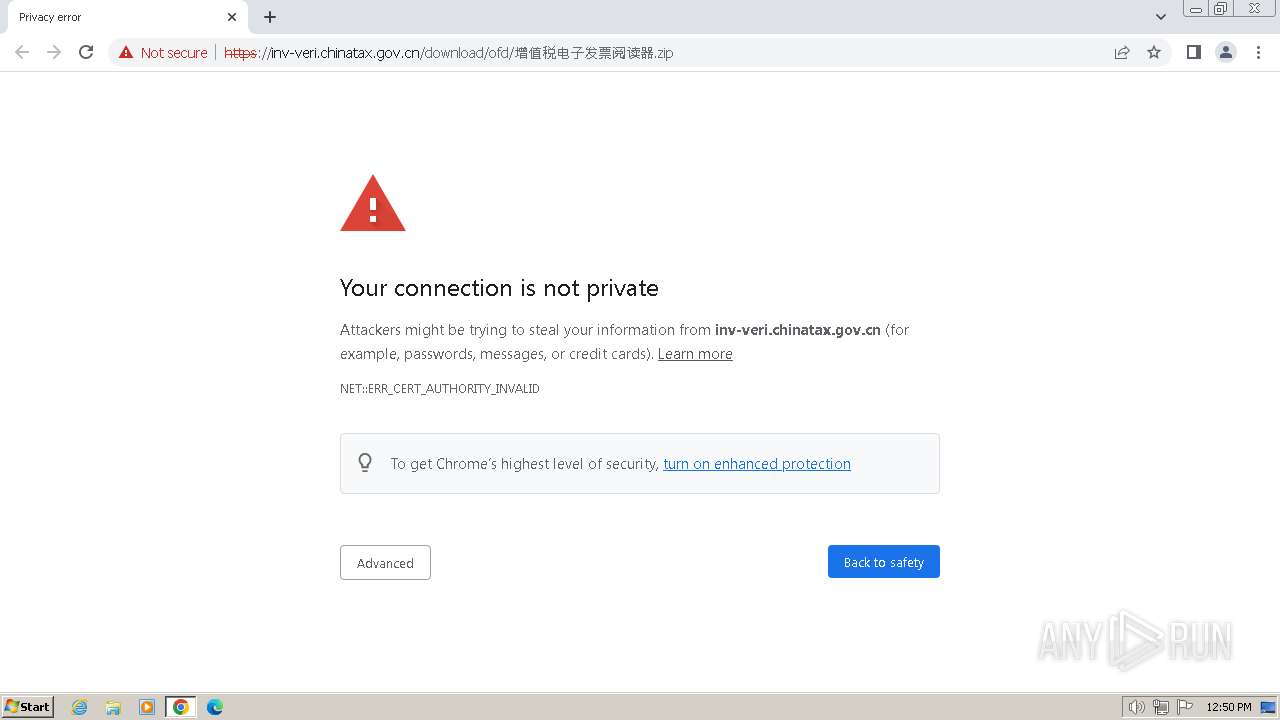
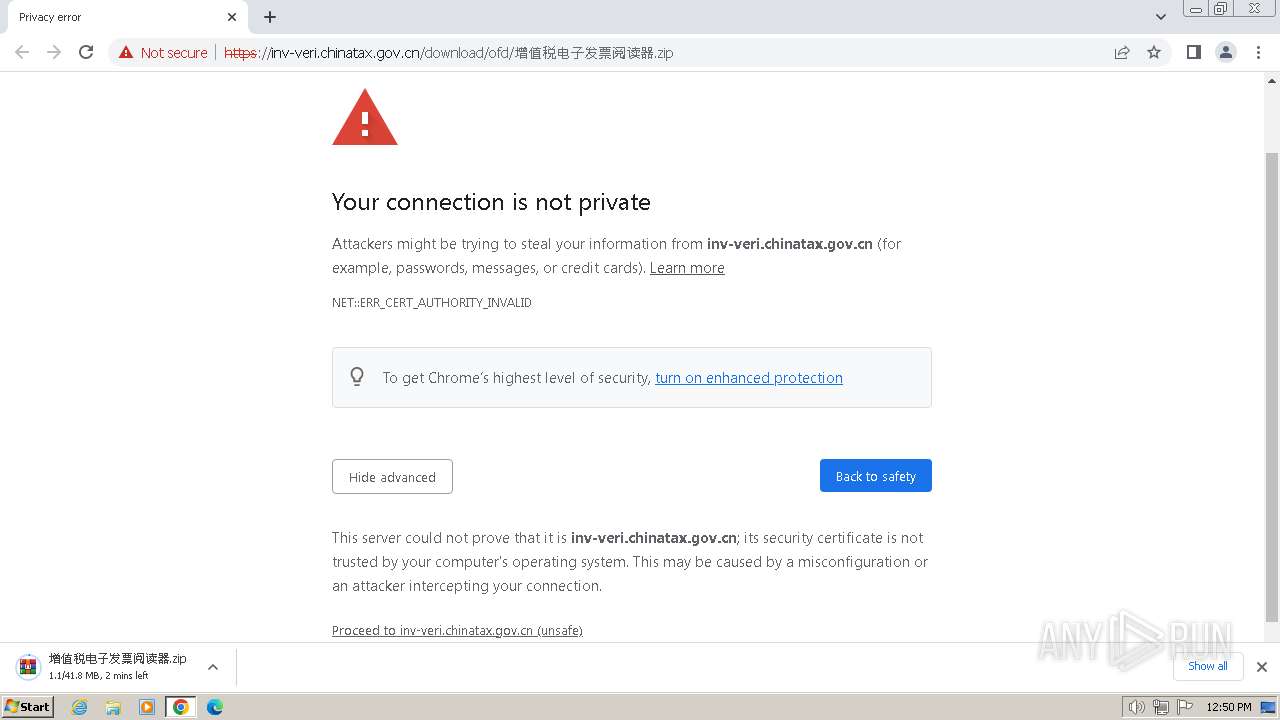
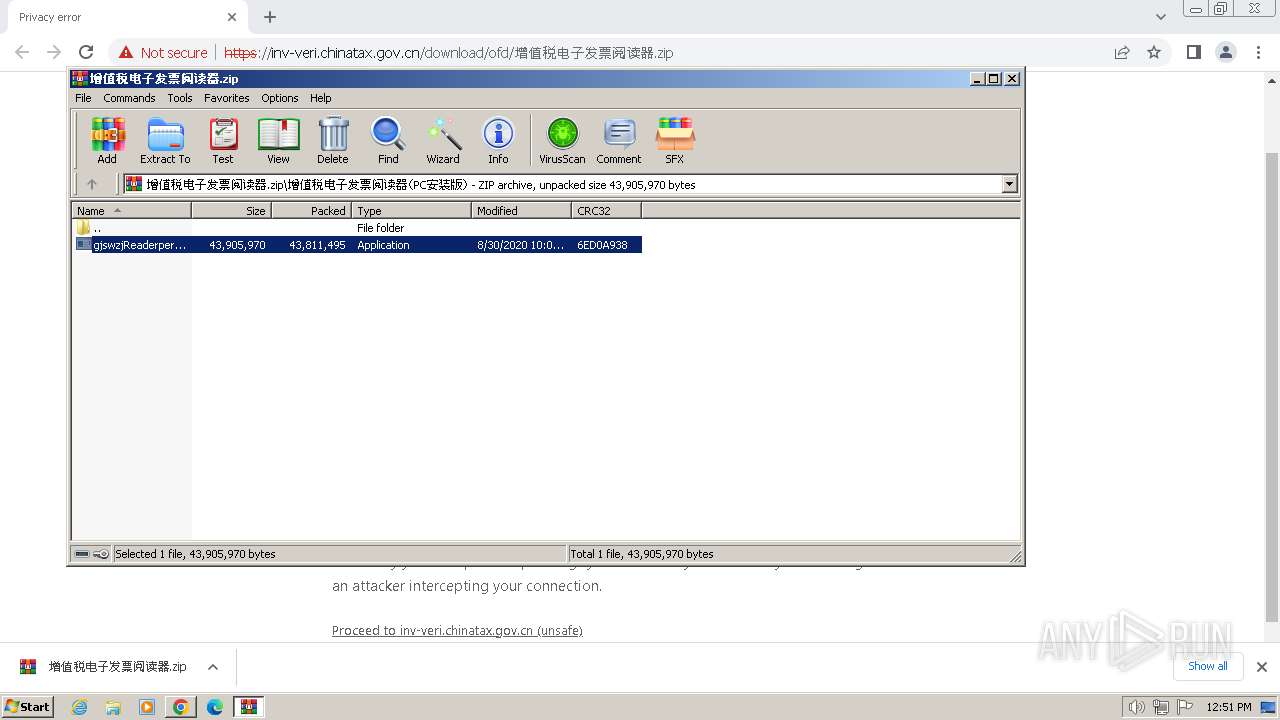
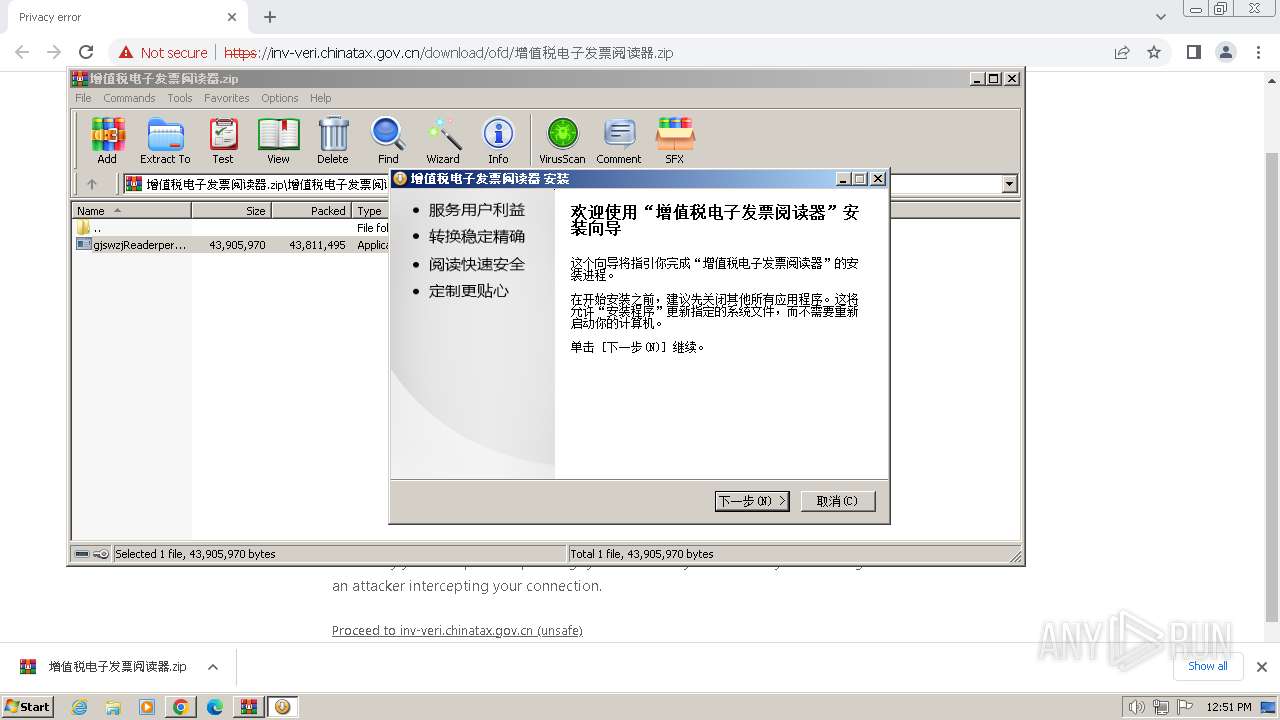
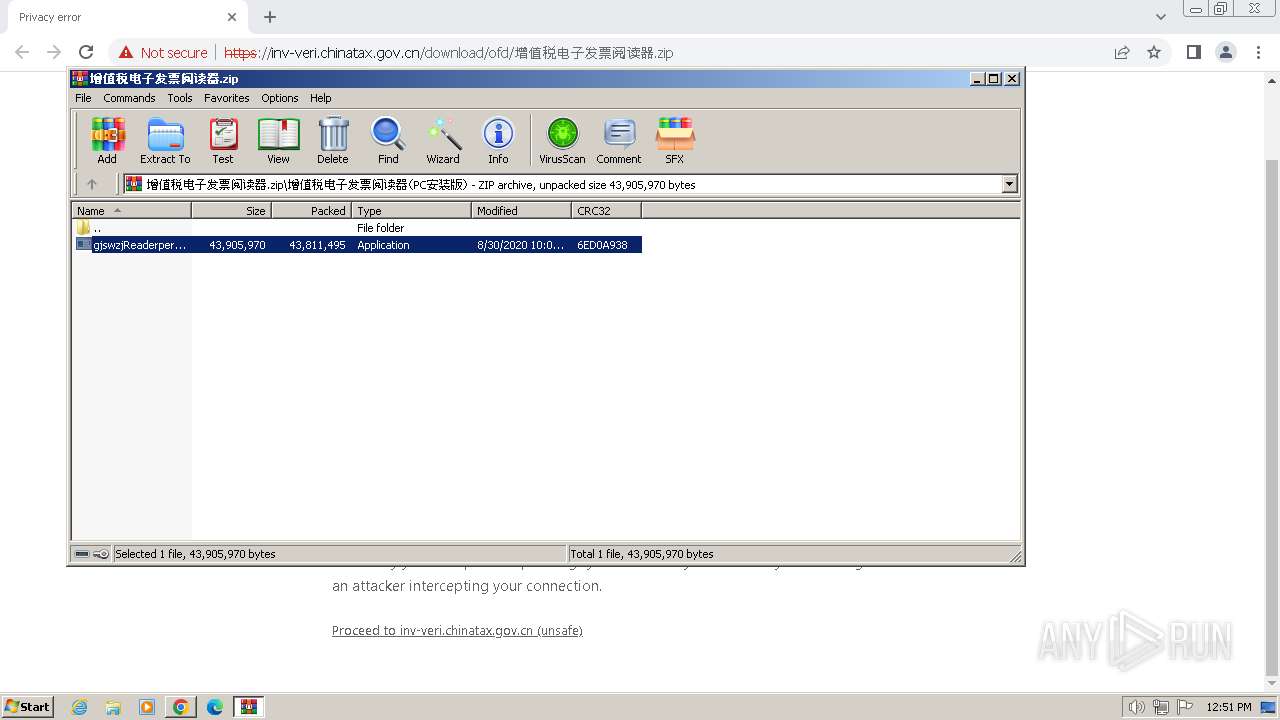
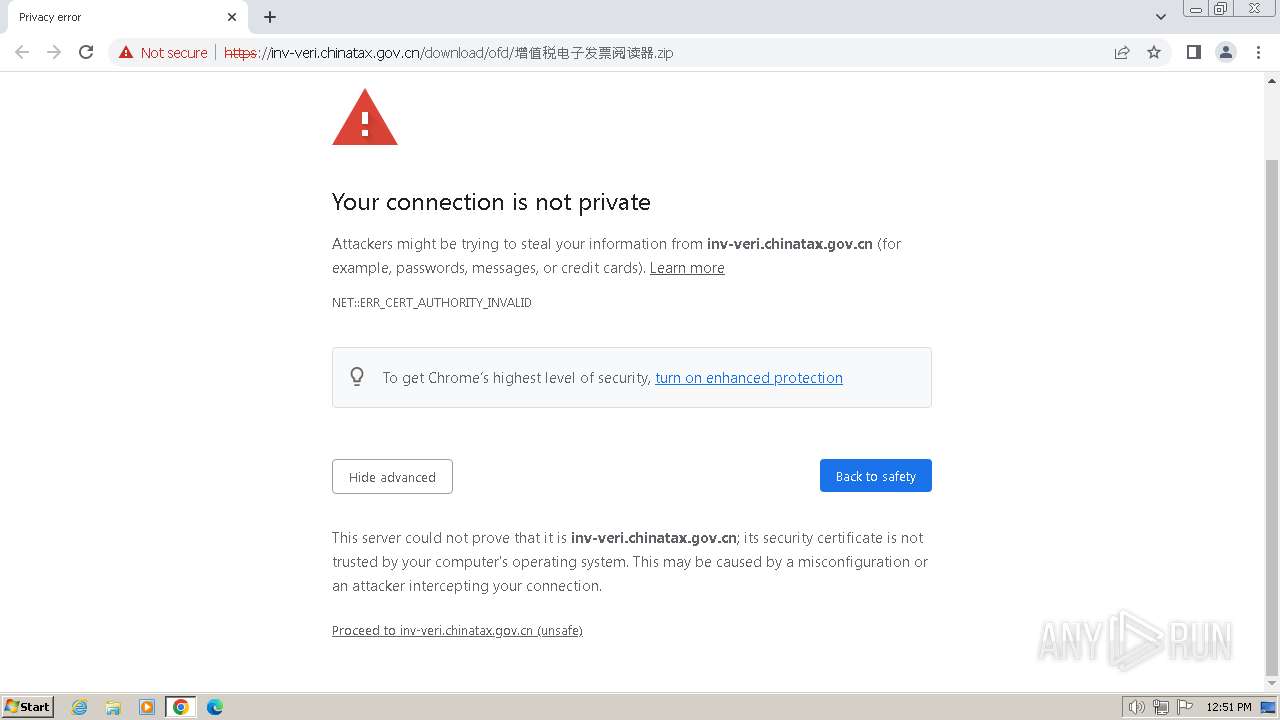
| URL: | https://inv-veri.chinatax.gov.cn/download/ofd/%E5%A2%9E%E5%80%BC%E7%A8%8E%E7%94%B5%E5%AD%90%E5%8F%91%E7%A5%A8%E9%98%85%E8%AF%BB%E5%99%A8.zip |
| Full analysis: | https://app.any.run/tasks/ca1b0f23-468d-4de5-87db-23df48b47977 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2024, 11:50:16 |
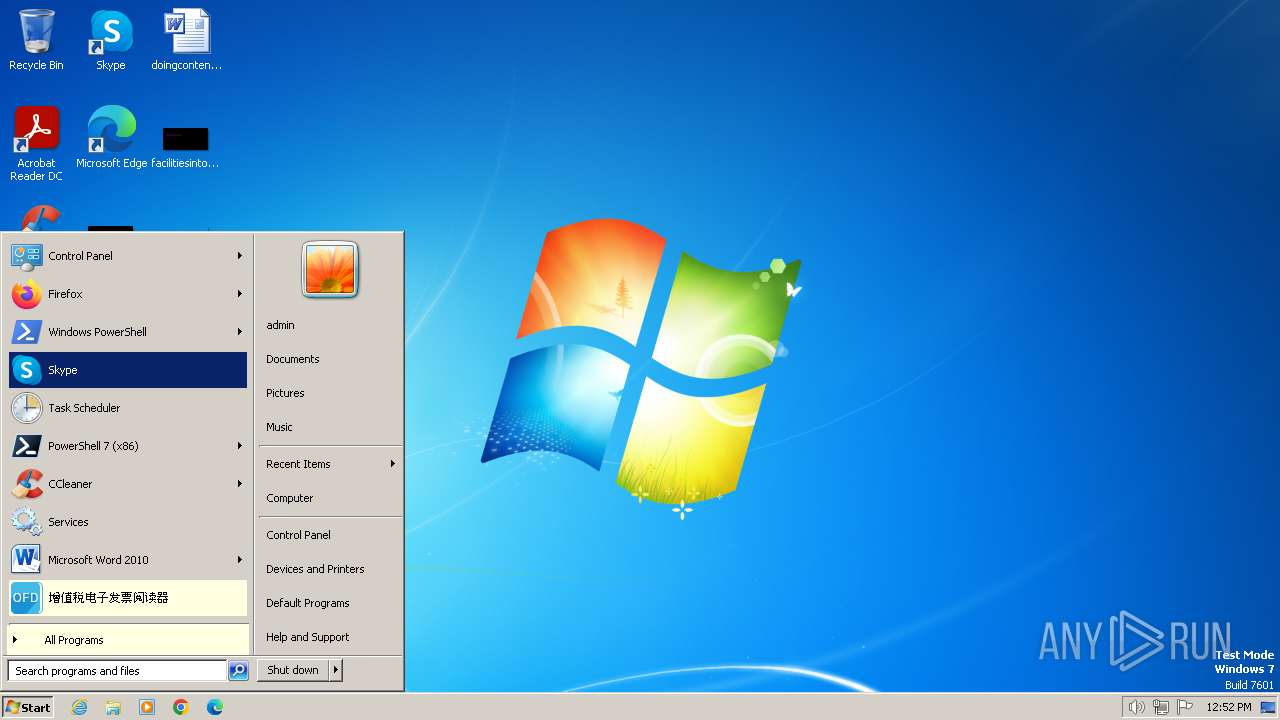
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D30D1441923C7FBB4AF35F1CCF75D574 |
| SHA1: | 353347E651D9208E3DF4746809B4312B48AA9997 |
| SHA256: | A463F5671EE80242D2ED8B7F484E9757CD8E322D6556DF038490AFB6B1C24705 |
| SSDEEP: | 3:N8OILHHCKTBKLXRFlXk/AX56VXZ33UFxcPAg2qA3Jc:2OILHibbRF9qZUstA+ |
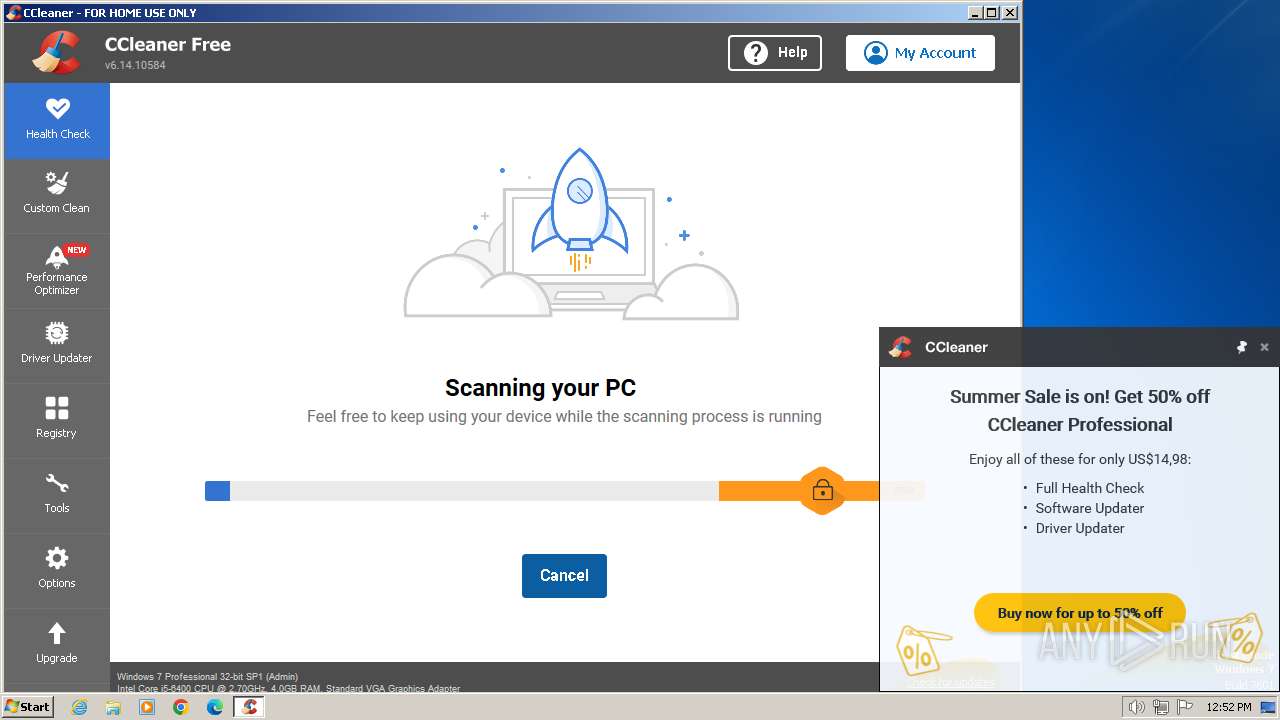
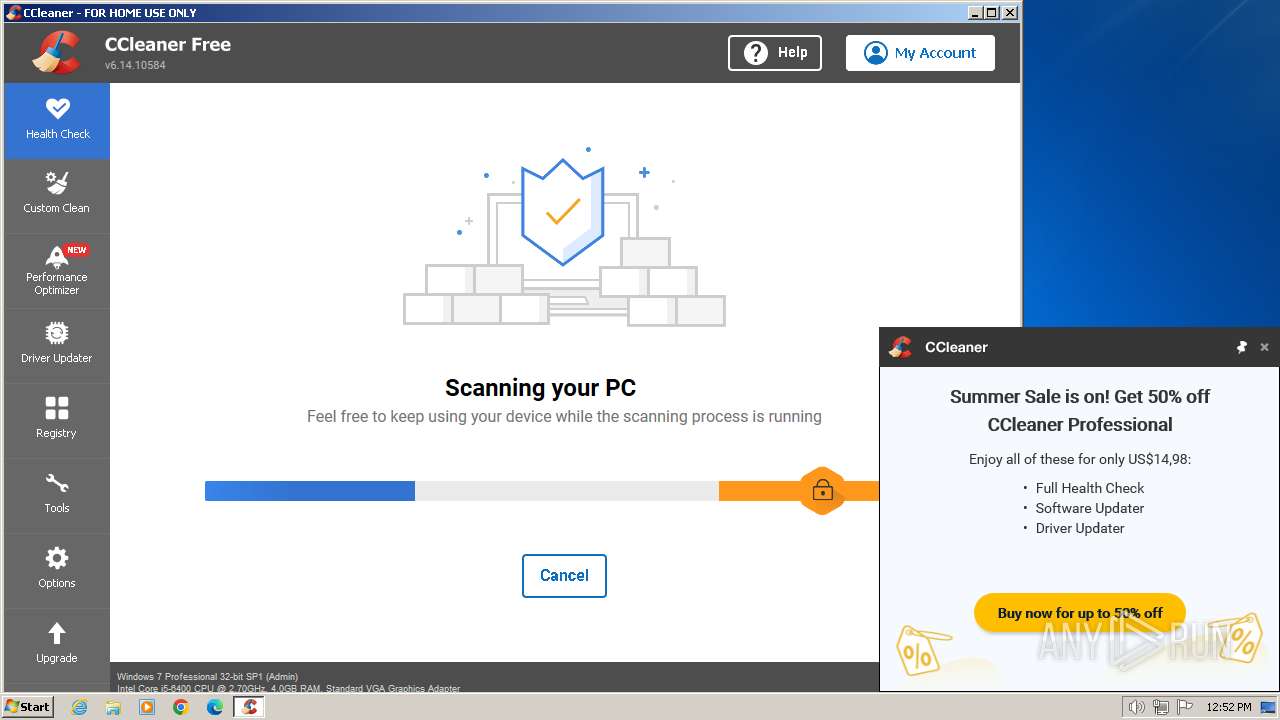
MALICIOUS
Drops the executable file immediately after the start
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Steals credentials from Web Browsers
