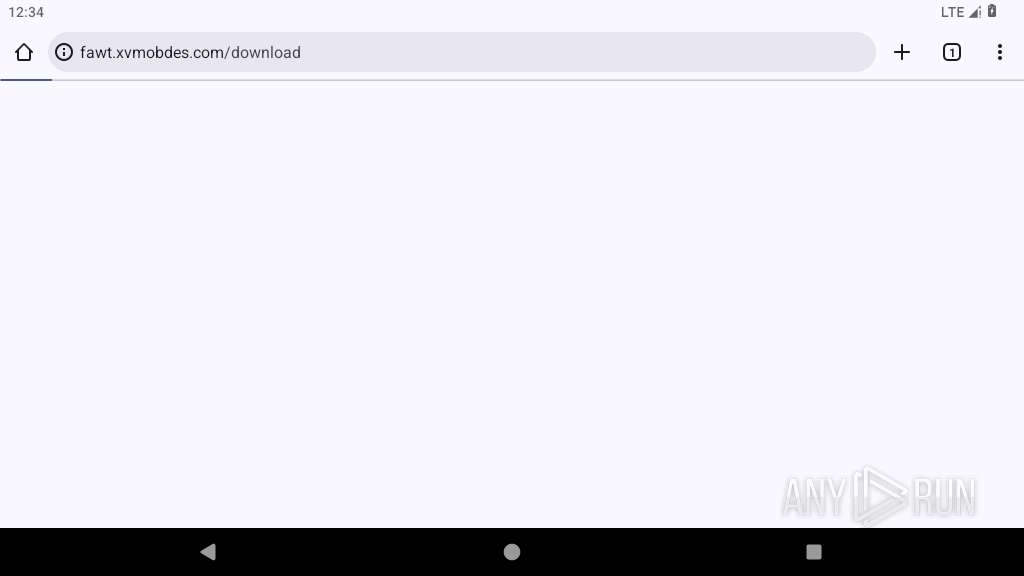
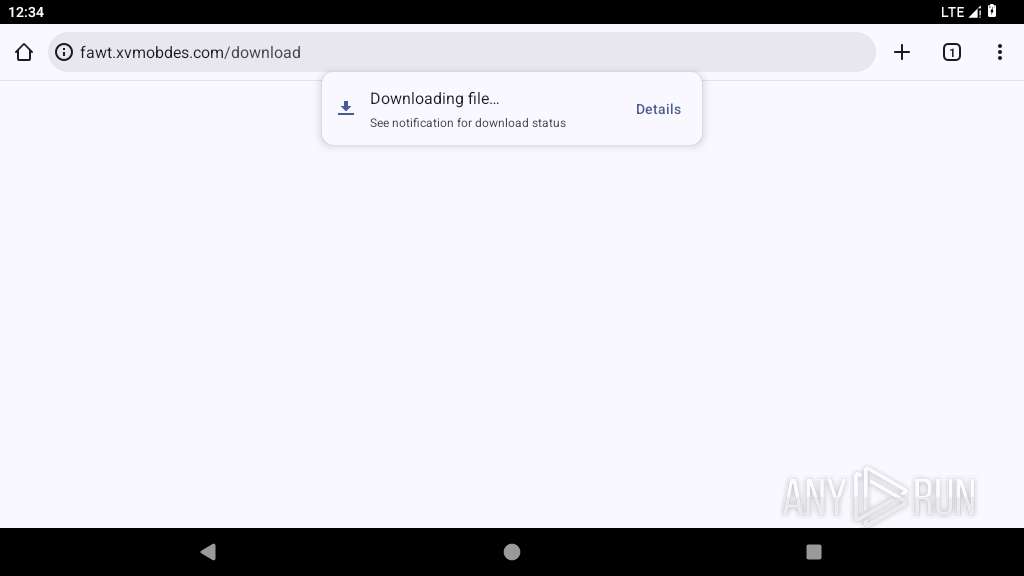
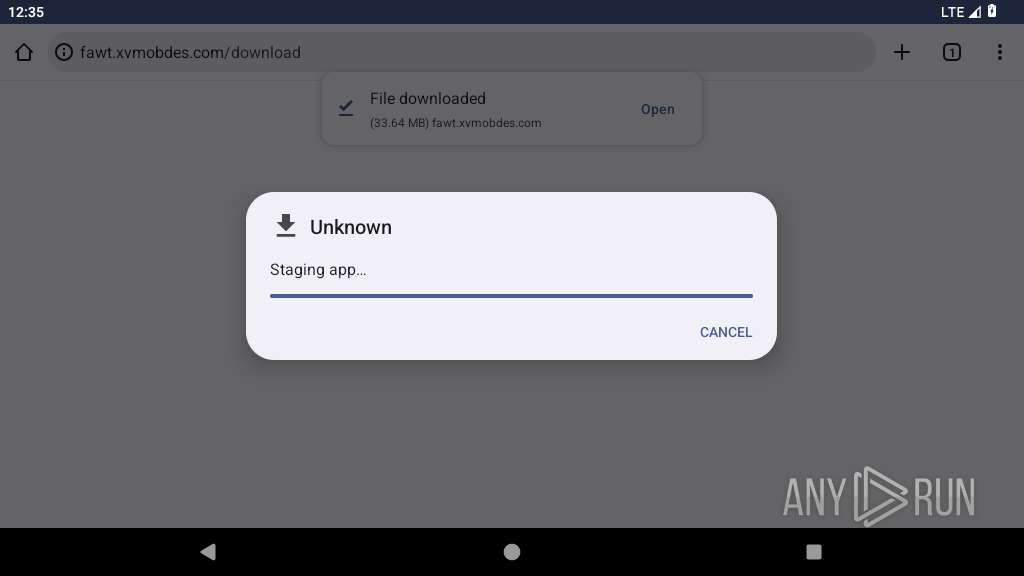
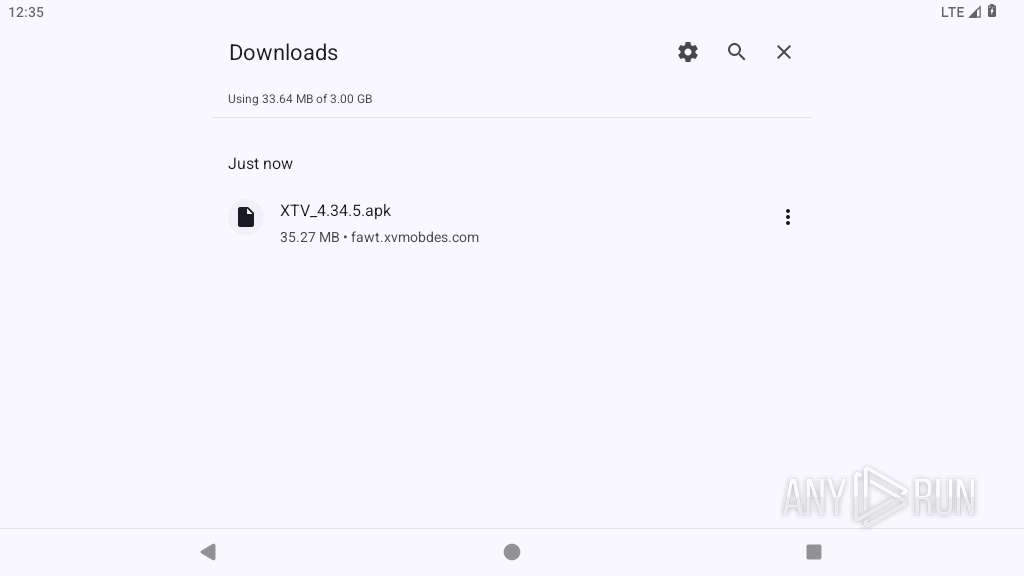
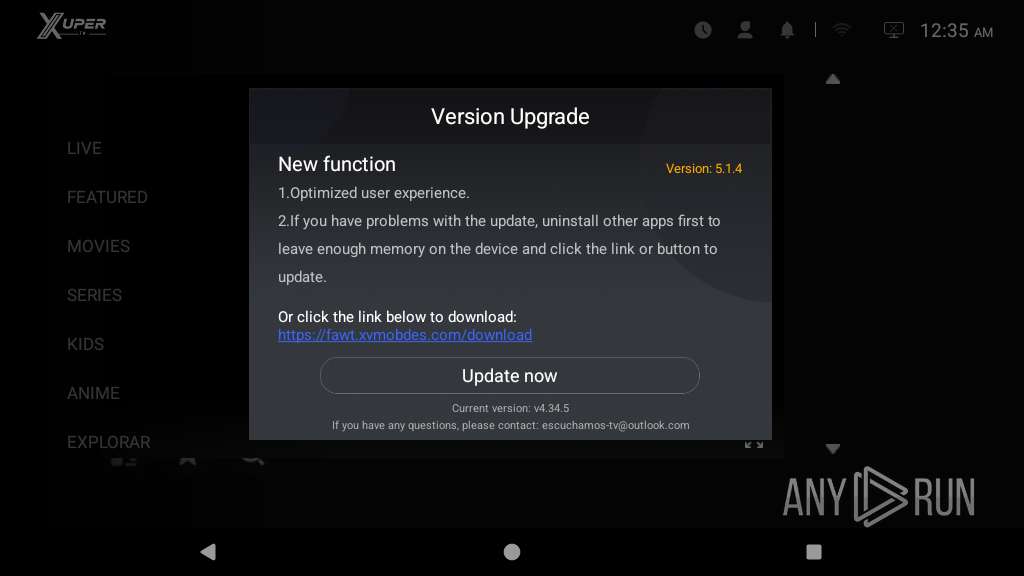
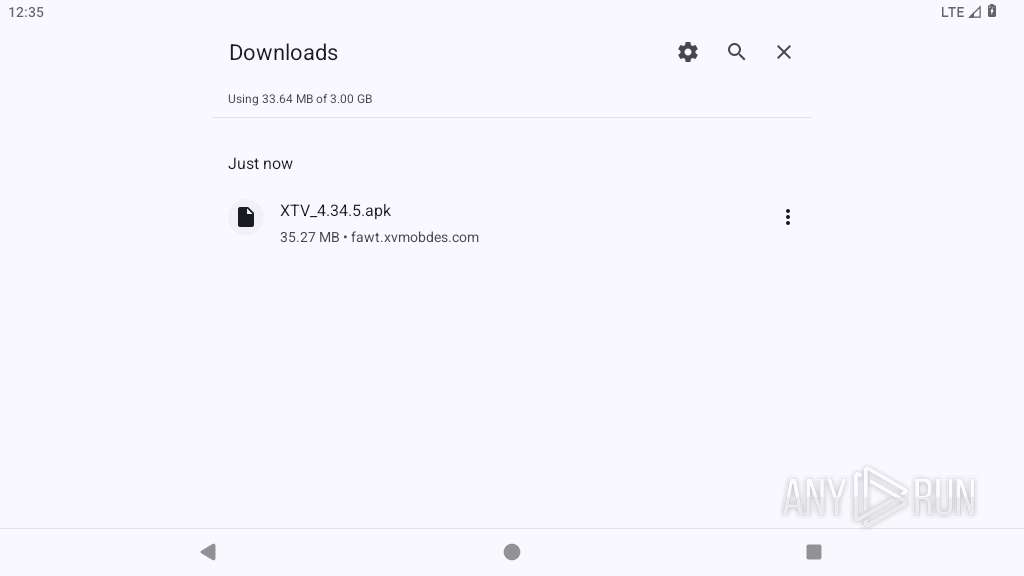
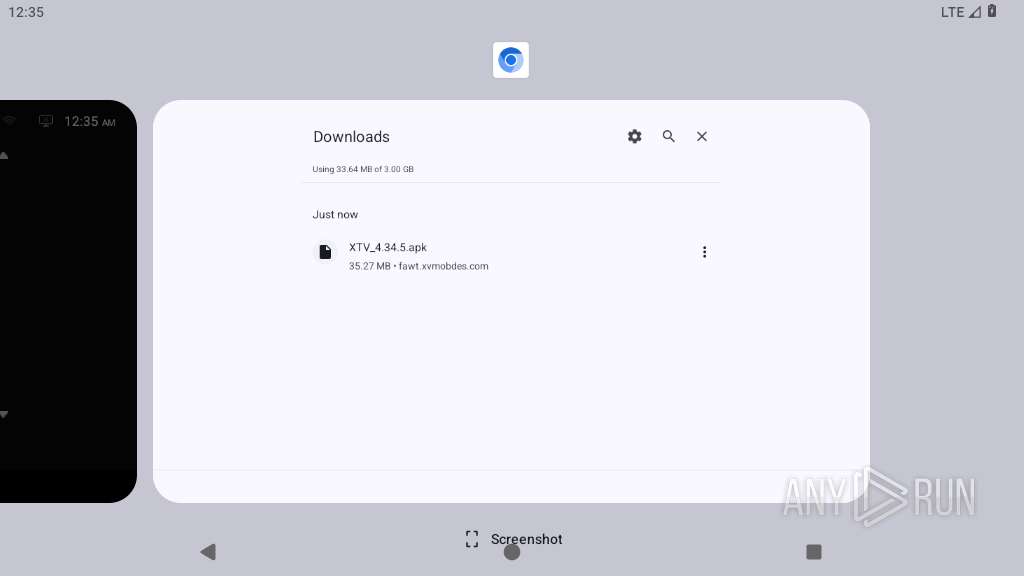
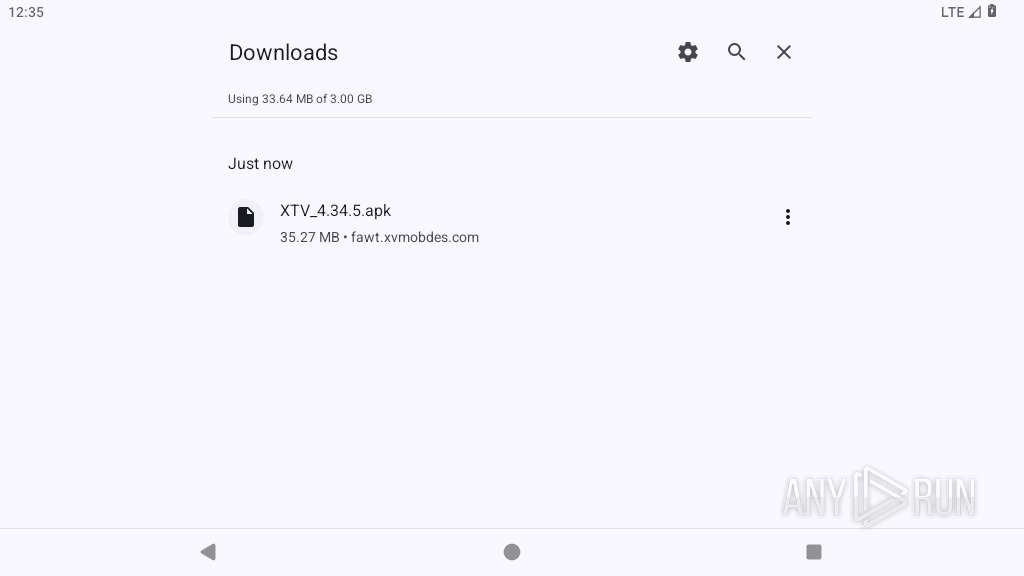
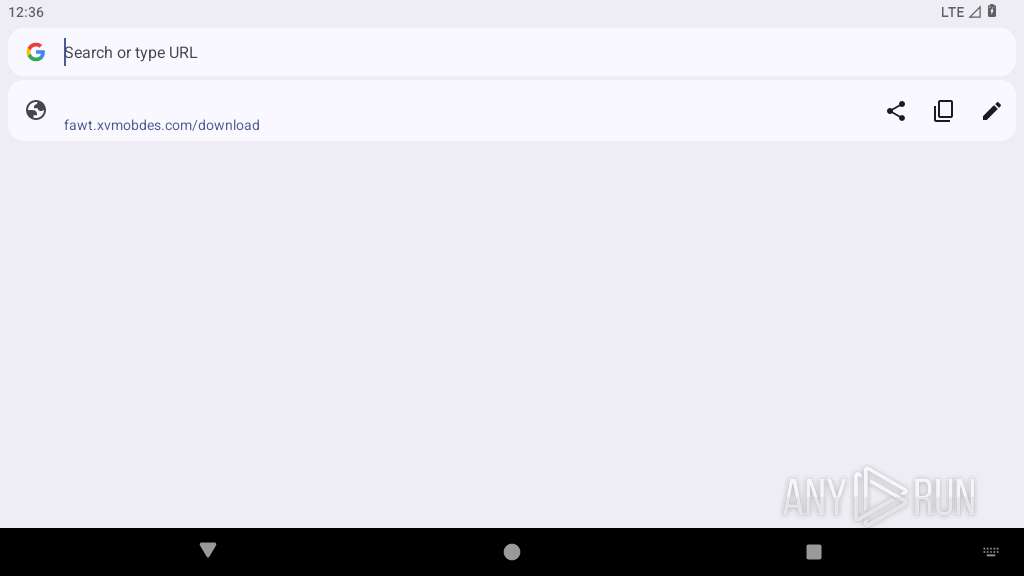
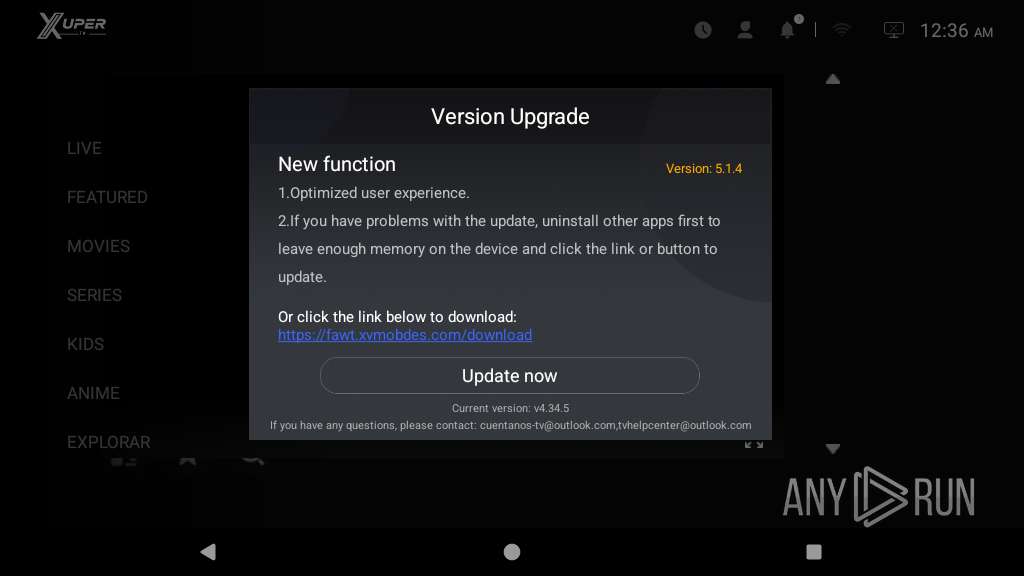
| URL: | https://fawt.xvmobdes.com/download |
| Full analysis: | https://app.any.run/tasks/5cd504eb-a61d-40c3-9ec4-a8ef520035b2 |
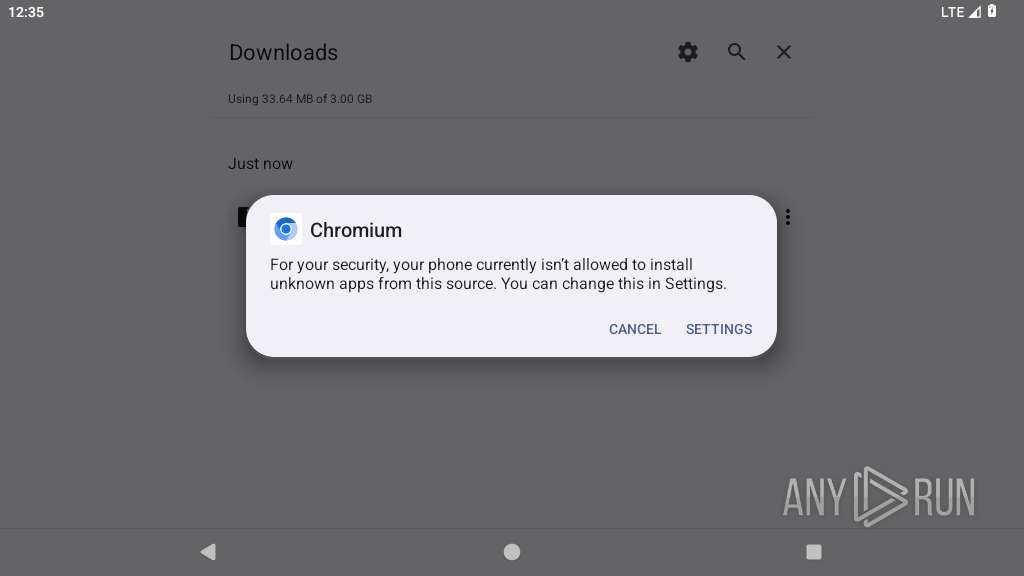
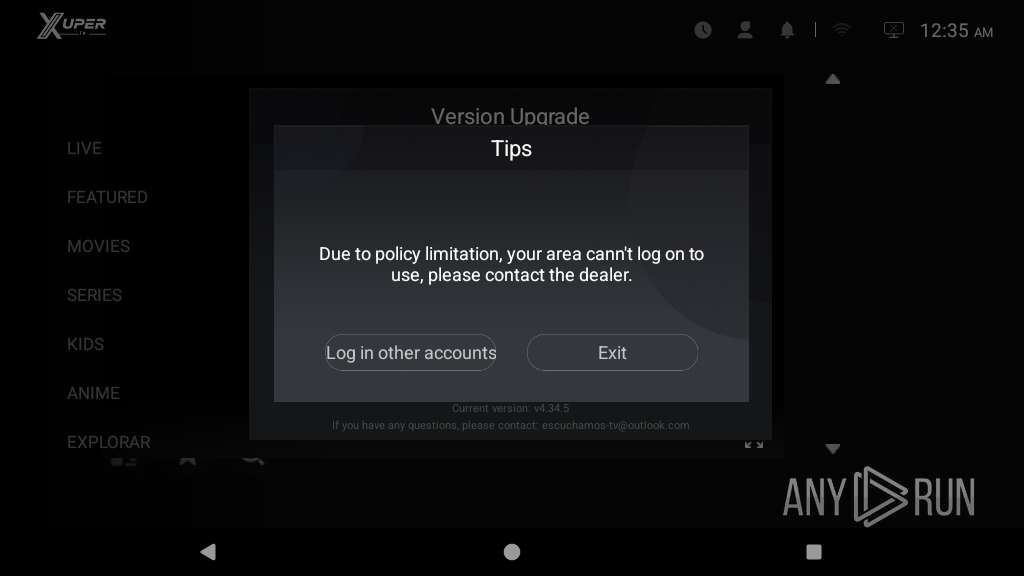
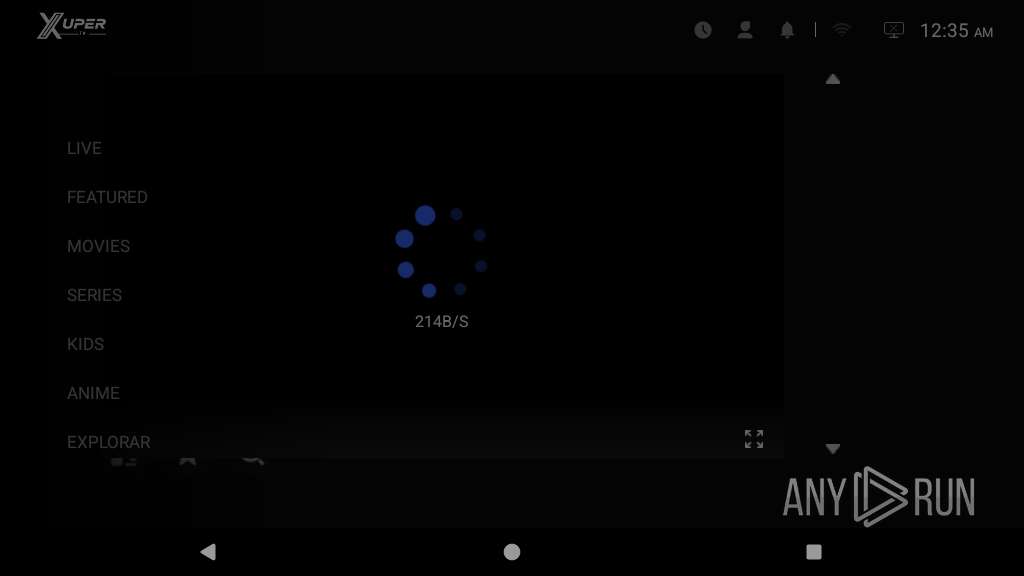
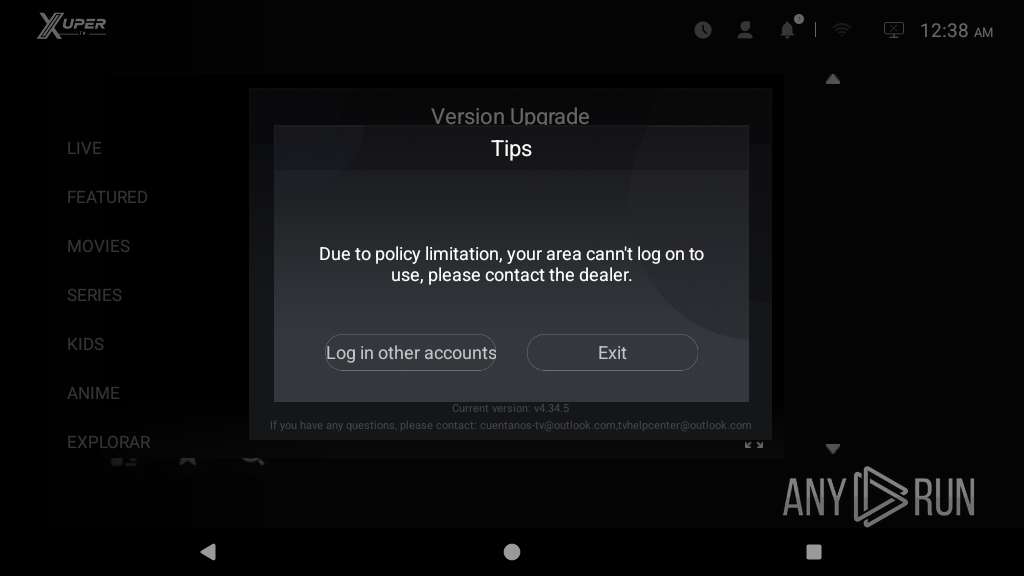
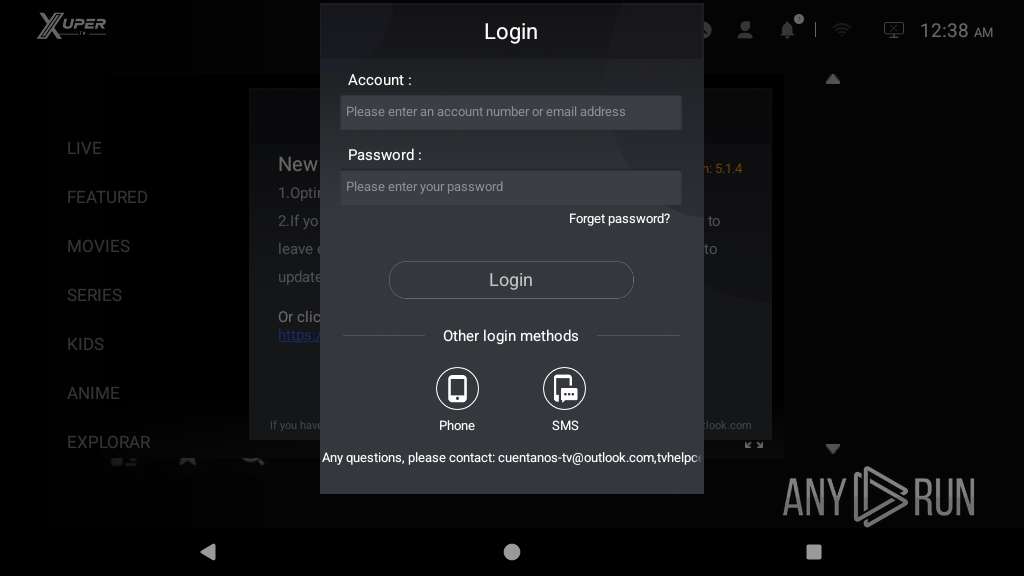
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2026, 00:34:43 |
| OS: | Android 14 |
| Indicators: | |
| MD5: | 4E8F778FCD82DFAC19BB36AFE91AF7B7 |
| SHA1: | 953465D35EFD35F993A83875582AE6B625DB240C |
| SHA256: | A43DBB3FFC06F967824FA3A4C33396E2C6320A6B35CD0DC372DFF864A02B99C6 |
| SSDEEP: | 3:N8b93HBGWKM:2p3BKM |
MALICIOUS
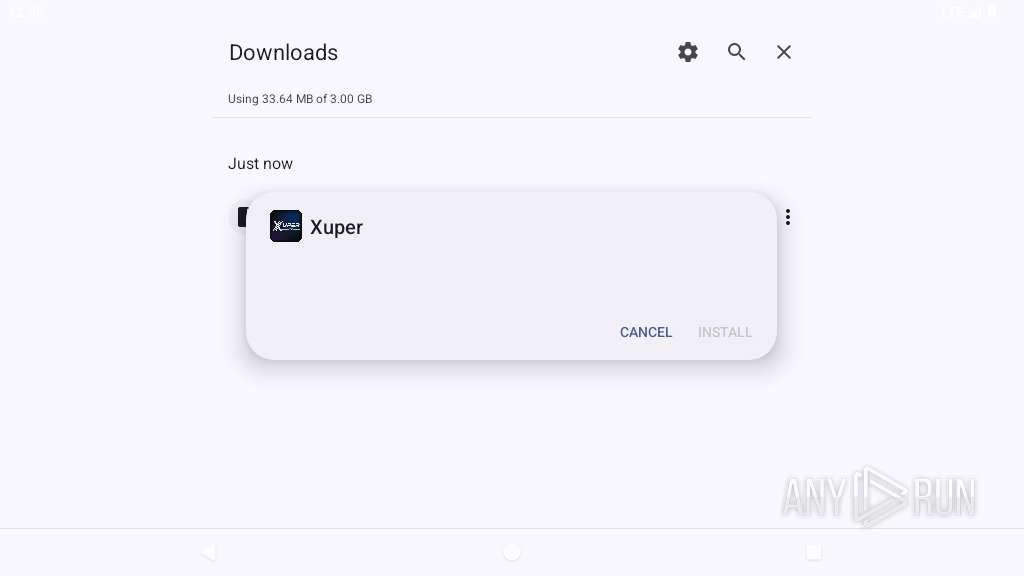
Hides app icon from display
- app_process64 (PID: 3148)
Executes system commands or scripts
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
SUSPICIOUS
Accesses external device storage files
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Accesses system-level resources
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Uses encryption API functions
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Establishing a connection
- app_process64 (PID: 3148)
- app_process64 (PID: 4215)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Retrieves Android OS build information
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Retrieves a list of running services
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Launches a new activity
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Reads device MAC address fingerprint
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 3148)
- app_process64 (PID: 4215)
INFO
Loads a native library into the application
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Returns elapsed time since boot
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Dynamically registers broadcast event listeners
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Stores data using SQLite database
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Verifies whether the device is connected to the internet
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Detects device power status
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Creates and writes local files
- app_process64 (PID: 3148)
Detects if debugger is connected
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Normally terminates current Java virtual machine
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
Listens for connection changes
- app_process64 (PID: 3148)
- app_process64 (PID: 4025)
- app_process64 (PID: 4215)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
89
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2797 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2850 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2868 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2894 | zygote64 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2896 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
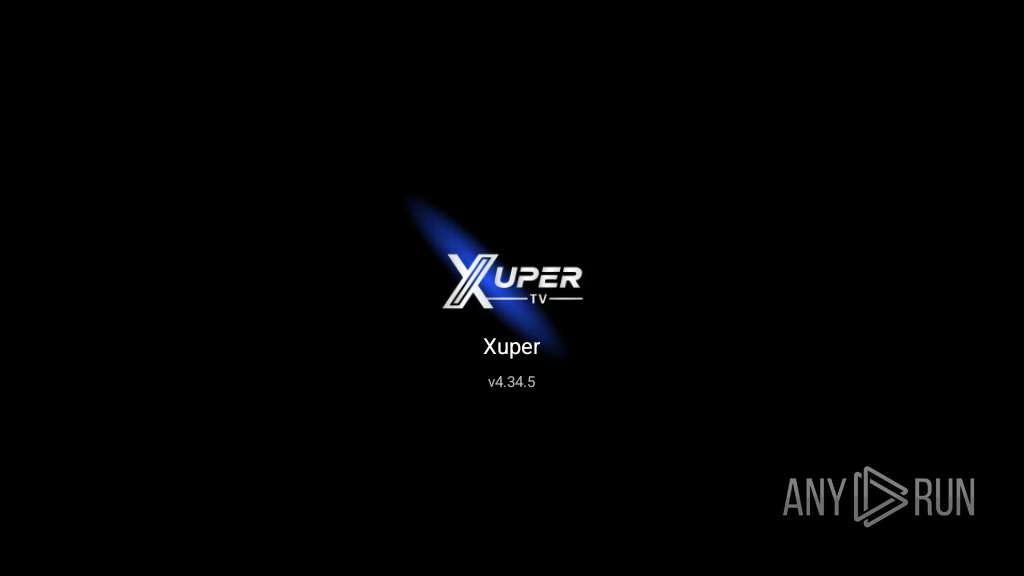
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2966 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3130 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
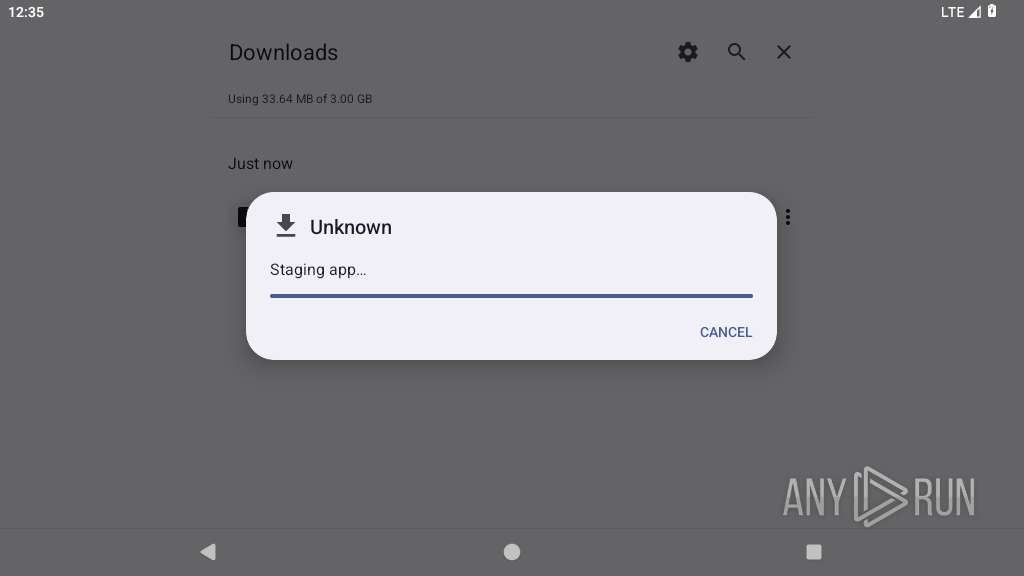
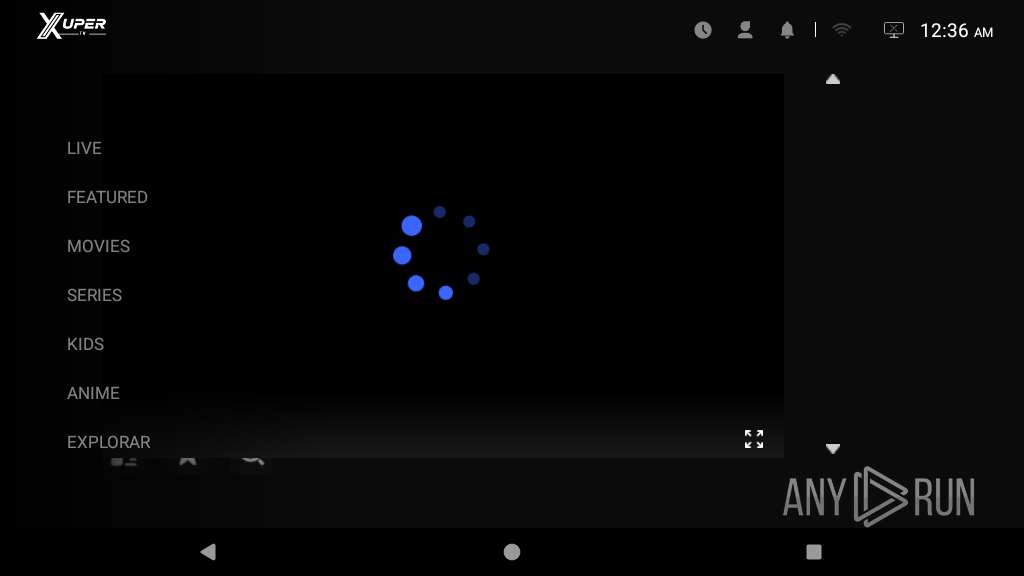
| 3133 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~rTR2qBIDzQ8BMJpFLShnfQ==/com.android.mgstv-P67PBsU5ue4r3WHRhozVIg==/base.apk --oat-fd=7 --oat-location=/data/app/~~rTR2qBIDzQ8BMJpFLShnfQ==/com.android.mgstv-P67PBsU5ue4r3WHRhozVIg==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context-fds=10 --class-loader-context=PCL[]{PCL[/system/framework/org.apache.http.legacy.jar]} --classpath-dir=/data/app/~~rTR2qBIDzQ8BMJpFLShnfQ==/com.android.mgstv-P67PBsU5ue4r3WHRhozVIg== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:33 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:4.34.5,app-version-code:43405,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3148 | zygote64 | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3276 | cat proc/cpuinfo | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
463
Text files
299
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | app_process64 | /data/data/com.android.mgstv/files/libexec.so | binary | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/files/libexecmain.so | binary | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/no_backup/appmetrica/analytics/db/client.db | binary | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/no_backup/appmetrica/analytics/uuid.dat | text | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/shared_prefs/log.xml | xml | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/shared_prefs/umeng_common_config.xml | xml | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/app_luna/block_cache/test.txt | binary | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/app_luna/.ntp_cache | binary | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/databases/ua.db | binary | |
MD5:— | SHA256:— | |||
| 3148 | app_process64 | /data/data/com.android.mgstv/shared_prefs/umeng_general_config.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
82
DNS requests
44
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2797 | app_process64 | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=%2FMOubJCEZblFizVyL%2FNuAfynF4er6odvumCQs0Py3Z%2Bu3knd7P%2Bb7PFd00zbg%2FogAl73BTwh5S60jE29TcqZUWPNPni7LAbpY%2B1%2FtegiwfrDHul1MSUqmiVPgmGB6FRzf9hv4Q%3D%3D | unknown | — | — | unknown |
822 | app_process64 | GET | 204 | 142.251.154.119:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
3148 | app_process64 | GET | 200 | 213.180.204.244:443 | https://startup.mobile.yandex.net/analytics/startup?deviceid=0a1e44a473544df7813d12fe69a47e08&adv_id=&oaid=&yandex_adv_id=&app_set_id=0a1e44a4-7354-4df7-813d-12fe69a47e08&app_set_id_scope=app&app_platform=android&protocol_version=2&analytics_sdk_version_name=7.14.0&model=P30_Pro&manufacturer=huawei&os_version=14&screen_width=1024&screen_height=576&screen_dpi=160&scalefactor=1.0&locale=en_US&device_type=tablet&queries=1&query_hosts=2&features=scr%2Cis%2Cpc%2Cfc%2Cg%2Ch%2Csi%2Csp&app_id=com.android.mgstv&app_debuggable=0&detect_locale=1&uuid=cc04f291939b4a868b03935bde1f5b21&time=1&stat_sending=1&rp=1&cc=1&pc=1&app_system_flag=0&at=1&su=1&exta=1&permissions=1&scr=1&aic=1&is=1 | unknown | — | — | unknown |
2797 | app_process64 | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&laf=b64bin&json=standard | unknown | — | — | whitelisted |
822 | app_process64 | GET | 204 | 142.250.186.35:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2797 | app_process64 | GET | 200 | 142.250.154.102:80 | http://clients2.google.com/time/1/current?cup2key=9:cWCNVhc8m7JeOMC-JXvX8sgvQE9C_0TJnNH8uCsrMl4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2797 | app_process64 | POST | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=%2FMOubJCEZblFizVyL%2FNuAfynF4er6odvumCQs0Py3Z%2Bu3knd7P%2Bb7PFd00zbg%2FogAl73BTwh5S60jE29TcqZUWPNPni7LAbpY%2B1%2FtegiwfrDHul1MSUqmiVPgmGB6FRzf9hv4Q%3D%3D | unknown | — | — | unknown |
1756 | app_process64 | POST | 200 | 142.251.127.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 778 b | whitelisted |
2797 | app_process64 | POST | 400 | 142.251.20.95:443 | https://androidchromeprotect.pa.googleapis.com/v1/download | unknown | text | 586 b | whitelisted |
1756 | app_process64 | POST | 200 | 142.251.127.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABnSy3RakBILStY-3Eycq_iePYoiRoNAChDc0=&request_id=36593f6c-b745-4eb3-a8c6-84f20a0404c1 | unknown | binary | 11.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.251.152.119:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.153.119:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 172.217.20.131:80 | — | GOOGLE | US | whitelisted |
2797 | app_process64 | 142.250.154.102:80 | clients2.google.com | GOOGLE | US | whitelisted |
2797 | app_process64 | 188.114.97.3:443 | fawt.xvmobdes.com | CLOUDFLARENET | US | whitelisted |
2797 | app_process64 | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2797 | app_process64 | 142.251.154.119:443 | www.google.com | GOOGLE | US | whitelisted |
2797 | app_process64 | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
822 | app_process64 | 142.250.186.35:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
fawt.xvmobdes.com |
| unknown |
www.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
androidchromeprotect.pa.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2797 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2797 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
3148 | app_process64 | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
3148 | app_process64 | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
3148 | app_process64 | Misc activity | ET INFO Cloudflare DNS Over HTTPS Certificate Inbound |
3148 | app_process64 | Misc activity | ET INFO Google DNS Over HTTPS Certificate Inbound |
3148 | app_process64 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
4025 | app_process64 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
4215 | app_process64 | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |