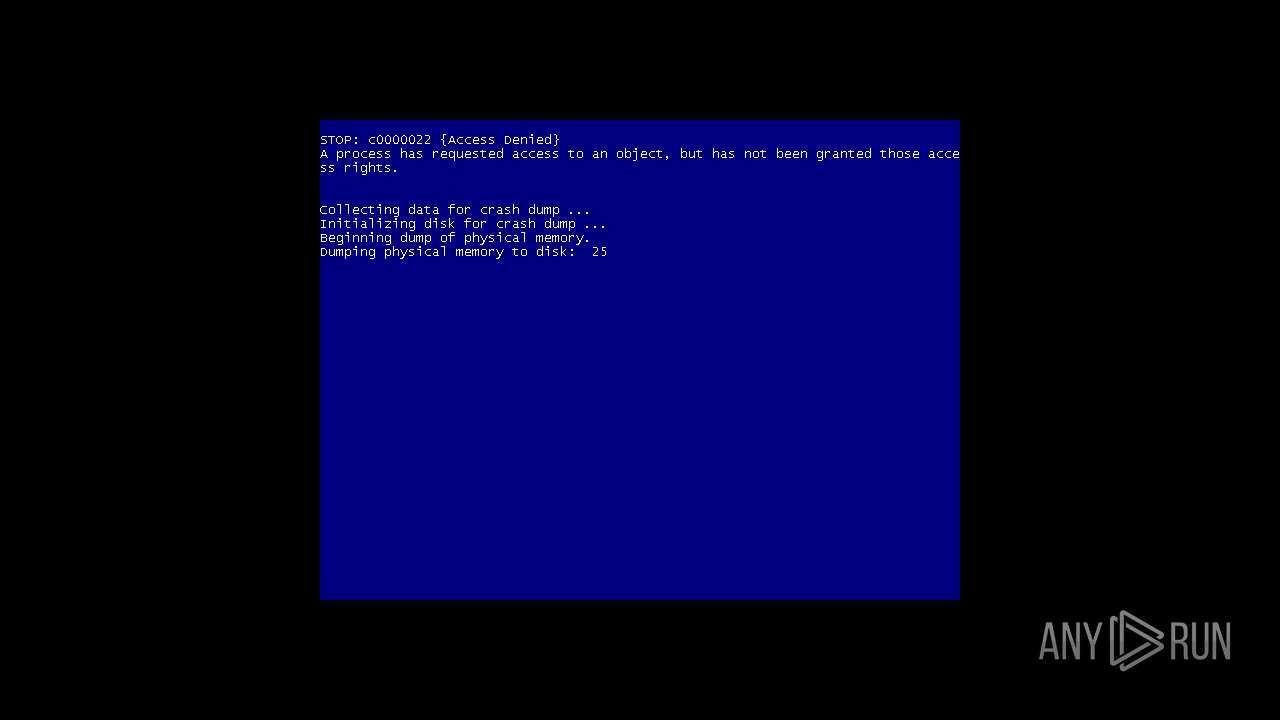
| File name: | Endermanch@MEMZ.exe |
| Full analysis: | https://app.any.run/tasks/d9e66d32-ffc8-45a1-b5e3-c513f69526ff |
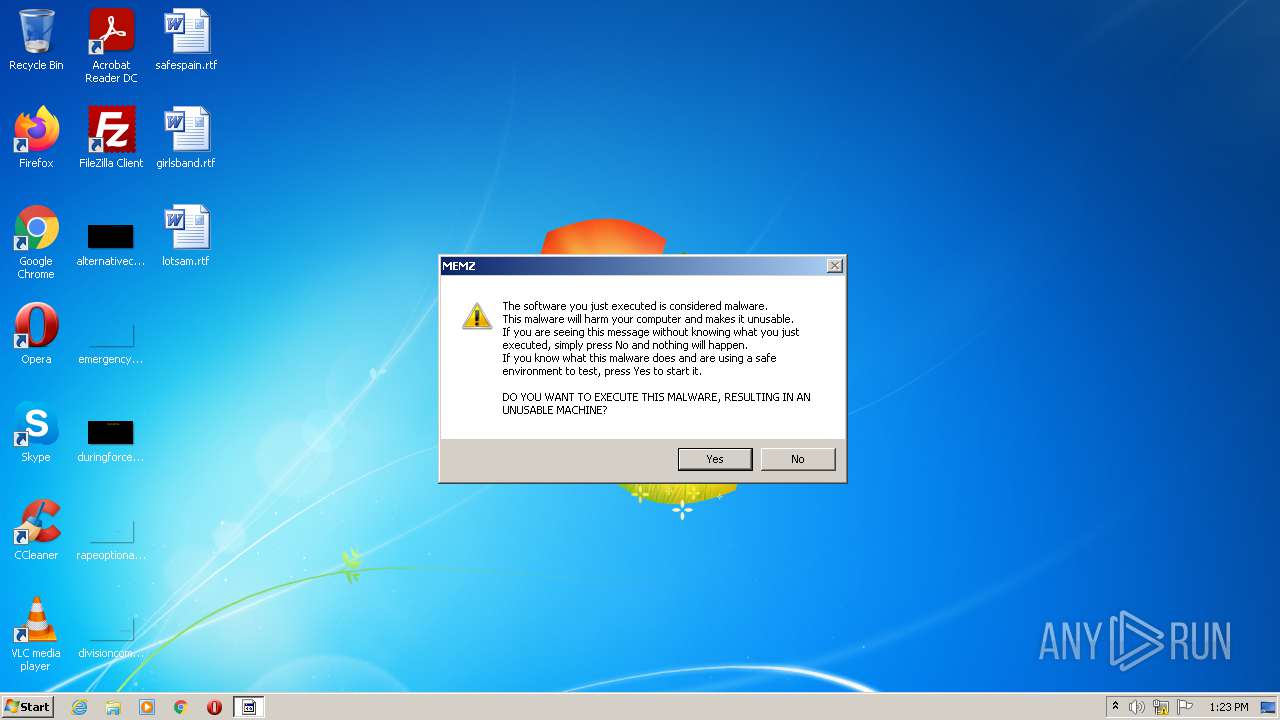
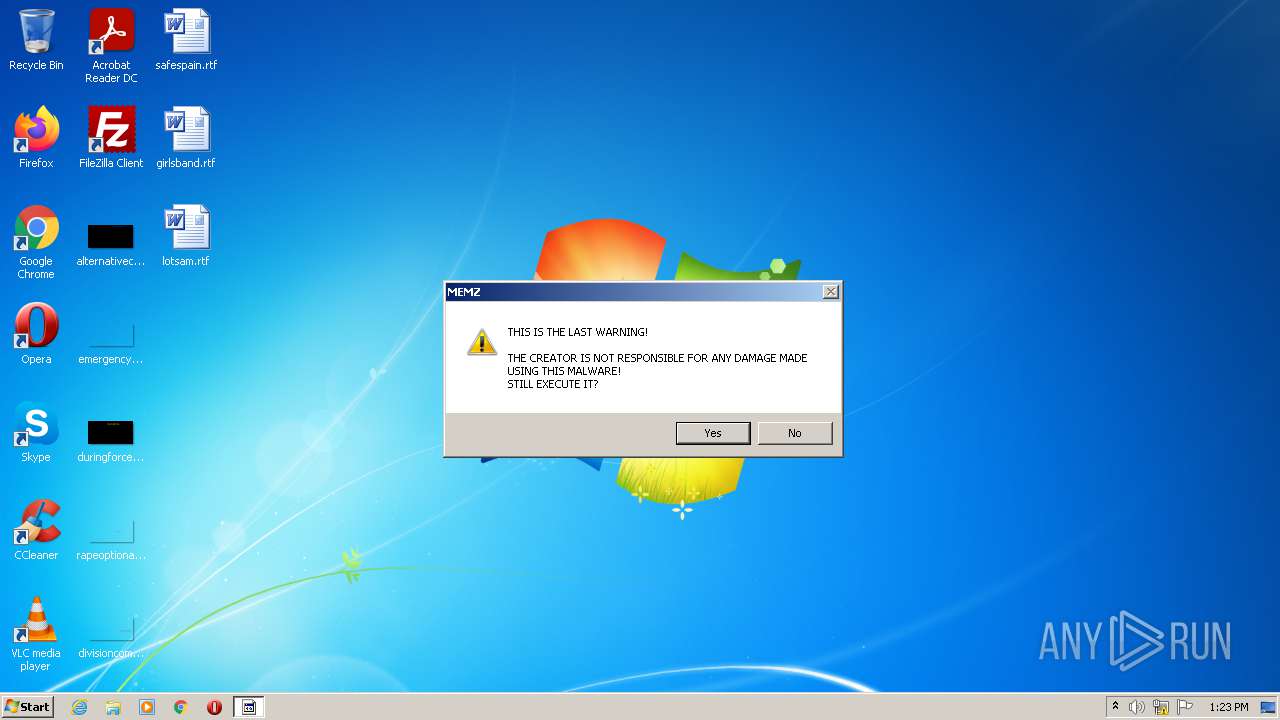
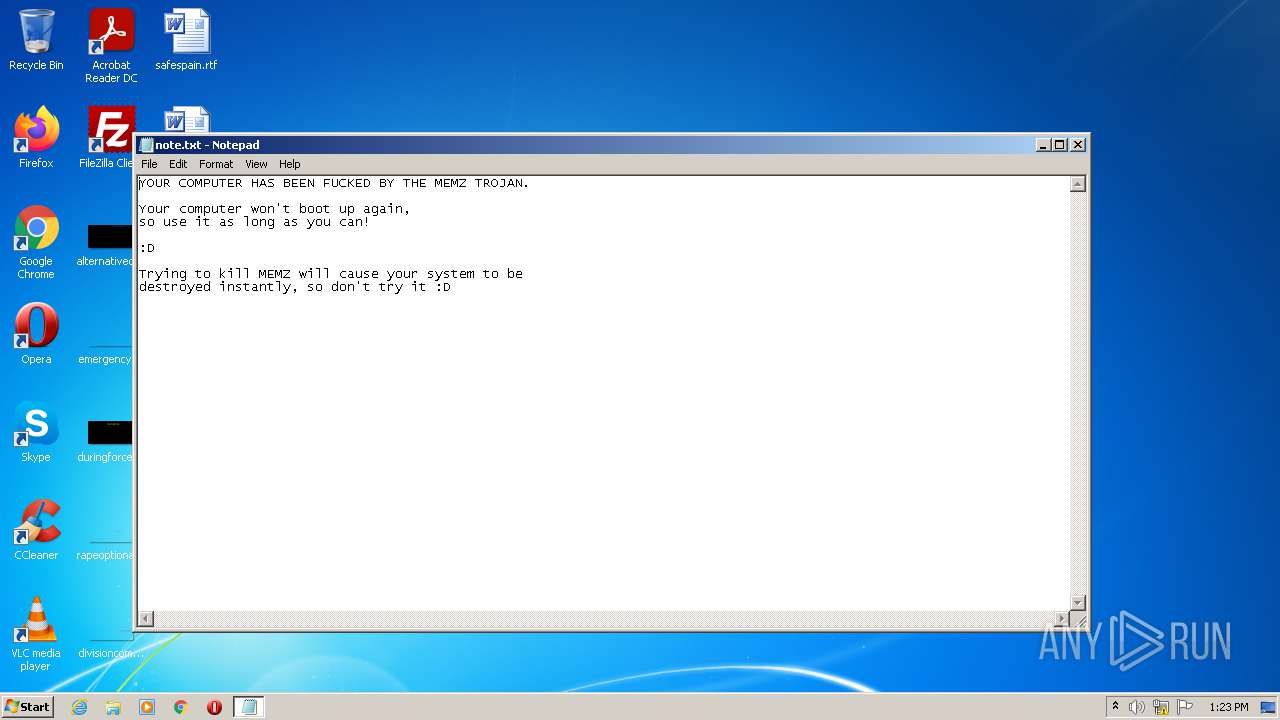
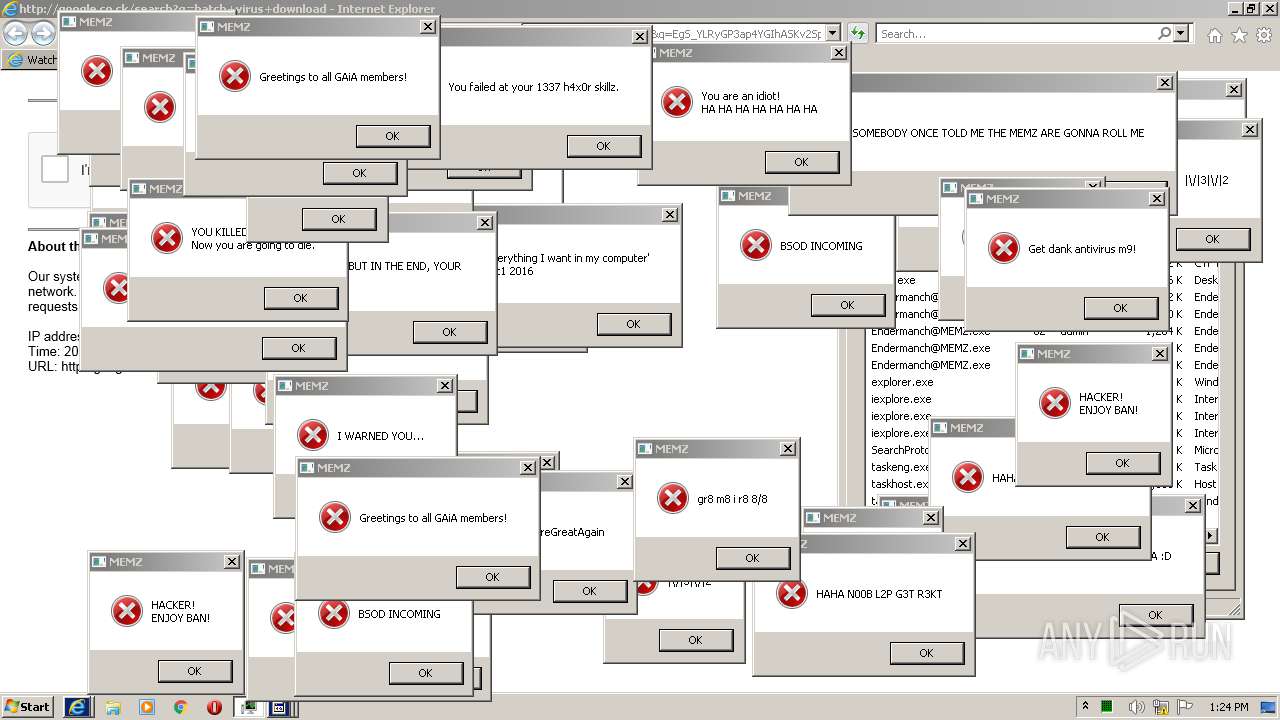
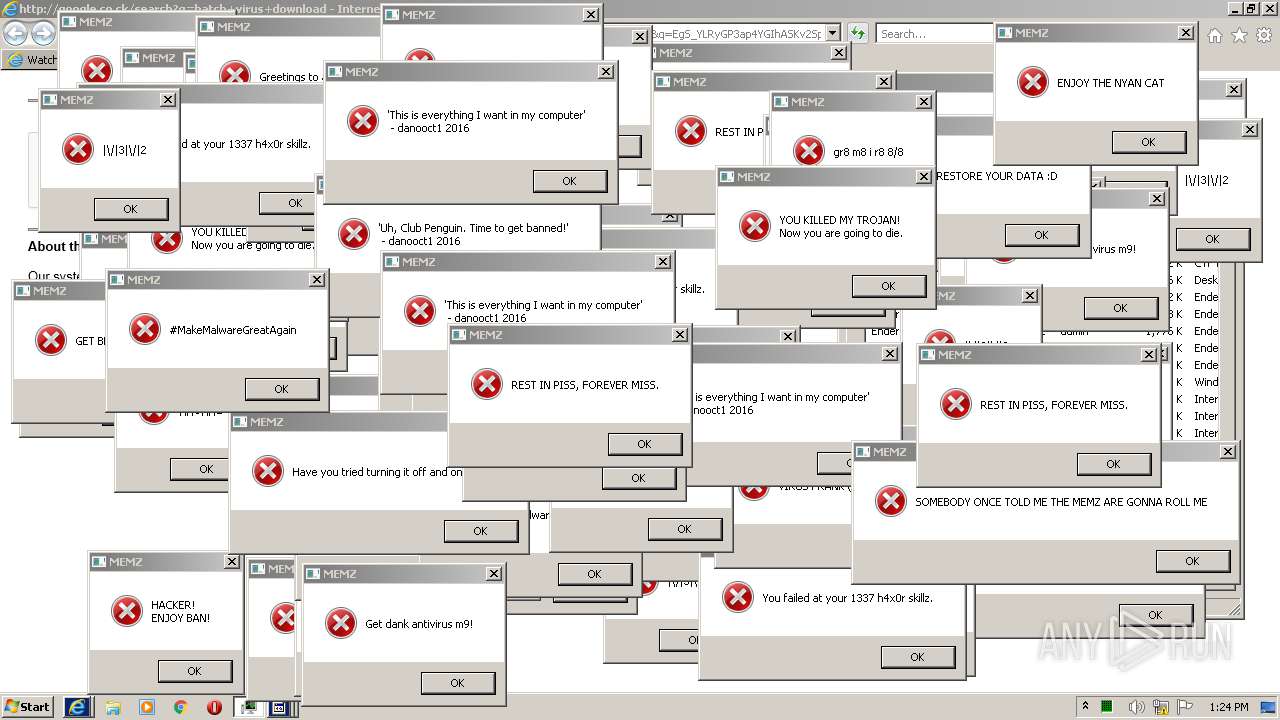
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2021, 12:23:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 19DBEC50735B5F2A72D4199C4E184960 |
| SHA1: | 6FED7732F7CB6F59743795B2AB154A3676F4C822 |
| SHA256: | A3D5715A81F2FBEB5F76C88C9C21EEEE87142909716472F911FF6950C790C24D |
| SSDEEP: | 192:sIvxdXSQeWSg9JJS/lcIEiwqZKBkDFR43xWTM3LHn8f26gyr6yfFCj3r:sMVSaSEglcIqq3agmLc+6gyWqFCj |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- Endermanch@MEMZ.exe (PID: 2880)
- Endermanch@MEMZ.exe (PID: 2384)
- Endermanch@MEMZ.exe (PID: 3616)
- Endermanch@MEMZ.exe (PID: 2324)
- Endermanch@MEMZ.exe (PID: 2584)
- Endermanch@MEMZ.exe (PID: 1048)
- Endermanch@MEMZ.exe (PID: 3644)
Reads the computer name
- Endermanch@MEMZ.exe (PID: 2324)
- Endermanch@MEMZ.exe (PID: 3644)
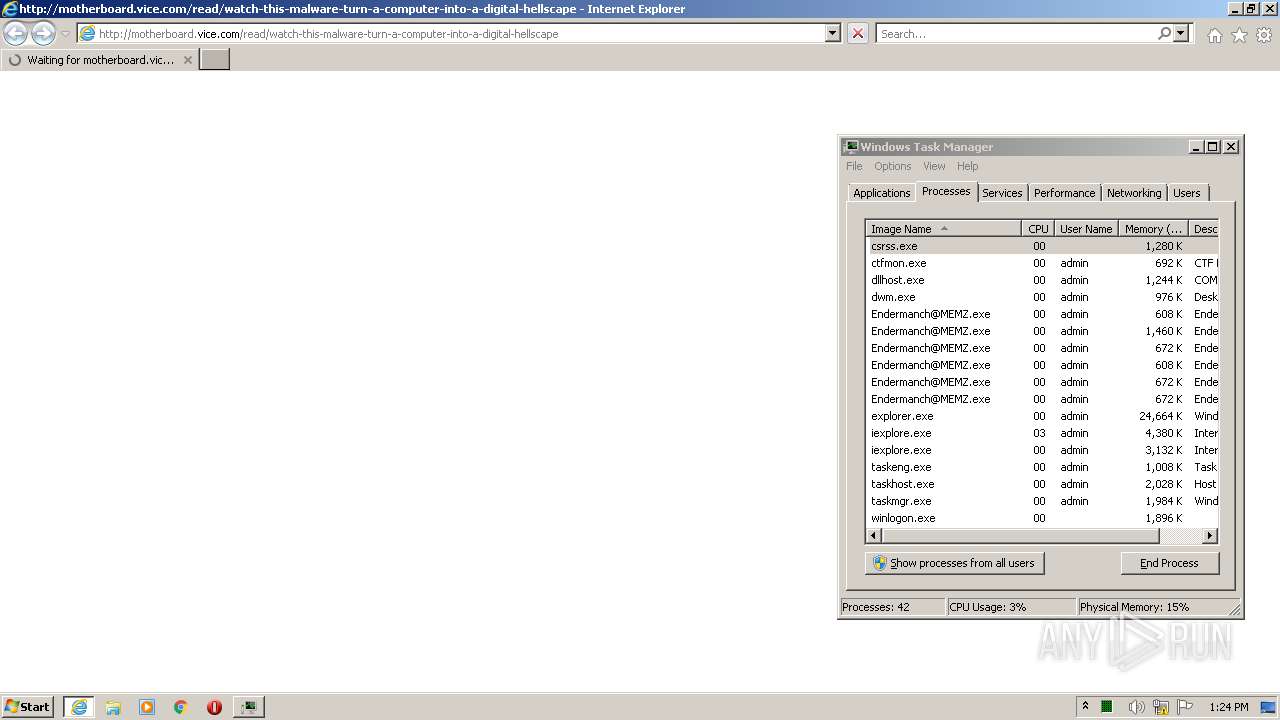
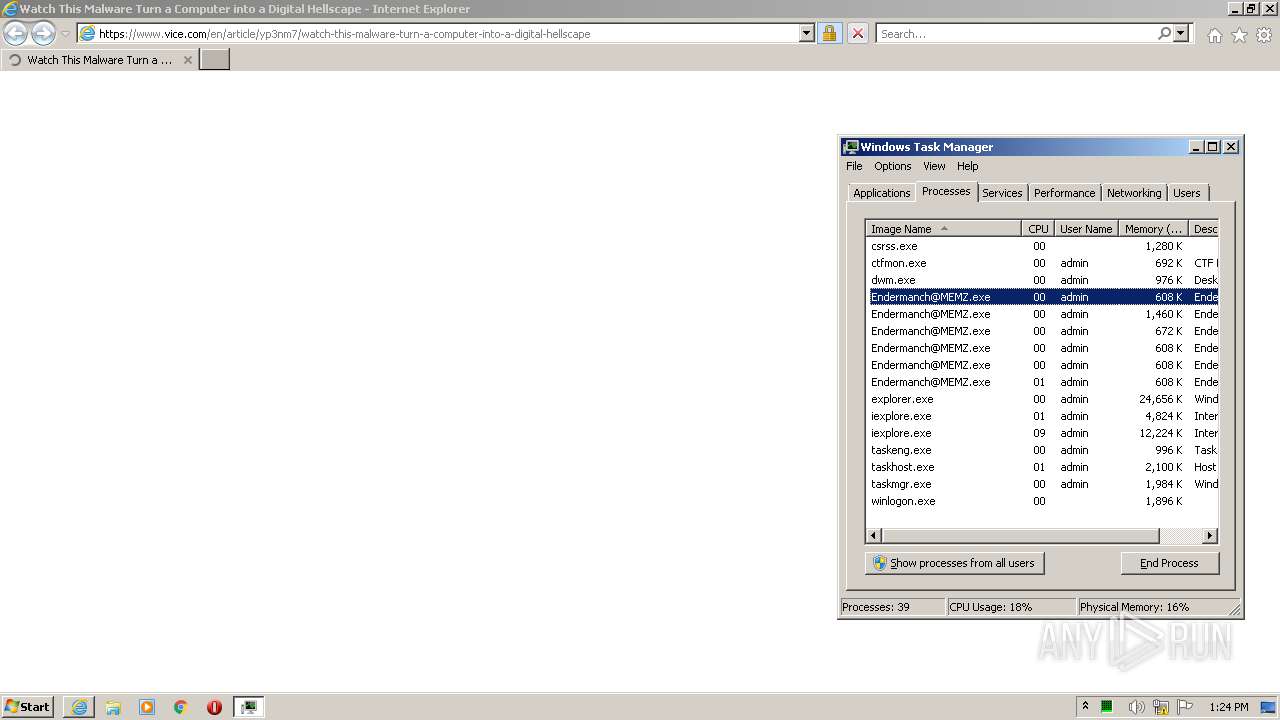
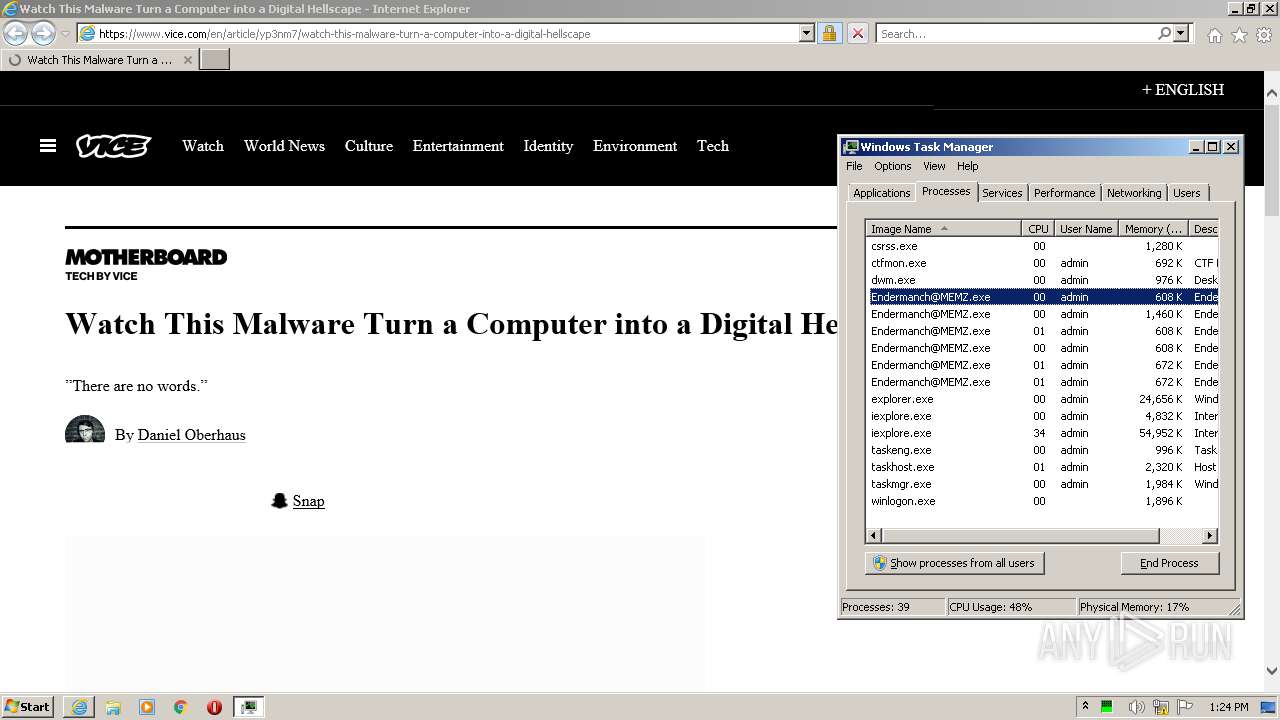
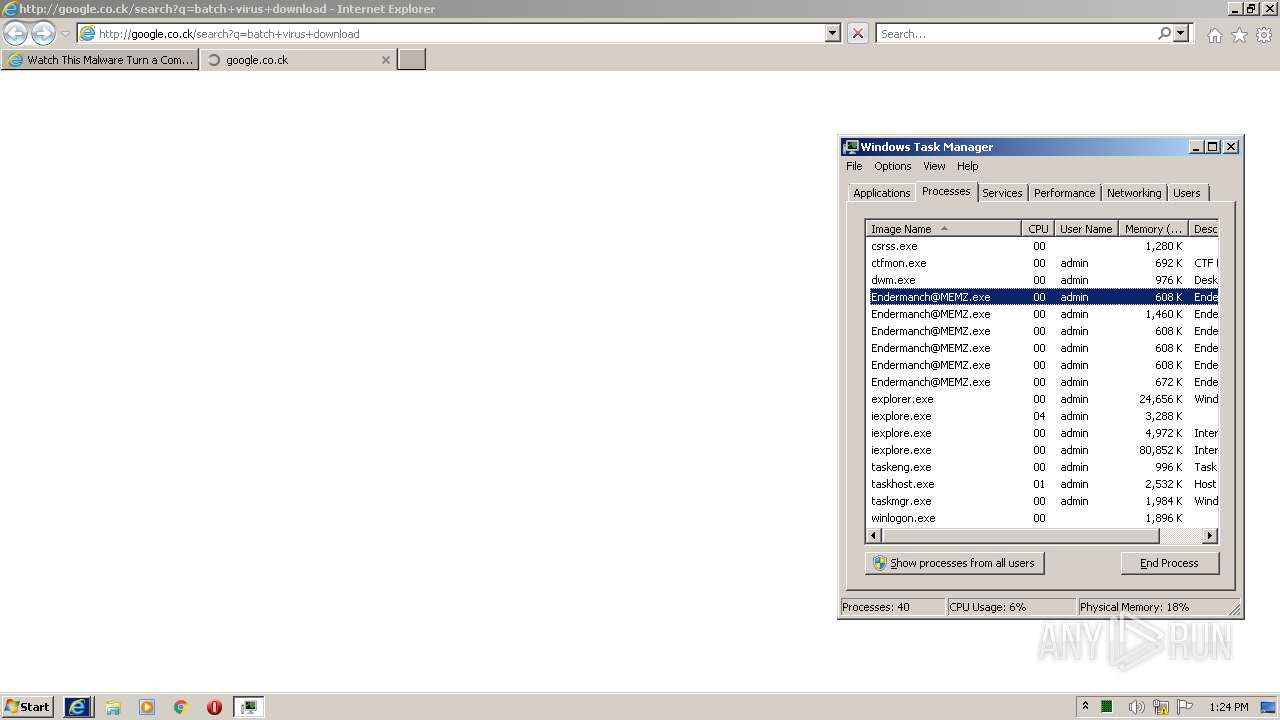
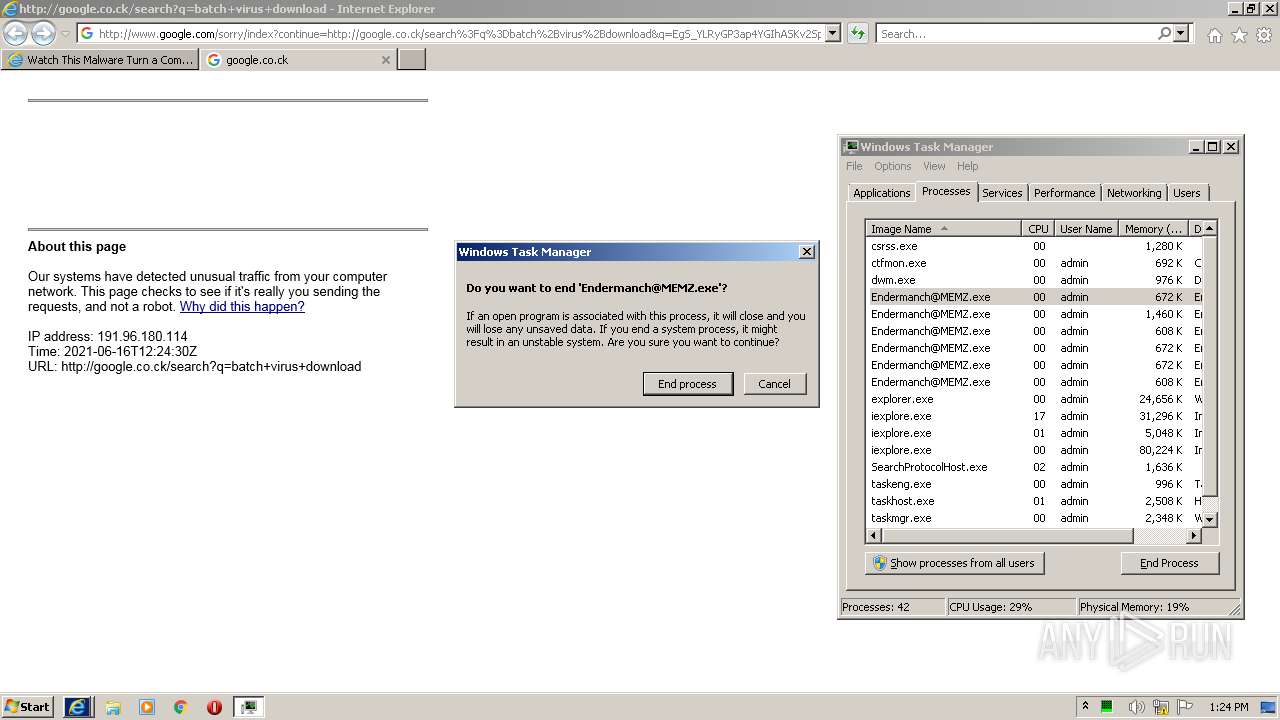
Starts Internet Explorer
- Endermanch@MEMZ.exe (PID: 2324)
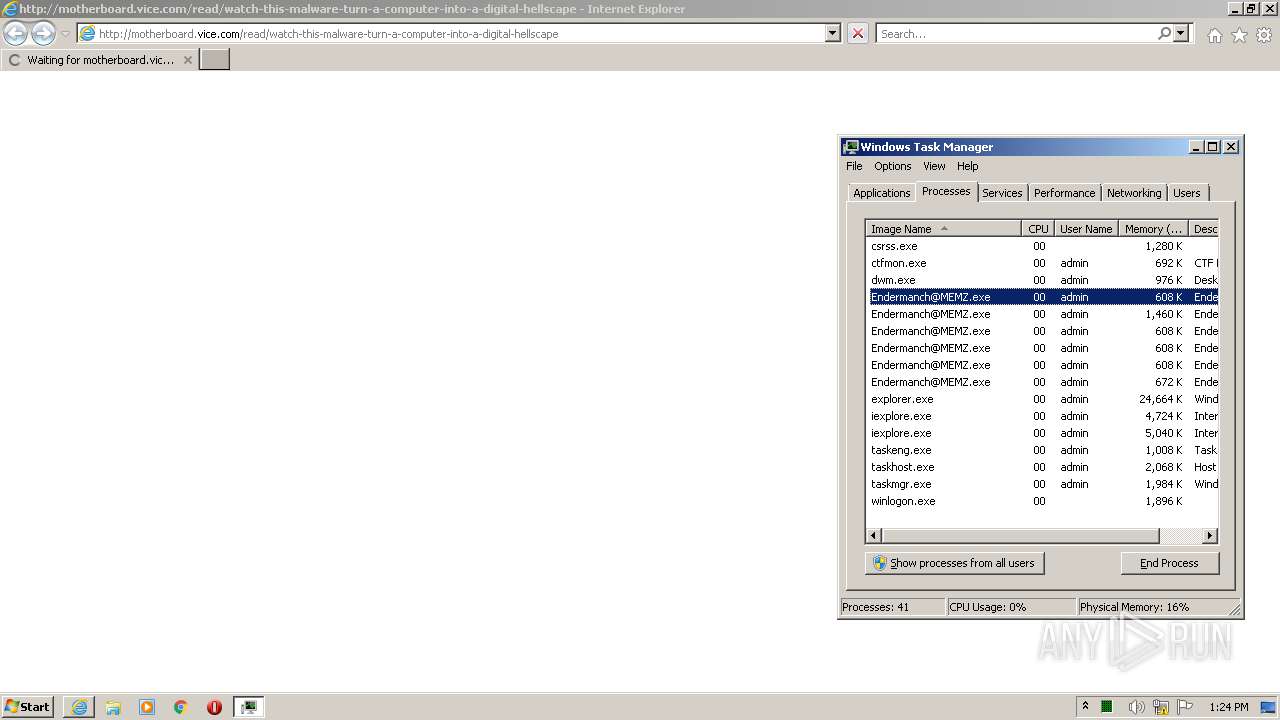
Application launched itself
- Endermanch@MEMZ.exe (PID: 3644)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1016)
INFO
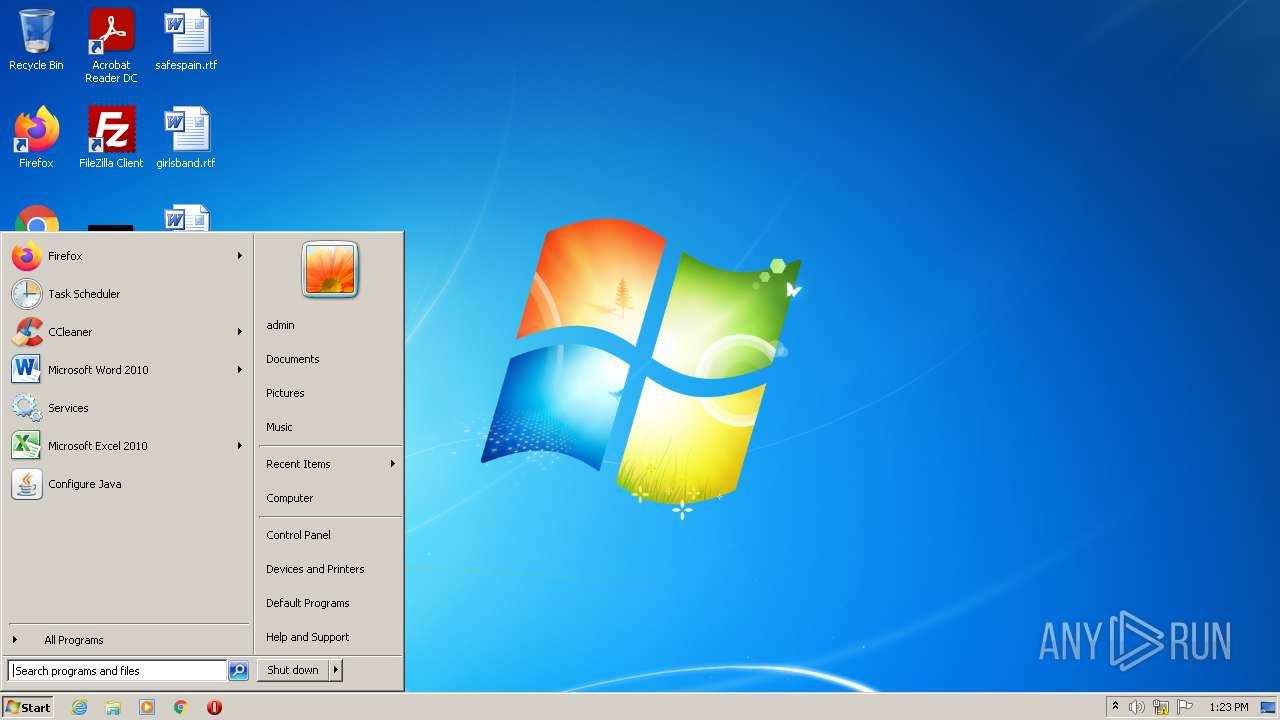
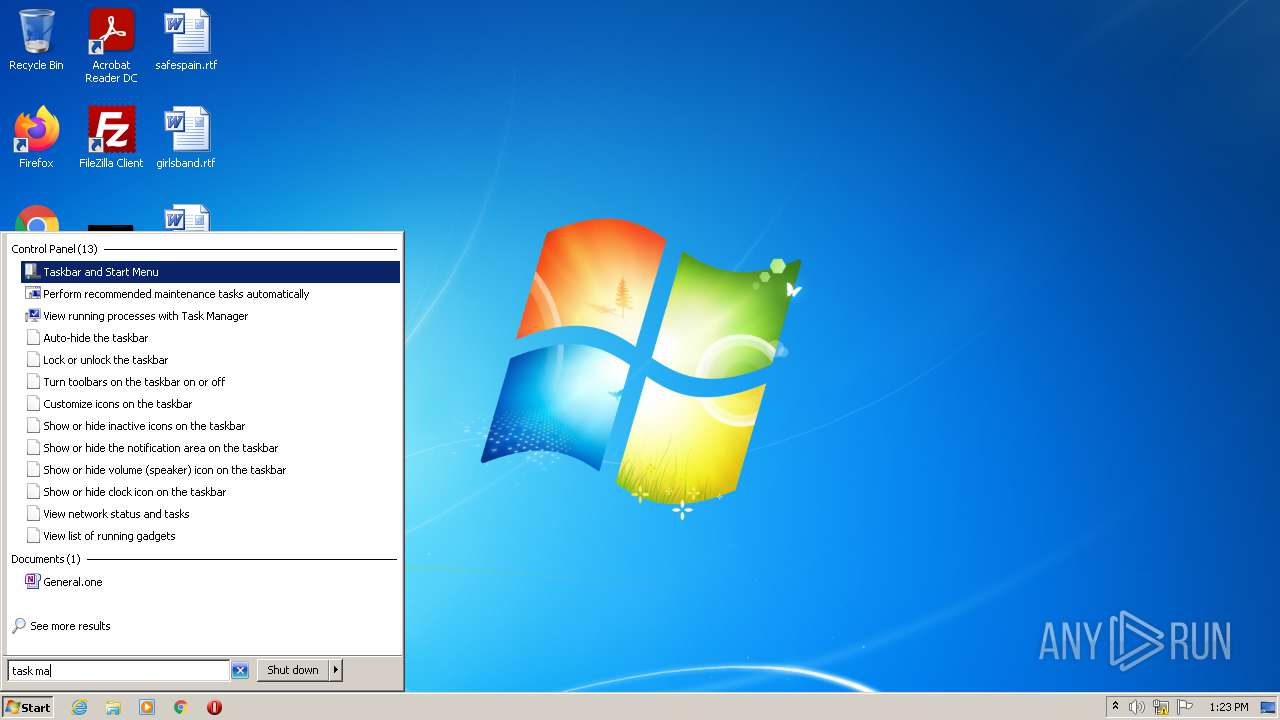
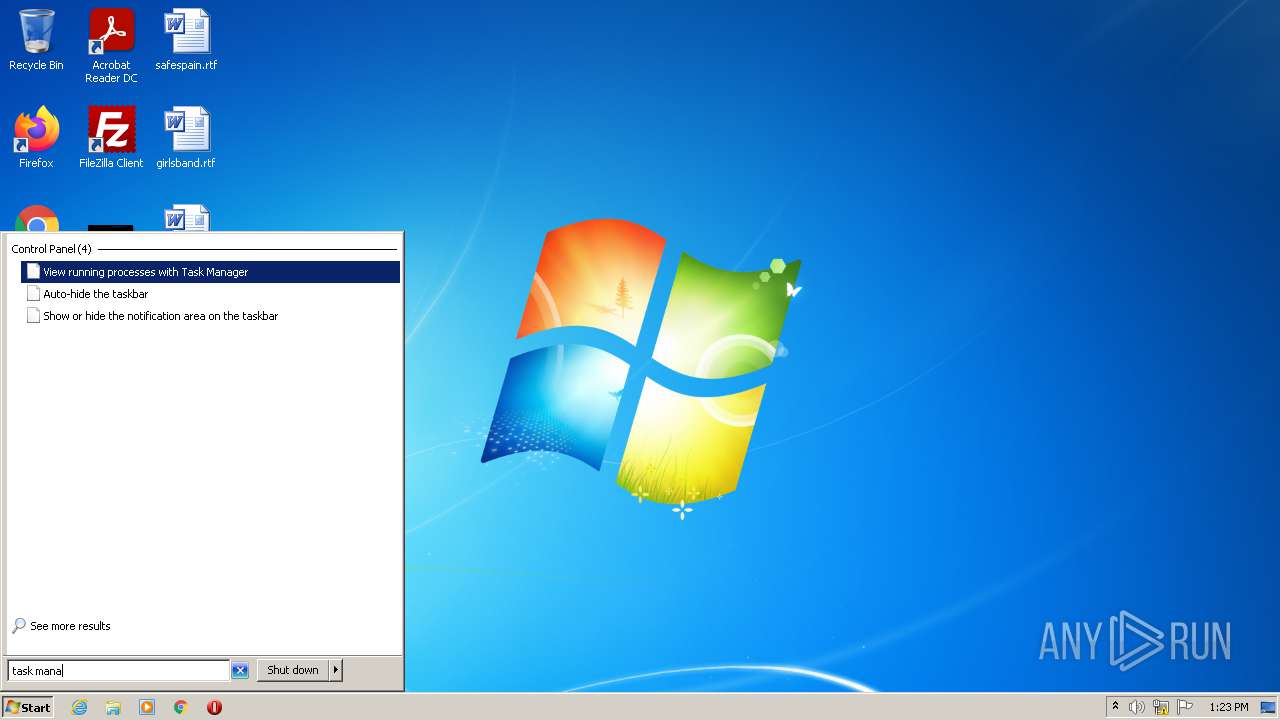
Manual execution by user
- taskmgr.exe (PID: 404)
Reads the computer name
- iexplore.exe (PID: 2356)
- taskmgr.exe (PID: 404)
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1016)
Application launched itself
- iexplore.exe (PID: 2356)
Checks supported languages
- iexplore.exe (PID: 2620)
- notepad.exe (PID: 3196)
- taskmgr.exe (PID: 404)
- iexplore.exe (PID: 2356)
- iexplore.exe (PID: 1016)
Checks Windows Trust Settings
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1016)
- iexplore.exe (PID: 2356)
Changes internet zones settings
- iexplore.exe (PID: 2356)
Reads settings of System Certificates
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1016)
- iexplore.exe (PID: 2356)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2620)
Reads internet explorer settings
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1016)
Changes settings of System certificates
- iexplore.exe (PID: 2620)
Creates files in the user directory
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 1016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x122d |
| UninitializedDataSize: | - |
| InitializedDataSize: | 10752 |
| CodeSize: | 3072 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2016:07:10 14:59:43+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jul-2016 12:59:43 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jul-2016 12:59:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000B2A | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85958 |
.rdata | 0x00002000 | 0x000021C2 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35229 |
.data | 0x00005000 | 0x00000194 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5782 |
.rsrc | 0x00006000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75224 |
.reloc | 0x00007000 | 0x0000020C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.99459 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
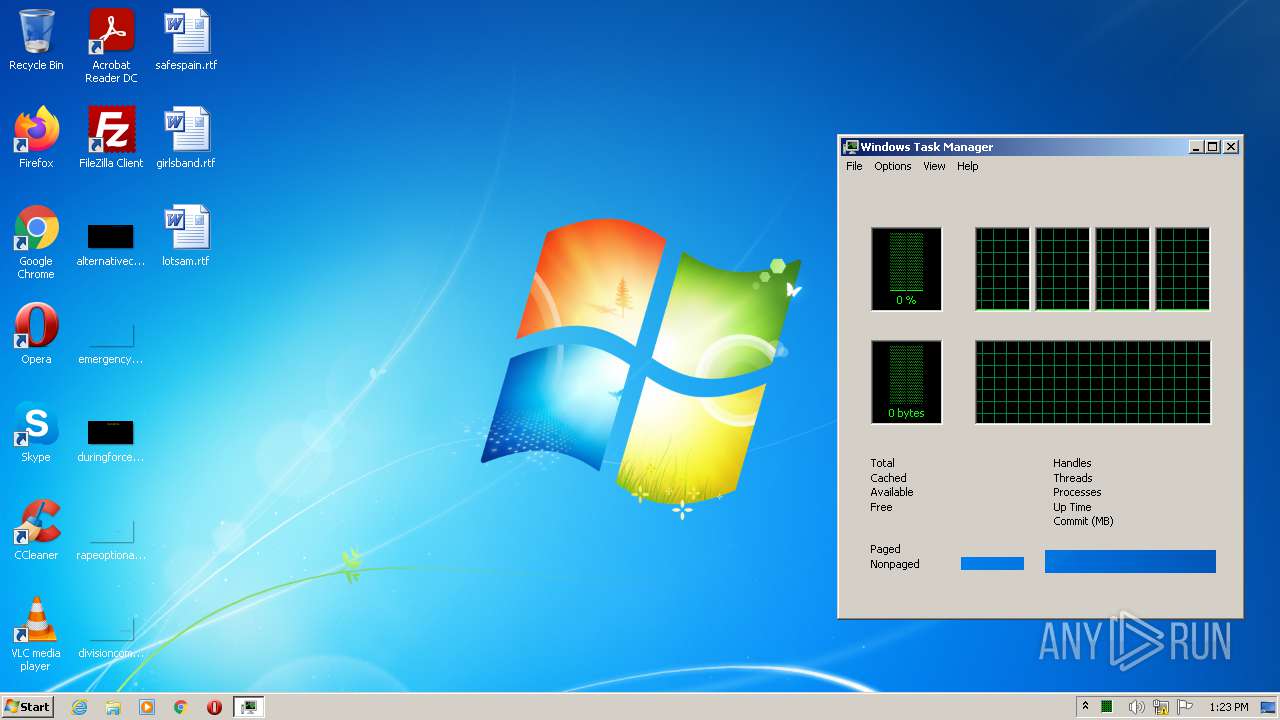
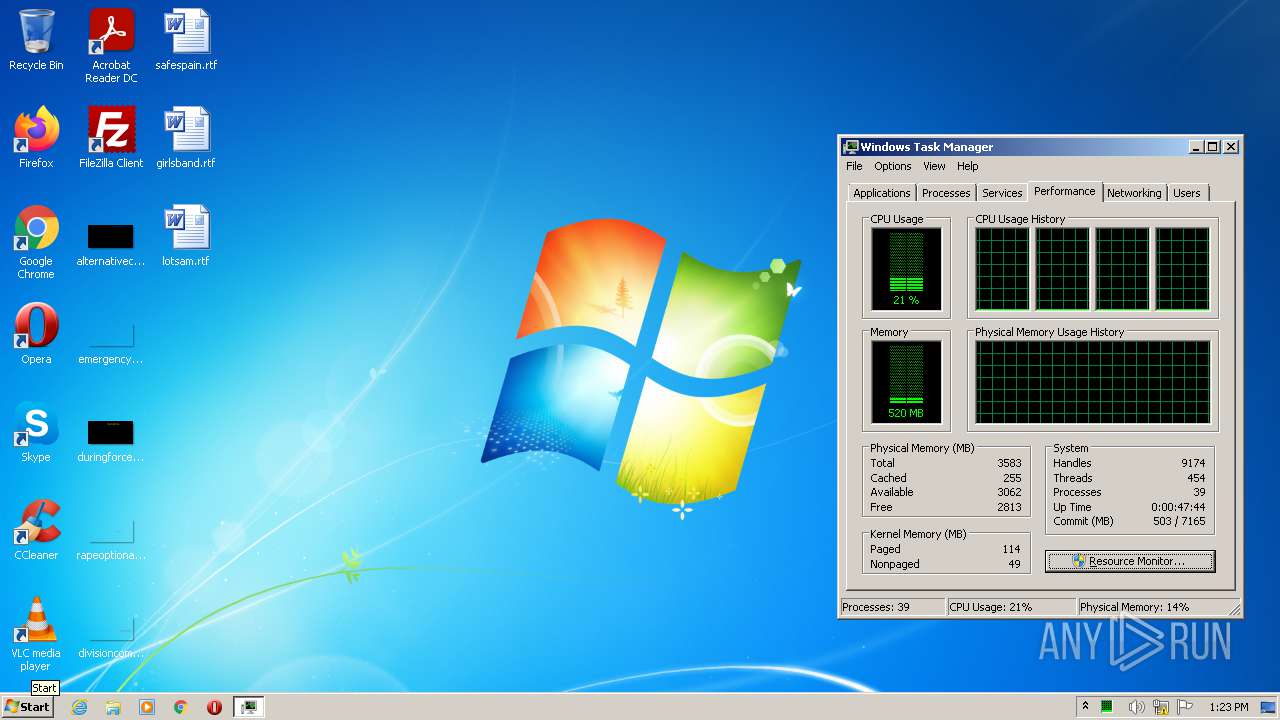
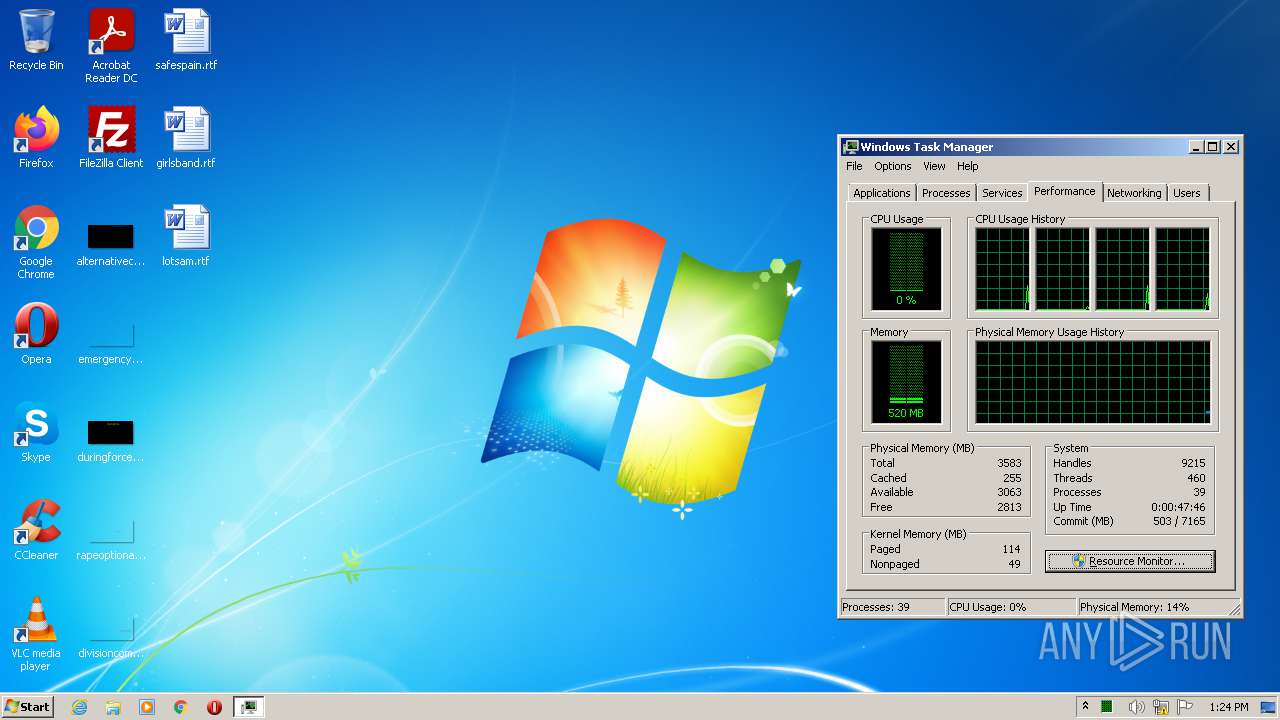
Total processes
51
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
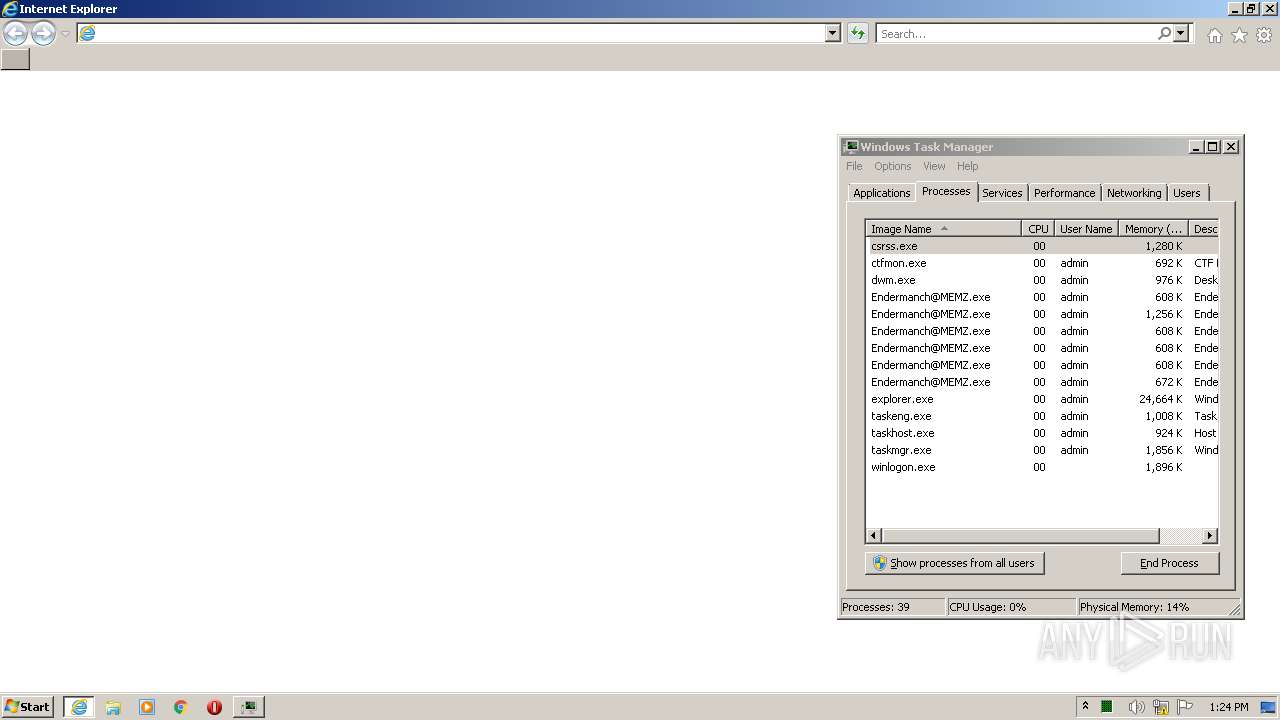
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2356 CREDAT:1651723 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1048 | "C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2036 | "C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe" | C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe" /main | C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Internet Explorer\iexplore.exe" http://motherboard.vice.com/read/watch-this-malware-turn-a-computer-into-a-digital-hellscape | C:\Program Files\Internet Explorer\iexplore.exe | Endermanch@MEMZ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2356 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2880 | "C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Endermanch@MEMZ.exe | — | Endermanch@MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
25 123
Read events
24 834
Write events
289
Delete events
0
Modification events
| (PID) Process: | (3644) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3644) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3644) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3644) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2324) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2324) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2324) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2324) Endermanch@MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
Executable files
0
Suspicious files
26
Text files
95
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_ACB084F1532E23E916946A083A45F6BF | der | |
MD5:9EF16114A8120C7B6684AD58BD7FB2E5 | SHA256:C056B3143D8708C870D3859179B4EB6256D70AF64B5369C75CD142A5BCDDE4E8 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BF15MZBG.txt | text | |
MD5:BC14F91CB91B4F4D50171FA9D69239A1 | SHA256:DC8FF0C8FC948D1E74EFBFB178C5E1904A0FBB1A1C5B6612573B00313DD06B1A | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_ACB084F1532E23E916946A083A45F6BF | binary | |
MD5:3F93F0E7DBF0BBDB76EA6D350B29C5E8 | SHA256:92FF602E8AD82B9DC4D0B58A1C41D76CD4042A1B41EED121B42B01E67AD27EC7 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2876FFED01F24E59D648DA8B8C4F6D92_0797A48C7081E5B5BC0656CF06D261C0 | der | |
MD5:0639C23EE77E21CF5BE28F9734BB63C6 | SHA256:0D9A21C5C038DEF8FE4269C53DF7B7984C29BA65F88FA9ECF5FA0E99FE52A847 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Z40MQ383.txt | text | |
MD5:C184D335726ADC2439BB2454B8FDB0B1 | SHA256:D74A3218D60CA08F31038E16D6F4F3F50D95BFE17F722BFF06A6685A6C1B3607 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:CE6701A7762BD6998A2AFA52DA7094A2 | SHA256:92FAA155479781BEF63D035393F43F3C1FB12EE33D1D29EA46A28CA9E37EFF53 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2876FFED01F24E59D648DA8B8C4F6D92_0797A48C7081E5B5BC0656CF06D261C0 | binary | |
MD5:73D3EB0E9EF56D52DC6B1182A0B57CA4 | SHA256:D39779DFA859DC31AD3394C04941CDB305AFED7CC090153360C52ECC048DB2ED | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vice.53b91dcde2f156454fa9936ab7cb2d9b[1].css | text | |
MD5:A809F30303DC41EE41C12A423D6EB89D | SHA256:CCFD8B08E10B5D365BA922C09223DA577F208F83B0E13A14D116D4D285566121 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\780f322452a54d4ead9acbfcc3de3f388ee2b90d_CSS.eb2ad766.chunk[1].css | text | |
MD5:955AC268450B94283B44F313781F620F | SHA256:BB00D4FAAA7E24237CBEEA8637E711421B5749B9A04FF6F1D5BF62ACDB910112 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\[slug].d251c577.chunk[1].css | text | |
MD5:F5AFFD6203F12892D4558A5AD163A6F0 | SHA256:AE7515C015008CAE3FA6D248373DCEA026E69C965A57C084D349A6FB43B7C530 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
83
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/ca/gsatlasr3dvtlsca2020/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQT6XbZiiF%2BR%2FUEno7LSD4H4YmN6gQUQm1XLU8fJnd0pidk9oD6j0ho%2FnwCEAGQTxcZ1j9Lh5OzuDaAynQ%3D | US | der | 1.42 Kb | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCI01RB3zwg9AoAAAAA1WvS | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCkNoyPUw1MCAoAAAAA2PQg | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDFlYUls3Fs%2BQoAAAAA2QMY | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHVRaep%2B14ZfCgAAAADVYgM%3D | US | der | 471 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDzcEjYf6OOhwoAAAAA2PRG | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEn1nbh4KCuVCgAAAADVYiA%3D | US | der | 471 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAjDldDVD7bYNJqd0UFfCKw%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2620 | iexplore.exe | 151.101.1.132:80 | motherboard.vice.com | Fastly | US | suspicious |
2620 | iexplore.exe | 8.248.135.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2620 | iexplore.exe | 151.101.1.132:443 | motherboard.vice.com | Fastly | US | suspicious |
2620 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
2620 | iexplore.exe | 13.225.84.145:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2620 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2620 | iexplore.exe | 142.250.184.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 151.101.1.132:443 | motherboard.vice.com | Fastly | US | suspicious |
2620 | iexplore.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2356 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
motherboard.vice.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
www.vice.com |
| whitelisted |
oembed.vice.com |
| whitelisted |
video-images.vice.com |
| whitelisted |
vice-web-statics-cdn.vice.com |
| whitelisted |