| File name: | AnyDesk.exe |
| Full analysis: | https://app.any.run/tasks/1c65a848-110d-42a1-a33d-b7798727d681 |
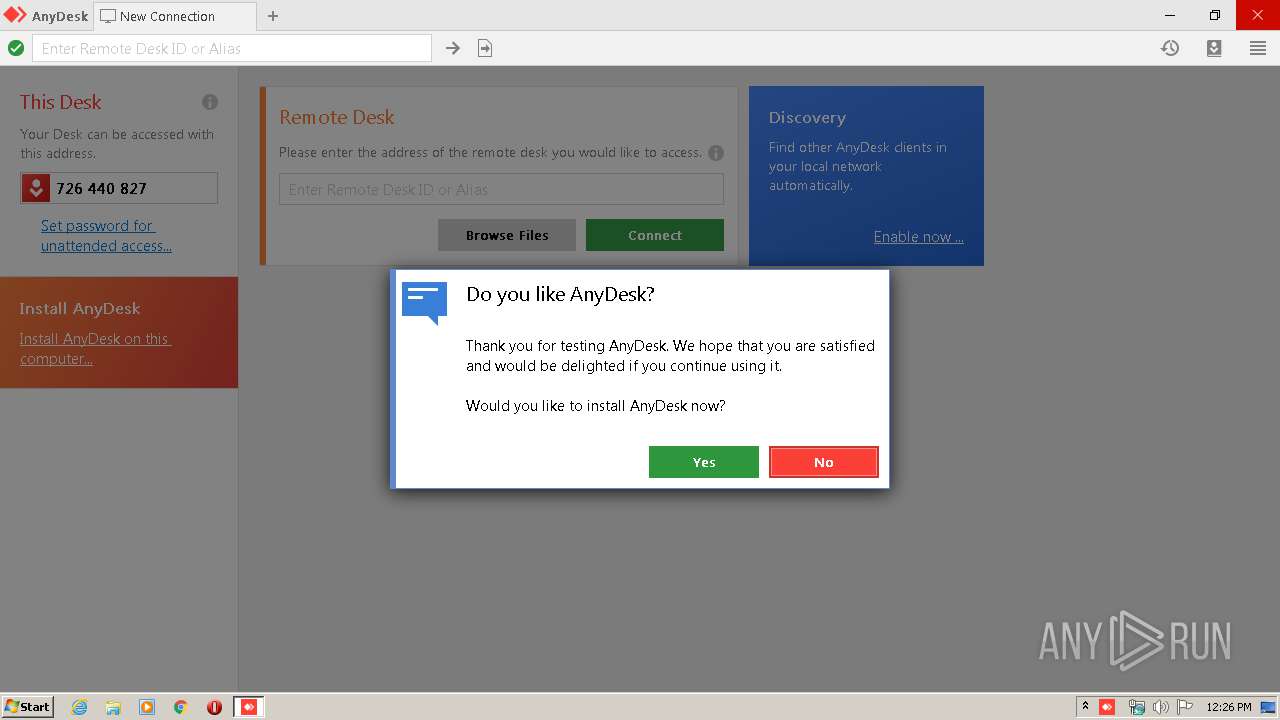
| Verdict: | Malicious activity |
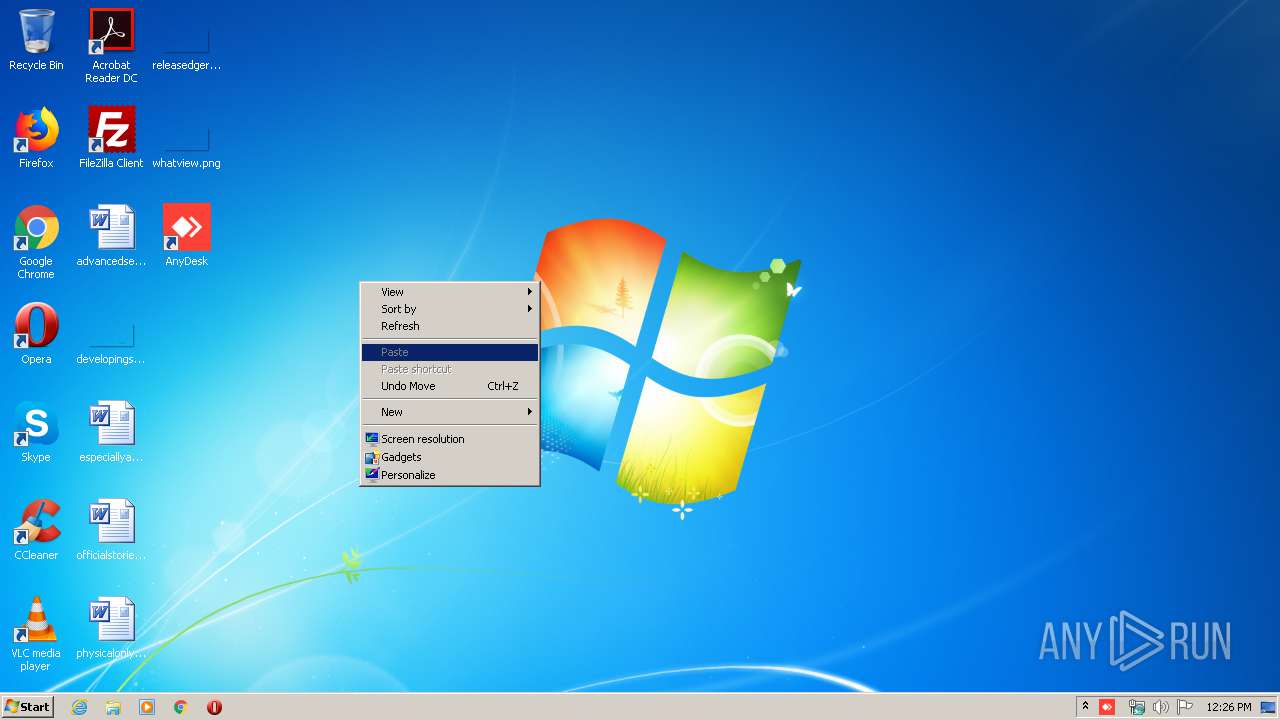
| Analysis date: | February 22, 2020, 12:26:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7CF4B655453D28F246C815A953F48936 |
| SHA1: | 5A791B09C44197E9F4D4273794BFEB887786E359 |
| SHA256: | A411CD9F330129F0278FB4EB9767E7AB0B2B7F6B67CA51CC7CE47806B477CE61 |
| SSDEEP: | 49152:B/Vq+uyU4GjG8rvRVDhlaTMT4Orlsu2JJWCJ47V8QekDGFHTgBEM8KWhSCfAIlOg:BU+uyzOG8PjagTL5suAJlJ+8QekDGuyn |
MALICIOUS
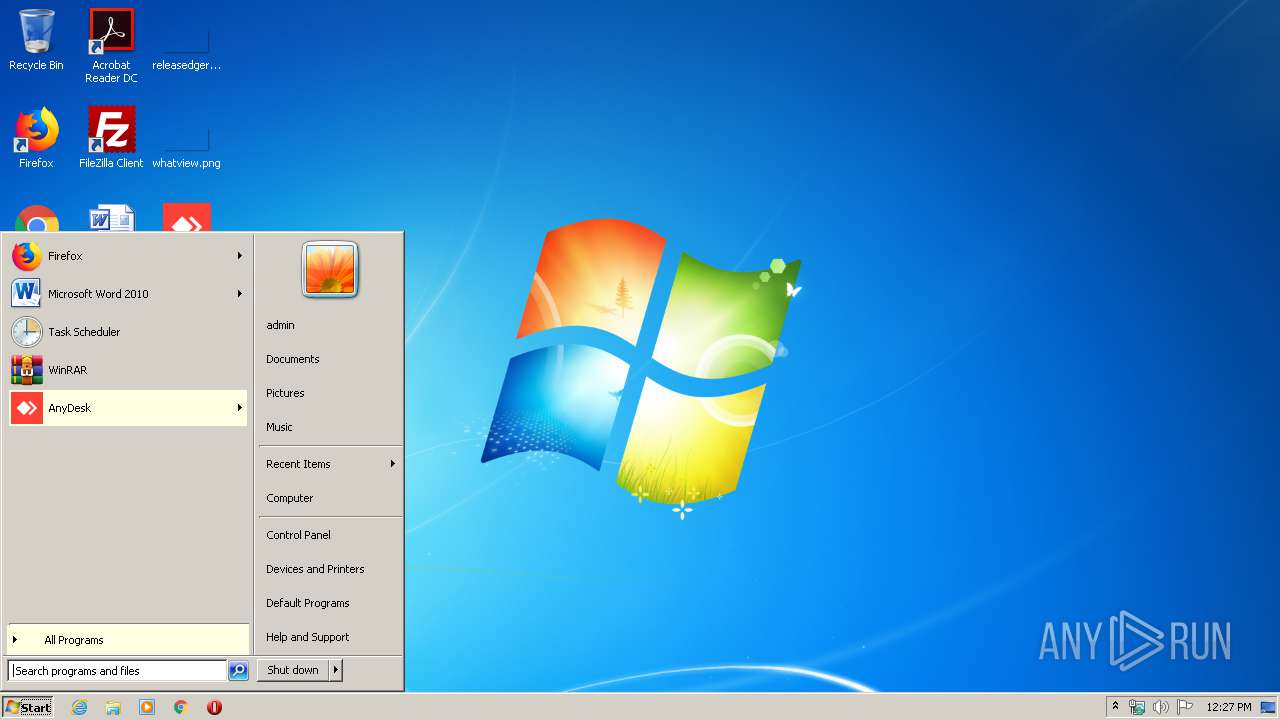
Writes to a start menu file
- AnyDesk.exe (PID: 1520)
SUSPICIOUS
Creates files in the user directory
- AnyDesk.exe (PID: 2568)
- AnyDesk.exe (PID: 3016)
- AnyDesk.exe (PID: 1352)
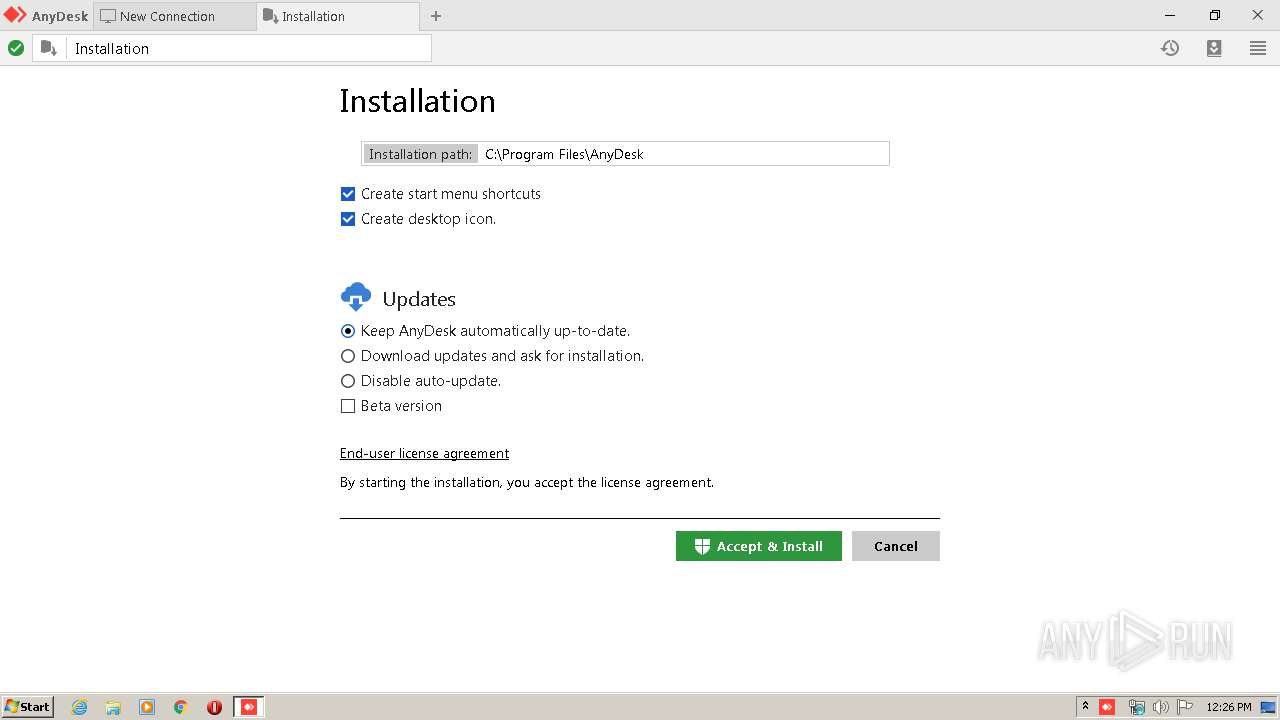
Executable content was dropped or overwritten
- AnyDesk.exe (PID: 1520)
Modifies the open verb of a shell class
- AnyDesk.exe (PID: 1520)
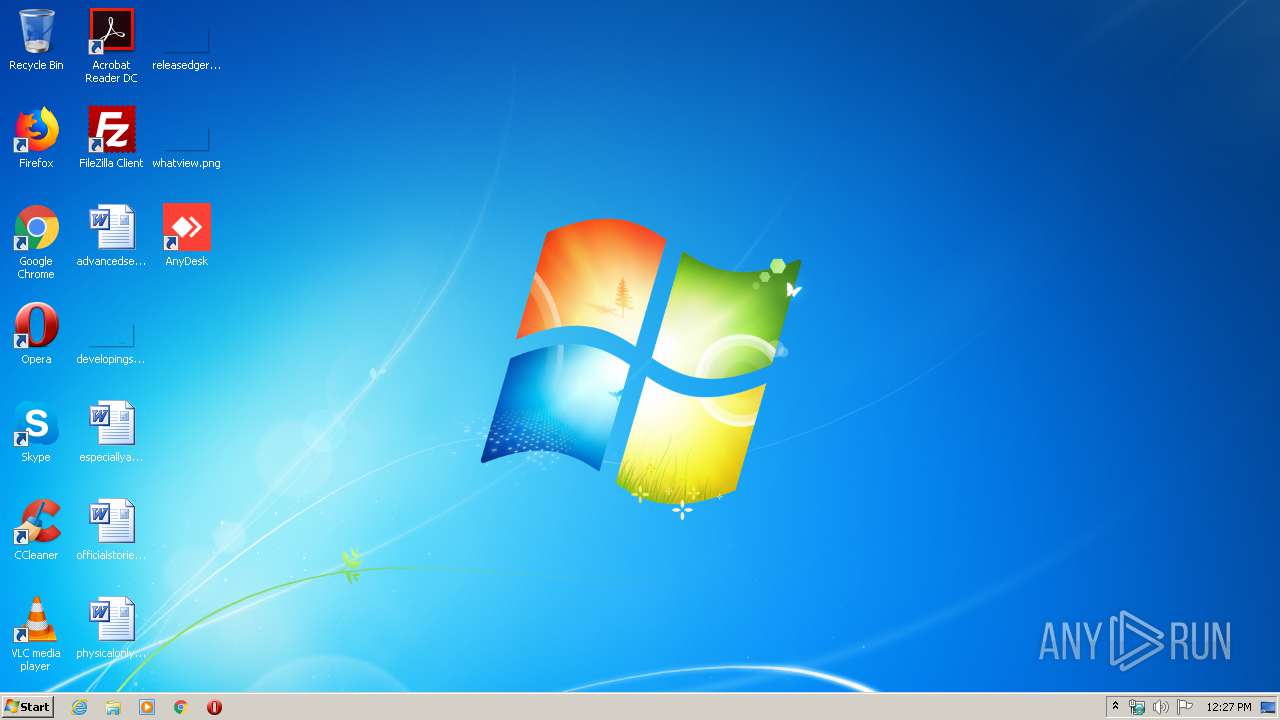
Creates a software uninstall entry
- AnyDesk.exe (PID: 3580)
- AnyDesk.exe (PID: 1520)
Executed as Windows Service
- AnyDesk.exe (PID: 3580)
Creates files in the program directory
- AnyDesk.exe (PID: 3580)
- AnyDesk.exe (PID: 1520)
Searches for installed software
- AnyDesk.exe (PID: 3580)
- AnyDesk.exe (PID: 1872)
- AnyDesk.exe (PID: 3016)
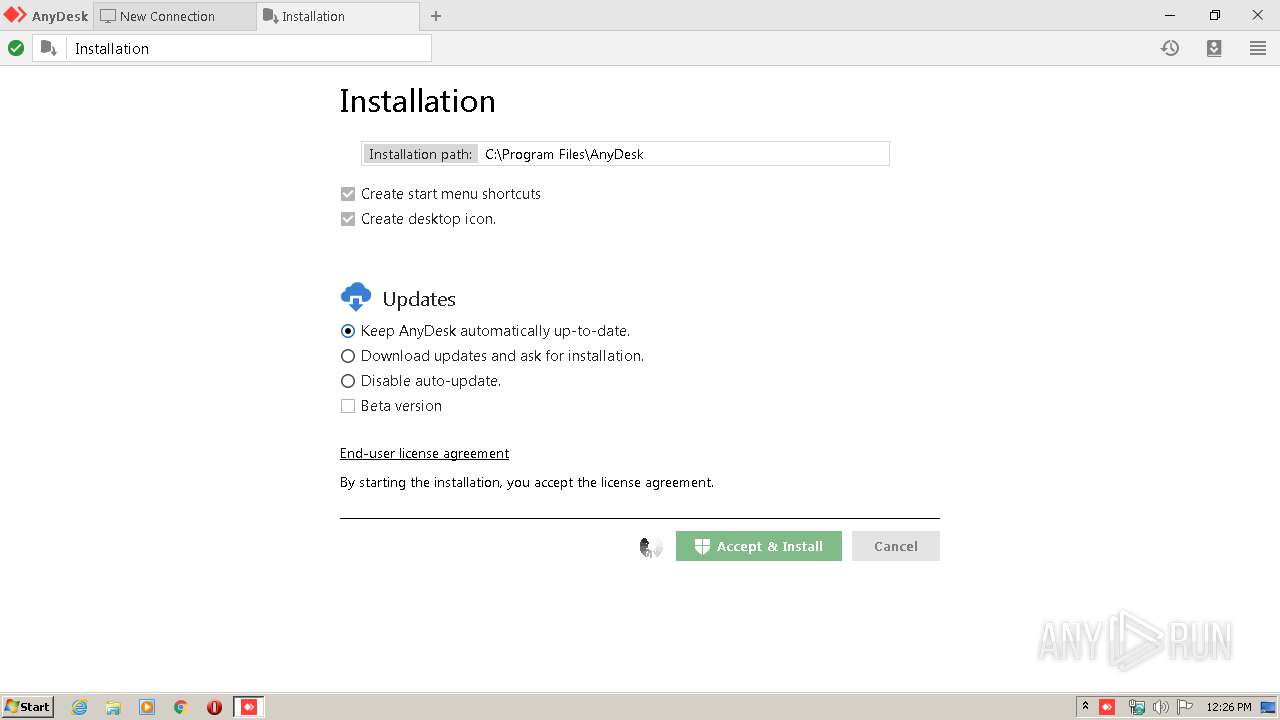
Application launched itself
- AnyDesk.exe (PID: 1352)
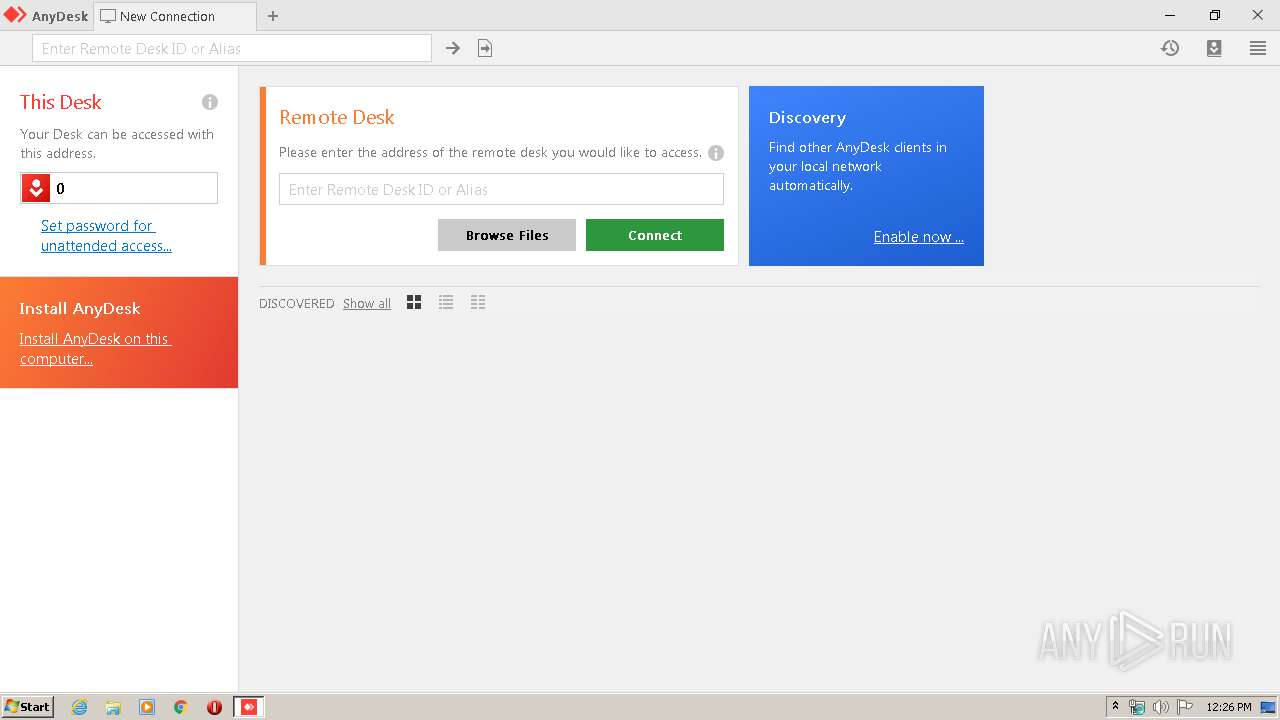
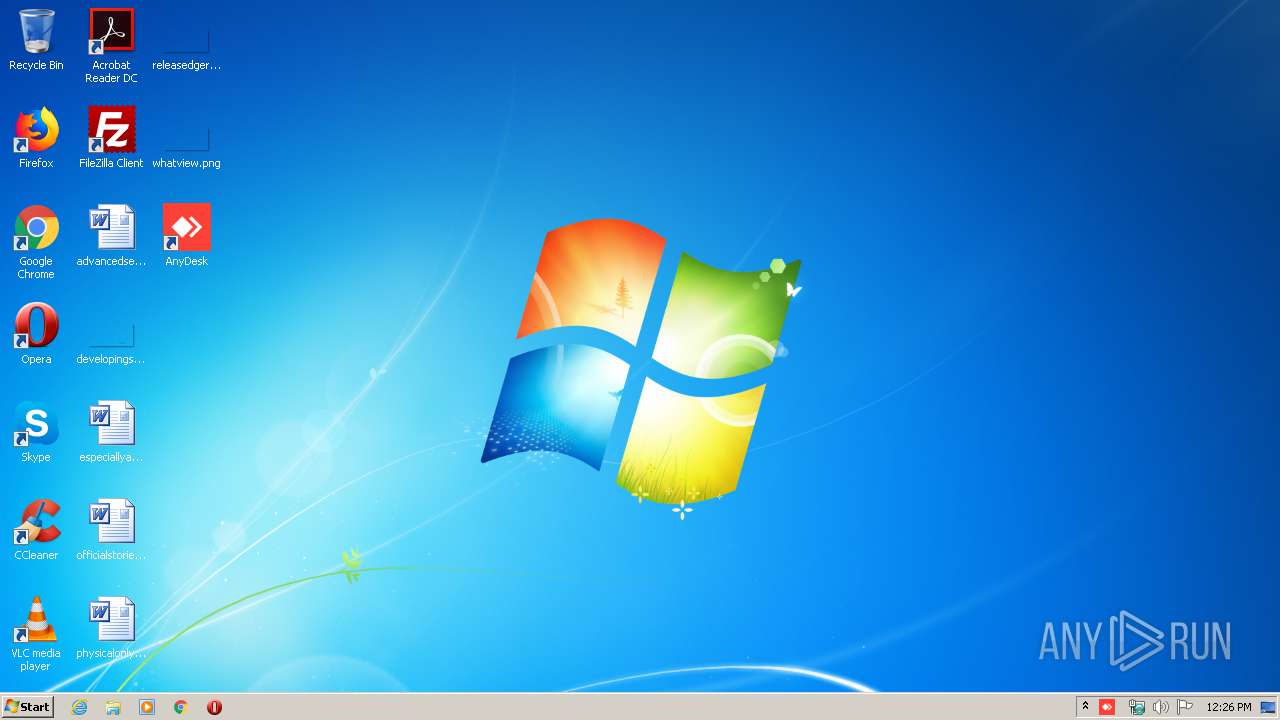
INFO
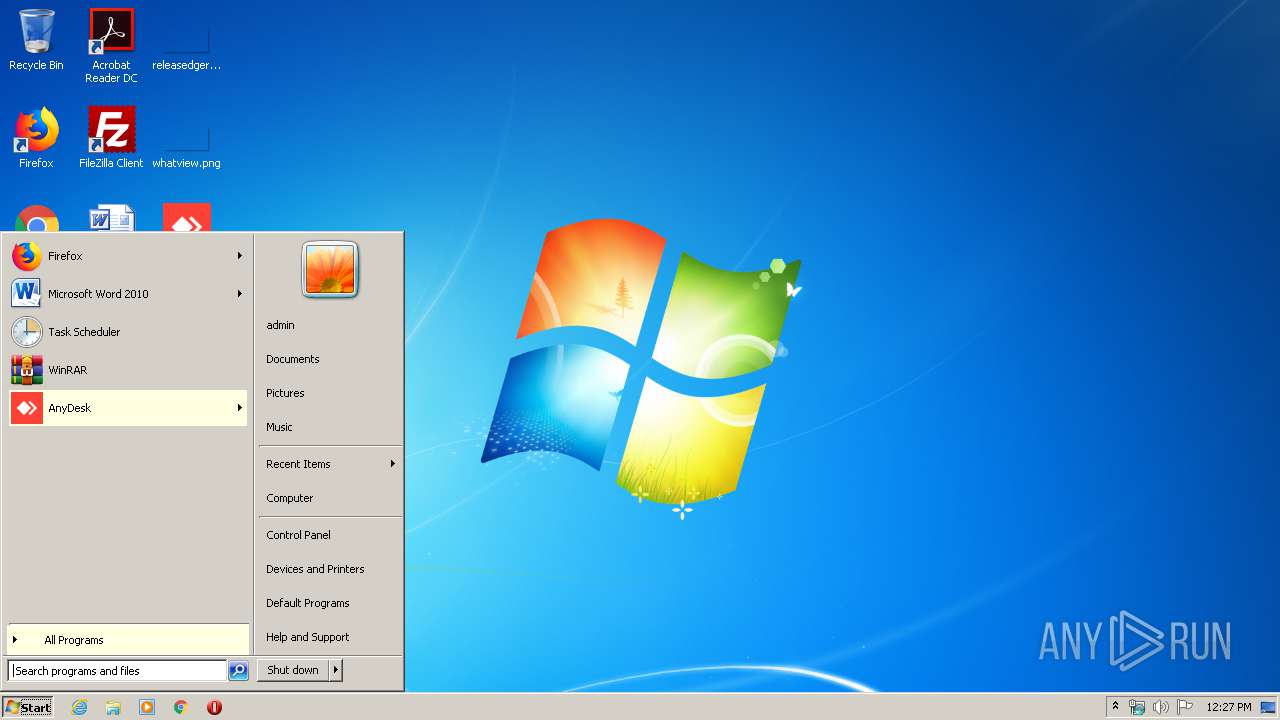
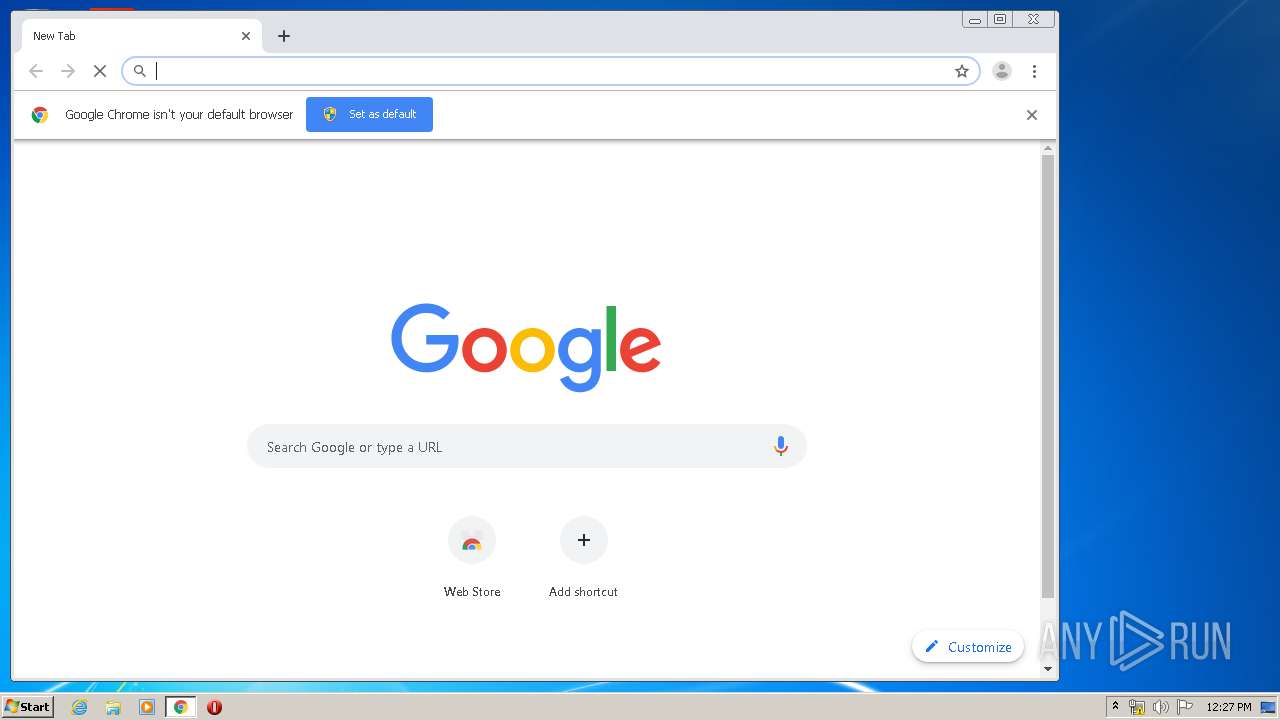
Manual execution by user
- AnyDesk.exe (PID: 2248)
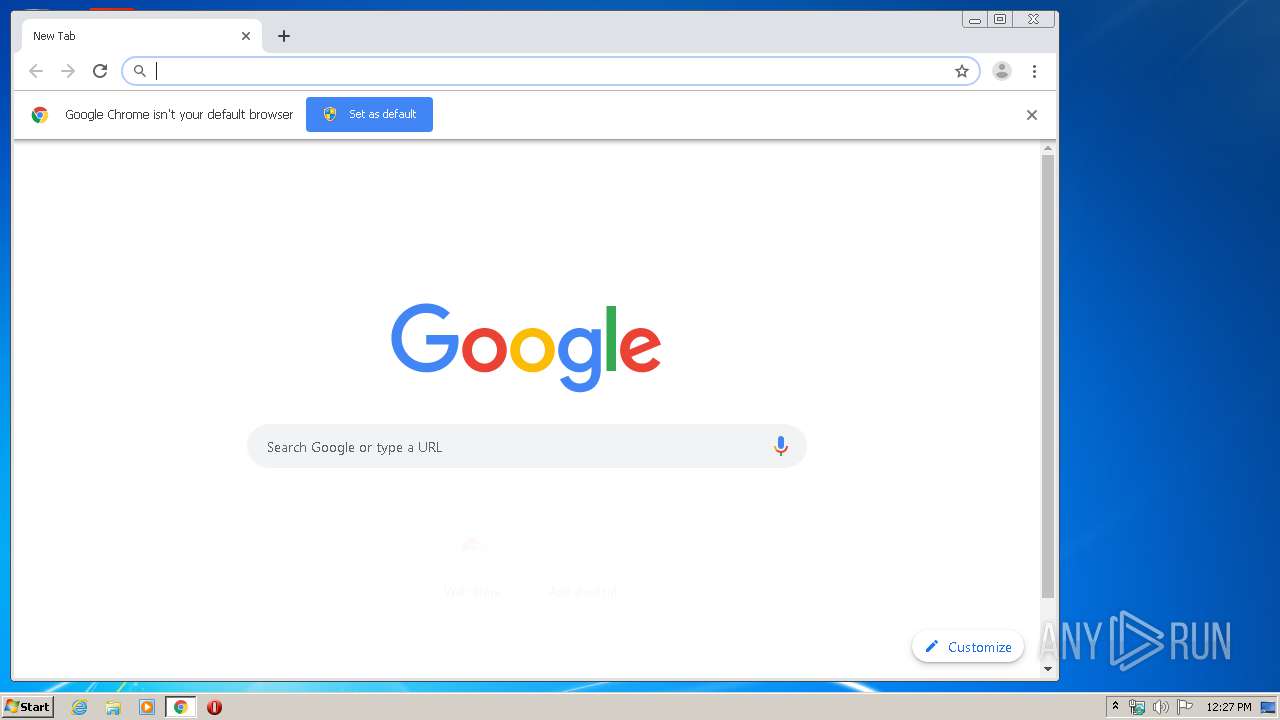
- chrome.exe (PID: 1948)
- AnyDesk.exe (PID: 3016)
Reads the hosts file
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2084)
Application launched itself
- chrome.exe (PID: 1948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:18 19:16:20+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 10752 |
| InitializedDataSize: | 3000832 |
| UninitializedDataSize: | 9262592 |
| EntryPoint: | 0x1ce9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.4.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 5.4.0.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 5.4 |
| LegalCopyright: | (C) 2019 philandro Software GmbH |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2019 18:16:20 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 5.4.0.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 5.4 |
| LegalCopyright: | (C) 2019 philandro Software GmbH |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 18-Nov-2019 18:16:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002835 | 0x00002A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50754 |
.itext | 0x00004000 | 0x008D5600 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x008DA000 | 0x000002F2 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.59561 |
.data | 0x008DB000 | 0x002D8DF4 | 0x002D8A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99994 |
.rsrc | 0x00BB4000 | 0x00003290 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.68371 |
.reloc | 0x00BB8000 | 0x00000300 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.18127 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39304 | 1543 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.29968 | 1640 | UNKNOWN | English - United States | RT_ICON |
3 | 3.6735 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 2.73746 | 488 | UNKNOWN | English - United States | RT_ICON |
5 | 3.69265 | 296 | UNKNOWN | English - United States | RT_ICON |
1000 | 2.78538 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
Total processes
69
Monitored processes
29
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2029891838189796973,15663671708467391790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10108827963011369264 --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2029891838189796973,15663671708467391790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10542884943631179280 --mojo-platform-channel-handle=3676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" --install "C:\Program Files\AnyDesk" --start-with-win --create-shortcuts --create-taskbar-icon --create-desktop-icon --install-drv --update-auto --svc-conf "C:\Users\admin\AppData\Roaming\AnyDesk\service.conf" | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | AnyDesk.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2029891838189796973,15663671708467391790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15651897940946275110 --mojo-platform-channel-handle=3568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" --local-control | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | — | AnyDesk.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2029891838189796973,15663671708467391790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8132173827138667552 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\AnyDesk\AnyDesk.exe" --control | C:\Program Files\AnyDesk\AnyDesk.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,2029891838189796973,15663671708467391790,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11905308796301615089 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
943
Read events
865
Write events
75
Delete events
3
Modification events
| (PID) Process: | (1352) AnyDesk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1352) AnyDesk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\AnyDesk\AnyDesk.exe" | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | DisplayName |
Value: AnyDesk | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | DisplayVersion |
Value: ad 5.4.0 | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | EstimatedSize |
Value: 2048 | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | HelpLink |
Value: http://help.anydesk.com/ | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | InstallLocation |
Value: "C:\Program Files\AnyDesk" | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | Publisher |
Value: philandro Software GmbH | |||
| (PID) Process: | (1520) AnyDesk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AnyDesk |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\AnyDesk\AnyDesk.exe" --uninstall | |||
Executable files
1
Suspicious files
21
Text files
236
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TQZXK73GR7CUOKOMKFMH.temp | — | |
MD5:— | SHA256:— | |||
| 1352 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\V3WDKNLQP7WCGUK9EG79.temp | — | |
MD5:— | SHA256:— | |||
| 3016 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VVAH97TO5816L628YKGJ.temp | — | |
MD5:— | SHA256:— | |||
| 2568 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\service.conf | text | |
MD5:— | SHA256:— | |||
| 1352 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\75fdacd8330bac18.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2568 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\system.conf | text | |
MD5:— | SHA256:— | |||
| 1520 | AnyDesk.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\AnyDesk\AnyDesk.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1520 | AnyDesk.exe | C:\Program Files\AnyDesk\AnyDesk.exe | executable | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E511E28-79C.pma | — | |
MD5:— | SHA256:— | |||
| 1520 | AnyDesk.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\AnyDesk.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2084 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
2084 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
2084 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1582374029&mv=u&mvi=3&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
2084 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1582374029&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
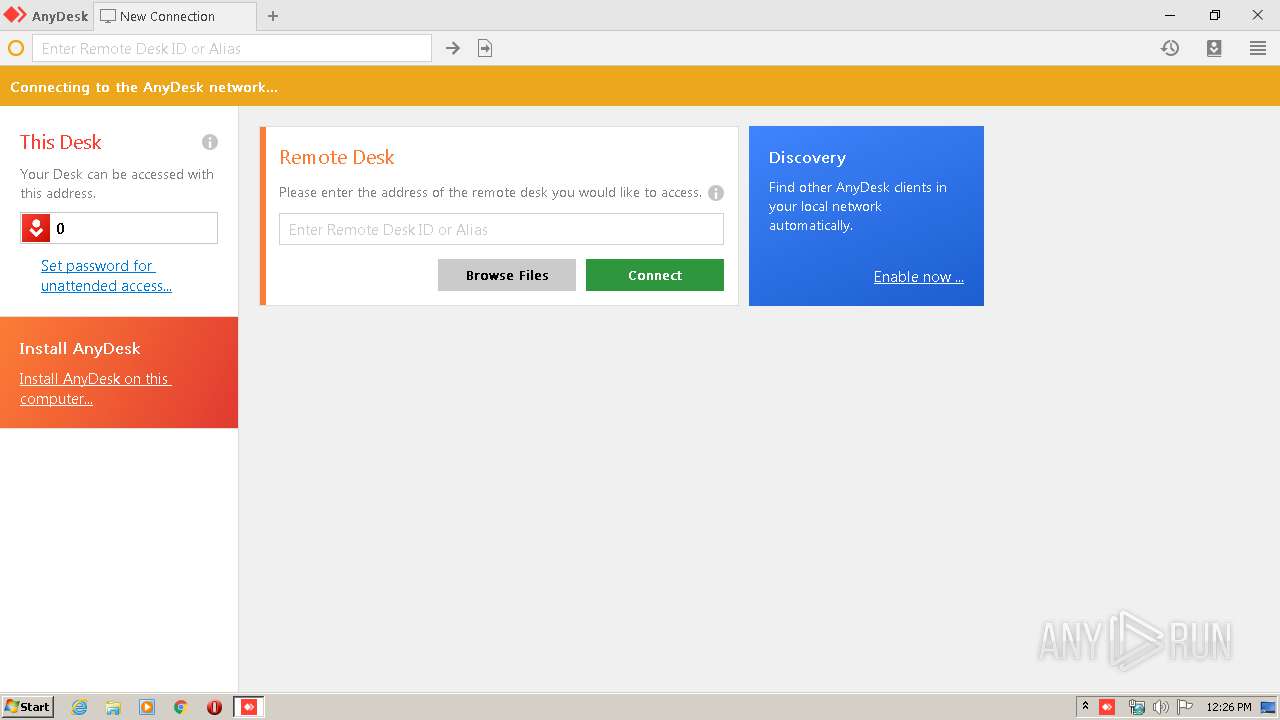
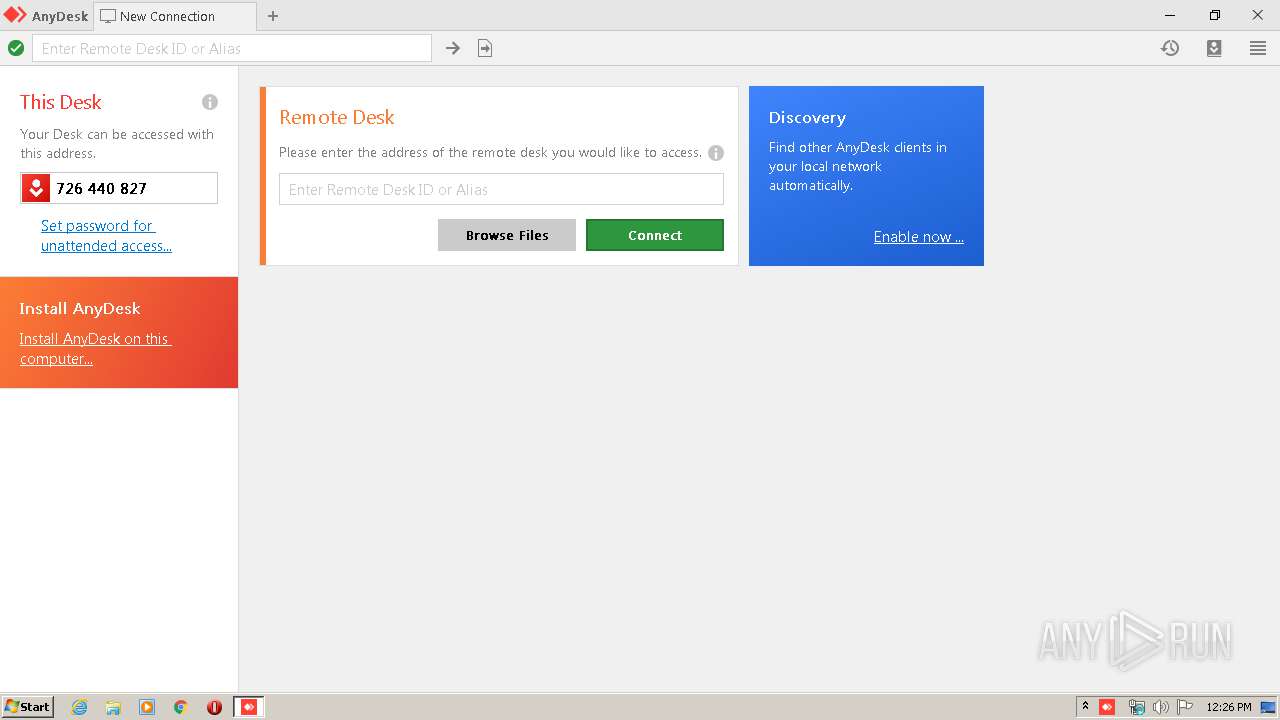
2568 | AnyDesk.exe | 151.106.27.117:443 | boot-01.net.anydesk.com | — | US | suspicious |
3580 | AnyDesk.exe | 151.106.27.117:443 | boot-01.net.anydesk.com | — | US | suspicious |
2568 | AnyDesk.exe | 148.251.121.236:80 | relay-1457bf2d.net.anydesk.com | Hetzner Online GmbH | DE | unknown |
3580 | AnyDesk.exe | 217.182.196.53:80 | relay-b78965e4.net.anydesk.com | OVH SAS | DE | suspicious |
2084 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2084 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
boot-01.net.anydesk.com |
| whitelisted |
relay-1457bf2d.net.anydesk.com |
| whitelisted |
relay-b78965e4.net.anydesk.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2568 | AnyDesk.exe | Potential Corporate Privacy Violation | ET POLICY SSL/TLS Certificate Observed (AnyDesk Remote Desktop Software) |