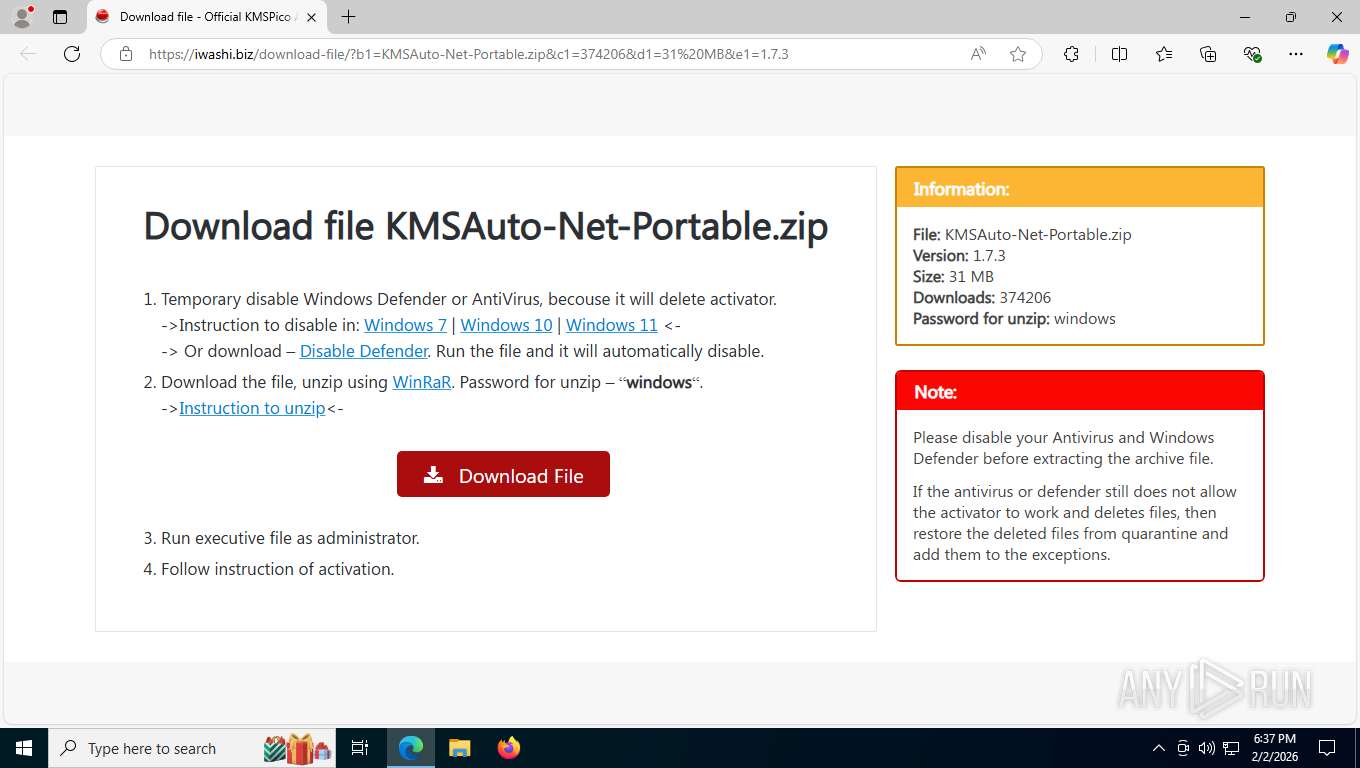
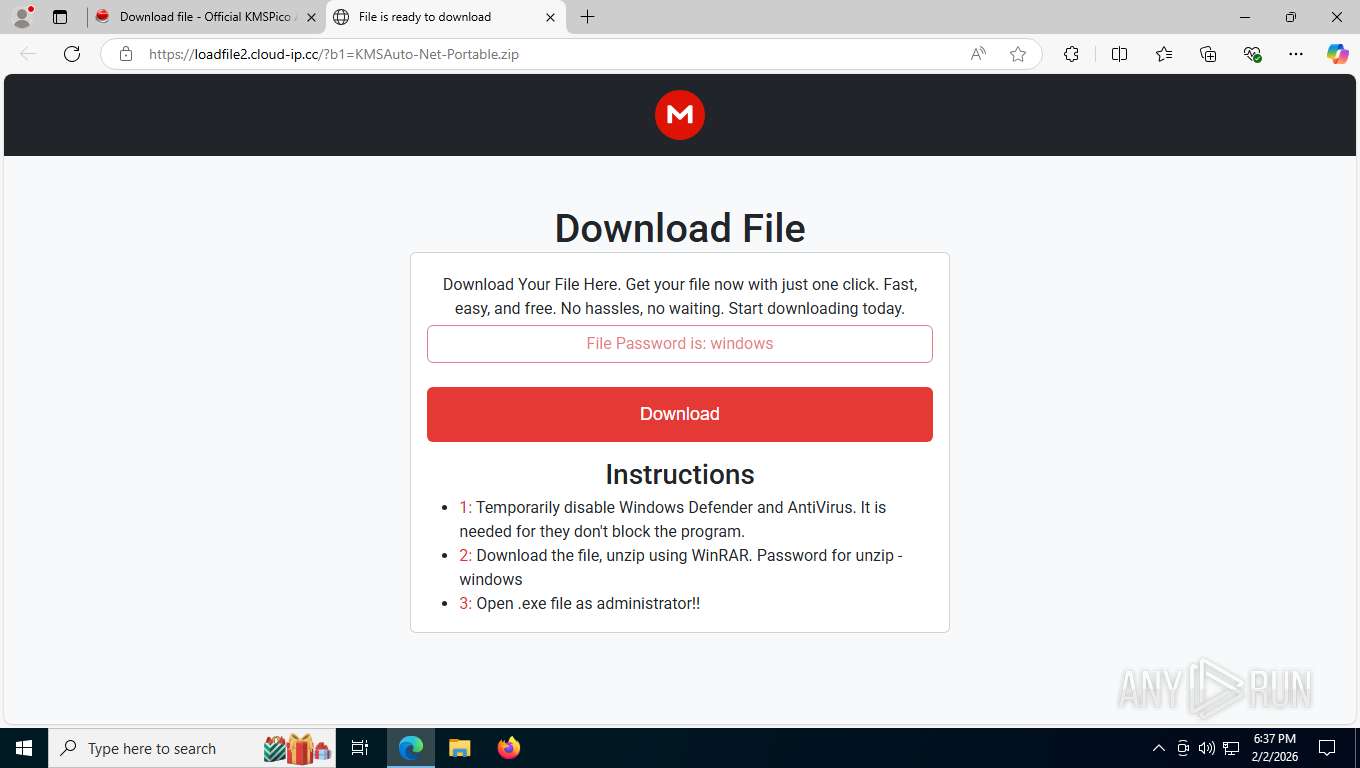
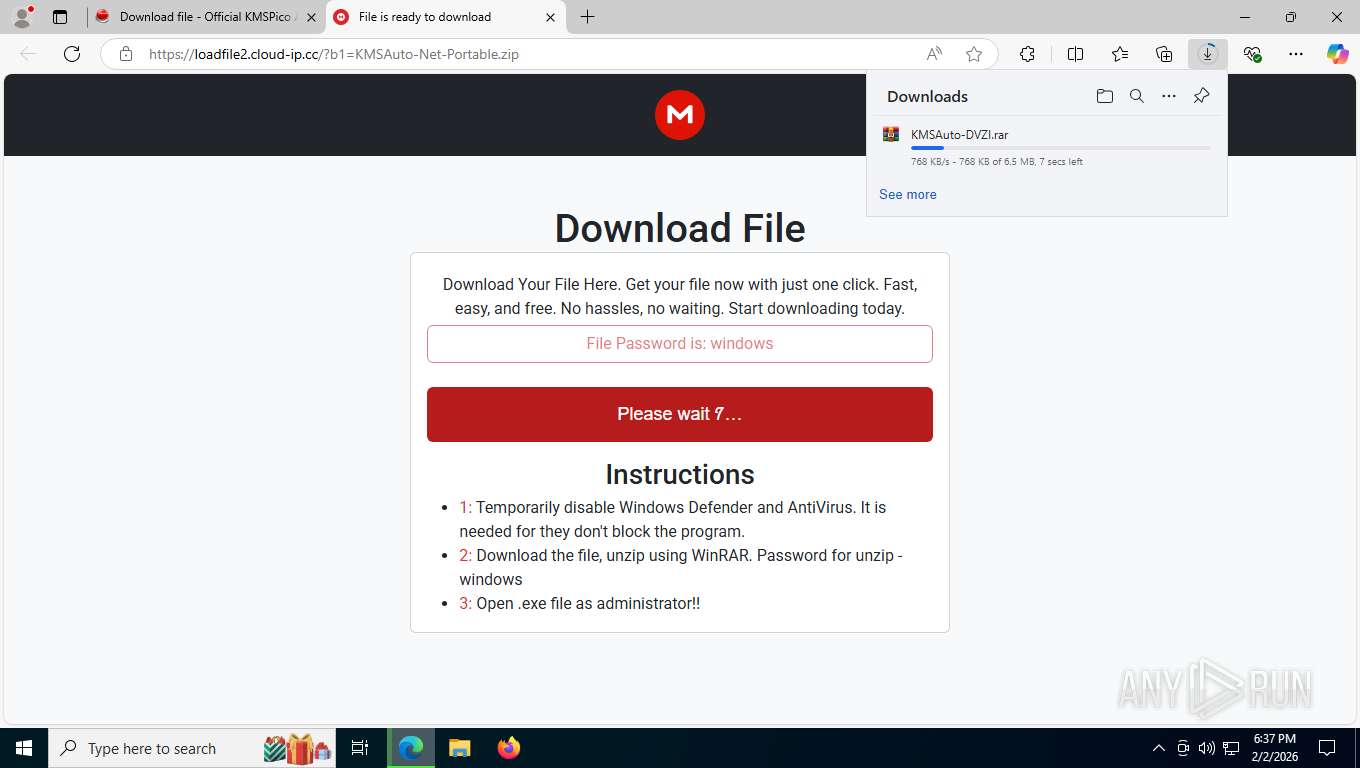
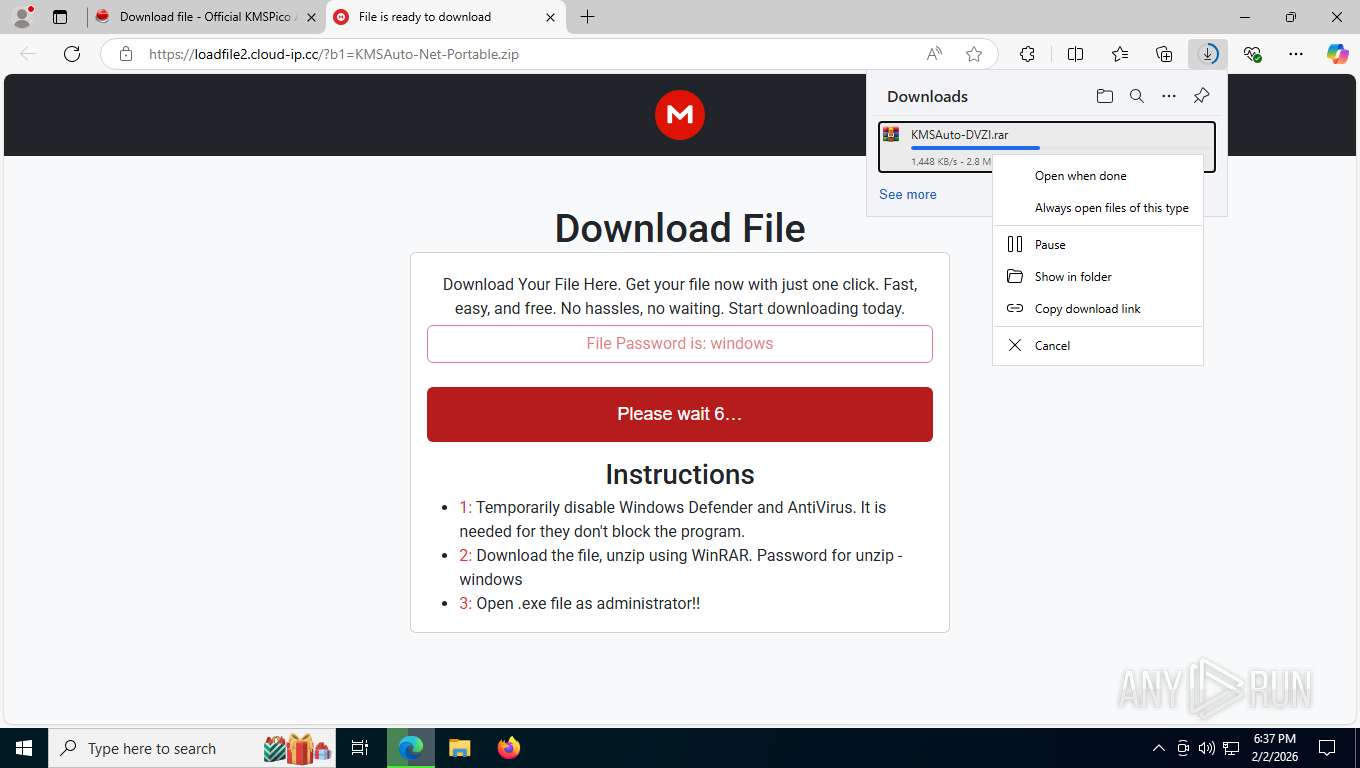
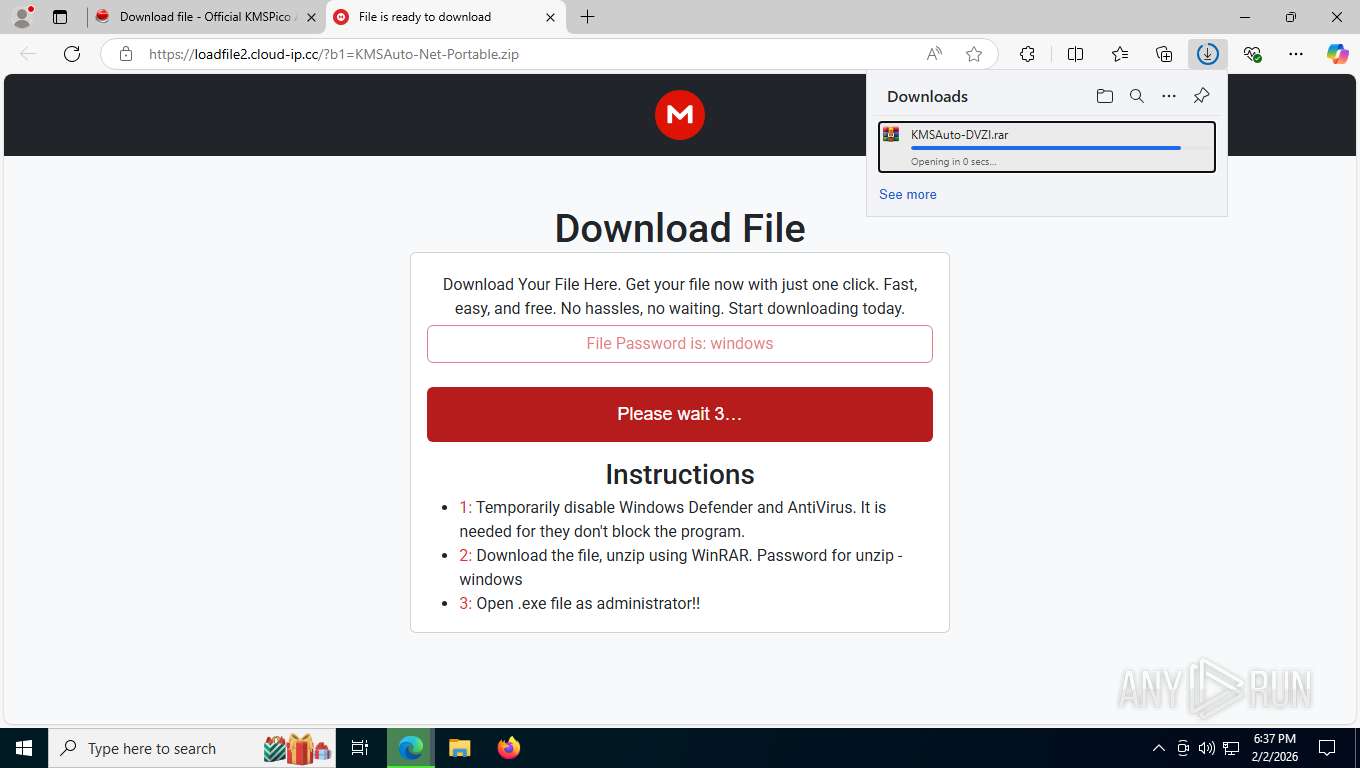
| URL: | https://iwashi.biz/download-file/?b1=KMSAuto-Net-Portable.zip&c1=374206&d1=31%20MB&e1=1.7.3 |
| Full analysis: | https://app.any.run/tasks/11e78c08-f65f-4905-9d4d-f806c58f1f60 |
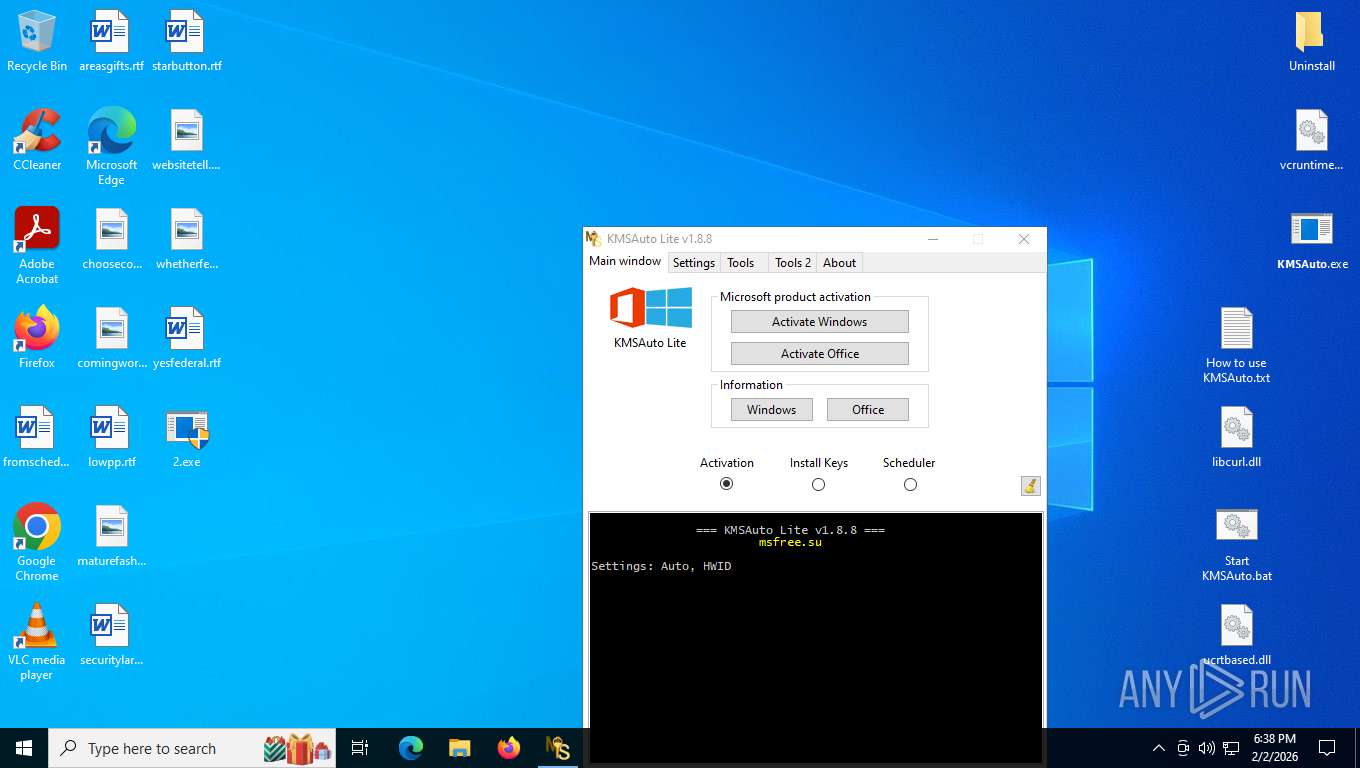
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 02, 2026, 23:37:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7D2C2738021F2FE3DA75A7E436F67ACB |
| SHA1: | 332958153B64D7808A2BC9E6B41BF0FB35530687 |
| SHA256: | A3BA9A4325458FED5D77AA7B214C5719165E6ACE11CDF9E204BB02770A4A2338 |
| SSDEEP: | 3:N8VNMLHVDLkDU0fxAZp17oDA6n:2nMLHZqmXqDz |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 2336)
Executing a file with an untrusted certificate
- activate.exe (PID: 7740)
Run PowerShell with an invisible window
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 2340)
- powershell.exe (PID: 5448)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 3440)
Starts CMD.EXE for self-deleting
- 2.exe (PID: 2684)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 5528)
Uses WMIC.EXE to add exclusions to the Windows Defender
- powershell.exe (PID: 2340)
- powershell.exe (PID: 5448)
- powershell.exe (PID: 3440)
Changes the autorun value in the registry
- setup-win32-bundle.exe (PID: 8068)
Uses Task Scheduler to run other applications
- setup.exe (PID: 6828)
- msiexec.exe (PID: 9076)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- msiexec.exe (PID: 5588)
Opens a text file (SCRIPT)
- msiexec.exe (PID: 5588)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- msiexec.exe (PID: 5588)
Reads the value of a key from the registry (SCRIPT)
- msiexec.exe (PID: 5588)
Checks whether a specified folder exists (SCRIPT)
- msiexec.exe (PID: 5588)
Creates a new folder (SCRIPT)
- msiexec.exe (PID: 5588)
Creates internet connection object (SCRIPT)
- msiexec.exe (PID: 5588)
Opens an HTTP connection (SCRIPT)
- msiexec.exe (PID: 5588)
Creates scheduled task from XML file
- msiexec.exe (PID: 9076)
Sends HTTP request (SCRIPT)
- msiexec.exe (PID: 5588)
Deletes a file (SCRIPT)
- msiexec.exe (PID: 5588)
Copies file to a new location (SCRIPT)
- msiexec.exe (PID: 5588)
Actions looks like stealing of personal data
- setup.exe (PID: 1792)
Steals credentials from Web Browsers
- setup.exe (PID: 2352)
- setup.exe (PID: 1792)
- setup.exe (PID: 5356)
- assistant_installer.exe (PID: 3276)
- assistant_installer.exe (PID: 7868)
- setup.exe (PID: 4212)
- installer.exe (PID: 6584)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 5012)
- assistant_installer.exe (PID: 1424)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1656)
- Assistant_126.0.5750.18_Setup.exe_sfx.exe (PID: 6296)
- setup.exe (PID: 4212)
Executable content was dropped or overwritten
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- 2.exe (PID: 2684)
- UnRAR.exe (PID: 5168)
- UnRAR.exe (PID: 3544)
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- setup-win32-bundle.exe (PID: 1784)
- setup-win32-bundle.exe (PID: 8068)
- setup.exe (PID: 6828)
- powershell.exe (PID: 5528)
- setup.exe (PID: 2352)
- OperaSetup.exe (PID: 6392)
- setup.exe (PID: 1792)
- setup.exe (PID: 9068)
- setup.exe (PID: 4212)
- setup.exe (PID: 5356)
- Assistant_126.0.5750.18_Setup.exe_sfx.exe (PID: 6296)
- installer.exe (PID: 6584)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 1424)
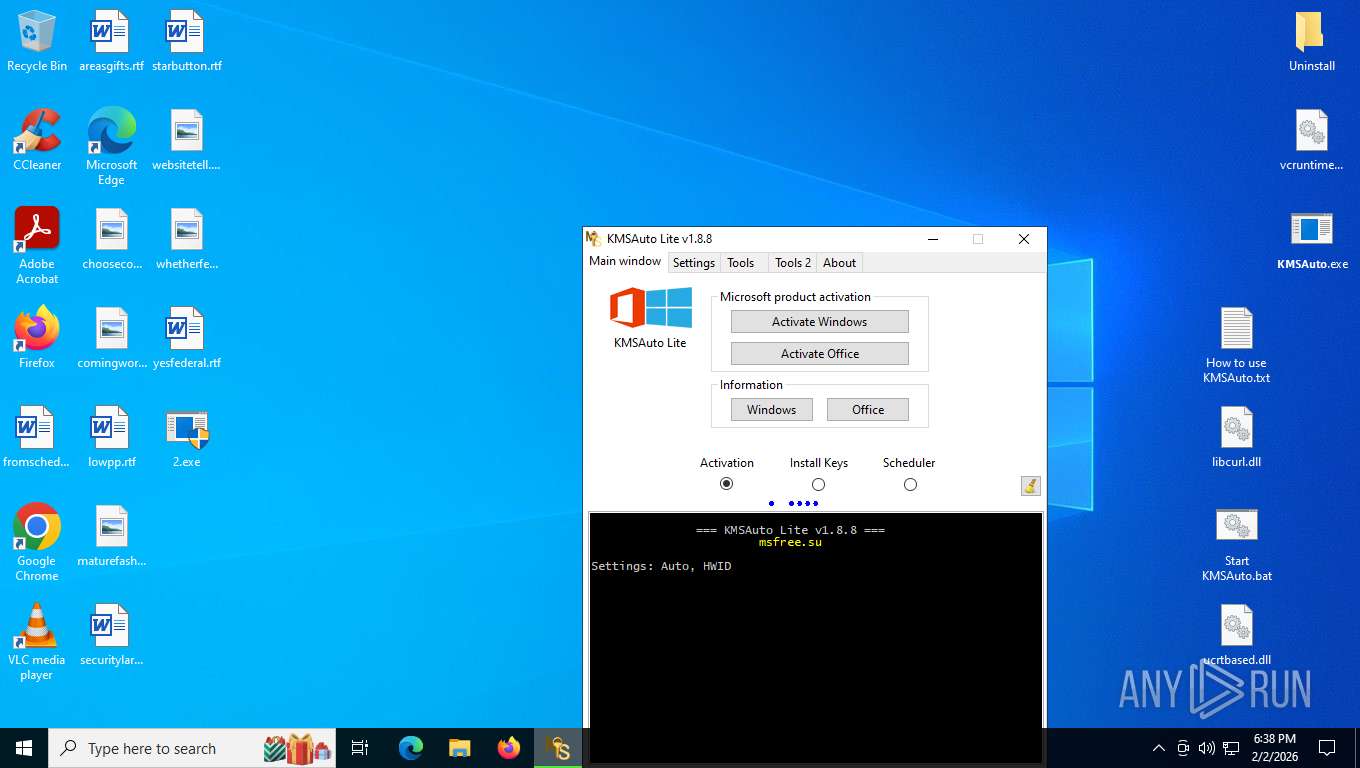
Starts CMD.EXE for commands execution
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- 2.exe (PID: 2684)
- Launch-Activator.exe (PID: 5392)
- setup.exe (PID: 6828)
- forfiles.exe (PID: 5012)
- forfiles.exe (PID: 7732)
- forfiles.exe (PID: 2372)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7236)
- cmd.exe (PID: 2260)
Hides command output
- cmd.exe (PID: 7236)
- cmd.exe (PID: 2260)
Starts SC.EXE for service management
- Launch-Activator.exe (PID: 5392)
Windows service management via SC.EXE
- sc.exe (PID: 6928)
- sc.exe (PID: 5180)
Uses WMIC.EXE
- Launch-Activator.exe (PID: 5392)
Probably download files using WebClient
- cmd.exe (PID: 2260)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2260)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 7100)
Found IP address in command line
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 5528)
Creates file in the systems drive root
- cmd.exe (PID: 2260)
Using the short paths format
- cmd.exe (PID: 2260)
Reads the BIOS version
- setup.exe (PID: 6828)
Found strings related to reading or modifying Windows Defender settings
- setup.exe (PID: 6828)
- forfiles.exe (PID: 7732)
- forfiles.exe (PID: 2372)
- forfiles.exe (PID: 5012)
Searches and executes a command on selected files
- forfiles.exe (PID: 5012)
- forfiles.exe (PID: 7732)
- forfiles.exe (PID: 2372)
Starts itself from another location
- setup-win32-bundle.exe (PID: 1784)
- setup.exe (PID: 1792)
Searches for installed software
- setup-win32-bundle.exe (PID: 8068)
- installer.exe (PID: 7748)
Application launched itself
- msiexec.exe (PID: 8668)
- setup.exe (PID: 1792)
- setup.exe (PID: 4212)
- assistant_installer.exe (PID: 7868)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 1424)
Reads data from a binary Stream object (SCRIPT)
- msiexec.exe (PID: 5588)
Creates FileSystem object to access computer's file system (SCRIPT)
- msiexec.exe (PID: 5588)
Writes binary data to a Stream object (SCRIPT)
- msiexec.exe (PID: 5588)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8668)
Executes application which crashes
- 2.exe (PID: 2684)
Reads the date of Windows installation
- installer.exe (PID: 7748)
INFO
Drops script file
- msedge.exe (PID: 8392)
- msedge.exe (PID: 2336)
- msedge.exe (PID: 7716)
- WinRAR.exe (PID: 1656)
- KMSAuto.exe (PID: 8012)
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 2340)
- powershell.exe (PID: 5448)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 3440)
- setup.exe (PID: 4212)
- installer.exe (PID: 7748)
Reads the computer name
- identity_helper.exe (PID: 5012)
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- KMSAuto.exe (PID: 8012)
- 2.exe (PID: 2684)
- Launch-Activator.exe (PID: 5392)
- activate.exe (PID: 7740)
- setup.exe (PID: 6828)
- setup-win32-bundle.exe (PID: 8068)
- msiexec.exe (PID: 8668)
- msiexec.exe (PID: 5588)
- msiexec.exe (PID: 9076)
- setup.exe (PID: 1792)
- setup.exe (PID: 4212)
- assistant_installer.exe (PID: 7868)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 1424)
Checks supported languages
- identity_helper.exe (PID: 5012)
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- UnRAR.exe (PID: 2872)
- KMSAuto.exe (PID: 8012)
- UnRAR.exe (PID: 5168)
- activate.exe (PID: 7740)
- 2.exe (PID: 2684)
- UnRAR.exe (PID: 3544)
- Launch-Activator.exe (PID: 5392)
- setup.exe (PID: 6828)
- setup-win32-bundle.exe (PID: 1784)
- setup-win32-bundle.exe (PID: 8068)
- msiexec.exe (PID: 8668)
- msiexec.exe (PID: 5588)
- msiexec.exe (PID: 9076)
- OperaSetup.exe (PID: 6392)
- setup.exe (PID: 1792)
- setup.exe (PID: 2352)
- setup.exe (PID: 9068)
- setup.exe (PID: 4212)
- setup.exe (PID: 5356)
- assistant_installer.exe (PID: 3276)
- assistant_installer.exe (PID: 7868)
- Assistant_126.0.5750.18_Setup.exe_sfx.exe (PID: 6296)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 1424)
- installer.exe (PID: 6584)
- assistant_installer.exe (PID: 5012)
Application launched itself
- msedge.exe (PID: 8392)
Reads Environment values
- identity_helper.exe (PID: 5012)
- Launch-Activator.exe (PID: 5392)
- msiexec.exe (PID: 5588)
The sample compiled with english language support
- WinRAR.exe (PID: 1656)
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- powershell.exe (PID: 6348)
- setup-win32-bundle.exe (PID: 1784)
- setup-win32-bundle.exe (PID: 8068)
- OperaSetup.exe (PID: 6392)
- setup.exe (PID: 2352)
- setup.exe (PID: 1792)
- setup.exe (PID: 9068)
- setup.exe (PID: 4212)
- setup.exe (PID: 5356)
- Assistant_126.0.5750.18_Setup.exe_sfx.exe (PID: 6296)
- installer.exe (PID: 6584)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 1424)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1656)
- msiexec.exe (PID: 8668)
- msiexec.exe (PID: 5588)
Manual execution by a user
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
Create files in a temporary directory
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- 2.exe (PID: 2684)
- KMSAuto.exe (PID: 8012)
- setup.exe (PID: 6828)
- msiexec.exe (PID: 5588)
- OperaSetup.exe (PID: 6392)
- setup.exe (PID: 1792)
- setup.exe (PID: 2352)
- setup.exe (PID: 9068)
- setup.exe (PID: 4212)
- setup.exe (PID: 5356)
- installer.exe (PID: 7748)
- Assistant_126.0.5750.18_Setup.exe_sfx.exe (PID: 6296)
- installer.exe (PID: 6584)
Creates files in the program directory
- 𝗞𝗠𝗦𝗔𝘂𝘁𝗼.exe (PID: 7000)
- activate.exe (PID: 7740)
FOR cycle in command line
- cmd.exe (PID: 7236)
Reads the machine GUID from the registry
- KMSAuto.exe (PID: 8012)
- activate.exe (PID: 7740)
- setup-win32-bundle.exe (PID: 8068)
- msiexec.exe (PID: 8668)
- setup.exe (PID: 1792)
- installer.exe (PID: 7748)
Reads security settings of Internet Explorer
- KMSAuto.exe (PID: 8012)
- WMIC.exe (PID: 2248)
- activate.exe (PID: 7740)
- setup.exe (PID: 6828)
- WMIC.exe (PID: 8996)
- setup-win32-bundle.exe (PID: 8068)
- WMIC.exe (PID: 6568)
- WMIC.exe (PID: 5160)
- setup.exe (PID: 1792)
- installer.exe (PID: 7748)
Checks if a key exists in the options dictionary (POWERSHELL)
- KMSAuto.exe (PID: 8012)
UPX packer has been detected
- 2.exe (PID: 2684)
Reads product name
- Launch-Activator.exe (PID: 5392)
There is functionality for taking screenshot (YARA)
- 2.exe (PID: 2684)
Creates a new folder
- cmd.exe (PID: 2260)
Checks proxy server information
- activate.exe (PID: 7740)
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- setup-win32-bundle.exe (PID: 8068)
- powershell.exe (PID: 5528)
- setup.exe (PID: 1792)
- WerFault.exe (PID: 7560)
Disables trace logs
- powershell.exe (PID: 6432)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 5528)
Process checks computer location settings
- setup.exe (PID: 6828)
Launching a file from a Registry key
- setup-win32-bundle.exe (PID: 8068)
Creates a software uninstall entry
- setup-win32-bundle.exe (PID: 8068)
- msiexec.exe (PID: 8668)
- installer.exe (PID: 7748)
Creates files or folders in the user directory
- setup-win32-bundle.exe (PID: 8068)
- msiexec.exe (PID: 5588)
- msiexec.exe (PID: 8668)
- setup.exe (PID: 2352)
- setup.exe (PID: 1792)
- WerFault.exe (PID: 7560)
- setup.exe (PID: 4212)
- installer.exe (PID: 7748)
- assistant_installer.exe (PID: 1424)
Launching a file from Task Scheduler
- setup.exe (PID: 6828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
97
Malicious processes
12
Suspicious processes
19
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2240,i,6082502579037512696,3470513881937336566,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2208 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\Desktop\2.exe" | C:\Users\admin\Desktop\2.exe | — | cmd.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: WinGup for Notepad++ Exit code: 3221226540 Version: 5.26 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=14 --always-read-main-dll --field-trial-handle=6676,i,6082502579037512696,3470513881937336566,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6732 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5856,i,6082502579037512696,3470513881937336566,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5576 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\AppData\Local\Temp\.opera\f3b8fbd4-8f5f-4a46-8ce4-fd676b90ca07 Opera Installer Temp\opera_package_202602021838161\assistant\assistant_installer.exe" --installfolder="C:\Users\admin\AppData\Local\Programs\Opera\assistant" --copyonly=0 --allusers=0 | C:\Users\admin\AppData\Local\Temp\.opera\f3b8fbd4-8f5f-4a46-8ce4-fd676b90ca07 Opera Installer Temp\opera_package_202602021838161\assistant\assistant_installer.exe | installer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera Browser Assistant Installer Version: 126.0.5750.18 Modules
| |||||||||||||||
| 1520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
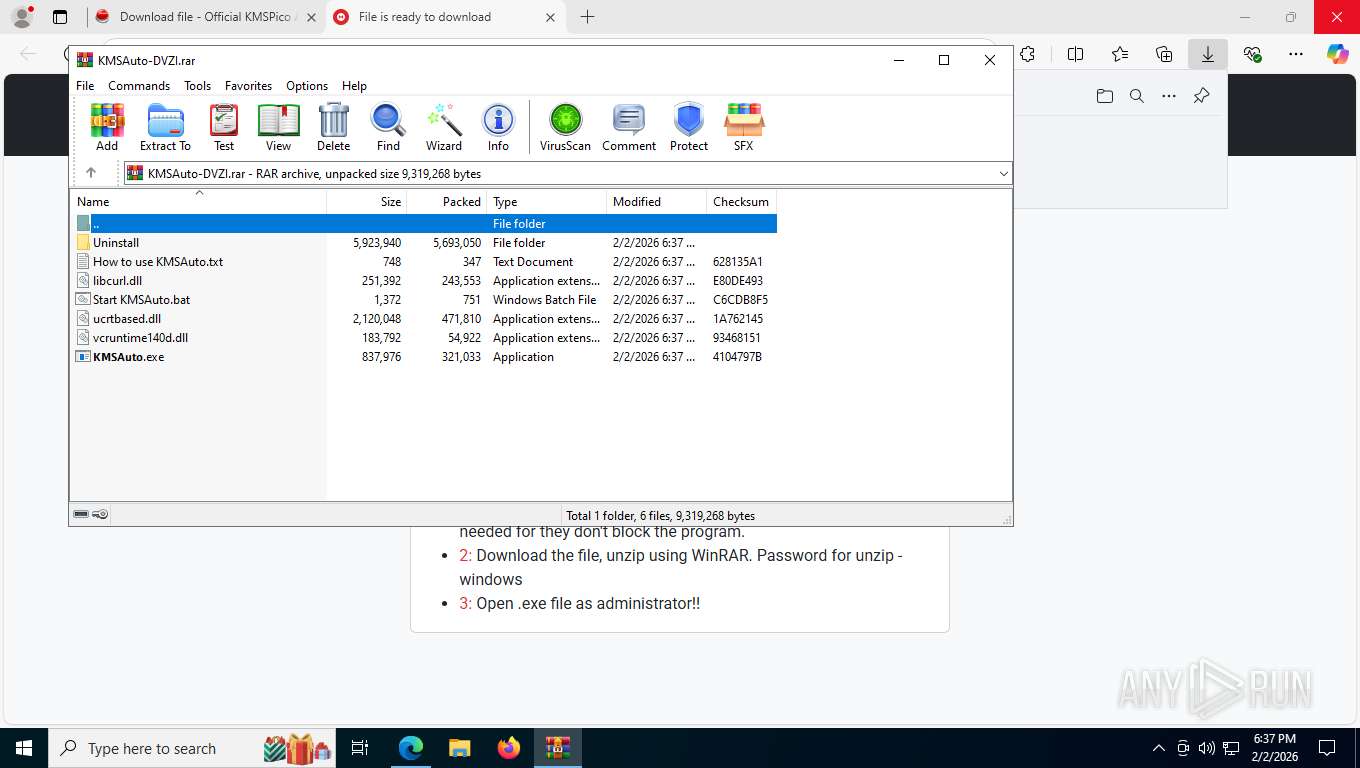
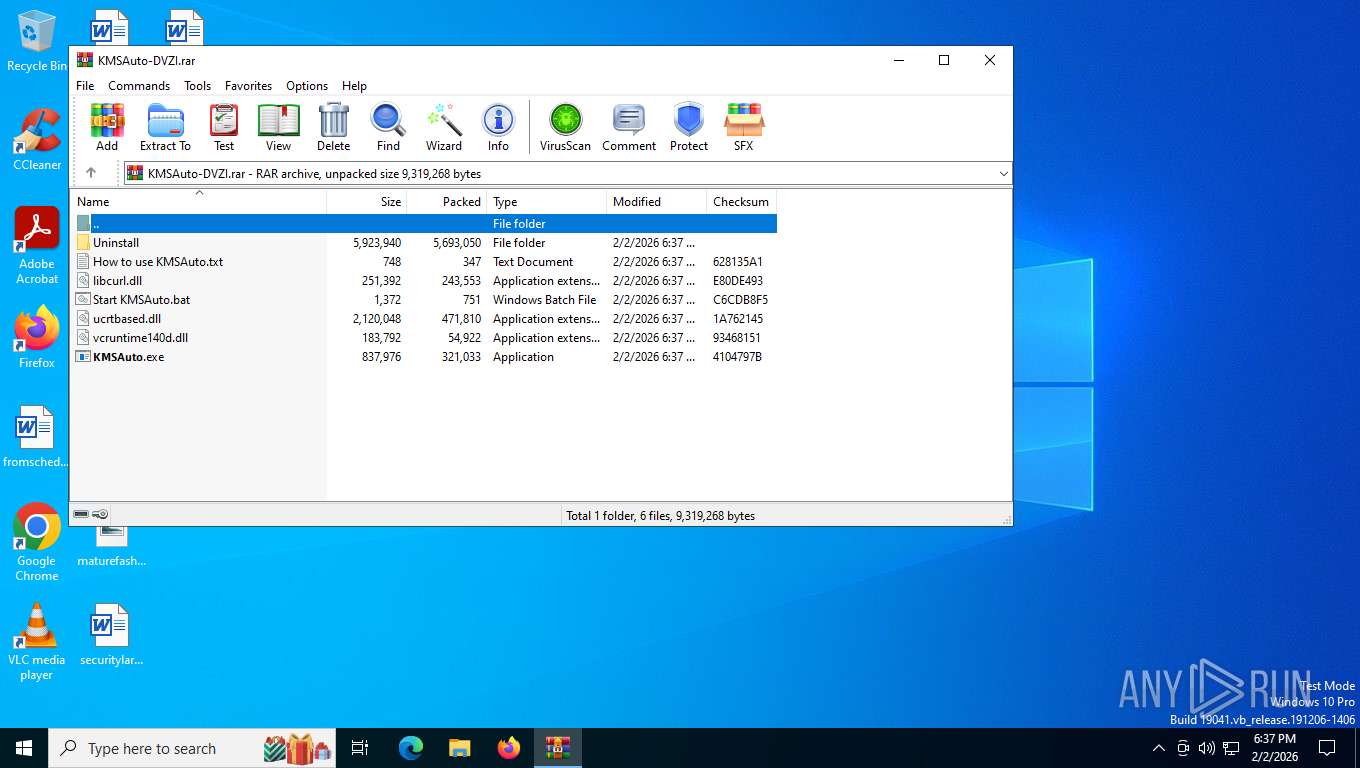
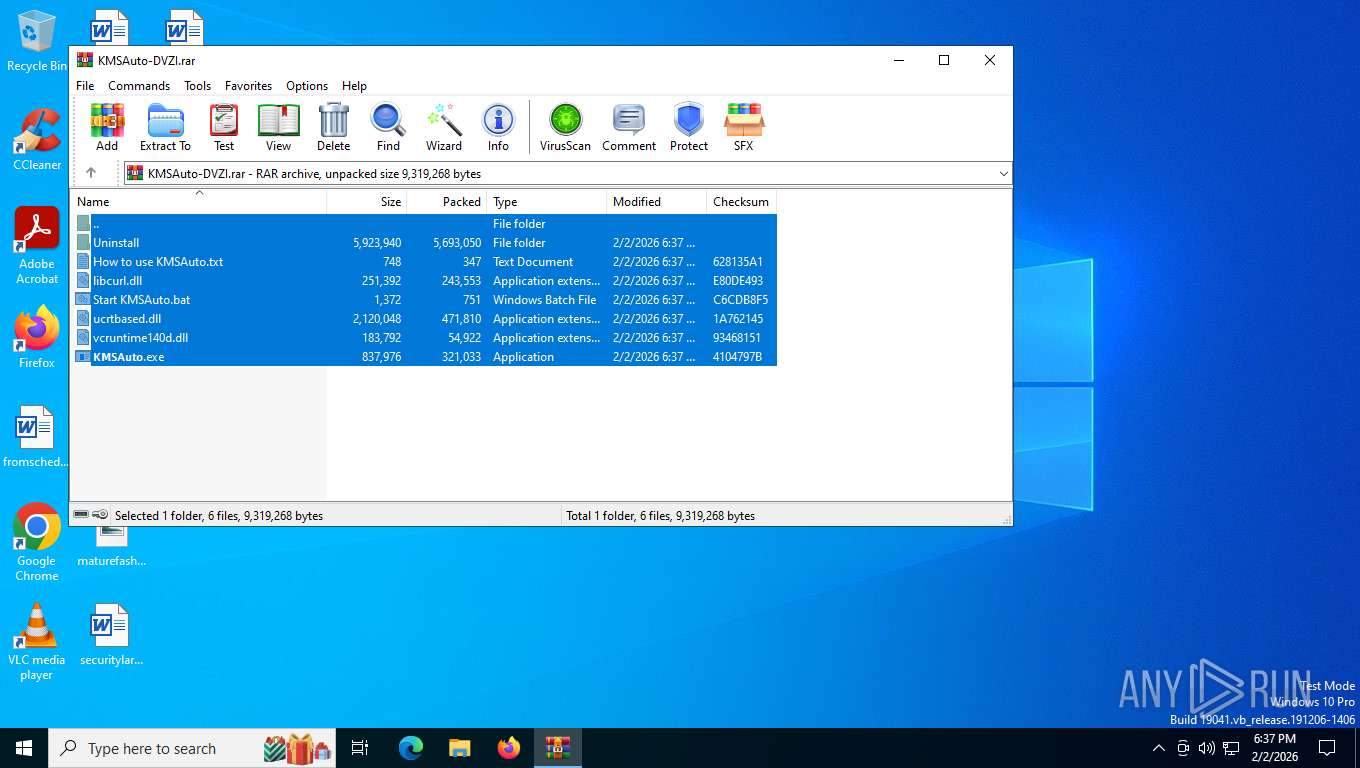
| 1656 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\KMSAuto-DVZI.rar" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5416,i,6082502579037512696,3470513881937336566,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5400 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
54 236
Read events
54 006
Write events
212
Delete events
18
Modification events
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\KMSAuto-DVZI.rar | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (1656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
67
Suspicious files
193
Text files
432
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e53da.TMP | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e53da.TMP | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e53da.TMP | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e53da.TMP | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e53da.TMP | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
97
TCP/UDP connections
89
DNS requests
95
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2336 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:cmIZd1wfFIDThYtgjN8aZSf0jRjkdiImEbFLXjIVopY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2336 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.87 Kb | whitelisted |
2336 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
2336 | msedge.exe | GET | 200 | 104.21.22.77:443 | https://iwashi.biz/download-file/?b1=KMSAuto-Net-Portable.zip&c1=374206&d1=31%20MB&e1=1.7.3 | unknown | html | 76.9 Kb | unknown |
2336 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | binary | 82 b | whitelisted |
2336 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1770075453&lafgdate=0 | unknown | text | 41.4 Kb | whitelisted |
2336 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
2336 | msedge.exe | GET | 200 | 104.21.22.77:443 | https://iwashi.biz/wp-content/plugins/shortcodes-ultimate/includes/css/icons.css?ver=1.1.5 | unknown | text | 36.1 Kb | unknown |
2336 | msedge.exe | GET | 200 | 104.21.22.77:443 | https://iwashi.biz/wp-content/themes/jannah/assets/css/style.min.css | unknown | text | 128 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5512 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5412 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.141:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2336 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2336 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
iwashi.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2336 | msedge.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
2336 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain ( .cloud-ip .cc) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2336 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
setup.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\Opera Software\Opera Stable directory exists )
|
setup.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\Opera Software\Opera Stable directory exists )
|
assistant_installer.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\Opera Software\Opera Stable directory exists )
|
assistant_installer.exe | [0202/183825.098:INFO:opera\desktop\windows\assistant\installer\assistant_installer_main.cc:170] Running assistant installer with command line "C:\Users\admin\AppData\Local\Temp\.opera\f3b8fbd4-8f5f-4a46-8ce4-fd676b90ca07 Opera Installer Temp\opera_package_202602021838161\assistant\assistant_installer.exe" --version
|
installer.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\Opera Software\Opera Stable directory exists )
|
assistant_installer.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\Opera Software\Opera Stable directory exists )
|
assistant_installer.exe | [0202/183833.924:INFO:opera\desktop\windows\assistant\installer\assistant_installer_main.cc:170] Running assistant installer with command line "C:\Users\admin\AppData\Local\Temp\.opera\f3b8fbd4-8f5f-4a46-8ce4-fd676b90ca07 Opera Installer Temp\opera_package_202602021838161\assistant\assistant_installer.exe" --installfolder="C:\Users\admin\AppData\Local\Programs\Opera\assistant" --copyonly=0 --allusers=0
|