| File name: | Setup.msi |
| Full analysis: | https://app.any.run/tasks/362e82bb-9818-4e21-b69f-49902fb888b9 |
| Verdict: | Malicious activity |
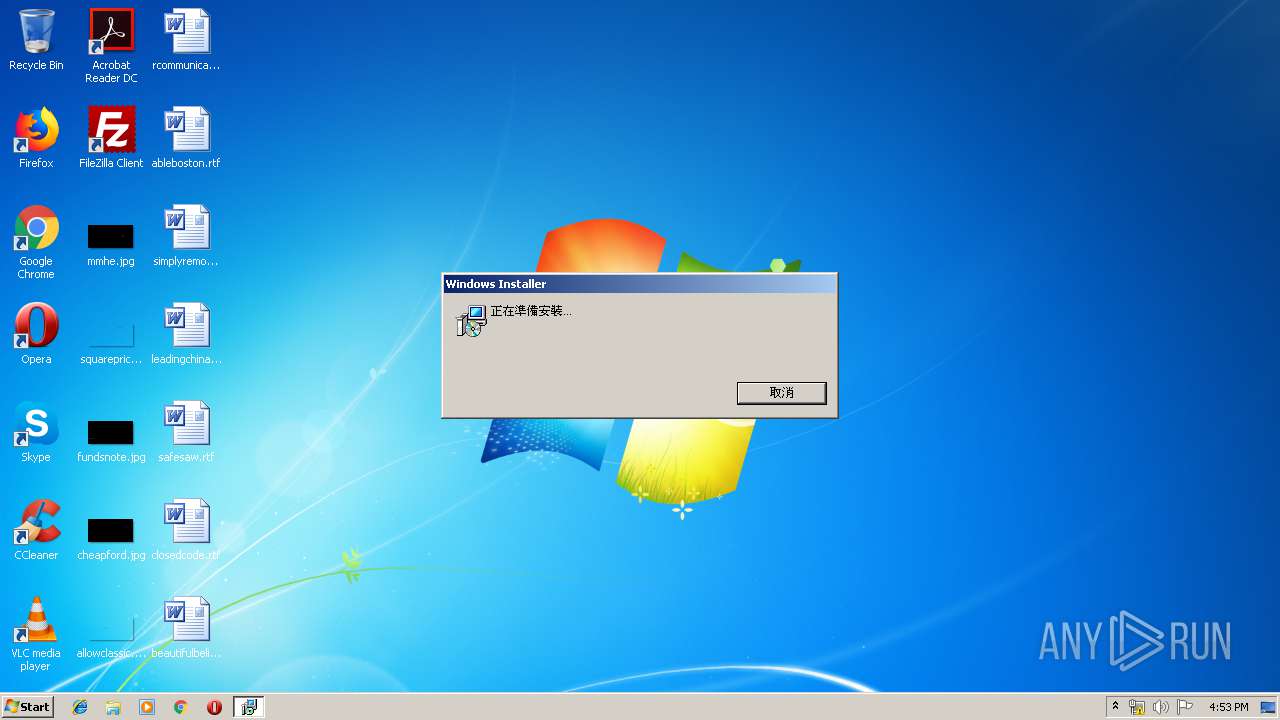
| Analysis date: | June 21, 2019, 15:53:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 950, Template: Intel;1028, Number of Pages: 200, Revision Number: {212EDB98-AD8C-4A85-8536-15A38736438F}, Title: Odw, Subject: Odw, Author: QdOIp, Comments: hsxw, Number of Words: 2, Last Saved Time/Date: Fri Feb 2 07:39:49 2018, Last Printed: Fri Feb 2 07:39:49 2018 |
| MD5: | 1A61454E2CF3A9BD17BAF6906187B2A0 |
| SHA1: | 41421ED1A0FF2D2052326B3FB1881EF4B7D171BC |
| SHA256: | A3C5FC11BE448AAB60B78F346172F2501DDF134740E3D85AF35B76550DF7471D |
| SSDEEP: | 49152:h/RBbyzzuU8elc6mz36kl4VYf3VOci3fuyvU4koD5QPogv0ulxCR8E7CHB/zqh4Y:oRc6mzq5U3G32SkDogMulI8pZt94Q1Q |
MALICIOUS
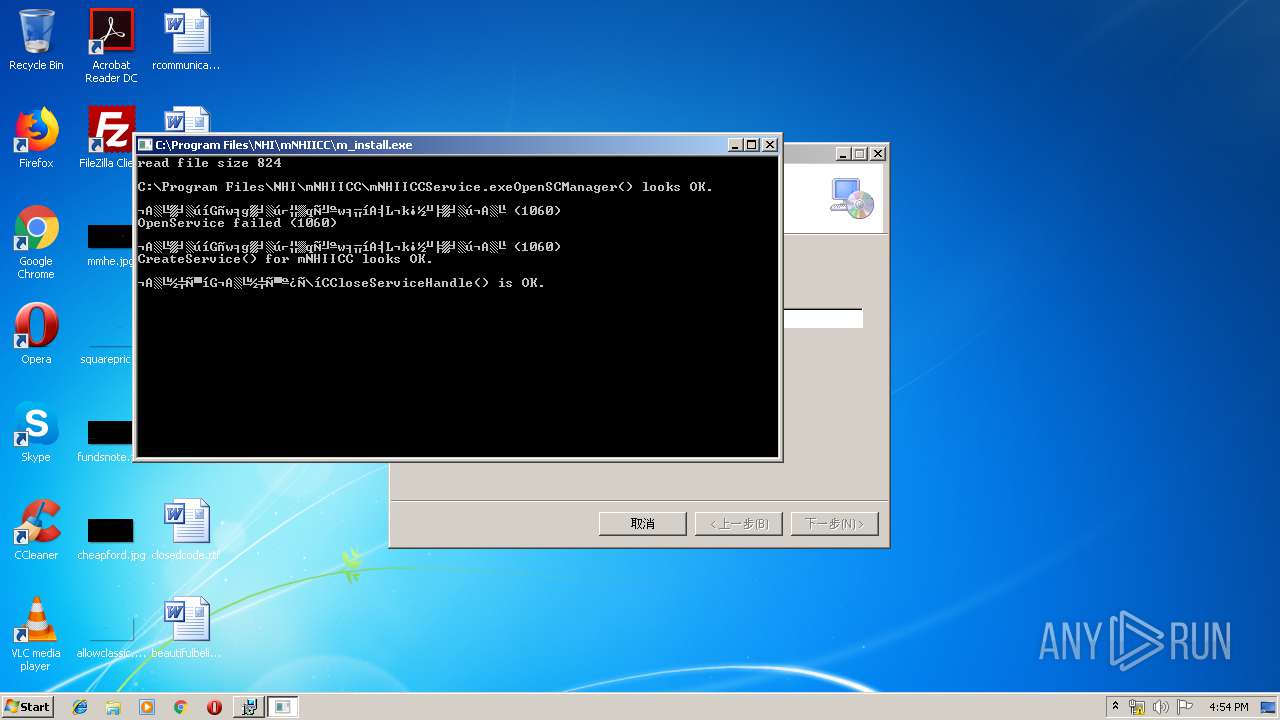
Application was dropped or rewritten from another process
- mNHIICCService.exe (PID: 3940)
- m_install.exe (PID: 3516)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3576)
- mNHIICCService.exe (PID: 3940)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 3720)
- mNHIICCService.exe (PID: 3940)
Creates files in the Windows directory
- msiexec.exe (PID: 1792)
- m_install.exe (PID: 3516)
- mNHIICCService.exe (PID: 3940)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1792)
Creates files in the user directory
- msiexec.exe (PID: 1792)
Executed via COM
- DrvInst.exe (PID: 996)
Creates COM task schedule object
- MsiExec.exe (PID: 3576)
Creates files in the driver directory
- m_install.exe (PID: 3516)
INFO
Searches for installed software
- msiexec.exe (PID: 1792)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3720)
Changes settings of System certificates
- DrvInst.exe (PID: 996)
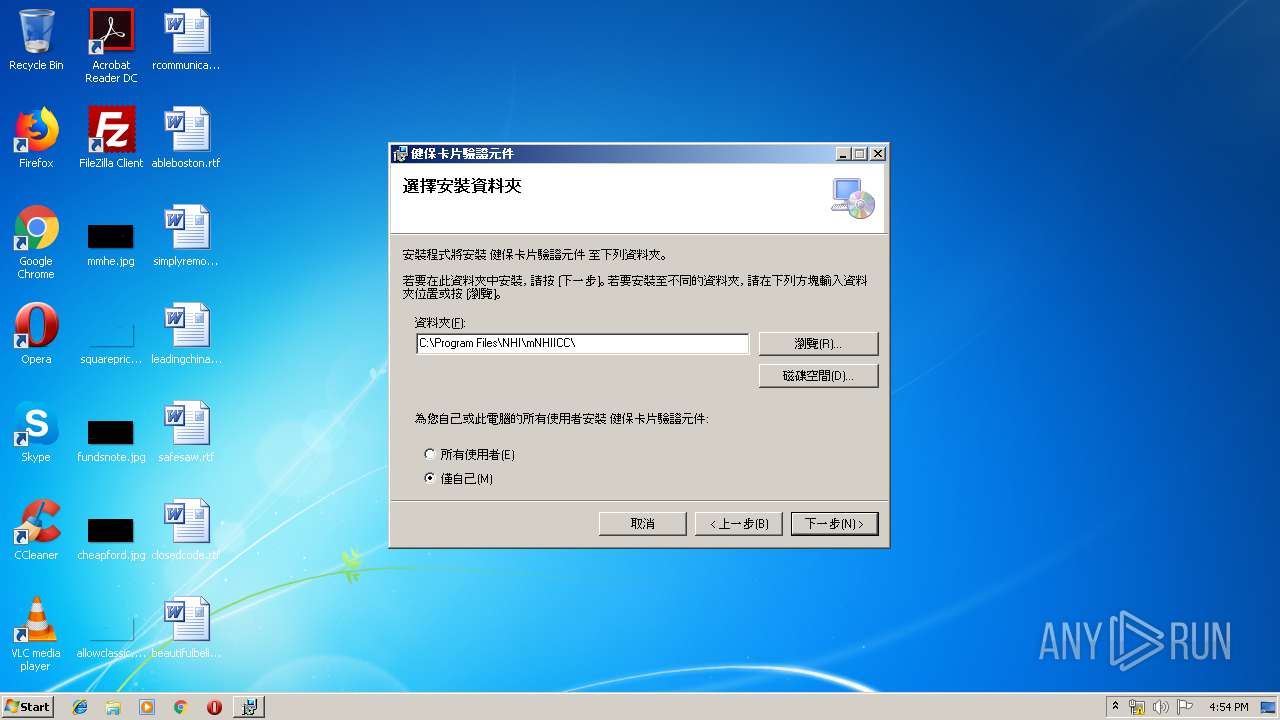
Creates files in the program directory
- msiexec.exe (PID: 1792)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 996)
Application launched itself
- msiexec.exe (PID: 1792)
Creates a software uninstall entry
- msiexec.exe (PID: 1792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
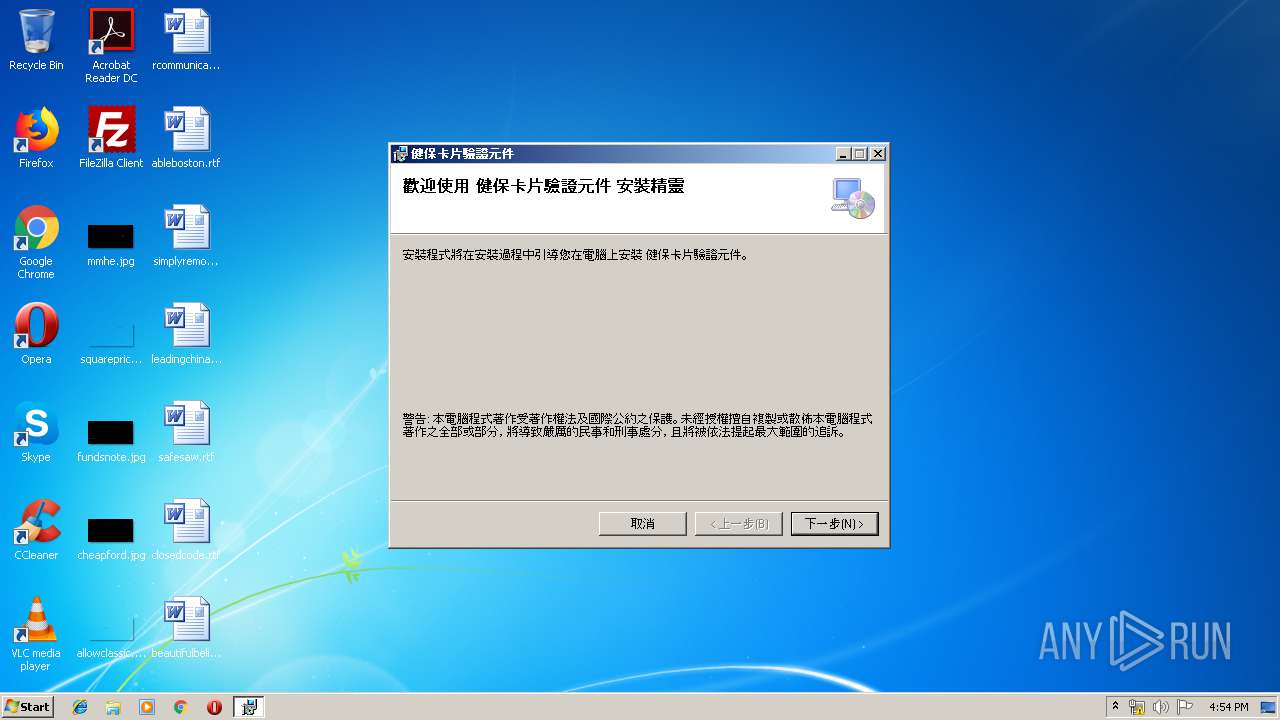
| CodePage: | Windows Traditional Chinese (Taiwan) |
| Template: | Intel;1028 |
| Pages: | 200 |
| RevisionNumber: | {212EDB98-AD8C-4A85-8536-15A38736438F} |
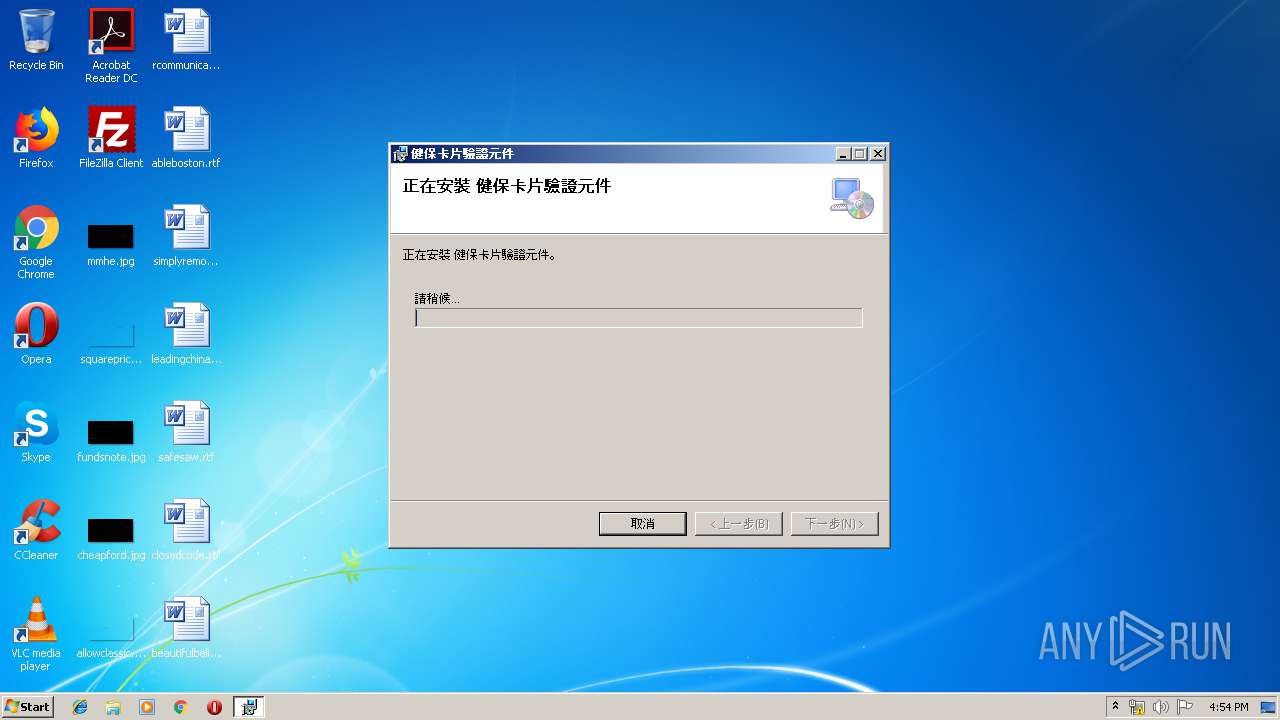
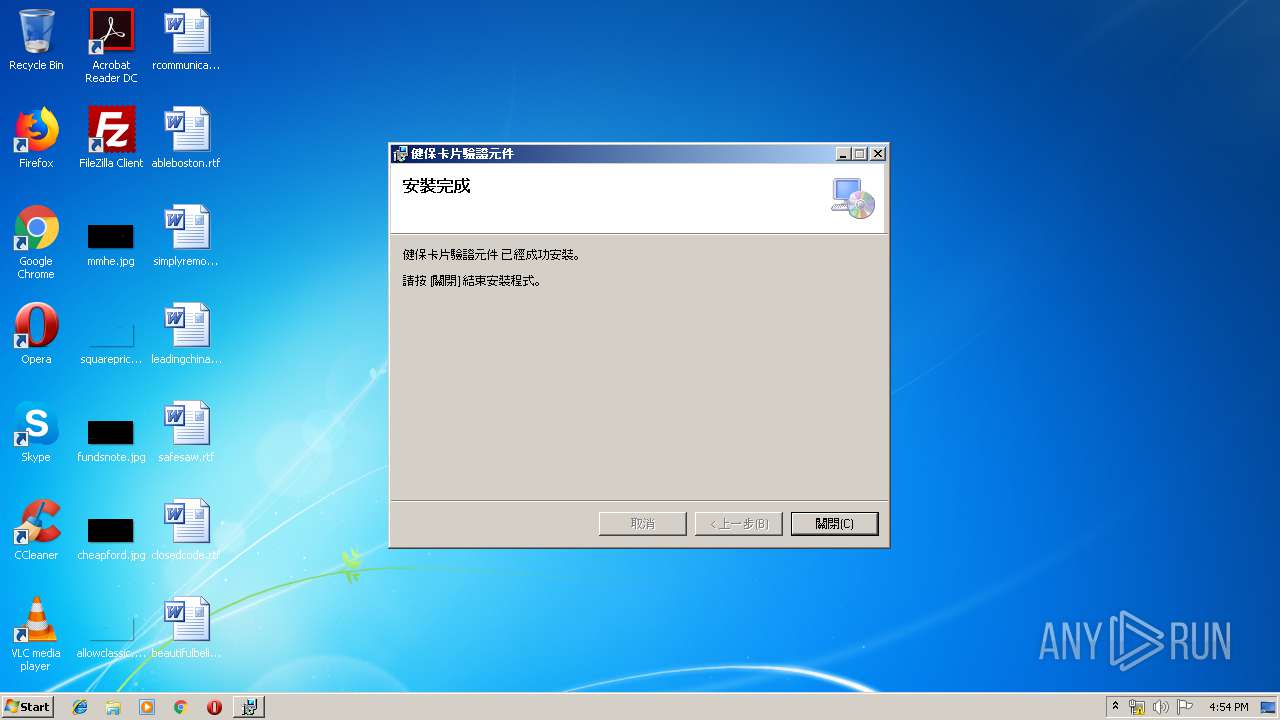
| Title: | ???O?d?????Ҧw???? |
| Subject: | ???O?d?????Ҧw???? |
| Author: | ?åͺ֧Q?????????d?O?I?p |
| Keywords: | - |
| Comments: | ?h???s???????x?w???? |
| Words: | 2 |
| ModifyDate: | 2018:02:02 07:39:49 |
| LastPrinted: | 2018:02:02 07:39:49 |
Total processes
40
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000560" "000004C0" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Setup.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | "C:\Program Files\NHI\mNHIICC\m_install.exe" /Install | C:\Program Files\NHI\mNHIICC\m_install.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3576 | "C:\Windows\system32\MsiExec.exe" /Y "C:\Windows\system32\NHIICC.dll" | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | "C:\Program Files\NHI\mNHIICC\mNHIICCService.exe" | C:\Program Files\NHI\mNHIICC\mNHIICCService.exe | services.exe | ||||||||||||
User: SYSTEM Company: 衛生福利部中央健康保險署 Integrity Level: SYSTEM Description: mNHIICC Service Exit code: 0 Version: 1.0.0.2 Modules
| |||||||||||||||
Total events
602
Read events
321
Write events
265
Delete events
16
Modification events
| (PID) Process: | (1792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000348C17944928D50100070000240A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000348C17944928D50100070000240A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (1792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000BA9A87944928D50100070000240A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1792) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000014FD89944928D5010007000058080000E80300000100000000000000000000009349717975E8FC4DAE487EA5A02D64E60000000000000000 | |||
| (PID) Process: | (3720) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000304B98944928D501880E0000A80B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3720) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000304B98944928D501880E0000D0090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3720) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000304B98944928D501880E0000F4030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3720) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000304B98944928D501880E0000AC090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3720) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000004C99A6944928D501880E0000D0090000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
6
Text files
128
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1792 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1792 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF2D1DD885FC36200E.TMP | — | |
MD5:— | SHA256:— | |||
| 3720 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1792 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{79714993-e875-4dfc-ae48-7ea5a02d64e6}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 1792 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 1792 | msiexec.exe | C:\Config.Msi\128a1a.rbs | — | |
MD5:— | SHA256:— | |||
| 1792 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFD6FC16024E195C0E.TMP | — | |
MD5:— | SHA256:— | |||
| 996 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 996 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 996 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3940 | mNHIICCService.exe | 210.69.214.206:443 | cloudicap.nhi.gov.tw | Data Communication Business Group | TW | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cloudicap.nhi.gov.tw |
| whitelisted |