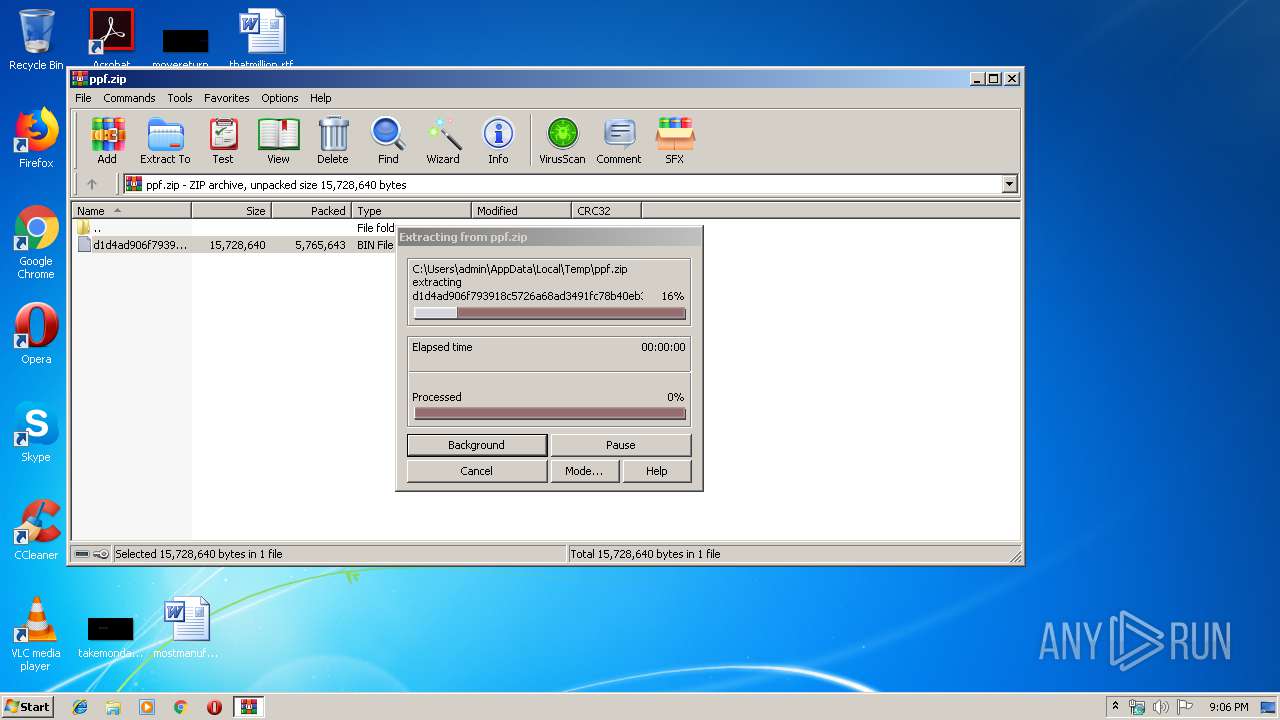
| File name: | ppf.zip |
| Full analysis: | https://app.any.run/tasks/7b5a788e-e6f3-4d4e-9c00-500e12a43284 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2019, 21:06:01 |
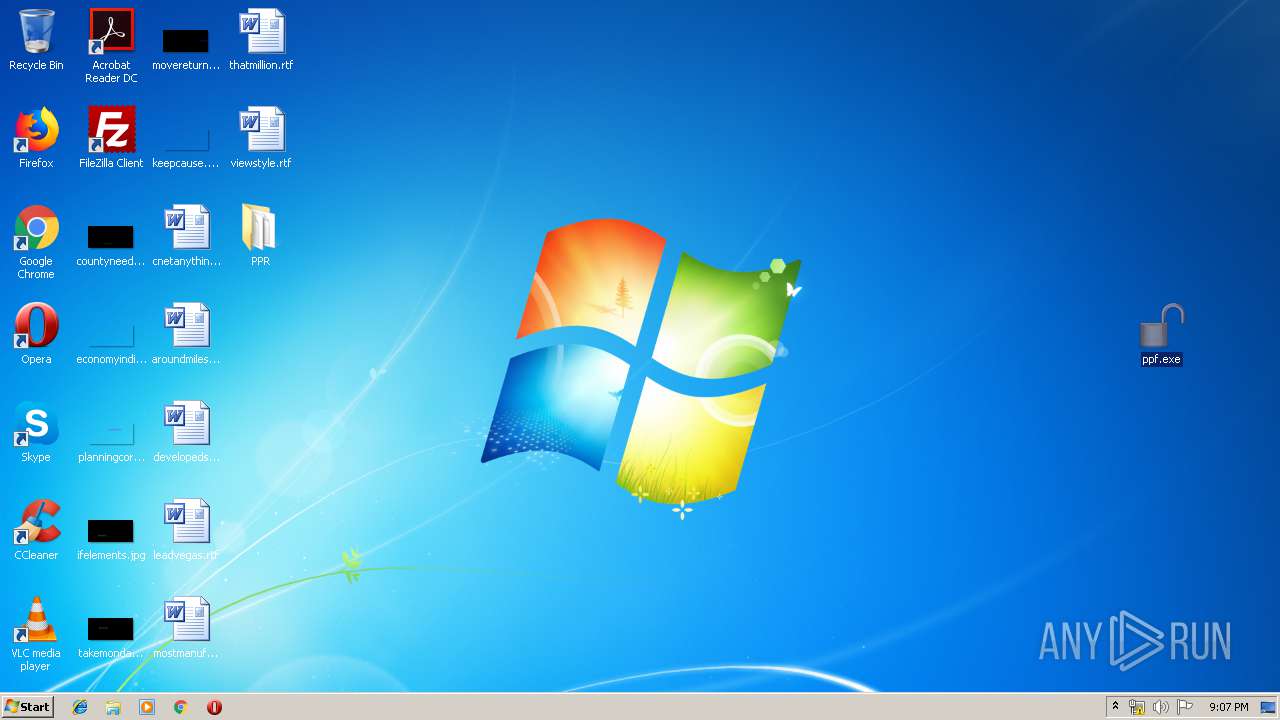
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A2F8B5582B0947CBBC45903796A8C790 |
| SHA1: | EE7F91BD71DAB924DDA8C733105DE8F5791FDA11 |
| SHA256: | A3E2ECDFBAED4D39DFABF6C6BB5085CA013D4355F7495C8BF28BD120AC4B61C2 |
| SSDEEP: | 98304:t87KHz7JUAKokGn8qTskytcBF+4HJX9RB9Ork0zdoJc/i7Yn/T2F/:t84P+ezkcz77Az+JcaQT2x |
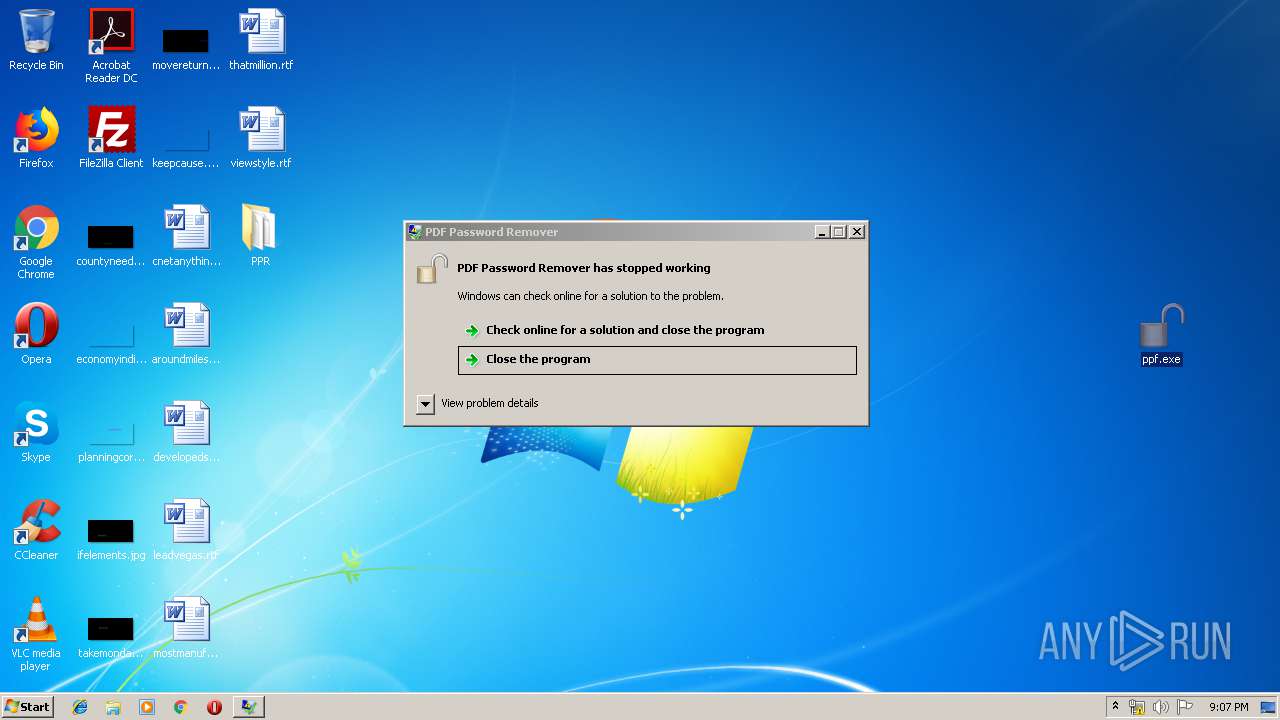
MALICIOUS
Application was dropped or rewritten from another process
- ppf.exe (PID: 2532)
- ppf.exe (PID: 1012)
- QualityAgent.exe (PID: 1848)
- qpdf.exe (PID: 2244)
- ppf.exe (PID: 2088)
- ppf.exe (PID: 3468)
- qpdf.exe (PID: 3036)
- pdftk.exe (PID: 3240)
Loads dropped or rewritten executable
- qpdf.exe (PID: 2244)
- qpdf.exe (PID: 3036)
SUSPICIOUS
Executable content was dropped or overwritten
- ppf.exe (PID: 2532)
- qpdf.exe (PID: 2244)
- ppf.exe (PID: 2088)
Starts Internet Explorer
- ppf.exe (PID: 2088)
INFO
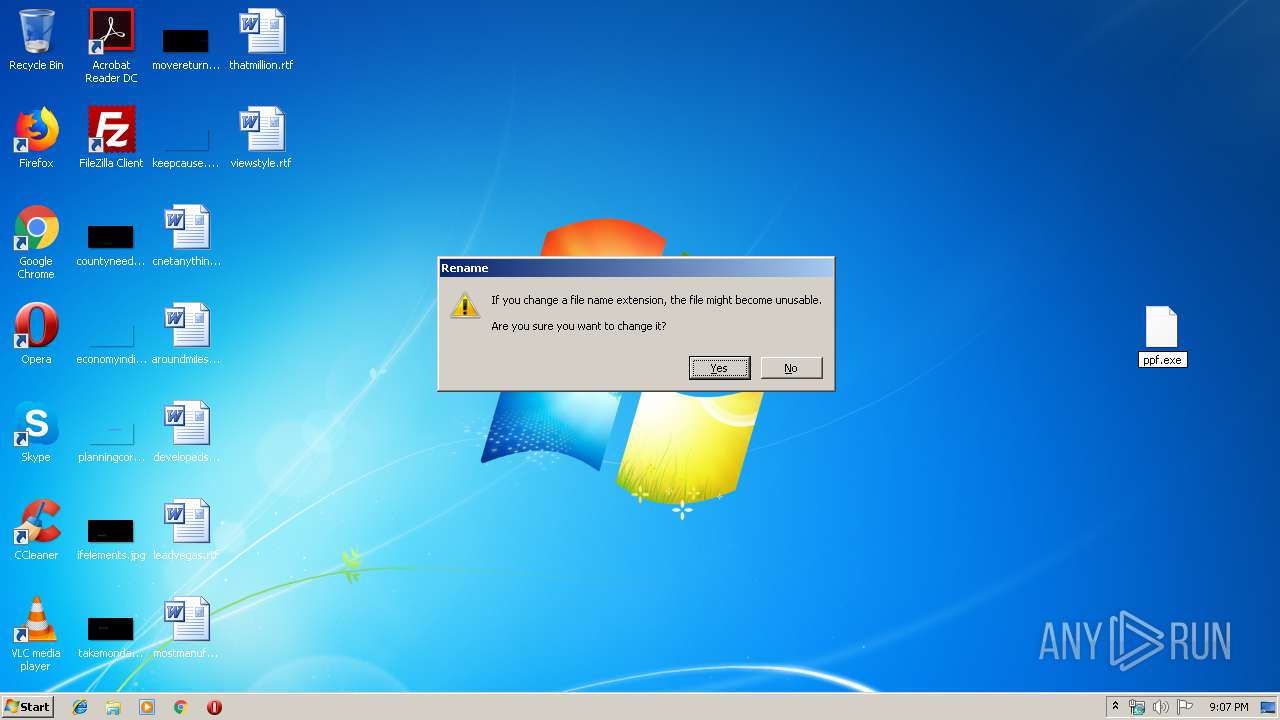
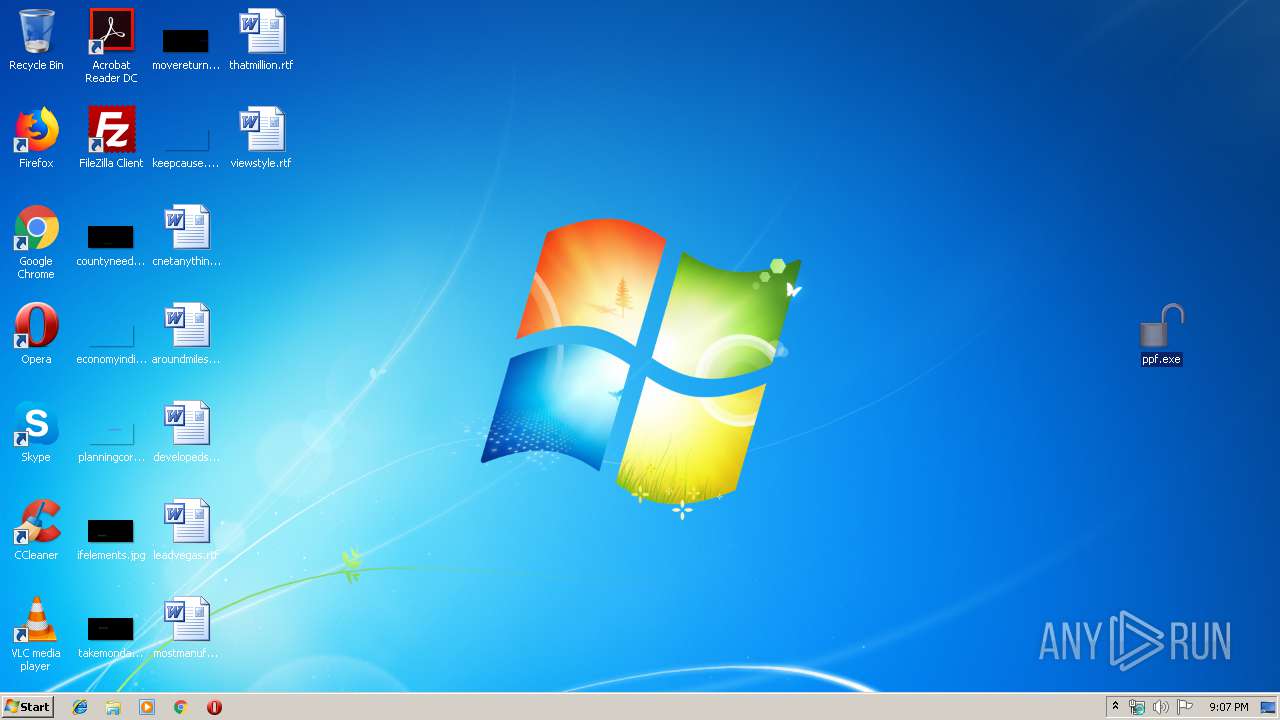
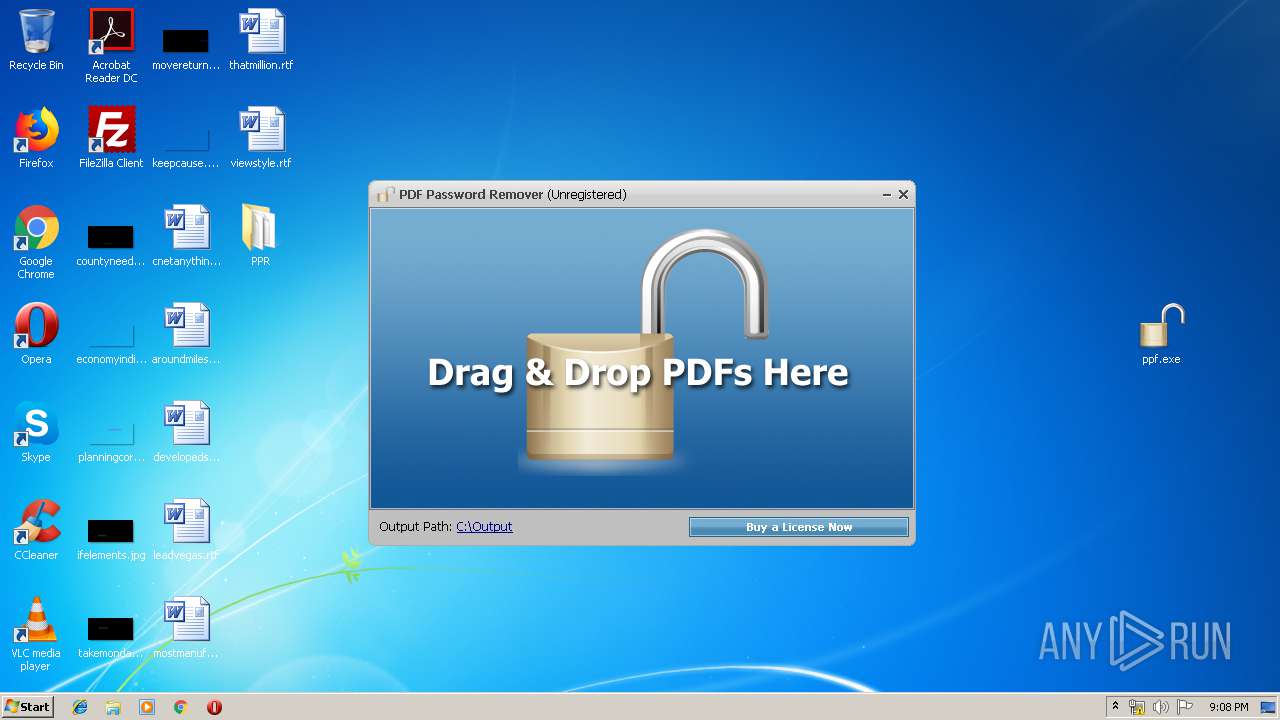
Manual execution by user
- ppf.exe (PID: 1012)
- ppf.exe (PID: 3468)
Application launched itself
- iexplore.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
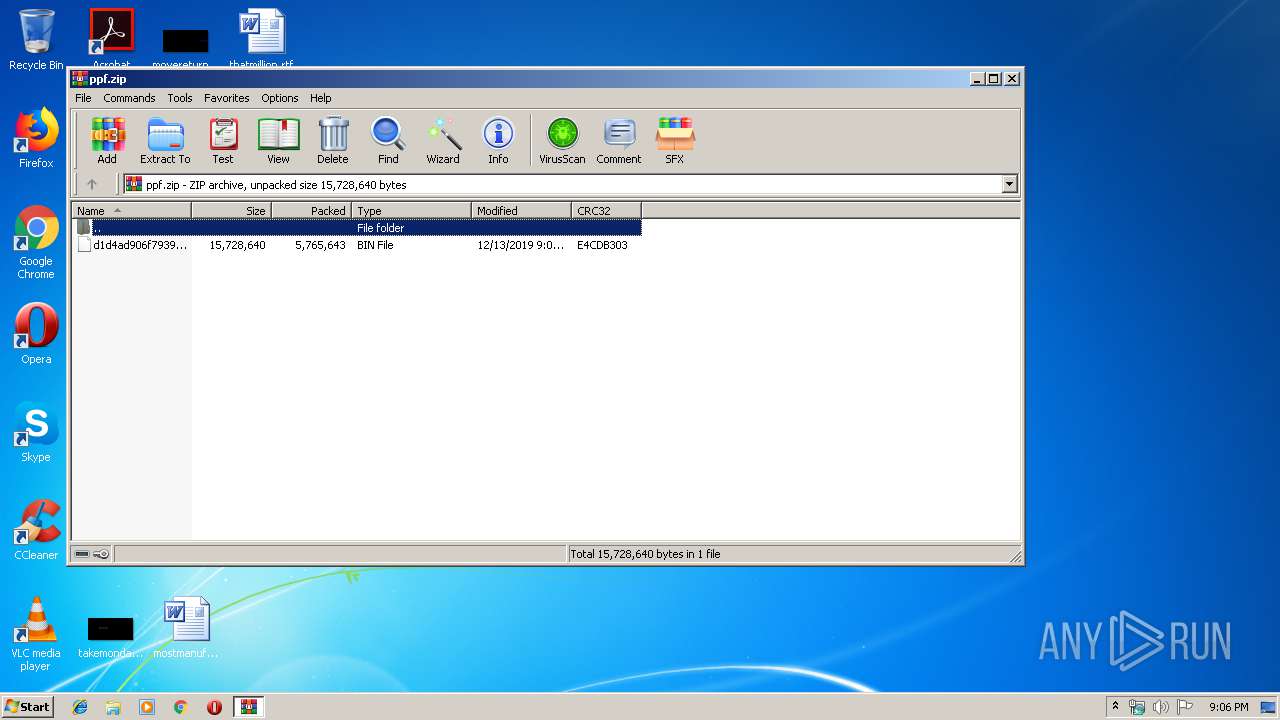
| ZipRequiredVersion: | 788 |
|---|---|
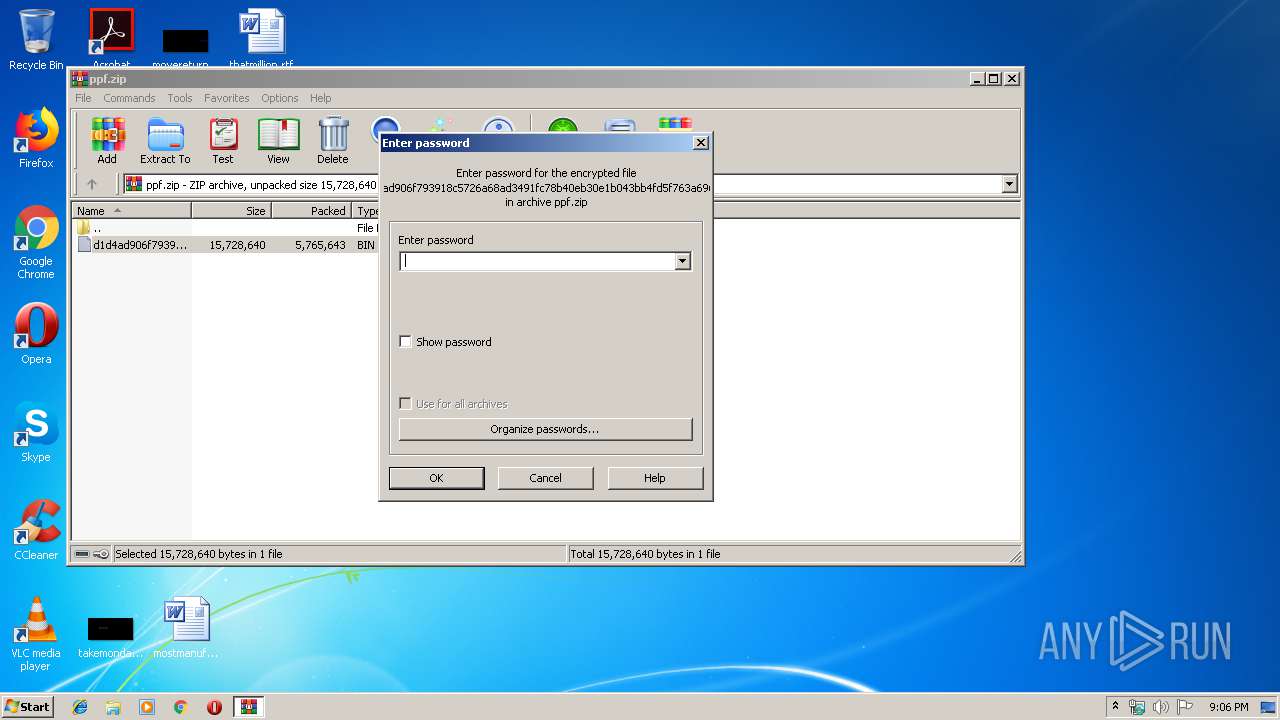
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:13 21:03:23 |
| ZipCRC: | 0xe4cdb303 |
| ZipCompressedSize: | 5765643 |
| ZipUncompressedSize: | 15728640 |
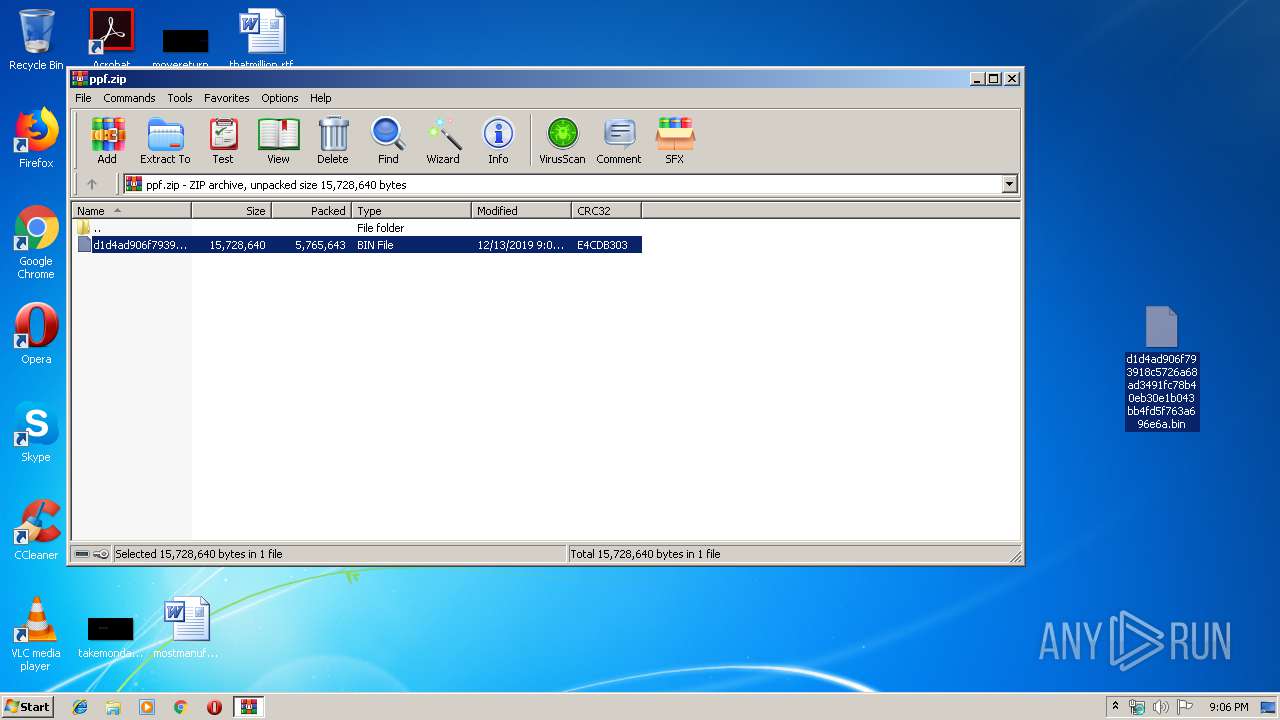
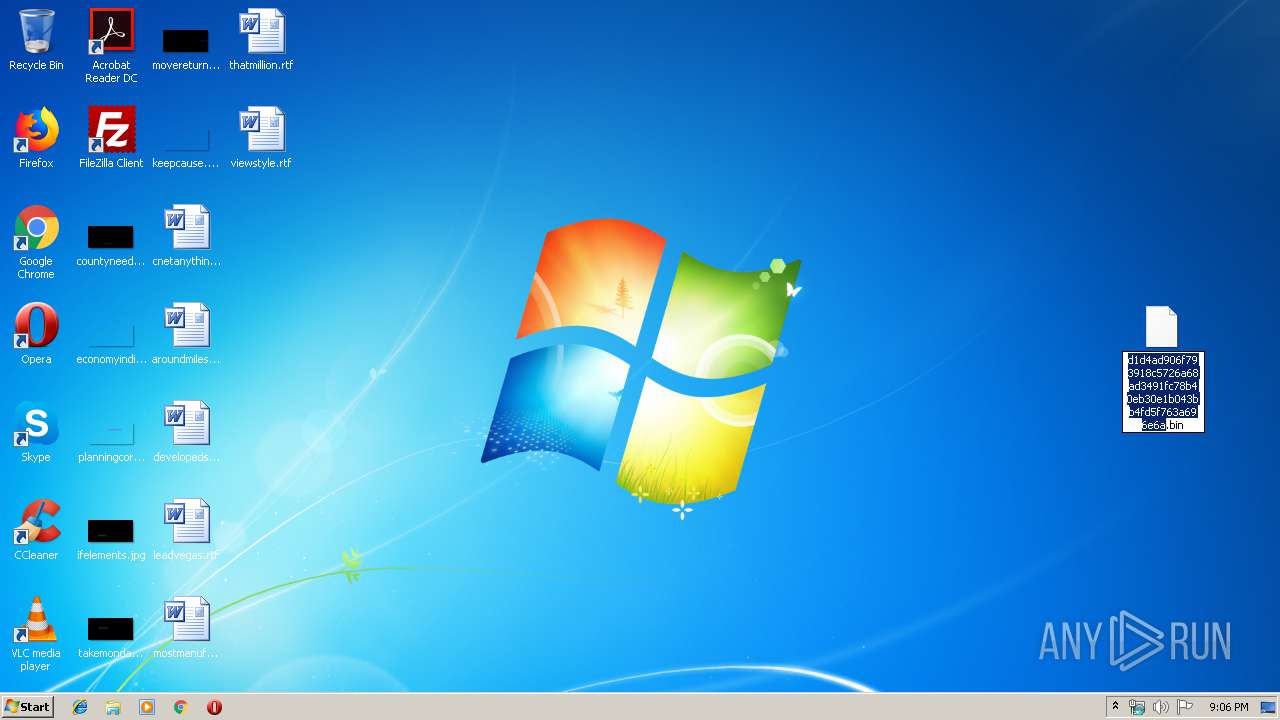
| ZipFileName: | d1d4ad906f793918c5726a68ad3491fc78b40eb30e1b043bb4fd5f763a696e6a.bin |
Total processes
58
Monitored processes
13
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
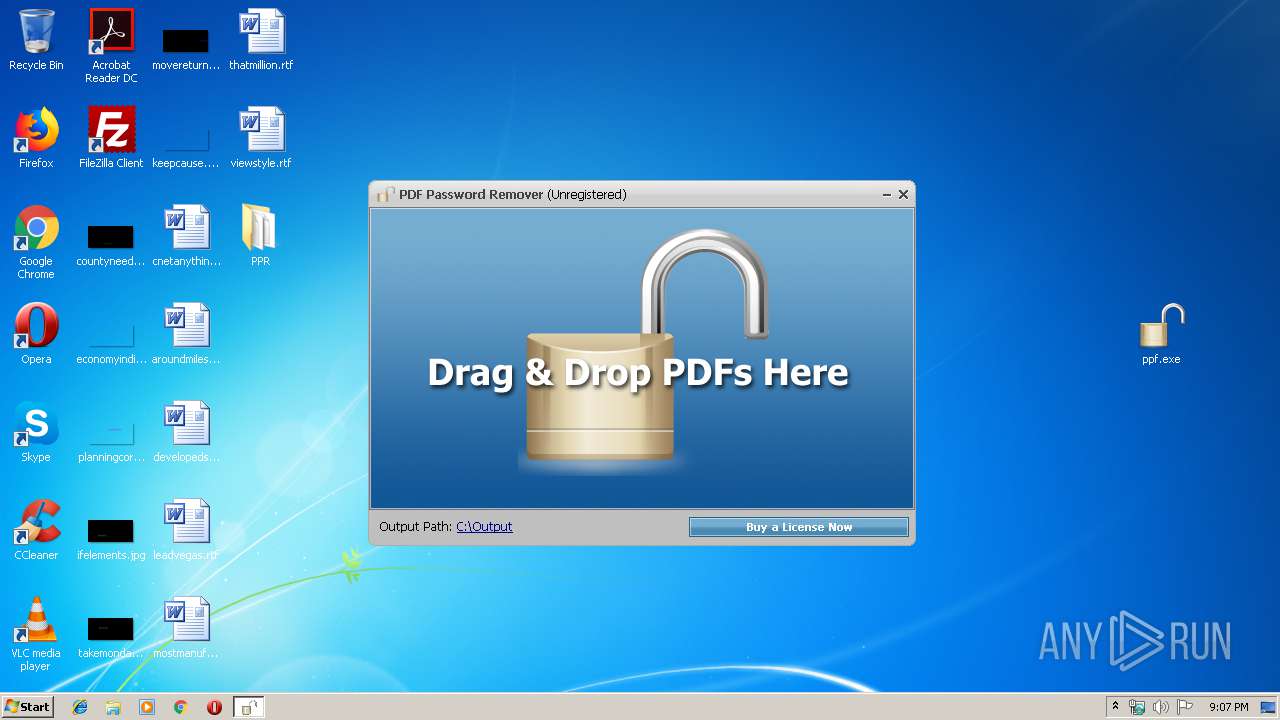
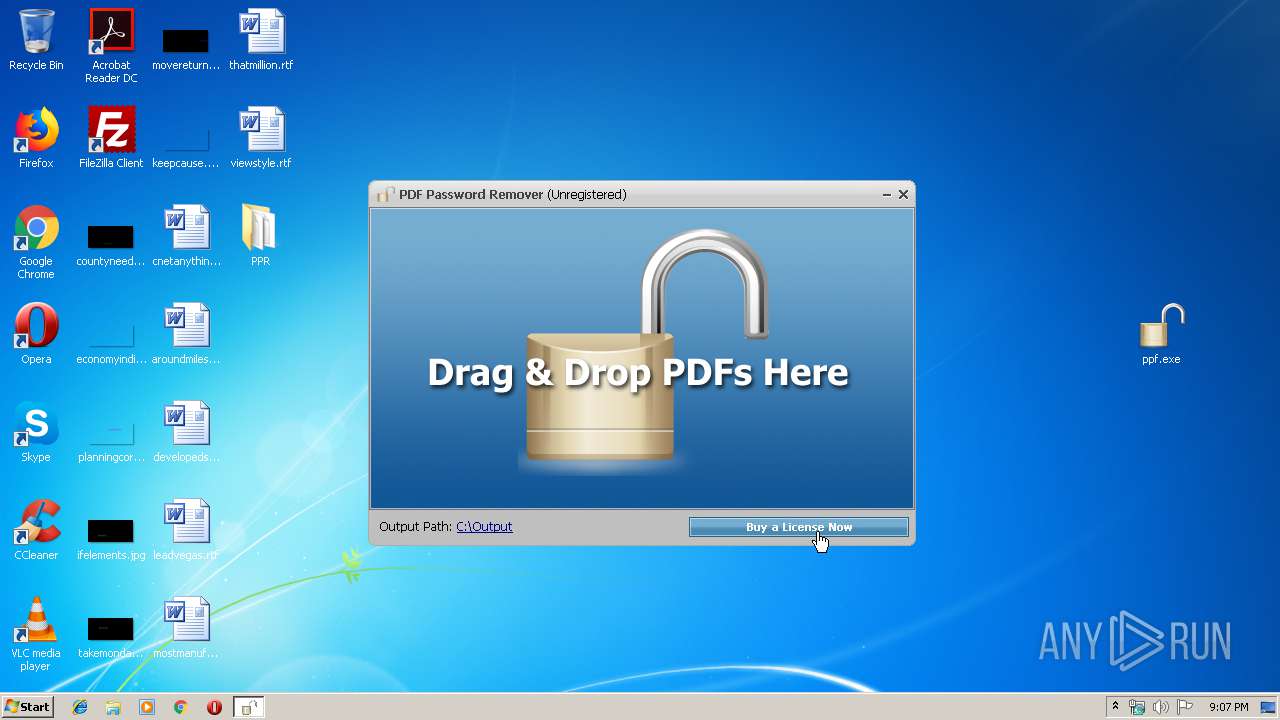
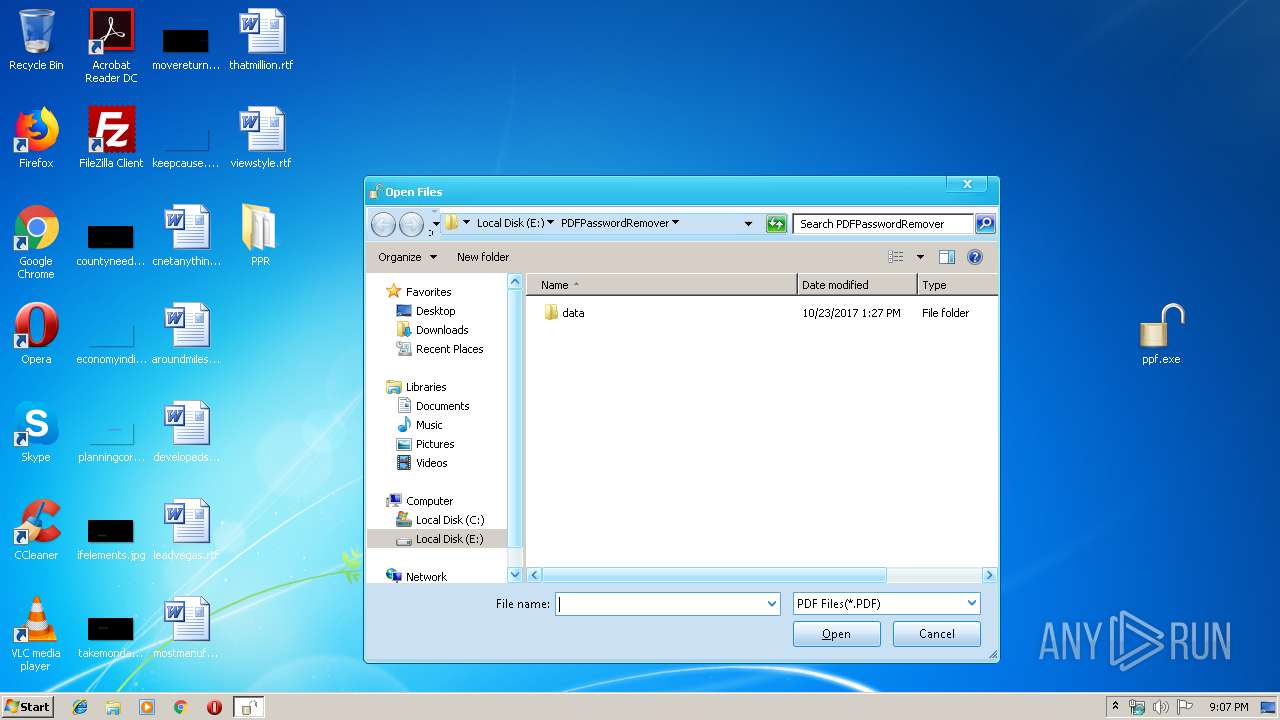
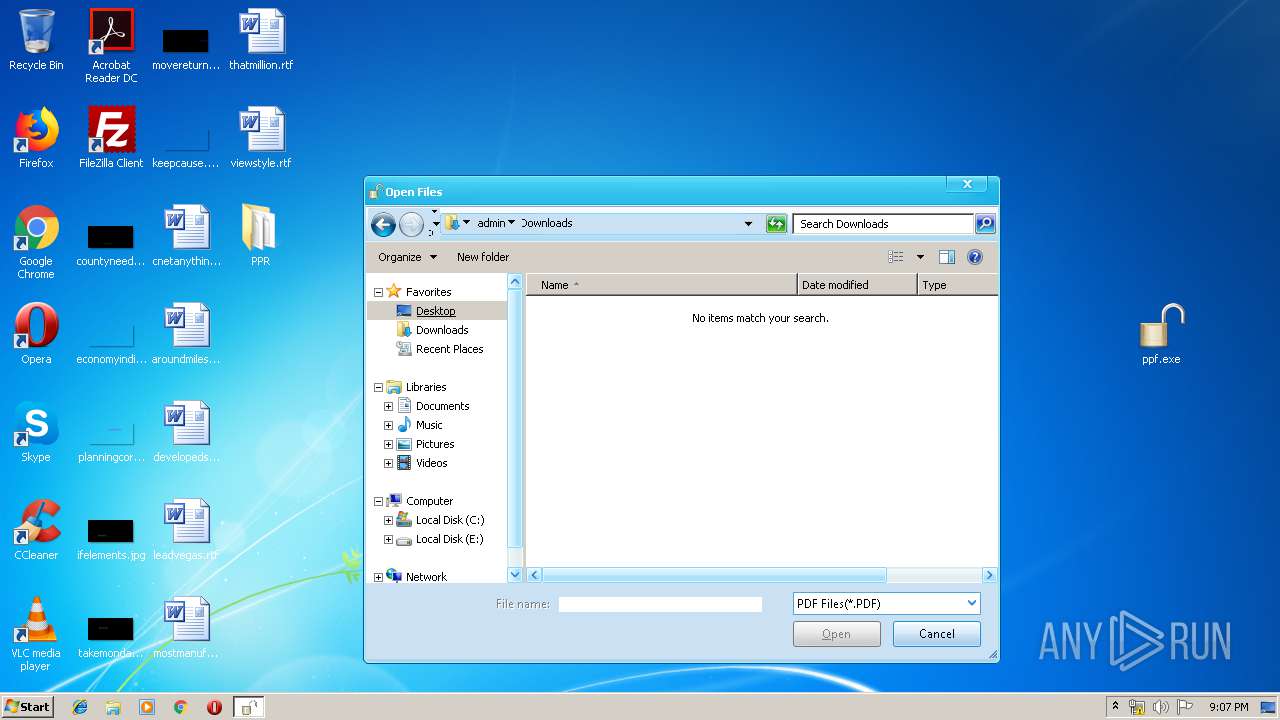
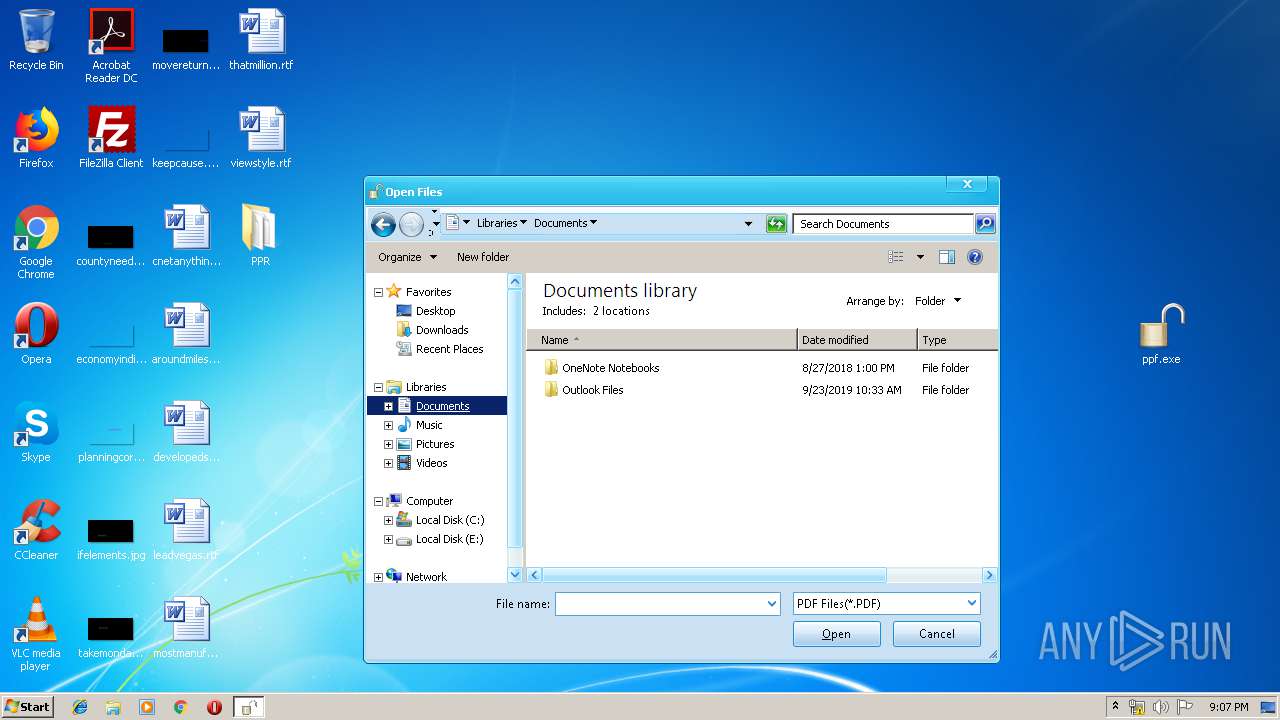
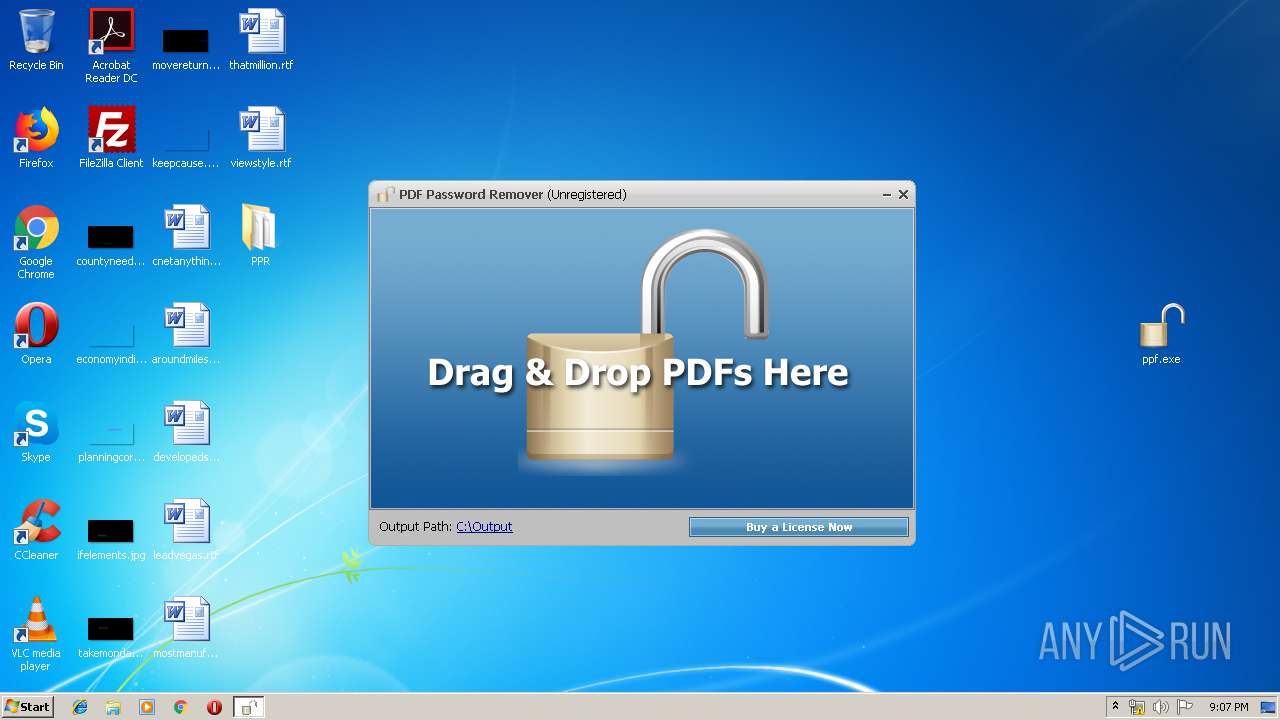
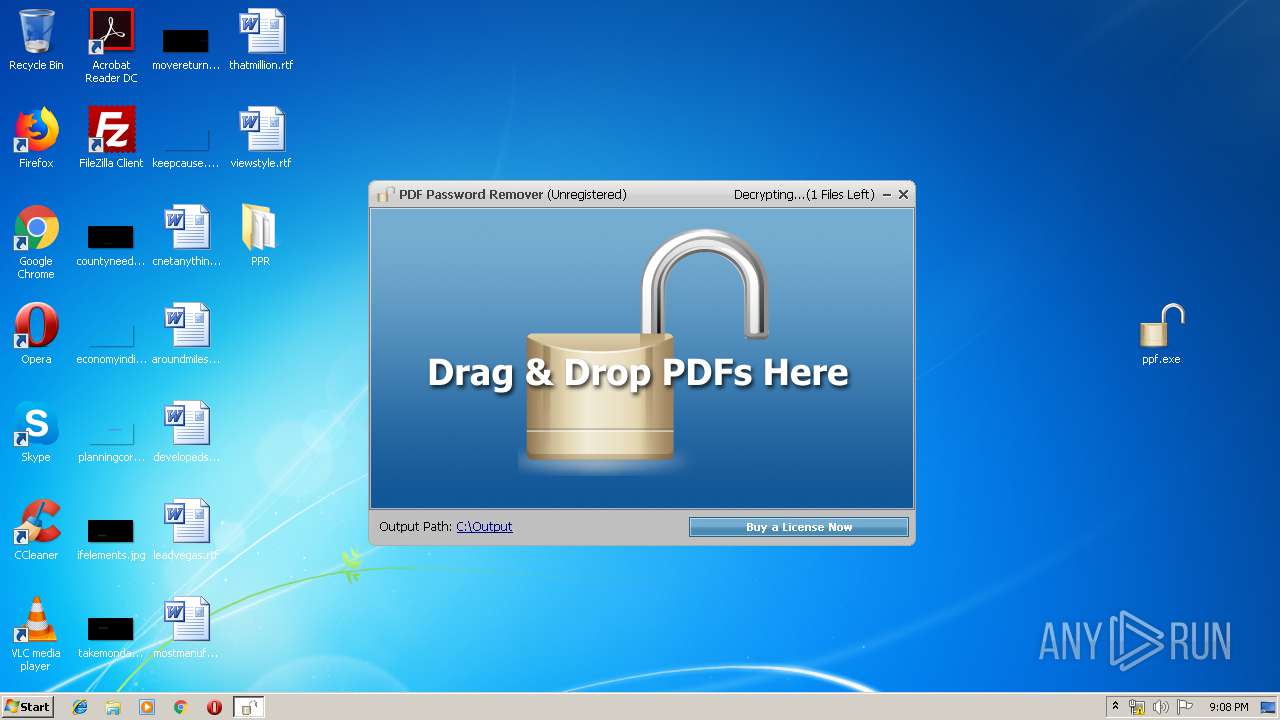
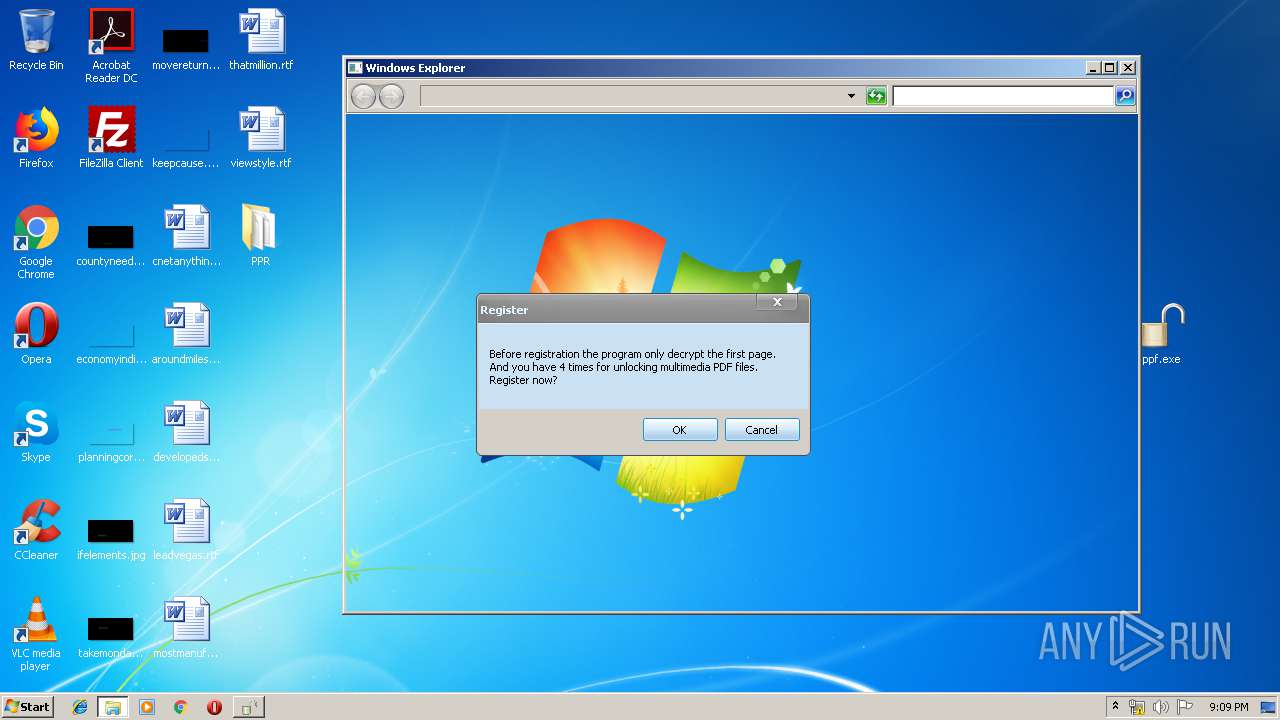
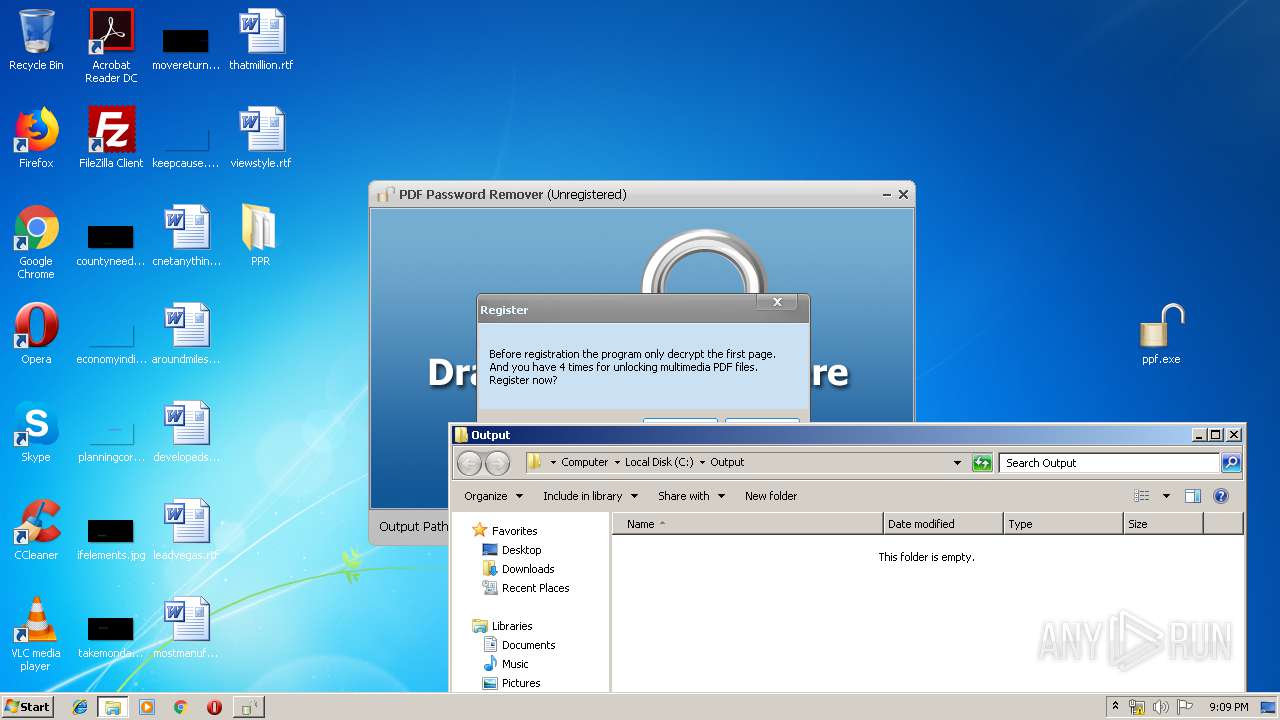
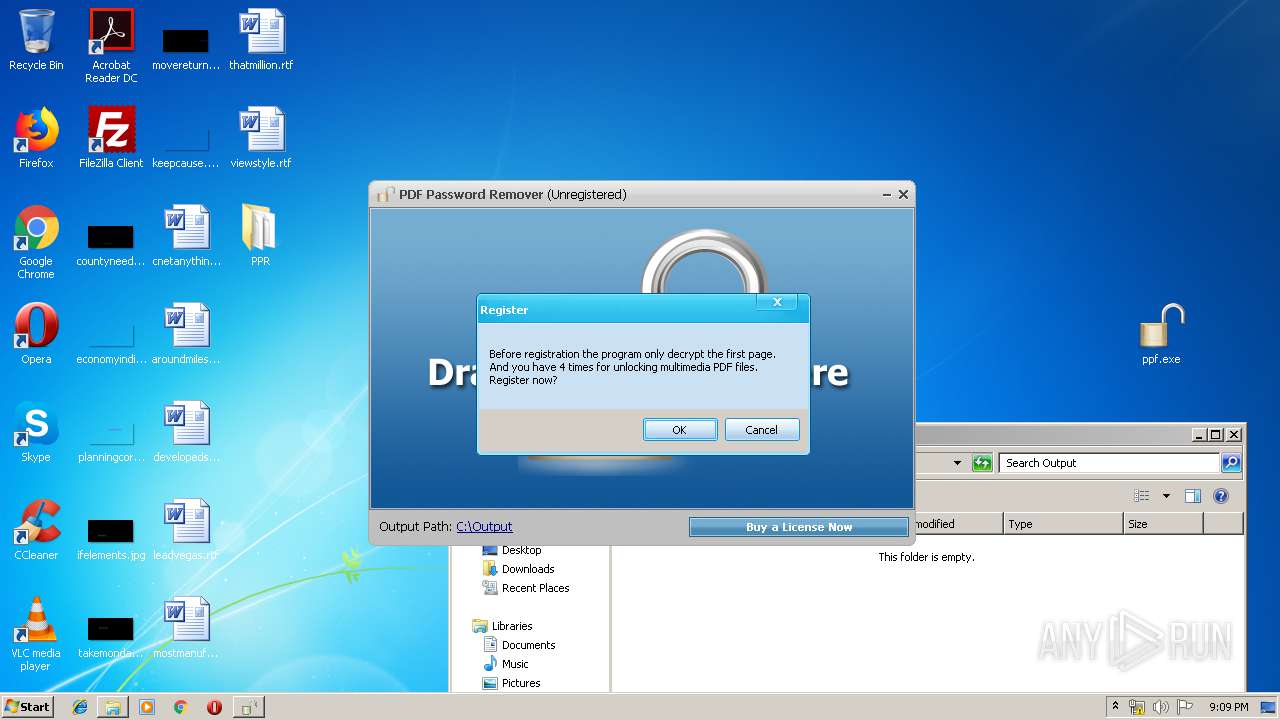
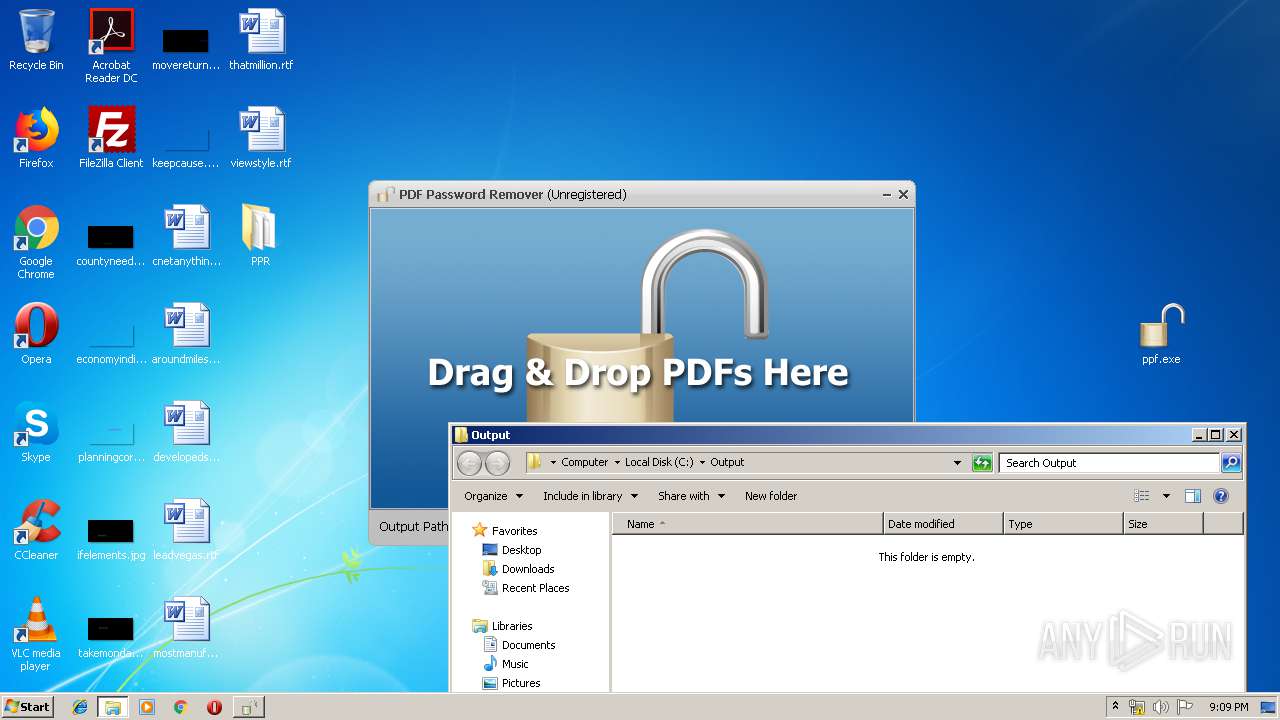
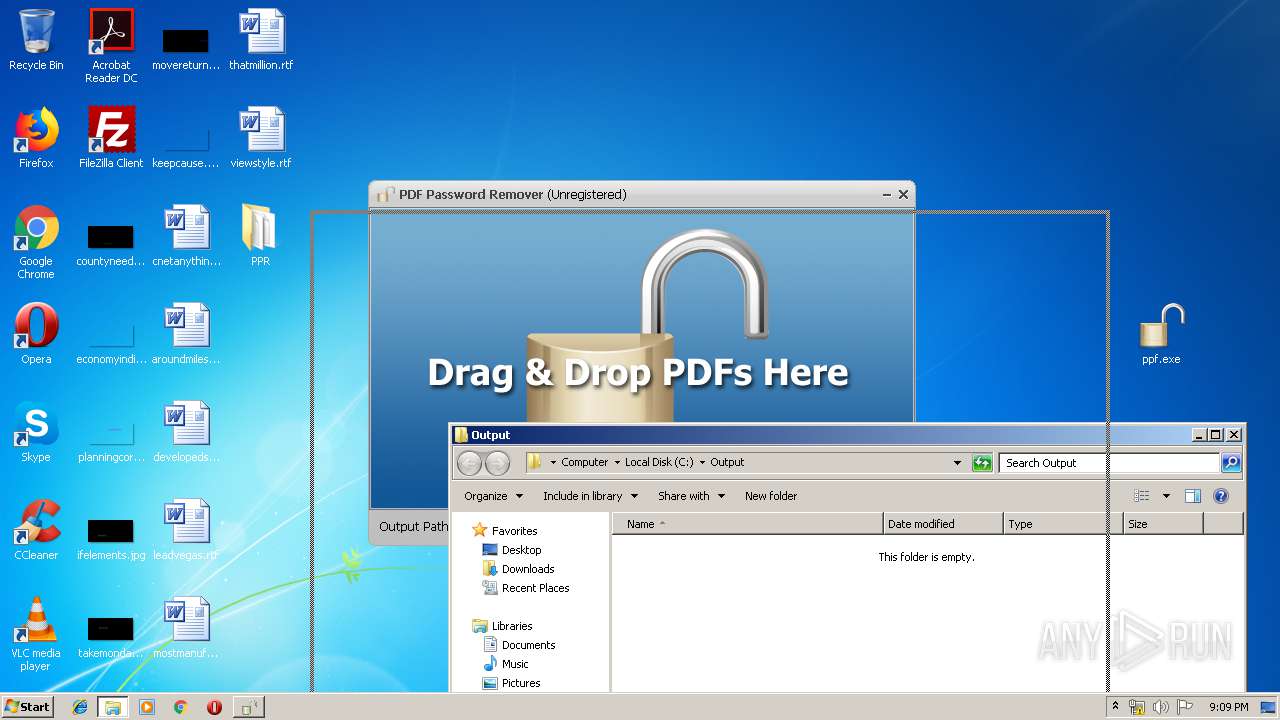
| 1012 | "C:\Users\admin\Desktop\ppf.exe" | C:\Users\admin\Desktop\ppf.exe | explorer.exe | ||||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 0 Version: 7.01 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3600 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1848 | "C:\Program Files\ThinstallPlugins\QualityAgent.exe" -Report "PPR" "C:\Users\admin\Desktop" | C:\Users\admin\Desktop\PPR\SKEL\be99b4bfd6b4adcef5fd621abd076ceec9f6e51b\QualityAgent.exe | ppf.exe | ||||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 0 Version: 7.01 Modules
| |||||||||||||||
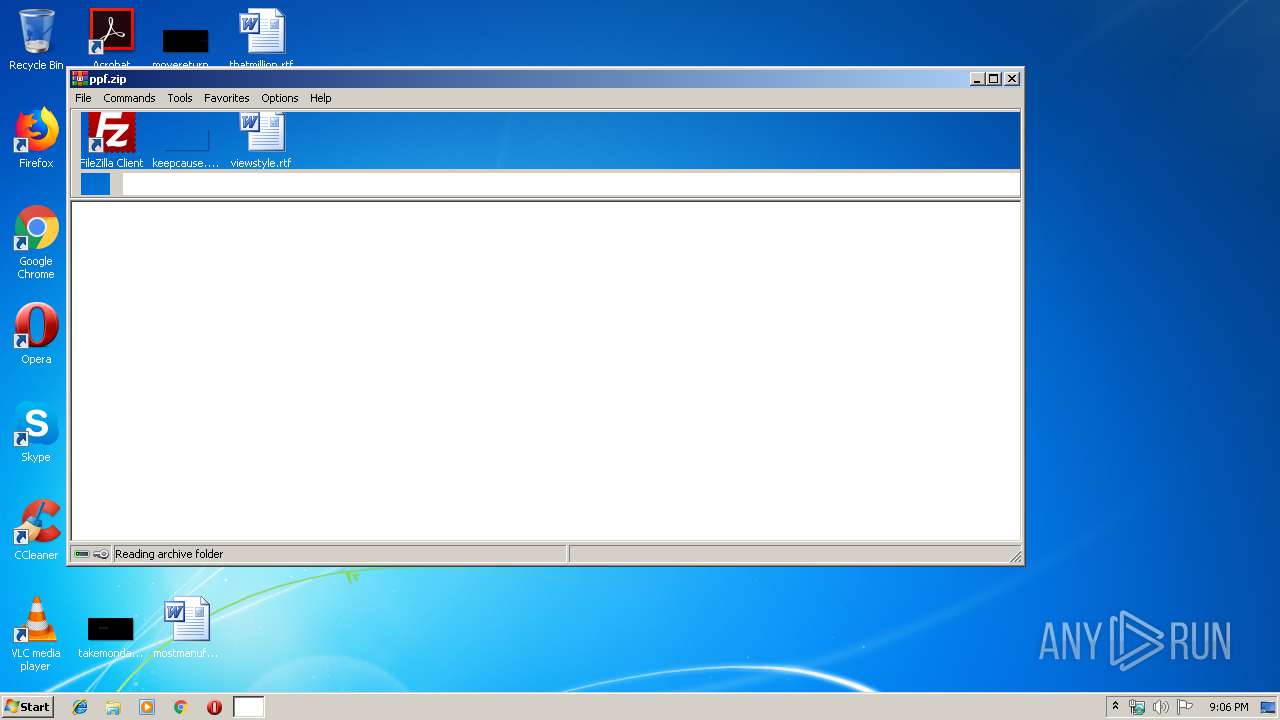
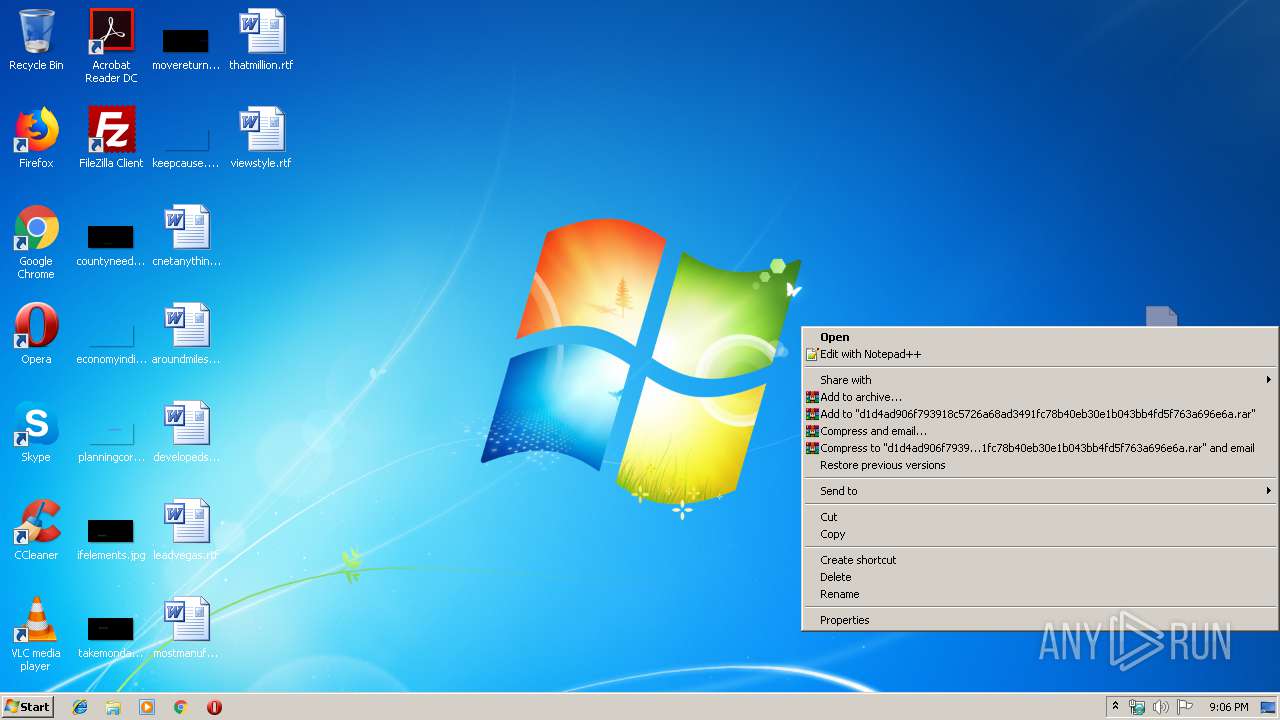
| 1928 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ppf.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
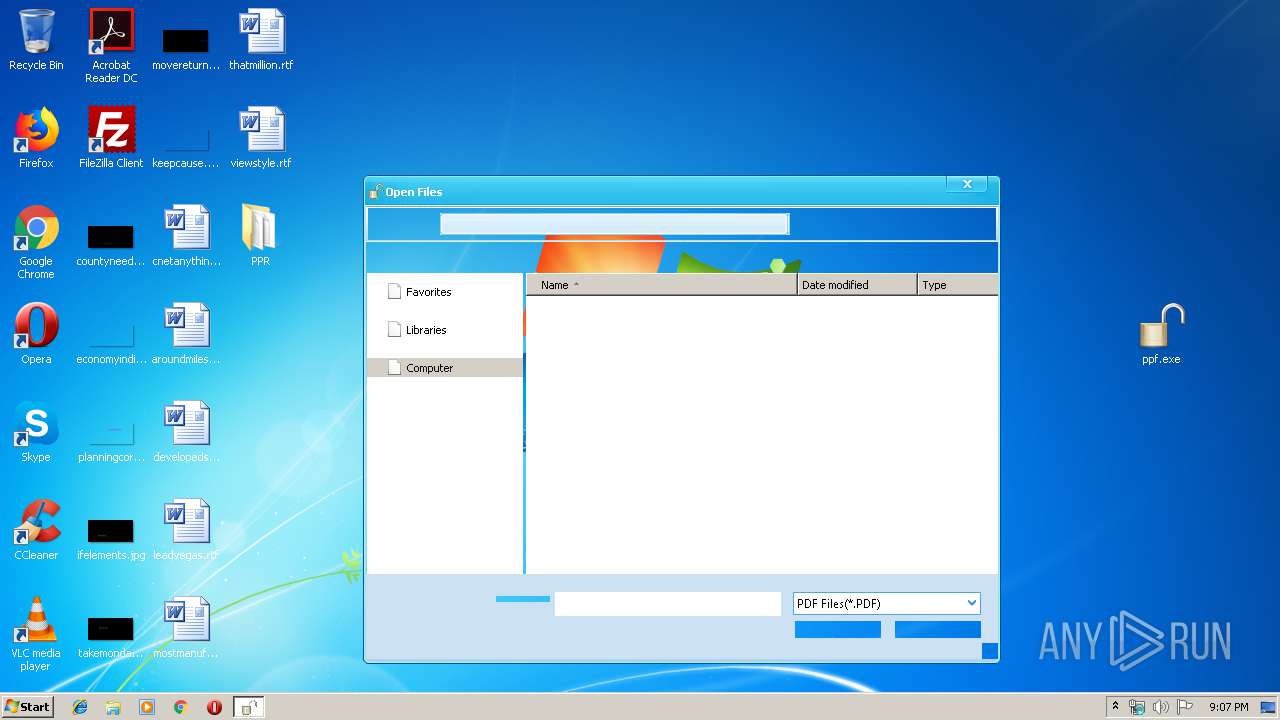
| 2088 | "E:\PDFPasswordRemover\PPR.exe" C:\Users\admin\Desktop\developedsent.rtf | C:\Users\admin\Desktop\ppf.exe | ppf.exe | ||||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 0 Version: 7.01 Modules
| |||||||||||||||
| 2244 | E:\PDFPasswordRemover\data\qpdf.exe --decrypt c:\tmpremove\prepare.tmp c:\tmpremove\1_tmp.tmp | C:\Users\admin\Desktop\PPR\SKEL\be99b4bfd6b4adcef5fd621abd076ceec9f6e51b\qpdf.exe | ppf.exe | ||||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 2 Version: 7.01 Modules
| |||||||||||||||
| 2532 | "E:\PDFPasswordRemover\PPR.exe" | C:\Users\admin\Desktop\ppf.exe | ppf.exe | ||||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 3221225477 Version: 7.01 Modules
| |||||||||||||||
| 3036 | E:\PDFPasswordRemover\data\qpdf.exe --password=1234 --decrypt c:\tmpremove\prepare.tmp c:\tmpremove\1_tmp.tmp | C:\Users\admin\Desktop\PPR\SKEL\be99b4bfd6b4adcef5fd621abd076ceec9f6e51b\qpdf.exe | — | ppf.exe | |||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 2 Version: 7.01 Modules
| |||||||||||||||
| 3240 | E:\PDFPasswordRemover\data\pdftk.exe c:\tmpremove\1_tmp.tmp cat 1 output c:\tmpremove\2_tmp.tmp | C:\Users\admin\Desktop\PPR\SKEL\be99b4bfd6b4adcef5fd621abd076ceec9f6e51b\pdftk.exe | — | ppf.exe | |||||||||||
User: admin Company: PDF Password Remover Integrity Level: MEDIUM Description: PDF Password Remover Exit code: 1 Version: 7.01 Modules
| |||||||||||||||
Total events
439
Read events
419
Write events
20
Delete events
0
Modification events
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ppf.zip | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1928) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
7
Suspicious files
12
Text files
18
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1928 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1928.21068\d1d4ad906f793918c5726a68ad3491fc78b40eb30e1b043bb4fd5f763a696e6a.bin | — | |
MD5:— | SHA256:— | |||
| 1012 | ppf.exe | C:\Users\admin\Desktop\PPR\Registry.rw.tvr.lck.USER-PC.ffffffff.6fc | — | |
MD5:— | SHA256:— | |||
| 2532 | ppf.exe | C:\Users\admin\Desktop\PPR\SKEL\be99b4bfd6b4adcef5fd621abd076ceec9f6e51b\QualityAgent.exe.900.9e4 | — | |
MD5:— | SHA256:— | |||
| 2532 | ppf.exe | C:\Users\admin\AppData\Local\Temp\~DF8C7DE2288677DD4F.TMP | — | |
MD5:— | SHA256:— | |||
| 3468 | ppf.exe | C:\Users\admin\Desktop\PPR\Registry.rw.tvr.lck.USER-PC.ffffffff.7d4 | — | |
MD5:— | SHA256:— | |||
| 2088 | ppf.exe | C:\Users\admin\Desktop\PPR\SKEL\be99b4bfd6b4adcef5fd621abd076ceec9f6e51b\qpdf.exe.81c.828 | — | |
MD5:— | SHA256:— | |||
| 2244 | qpdf.exe | C:\Users\admin\Desktop\PPR\SKEL\1dc734360b91b81a4927b2bd124095eaff42872f.Tls-2244-2232.Tls | — | |
MD5:— | SHA256:— | |||
| 2244 | qpdf.exe | C:\Users\admin\Desktop\PPR\SKEL\31593646bc21d84f3ed4974742a6c91b0d13831c.Tls-2244-2232.Tls | — | |
MD5:— | SHA256:— | |||
| 2532 | ppf.exe | C:\Users\admin\Desktop\PPR\%Local AppData%\Microsoft\Windows\Explorer\thumbcache_256.db | binary | |
MD5:— | SHA256:— | |||
| 2244 | qpdf.exe | C:\Users\admin\Desktop\PPR\SKEL\0ea89f491acf0d7cbe48ed1d1ed66893ae10e464.Tls-2244-2232.Tls | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
3
Threats
0
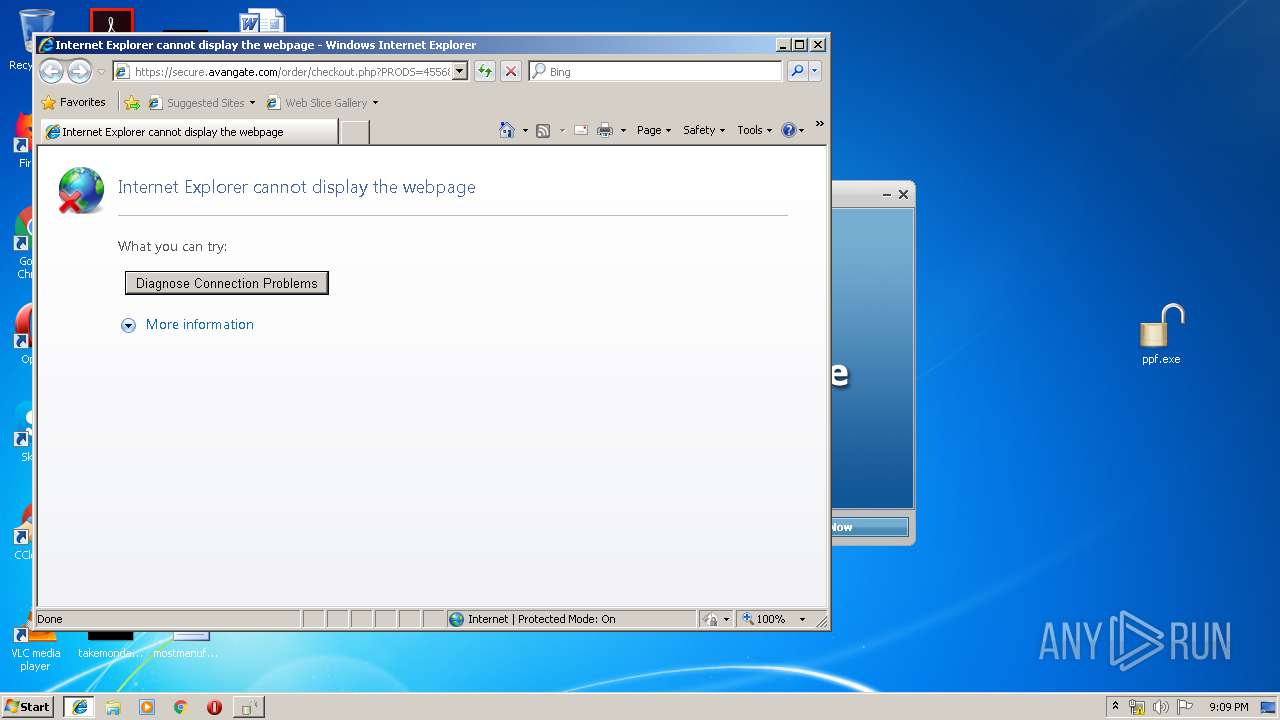
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3600 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1848 | QualityAgent.exe | 208.91.0.34:443 | thinapp-qr.vmware.com | VMWare, Inc. | US | unknown |
3600 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1212 | iexplore.exe | 45.60.14.94:443 | secure.avangate.com | Incapsula Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thinapp-qr.vmware.com |
| unknown |
www.bing.com |
| whitelisted |
secure.avangate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ppf.exe | <?dml?>#1 p=1012/3F4h t=1788/6FCh: <link cmd=".reload /f boot_loader.exe=0x66200000">Reload</link> <b>boot_loader.exe</b> 0x66200000
|
ppf.exe | <?dml?>#2 p=1012/3F4h t=1788/6FCh: Loading packaged nt0_dll.dll...
|
ppf.exe | <?dml?>#3 p=1012/3F4h t=1788/6FCh: <link cmd=".reload /f nt0_dll.dll=0x7FDD0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDD0000 packaged
|
ppf.exe | <?dml?>#1 p=1012/3F4h t=1788/6FCh: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=2532/9E4h</b>
|
ppf.exe | <?dml?>#1 p=2532/9E4h t=2304/900h: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=1848/738h</b>
|
ppf.exe | <?dml?>#1 p=3468/D8Ch t=2004/7D4h: <link cmd=".reload /f boot_loader.exe=0x66200000">Reload</link> <b>boot_loader.exe</b> 0x66200000
|
ppf.exe | <?dml?>#2 p=3468/D8Ch t=2004/7D4h: Loading packaged nt0_dll.dll...
|
ppf.exe | <?dml?>#3 p=3468/D8Ch t=2004/7D4h: <link cmd=".reload /f nt0_dll.dll=0x7FDD0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDD0000 packaged
|
ppf.exe | <?dml?>#1 p=3468/D8Ch t=2004/7D4h: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=2088/828h</b>
|
ppf.exe | <?dml?>#1 p=2088/828h t=2076/81Ch: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=2244/8C4h</b>
|