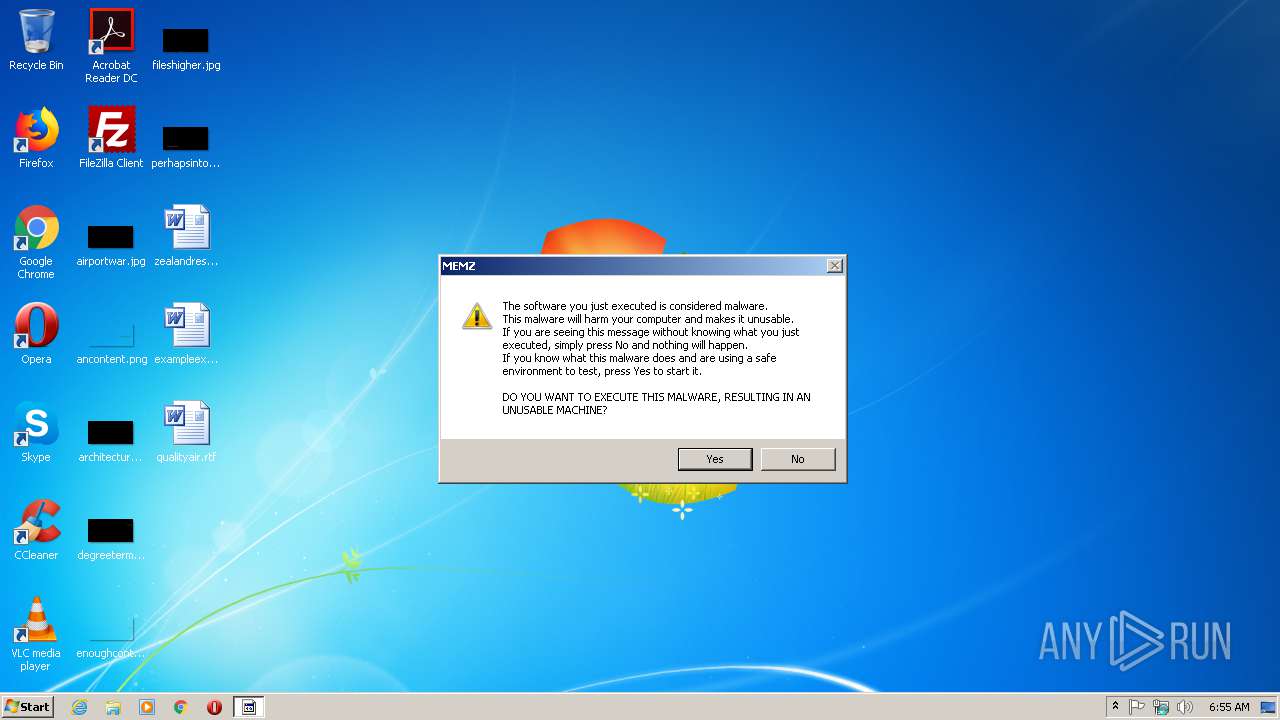
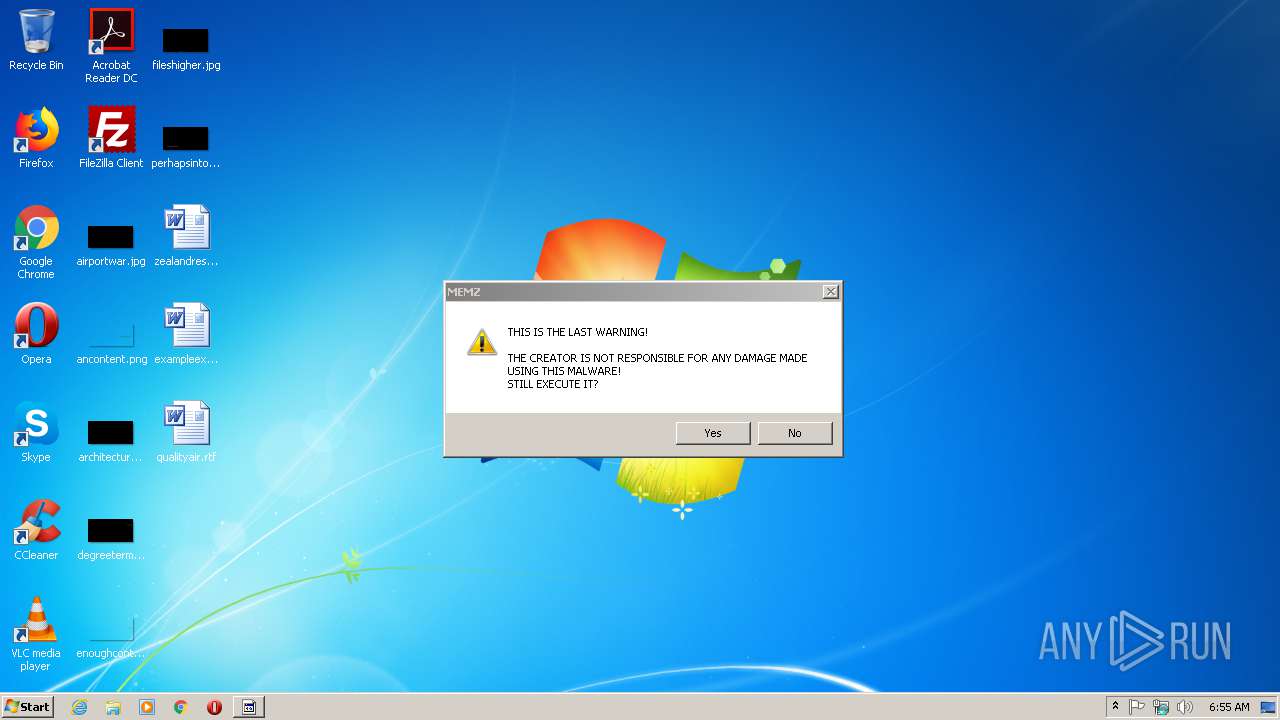
| File name: | MEMZ.exe |
| Full analysis: | https://app.any.run/tasks/3ce48278-960e-46c6-9ee6-ceb9654ddb09 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 05:54:50 |
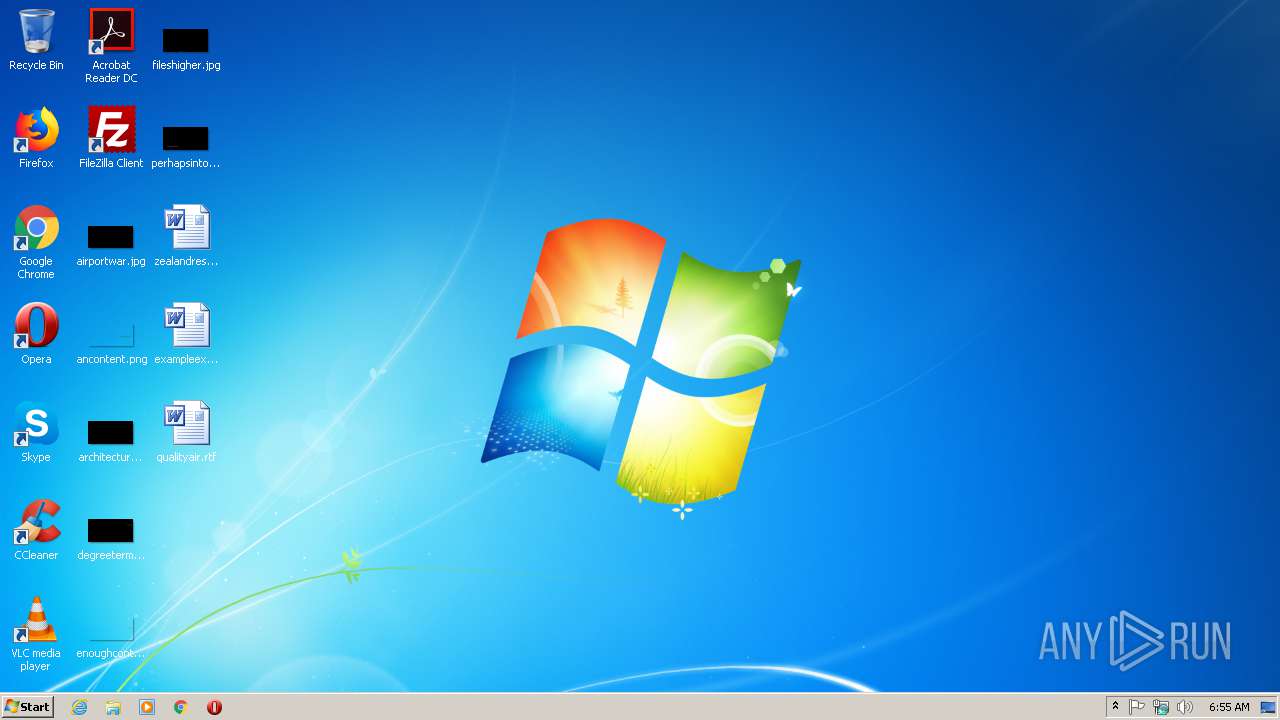
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 19DBEC50735B5F2A72D4199C4E184960 |
| SHA1: | 6FED7732F7CB6F59743795B2AB154A3676F4C822 |
| SHA256: | A3D5715A81F2FBEB5F76C88C9C21EEEE87142909716472F911FF6950C790C24D |
| SSDEEP: | 192:sIvxdXSQeWSg9JJS/lcIEiwqZKBkDFR43xWTM3LHn8f26gyr6yfFCj3r:sMVSaSEglcIqq3agmLc+6gyWqFCj |
MALICIOUS
Low-level write access rights to disk partition
- MEMZ.exe (PID: 3152)
Actions looks like stealing of personal data
- DllHost.exe (PID: 3832)
SUSPICIOUS
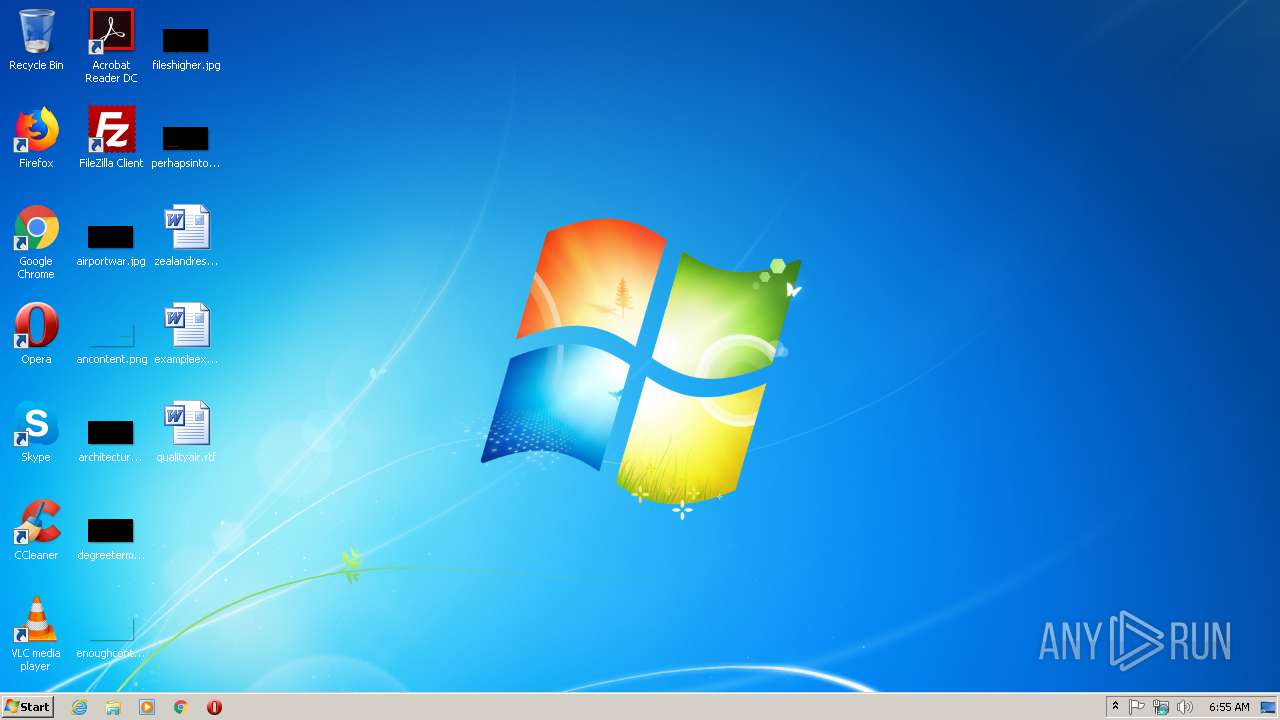
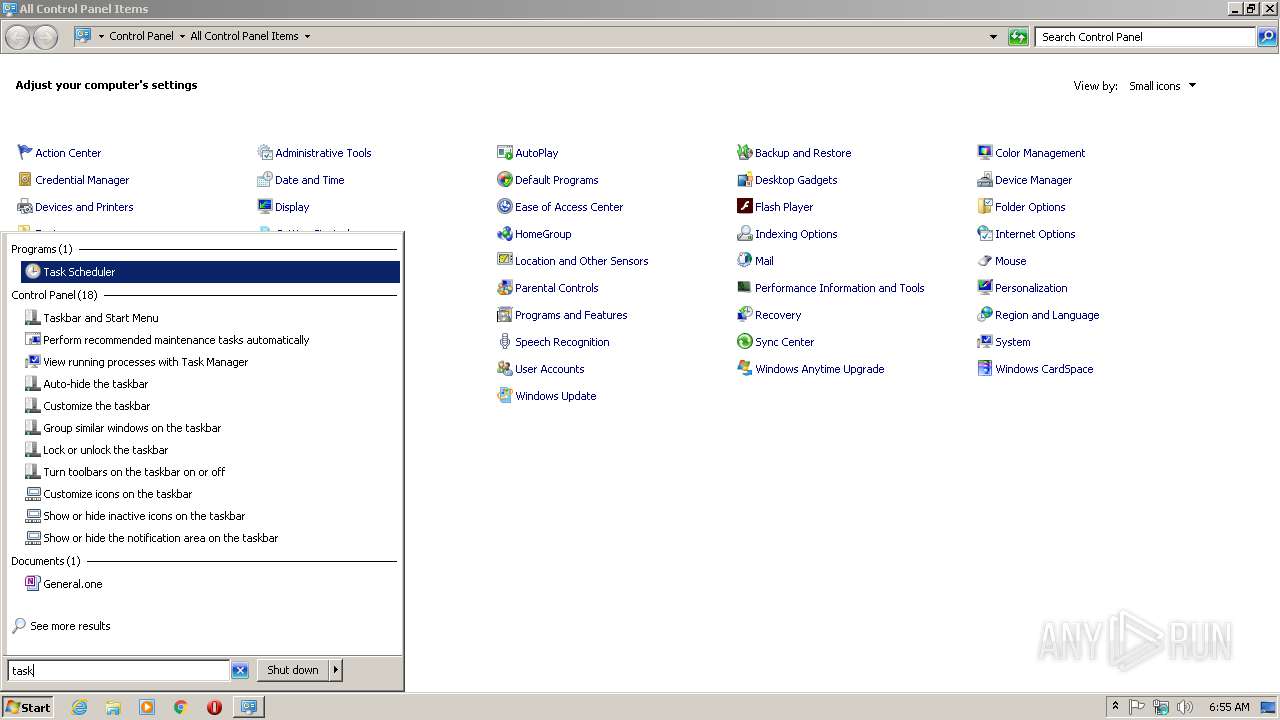
Application launched itself
- MEMZ.exe (PID: 2708)
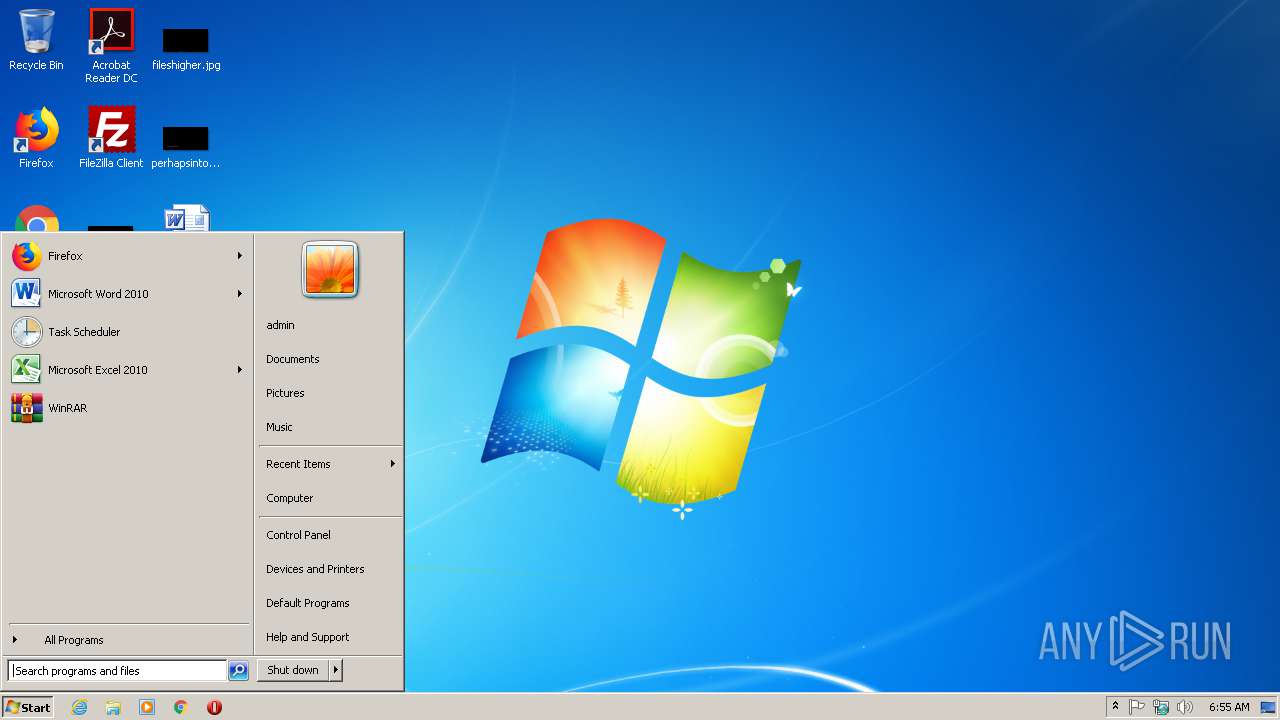
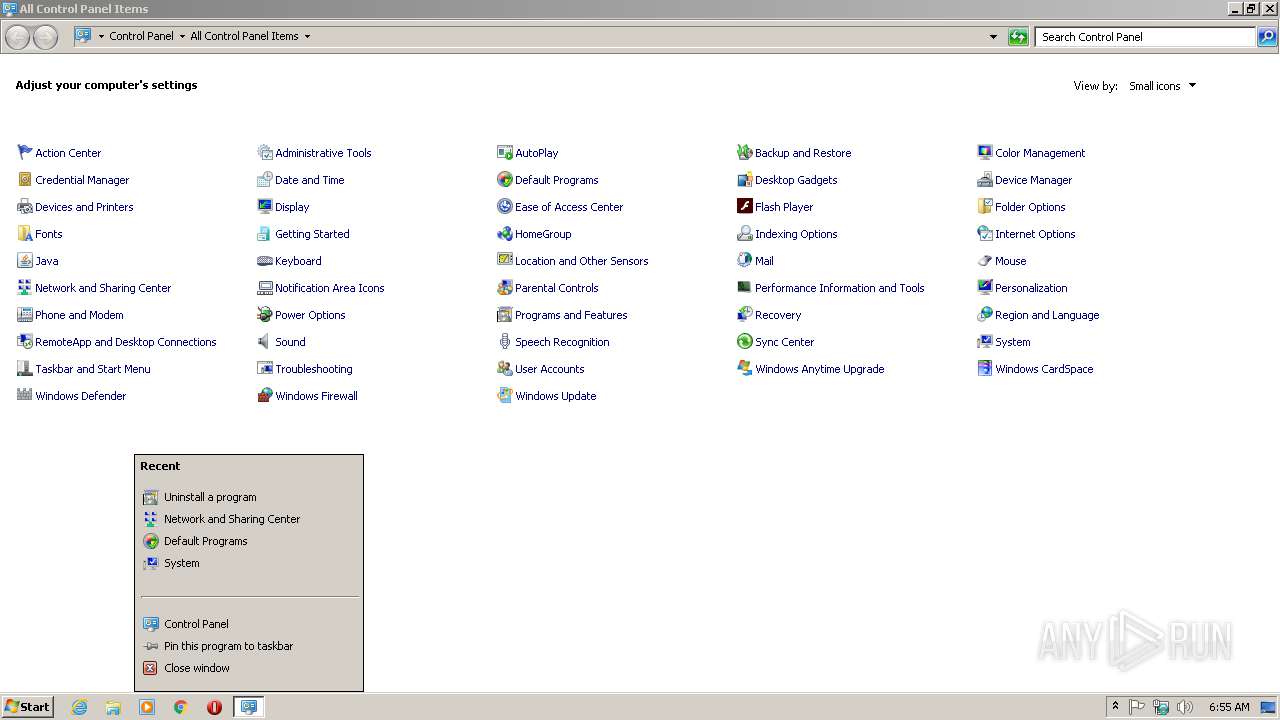
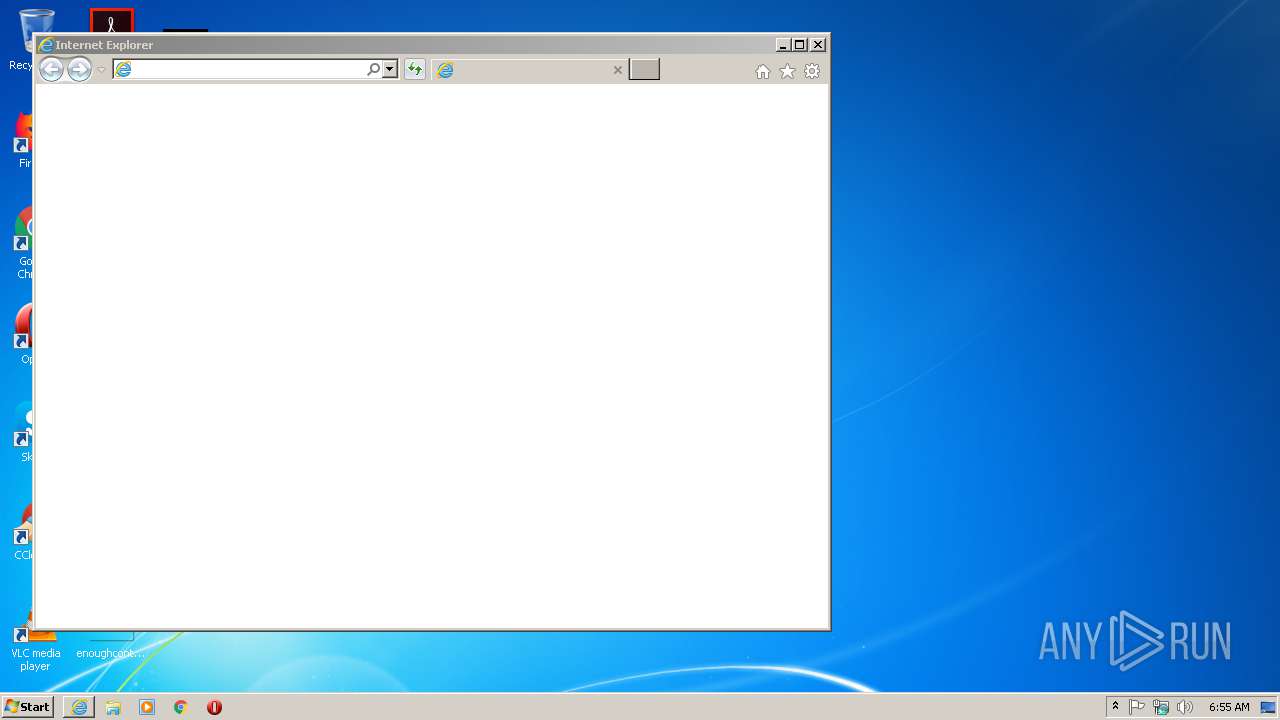
Starts Internet Explorer
- MEMZ.exe (PID: 3152)
Low-level read access rights to disk partition
- MEMZ.exe (PID: 3152)
Executed via COM
- DllHost.exe (PID: 3832)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3284)
Application launched itself
- iexplore.exe (PID: 3284)
Changes internet zones settings
- iexplore.exe (PID: 3284)
Creates files in the user directory
- iexplore.exe (PID: 3892)
Reads settings of System Certificates
- iexplore.exe (PID: 3892)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3892)
Changes settings of System certificates
- iexplore.exe (PID: 3892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:10 14:59:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3072 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jul-2016 12:59:43 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jul-2016 12:59:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000B2A | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85958 |
.rdata | 0x00002000 | 0x000021C2 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35229 |
.data | 0x00005000 | 0x00000194 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5782 |
.rsrc | 0x00006000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75224 |
.reloc | 0x00007000 | 0x0000020C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.99459 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
Total processes
48
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1396 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
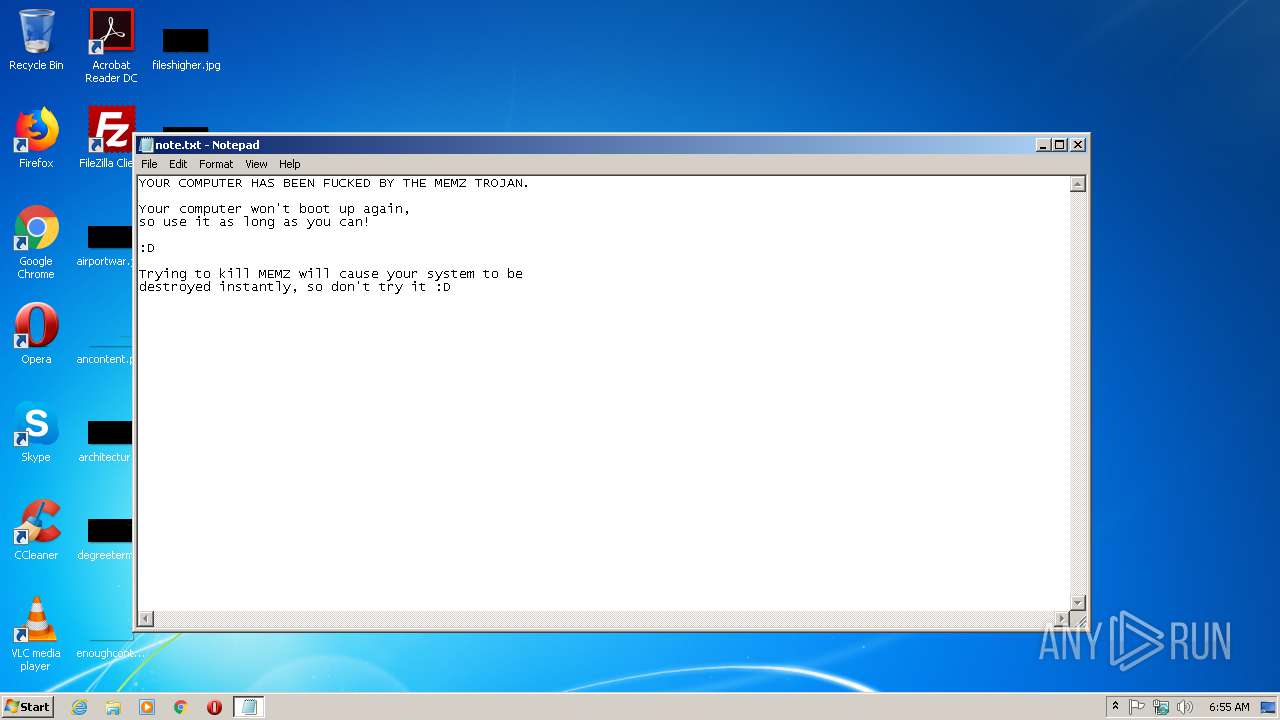
| 2480 | "C:\Windows\System32\notepad.exe" \note.txt | C:\Windows\System32\notepad.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /main | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3284 | "C:\Program Files\Internet Explorer\iexplore.exe" http://google.co.ck/search?q=virus+builder+legit+free+download | C:\Program Files\Internet Explorer\iexplore.exe | MEMZ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 643
Read events
639
Write events
1 000
Delete events
4
Modification events
| (PID) Process: | (2708) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2708) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3152) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3152) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2480) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 132 | |||
| (PID) Process: | (2480) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 133 | |||
| (PID) Process: | (2480) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2480) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 500 | |||
| (PID) Process: | (3152) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000001A521AF74636D601 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 152292510 | |||
Executable files
0
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9F63D990A285EF14.TMP | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF712E2801AAC1BB68.TMP | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF96148F5393D05113.TMP | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\{34D2C9B9-A23A-11EA-B44D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF35DF7E13AA2A026A.TMP | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{34D2C9B7-A23A-11EA-B44D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\IXRZR3PW.txt | text | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\QVDIW2SU.txt | text | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\7JN1SGI7.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | iexplore.exe | GET | 301 | 172.217.22.36:80 | http://google.co.ck/search?q=virus+builder+legit+free+download | US | html | 263 b | whitelisted |
3892 | iexplore.exe | GET | 302 | 216.58.207.67:80 | http://www.google.co.ck/search?q=virus+builder+legit+free+download | US | html | 279 b | whitelisted |
3284 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | iexplore.exe | 172.217.22.36:80 | google.co.ck | Google Inc. | US | whitelisted |
3284 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 216.58.207.67:443 | www.google.co.ck | Google Inc. | US | whitelisted |
3892 | iexplore.exe | 216.58.207.67:80 | www.google.co.ck | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.co.ck |
| whitelisted |
www.google.co.ck |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |