| File name: | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer |
| Full analysis: | https://app.any.run/tasks/3eeb5ae9-dace-4176-af58-bcc0aec24638 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 22:39:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 2453CE5EB9620D15AAF46E0BFB255248 |
| SHA1: | A9D7A4F067E0F50323C3DBAEAEDE78E1FDB614D3 |
| SHA256: | A451AA6BC6FB898608CDD3E7C15DBF3DBBE6EB12037851026FA80DC58C63353C |
| SSDEEP: | 49152:A9BS9BW9Bu9BC9BO9BC9BW9BE9BS9BW9Bu9BC9BO9BC9BW9B09BGKv7EXo/Tbmvo:5XoPmeewAOf8P0Om2QcAy+ |
MALICIOUS
The process uses screensaver hijack for persistence
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
UAC/LUA settings modification
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Changes the autorun value in the registry
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Changes image file execution options
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
SUSPICIOUS
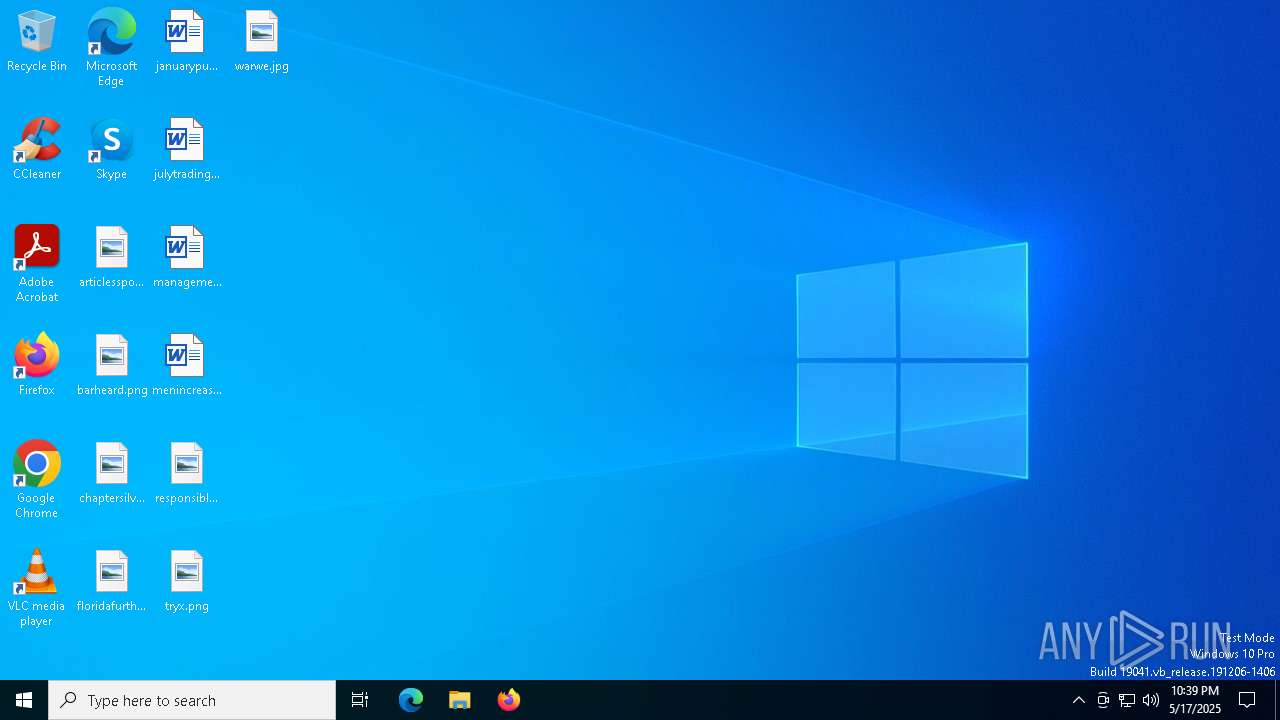
Changes the desktop background image
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Creates file in the systems drive root
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Executable content was dropped or overwritten
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Reads security settings of Internet Explorer
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Write to the desktop.ini file (may be used to cloak folders)
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
INFO
Checks supported languages
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
The sample compiled with english language support
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Reads the computer name
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Create files in a temporary directory
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Failed to create an executable file in Windows directory
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Auto-launch of the file from Registry key
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
UPX packer has been detected
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Checks proxy server information
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
- slui.exe (PID: 2240)
Creates files or folders in the user directory
- 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe (PID: 7052)
Reads the software policy settings
- slui.exe (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:01:12 14:58:39+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 57344 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 98304 |
| EntryPoint: | 0x26540 |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.2008 |
| ProductVersionNumber: | 6.1.0.2008 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | http:/www.narutogames.com |
| ProductName: | Gaara The Kazekage By : Paraysutki VM Community |
| Mission: | Destroy HokageFile, KSpoold, AutoitV3, Autoruner, BlueFantasi, Sys, VBSvir, PornFile, and Kick Anbu-Team-Sampit |
| FileVersion: | 06.01.2008 (A) Update |
| ProductVersion: | 06.01.2008 (A) Update |
| InternalName: | Kazekage Was Here |
| FileDescription: | Kazekage Games Action |
| LegalCopyright: | © Kota Cantik - Paray City |
| OriginalFileName: | Kazekage of the Sand |
Total processes
139
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1040 | ping -a -l www.rasasayang.com.my 65500 | C:\Windows\SysWOW64\PING.EXE | — | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PING.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | ping -a -l www.duniasex.com 65500 | C:\Windows\SysWOW64\PING.EXE | — | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PING.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PING.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PING.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | ping -a -l www.rasasayang.com.my 65500 | C:\Windows\SysWOW64\PING.EXE | — | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5428 | ping -a -l www.duniasex.com 65500 | C:\Windows\SysWOW64\PING.EXE | — | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | ping -a -l www.rasasayang.com.my 65500 | C:\Windows\SysWOW64\PING.EXE | — | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 818
Read events
5 311
Write events
507
Delete events
0
Modification events
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | ConvertedWallpaper |
Value: C:\WINDOWS\Fonts\The Kazekage.jpg | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\WINDOWS\Fonts\The Kazekage.jpg | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 2 | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | ConvertedWallpaper |
Value: Fonts\The Kazekage.jpg | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | SCRNSAVE.EXE |
Value: ssmarque.scr | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | ScreenSaveTimeOut |
Value: 400 | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Screen Saver.Marquee |
| Operation: | write | Name: | BackgroundColor |
Value: 0 0 0 | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Screen Saver.Marquee |
| Operation: | write | Name: | Font |
Value: Blackadder ITC | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Screen Saver.Marquee |
| Operation: | write | Name: | Mode.EXE |
Value: 1 | |||
| (PID) Process: | (7052) 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\Control Panel\Screen Saver.Marquee |
| Operation: | write | Name: | Size |
Value: 72 | |||
Executable files
5
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\admin Games\Naruto games.exe | executable | |
MD5:2453CE5EB9620D15AAF46E0BFB255248 | SHA256:A451AA6BC6FB898608CDD3E7C15DBF3DBBE6EB12037851026FA80DC58C63353C | |||
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\Users\admin\Desktop\Gaara The Kazekage.exe | executable | |
MD5:2453CE5EB9620D15AAF46E0BFB255248 | SHA256:A451AA6BC6FB898608CDD3E7C15DBF3DBBE6EB12037851026FA80DC58C63353C | |||
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\admin Games\Readme.txt | text | |
MD5:BB5D6ABDF8D0948AC6895CE7FDFBC151 | SHA256:5DB2E0915B5464D32E83484F8AE5E3C73D2C78F238FDE5F58F9B40DBB5322DE8 | |||
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\admin Games\Gaara go to Kazekage.exe | executable | |
MD5:2453CE5EB9620D15AAF46E0BFB255248 | SHA256:A451AA6BC6FB898608CDD3E7C15DBF3DBBE6EB12037851026FA80DC58C63353C | |||
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\SysWOW64\Desktop.ini | ini | |
MD5:64ACFA7E03B01F48294CF30D201A0026 | SHA256:BA8159D865D106E7B4D0043007A63D1541E1DE455DC8D7FF0EDD3013BD425C62 | |||
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\admin Games\Anbu Team Sampit (Nothing).exe | executable | |
MD5:2453CE5EB9620D15AAF46E0BFB255248 | SHA256:A451AA6BC6FB898608CDD3E7C15DBF3DBBE6EB12037851026FA80DC58C63353C | |||
| 7052 | 2025-05-17_2453ce5eb9620d15aaf46e0bfb255248_amadey_black-basta_elex_luca-stealer.exe | C:\admin Games\Gaara games - Naruto.exe | executable | |
MD5:2453CE5EB9620D15AAF46E0BFB255248 | SHA256:A451AA6BC6FB898608CDD3E7C15DBF3DBBE6EB12037851026FA80DC58C63353C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
43
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | RUXIMICS.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2568 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2568 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2568 | RUXIMICS.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2568 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
220.255.0.0.in-addr.arpa |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |