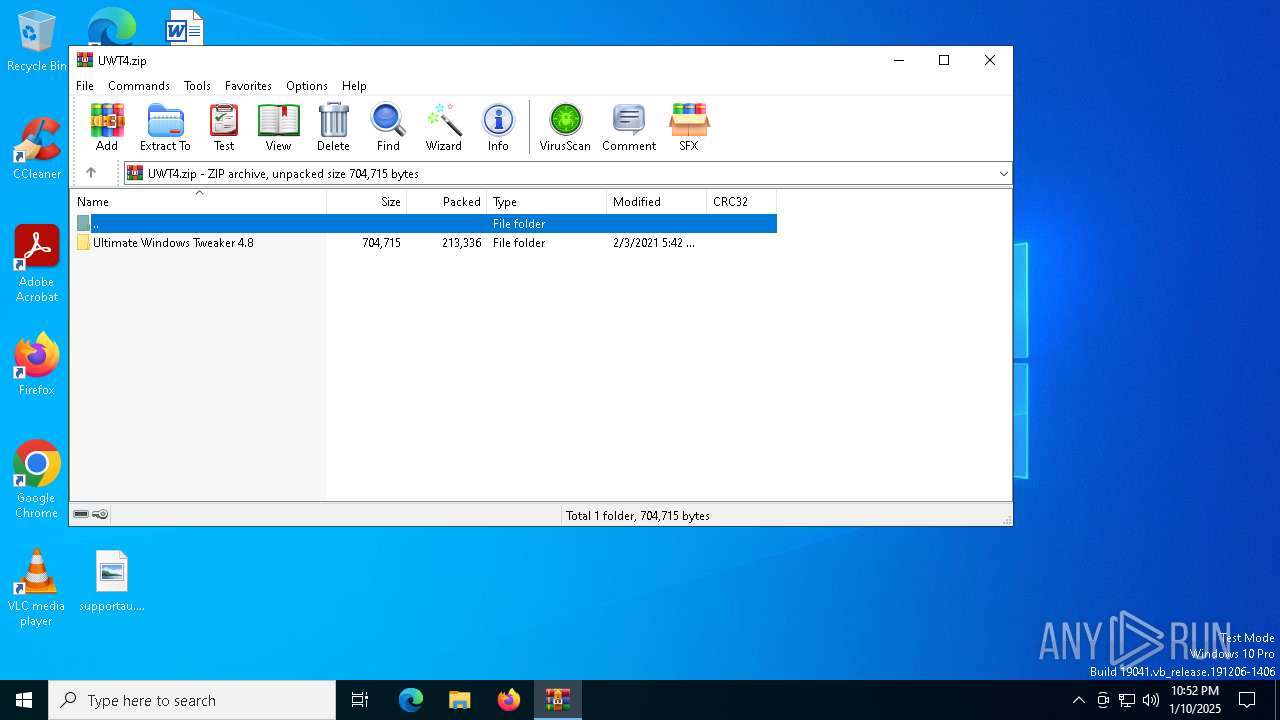
| File name: | UWT4.zip |
| Full analysis: | https://app.any.run/tasks/c44e662b-9cfd-4ec8-837c-e17c99a16bae |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 22:52:05 |
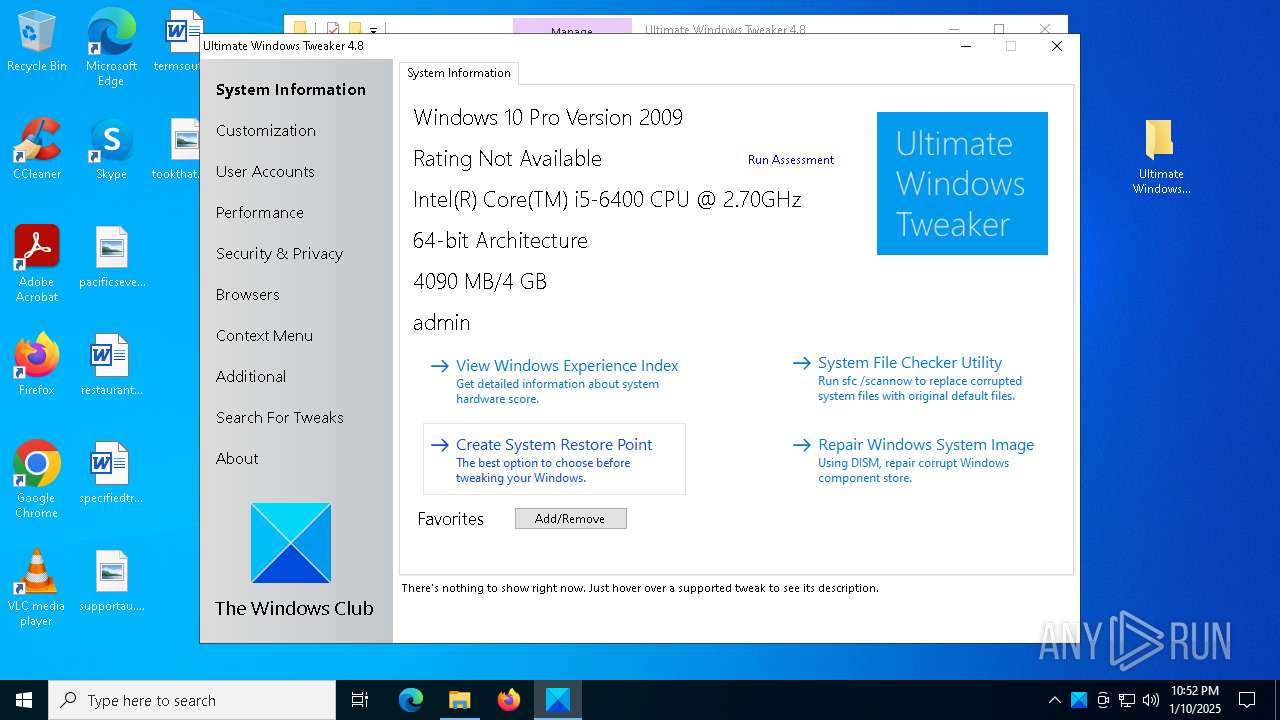
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | E668044896AEAF341E15F441F7C2A4FD |
| SHA1: | 03E44CF38696BF16C3C765438C2E6CF320D99E30 |
| SHA256: | A3D95804F4BB62D1618DDE448F0F2F2E6073ED660F1F96D88CA41EE368CEFE6A |
| SSDEEP: | 6144:GPqVT7bmtnkt6XjP3OqEgiSCwygdKa+5ZIAo9N8Y:JXbv6+qEgx7NbCqAoH |
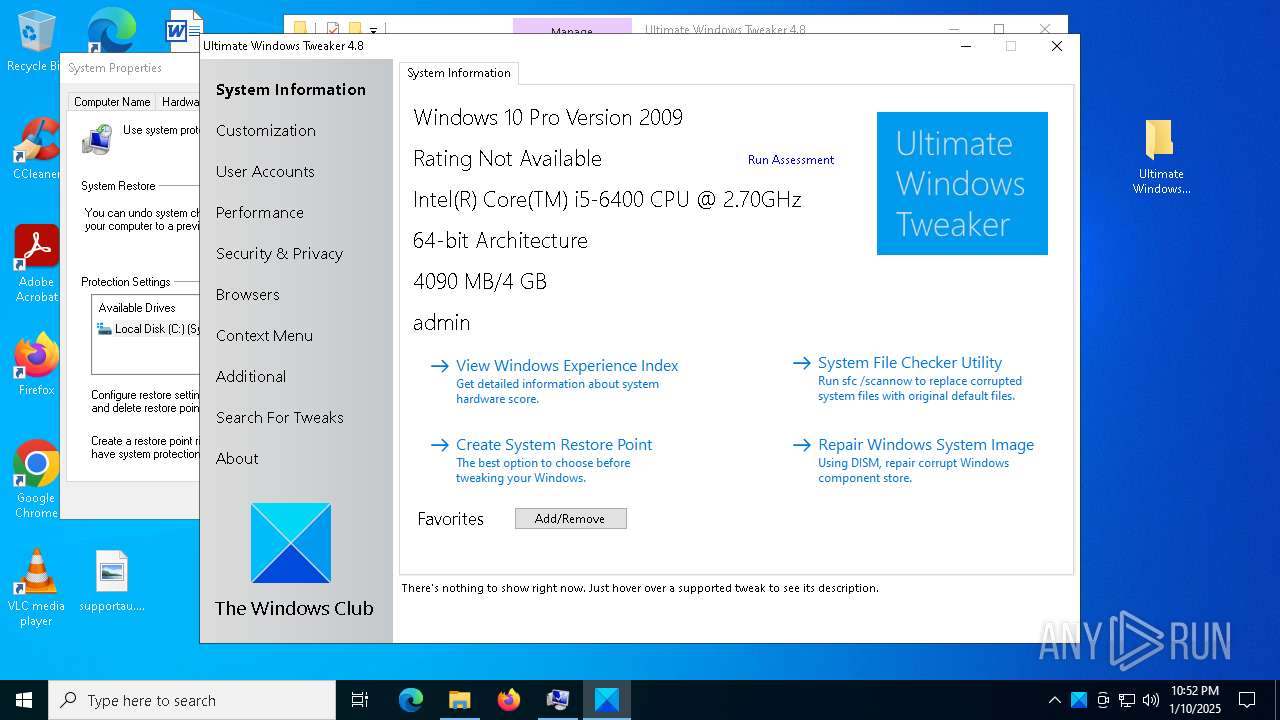
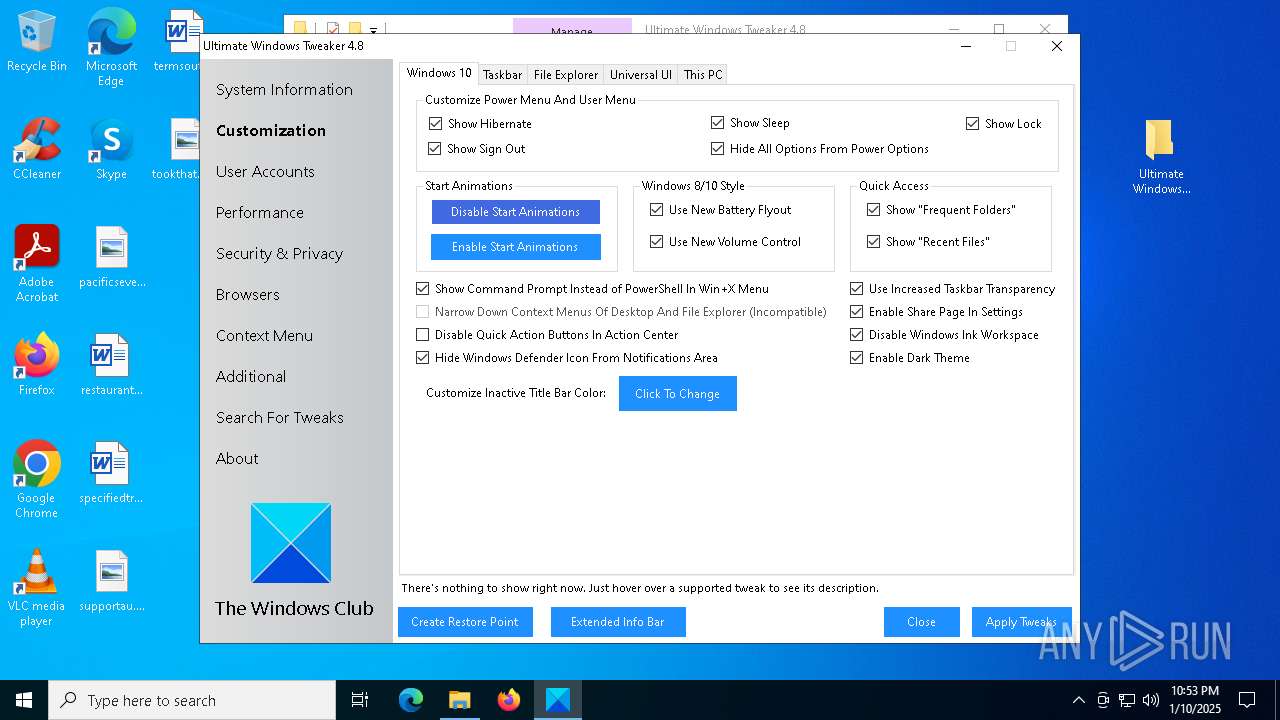
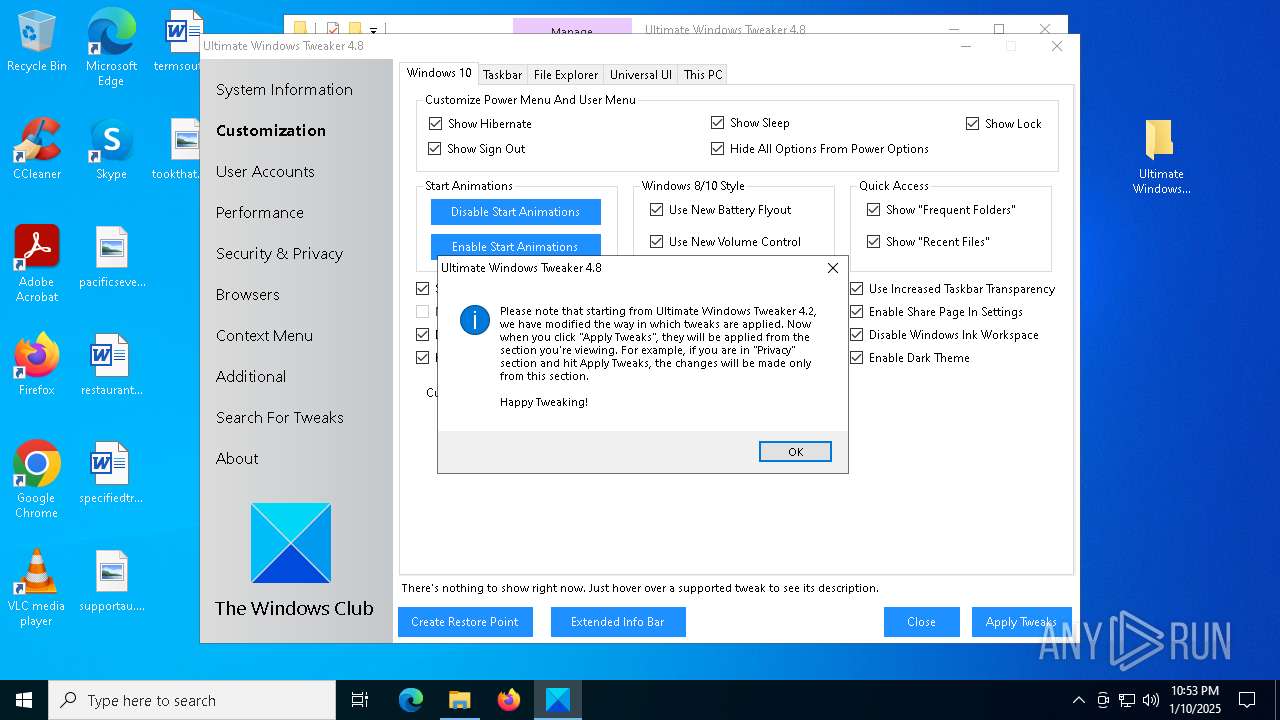
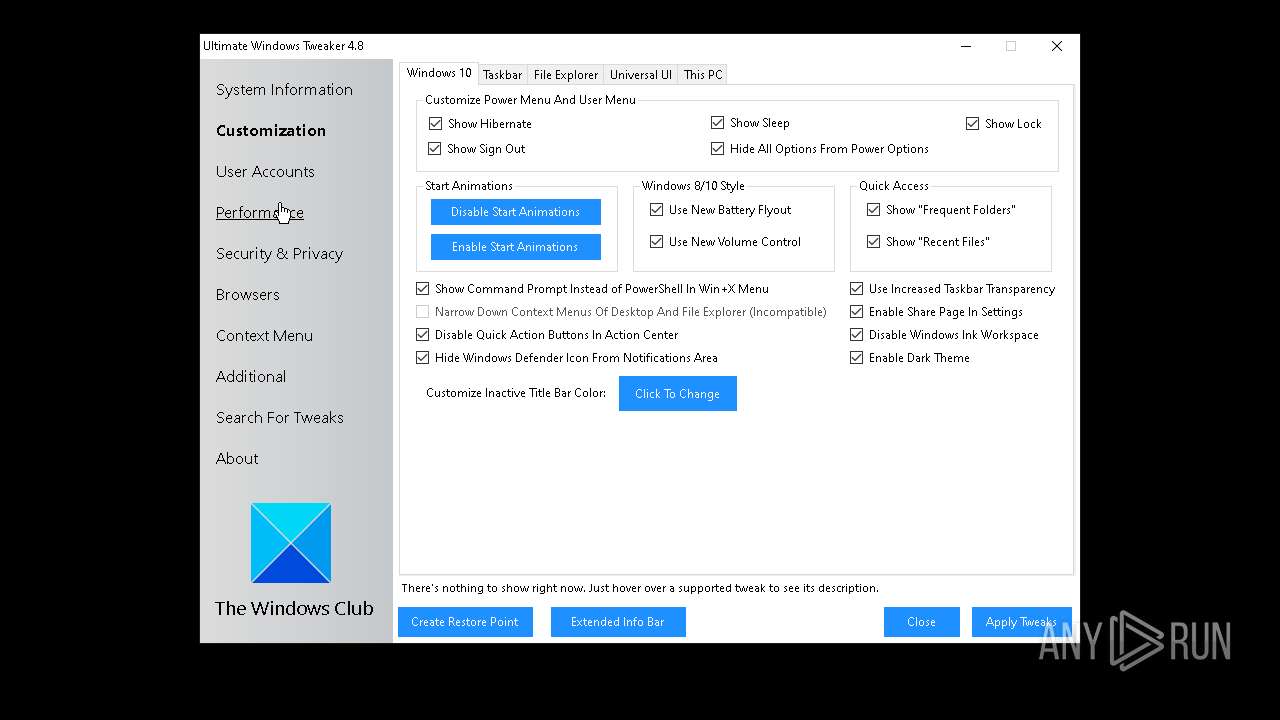
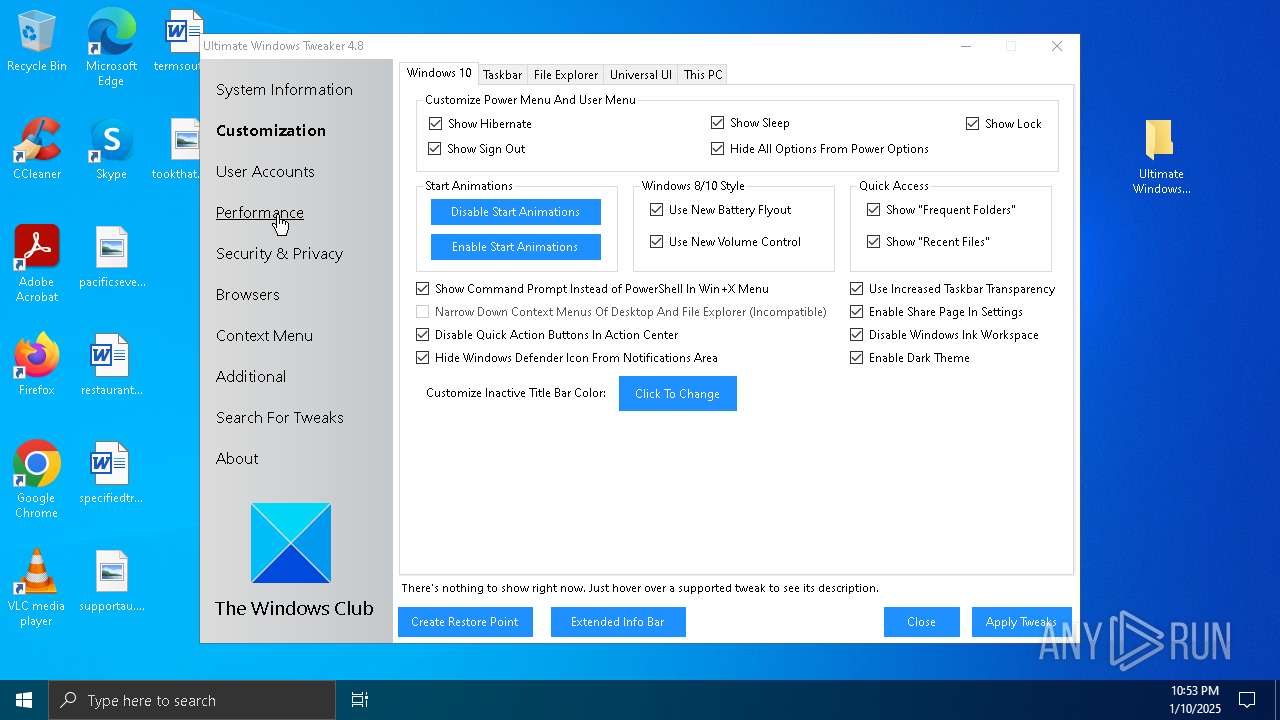
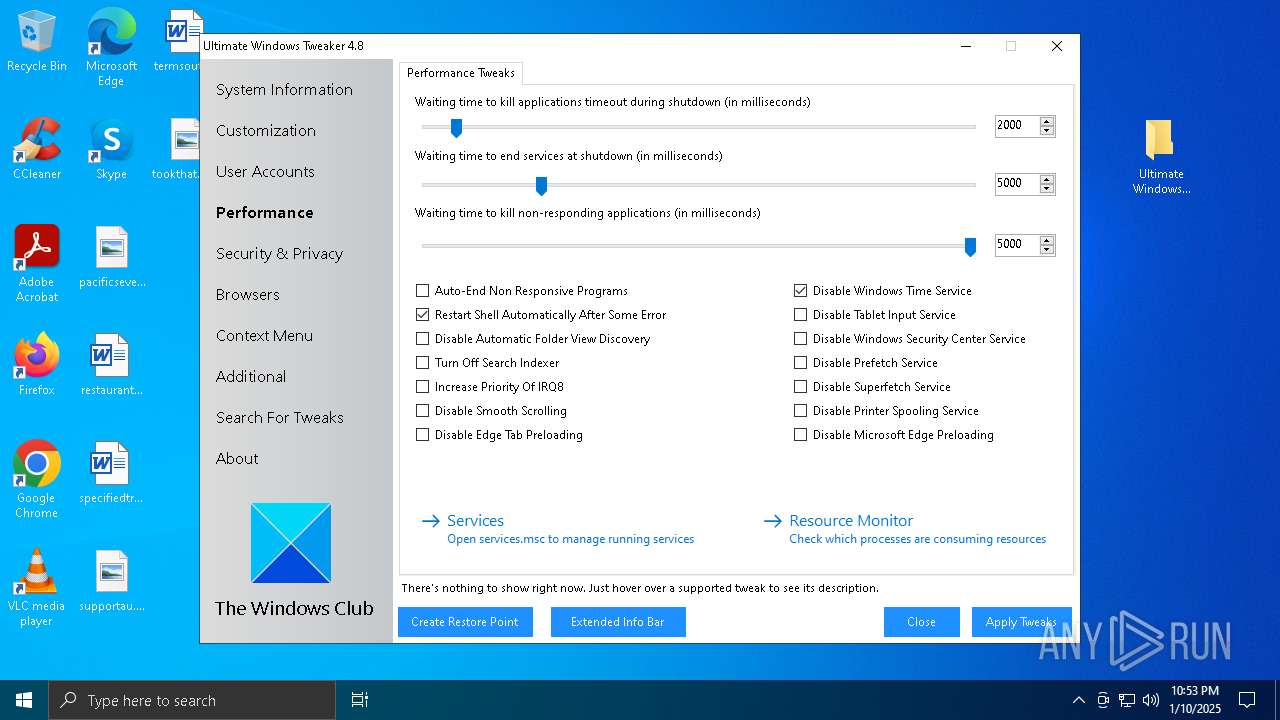
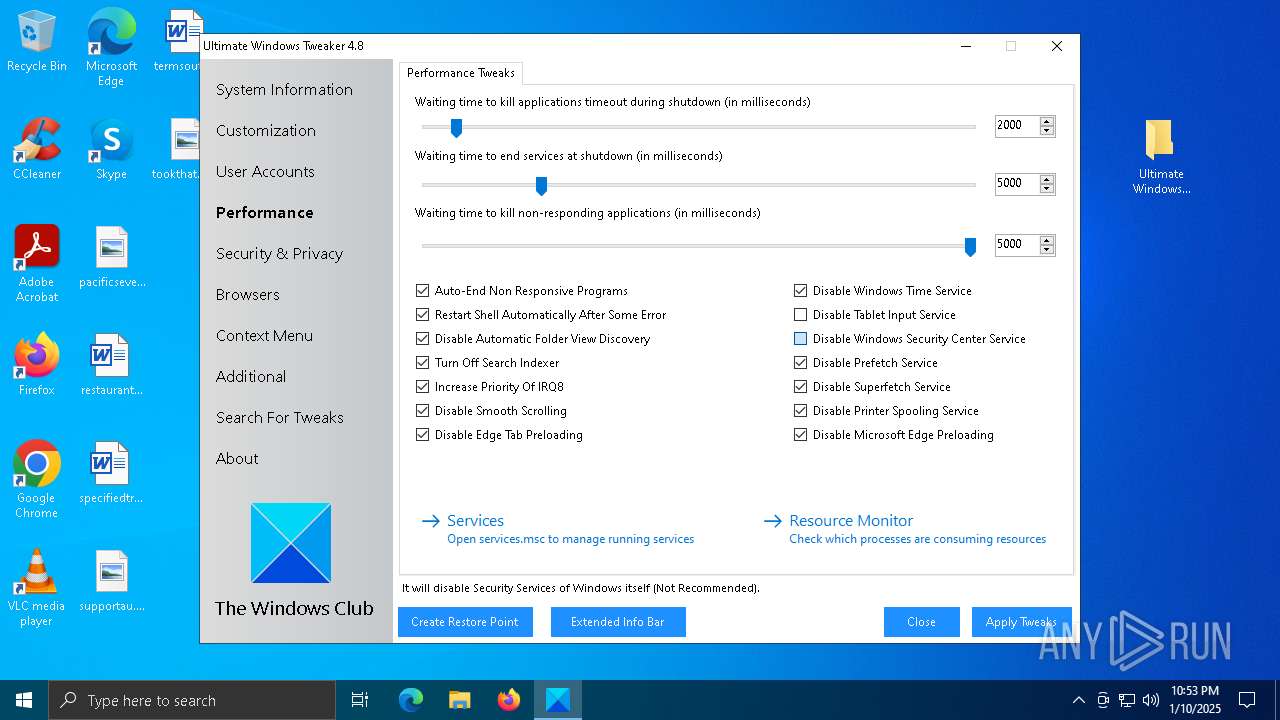
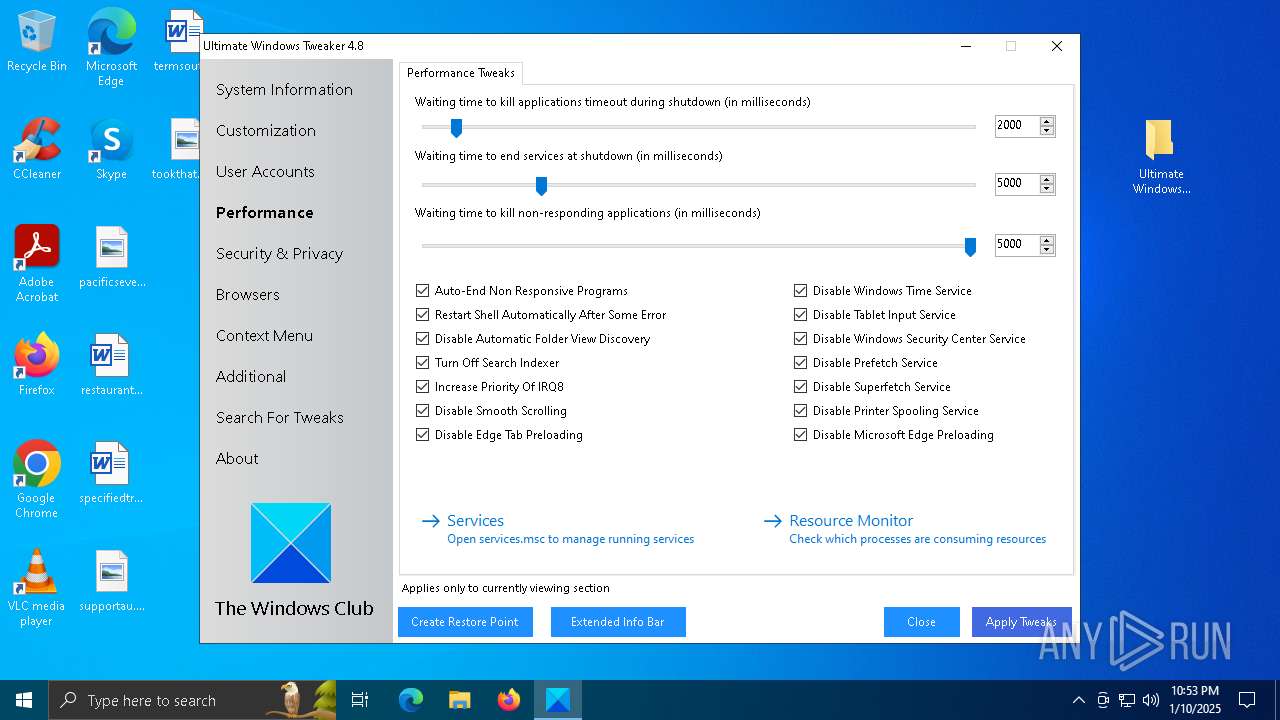
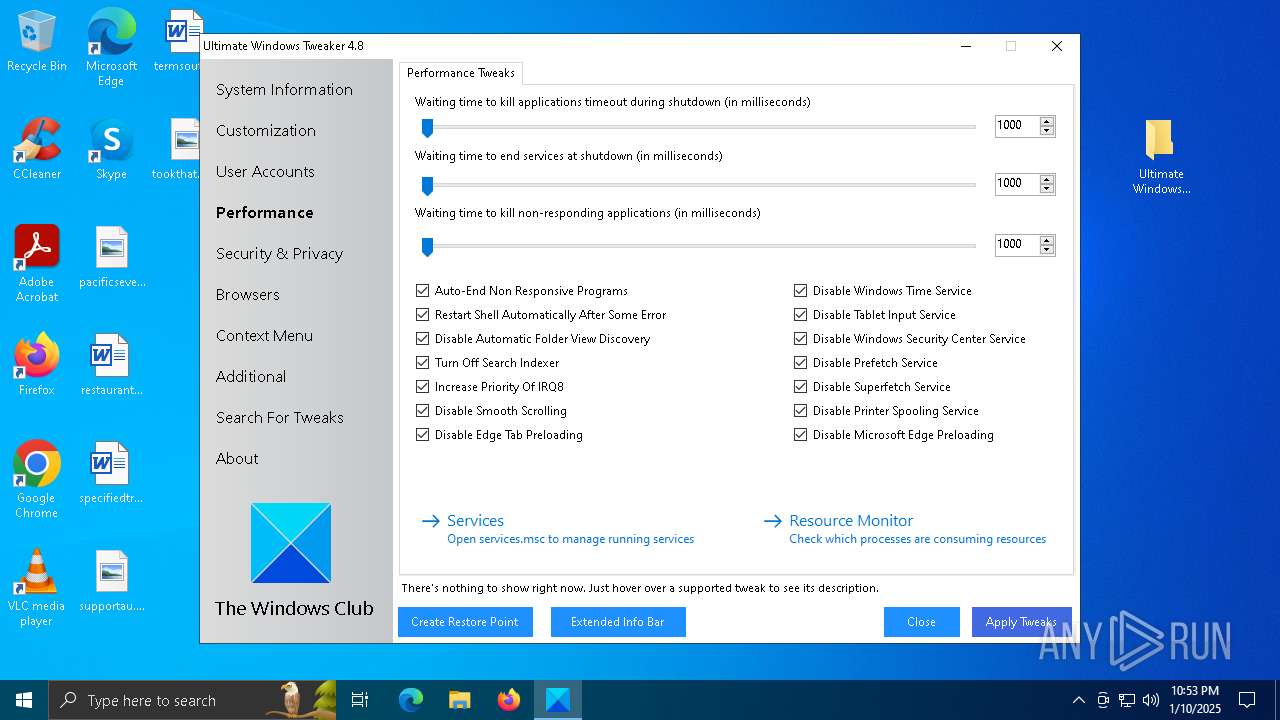
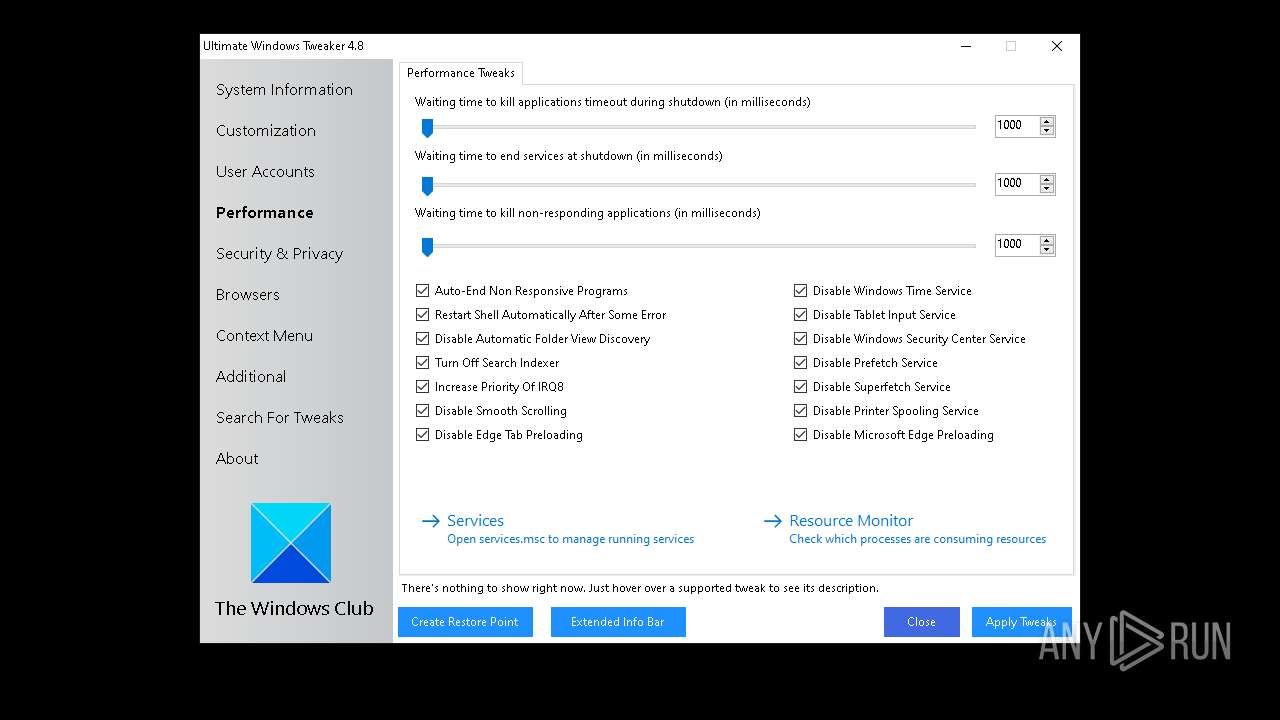
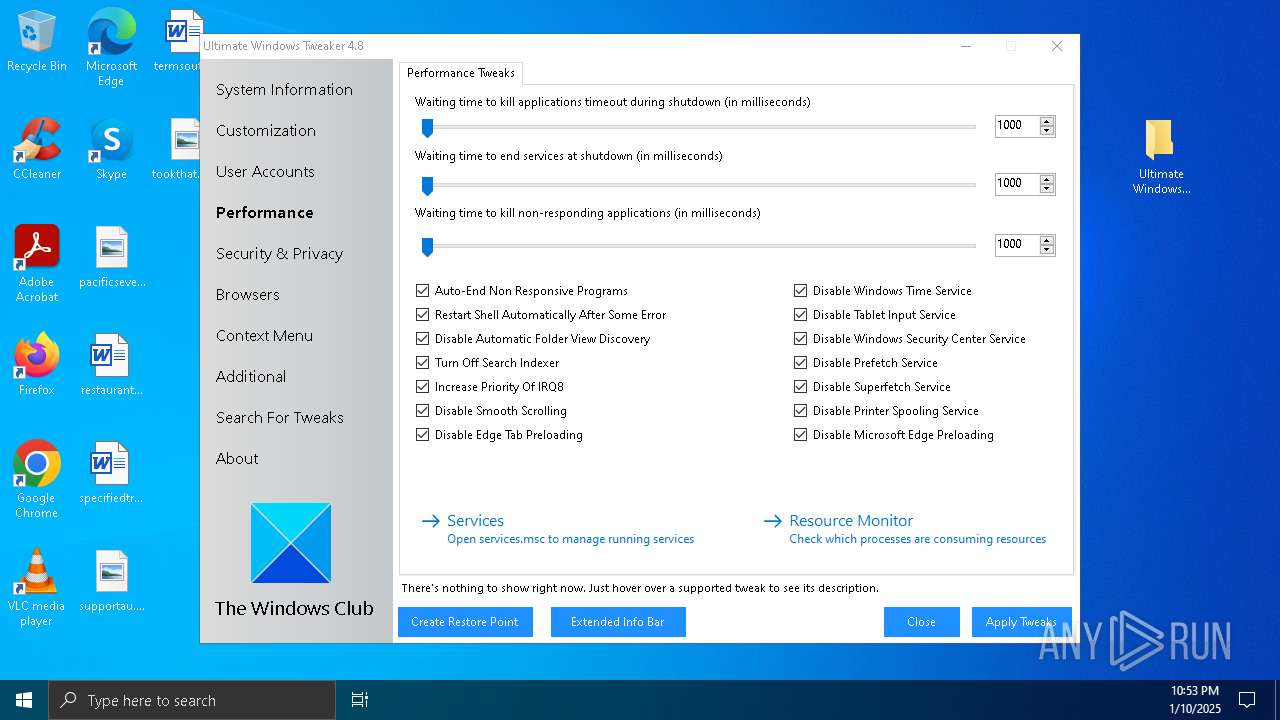
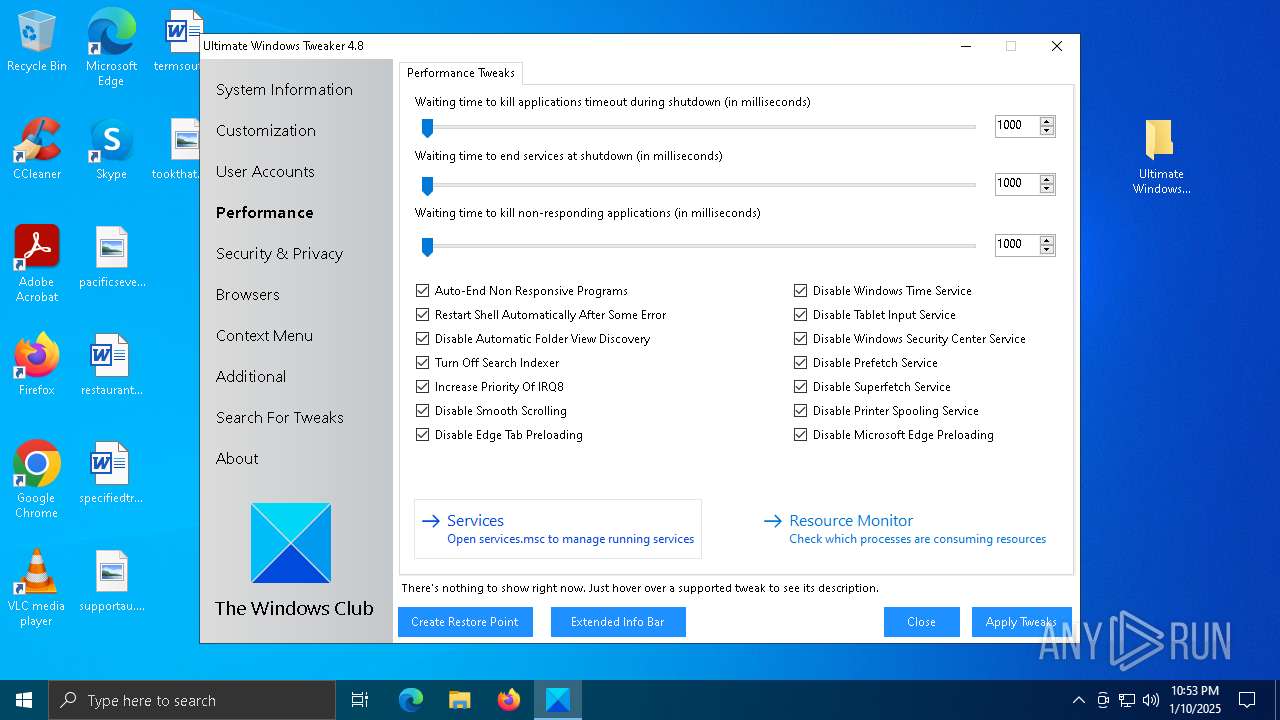
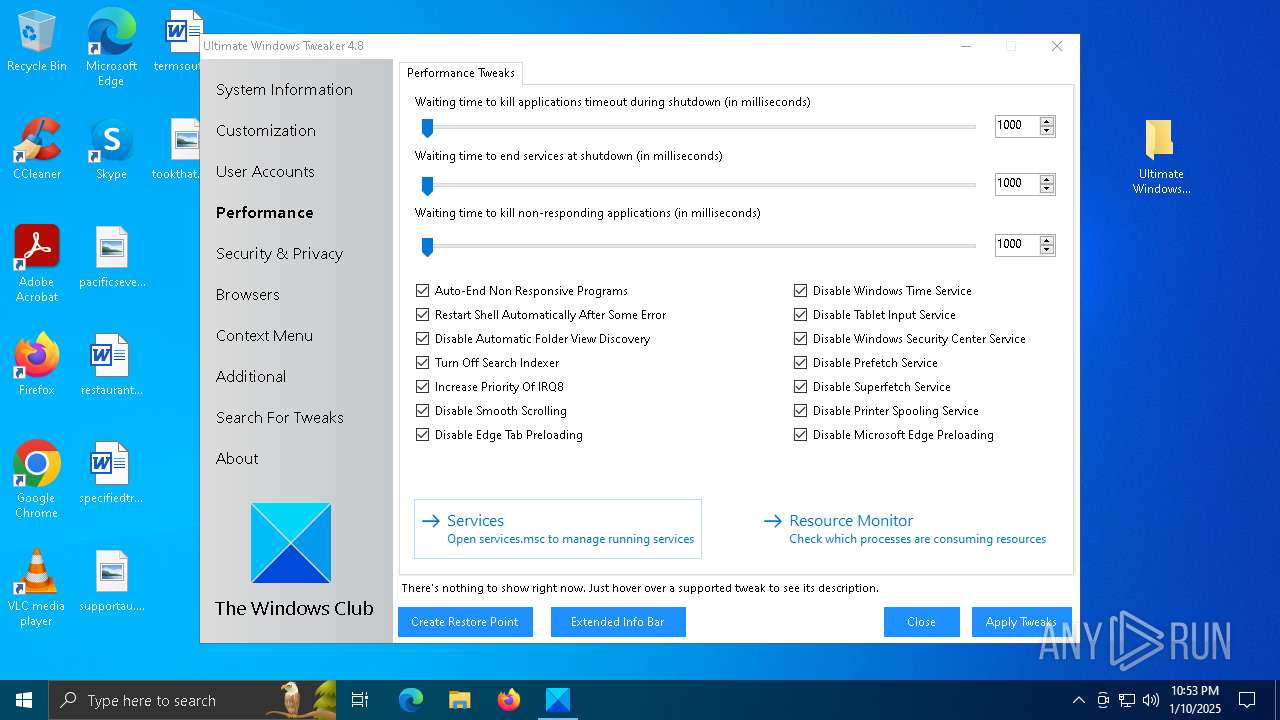
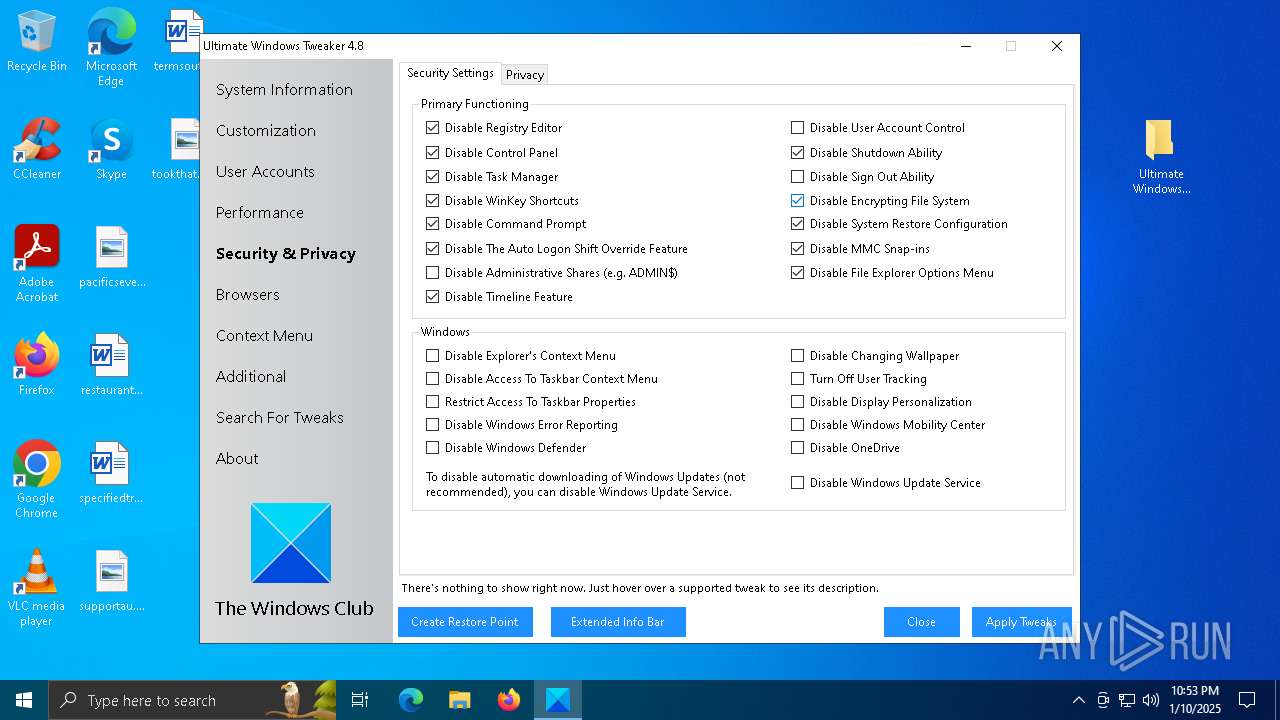
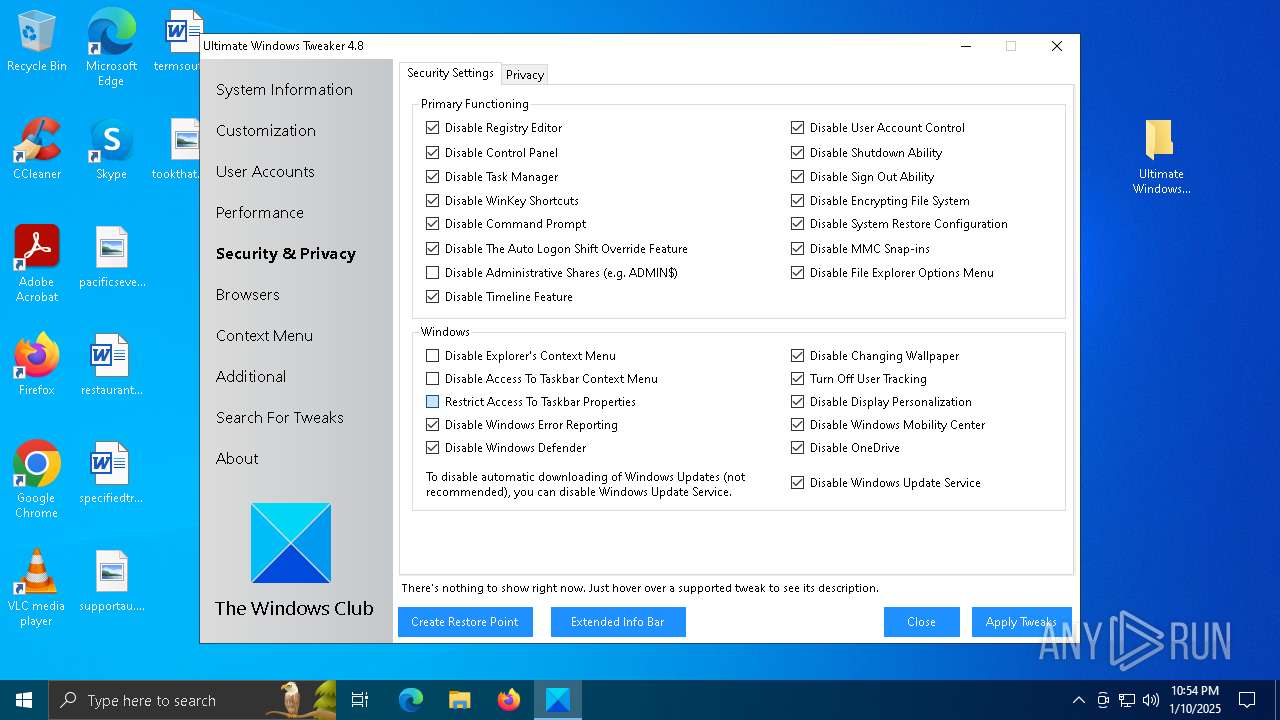
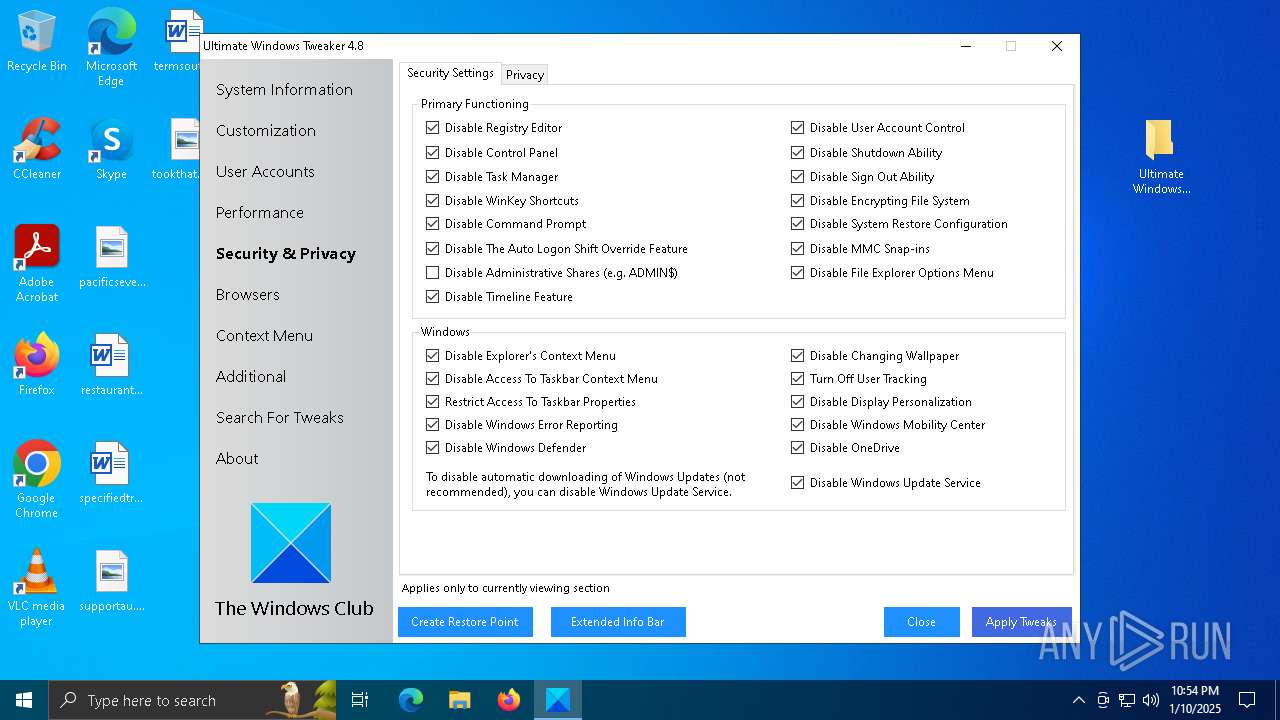
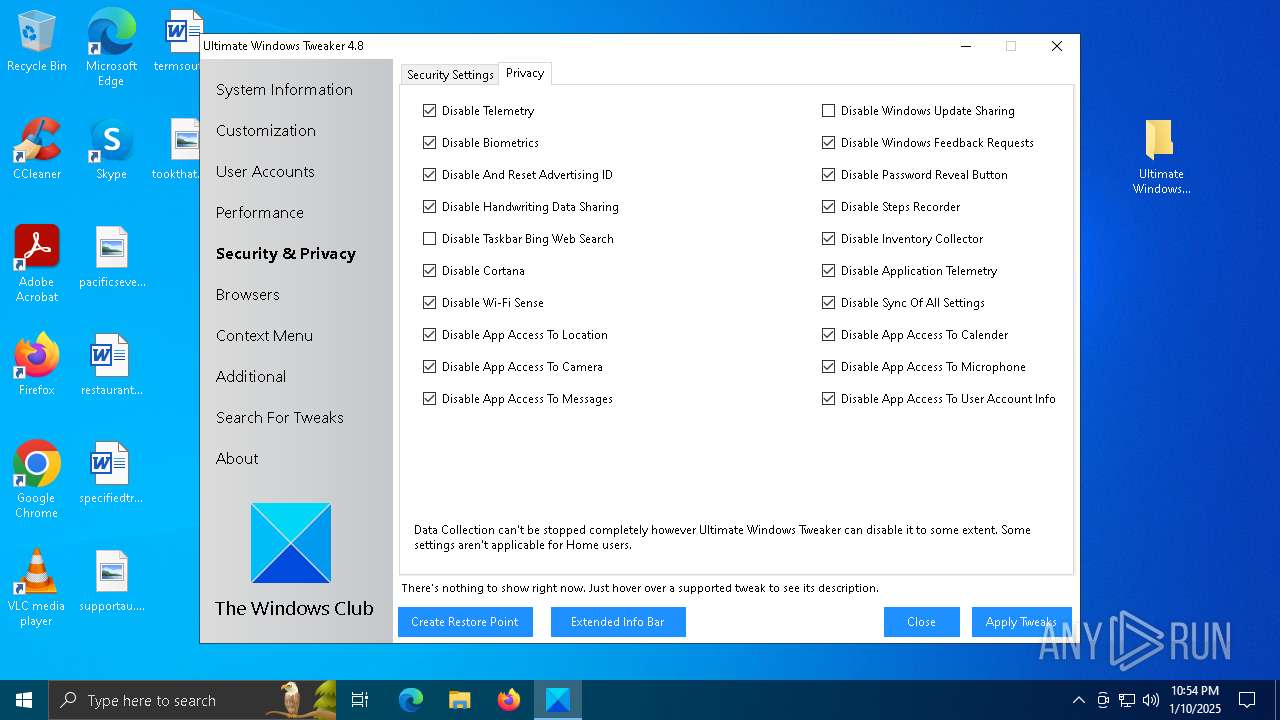
MALICIOUS
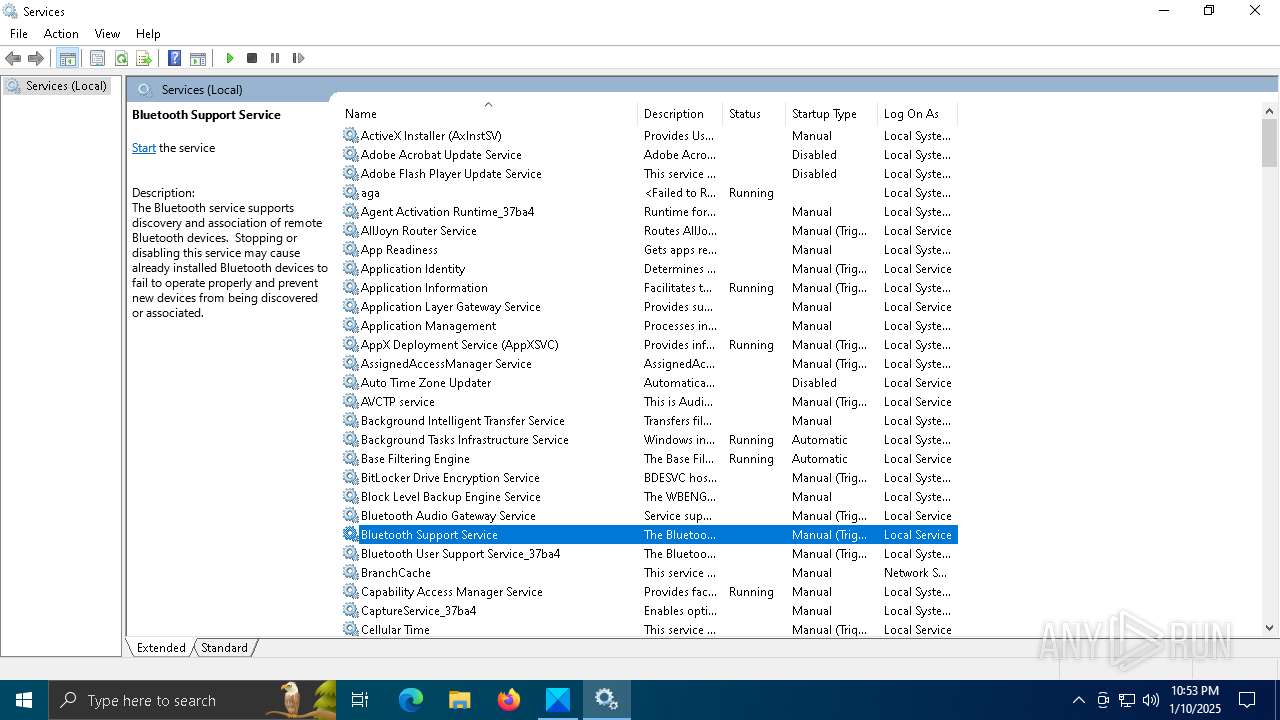
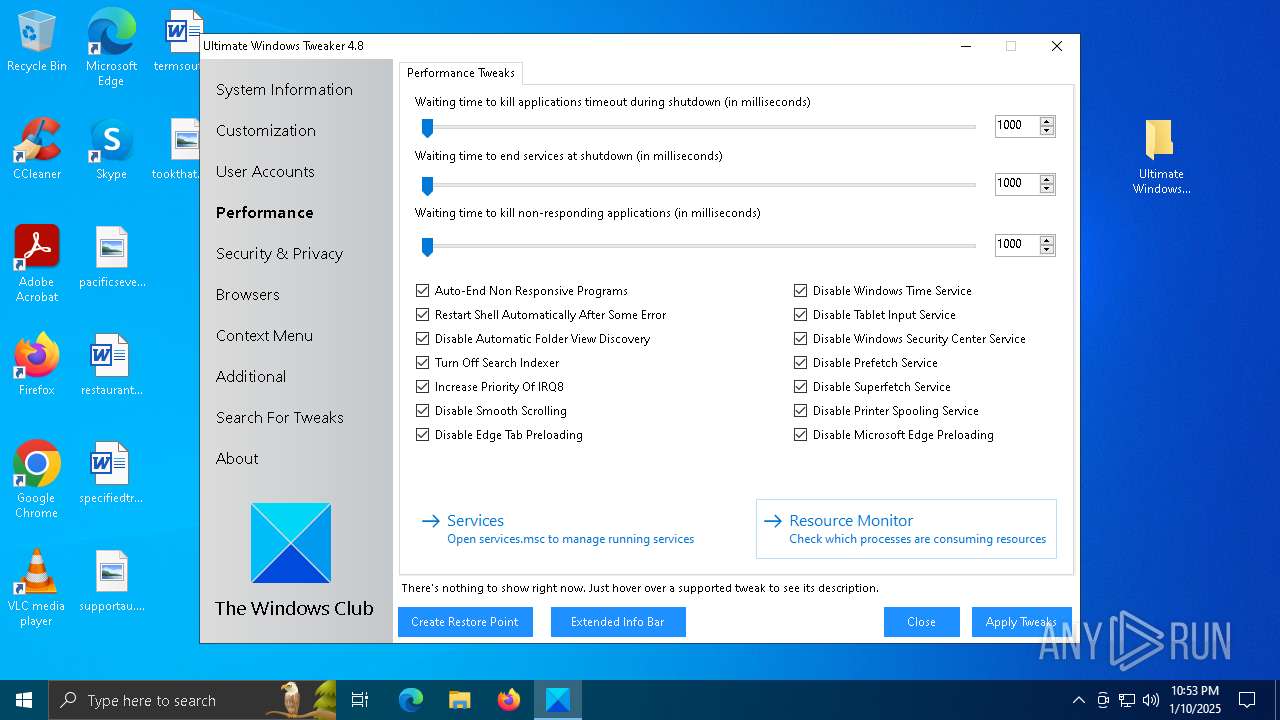
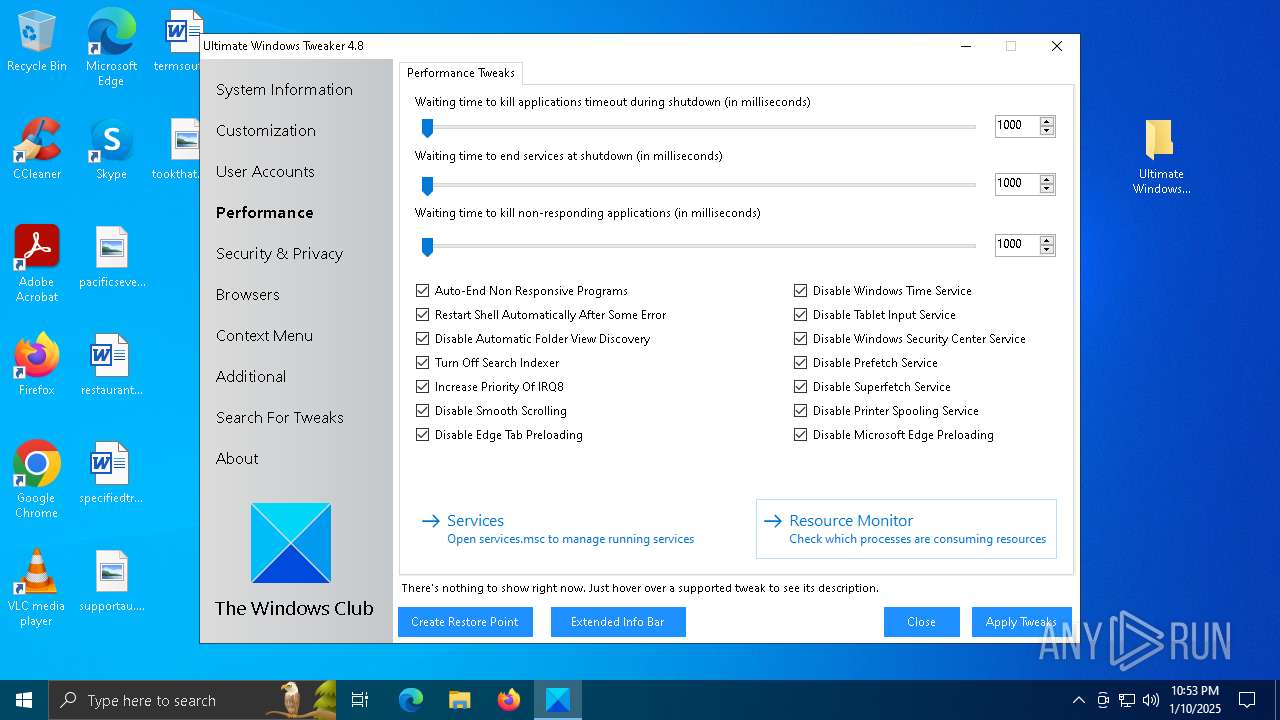
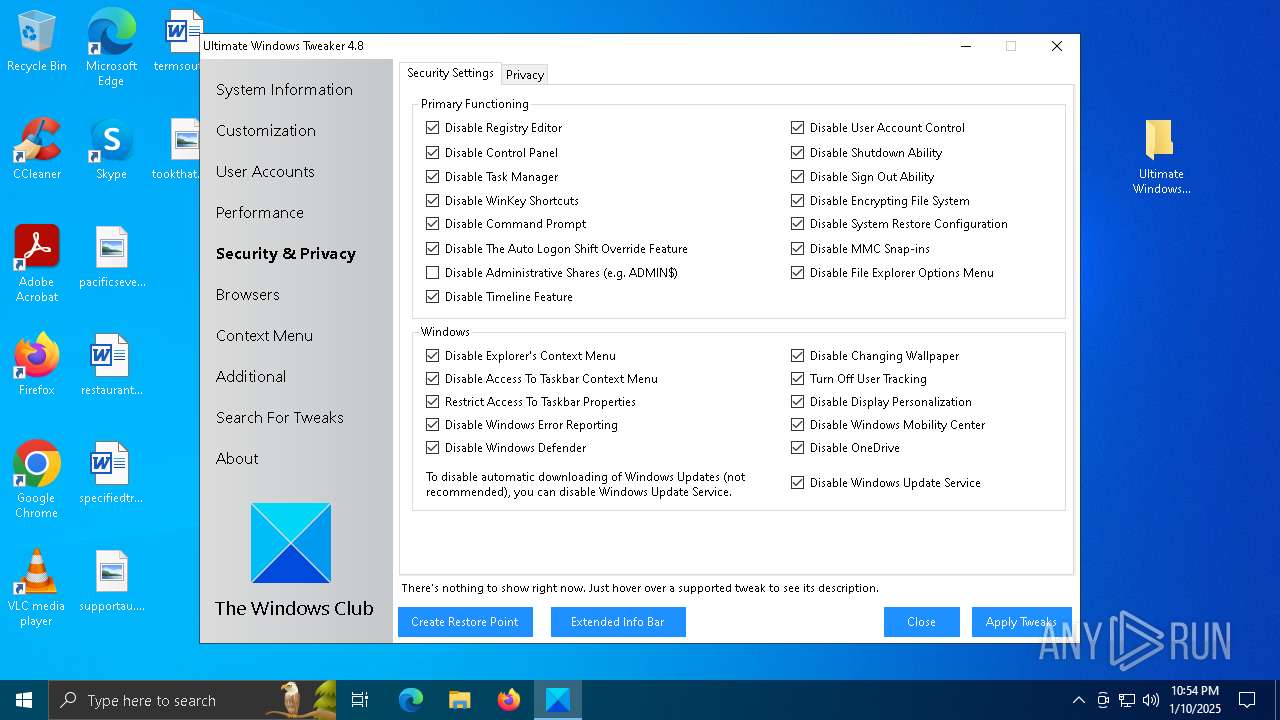
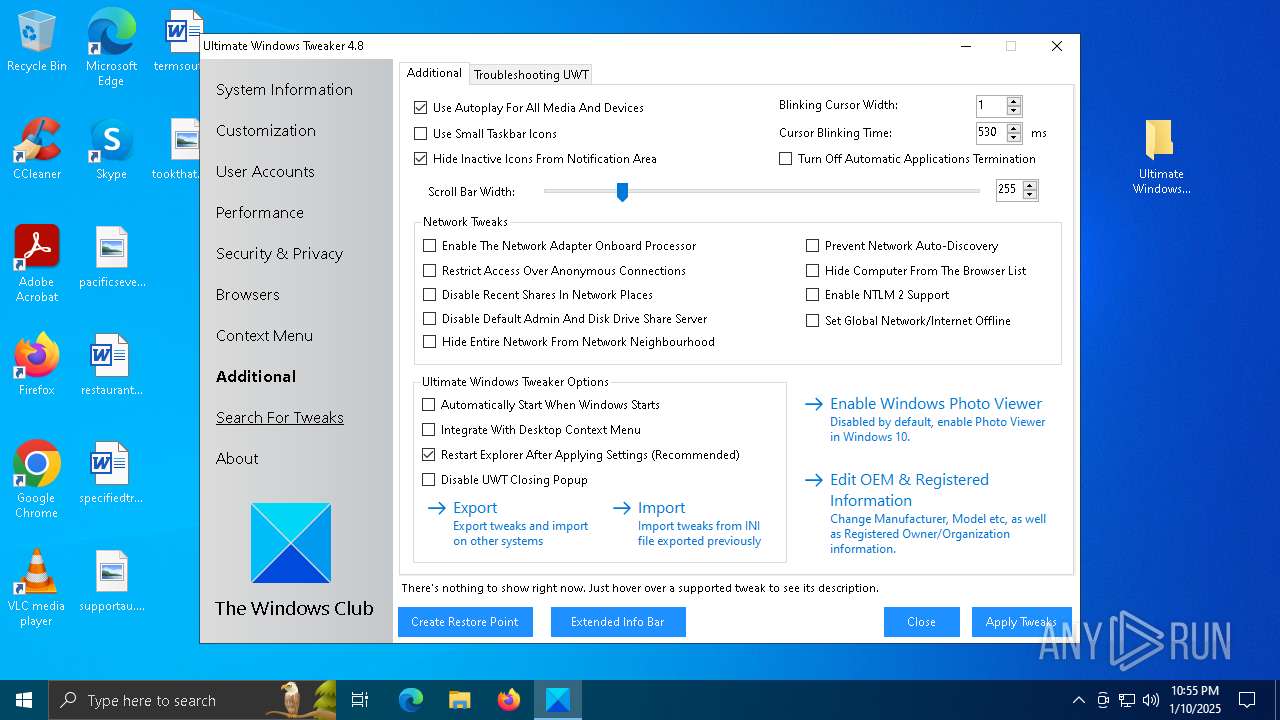
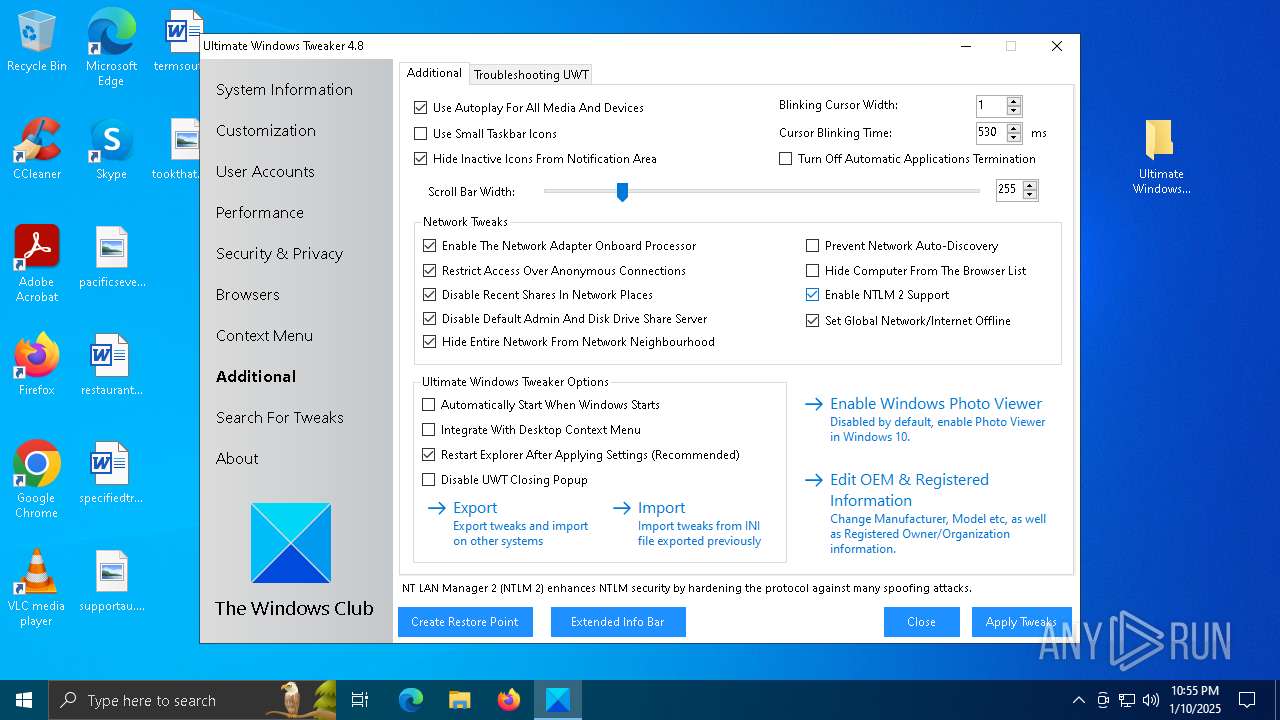
Uses NET.EXE to stop Windows Security Center service
- net.exe (PID: 5704)
- cmd.exe (PID: 4116)
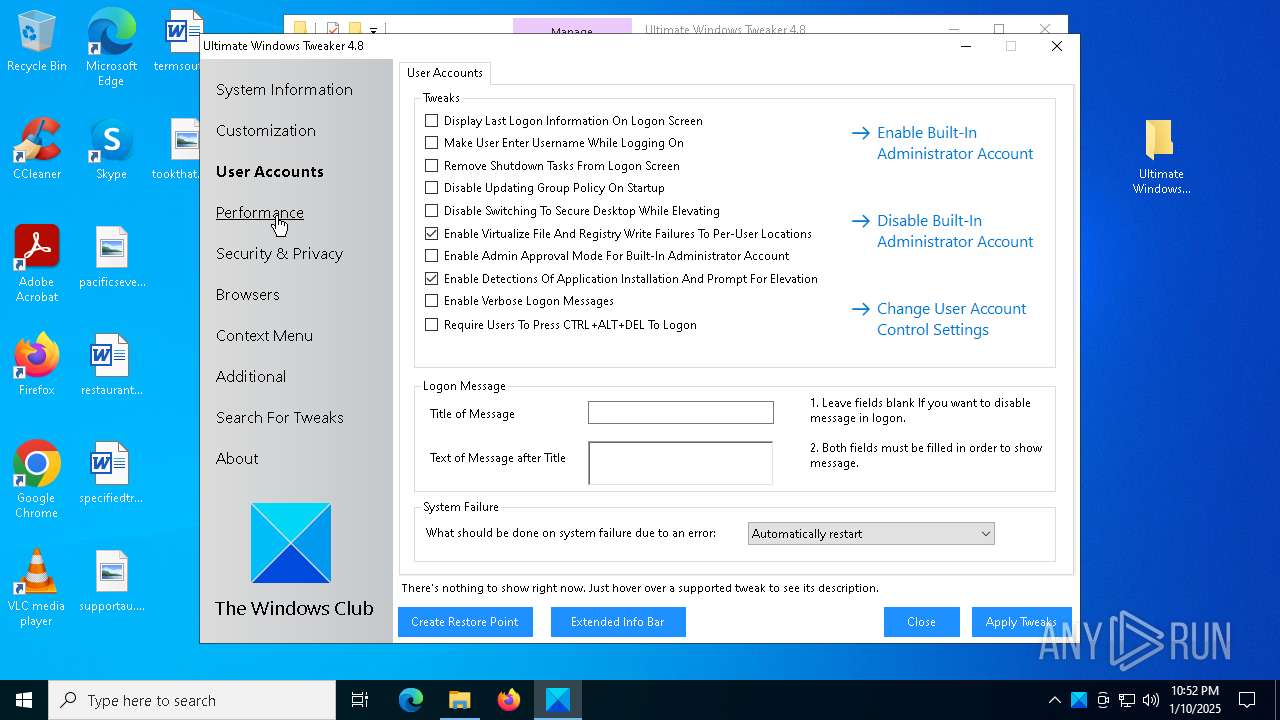
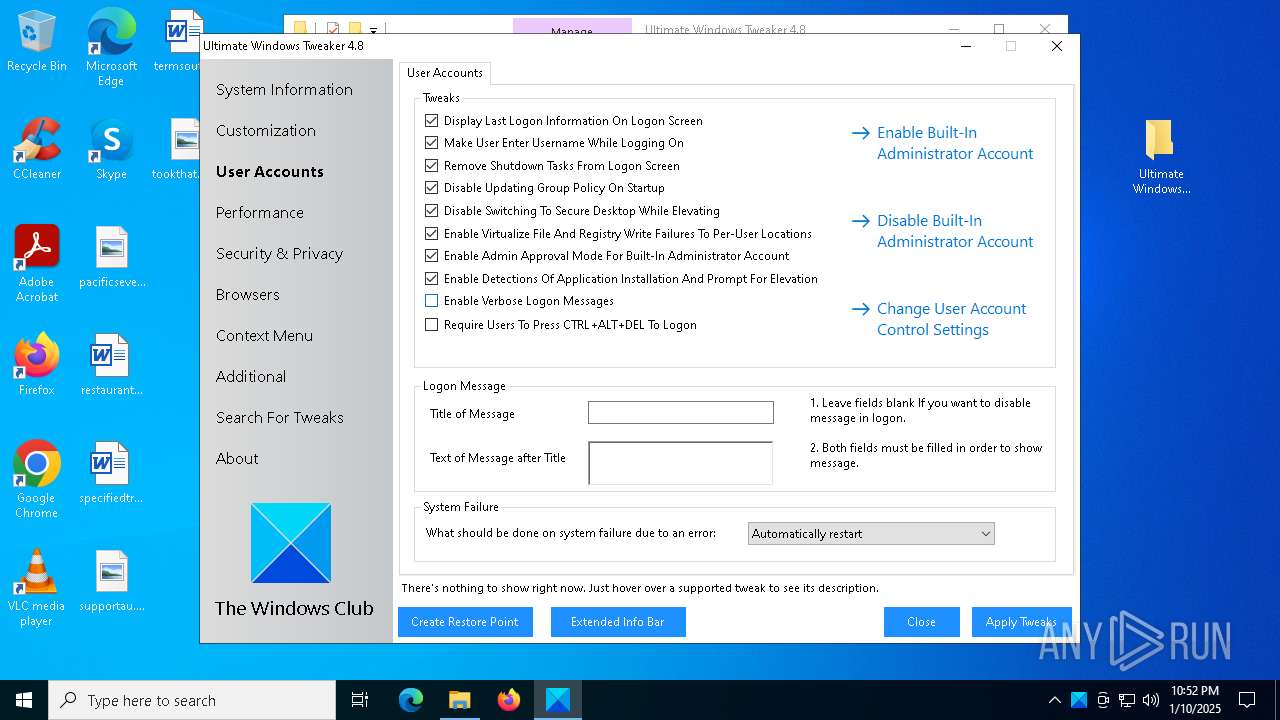
Changes the login/logoff helper path in the registry
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Starts NET.EXE for service management
- cmd.exe (PID: 4116)
- net.exe (PID: 3852)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5068)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 6428)
- net.exe (PID: 6352)
- net.exe (PID: 544)
- net.exe (PID: 4804)
- net.exe (PID: 5376)
- net.exe (PID: 5704)
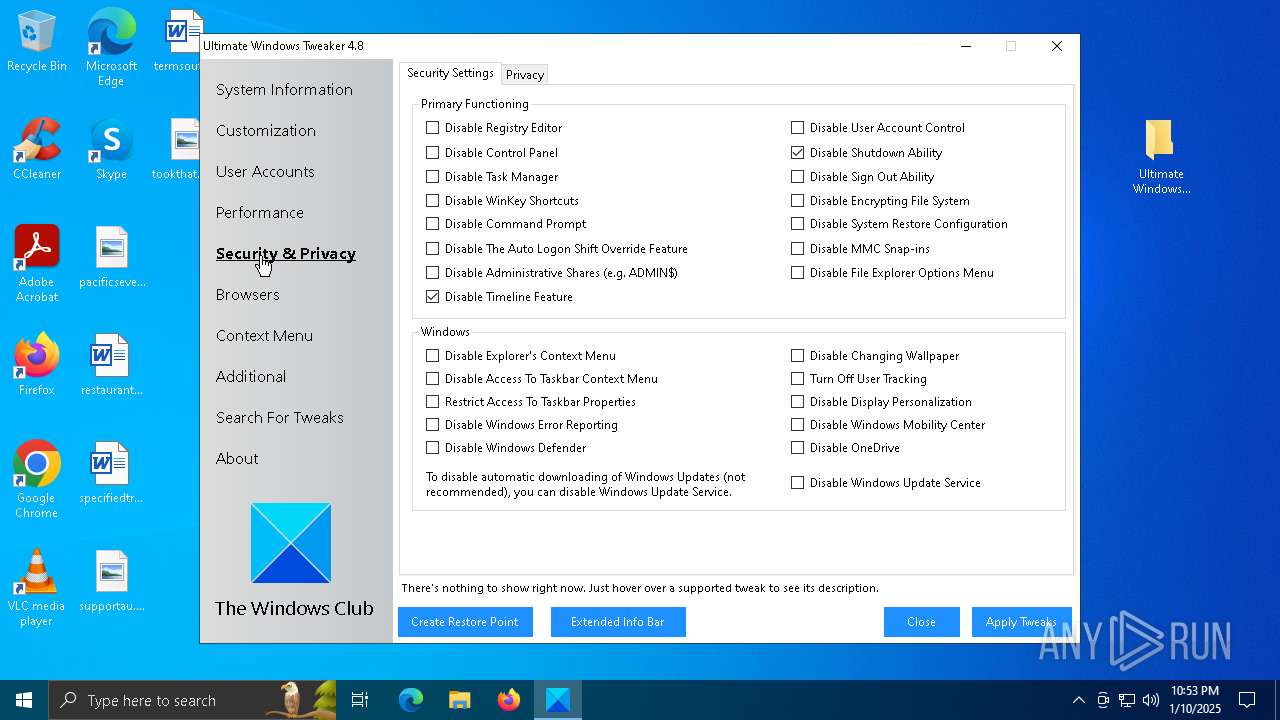
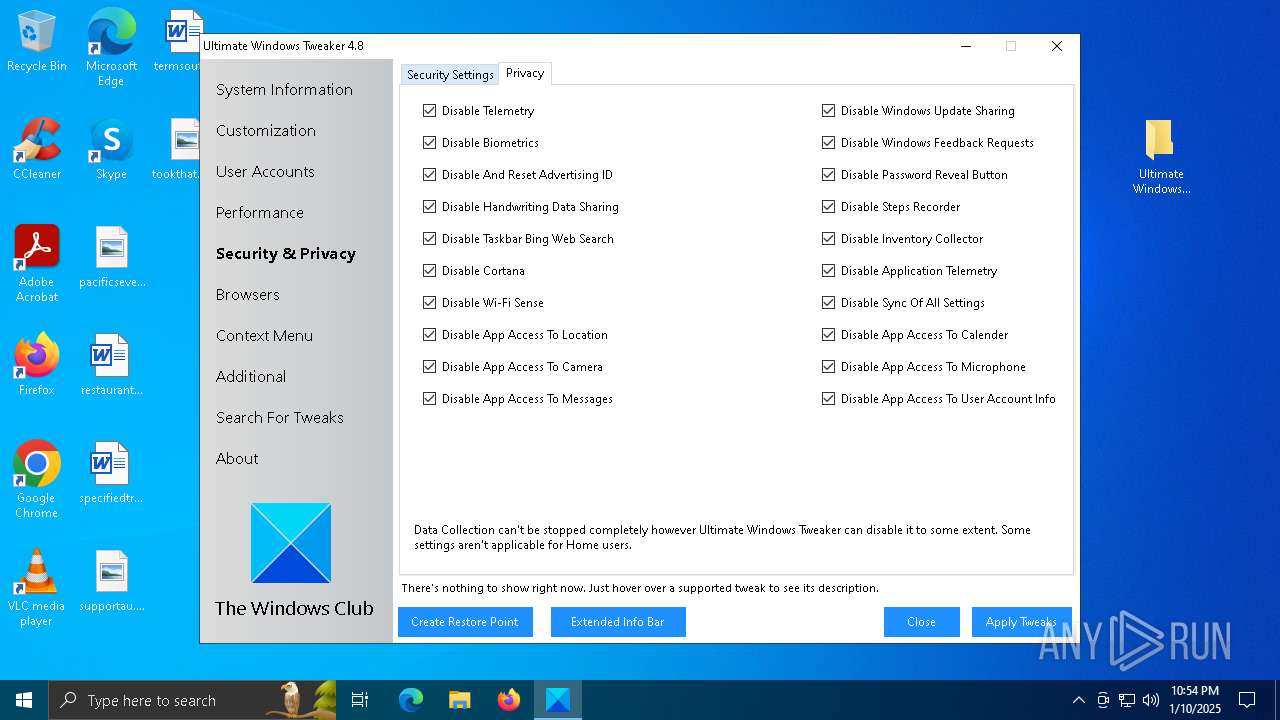
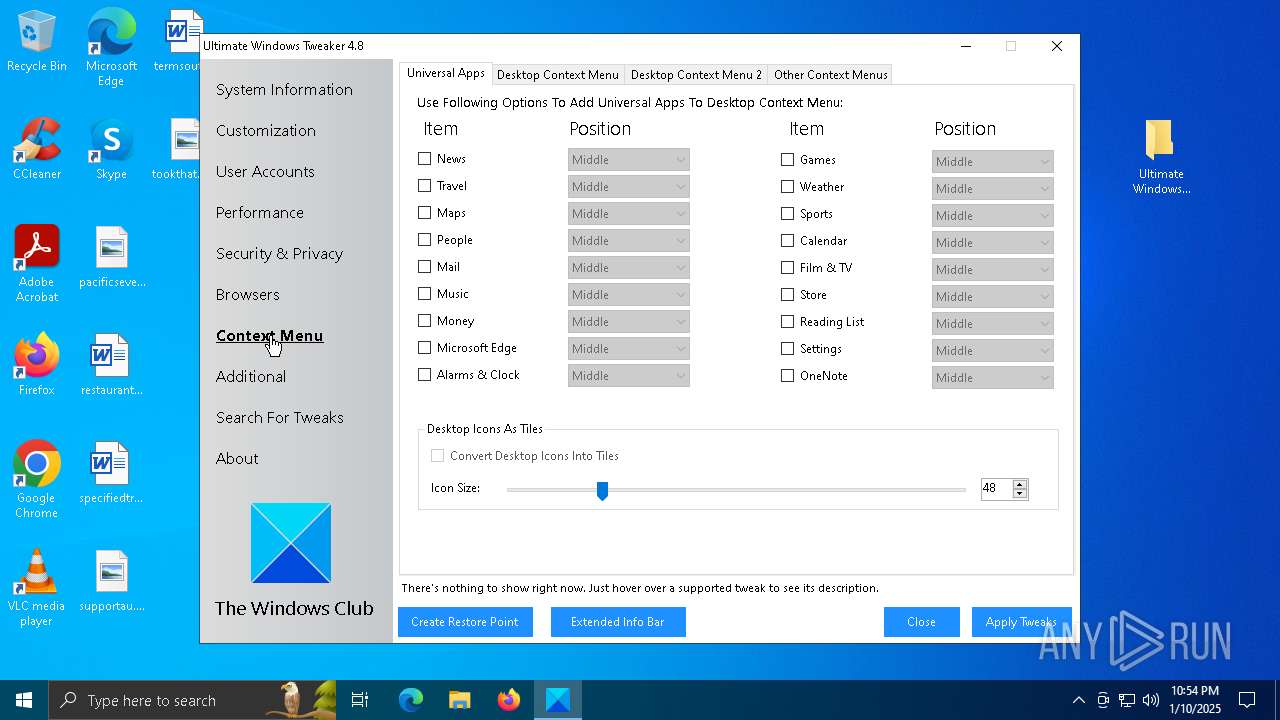
Disables the Command Prompt (cmd)
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Disables the Shutdown in the Start menu
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
UAC/LUA settings modification
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Changes Windows Error Reporting flag
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Creates or modifies Windows services
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Task Manager has been disabled (taskmgr)
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Modify registry editing tools (regedit)
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Changes the autorun value in the registry
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Disables Windows Defender
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
SUSPICIOUS
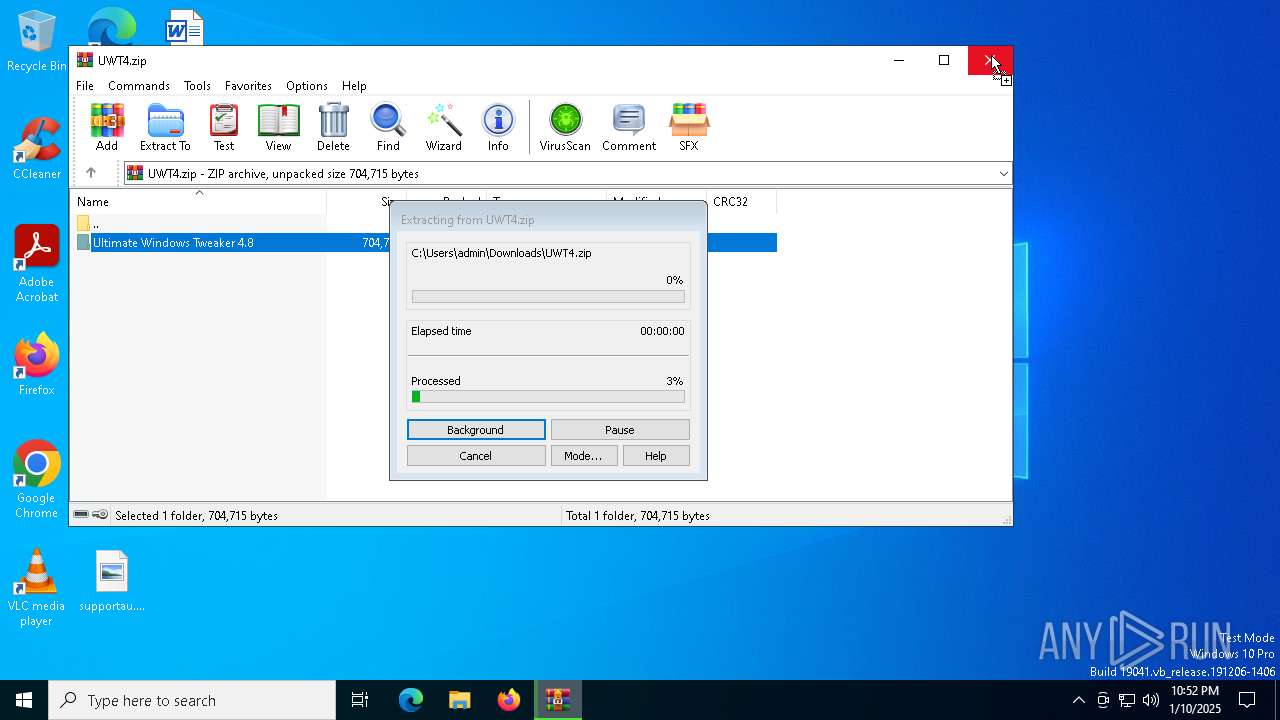
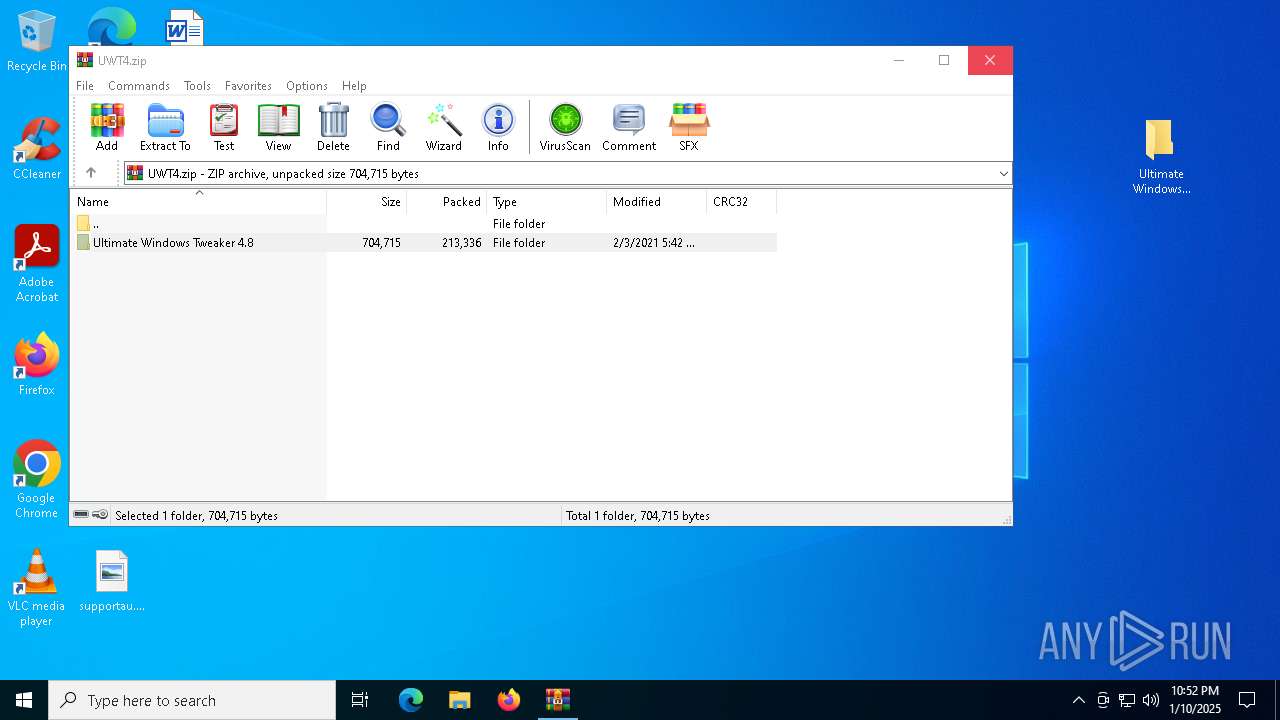
Generic archive extractor
- WinRAR.exe (PID: 1412)
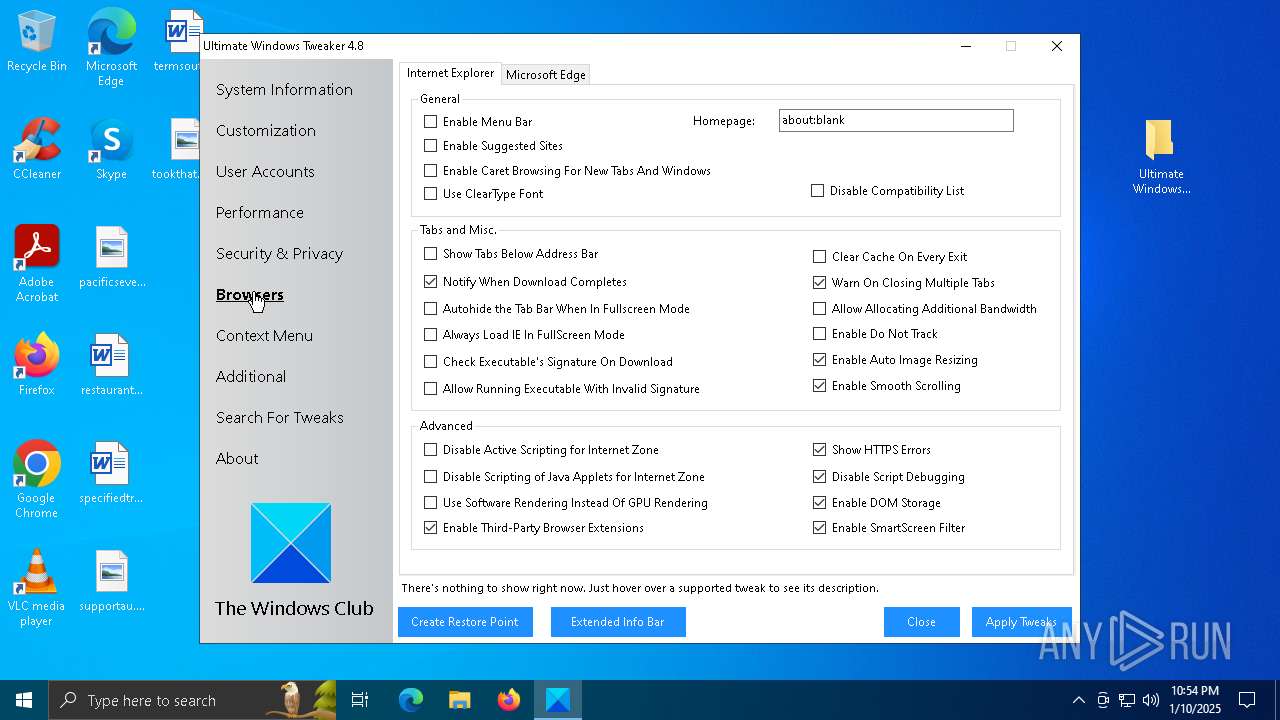
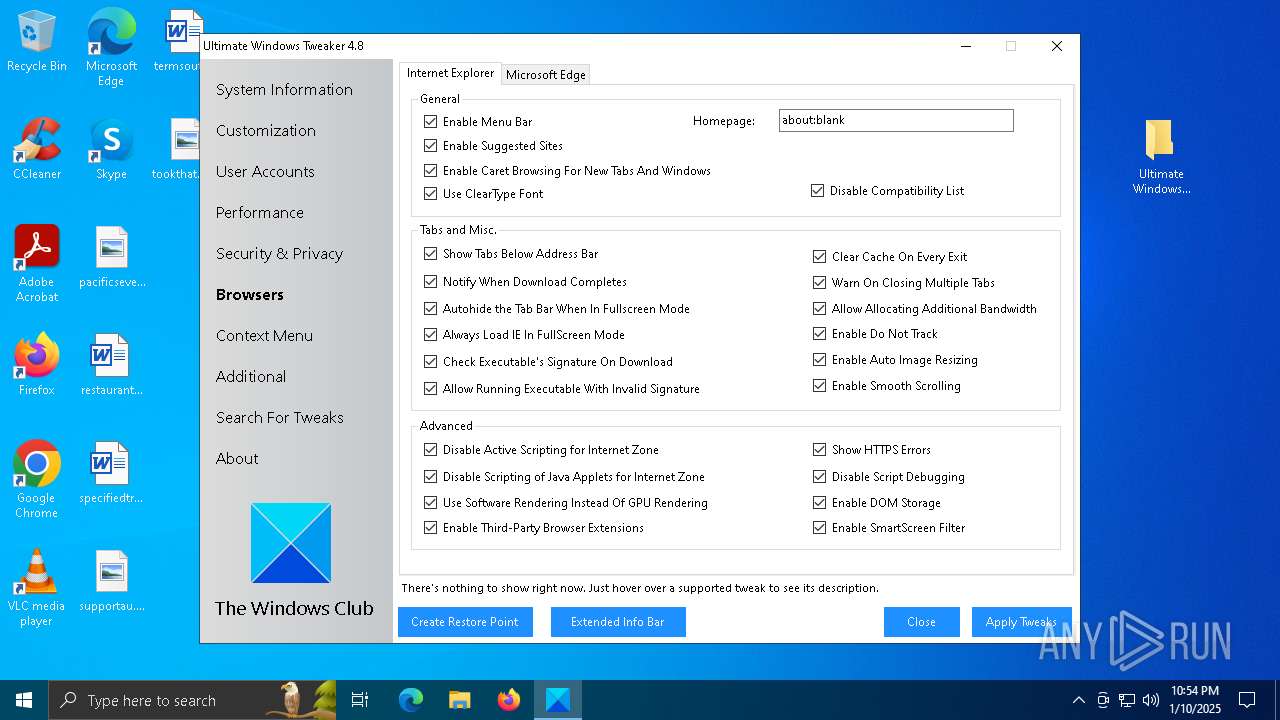
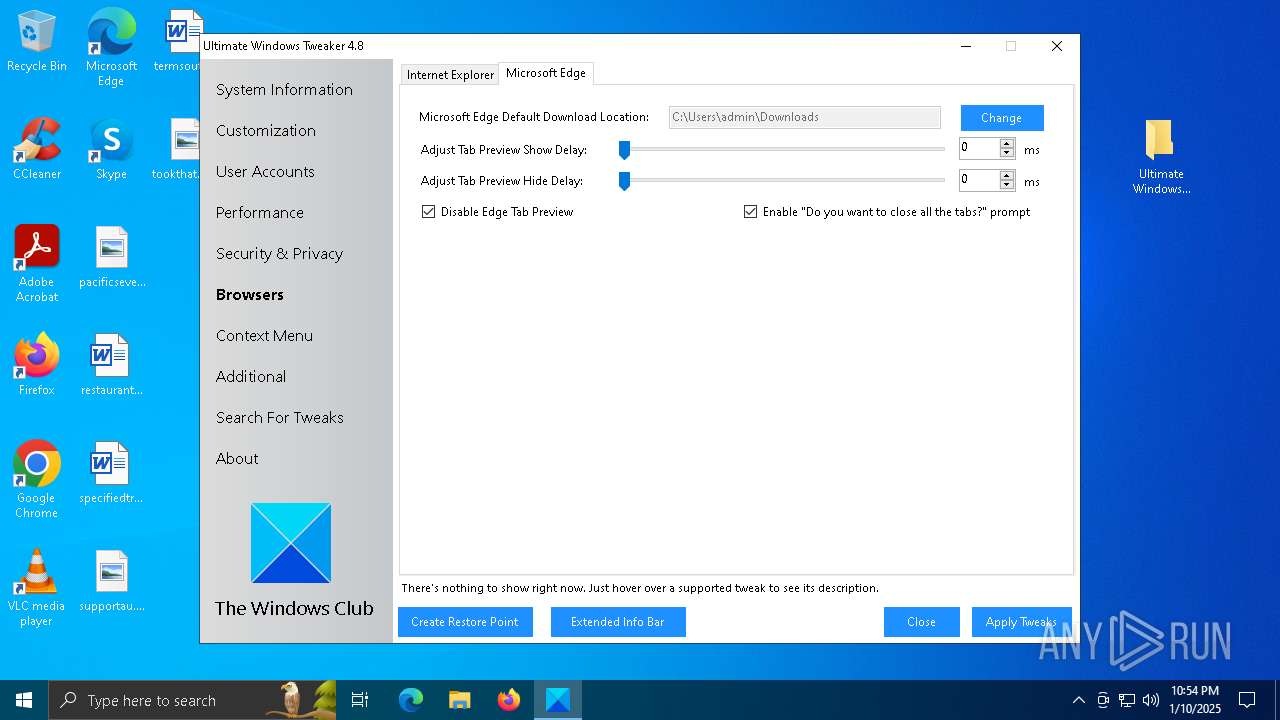
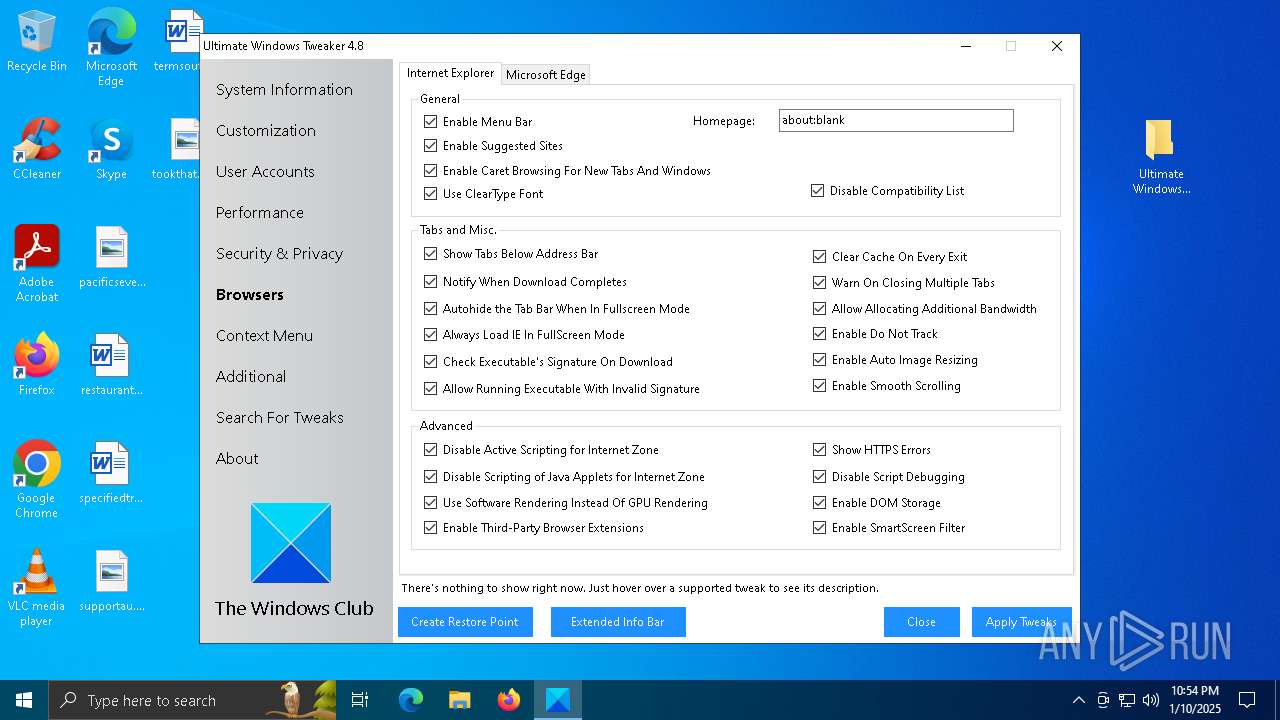
Reads security settings of Internet Explorer
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- StartMenuExperienceHost.exe (PID: 3552)
- StartMenuExperienceHost.exe (PID: 6468)
Reads the date of Windows installation
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- SearchApp.exe (PID: 436)
- StartMenuExperienceHost.exe (PID: 3552)
- SearchApp.exe (PID: 5004)
Executes as Windows Service
- VSSVC.exe (PID: 7104)
Reads Internet Explorer settings
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- mmc.exe (PID: 4164)
Starts CMD.EXE for commands execution
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
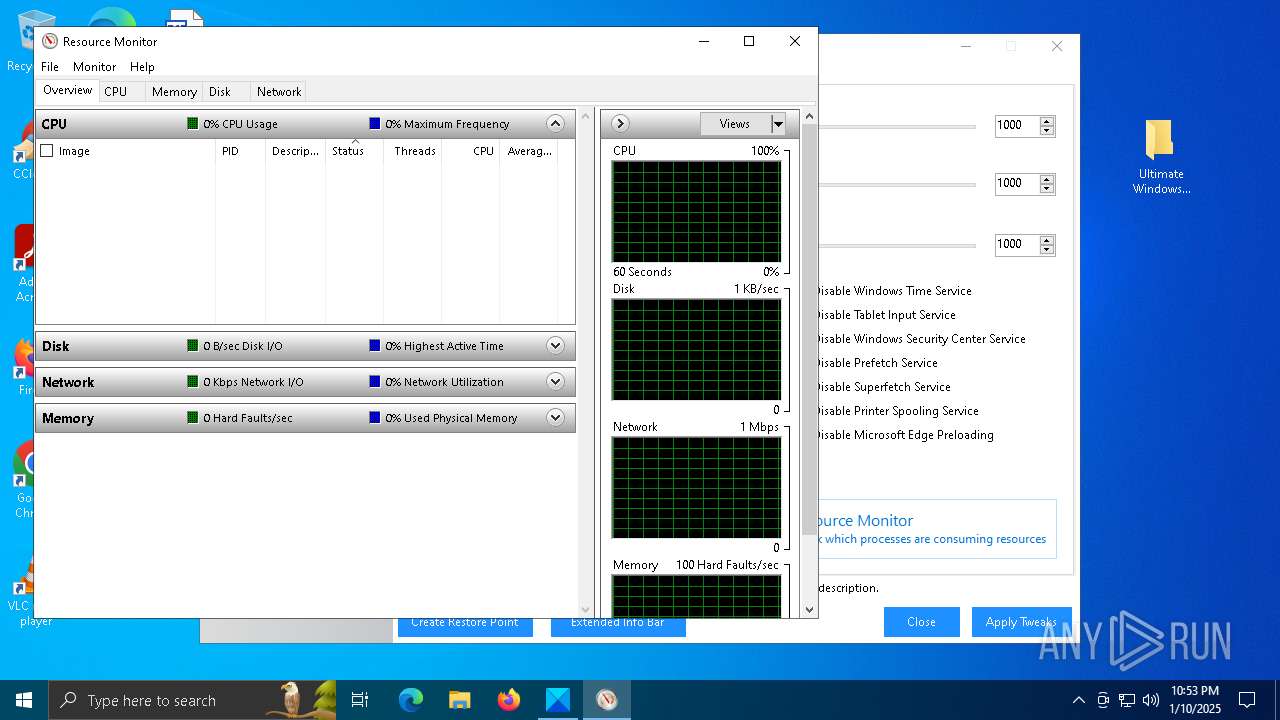
The process checks if it is being run in the virtual environment
- perfmon.exe (PID: 3260)
Changes the desktop background image
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Creates or modifies Windows services
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Changes the title of the Internet Explorer window
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Changes the Home page of Internet Explorer
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 1412)
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- cmd.exe (PID: 2704)
- resmon.exe (PID: 6512)
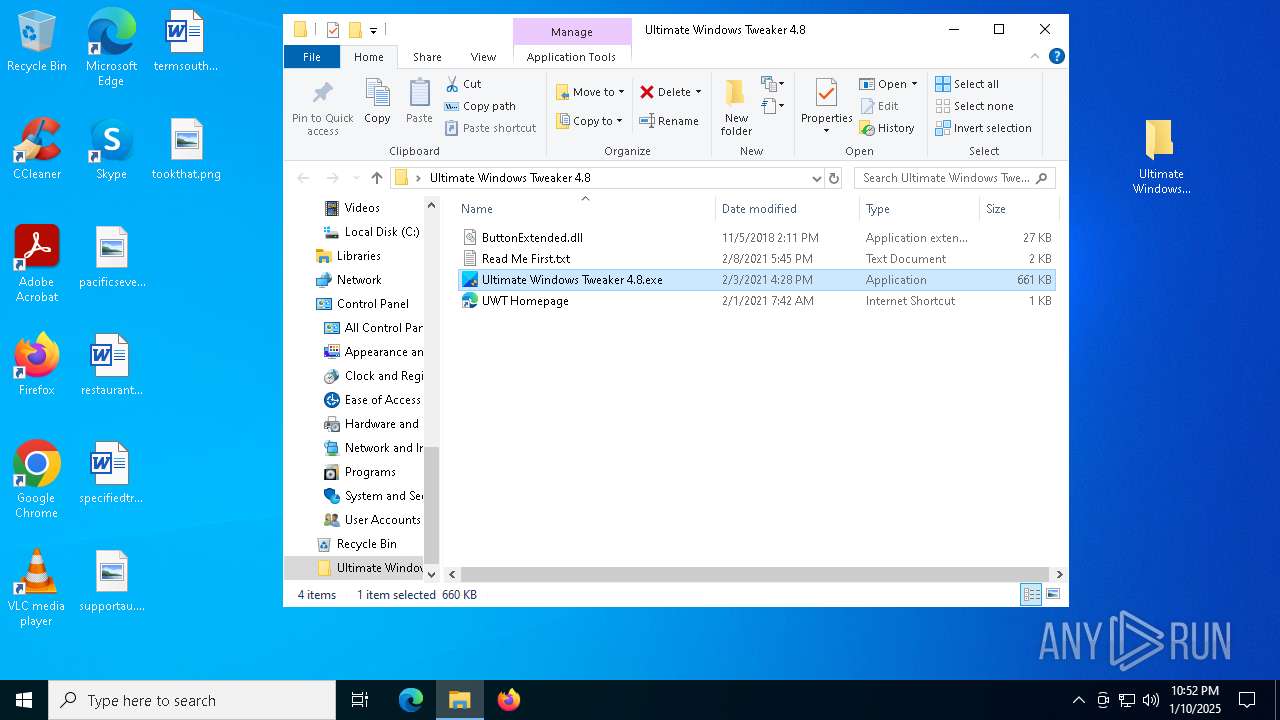
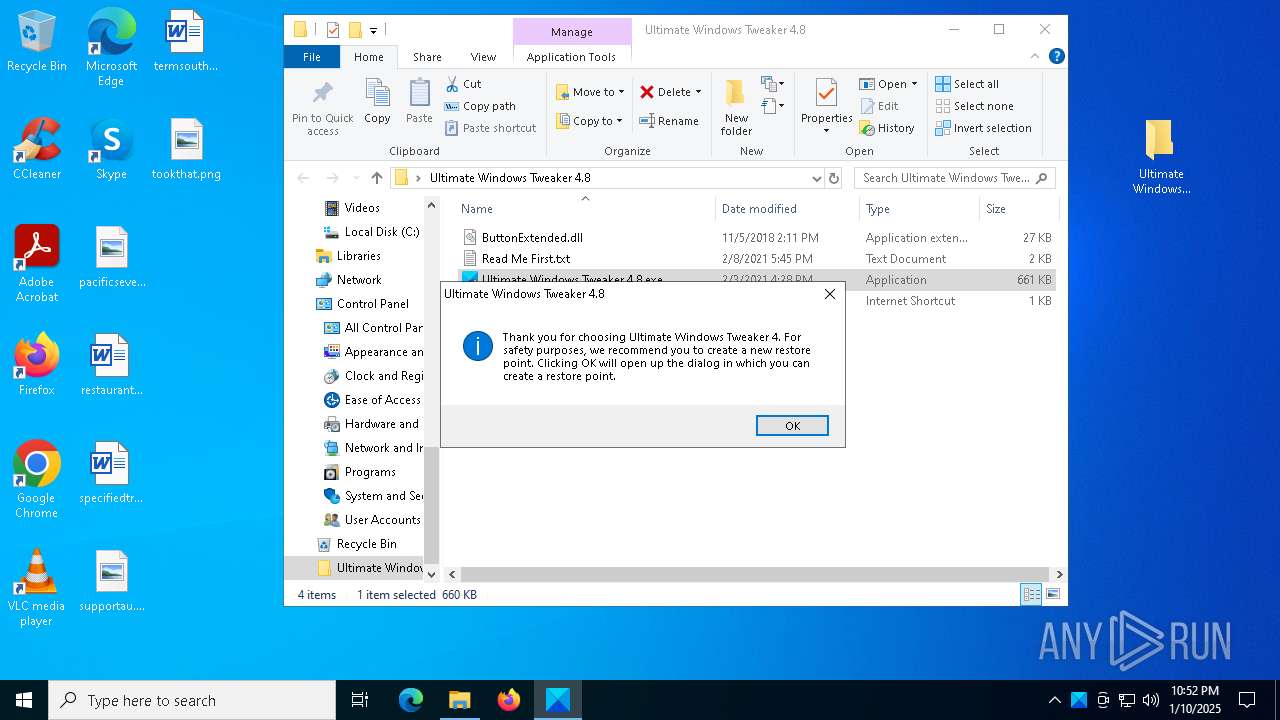
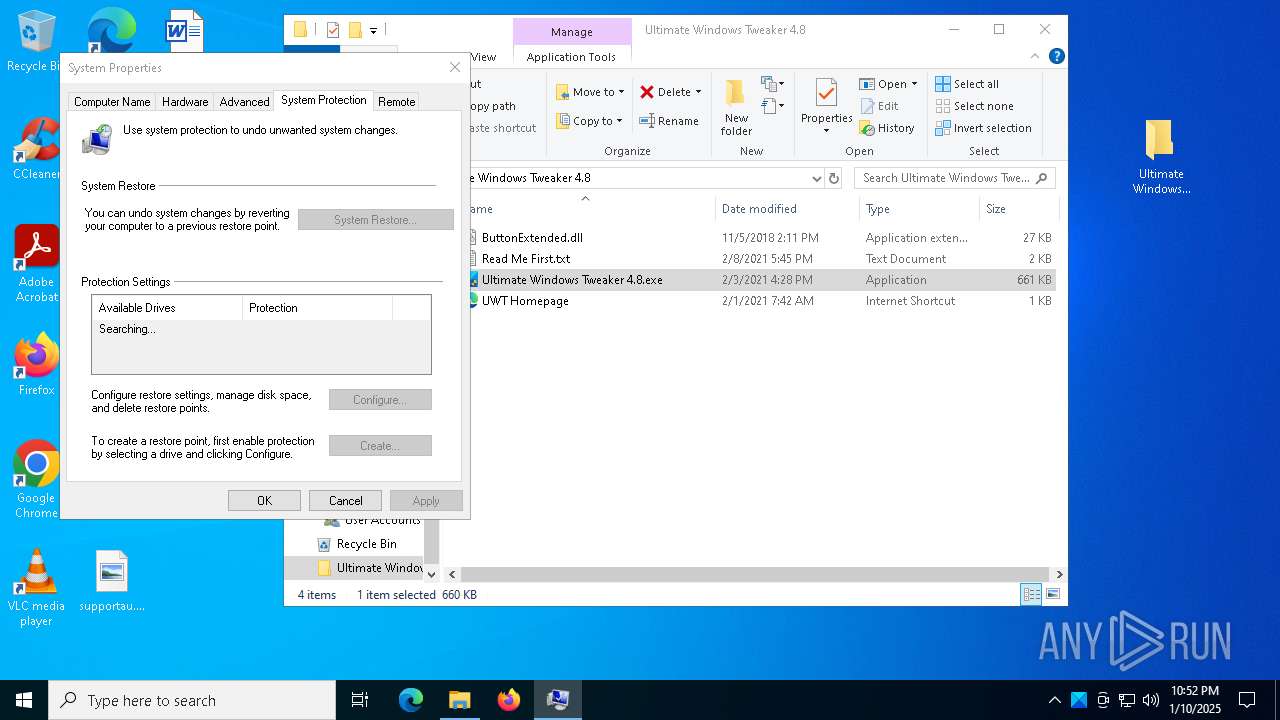
Manual execution by a user
- Ultimate Windows Tweaker 4.8.exe (PID: 6856)
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1412)
Reads the computer name
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- SearchApp.exe (PID: 436)
- TextInputHost.exe (PID: 3140)
- StartMenuExperienceHost.exe (PID: 3552)
- StartMenuExperienceHost.exe (PID: 6468)
- TextInputHost.exe (PID: 7064)
- perfmon.exe (PID: 3260)
Checks supported languages
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- TextInputHost.exe (PID: 3140)
- StartMenuExperienceHost.exe (PID: 3552)
- SearchApp.exe (PID: 436)
- TextInputHost.exe (PID: 7064)
- SearchApp.exe (PID: 5004)
- perfmon.exe (PID: 3260)
- StartMenuExperienceHost.exe (PID: 6468)
Process checks computer location settings
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- SearchApp.exe (PID: 436)
- SearchApp.exe (PID: 5004)
- StartMenuExperienceHost.exe (PID: 6468)
Creates files in the program directory
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Reads the machine GUID from the registry
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- SearchApp.exe (PID: 436)
- SearchApp.exe (PID: 5004)
Reads product name
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Reads CPU info
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Process checks whether UAC notifications are on
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Reads Environment values
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
- SearchApp.exe (PID: 436)
- SearchApp.exe (PID: 5004)
Confuser has been detected (YARA)
- Ultimate Windows Tweaker 4.8.exe (PID: 6908)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 3552)
- StartMenuExperienceHost.exe (PID: 6468)
Checks proxy server information
- SearchApp.exe (PID: 436)
- mmc.exe (PID: 4164)
Reads the software policy settings
- SearchApp.exe (PID: 436)
Creates files or folders in the user directory
- mmc.exe (PID: 4164)
- perfmon.exe (PID: 3260)
Reads security settings of Internet Explorer
- mmc.exe (PID: 4164)
- resmon.exe (PID: 6512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:02:03 23:12:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Ultimate Windows Tweaker 4.8/ |
Total processes
215
Monitored processes
74
Malicious processes
3
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | net stop W32Time | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1016 | cmd.exe /c net stop UsoSvc | C:\Windows\System32\cmd.exe | — | Ultimate Windows Tweaker 4.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | C:\WINDOWS\system32\net1 stop TabletInputService | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\UWT4.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1496 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | C:\WINDOWS\system32\net1 stop W32Time | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2684 | cmd.exe /c net stop UsoSvc | C:\Windows\System32\cmd.exe | — | Ultimate Windows Tweaker 4.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | cmd.exe /c net stop WaaSMedicSvc | C:\Windows\System32\cmd.exe | — | Ultimate Windows Tweaker 4.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
37 195
Read events
36 812
Write events
371
Delete events
12
Modification events
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\UWT4.zip | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (1412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
3
Suspicious files
53
Text files
118
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 436 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\fvNdnrKxhhxDQUEi09cCaSWpzzE[1].css | text | |
MD5:15DC838A1A66277F9F4D915124DFFBBC | SHA256:9C947D5F732431197DA9DB1F159CB3D4CDC5DBFE55FDC0A9513E571FF31236A1 | |||
| 436 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:AA8D25351910D5CAB677E04ABDAE4271 | SHA256:3F4DC7C9A61AAA036A96FD81576E5F62D3F6D13726D52C3442D33058F78F5517 | |||
| 436 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\6hU_LneafI_NFLeDvM367ebFaKQ[1].js | s | |
MD5:C6C21B7634D82C53FB86080014D86E66 | SHA256:D39E9BA92B07F4D50B11A49965E9B162452D7B9C9F26D9DCB07825727E31057E | |||
| 436 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\Swi4yFavETfuSZ9mHxnUvb4UdTw[1].js | s | |
MD5:B2C3CBF8A1D940D6C83D59A67486675C | SHA256:08EA9109346E9018ED50567503D2C141F7A84CFDE80EB25E97FDDCFE270BAA67 | |||
| 436 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\mIBK4Tj4MH4TuENc-SRjlybWA2M[1].css | text | |
MD5:61218F90D3B3B1F74B9253D4E5DDF682 | SHA256:0553F7C64CC8A8034532FF32F86F5B0DDB061D03843B66C0868CDCA1674E03CC | |||
| 436 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\95d9a2a97a42f02325559b453ba7f8fe839baa18.tbres | binary | |
MD5:1711E6FCB01F2F29626BBC5279E29976 | SHA256:73BB3BD15DB9051FD964E17CF3A381FF88D37C634007379EB633D8B63A66899B | |||
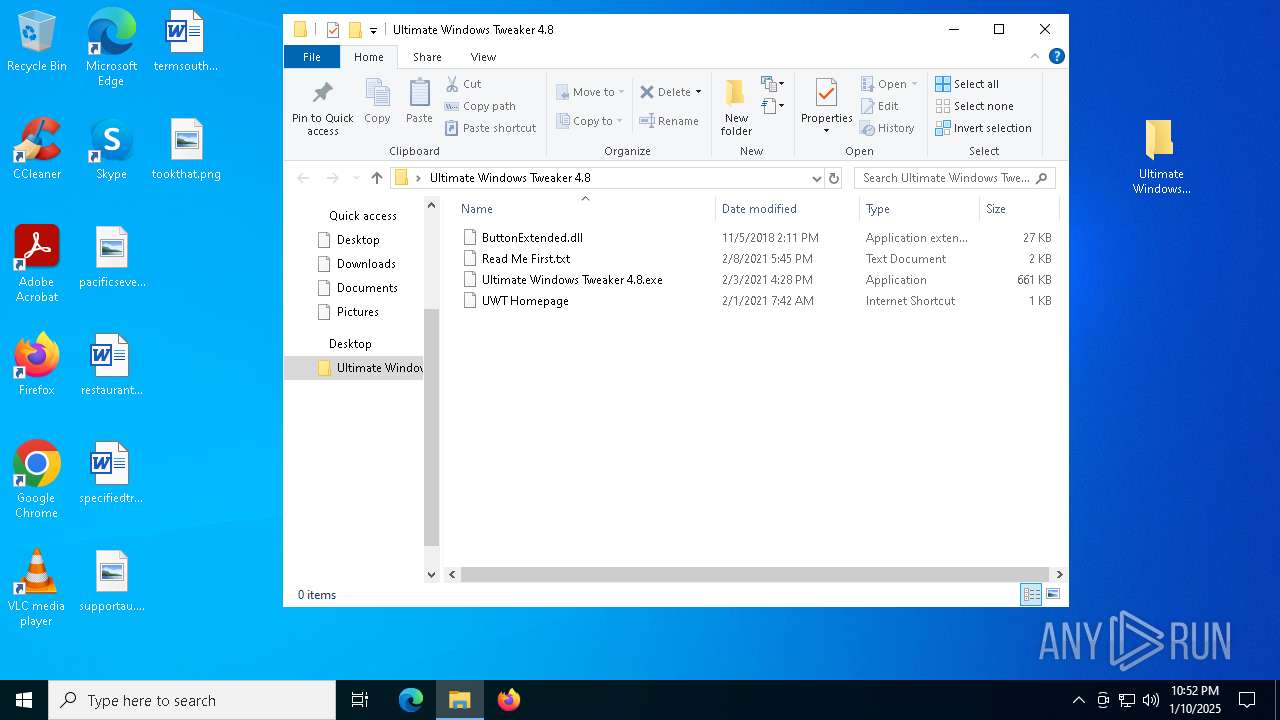
| 1412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1412.34326\Ultimate Windows Tweaker 4.8\Read Me First.txt | text | |
MD5:A0AF49B80631107F6D3C277562F0D107 | SHA256:BC5910676B5CF8AB9C4F0D6FFC98FF8351E9386EA81E75A781FF988AD9DFB4DA | |||
| 1412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1412.34326\Ultimate Windows Tweaker 4.8\UWT Homepage.url | url | |
MD5:2D98D02E794606F540235133D238FDFA | SHA256:9C49F370899CDC0F7DA299BF038AA374D4D4DFDB1E5EBBB2325E086BC893865D | |||
| 1412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1412.34326\Ultimate Windows Tweaker 4.8\Ultimate Windows Tweaker 4.8.exe | executable | |
MD5:DFD18EABCFA63CE63FDBEBE4673E99C8 | SHA256:B25B8E40616136045F021A9AC1E2143B3460CAED08C01606820CA4FA4107E5F2 | |||
| 1412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1412.34326\Ultimate Windows Tweaker 4.8\ButtonExtended.dll | executable | |
MD5:D45CAB94CFB2D3DD1B7BBAD86090E896 | SHA256:11692A5C5001628E294AE9E1146ABD4B4470E81F21883F80A7AF7FE6D197D44B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
48
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
4144 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6288 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
3864 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1016 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |