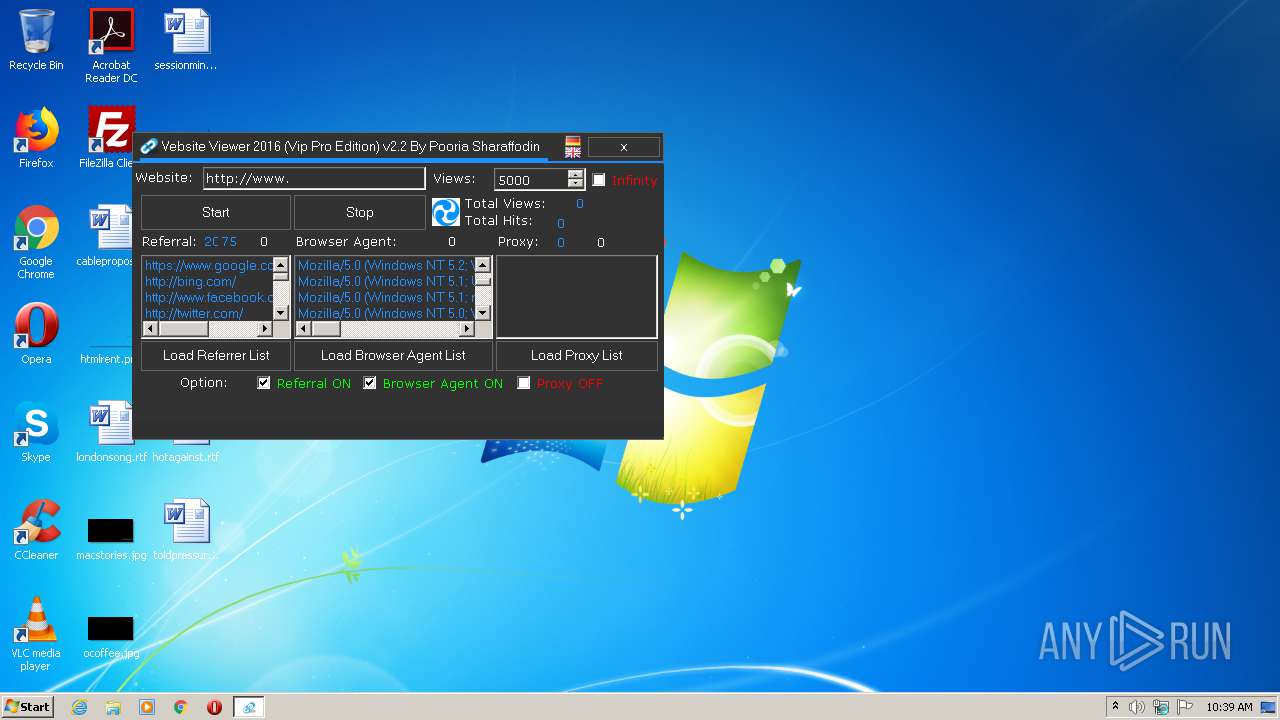
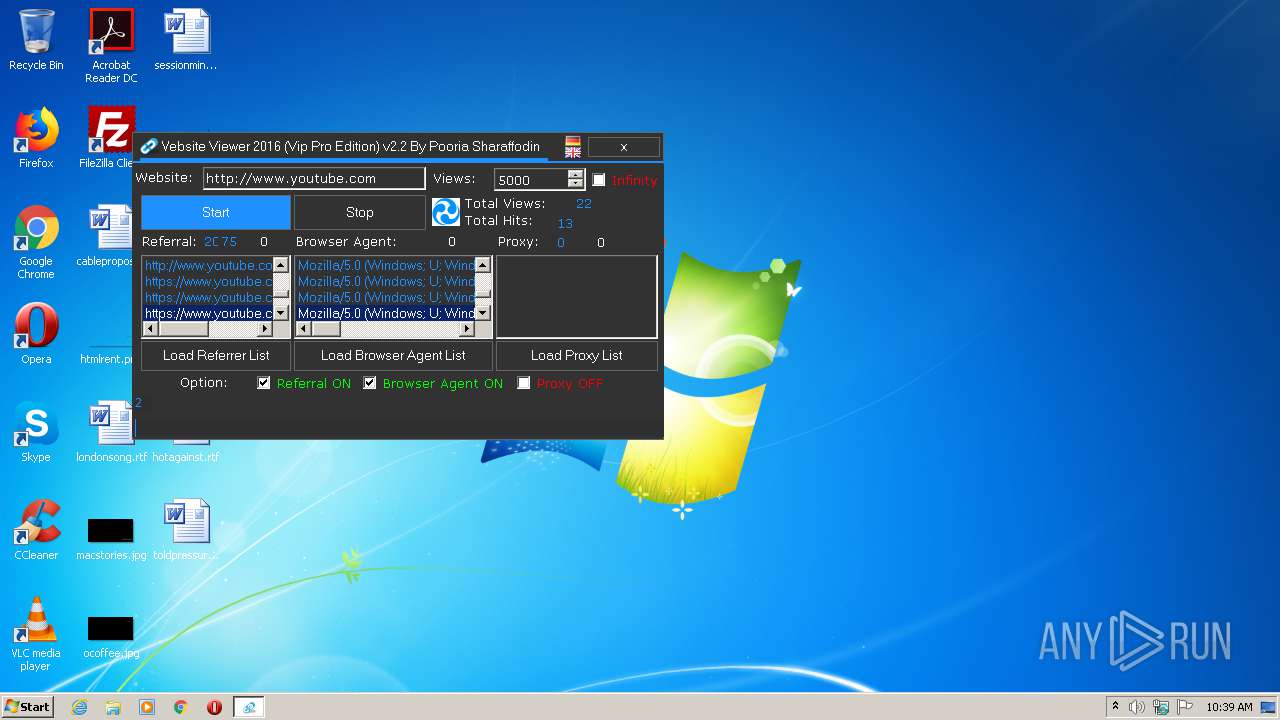
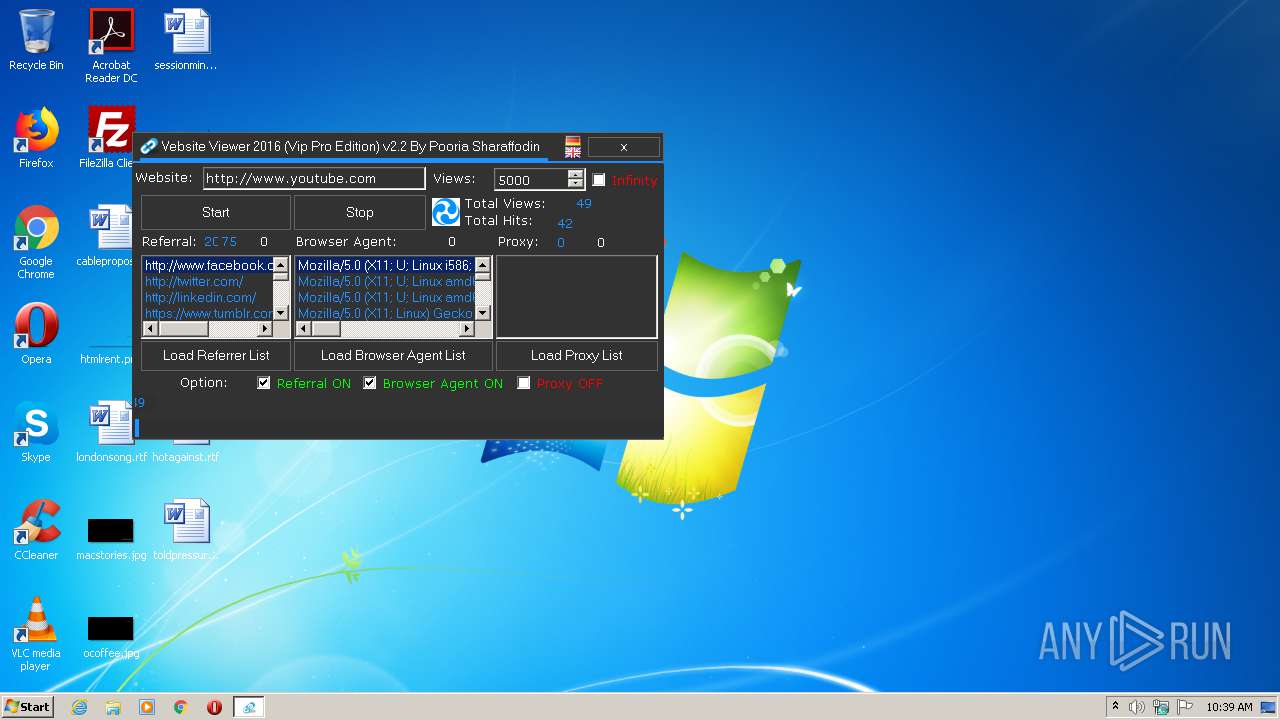
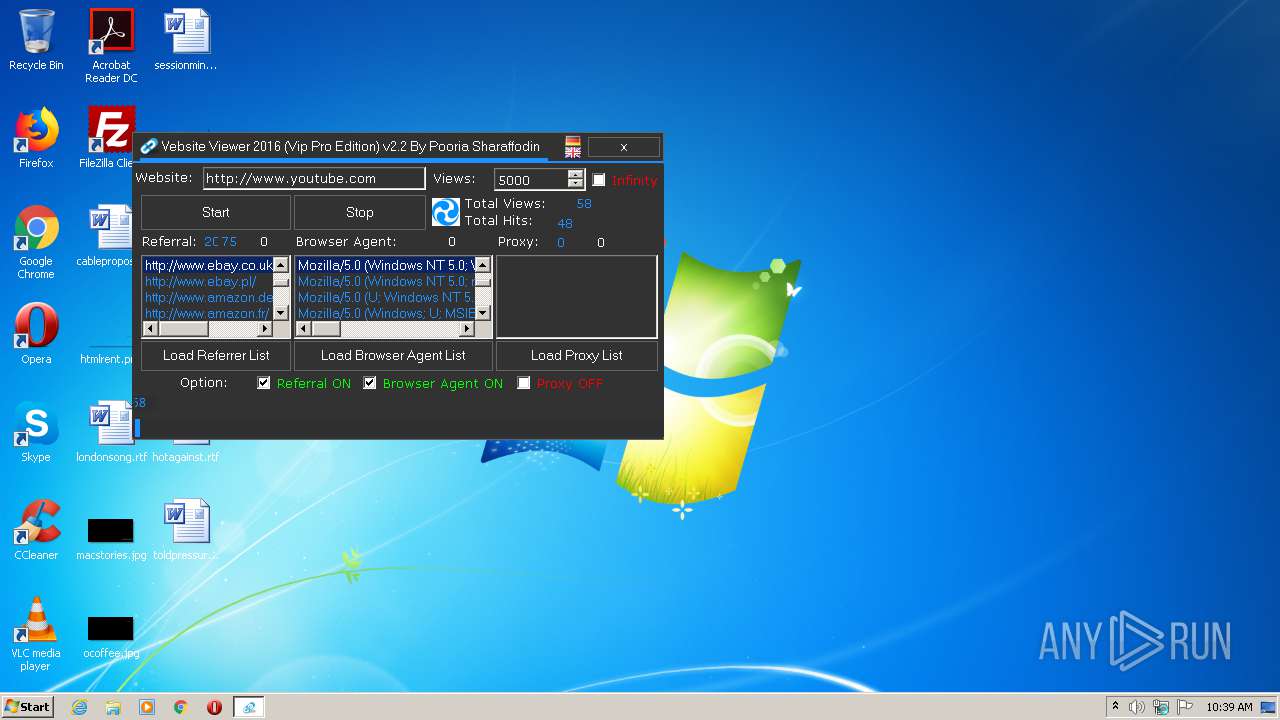
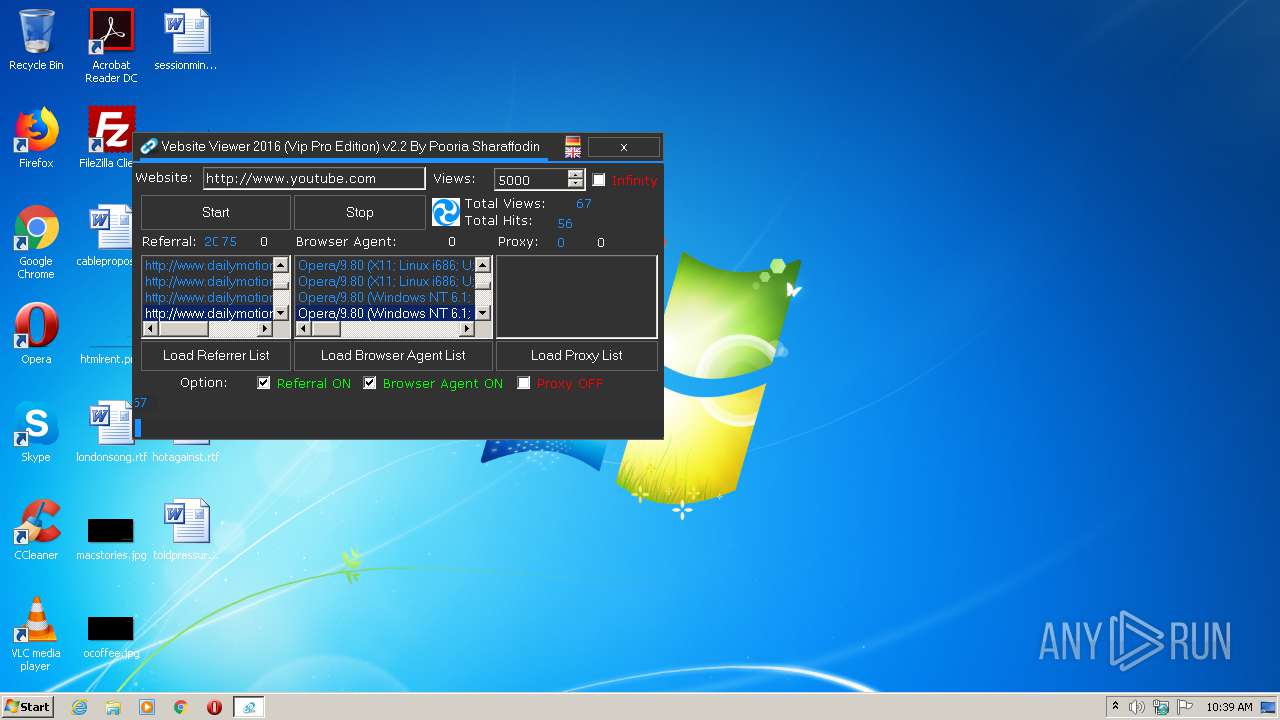
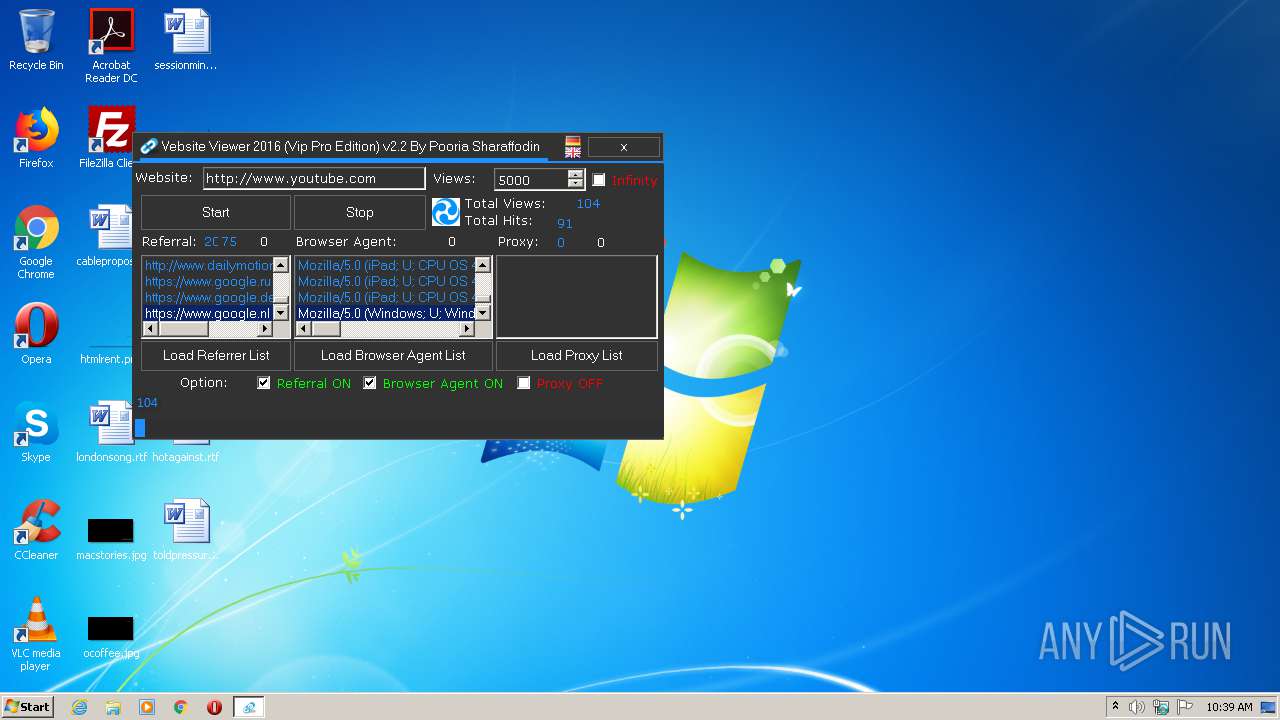
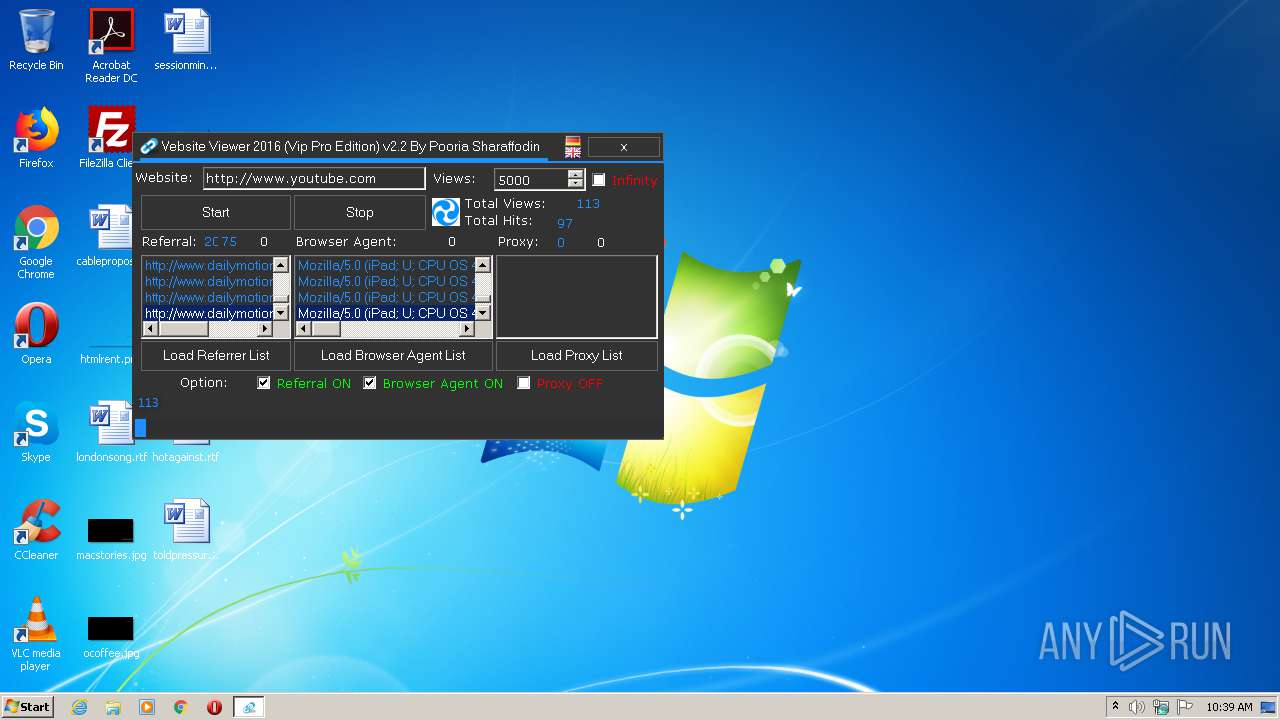
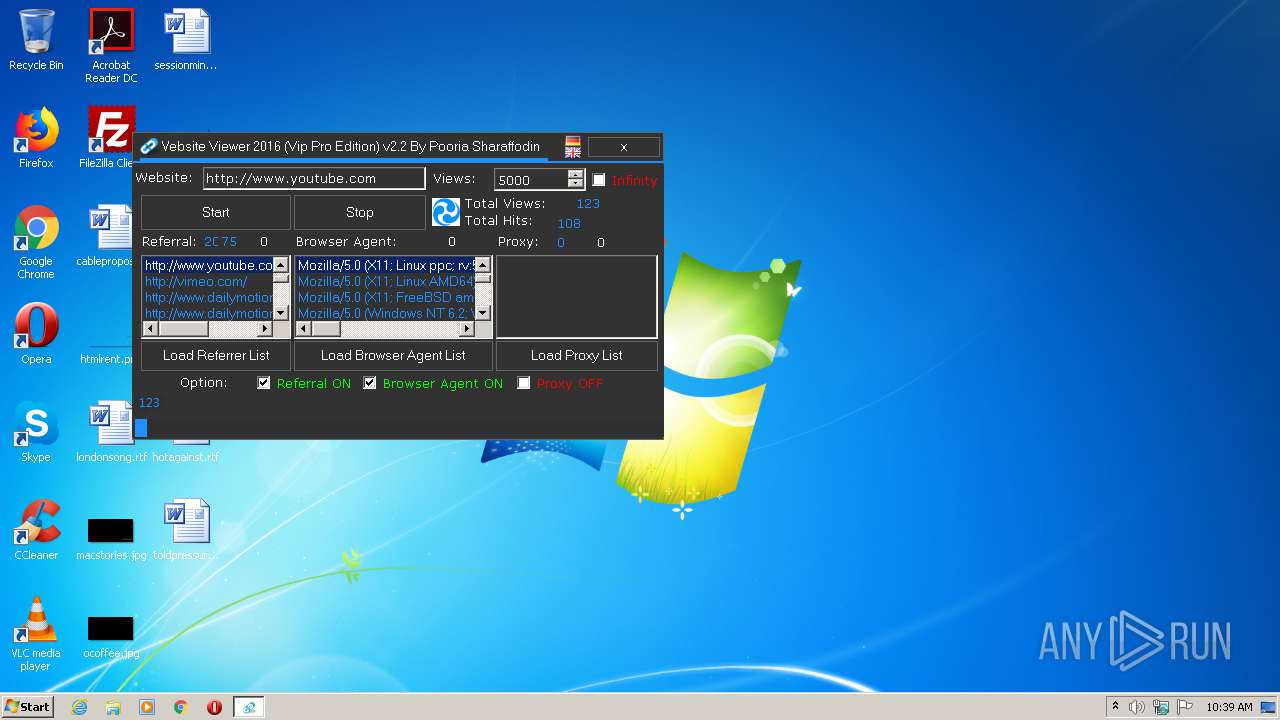
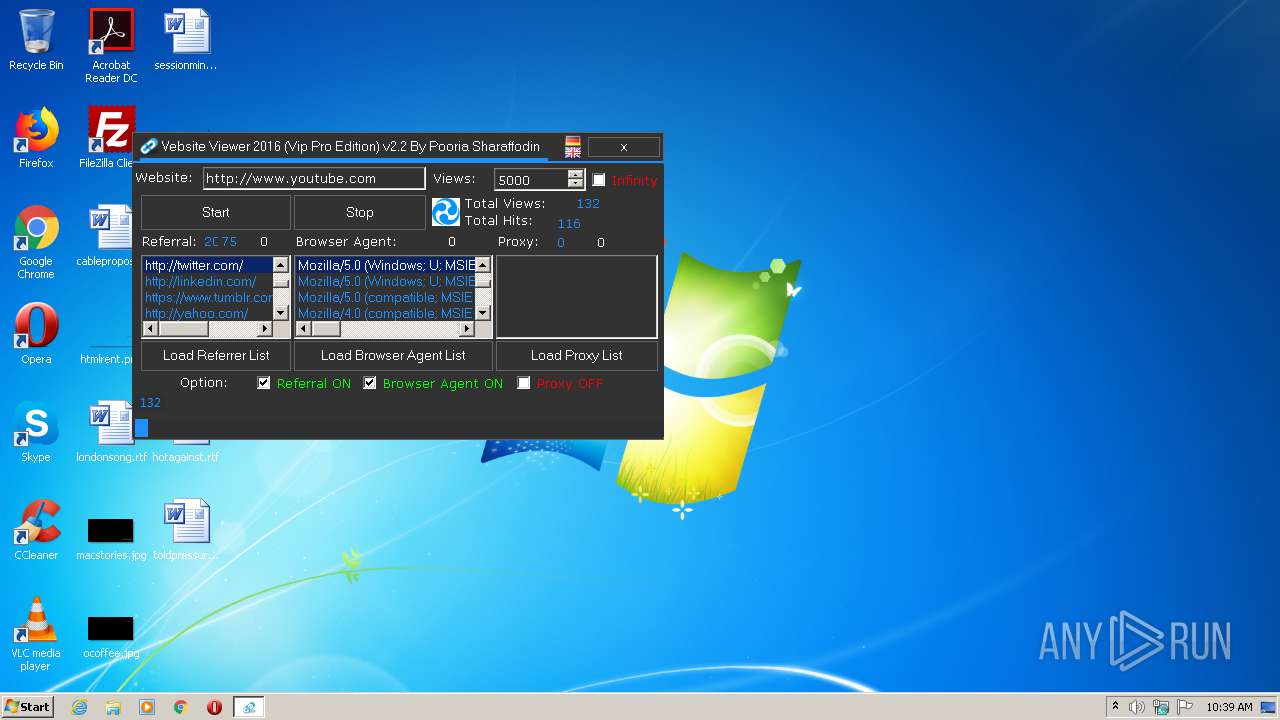
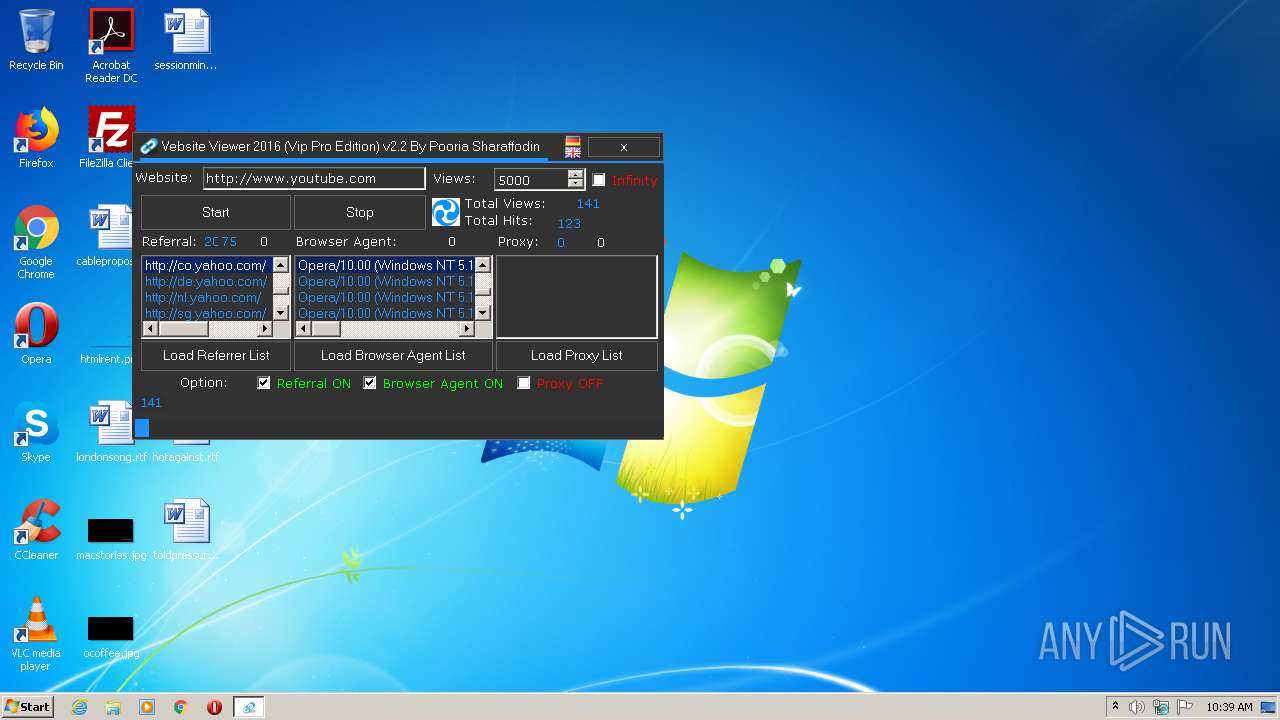
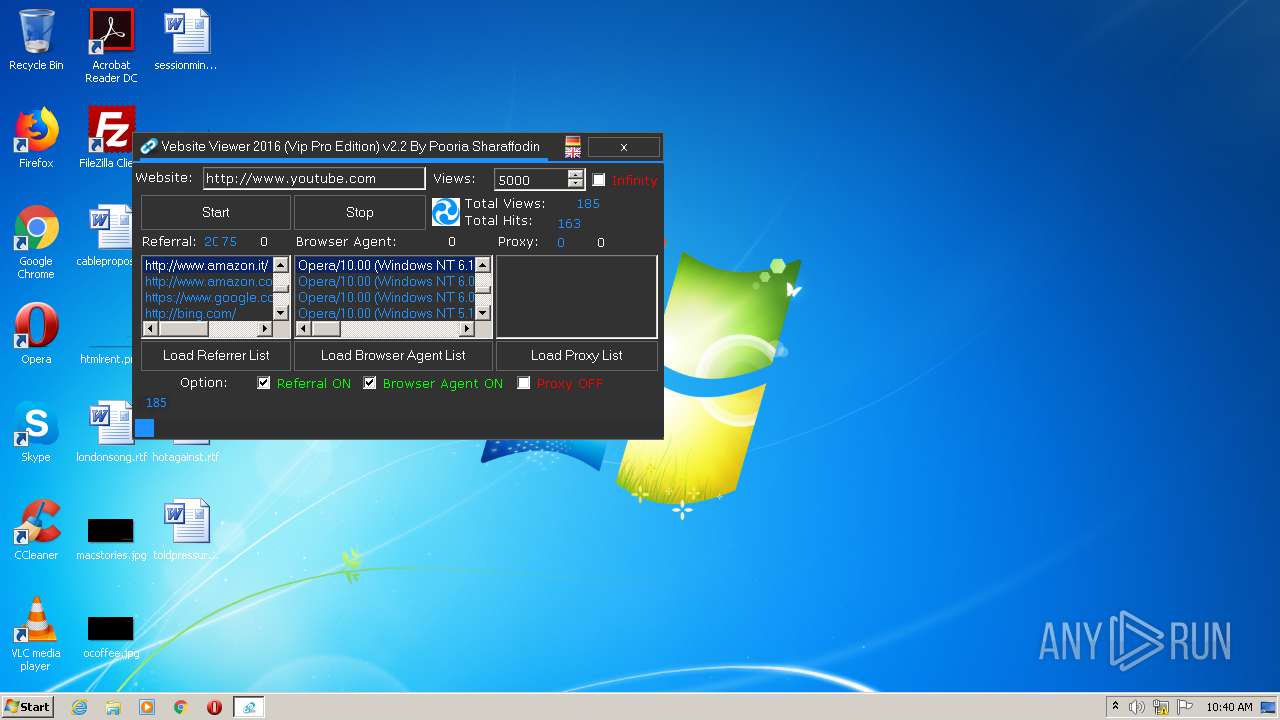
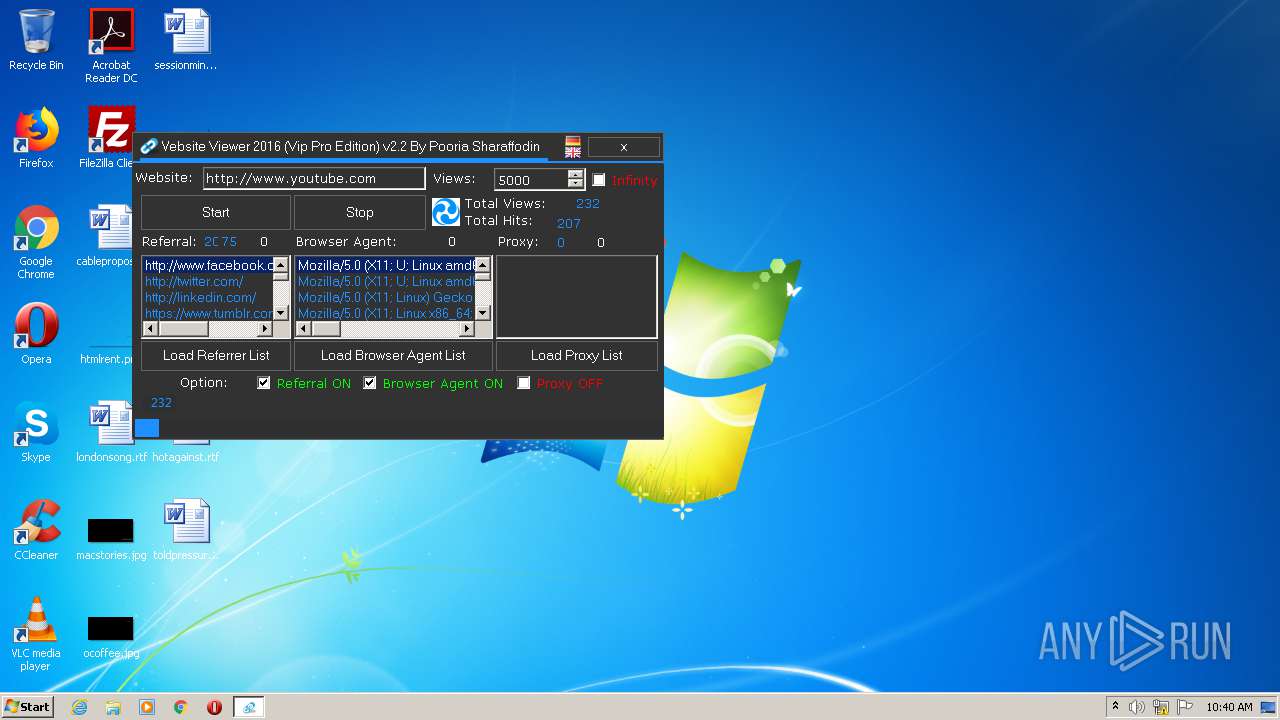
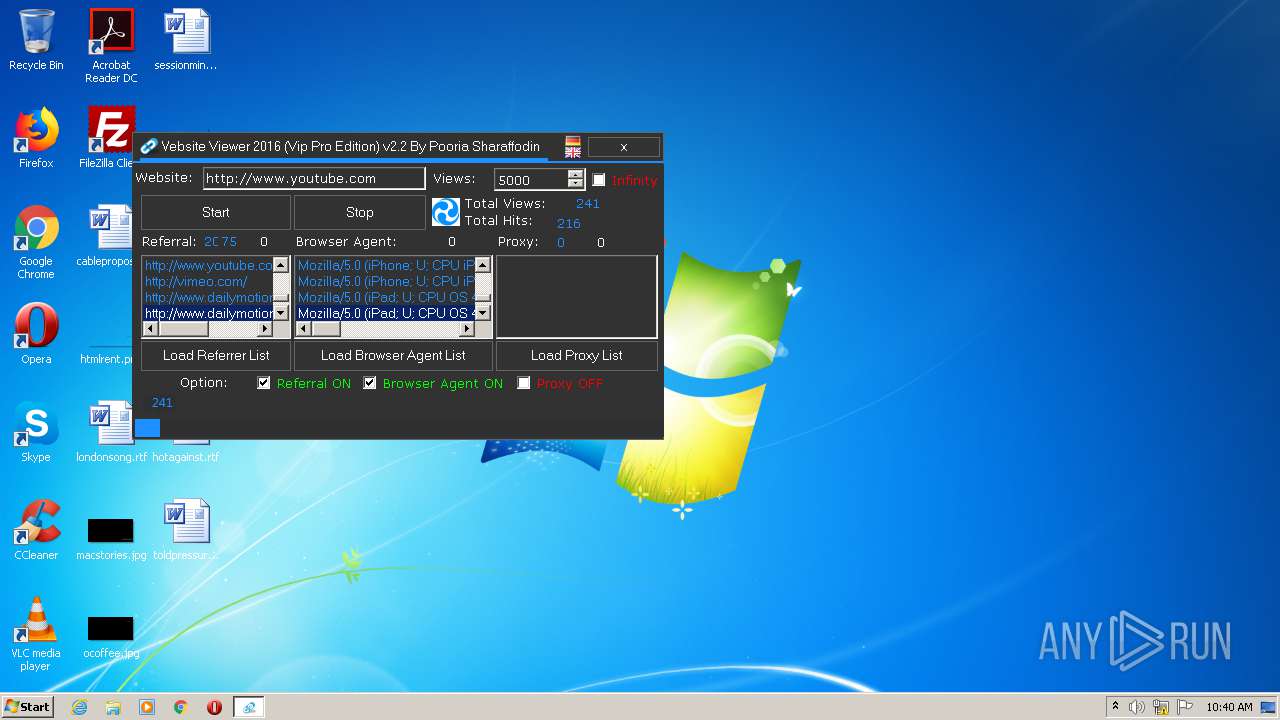
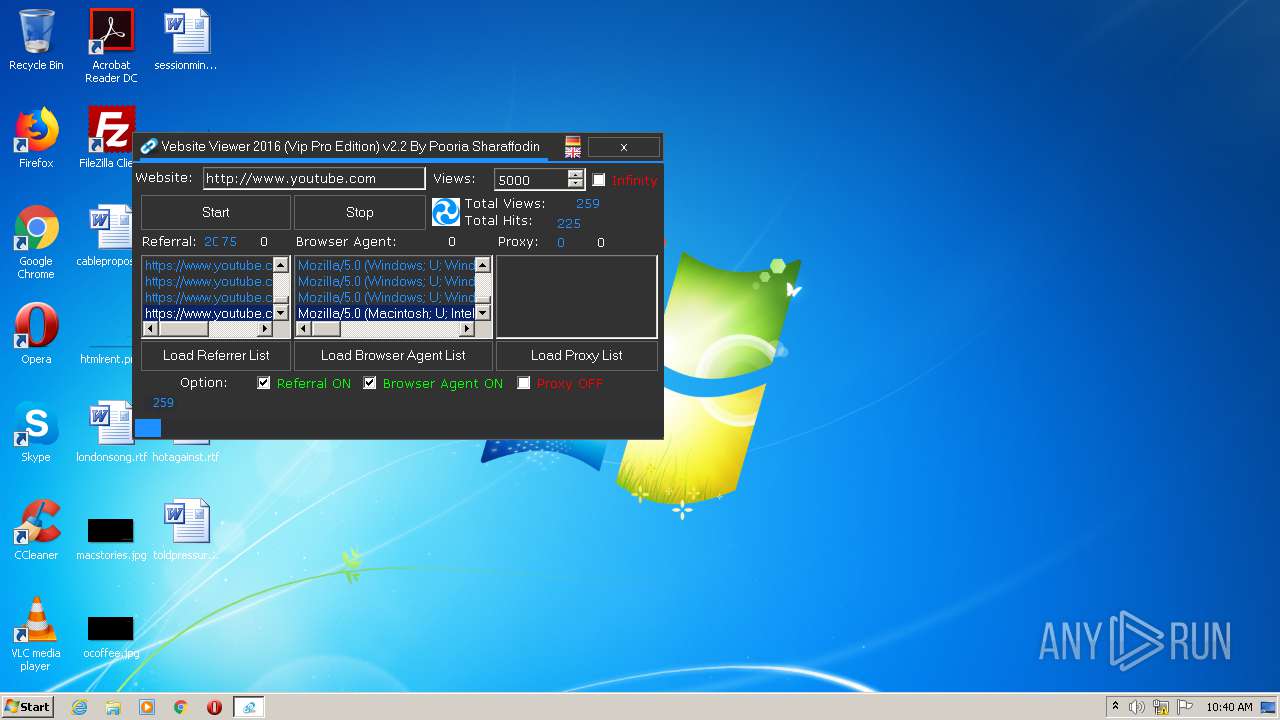
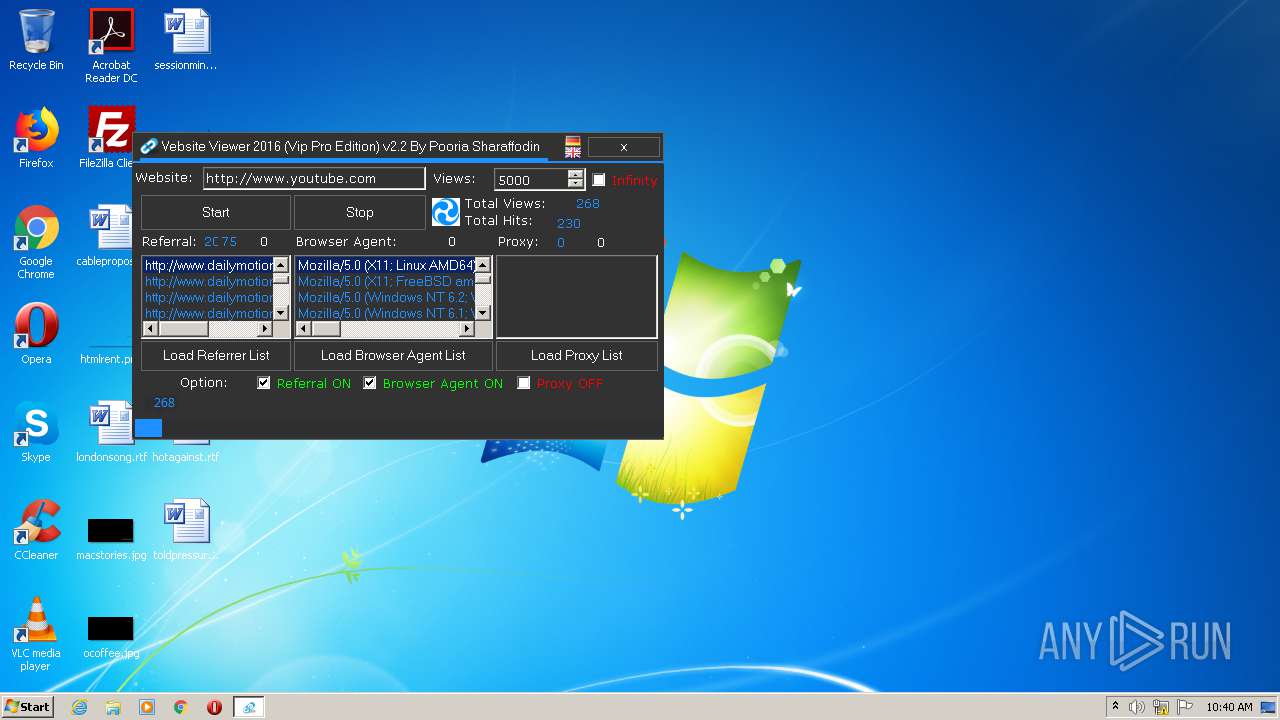
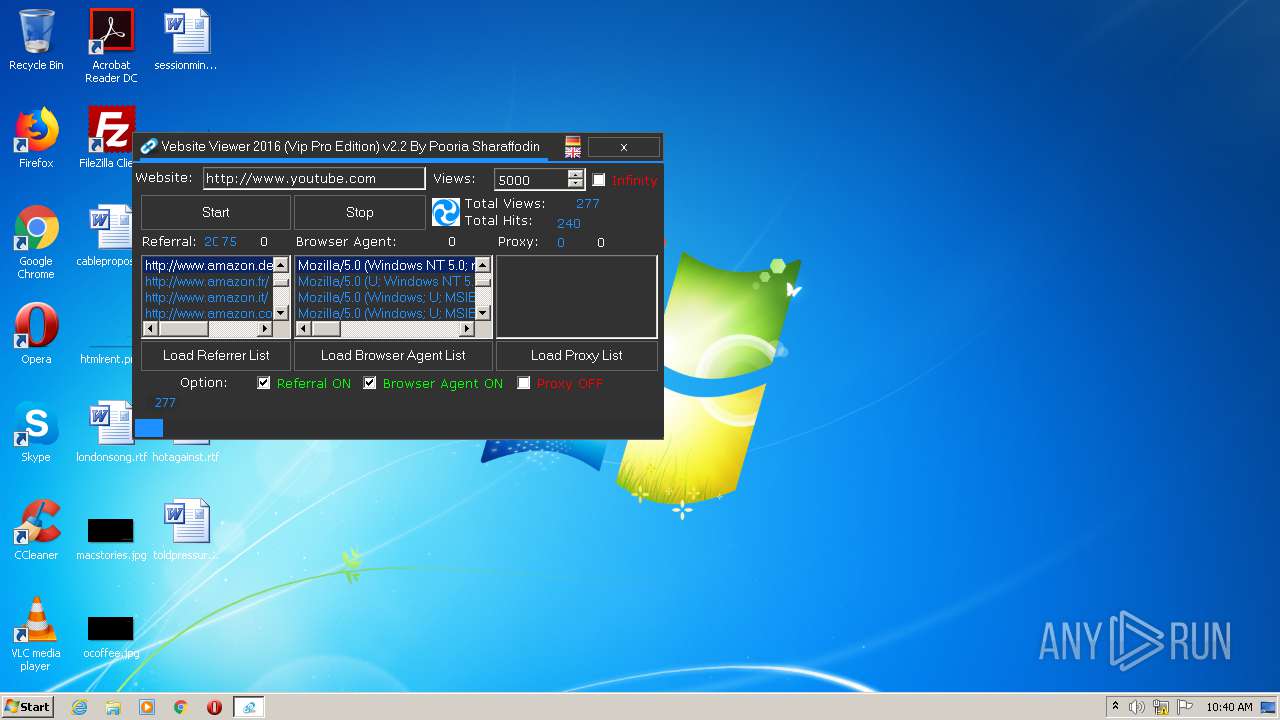
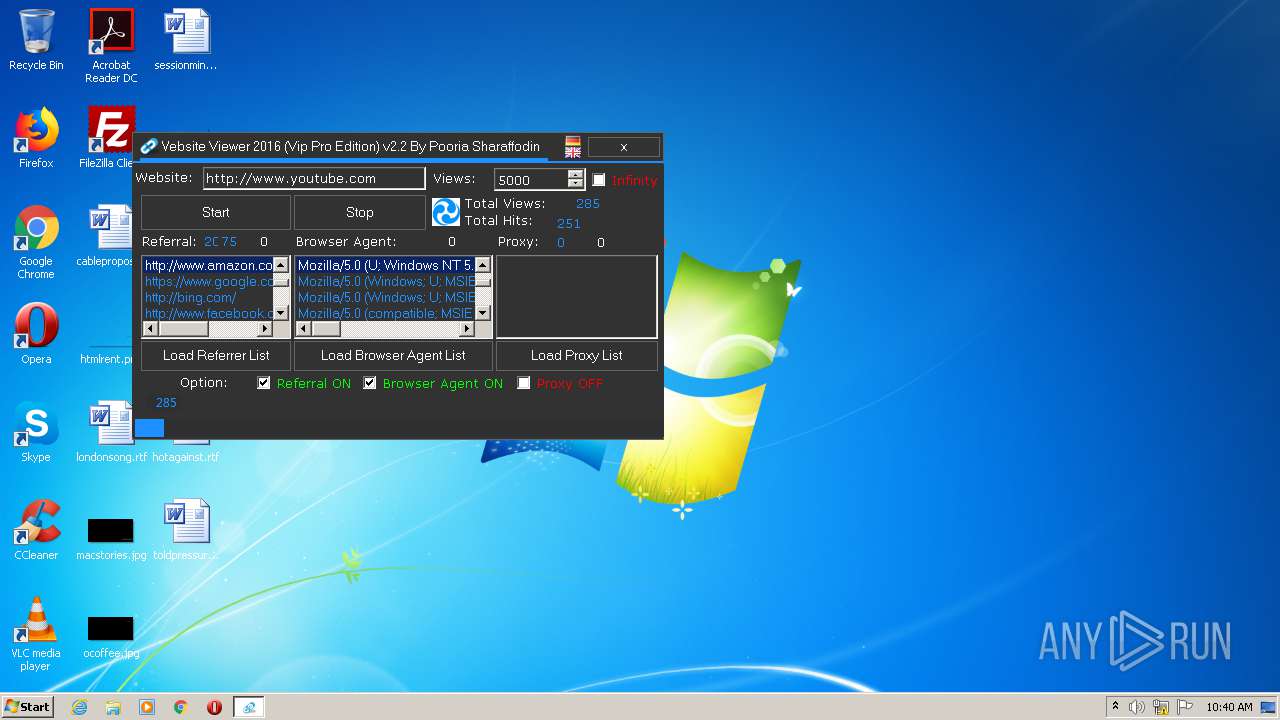
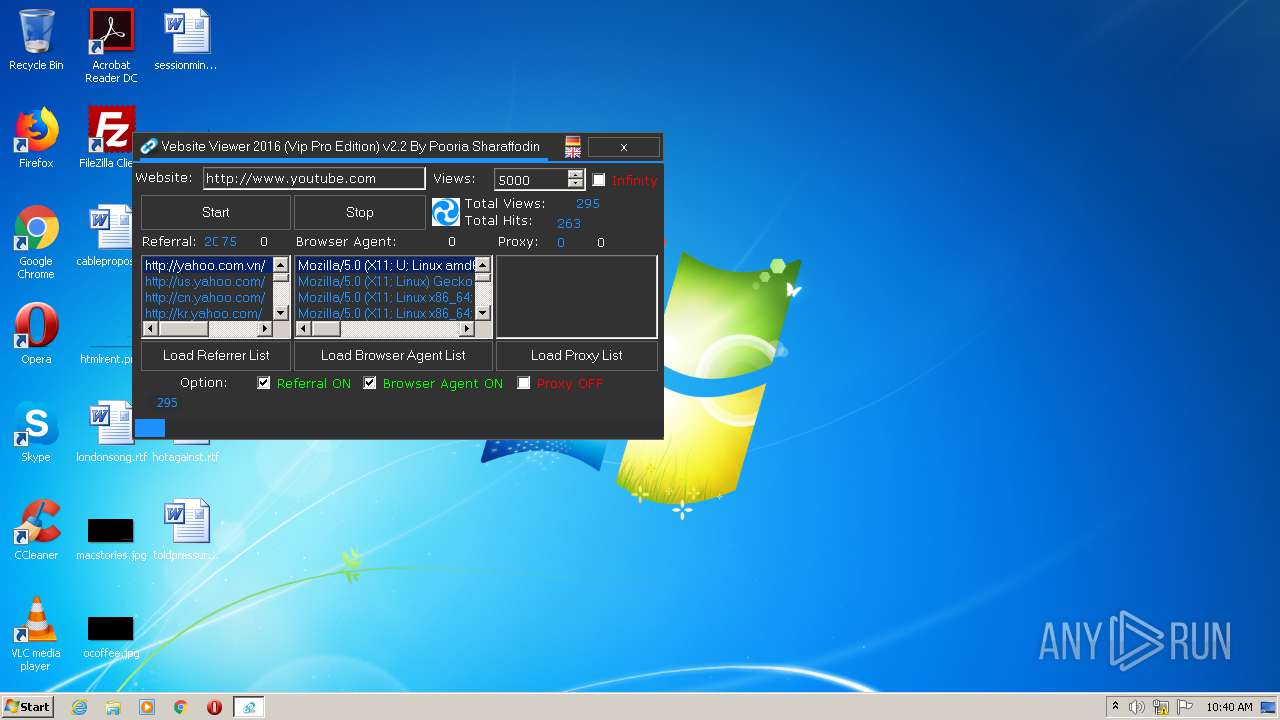
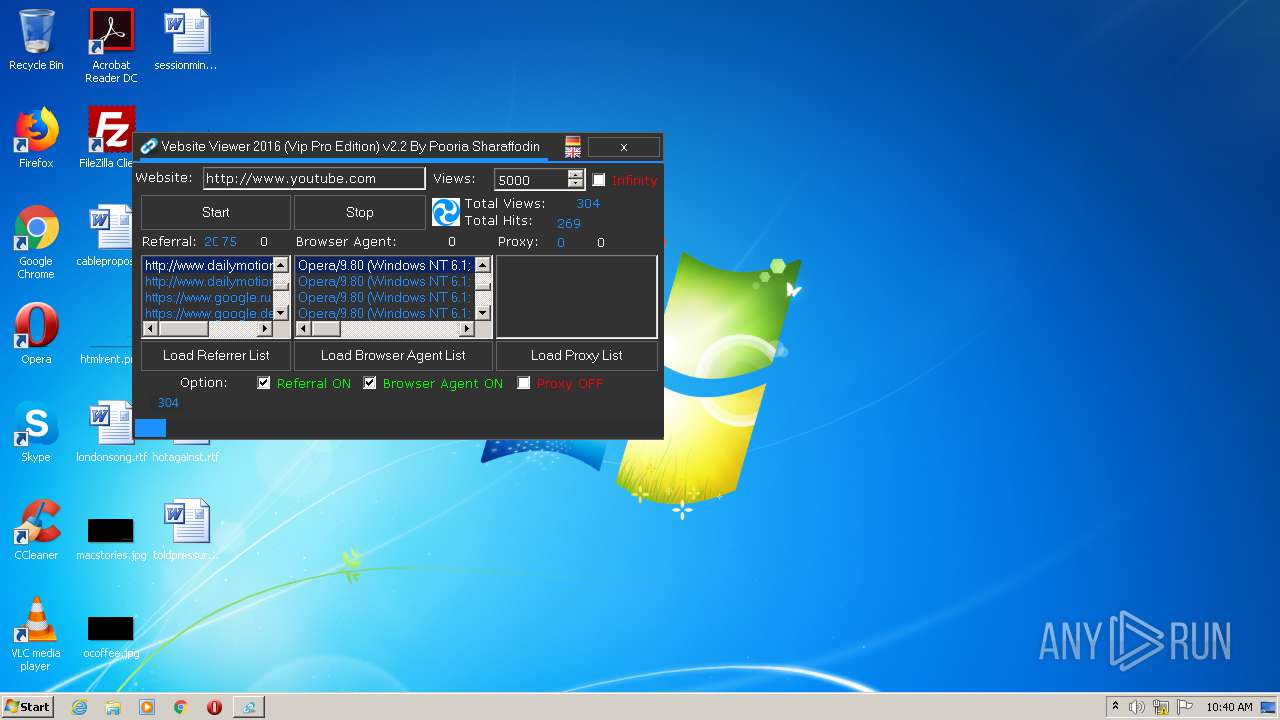
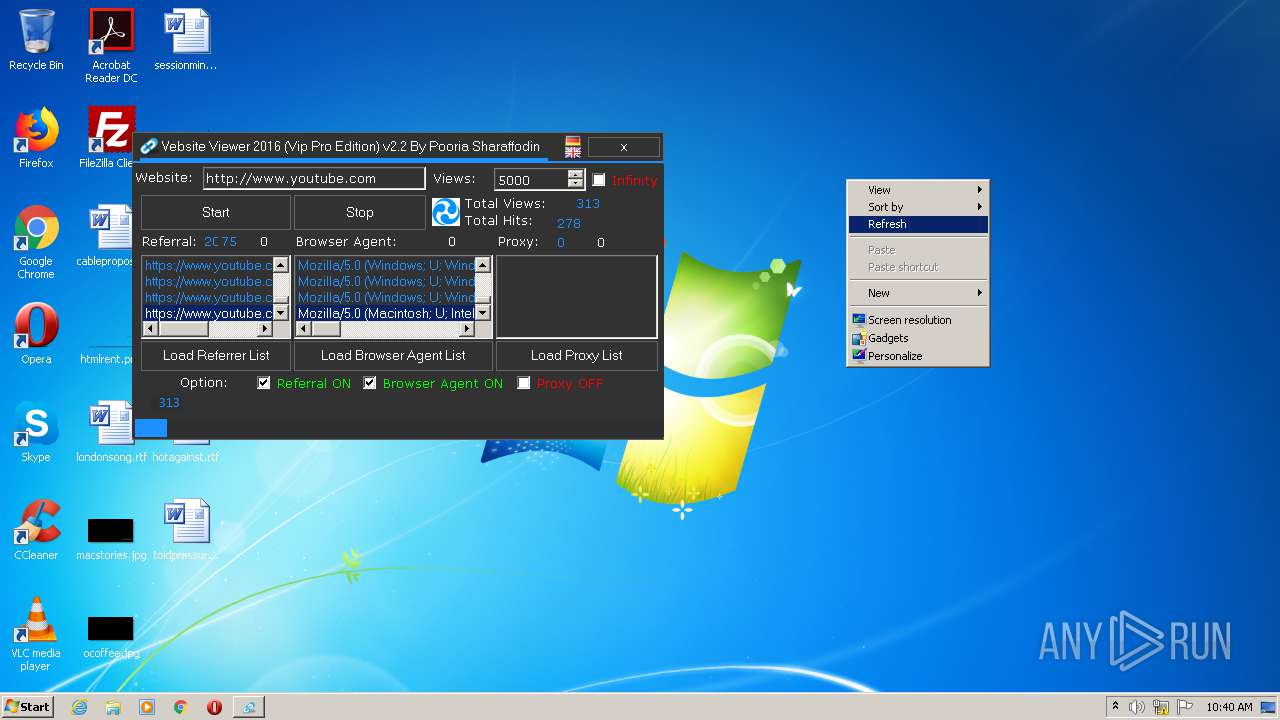
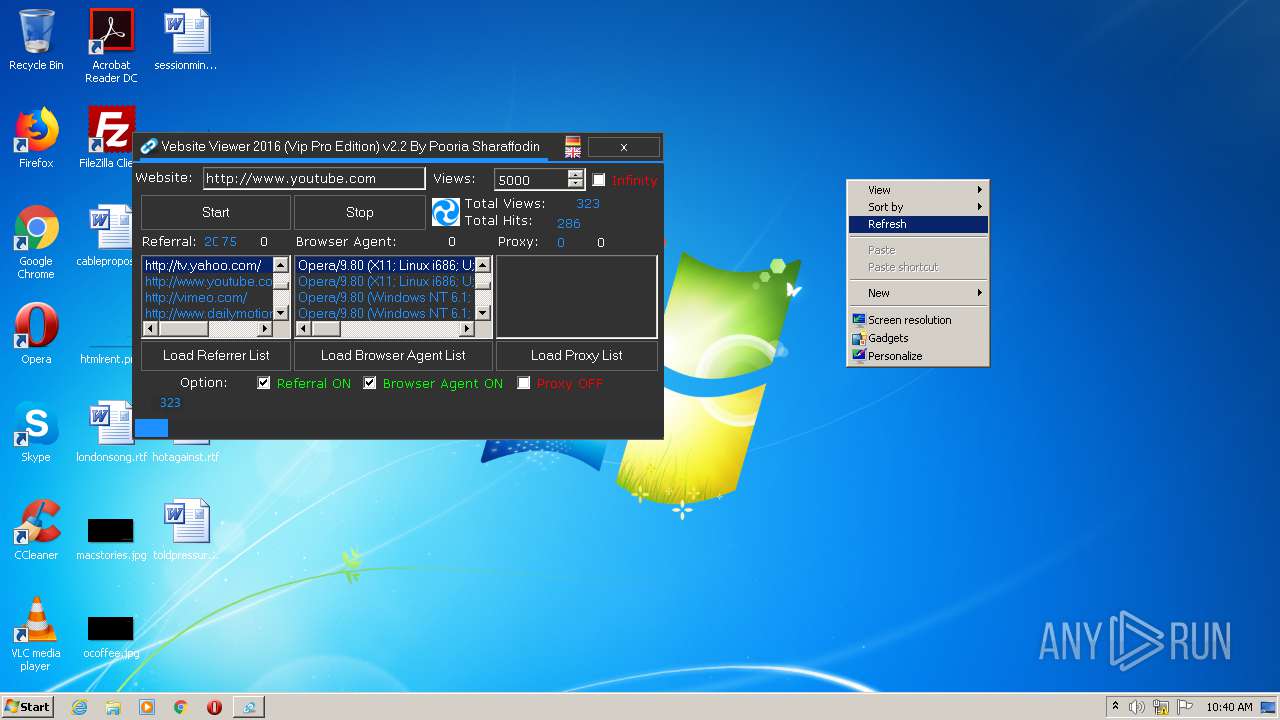
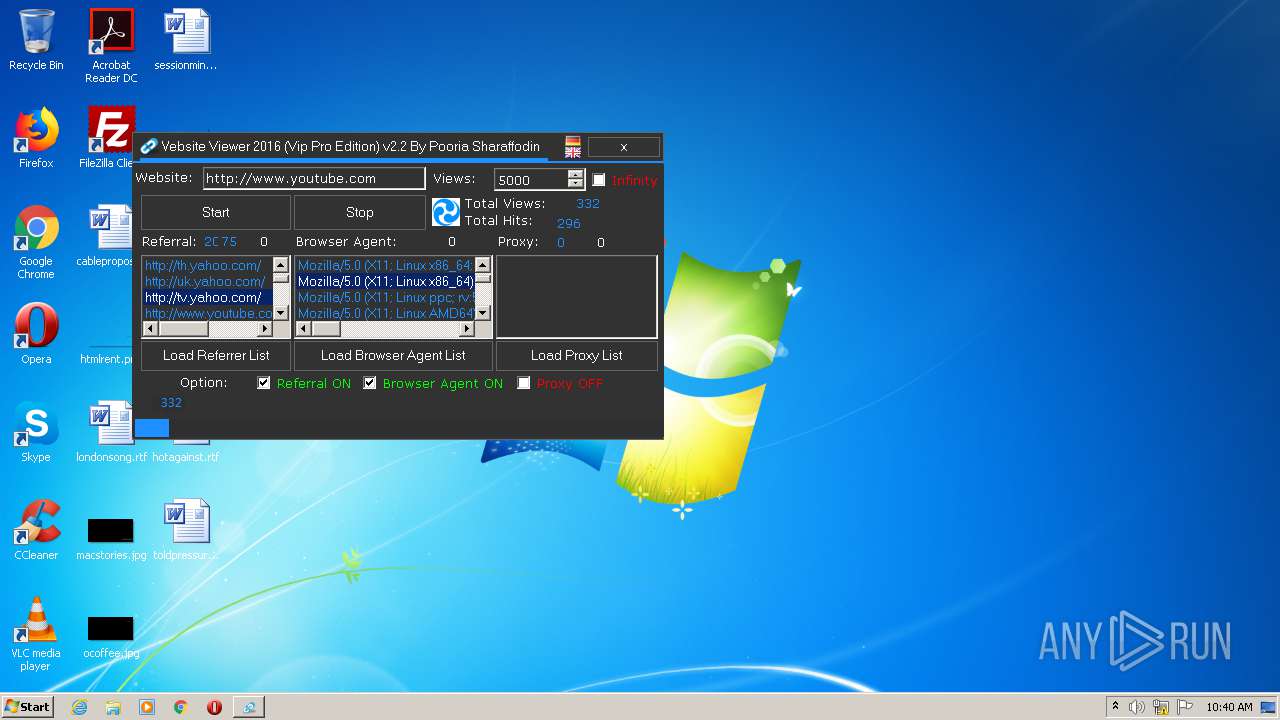
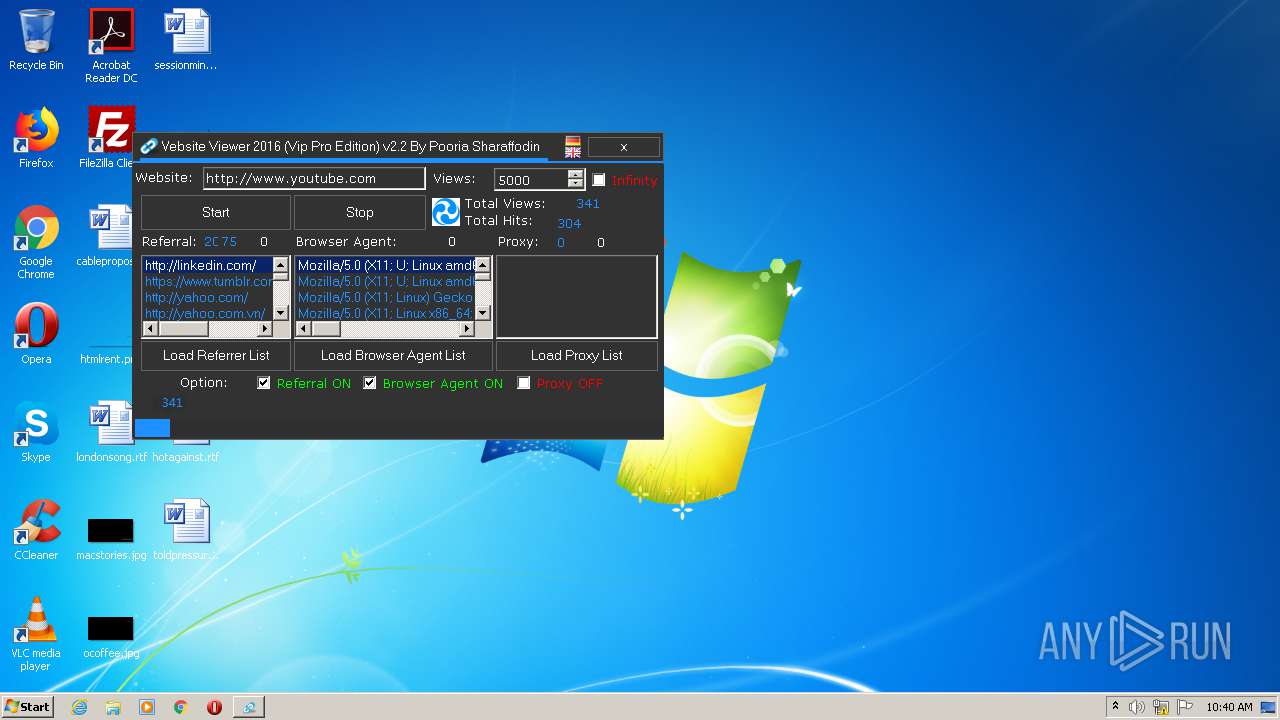
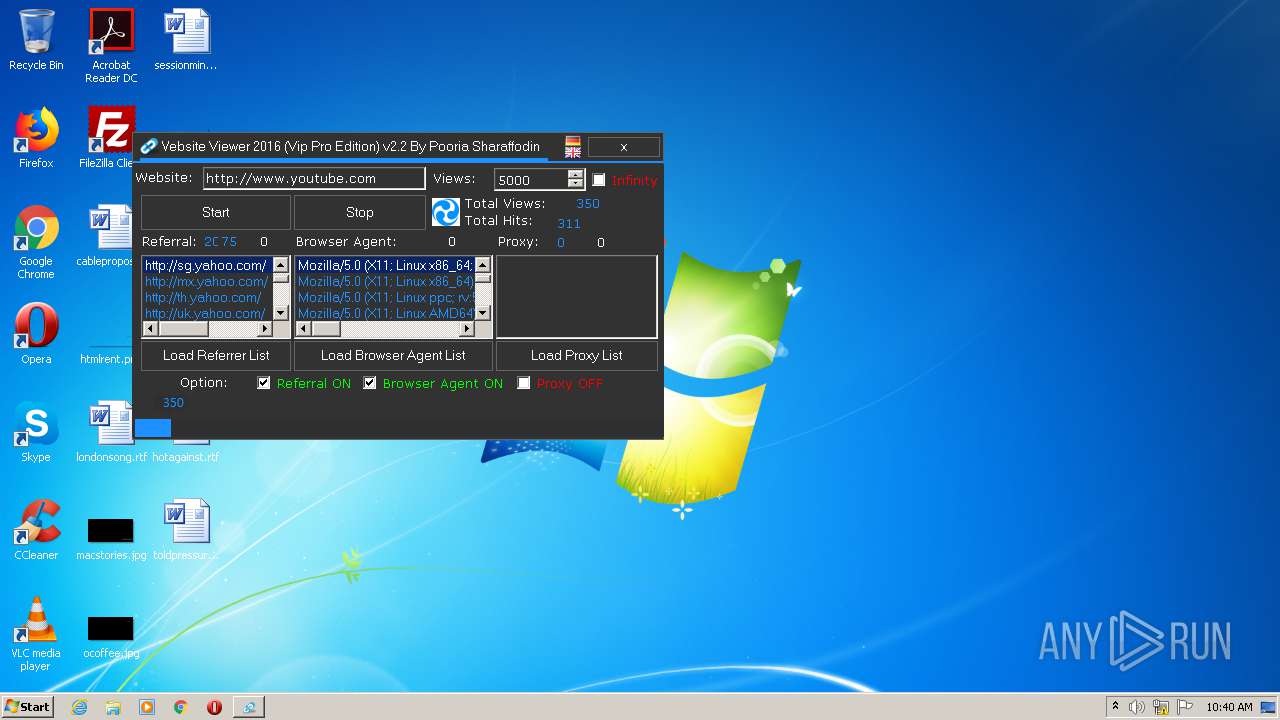
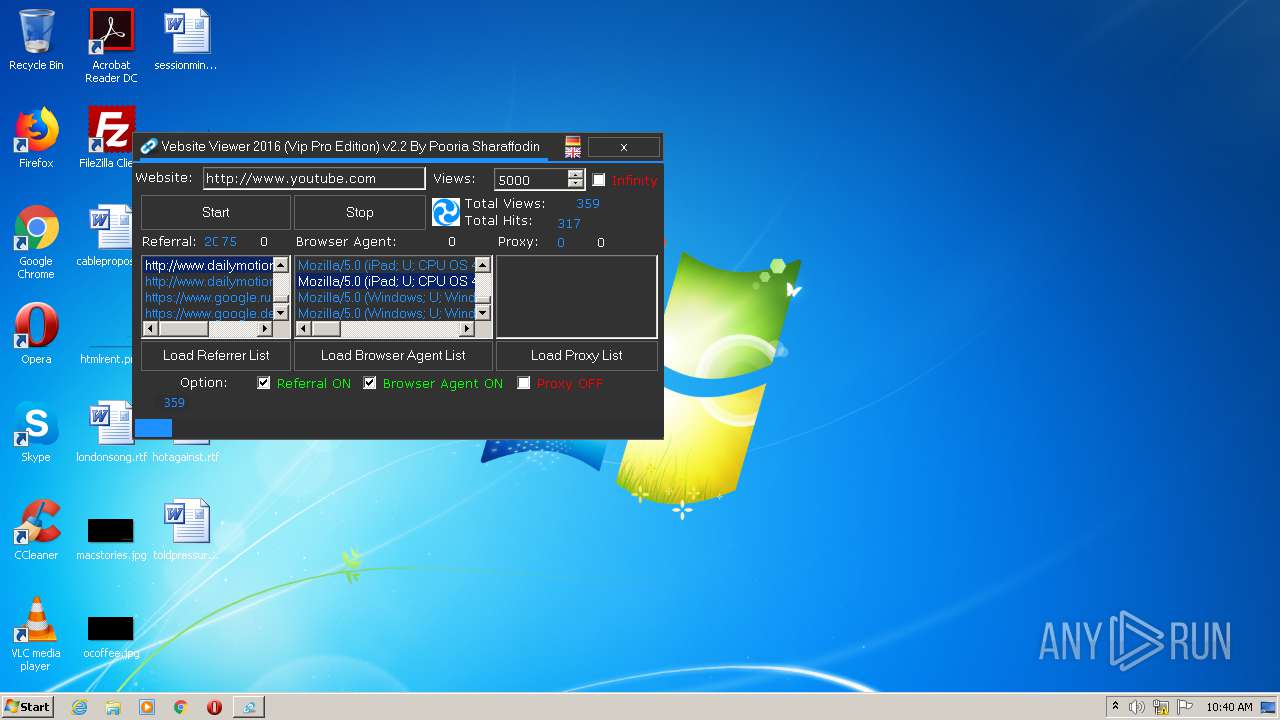
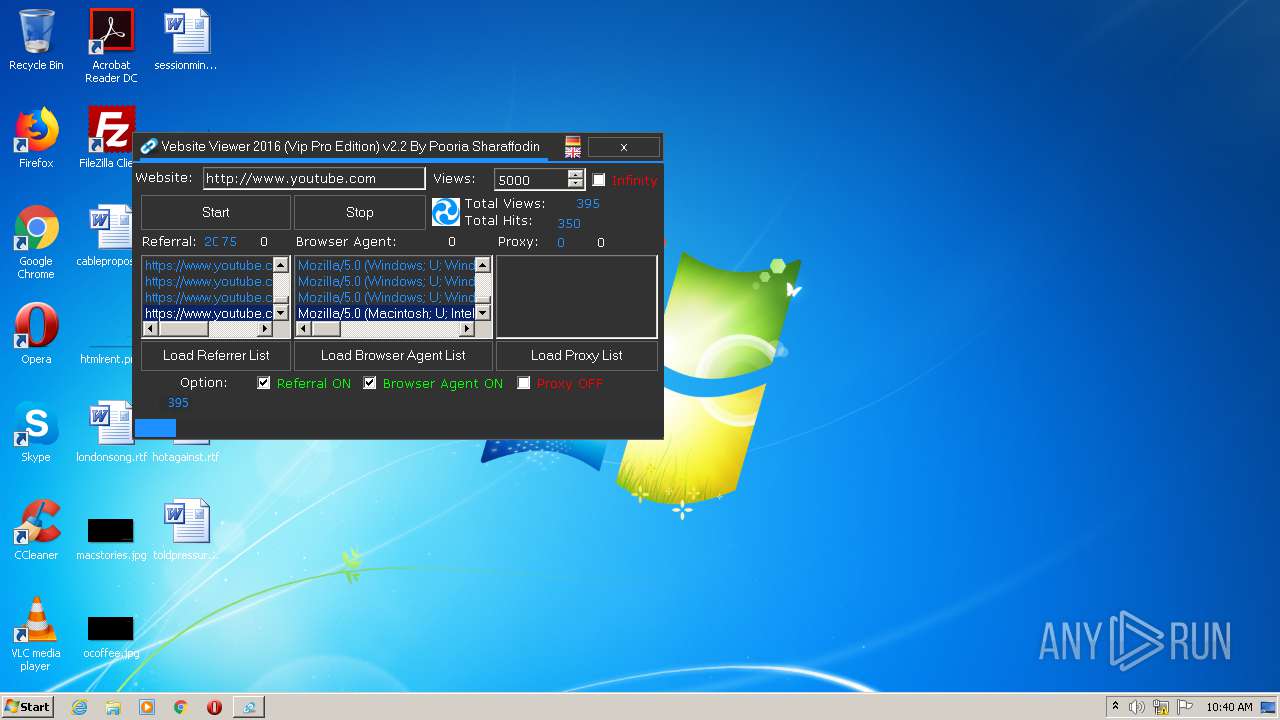
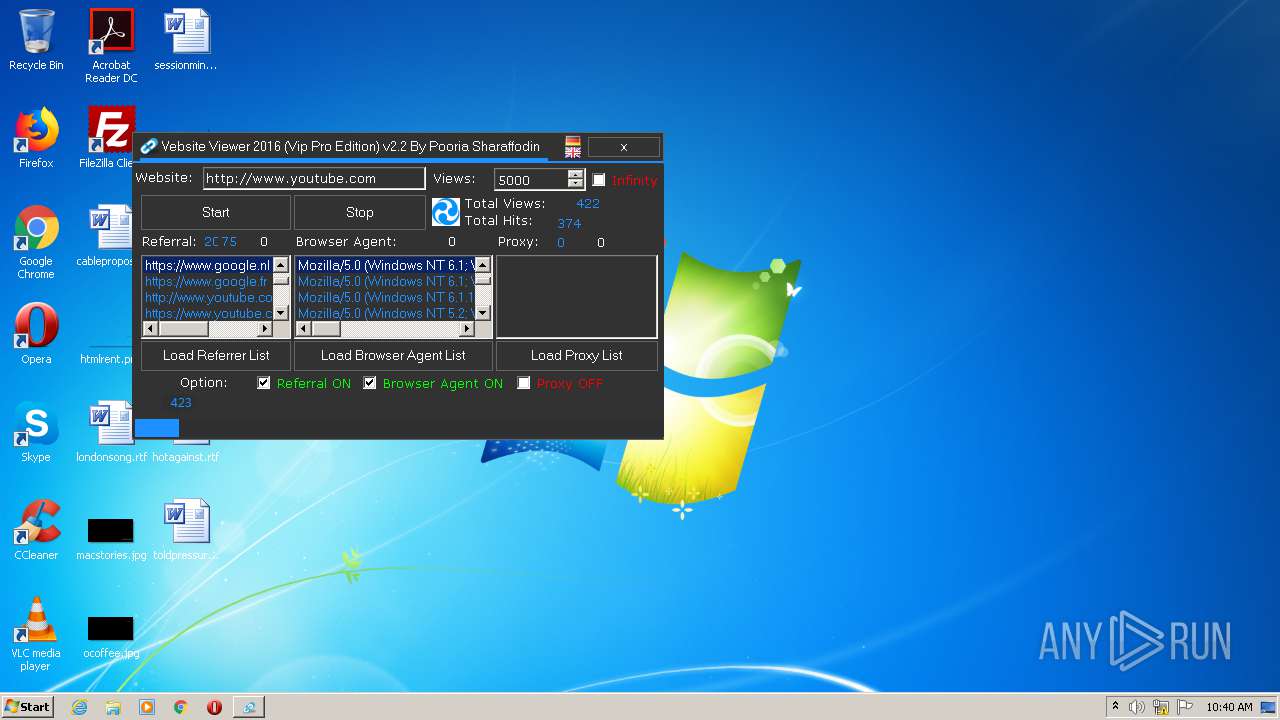
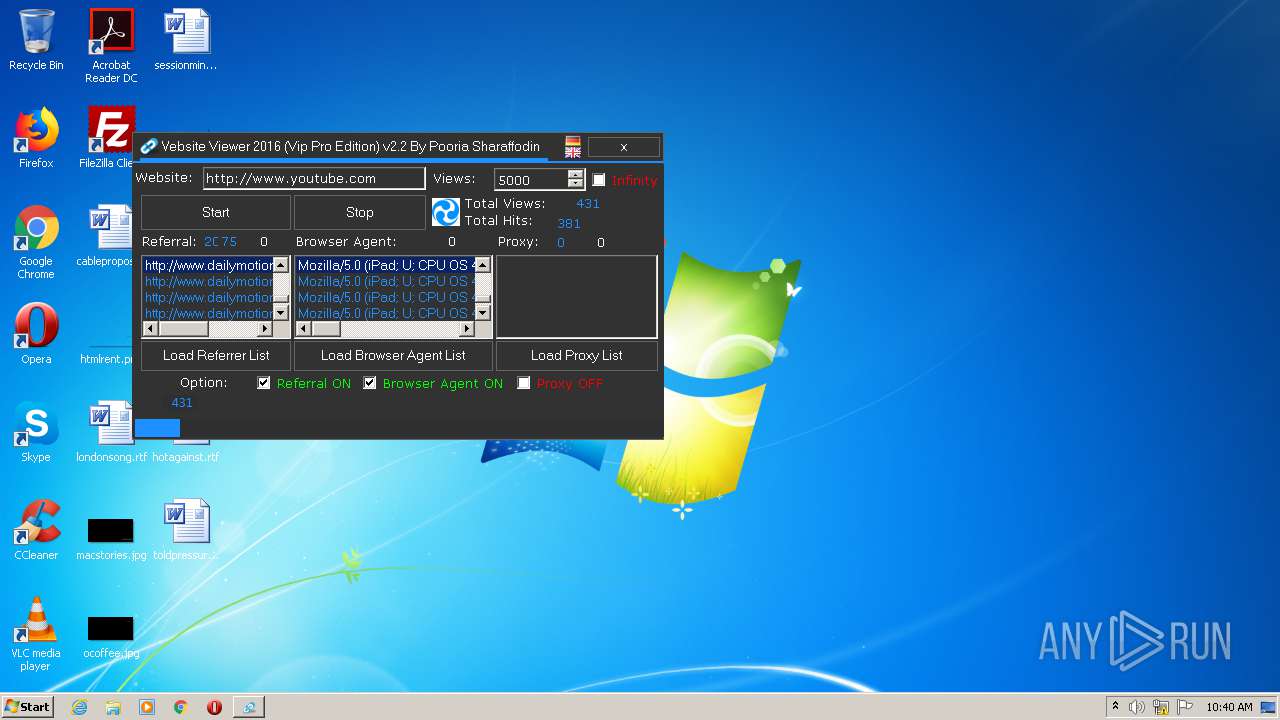
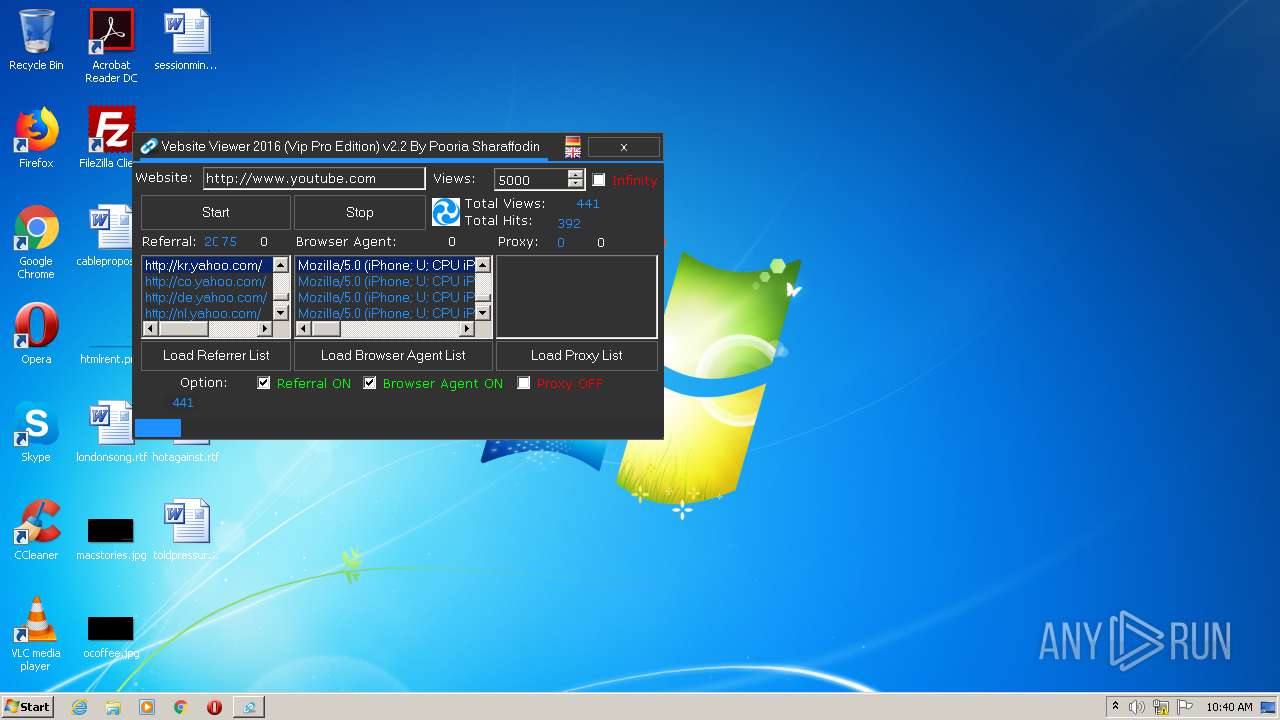
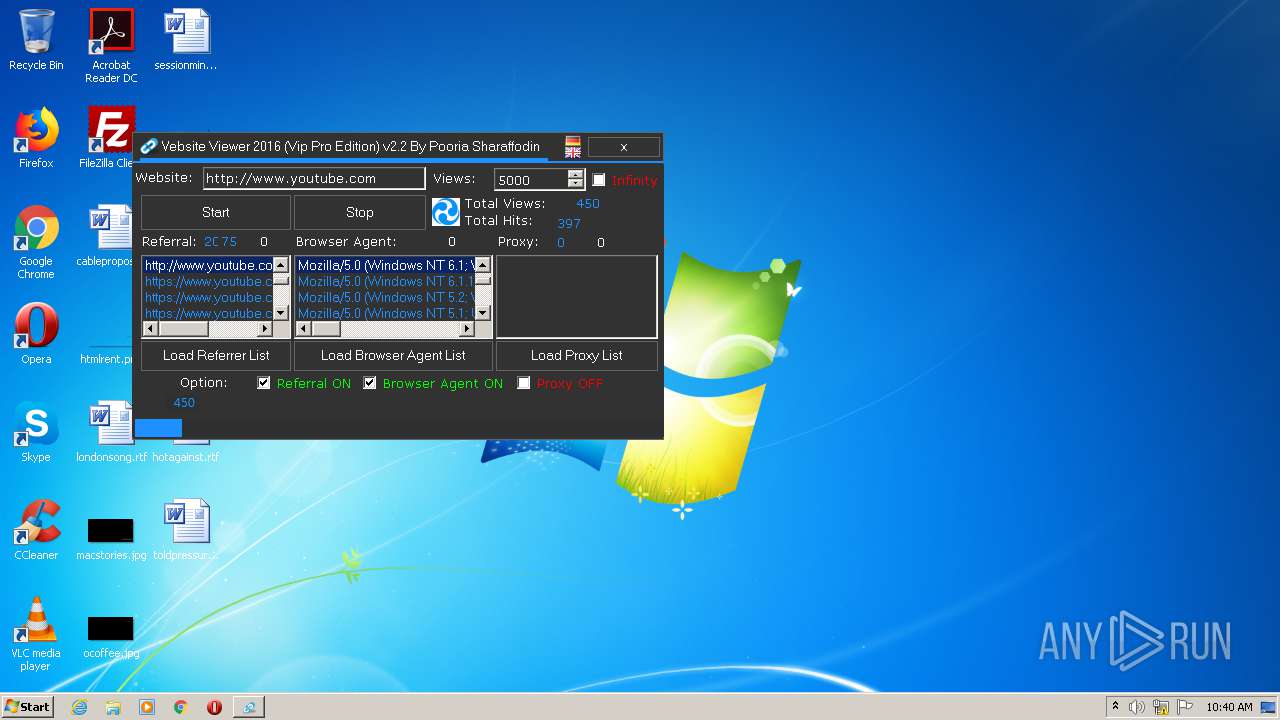
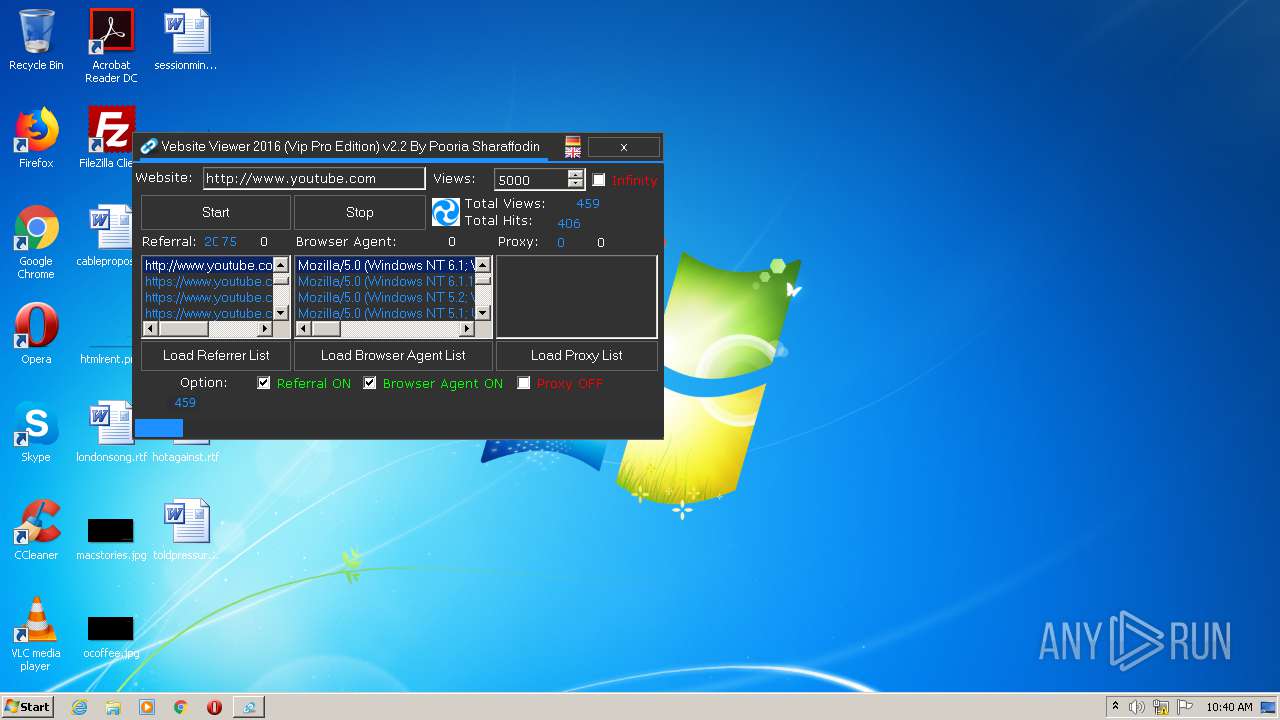
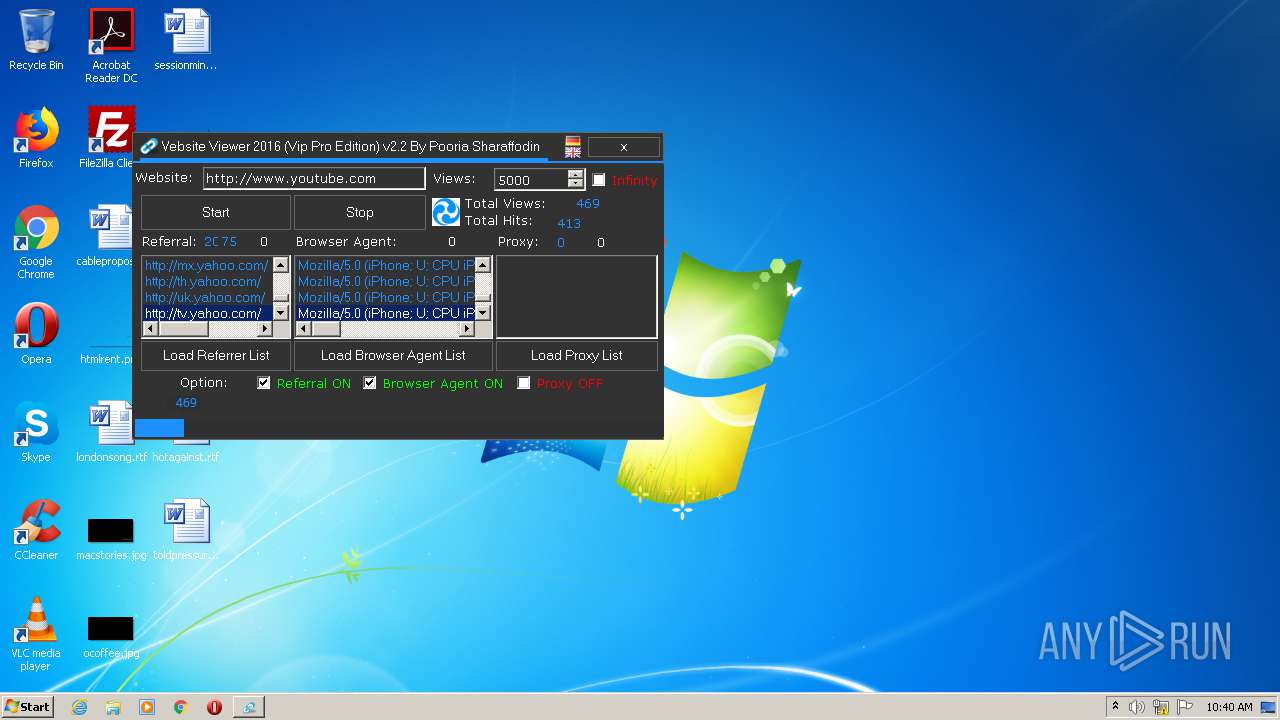
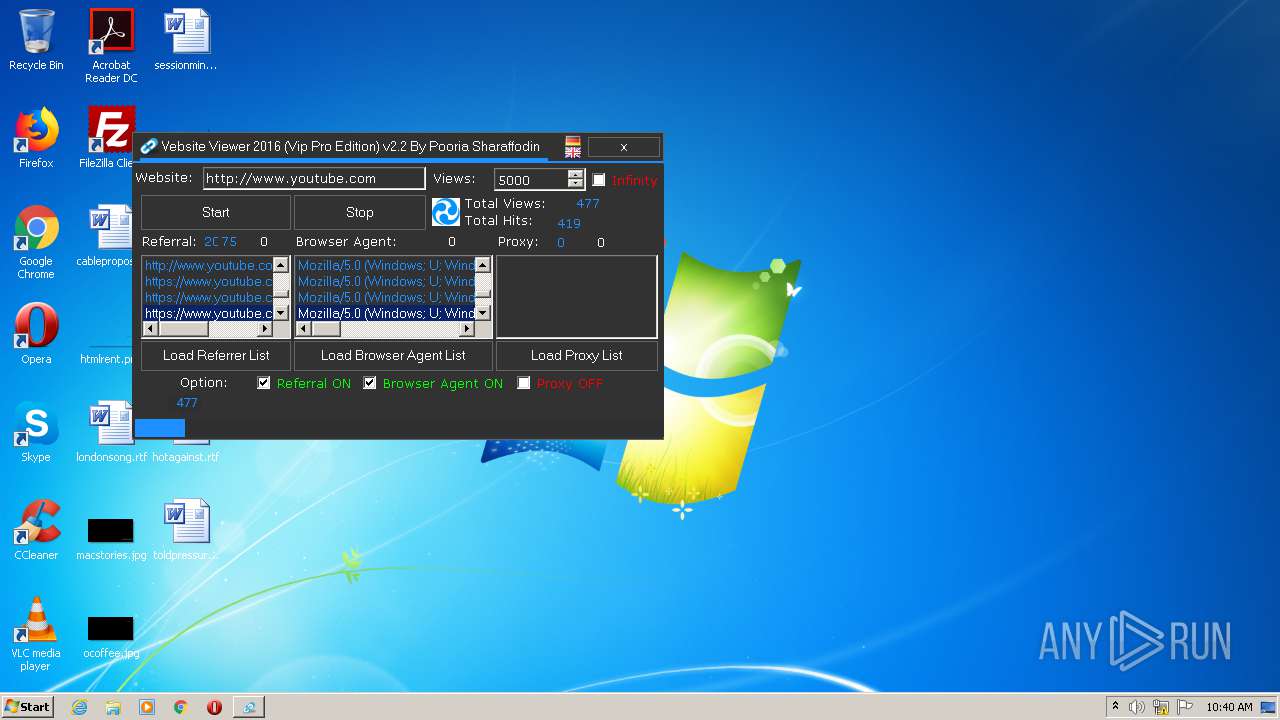
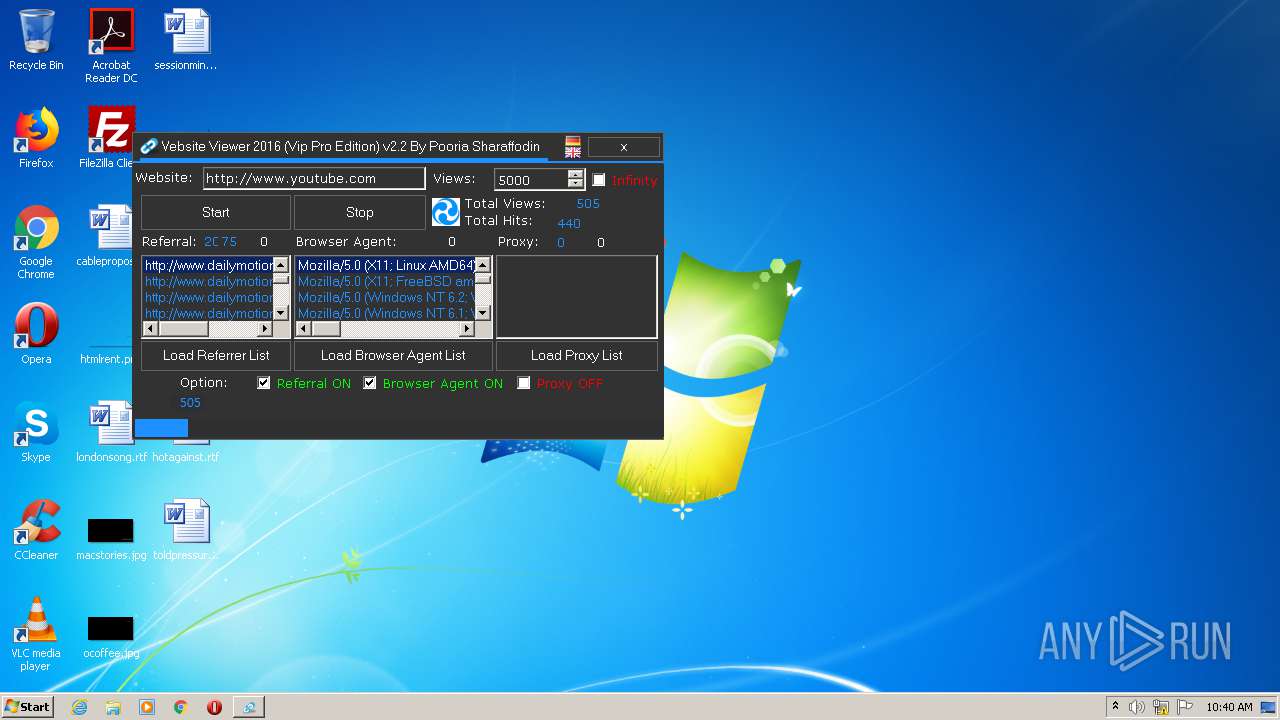
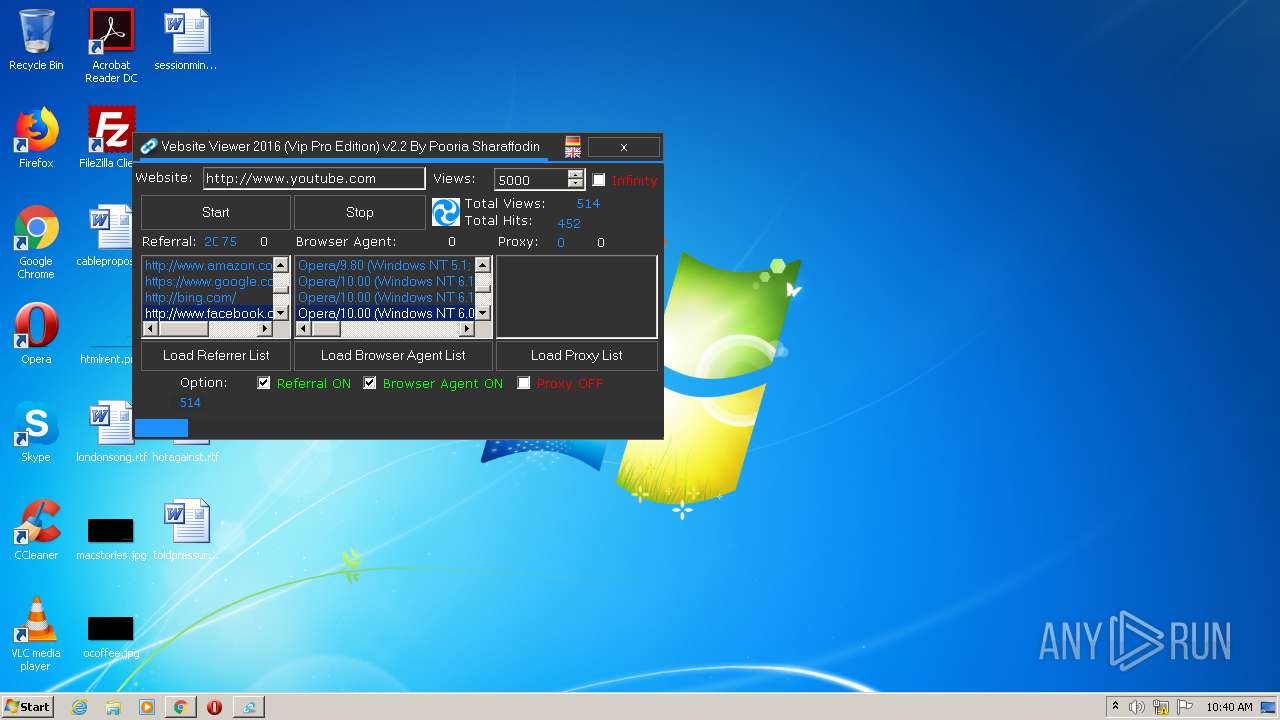
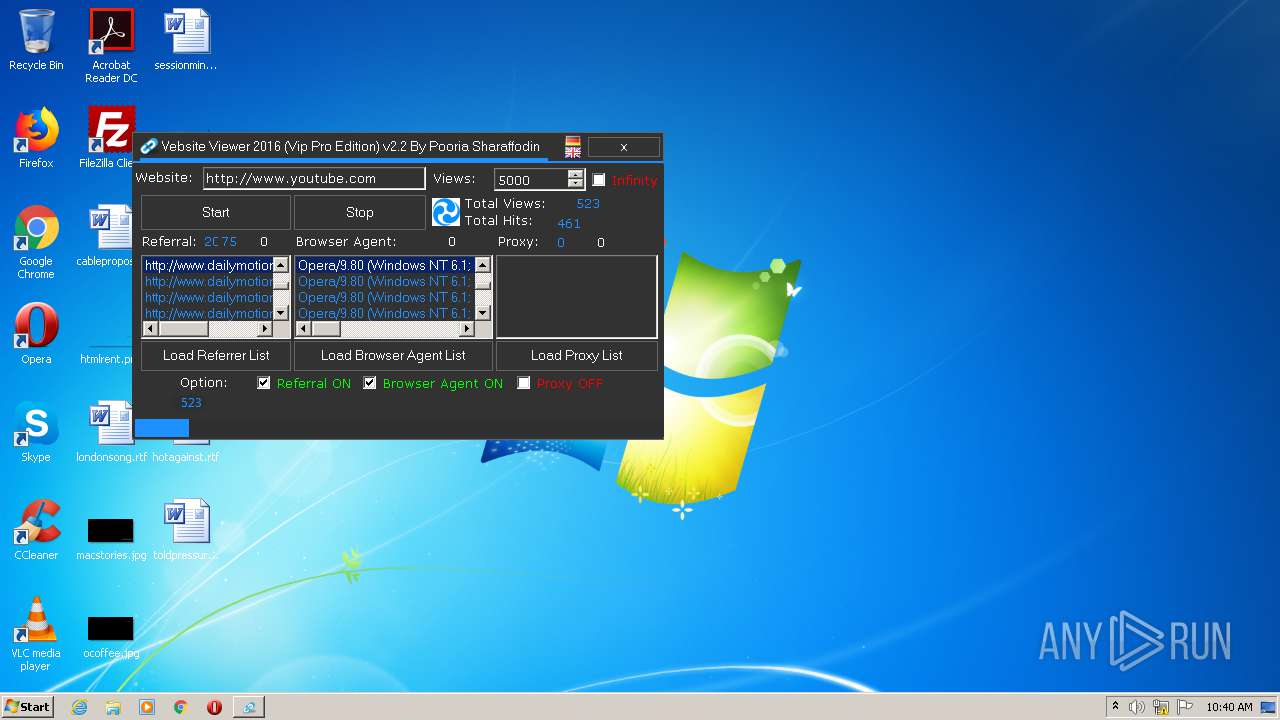
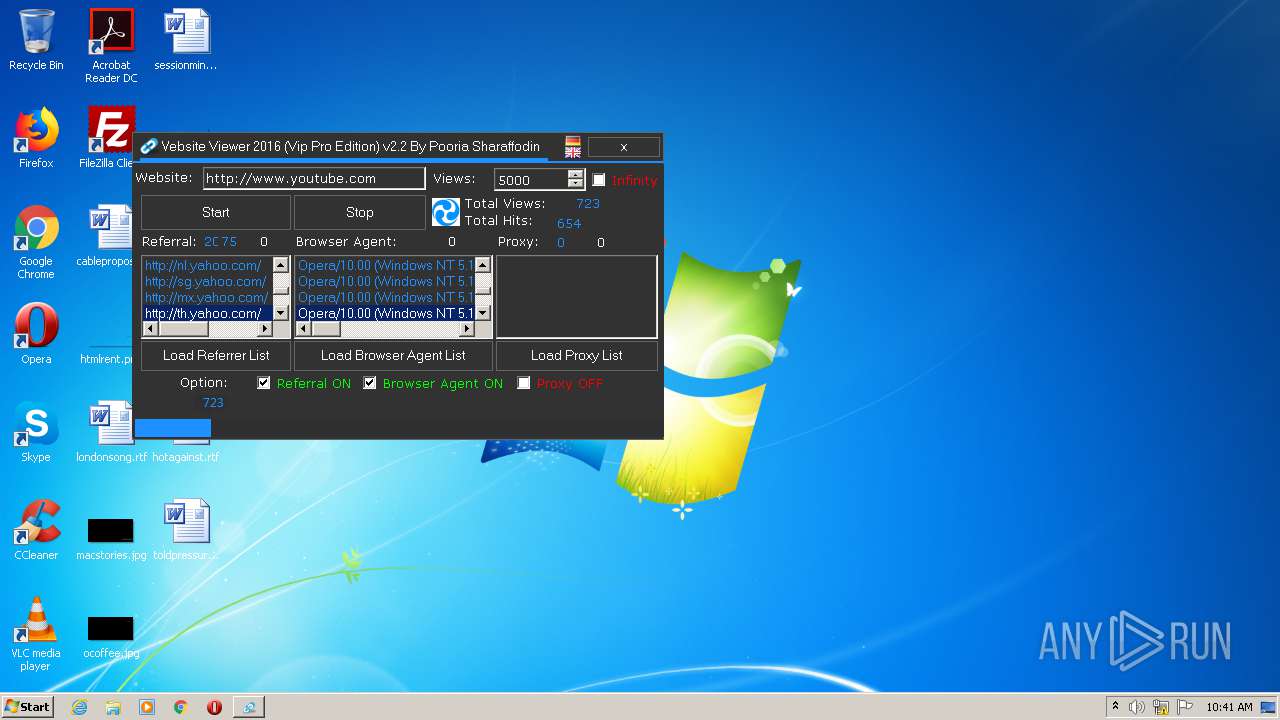
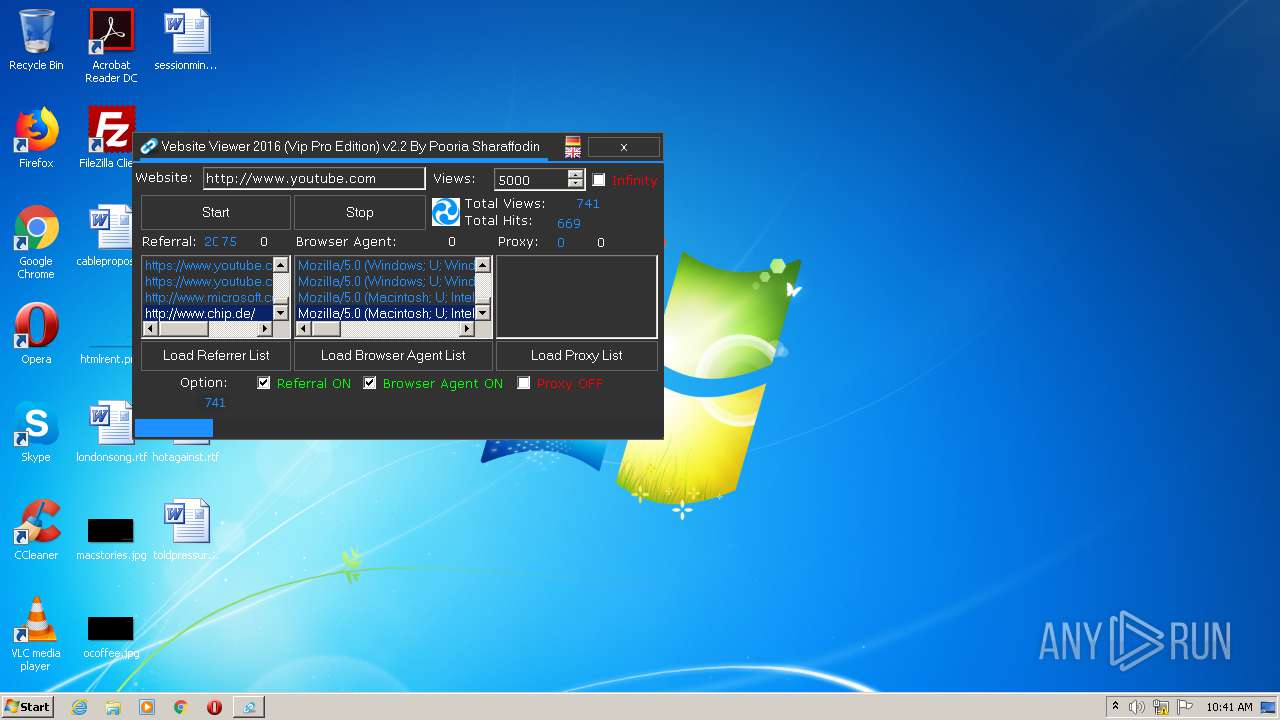
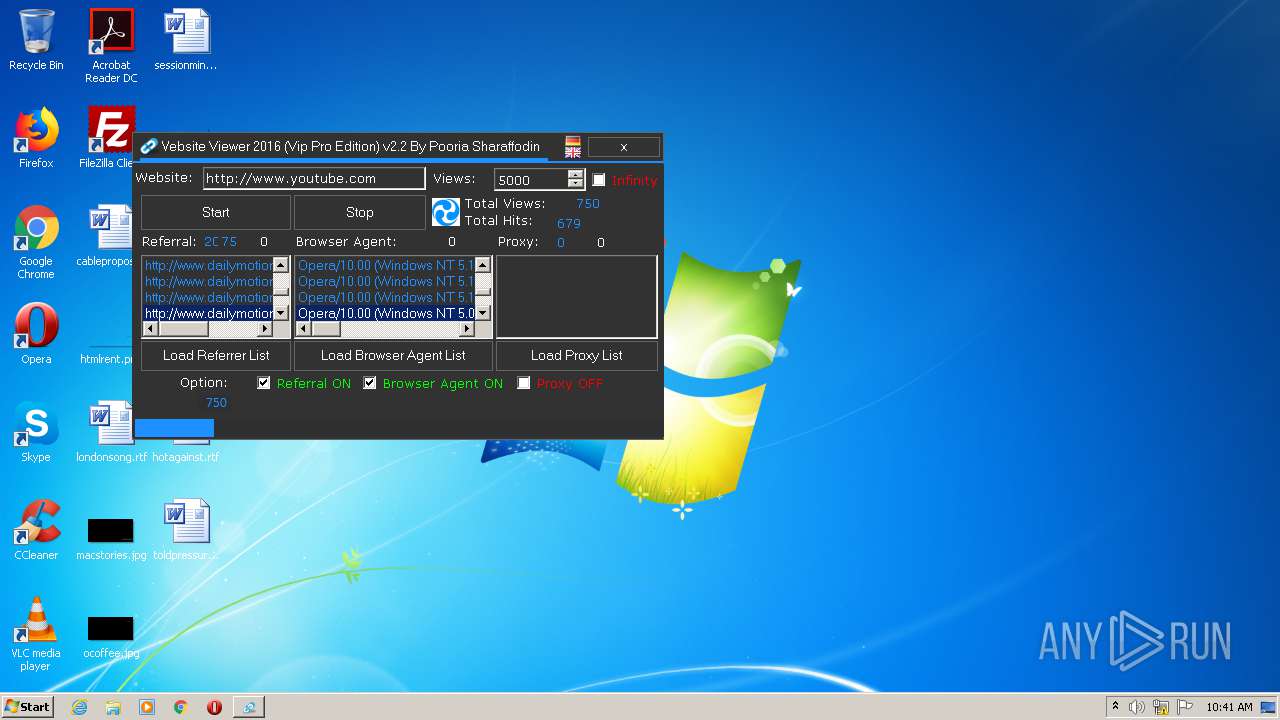
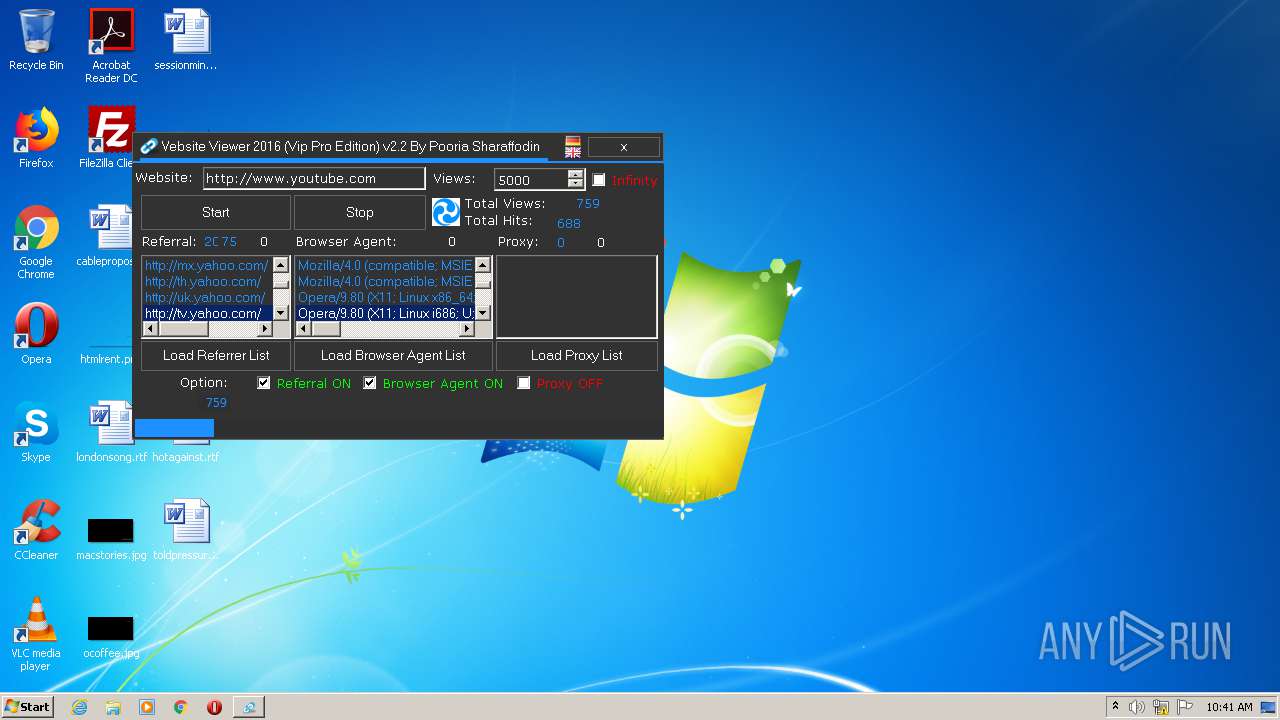
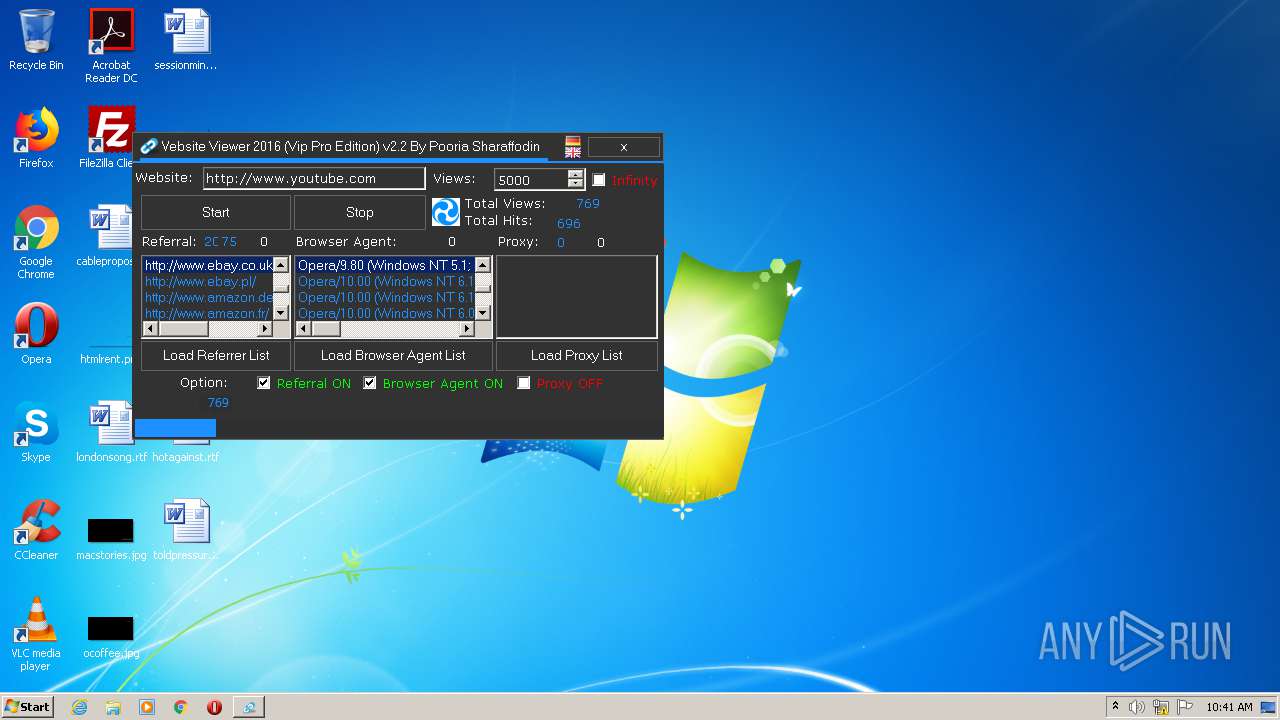
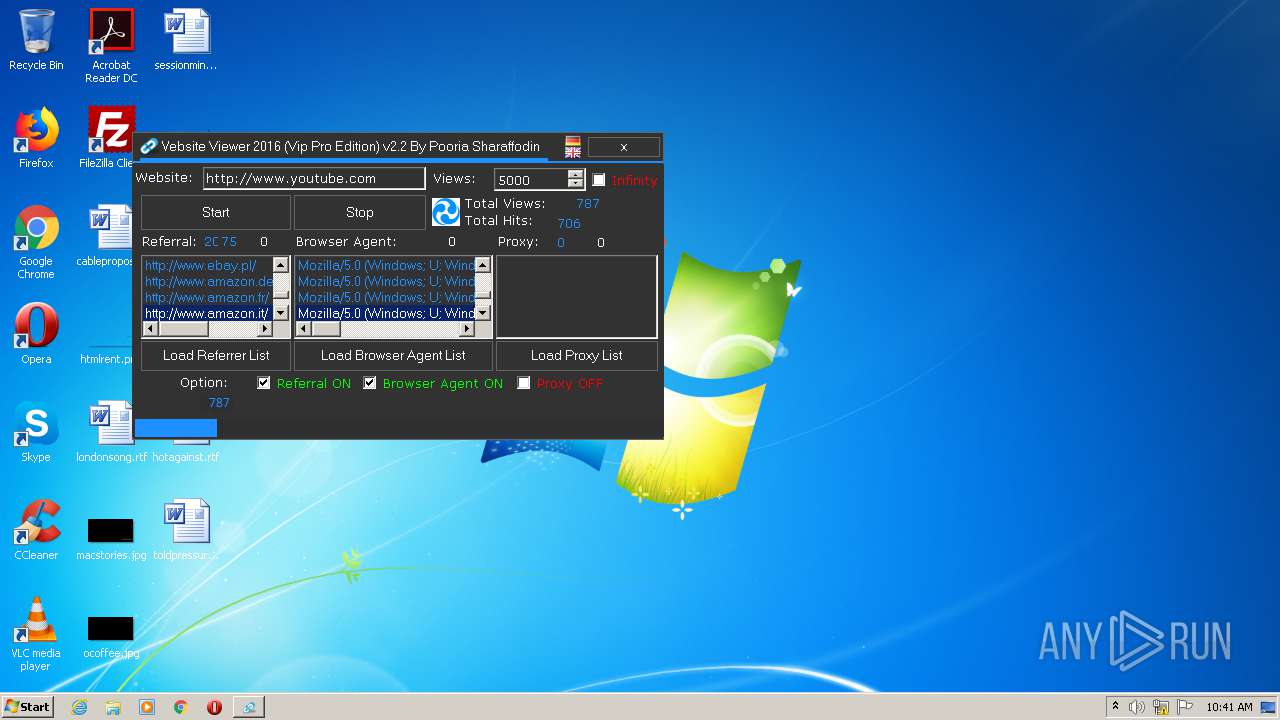
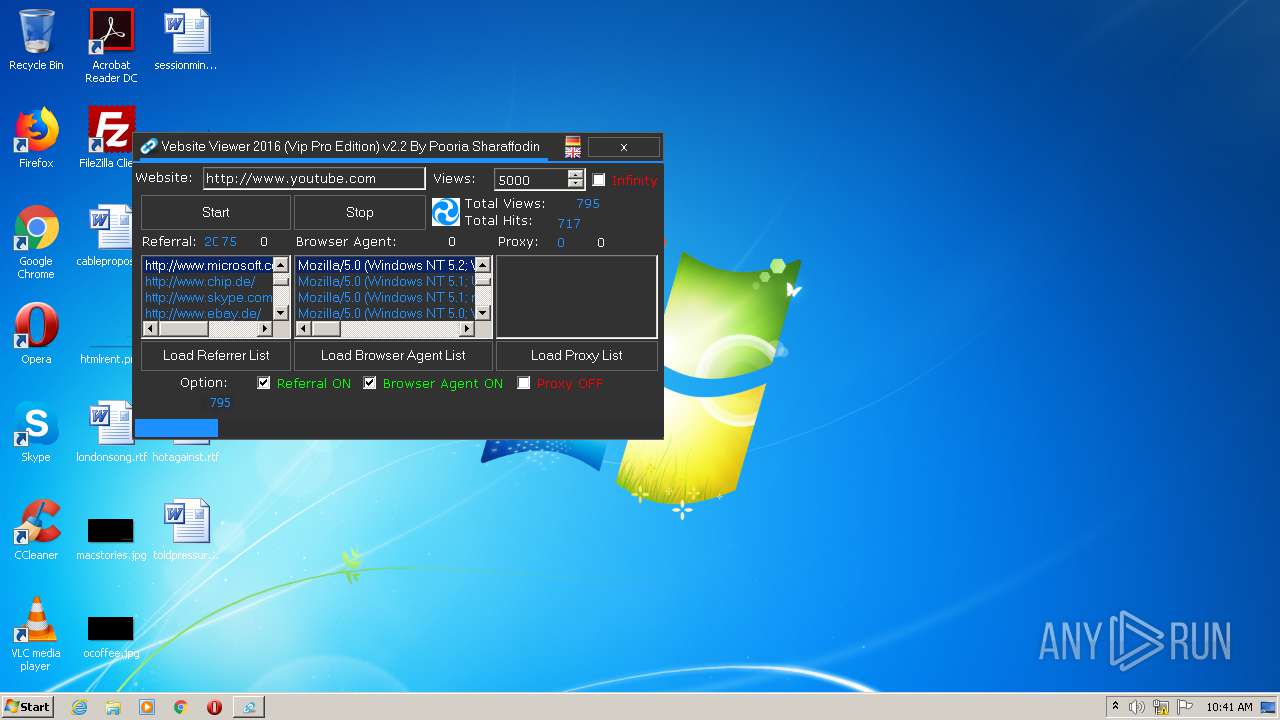
| File name: | Website Viewer 2016 v2.2 (Vip Pro Edition).exe |
| Full analysis: | https://app.any.run/tasks/04095786-144f-4d97-be2a-67f348709074 |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2021, 10:38:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CF9BEC787E437AC0A28058C250993BDF |
| SHA1: | 7124ACA070C0DC0990C4B77E5E6CEC30BBBF4537 |
| SHA256: | A39EFF4521D8491565A347E297BA508CE85D99EF3C1E057C90C4037C6E4D8610 |
| SSDEEP: | 3072:u3L6Yi4fvniJ0SW5z5ykJ/+AlWtYanl5kvCqA2SEJLm7+JIHzmqimmdiv9obGNw6:wni45ykJ2p01Sj7vSk0oo0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- Website Viewer 2016 v2.2 (Vip Pro Edition).exe (PID: 2560)
Reads the hosts file
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3752)
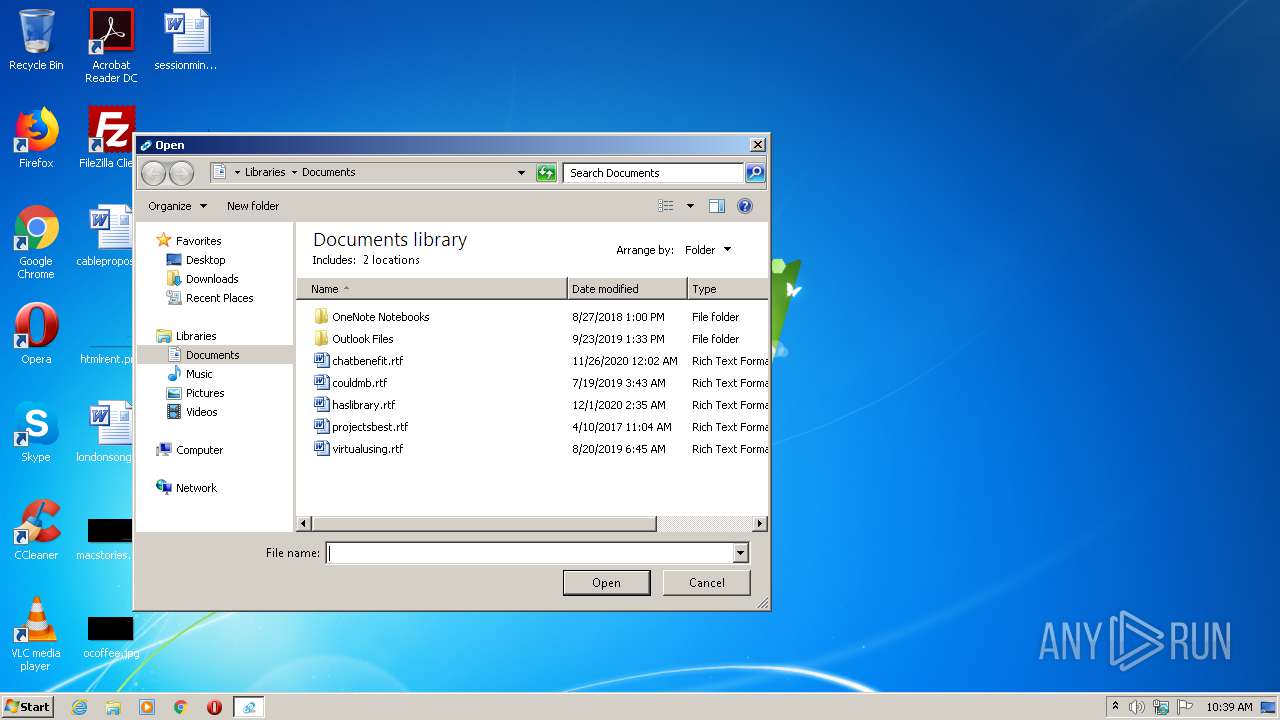
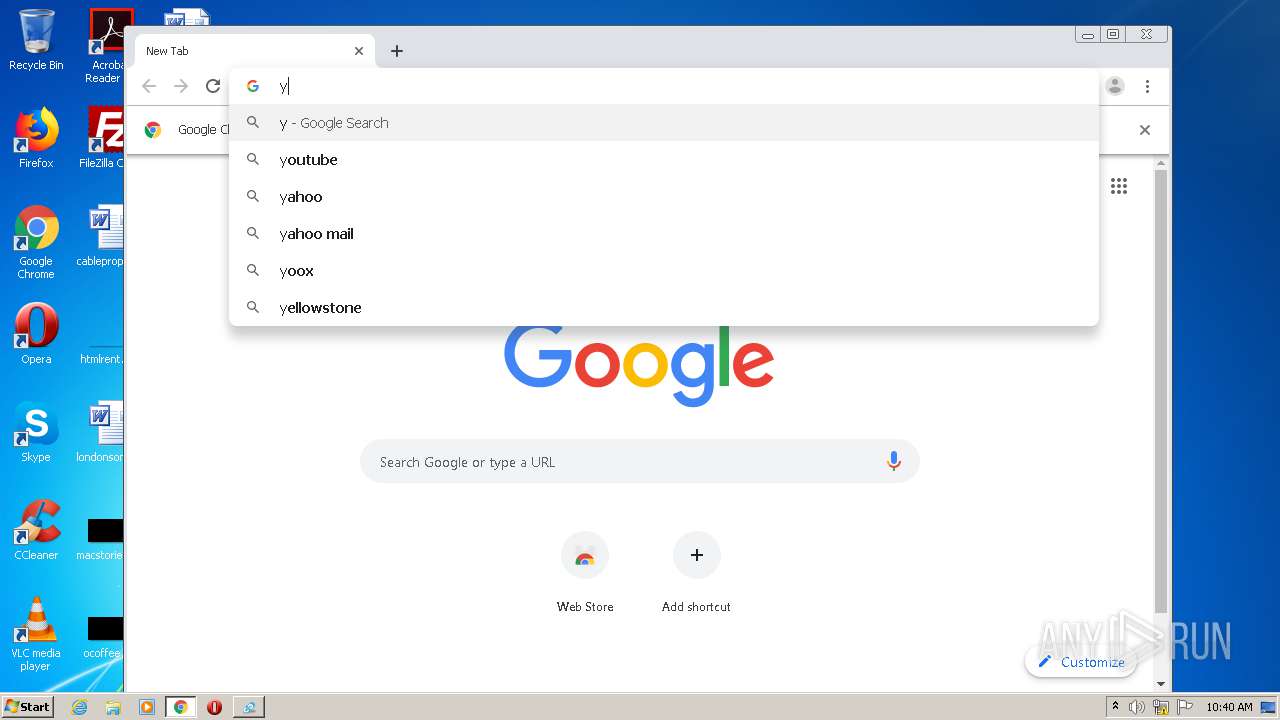
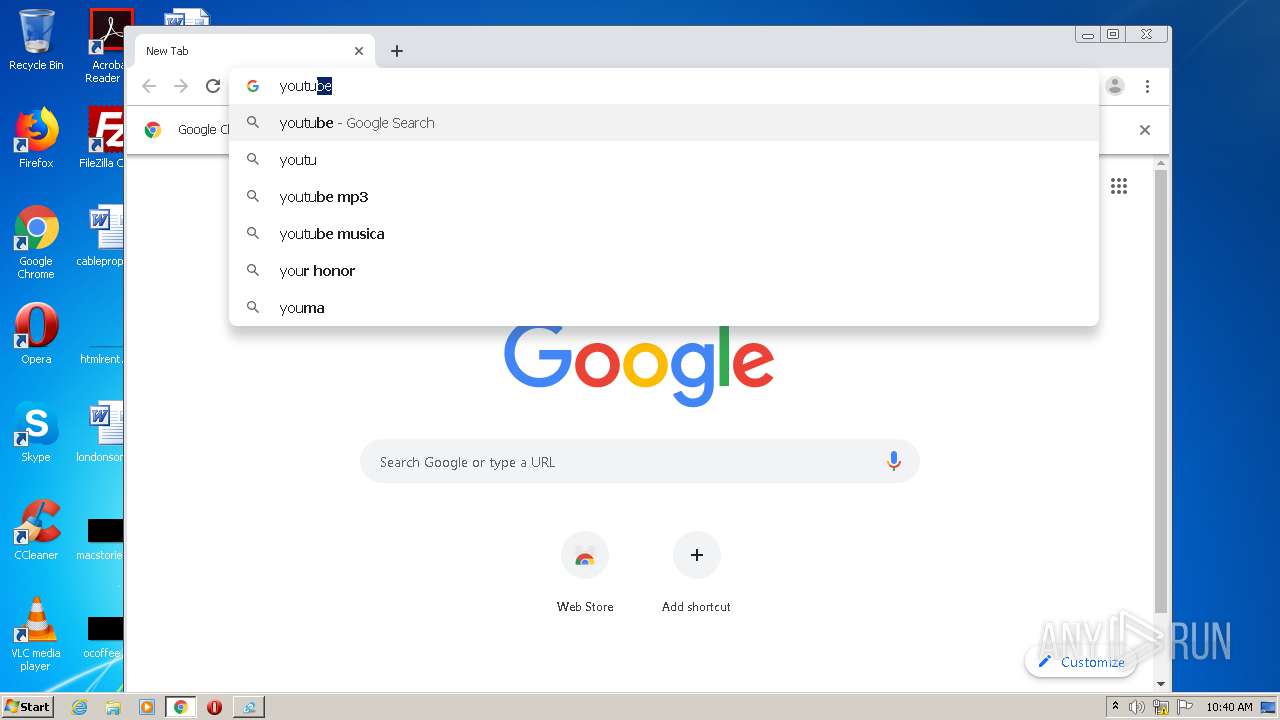
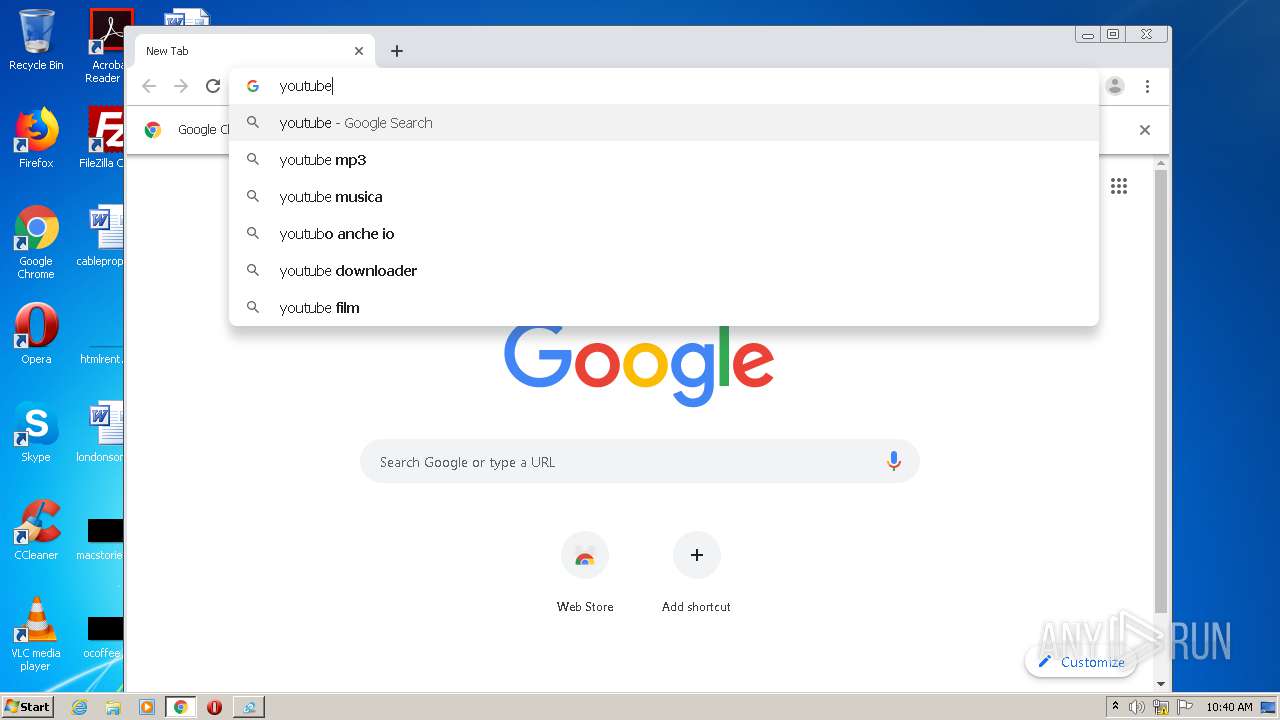
Manual execution by user
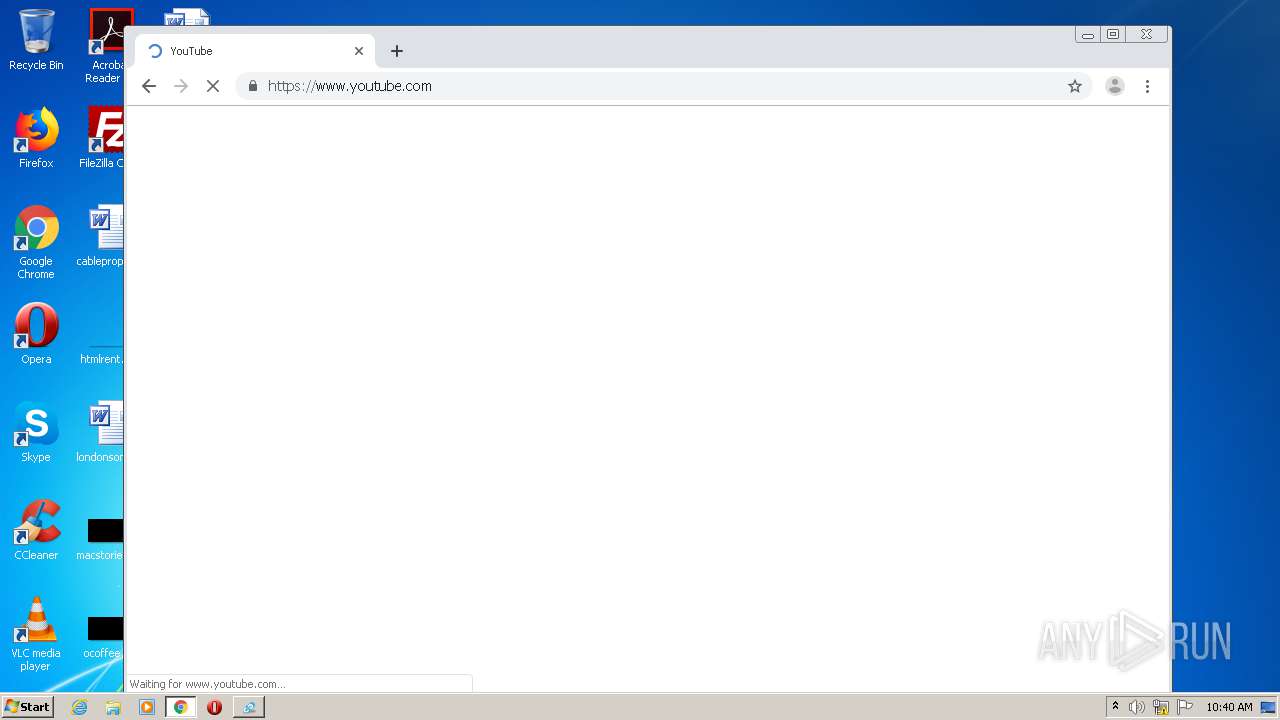
- chrome.exe (PID: 3752)
Application launched itself
- chrome.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:31 22:41:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 287744 |
| InitializedDataSize: | 5632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4821e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Website Viewer 2016 v2.2 (Vip Pro Edition) By Pooria Sharaffodin |
| CompanyName: | Pooria Sharaffodin - www.BabaTools.com |
| FileDescription: | Website Viewer 2016 v2.2 (Vip Pro Edition) By Pooria Sharaffodin |
| FileVersion: | 2.2.0.0 |
| InternalName: | Website Viewer 2016 v2.2 (Vip Pro Edition).exe |
| LegalCopyright: | Copyright © 2016 Pooria Sharaffodin |
| LegalTrademarks: | Pooria Sharaffodin - www.BabaTools.com |
| OriginalFileName: | Website Viewer 2016 v2.2 (Vip Pro Edition).exe |
| ProductName: | URL Website Viewer Clicker Click Generator |
| ProductVersion: | 2.2.0.0 |
| AssemblyVersion: | 2.2.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Jul-2016 20:41:50 |
| Comments: | Website Viewer 2016 v2.2 (Vip Pro Edition) By Pooria Sharaffodin |
| CompanyName: | Pooria Sharaffodin - www.BabaTools.com |
| FileDescription: | Website Viewer 2016 v2.2 (Vip Pro Edition) By Pooria Sharaffodin |
| FileVersion: | 2.2.0.0 |
| InternalName: | Website Viewer 2016 v2.2 (Vip Pro Edition).exe |
| LegalCopyright: | Copyright © 2016 Pooria Sharaffodin |
| LegalTrademarks: | Pooria Sharaffodin - www.BabaTools.com |
| OriginalFilename: | Website Viewer 2016 v2.2 (Vip Pro Edition).exe |
| ProductName: | URL Website Viewer Clicker Click Generator |
| ProductVersion: | 2.2.0.0 |
| Assembly Version: | 2.2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 31-Jul-2016 20:41:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00046224 | 0x00046400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.67498 |
.rsrc | 0x0004A000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.88167 |
.reloc | 0x0004C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.58411 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.0815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
74
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15115659393197638517 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9001989694977065703 --mojo-platform-channel-handle=3608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4241891552349322645 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3656 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6543864695636795714 --mojo-platform-channel-handle=3452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1422454609695339034 --mojo-platform-channel-handle=3996 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9366773989017052817 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13658631270340450361 --mojo-platform-channel-handle=3500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12619524853005895051 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15582655213209912175,11479411538732371437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12962797510659027254 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
771
Read events
653
Write events
113
Delete events
5
Modification events
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2560) Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Website Viewer 2016 v2_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
63
Text files
277
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-605F0BA9-EA8.pma | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe66a5.TMP | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2529a4fd-0da7-4cb1-bf16-6fa7e0a6f4a7.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe66e3.TMP | text | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFe6703.TMP | text | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe68b8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 558
TCP/UDP connections
121
DNS requests
29
Threats
63
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
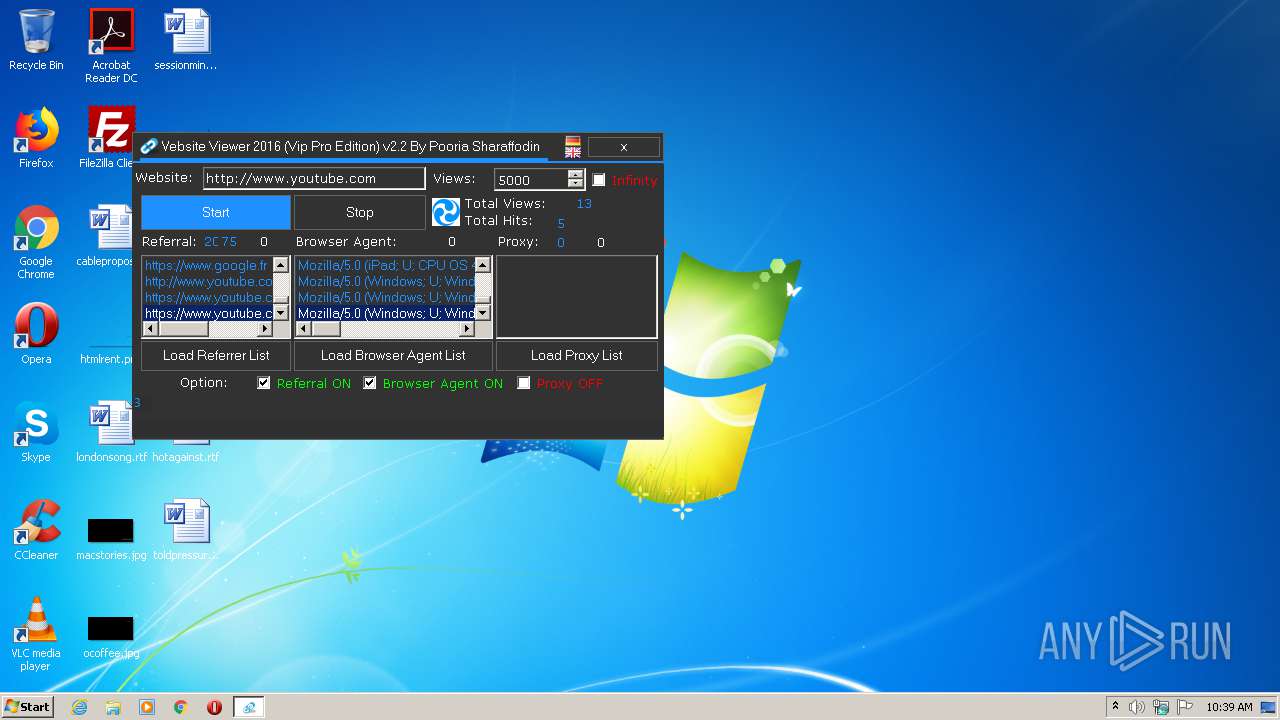
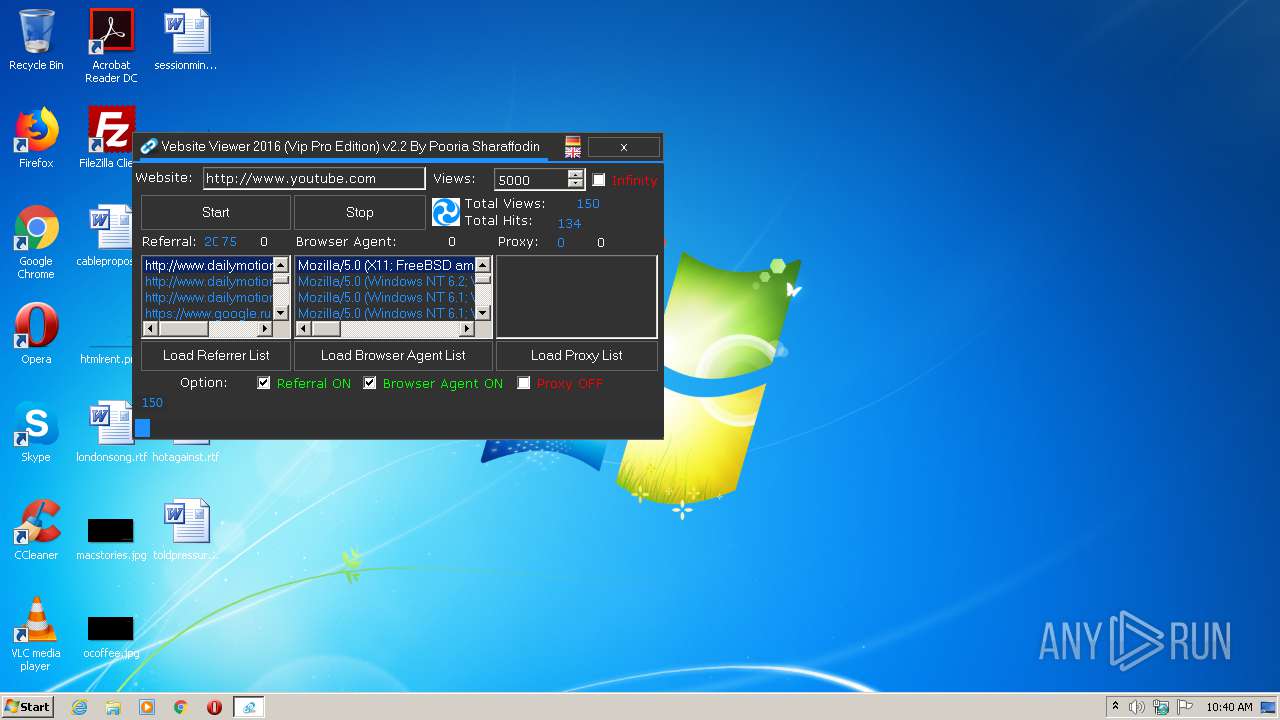
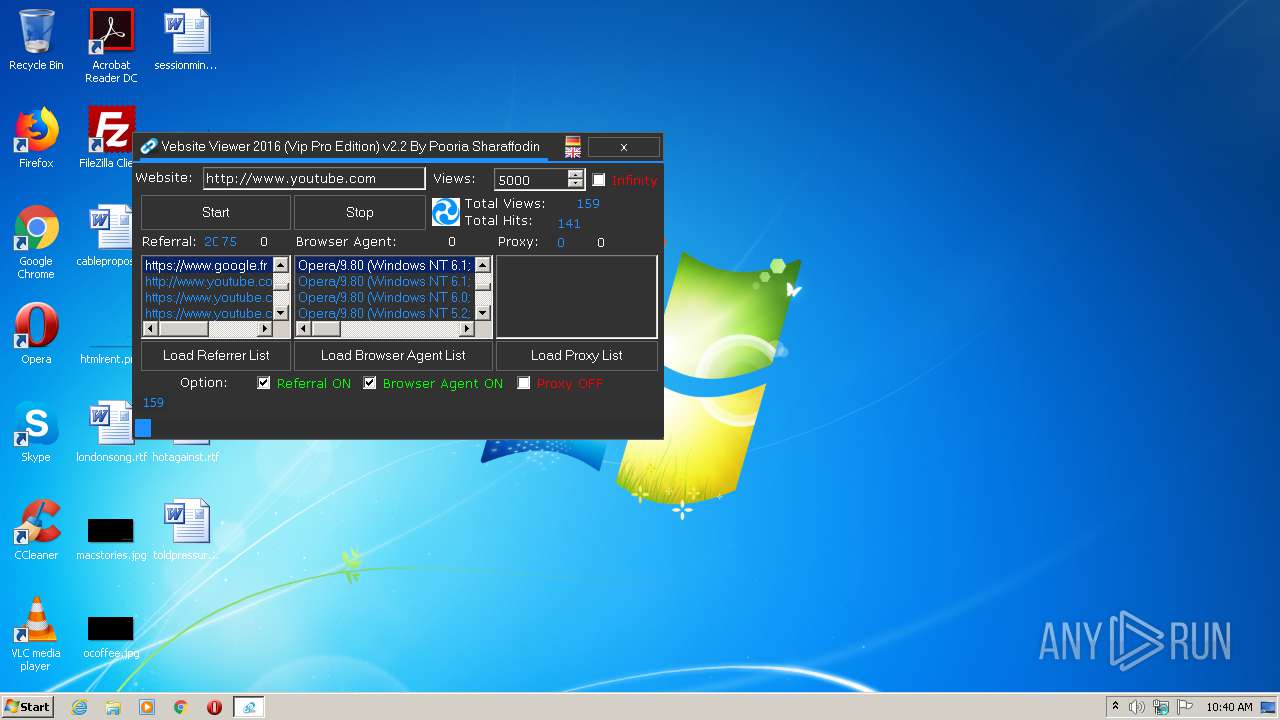
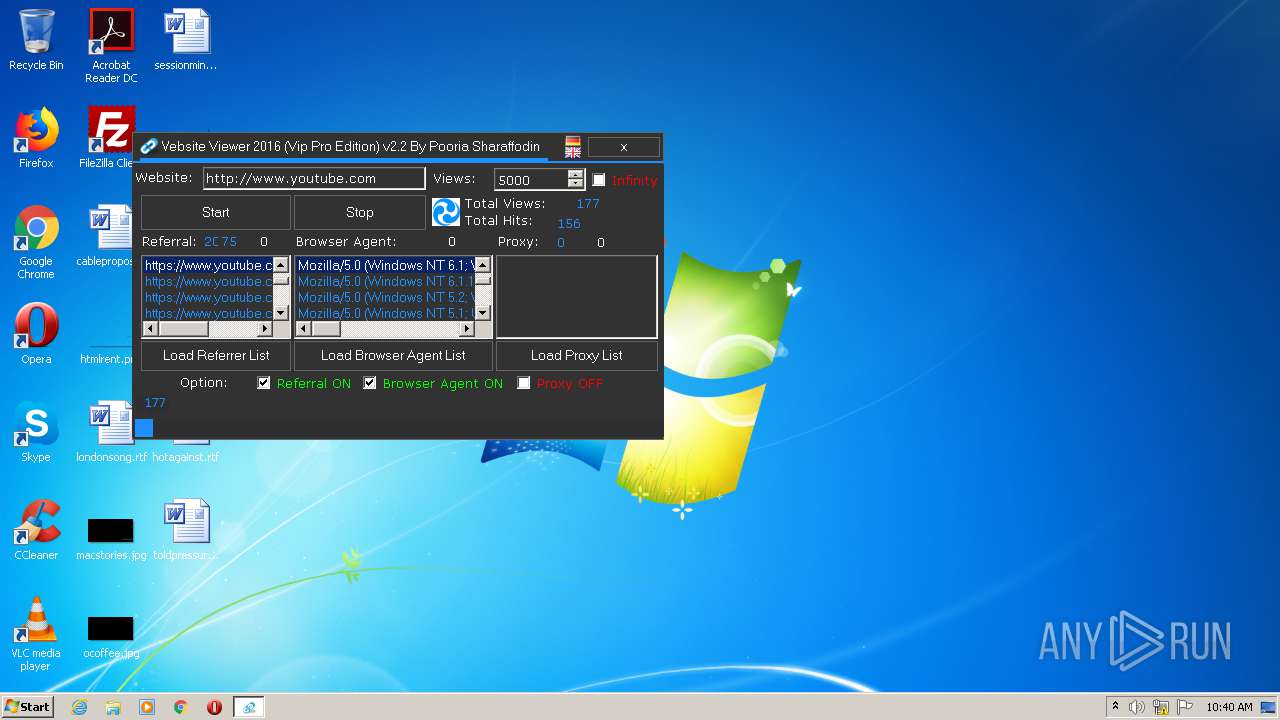
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 302 | 142.250.186.78:80 | http://www.youtube.com/ | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 301 | 142.250.186.78:80 | http://www.youtube.com/supported_browsers?next_url=http%3A%2F%2Fwww.youtube.com%2F | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 301 | 142.250.186.78:80 | http://www.youtube.com/supported_browsers?next_url=http%3A%2F%2Fwww.youtube.com%2F | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 302 | 142.250.186.78:80 | http://www.youtube.com/ | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 302 | 142.250.186.78:80 | http://www.youtube.com/ | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 301 | 142.250.186.78:80 | http://www.youtube.com/ | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | HEAD | 302 | 142.250.186.78:80 | http://www.youtube.com/ | US | — | — | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | GET | 200 | 216.105.38.10:80 | http://proxysearcher.sourceforge.net/Proxy%20List.php?type=http&filtered=true | US | html | 54.5 Kb | malicious |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | GET | 200 | 216.58.212.129:80 | http://newfreshproxies24.blogspot.com/ | US | html | 829 b | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | GET | 200 | 142.250.186.115:80 | http://www.sslproxies24.top/ | US | html | 52.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 216.58.212.129:80 | sslproxies24.blogspot.de | Google Inc. | US | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 142.250.186.115:80 | www.sslproxies24.top | Google Inc. | US | malicious |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 142.250.186.78:80 | www.youtube.com | Google Inc. | US | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 142.250.186.78:443 | www.youtube.com | Google Inc. | US | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 108.61.40.123:80 | www.xroxy.com | Choopa, LLC | US | unknown |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 142.250.186.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | 108.61.40.123:443 | www.xroxy.com | Choopa, LLC | US | unknown |
— | — | 108.61.40.123:443 | www.xroxy.com | Choopa, LLC | US | unknown |
2660 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2660 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sslproxies24.blogspot.de |
| whitelisted |
newfreshproxies24.blogspot.de |
| whitelisted |
proxysearcher.sourceforge.net |
| malicious |
sslproxies24.blogspot.com |
| whitelisted |
newfreshproxies24.blogspot.com |
| whitelisted |
www.sslproxies24.top |
| whitelisted |
www.xroxy.com |
| suspicious |
www.youtube.com |
| whitelisted |
m.youtube.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | Potentially Bad Traffic | ET INFO Request to .TOP Domain with Minimal Headers |
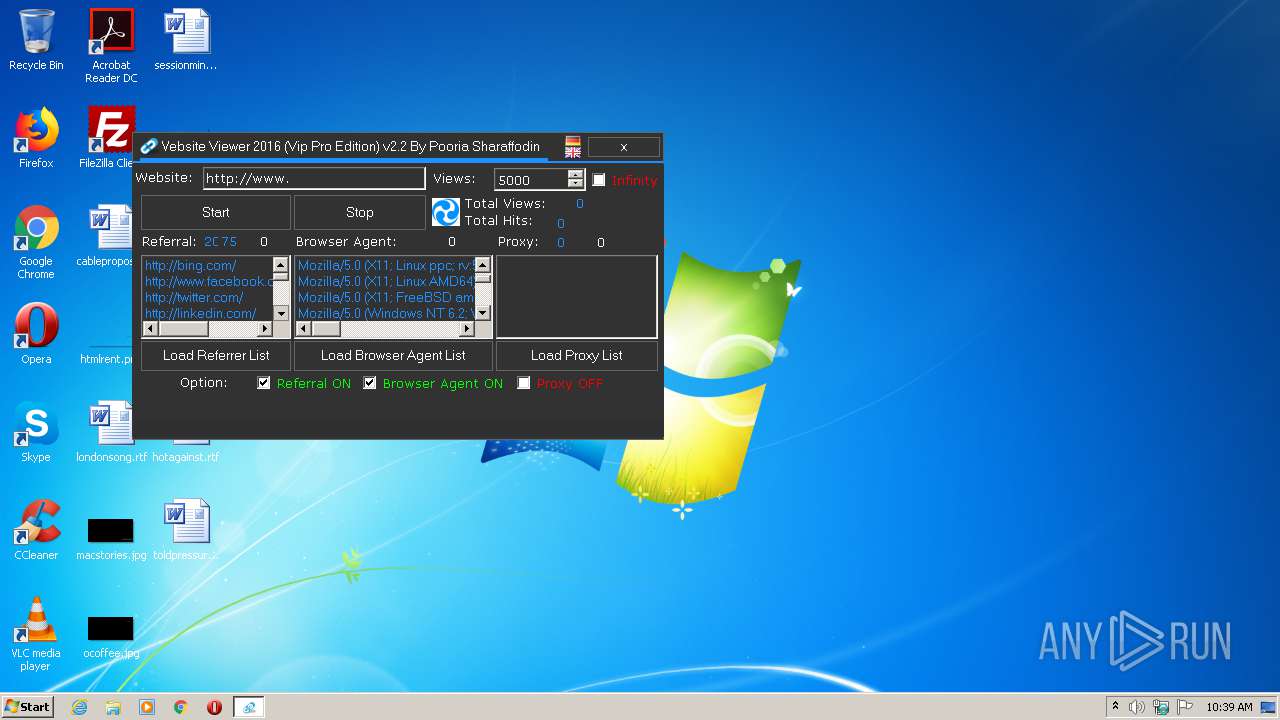
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET MALWARE Alexa Search Toolbar User-Agent 2 (Alexa Toolbar) |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET MALWARE Alexa Search Toolbar User-Agent 2 (Alexa Toolbar) |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET INFO Suspicious Windows NT version 7 User-Agent |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET INFO Suspicious Windows NT version 7 User-Agent |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET INFO Suspicious Windows NT version 7 User-Agent |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET INFO Suspicious Windows NT version 7 User-Agent |
2560 | Website Viewer 2016 v2.2 (Vip Pro Edition).exe | A Network Trojan was detected | ET INFO Suspicious Windows NT version 9 User-Agent |