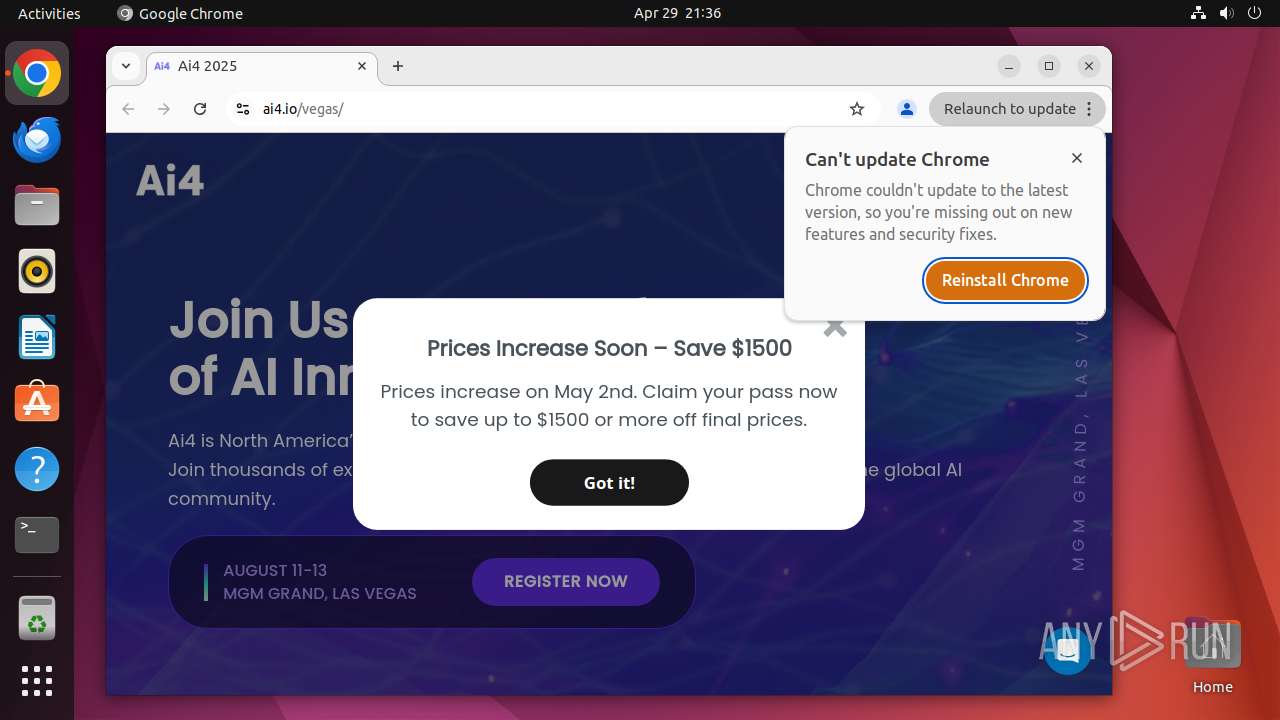
| URL: | https://ai4.io/vegas/ |
| Full analysis: | https://app.any.run/tasks/062090a5-a510-4eaf-b6e5-ef1bcf4ff9a3 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 20:36:03 |
| OS: | Ubuntu 22.04.2 |
| Indicators: | |
| MD5: | 718D0D79EDDB2CEF4CCFA1CD7747D2D8 |
| SHA1: | E11EDCD5D46B234AFB9CCD4DE9F430E41B91649D |
| SHA256: | A412F13D8F3F09B00C59905B887A340D624DF3FC2EE216D80CCD2A7971EB1E51 |
| SSDEEP: | 3:N8GAtn:29n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 40660)
- chrome (PID: 40661)
INFO
Checks timezone
- chrome (PID: 40661)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
307
Monitored processes
87
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40659 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://ai4\.io/vegas/ " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 40660 | sudo -iu user google-chrome https://ai4.io/vegas/ | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40661 | /usr/bin/google-chrome https://ai4.io/vegas/ | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 40662 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40663 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40664 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40665 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40667 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40668 | "/opt/google/chrome/chrome https://ai4\.io/vega" | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
106
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40661 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40707 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40812 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
80
DNS requests
100
Threats
92
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40710 | chrome | 172.67.72.30:443 | ai4.io | — | — | unknown |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40710 | chrome | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40710 | chrome | 216.58.212.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40710 | chrome | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
40710 | chrome | 18.173.184.19:443 | d1b3llzbo1rqxo.cloudfront.net | — | US | whitelisted |
40710 | chrome | 104.21.27.152:443 | use.fontawesome.com | — | — | whitelisted |
40710 | chrome | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
ai4.io |
| unknown |
accounts.google.com |
| whitelisted |
d1b3llzbo1rqxo.cloudfront.net |
| whitelisted |
use.fontawesome.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |