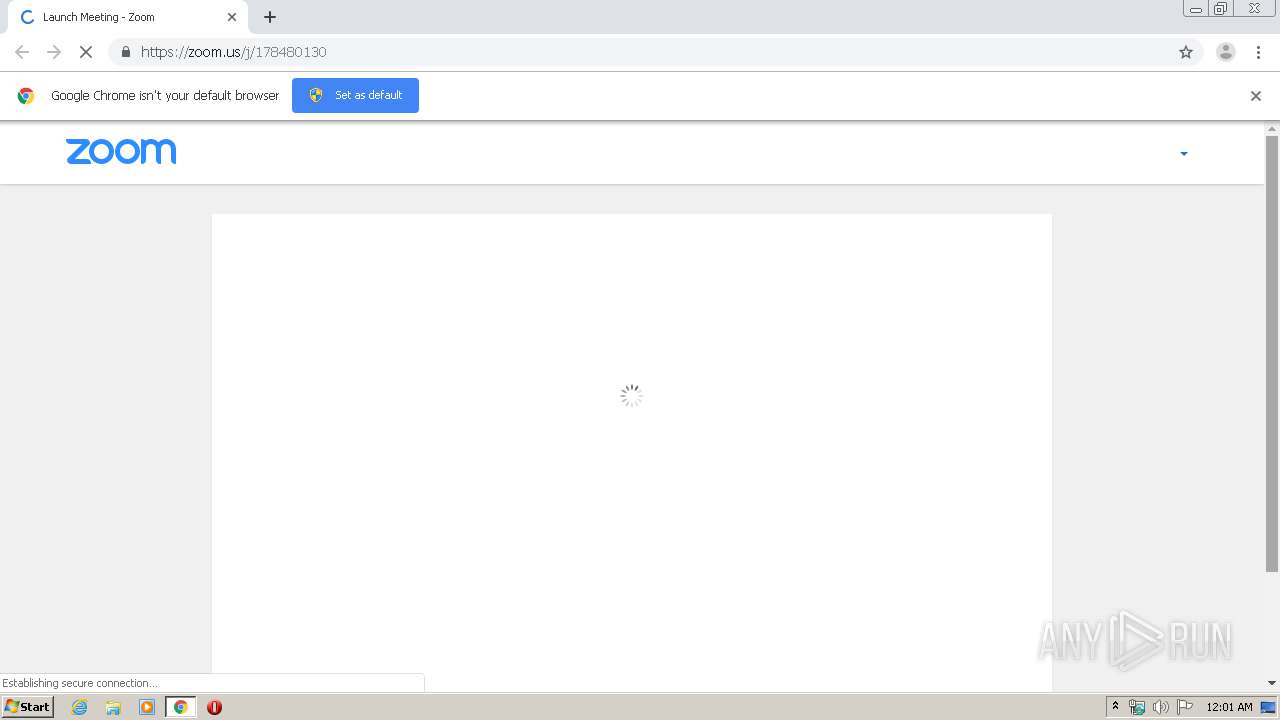
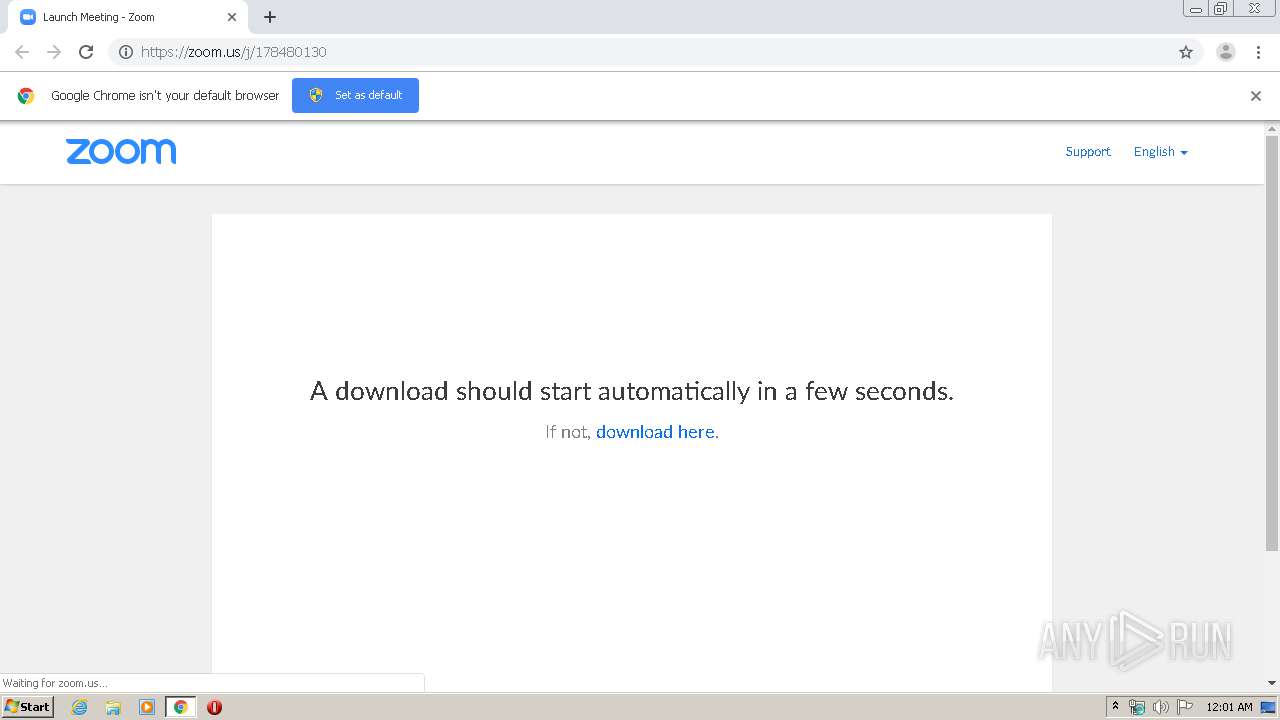
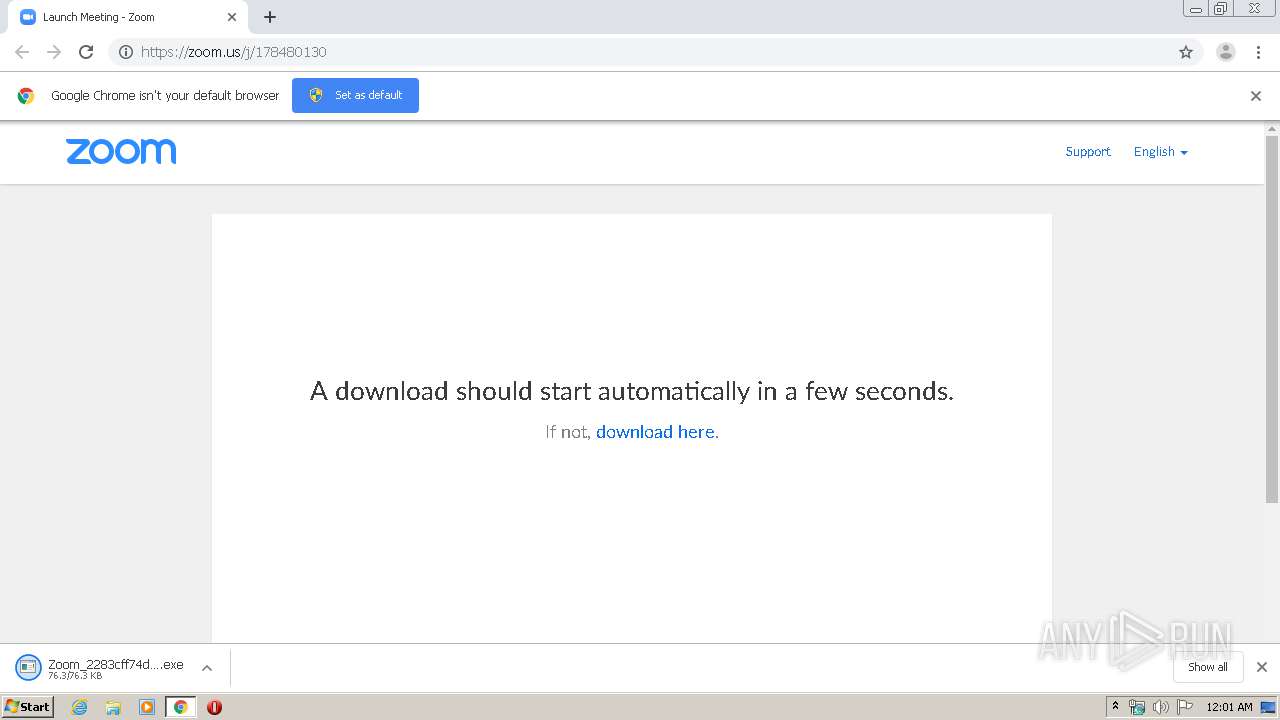
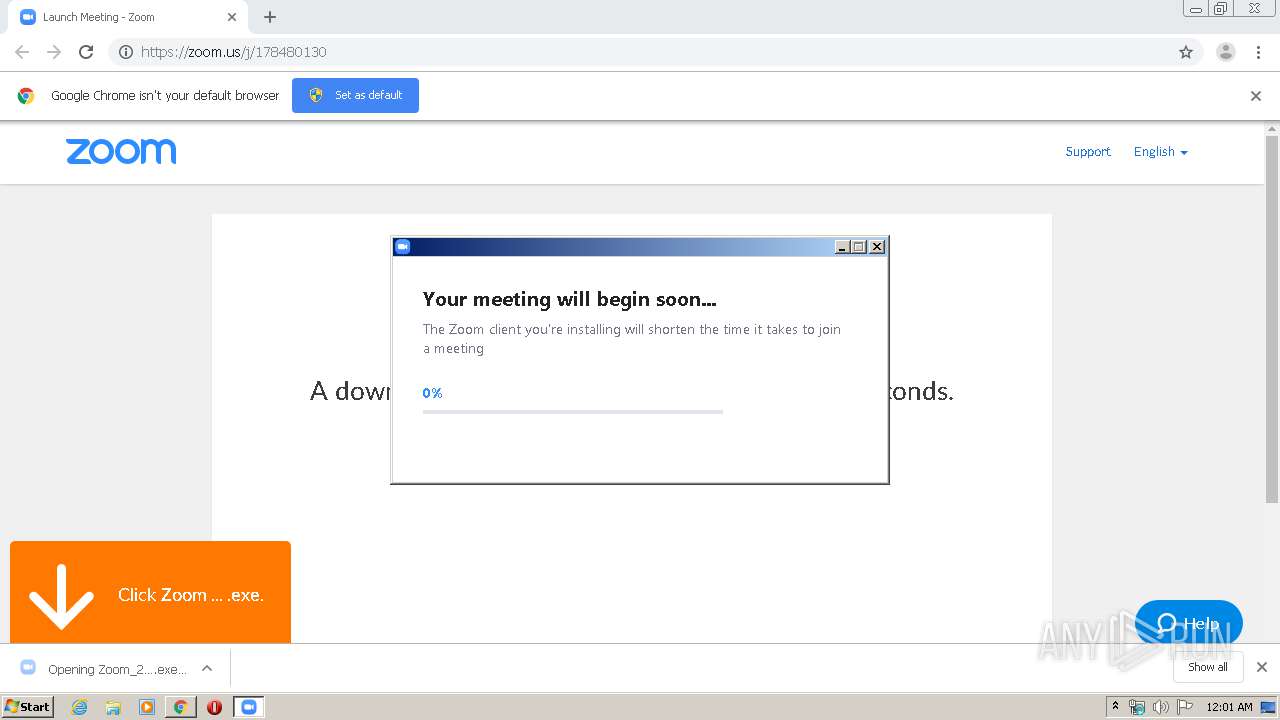
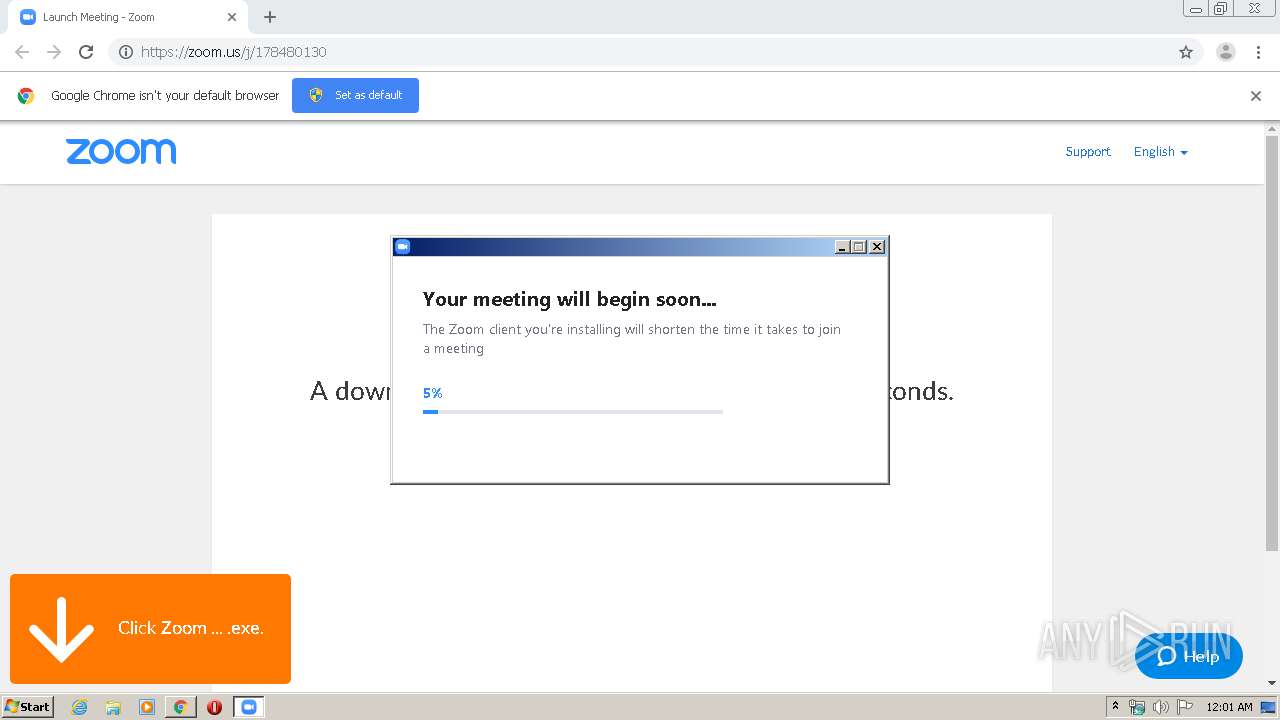
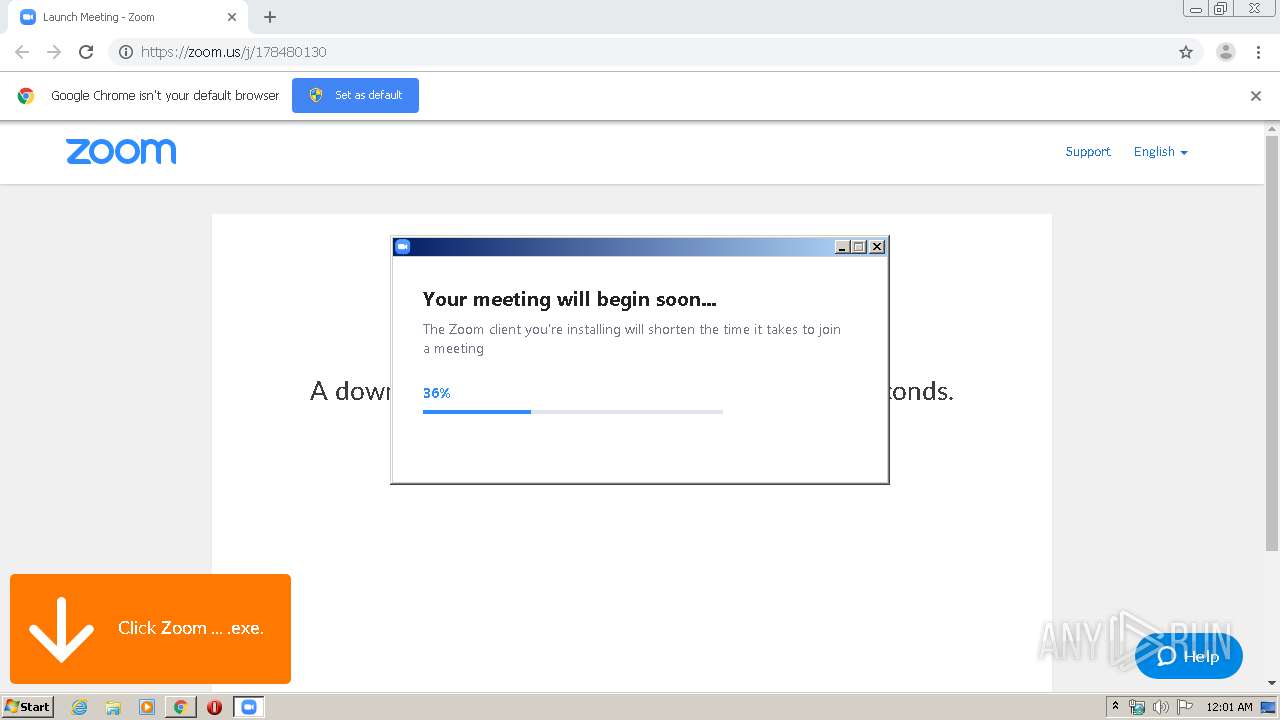
| URL: | https://zoom.us/j/178480130 |
| Full analysis: | https://app.any.run/tasks/e0ea0f7a-b336-4cb9-ab30-b469ffd06564 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 23:00:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E2BE6B1CD3466FDBAD399DDB1DED2A50 |
| SHA1: | EDDEDCCBB85C9C0290704D22A4B48E7E1029A0E6 |
| SHA256: | A3DAF8728F79C28DB3DFD8F1668404B6834536108900C0C06773B6E6059E947F |
| SSDEEP: | 3:N88LWOvn:28LWOvn |
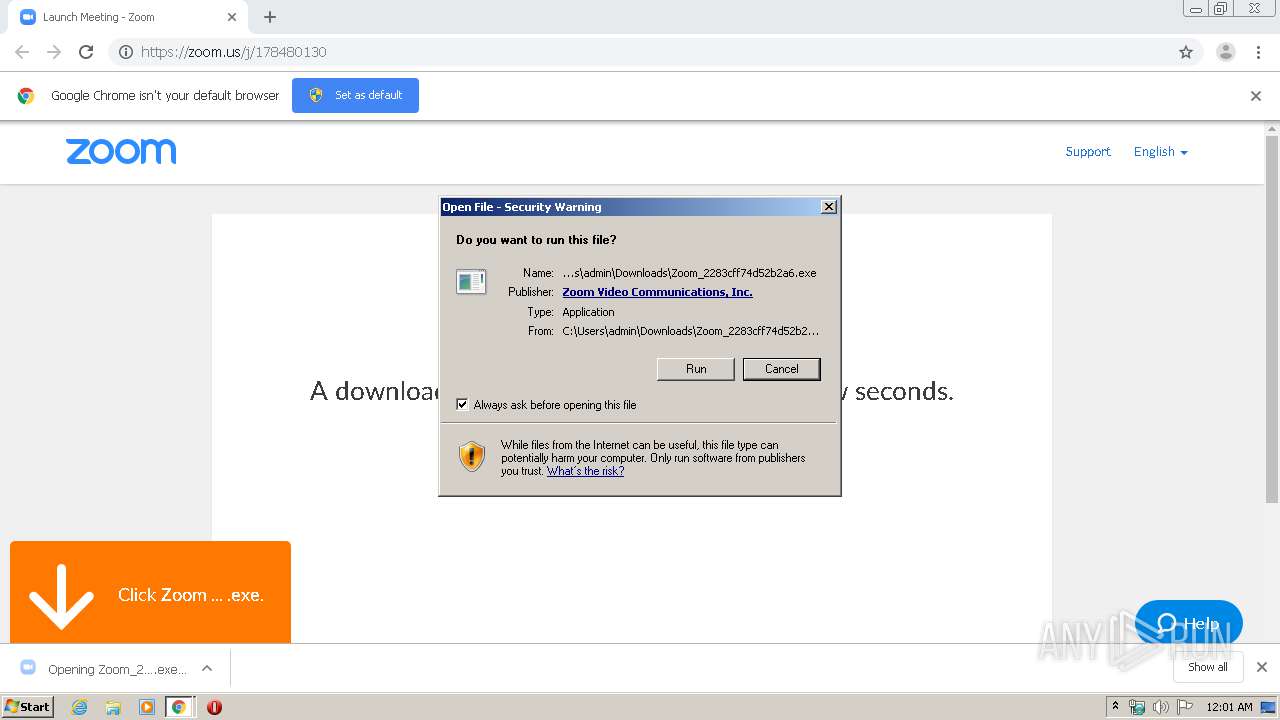
MALICIOUS
Application was dropped or rewritten from another process
- Installer.exe (PID: 620)
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
- Installer.exe (PID: 3612)
- zm3926.tmp (PID: 1940)
- Zoom.exe (PID: 2464)
Loads dropped or rewritten executable
- Installer.exe (PID: 620)
Changes settings of System certificates
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
SUSPICIOUS
Creates files in the user directory
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
- Installer.exe (PID: 620)
Executable content was dropped or overwritten
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2836)
- Installer.exe (PID: 620)
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
Application launched itself
- Installer.exe (PID: 620)
Modifies the open verb of a shell class
- Installer.exe (PID: 620)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 620)
Creates a software uninstall entry
- Installer.exe (PID: 620)
Starts itself from another location
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
Starts application with an unusual extension
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
Reads Internet Cache Settings
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2836)
Adds / modifies Windows certificates
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
INFO
Reads the hosts file
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3448)
Application launched itself
- chrome.exe (PID: 2836)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 620)
Reads Internet Cache Settings
- chrome.exe (PID: 2836)
Reads settings of System Certificates
- Zoom_2283cff74d52b2a6.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
30
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe" ZInstaller --conf.mode=silent --ipc_wnd=328128 | C:\Users\admin\AppData\Roaming\Zoom\ZoomDownload\Installer.exe | Zoom_2283cff74d52b2a6.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Installer Exit code: 0 Version: 4,6,19178,0323 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18406949934702842564 --mojo-platform-channel-handle=4904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8245970553770556251 --mojo-platform-channel-handle=4496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8315611120384589993 --mojo-platform-channel-handle=4444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14663709241828823876 --mojo-platform-channel-handle=4184 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11967828329400331436 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Users\admin\AppData\Local\Temp\zm3926.tmp" -DAF8C715436E44649F1312698287E6A5=C:\Users\admin\Downloads\Zoom_2283cff74d52b2a6.exe | C:\Users\admin\AppData\Local\Temp\zm3926.tmp | — | Zoom_2283cff74d52b2a6.exe | |||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Opener Exit code: 0 Version: 4,6,19178,0323 | |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5137298272284333950 --mojo-platform-channel-handle=1048 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6248682365585974639 --mojo-platform-channel-handle=4248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 279
Read events
1 997
Write events
3 557
Delete events
1 725
Modification events
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2836-13230082867183375 |
Value: 259 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
58
Suspicious files
57
Text files
251
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E827A33-B14.pma | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c01.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a97f6b34-167b-4767-b9bf-8b31af00e426.tmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e23.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
38
DNS requests
26
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3448 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
3448 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
3984 | Zoom_2283cff74d52b2a6.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
3984 | Zoom_2283cff74d52b2a6.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3448 | chrome.exe | GET | 200 | 173.194.151.108:80 | http://r6---sn-4g5e6ne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=92.118.13.5&mm=28&mn=sn-4g5e6ne6&ms=nvh&mt=1585609211&mv=m&mvi=5&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3448 | chrome.exe | GET | 200 | 74.125.11.26:80 | http://r4---sn-4g5ednee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=92.118.13.5&mm=28&mn=sn-4g5ednee&ms=nvh&mt=1585609211&mv=m&mvi=3&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 3.235.71.132:443 | zoom.us | — | US | unknown |
3448 | chrome.exe | 172.217.21.206:443 | clients4.google.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 13.35.254.162:443 | d24cgw3uvb9a9h.cloudfront.net | — | US | unknown |
3448 | chrome.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3448 | chrome.exe | 104.18.72.113:443 | assets.zendesk.com | Cloudflare Inc | US | shared |
— | — | 104.18.71.113:443 | assets.zendesk.com | Cloudflare Inc | US | shared |
3448 | chrome.exe | 52.202.62.237:443 | launcher.zoom.us | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zoom.us |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients4.google.com |
| whitelisted |
d24cgw3uvb9a9h.cloudfront.net |
| shared |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
assets.zendesk.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3448 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
3448 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
Process | Message |
|---|---|
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\bin |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | |
Installer.exe | [CZoomProductPathHelper::RecursiveRemoveDirA] Path is: |