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- taskhost.exe (PID: 1488)
- CCleaner.exe (PID: 2480)
Actions looks like stealing of personal data
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Uses Task Scheduler to autorun other applications
- ns4331.tmp (PID: 1904)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
The process creates files with name similar to system file names
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
Executable content was dropped or overwritten
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2916)
- CCleaner.exe (PID: 2480)
Starts application with an unusual extension
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
Uses TASKKILL.EXE to kill process
- ns1D41.tmp (PID: 2964)
- ns2986.tmp (PID: 580)
- ns2A72.tmp (PID: 3604)
- ns2B4D.tmp (PID: 3524)
- ns2CA7.tmp (PID: 3276)
- ns2E6E.tmp (PID: 680)
- ns2D83.tmp (PID: 3168)
- ns2EEC.tmp (PID: 1264)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 2672)
The process drops C-runtime libraries
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
Process drops legitimate windows executable
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Changes internet zones settings
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
Creates a software uninstall entry
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
The process executes via Task Scheduler
- CCleaner.exe (PID: 2480)
Reads Internet Explorer settings
- CCleaner.exe (PID: 2480)
Checks Windows Trust Settings
- CCleaner.exe (PID: 2480)
Searches for installed software
- CCleaner.exe (PID: 2480)
Reads settings of System Certificates
- CCleaner.exe (PID: 2480)
Reads the date of Windows installation
- CCleaner.exe (PID: 2480)
Reads the Internet Settings
- CCleaner.exe (PID: 2480)
The process verifies whether the antivirus software is installed
- CCleaner.exe (PID: 2480)
Reads Microsoft Outlook installation path
- CCleaner.exe (PID: 2480)
Checks for external IP
- CCleaner.exe (PID: 2480)
Executes as Windows Service
- taskhost.exe (PID: 1488)
Starts application from unusual location
- CCleaner.exe (PID: 2480)
INFO
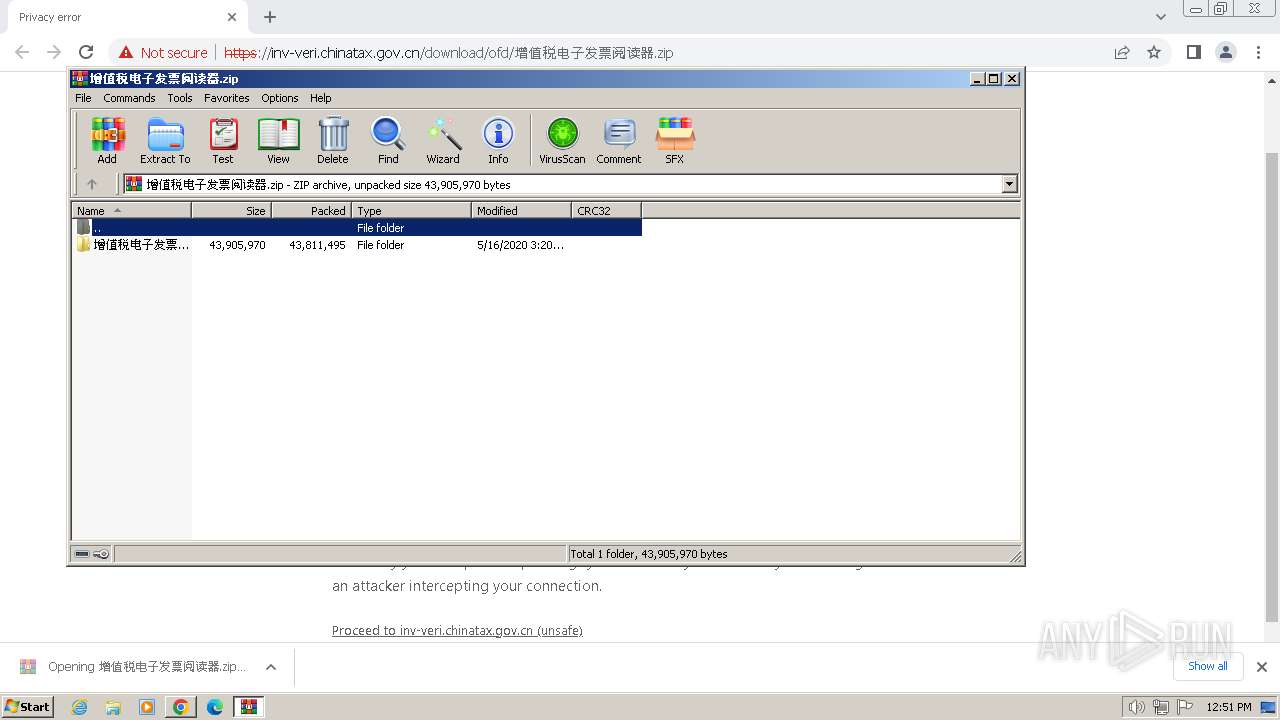
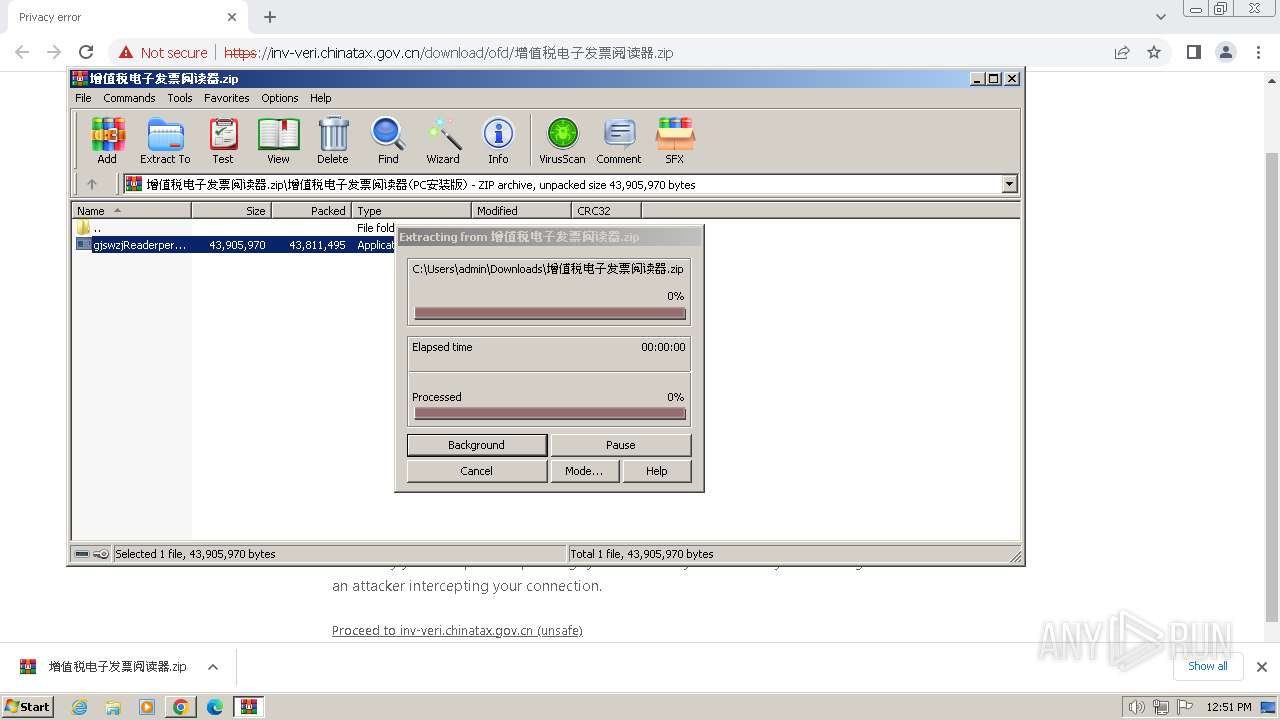
The process uses the downloaded file
- chrome.exe (PID: 4028)
- WinRAR.exe (PID: 2916)
Application launched itself
- chrome.exe (PID: 3368)
Drops the executable file immediately after the start
- chrome.exe (PID: 3368)
Reads the computer name
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 3972)
- CCleaner.exe (PID: 2480)
Create files in a temporary directory
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
Checks supported languages
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- ns1D41.tmp (PID: 2964)
- ns2986.tmp (PID: 580)
- ns2A72.tmp (PID: 3604)
- ns2B4D.tmp (PID: 3524)
- ns2C29.tmp (PID: 828)
- ns2CA7.tmp (PID: 3276)
- ns2D83.tmp (PID: 3168)
- ns2E6E.tmp (PID: 680)
- ns2EEC.tmp (PID: 1264)
- CCleaner.exe (PID: 3972)
- CCleaner.exe (PID: 2480)
- ns4331.tmp (PID: 1904)
Creates files in the program directory
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Reads the machine GUID from the registry
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Creates files or folders in the user directory
- gjswzjReaderper-3.0.20.0830-setup.exe (PID: 1228)
- CCleaner.exe (PID: 2480)
Manual execution by a user
- CCleaner.exe (PID: 3972)
Reads Environment values
- CCleaner.exe (PID: 3972)
- CCleaner.exe (PID: 2480)
Reads CPU info
- CCleaner.exe (PID: 2480)
Reads product name
- CCleaner.exe (PID: 2480)
Reads the software policy settings
- CCleaner.exe (PID: 2480)
Checks proxy server information
- CCleaner.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
41
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2986.tmp" taskkill /f /t /im AppUpdate.exe | C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2986.tmp | — | gjswzjReaderper-3.0.20.0830-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1056 --field-trial-handle=1132,i,17845075254634496673,16082517789830100692,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2E6E.tmp" taskkill /f /t /im AppUpdate.exe | C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2E6E.tmp | — | gjswzjReaderper-3.0.20.0830-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 828 | "C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2C29.tmp" schtasks /delete /tn "gjswzjReader" /f | C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2C29.tmp | — | gjswzjReaderper-3.0.20.0830-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2956 --field-trial-handle=1132,i,17845075254634496673,16082517789830100692,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=516 --field-trial-handle=1132,i,17845075254634496673,16082517789830100692,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2916.814\增值税电子发票阅读器(PC安装版)\gjswzjReaderper-3.0.20.0830-setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2916.814\增值税电子发票阅读器(PC安装版)\gjswzjReaderper-3.0.20.0830-setup.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 增值税电子发票阅读器 Exit code: 0 Version: 3.0.20.0830 Modules
| |||||||||||||||
| 1264 | "C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2EEC.tmp" taskkill /f /t /im gjswzjReader.exe | C:\Users\admin\AppData\Local\Temp\nsg1D01.tmp\ns2EEC.tmp | — | gjswzjReaderper-3.0.20.0830-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 1392 | taskkill /f /t /im gjswzjReader.exe | C:\Windows\System32\taskkill.exe | — | ns1D41.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | "taskhost.exe" | C:\Windows\System32\taskhost.exe | services.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
37 304
Read events
36 912
Write events
304
Delete events
88
Modification events
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
76
Suspicious files
109
Text files
69
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4ede6.TMP | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF4f0d4.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF4ef8c.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF4f46e.TMP | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF4f0f4.TMP | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF50130.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
52
DNS requests
45
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2108 | chrome.exe | GET | 204 | 142.250.186.35:80 | http://www.gstatic.com/generate_204 | US | — | — | unknown |
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | GB | — | — | unknown |
1372 | svchost.exe | GET | 200 | 88.221.132.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 1.01 Kb | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | GB | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.18.173.151:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NO | binary | 973 b | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 6.55 Kb | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.0 Kb | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.93 Kb | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 79.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3368 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2108 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
2108 | chrome.exe | 116.179.52.55:443 | inv-veri.chinatax.gov.cn | CHINA UNICOM China169 Backbone | CN | unknown |
2108 | chrome.exe | 142.250.186.35:80 | www.gstatic.com | GOOGLE | US | whitelisted |
2108 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
inv-veri.chinatax.gov.cn |
| unknown |
www.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
2480 | CCleaner.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
Process | Message |
|---|---|
CCleaner.exe | [2024-06-21 11:52:04.308] [error ] [settings ] [ 2480: 840] [6000C4: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | [2024-06-21 11:52:05.590] [error ] [settings ] [ 2480: 2692] [9434E9: 359] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | [2024-06-21 11:52:05.605] [error ] [Burger ] [ 2480: 2692] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | [2024-06-21 11:52:05.605] [error ] [Burger ] [ 2480: 2692] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|