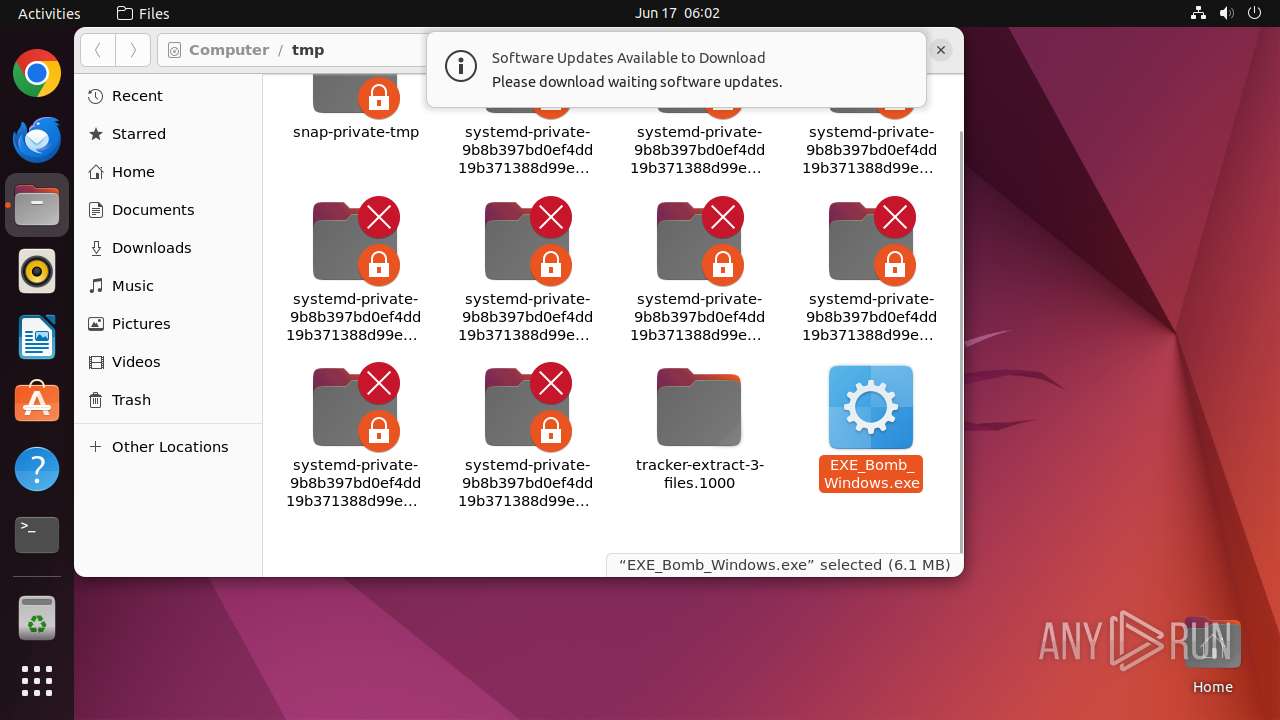
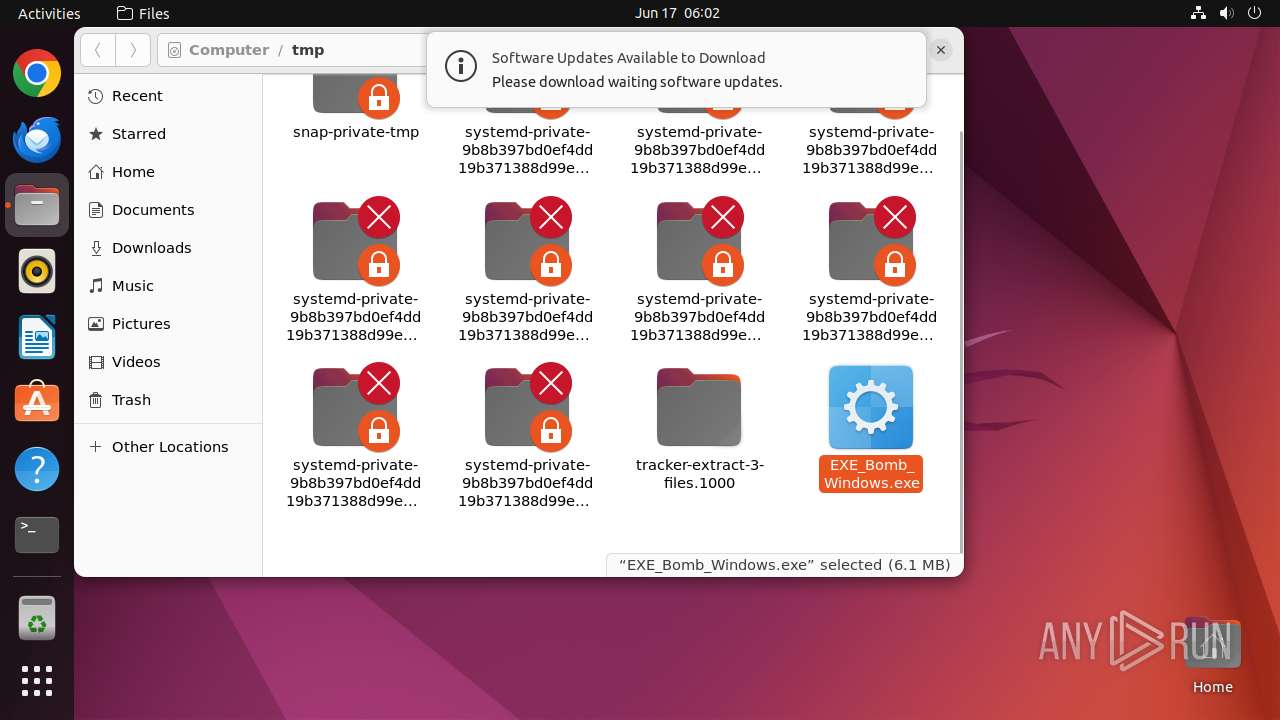
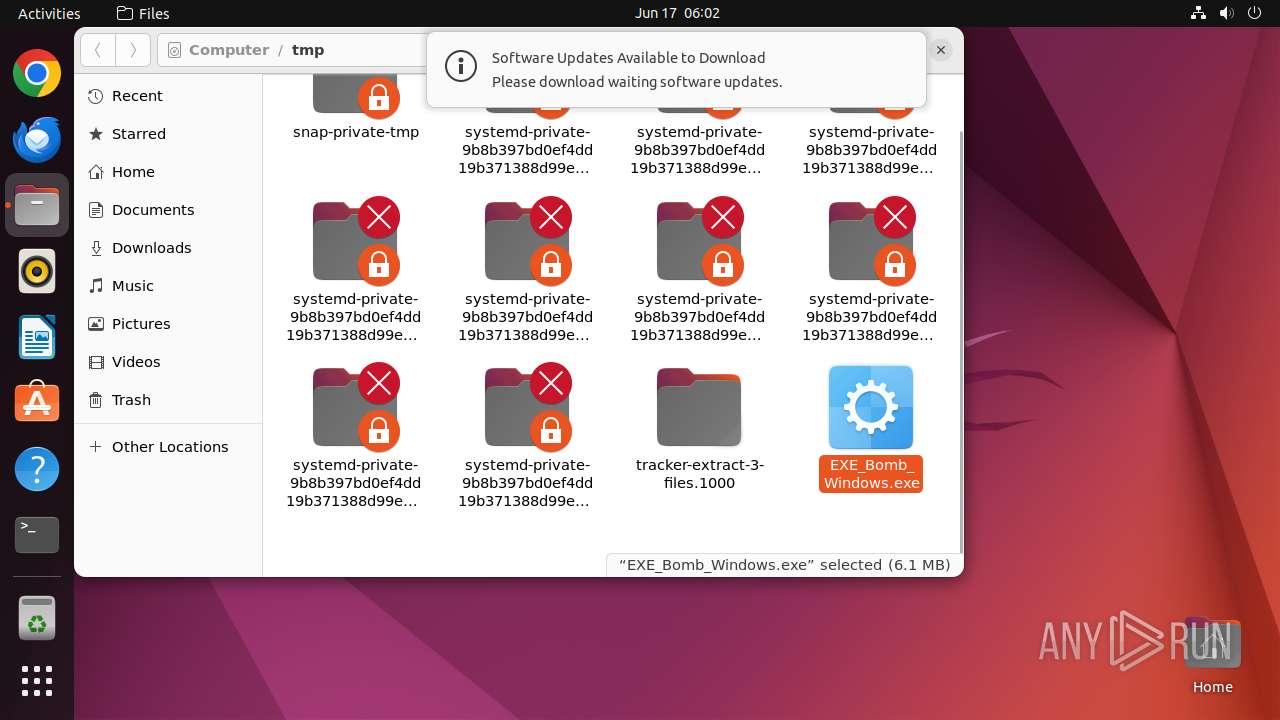
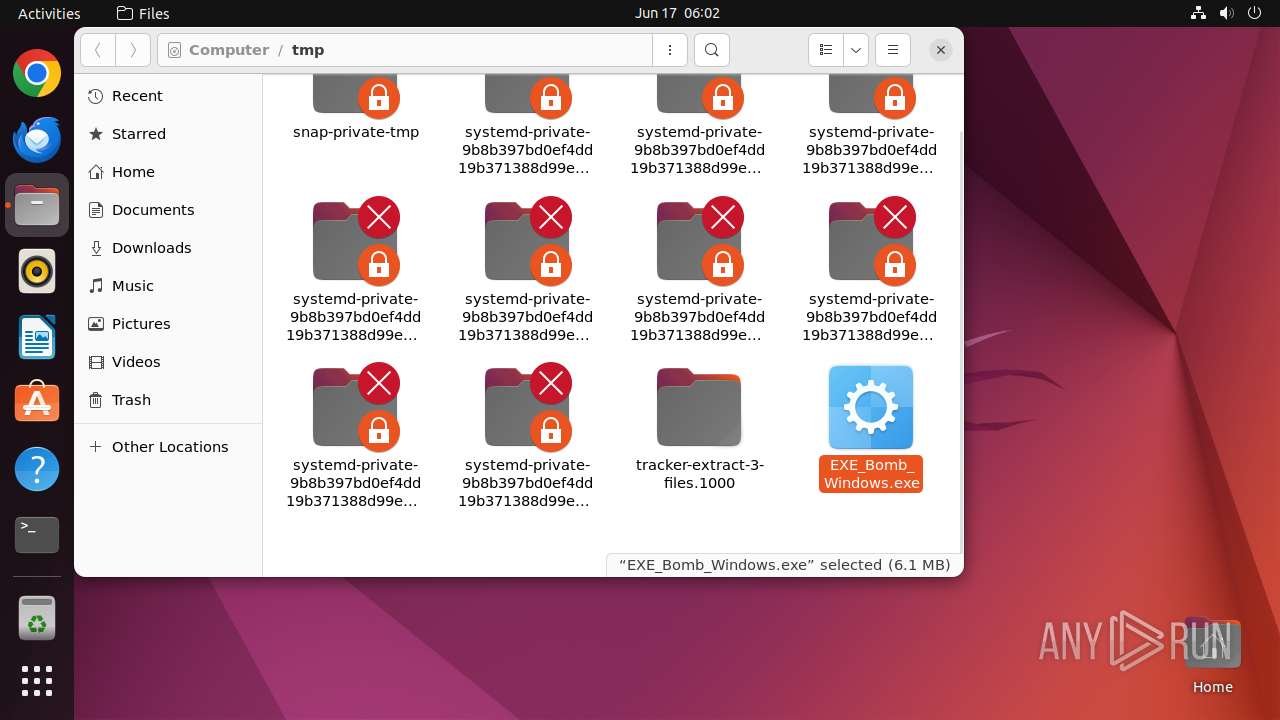
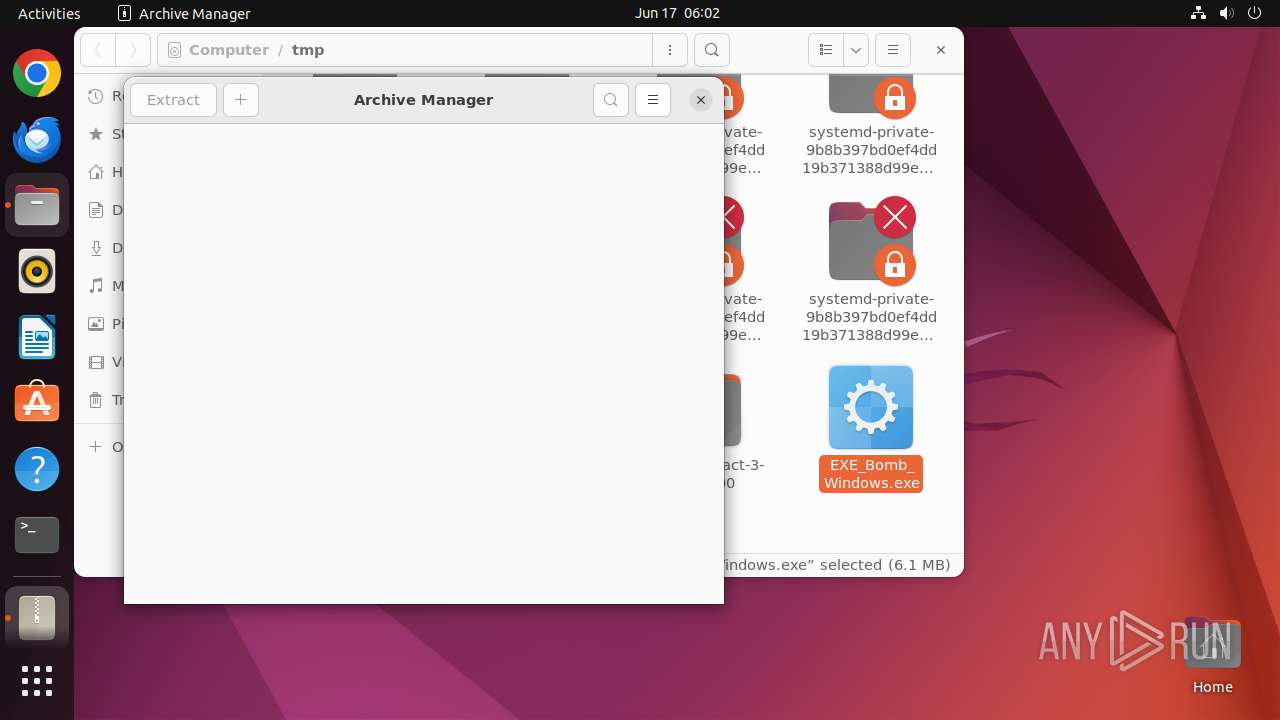
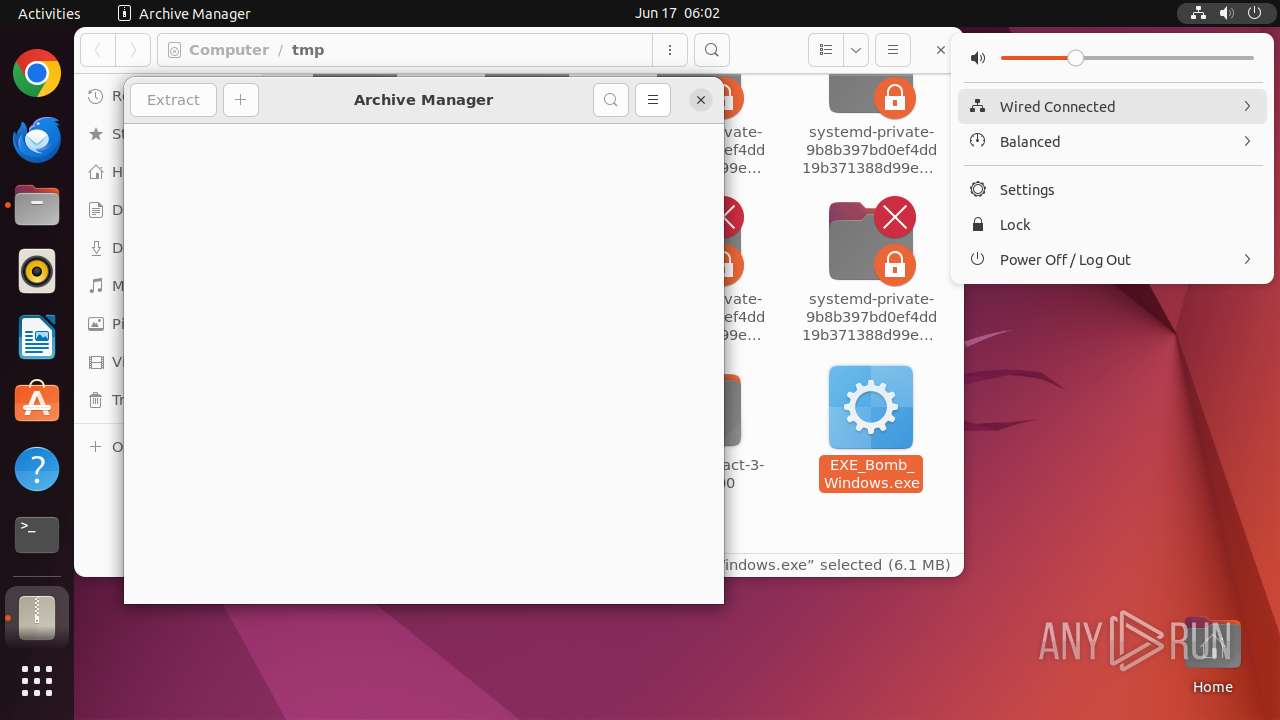
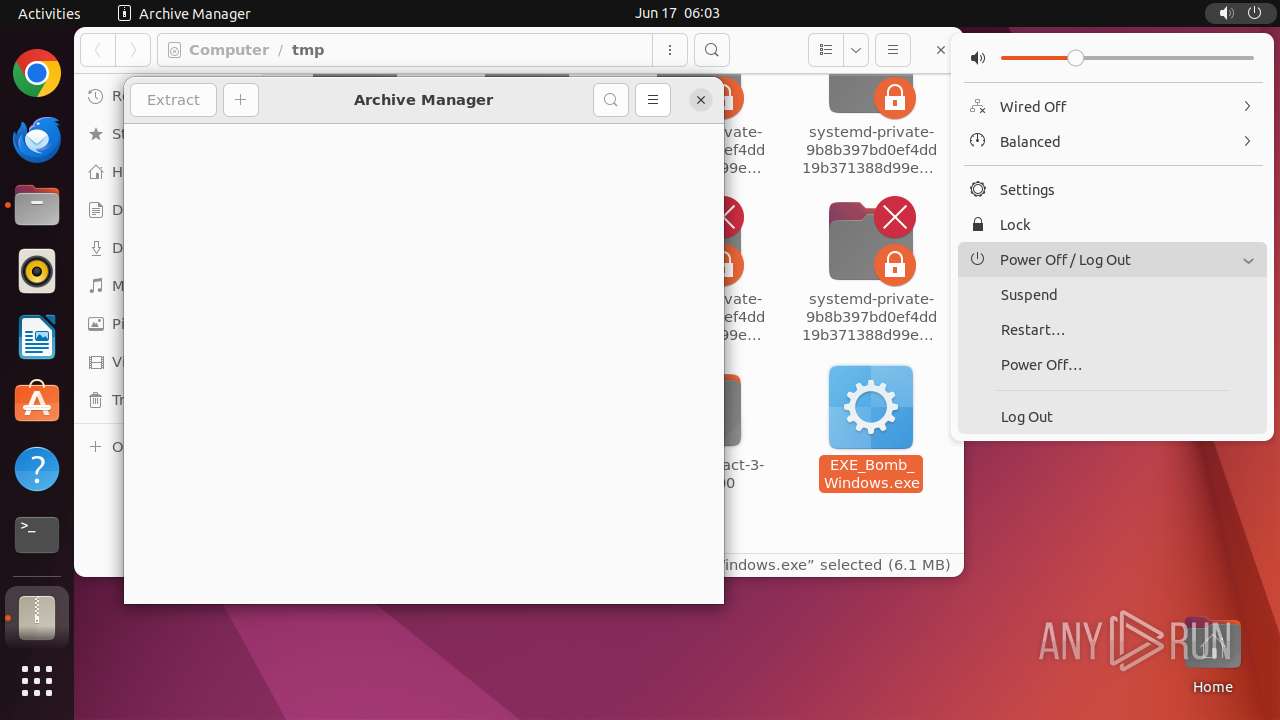
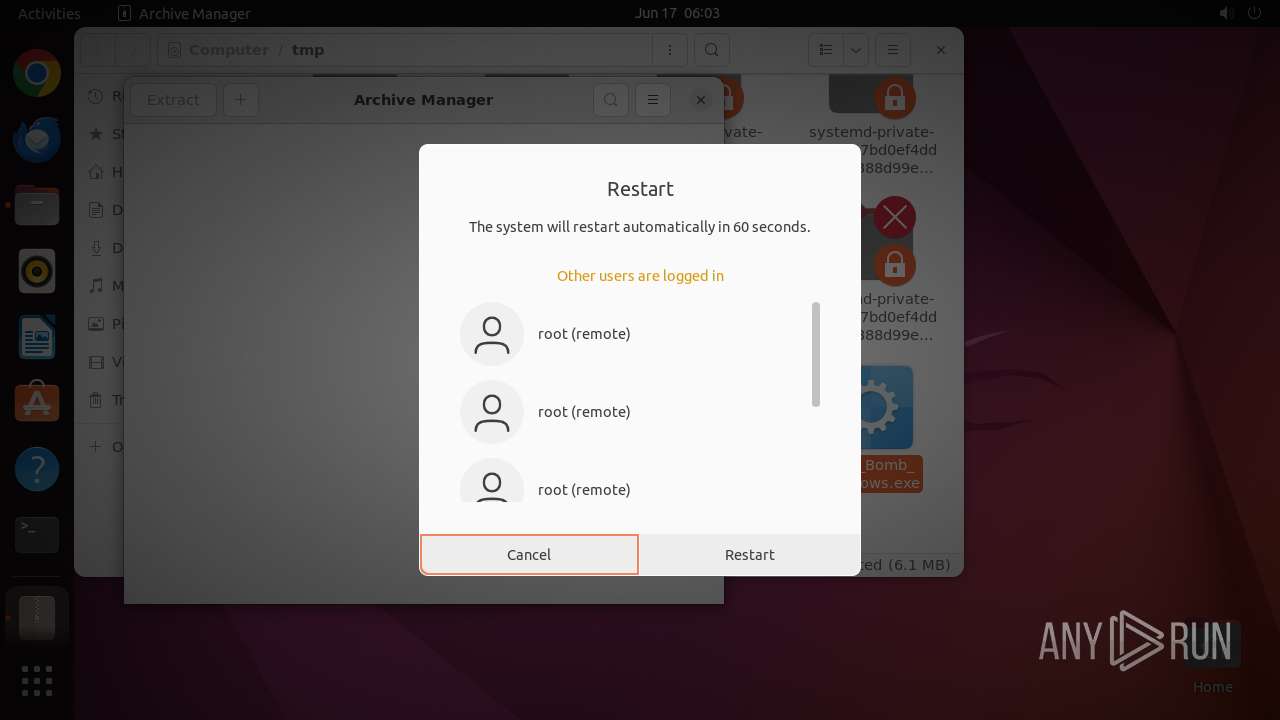
| File name: | EXE_Bomb_Windows.exe |
| Full analysis: | https://app.any.run/tasks/5057c487-e0dd-4467-a243-9ea28c044e04 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2024, 05:02:29 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 321A25C61BB513862F8FFFB5DB7A4489 |
| SHA1: | F7A1949EBCD01C1CE4175A32CCD1E1DAE9E5811B |
| SHA256: | A3E48CF8947F839D542B4AE3B735D204266B143F1D586B1318367BF3CF7F7FC5 |
| SSDEEP: | 98304:4StJF80nVgIYHcz8Z3NaeNQarak9Sz4yEtZxrSxdG2i+6Y0YTShZMPeZznZXgD5r:RTLKZUbmIaD |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 12953)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2020:01:05 12:15:46+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 134656 |
| InitializedDataSize: | 259584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8ef8 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | SebastianEPH |
| FileDescription: | [Virus troyano, (Fines educativos)] |
| FileVersion: | 1.0 (win7sp1_rtm.101119-1850) |
| InternalName: | EXEBombWindows |
| LegalCopyright: | SebastianEPH©. |
| OriginalFileName: | EXE_Bomb_Windows.exe |
| ProductName: | EXE Bomb Windows® |
| ProductVersion: | 1 |
Total processes
237
Monitored processes
24
Malicious processes
0
Suspicious processes
0
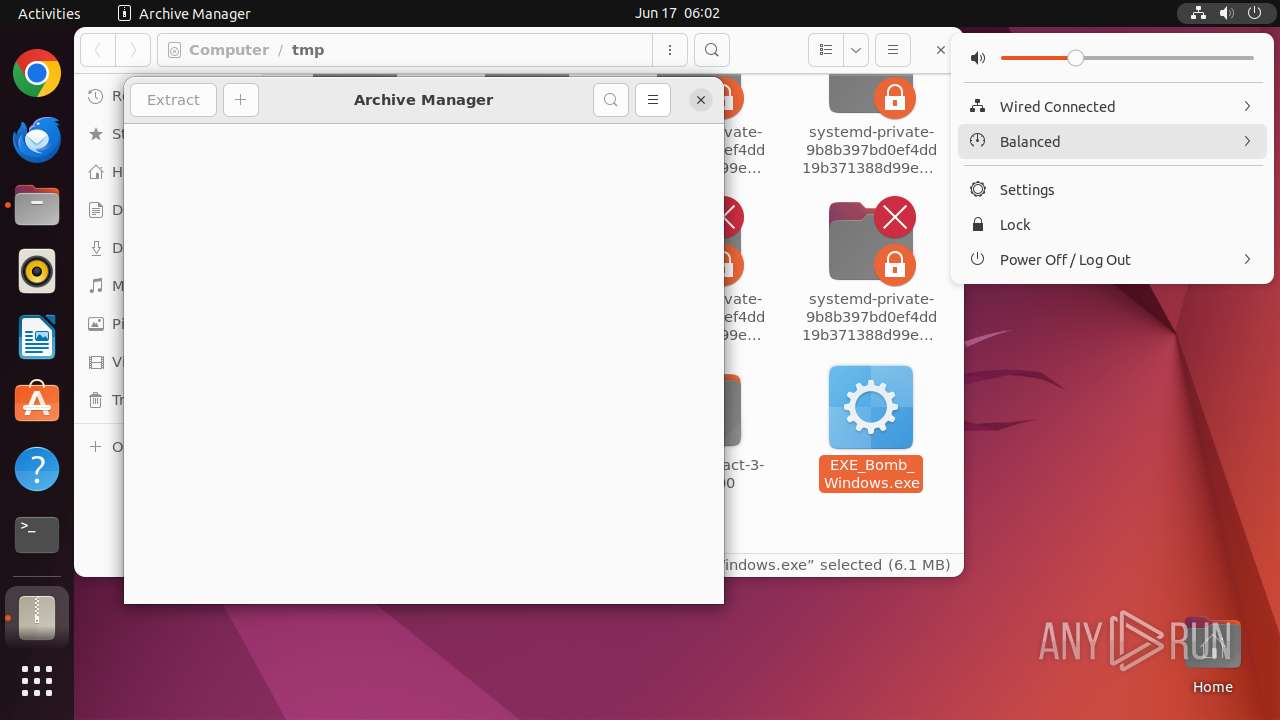
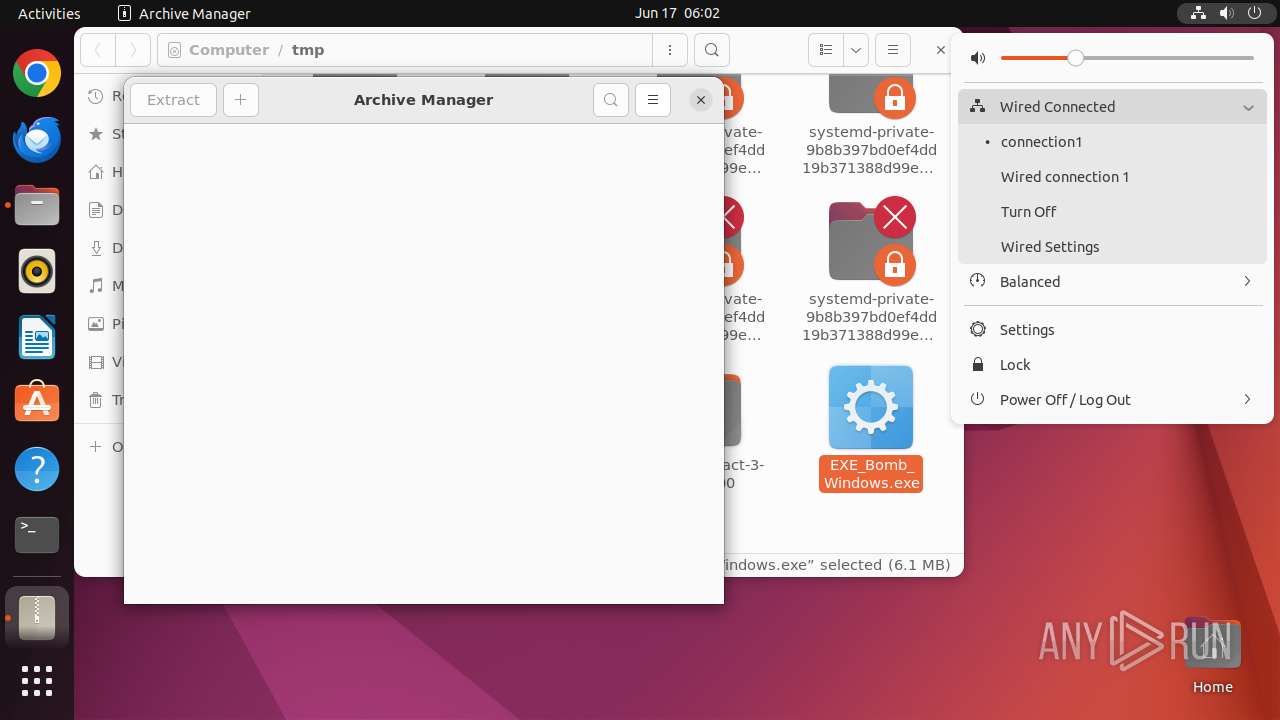
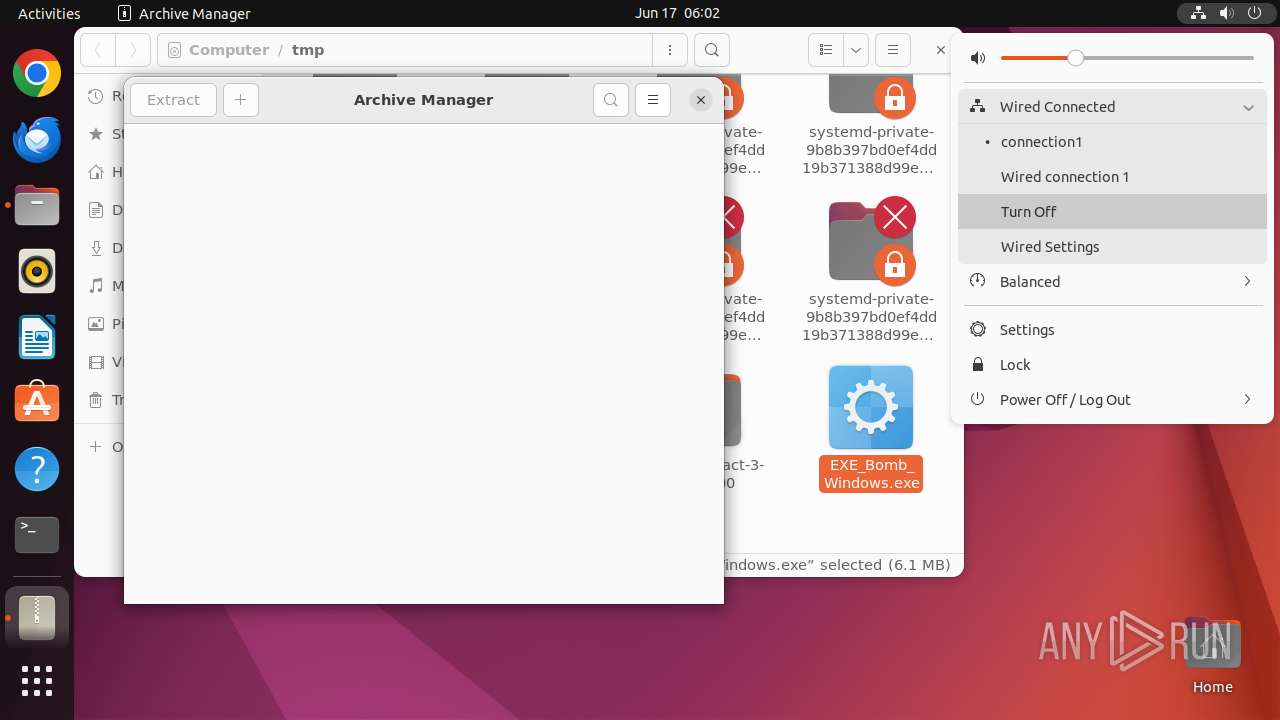
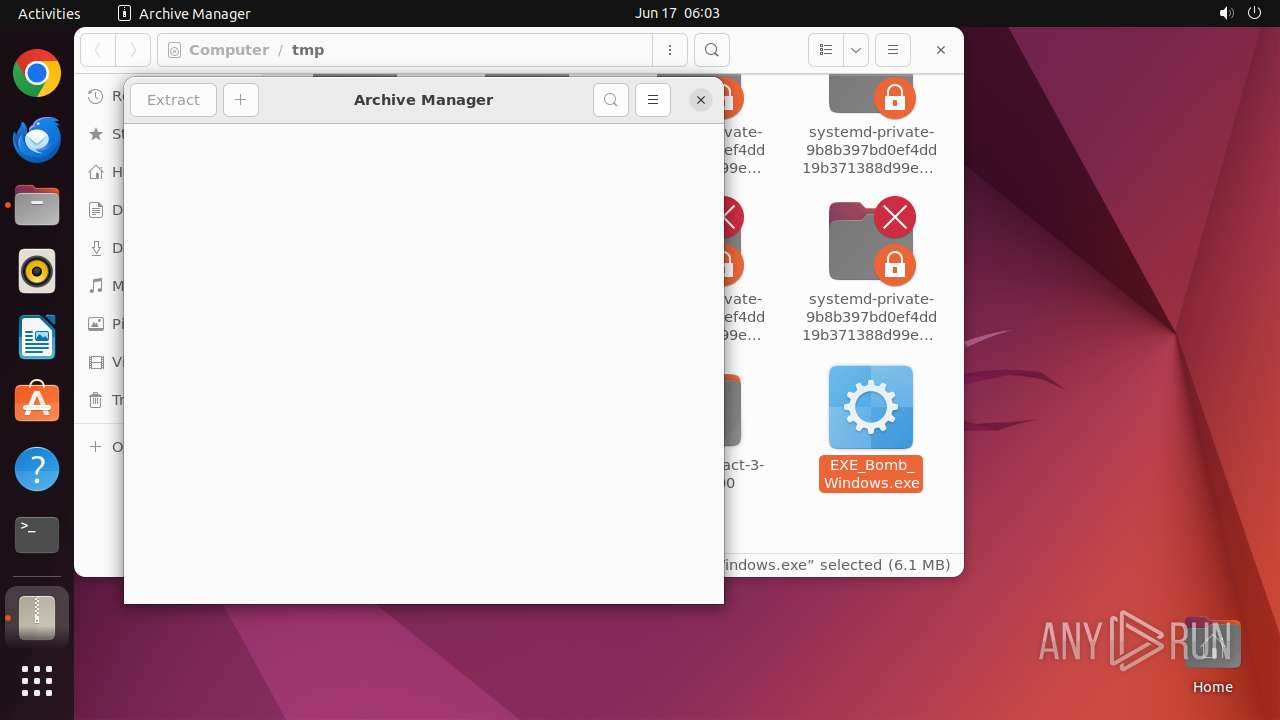
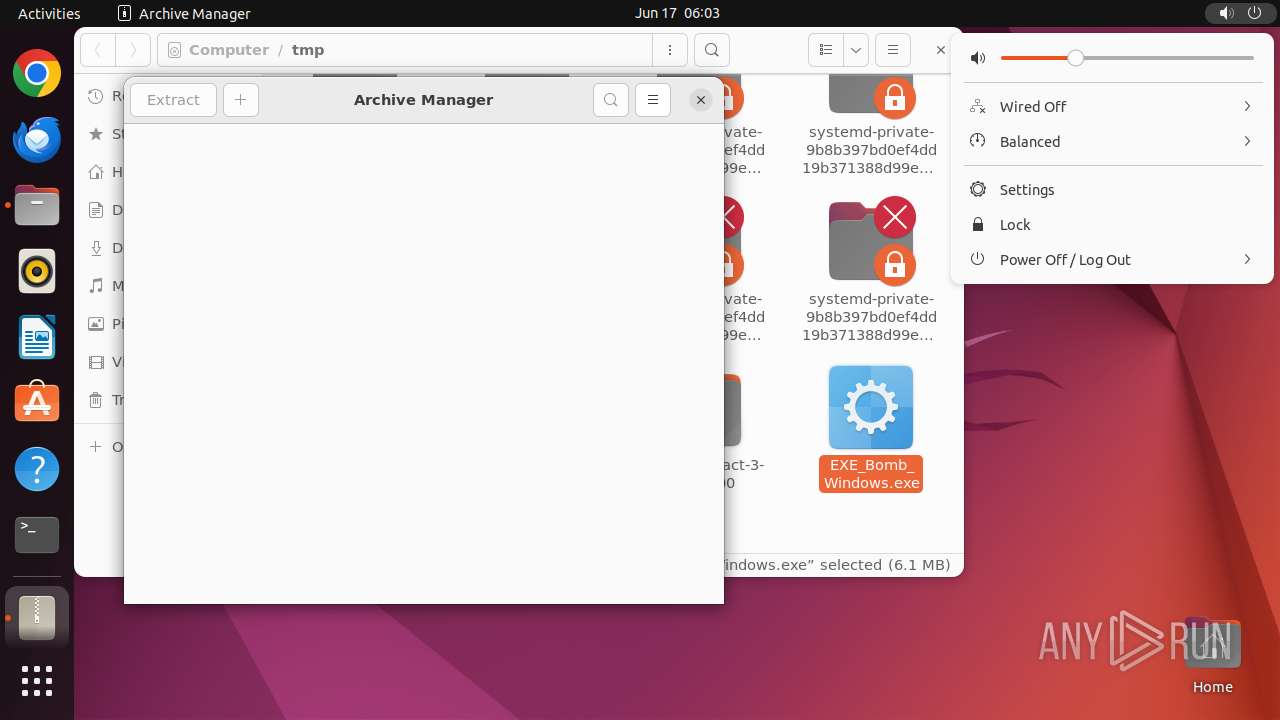
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12931 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12932 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12933 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12934 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12935 | sh -c "file --mime-type /tmp/EXE_Bomb_Windows\.exe" | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12936 | file --mime-type /tmp/EXE_Bomb_Windows.exe | /usr/bin/file | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
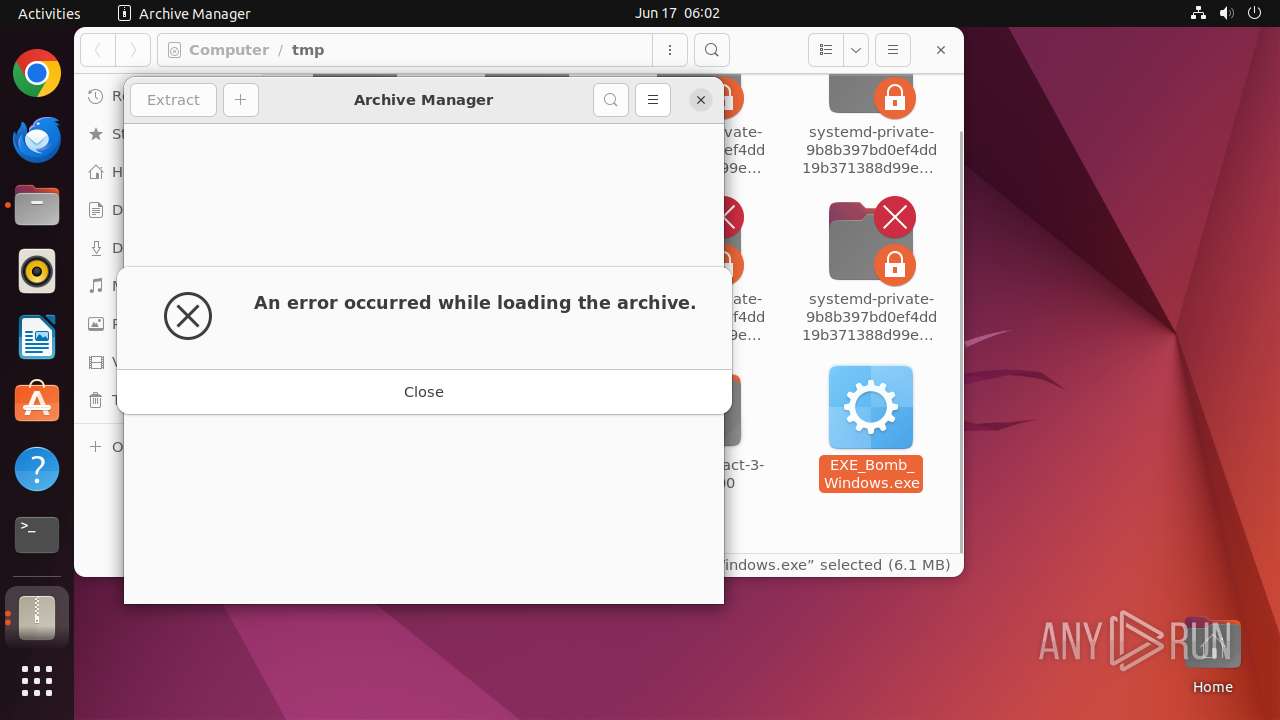
| 12937 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /tmp/EXE_Bomb_Windows\.exe " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 12938 | sudo -iu user nautilus /tmp/EXE_Bomb_Windows.exe | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 12939 | nautilus /tmp/EXE_Bomb_Windows.exe | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 12940 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12939 | nautilus | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 12965 | file-roller | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
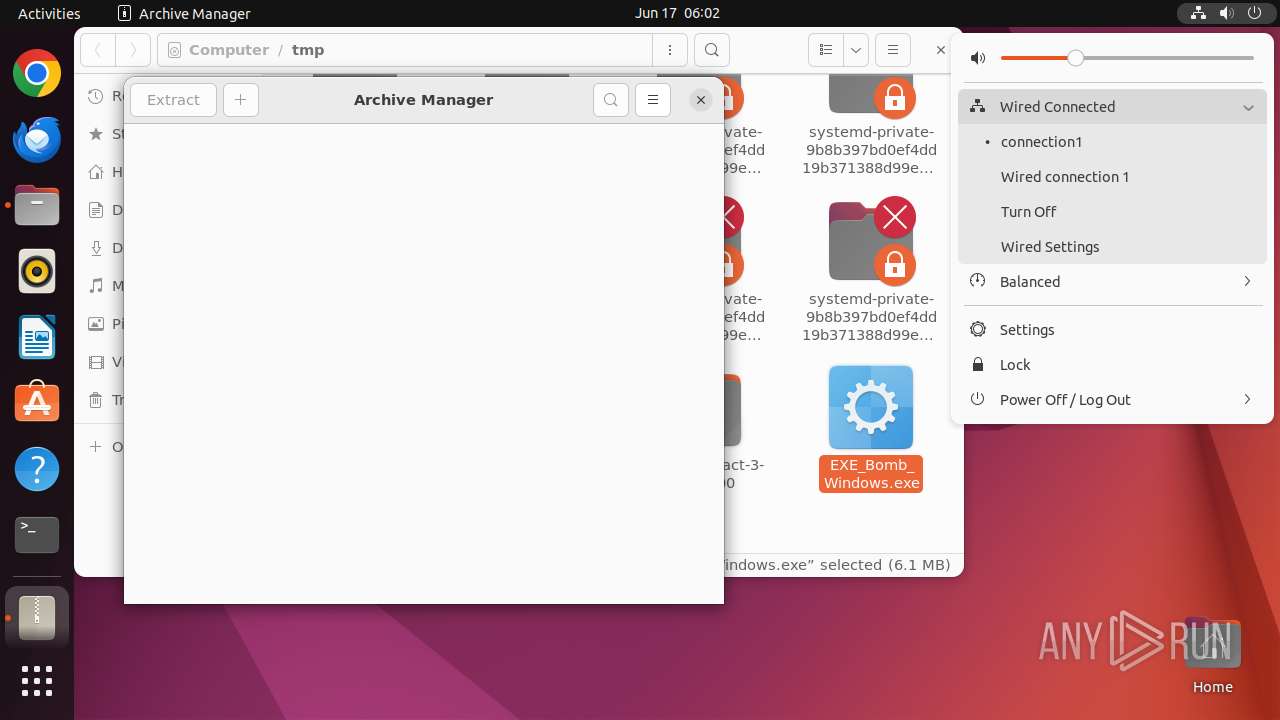
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 195.181.170.18:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
473 | NetworkManager | 91.189.91.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| unknown |
api.snapcraft.io |
| unknown |
59.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
dashboard.snapcraft.io |
| unknown |
appstream.ubuntu.com |
| unknown |