| File name: | amba_5.1.0.13_win--1548386245064.exe |
| Full analysis: | https://app.any.run/tasks/5ec3c625-f53d-43df-9fdb-182b1235dedf |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2020, 19:07:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 797A5915FE4D1679391C195B5649DC14 |
| SHA1: | 75A82ED83E738BCA97FF1C36CC017948FEC605DB |
| SHA256: | A44B00C55CEAE7EF02FAD9CC3B85AC4376BA98B309525EE65168A75DC9FA7413 |
| SSDEEP: | 49152:4PdnZmFDBPG0UQhF2MfpD9P30qOSs0Xx13HGBEubCoxyQkBPZT46JSuD10UpVA:CdnZmF1PmxsHP9ThYyoje546JSuc |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- amba_5.1.0.13_win--1548386245064.tmp (PID: 572)
Loads dropped or rewritten executable
- FosIPCCoreManager.exe (PID: 1696)
- FosIPCCoreManager.exe (PID: 2820)
- regsvr32.exe (PID: 3152)
- FosIPCCore.exe (PID: 2488)
Application was dropped or rewritten from another process
- loopback.exe (PID: 3232)
- FosIPCCoreManager.exe (PID: 2820)
- FosIPCCoreManager.exe (PID: 1696)
- FosIPCCore.exe (PID: 2488)
SUSPICIOUS
Executable content was dropped or overwritten
- amba_5.1.0.13_win--1548386245064.exe (PID: 2928)
- amba_5.1.0.13_win--1548386245064.exe (PID: 3836)
- amba_5.1.0.13_win--1548386245064.tmp (PID: 572)
Executed as Windows Service
- FosIPCCoreManager.exe (PID: 1696)
Creates files in the Windows directory
- FosIPCCoreManager.exe (PID: 1696)
Creates files in the user directory
- FosIPCCore.exe (PID: 2488)
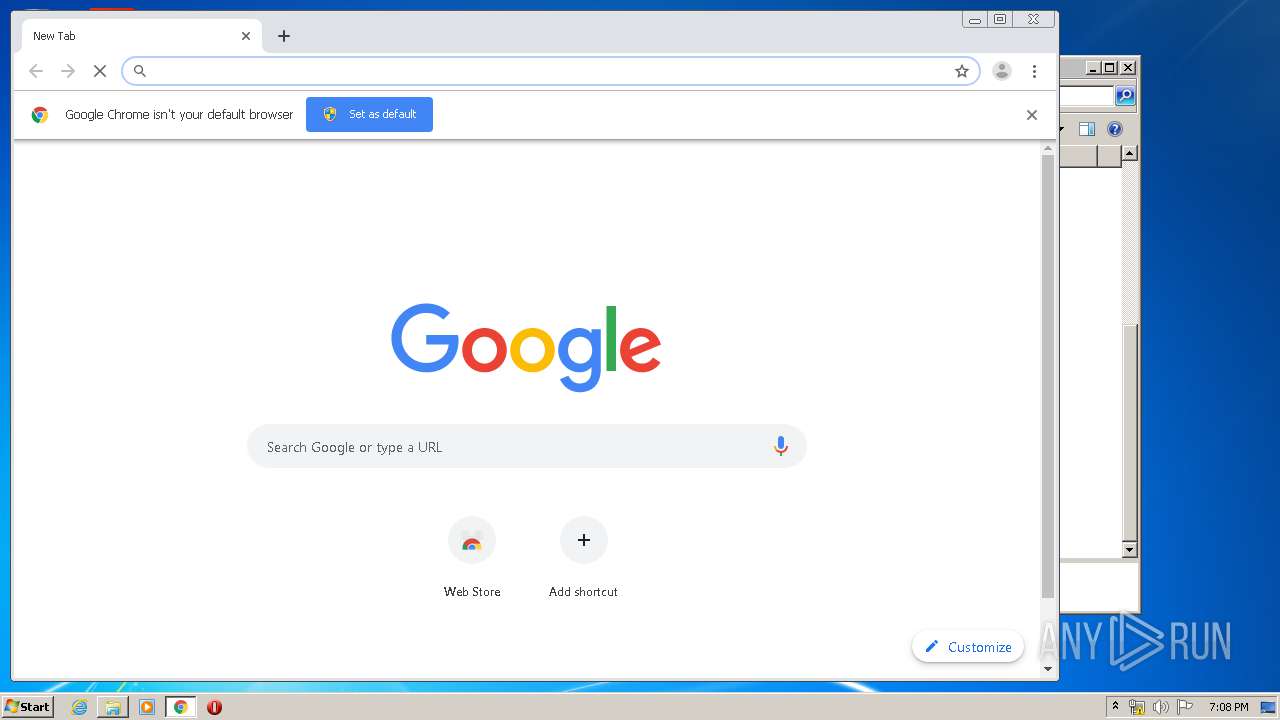
Modifies files in Chrome extension folder
- chrome.exe (PID: 2864)
INFO
Application was dropped or rewritten from another process
- amba_5.1.0.13_win--1548386245064.tmp (PID: 376)
- amba_5.1.0.13_win--1548386245064.tmp (PID: 572)
Loads dropped or rewritten executable
- amba_5.1.0.13_win--1548386245064.tmp (PID: 572)
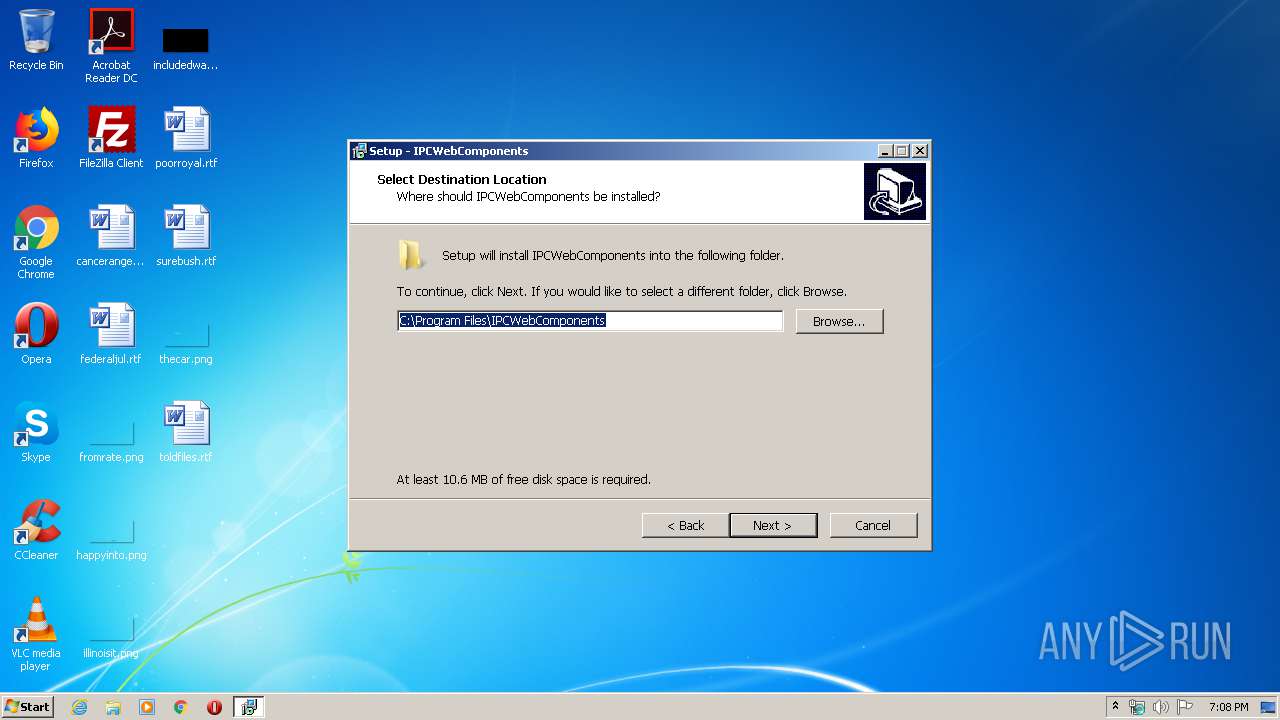
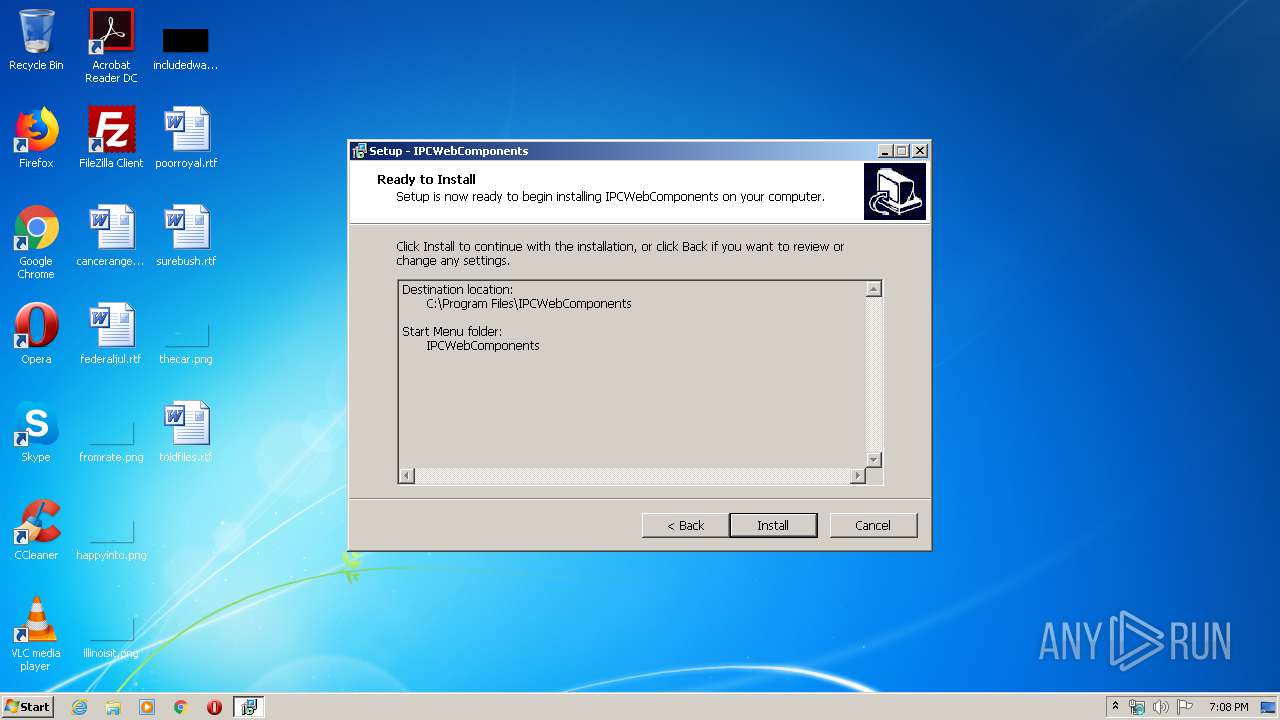
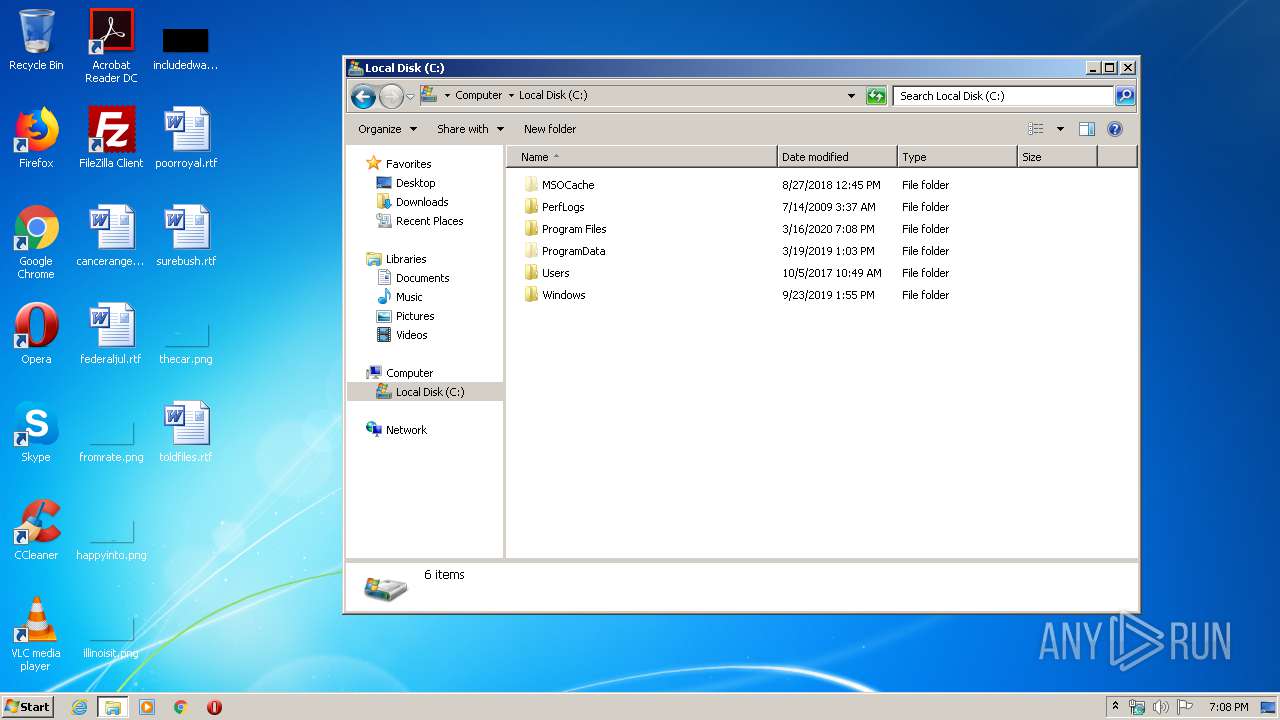
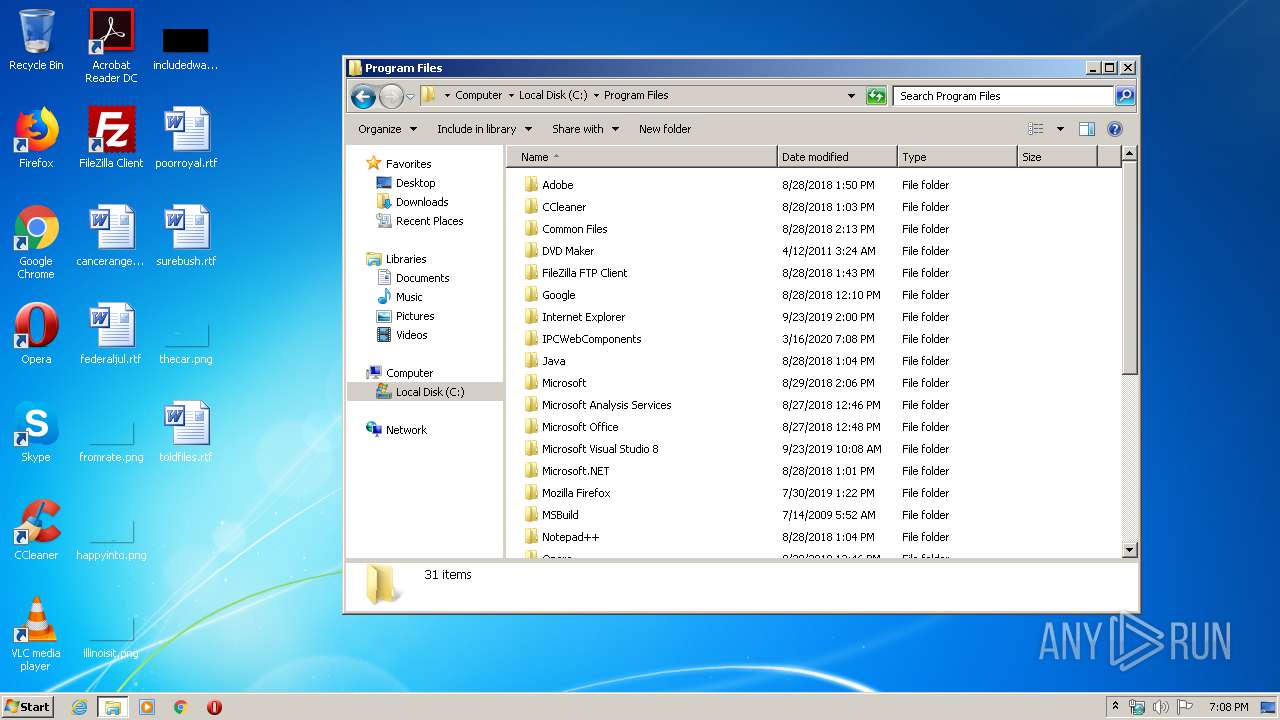
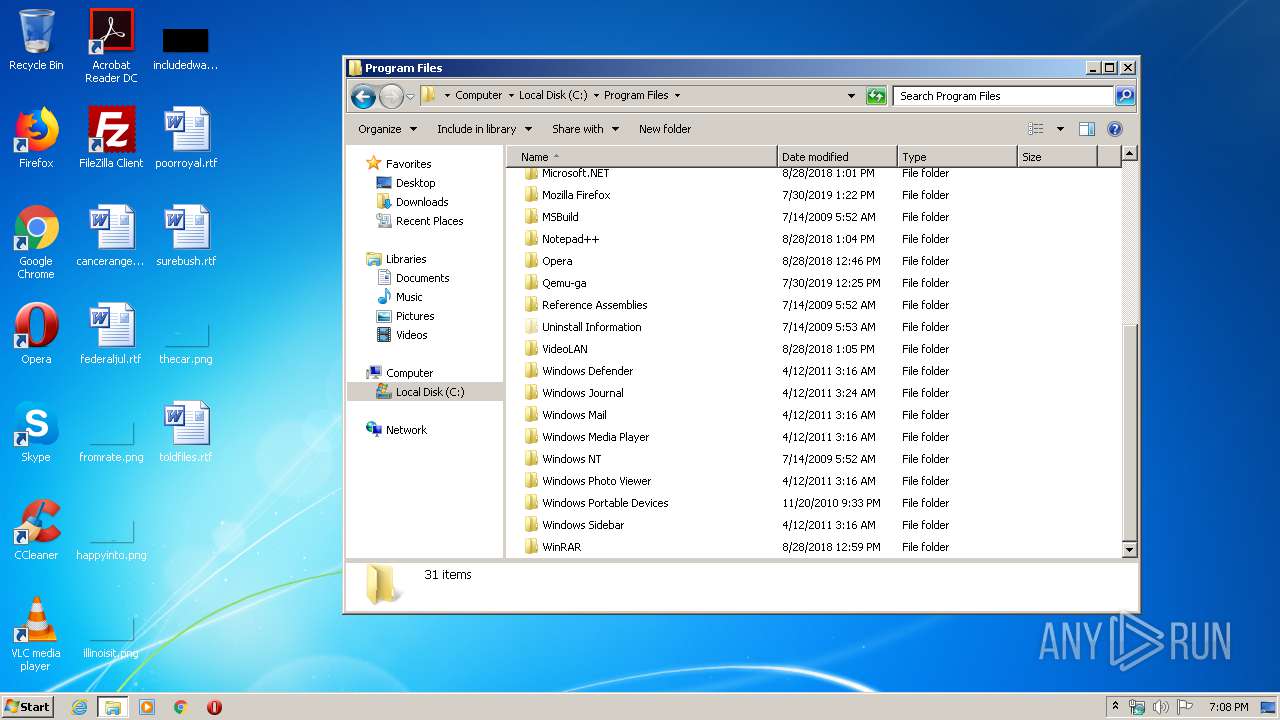
Creates files in the program directory
- amba_5.1.0.13_win--1548386245064.tmp (PID: 572)
Application launched itself
- chrome.exe (PID: 2864)
Manual execution by user
- chrome.exe (PID: 2864)
Creates a software uninstall entry
- amba_5.1.0.13_win--1548386245064.tmp (PID: 572)
Reads the hosts file
- chrome.exe (PID: 2864)
- chrome.exe (PID: 3264)
Reads settings of System Certificates
- chrome.exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41984 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xac2c |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | ASCII |
| Comments: | 此安装程序由 Inno Setup 构建。 |
| CompanyName: | FOSCAM |
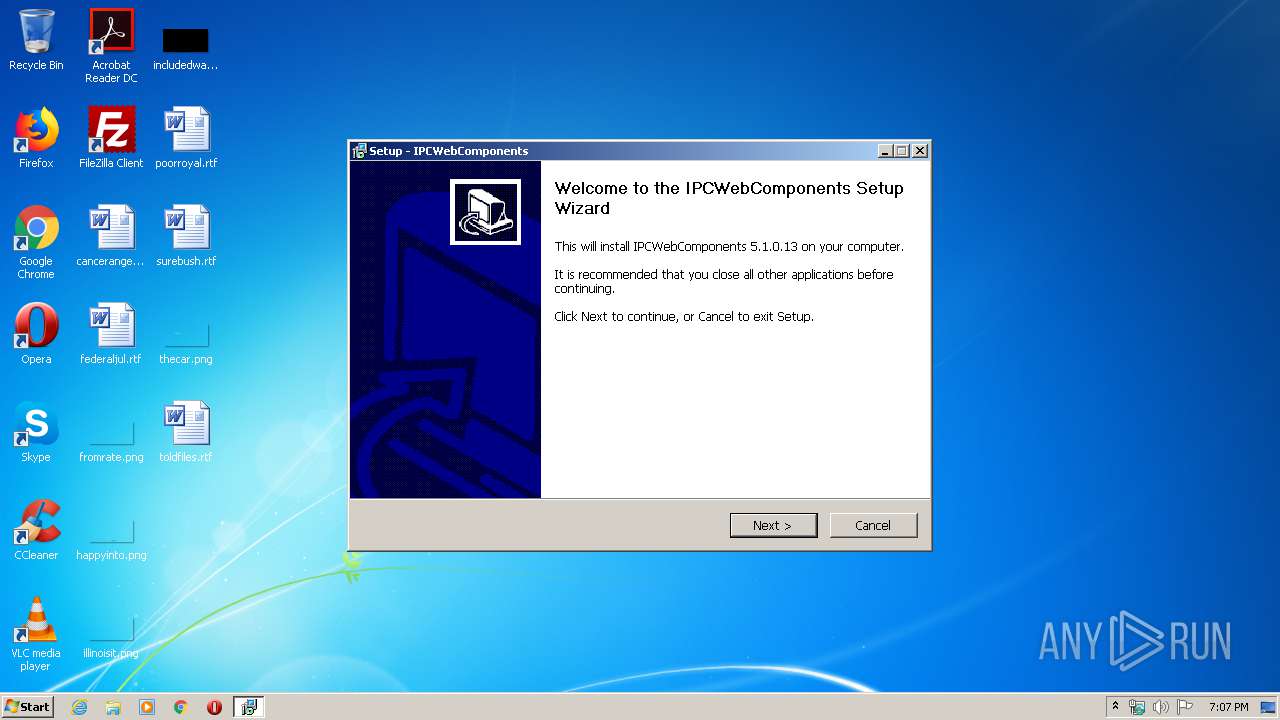
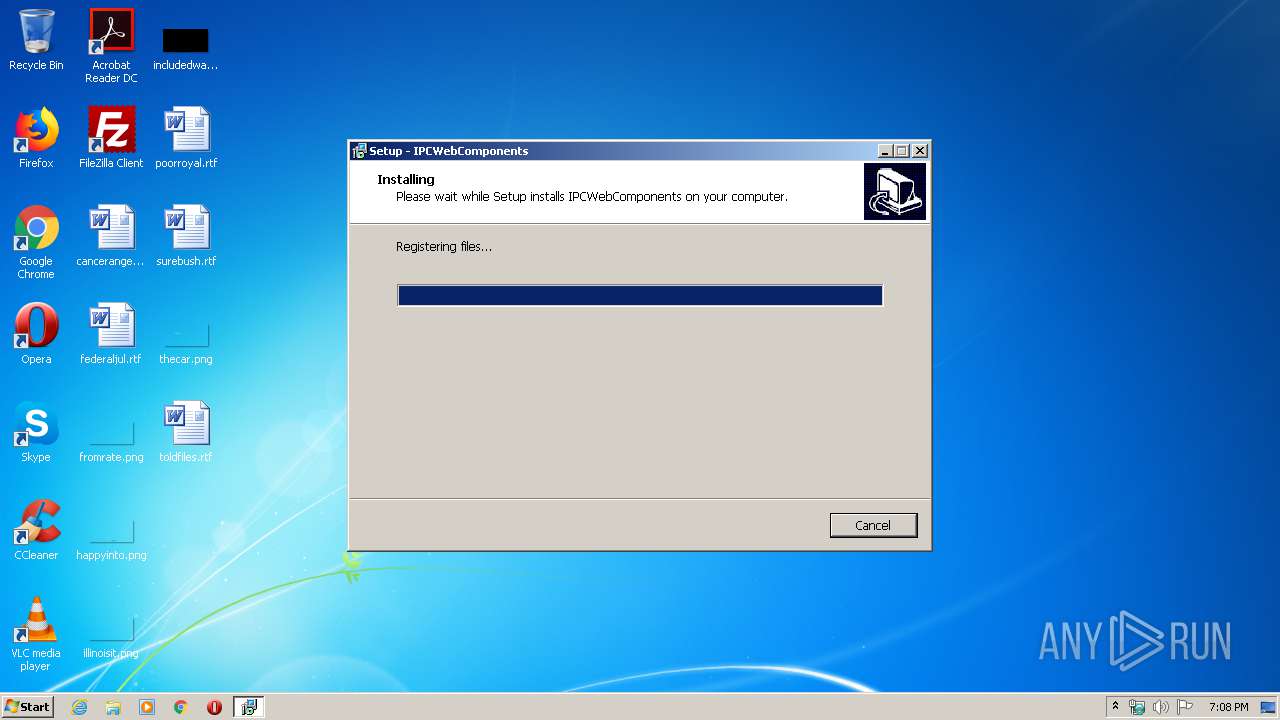
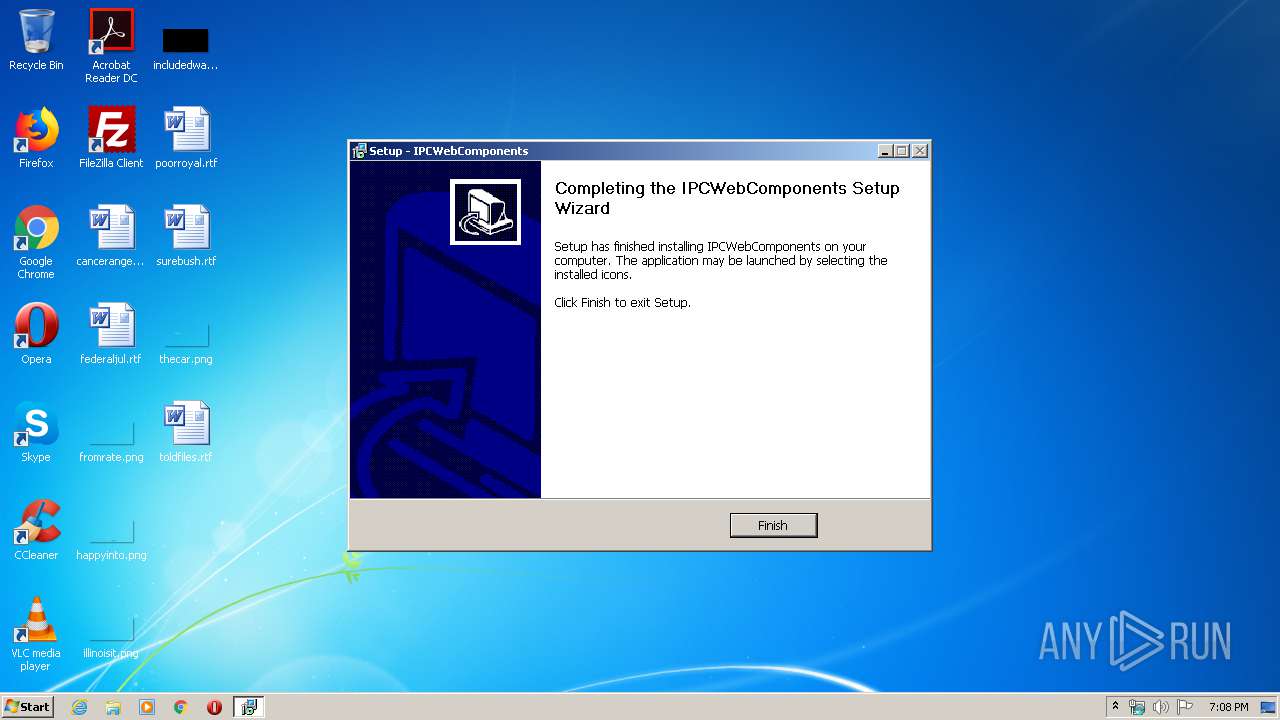
| FileDescription: | IPCWebComponents Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | IPCWebComponents |
| ProductVersion: | 5.1.0.13 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | 此安装程序由 Inno Setup 构建。 |
| CompanyName: | FOSCAM |
| FileDescription: | IPCWebComponents Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | IPCWebComponents |
| ProductVersion: | 5.1.0.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A364 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75232 |
BSS | 0x0000D000 | 0x00000E88 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000094C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.42897 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00002600 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.95343 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 5.50613 | 322 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 5.62693 | 278 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 5.87174 | 254 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
83
Monitored processes
40
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Users\admin\AppData\Local\Temp\is-V07E9.tmp\amba_5.1.0.13_win--1548386245064.tmp" /SL5="$90140,2729924,56832,C:\Users\admin\AppData\Local\Temp\amba_5.1.0.13_win--1548386245064.exe" | C:\Users\admin\AppData\Local\Temp\is-V07E9.tmp\amba_5.1.0.13_win--1548386245064.tmp | — | amba_5.1.0.13_win--1548386245064.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 安装/卸载 Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 572 | "C:\Users\admin\AppData\Local\Temp\is-1PKN3.tmp\amba_5.1.0.13_win--1548386245064.tmp" /SL5="$701CA,2729924,56832,C:\Users\admin\AppData\Local\Temp\amba_5.1.0.13_win--1548386245064.exe" /SPAWNWND=$A012E /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\is-1PKN3.tmp\amba_5.1.0.13_win--1548386245064.tmp | amba_5.1.0.13_win--1548386245064.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 安装/卸载 Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,14832873431864129908,2887788954741333052,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3670358240460362211 --mojo-platform-channel-handle=4248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,14832873431864129908,2887788954741333052,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=948271650888552159 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2736 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,14832873431864129908,2887788954741333052,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18341735188469589273 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,14832873431864129908,2887788954741333052,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10603317969265673861 --mojo-platform-channel-handle=3276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\IPCWebComponents\FosIPCCoreManager.exe" | C:\Program Files\IPCWebComponents\FosIPCCoreManager.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,14832873431864129908,2887788954741333052,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16725444822110673817 --mojo-platform-channel-handle=3756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,14832873431864129908,2887788954741333052,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7631521104913933389 --mojo-platform-channel-handle=2568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 369
Read events
1 224
Write events
134
Delete events
11
Modification events
| (PID) Process: | (572) amba_5.1.0.13_win--1548386245064.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 3C020000C4263C30C6FBD501 | |||
| (PID) Process: | (572) amba_5.1.0.13_win--1548386245064.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 37C19054F3753EB9FD14CD97AE0F85C5F62D3510A7B110ED4AFE50DEC557F528 | |||
| (PID) Process: | (572) amba_5.1.0.13_win--1548386245064.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (572) amba_5.1.0.13_win--1548386245064.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\IPCWebComponents\avcodec-57.dll | |||
| (PID) Process: | (572) amba_5.1.0.13_win--1548386245064.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 4A243402A8EAD786DB7F8F47F07F066153015497E9B9888E3BA9E6F46B75DCA7 | |||
| (PID) Process: | (3152) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{3CB639F8-8566-4252-A01E-90CED93D8662}\1.0 |
| Operation: | write | Name: | |
Value: ocxIPcam ActiveX ¿Ø¼þÄ£¿é | |||
| (PID) Process: | (3152) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{3CB639F8-8566-4252-A01E-90CED93D8662}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (3152) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{3CB639F8-8566-4252-A01E-90CED93D8662}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Program Files\IPCWebComponents\ocxIPCReg.ocx | |||
| (PID) Process: | (3152) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{3CB639F8-8566-4252-A01E-90CED93D8662}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3152) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{782AE8DF-324B-4A91-AC19-95DBEB211CD1} |
| Operation: | write | Name: | |
Value: _DocxIPcam | |||
Executable files
21
Suspicious files
37
Text files
344
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-PQKE1.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-80FV4.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-U450S.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-KAF6Q.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-RJEMQ.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-S9J20.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-39J26.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-EGECC.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-867DJ.tmp | — | |
MD5:— | SHA256:— | |||
| 572 | amba_5.1.0.13_win--1548386245064.tmp | C:\Program Files\IPCWebComponents\is-JAUQU.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
37
DNS requests
19
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
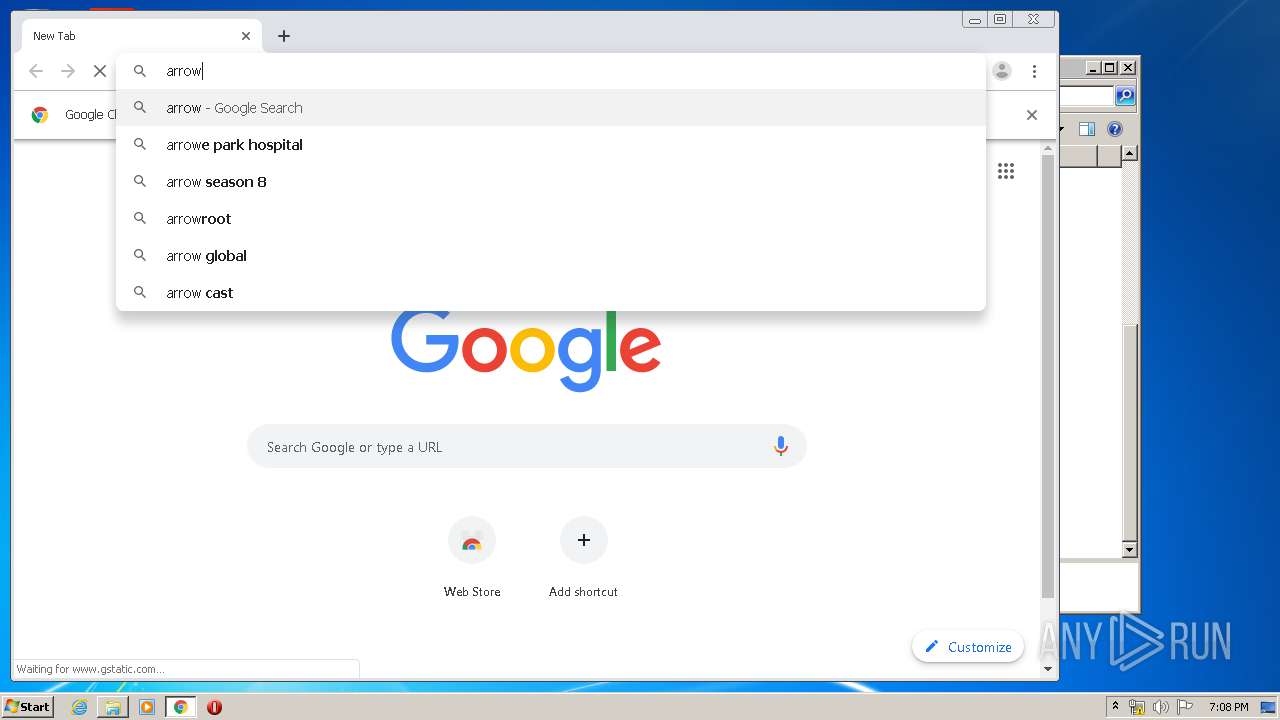
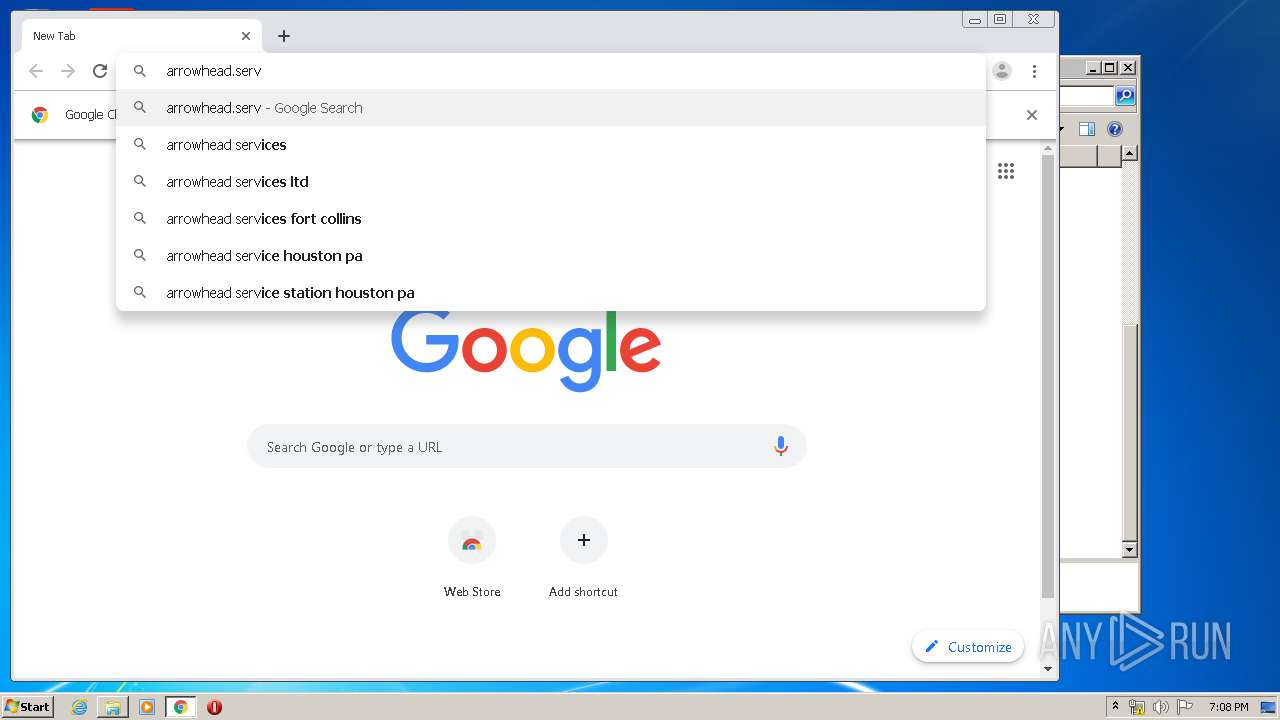
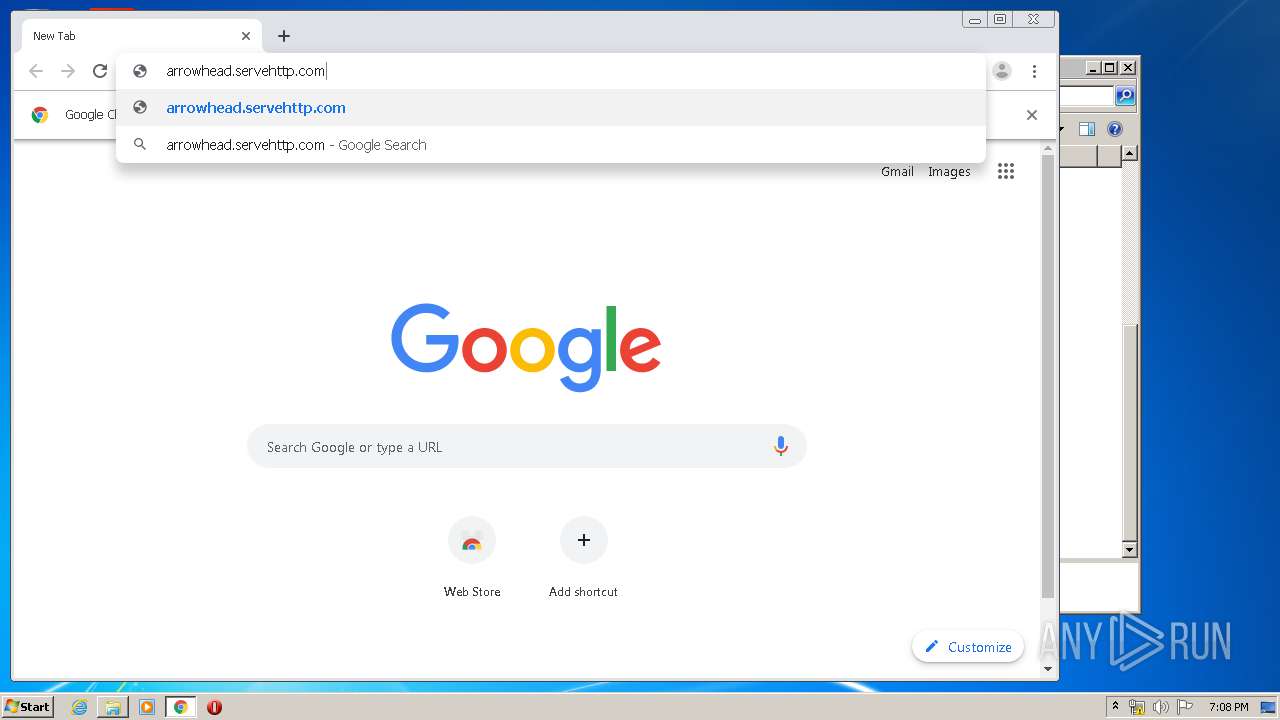
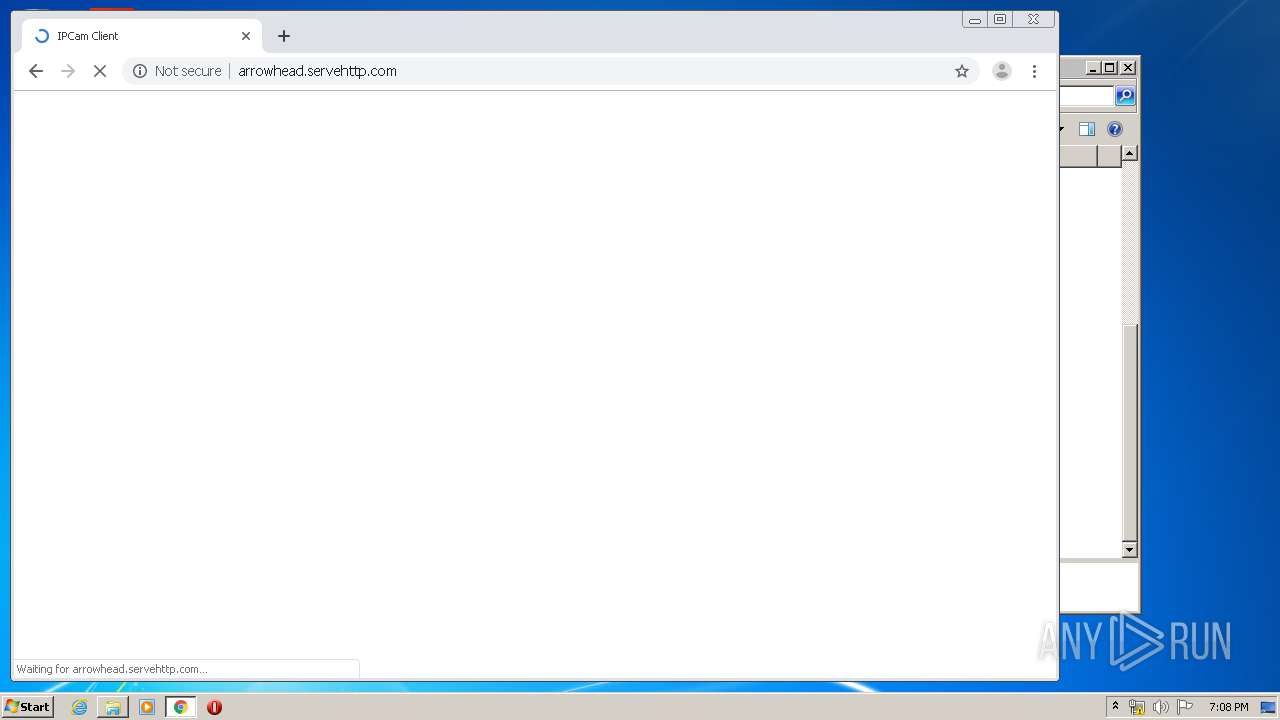
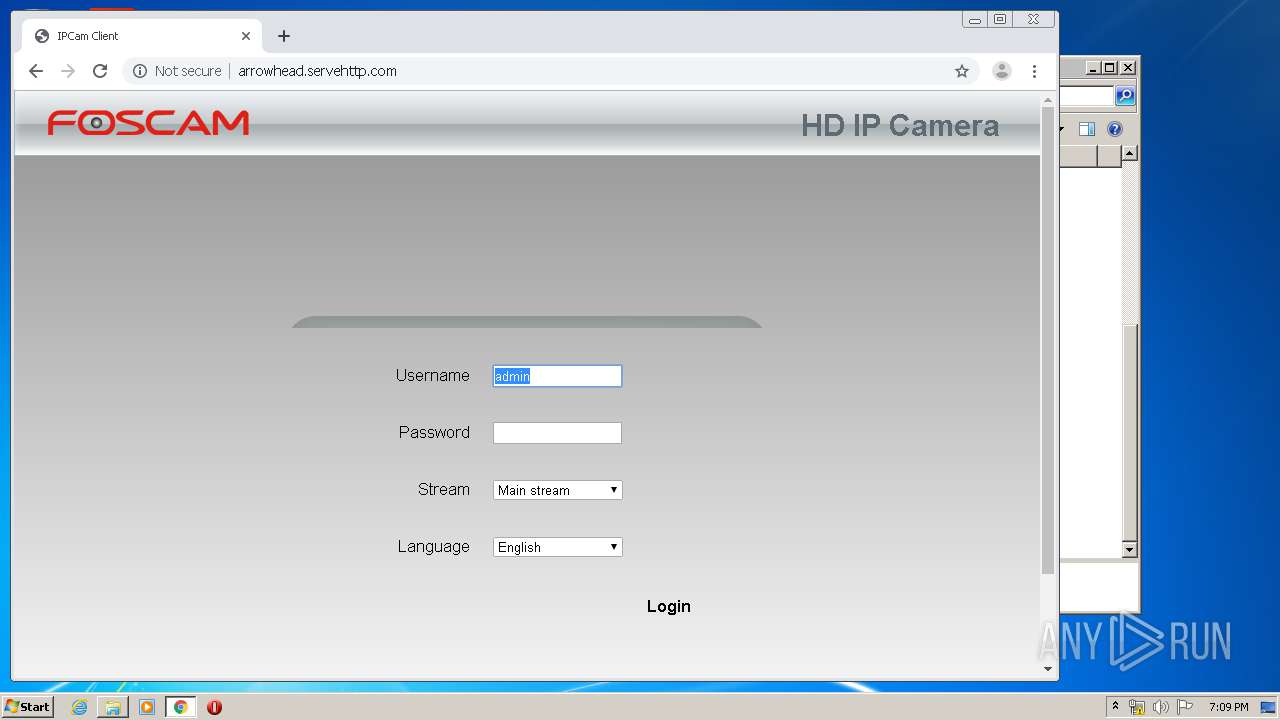
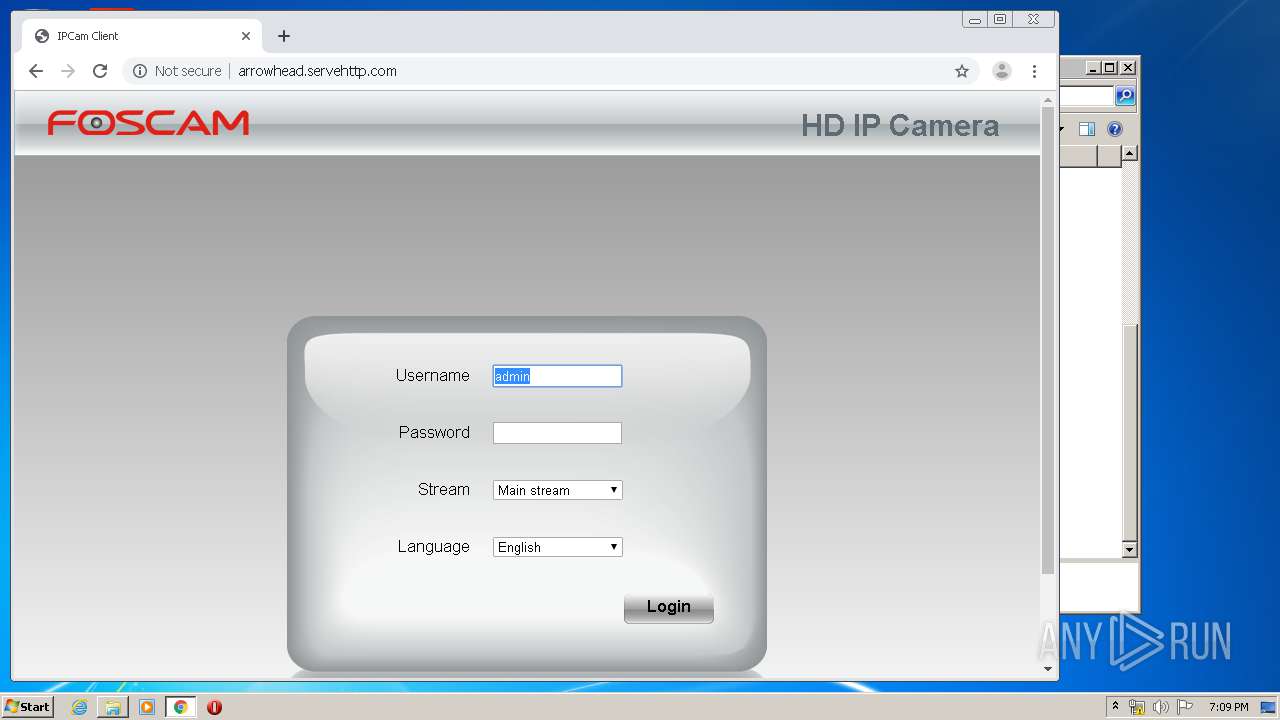
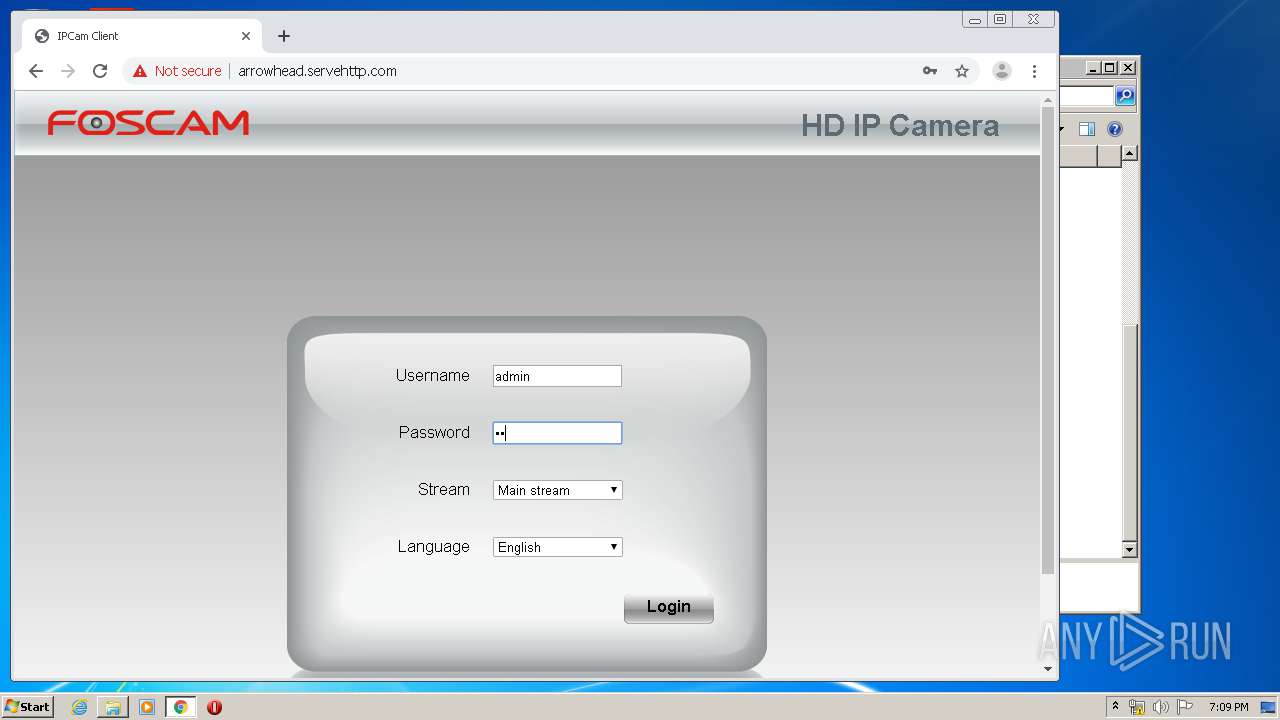
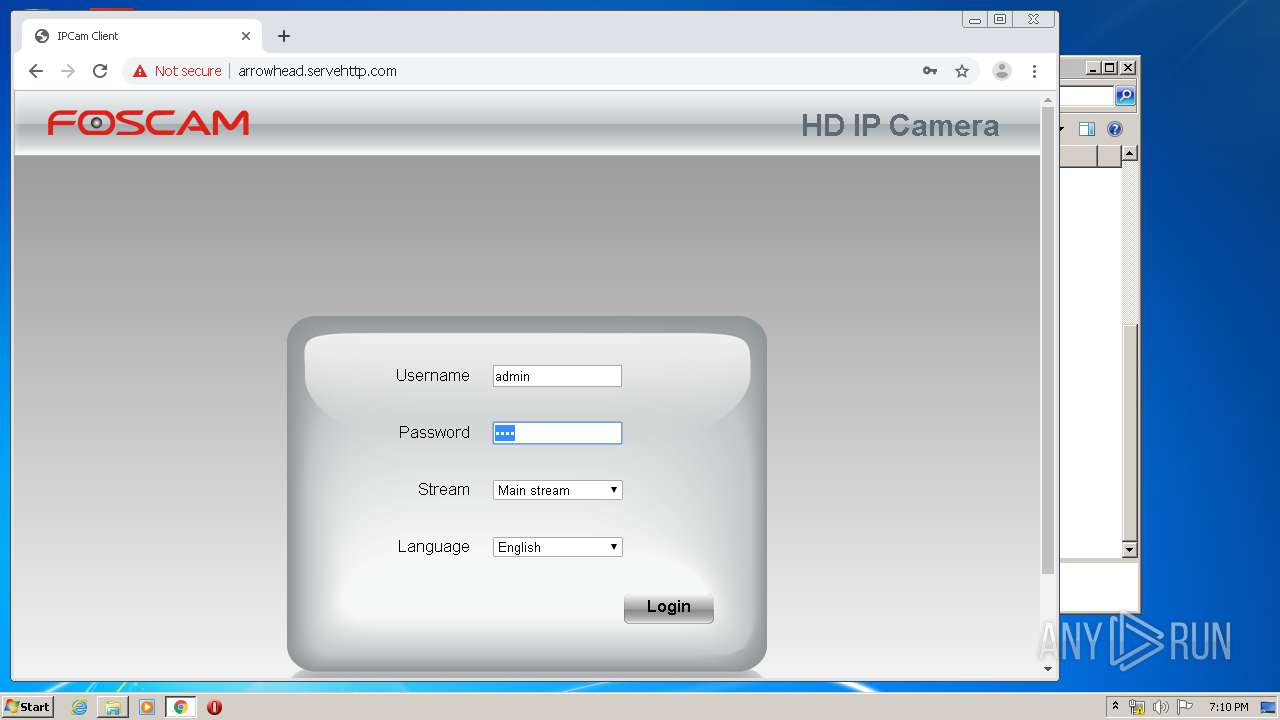
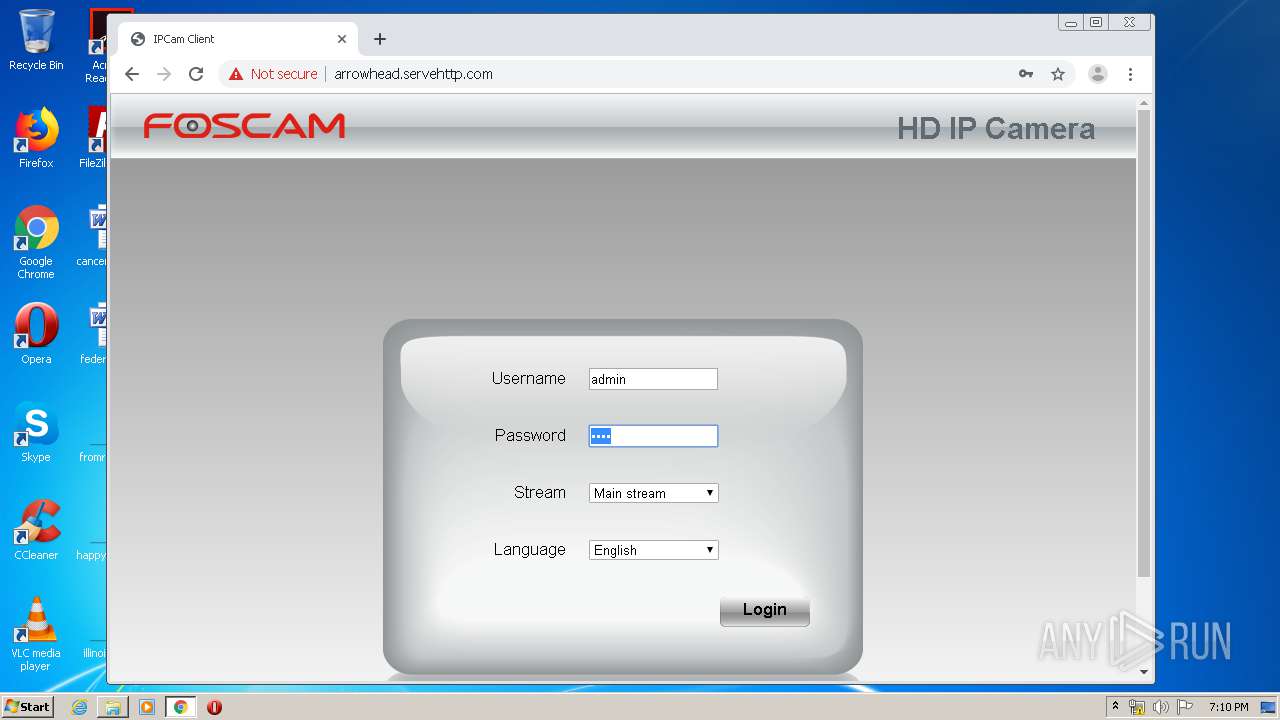
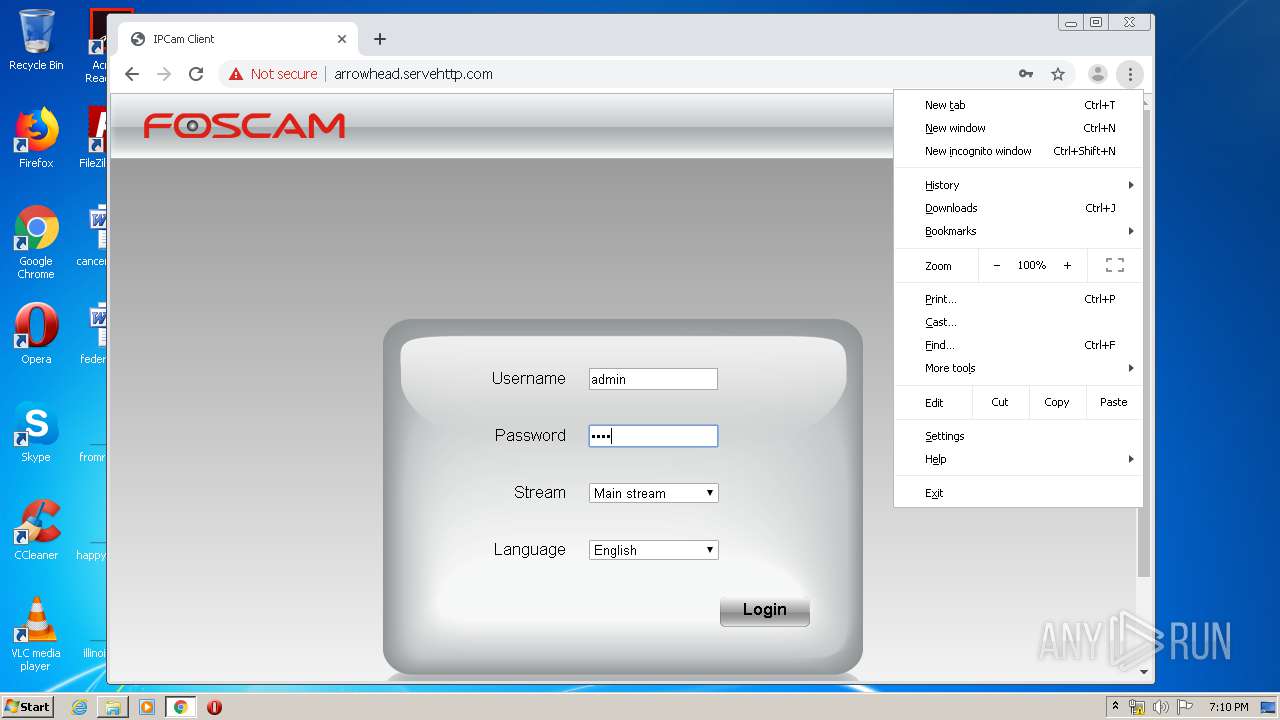
3264 | chrome.exe | GET | — | 47.34.144.49:80 | http://arrowhead.servehttp.com/css/main1.css | US | — | — | suspicious |
3264 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3264 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3264 | chrome.exe | GET | 200 | 47.34.144.49:80 | http://arrowhead.servehttp.com/js/pluginUpgradeCheck.js?ver=1584385747868 | US | text | 8.82 Kb | suspicious |
3264 | chrome.exe | GET | 200 | 47.34.144.49:80 | http://arrowhead.servehttp.com/ | US | html | 38.2 Kb | suspicious |
3264 | chrome.exe | GET | 200 | 47.34.144.49:80 | http://arrowhead.servehttp.com/js/class.js?ver=1584385747868 | US | text | 44.7 Kb | suspicious |
3264 | chrome.exe | GET | 200 | 47.34.144.49:80 | http://arrowhead.servehttp.com/js/main.js?ver=1584385747868 | US | text | 198 Kb | suspicious |
3264 | chrome.exe | GET | 200 | 47.34.144.49:80 | http://arrowhead.servehttp.com/js/jquery-3.3.1.min.js | US | text | 84.8 Kb | suspicious |
3264 | chrome.exe | GET | 200 | 47.34.144.49:80 | http://arrowhead.servehttp.com/js/checkUpgradeUrl.js?ver=1584385747868 | US | text | 88 b | suspicious |
3264 | chrome.exe | GET | 200 | 173.194.183.103:80 | http://r2---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=185.217.117.48&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1584385638&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 216.58.207.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 216.58.205.227:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servehttp .com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
3264 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
Process | Message |
|---|---|
amba_5.1.0.13_win--1548386245064.tmp | terminate foscloud sub process |
FosIPCCoreManager.exe | log full mode |
FosIPCCoreManager.exe | log mode is LOG_ALL [file not exist] |
FosIPCCoreManager.exe | C:\Windows\System32\config\SYSTEM~1\AppData\Roaming\FosRtmp.log |
FosIPCCoreManager.exe | log full mode |
FosIPCCoreManager.exe | log mode is LOG_ALL [file not exist] |
FosIPCCoreManager.exe | C:\Windows\System32\config\SYSTEM~1\AppData\Roaming\FosPlugin.log |
FosIPCCoreManager.exe | [2020-03-16 19:08:05.958][INFO ][pid=000006a0 tid=00000d68] [FosIPCCoreManager.cpp:305] : [ServiceWork] >>>> service start
|
FosIPCCoreManager.exe | C:\Windows\System32\config\SYSTEM~1\AppData\Roaming\FosRtmp.log |
FosIPCCoreManager.exe | [2020-03-16 19:08:05.958][INFO ][pid=000006a0 tid=00000d68] [webParse.cpp:10] : [CWebParse::CWebParse] >>>> construct this:01350C68
|