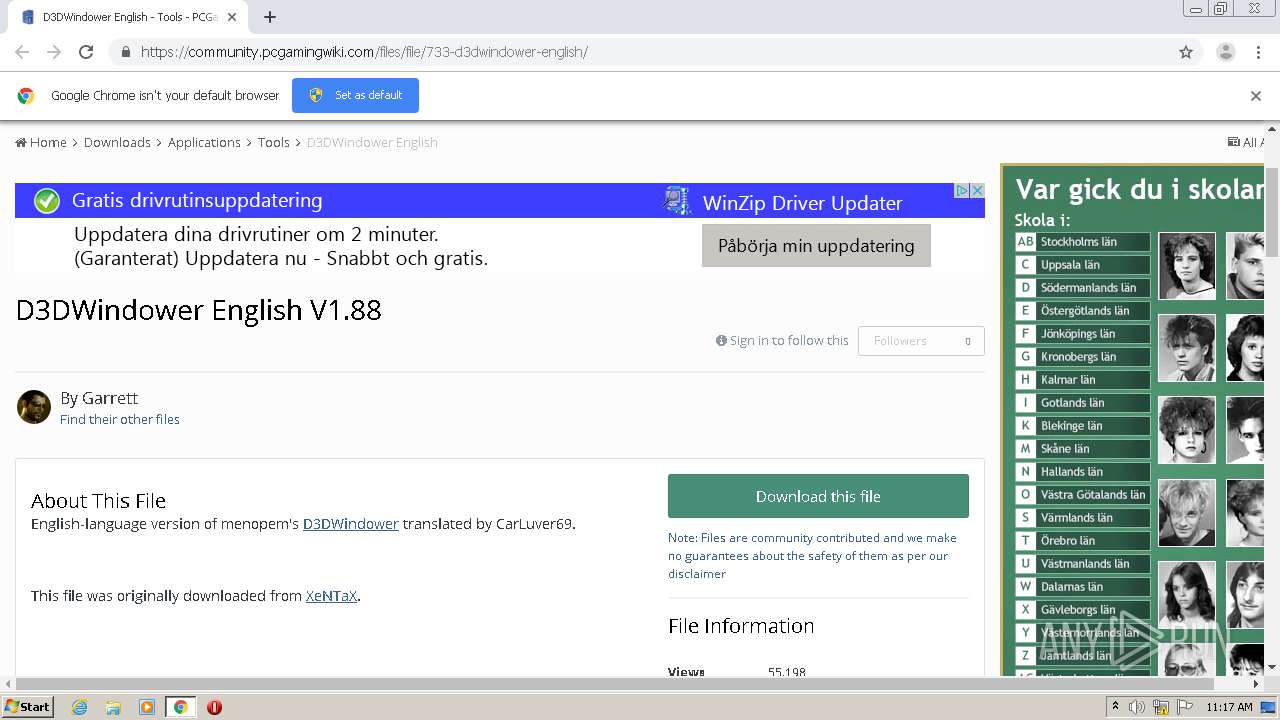
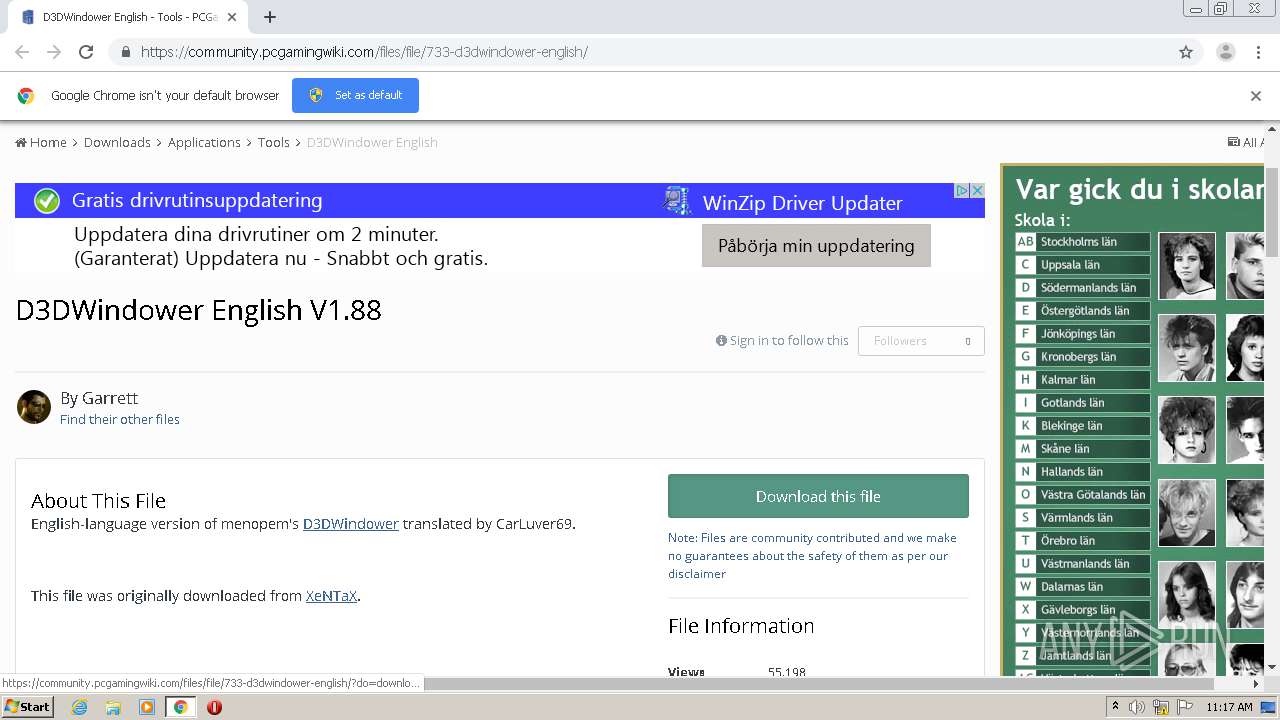
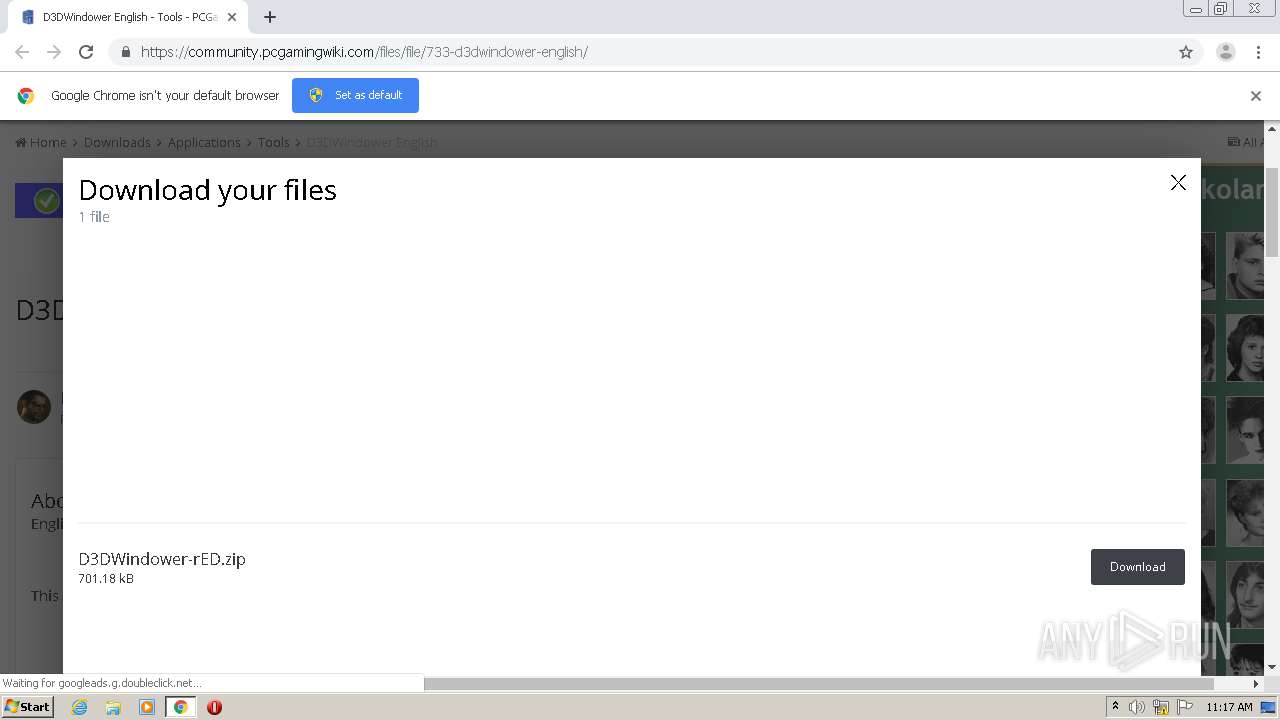
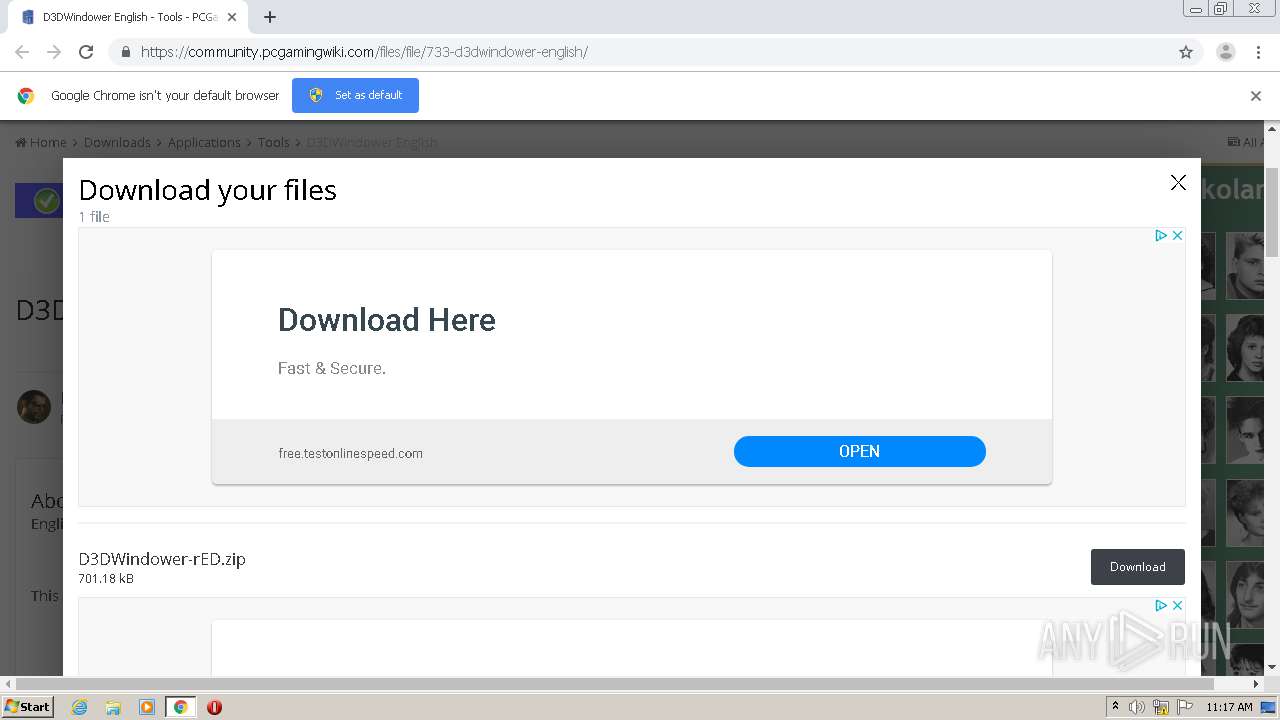
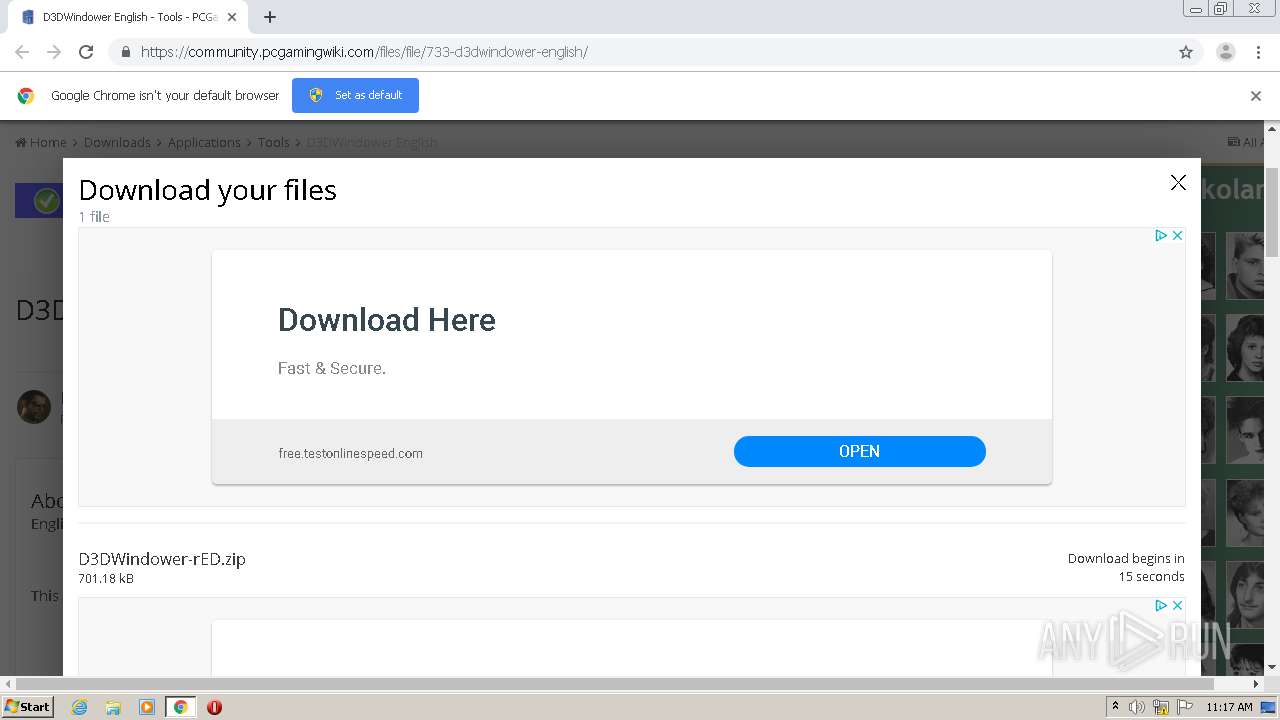
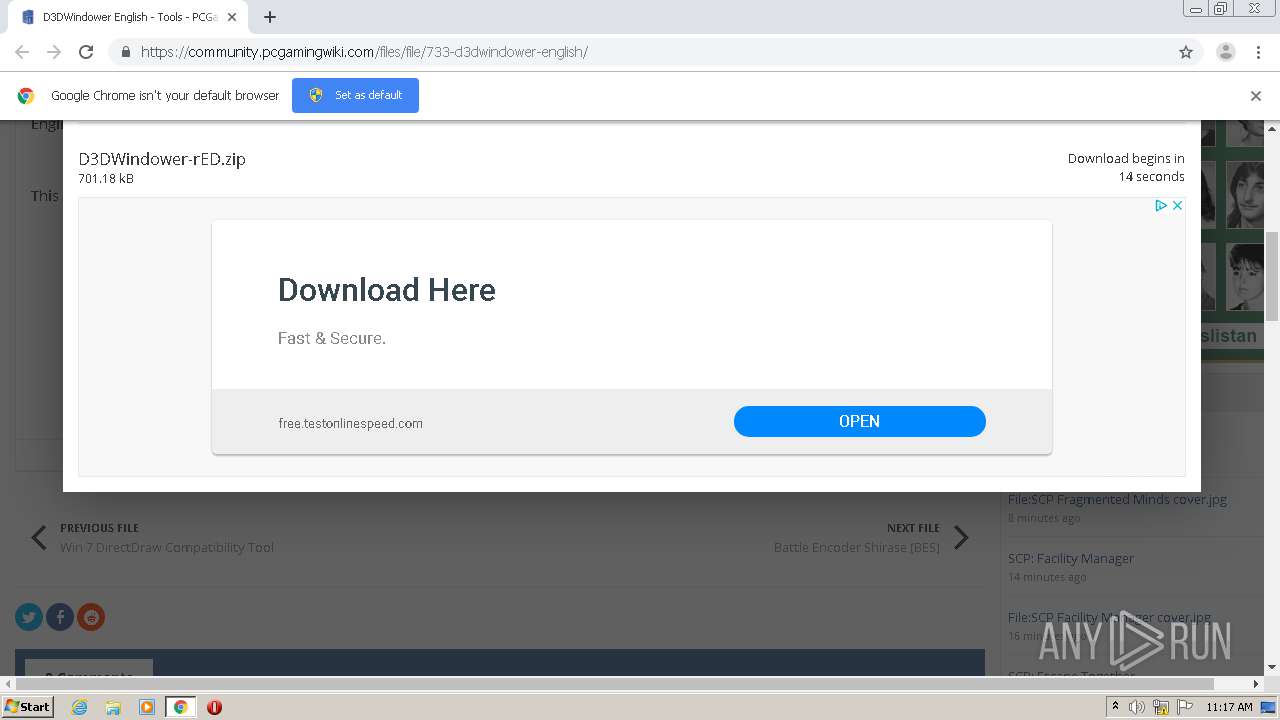
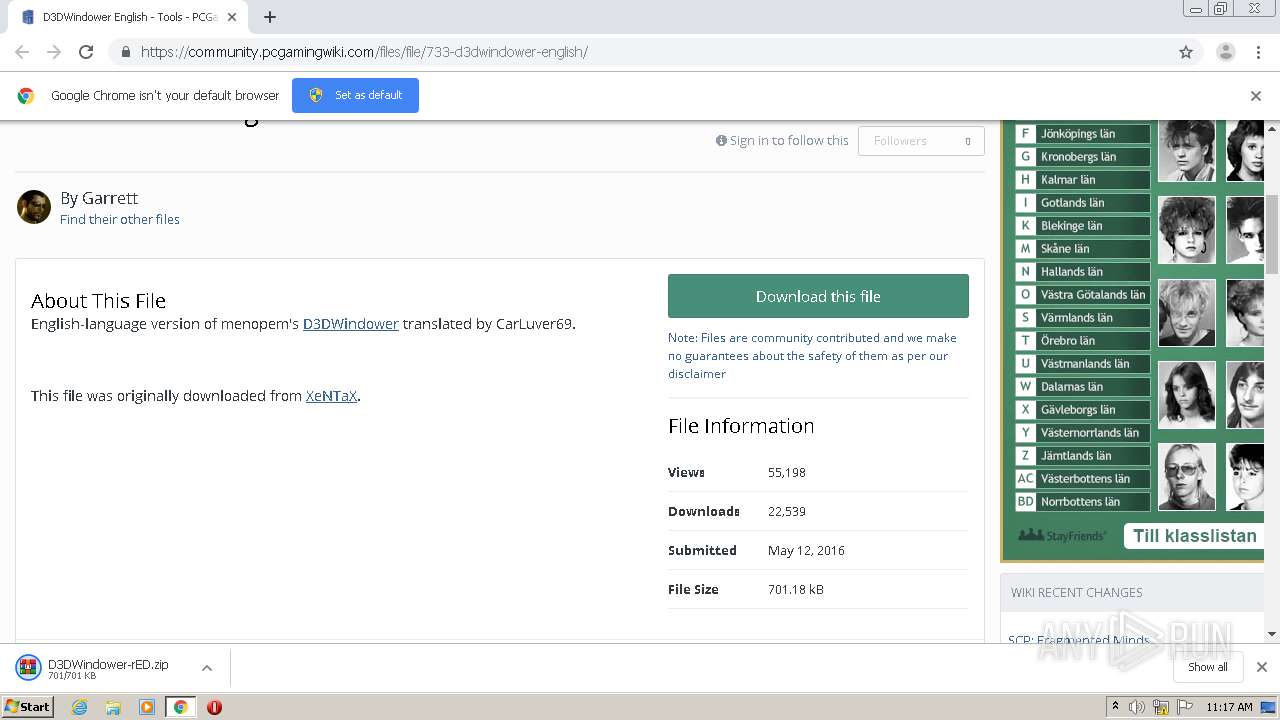
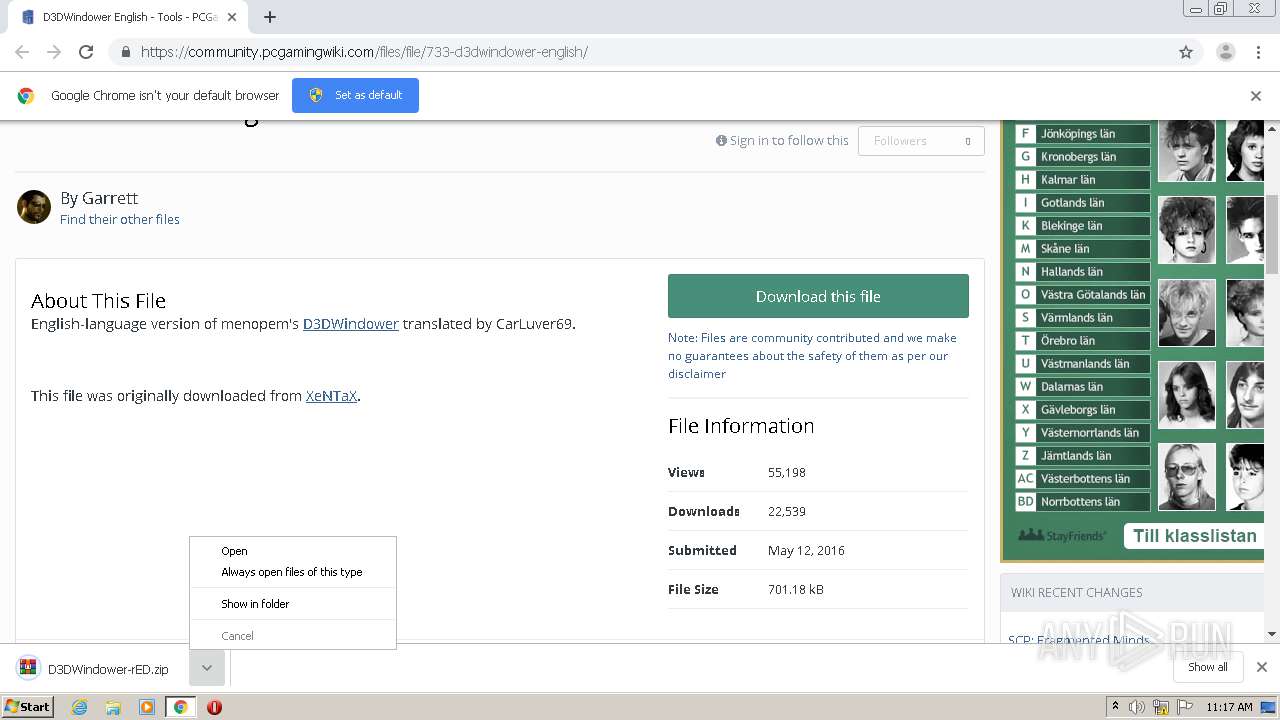
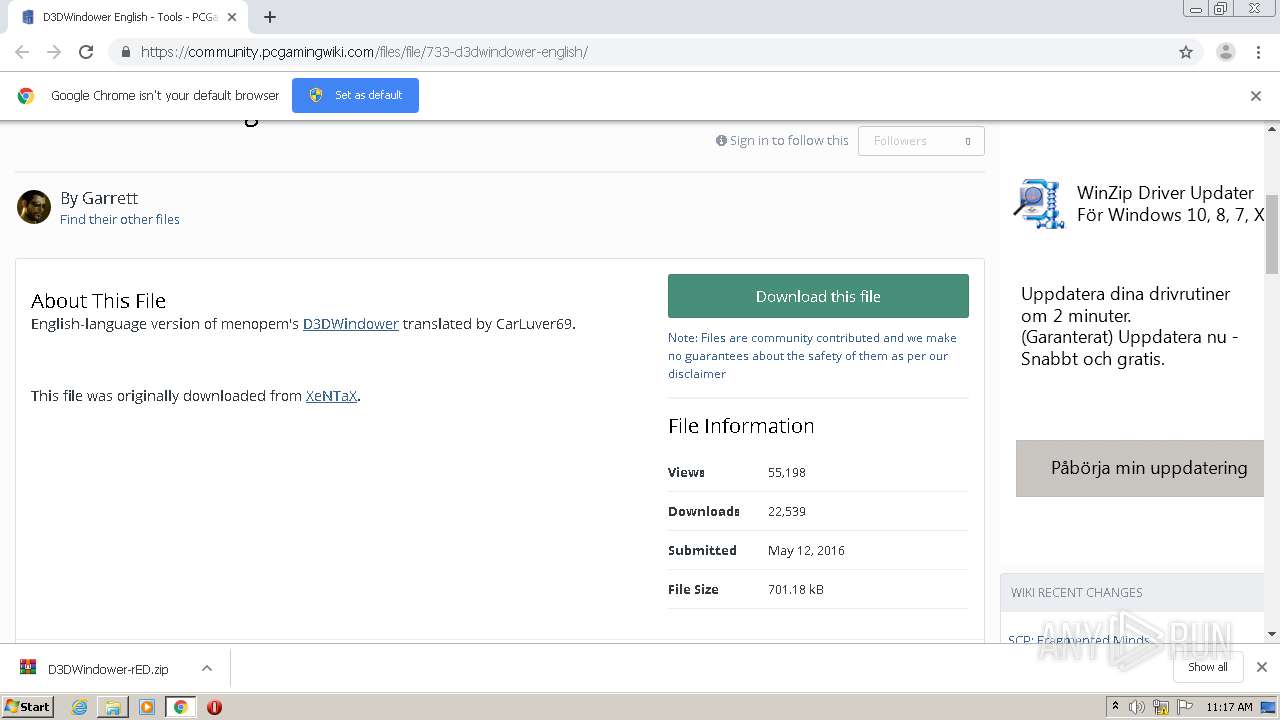
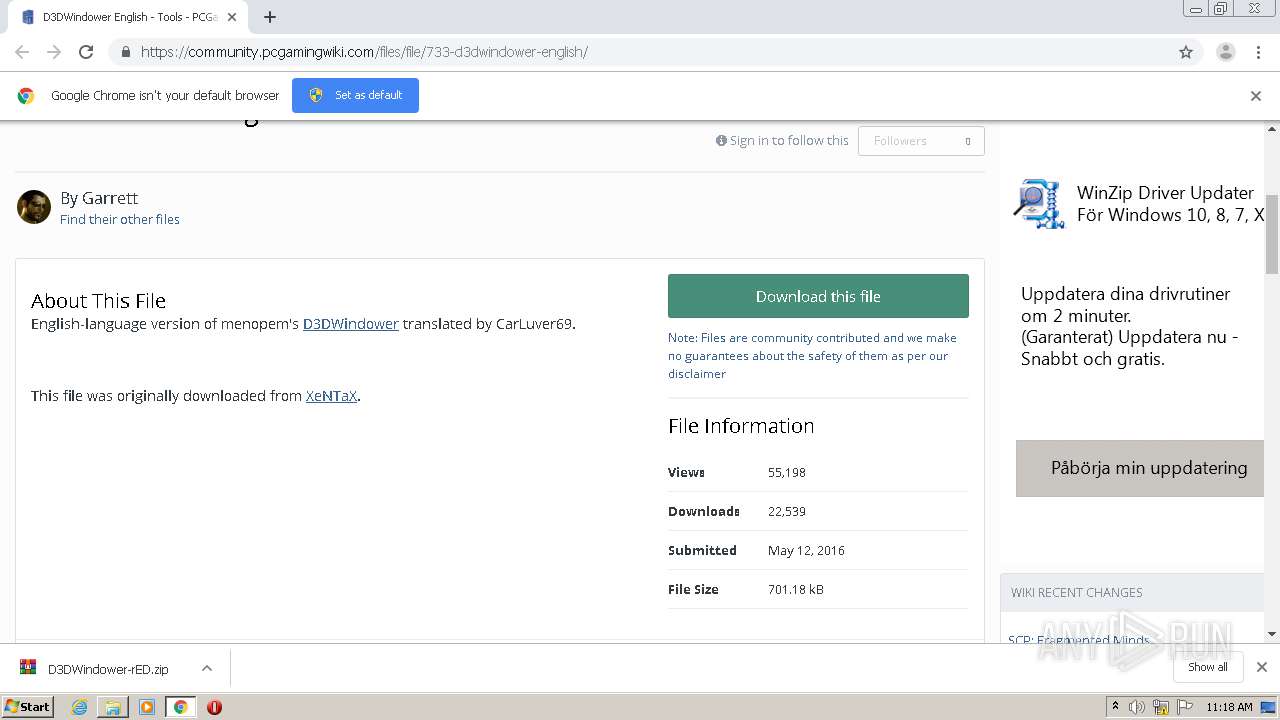
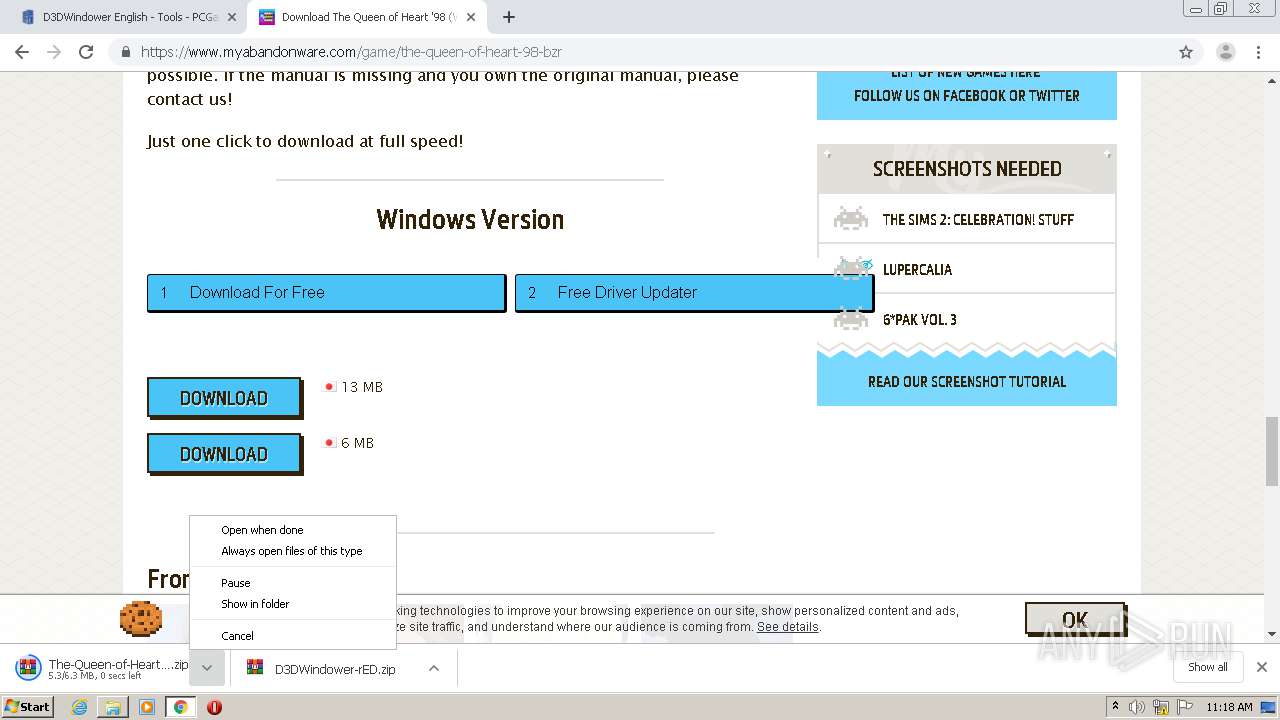
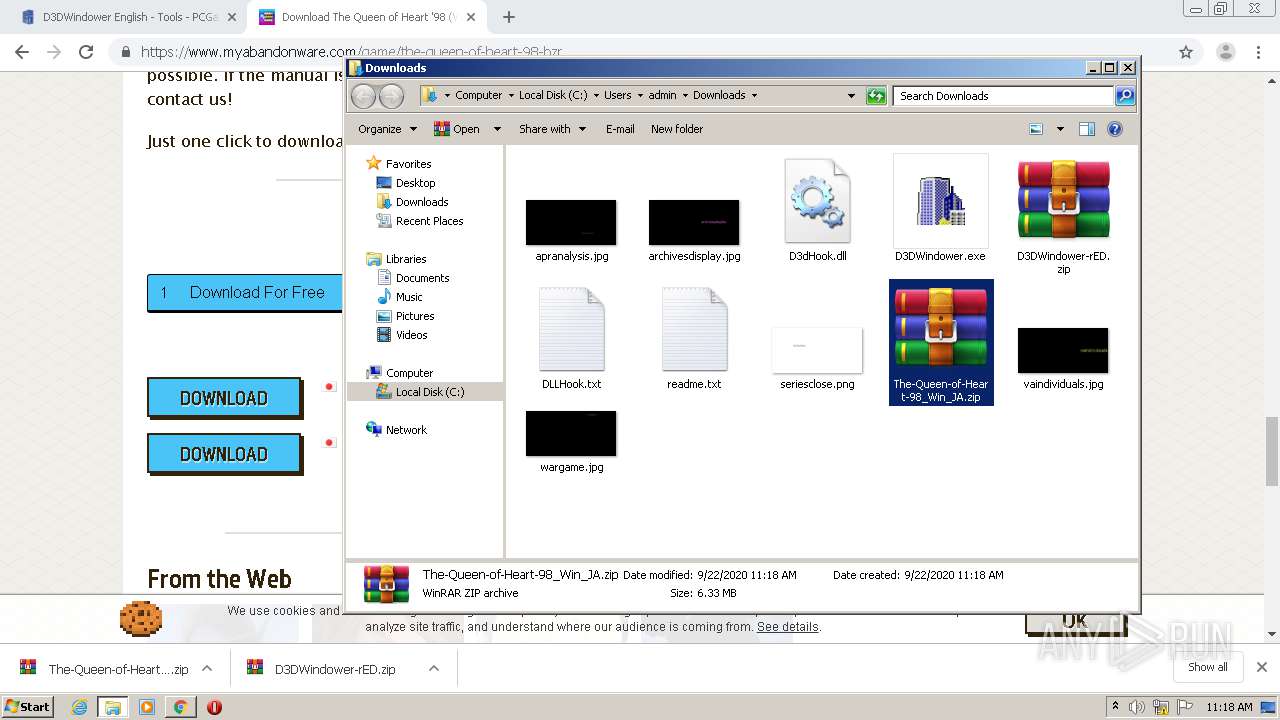
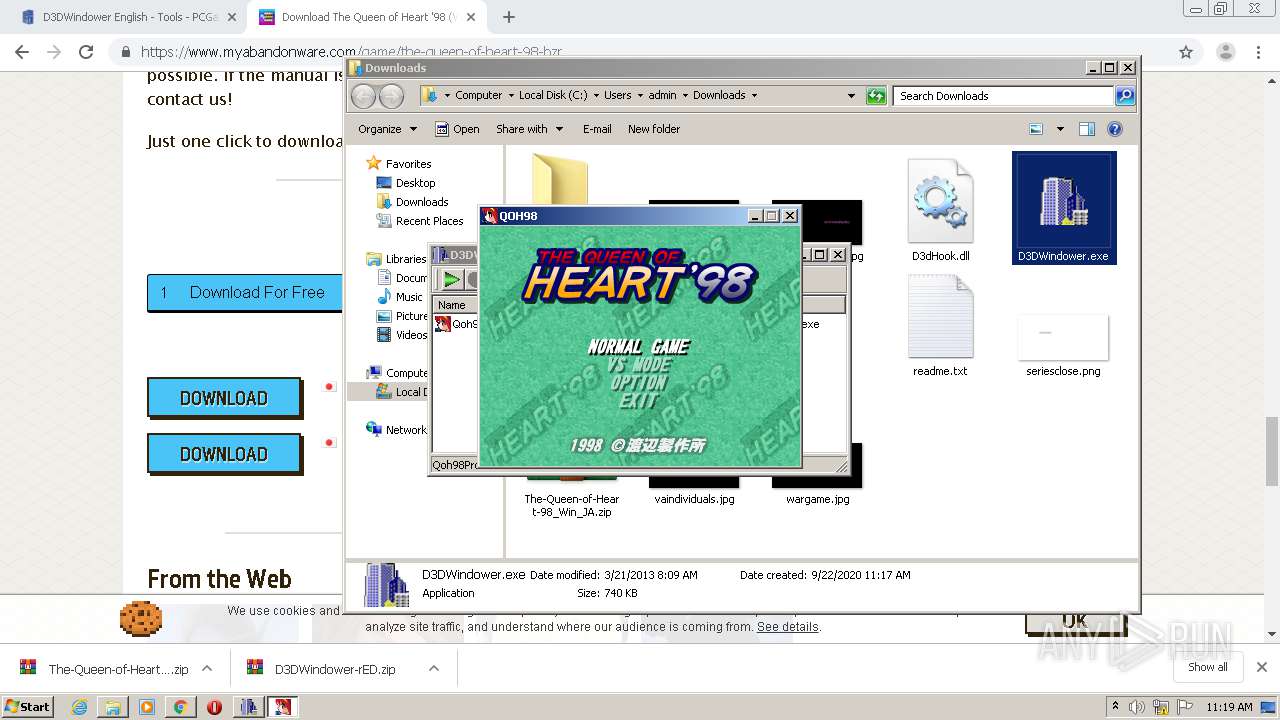
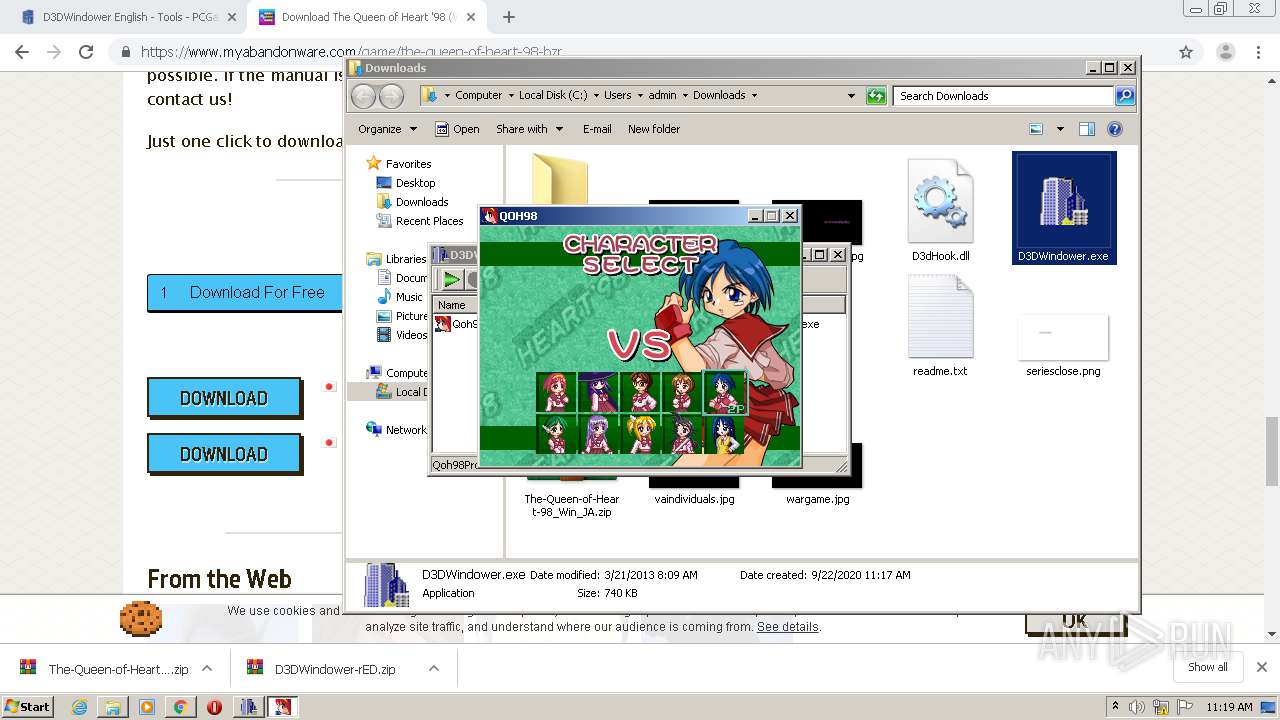
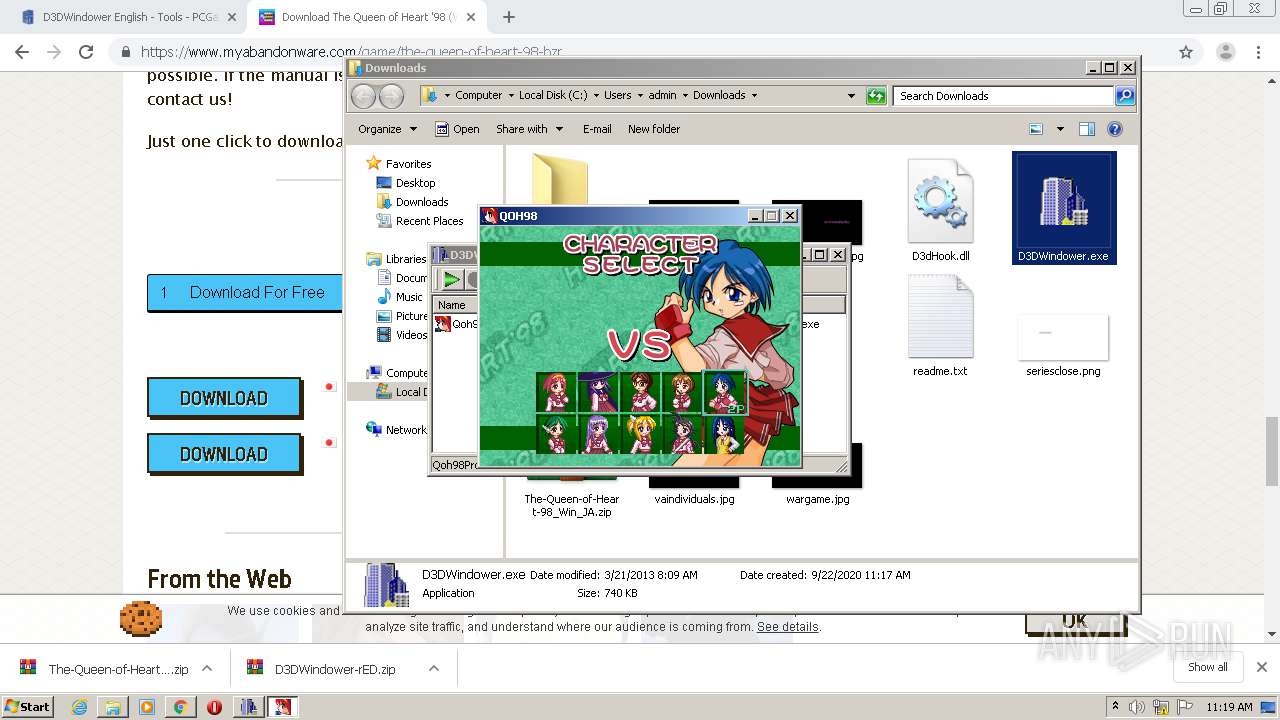
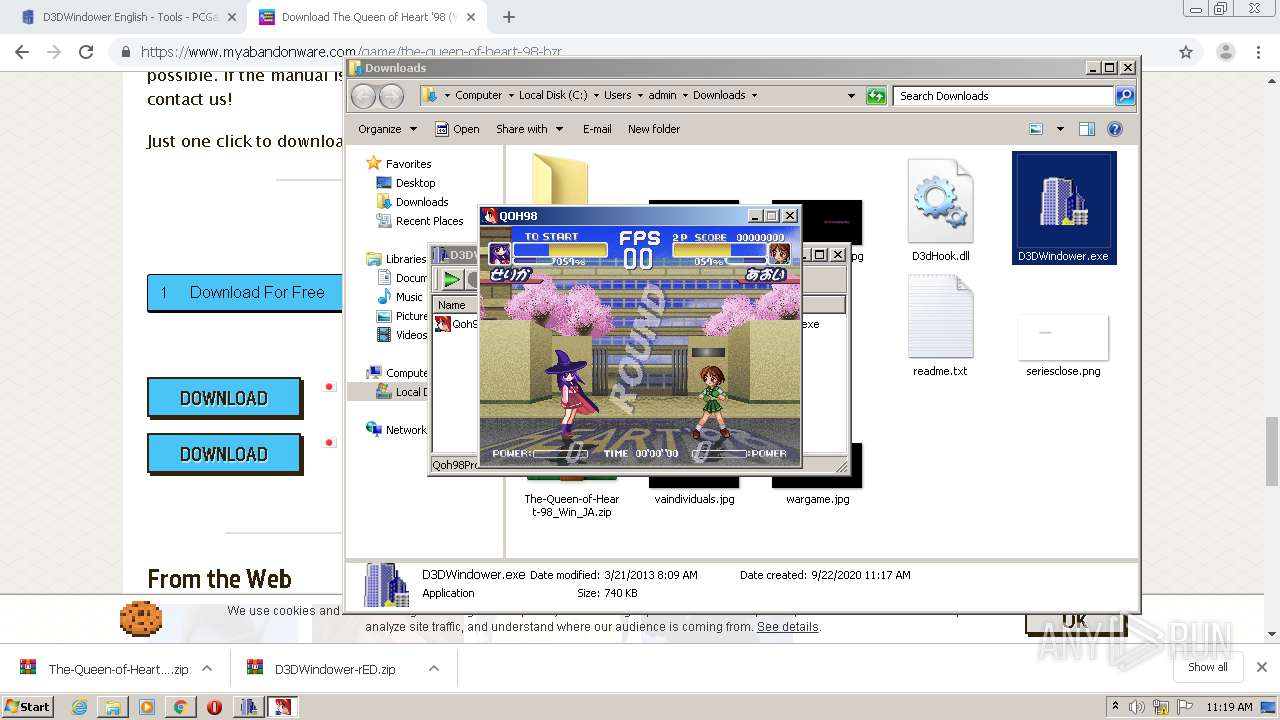
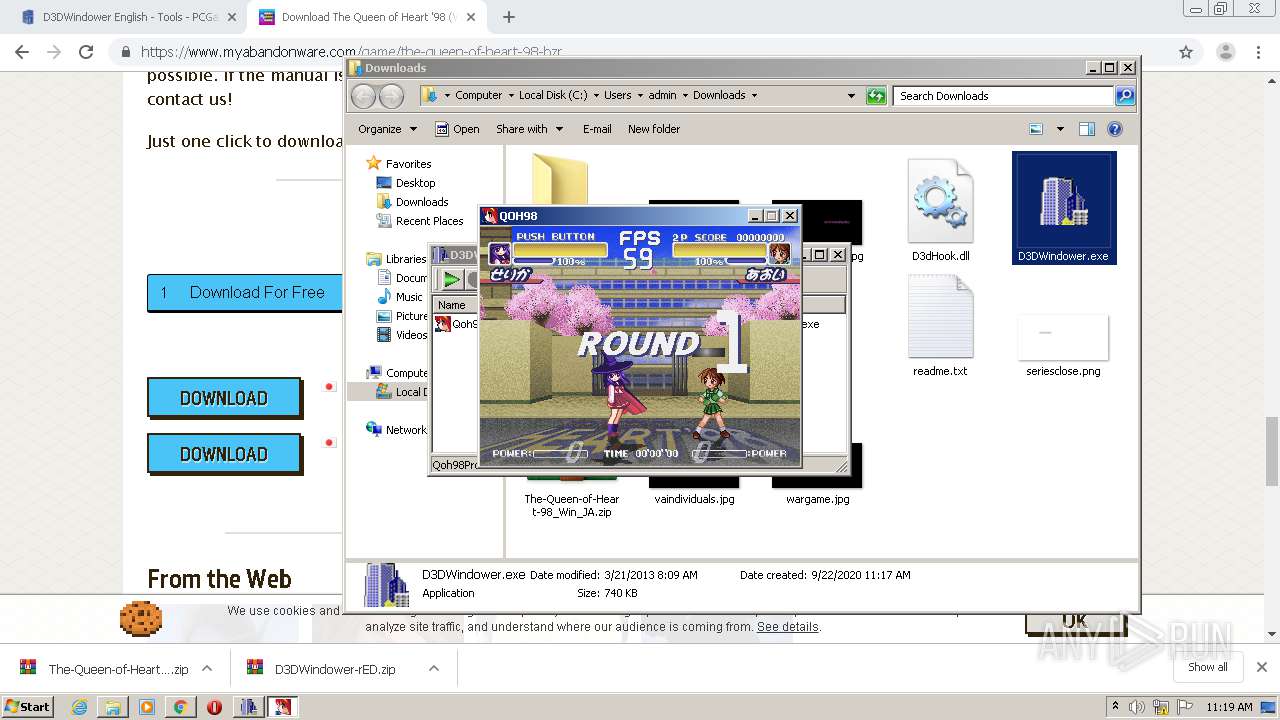
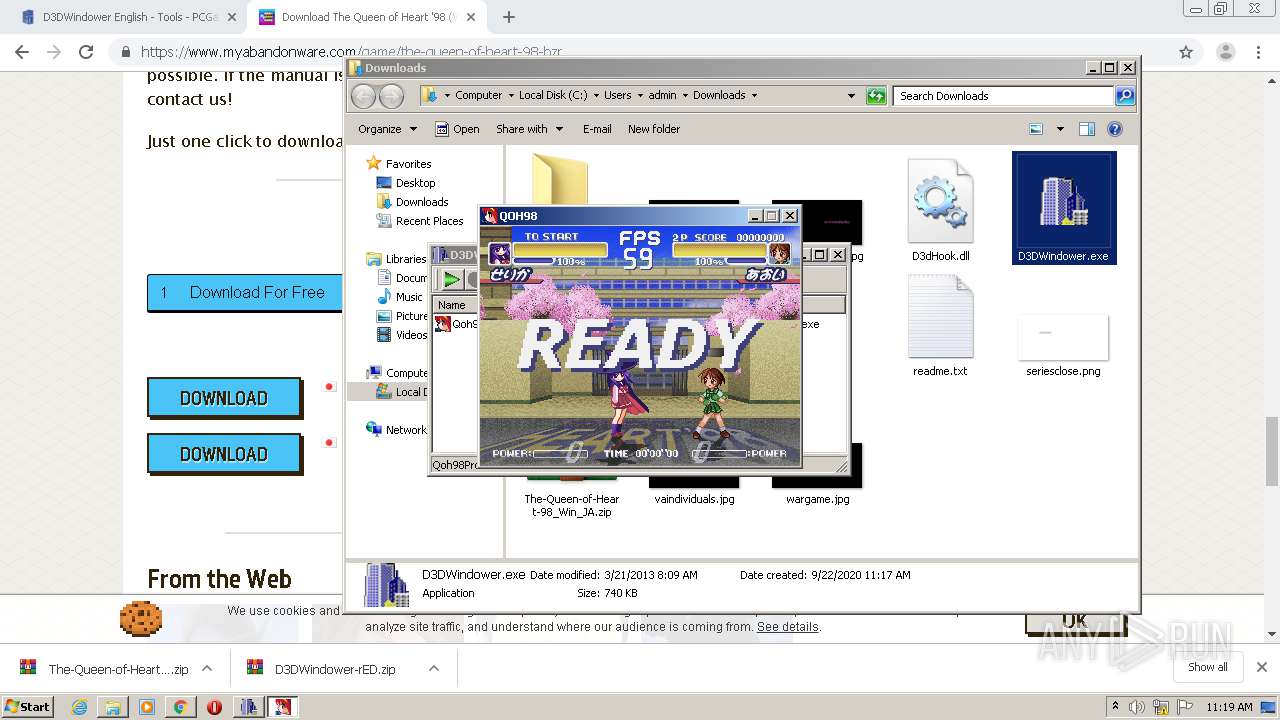
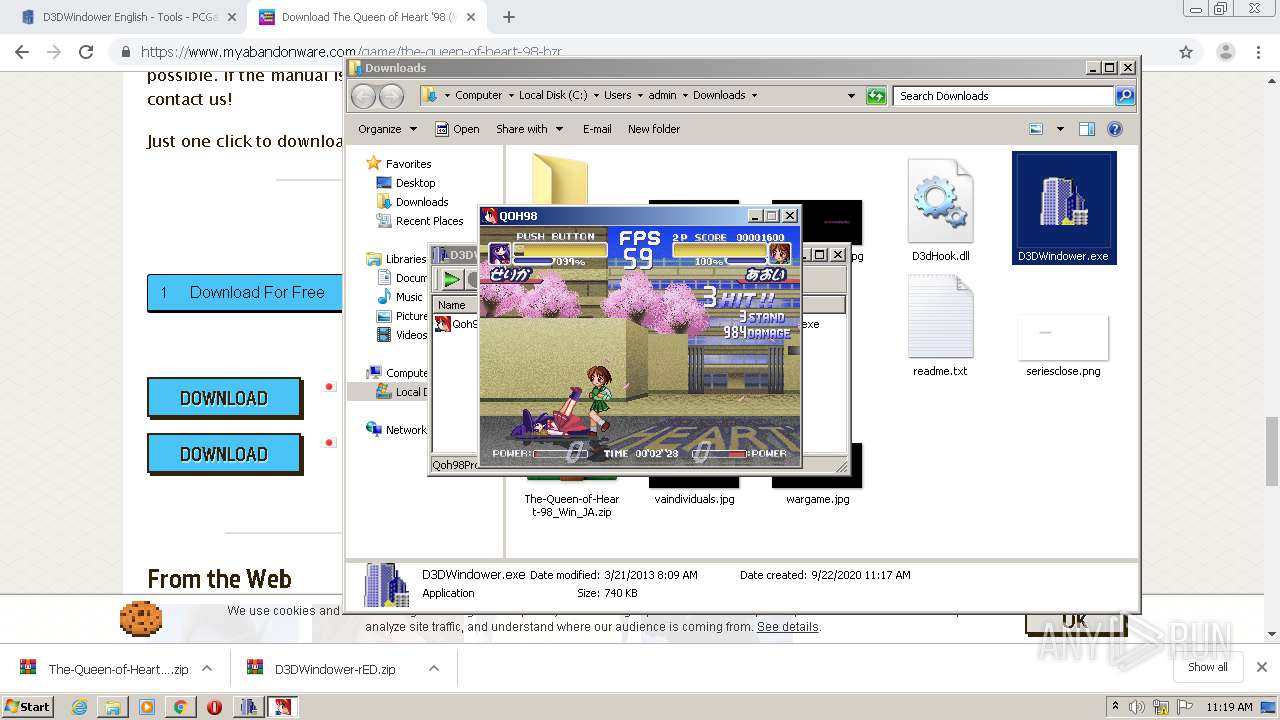
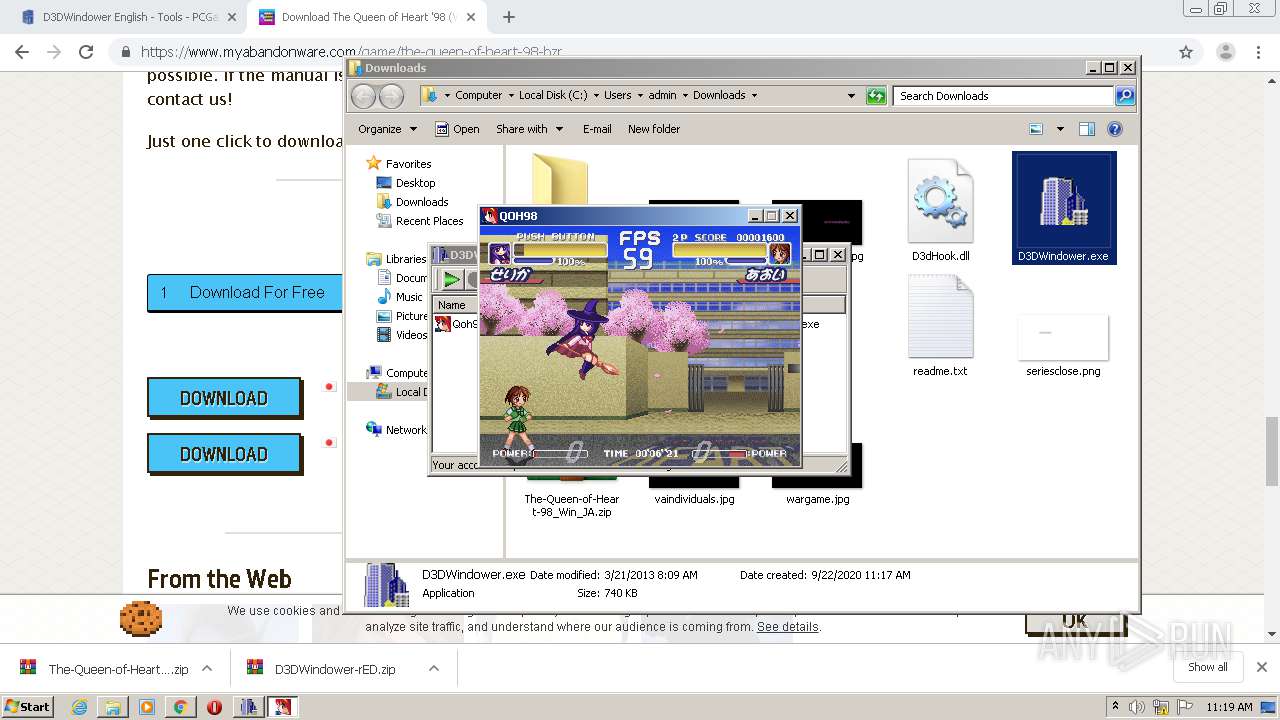
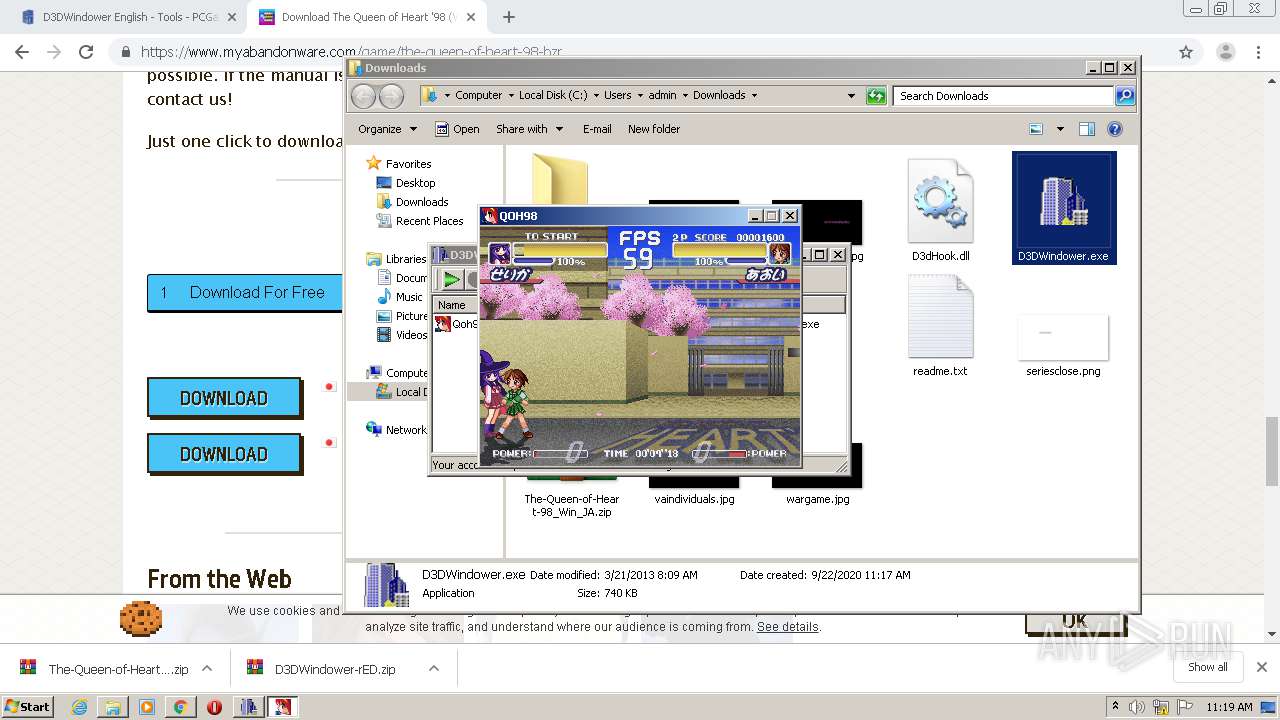
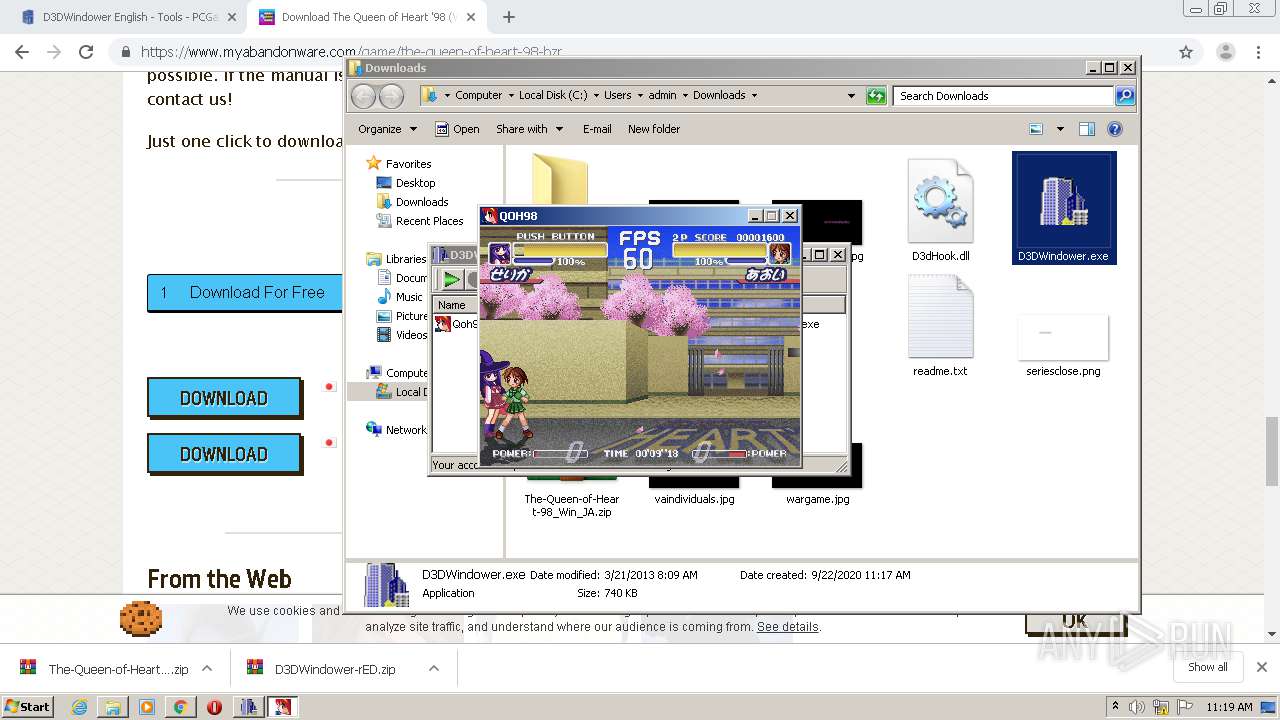
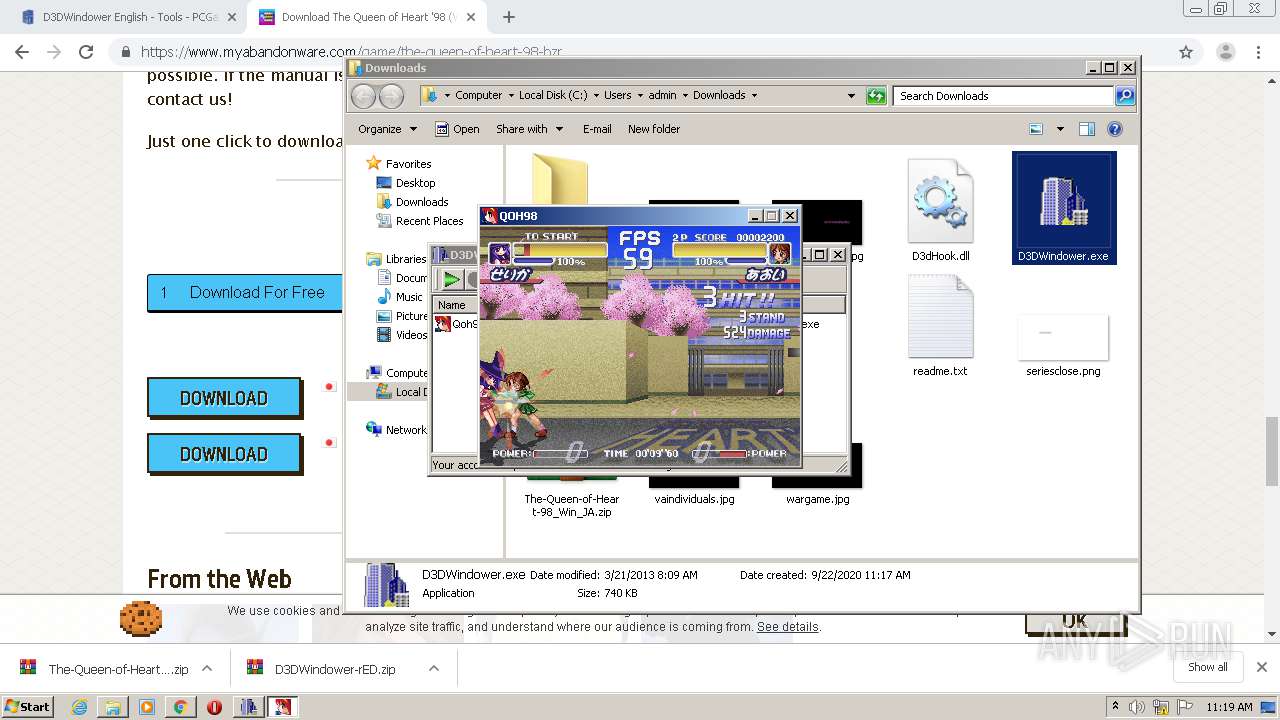
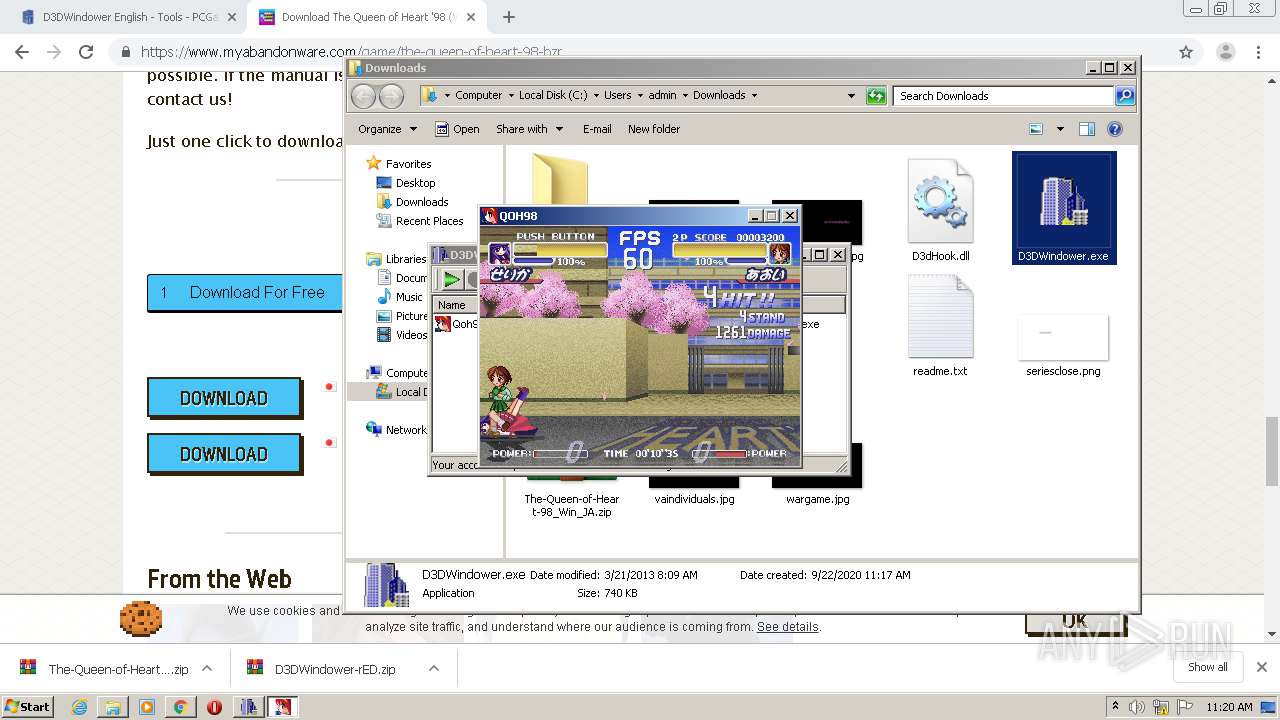
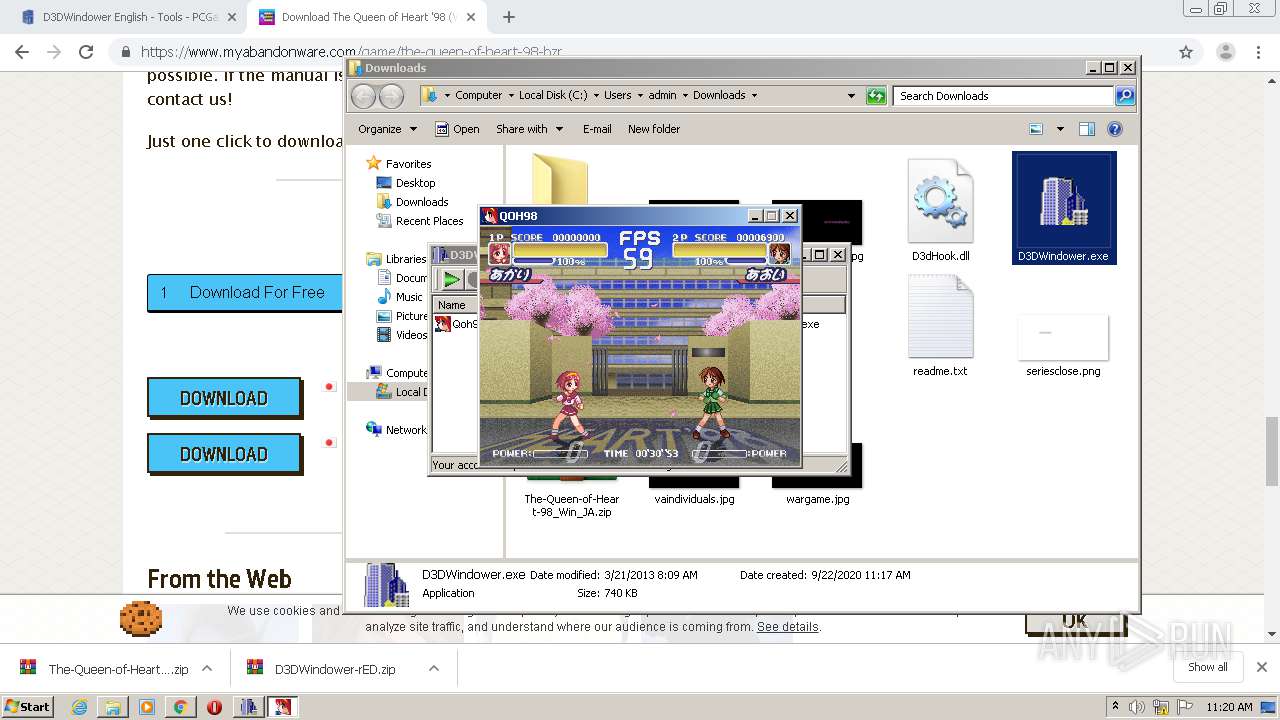
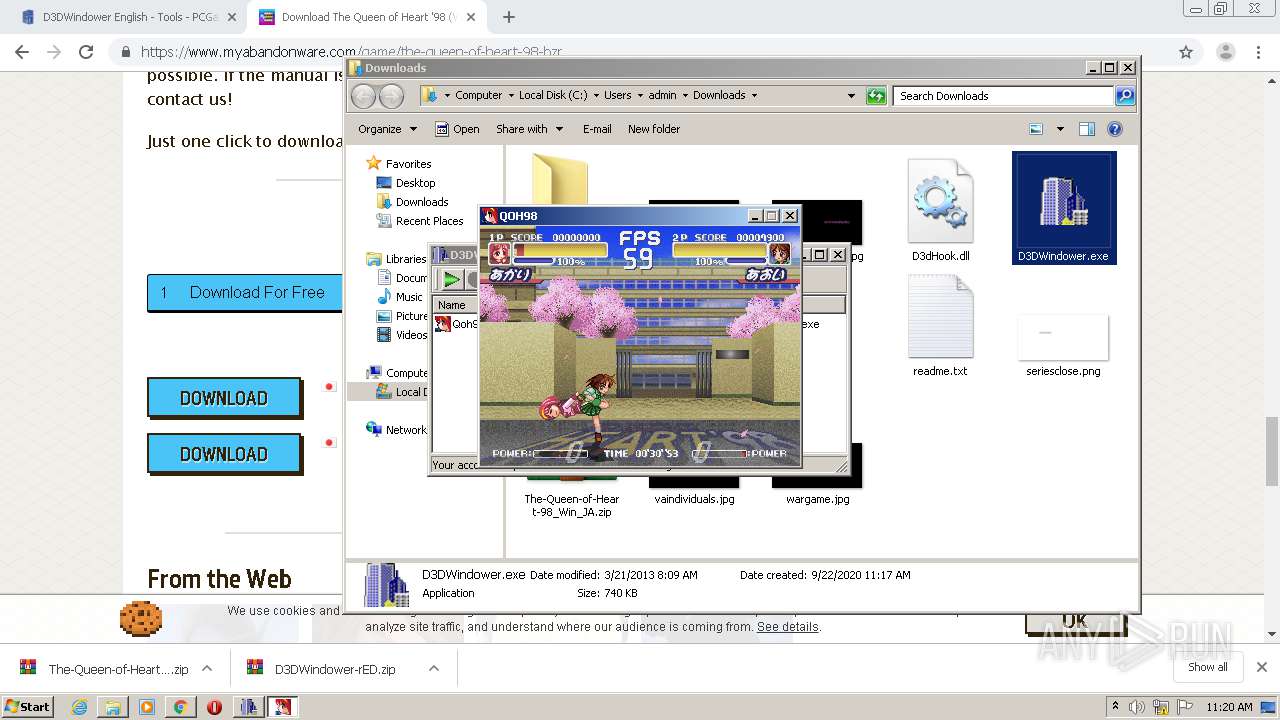
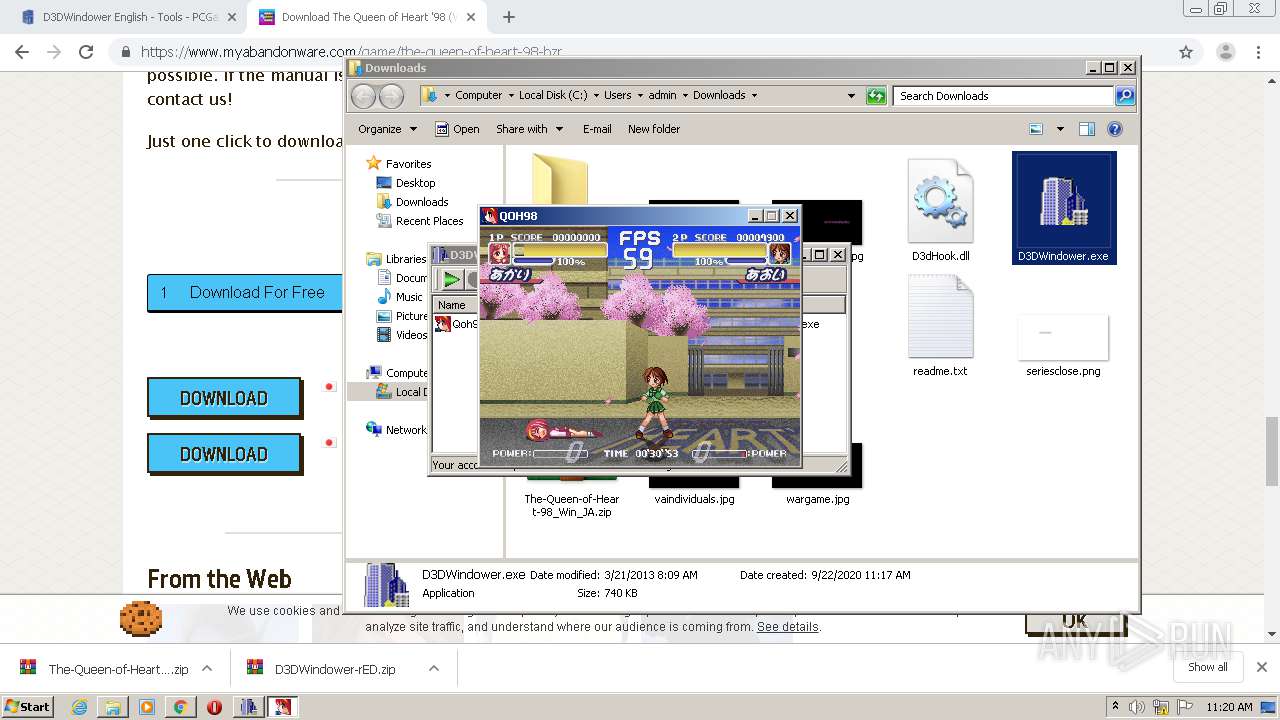
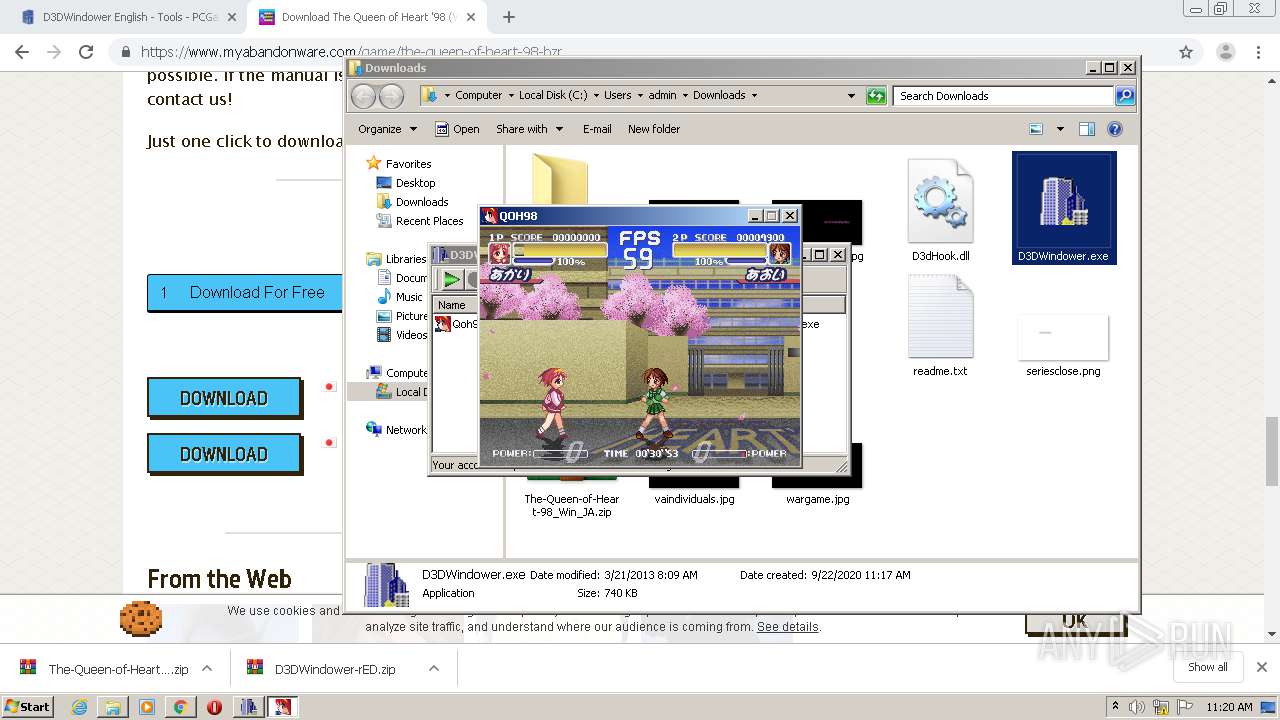
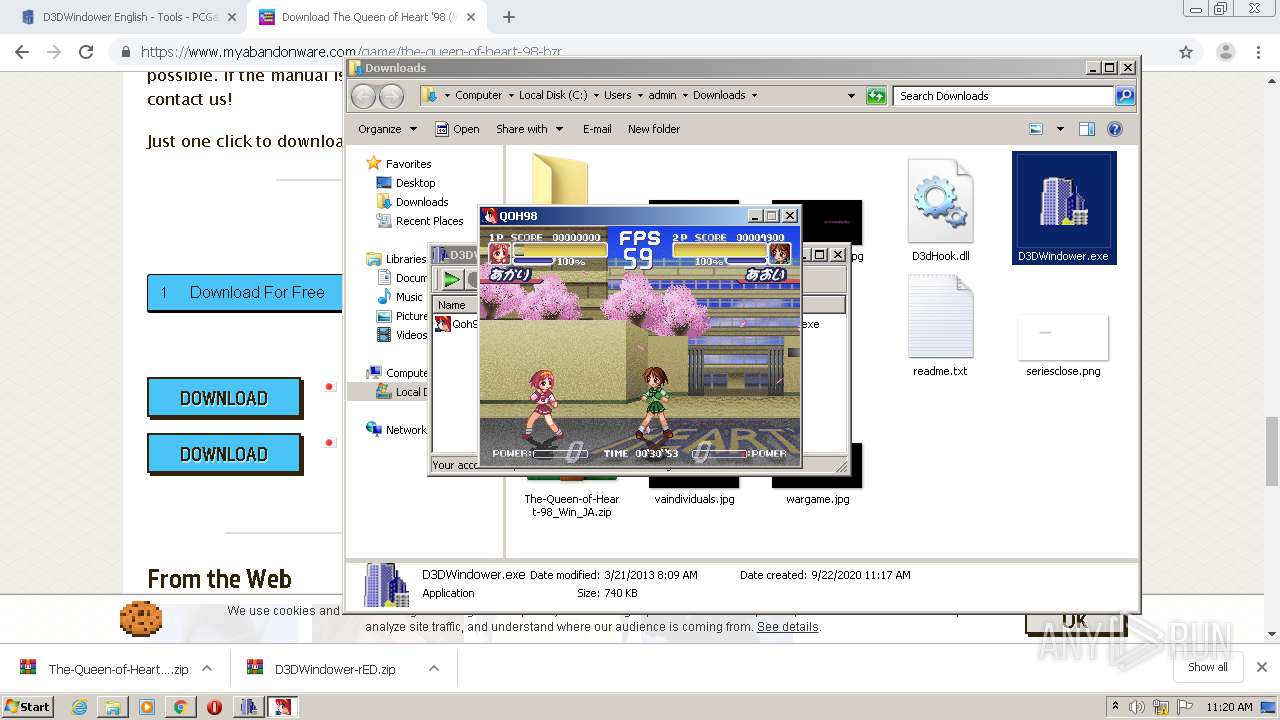
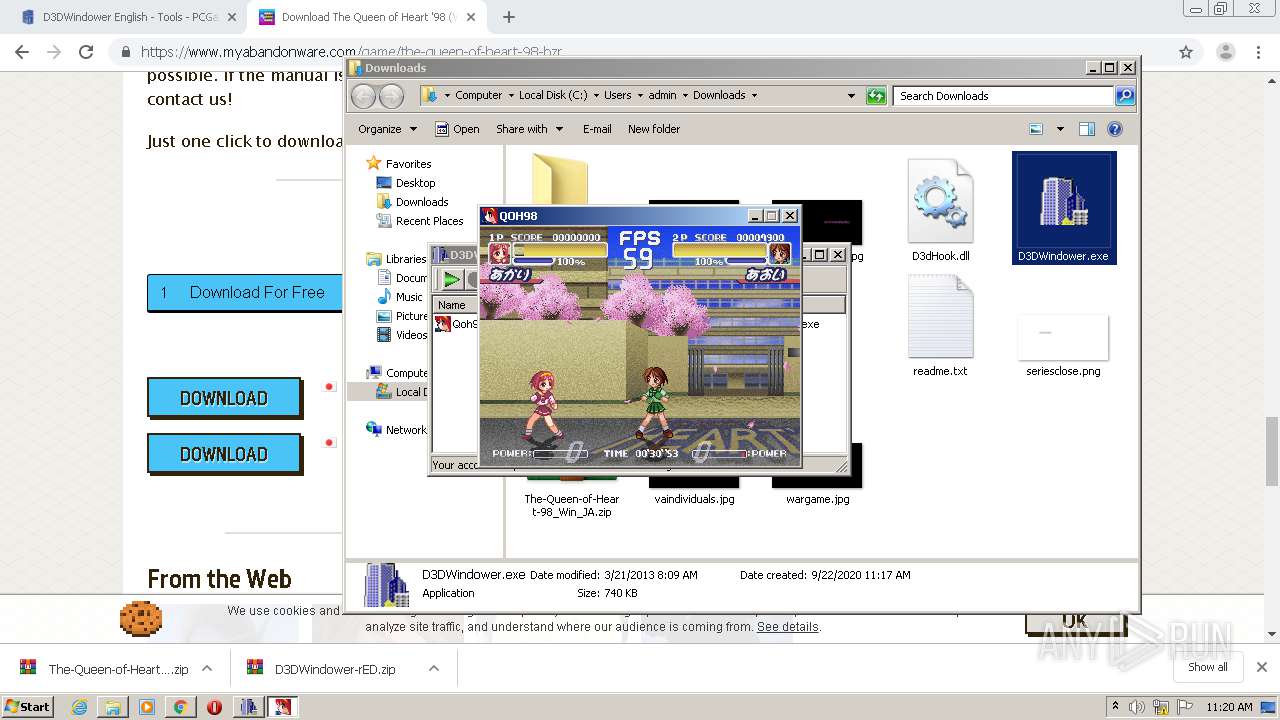
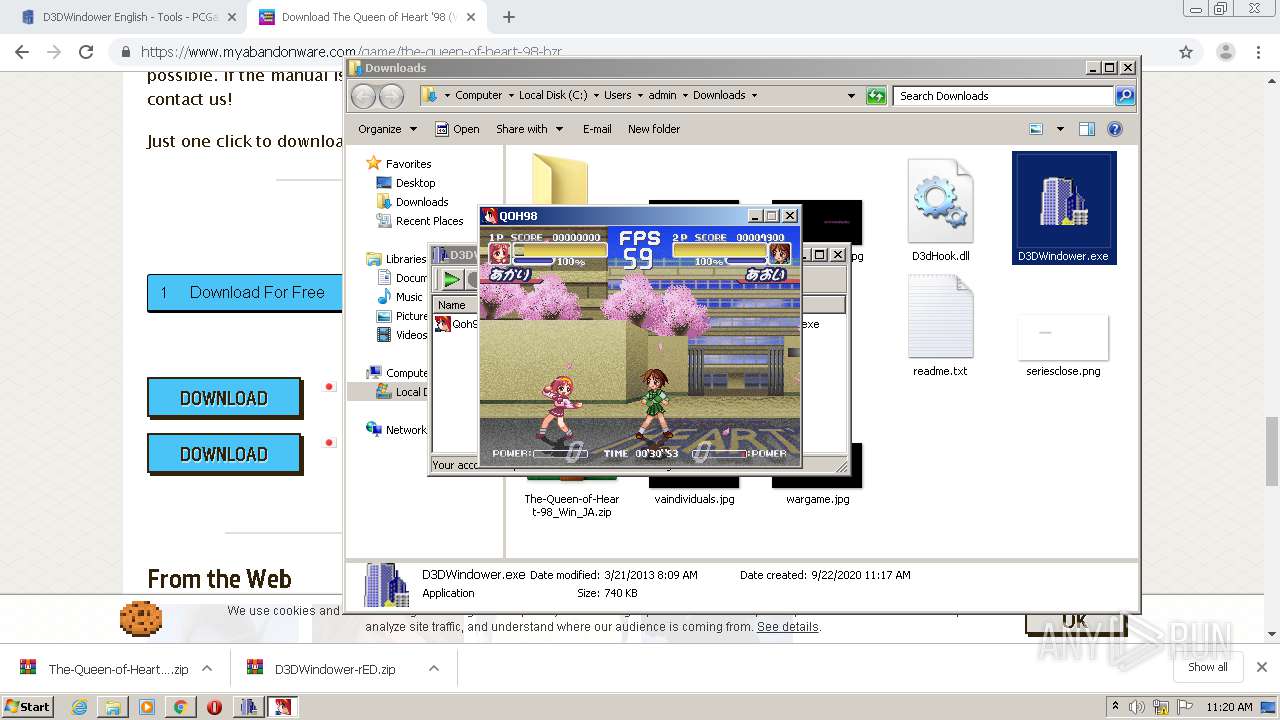
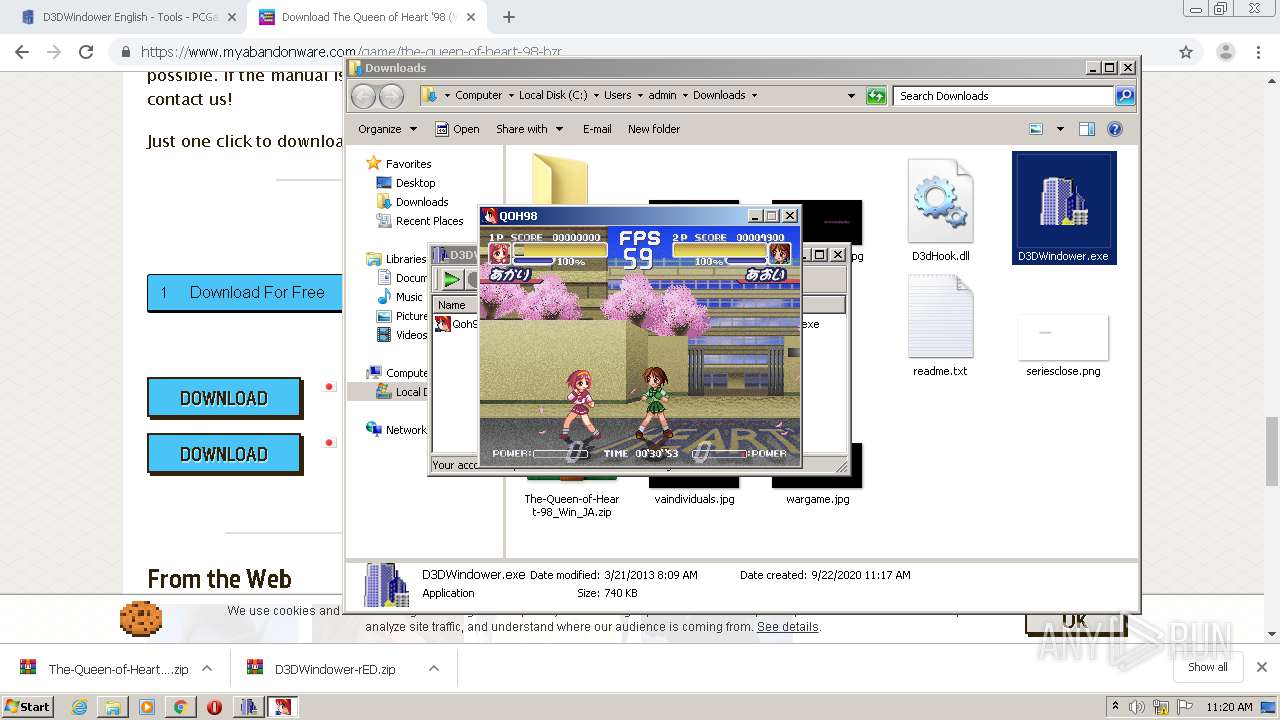
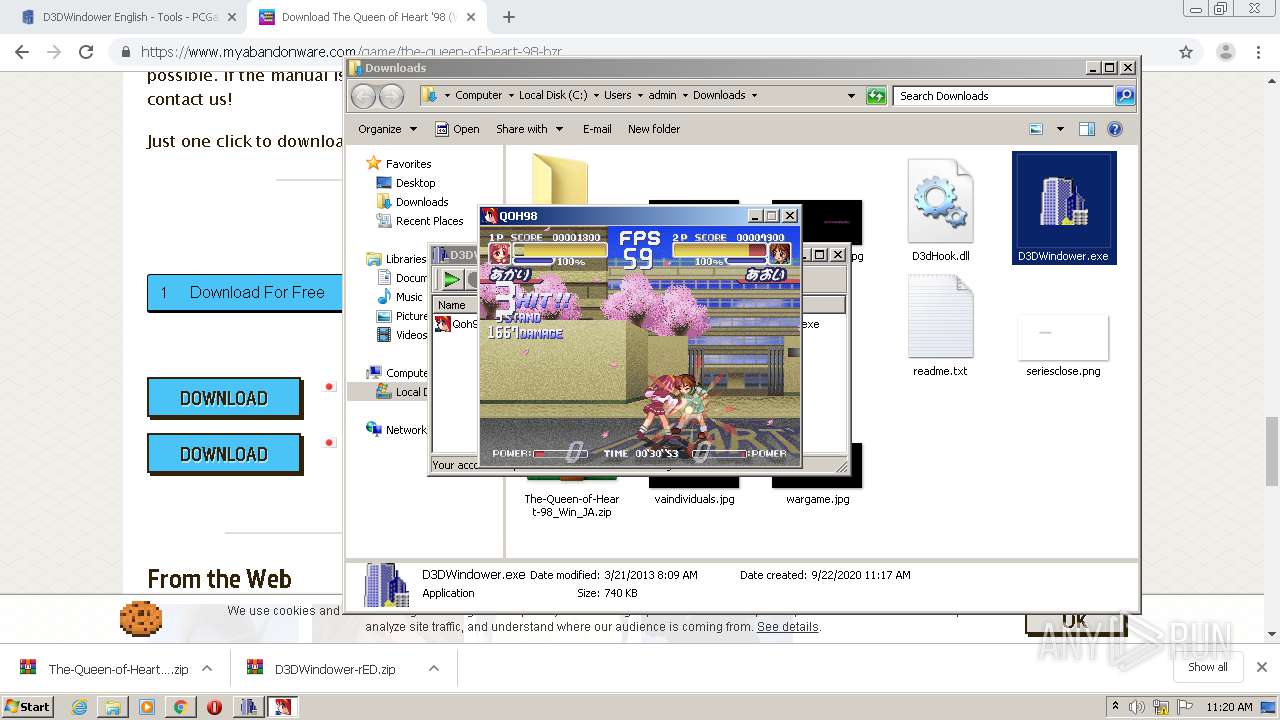
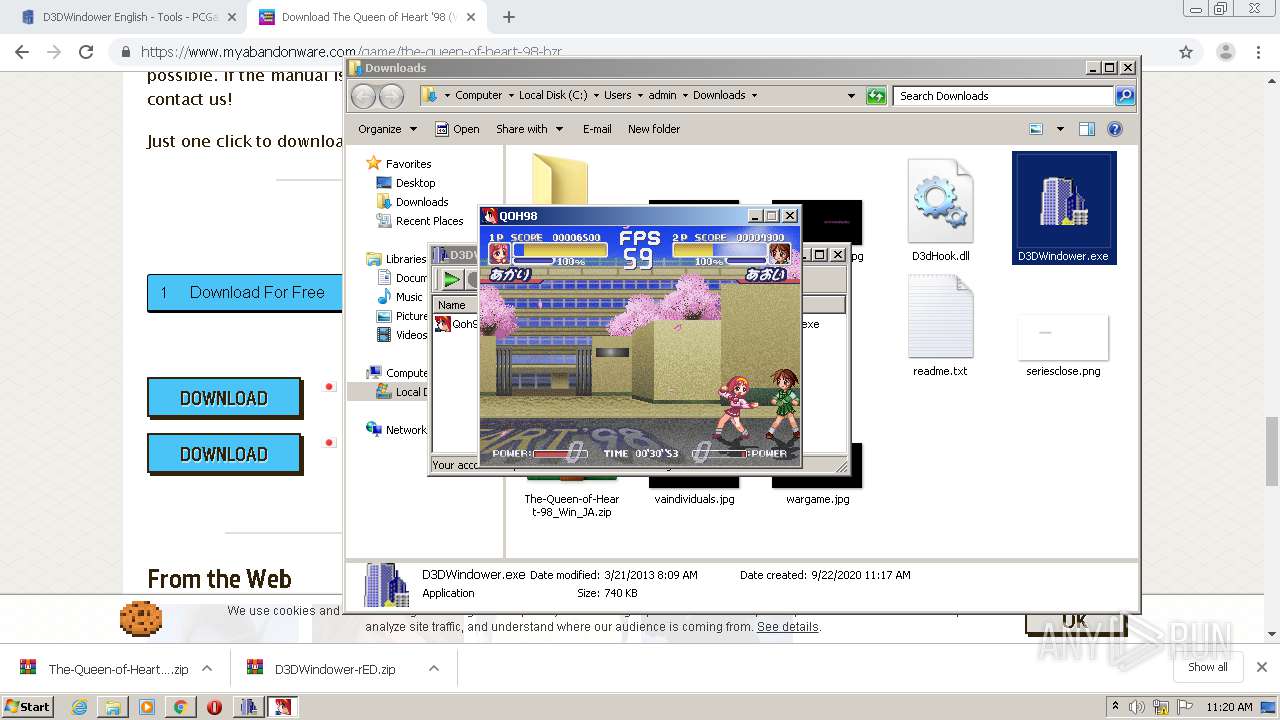
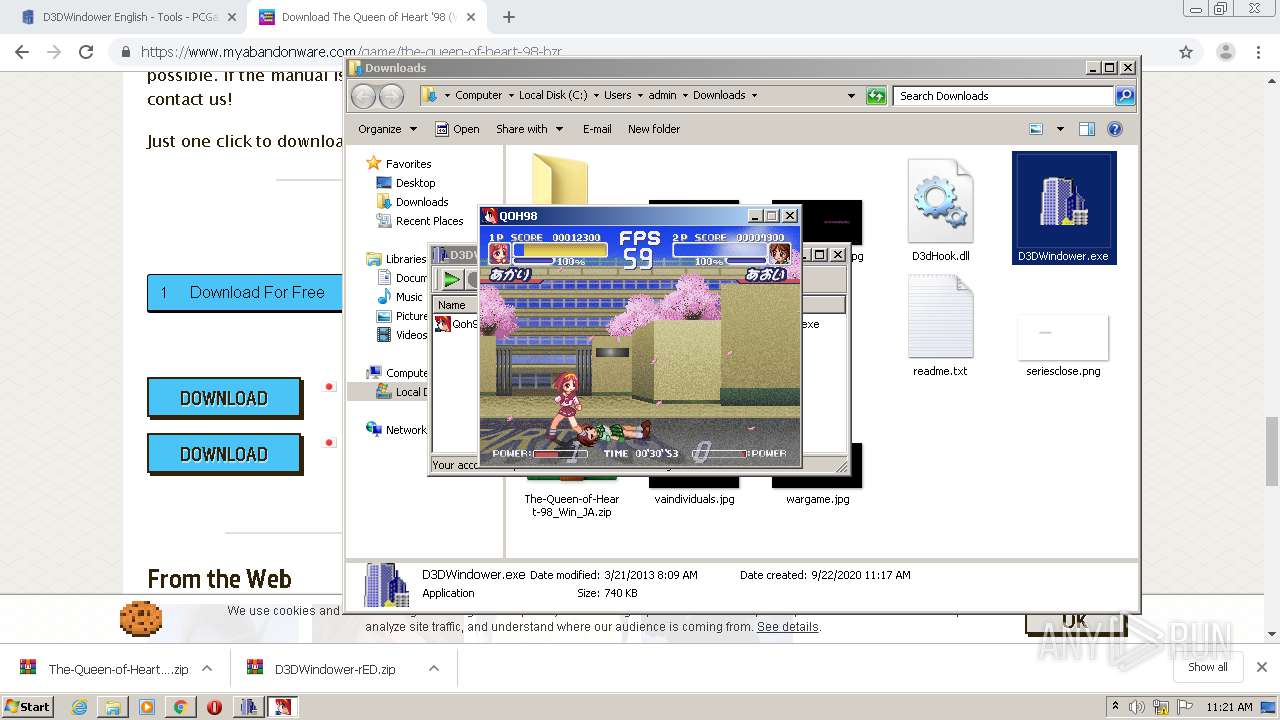
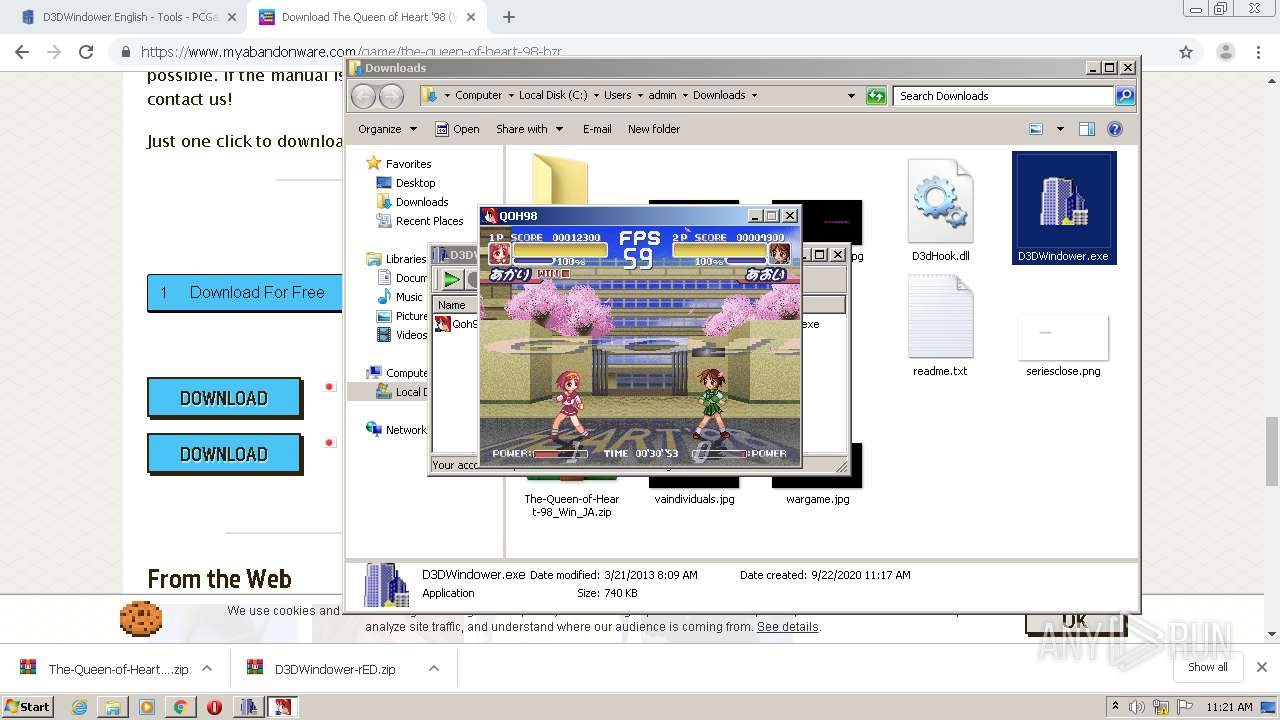
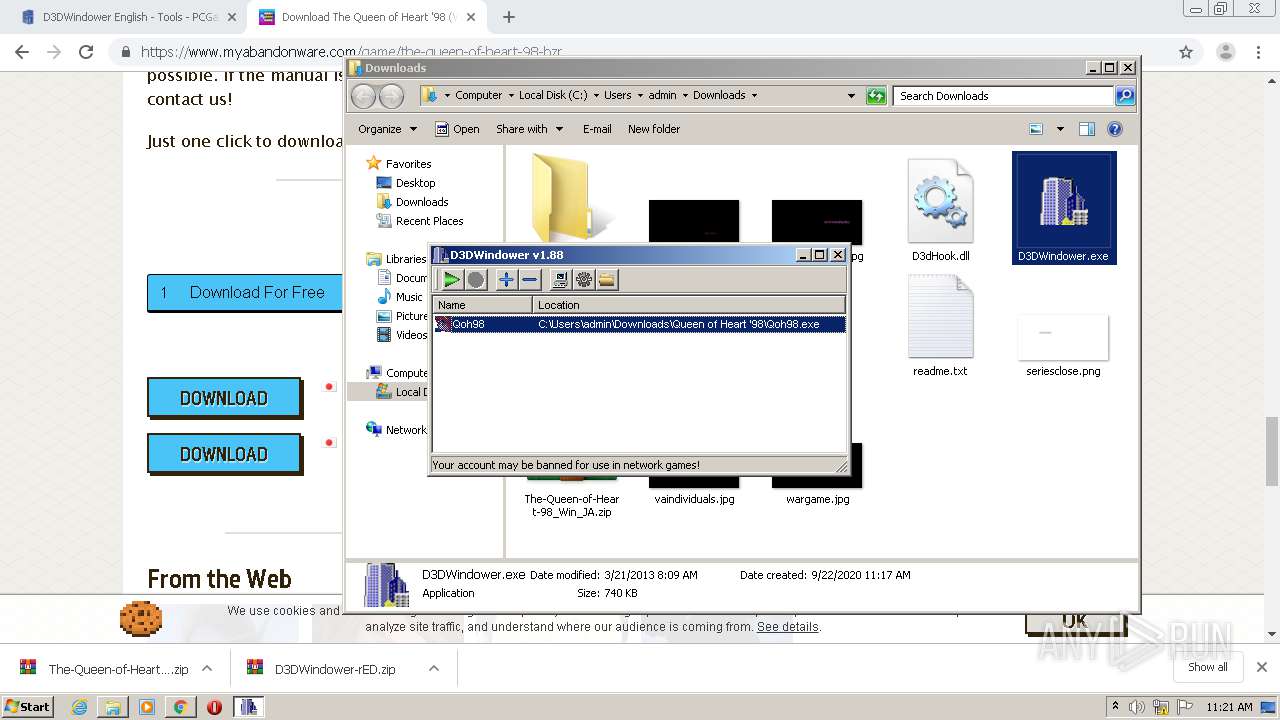
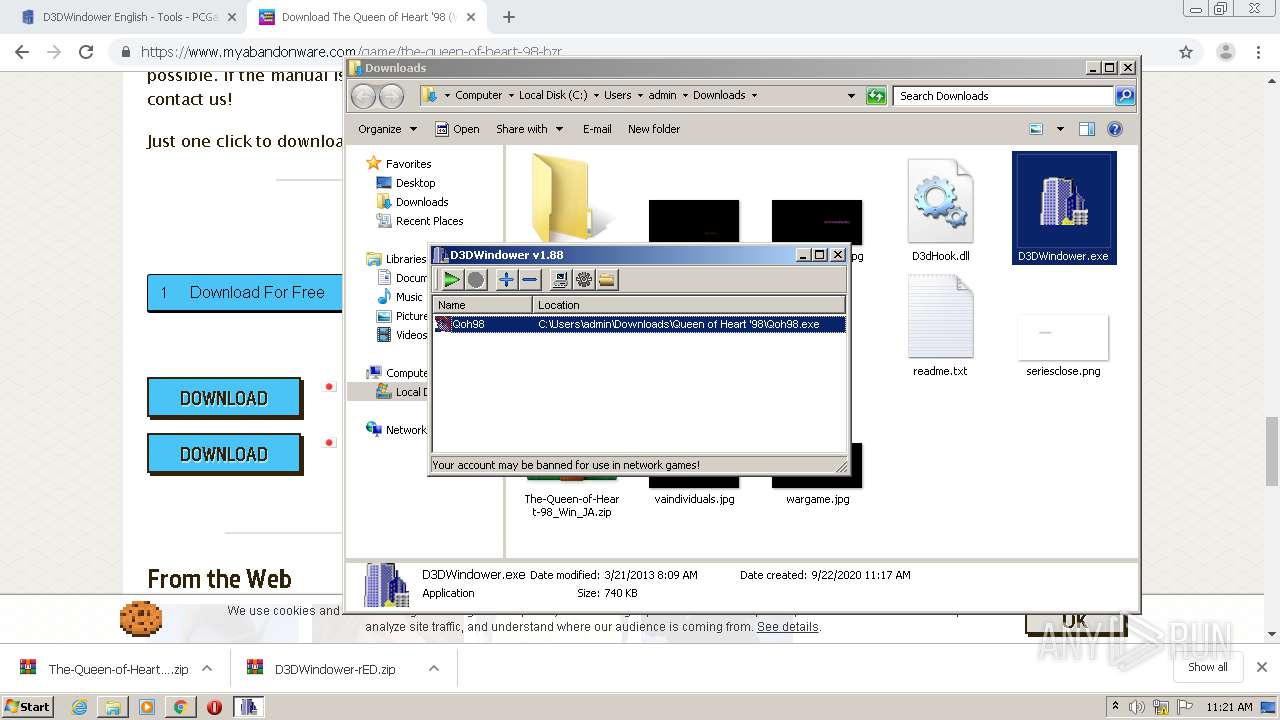
| URL: | https://community.pcgamingwiki.com/files/file/733-d3dwindower-english/ |
| Full analysis: | https://app.any.run/tasks/12dbbca1-f8fa-4f12-a253-ade39fc00bec |
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2020, 10:16:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F9CD3E05970A9288E81F27560EE833CF |
| SHA1: | 35DEB4711E43FF39646452763B19ED29197F650D |
| SHA256: | A4526247408E7A759FED27C144204FA773E5AE73FCFA57B387E7BA6C4744B69D |
| SSDEEP: | 3:N8XAMTt1KGHKTuBFaJ/NK:2QMTtcGfqFK |
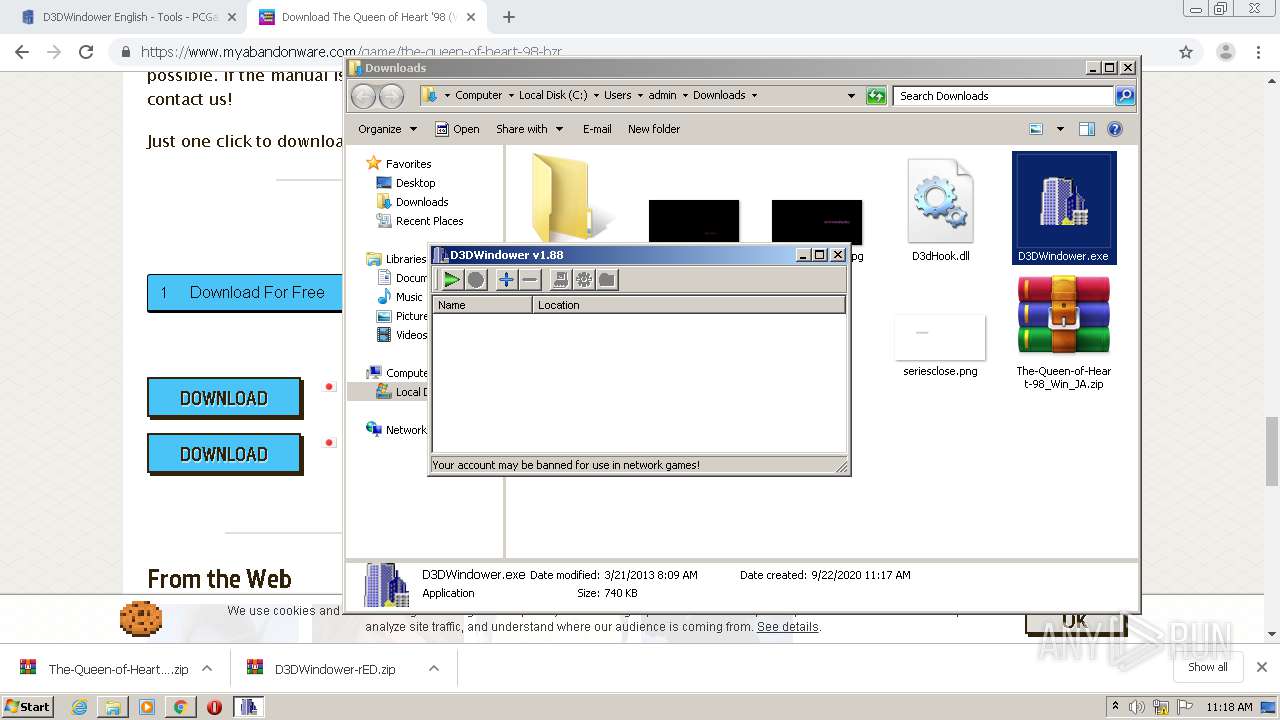
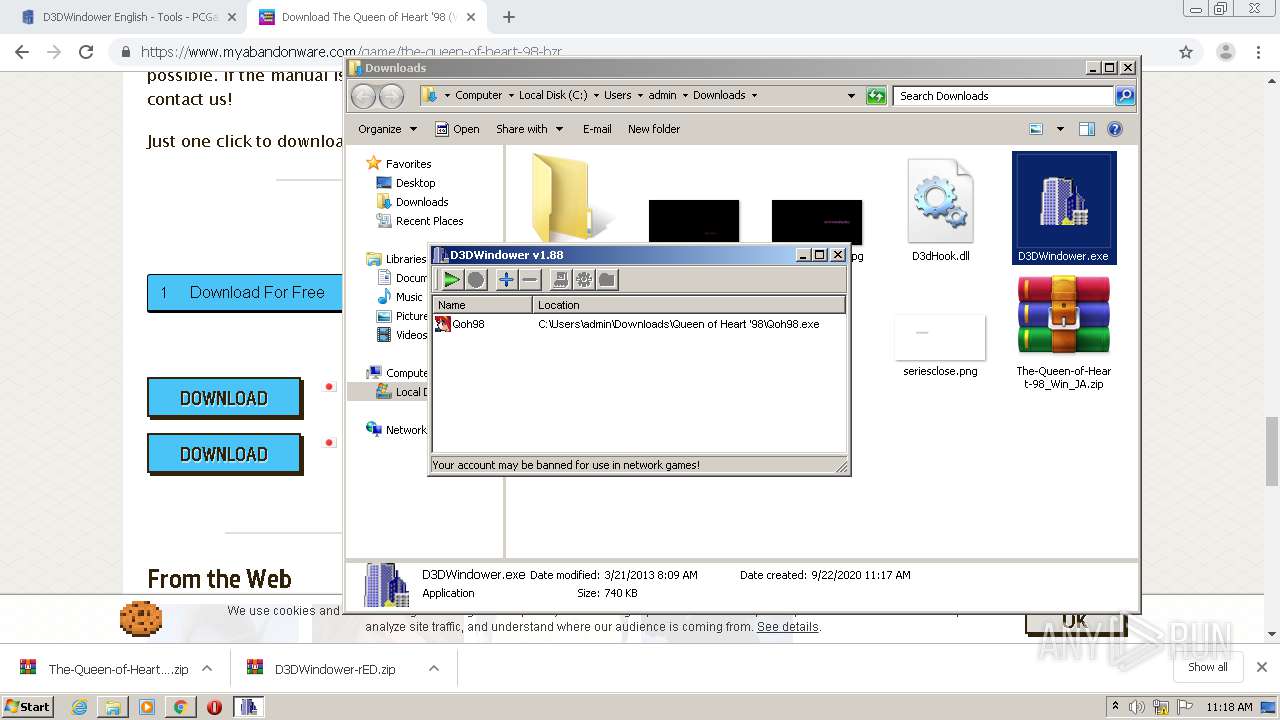
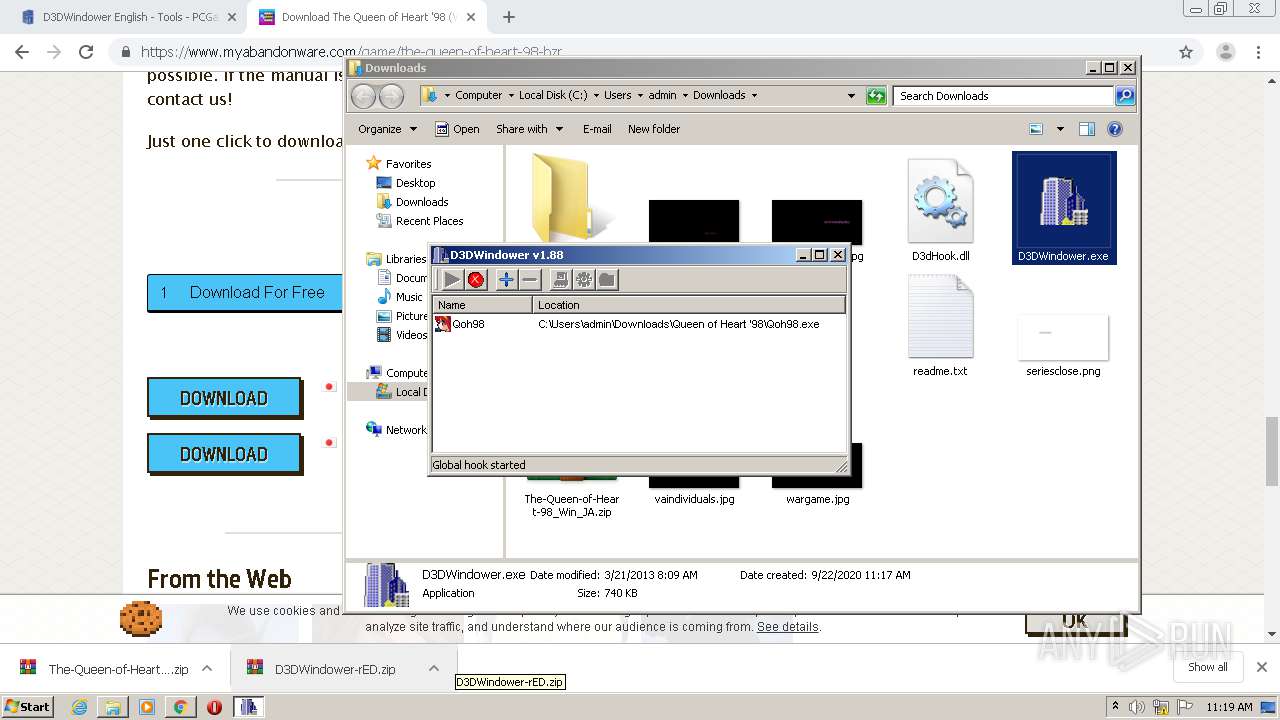
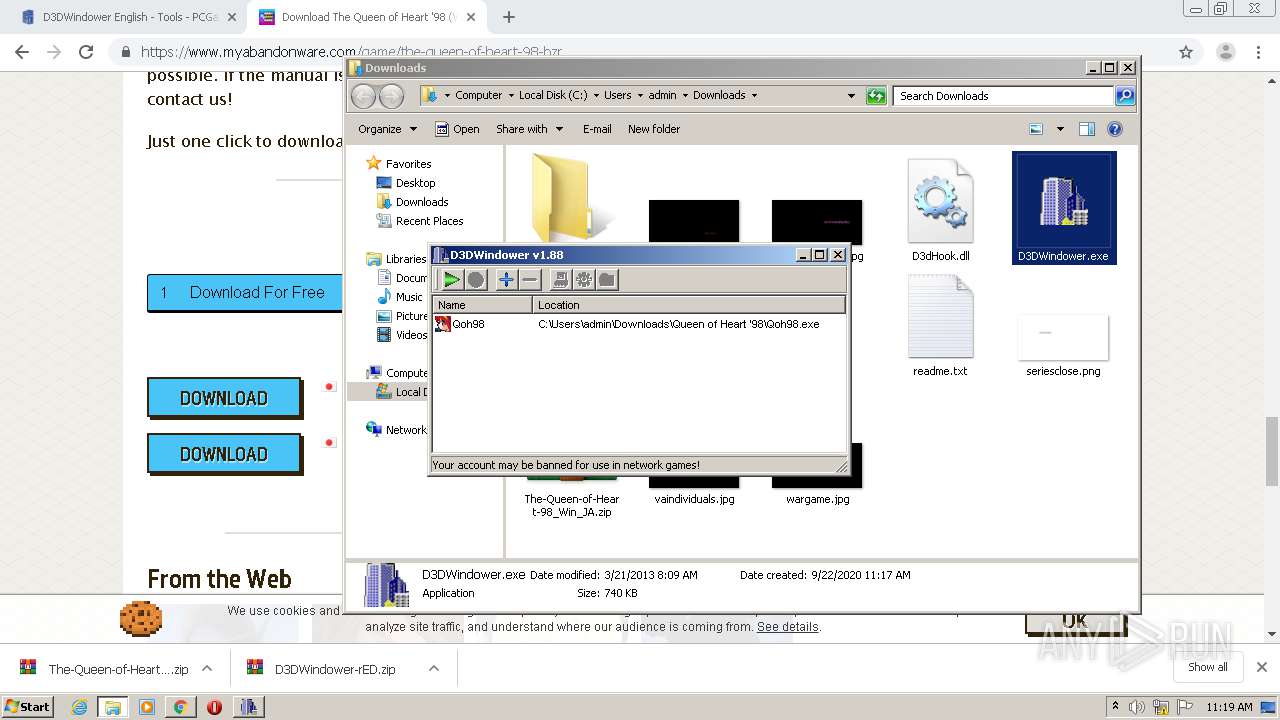
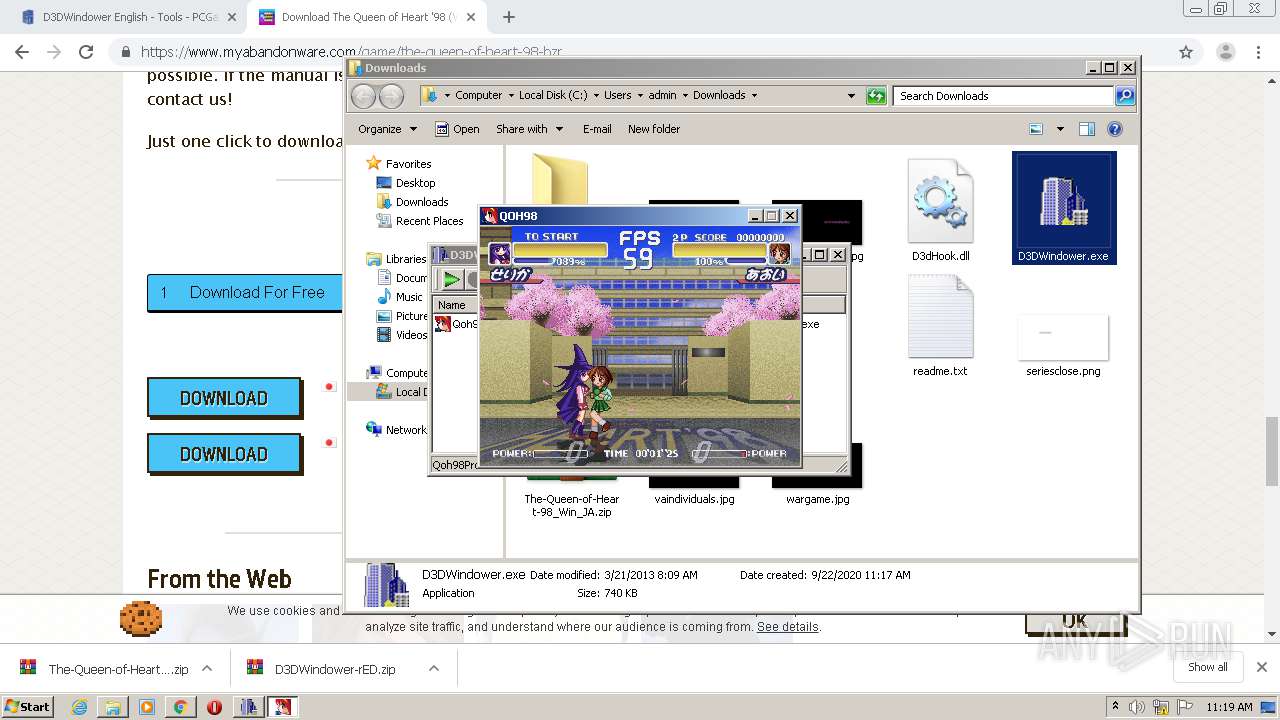
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3464)
- ctfmon.exe (PID: 572)
- chrome.exe (PID: 4076)
- taskhost.exe (PID: 1952)
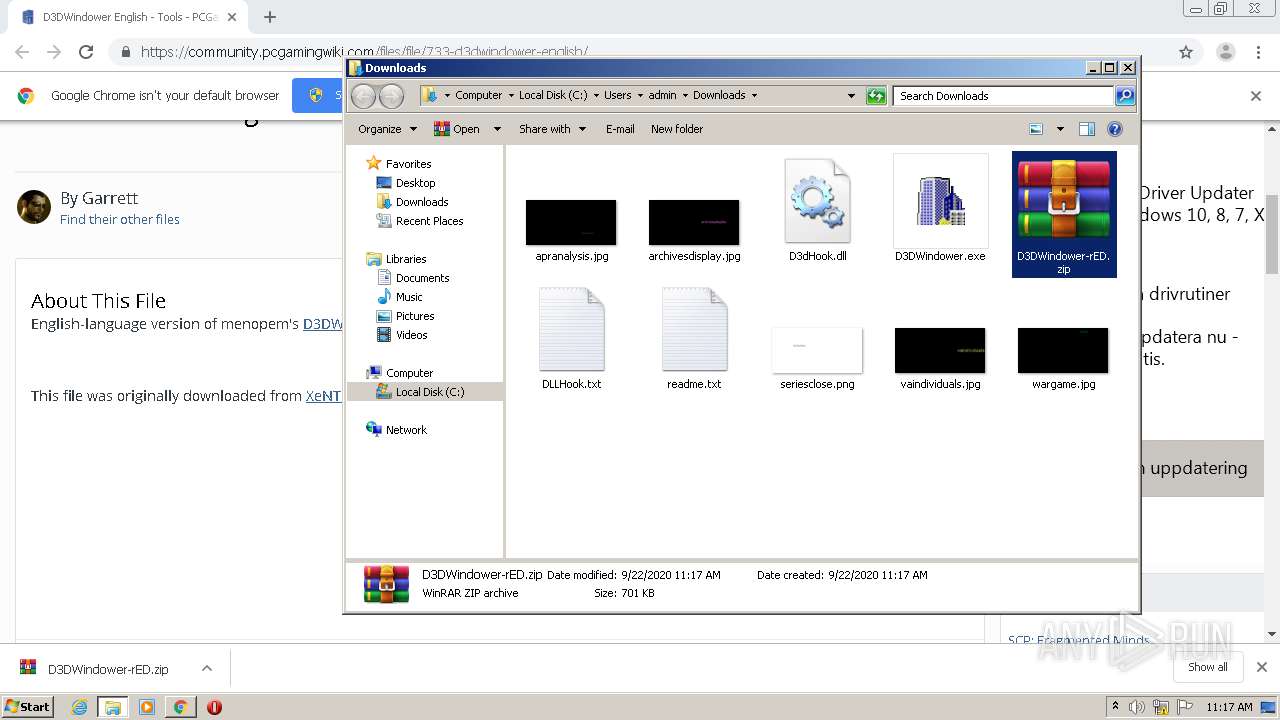
- D3DWindower.exe (PID: 5792)
- taskeng.exe (PID: 1972)
- dwm.exe (PID: 2032)
- explorer.exe (PID: 352)
- DllHost.exe (PID: 4252)
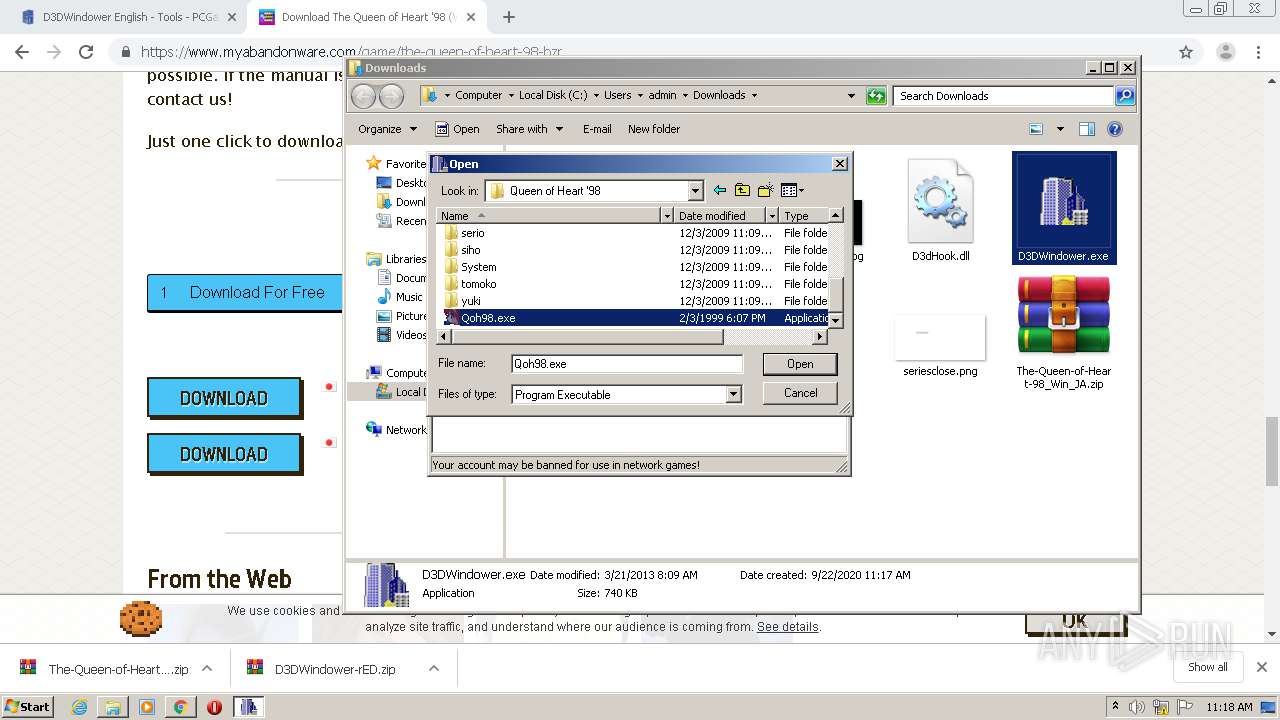
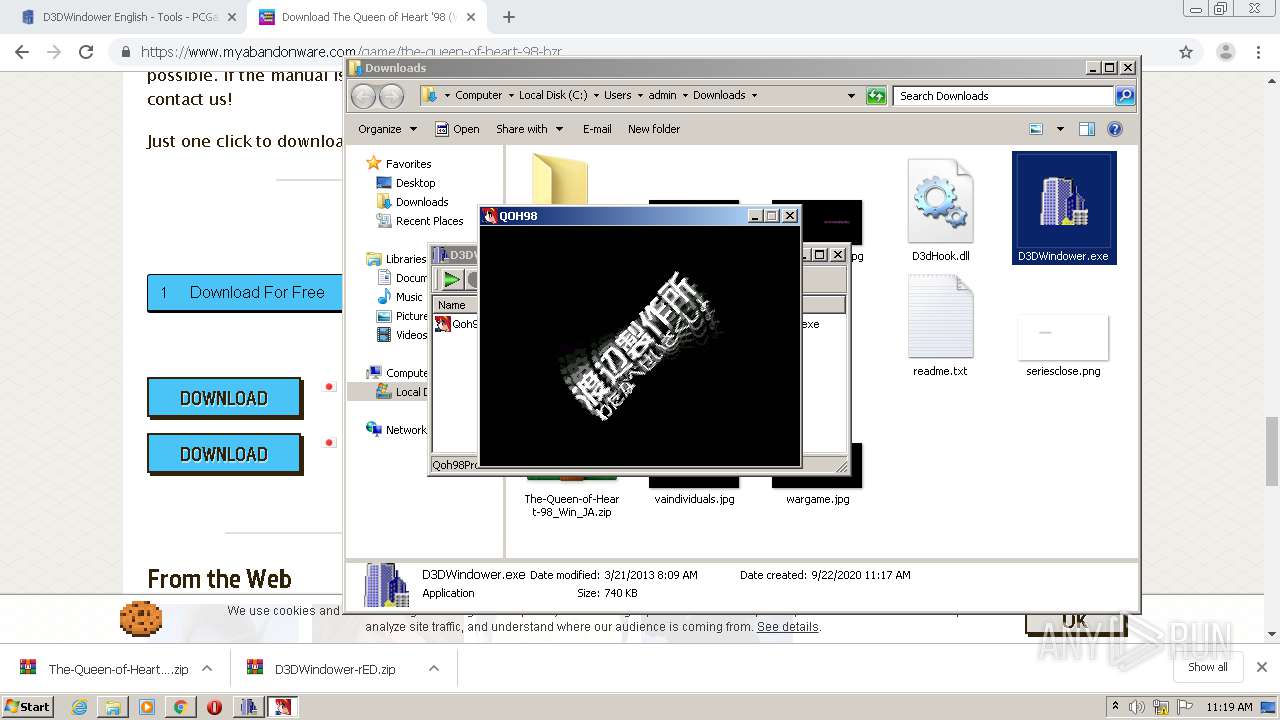
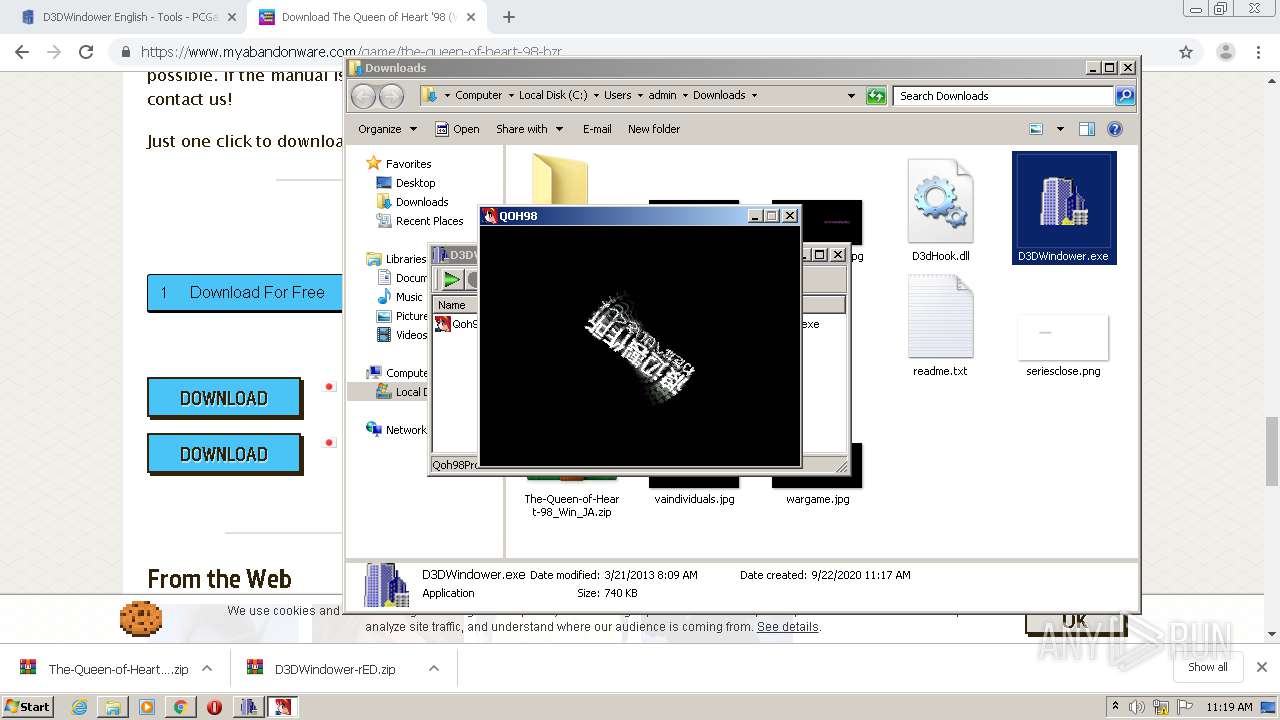
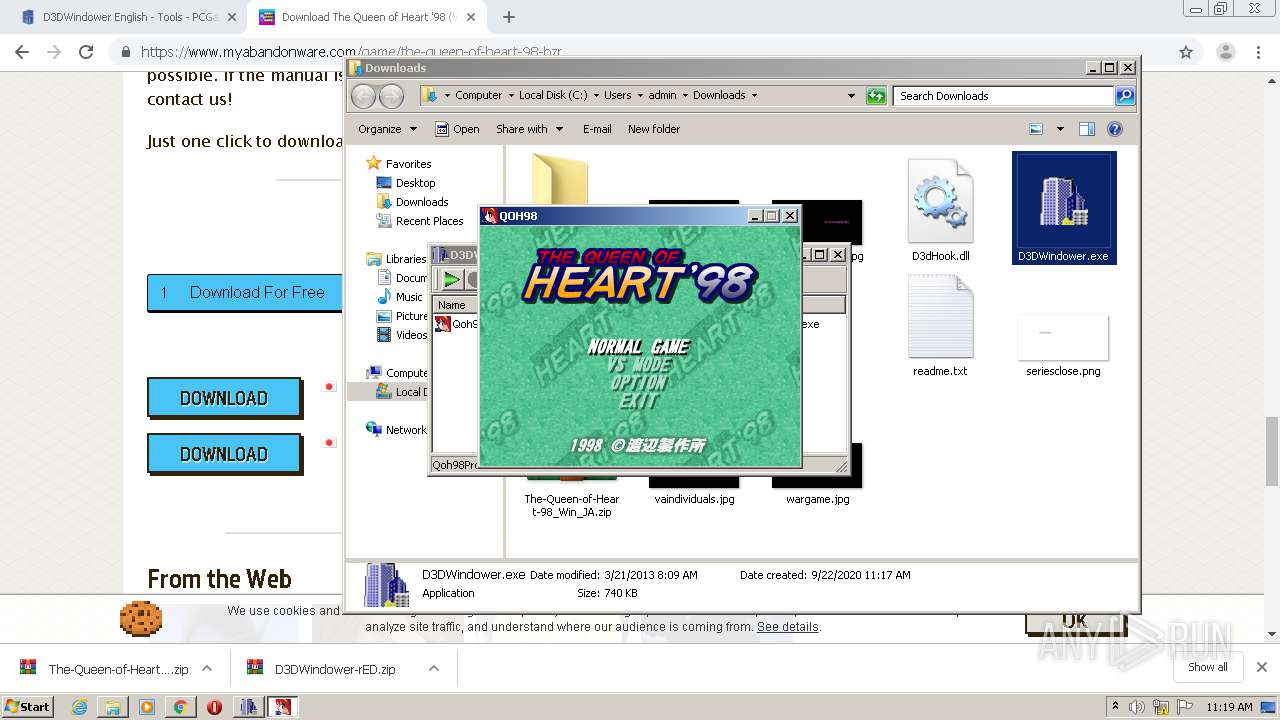
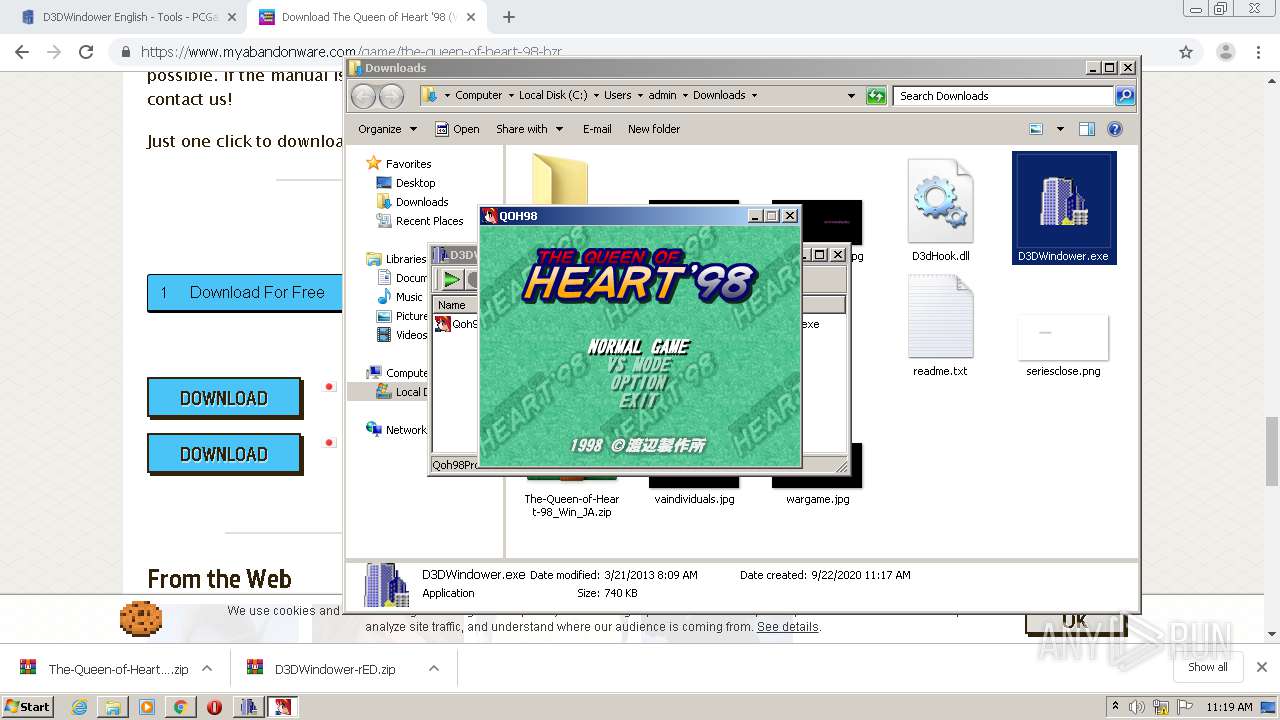
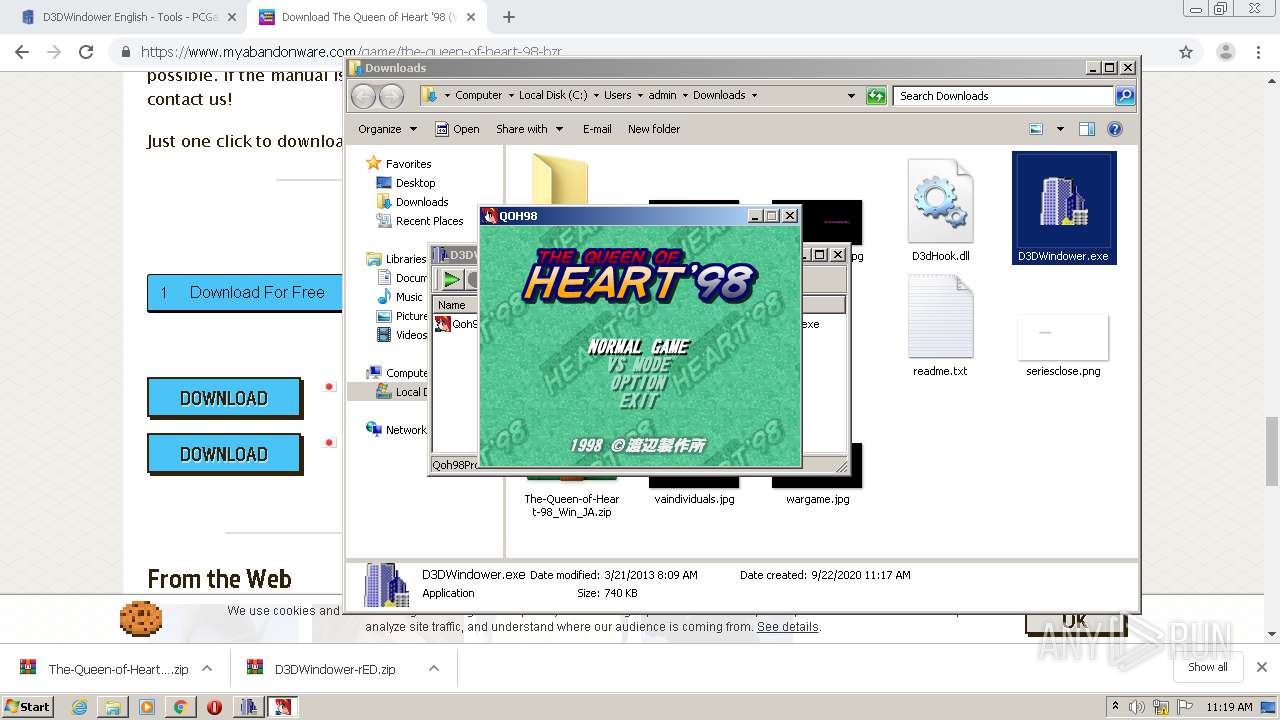
- Qoh98.exe (PID: 5816)
- chrome.exe (PID: 1228)
- host.exe (PID: 2976)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 2088)
- DllHost.exe (PID: 6004)
- D3DWindower.exe (PID: 4284)
- Qoh98.exe (PID: 5180)
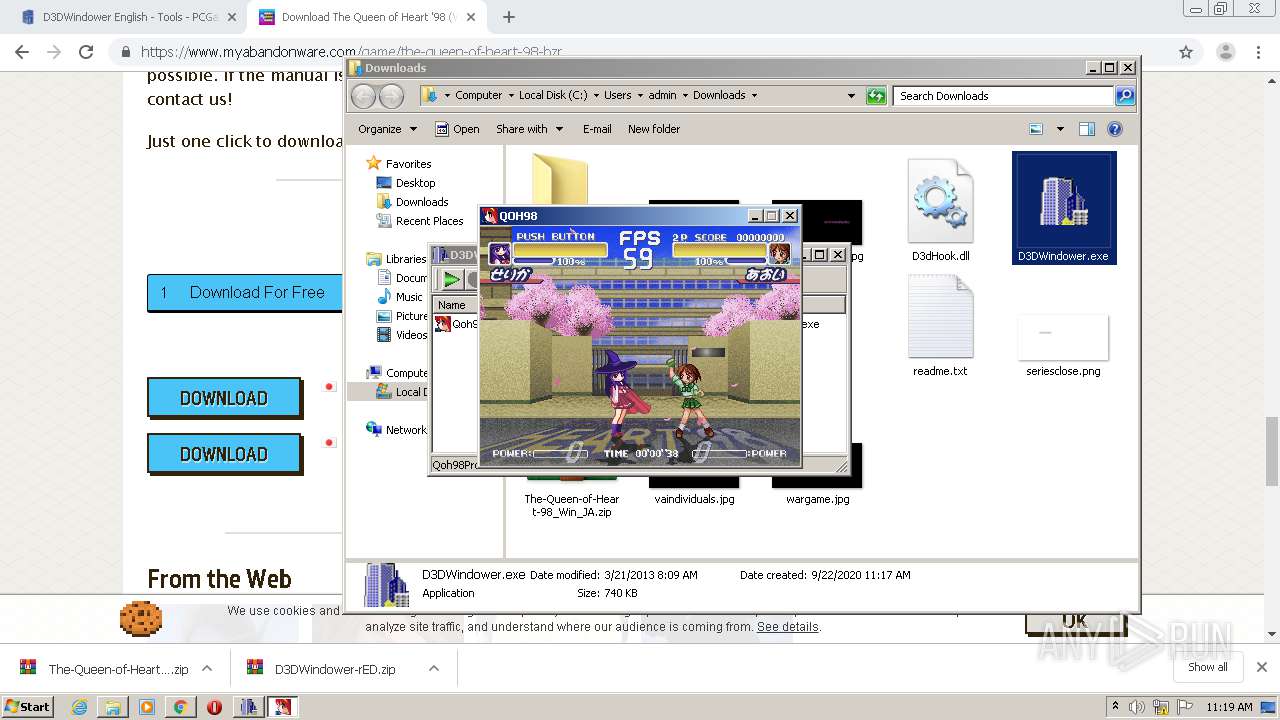
Application was injected by another process
- dwm.exe (PID: 2032)
- ctfmon.exe (PID: 572)
- taskeng.exe (PID: 1972)
- DllHost.exe (PID: 4252)
- explorer.exe (PID: 352)
- host.exe (PID: 2976)
- DllHost.exe (PID: 6004)
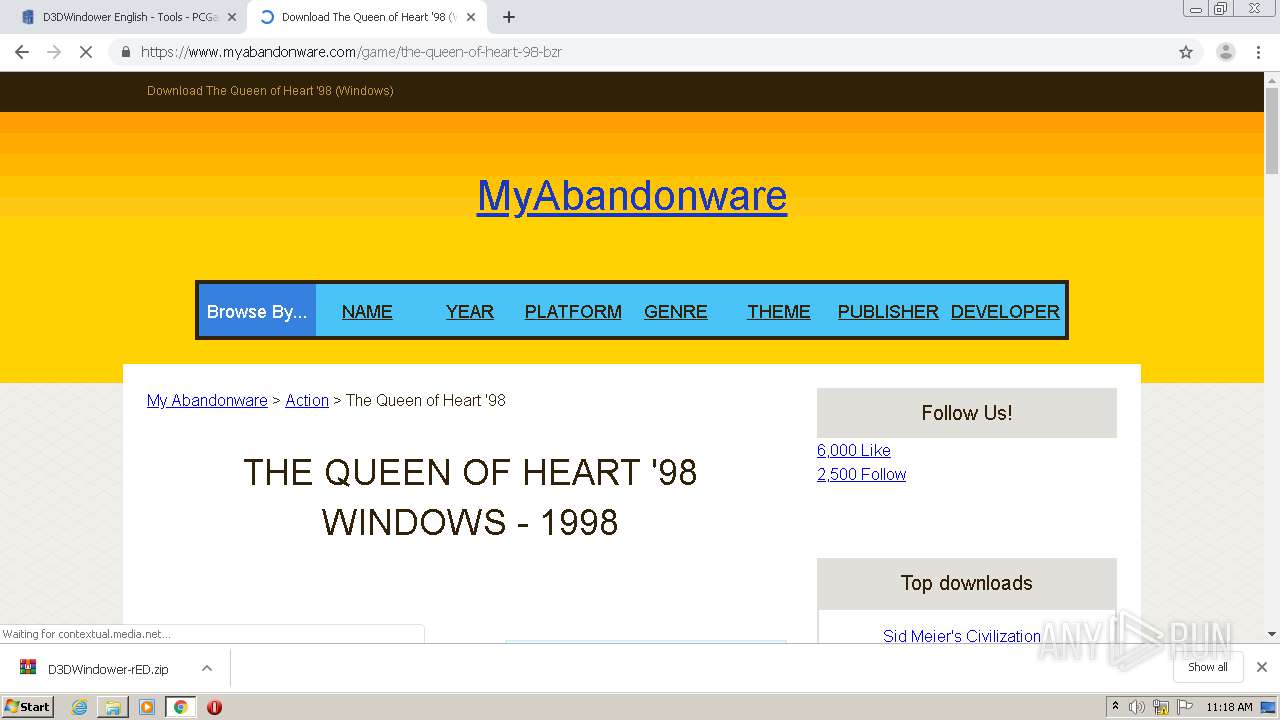
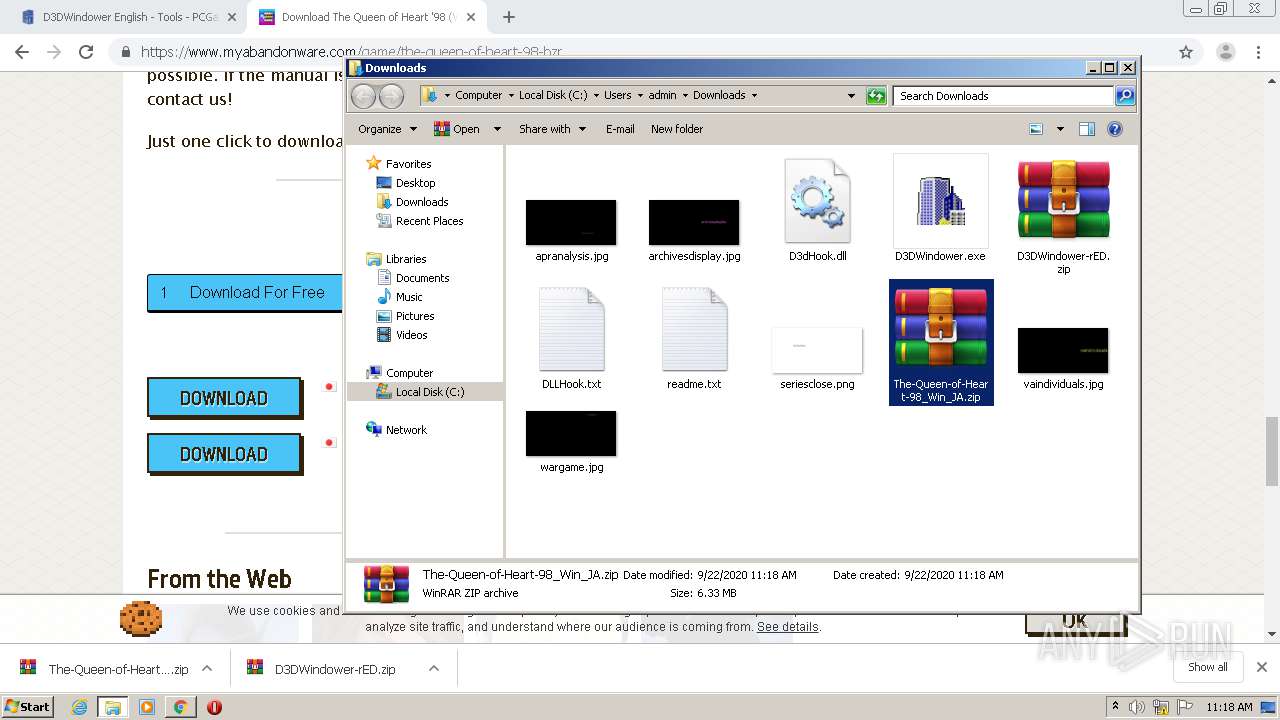
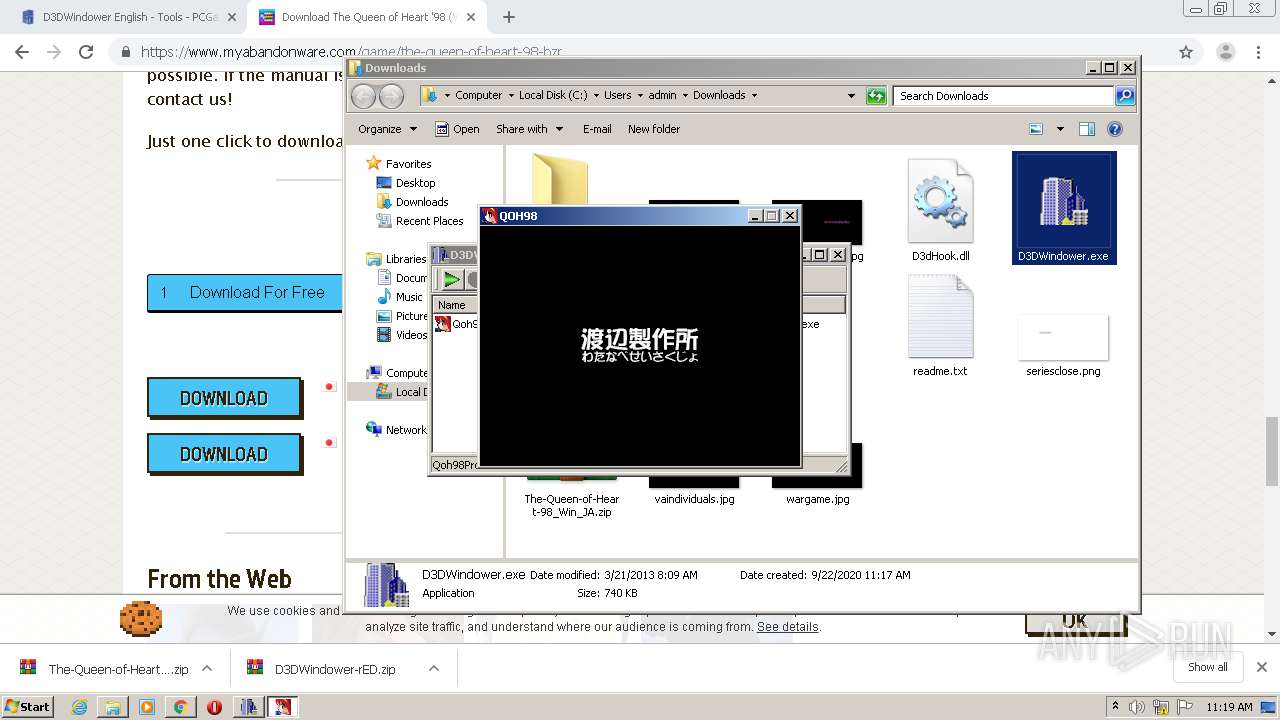
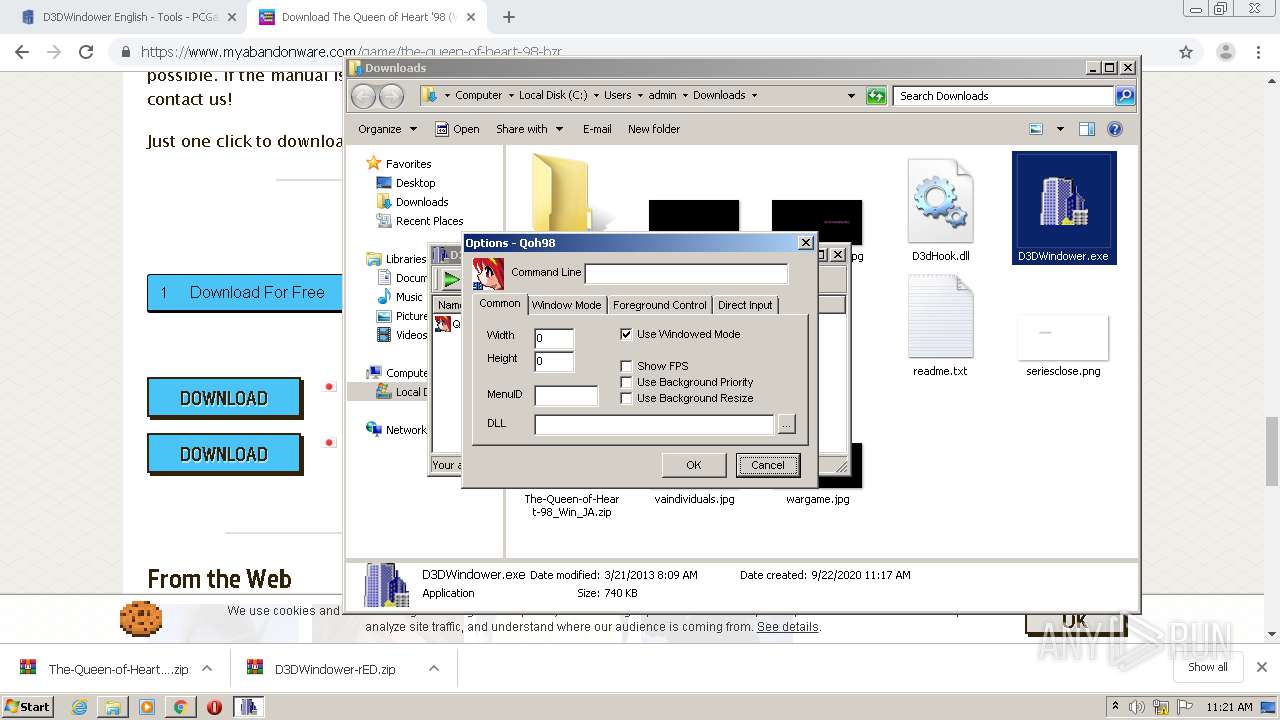
Application was dropped or rewritten from another process
- D3DWindower.exe (PID: 5792)
- Qoh98.exe (PID: 5816)
- D3DWindower.exe (PID: 4284)
- Qoh98.exe (PID: 5180)
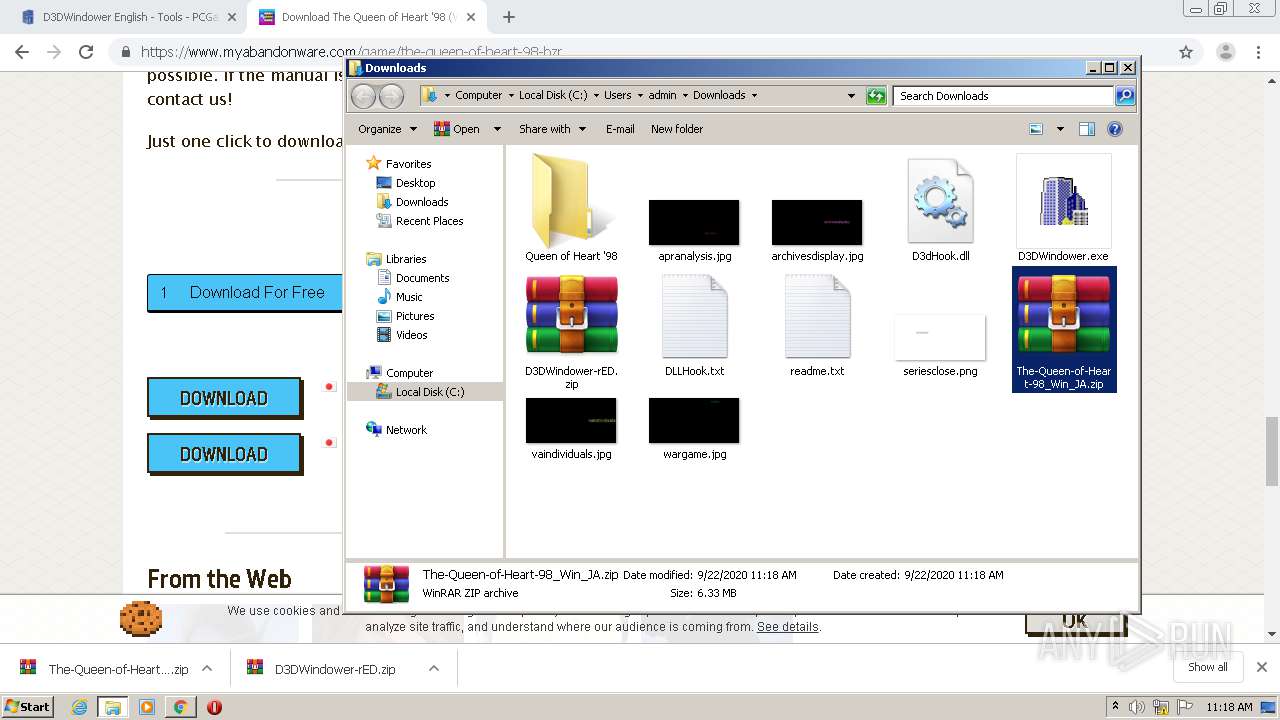
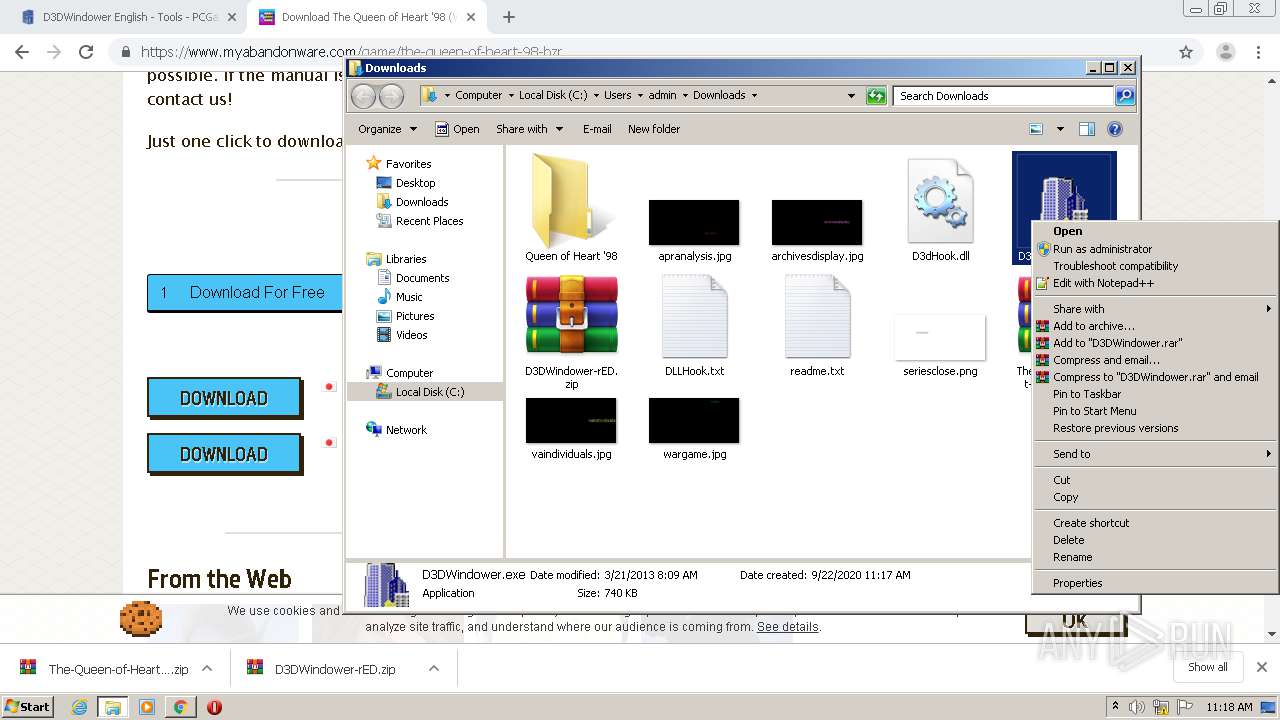
Runs injected code in another process
- D3DWindower.exe (PID: 5792)
- D3DWindower.exe (PID: 4284)
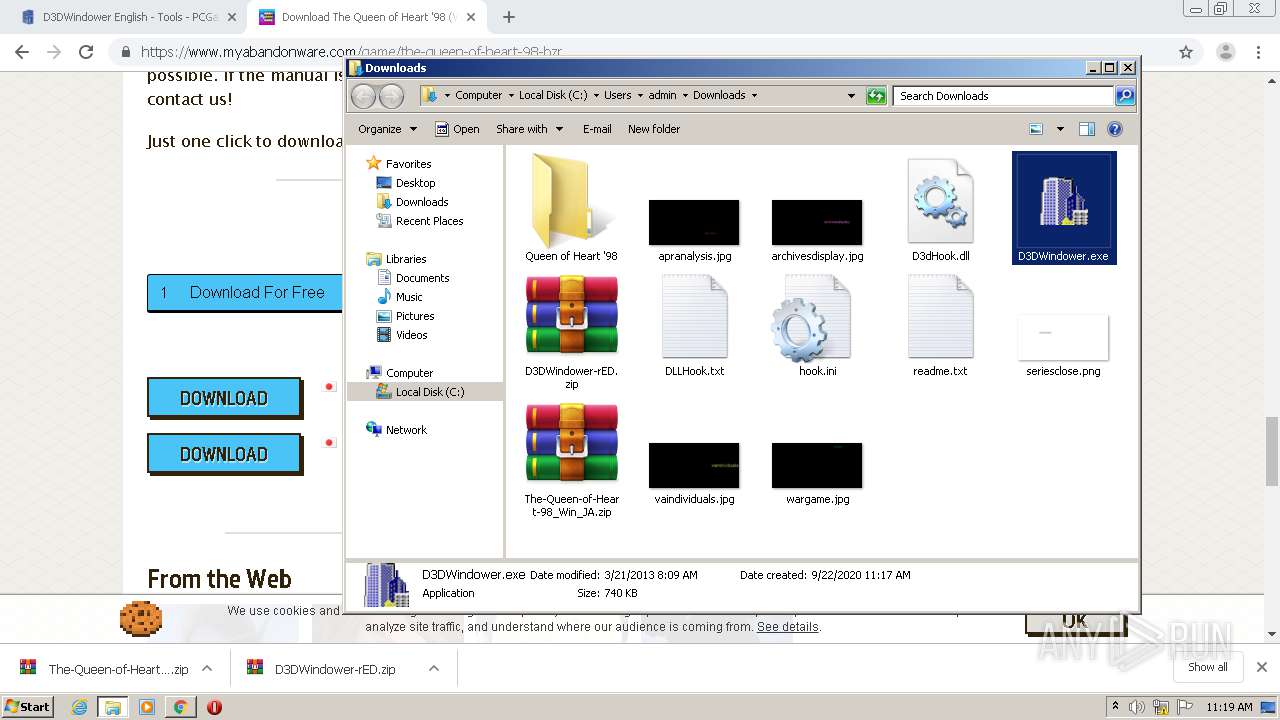
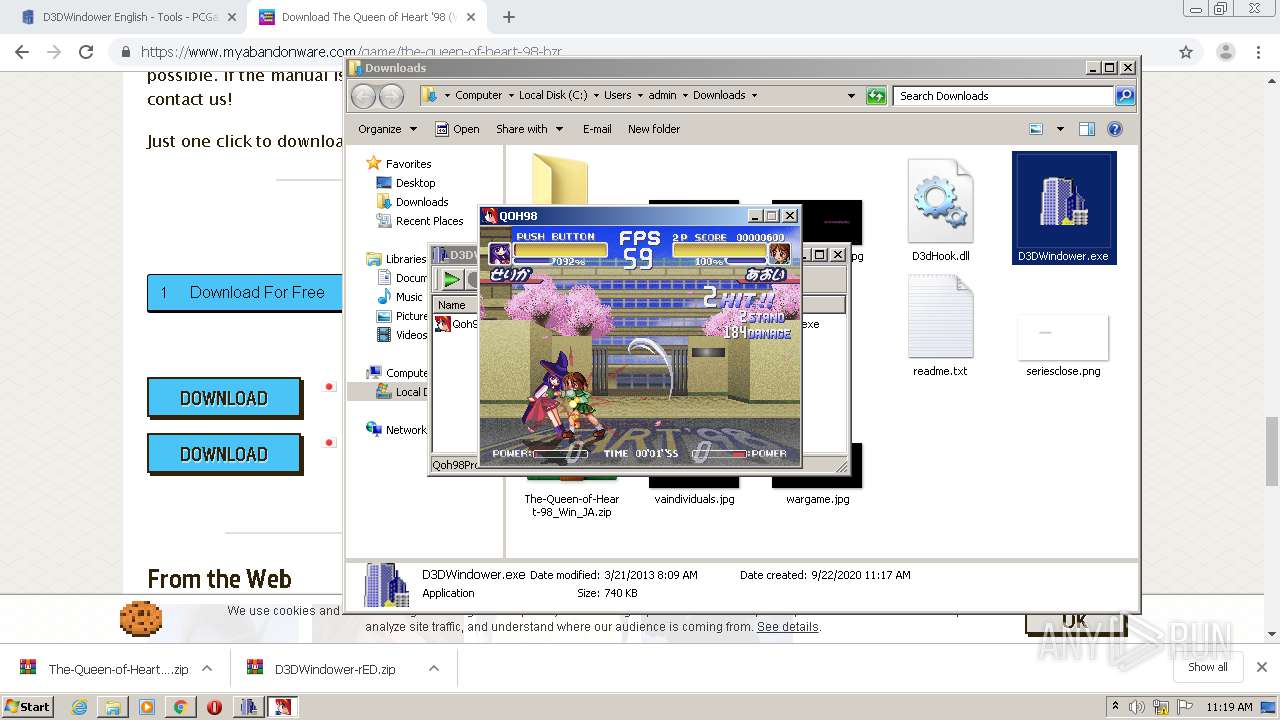
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 4076)
Executable content was dropped or overwritten
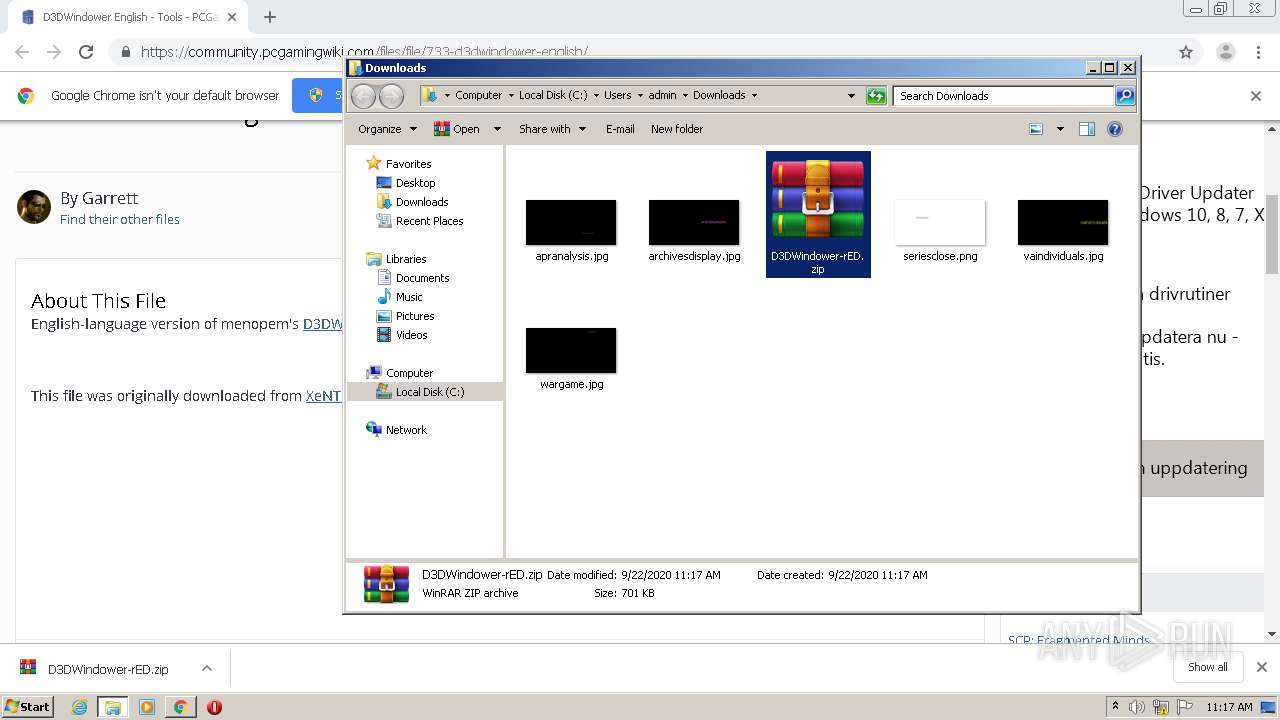
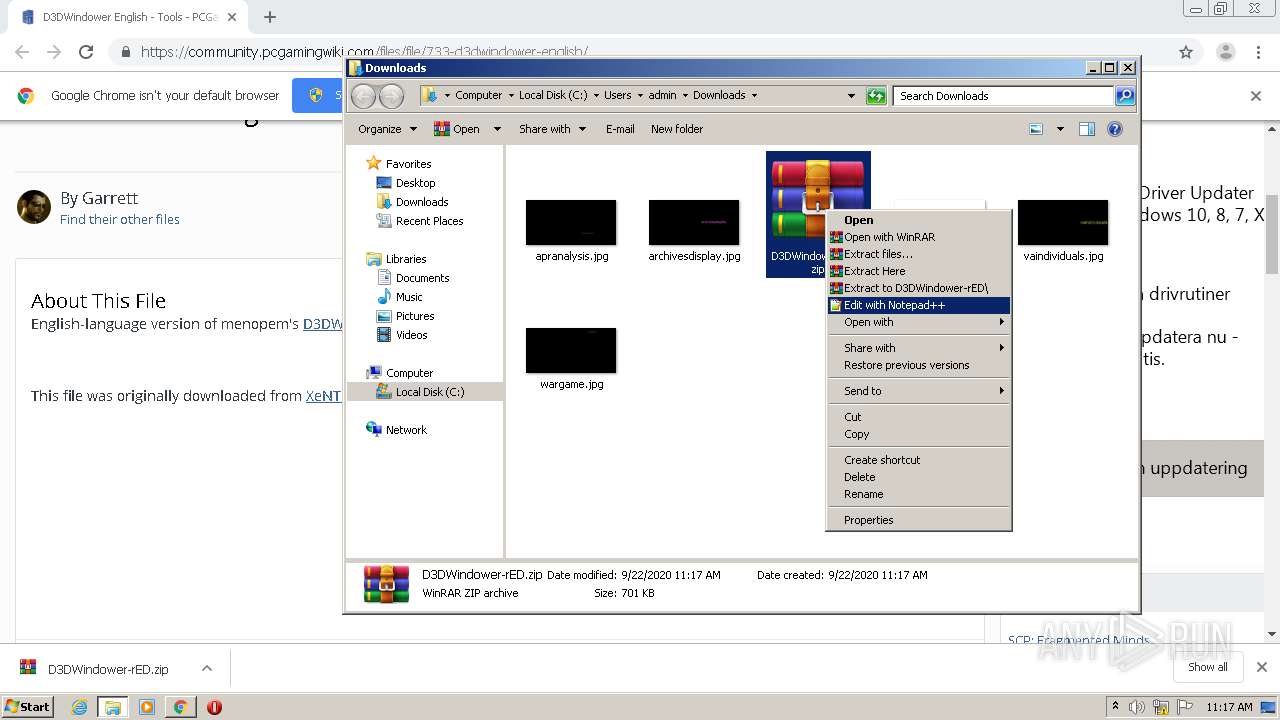
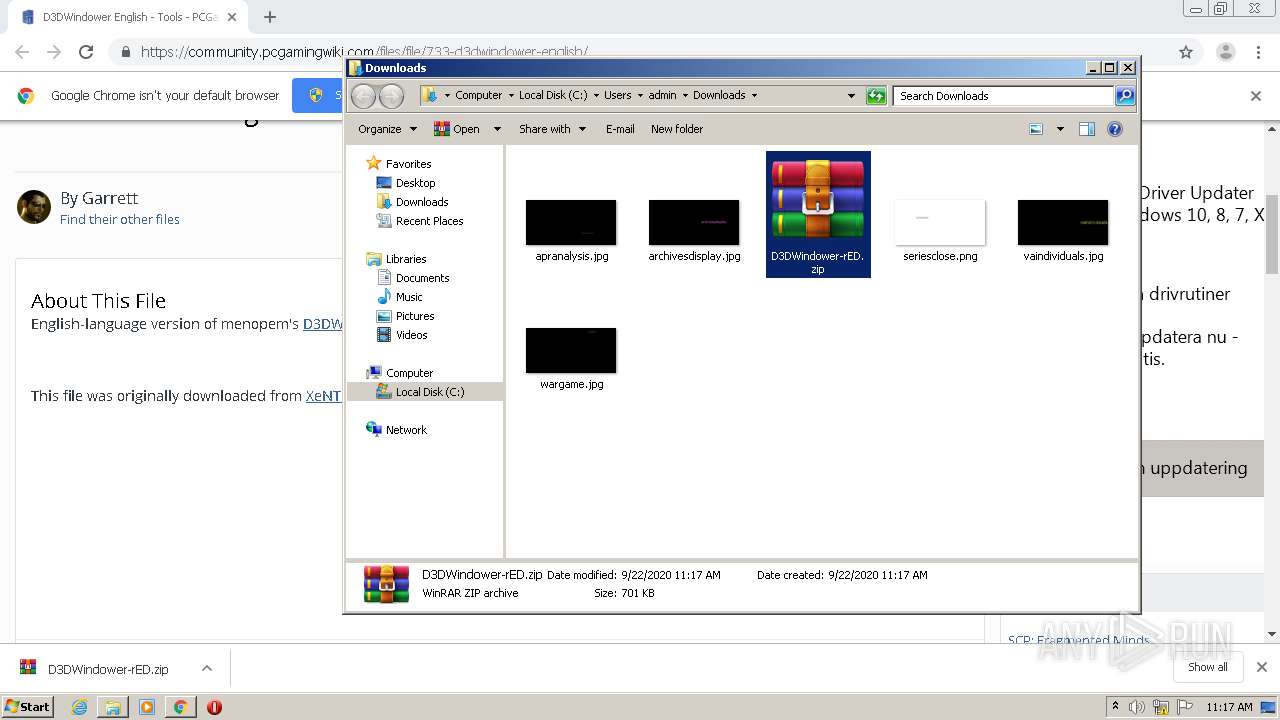
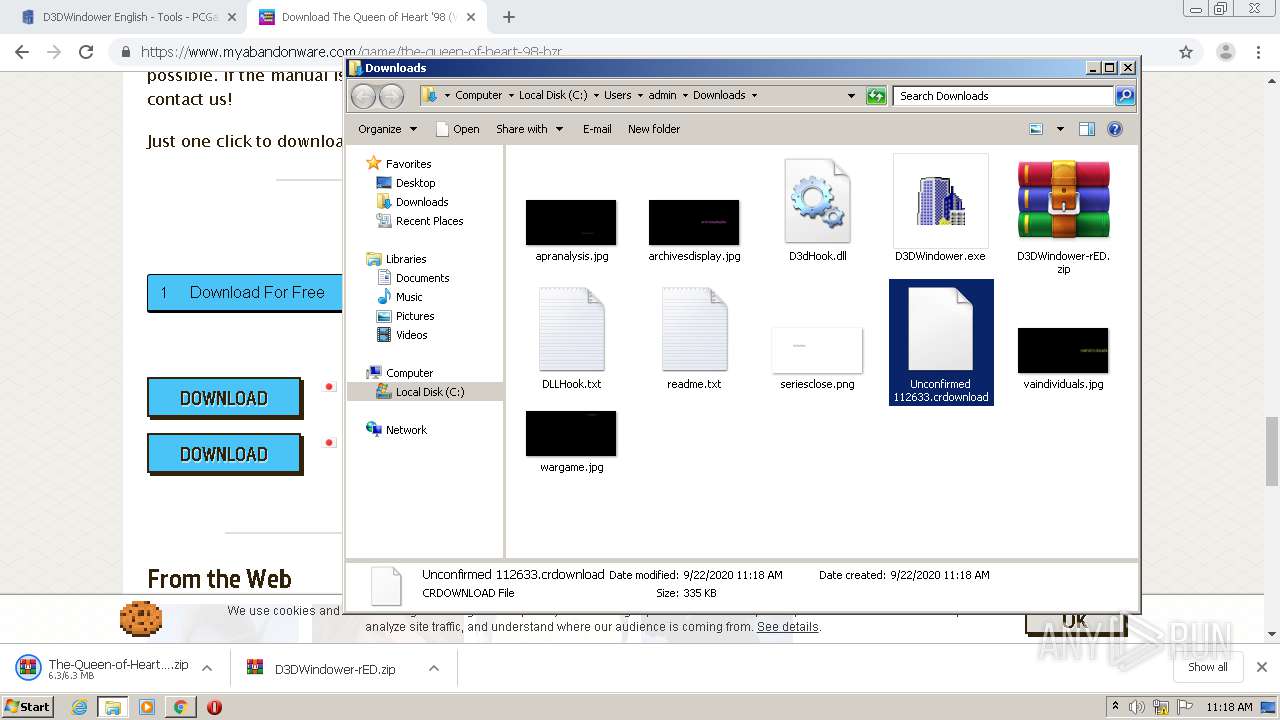
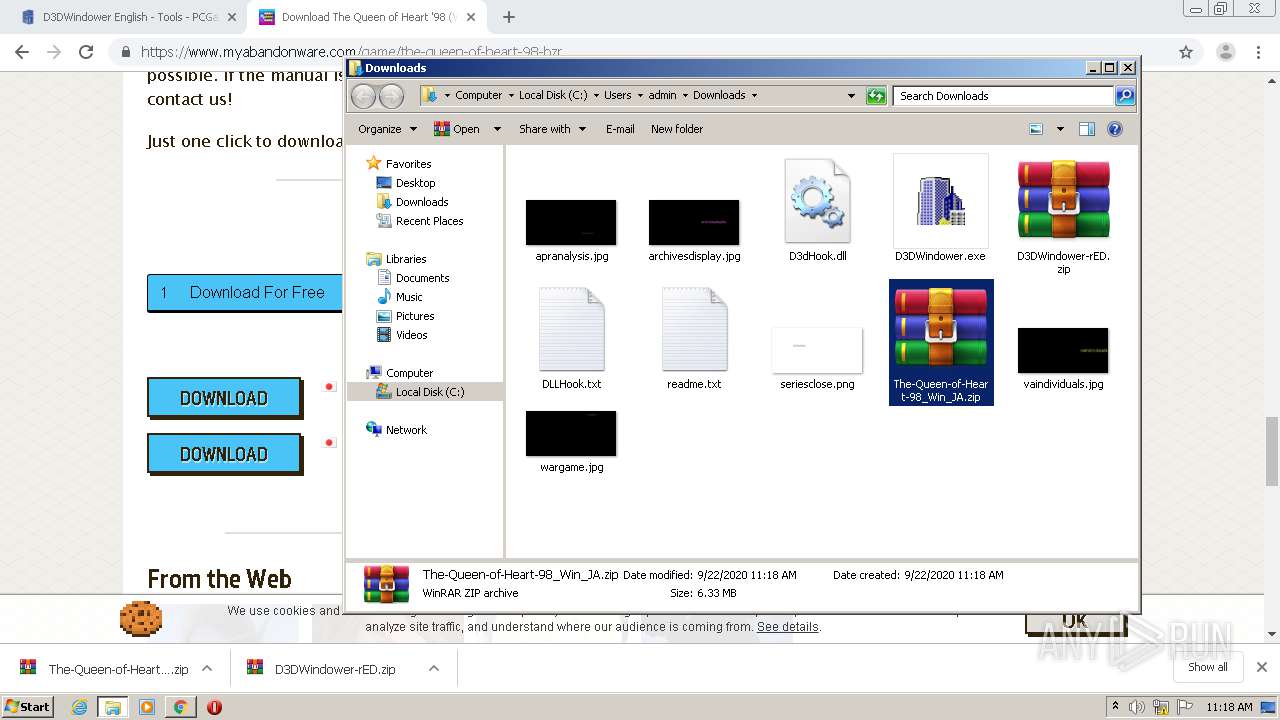
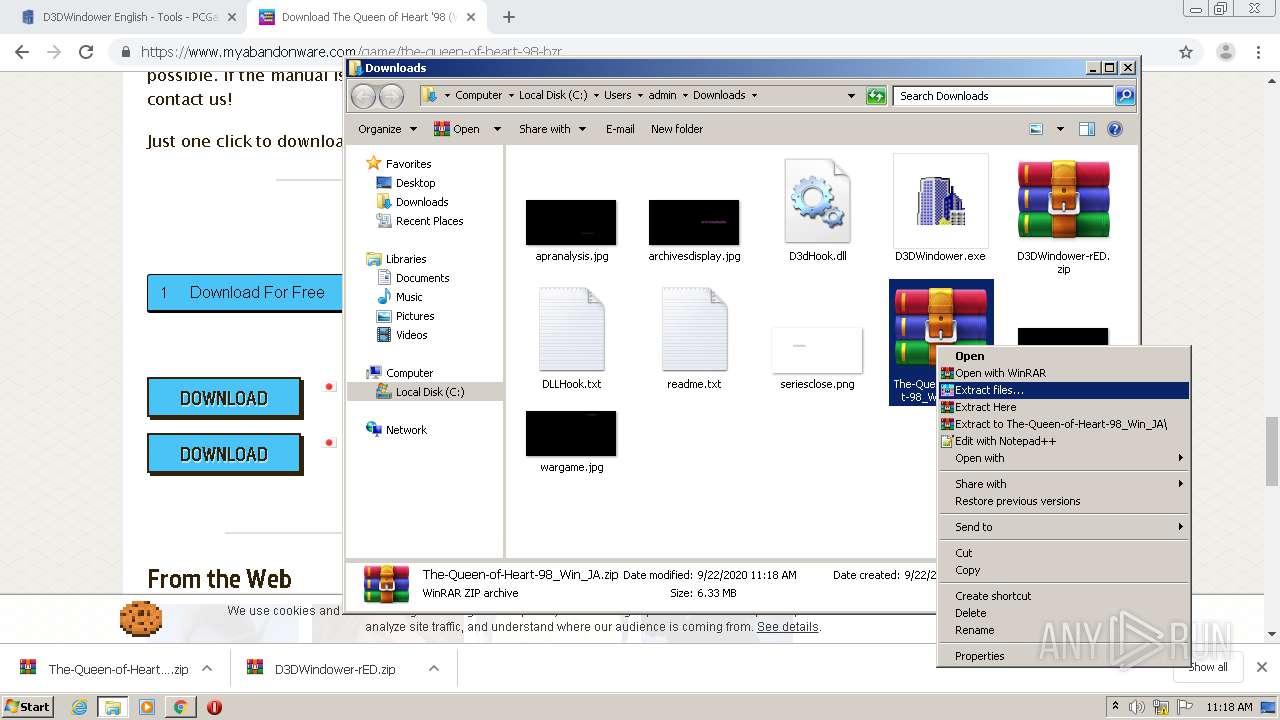
- WinRAR.exe (PID: 3980)
- WinRAR.exe (PID: 4600)
- D3DWindower.exe (PID: 5792)
Creates or modifies windows services
- D3DWindower.exe (PID: 5792)
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 4600)
INFO
Reads the hosts file
- chrome.exe (PID: 1832)
- chrome.exe (PID: 4076)
Application launched itself
- chrome.exe (PID: 4076)
Reads Internet Cache Settings
- chrome.exe (PID: 4076)
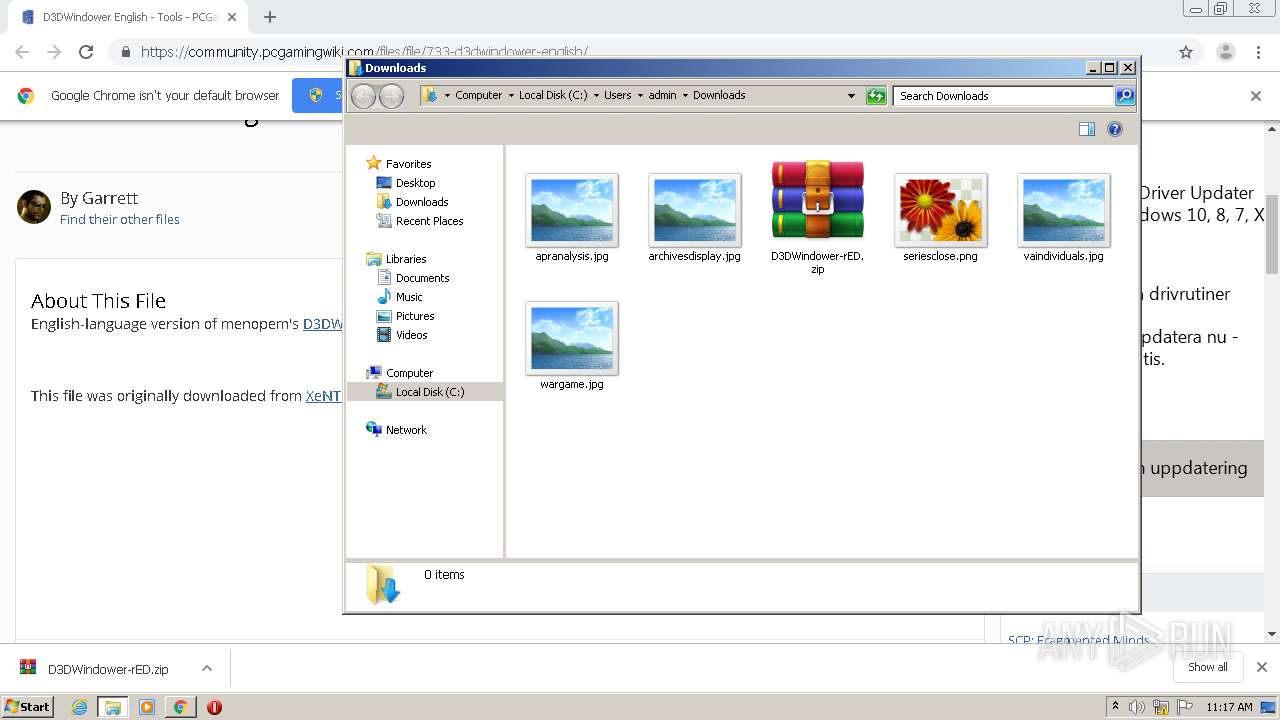
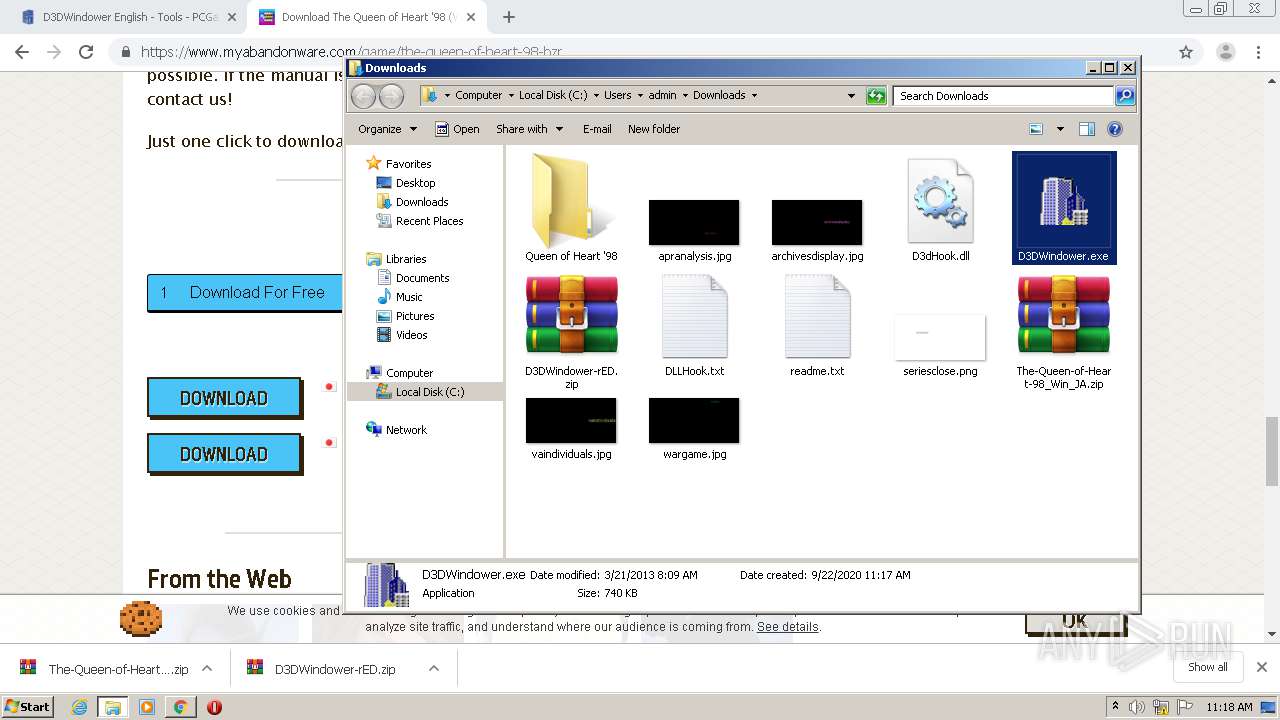
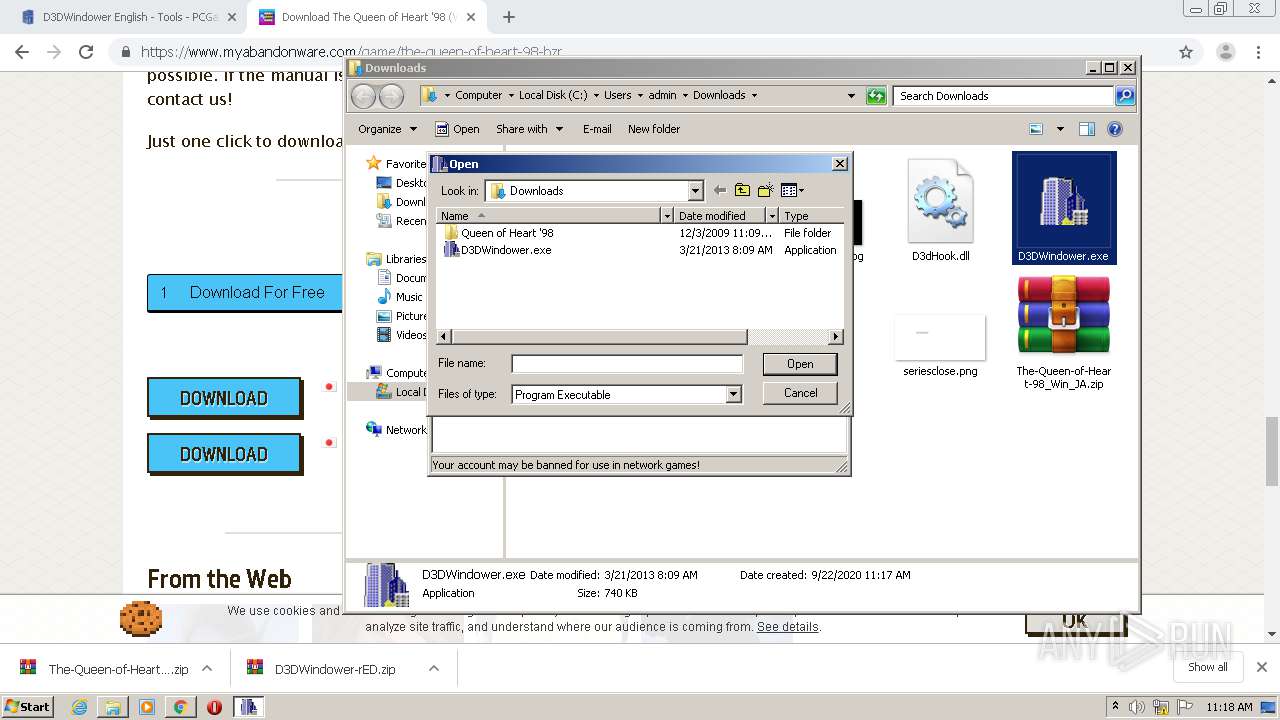
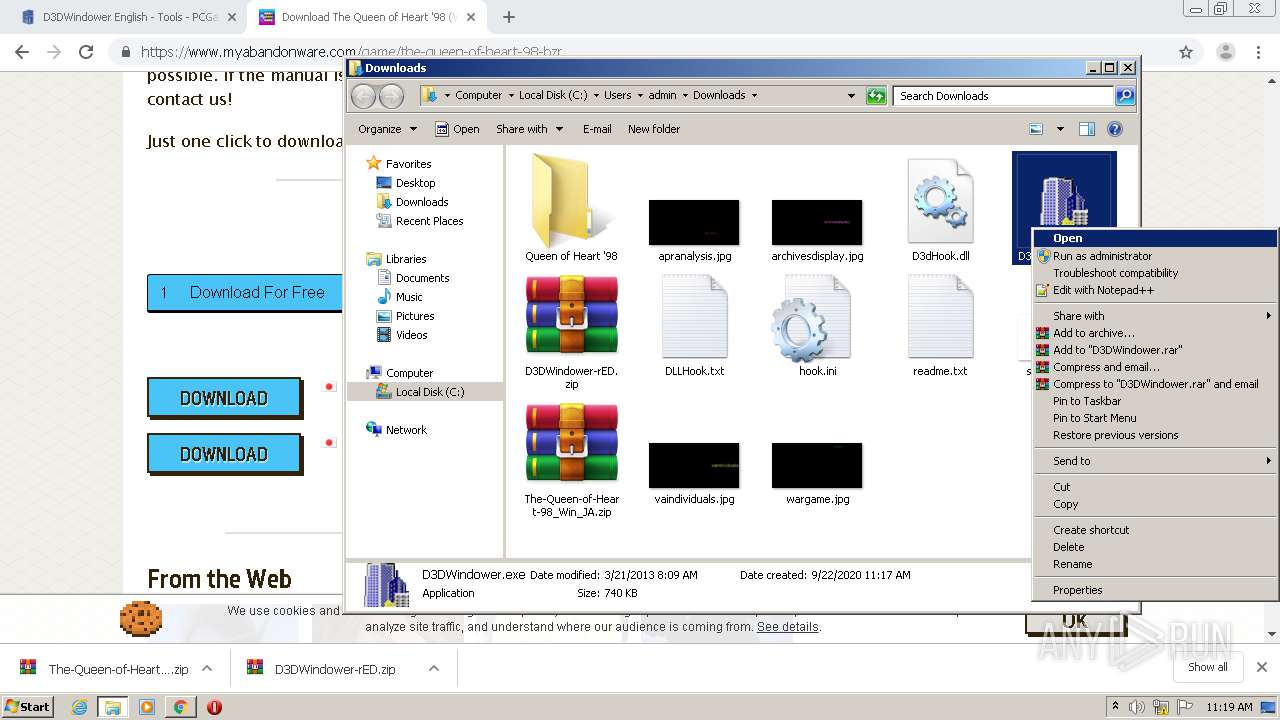
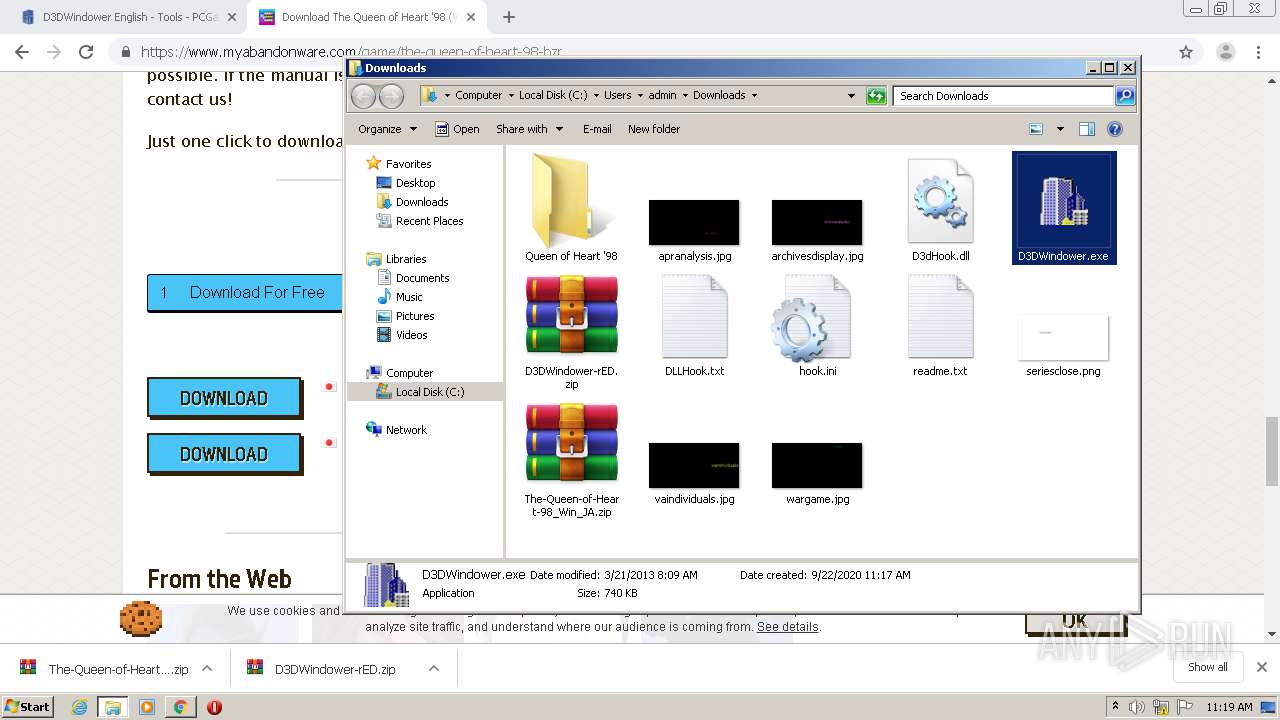
Manual execution by user
- WinRAR.exe (PID: 3980)
- WinRAR.exe (PID: 4600)
- D3DWindower.exe (PID: 5792)
Reads settings of System Certificates
- chrome.exe (PID: 1832)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 4600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
122
Monitored processes
80
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15507276322638371717 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9013113182894168510 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7406041314997919502 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8345975681192010602 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8791665550045654220 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4072 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17376126678713948899 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5052950640469681977,14878844320739956511,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6900455211132301636 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 312
Read events
2 837
Write events
469
Delete events
6
Modification events
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4076-13245243417644625 |
Value: 259 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
4
Suspicious files
363
Text files
250
Unknown types
242
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cde8c62c-74af-4dae-b7ba-e6237aa32a4b.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFed59b.TMP | text | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFed5e9.TMP | text | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed770.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
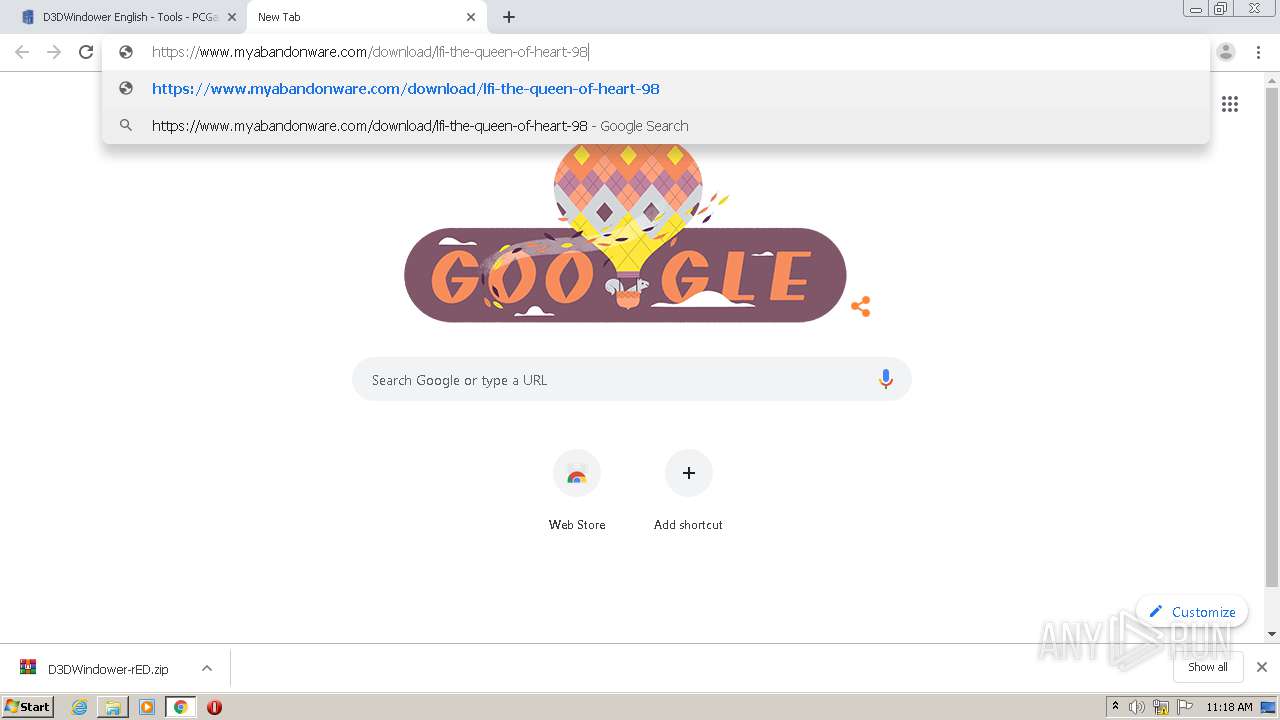
HTTP(S) requests
9
TCP/UDP connections
270
DNS requests
176
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1832 | chrome.exe | GET | 200 | 173.194.188.198:80 | http://r1---sn-4g5ednsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=45.135.187.30&mm=28&mn=sn-4g5ednsd&ms=nvh&mt=1600769719&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 834 Kb | whitelisted |
1832 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1832 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1832 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1832 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1832 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
1832 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1832 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1832 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1832 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
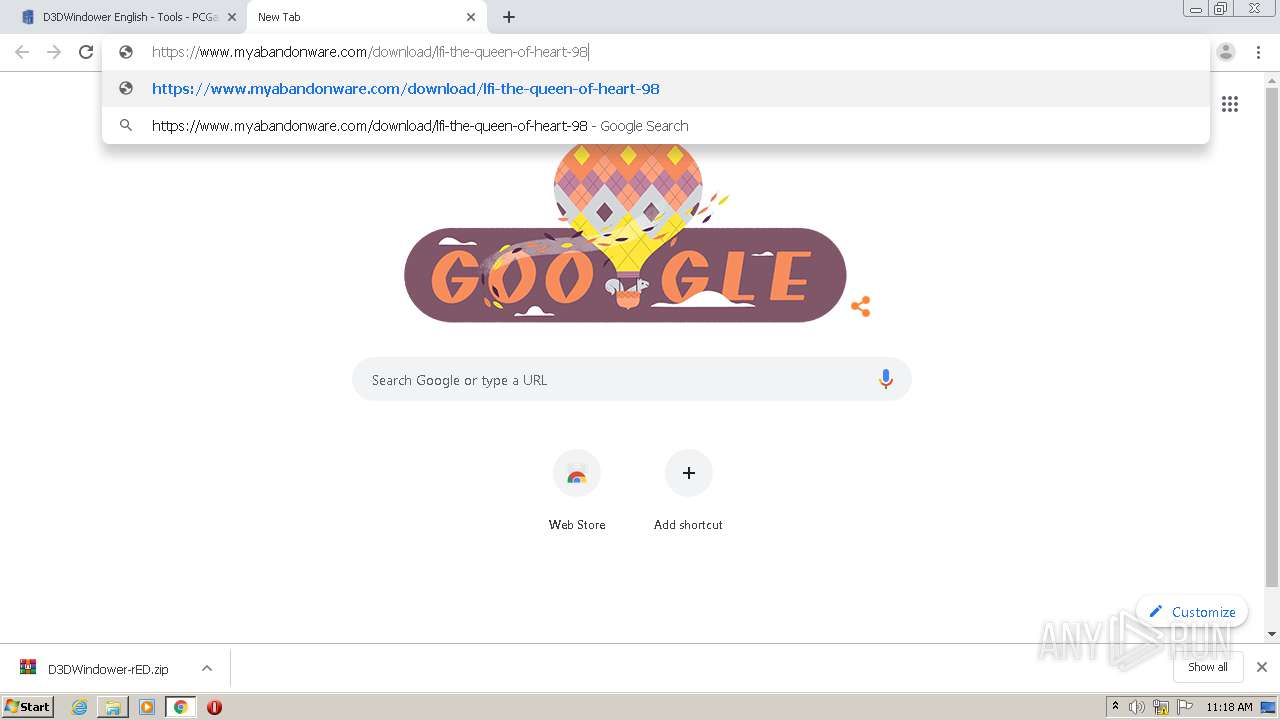
1832 | chrome.exe | 159.69.37.178:443 | community.pcgamingwiki.com | — | US | unknown |
1832 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 151.139.128.11:443 | hb.vntsm.com | Highwinds Network Group, Inc. | US | malicious |
1832 | chrome.exe | 5.101.110.225:443 | pcgamingwiki.ams3.digitaloceanspaces.com | Digital Ocean, Inc. | NL | suspicious |
1832 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 205.185.216.42:443 | pcgw-avatars.sfo2.cdn.digitaloceanspaces.com | Highwinds Network Group, Inc. | US | whitelisted |
1832 | chrome.exe | 138.68.32.225:443 | sfo2.digitaloceanspaces.com | Digital Ocean, Inc. | US | unknown |
1832 | chrome.exe | 173.194.76.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
community.pcgamingwiki.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
hb.vntsm.com |
| whitelisted |
pcgamingwiki.ams3.digitaloceanspaces.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
pcgw-avatars.sfo2.cdn.digitaloceanspaces.com |
| malicious |
sfo2.digitaloceanspaces.com |
| unknown |
stats.g.doubleclick.net |
| whitelisted |