| File name: | MEMZ-Destructive.exe |
| Full analysis: | https://app.any.run/tasks/aa979be5-823d-40d4-ba0f-731000f0d6dd |
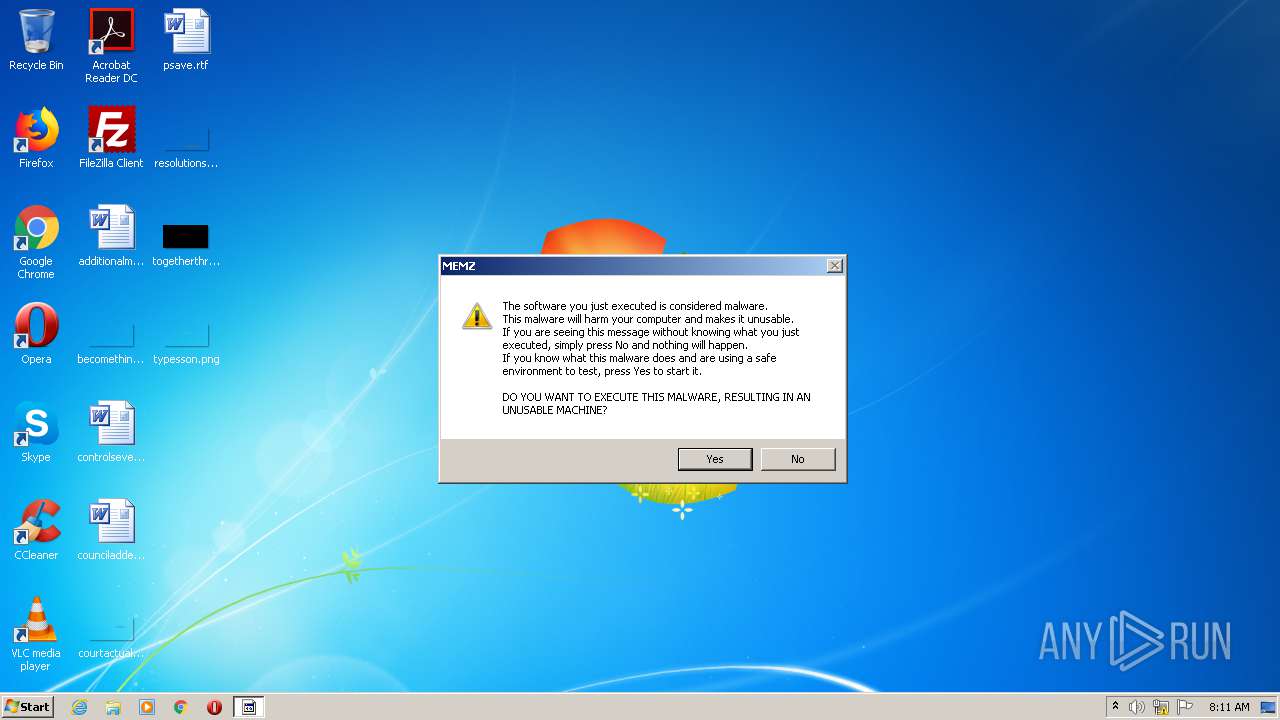
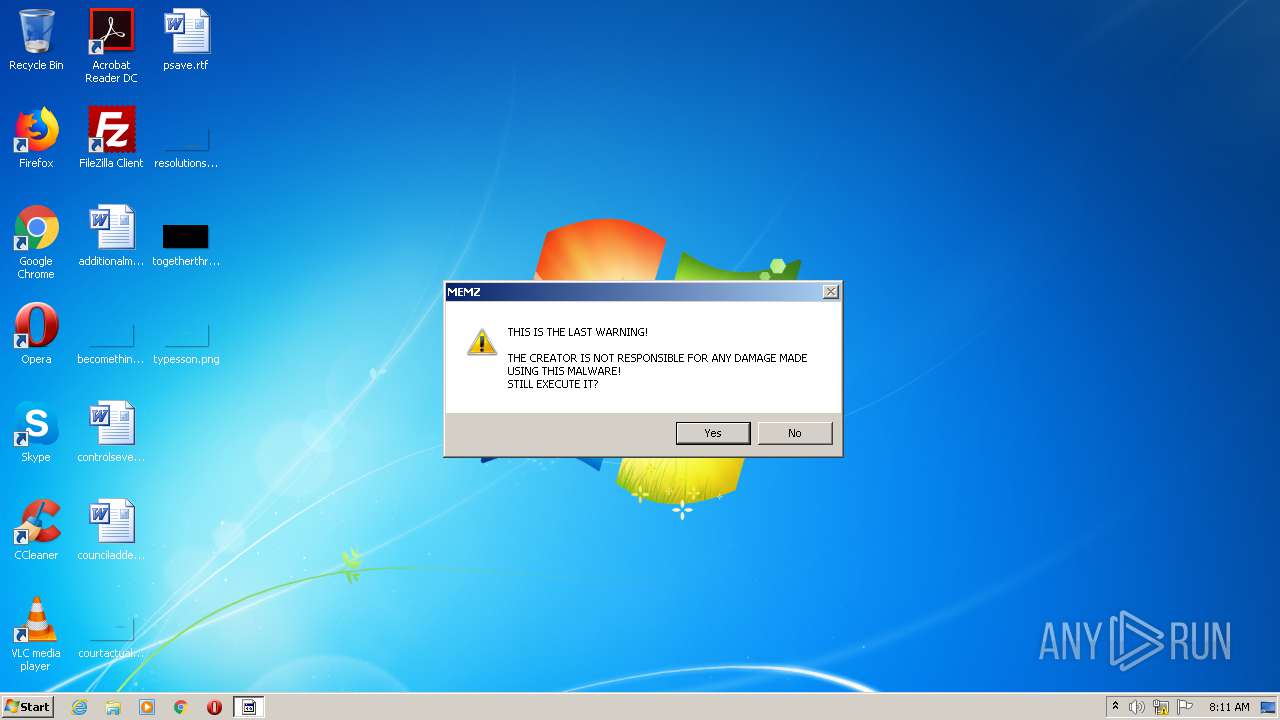
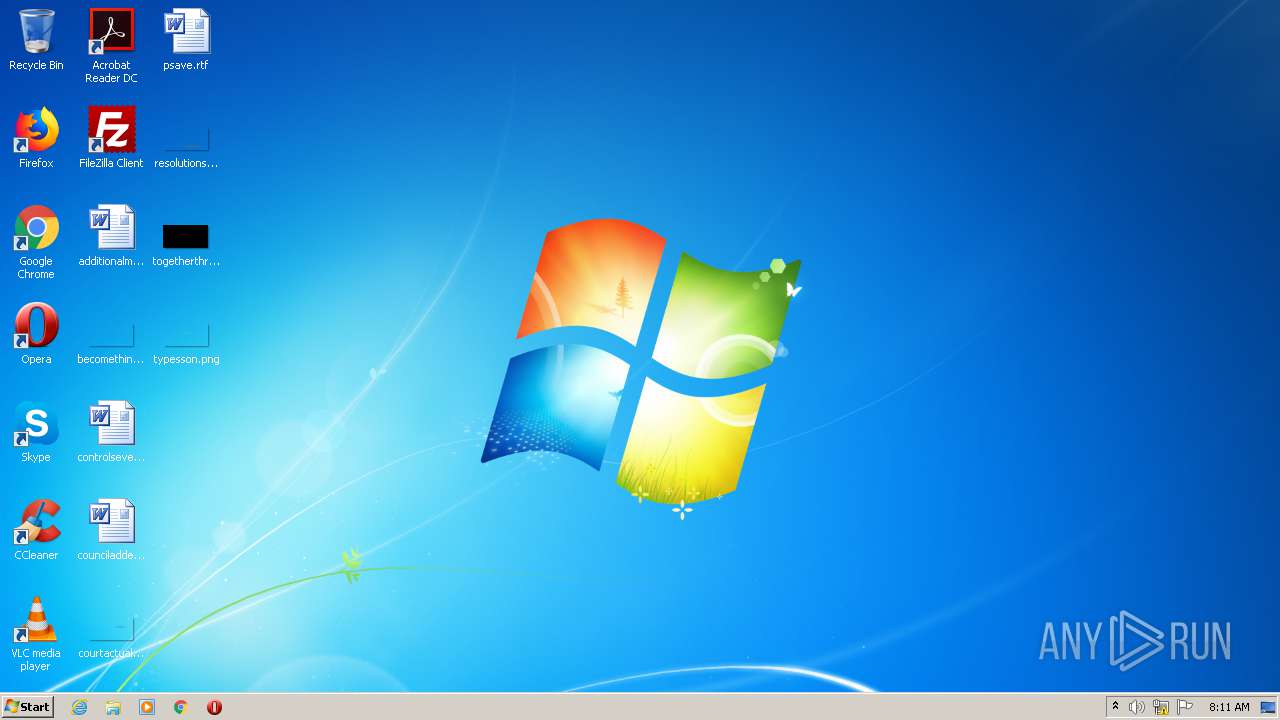
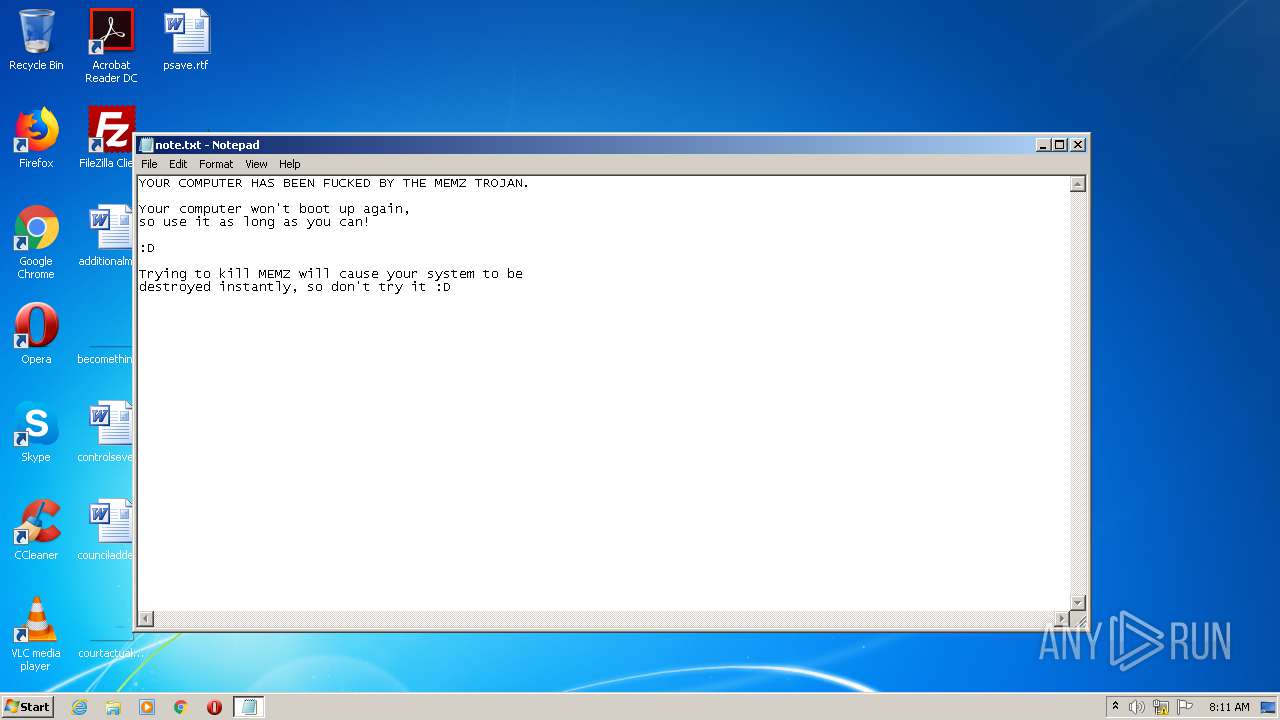
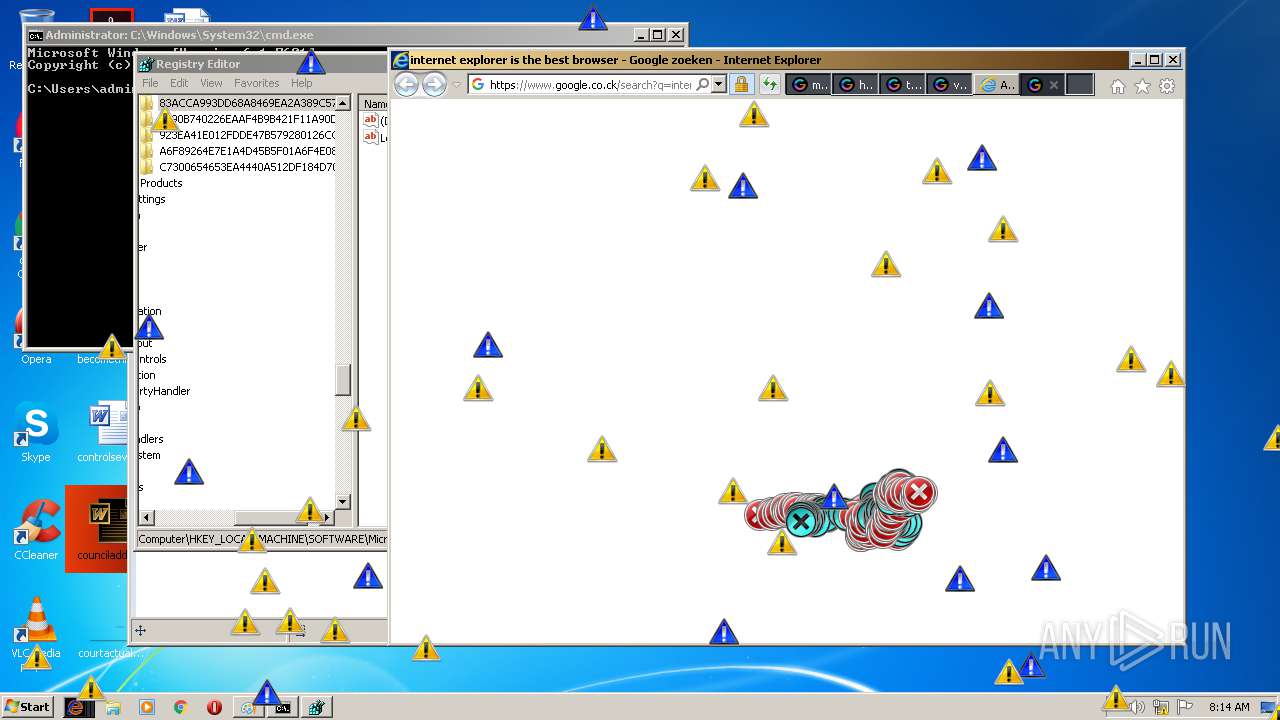
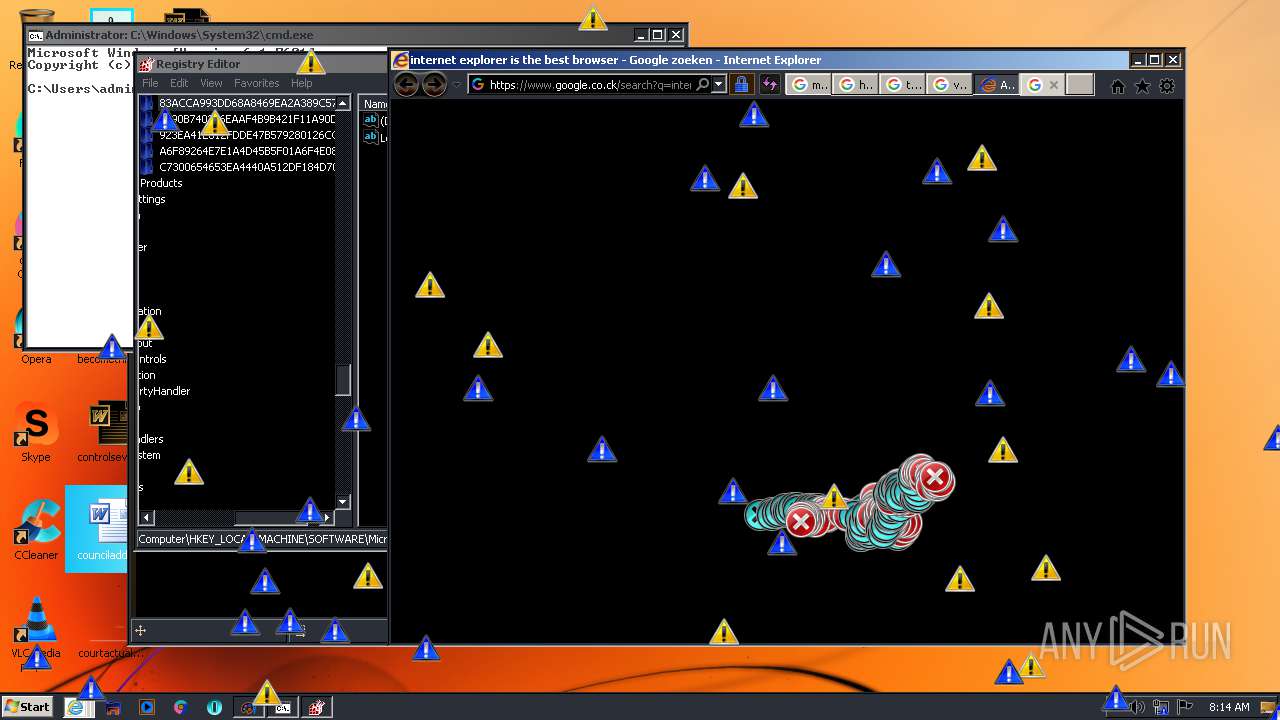
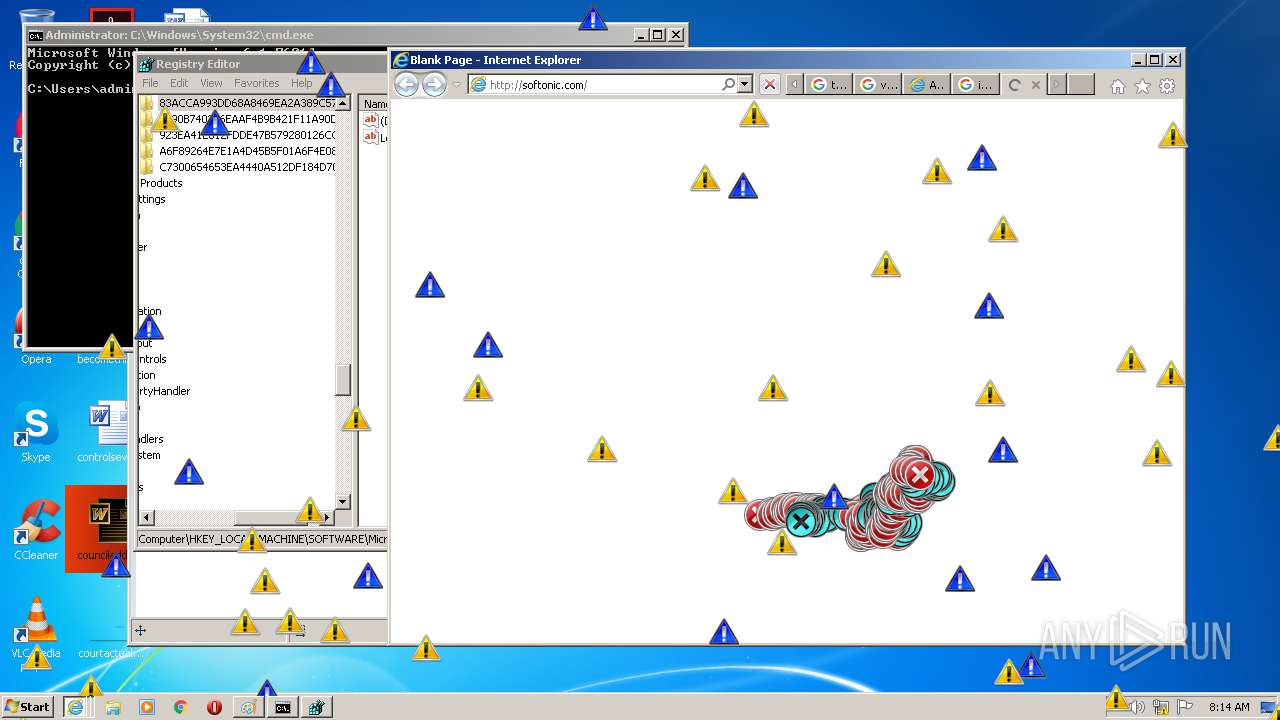
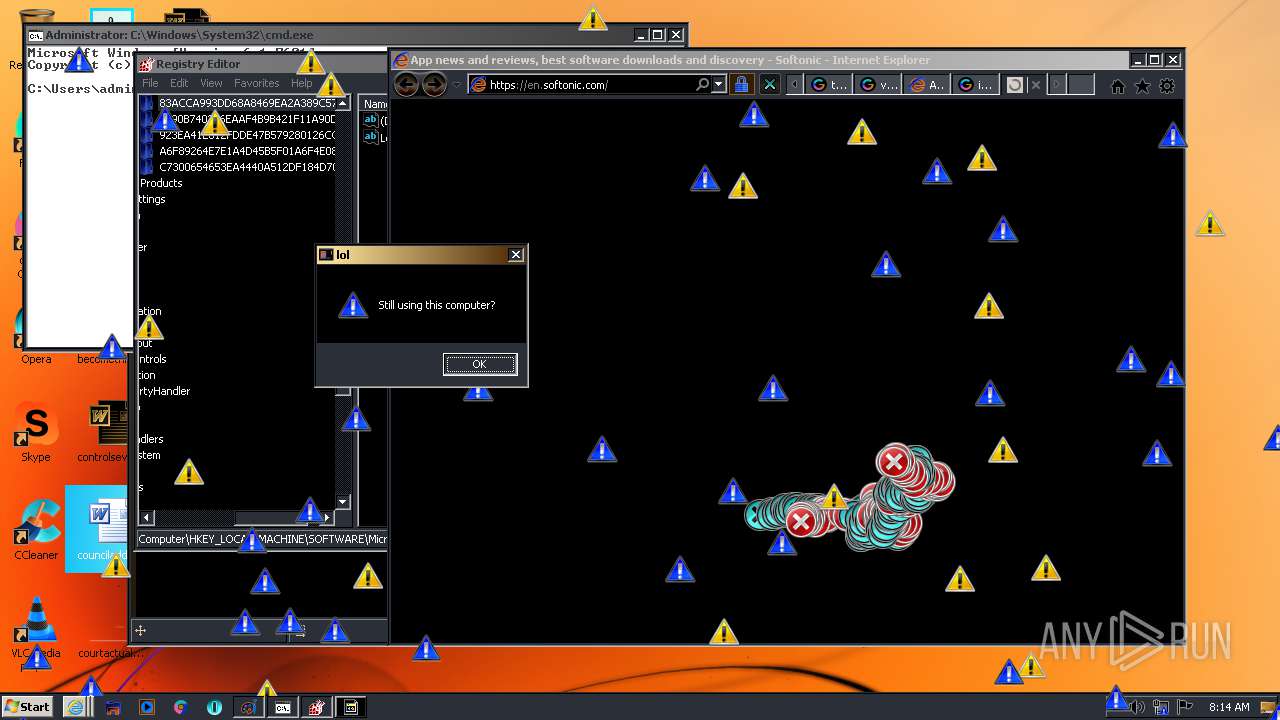
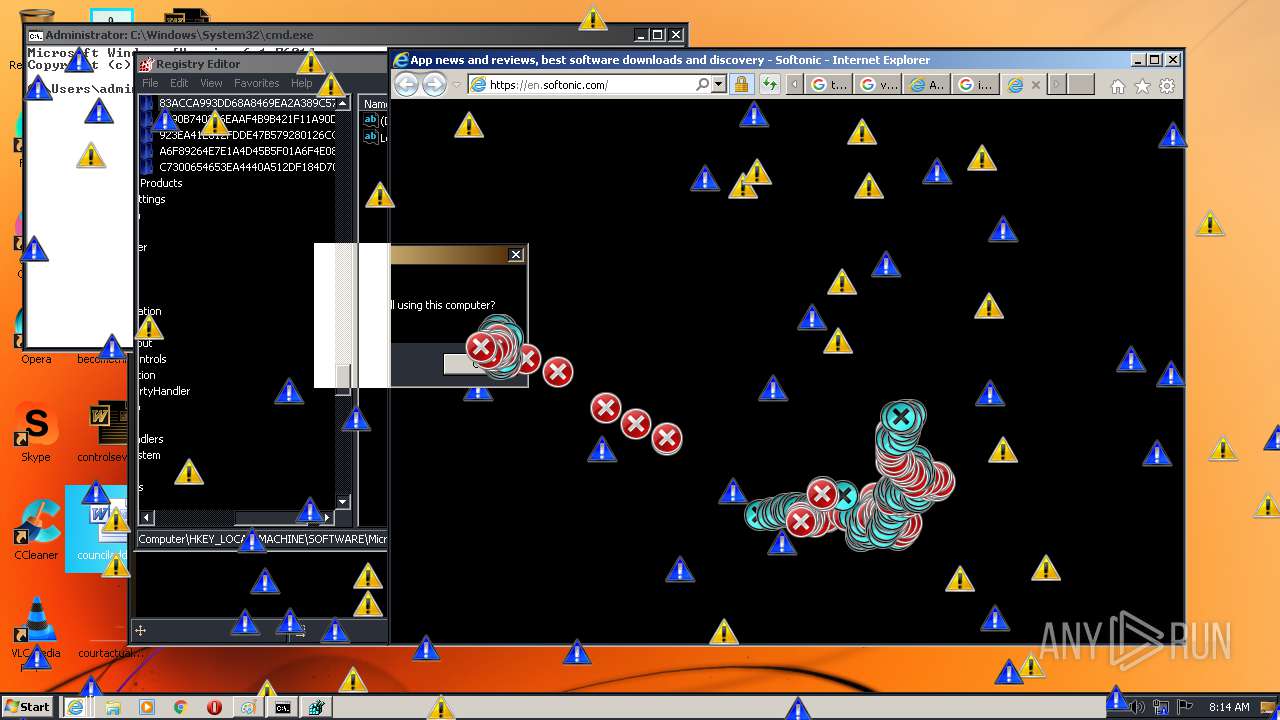
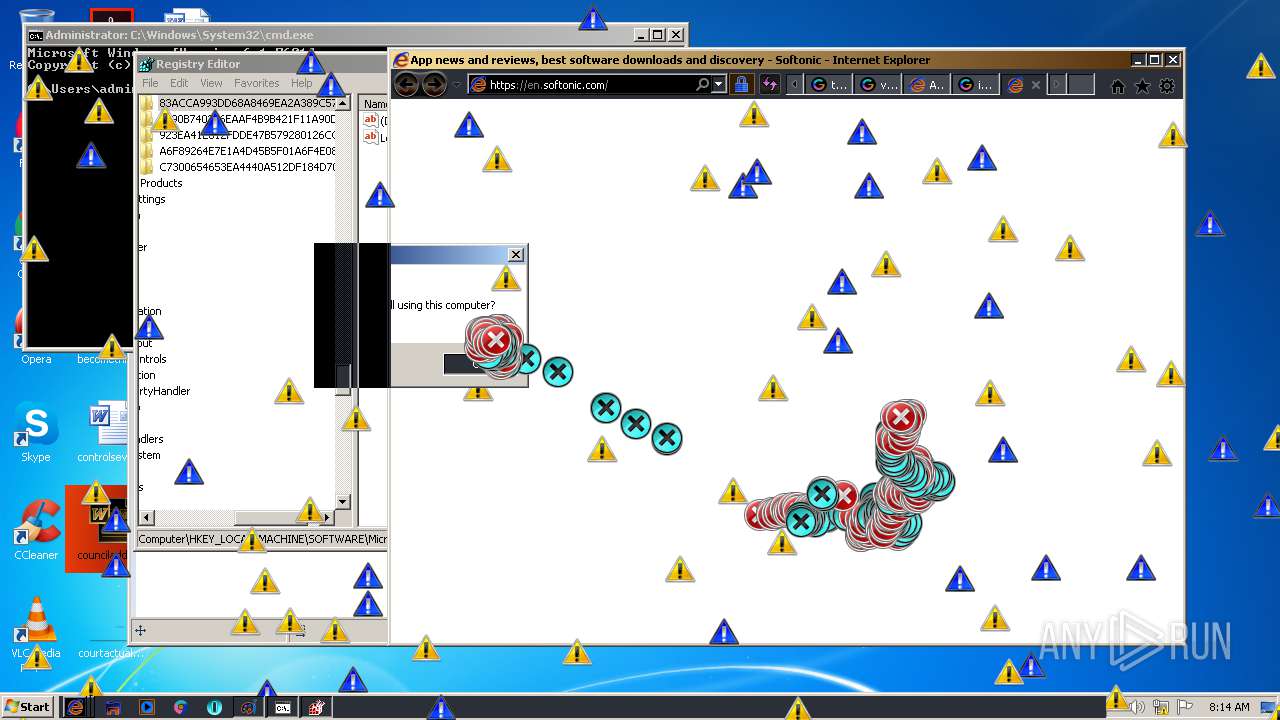
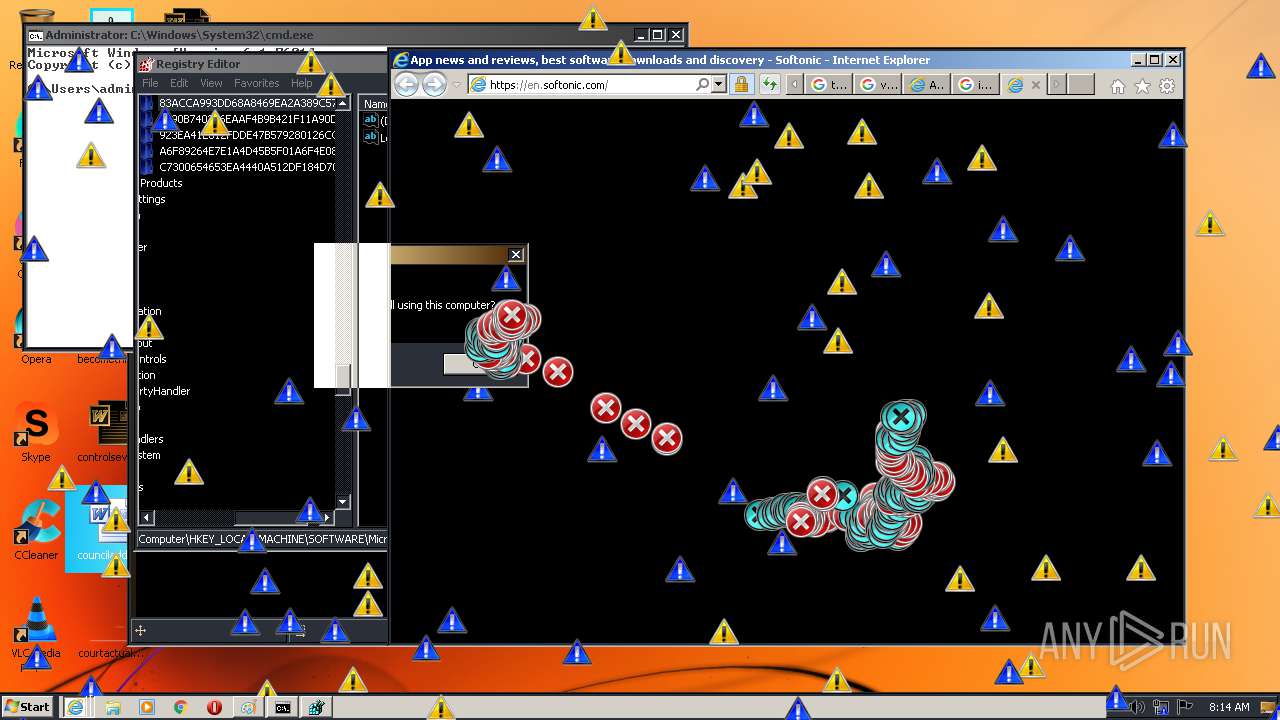
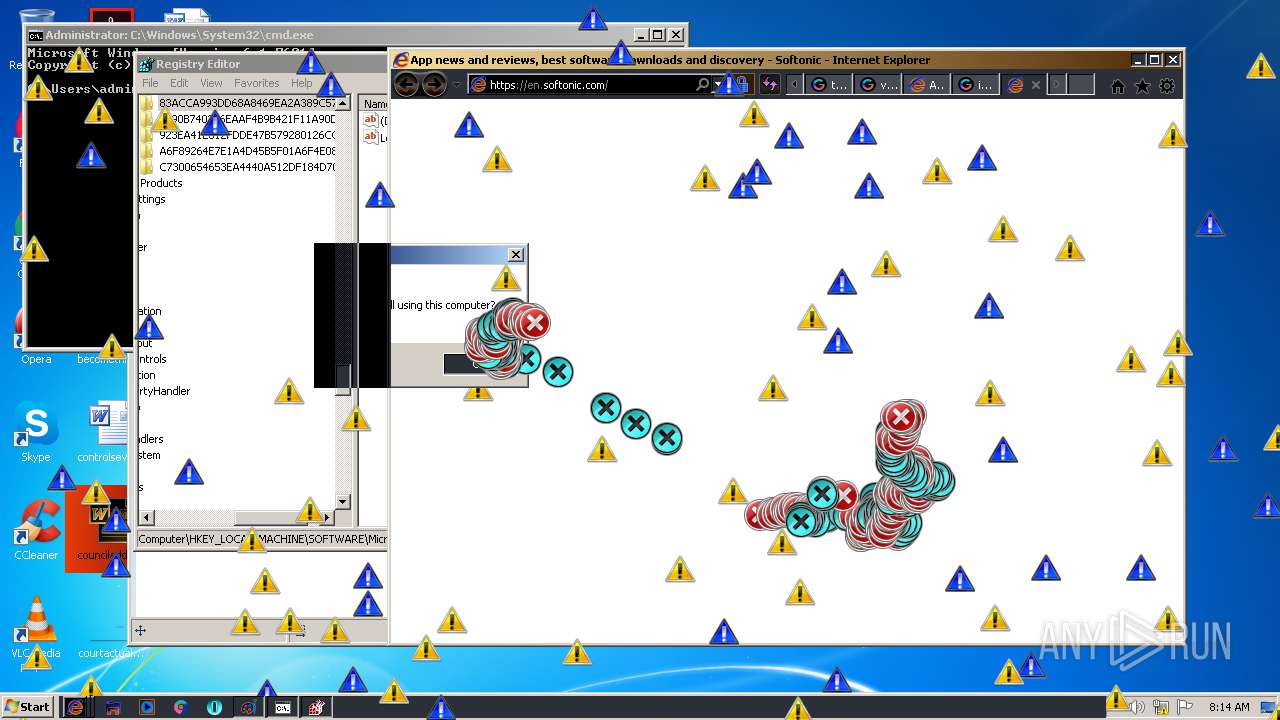
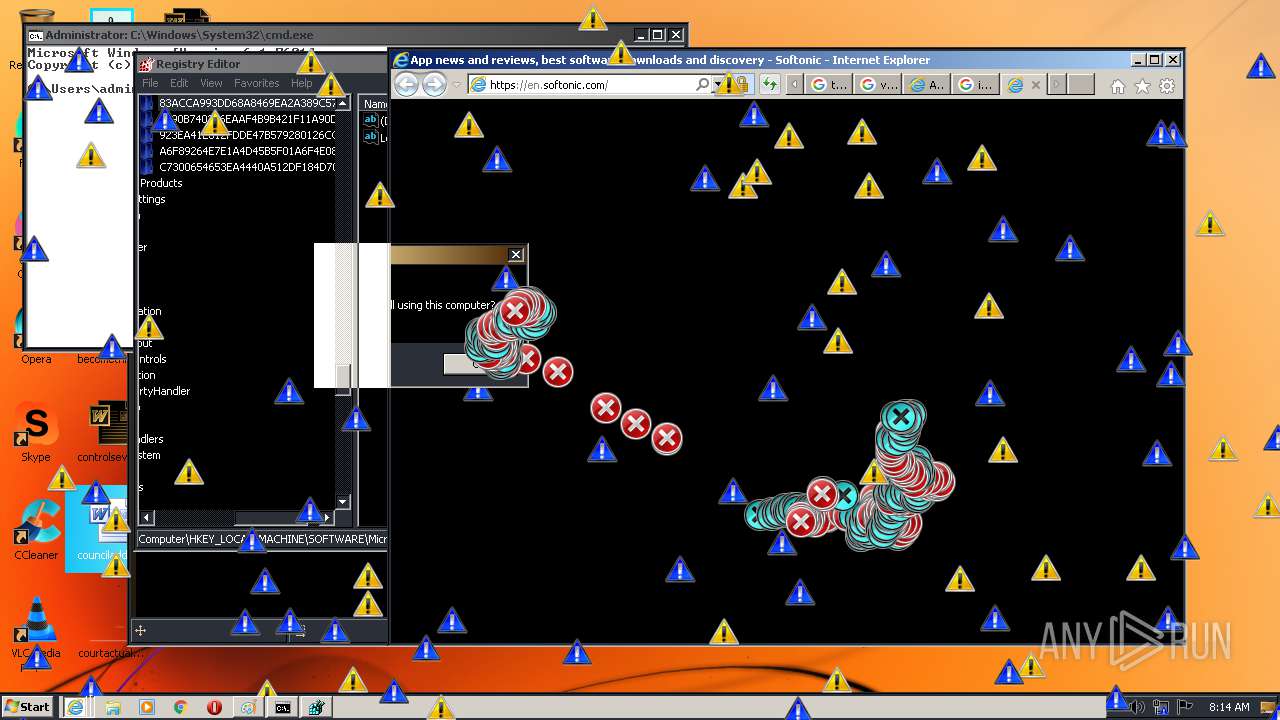
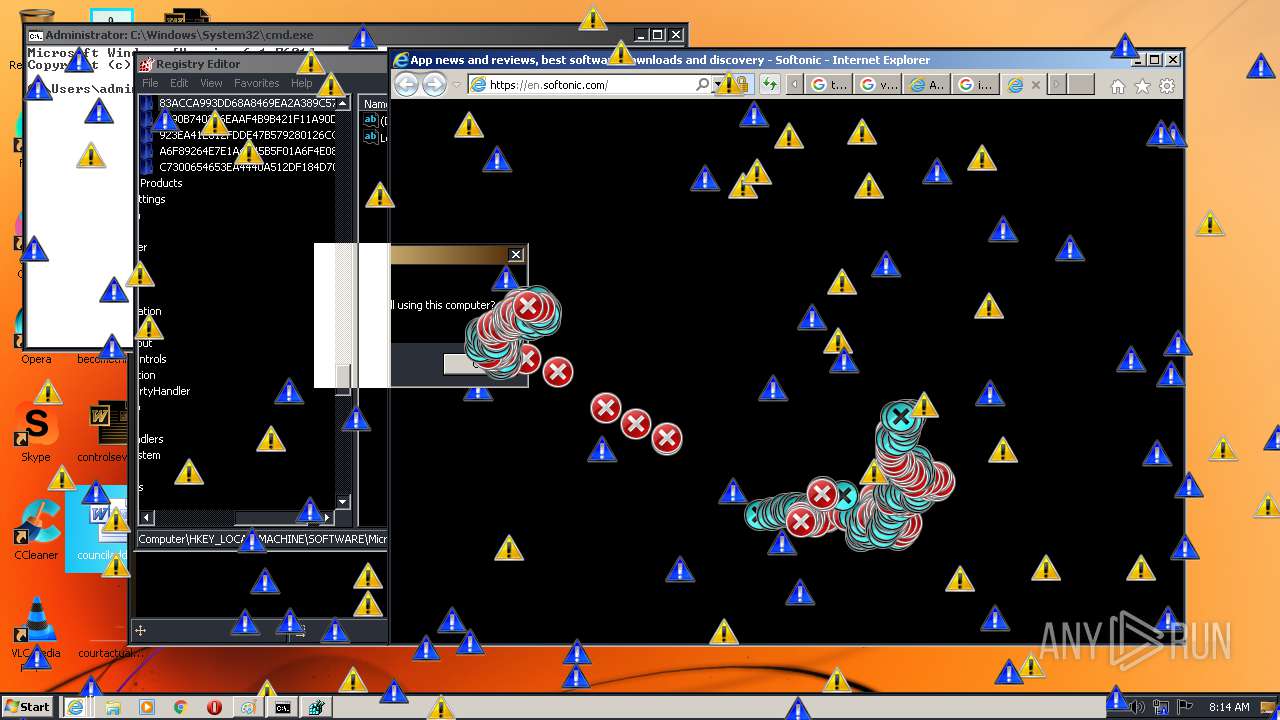
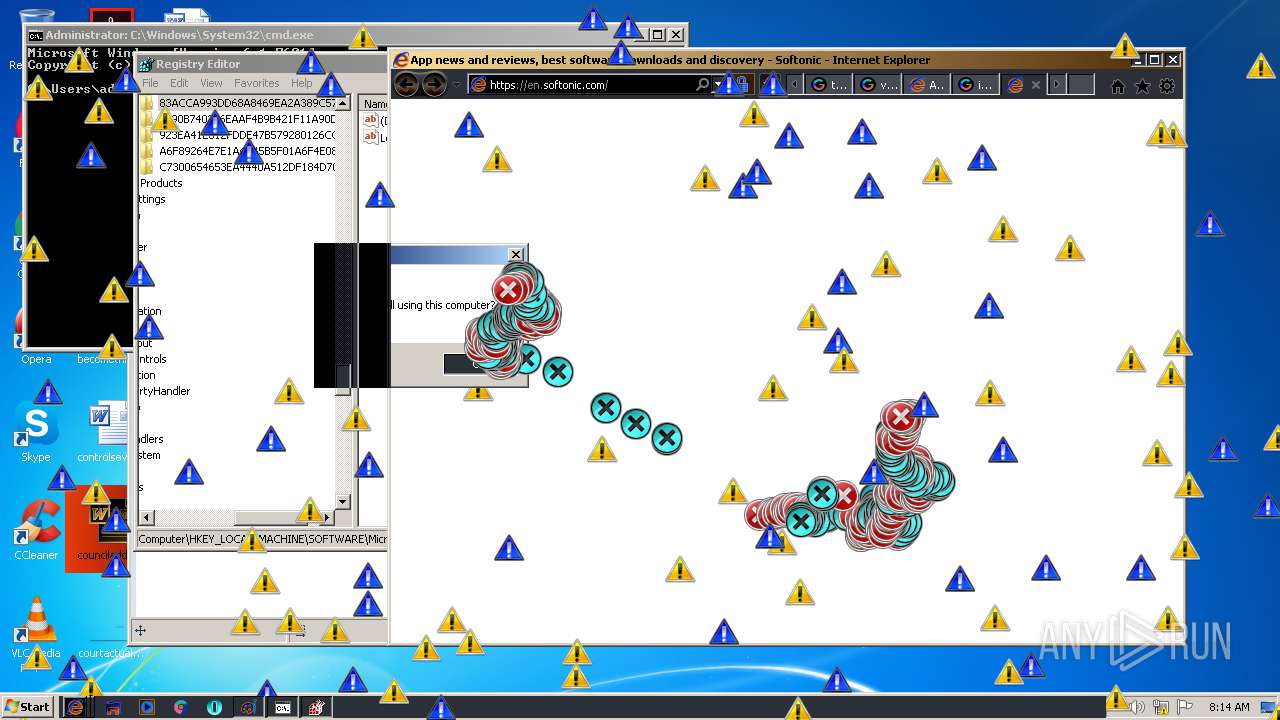
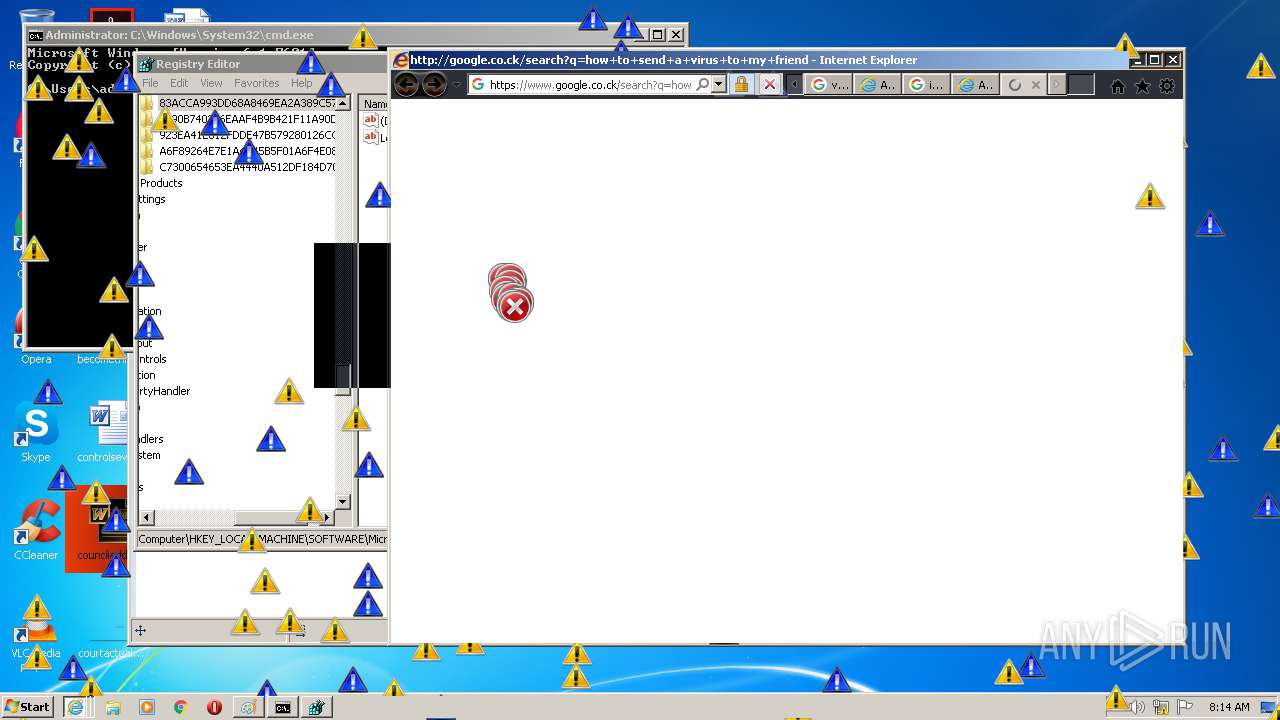
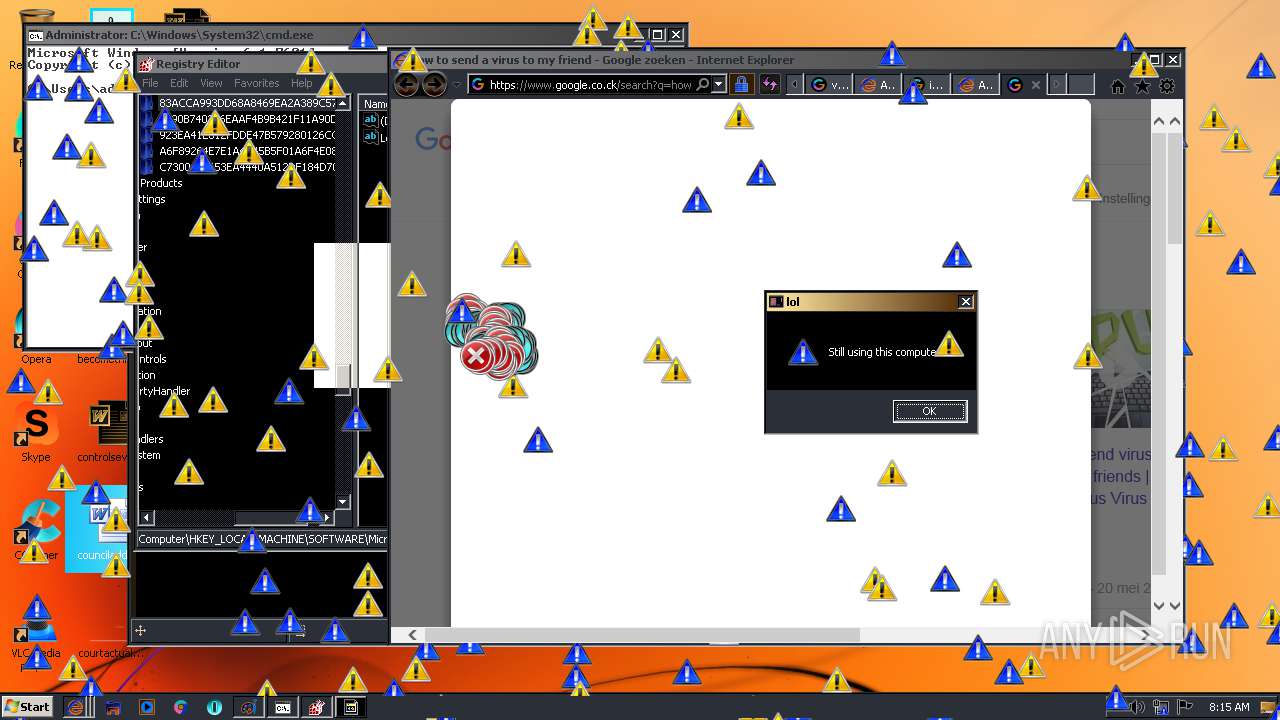
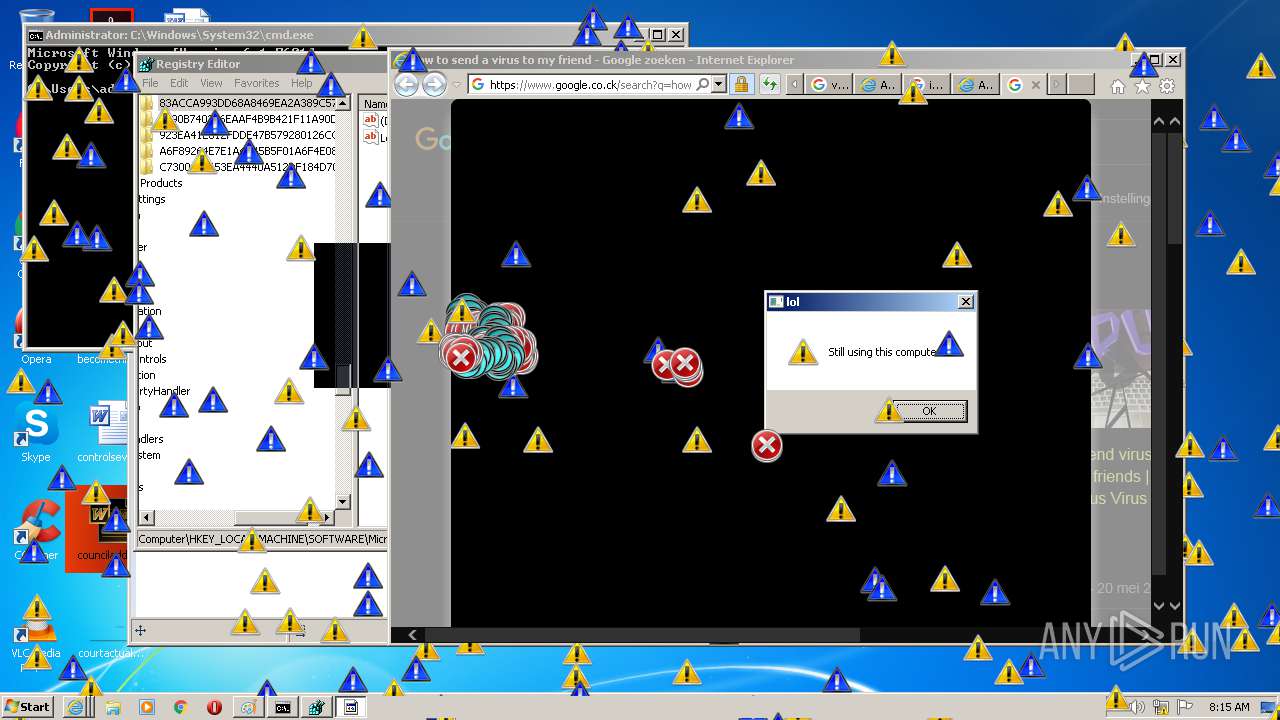
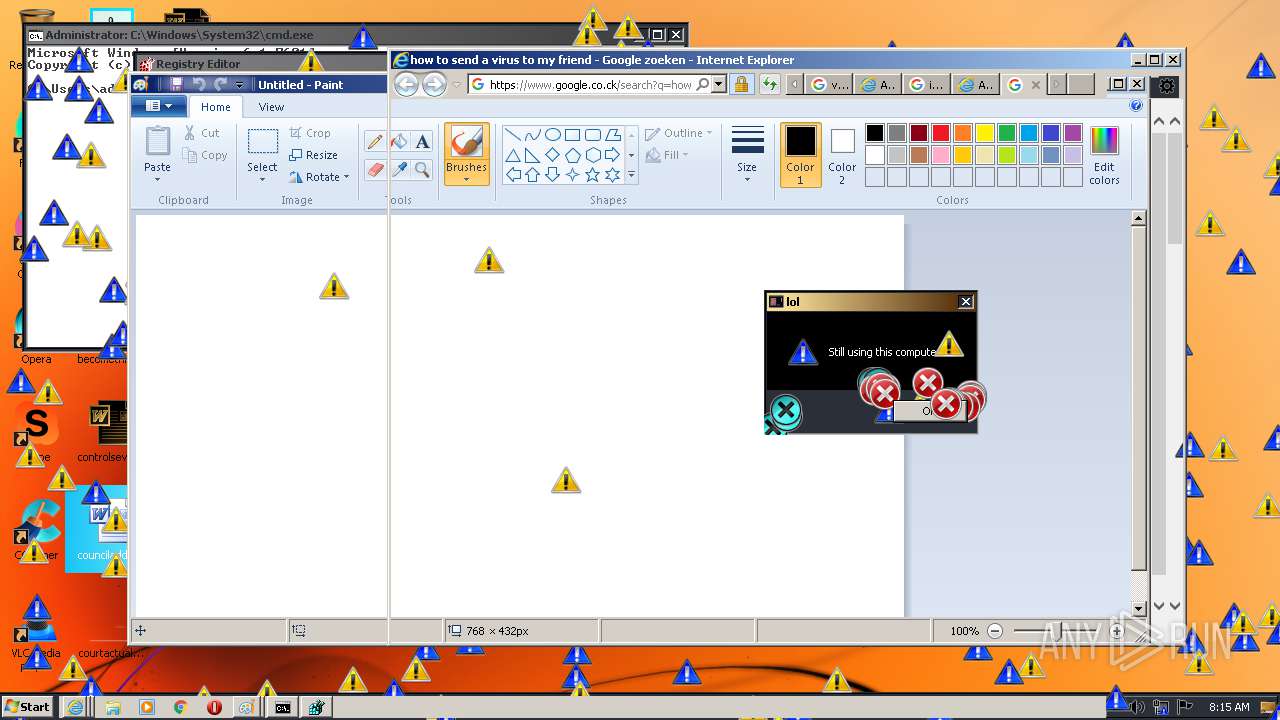
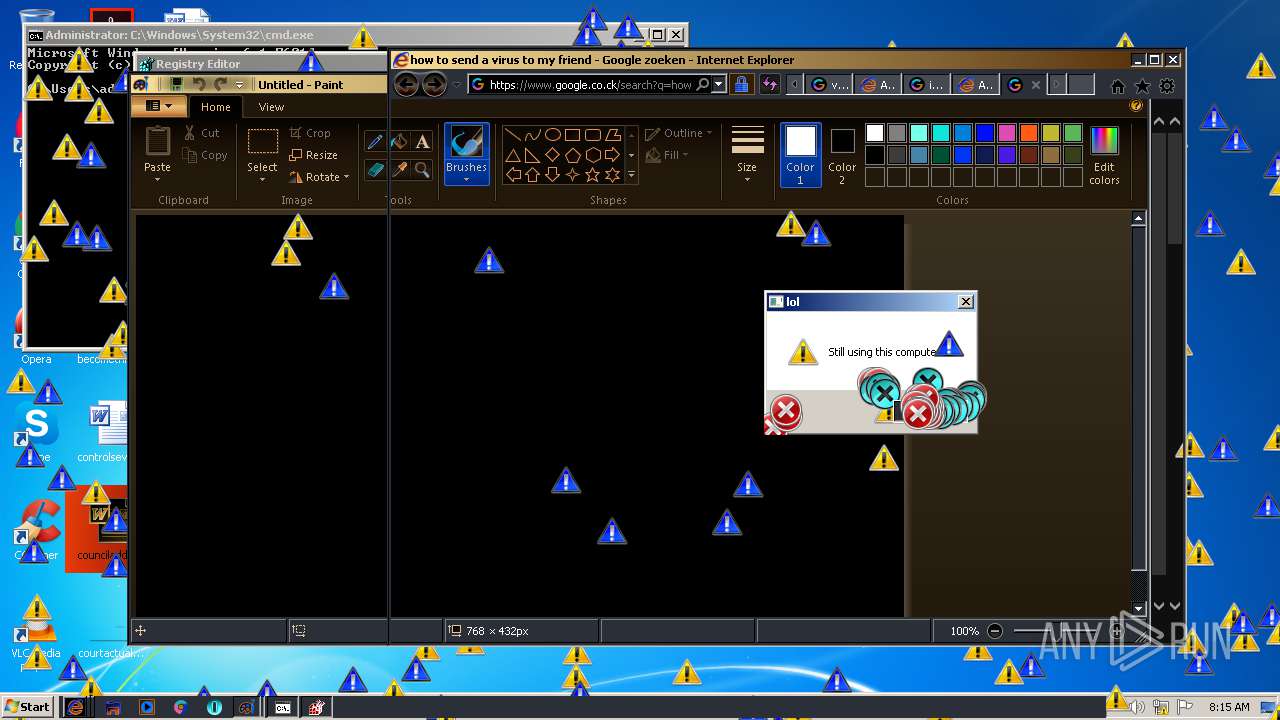
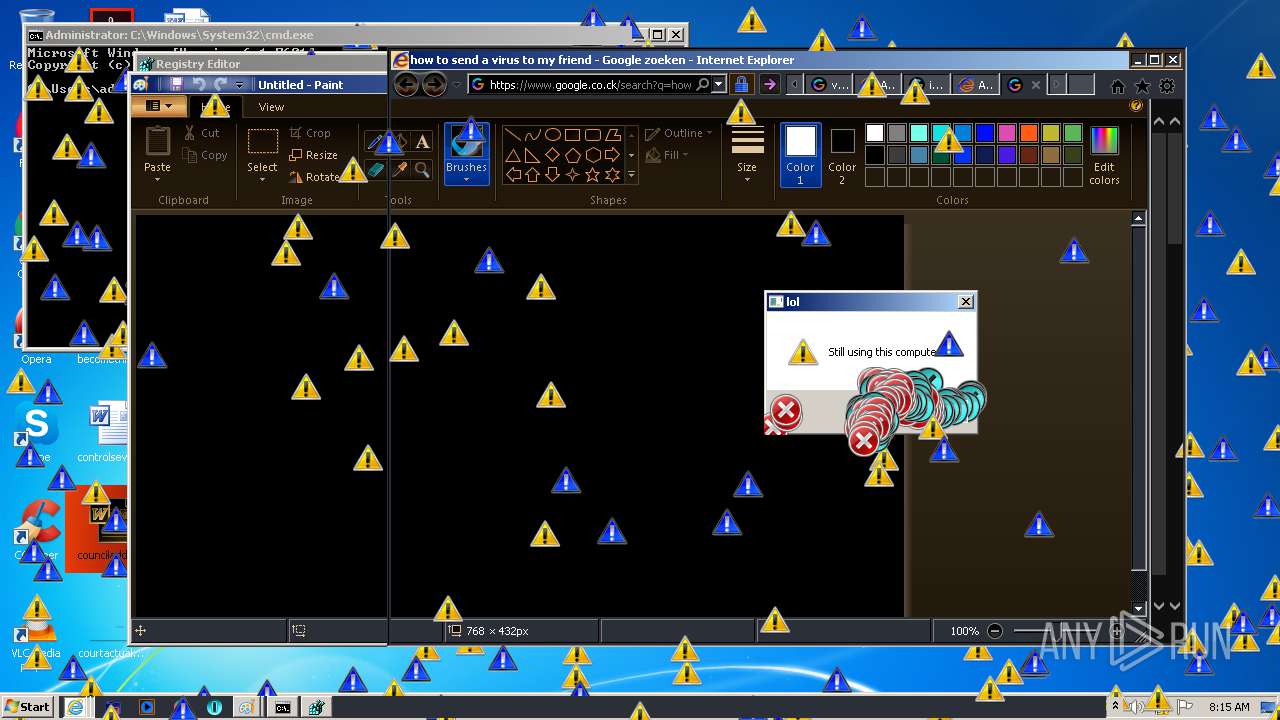
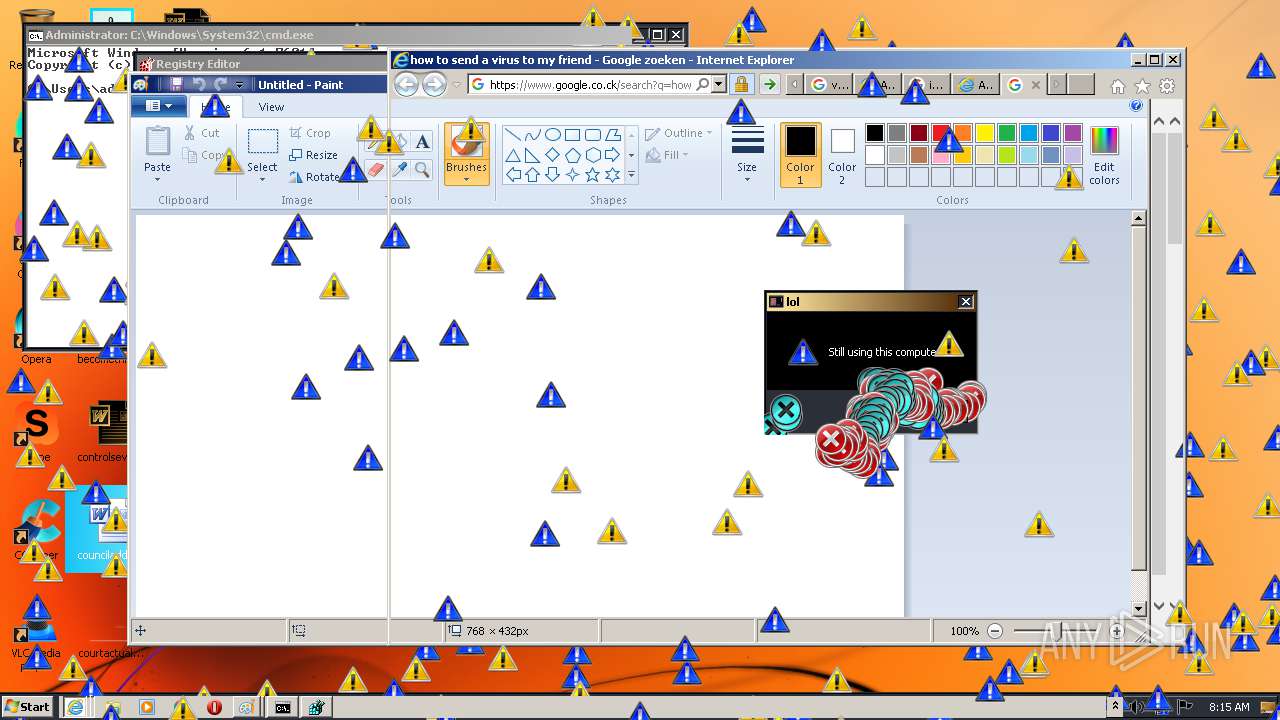
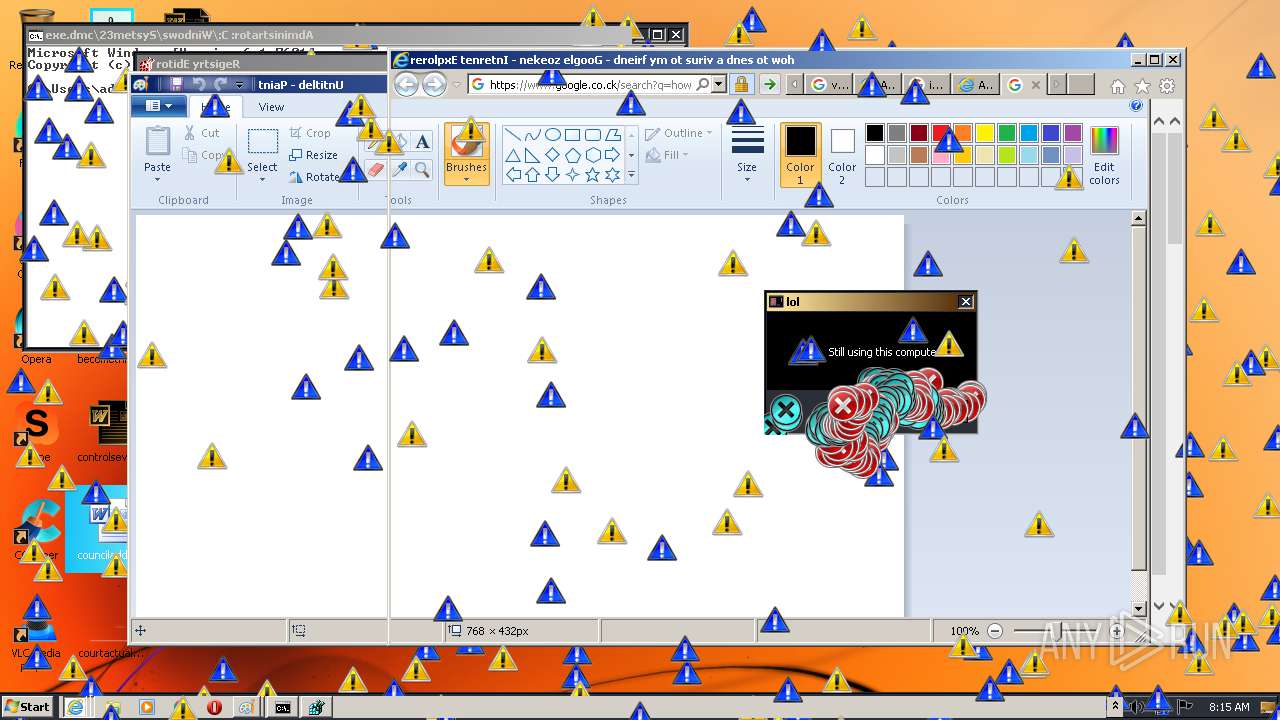
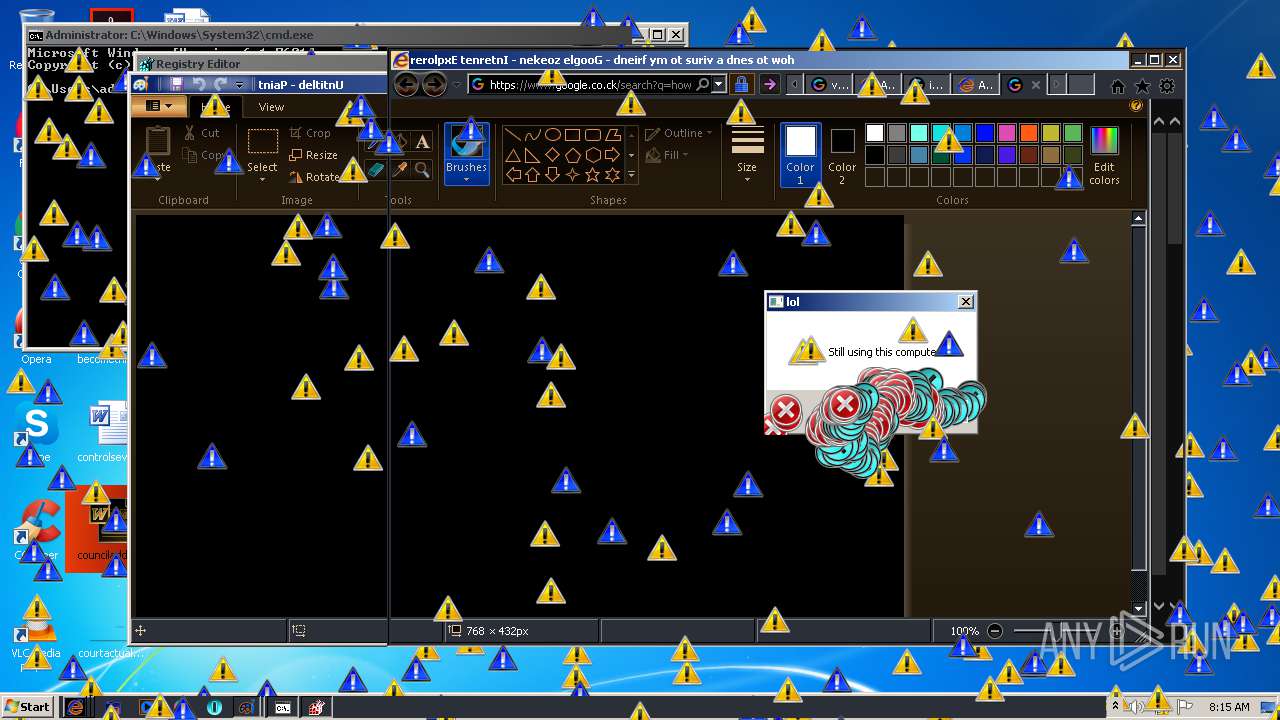
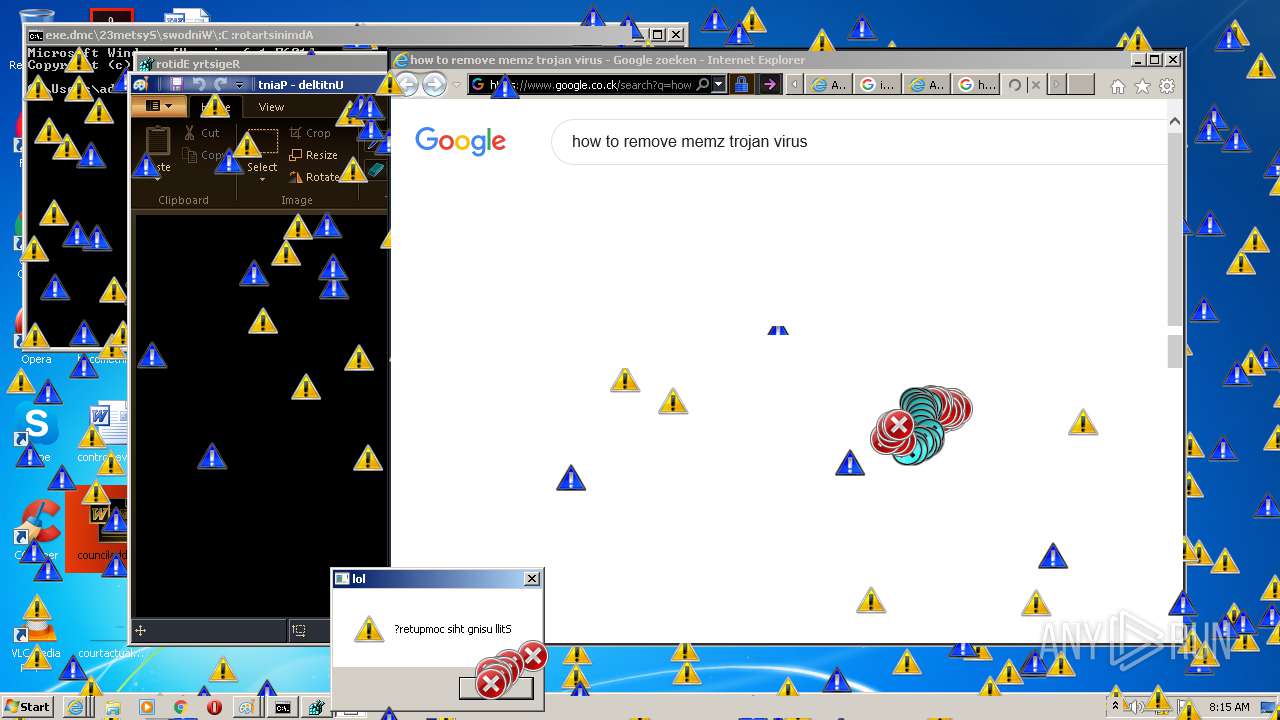
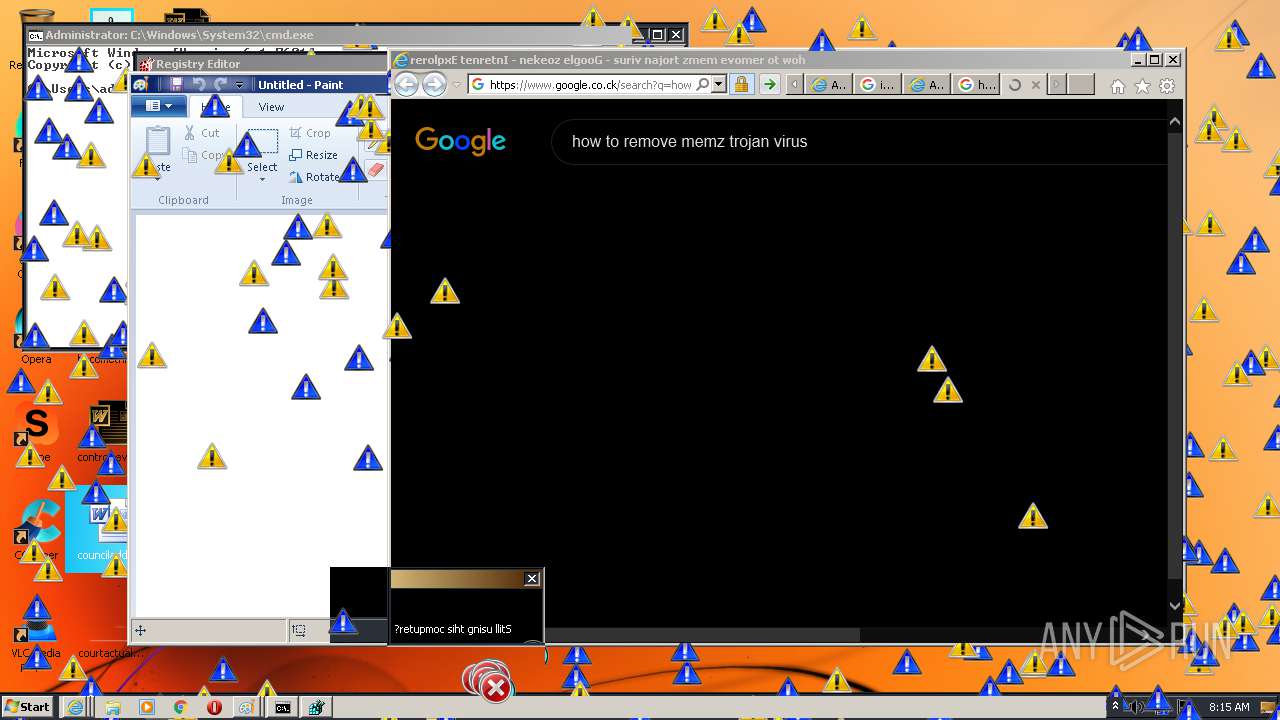
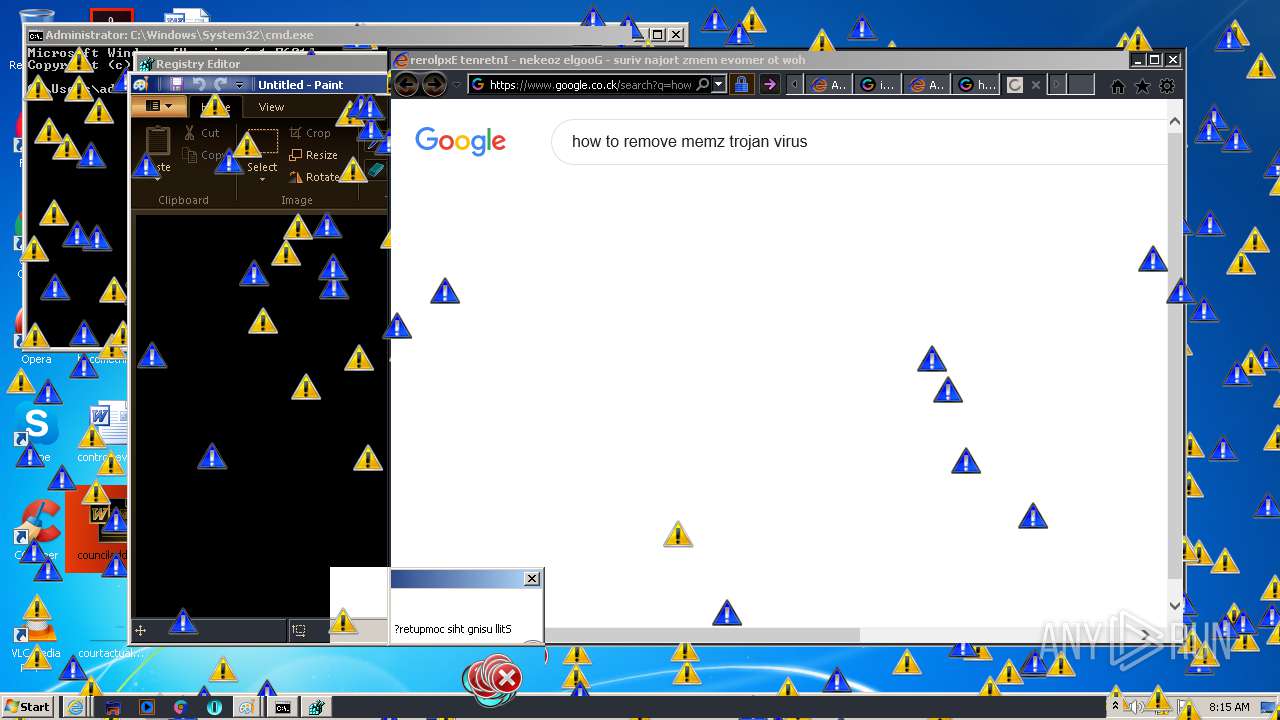
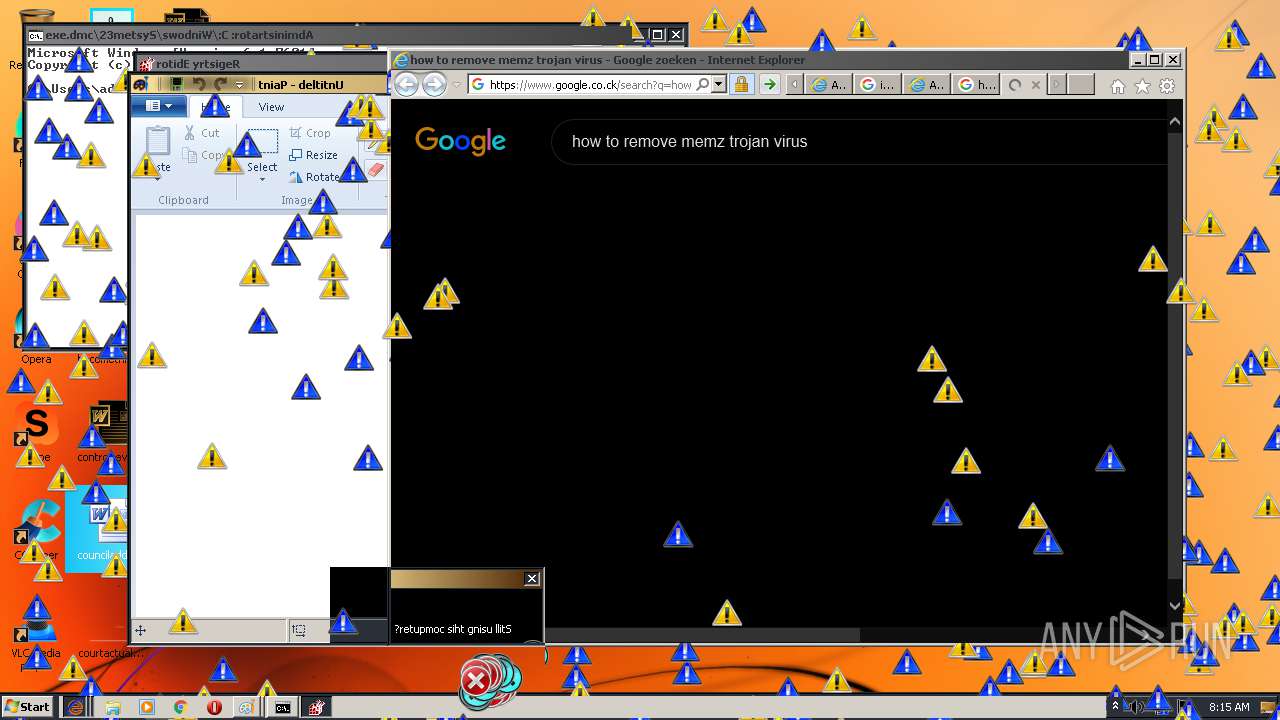
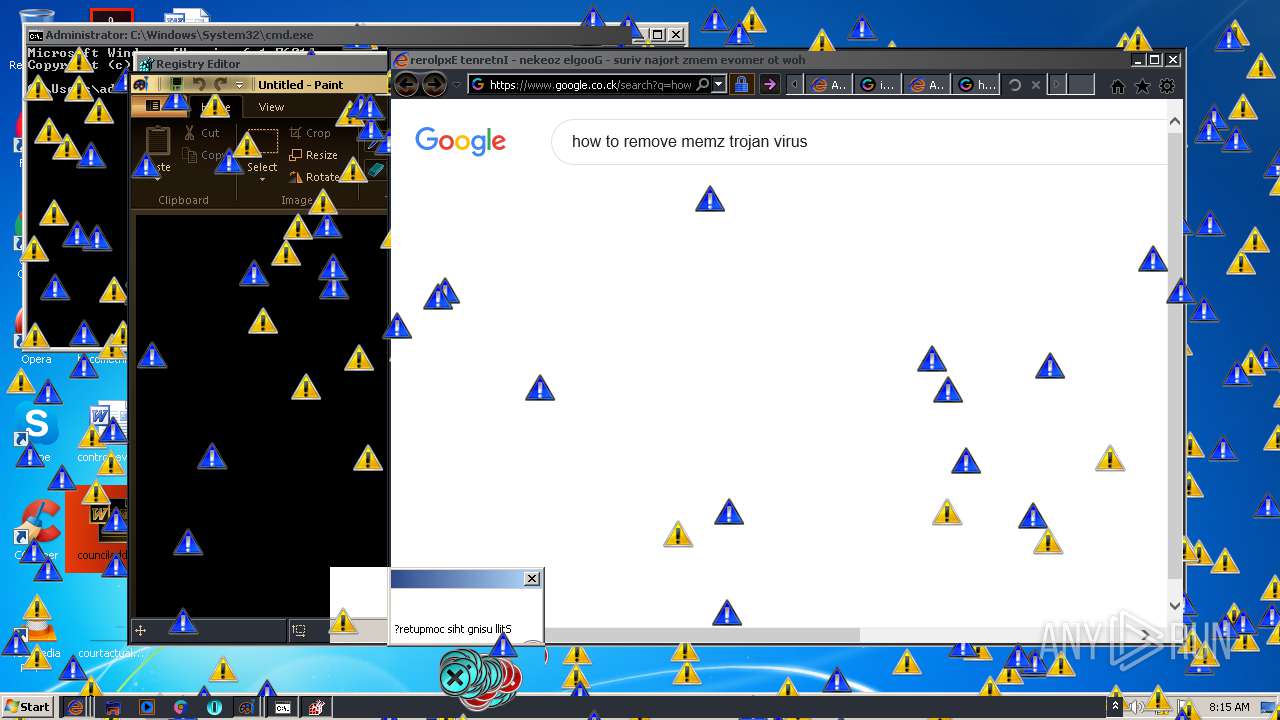
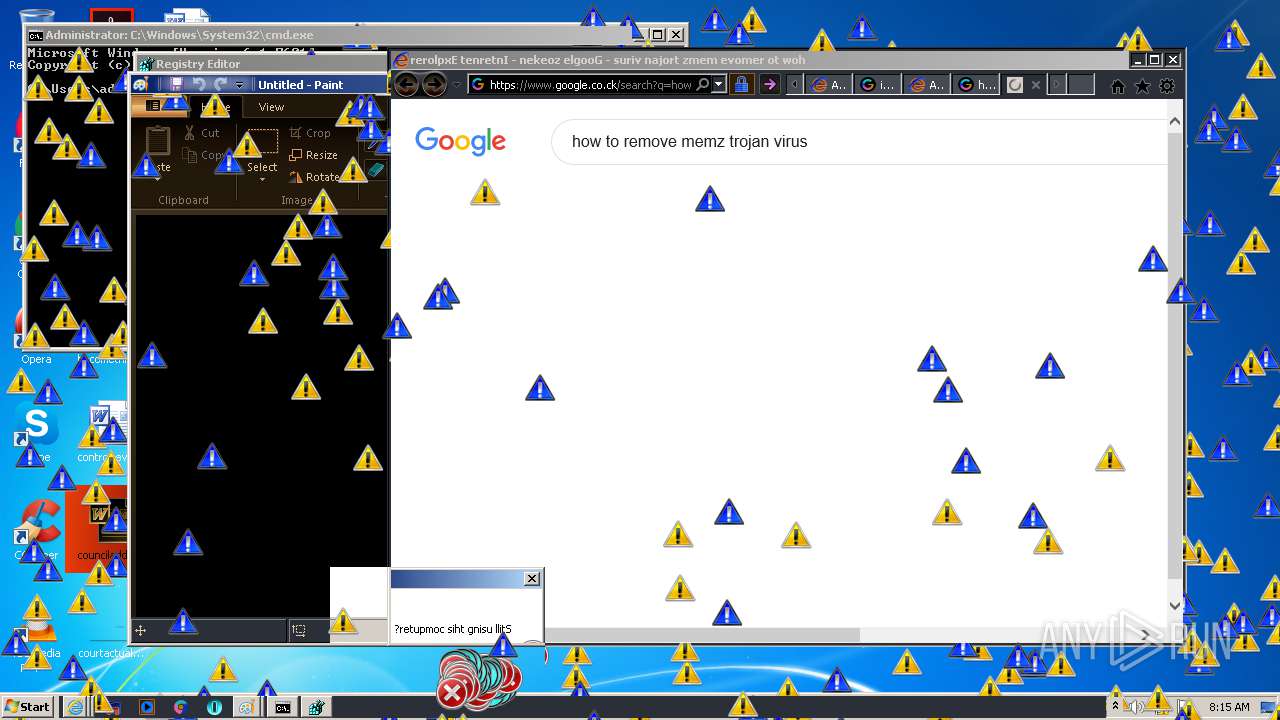
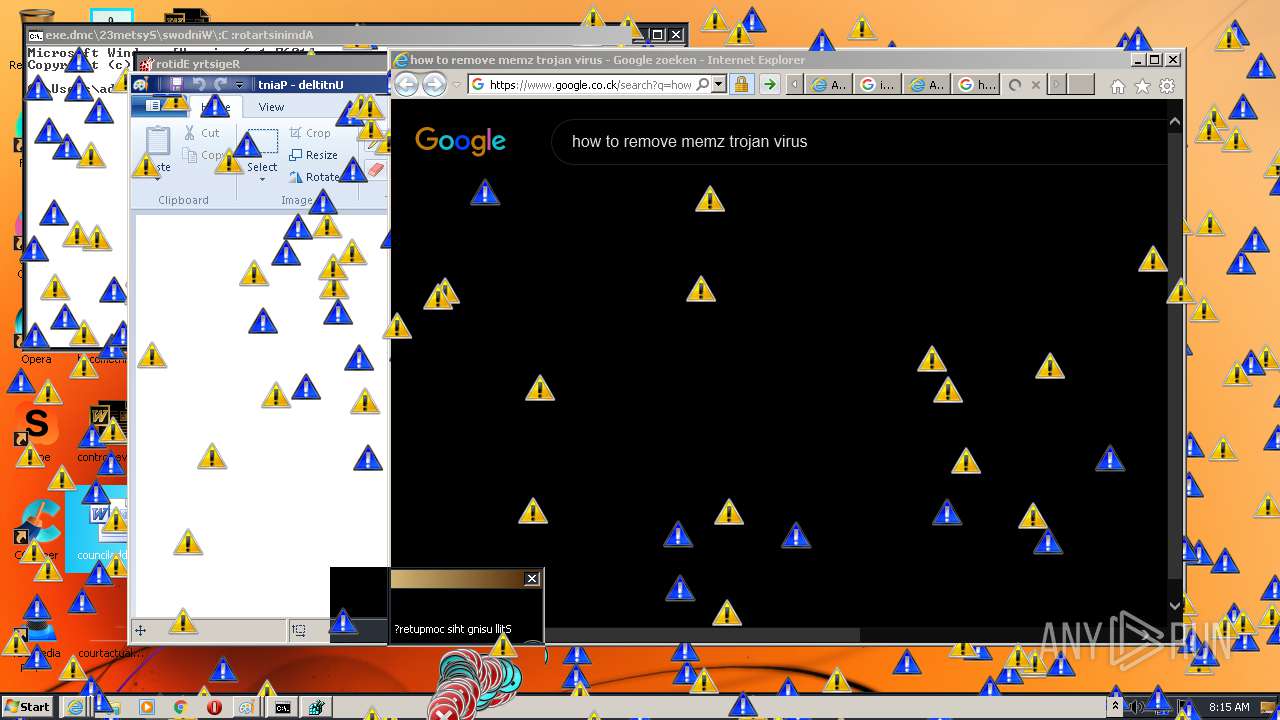
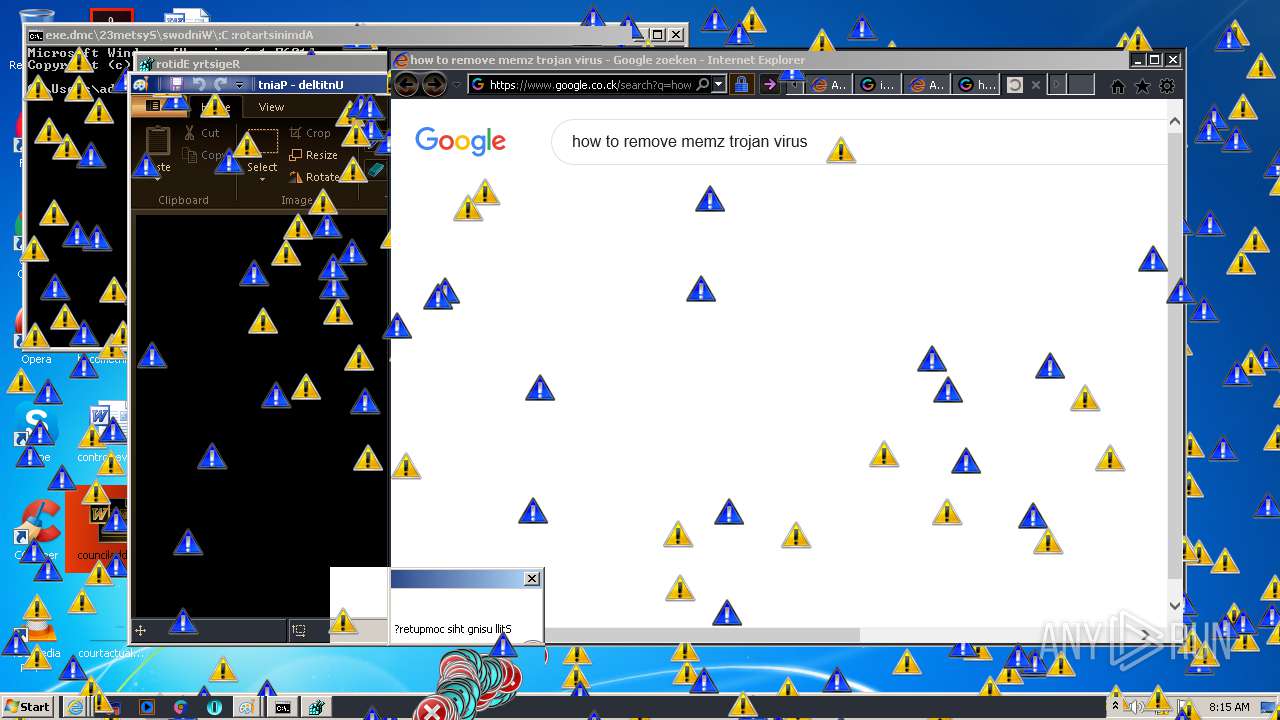
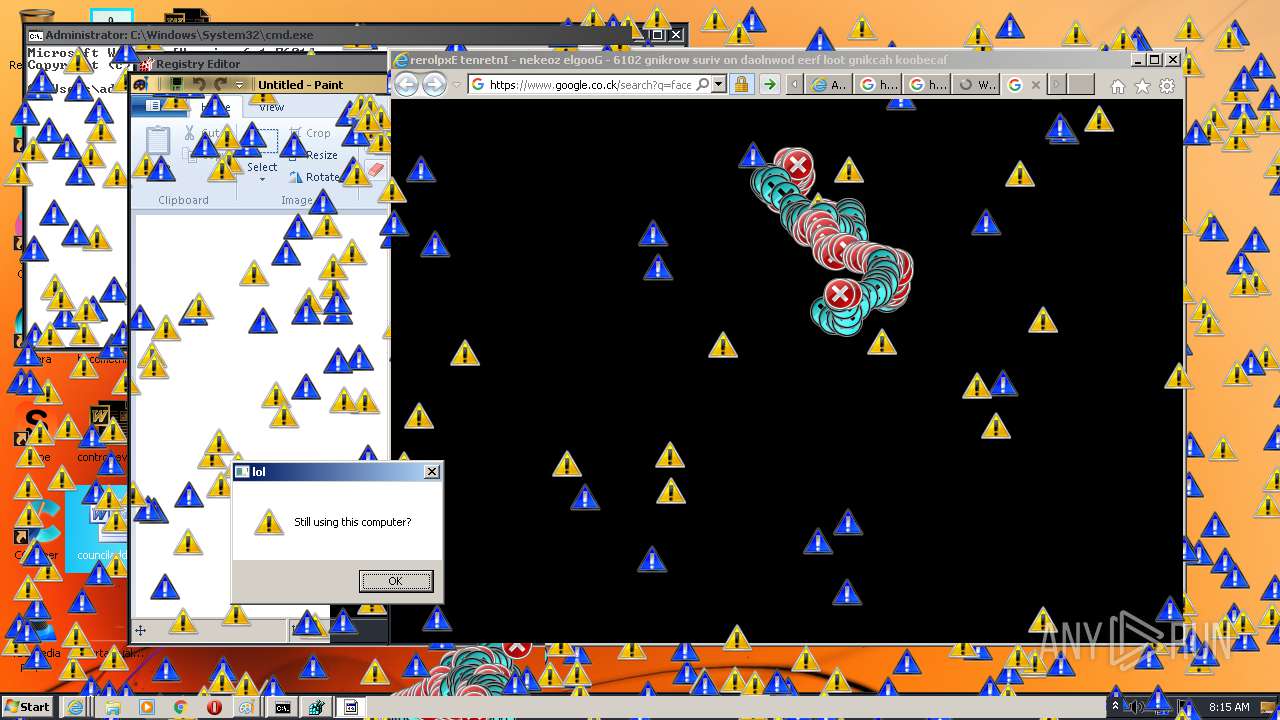
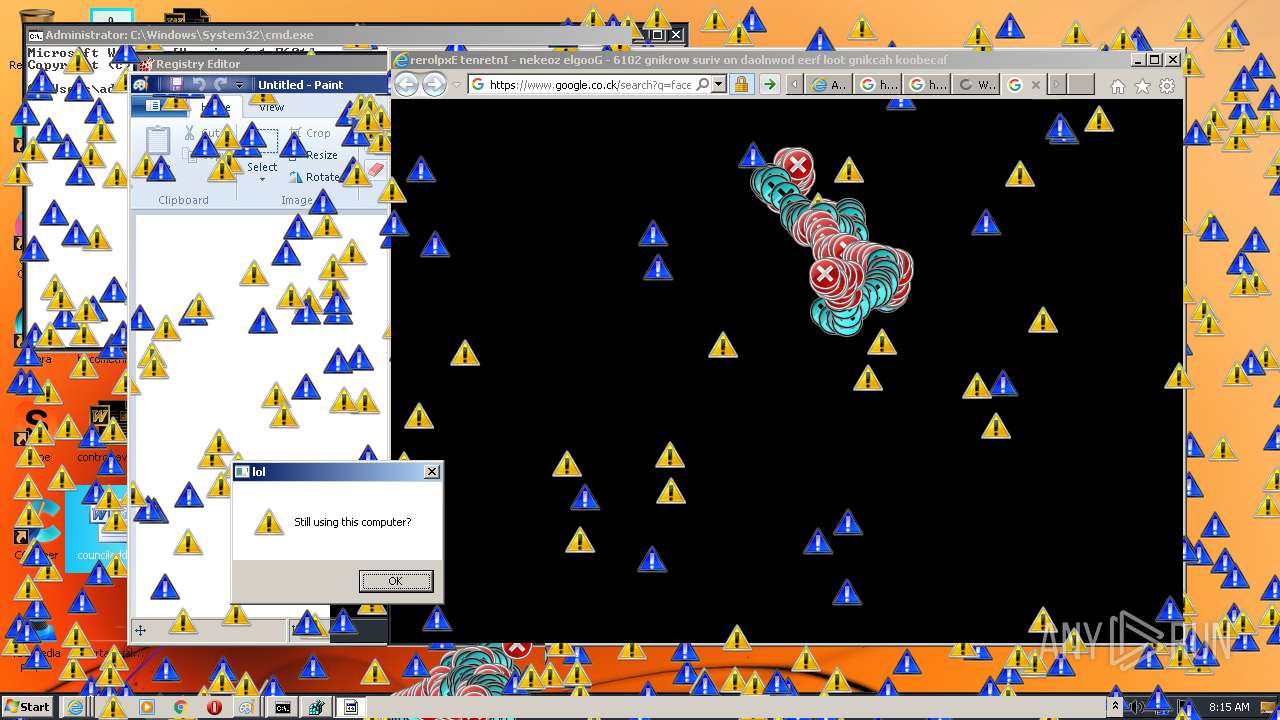
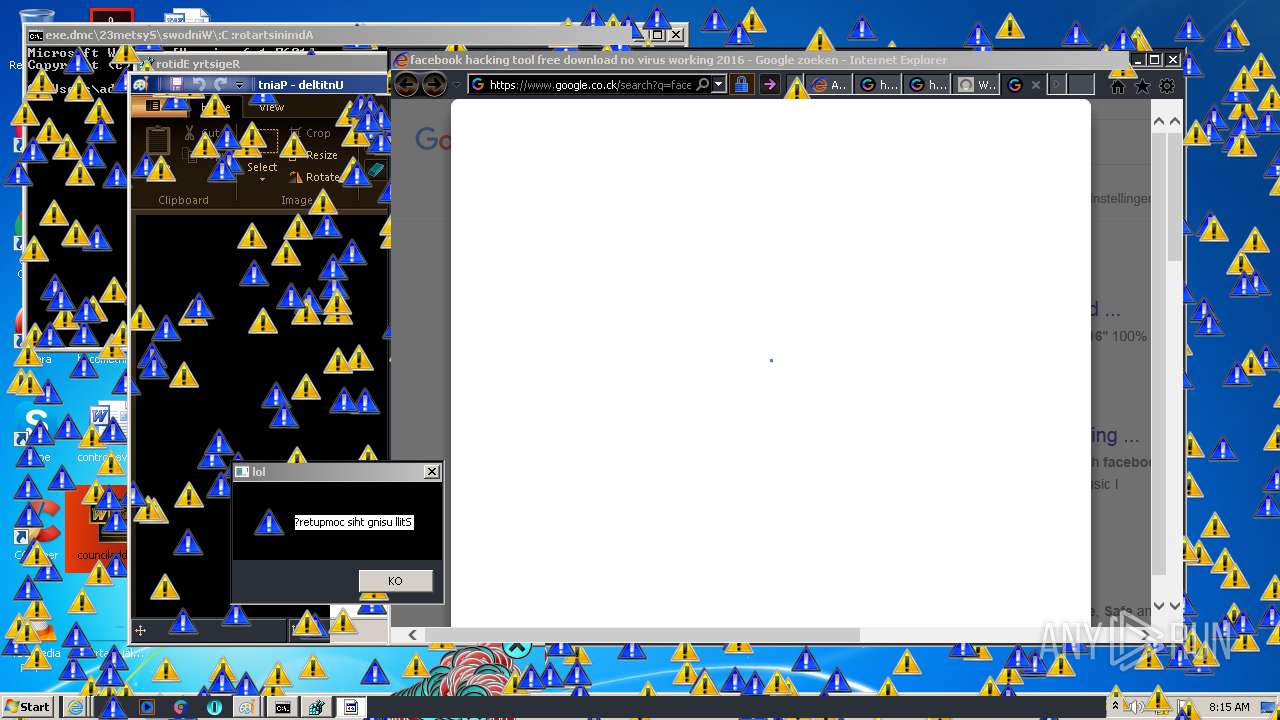
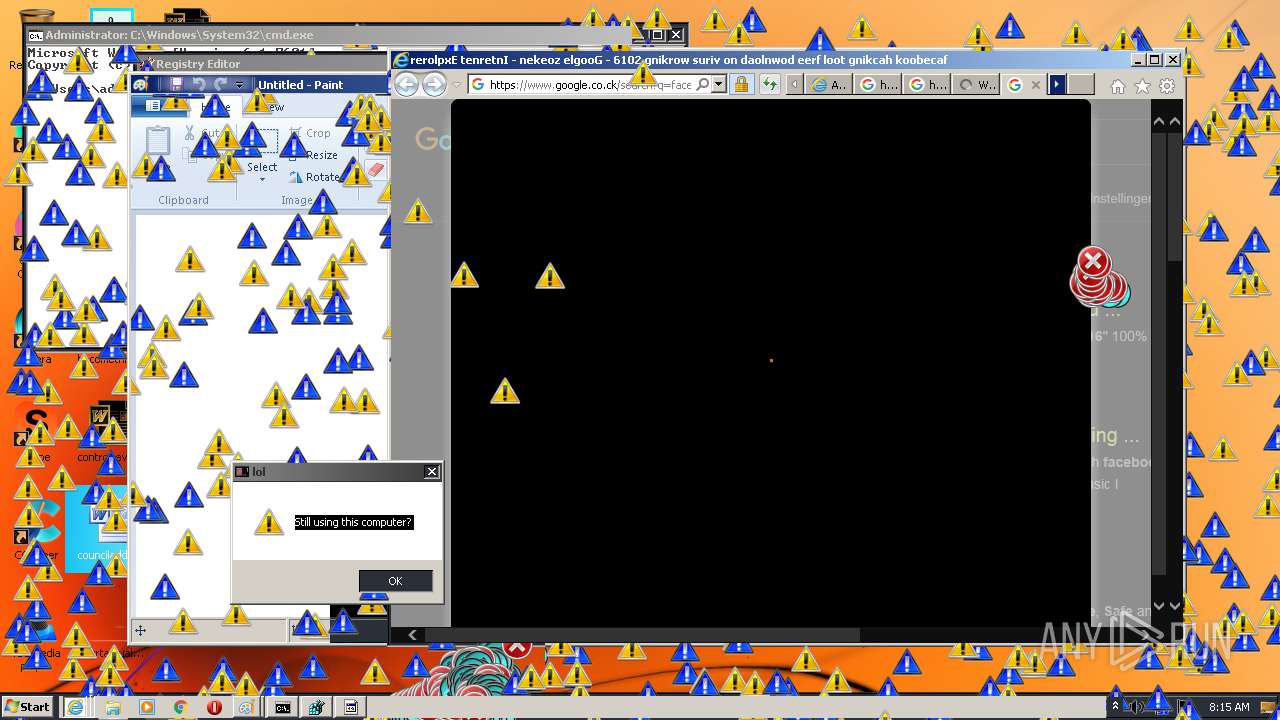
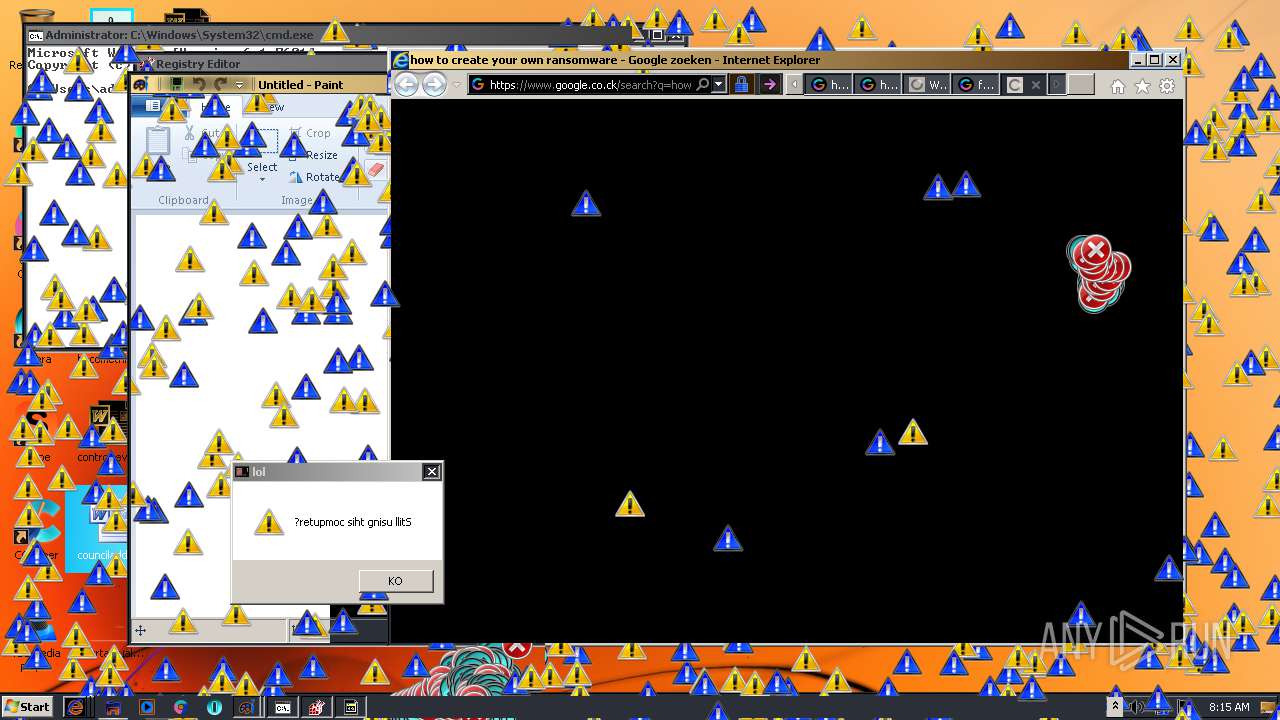
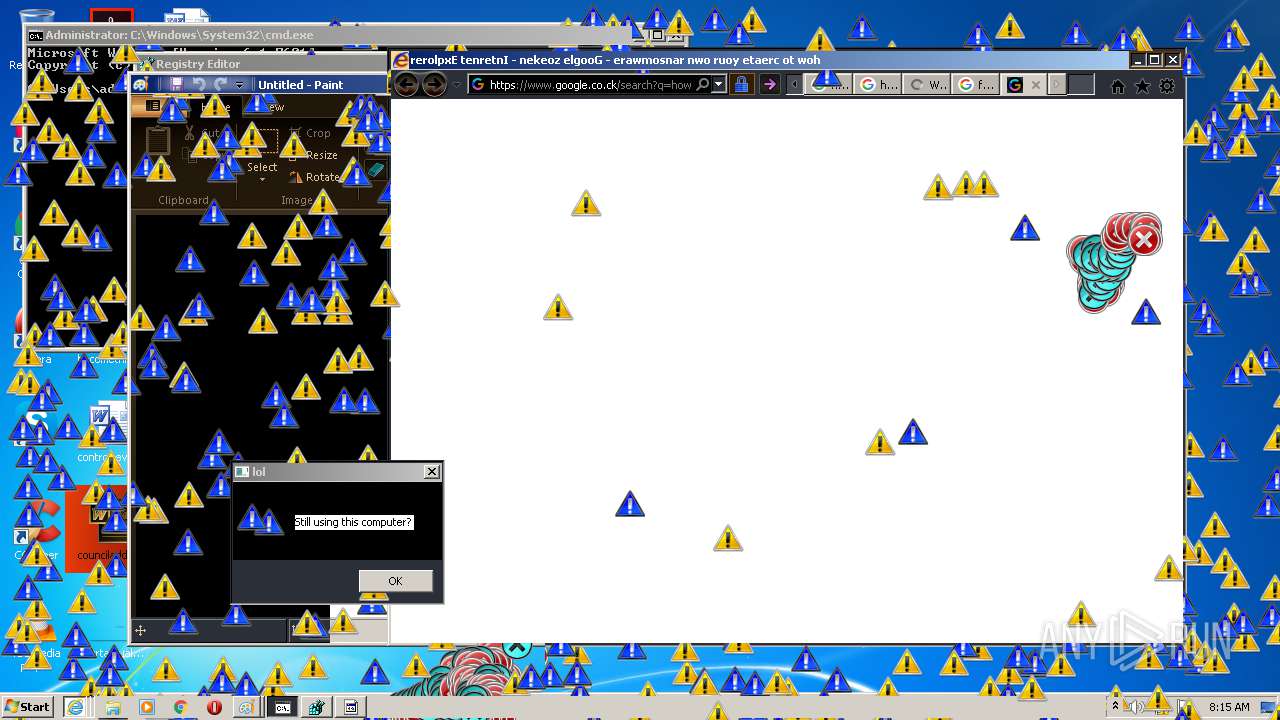
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2020, 07:10:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 19DBEC50735B5F2A72D4199C4E184960 |
| SHA1: | 6FED7732F7CB6F59743795B2AB154A3676F4C822 |
| SHA256: | A3D5715A81F2FBEB5F76C88C9C21EEEE87142909716472F911FF6950C790C24D |
| SSDEEP: | 192:sIvxdXSQeWSg9JJS/lcIEiwqZKBkDFR43xWTM3LHn8f26gyr6yfFCj3r:sMVSaSEglcIqq3agmLc+6gyWqFCj |
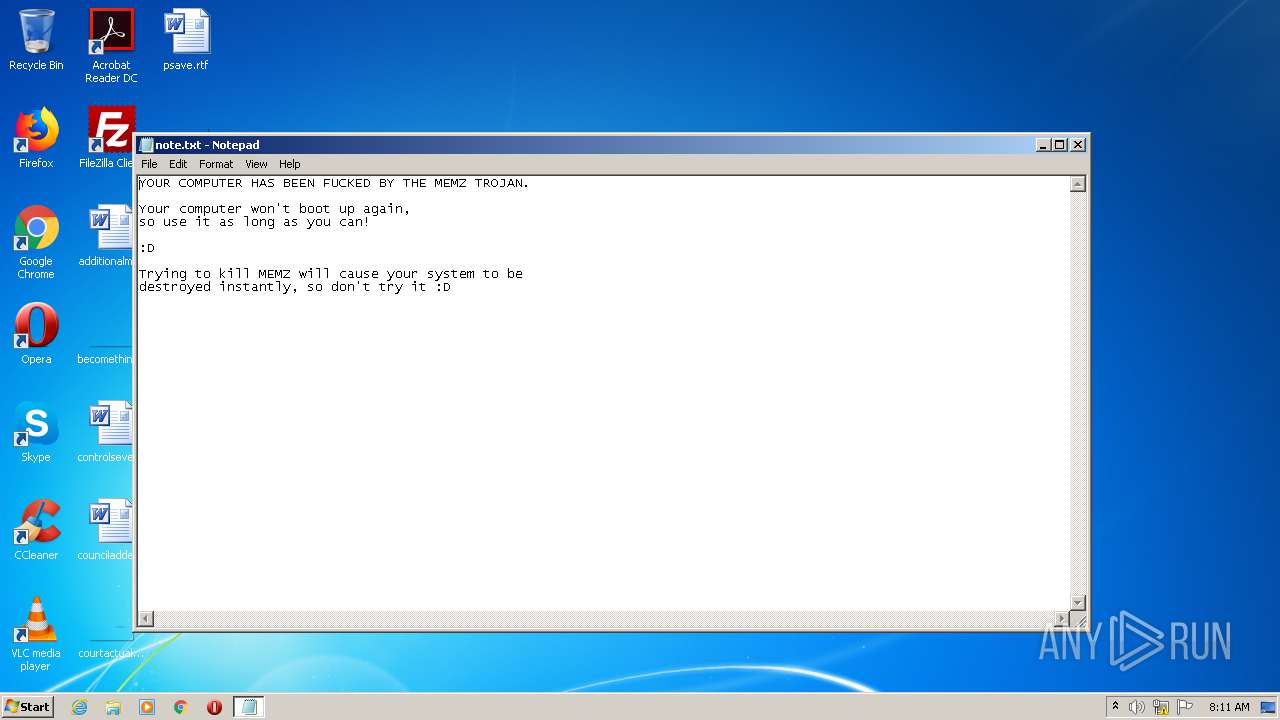
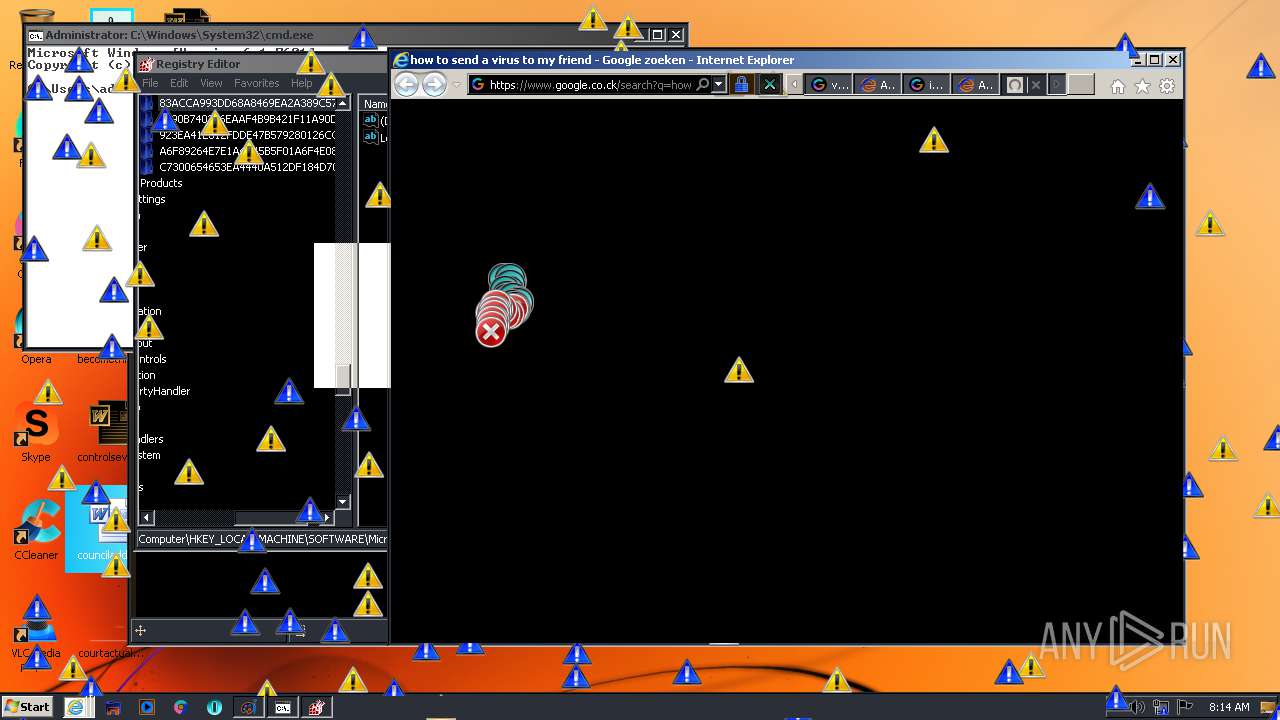
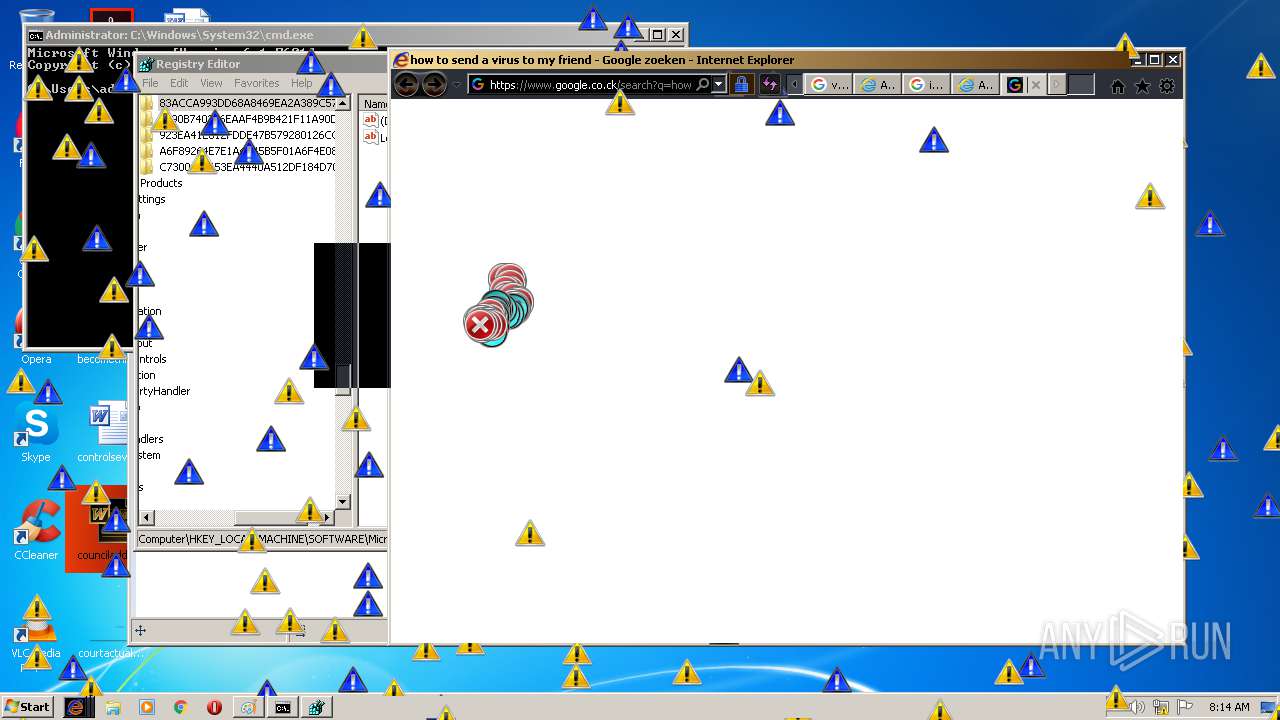
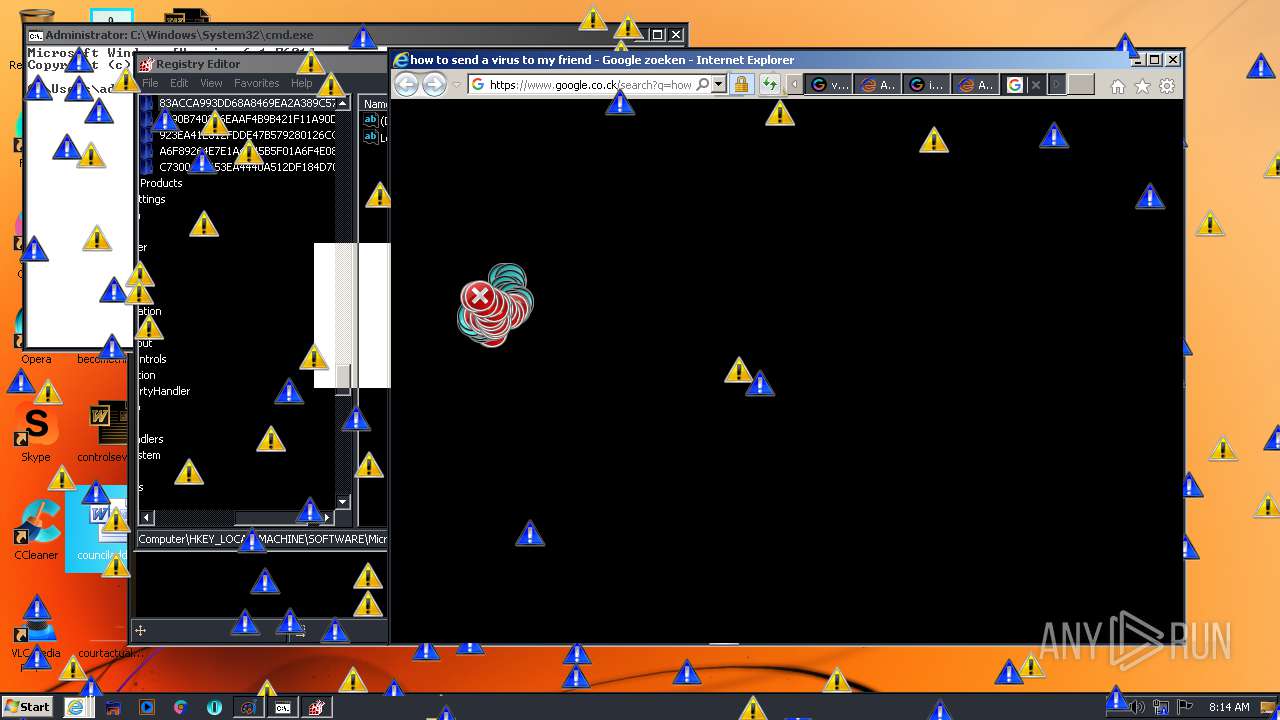
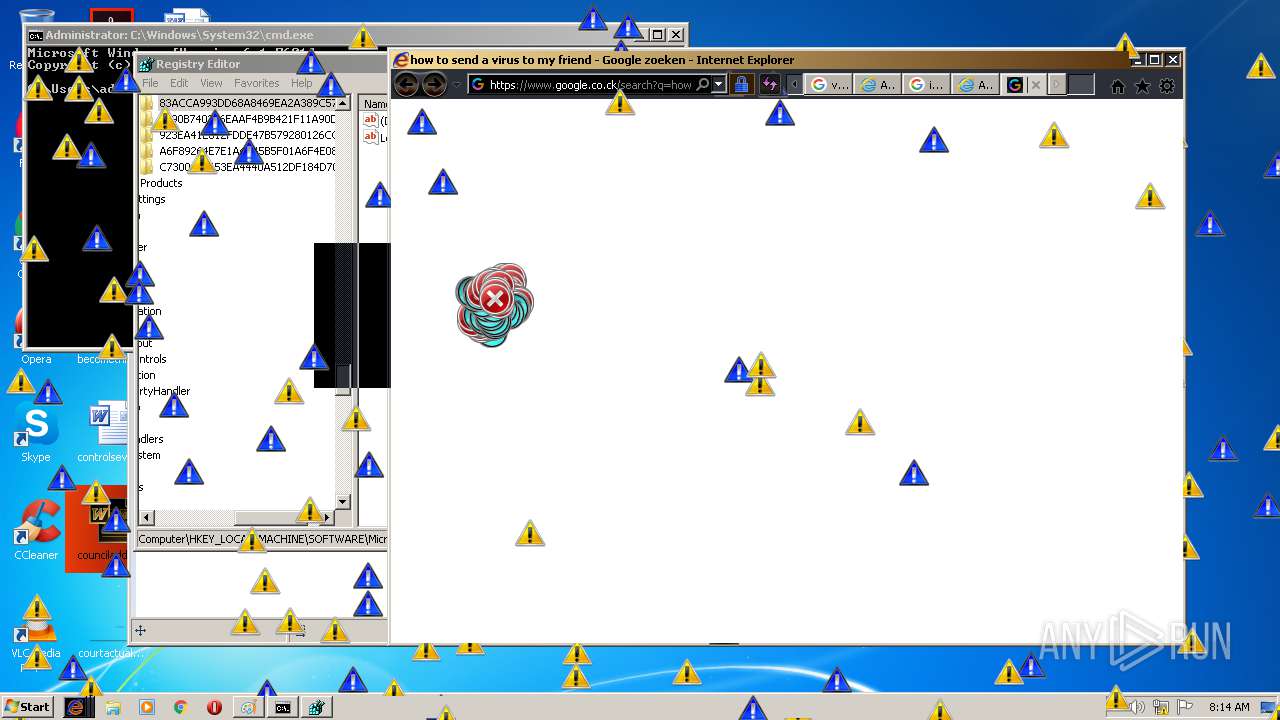
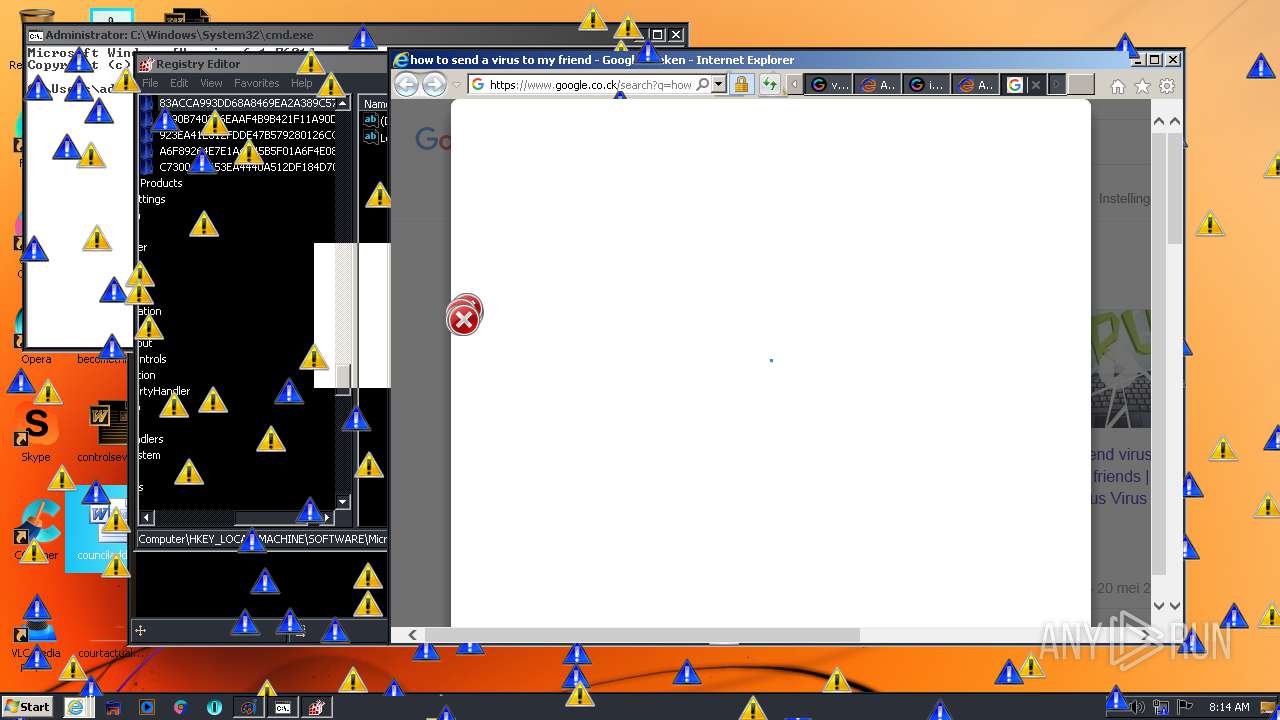
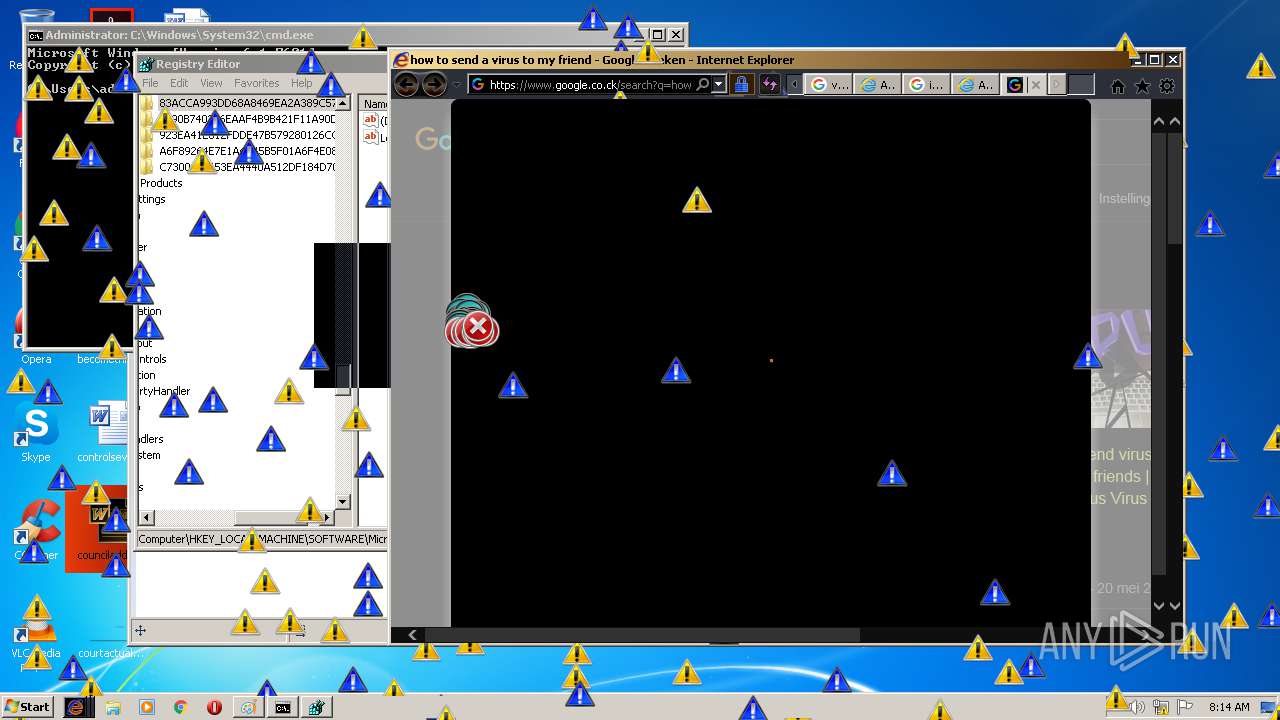
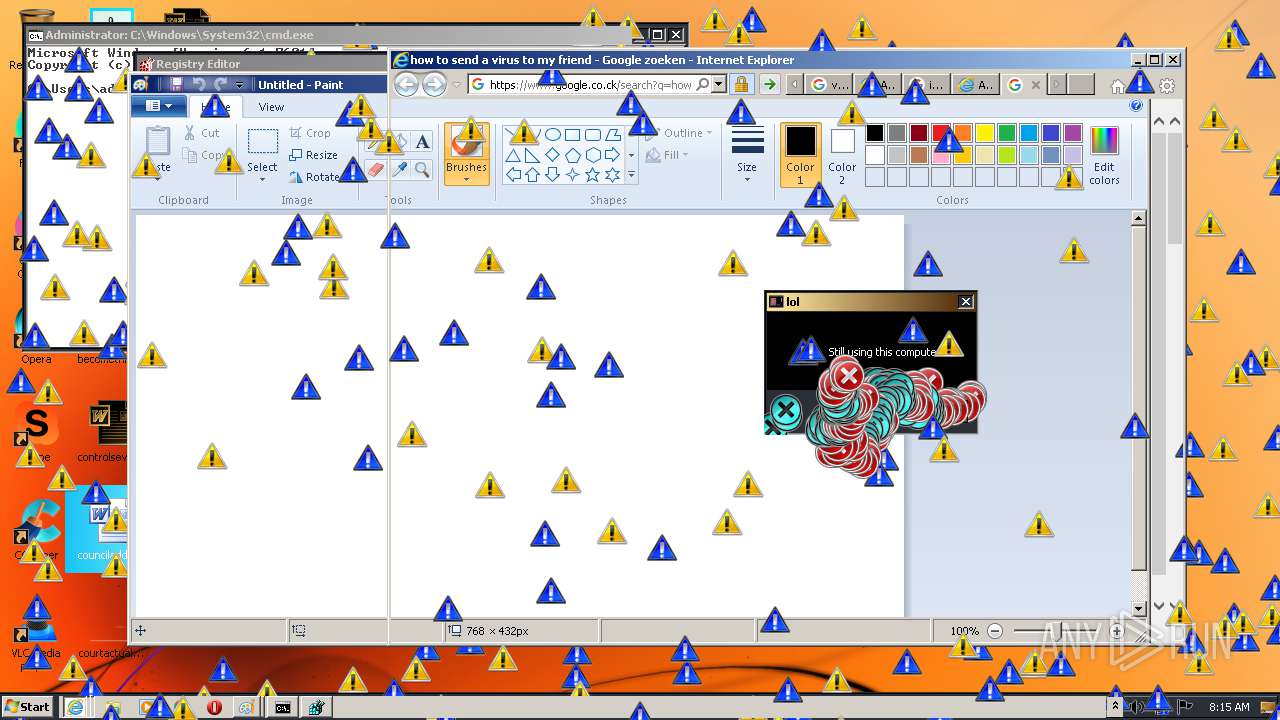
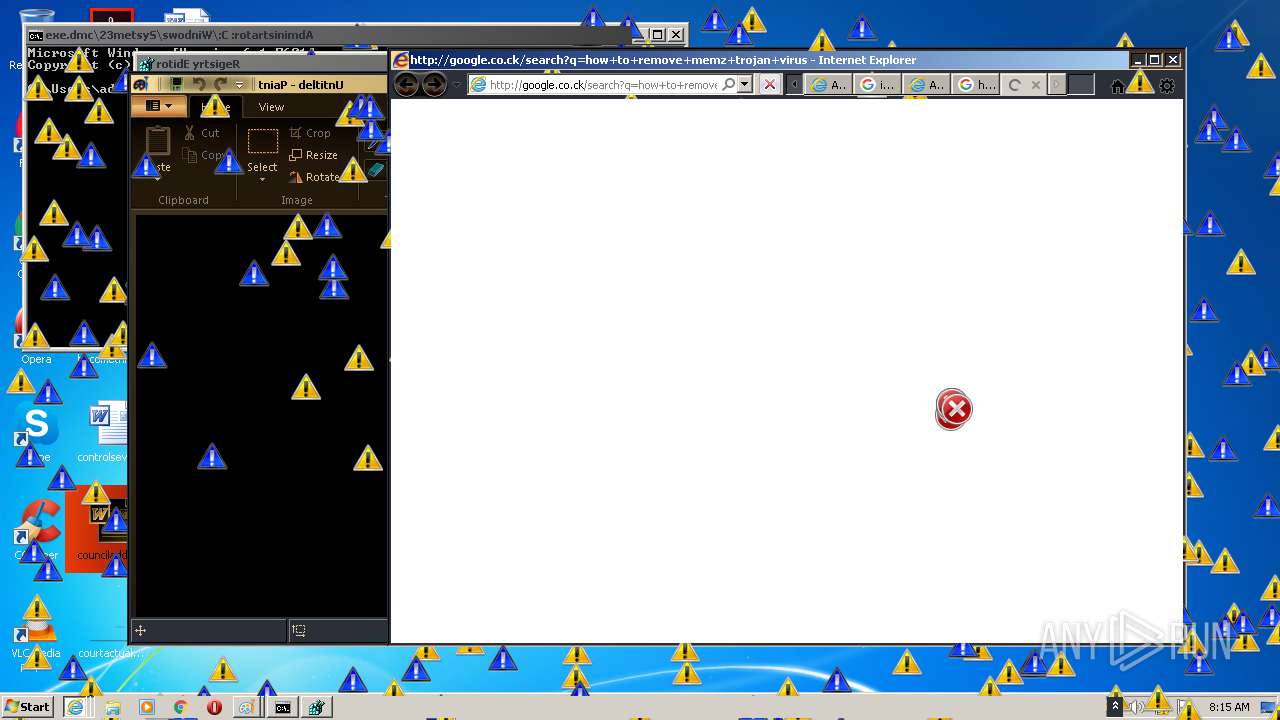
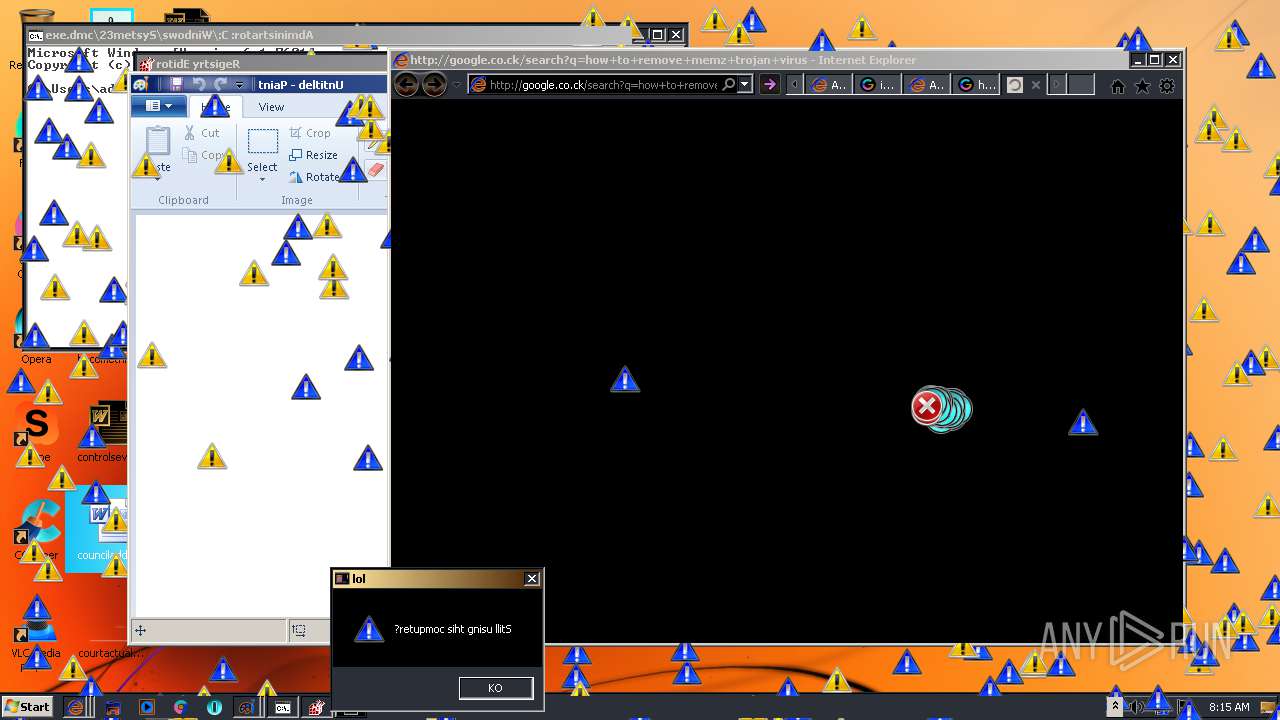
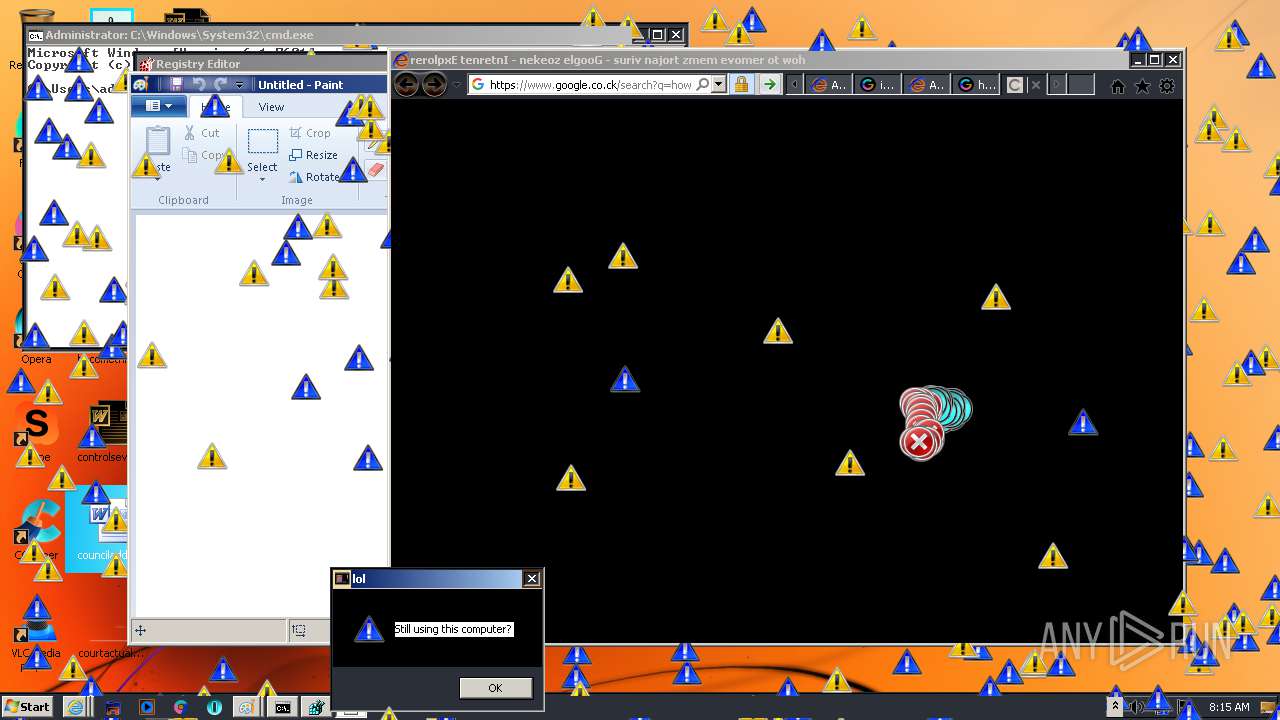
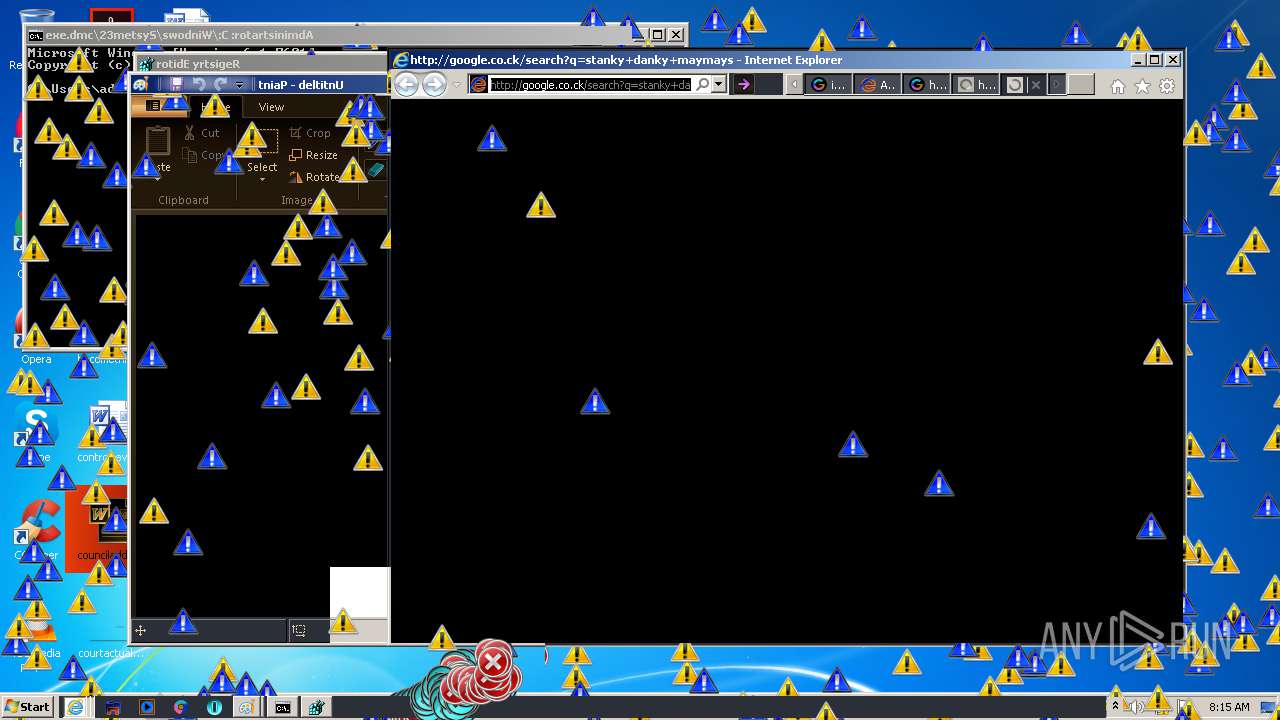
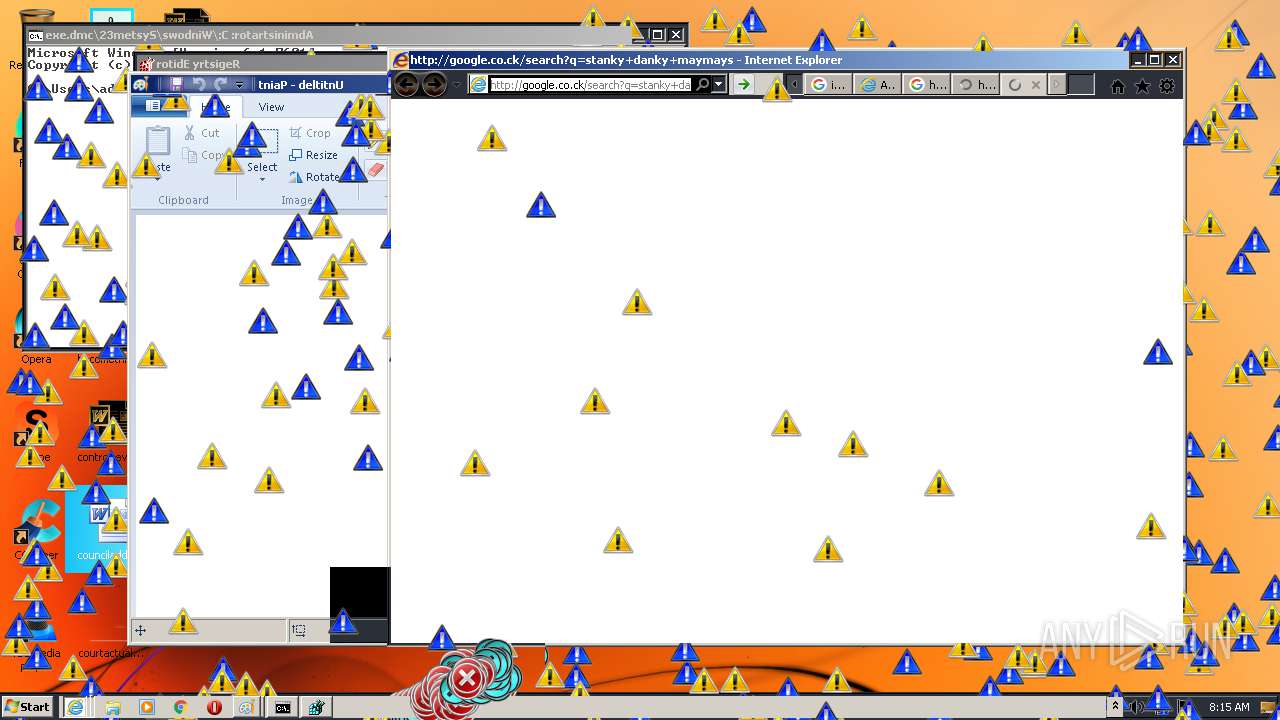
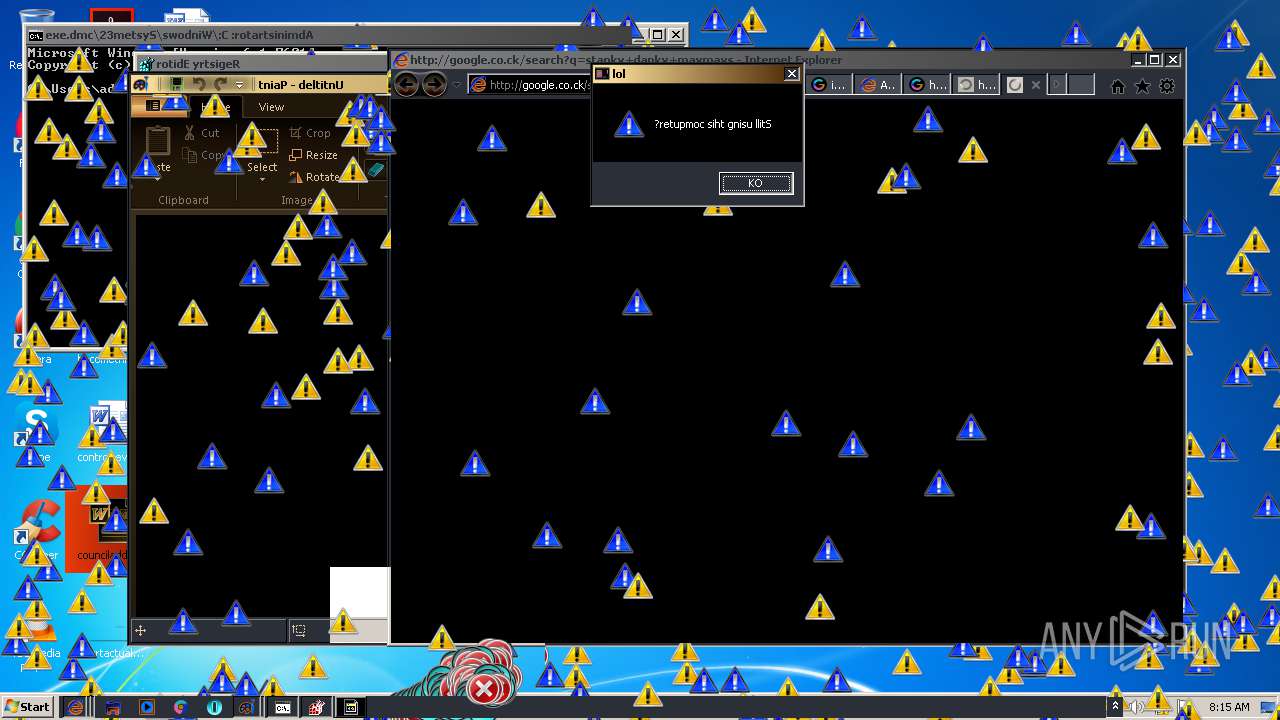
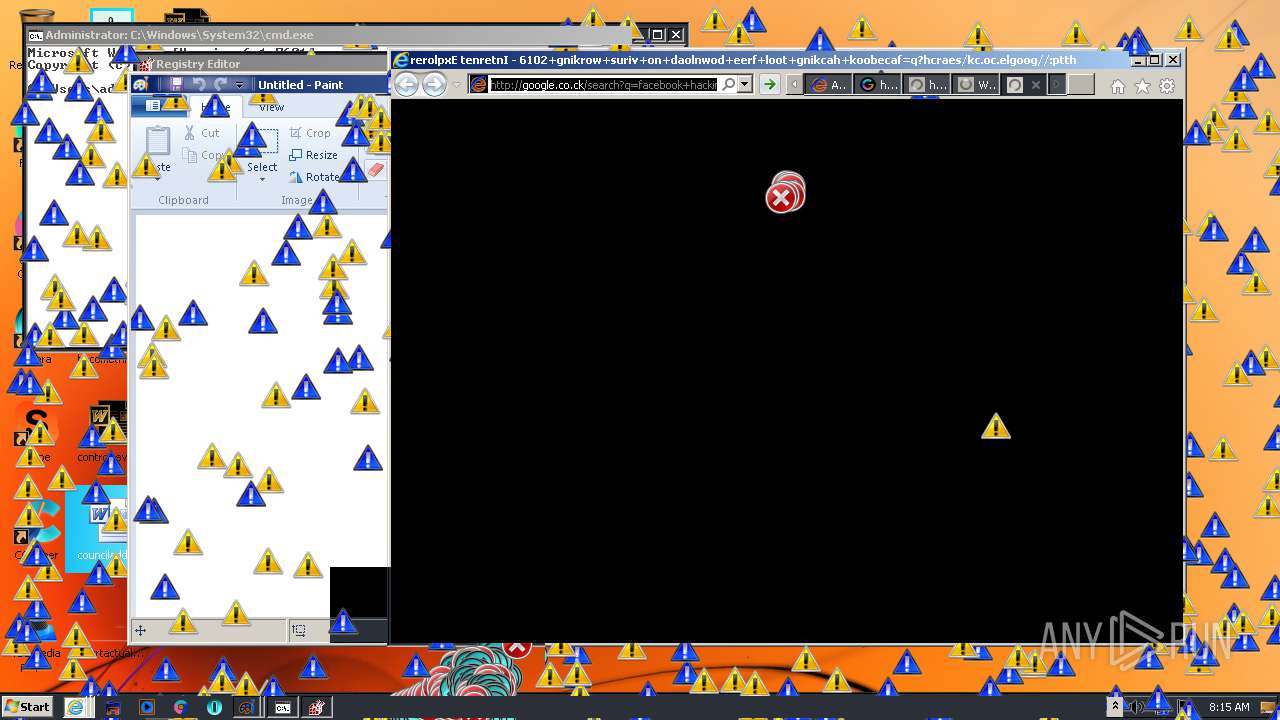
MALICIOUS
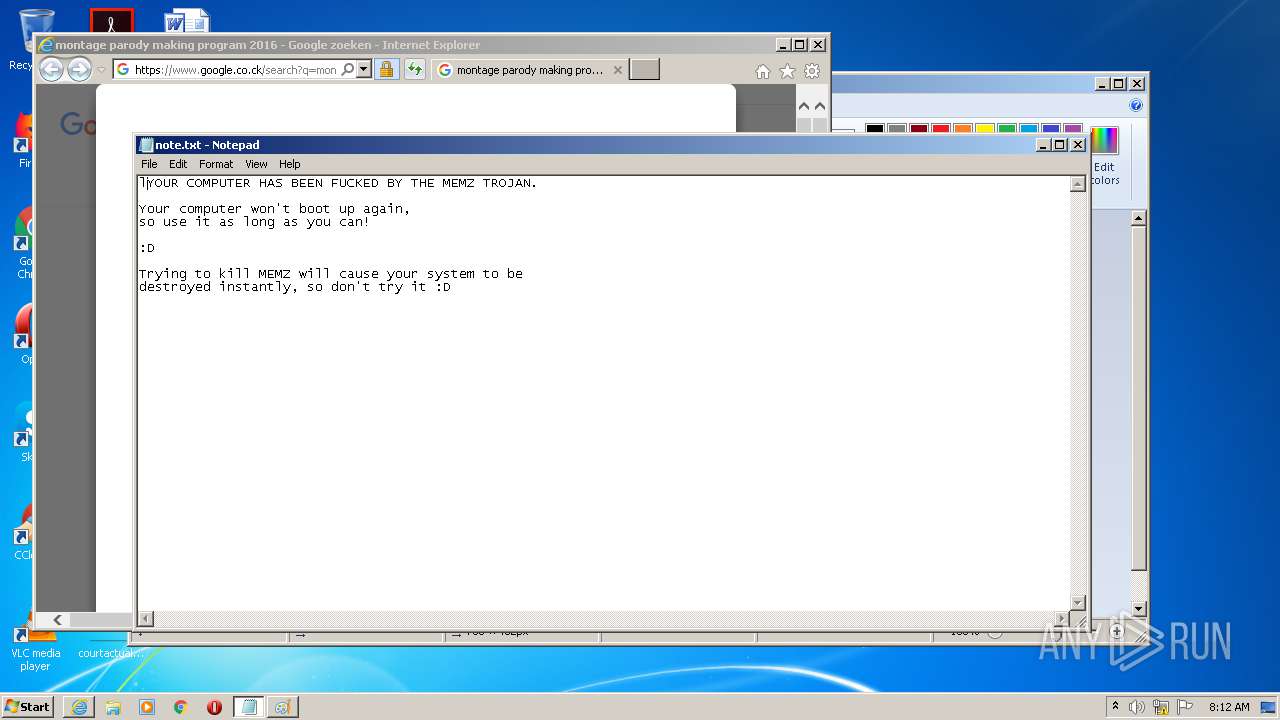
Low-level write access rights to disk partition
- MEMZ-Destructive.exe (PID: 1348)
Runs app for hidden code execution
- MEMZ-Destructive.exe (PID: 1348)
SUSPICIOUS
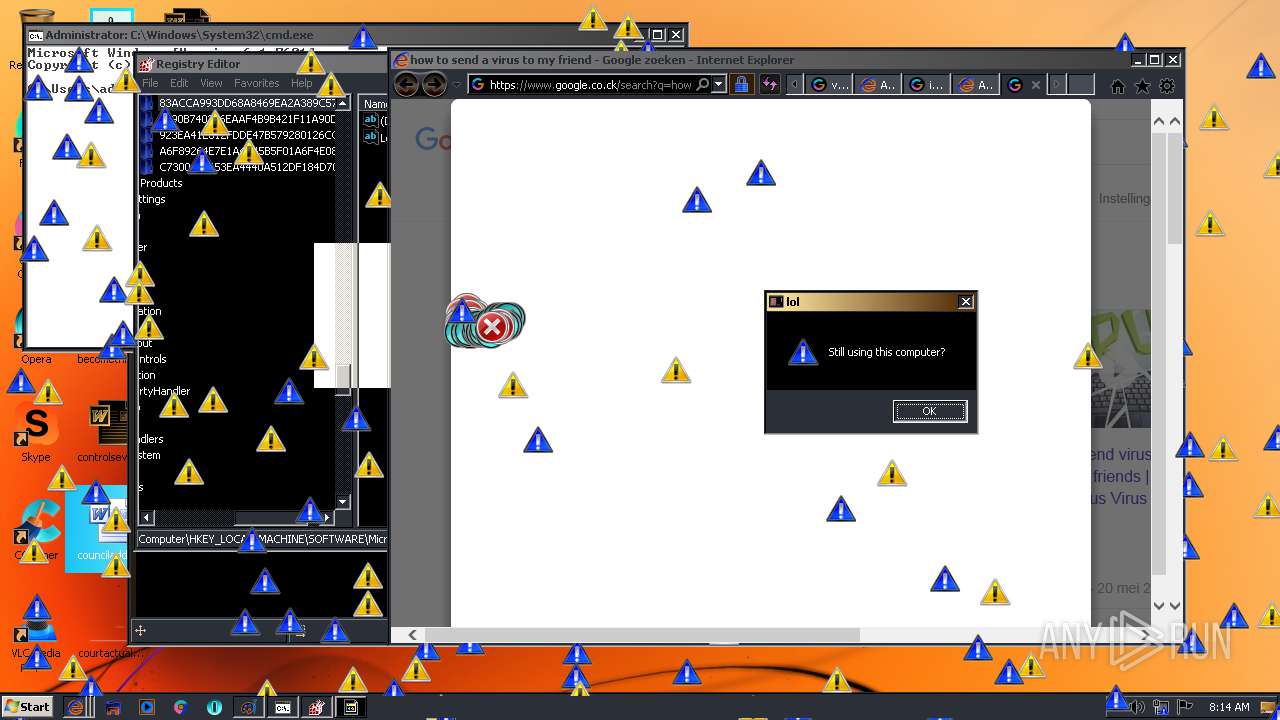
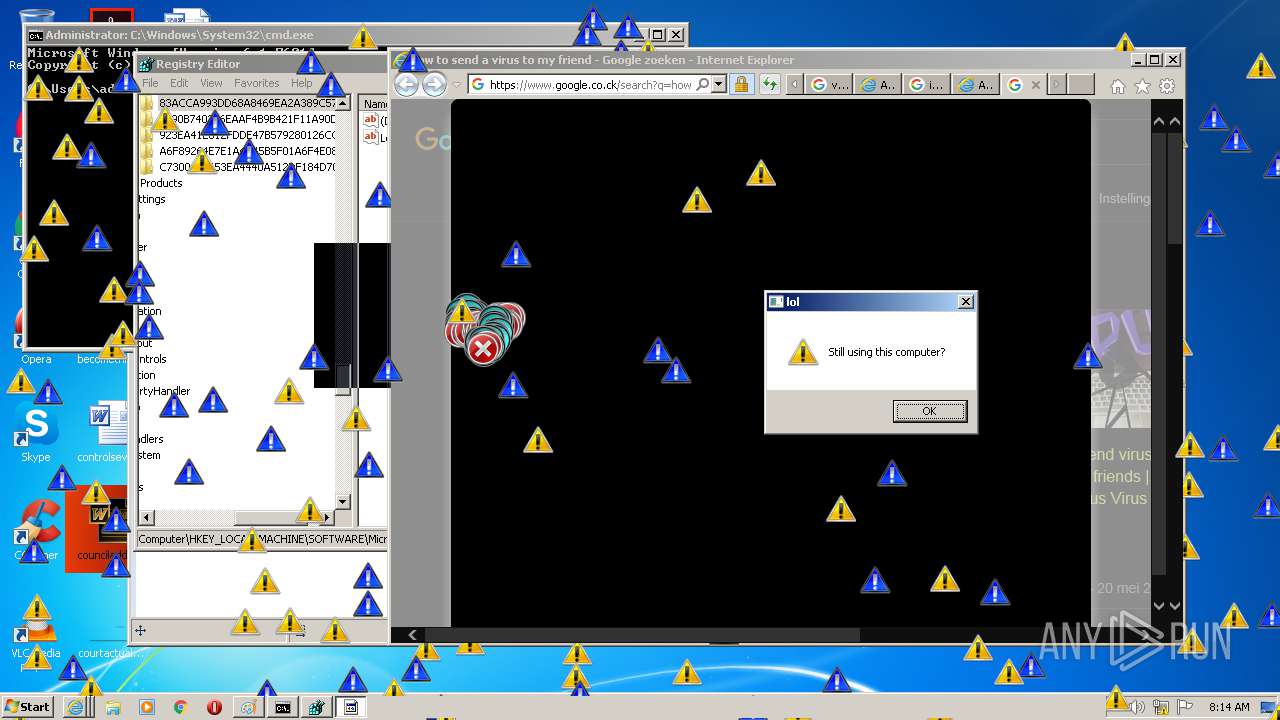
Application launched itself
- MEMZ-Destructive.exe (PID: 3248)
Low-level read access rights to disk partition
- MEMZ-Destructive.exe (PID: 1348)
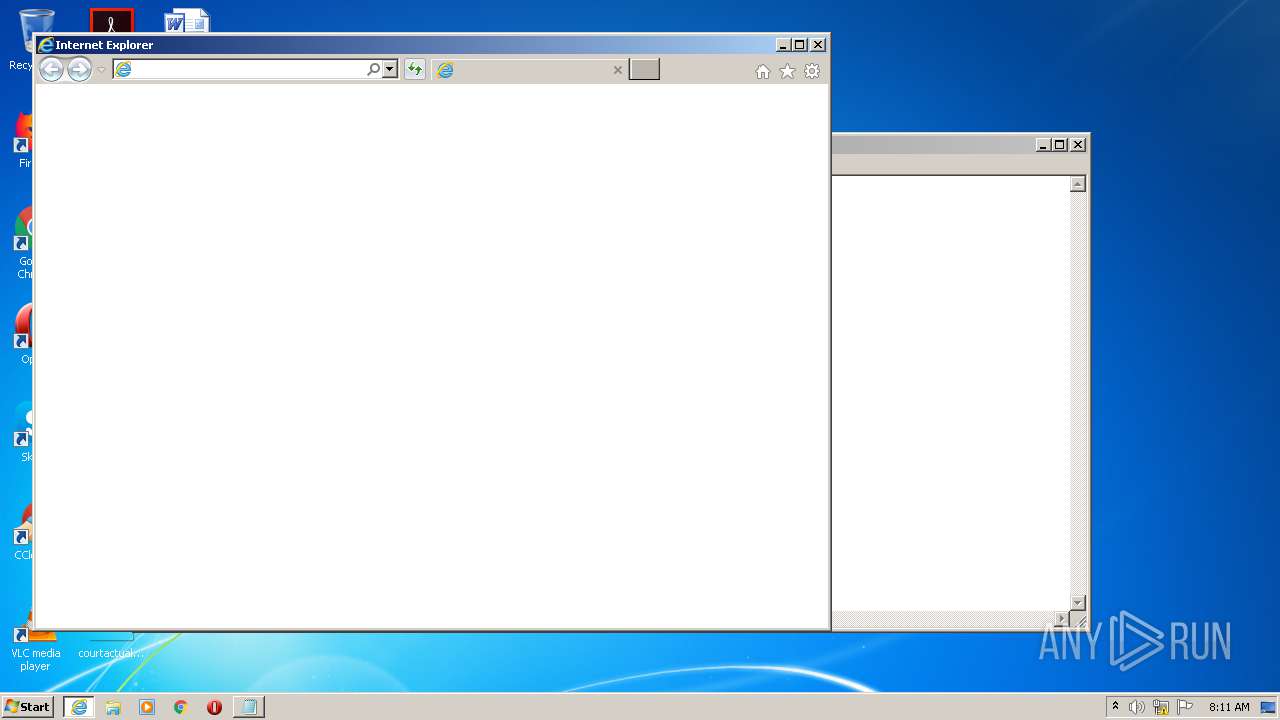
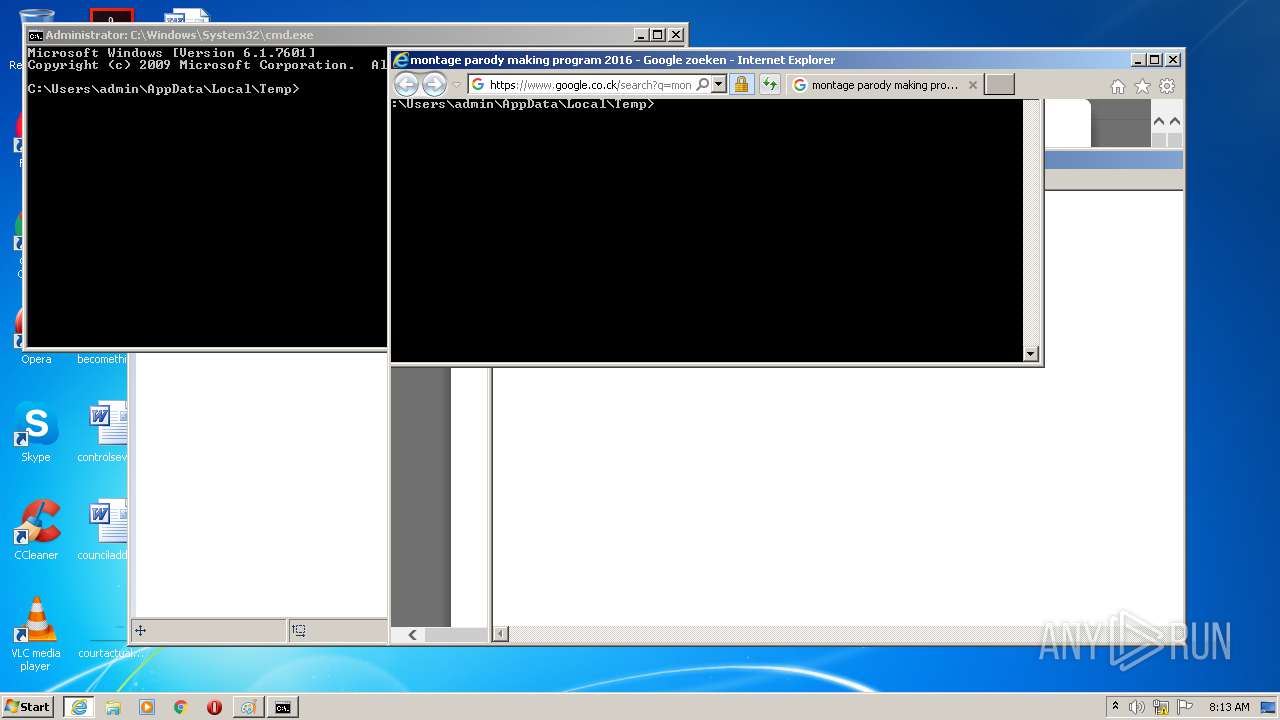
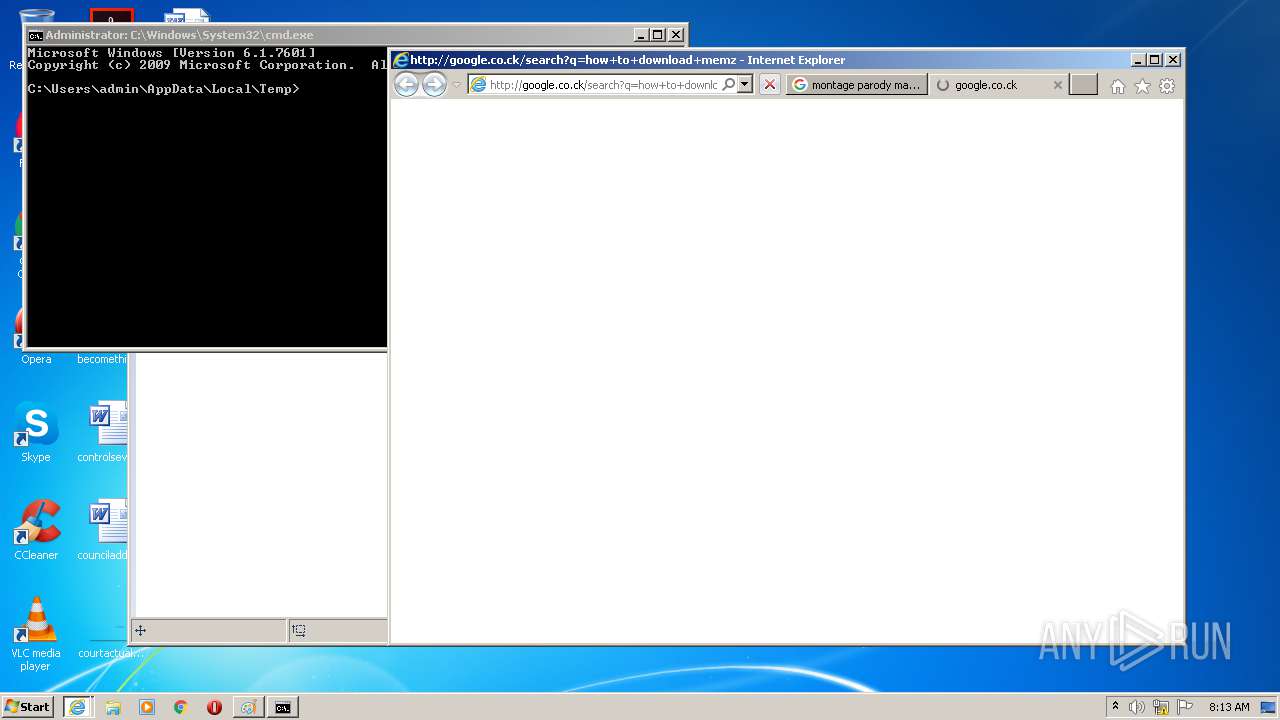
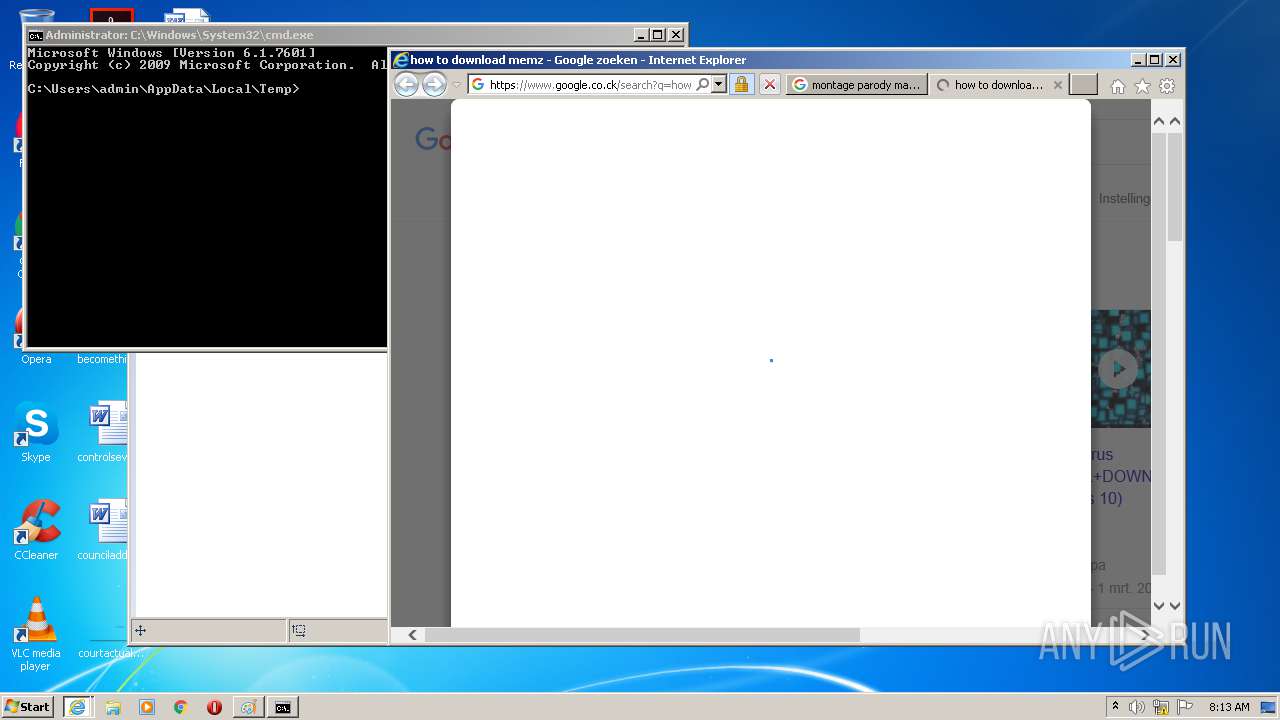
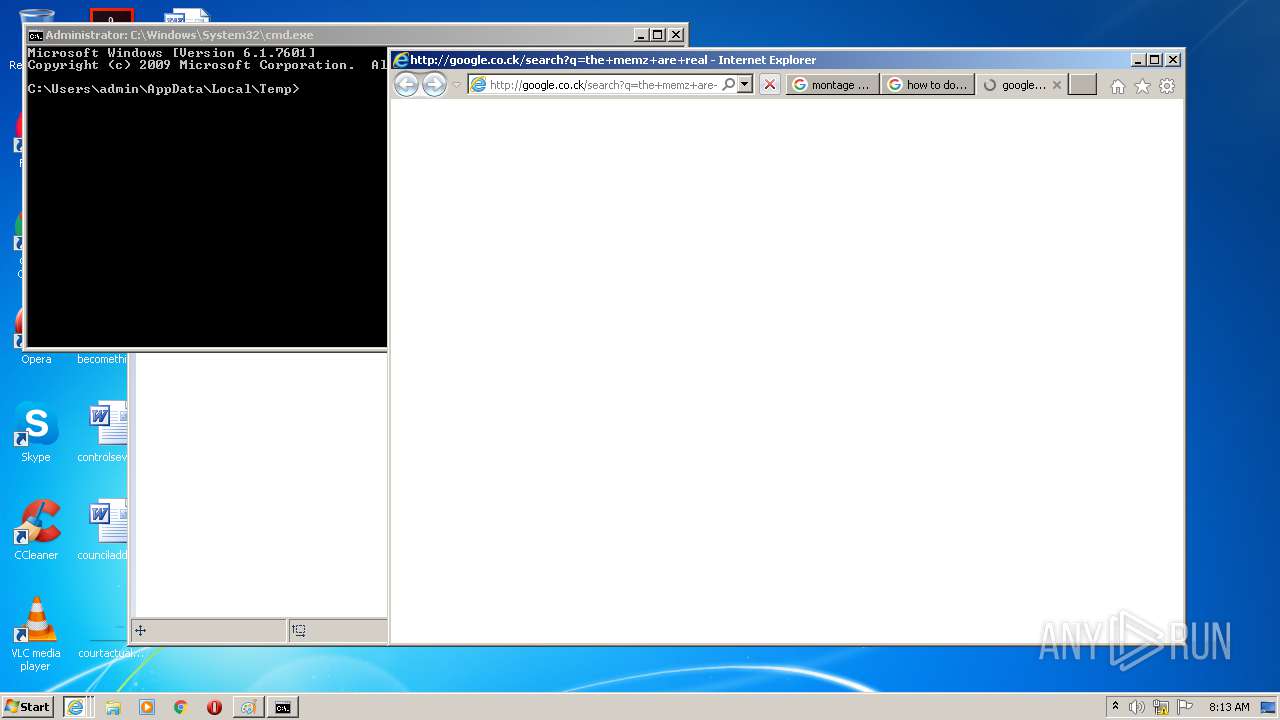
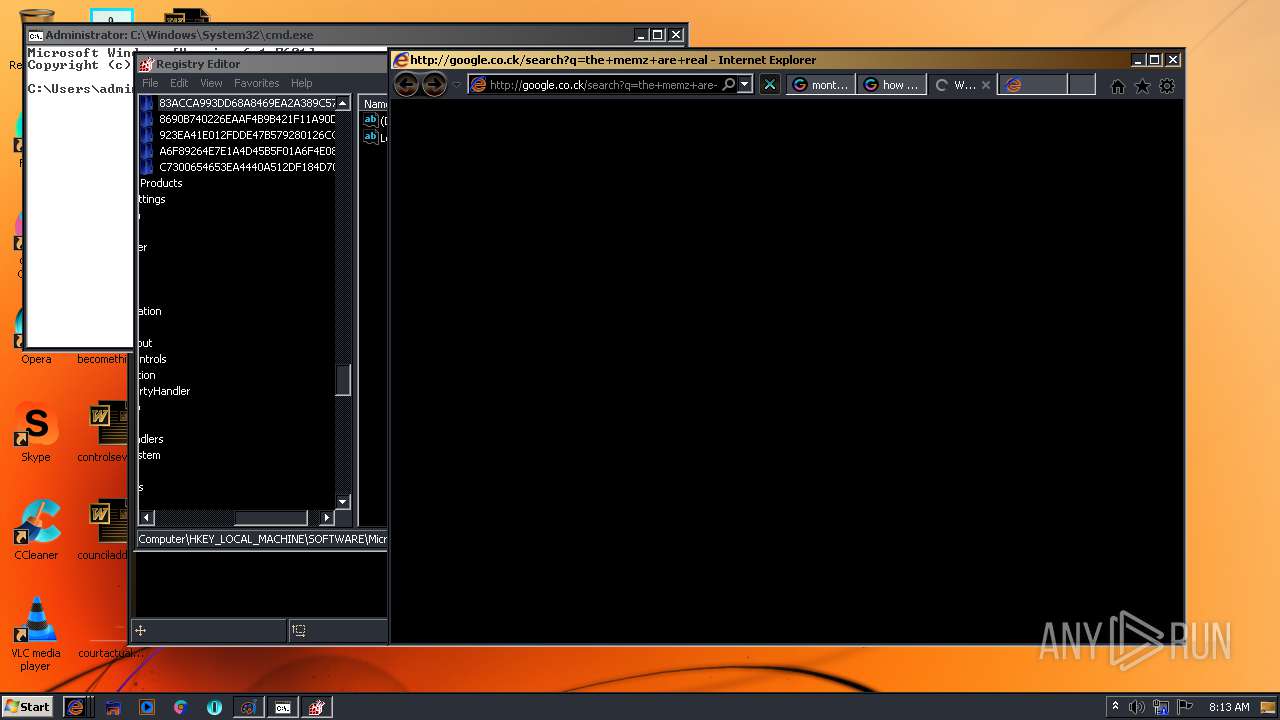
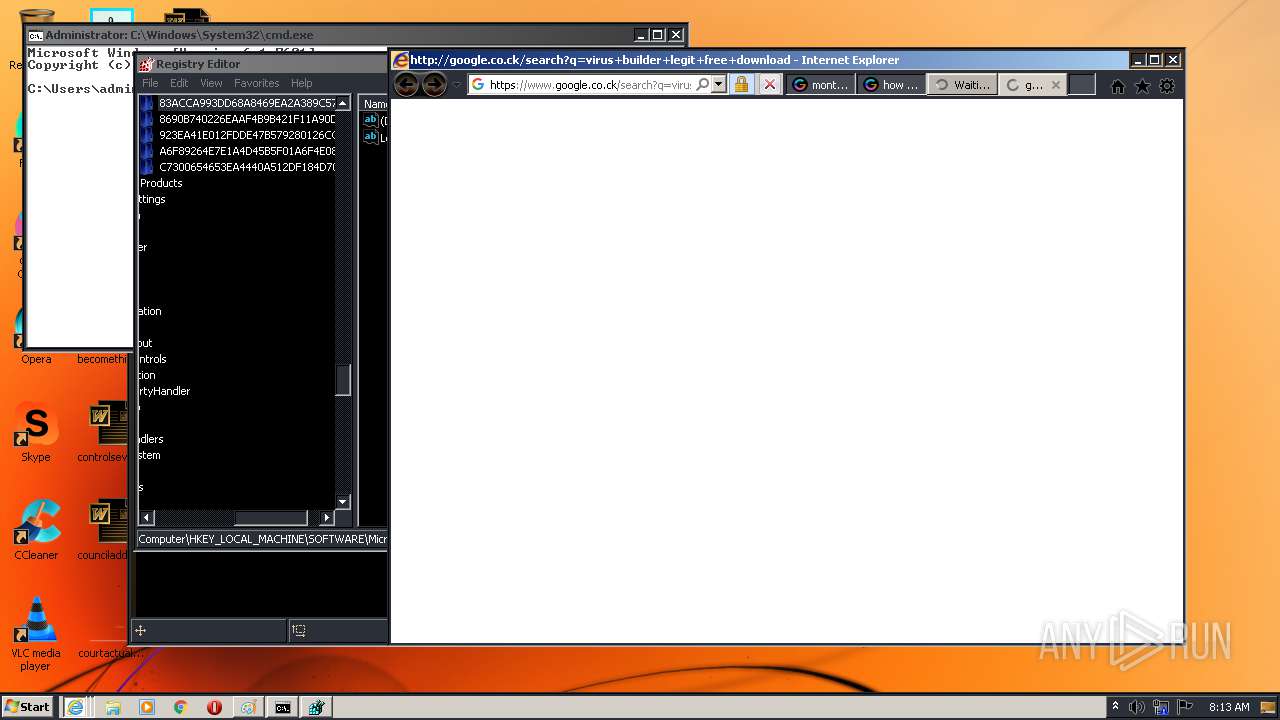
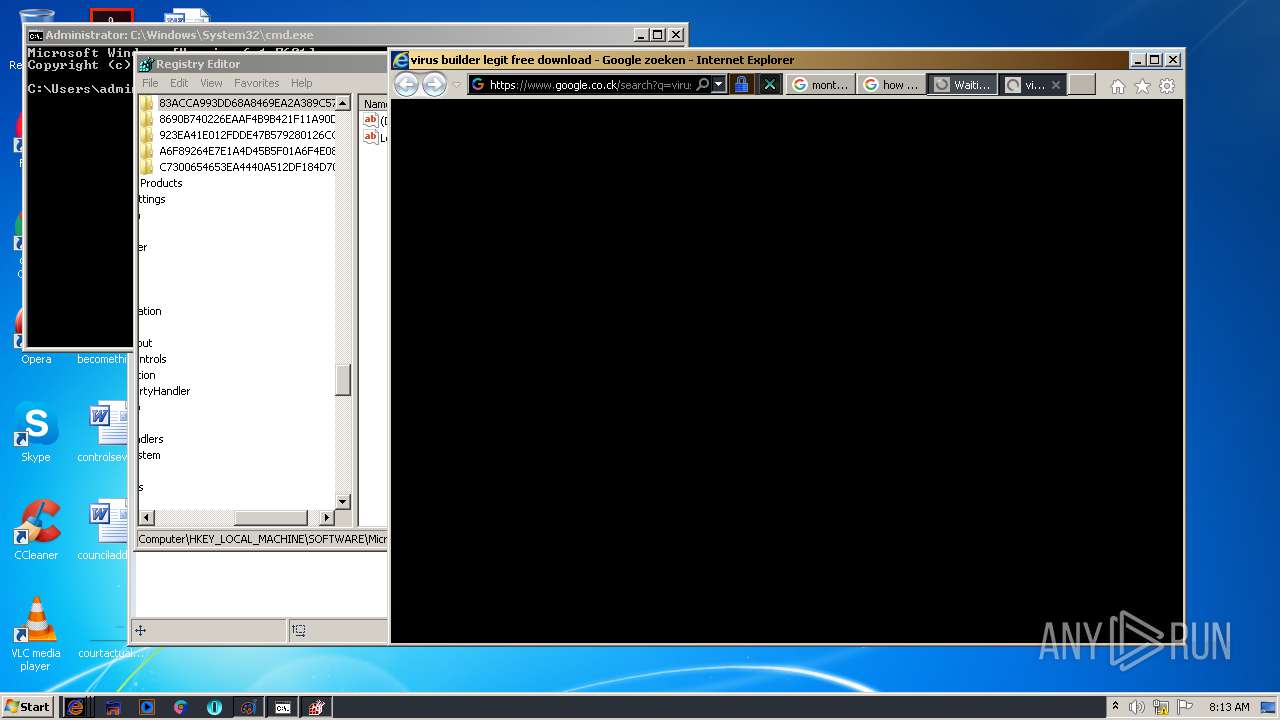
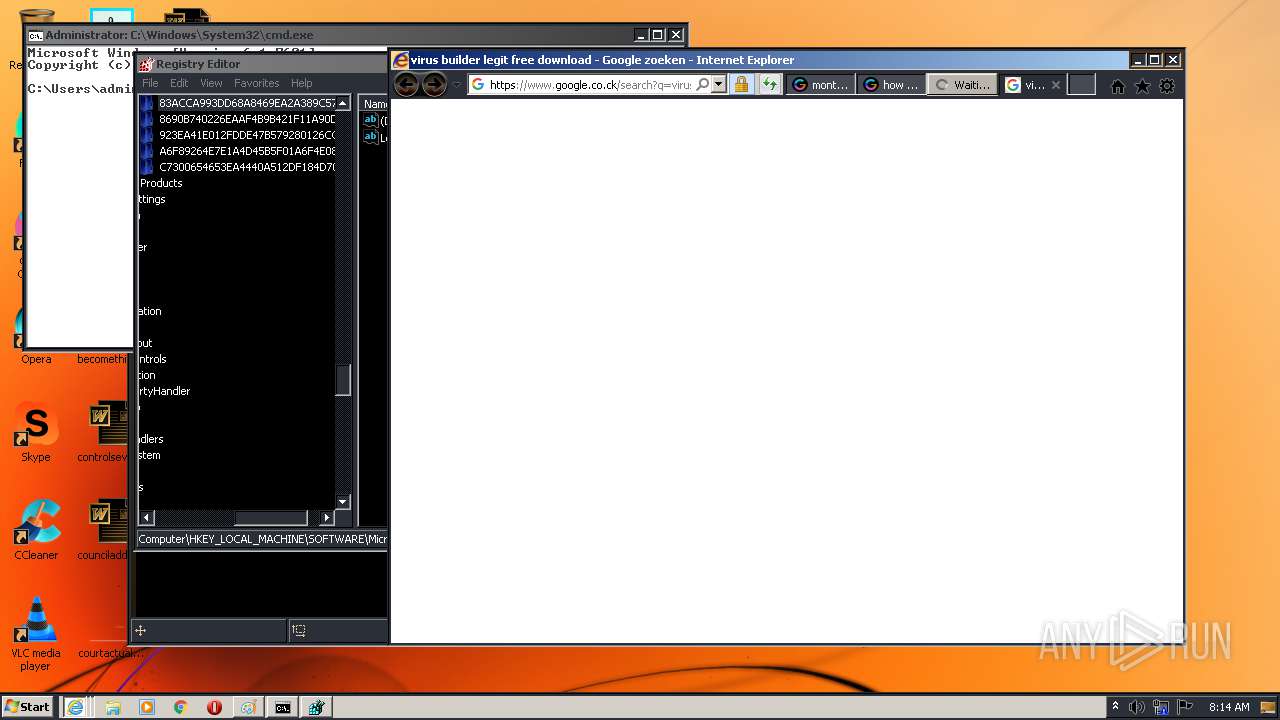
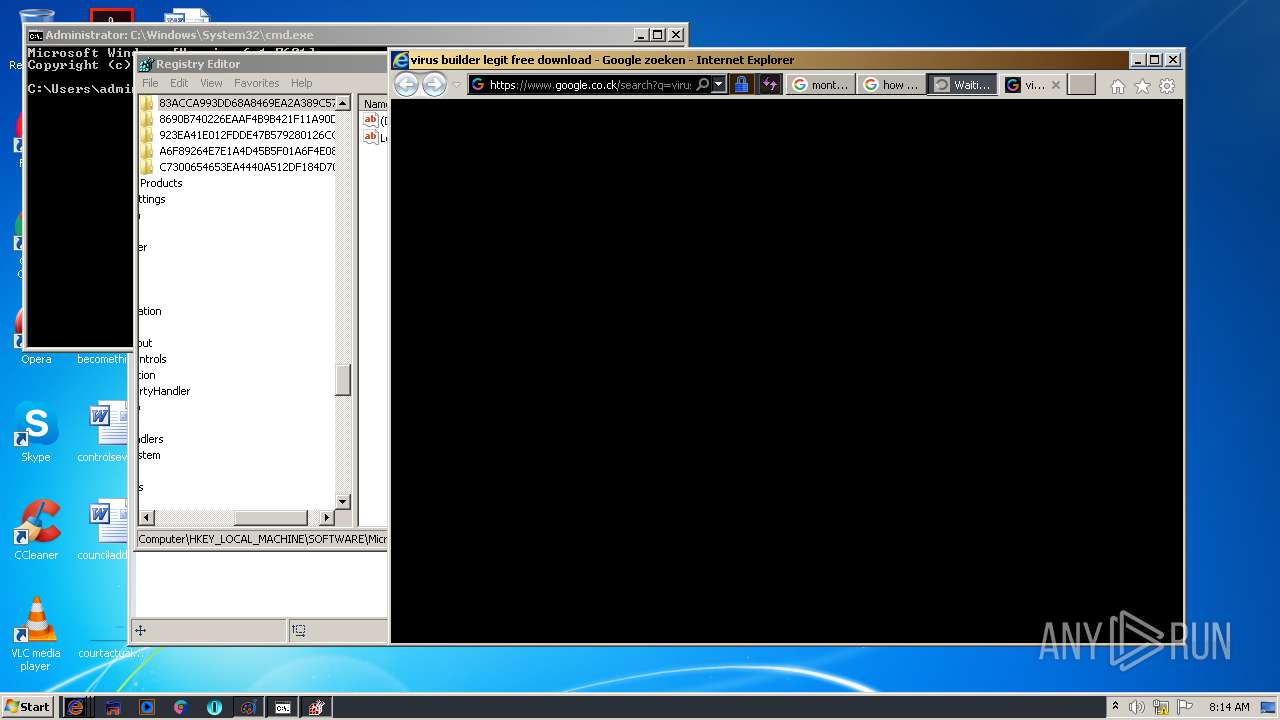
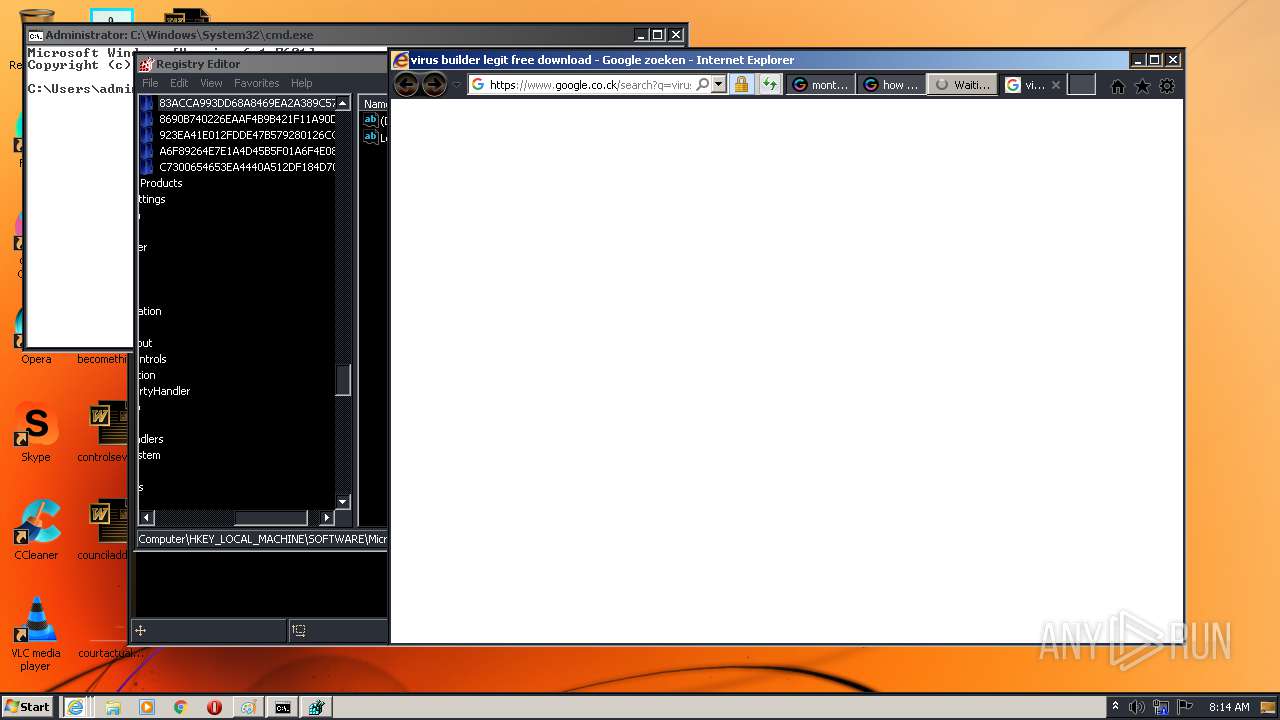
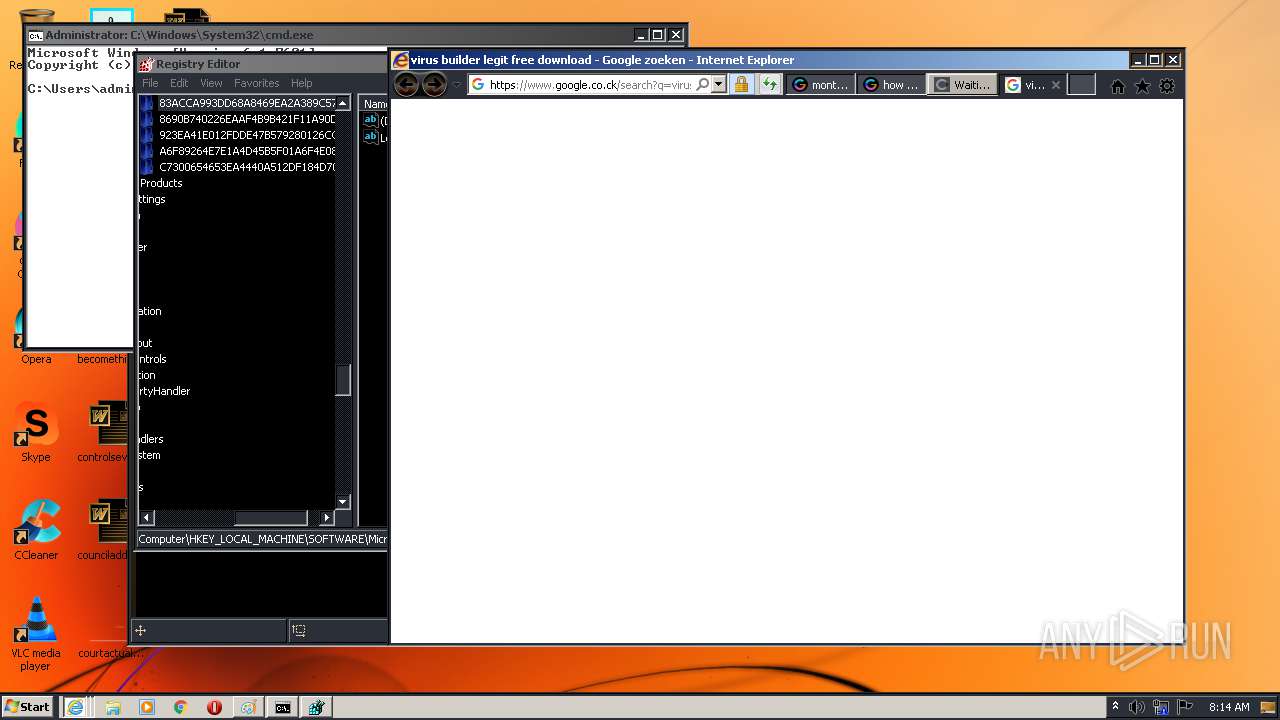
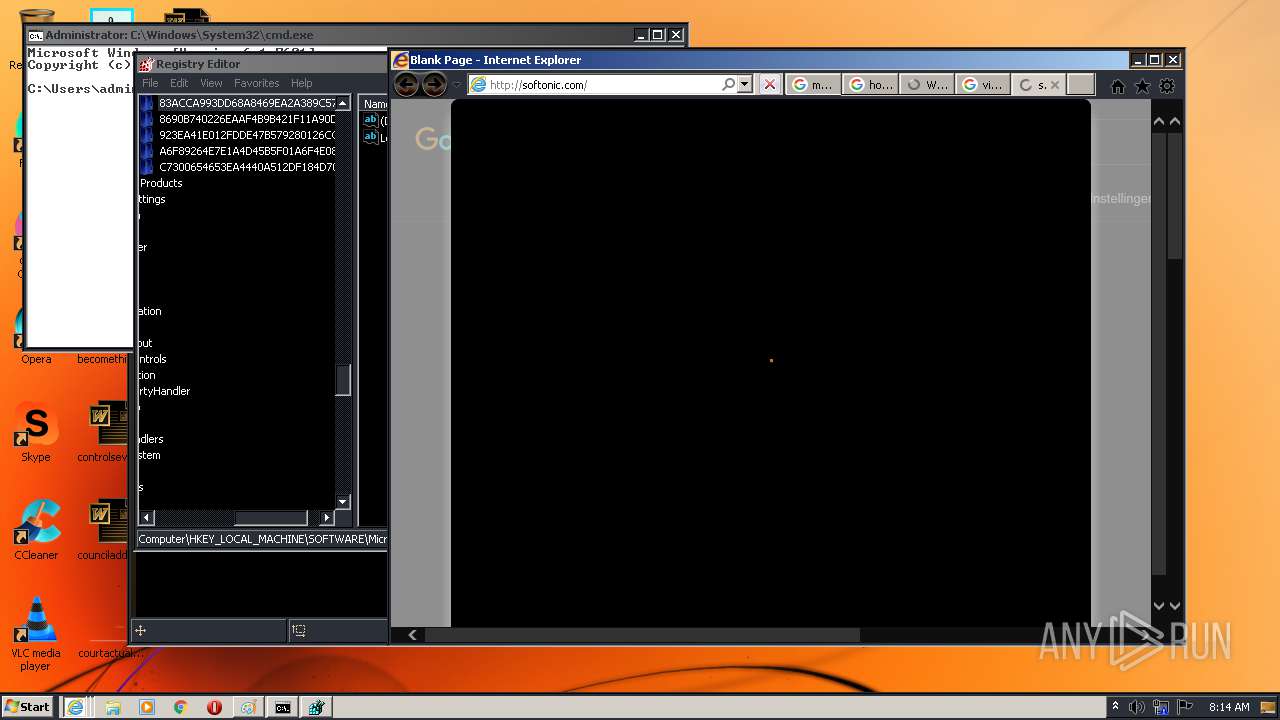
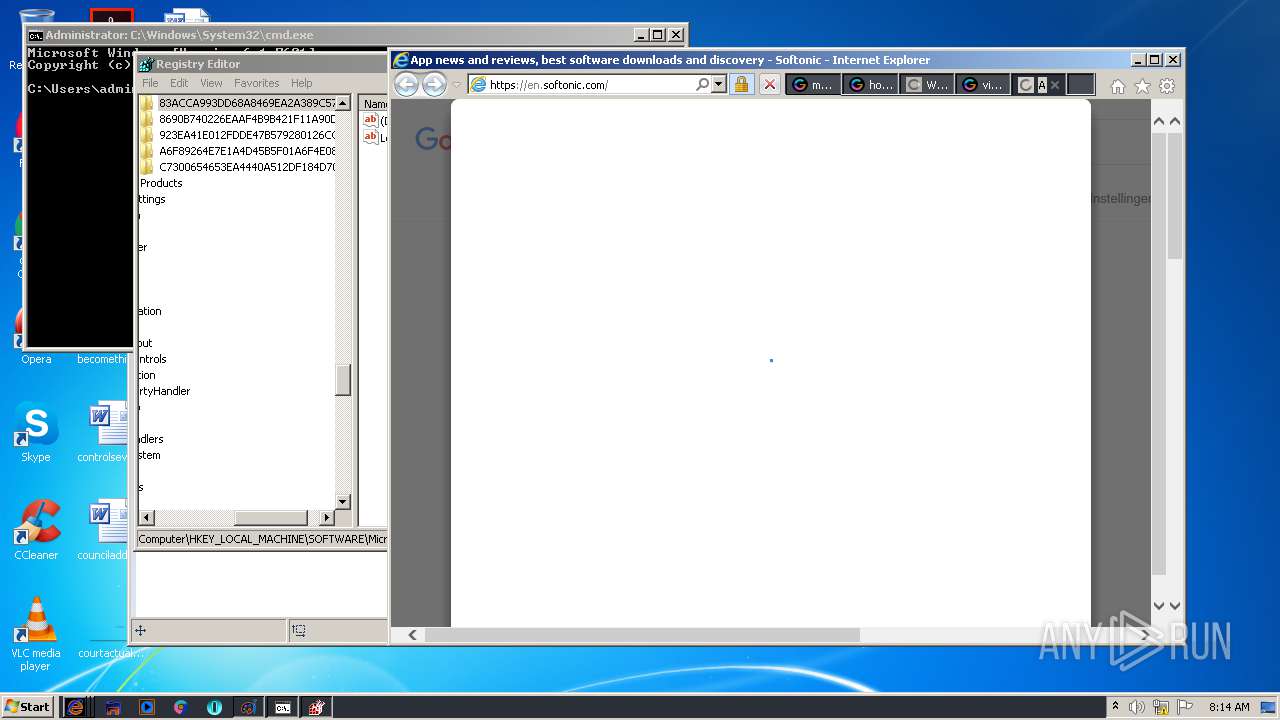
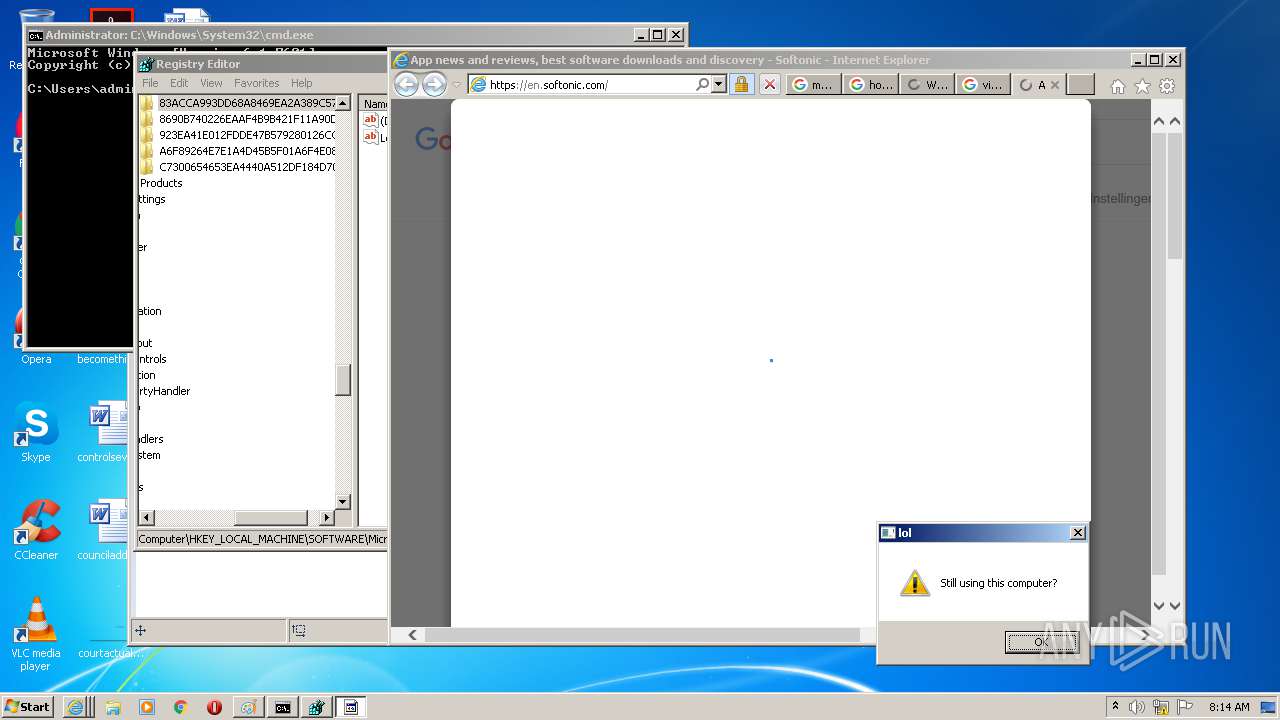
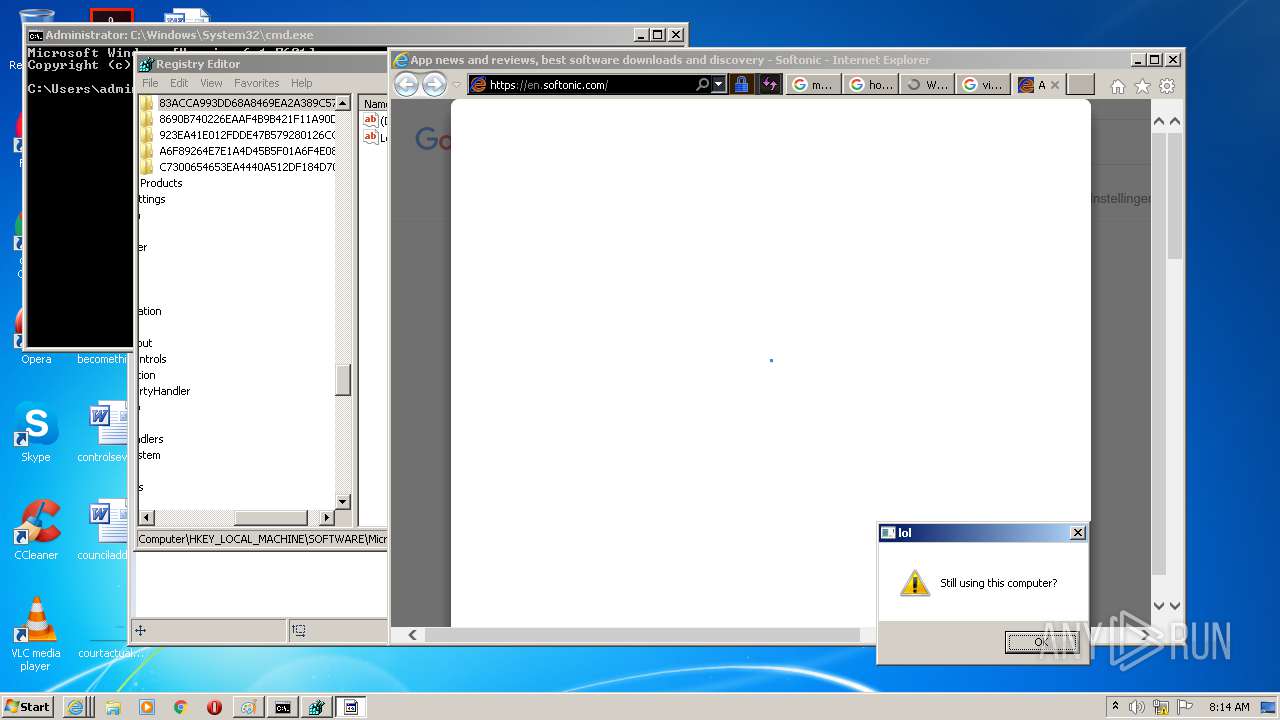
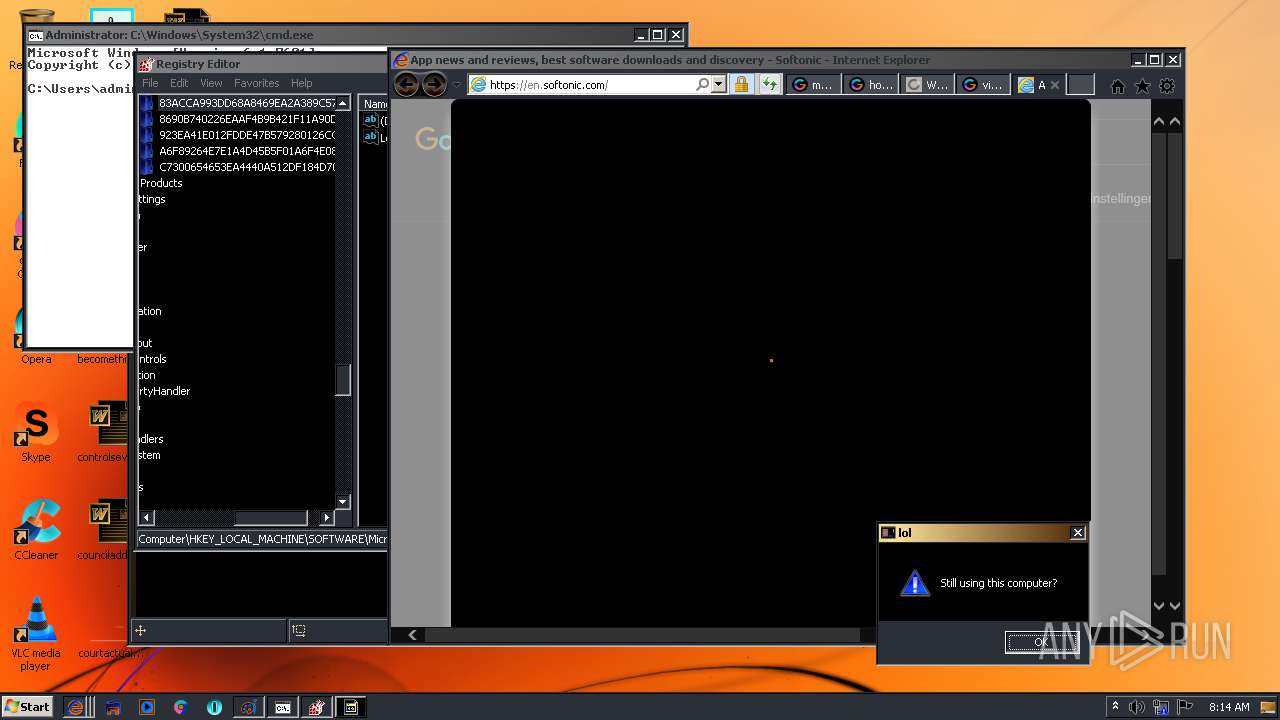
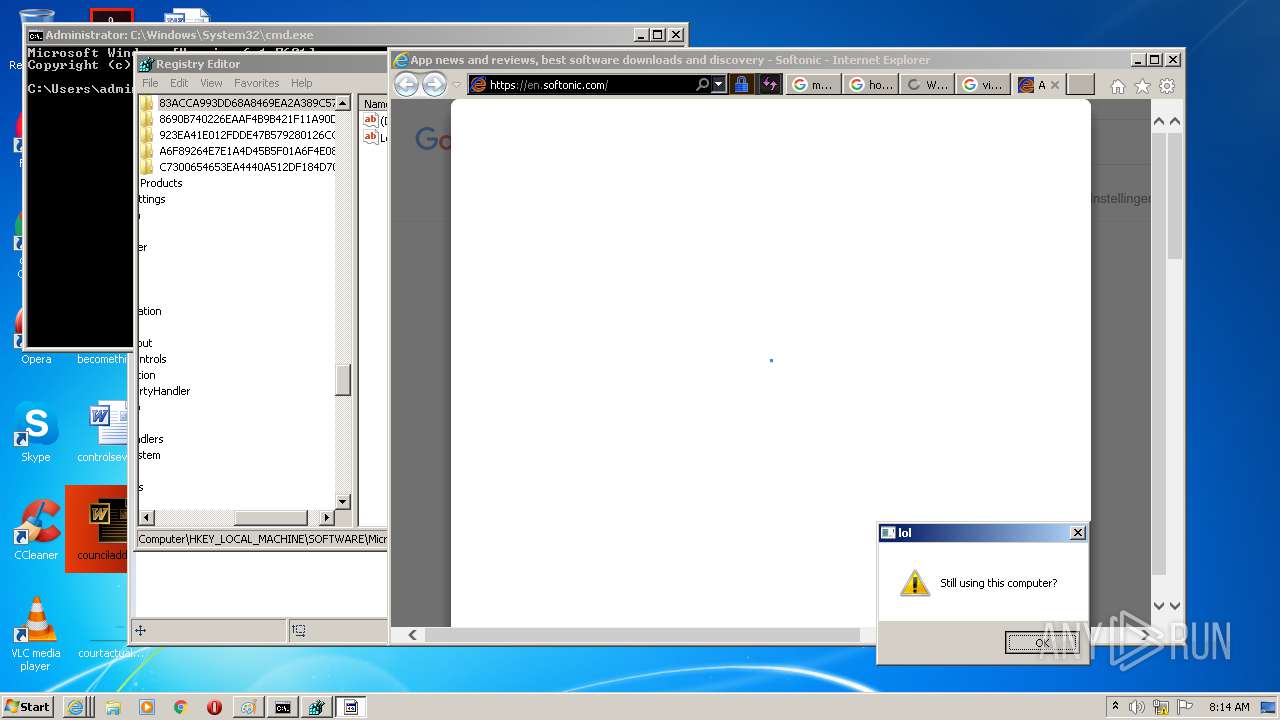
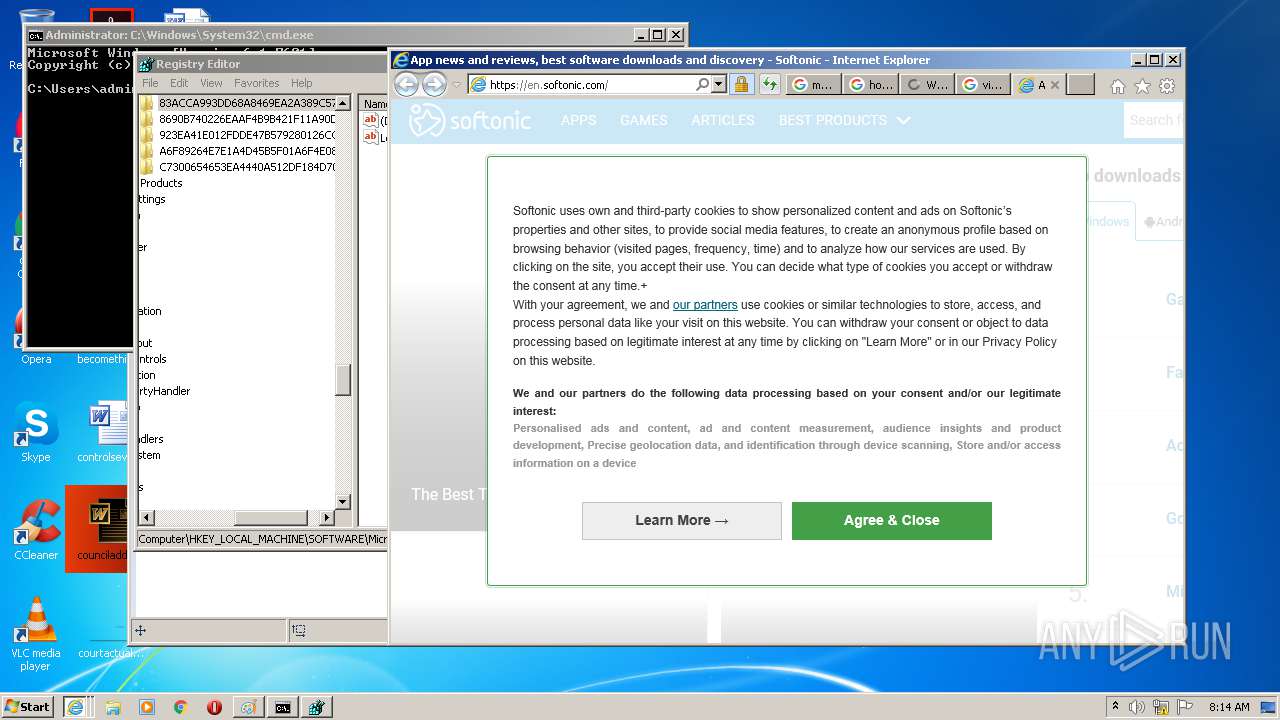
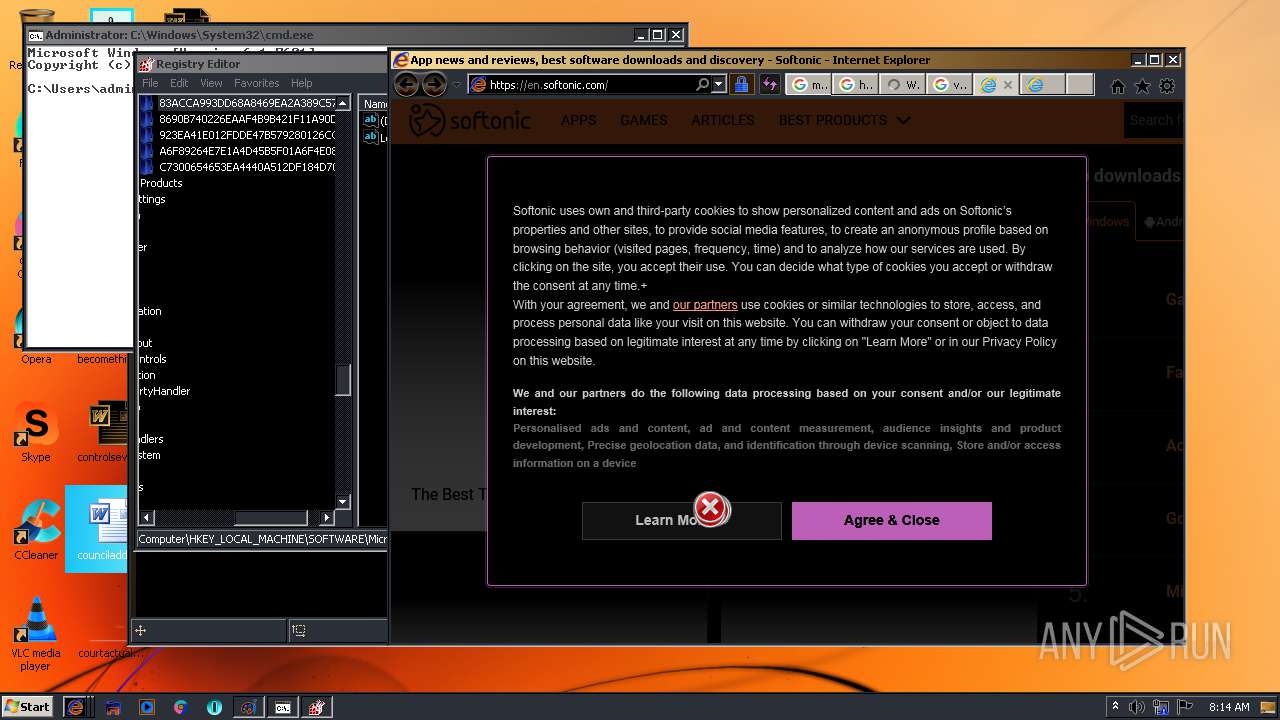
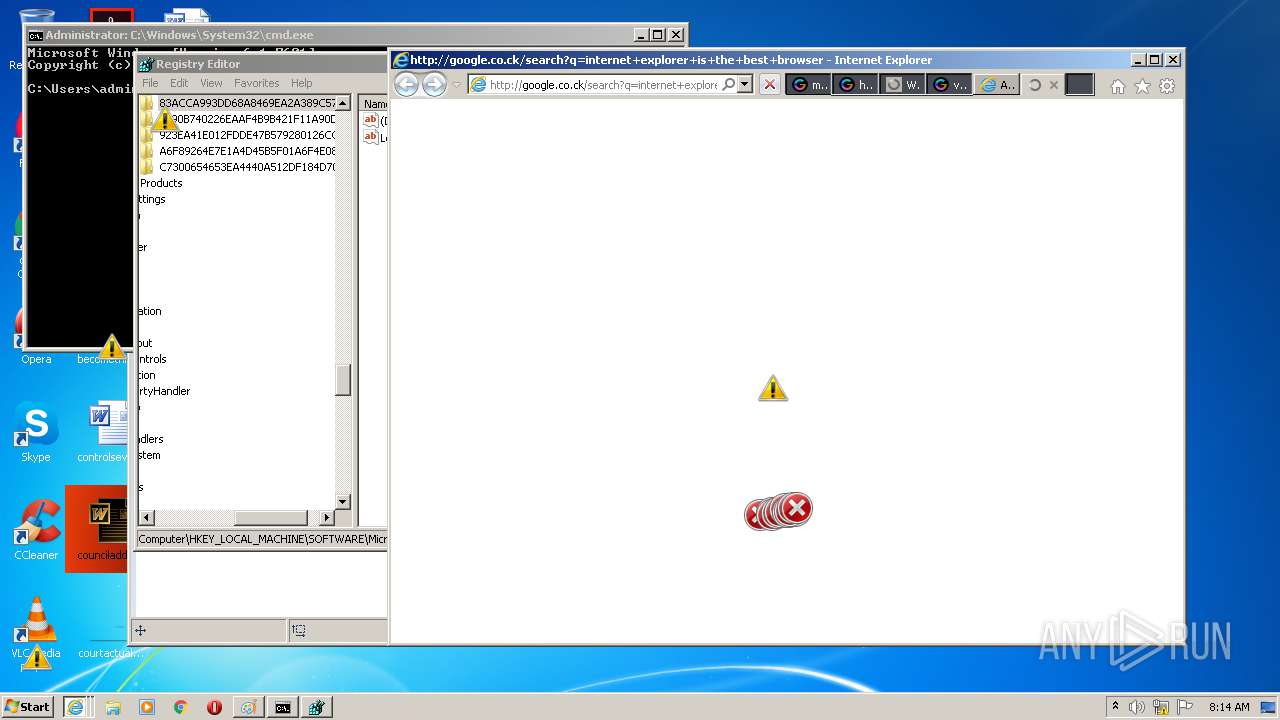
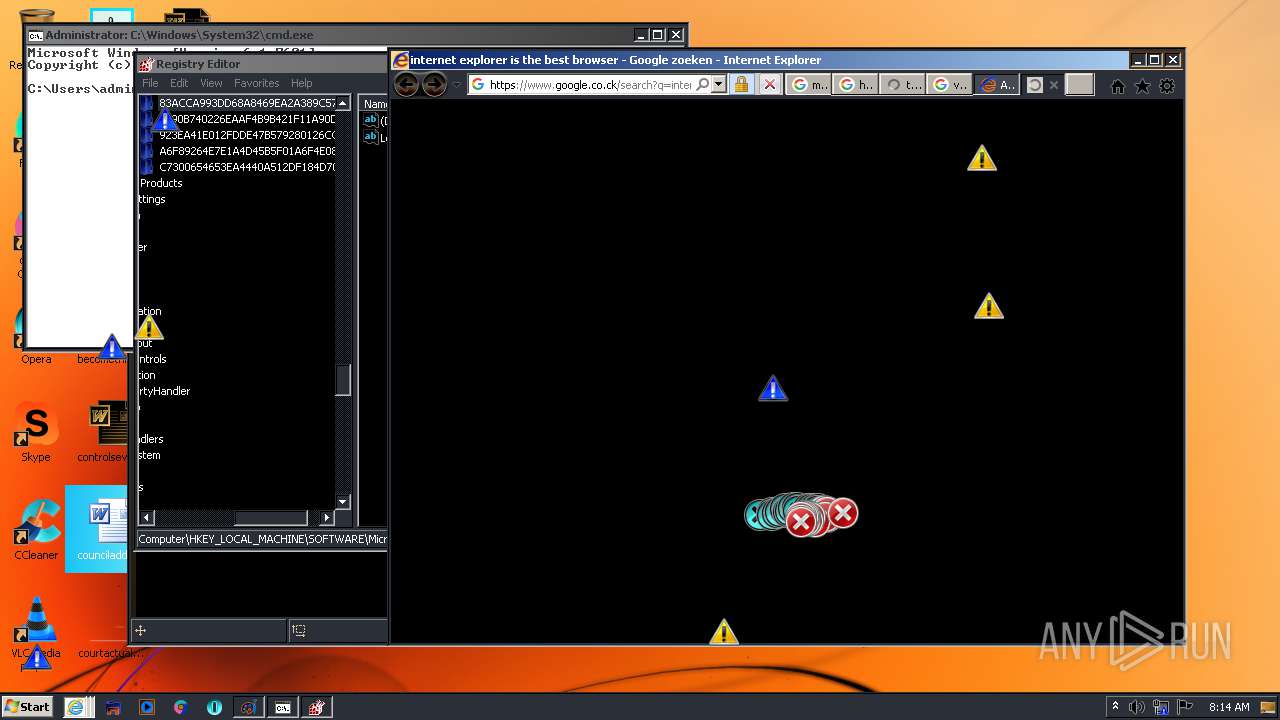
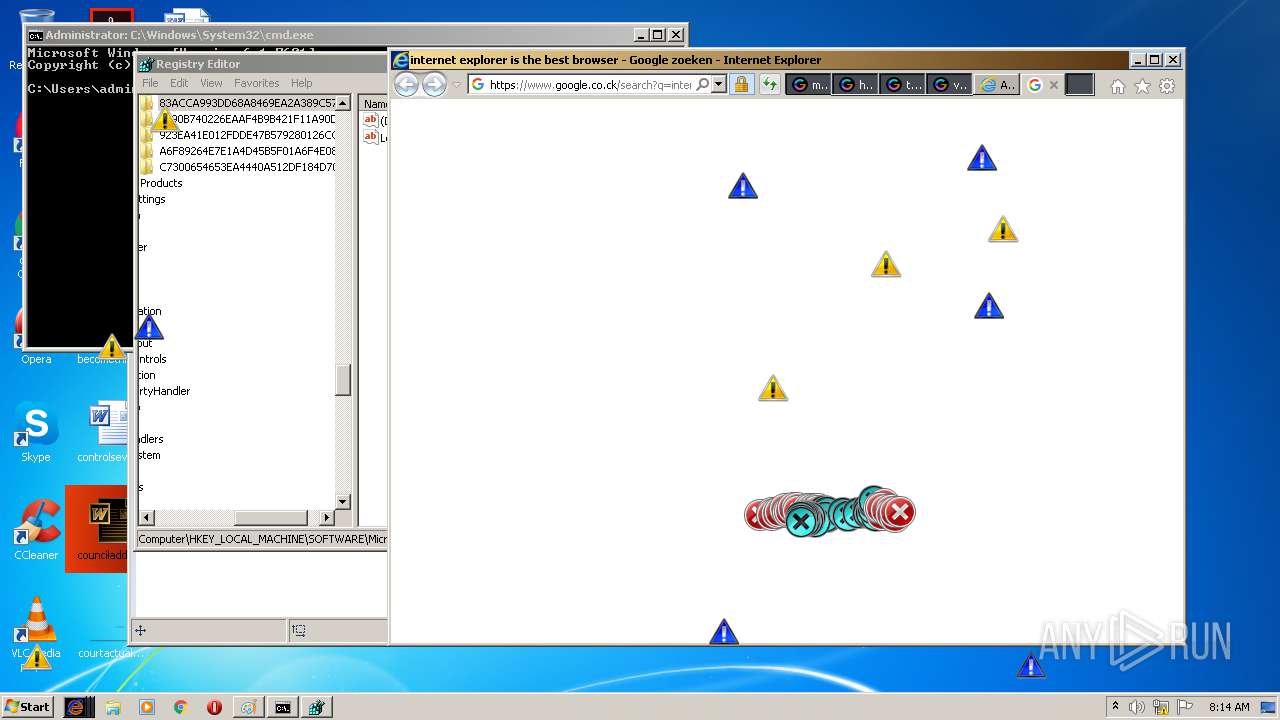
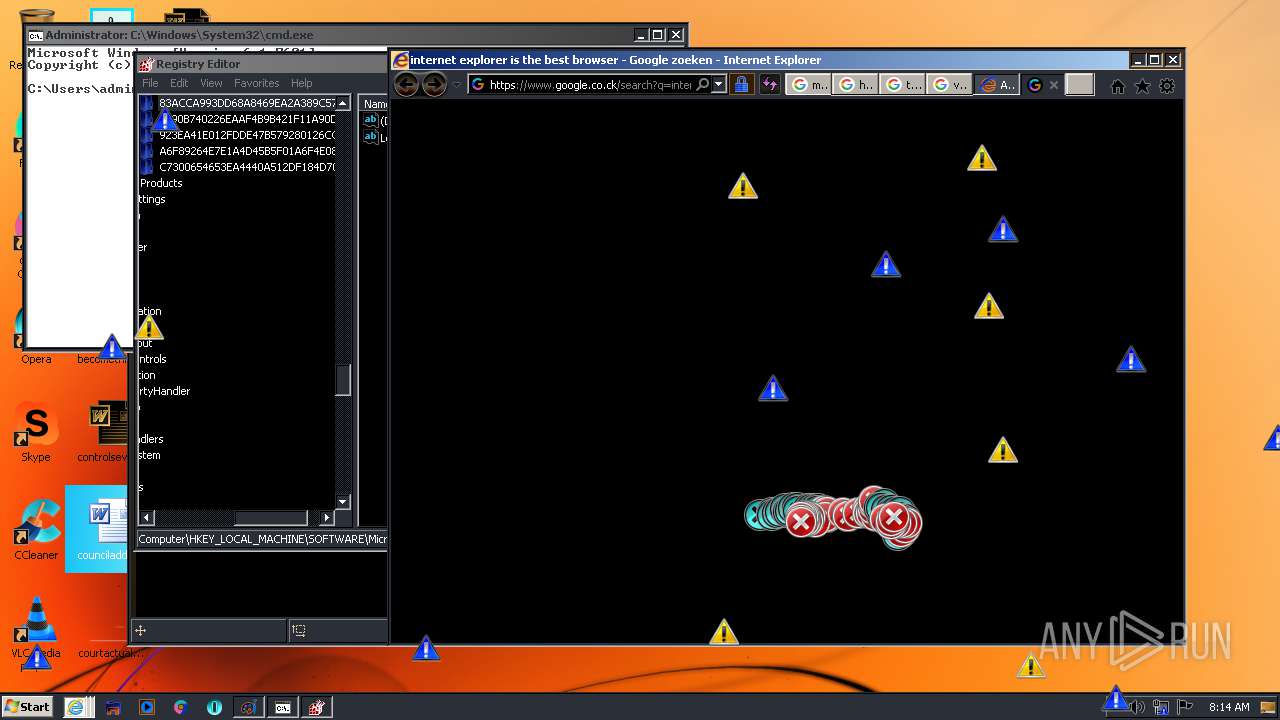
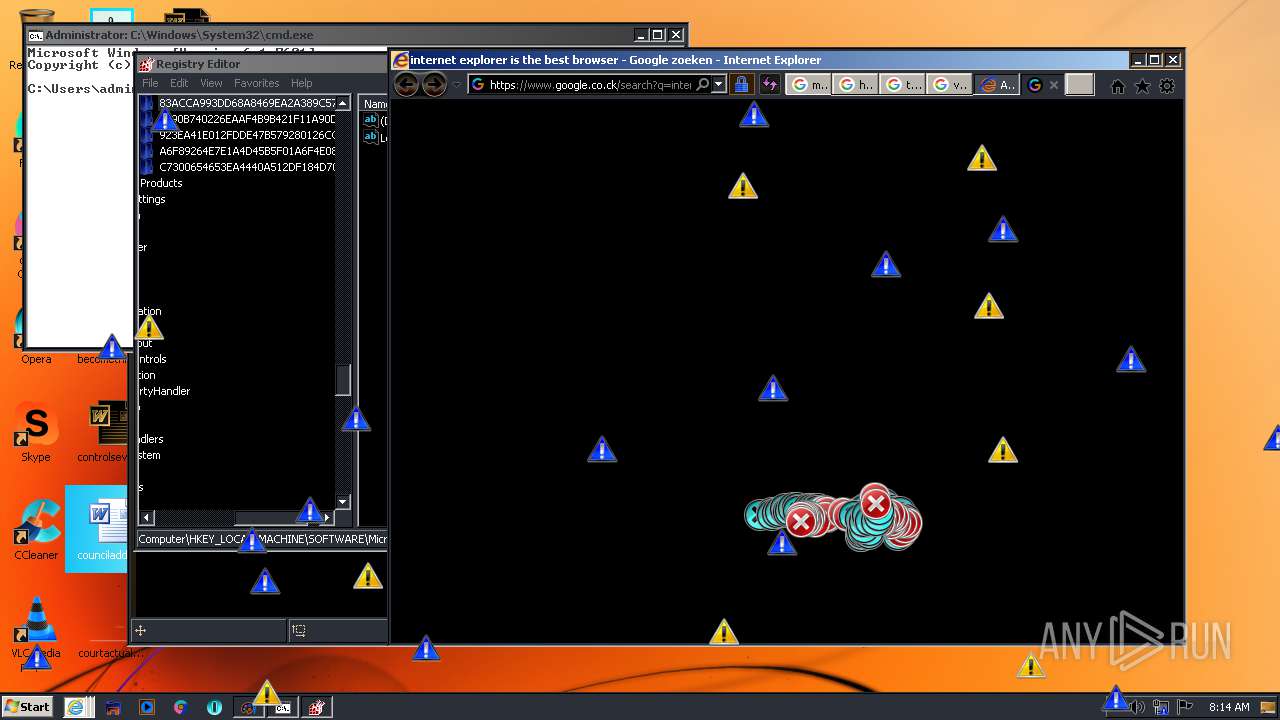
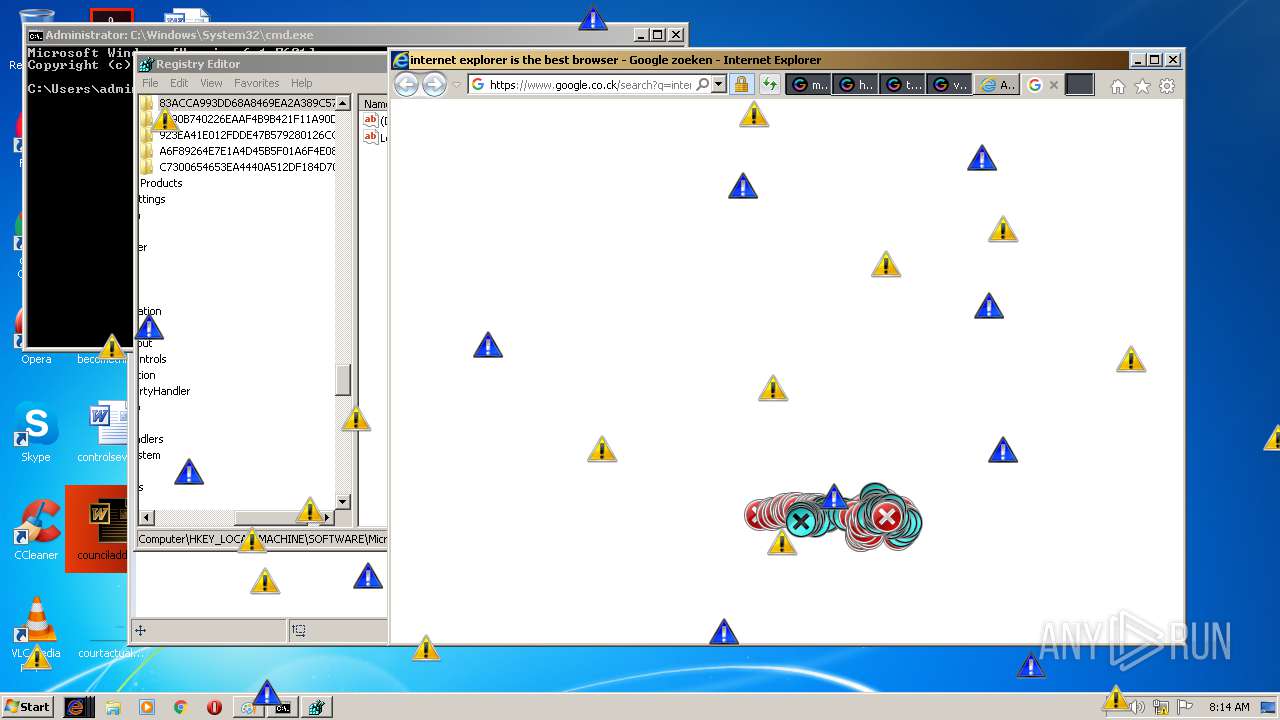
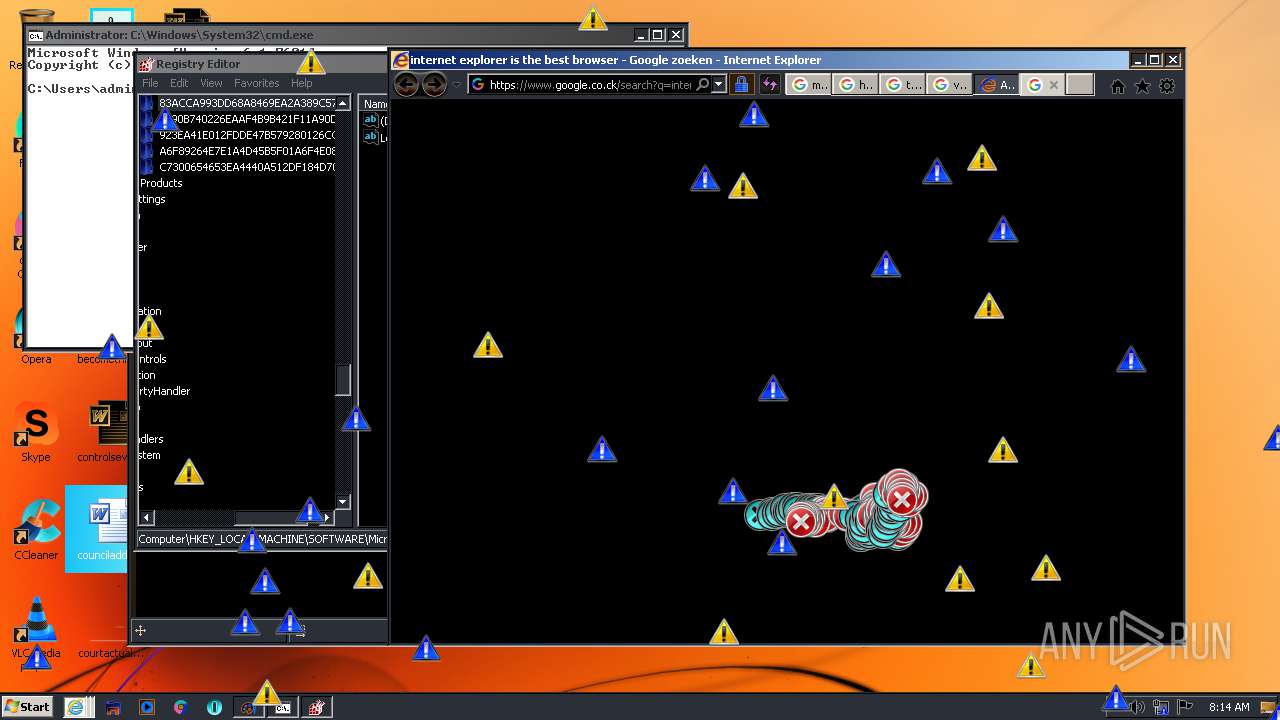
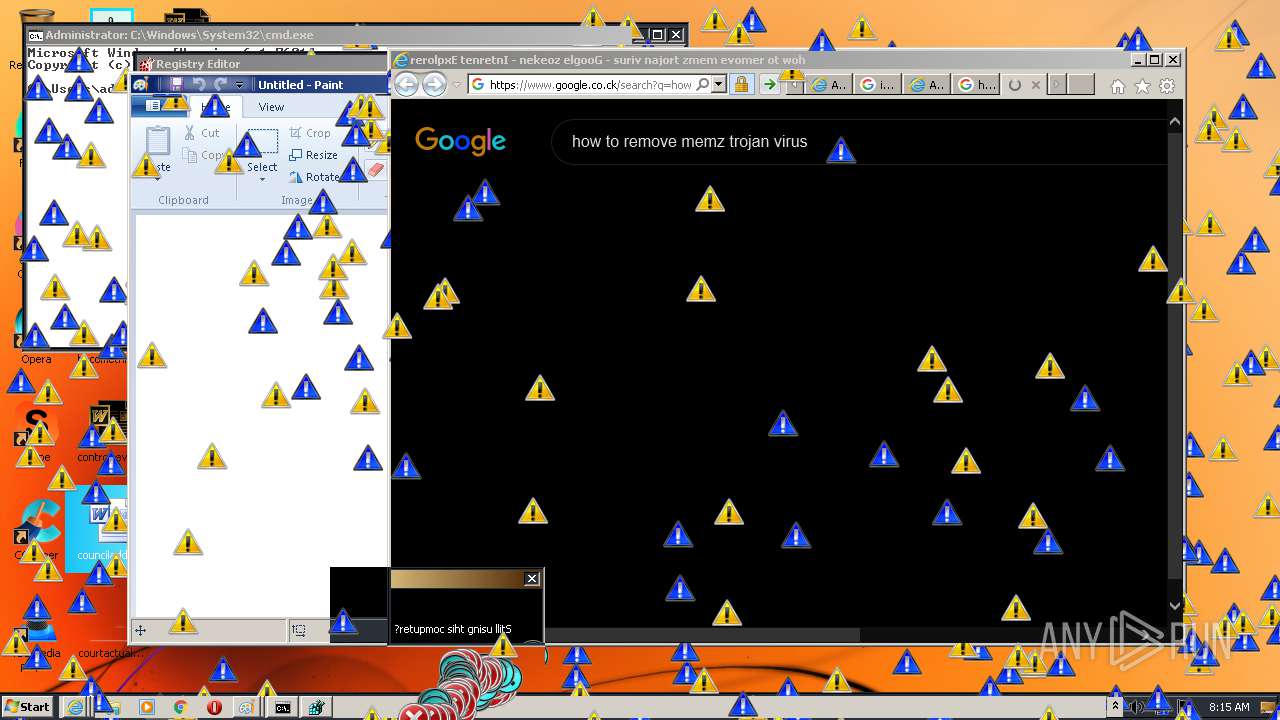
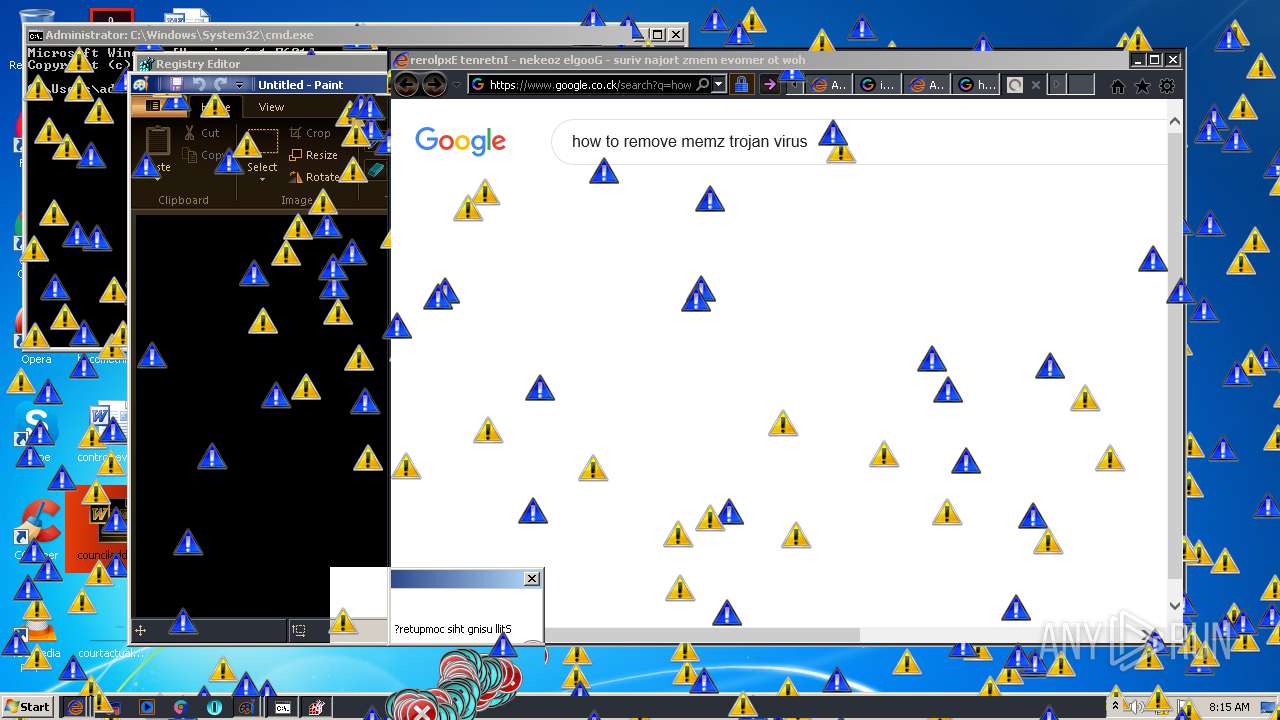
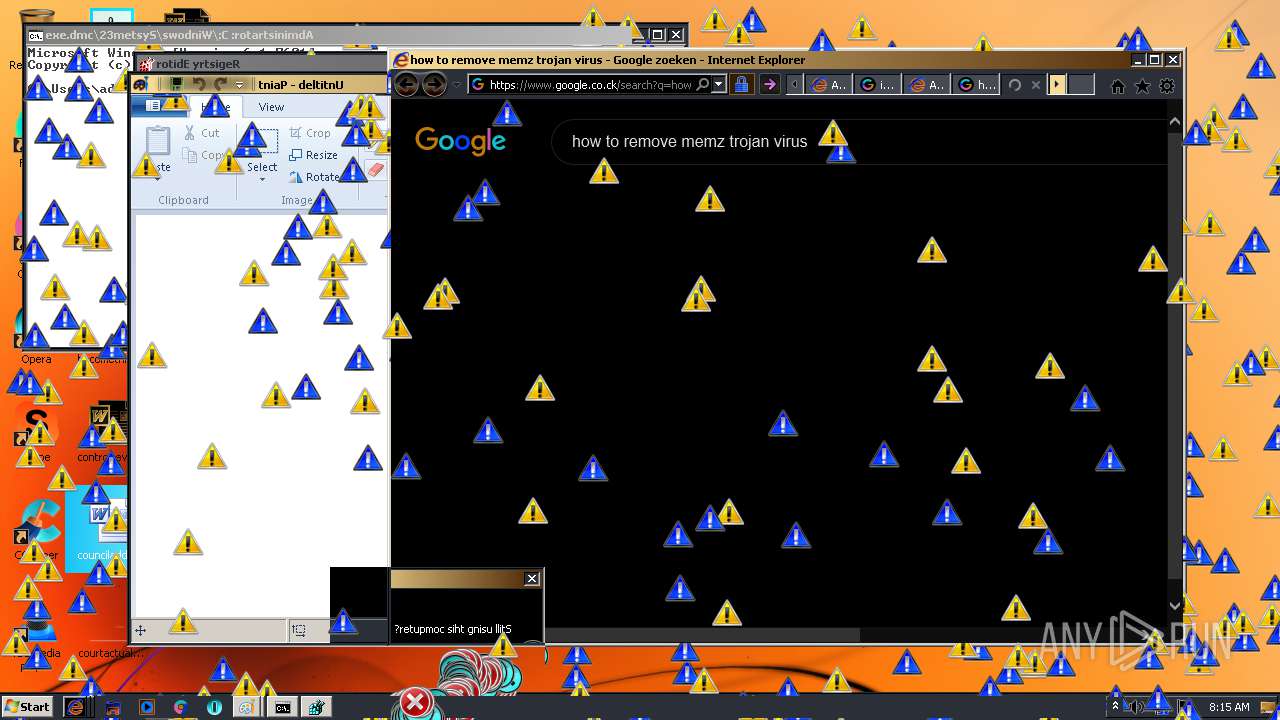
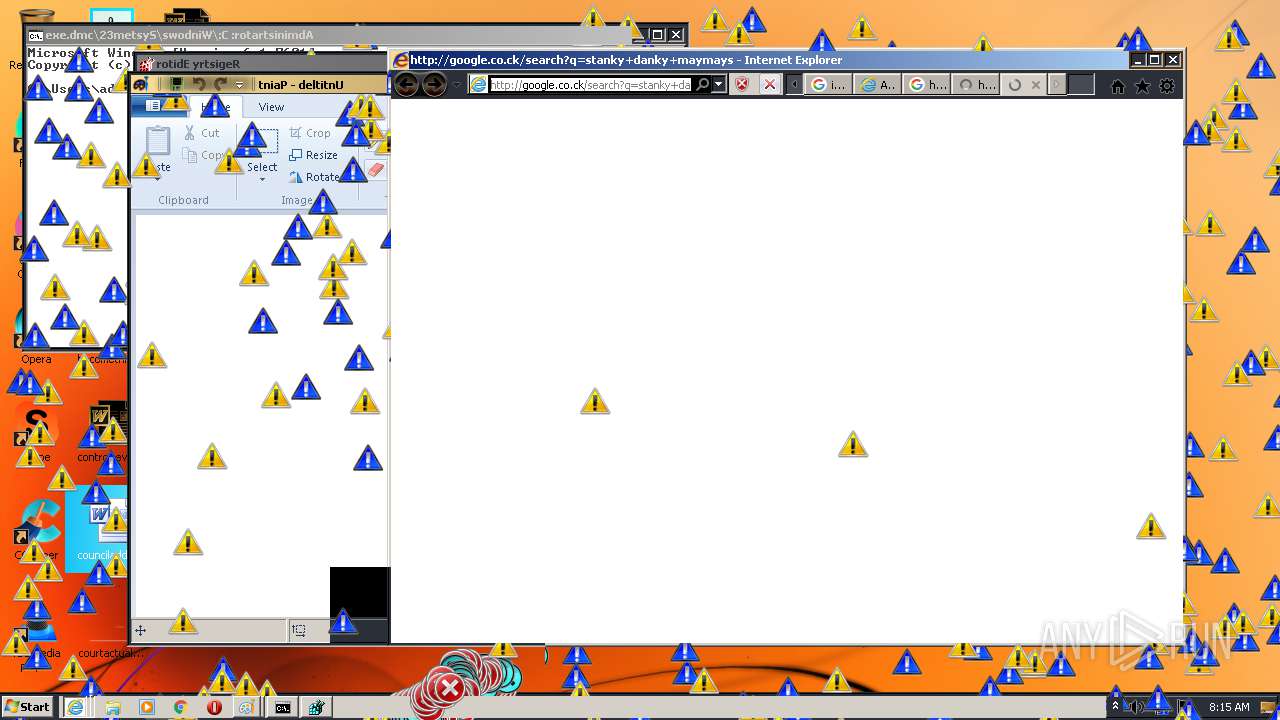
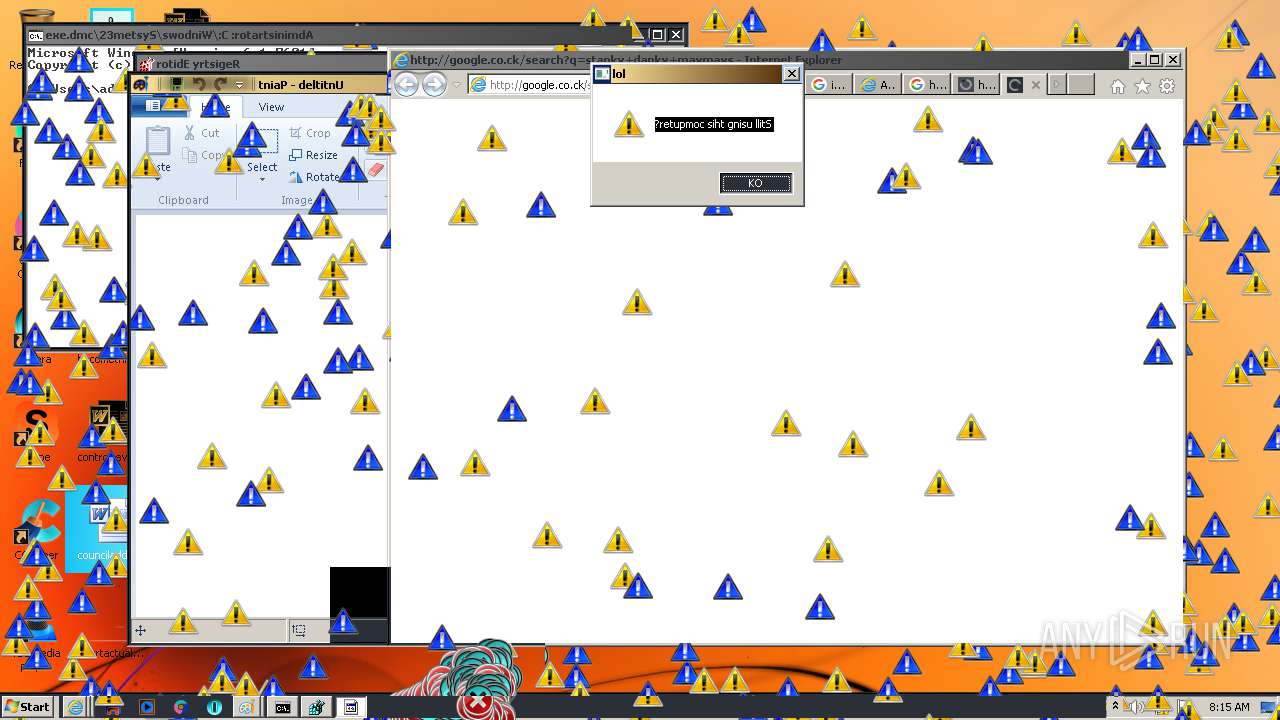
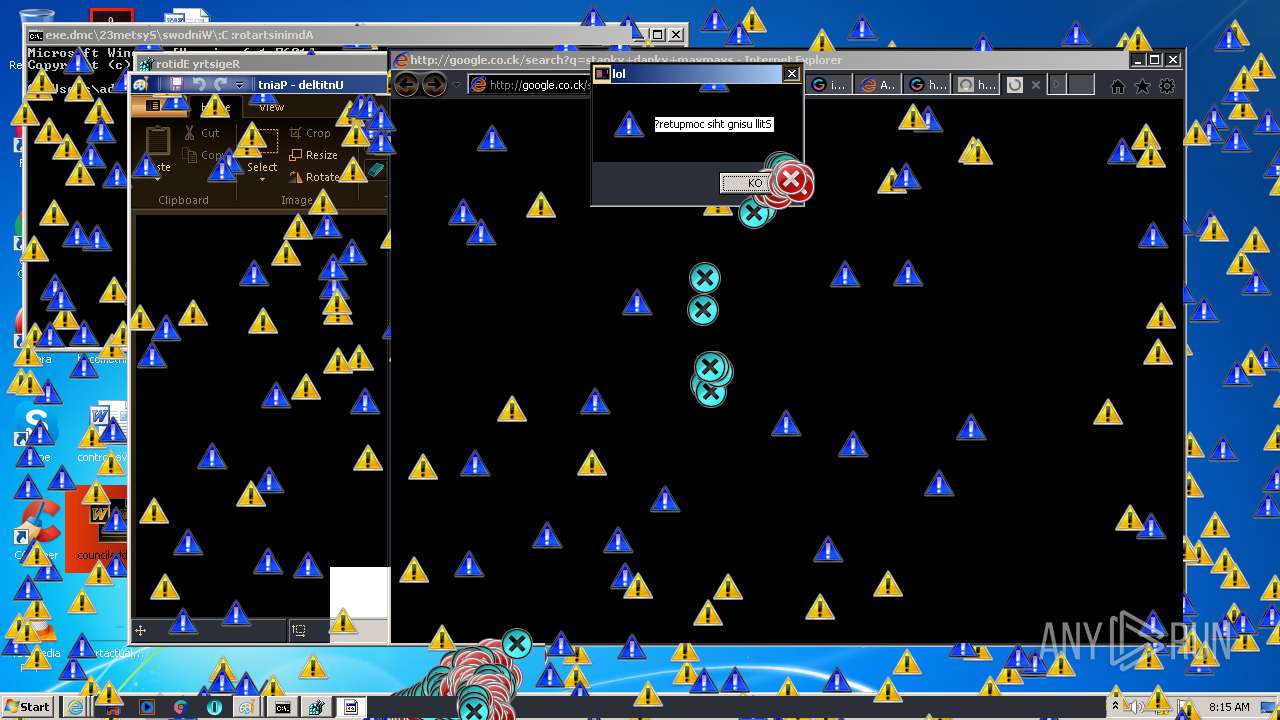
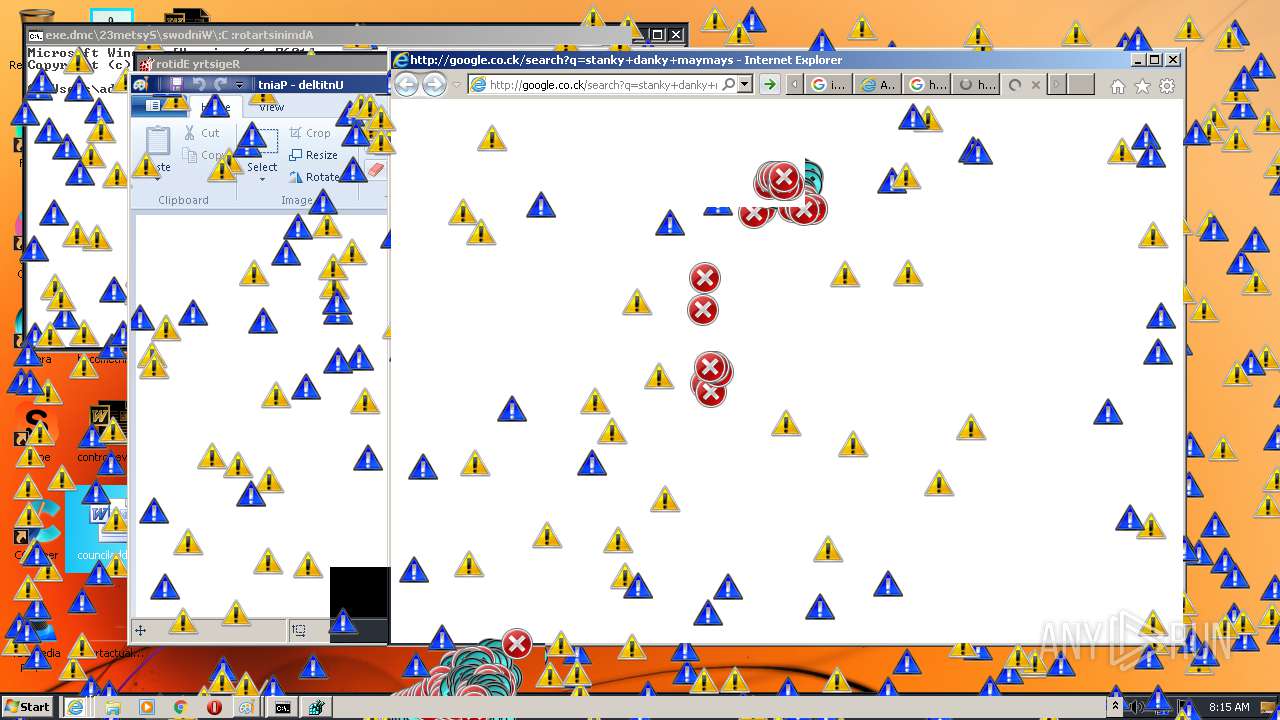
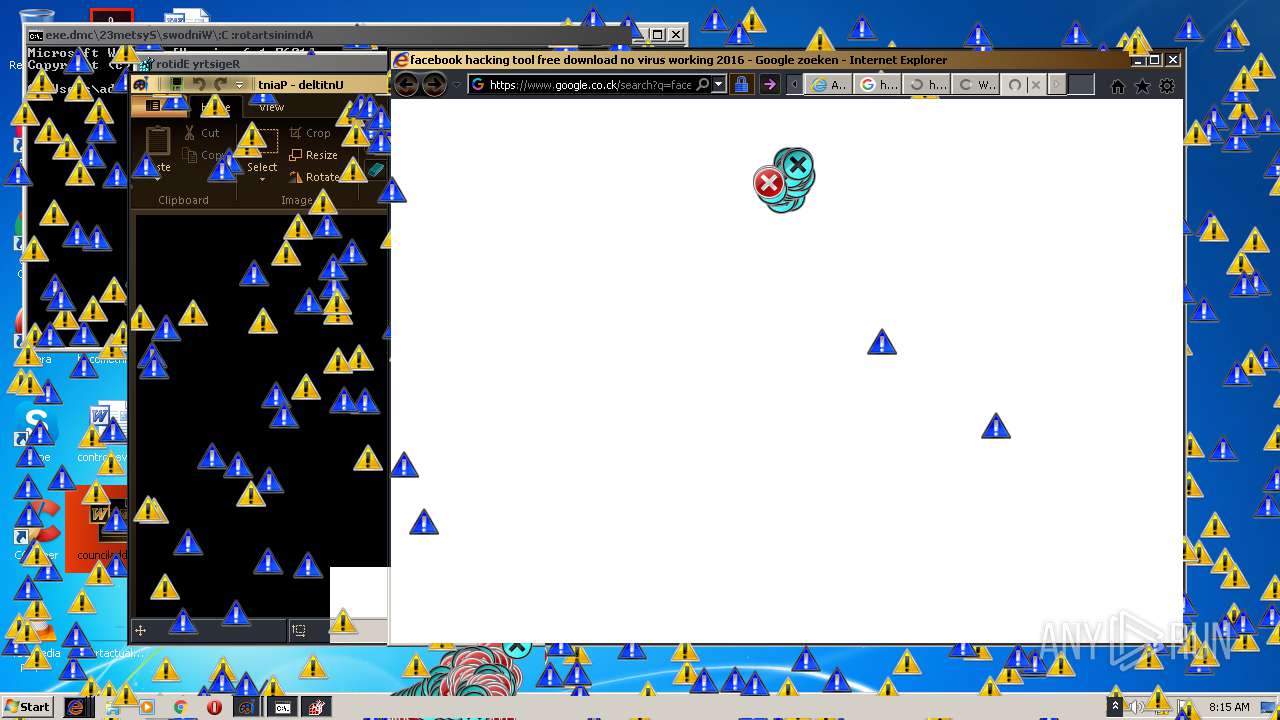
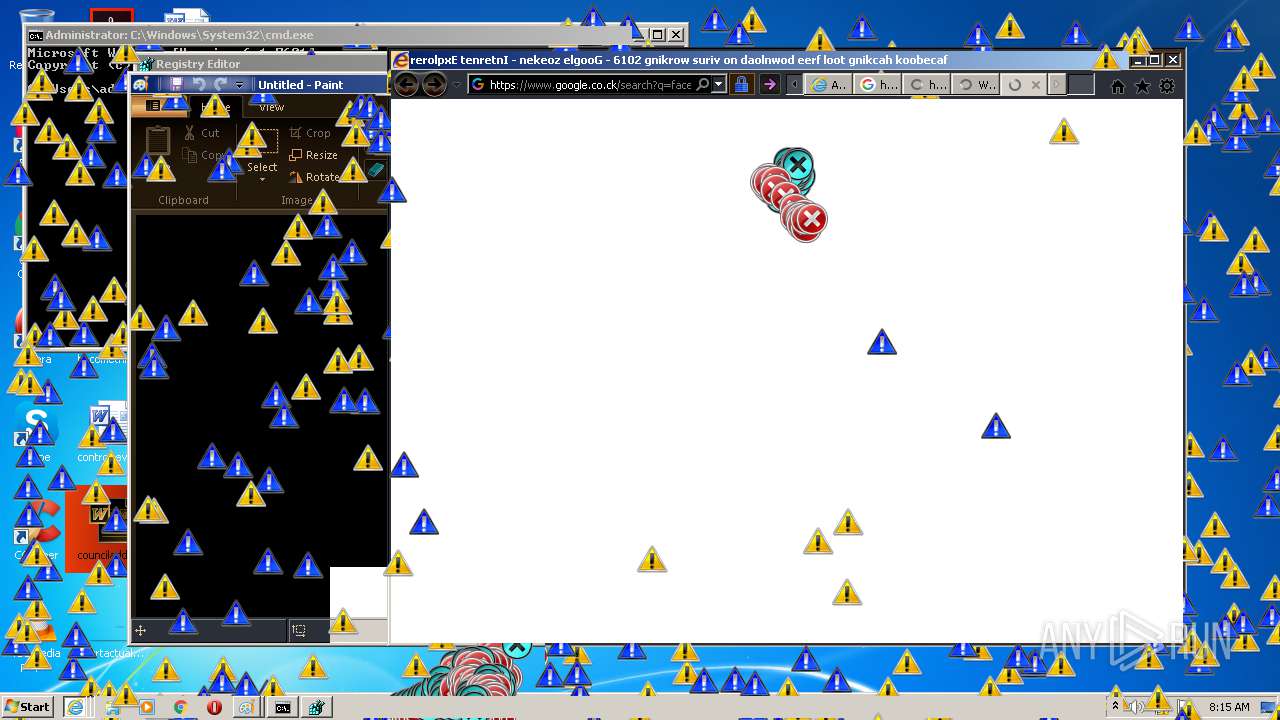
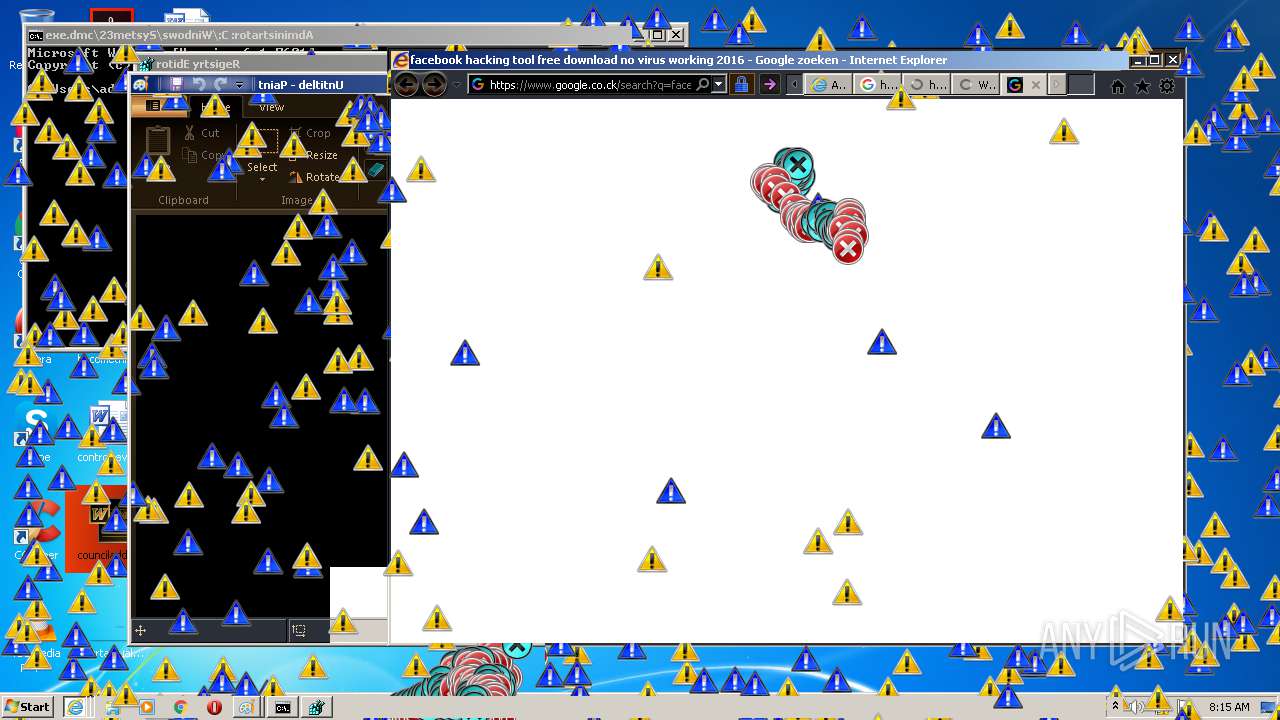
Starts Internet Explorer
- MEMZ-Destructive.exe (PID: 1348)
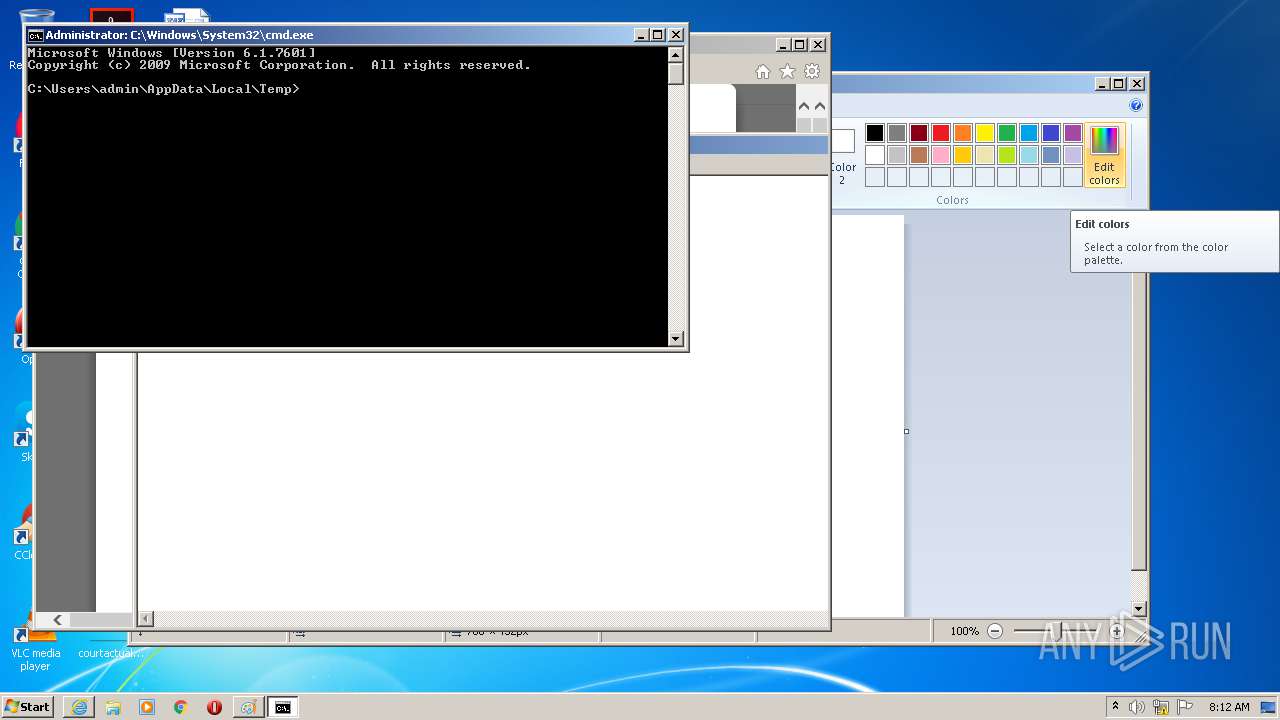
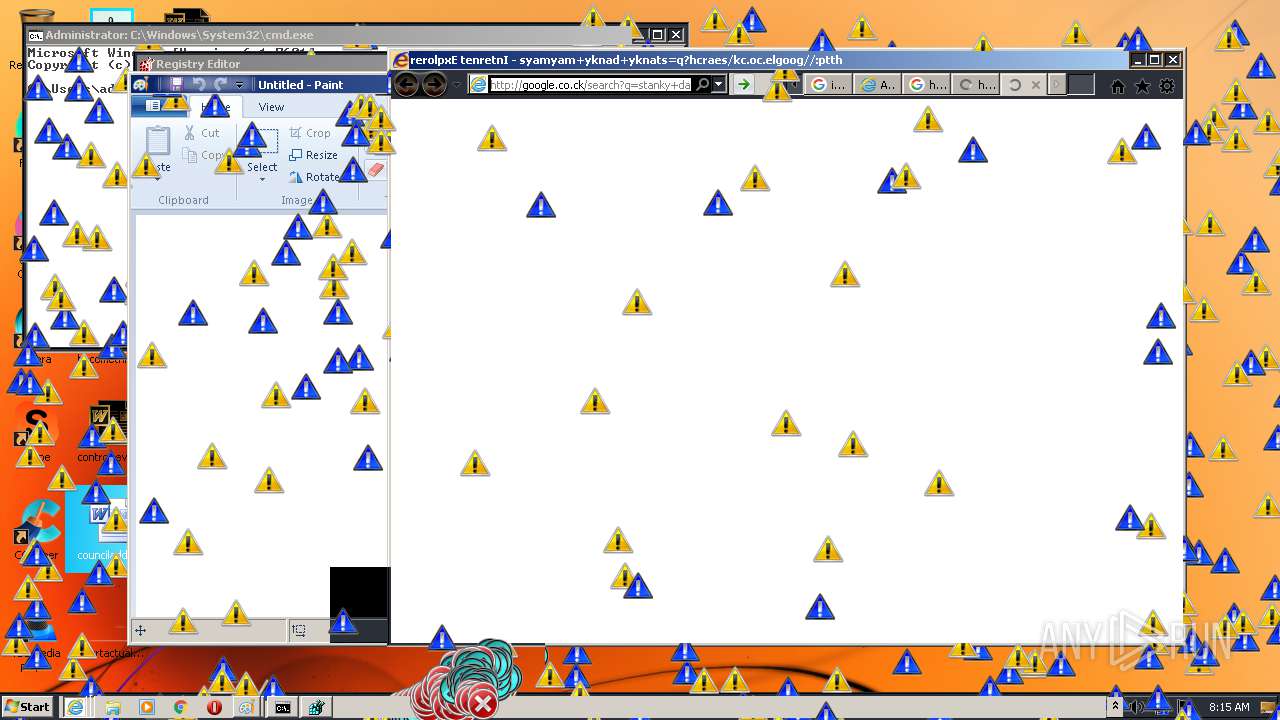
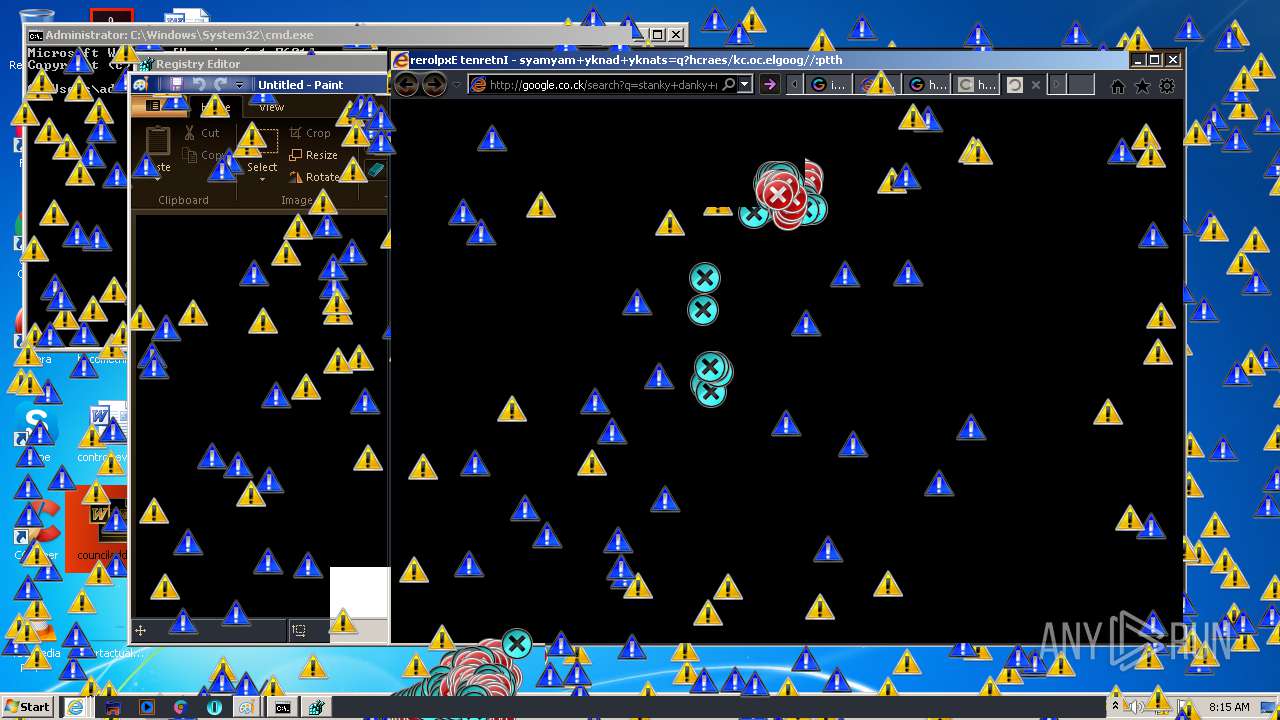
Starts CMD.EXE for commands execution
- MEMZ-Destructive.exe (PID: 1348)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 988)
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 764)
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3936)
- iexplore.exe (PID: 2768)
Changes internet zones settings
- iexplore.exe (PID: 988)
- iexplore.exe (PID: 2244)
Changes settings of System certificates
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 988)
- iexplore.exe (PID: 780)
Reads internet explorer settings
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 764)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3936)
- iexplore.exe (PID: 2768)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 988)
- iexplore.exe (PID: 780)
Application launched itself
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 988)
Reads settings of System Certificates
- iexplore.exe (PID: 988)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 764)
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 952)
Creates files in the user directory
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2860)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:10 14:59:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3072 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jul-2016 12:59:43 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jul-2016 12:59:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000B2A | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85958 |
.rdata | 0x00002000 | 0x000021C2 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35229 |
.data | 0x00005000 | 0x00000194 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5782 |
.rsrc | 0x00006000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75224 |
.reloc | 0x00007000 | 0x0000020C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.99459 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
Total processes
65
Monitored processes
24
Malicious processes
2
Suspicious processes
0
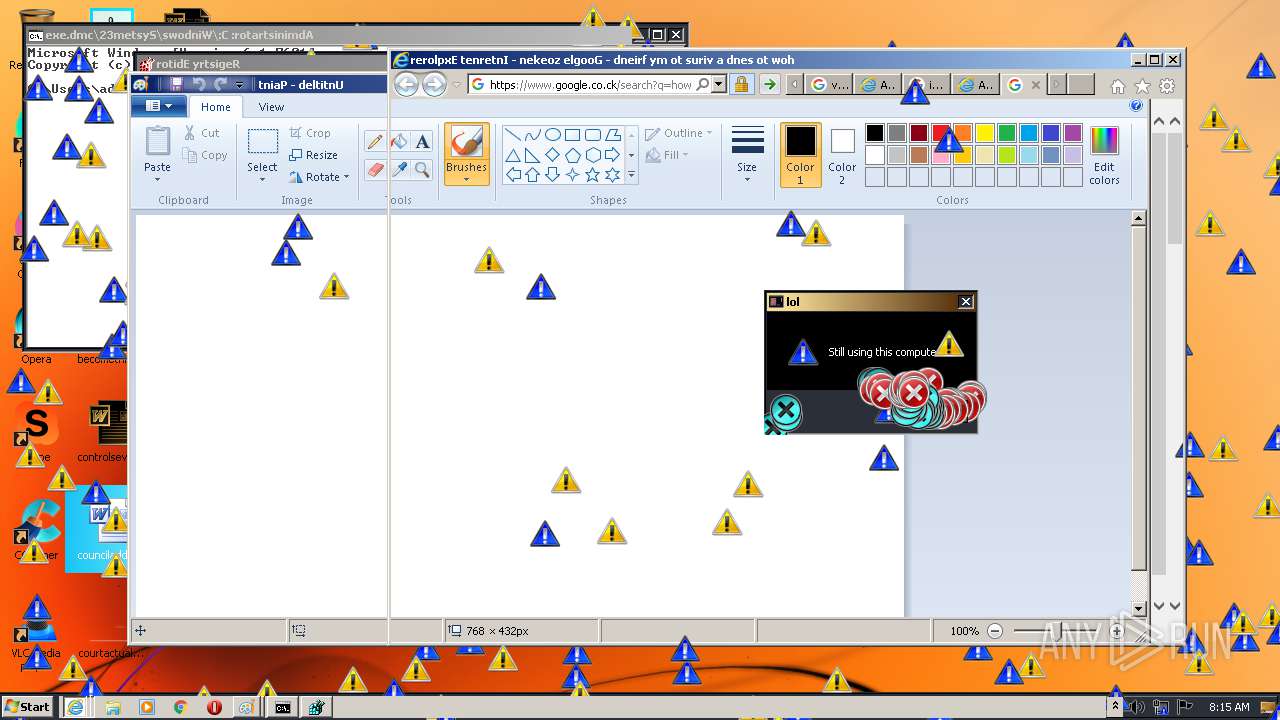
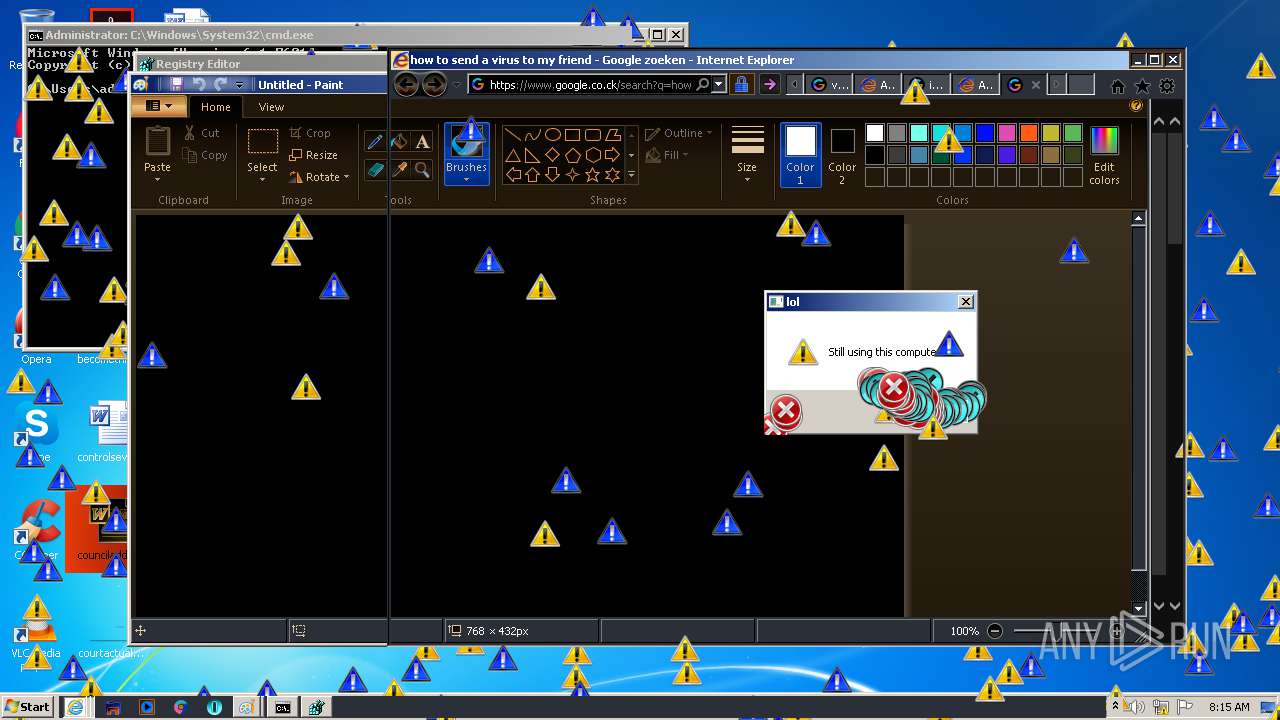
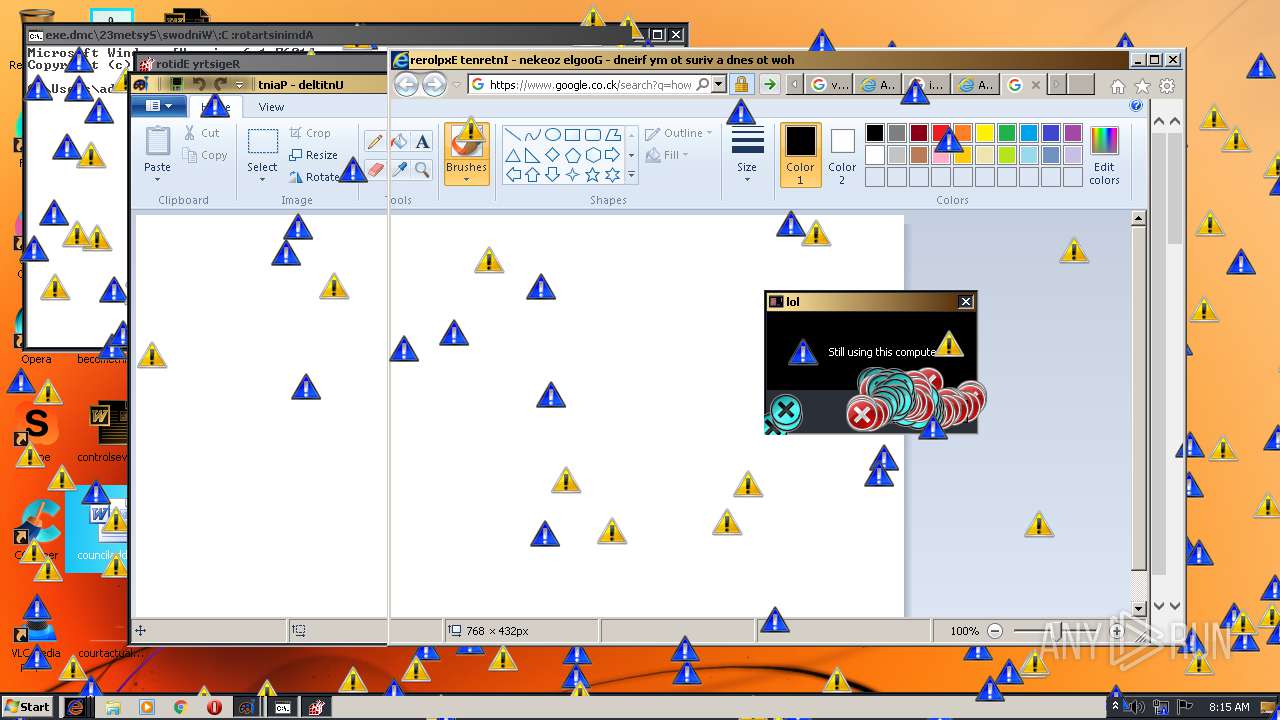
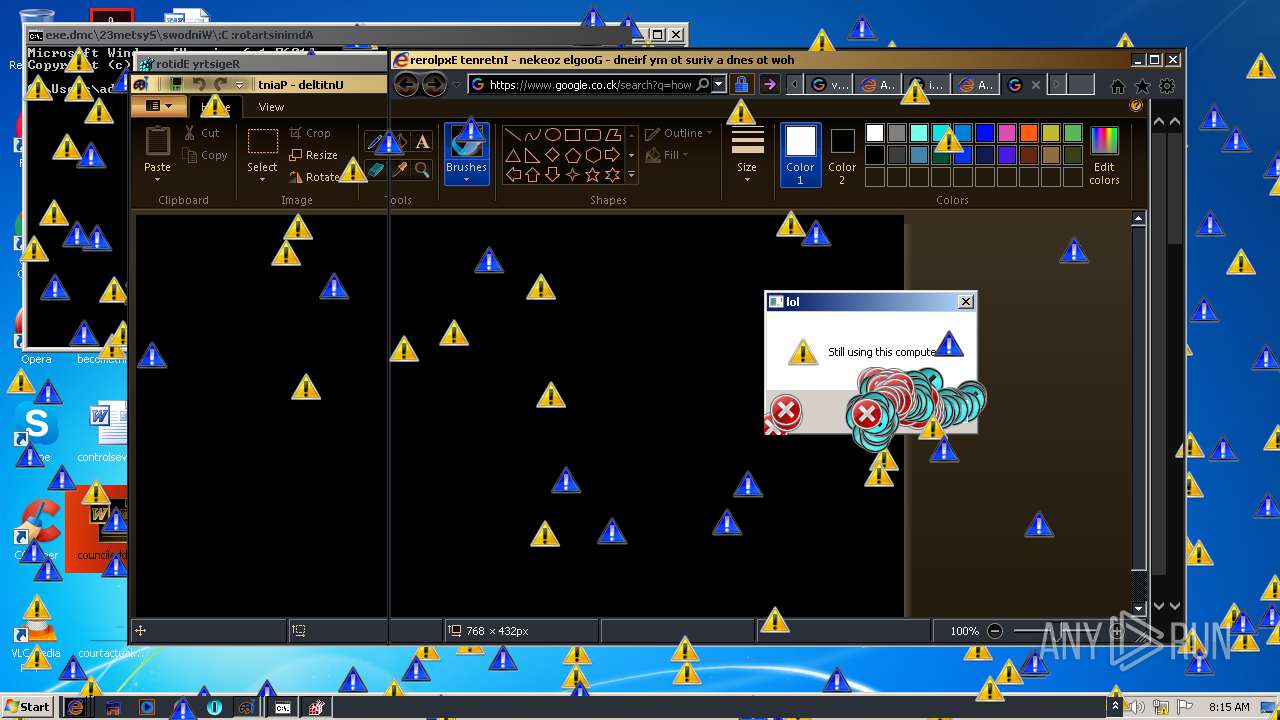
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2244 CREDAT:472085 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2244 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2244 CREDAT:537640 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 988 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=skrillex+scay+onster+an+nice+sprites+midi | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ-Destructive.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe" /main | C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe | MEMZ-Destructive.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
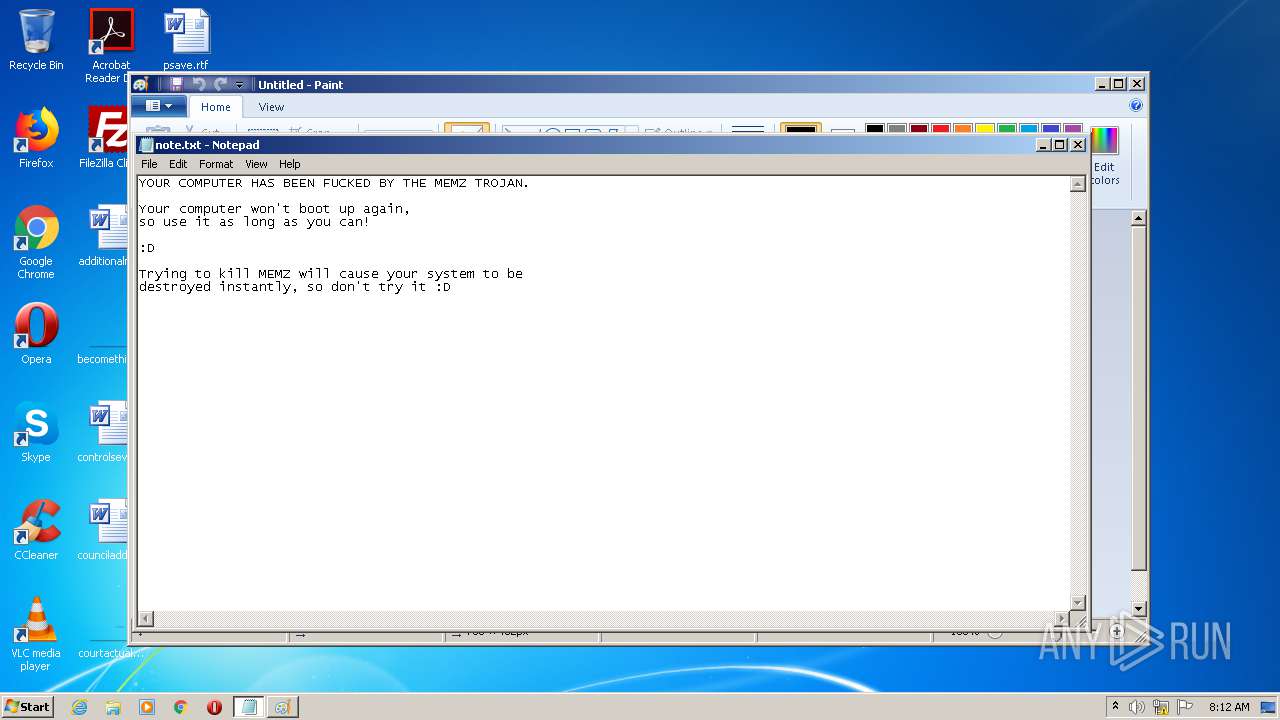
| 1452 | "C:\Windows\System32\mspaint.exe" | C:\Windows\System32\mspaint.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | "C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
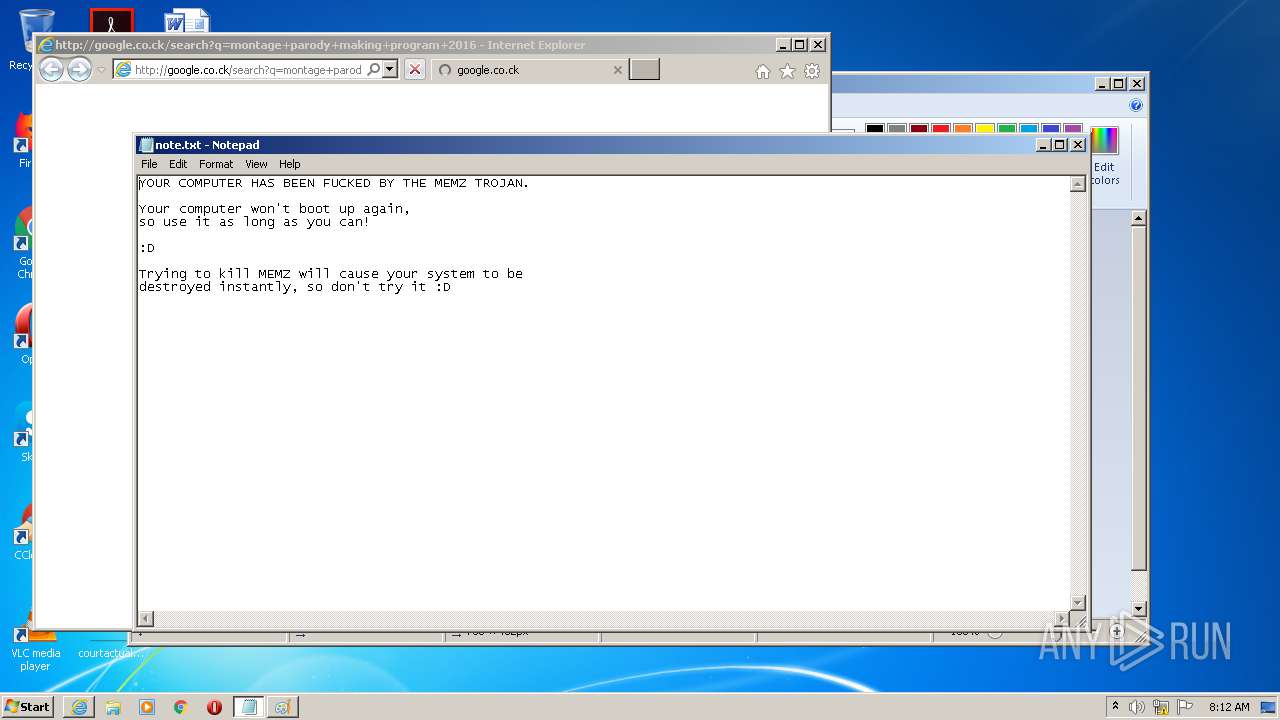
| 2244 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=montage+parody+making+program+2016 | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ-Destructive.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 682
Read events
2 818
Write events
859
Delete events
5
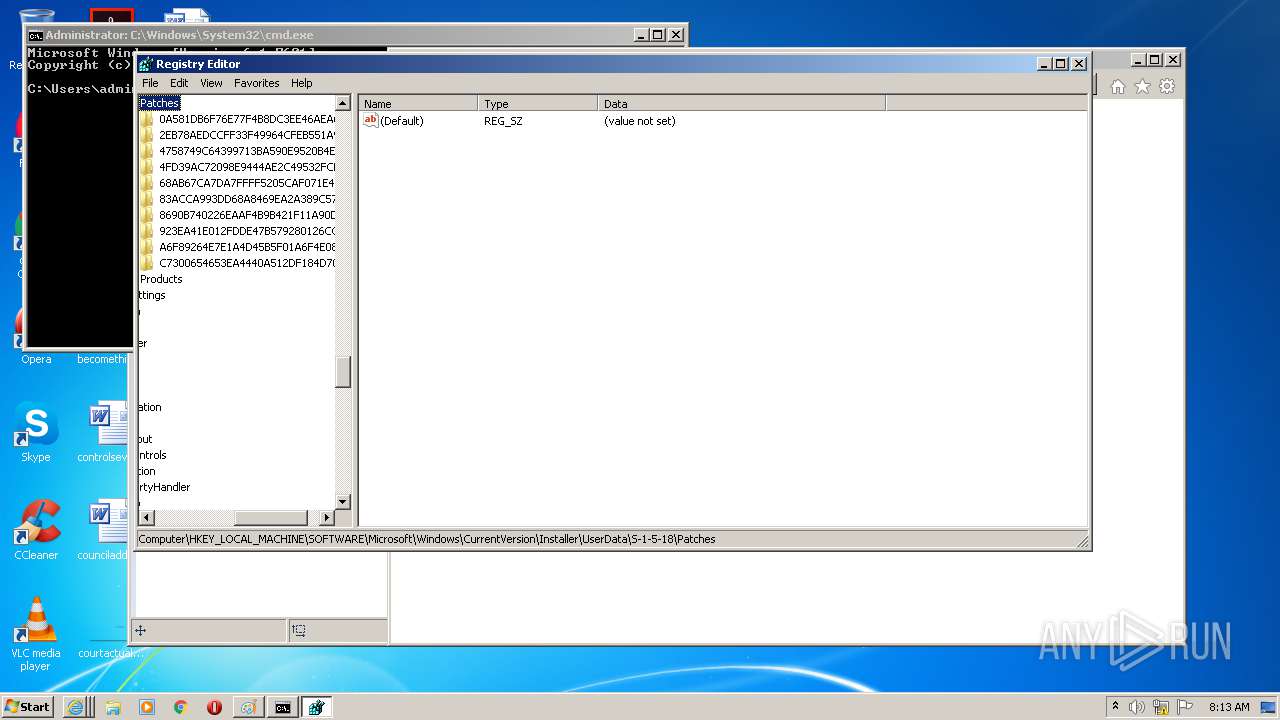
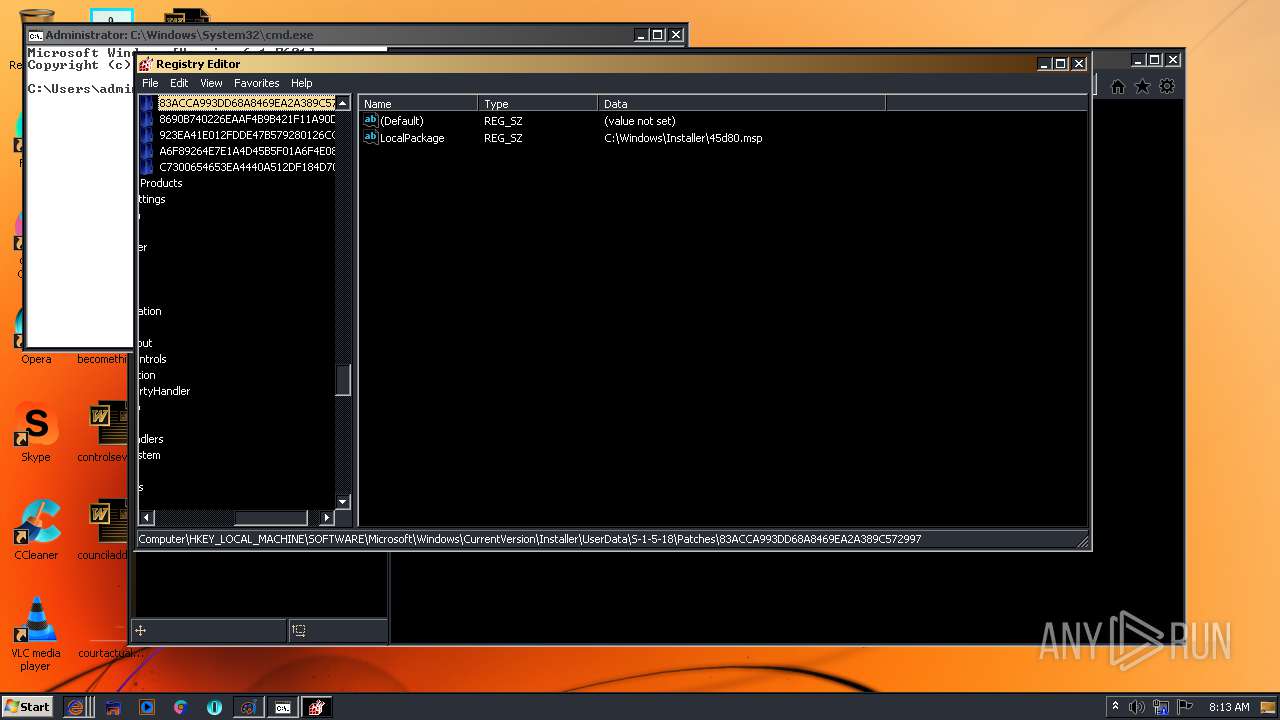
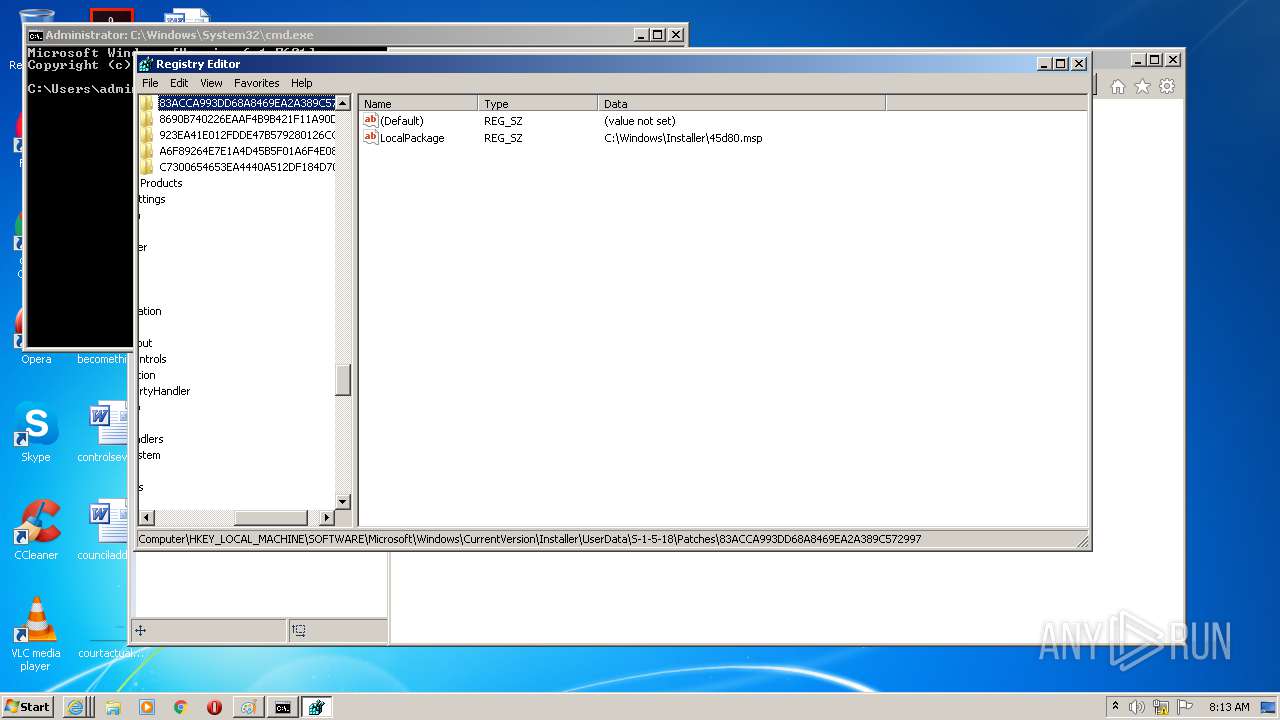
Modification events
| (PID) Process: | (3248) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3248) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1348) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1348) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3035271408 | |||
| (PID) Process: | (988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30837752 | |||
| (PID) Process: | (988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
126
Text files
198
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2D1A.tmp | — | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2D1B.tmp | — | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\W8TOO6IC.txt | — | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\72UO3GP5.txt | — | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_78F22350030542A8050E2AF00EF74543 | binary | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\IZSI21P5.txt | text | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BY5KXJG6.txt | text | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\keyboard_arrow_down_grey600_24dp[1].png | — | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 3820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\googlelogo_color_92x36dp[1].png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
280
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFAwTjBMMEowSDAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCDwJ7Pgqx7j4CAAAAAHpL0A%3D%3D | US | der | 470 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDOs%2FDKHsIMiAIAAAAAeksR | US | der | 472 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBnDSwYD0b%2FmAgAAAAB5ZF4%3D | US | der | 471 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDOs%2FDKHsIMiAIAAAAAeksR | US | der | 472 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEF63qnz4WG%2FPCAAAAABWBp0%3D | US | der | 471 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBnDSwYD0b%2FmAgAAAAB5ZF4%3D | US | der | 471 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFAwTjBMMEowSDAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCDwJ7Pgqx7j4CAAAAAHpL0A%3D%3D | US | der | 470 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBnDSwYD0b%2FmAgAAAAB5ZF4%3D | US | der | 471 b | whitelisted |
3820 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBnDSwYD0b%2FmAgAAAAB5ZF4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3820 | iexplore.exe | 216.58.207.68:80 | google.co.ck | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 172.217.16.195:80 | www.google.co.ck | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 172.217.16.195:443 | www.google.co.ck | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 172.217.18.174:443 | consent.google.co.ck | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 172.217.22.46:443 | consent.google.com | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3820 | iexplore.exe | 216.58.212.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
988 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
988 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.co.ck |
| whitelisted |
www.google.co.ck |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
consent.google.com |
| shared |
consent.google.co.ck |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |