| File name: | MEMZ-Destructive.exe |
| Full analysis: | https://app.any.run/tasks/63148cec-d0a6-44cc-a10d-f296893b3280 |
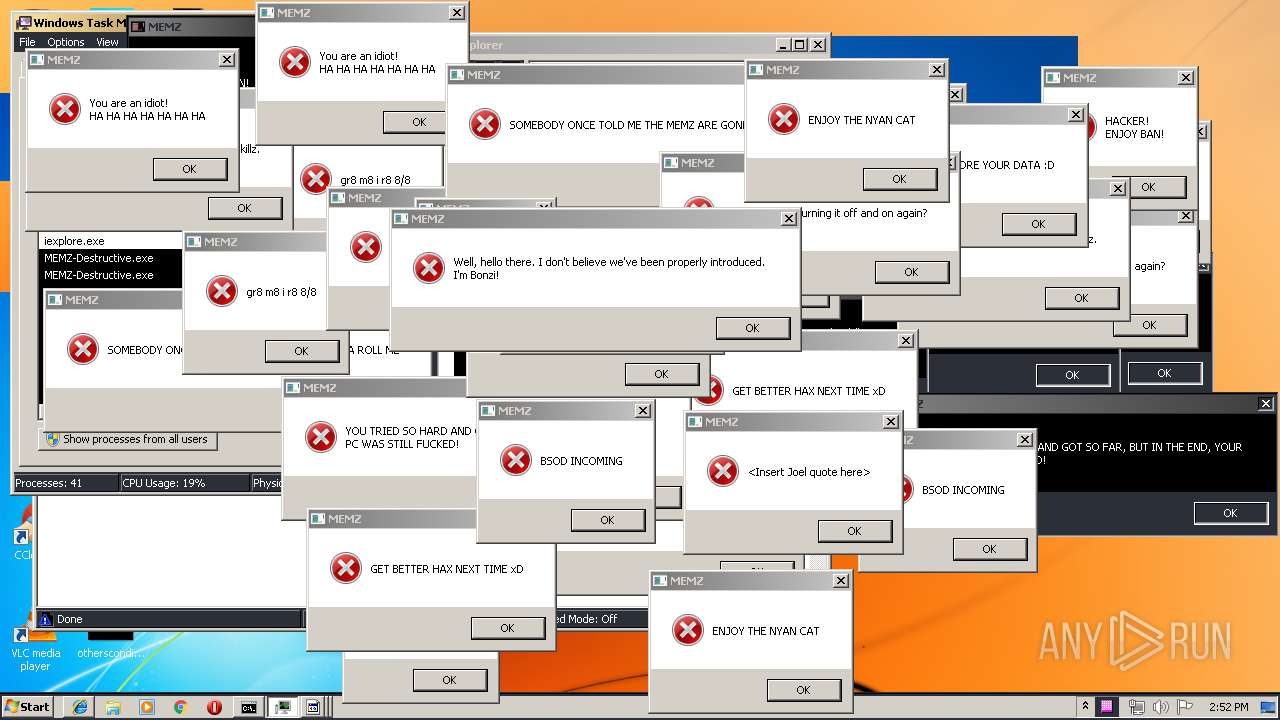
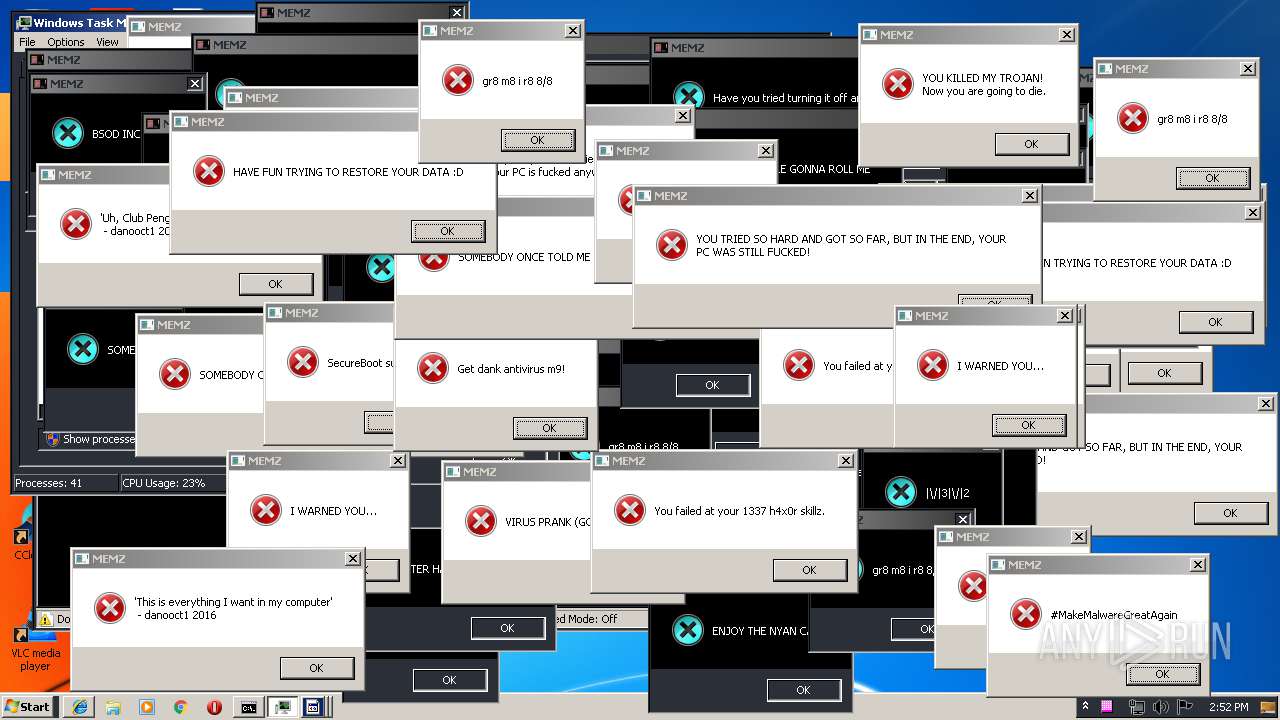
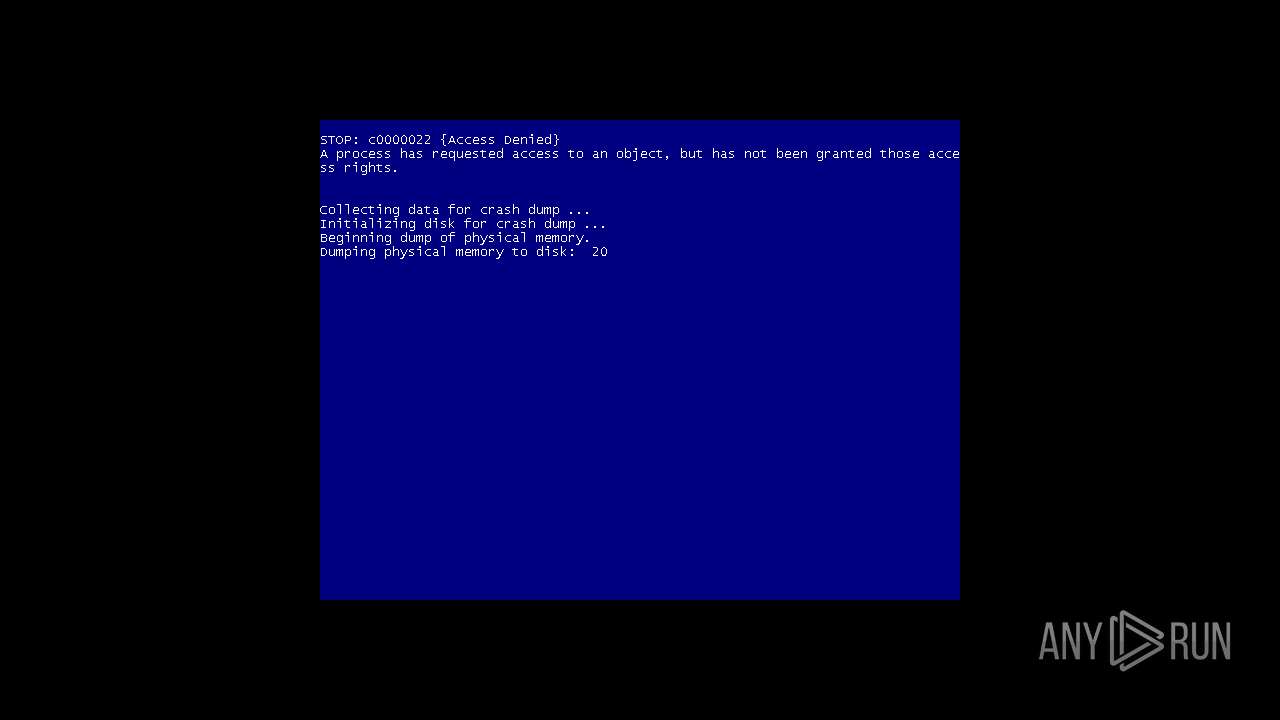
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 13:49:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 19DBEC50735B5F2A72D4199C4E184960 |
| SHA1: | 6FED7732F7CB6F59743795B2AB154A3676F4C822 |
| SHA256: | A3D5715A81F2FBEB5F76C88C9C21EEEE87142909716472F911FF6950C790C24D |
| SSDEEP: | 192:sIvxdXSQeWSg9JJS/lcIEiwqZKBkDFR43xWTM3LHn8f26gyr6yfFCj3r:sMVSaSEglcIqq3agmLc+6gyWqFCj |
MALICIOUS
Low-level write access rights to disk partition
- MEMZ-Destructive.exe (PID: 2448)
Application was dropped or rewritten from another process
- firefox.exe (PID: 3032)
- firefox.exe (PID: 1020)
- firefox.exe (PID: 908)
- firefox.exe (PID: 2212)
- firefox.exe (PID: 3580)
- firefox.exe (PID: 2352)
- pingsender.exe (PID: 3440)
- pingsender.exe (PID: 1360)
- updater.exe (PID: 3548)
- updater.exe (PID: 3156)
- helper.exe (PID: 3740)
- firefox.exe (PID: 2856)
- firefox.exe (PID: 3892)
- firefox.exe (PID: 3872)
- firefox.exe (PID: 2680)
- firefox.exe (PID: 3592)
- firefox.exe (PID: 2104)
- firefox.exe (PID: 3396)
- pingsender.exe (PID: 1556)
- pingsender.exe (PID: 3508)
- pingsender.exe (PID: 1712)
Loads dropped or rewritten executable
- firefox.exe (PID: 3032)
- firefox.exe (PID: 908)
- firefox.exe (PID: 2352)
- firefox.exe (PID: 1020)
- pingsender.exe (PID: 1360)
- firefox.exe (PID: 2212)
- pingsender.exe (PID: 3440)
- firefox.exe (PID: 3580)
- firefox.exe (PID: 2680)
- csrss.exe (PID: 404)
- firefox.exe (PID: 2856)
- helper.exe (PID: 3740)
- firefox.exe (PID: 2104)
- firefox.exe (PID: 3892)
- firefox.exe (PID: 3872)
- firefox.exe (PID: 3592)
- firefox.exe (PID: 3396)
- pingsender.exe (PID: 3508)
- pingsender.exe (PID: 1556)
- pingsender.exe (PID: 1712)
Runs app for hidden code execution
- MEMZ-Destructive.exe (PID: 2448)
SUSPICIOUS
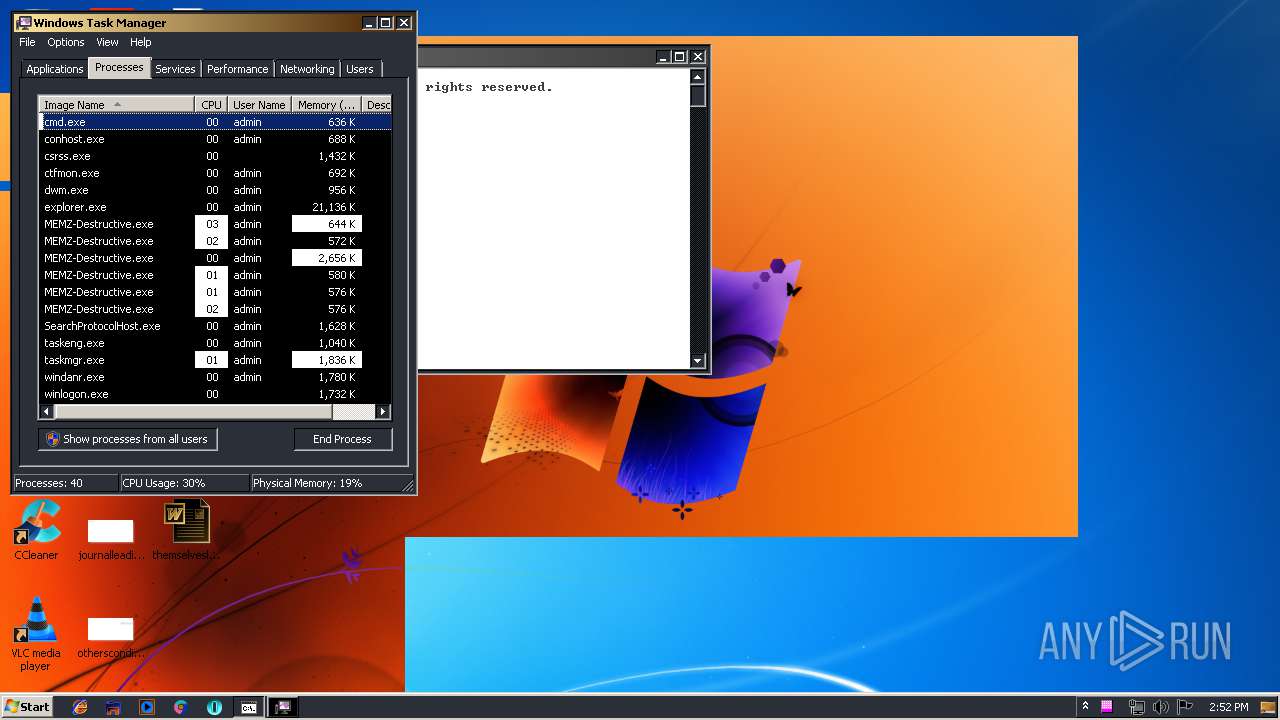
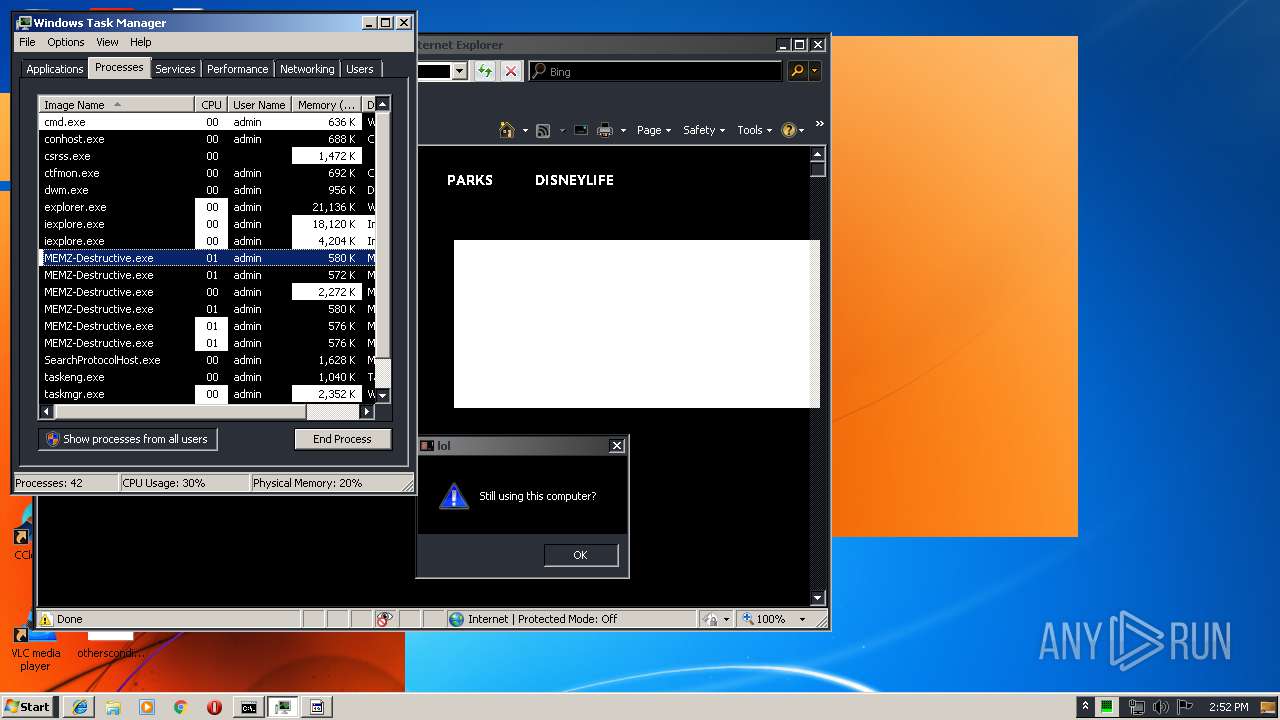
Application launched itself
- MEMZ-Destructive.exe (PID: 3480)
- updater.exe (PID: 3548)
Low-level read access rights to disk partition
- MEMZ-Destructive.exe (PID: 2448)
Creates files in the program directory
- firefox.exe (PID: 1020)
- updater.exe (PID: 3548)
- updater.exe (PID: 3156)
- helper.exe (PID: 3740)
- firefox.exe (PID: 2680)
Creates files in the user directory
- MEMZ-Destructive.exe (PID: 2448)
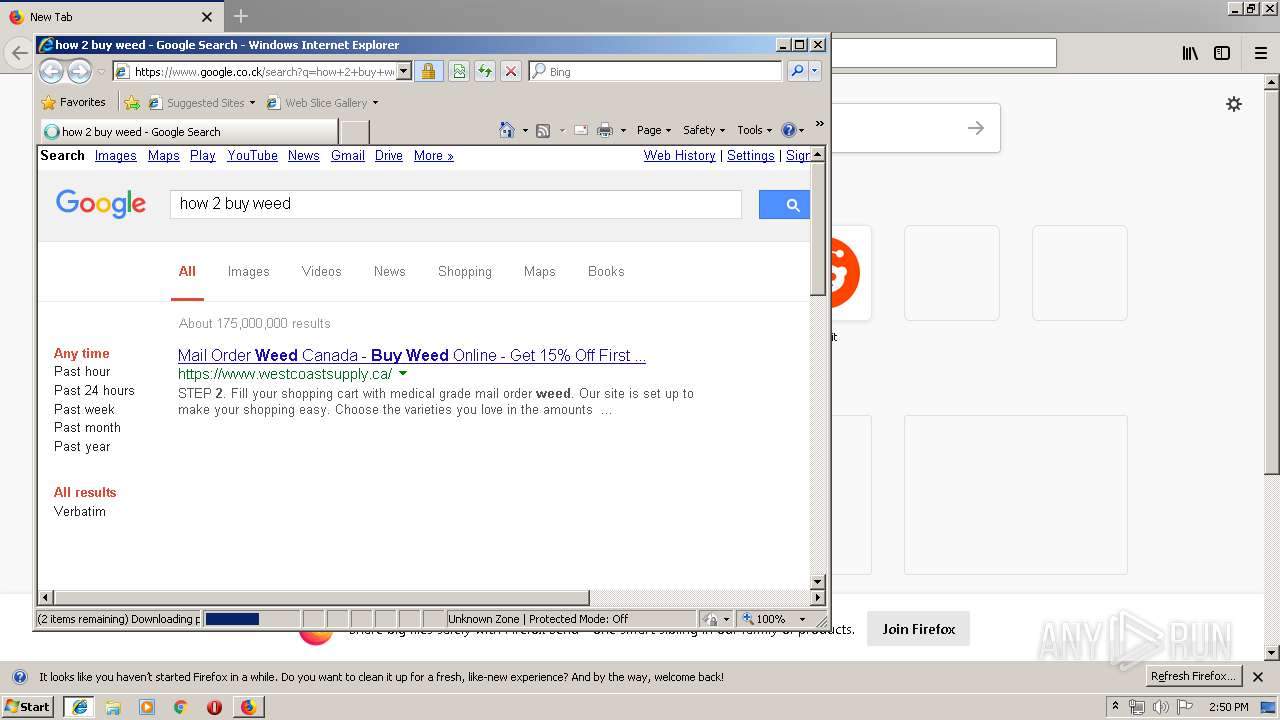
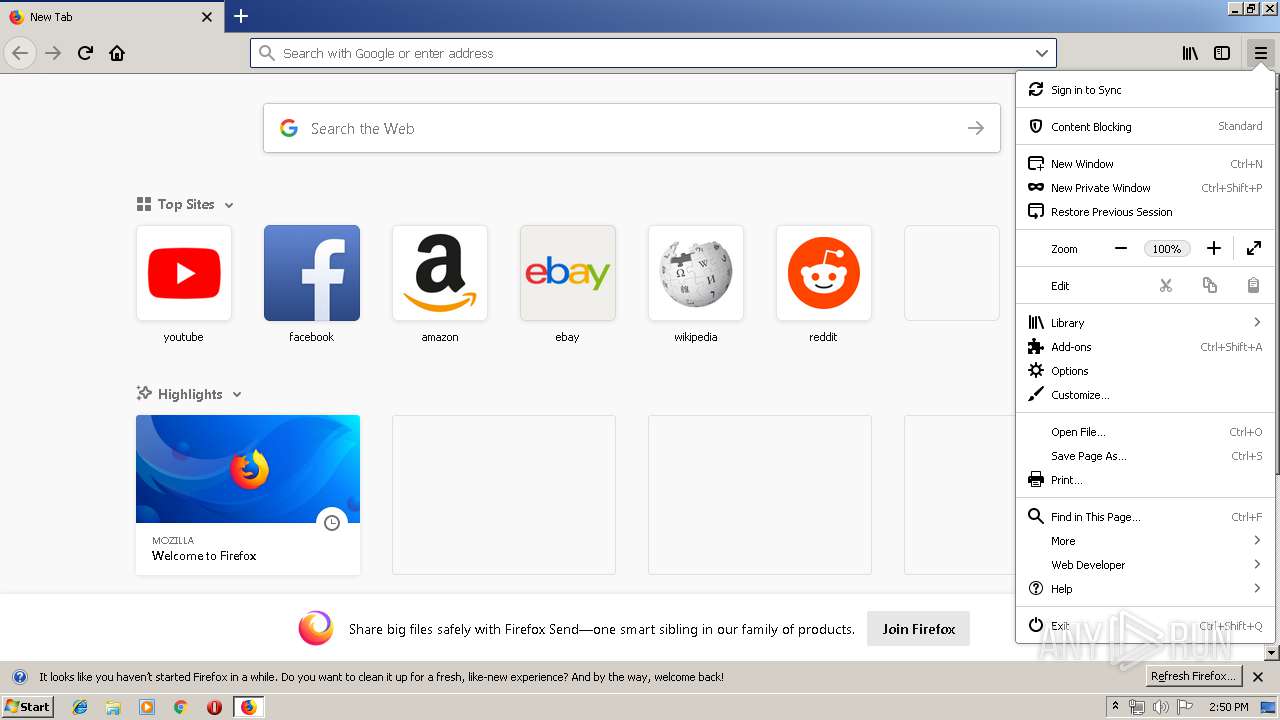
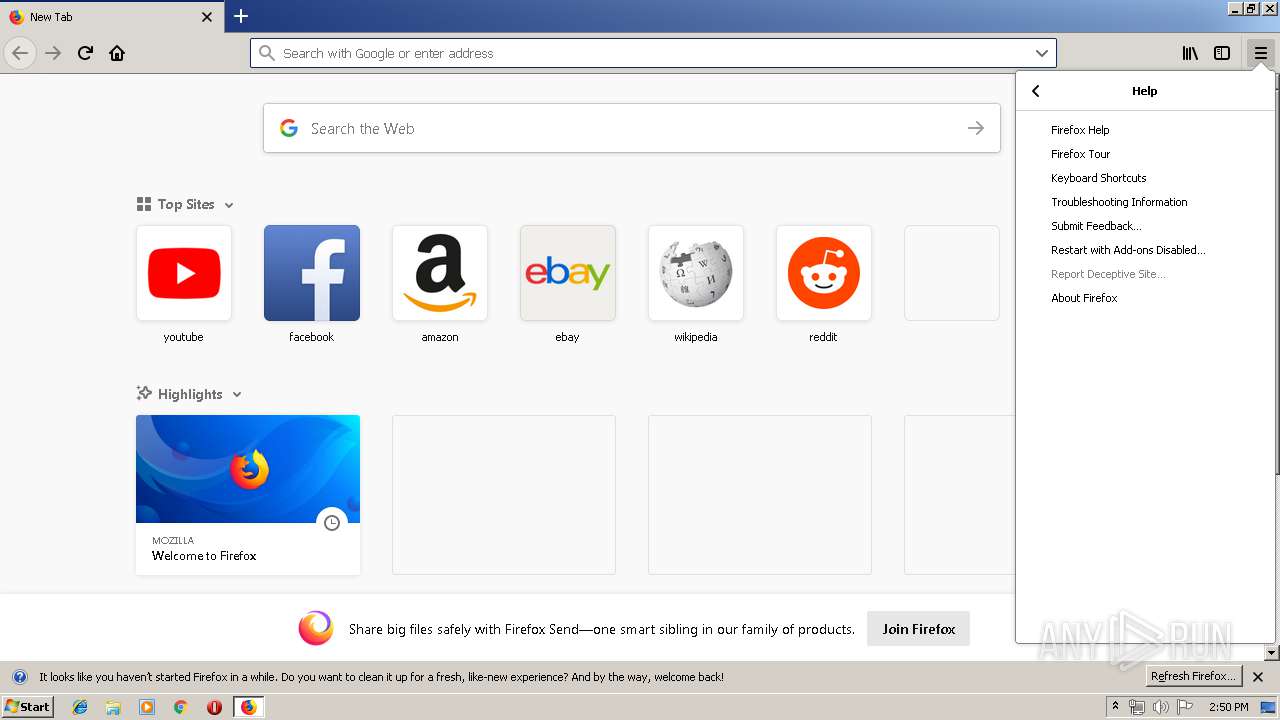
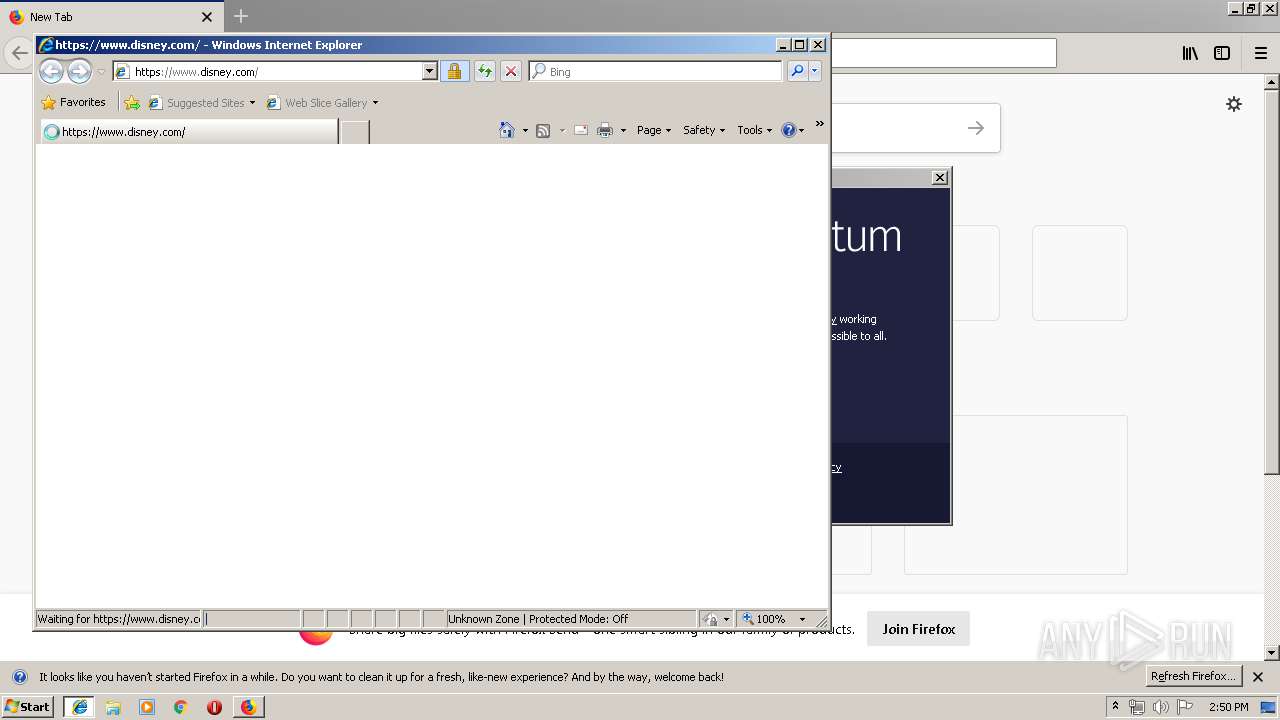
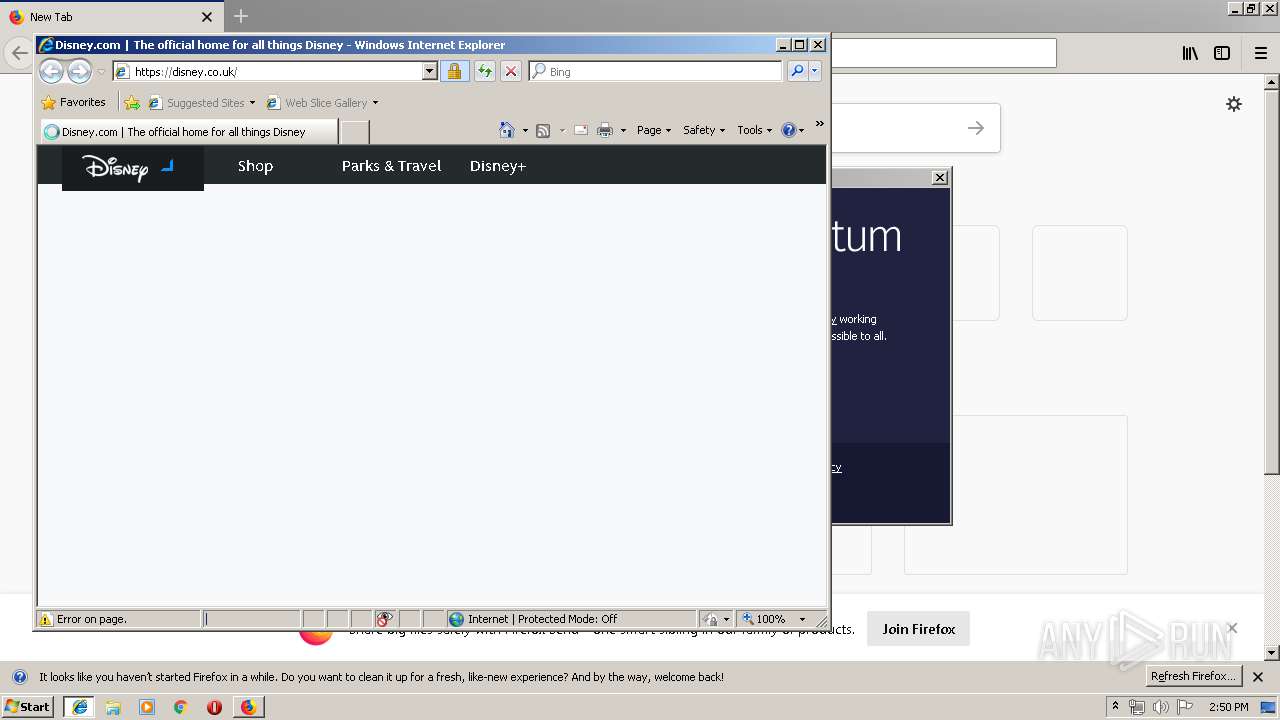
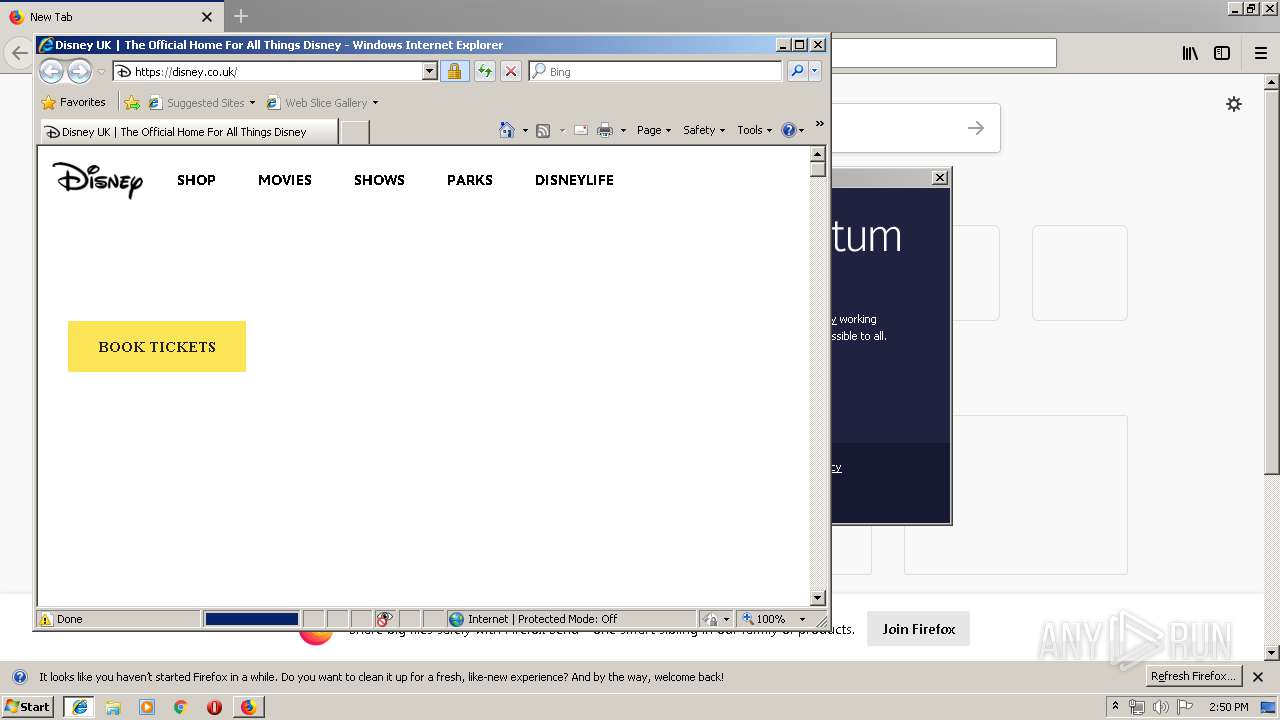
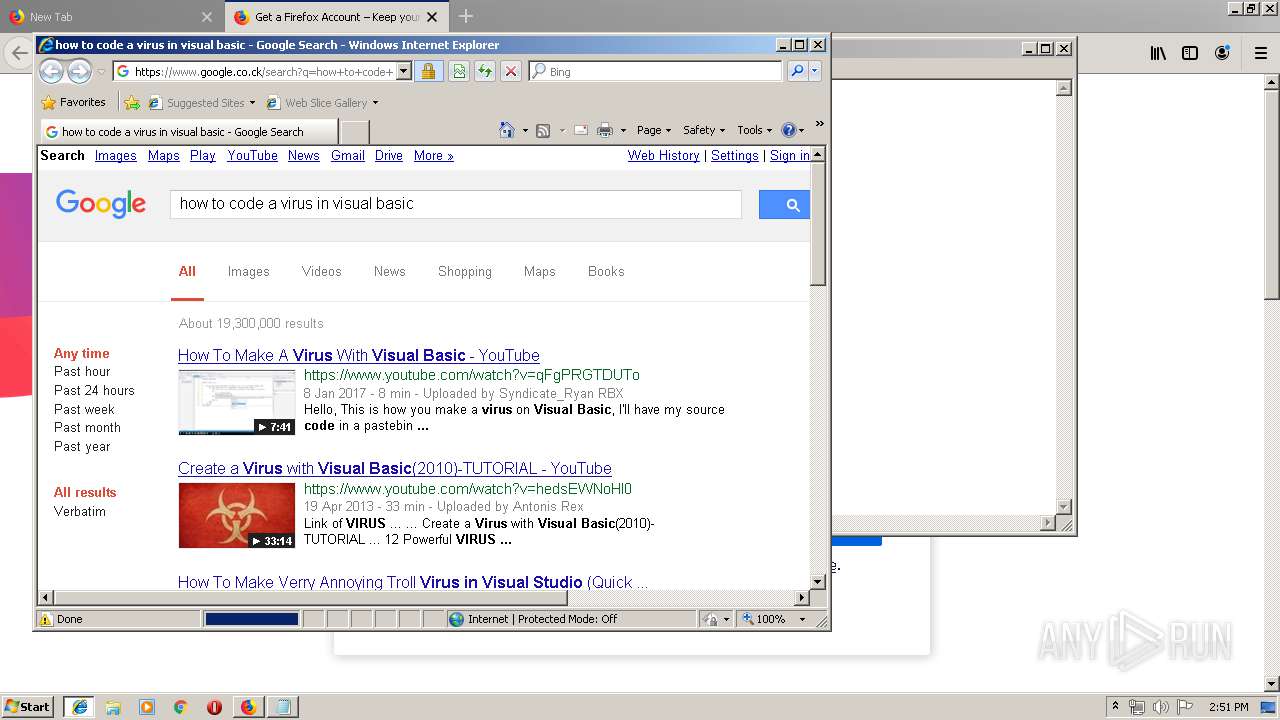
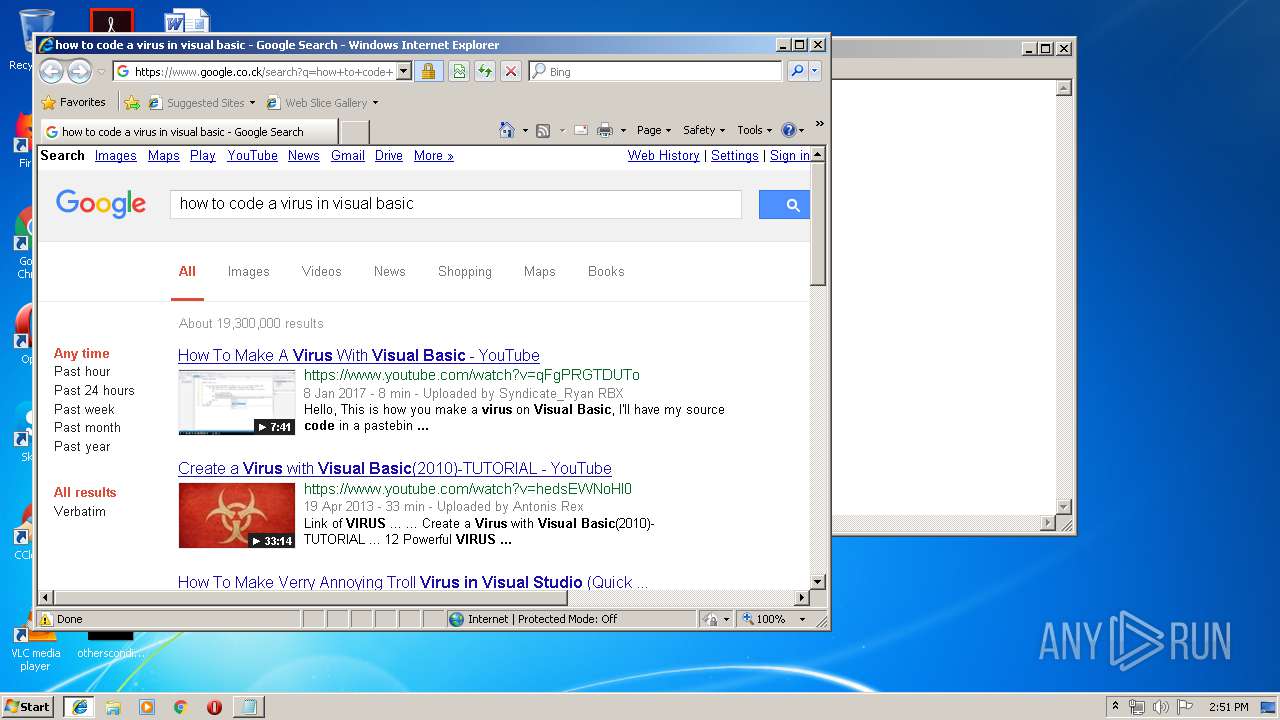
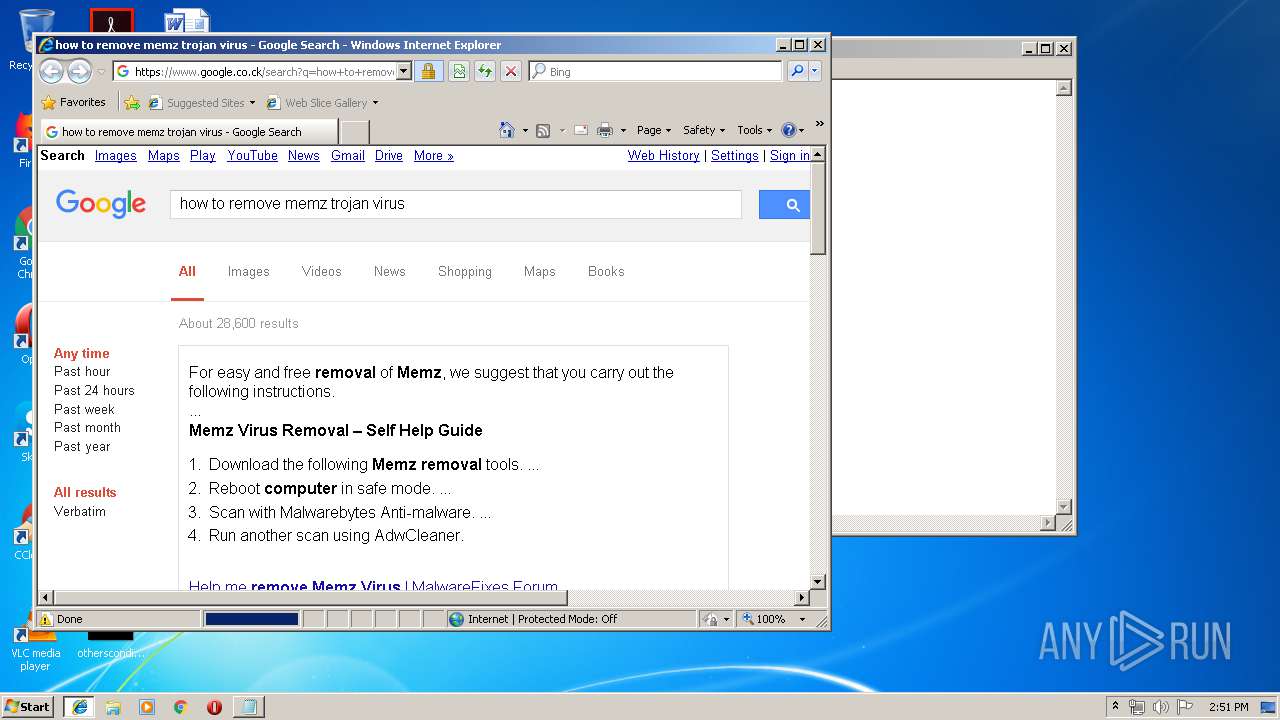
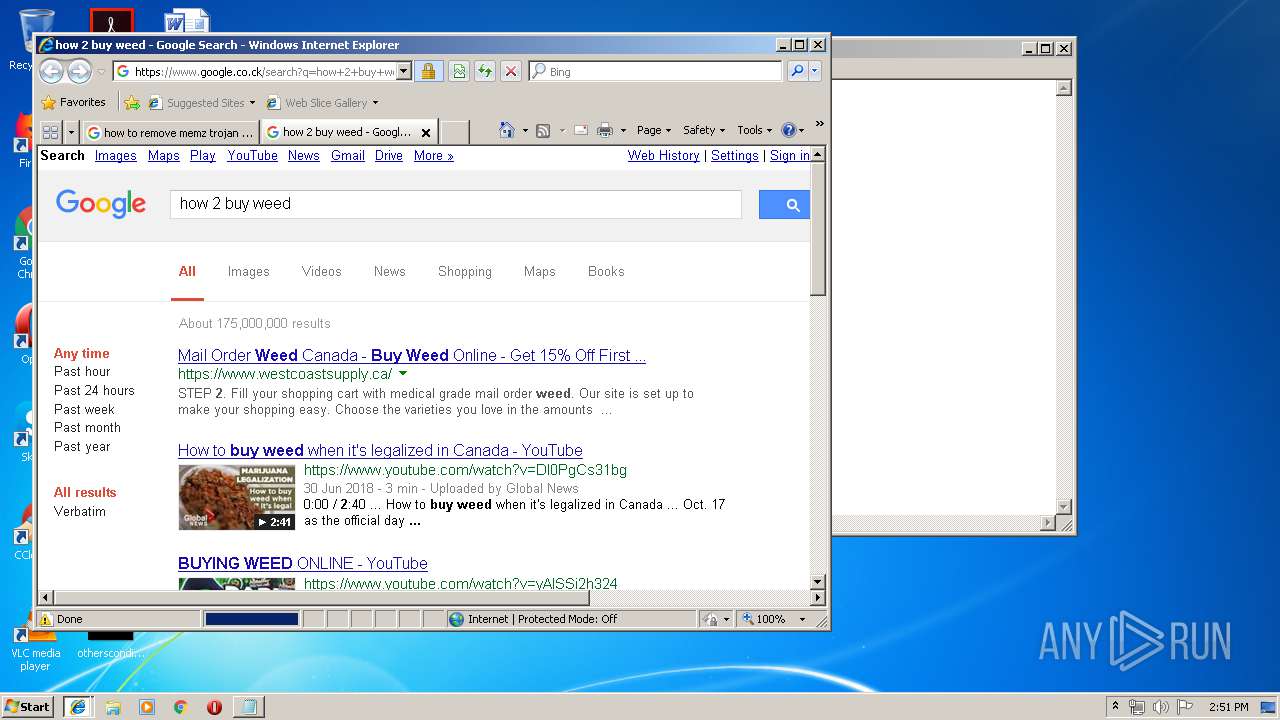
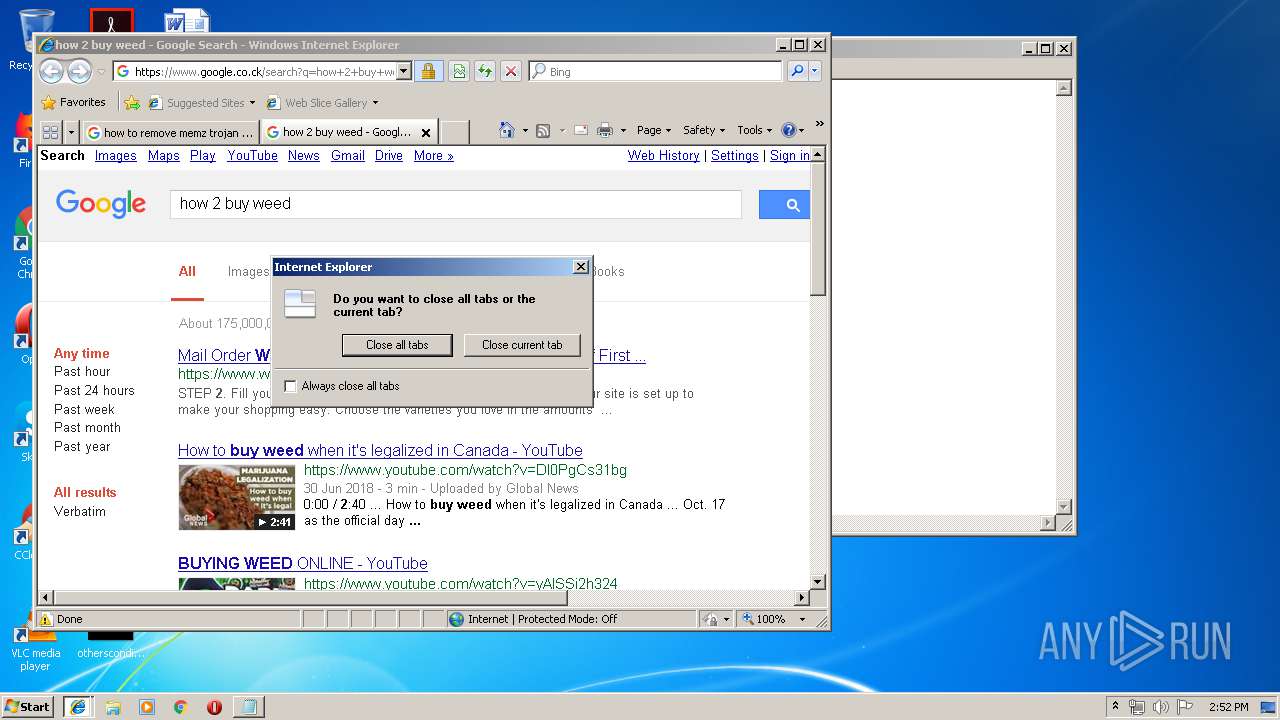
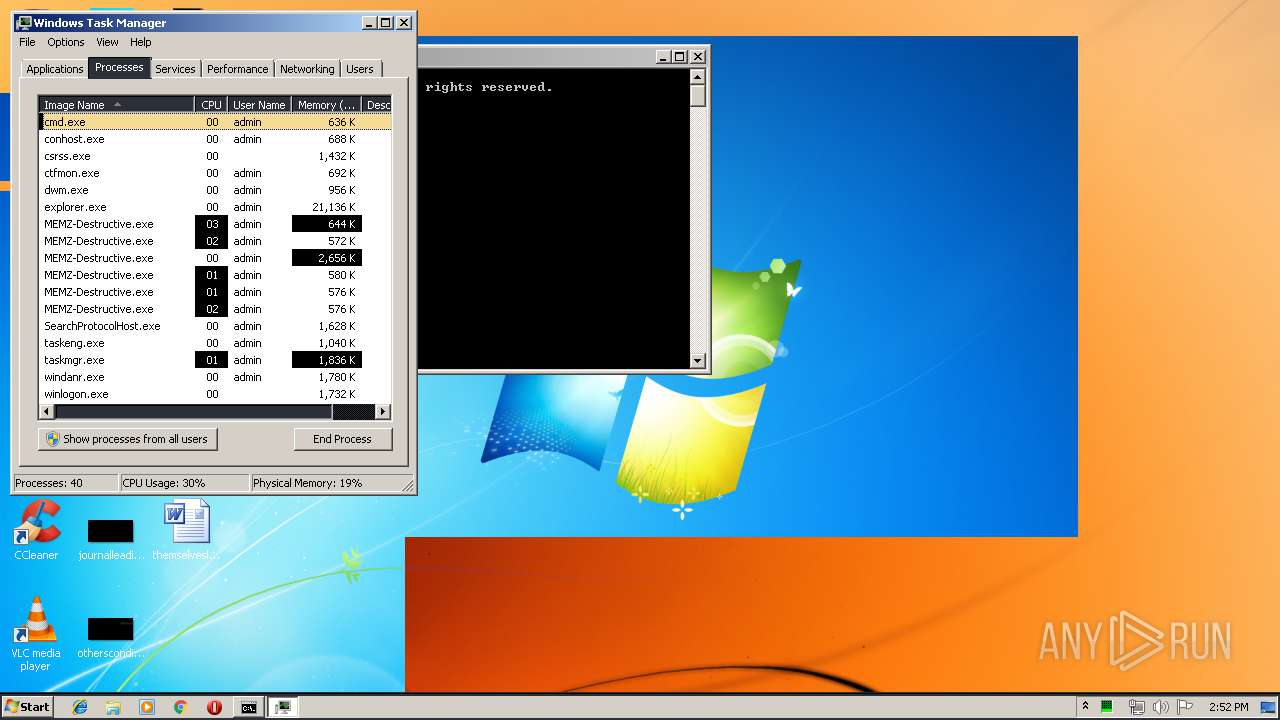
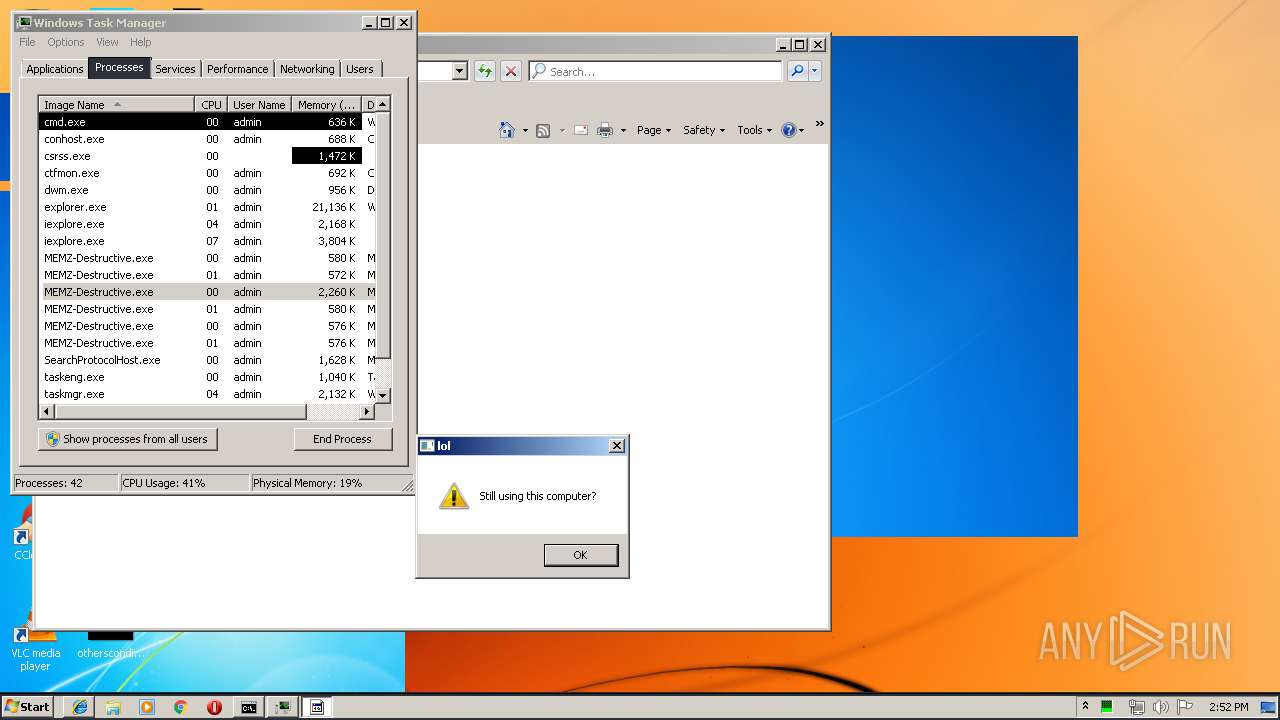
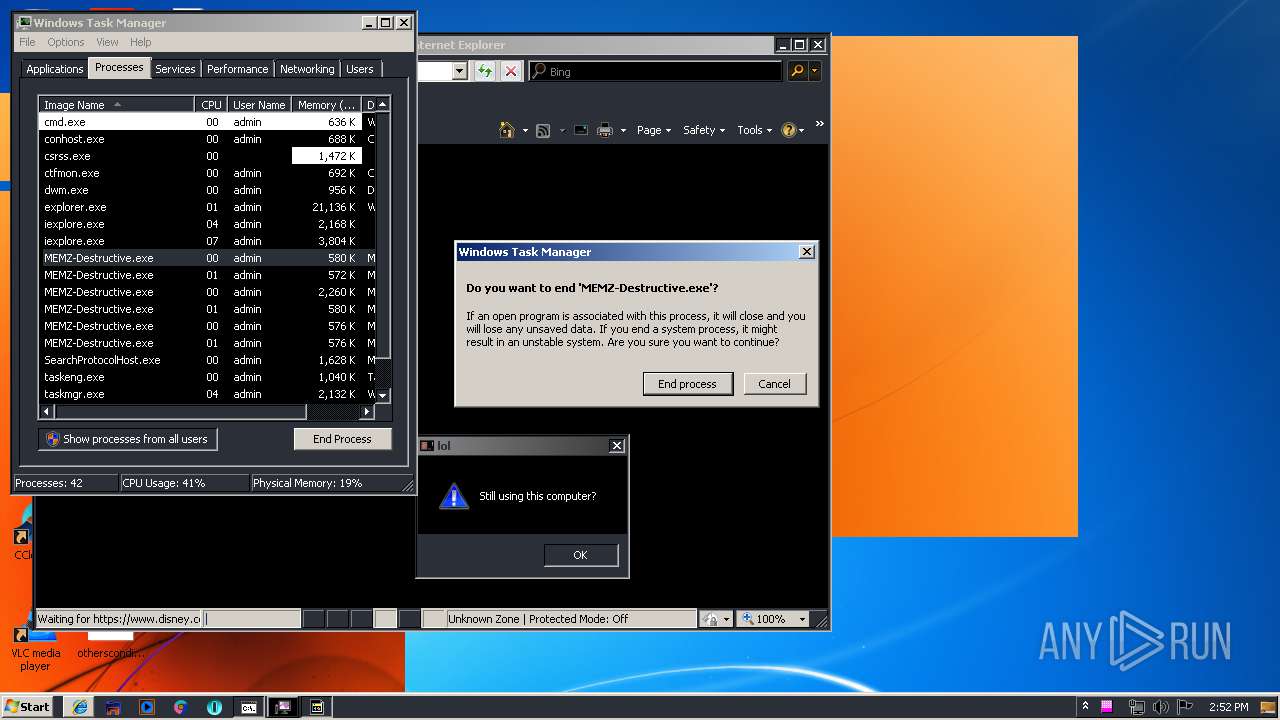
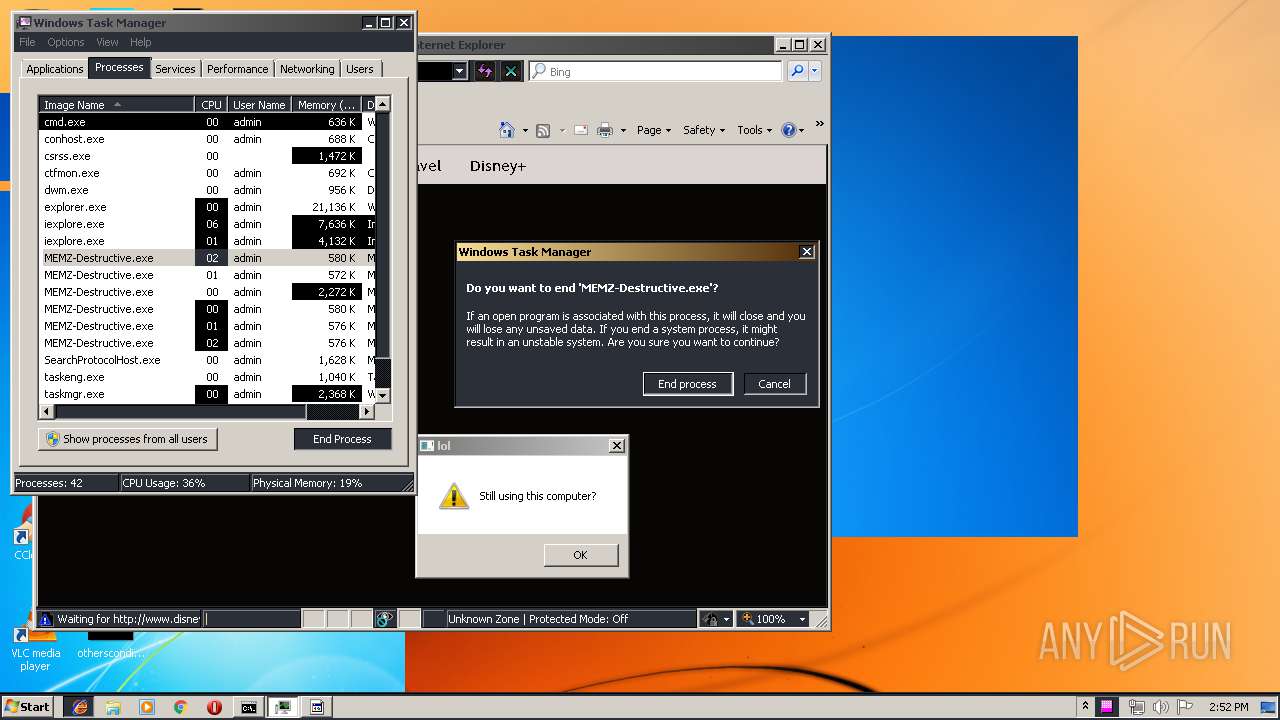
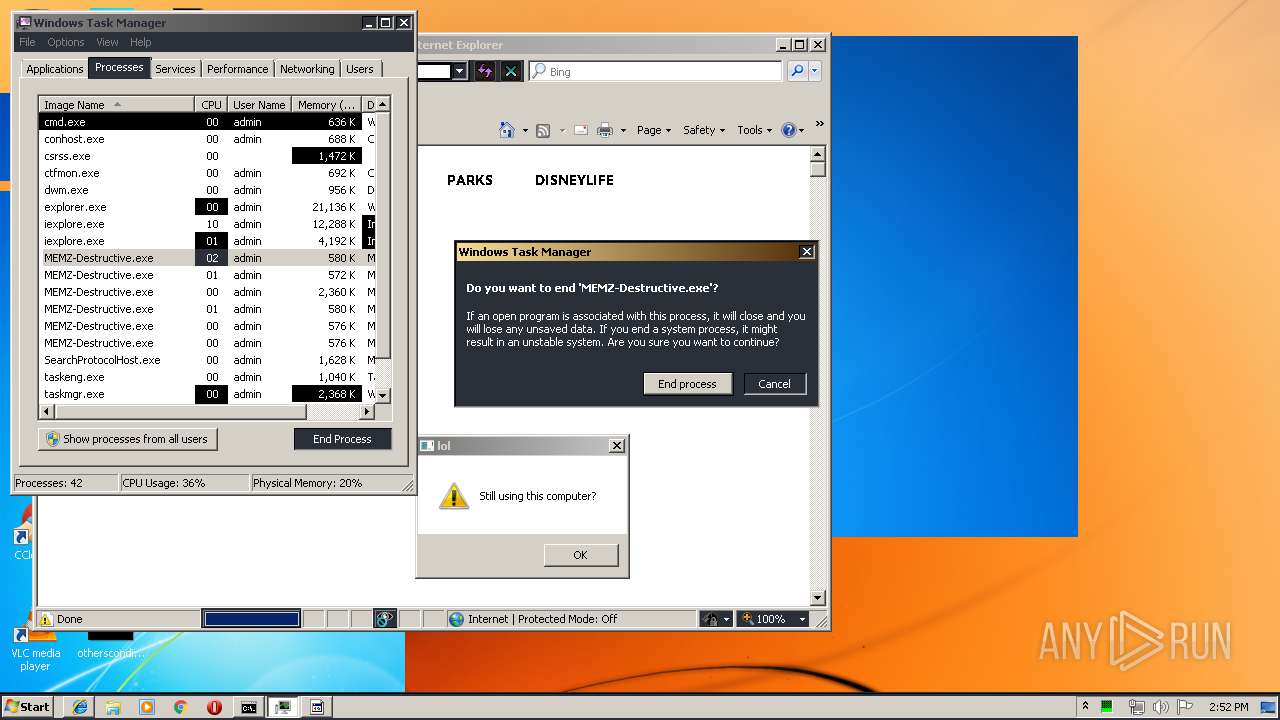
Starts Internet Explorer
- MEMZ-Destructive.exe (PID: 2448)
Loads DLL from Mozilla Firefox
- csrss.exe (PID: 404)
- helper.exe (PID: 3740)
Executable content was dropped or overwritten
- updater.exe (PID: 3156)
- helper.exe (PID: 3740)
Creates a software uninstall entry
- helper.exe (PID: 3740)
Creates COM task schedule object
- helper.exe (PID: 3740)
Modifies the open verb of a shell class
- helper.exe (PID: 3740)
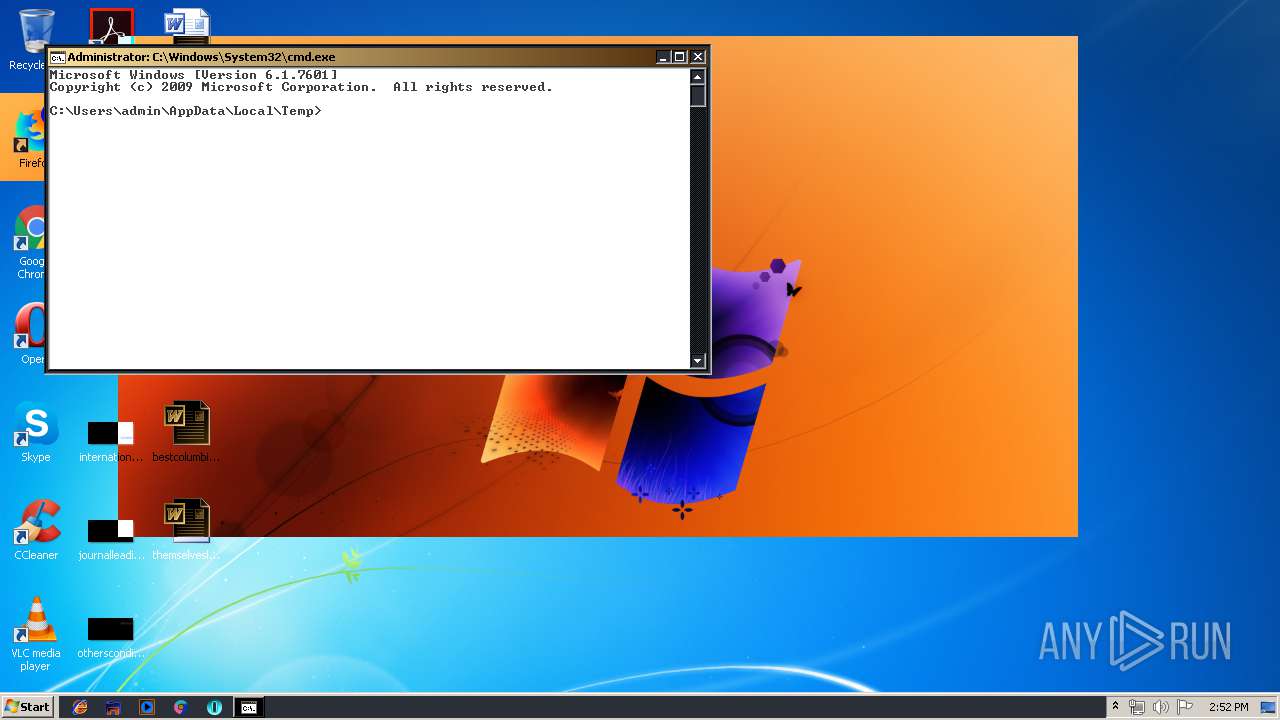
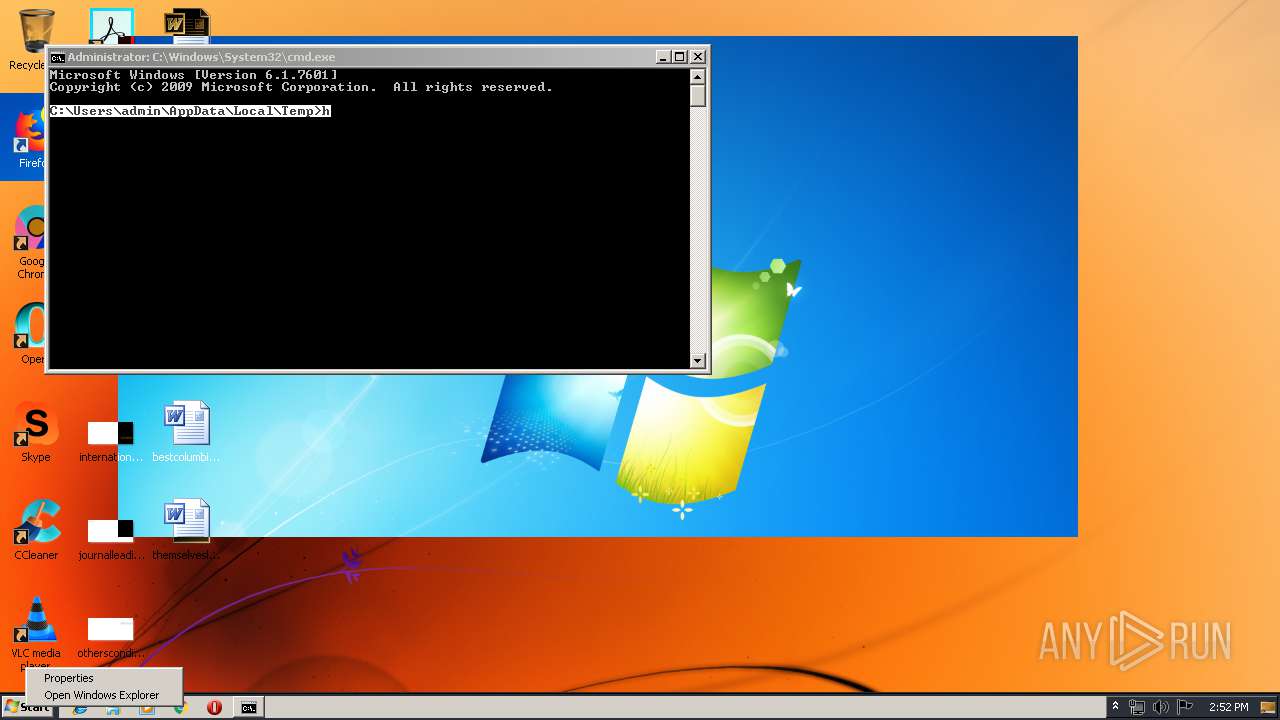
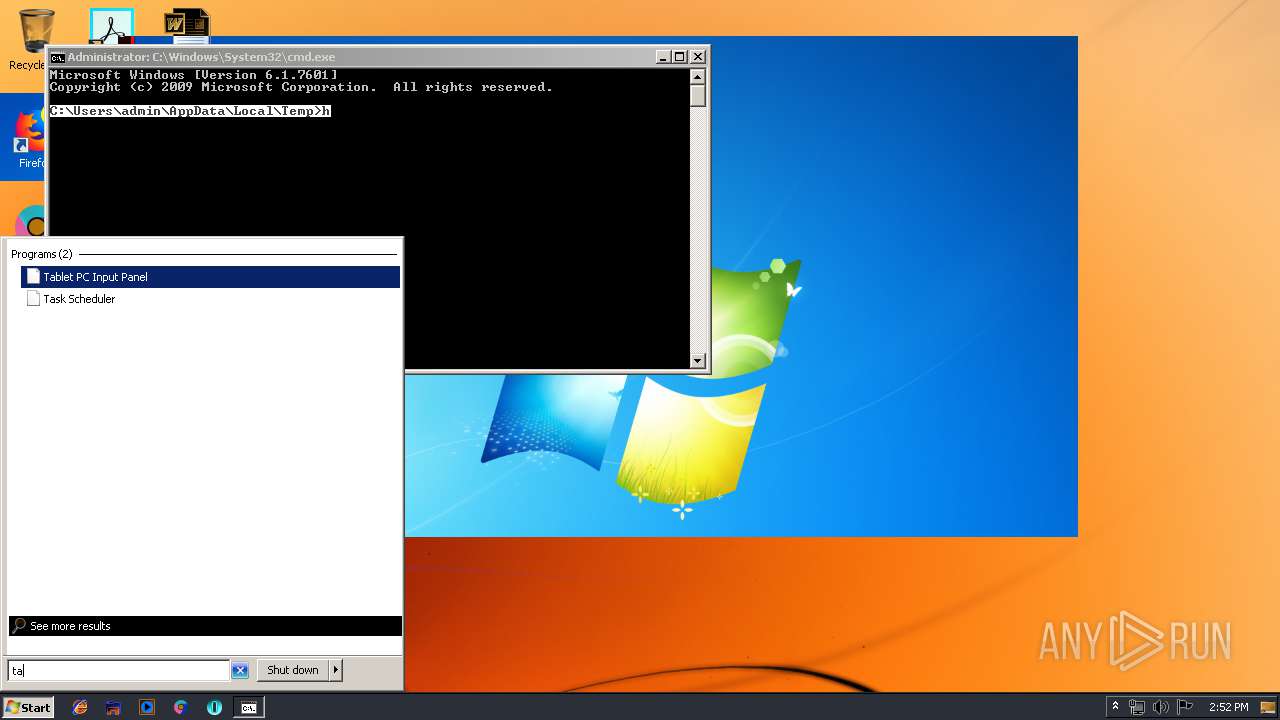
Starts CMD.EXE for commands execution
- MEMZ-Destructive.exe (PID: 2448)
INFO
Creates files in the user directory
- firefox.exe (PID: 1020)
- iexplore.exe (PID: 4028)
- firefox.exe (PID: 2680)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 1884)
- iexplore.exe (PID: 3712)
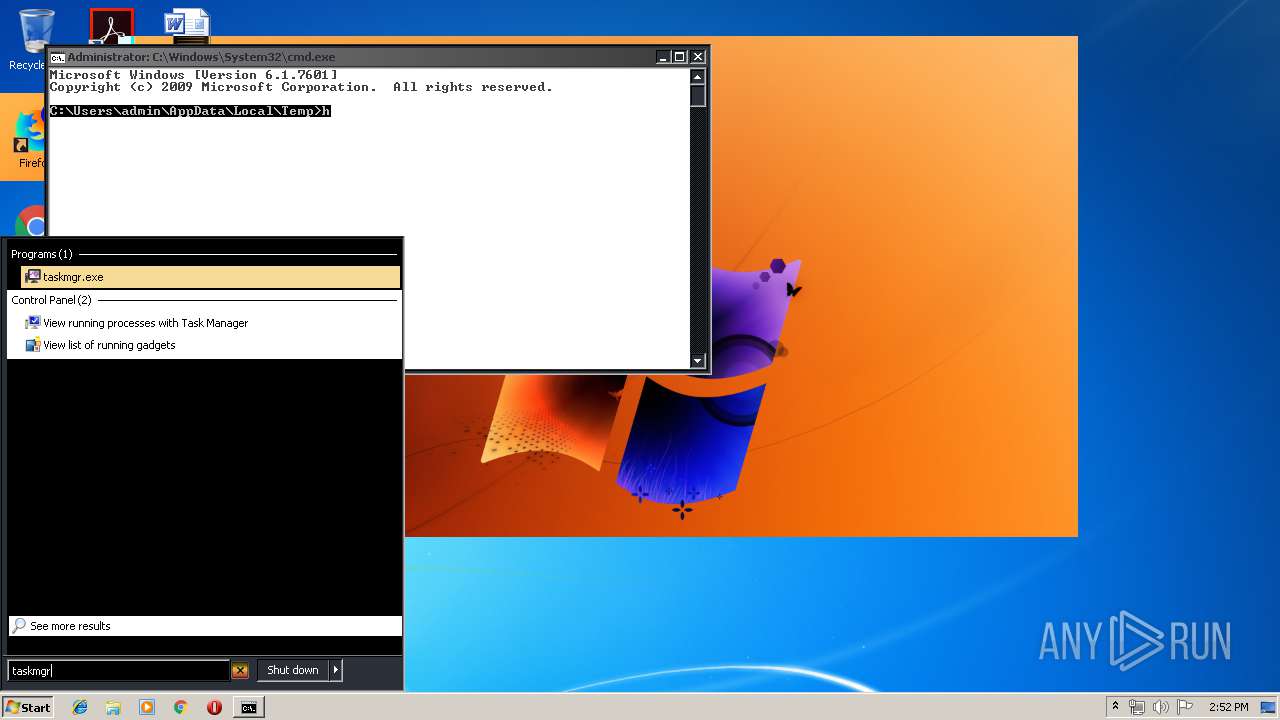
Manual execution by user
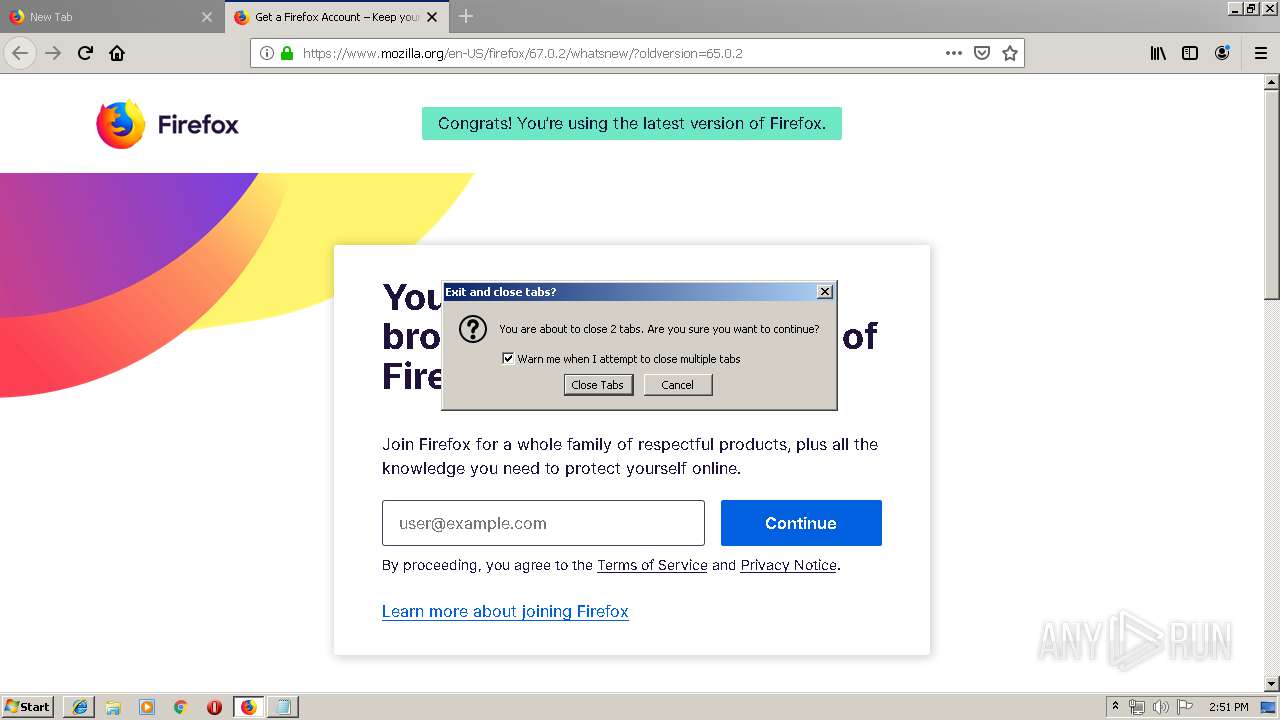
- firefox.exe (PID: 1020)
- taskmgr.exe (PID: 2456)
Reads CPU info
- firefox.exe (PID: 1020)
- firefox.exe (PID: 2680)
Application launched itself
- firefox.exe (PID: 1020)
- iexplore.exe (PID: 3188)
- firefox.exe (PID: 2680)
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 2208)
Changes internet zones settings
- iexplore.exe (PID: 3188)
- iexplore.exe (PID: 1032)
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 2208)
Changes settings of System certificates
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1972)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1972)
Reads internet explorer settings
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 1884)
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2144)
Reads Internet Cache Settings
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2144)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 2592)
Reads settings of System Certificates
- iexplore.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:10 14:59:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3072 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jul-2016 12:59:43 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jul-2016 12:59:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000B2A | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85958 |
.rdata | 0x00002000 | 0x000021C2 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35229 |
.data | 0x00005000 | 0x00000194 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5782 |
.rsrc | 0x00006000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75224 |
.reloc | 0x00007000 | 0x0000020C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.99459 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
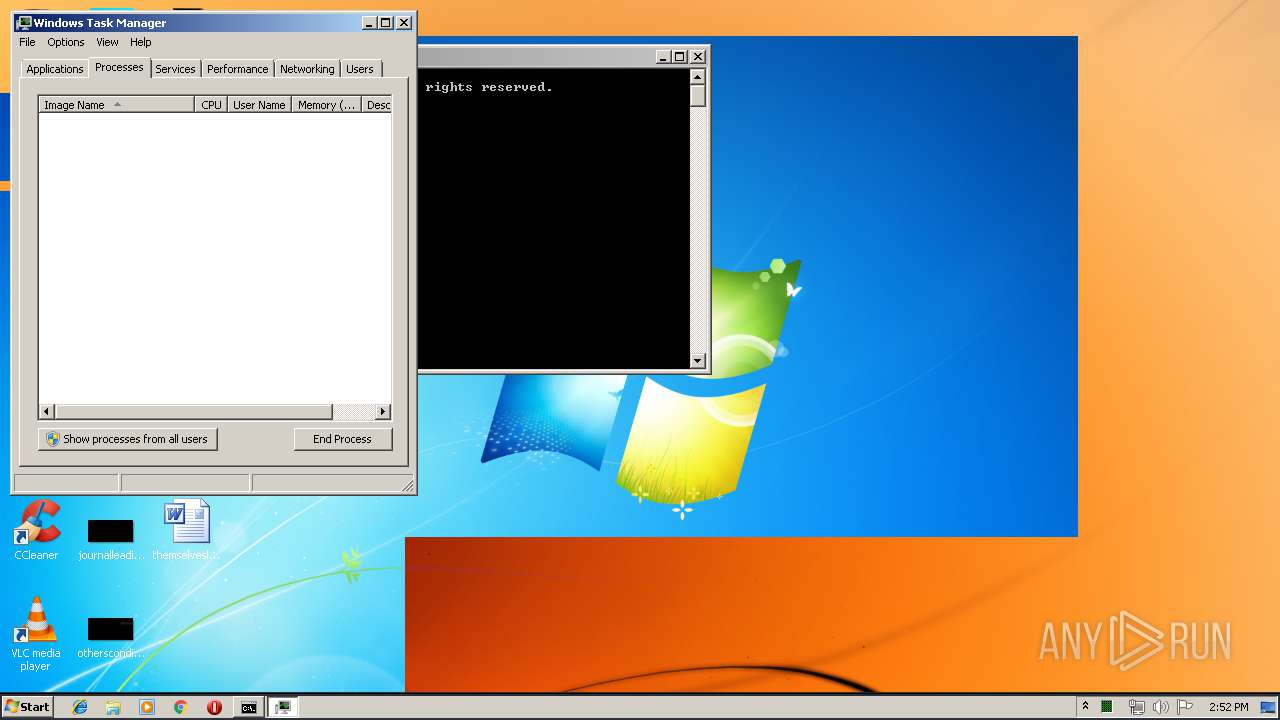
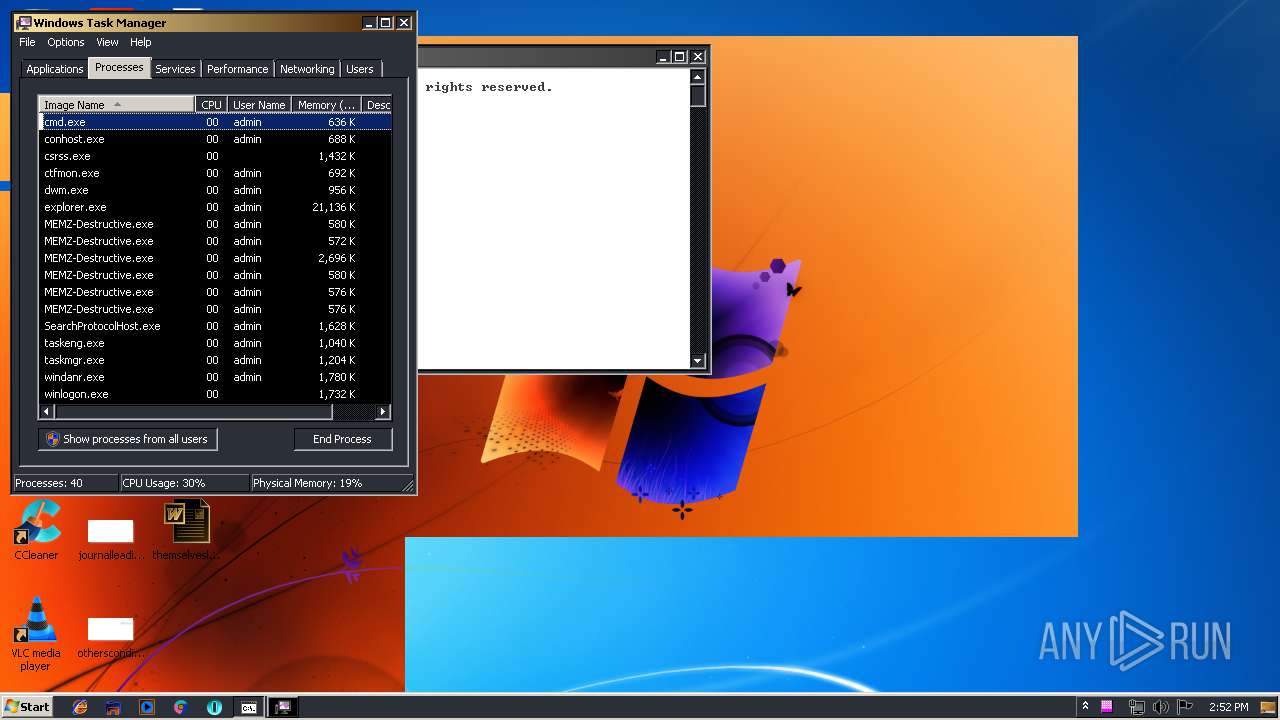
Total processes
92
Monitored processes
45
Malicious processes
25
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe" | C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 404 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1020.6.1118428661\161214342" -childID 1 -isForBrowser -prefsHandle 1540 -prefMapHandle 1740 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1020 "\\.\pipe\gecko-crash-server-pipe.1020" 1648 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ-Destructive.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/6a787482-8133-4ac7-9db8-b3de081e1c20/main/Firefox/65.0.2/release/20190225143501?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\6a787482-8133-4ac7-9db8-b3de081e1c20 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ-Destructive.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/710ec4eb-b328-470e-ad0a-8cdc02d507fb/event/Firefox/67.0.2/release/20190607204818?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\710ec4eb-b328-470e-ad0a-8cdc02d507fb | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 67.0.2 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/0c6e8168-0f15-43b4-a86c-975fc426cd14/main/Firefox/67.0.2/release/20190607204818?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\0c6e8168-0f15-43b4-a86c-975fc426cd14 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 67.0.2 Modules
| |||||||||||||||
Total events
3 664
Read events
3 064
Write events
581
Delete events
19
Modification events
| (PID) Process: | (3480) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3480) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2448) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2448) MEMZ-Destructive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
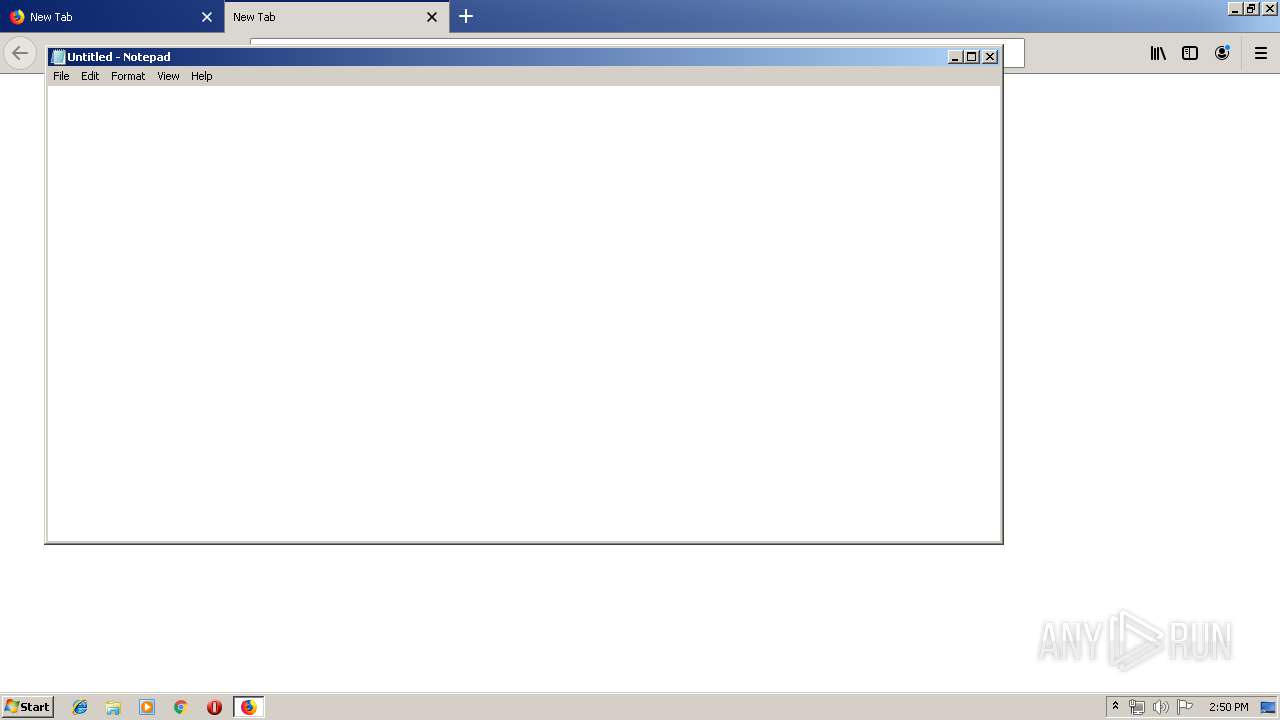
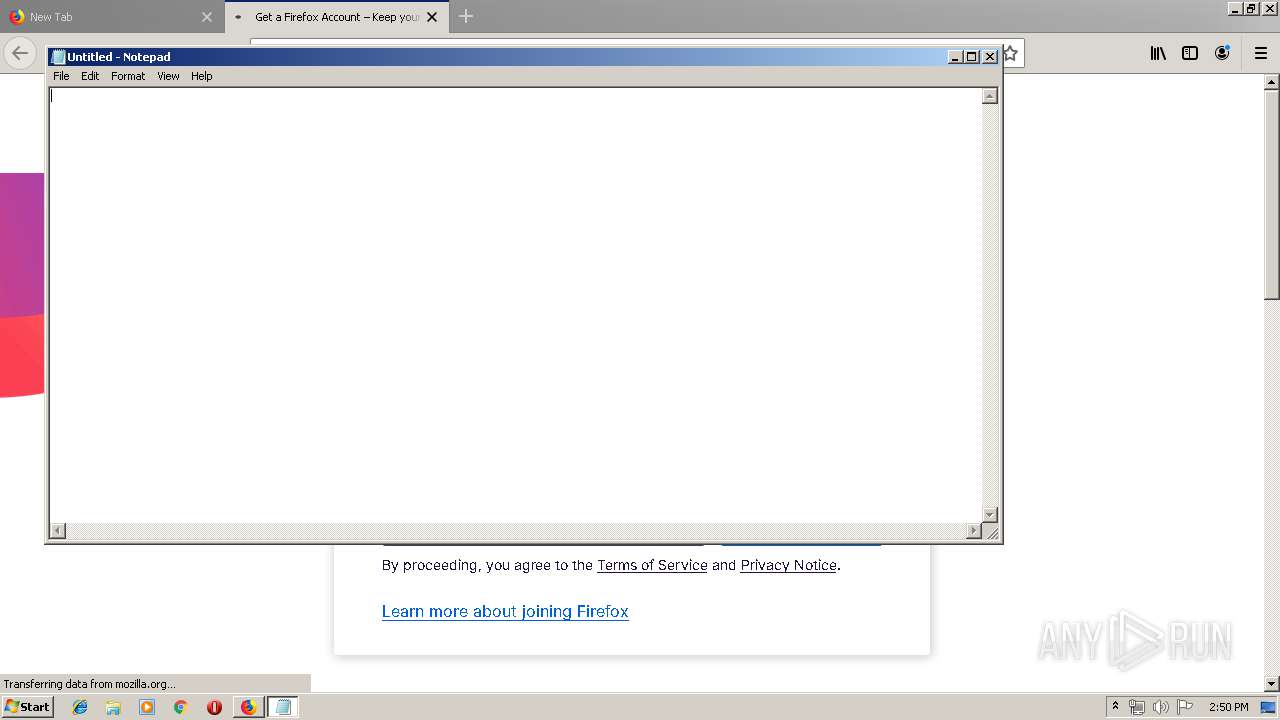
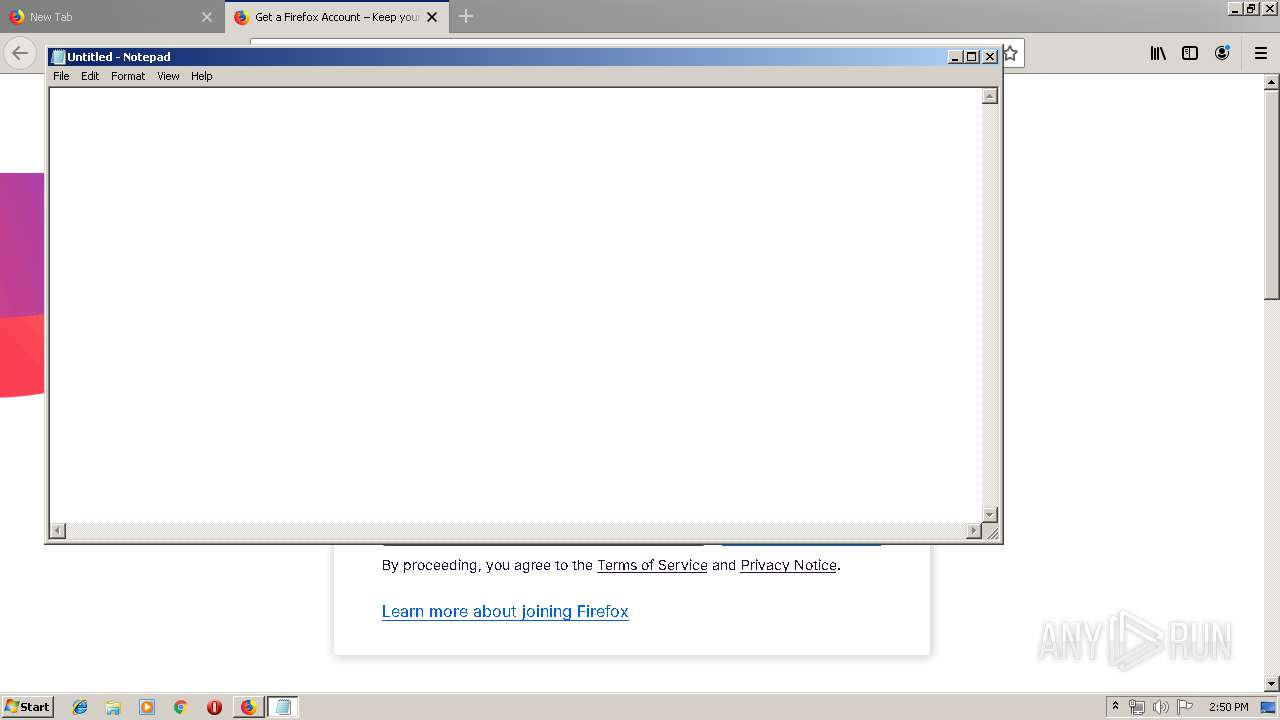
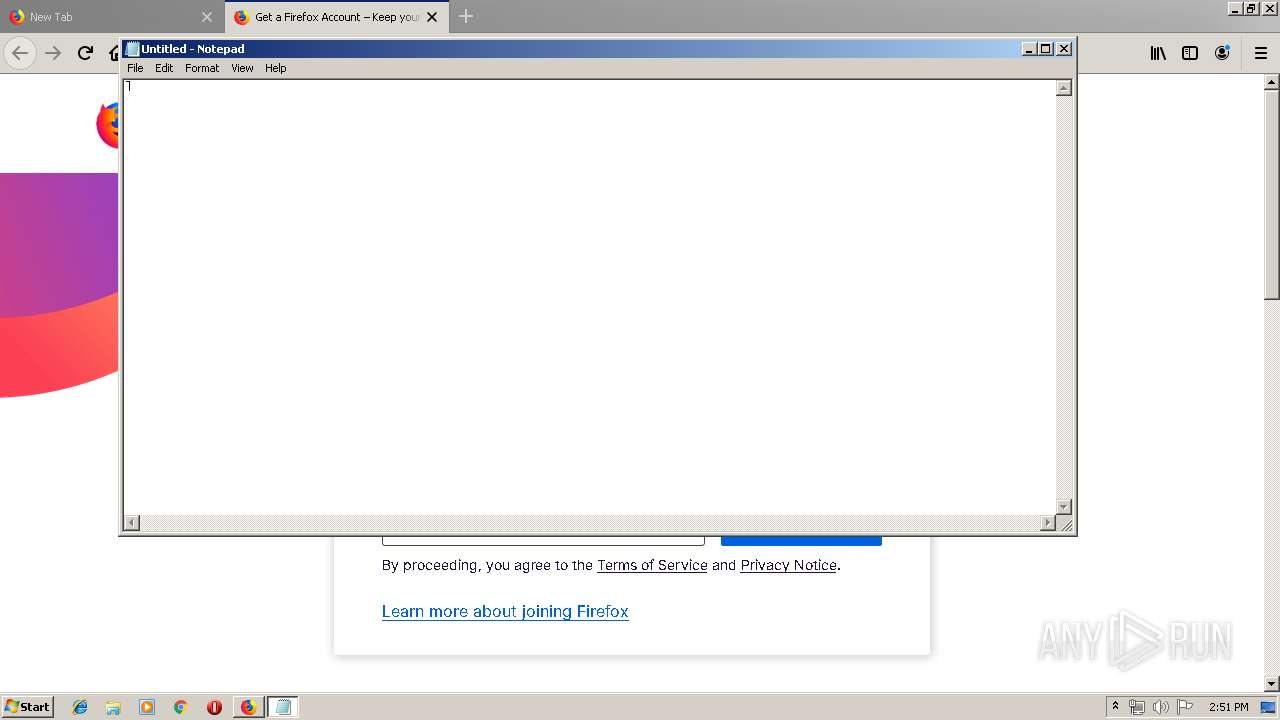
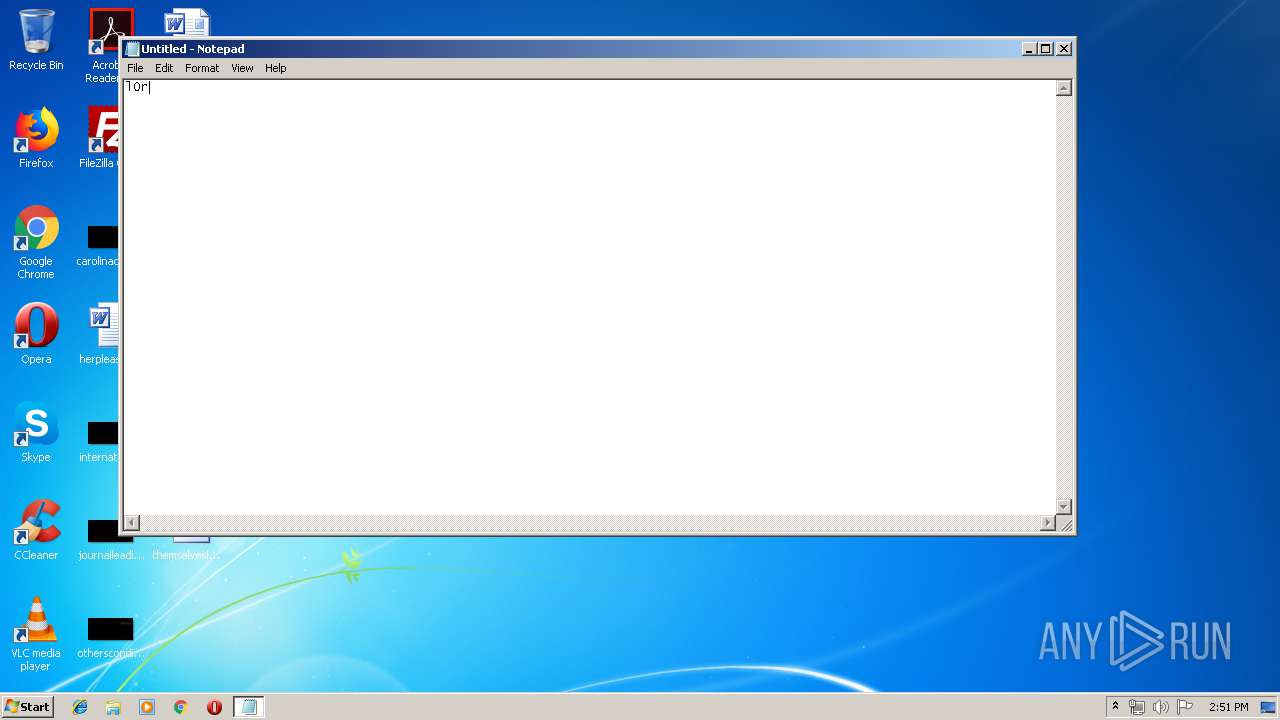
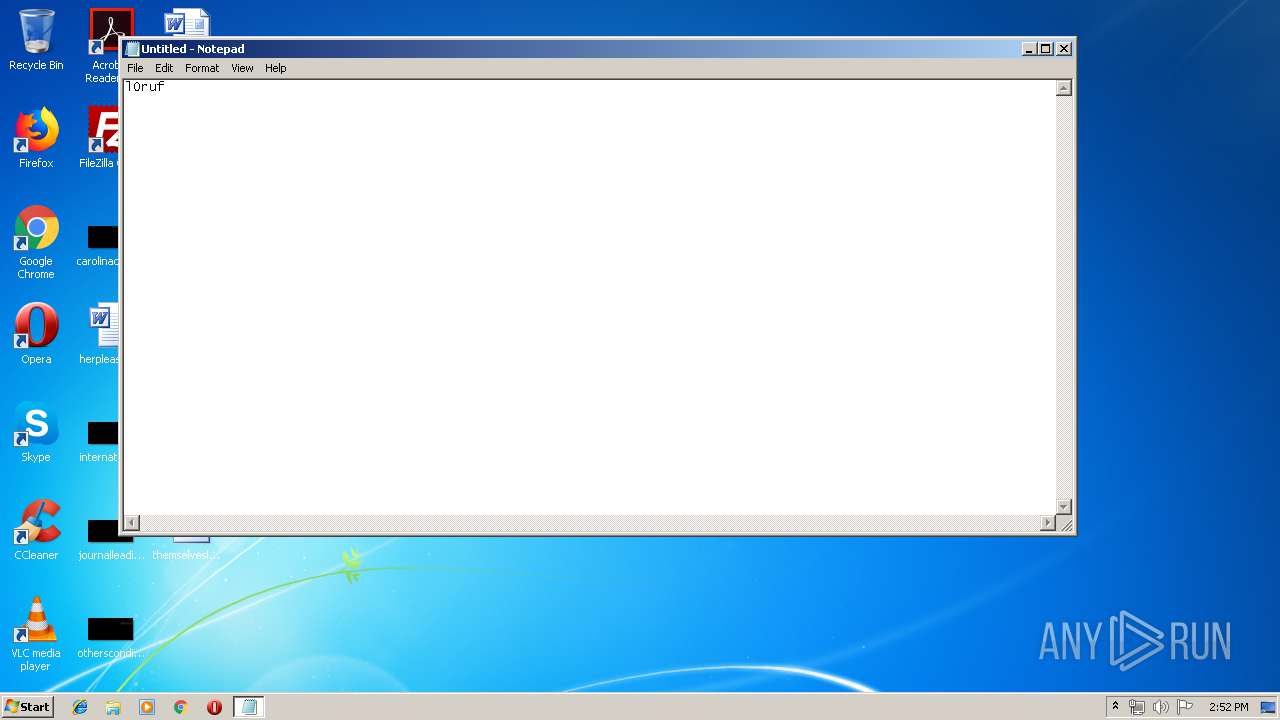
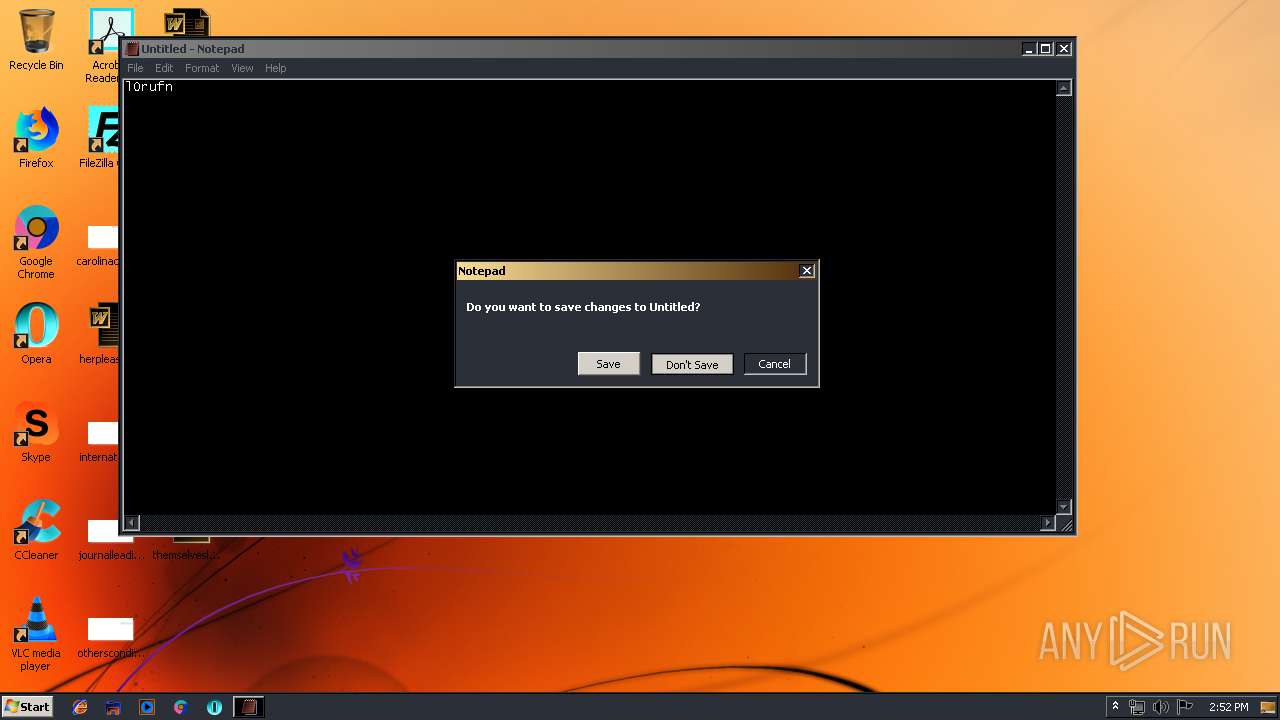
| (PID) Process: | (2528) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 44 | |||
| (PID) Process: | (2528) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 44 | |||
| (PID) Process: | (2528) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2528) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (1020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
149
Suspicious files
151
Text files
212
Unknown types
128
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash22103 | — | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\E0C0CECE28B030D812EB7F970B23FA54B1EF47EF | der | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 1020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\AE256850853CDE9848769115F5EDCCDC4849280C | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
144
DNS requests
127
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1972 | iexplore.exe | GET | 301 | 2.16.106.106:80 | http://play.clubpenguin.com/ | unknown | — | — | whitelisted |
1020 | firefox.exe | GET | — | 104.111.215.142:80 | http://download.cdn.mozilla.net/pub/firefox/releases/67.0.2/update/win32/en-US/firefox-67.0.2.complete.mar | NL | — | — | whitelisted |
1020 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1020 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1972 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
1972 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
1972 | iexplore.exe | GET | 200 | 67.27.234.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
1972 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.2 Kb | whitelisted |
1972 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
1972 | iexplore.exe | GET | 200 | 67.27.233.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1020 | firefox.exe | 54.186.120.41:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4028 | iexplore.exe | 216.58.207.68:80 | google.co.ck | Google Inc. | US | whitelisted |
4028 | iexplore.exe | 172.217.18.163:80 | www.google.co.ck | Google Inc. | US | whitelisted |
3188 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4028 | iexplore.exe | 172.217.18.163:443 | www.google.co.ck | Google Inc. | US | whitelisted |
1020 | firefox.exe | 54.230.102.18:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4028 | iexplore.exe | 172.217.22.78:443 | img.youtube.com | Google Inc. | US | whitelisted |
1020 | firefox.exe | 54.230.102.44:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1032 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1020 | firefox.exe | 35.244.181.201:443 | aus5.mozilla.org | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aus5.mozilla.org |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |