| URL: | https://www.yahoo.com/geo.yahoo.com/p?_E=adperf&outcm=performance&etrg=backgroundPost&usergenf=0&etag=performance,darla&s=2023538075&pvid=0E.zWzEyNy6cBaOcXVRIlgA0MTY1LgAAAABAZGYz&D_bv=1.0.0&D_ts=0&D_v=sdarla_4-6-0&D_l=292,-1,-1,-1,-1,-1,-1,0,3&D_m=1,,4g,0,&test=FPNODEUP100&D_e=pt=index&pd=modal&rid=61jc8hpge0q1v&sid=&bucket=FPNODEUP100&D_p=7,11115211,LREC,300x250,999999,999999,999999,0,0,7833,7,-1,26803111,-1,2,0E.zWzEyNy6cBaOcXVRIlgA0MTY1LgAAAABAZGYz:-1:LREC,2,2,0,2,0,2,0,0,8,1,8,2,0,0,0,0,0,0,3,https%3A//www.yahoo.com,,7,2,3,0,0,-1,0,0,-1,-1,370,370;&D_res={"LREC":[{"name":"https://fw.adsafeprotected.com/rjss/st/554763/54777353/skeleton.js","dur":7040,"st":352,"ssl":null,"dns":null,"conn":null},{"name":"https://contextual.media.net/checksync.php?vsSync=1&cs=10&cv=31&https=1&cid=8CU857501&prvid=251%2C178%2C214%2C238%2C239%2C77%2C99%2C182%2C260%2C184%2C261%2C262%2C188%2C222%2C201%2C147%2C246%2C4%2C126%2C203%2C226%2C10000%2C80%2C229%2C9&purpose1=1&gdprconsent=1&gdpr=0&usp_status=0&usp_consent=1&itype=BRIGHTROLL","dur":707,"st":368,"ssl":null,"dns":null,"conn":null},{"name":"https://pagead2.googlesyndication.com/pcs/activeview?xai=AKAOjsuXqrZVvVXWn6R8a1i267_b62fLgQN350LkxGEcXC8-rthu2iazpvEiTgWJyafkORgu0qYx3mAXg7sdTVKI_wbrEaWbZ3H1E7tvzTar&sig=Cg0ArKJSzLbL9yR5QGlmEAE&id=lidar2&mcvt=1000&p=0,0,251,301&mtos=0,1000,1000,1000,1000&tos=0,1000,0,0,0&v=20210702&bin=7&avms=nio&bs=0,0&mc=0.78&if=1&app=0&itpl=32&adk=0&rs=6&la=0&cr=0&uach=WyJXaW5kb3dzIiwiMTAuMCIsIng4NiIsIiIsIjkwLjAuNDQzMC44NSIsW10sbnVsbCxudWxsLG51bGxd&vs=4&eosm=0&rst=1625319783569&rpt=407&r=v&speed=1","dur":659,"st":1413,"ssl":0,"dns":0,"conn":0},{"name":"https://hblg.media.net/log?log=kfk&evtid=adplog&&prvAccId=134&ckfl=1&pgcatsprig=16&lper=1&mx_tgs=300x250&cbdp=2.809&os_id=101&mx_nsz=1&sc_advUrl=jobs.fidelity.com&spSource=7&vid=881cd13cac604ad4af60eda2423af2cf&pvdTmax=154&s_city=ashburn<ime=150.0&ugd=4&epc=470967883&mx_vsidFlt=false&prvReqId=12259514346077_1291666288_8625413772511&bId=51085220&exp=ssProfile%3D0%7Cebc%3D1%7Csfl%3Dfalse%7Cebv%3D1%7CssBucket%3D0%7Cbfl%3D-100%7Csch%3D1%7C |
| Full analysis: | https://app.any.run/tasks/3628a5f0-3922-40bd-886f-71d58b539119 |
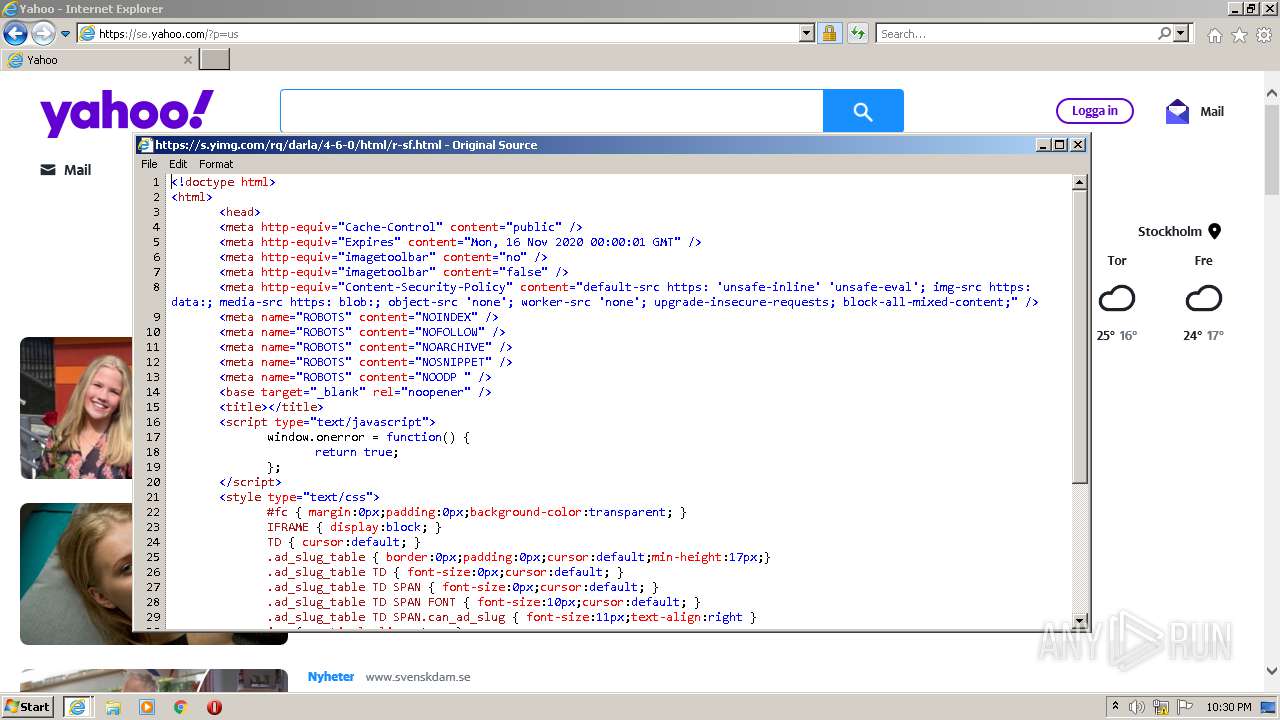
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2021, 21:29:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8EC1BDC5CFFD5DA03C712E52920D4CE6 |
| SHA1: | 4F46265BDA7BAAA73CF057429222D41E4DF1A174 |
| SHA256: | A3AA7C7E693A812BA1B117F7168C42DFD38BA72BDC3319B347D8CB9F22AA152E |
| SSDEEP: | 48:ALx9EL6tL5F3M/ty68q69XXbfCTDlVaVbPW0wmJbuLV5jByfW:AL7V7Ms68q6VbIQpu9MbuLx3 |
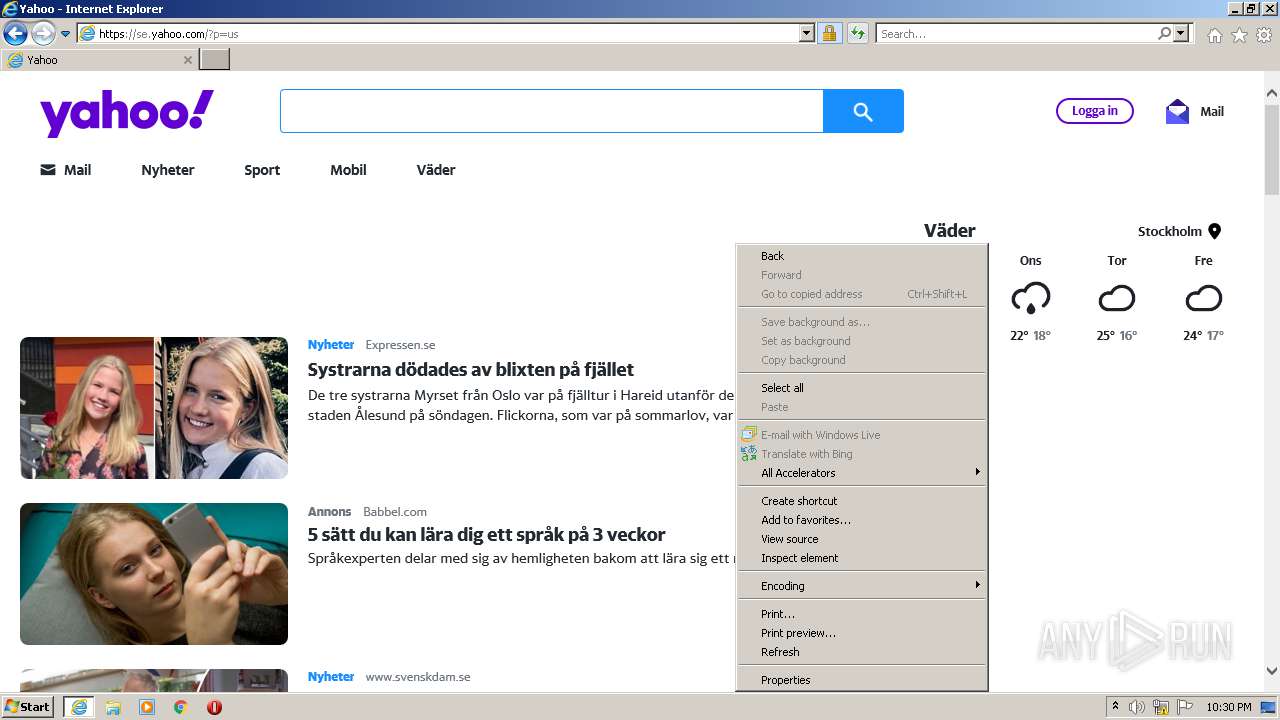
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2956)
INFO
Reads the computer name
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 2956)
Checks Windows Trust Settings
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 2956)
Reads settings of System Certificates
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 2956)
Checks supported languages
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 2956)
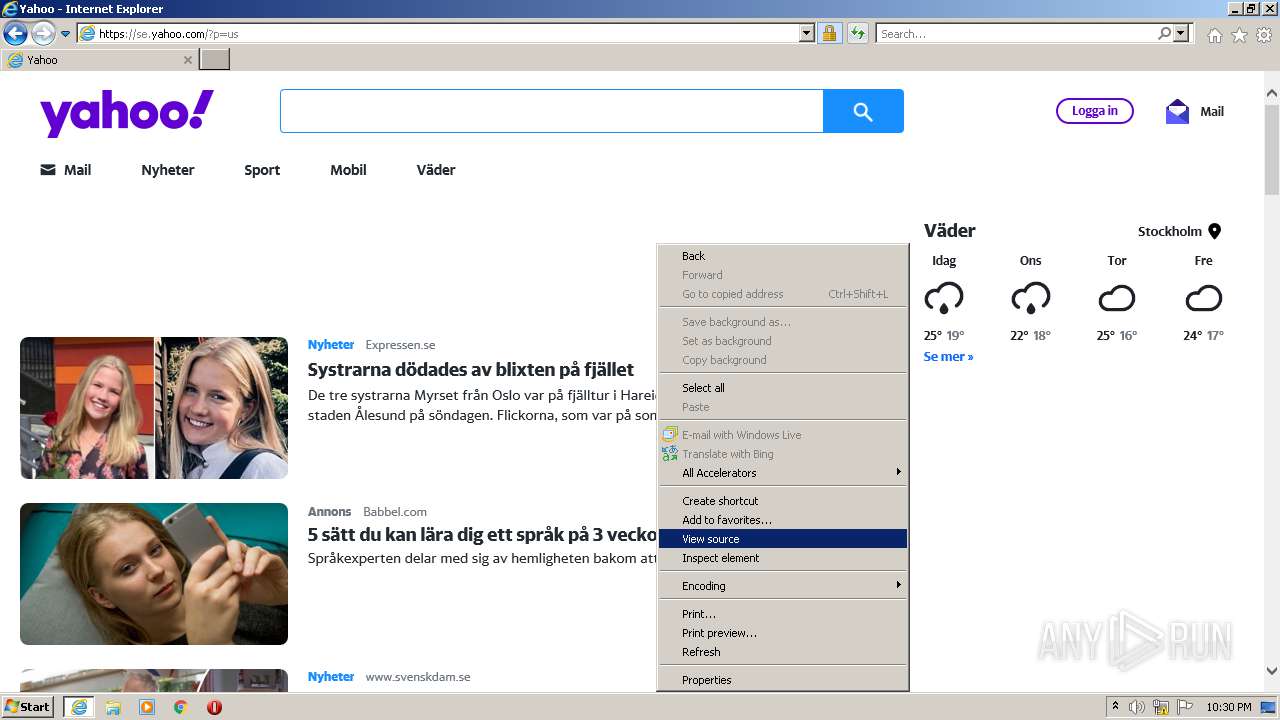
Changes internet zones settings
- iexplore.exe (PID: 2916)
Application launched itself
- iexplore.exe (PID: 2916)
Creates files in the user directory
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
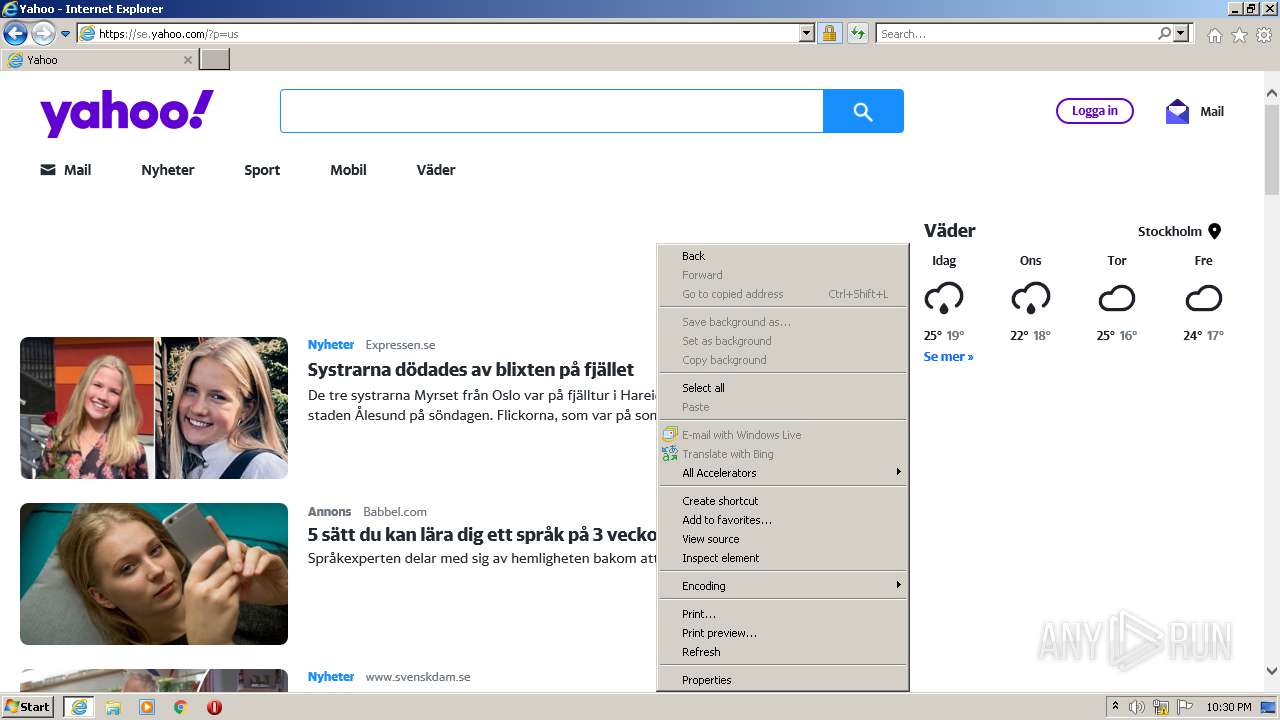
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2916 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.yahoo.com/geo.yahoo.com/p?_E=adperf&outcm=performance&etrg=backgroundPost&usergenf=0&etag=performance,darla&s=2023538075&pvid=0E.zWzEyNy6cBaOcXVRIlgA0MTY1LgAAAABAZGYz&D_bv=1.0.0&D_ts=0&D_v=sdarla_4-6-0&D_l=292,-1,-1,-1,-1,-1,-1,0,3&D_m=1,,4g,0,&test=FPNODEUP100&D_e=pt=index&pd=modal&rid=61jc8hpge0q1v&sid=&bucket=FPNODEUP100&D_p=7,11115211,LREC,300x250,999999,999999,999999,0,0,7833,7,-1,26803111,-1,2,0E.zWzEyNy6cBaOcXVRIlgA0MTY1LgAAAABAZGYz:-1:LREC,2,2,0,2,0,2,0,0,8,1,8,2,0,0,0,0,0,0,3,https%3A//www.yahoo.com,,7,2,3,0,0,-1,0,0,-1,-1,370,370;&D_res={"LREC":[{"name":"https://fw.adsafeprotected.com/rjss/st/554763/54777353/skeleton.js","dur":7040,"st":352,"ssl":null,"dns":null,"conn":null},{"name":"https://contextual.media.net/checksync.php?vsSync=1&cs=10&cv=31&https=1&cid=8CU857501&prvid=251%2C178%2C214%2C238%2C239%2C77%2C99%2C182%2C260%2C184%2C261%2C262%2C188%2C222%2C201%2C147%2C246%2C4%2C126%2C203%2C226%2C10000%2C80%2C229%2C9&purpose1=1&gdprconsent=1&gdpr=0&usp_status=0&usp_consent=1&itype=BRIGHTROLL","dur":707,"st":368,"ssl":null,"dns":null,"conn":null},{"name":"https://pagead2.googlesyndication.com/pcs/activeview?xai=AKAOjsuXqrZVvVXWn6R8a1i267_b62fLgQN350LkxGEcXC8-rthu2iazpvEiTgWJyafkORgu0qYx3mAXg7sdTVKI_wbrEaWbZ3H1E7tvzTar&sig=Cg0ArKJSzLbL9yR5QGlmEAE&id=lidar2&mcvt=1000&p=0,0,251,301&mtos=0,1000,1000,1000,1000&tos=0,1000,0,0,0&v=20210702&bin=7&avms=nio&bs=0,0&mc=0.78&if=1&app=0&itpl=32&adk=0&rs=6&la=0&cr=0&uach=WyJXaW5kb3dzIiwiMTAuMCIsIng4NiIsIiIsIjkwLjAuNDQzMC44NSIsW10sbnVsbCxudWxsLG51bGxd&vs=4&eosm=0&rst=1625319783569&rpt=407&r=v&speed=1","dur":659,"st":1413,"ssl":0,"dns":0,"conn":0},{"name":"https://hblg.media.net/log?log=kfk&evtid=adplog&&prvAccId=134&ckfl=1&pgcatsprig=16&lper=1&mx_tgs=300x250&cbdp=2.809&os_id=101&mx_nsz=1&sc_advUrl=jobs.fidelity.com&spSource=7&vid=881cd13cac604ad4af60eda2423af2cf&pvdTmax=154&s_city=ashburn<ime=150.0&ugd=4&epc=470967883&mx_vsidFlt=false&prvReqId=12259514346077_1291666288_8625413772511&bId=51085220&exp=ssProfile%3D0%7Cebc%3D1%7Csfl%3Dfalse%7Cebv%3D1%7CssBucket%3D0%7Cbfl%3D-100%7Csch%3D1%7C" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2916 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 901
Read events
16 779
Write events
122
Delete events
0
Modification events
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 80015056 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30896814 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 380015212 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30896814 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
33
Text files
138
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\collectConsent[1].htm | html | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_ED812D8F173DDFB351644DCD5A7C2011 | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2WBK7Z8R.txt | text | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_33FA26A74462EC5D83A4FAC7BE23210B | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\site-480c5cfb[1].js | text | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\cerebro_min[1].js | text | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_ED812D8F173DDFB351644DCD5A7C2011 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
122
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2956 | iexplore.exe | GET | 200 | 13.32.145.101:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA5M4BhGVfX8tCX7PHXV%2Bmw%3D | US | der | 471 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAPYPZLIorB8gp5TrTVOpcE%3D | US | der | 471 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 13.32.145.165:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2916 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAEqSO0M9OTV51x6Lt0scao%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2956 | iexplore.exe | 87.248.100.215:443 | www.yahoo.com | Yahoo! UK Services Limited | GB | malicious |
2956 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2956 | iexplore.exe | 205.185.216.10:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2956 | iexplore.exe | 54.76.68.102:443 | guce.yahoo.com | Amazon.com, Inc. | IE | unknown |
2956 | iexplore.exe | 87.248.118.23:443 | s.yimg.com | Yahoo! UK Services Limited | GB | malicious |
2916 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2916 | iexplore.exe | 87.248.118.23:443 | s.yimg.com | Yahoo! UK Services Limited | GB | malicious |
2916 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2956 | iexplore.exe | 87.248.100.214:443 | se.yahoo.com | Yahoo! UK Services Limited | GB | malicious |
2956 | iexplore.exe | 152.199.22.12:443 | aka-cdn.adtech.de | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.yahoo.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
guce.yahoo.com |
| whitelisted |
consent.yahoo.com |
| whitelisted |
s.yimg.com |
| shared |
edge-mcdn.secure.yahoo.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |