| File name: | a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl |
| Full analysis: | https://app.any.run/tasks/ec6f2ff6-3b7d-4b1f-9d22-9eb18670b813 |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 18:02:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 19DBEC50735B5F2A72D4199C4E184960 |
| SHA1: | 6FED7732F7CB6F59743795B2AB154A3676F4C822 |
| SHA256: | A3D5715A81F2FBEB5F76C88C9C21EEEE87142909716472F911FF6950C790C24D |
| SSDEEP: | 192:sIvxdXSQeWSg9JJS/lcIEiwqZKBkDFR43xWTM3LHn8f26gyr6yfFCj3rC:sMVSaSEglcIqq3agmLc+6gyWqFCje |
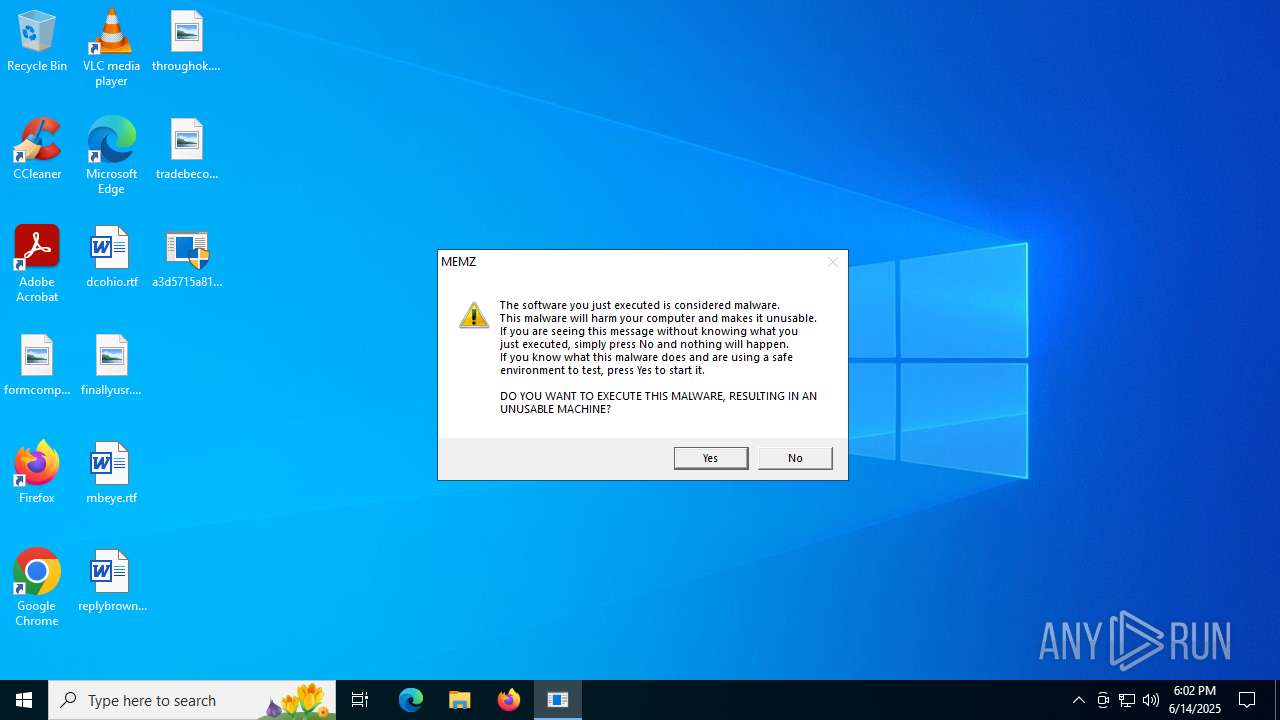
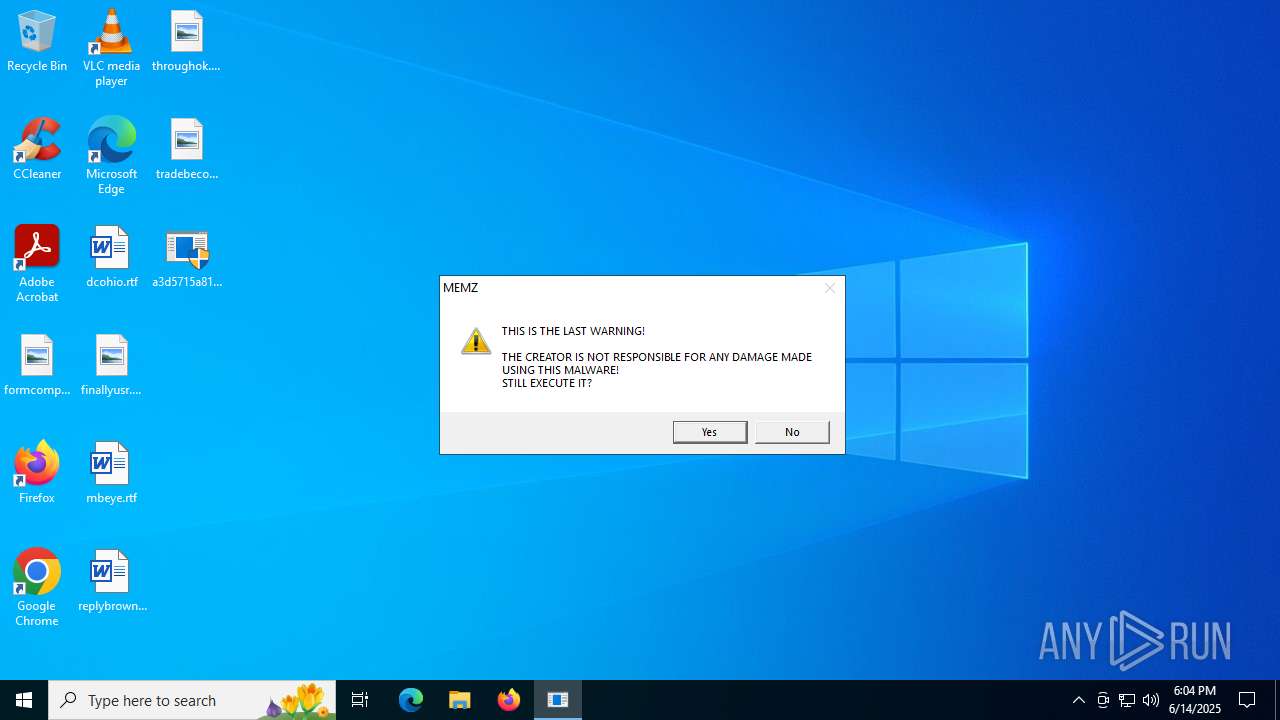
MALICIOUS
MEMZ has been detected (YARA)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 1044)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 7000)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 6348)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 1028)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5528)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
SUSPICIOUS
Reads security settings of Internet Explorer
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
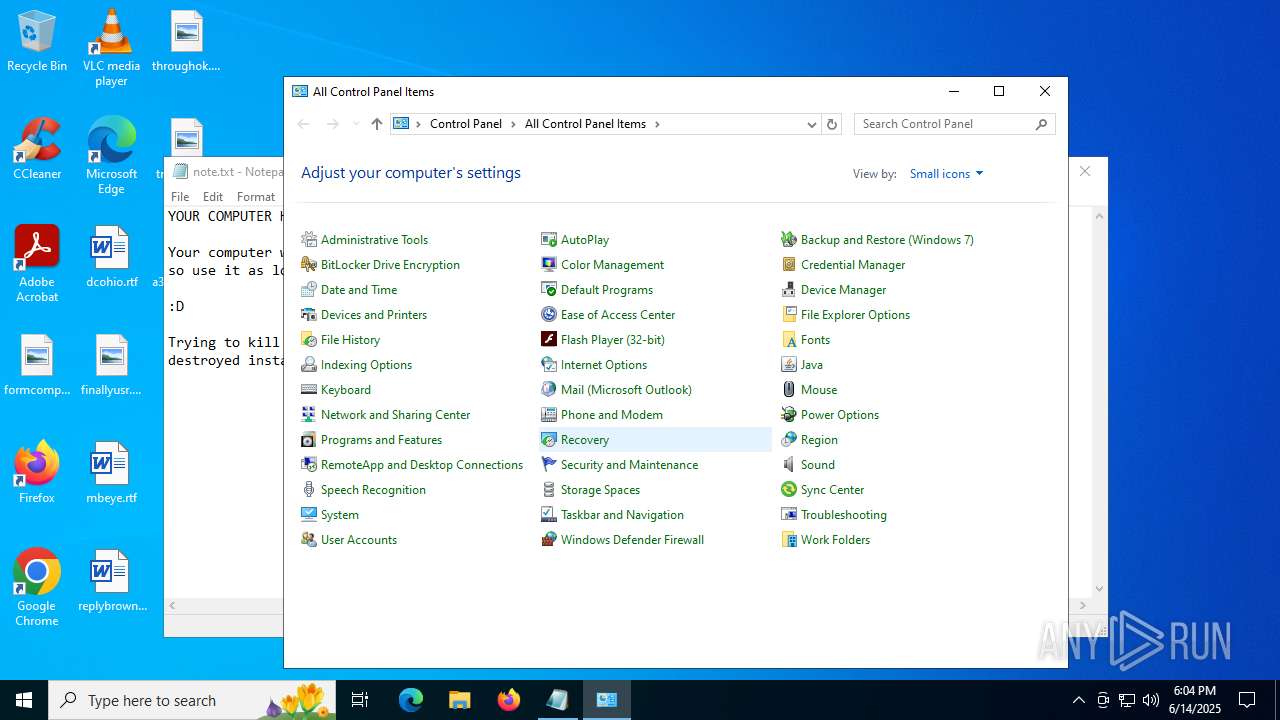
Application launched itself
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
There is functionality for taking screenshot (YARA)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 6348)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 1044)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 1028)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 7000)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5528)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
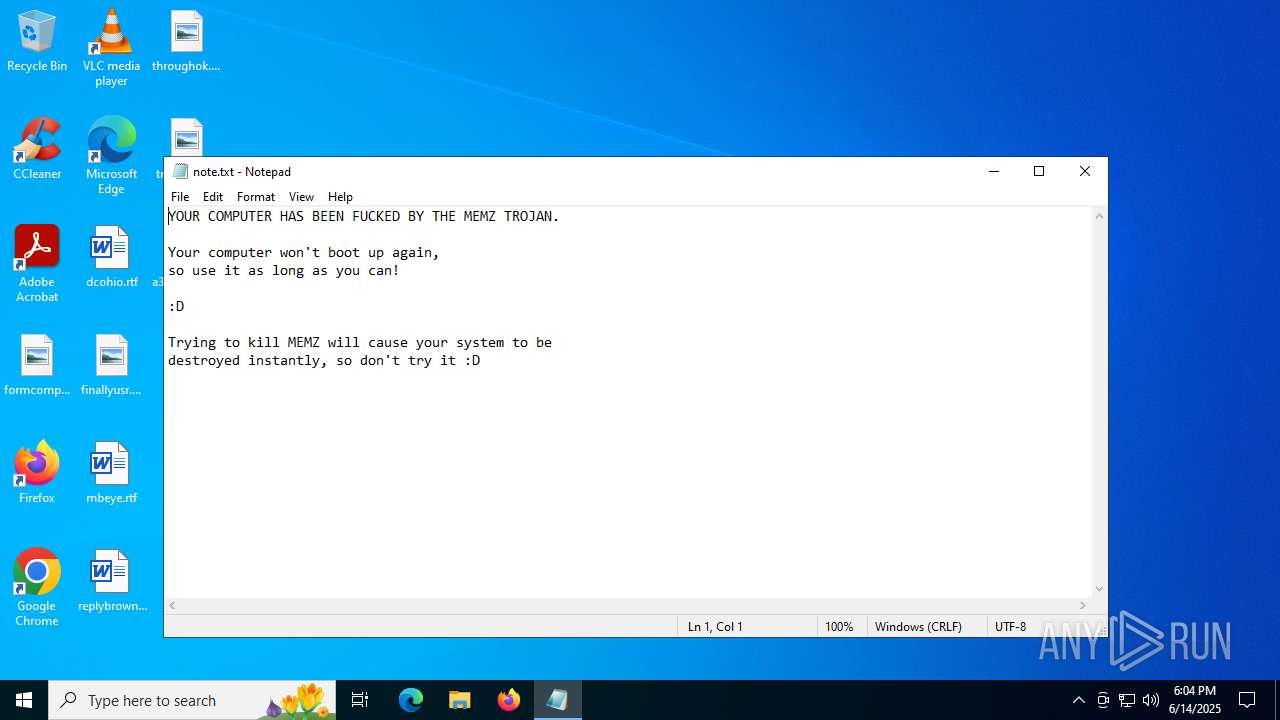
Creates file in the systems drive root
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
- notepad.exe (PID: 1652)
Start notepad (likely ransomware note)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
INFO
Checks supported languages
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 1044)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 1028)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 6348)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5528)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 7000)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
Reads the computer name
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
Process checks computer location settings
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 504)
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1652)
Reads the software policy settings
- slui.exe (PID: 6304)
Application launched itself
- msedge.exe (PID: 3588)
- msedge.exe (PID: 5644)
- msedge.exe (PID: 2628)
Checks proxy server information
- slui.exe (PID: 6304)
Reads the machine GUID from the registry
- a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe (PID: 5900)
Manual execution by a user
- msedge.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:10 12:59:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3072 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
163
Monitored processes
27
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe" | C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe" /watchdog | C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe" /watchdog | C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe" | C:\Users\admin\Desktop\a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1652 | "C:\Windows\System32\notepad.exe" \note.txt | C:\Windows\SysWOW64\notepad.exe | — | a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3556,i,12149513827207470414,7103724459849943021,262144 --variations-seed-version --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2428 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
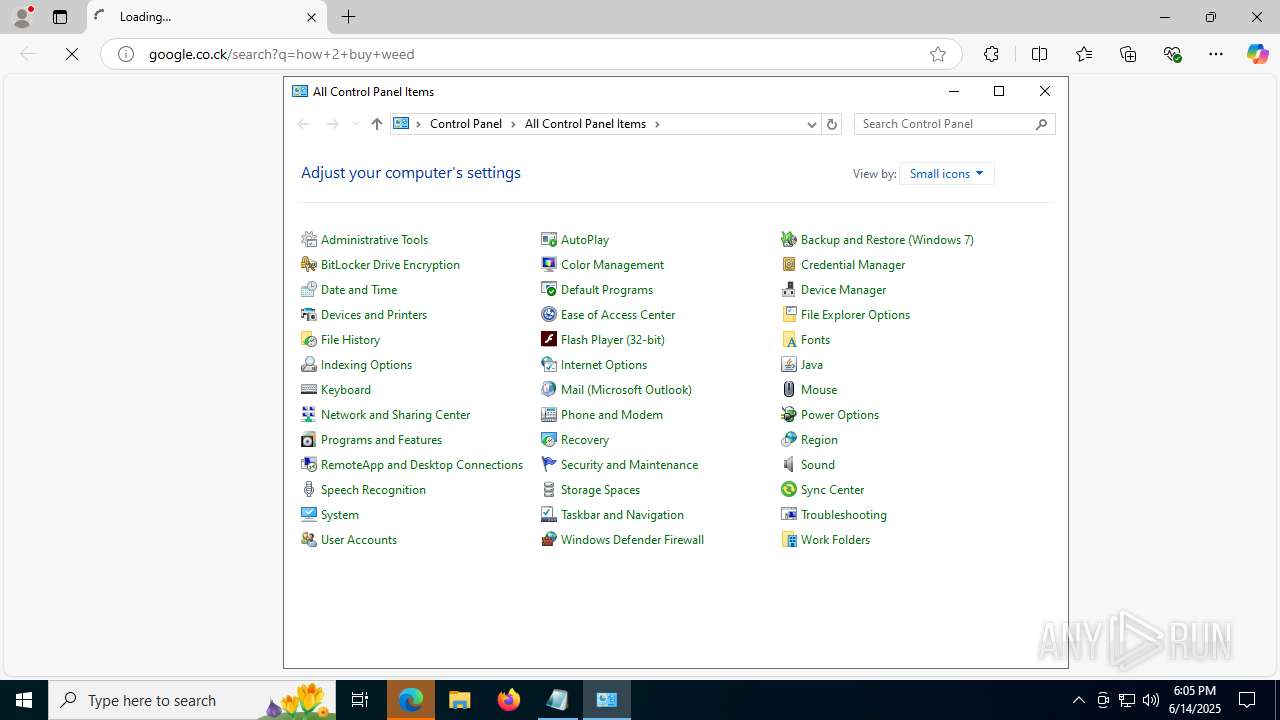
| 2628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate --single-argument http://google.co.ck/search?q=how+2+buy+weed | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2228,i,12149513827207470414,7103724459849943021,262144 --variations-seed-version --mojo-platform-channel-handle=2616 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3588 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://google.co.ck/search?q=how+2+buy+weed | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
11 131
Read events
11 104
Write events
27
Delete events
0
Modification events
| (PID) Process: | (2428) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2428) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 000000000400000003000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (2428) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (5900) a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5900) a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5900) a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3588) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3588) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
| (PID) Process: | (5644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
5
Suspicious files
17
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5900 | a3d5715a81f2fbeb5f76c88c9c21eeee87142909716472f911ff6950c790c24d_rl.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF19afed.TMP | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF19affd.TMP | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF19affd.TMP | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF19affd.TMP | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF19b00c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
50
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5908 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.73:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.3:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 23.9 Kb | whitelisted |
1948 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
1948 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
1948 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
1948 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5908 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2292 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5908 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5908 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |