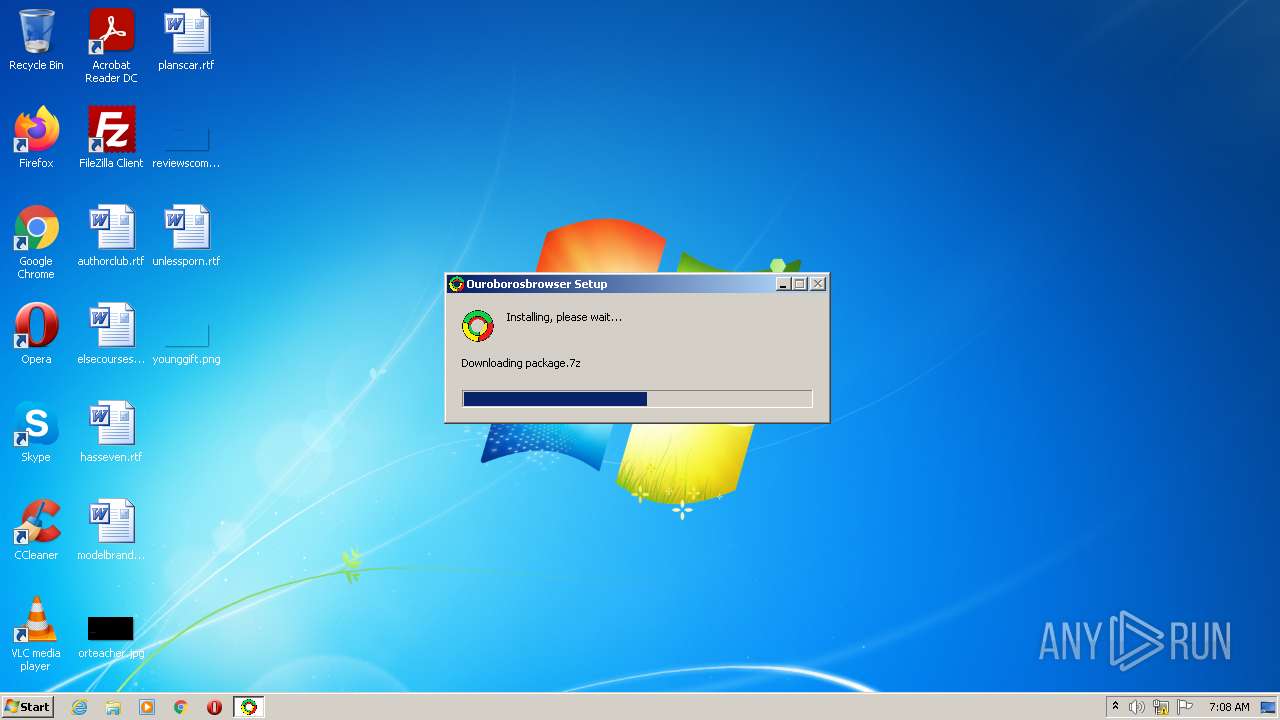
| File name: | Click.Here.to.Install.Ouroborosbrowser.exe |
| Full analysis: | https://app.any.run/tasks/5045d337-2f94-4736-9eab-367bdda60cf5 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2022, 07:08:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2869491A0D2E9B8E2D54D2B26B021BD1 |
| SHA1: | D28856CD30BC4F82410663B3846DAEFFC11914EA |
| SHA256: | A44438DC7BC072A67CE7988BF5BE5F71E4AFFCB49A1999215E218802D804151F |
| SSDEEP: | 12288:FZ6+WOJxRKaDPNKT1zH3ptaR1sDfOQSvJqFZ6qMa+OcfCJYsqa:FkonMaDu173pG1szLSvJw5eaRqa |
MALICIOUS
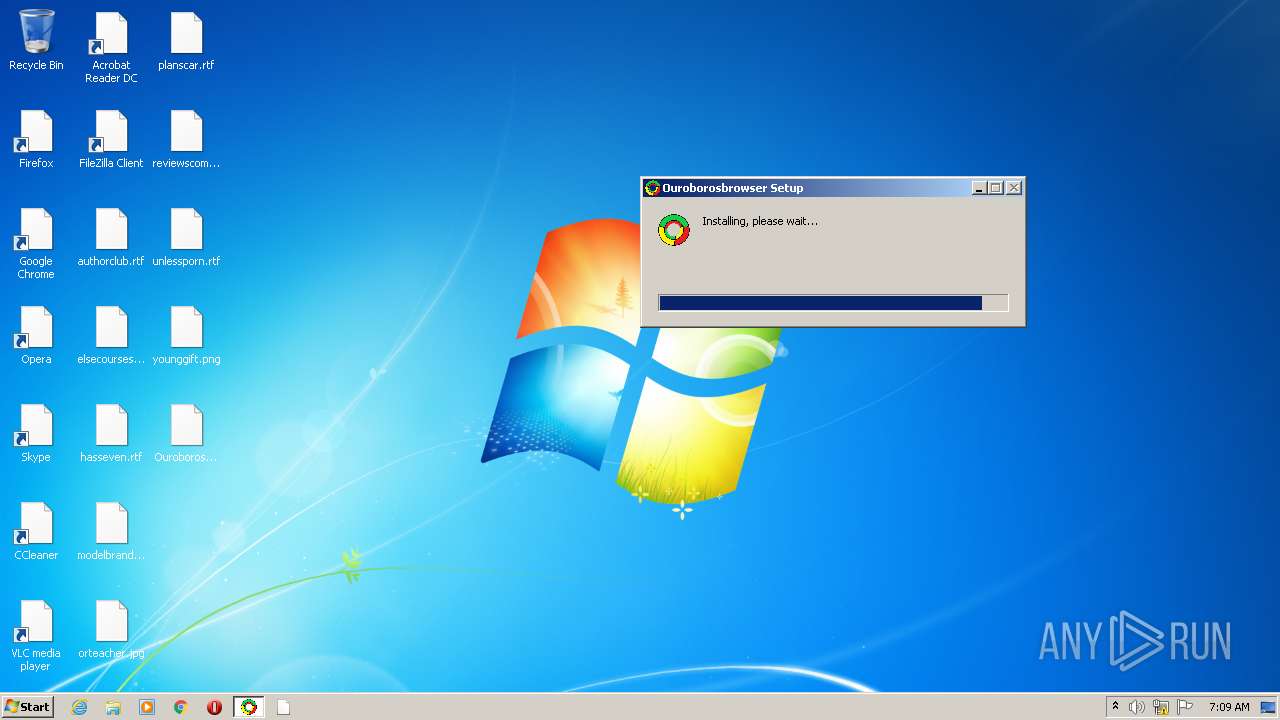
Drops executable file immediately after starts
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
Loads dropped or rewritten executable
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
- Ouroborosbrowser.exe (PID: 3968)
- Ouroborosbrowser.exe (PID: 576)
- Ouroborosbrowser.exe (PID: 2028)
- Ouroborosbrowser.exe (PID: 4060)
- Ouroborosbrowser.exe (PID: 1468)
- Ouroborosbrowser.exe (PID: 424)
- Ouroborosbrowser.exe (PID: 2888)
- Ouroborosbrowser.exe (PID: 1552)
- Ouroborosbrowser.exe (PID: 360)
- Ouroborosbrowser.exe (PID: 116)
- Ouroborosbrowser.exe (PID: 1960)
- Ouroborosbrowser.exe (PID: 312)
- Ouroborosbrowser.exe (PID: 1288)
Changes the autorun value in the registry
- reg.exe (PID: 3704)
Actions looks like stealing of personal data
- powershell.exe (PID: 1096)
SUSPICIOUS
Reads the computer name
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
- Ouroborosbrowser.exe (PID: 576)
- Ouroborosbrowser.exe (PID: 4060)
- Ouroborosbrowser.exe (PID: 2028)
- powershell.exe (PID: 1096)
- WMIC.exe (PID: 468)
- Ouroborosbrowser.exe (PID: 360)
- Ouroborosbrowser.exe (PID: 1288)
Drops a file with too old compile date
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
Reads Environment values
- Ouroborosbrowser.exe (PID: 576)
- Ouroborosbrowser.exe (PID: 1552)
Uses REG.EXE to modify Windows registry
- Ouroborosbrowser.exe (PID: 576)
Checks supported languages
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
- Ouroborosbrowser.exe (PID: 3968)
- Ouroborosbrowser.exe (PID: 576)
- Ouroborosbrowser.exe (PID: 4060)
- Ouroborosbrowser.exe (PID: 2028)
- Ouroborosbrowser.exe (PID: 1468)
- Ouroborosbrowser.exe (PID: 424)
- Ouroborosbrowser.exe (PID: 2888)
- powershell.exe (PID: 1096)
- Ouroborosbrowser.exe (PID: 1552)
- Ouroborosbrowser.exe (PID: 360)
- WMIC.exe (PID: 468)
- cmd.exe (PID: 3384)
- chcp.com (PID: 320)
- Ouroborosbrowser.exe (PID: 1960)
- Ouroborosbrowser.exe (PID: 116)
- cmd.exe (PID: 3204)
- Ouroborosbrowser.exe (PID: 312)
- Ouroborosbrowser.exe (PID: 1288)
Drops a file that was compiled in debug mode
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
Creates a software uninstall entry
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
Creates files in the user directory
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
- Ouroborosbrowser.exe (PID: 2028)
- powershell.exe (PID: 1096)
- Ouroborosbrowser.exe (PID: 576)
Changes default file association
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
Executable content was dropped or overwritten
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
Application launched itself
- Ouroborosbrowser.exe (PID: 576)
Executes PowerShell scripts
- Ouroborosbrowser.exe (PID: 576)
Reads the date of Windows installation
- powershell.exe (PID: 1096)
Starts CMD.EXE for commands execution
- Ouroborosbrowser.exe (PID: 576)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3204)
Writes to a desktop.ini file (may be used to cloak folders)
- powershell.exe (PID: 1096)
Starts application with an unusual extension
- cmd.exe (PID: 3384)
INFO
Reads settings of System Certificates
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
- Ouroborosbrowser.exe (PID: 2028)
Manual execution by user
- Ouroborosbrowser.exe (PID: 3968)
- Ouroborosbrowser.exe (PID: 576)
Checks Windows Trust Settings
- Click.Here.to.Install.Ouroborosbrowser.exe (PID: 3568)
- powershell.exe (PID: 1096)
Checks supported languages
- reg.exe (PID: 2800)
- reg.exe (PID: 3704)
Reads the hosts file
- Ouroborosbrowser.exe (PID: 576)
- Ouroborosbrowser.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 1.0.4 |
|---|---|
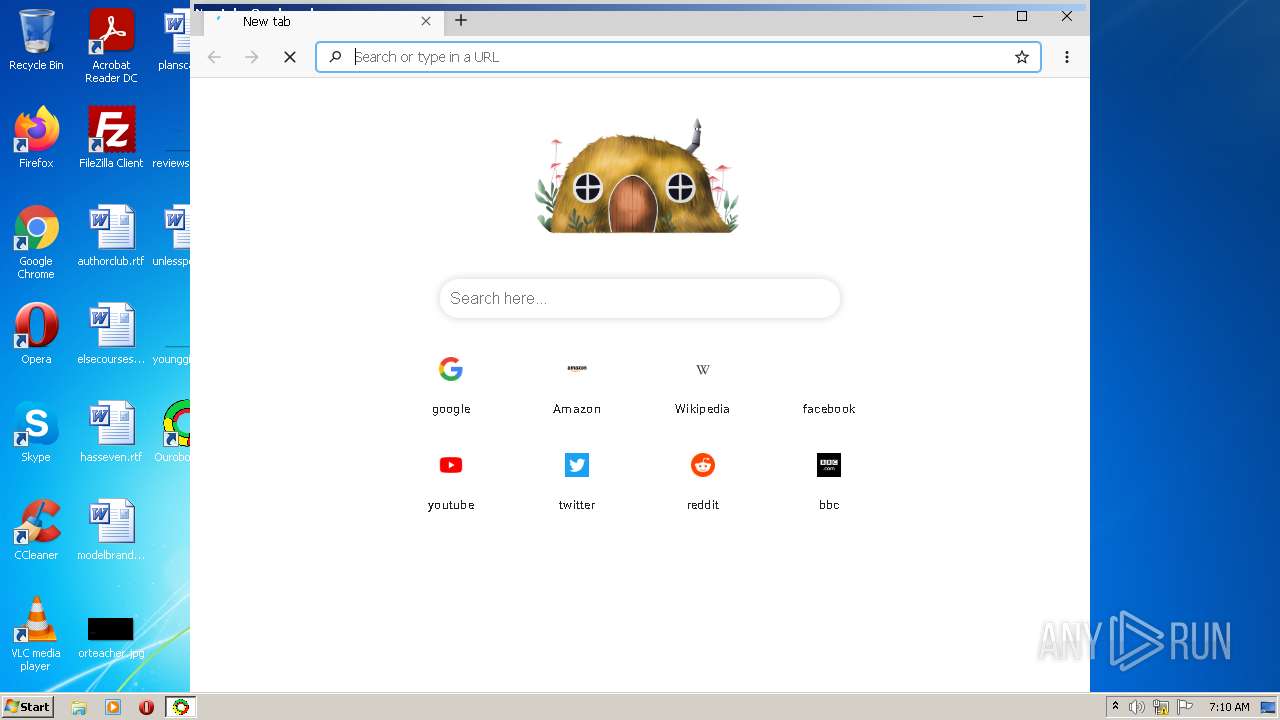
| ProductName: | Ouroborosbrowser |
| LegalCopyright: | Copyright © 2021 White Sand Media, Inc |
| FileVersion: | 1.0.4 |
| FileDescription: | Extensible, fast and Secure web browser. |
| CompanyName: | White Sand Media, Inc |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.4.0 |
| FileVersionNumber: | 1.0.4.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x338f |
| UninitializedDataSize: | 16384 |
| InitializedDataSize: | 473088 |
| CodeSize: | 26624 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2018:12:15 23:26:14+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:26:14 |
| Detected languages: |
|
| CompanyName: | White Sand Media, Inc |
| FileDescription: | Extensible, fast and Secure web browser. |
| FileVersion: | 1.0.4 |
| LegalCopyright: | Copyright © 2021 White Sand Media, Inc |
| ProductName: | Ouroborosbrowser |
| ProductVersion: | 1.0.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:26:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45028 |
.rdata | 0x00008000 | 0x000014A2 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02518 |
.data | 0x0000A000 | 0x00070FF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03712 |
.ndata | 0x0007B000 | 0x0012C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001A7000 | 0x00009B28 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.43263 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.51664 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.78574 | 506 | UNKNOWN | English - United States | RT_DIALOG |
206 | 3.04696 | 240 | UNKNOWN | English - United States | RT_DIALOG |
211 | 3.09674 | 230 | UNKNOWN | English - United States | RT_DIALOG |
305 | 2.68176 | 494 | UNKNOWN | English - United States | RT_DIALOG |
306 | 2.86295 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
67
Monitored processes
21
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" --type=renderer --field-trial-handle=1040,5939558900975752076,15629312855023004388,131072 --enable-features=CSSColorSchemeUARendering,ImpulseScrollAnimations,ParallelDownloading,WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --disable-gpu-compositing --lang=en-US --standard-schemes=ouroborosbrowser --secure-schemes=ouroborosbrowser --bypasscsp-schemes=ouroborosbrowser --cors-schemes --fetch-schemes=ouroborosbrowser --service-worker-schemes=ouroborosbrowser --streaming-schemes --app-path="C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\resources\app.asar" --enable-plugins --enable-sandbox --native-window-open --preload="C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\resources\app.asar/build/view-preload.bundle.js" --context-isolation --background-color=#fff --enable-spellcheck --enable-websql --disable-electron-site-instance-overrides --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | — | Ouroborosbrowser.exe | |||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: LOW Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
| 312 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" --type=renderer --field-trial-handle=1040,5939558900975752076,15629312855023004388,131072 --enable-features=CSSColorSchemeUARendering,ImpulseScrollAnimations,ParallelDownloading,WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --disable-gpu-compositing --lang=en-US --standard-schemes=ouroborosbrowser --secure-schemes=ouroborosbrowser --bypasscsp-schemes=ouroborosbrowser --cors-schemes --fetch-schemes=ouroborosbrowser --service-worker-schemes=ouroborosbrowser --streaming-schemes --app-path="C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\resources\app.asar" --enable-plugins --enable-sandbox --native-window-open --preload="C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\resources\app.asar/build/view-preload.bundle.js" --context-isolation --background-color=#fff --enable-spellcheck --enable-websql --disable-electron-site-instance-overrides --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | — | Ouroborosbrowser.exe | |||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: LOW Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
| 320 | chcp | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 360 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" --type=gpu-process --field-trial-handle=1040,5939558900975752076,15629312855023004388,131072 --enable-features=CSSColorSchemeUARendering,ImpulseScrollAnimations,ParallelDownloading,WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1080 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | — | Ouroborosbrowser.exe | |||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: LOW Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
| 424 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" --type=renderer --field-trial-handle=1040,5939558900975752076,15629312855023004388,131072 --enable-features=CSSColorSchemeUARendering,ImpulseScrollAnimations,ParallelDownloading,WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --lang=en-US --standard-schemes=ouroborosbrowser --secure-schemes=ouroborosbrowser --bypasscsp-schemes=ouroborosbrowser --cors-schemes --fetch-schemes=ouroborosbrowser --service-worker-schemes=ouroborosbrowser --streaming-schemes --app-path="C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\resources\app.asar" --node-integration --no-sandbox --no-zygote --enable-remote-module --background-color=#fff --enable-spellcheck --enable-websql --disable-electron-site-instance-overrides --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1548 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | — | Ouroborosbrowser.exe | |||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: MEDIUM Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
| 468 | wmic logicaldisk get Caption,FreeSpace,Size,VolumeSerialNumber,Description /format:list | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | Explorer.EXE | ||||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: MEDIUM Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
| 1096 | powershell.exe -ExecutionPolicy Bypass -NoProfile -NoLogo -NoExit -InputFormat Text -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Ouroborosbrowser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1040,5939558900975752076,15629312855023004388,131072 --enable-features=CSSColorSchemeUARendering,ImpulseScrollAnimations,ParallelDownloading,WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=audio --standard-schemes=ouroborosbrowser --secure-schemes=ouroborosbrowser --bypasscsp-schemes=ouroborosbrowser --cors-schemes --fetch-schemes=ouroborosbrowser --service-worker-schemes=ouroborosbrowser --streaming-schemes --mojo-platform-channel-handle=2632 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | — | Ouroborosbrowser.exe | |||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: LOW Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe" --type=renderer --field-trial-handle=1040,5939558900975752076,15629312855023004388,131072 --enable-features=CSSColorSchemeUARendering,ImpulseScrollAnimations,ParallelDownloading,WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --lang=en-US --standard-schemes=ouroborosbrowser --secure-schemes=ouroborosbrowser --bypasscsp-schemes=ouroborosbrowser --cors-schemes --fetch-schemes=ouroborosbrowser --service-worker-schemes=ouroborosbrowser --streaming-schemes --app-path="C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\resources\app.asar" --node-integration --webview-tag --no-sandbox --no-zygote --enable-remote-module --background-color=#fff --enable-spellcheck --enable-websql --disable-electron-site-instance-overrides --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1488 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\Ouroborosbrowser.exe | — | Ouroborosbrowser.exe | |||||||||||
User: admin Company: White Sand Media, Inc Integrity Level: MEDIUM Description: Ouroborosbrowser Exit code: 0 Version: 1.0.7 Modules
| |||||||||||||||
Total events
20 443
Read events
20 043
Write events
400
Delete events
0
Modification events
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3568) Click.Here.to.Install.Ouroborosbrowser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
17
Suspicious files
147
Text files
44
Unknown types
92
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ouroborosbrowser-1.0.4-ia32.nsis[1].7z | — | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\Local\Temp\nsbD658.tmp\package.7z | — | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\Local\Programs\ouroborosbrowser\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | der | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 3568 | Click.Here.to.Install.Ouroborosbrowser.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
93
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAUYmlTr6MfpA%2BCrDZJVRd4%3D | US | der | 313 b | whitelisted |
2028 | Ouroborosbrowser.exe | GET | 200 | 128.199.5.22:80 | http://128.199.5.22/api/get_whitelist_url | SG | ini | 6.47 Kb | unknown |
2028 | Ouroborosbrowser.exe | POST | 200 | 128.199.5.22:80 | http://128.199.5.22/api/desktop_device | SG | binary | 84 b | unknown |
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?524d29af5b4b0a16 | US | compressed | 4.70 Kb | whitelisted |
2028 | Ouroborosbrowser.exe | GET | 200 | 2.16.186.114:80 | http://g-ec2.images-amazon.com/images/G/01/social/api-share/amazon_logo_500500._V323939215_.png | unknown | image | 13.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | 185.199.111.133:443 | objects.githubusercontent.com | GitHub, Inc. | NL | suspicious |
3568 | Click.Here.to.Install.Ouroborosbrowser.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
576 | Ouroborosbrowser.exe | 185.199.111.133:443 | objects.githubusercontent.com | GitHub, Inc. | NL | suspicious |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
2028 | Ouroborosbrowser.exe | 128.199.5.22:80 | — | — | SG | unknown |
2028 | Ouroborosbrowser.exe | 104.26.4.30:443 | picsum.photos | Cloudflare Inc | US | unknown |
2028 | Ouroborosbrowser.exe | 142.250.186.68:443 | www.google.com | Google Inc. | US | whitelisted |
2028 | Ouroborosbrowser.exe | 91.198.174.192:443 | www.wikipedia.org | Wikimedia Foundation, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
raw.githubusercontent.com |
| shared |
redirector.gvt1.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
r5---sn-1gi7znek.gvt1.com |
| whitelisted |
r2---sn-4g5e6nsr.gvt1.com |
| whitelisted |