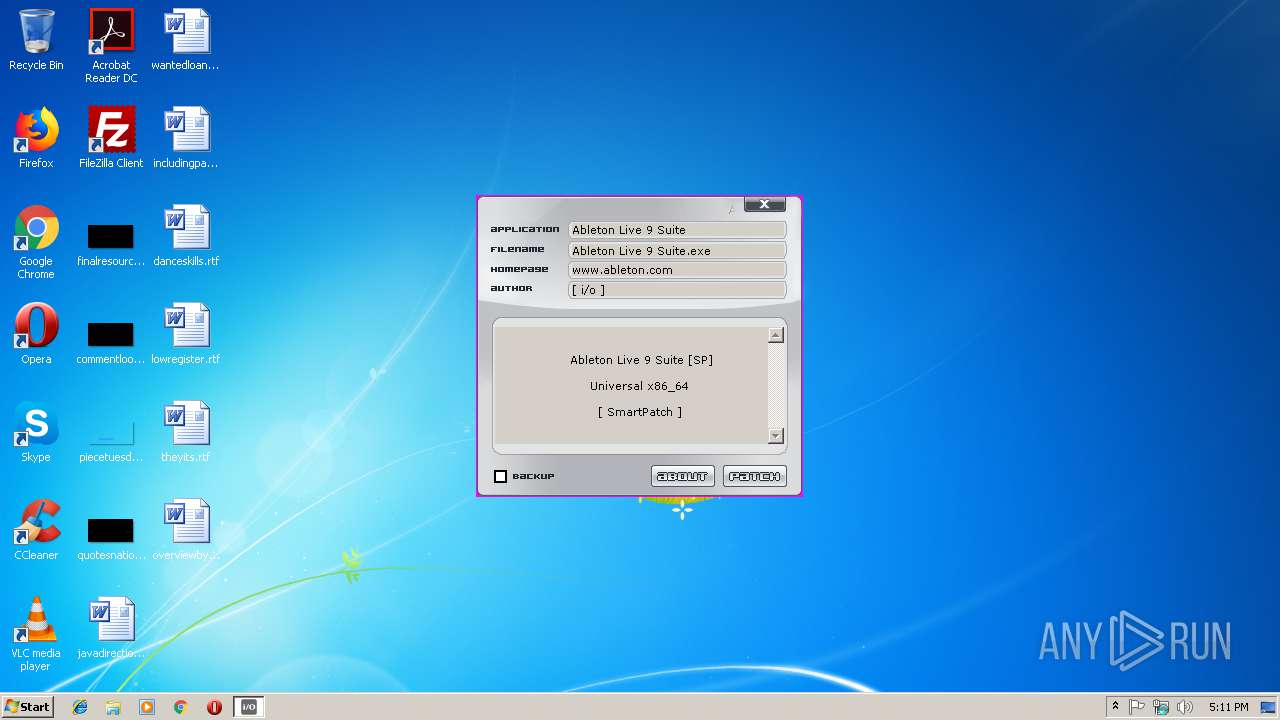
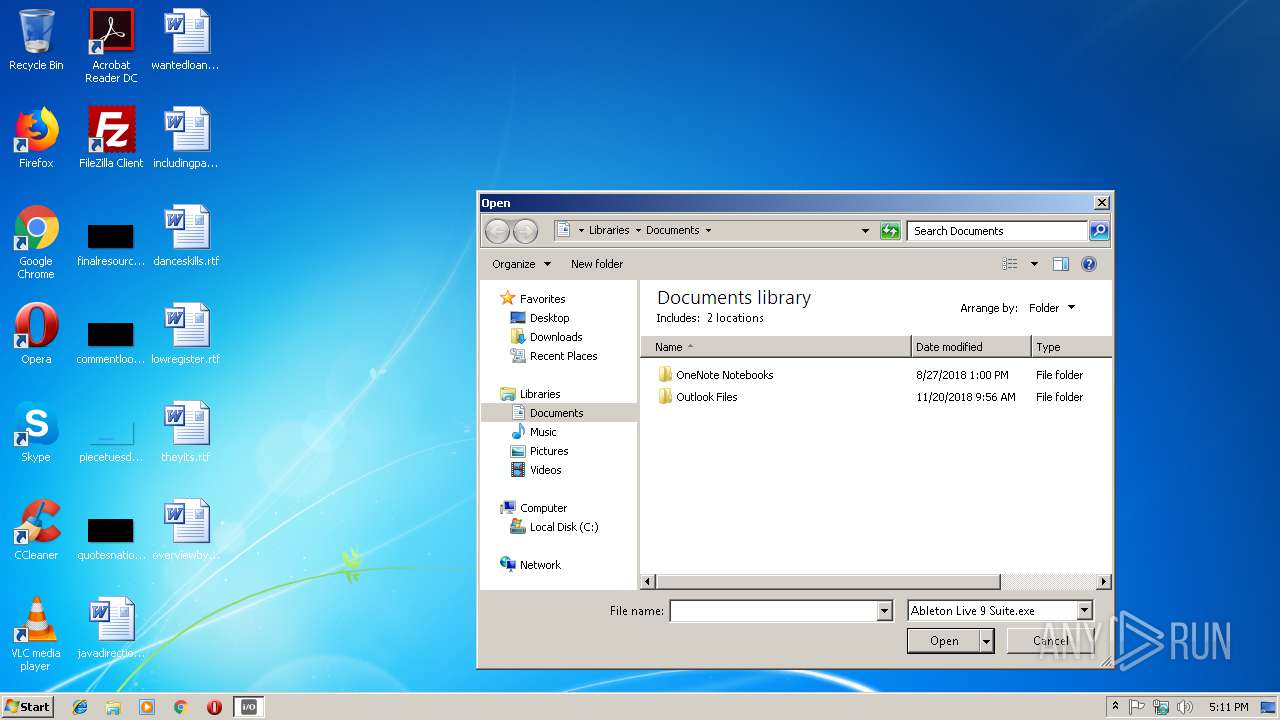
| File name: | Ableton LivePatch [io].exe |
| Full analysis: | https://app.any.run/tasks/e03c0a7c-ea4a-4a7e-9329-6faac67b407b |
| Verdict: | Suspicious activity |
| Analysis date: | December 09, 2018, 17:10:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E2F36B23167882C584D1EF1642FC2B01 |
| SHA1: | 41AD4B4F935C54B284F8B993EFA9F5E81A887006 |
| SHA256: | A417E8C0A5E9F8A93743E4C8972CFC4F912EC0F9000F706DF4836037DCA38D53 |
| SSDEEP: | 12288:u1y/NW3cE/07TmYuVR7YQU3lbggexIZtTV2sjFvcdC2QL13oSqu:u1y1W3B03mYucQU3lbggpJ2sNEC2QL1s |
MALICIOUS
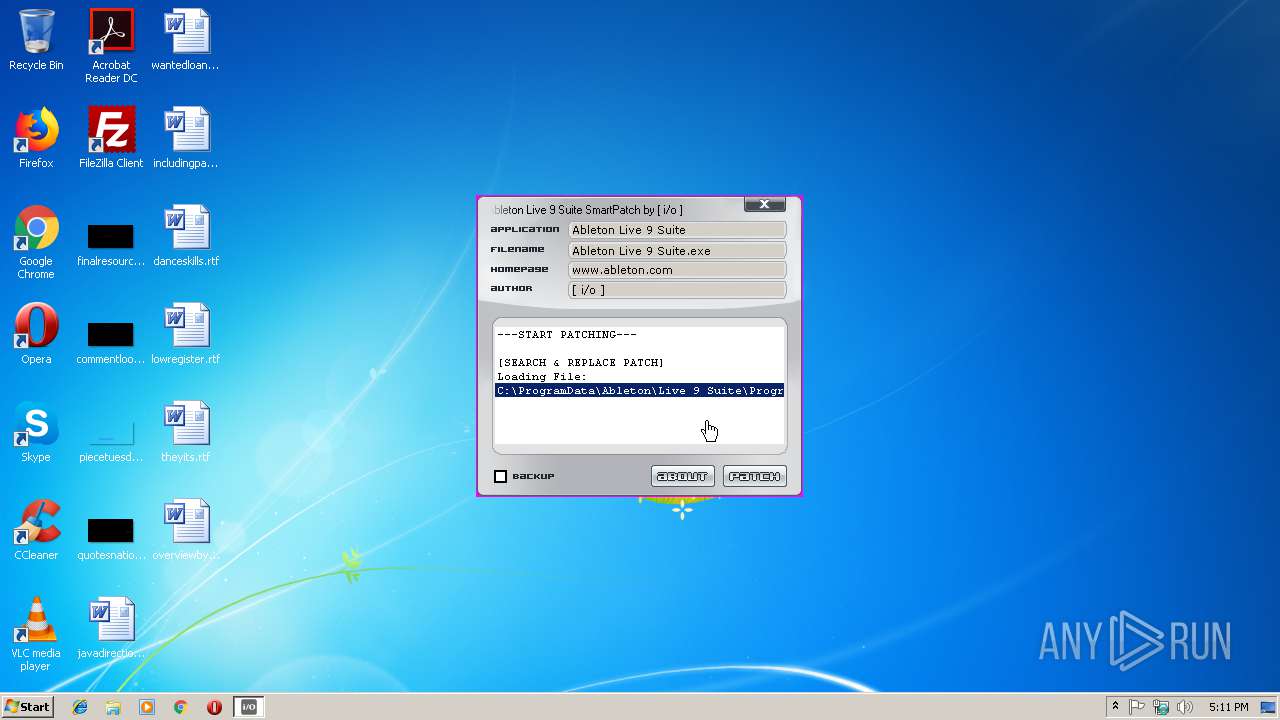
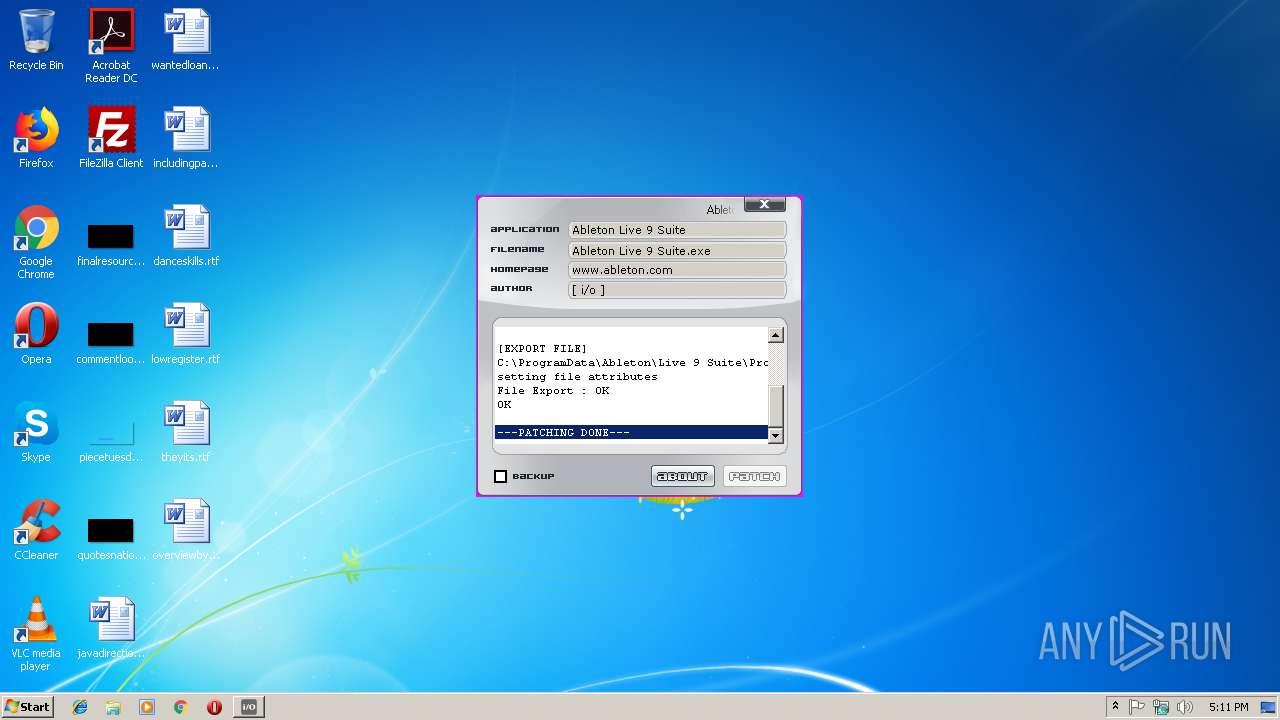
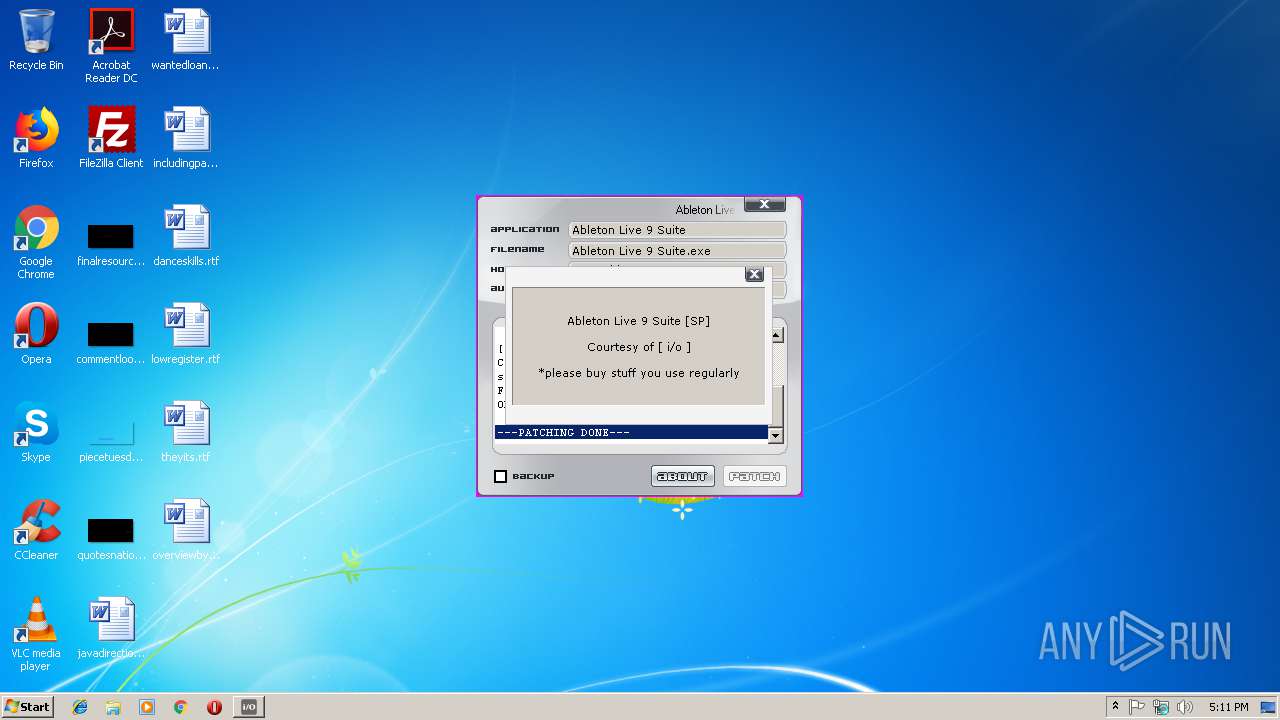
Loads dropped or rewritten executable
- Ableton LivePatch [io].exe (PID: 2996)
SUSPICIOUS
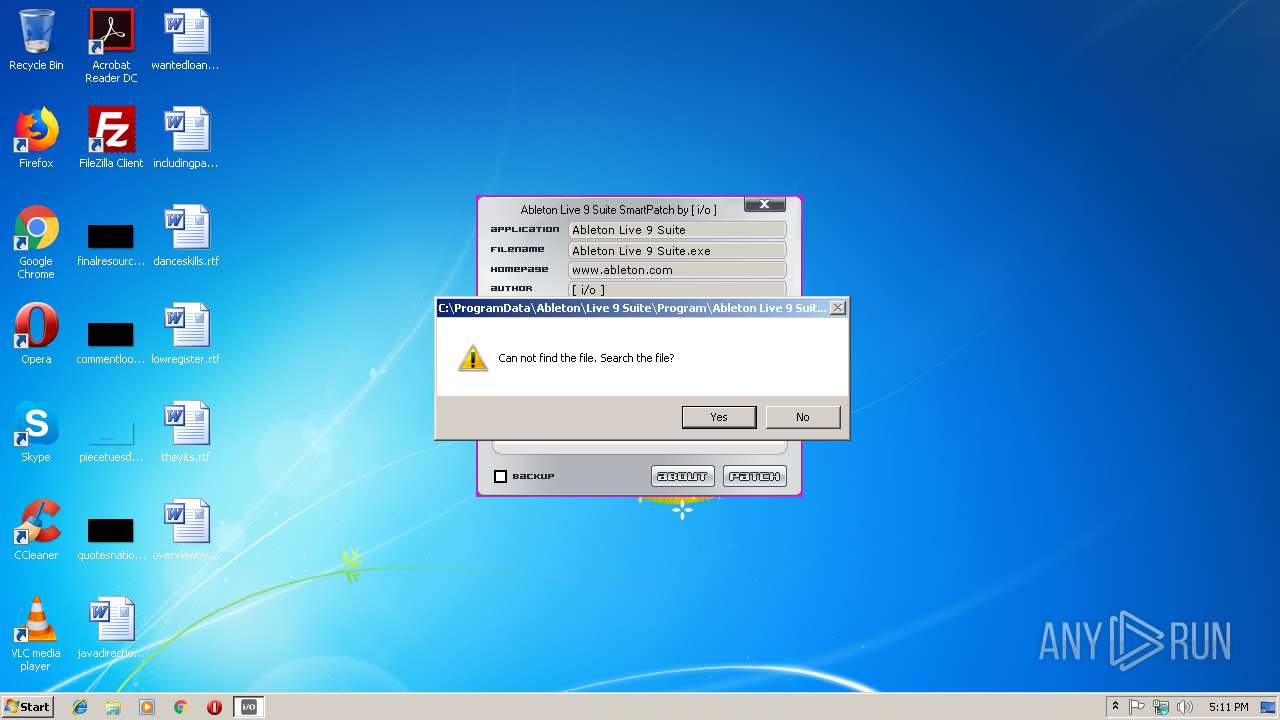
Creates files in the program directory
- Ableton LivePatch [io].exe (PID: 2996)
Executable content was dropped or overwritten
- Ableton LivePatch [io].exe (PID: 2996)
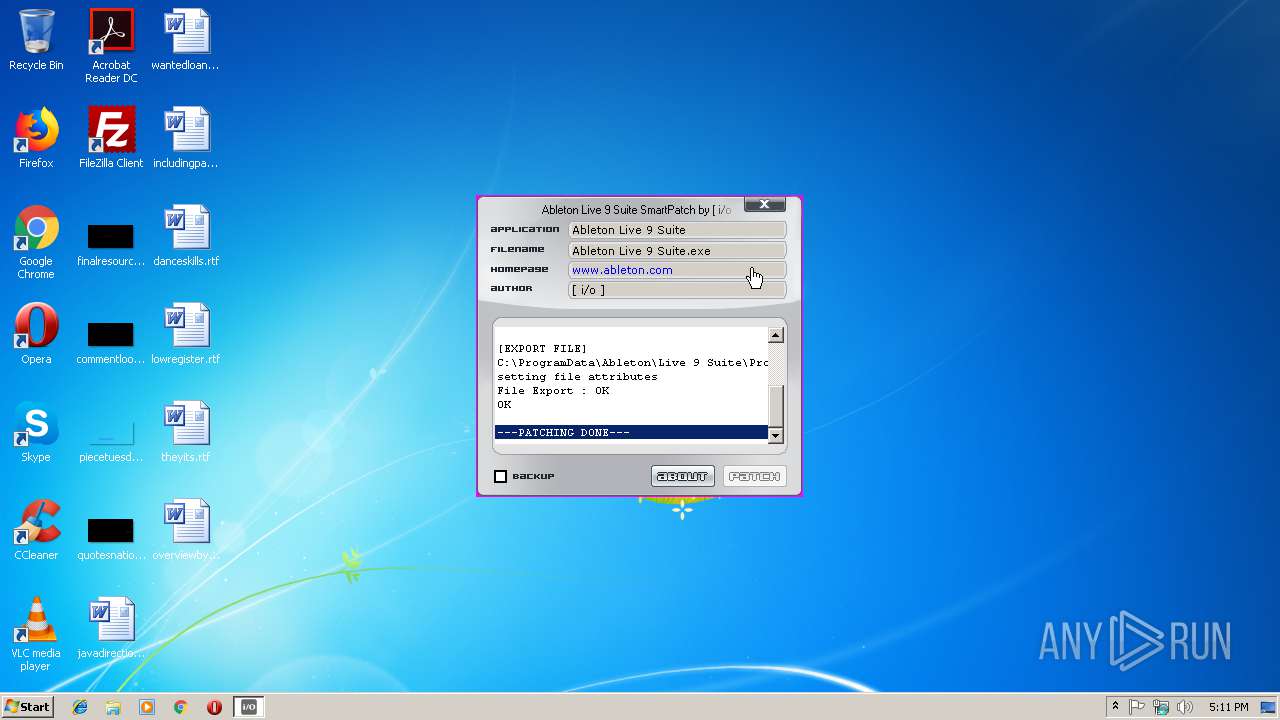
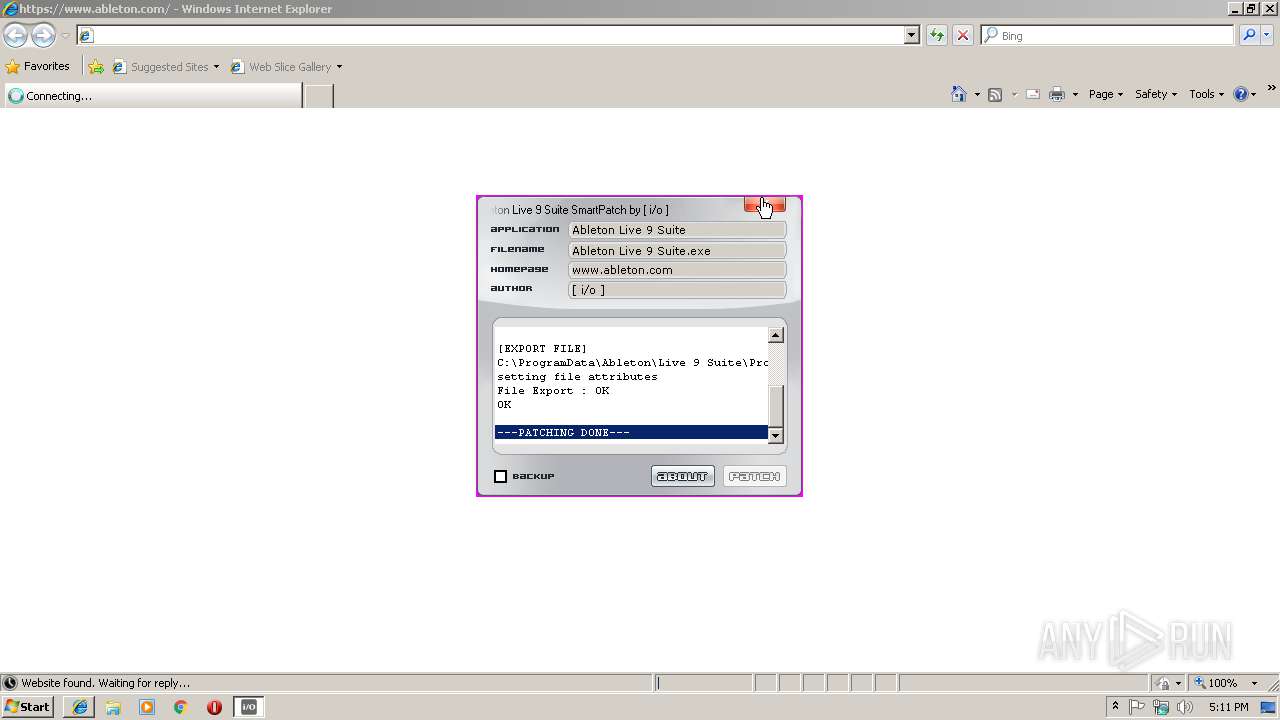
Starts Internet Explorer
- Ableton LivePatch [io].exe (PID: 2996)
INFO
Application launched itself
- iexplore.exe (PID: 2676)
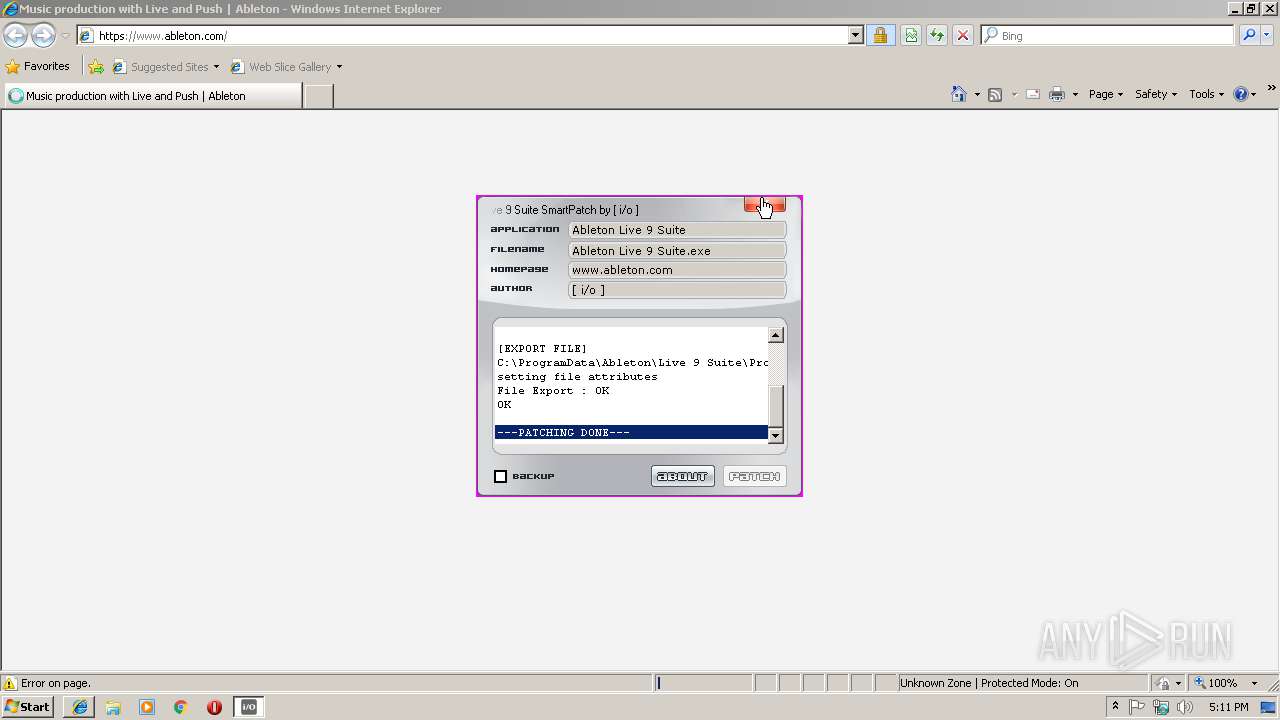
Changes internet zones settings
- iexplore.exe (PID: 2676)
Reads Internet Cache Settings
- iexplore.exe (PID: 3272)
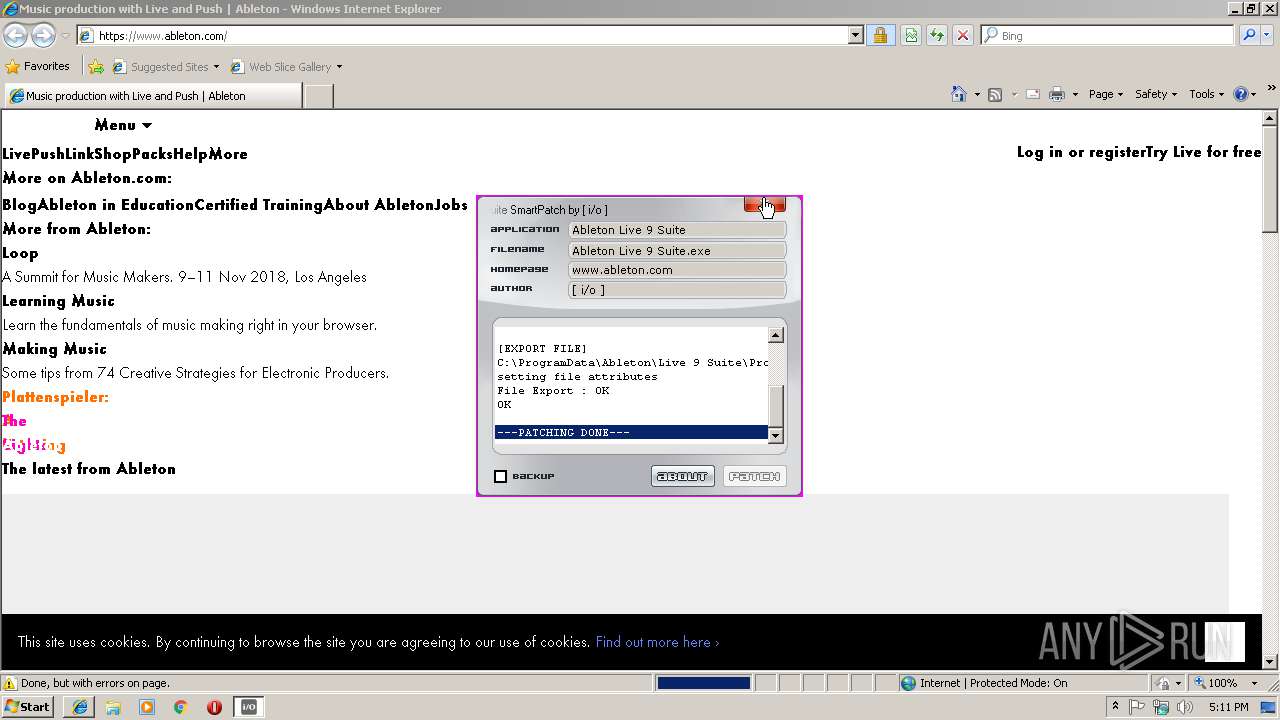
Creates files in the user directory
- iexplore.exe (PID: 3272)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2852)
- iexplore.exe (PID: 2676)
Reads internet explorer settings
- iexplore.exe (PID: 3272)
Reads settings of System Certificates
- iexplore.exe (PID: 2676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE Yoda's Crypter (63.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.7) |
| .exe | | | Win32 Executable (generic) (10.8) |
| .exe | | | Generic Win/DOS Executable (4.8) |
| .exe | | | DOS Executable Generic (4.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:03:05 18:19:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 495616 |
| InitializedDataSize: | 86016 |
| UninitializedDataSize: | 180224 |
| EntryPoint: | 0xa4bd0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Mar-2012 17:19:28 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Mar-2012 17:19:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\x05 | 0x0002D000 | 0x00079000 | 0x00078800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99929 |
.rsrc | 0x000A6000 | 0x00015000 | 0x00014A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.02775 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85948 | 887 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.97569 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.85912 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.85109 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
500 | 2.65982 | 62 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.58935 | 560128 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.DLL |
Total processes
33
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2676 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Ableton LivePatch [io].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\Ableton LivePatch [io].exe" | C:\Users\admin\AppData\Local\Temp\Ableton LivePatch [io].exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 033
Read events
899
Write events
132
Delete events
2
Modification events
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
| (PID) Process: | (2996) Ableton LivePatch [io].exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
2
Suspicious files
2
Text files
33
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@ableton[2].txt | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ableton_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\40a91f7c660b[1].css | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\810bbcee4deb[1].css | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@ableton[1].txt | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\futura-pt-book-oblique.bd17c4c4318c[1].eot | eot | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\homepage.1d724eeb23a5[1].js | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\el-pagination.57281e3a57b3[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
22
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3272 | iexplore.exe | GET | 301 | 195.122.191.209:80 | http://www.ableton.com/ | GB | html | 178 b | unknown |
2676 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3272 | iexplore.exe | 52.85.199.181:443 | script.crazyegg.com | Amazon.com, Inc. | US | unknown |
2676 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3272 | iexplore.exe | 195.122.191.209:80 | www.ableton.com | Level 3 Communications, Inc. | GB | unknown |
3272 | iexplore.exe | 195.122.191.209:443 | www.ableton.com | Level 3 Communications, Inc. | GB | unknown |
3272 | iexplore.exe | 104.16.147.208:443 | cdn-resources.ableton.com | Cloudflare Inc | US | shared |
3272 | iexplore.exe | 216.58.215.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3272 | iexplore.exe | 18.196.54.77:443 | recommender.scarabresearch.com | Amazon.com, Inc. | DE | unknown |
3272 | iexplore.exe | 216.58.215.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3272 | iexplore.exe | 173.194.79.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2676 | iexplore.exe | 104.16.147.208:443 | cdn-resources.ableton.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.ableton.com |
| unknown |
cdn-resources.ableton.com |
| unknown |
www.google-analytics.com |
| whitelisted |
recommender.scarabresearch.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.googleadservices.com |
| whitelisted |
www.google.com |
| malicious |
connect.facebook.net |
| whitelisted |