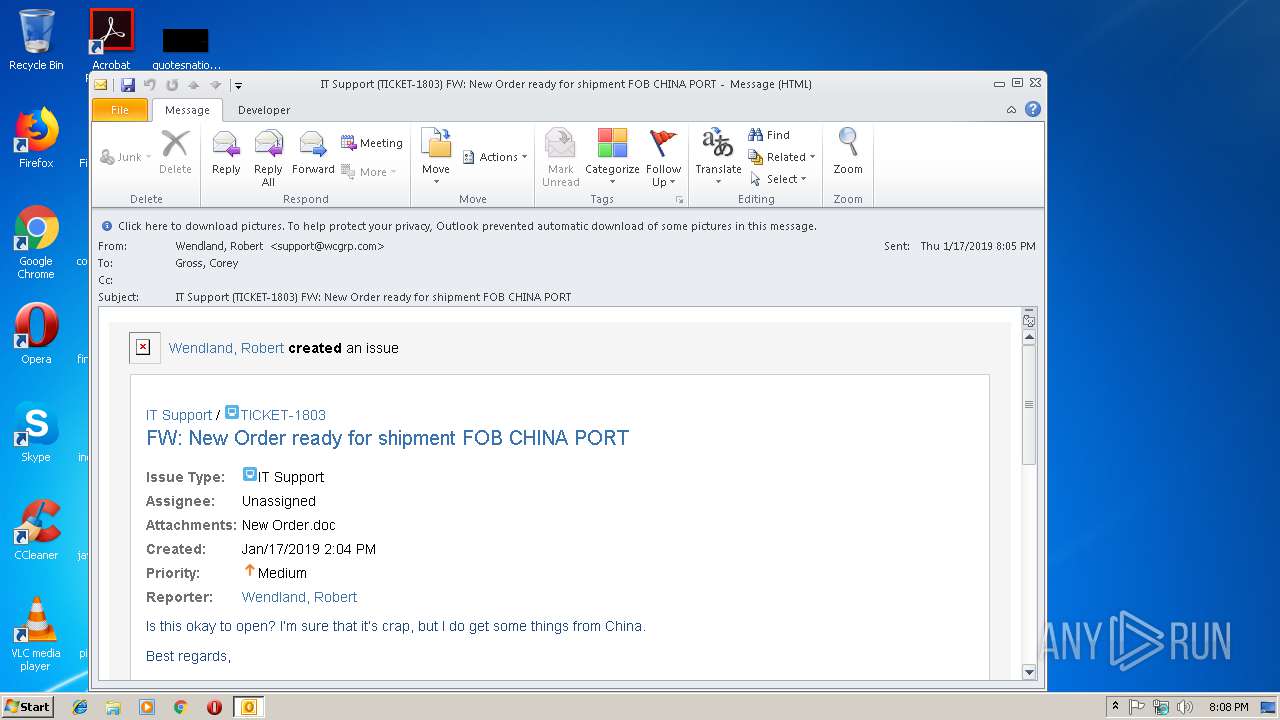
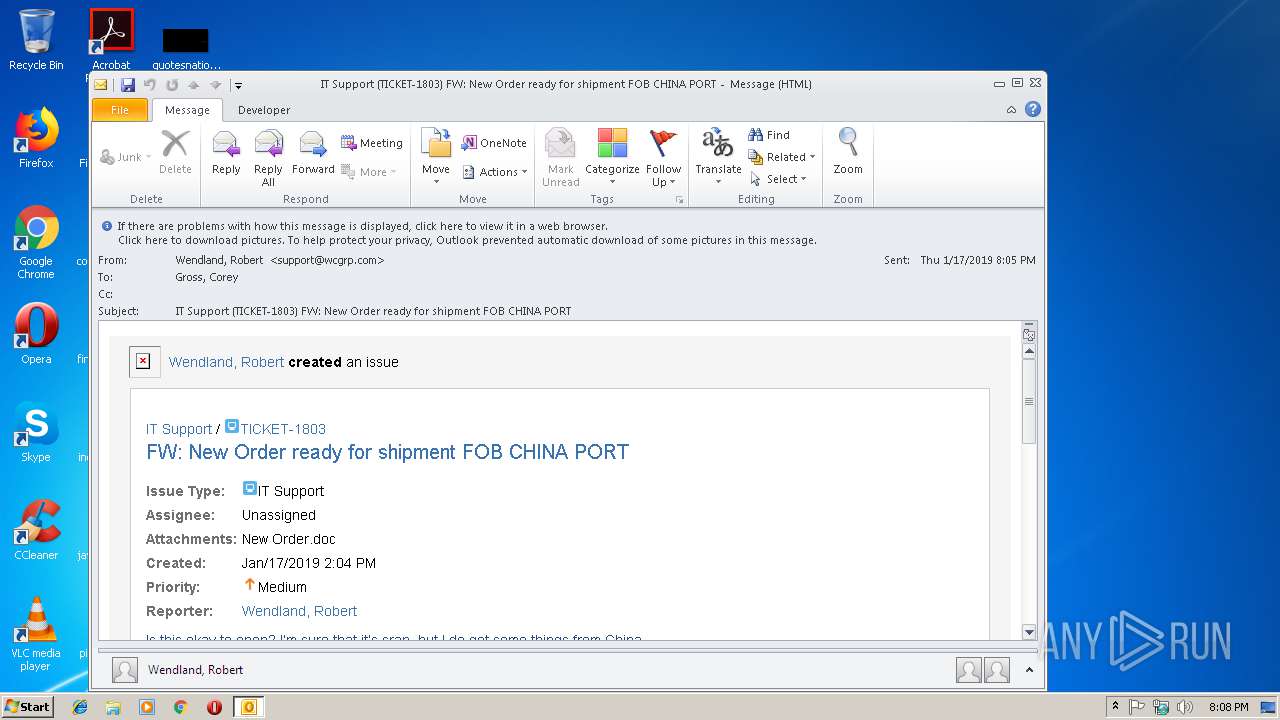
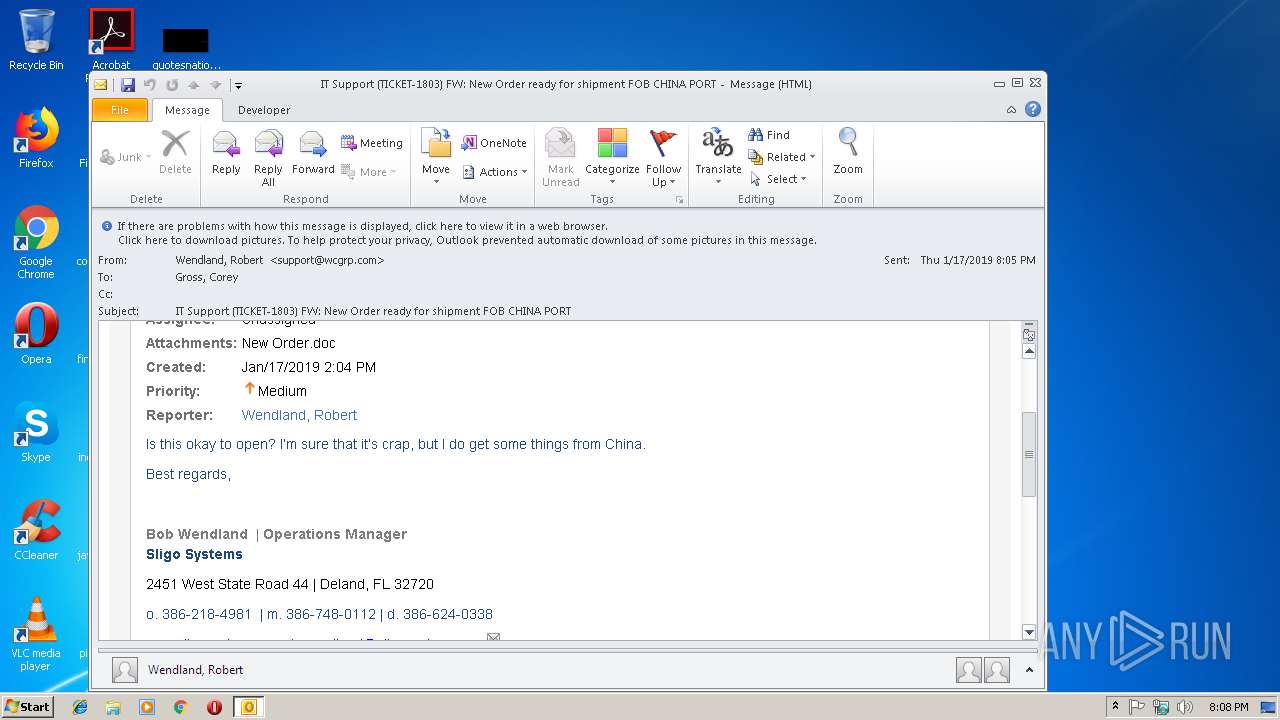
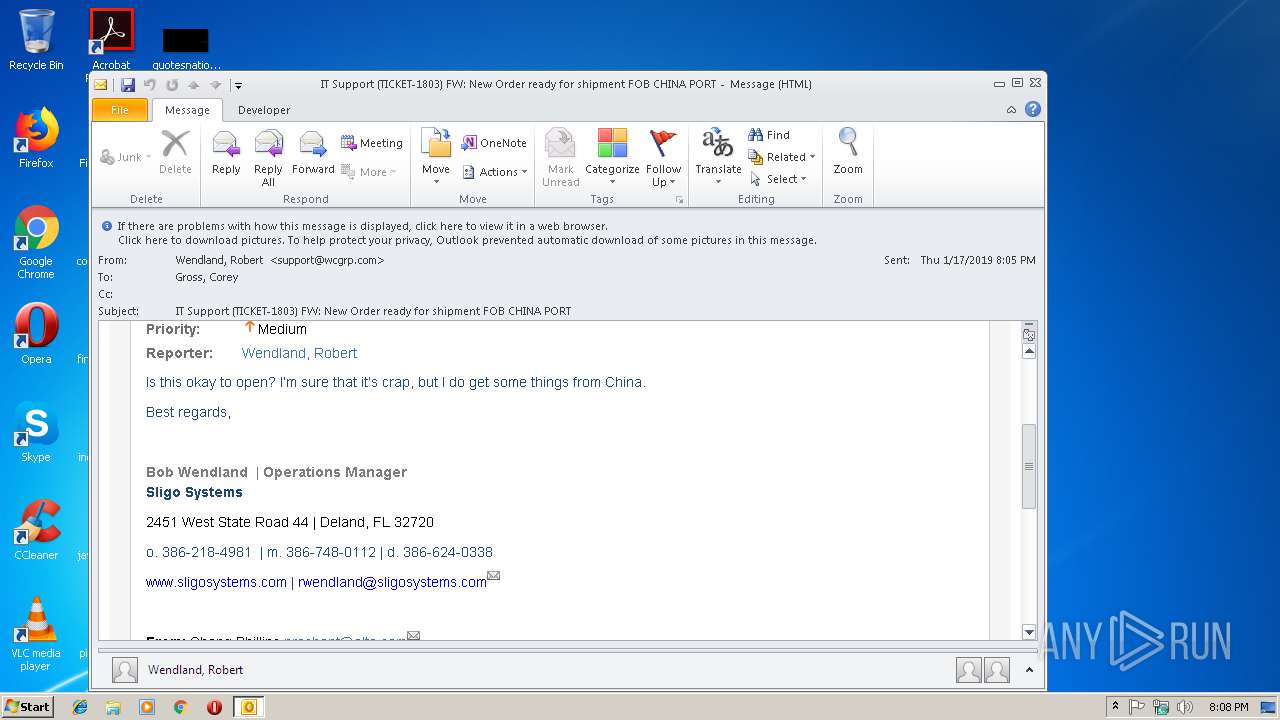
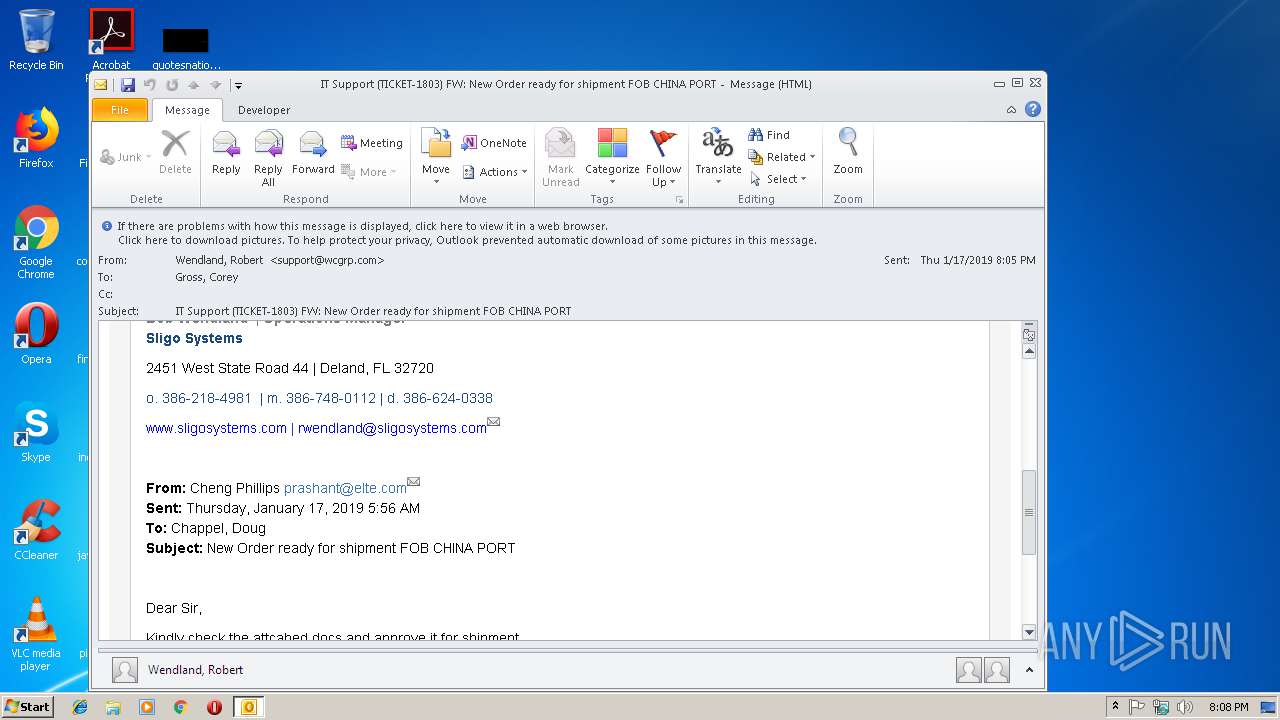
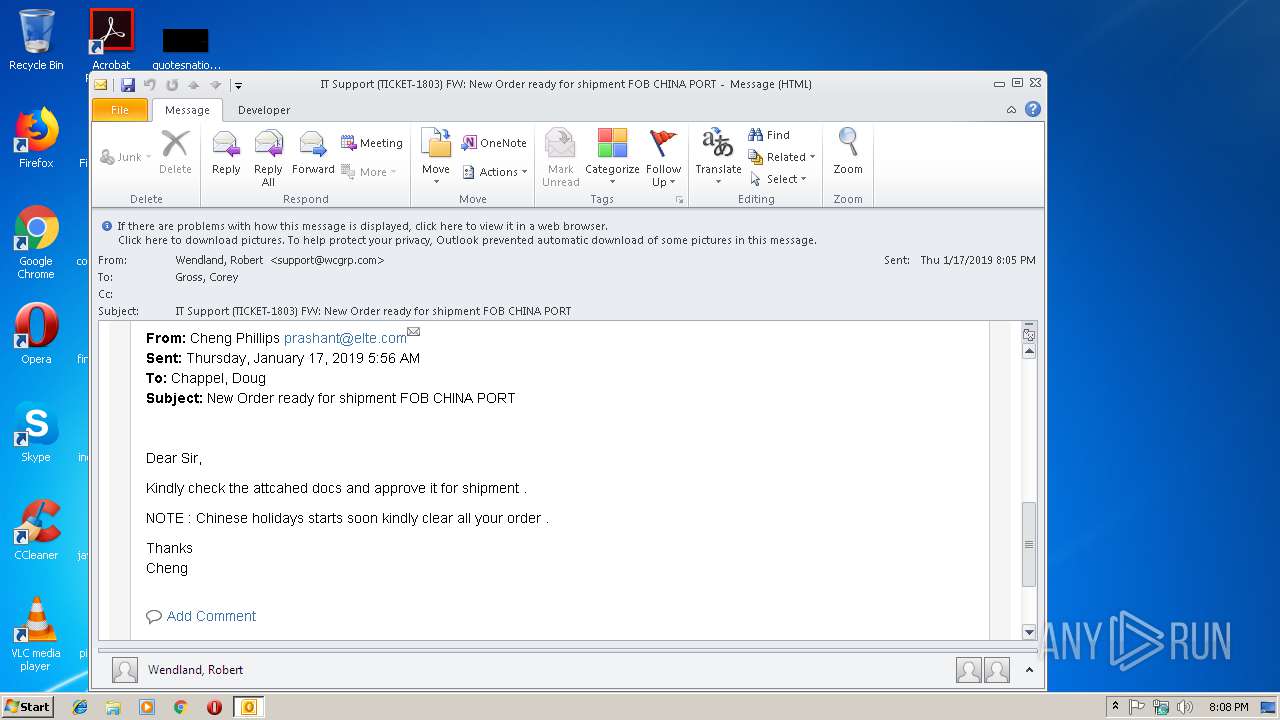
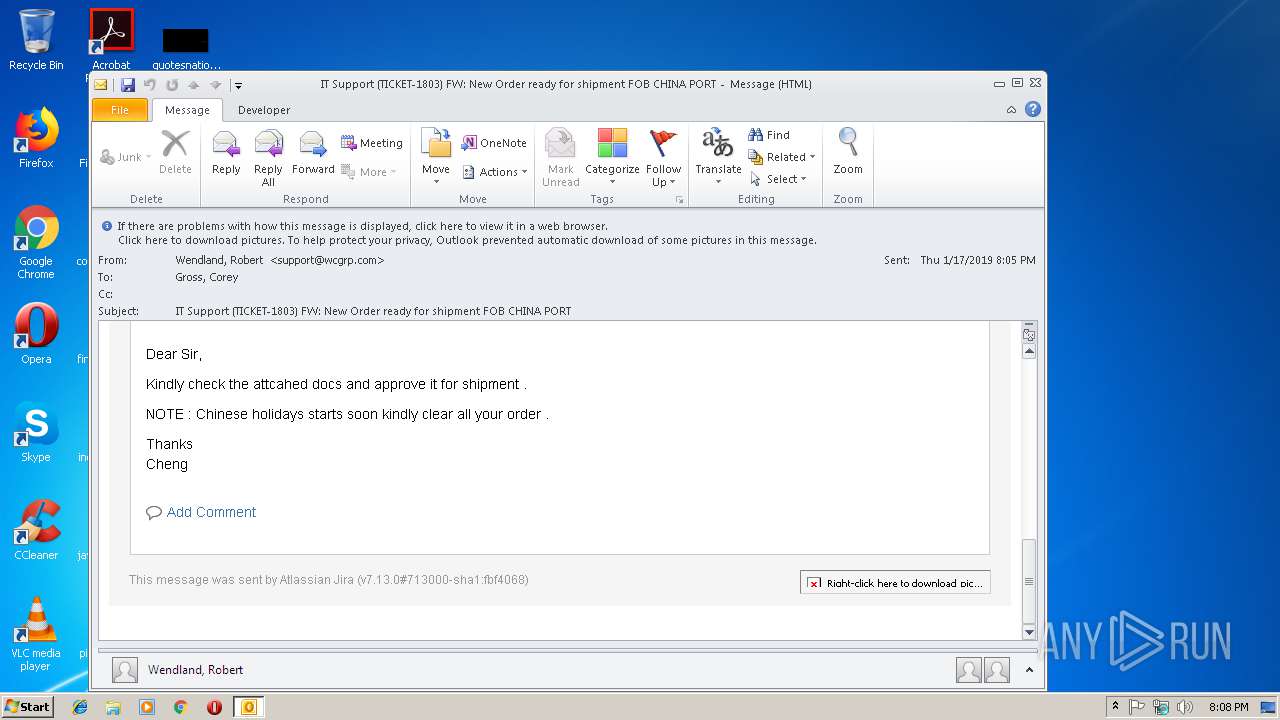
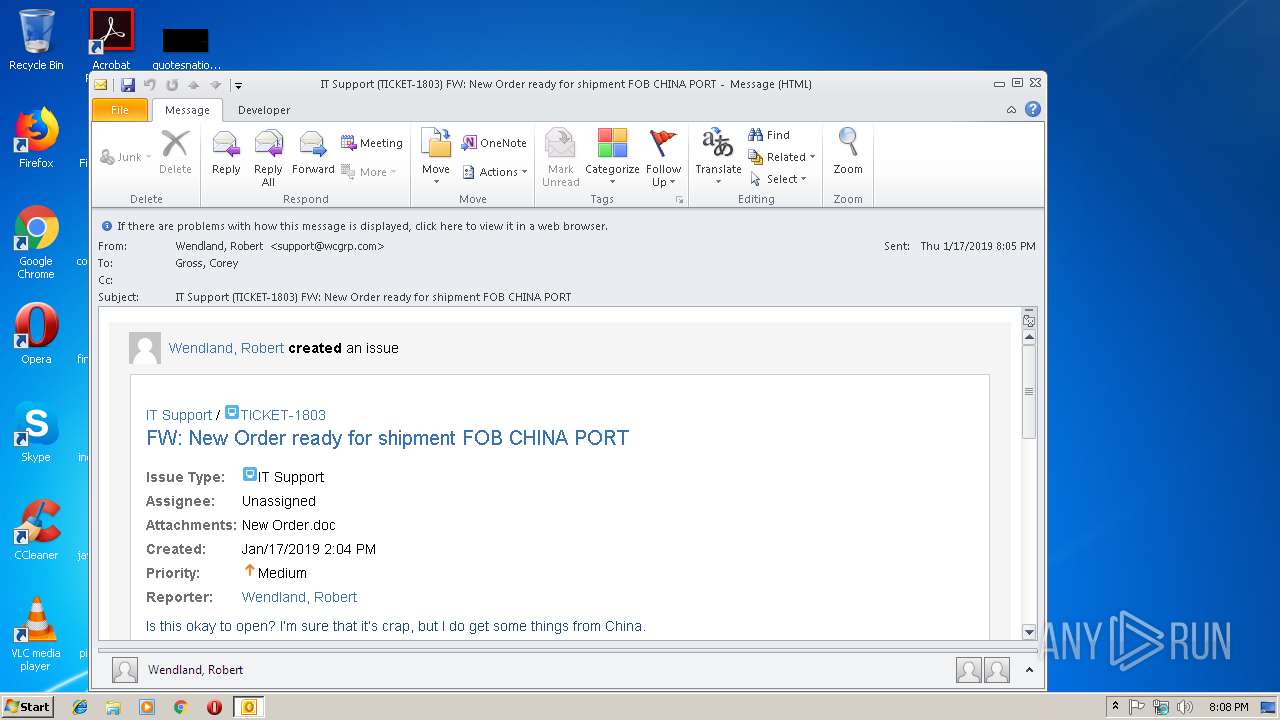
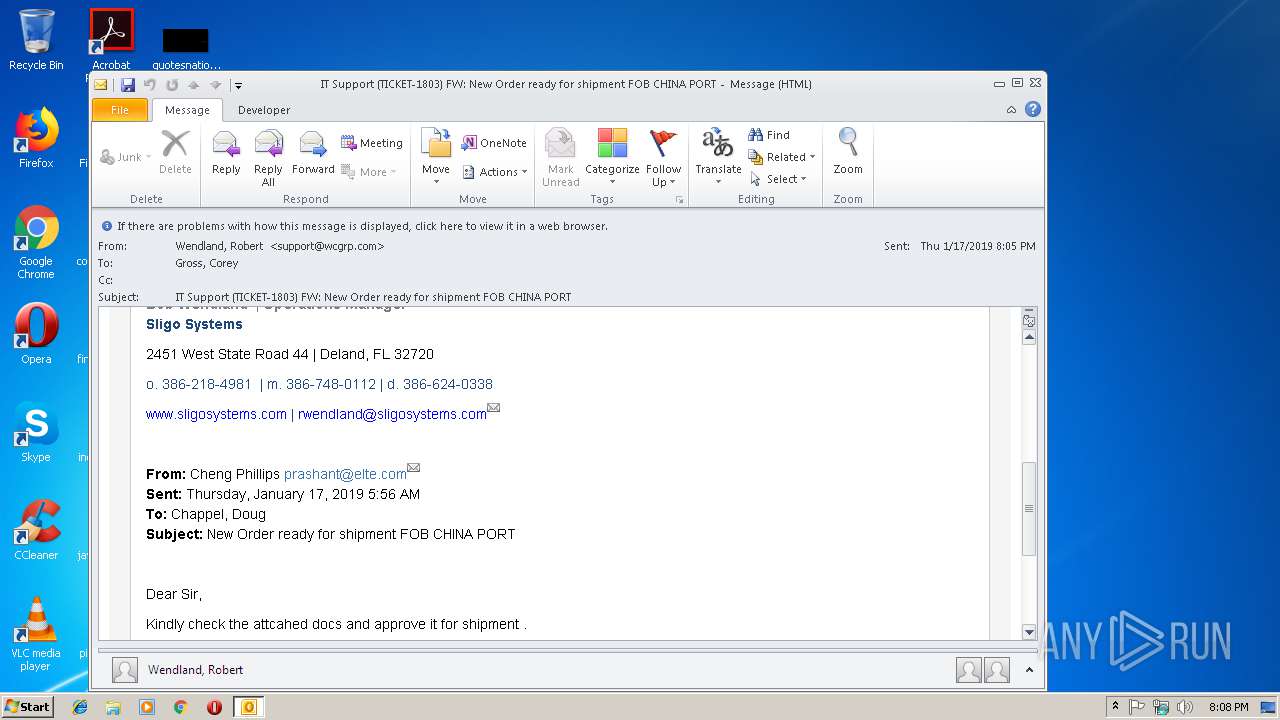
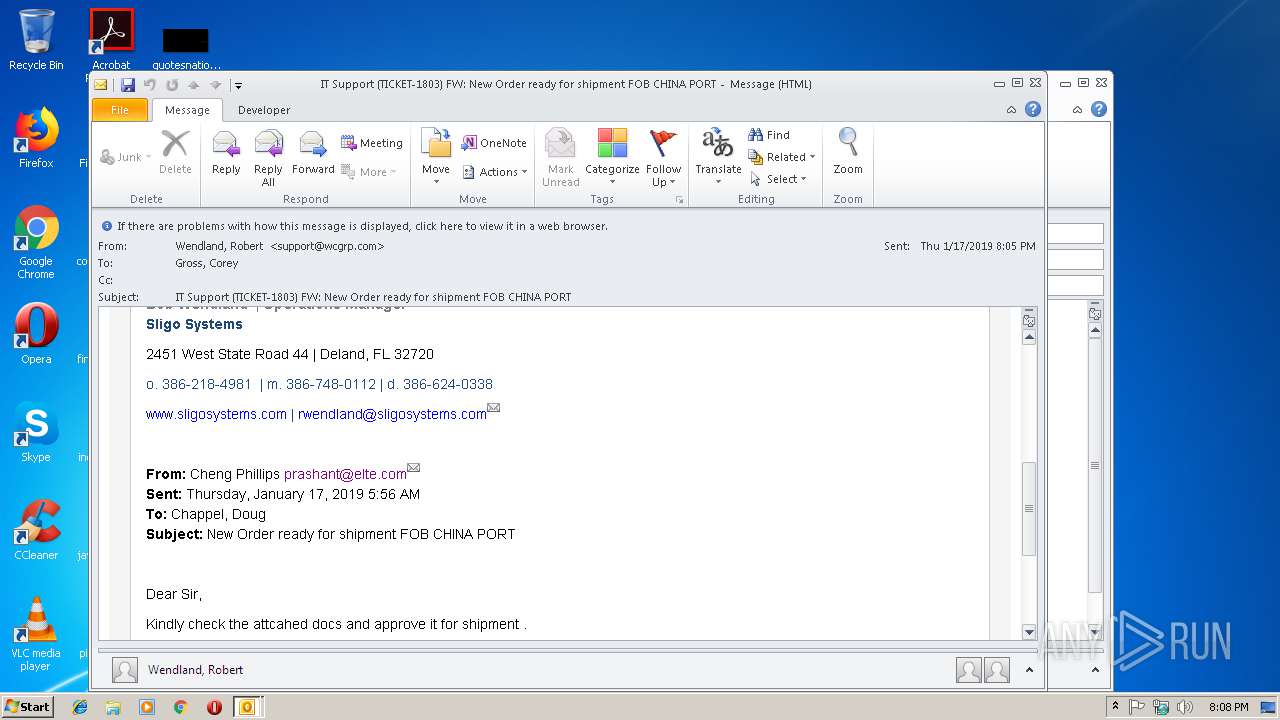
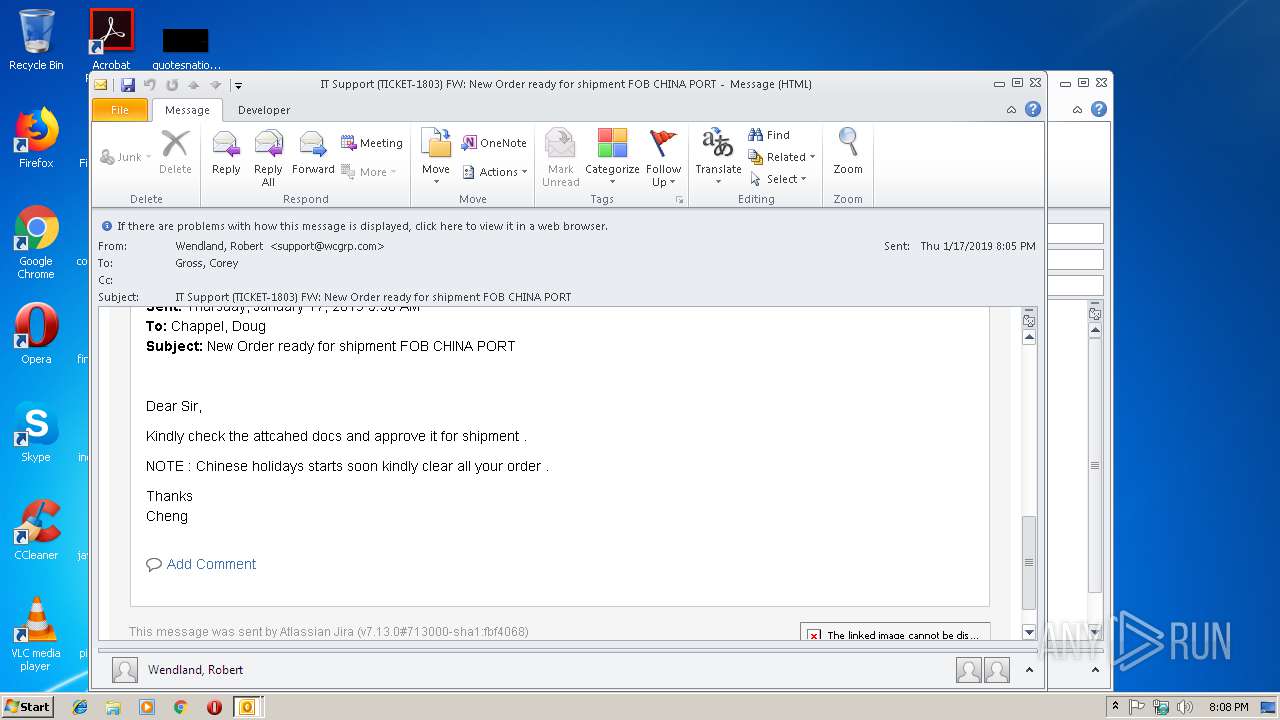
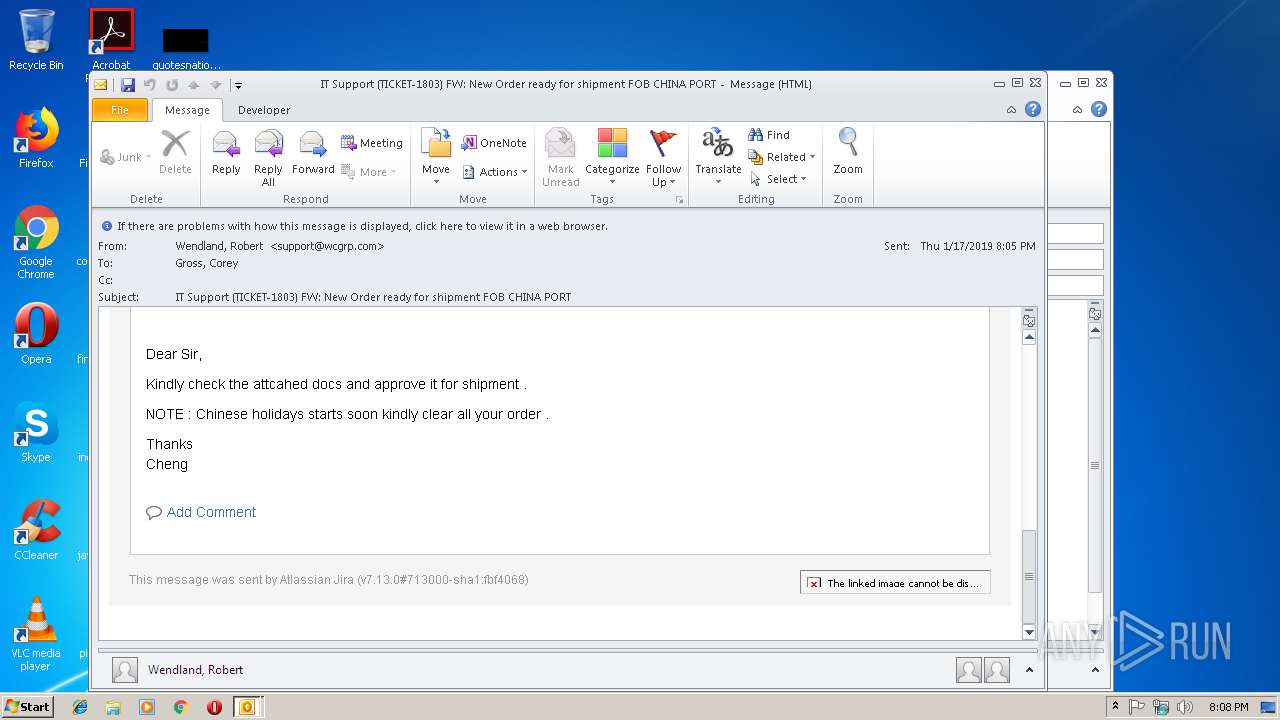
| File name: | IT Support (TICKET-1803) FW New Order ready for shipment FOB CHINA PORT.msg |
| Full analysis: | https://app.any.run/tasks/7d375ae5-cf63-410b-87db-1df9c4628207 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 20:07:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | D5641FC62C6D4F6AB52EFFAC8AE16D99 |
| SHA1: | 6DDBACABC16D2CBC67840081374C30C1FCFA7ACE |
| SHA256: | A3BC77A4A2B81BBB88FF1E85496215D4192FE78AF66566BD01A097FAC3755EAB |
| SSDEEP: | 768:FxJx4+gk34sKBsKjQUqXvTi+9FiRzLRVnqKwReKpvLgYJ24LEO/9U1oMCkm9Ufg4:FdmZ7skzDnqnReyDgYJ24L69Lsy |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2976)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2976)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2976)
Starts itself from another location
- OUTLOOK.EXE (PID: 2976)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2976)
- OUTLOOK.EXE (PID: 2732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
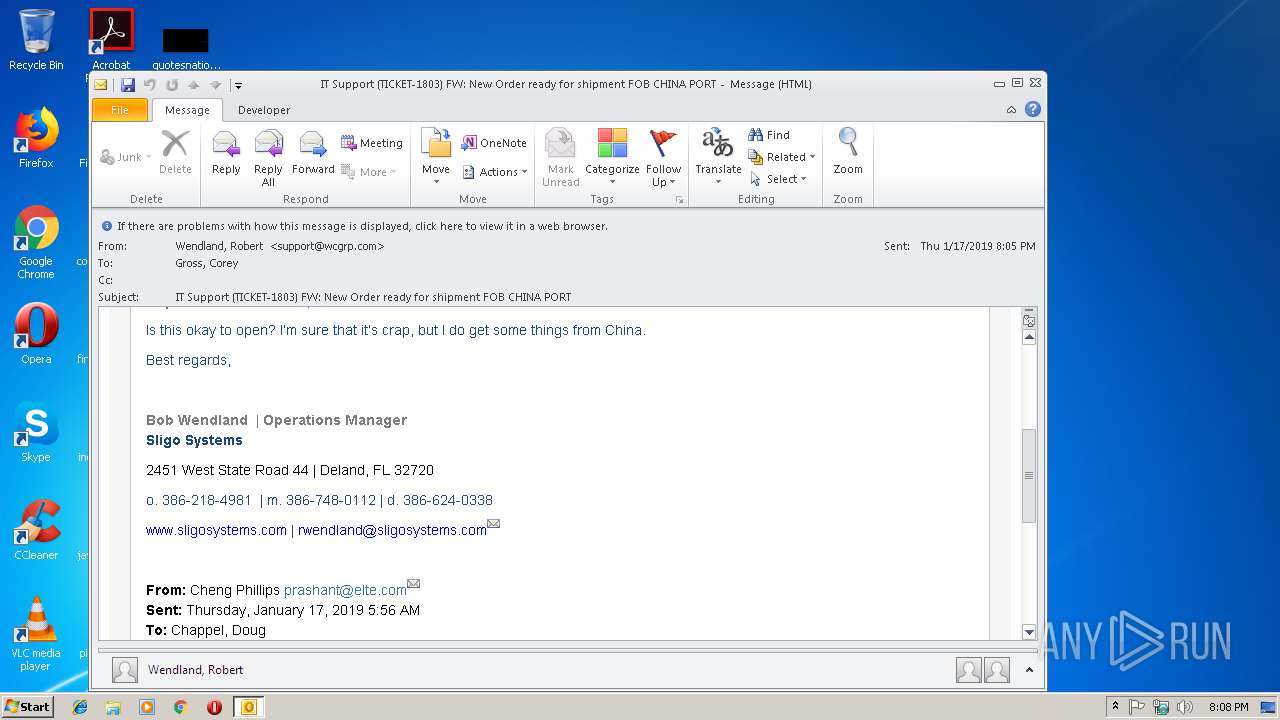
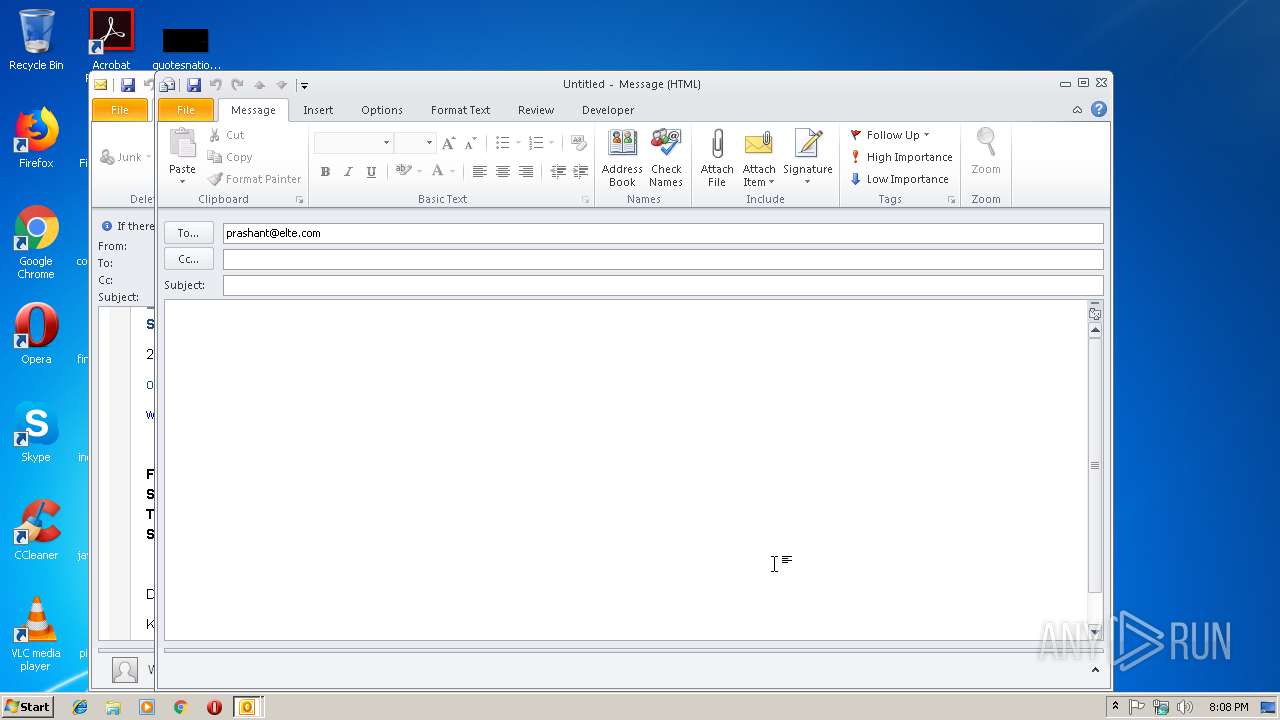
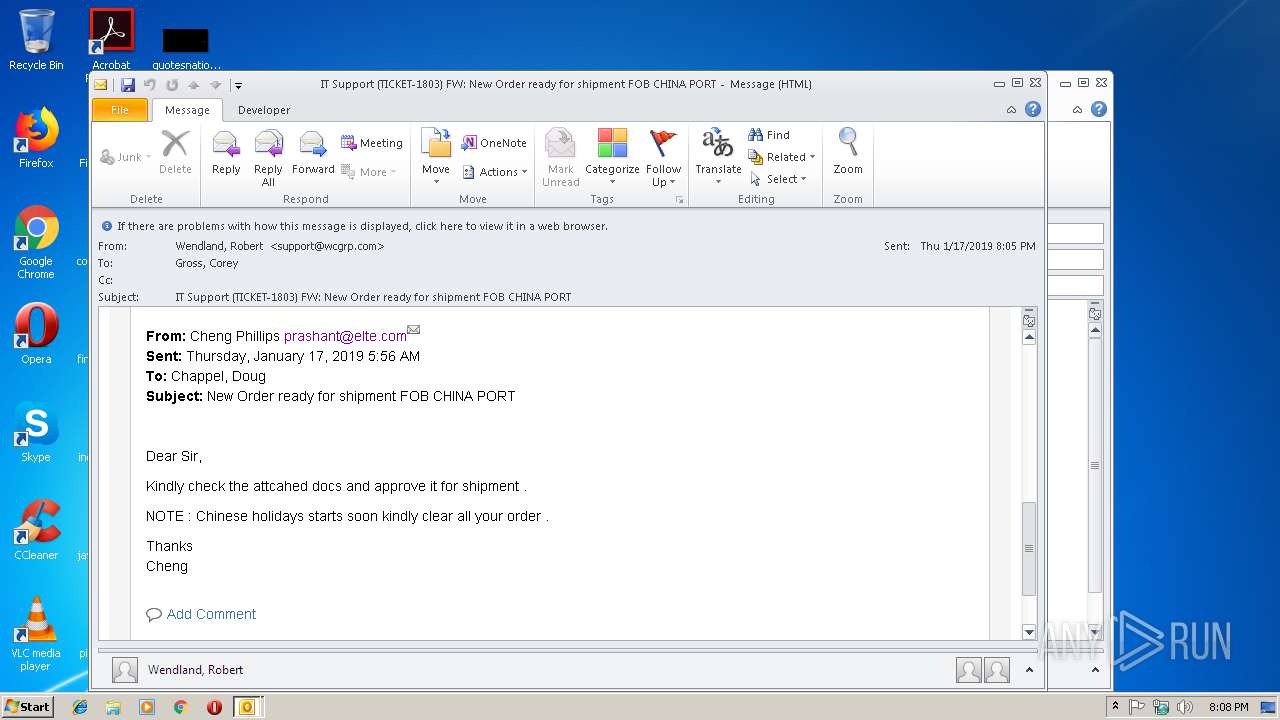
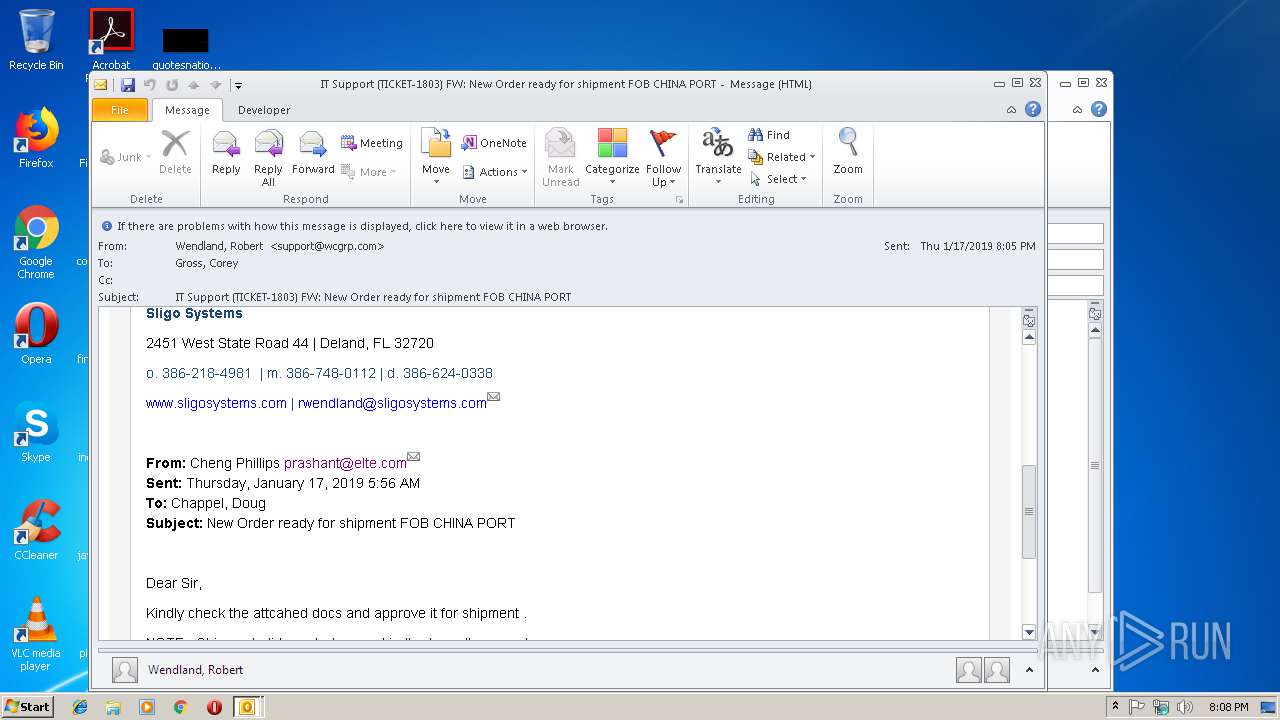
| 2732 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:prashant@elte.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\IT Support (TICKET-1803) FW New Order ready for shipment FOB CHINA PORT.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 345
Read events
903
Write events
413
Delete events
29
Modification events
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | u3% |
Value: 75332500A00B0000010000000000000000000000 | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: A00B00004261C35AA0AED40100000000 | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219869280 | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2976) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1311834133 | |||
Executable files
0
Suspicious files
0
Text files
32
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8F46.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\78A10873.dat | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1CC63FD8.dat | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AF994DF9.dat | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9D2B2BA6.dat | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\a9f987c1c1e26cbdab09da4b998e0370[1].png | — | |
MD5:— | SHA256:— | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRFCD5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E2B8C680.dat | image | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\84F91481.dat | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2976 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
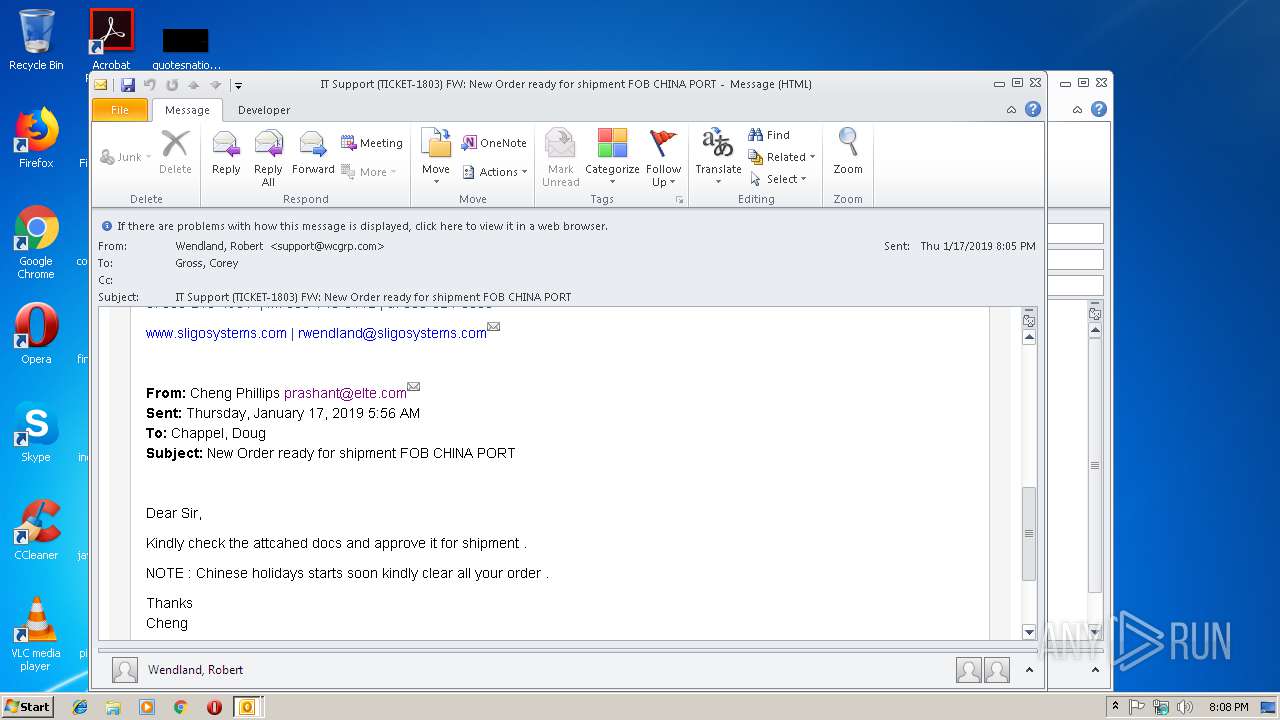
2976 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2976 | OUTLOOK.EXE | 192.0.73.2:443 | www.gravatar.com | Automattic, Inc | US | whitelisted |
2976 | OUTLOOK.EXE | 67.217.38.247:443 | support.wcgrp.com | NetSource Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.gravatar.com |
| whitelisted |
support.wcgrp.com |
| unknown |
dns.msftncsi.com |
| shared |