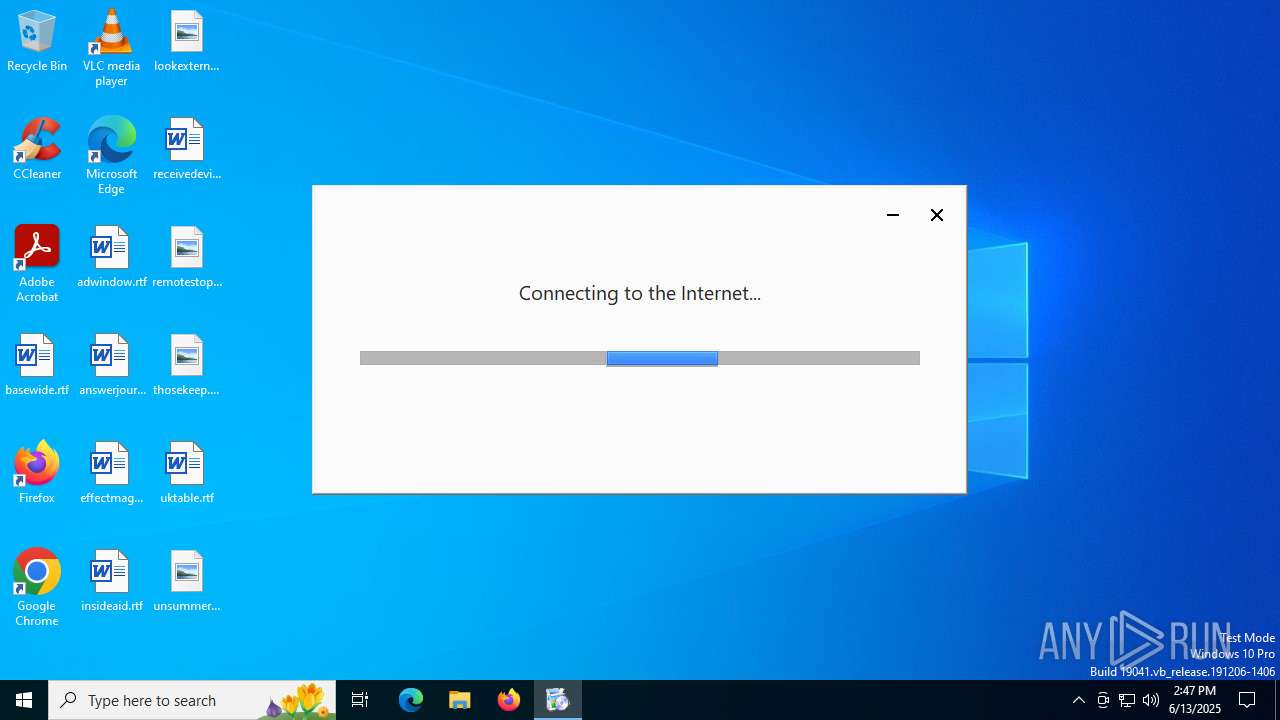
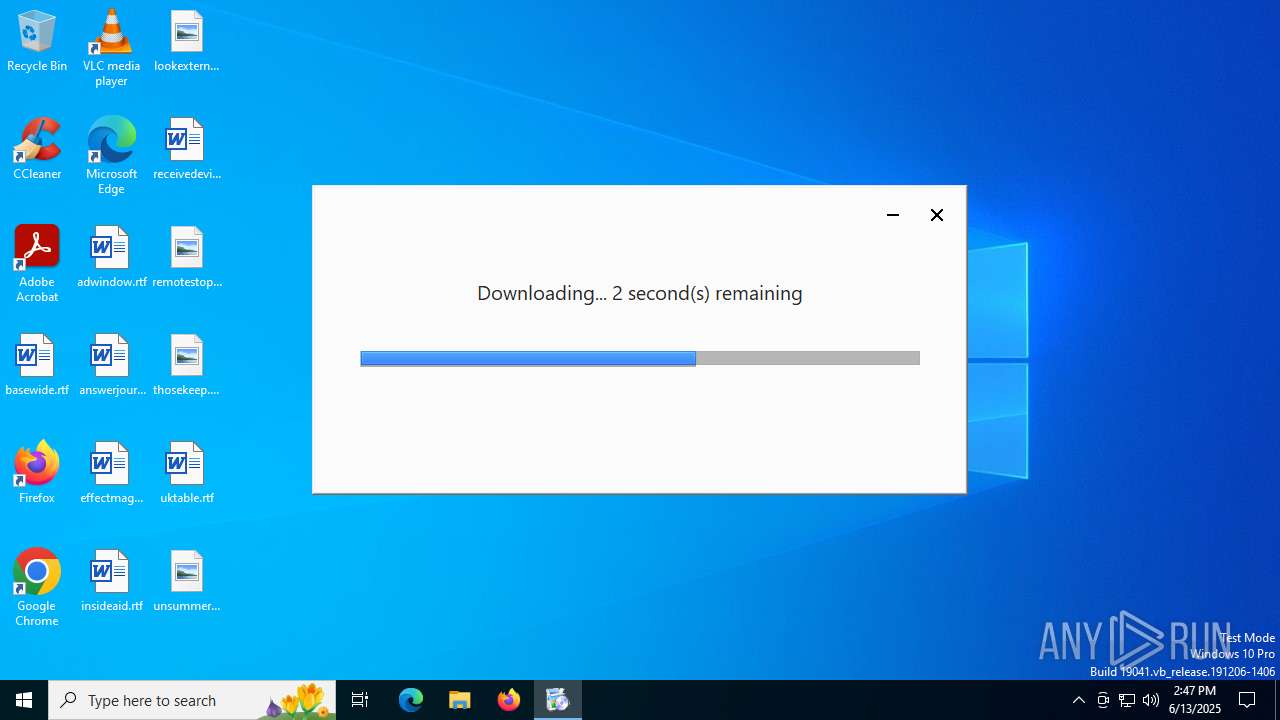
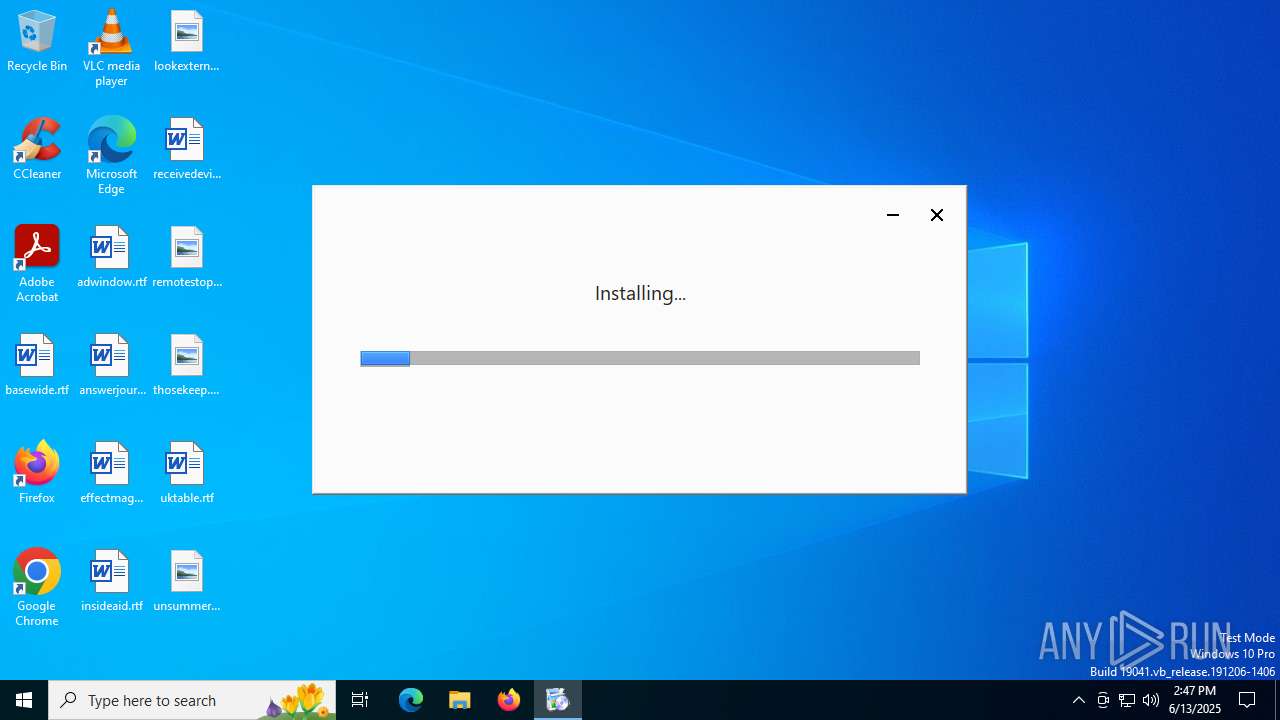
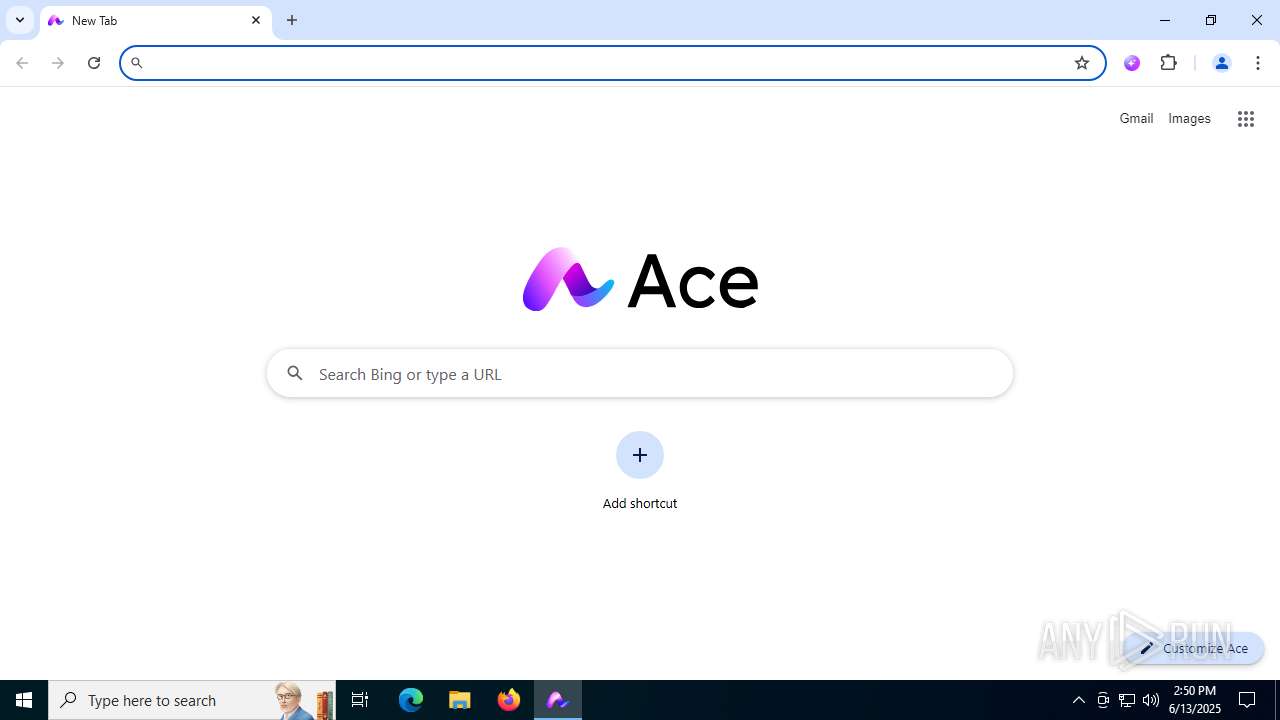
| File name: | AceSetup.exe |
| Full analysis: | https://app.any.run/tasks/e5421c00-d5ad-490b-821e-7b138618c3c1 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2025, 14:47:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 11 sections |
| MD5: | 6F6079E16AB939B0DF84714614D9A64F |
| SHA1: | F0B2F7C47AD1720CA39894DC41E85EA59ED419C0 |
| SHA256: | A39EA940F090DABB44B7501C4D83685E0A965C68B7C76184520219E0B861E00C |
| SSDEEP: | 98304:71WfWxy06eQaLWA7hm7ASTFOOe8qBJNJKcVEoVCNol0oa/D13XYsQEJZvgY0IaeA:coVCNo9Zv4fjl7LhEf5 |
MALICIOUS
Executing a file with an untrusted certificate
- AceSetup.exe (PID: 1324)
- AceSetup.exe (PID: 3732)
- updater.exe (PID: 3588)
- mini_installer.exe (PID: 4192)
- setup.exe (PID: 1356)
- setup.exe (PID: 2188)
- setup.exe (PID: 1932)
- setup.exe (PID: 3844)
- ace.exe (PID: 4172)
- ace.exe (PID: 3936)
- ace.exe (PID: 6012)
- ace.exe (PID: 5904)
- ace.exe (PID: 2064)
- ace.exe (PID: 7104)
- ace.exe (PID: 2524)
- ace.exe (PID: 6160)
- chrmstp.exe (PID: 4676)
- ace.exe (PID: 5764)
- chrmstp.exe (PID: 6368)
- updater.exe (PID: 7384)
- ace.exe (PID: 7500)
- updater.exe (PID: 7404)
- ace.exe (PID: 7580)
- ace.exe (PID: 7640)
- ace.exe (PID: 7840)
- ace.exe (PID: 7652)
- ace.exe (PID: 7772)
- ace.exe (PID: 7904)
- ace.exe (PID: 4752)
- ace.exe (PID: 7500)
- ace.exe (PID: 864)
- ace.exe (PID: 1984)
- ace.exe (PID: 8004)
- ace.exe (PID: 1524)
- ace.exe (PID: 7968)
- ace.exe (PID: 7812)
- ace.exe (PID: 7836)
- ace.exe (PID: 7960)
- updater.exe (PID: 2916)
- updater.exe (PID: 3044)
- updater.exe (PID: 3096)
- updater.exe (PID: 3500)
- updater.exe (PID: 3856)
- updater.exe (PID: 3588)
- updater.exe (PID: 4008)
- updater.exe (PID: 3816)
- updater.exe (PID: 4036)
- updater.exe (PID: 4520)
- chrmstp.exe (PID: 4552)
- updater.exe (PID: 4644)
- chrmstp.exe (PID: 4756)
- chrmstp.exe (PID: 4688)
- ace.exe (PID: 7156)
- ace.exe (PID: 6108)
- ace.exe (PID: 2748)
- ace.exe (PID: 7216)
- ace.exe (PID: 7288)
- updater.exe (PID: 7624)
- updater.exe (PID: 7644)
- ace.exe (PID: 5388)
- ace.exe (PID: 5188)
- ace.exe (PID: 2816)
- ace.exe (PID: 5460)
- ace.exe (PID: 6708)
- chrmstp.exe (PID: 1520)
- chrmstp.exe (PID: 7172)
Changes the autorun value in the registry
- setup.exe (PID: 1356)
- ace.exe (PID: 4544)
SUSPICIOUS
Reads security settings of Internet Explorer
- AceSetup.exe (PID: 1324)
- updater.exe (PID: 2216)
- chrmstp.exe (PID: 1520)
Reads the date of Windows installation
- AceSetup.exe (PID: 1324)
- chrmstp.exe (PID: 1520)
Application launched itself
- updater.exe (PID: 2216)
- AceSetup.exe (PID: 1324)
- updater.exe (PID: 4920)
- updater.exe (PID: 3588)
- setup.exe (PID: 1356)
- setup.exe (PID: 1932)
- ace.exe (PID: 4544)
- chrmstp.exe (PID: 4676)
- chrmstp.exe (PID: 1520)
- updater.exe (PID: 7384)
- ace.exe (PID: 7500)
- updater.exe (PID: 2916)
- updater.exe (PID: 2908)
- updater.exe (PID: 3500)
- updater.exe (PID: 3816)
- updater.exe (PID: 4008)
- chrmstp.exe (PID: 4612)
- updater.exe (PID: 4520)
- chrmstp.exe (PID: 4688)
- updater.exe (PID: 4540)
- ace.exe (PID: 7156)
- updater.exe (PID: 7624)
Executable content was dropped or overwritten
- updater.exe (PID: 2216)
- updater.exe (PID: 3588)
- mini_installer.exe (PID: 4192)
- setup.exe (PID: 1356)
Executes as Windows Service
- updater.exe (PID: 3588)
- updater.exe (PID: 4920)
- updater.exe (PID: 7384)
Creates a software uninstall entry
- setup.exe (PID: 1356)
Searches for installed software
- setup.exe (PID: 1356)
- setup.exe (PID: 1932)
- chrmstp.exe (PID: 4676)
- chrmstp.exe (PID: 1520)
The process checks if it is being run in the virtual environment
- ace.exe (PID: 4544)
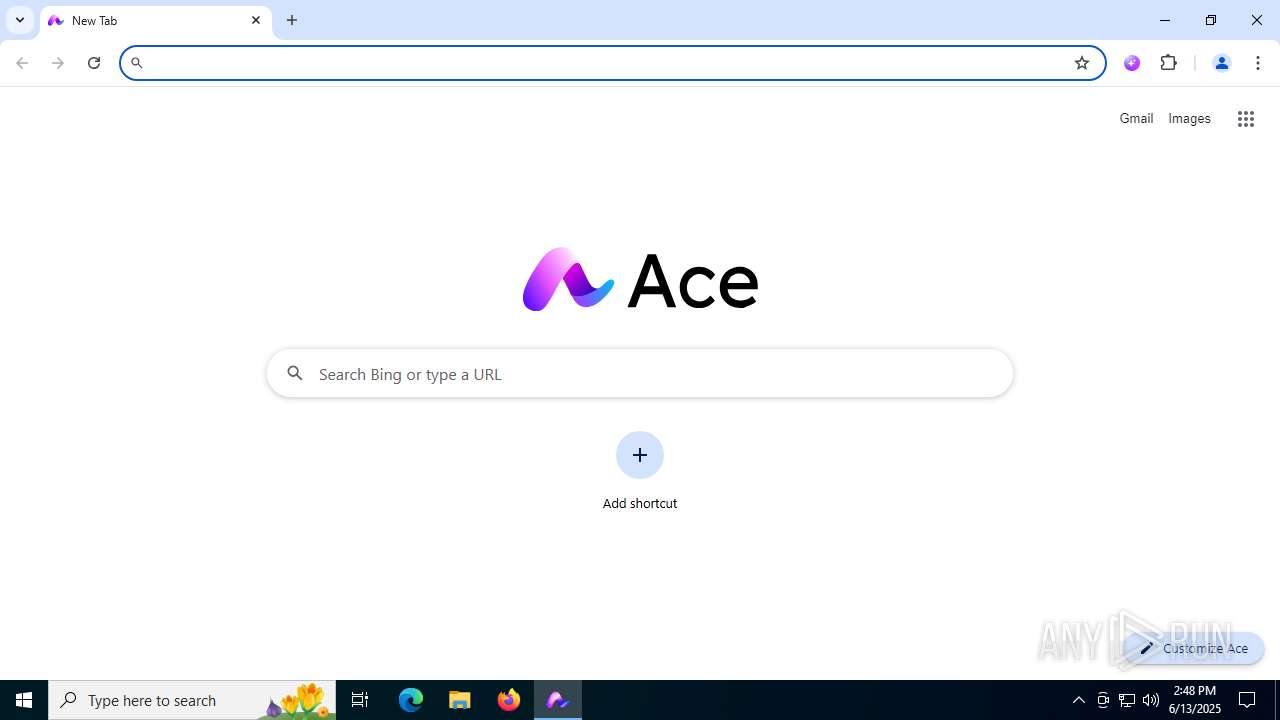
Reads Mozilla Firefox installation path
- ace.exe (PID: 4544)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4504)
- updater.exe (PID: 4540)
- updater.exe (PID: 4520)
INFO
Checks supported languages
- AceSetup.exe (PID: 3732)
- AceSetup.exe (PID: 1324)
- updater.exe (PID: 2216)
- updater.exe (PID: 2220)
- updater.exe (PID: 3588)
- updater.exe (PID: 1760)
- updater.exe (PID: 5900)
- updater.exe (PID: 4920)
- setup.exe (PID: 1356)
- mini_installer.exe (PID: 4192)
- setup.exe (PID: 2188)
- setup.exe (PID: 1932)
- ace.exe (PID: 4172)
- setup.exe (PID: 3844)
- ace.exe (PID: 4544)
- ace.exe (PID: 3936)
- ace.exe (PID: 6012)
- ace.exe (PID: 2064)
- ace.exe (PID: 7104)
- ace.exe (PID: 5904)
- ace.exe (PID: 2524)
- ace.exe (PID: 6160)
- chrmstp.exe (PID: 4676)
- ace.exe (PID: 5764)
- chrmstp.exe (PID: 6368)
- chrmstp.exe (PID: 7172)
- chrmstp.exe (PID: 1520)
The sample compiled with english language support
- AceSetup.exe (PID: 1324)
- updater.exe (PID: 2216)
- updater.exe (PID: 3588)
- mini_installer.exe (PID: 4192)
- setup.exe (PID: 1356)
Reads the computer name
- AceSetup.exe (PID: 1324)
- AceSetup.exe (PID: 3732)
- updater.exe (PID: 2216)
- updater.exe (PID: 3588)
- updater.exe (PID: 4920)
- mini_installer.exe (PID: 4192)
- setup.exe (PID: 1356)
- ace.exe (PID: 4544)
- setup.exe (PID: 1932)
- ace.exe (PID: 3936)
- ace.exe (PID: 6012)
- ace.exe (PID: 5764)
- chrmstp.exe (PID: 4676)
- chrmstp.exe (PID: 1520)
Creates files in the program directory
- AceSetup.exe (PID: 3732)
- updater.exe (PID: 2220)
- updater.exe (PID: 2216)
- updater.exe (PID: 3588)
- updater.exe (PID: 4920)
- setup.exe (PID: 1356)
- setup.exe (PID: 1932)
Process checks computer location settings
- AceSetup.exe (PID: 1324)
- ace.exe (PID: 4544)
- ace.exe (PID: 2524)
- ace.exe (PID: 7104)
- ace.exe (PID: 2064)
- ace.exe (PID: 6160)
Process checks whether UAC notifications are on
- updater.exe (PID: 2216)
- updater.exe (PID: 4920)
- updater.exe (PID: 3588)
Checks proxy server information
- updater.exe (PID: 2216)
- ace.exe (PID: 4544)
Reads the machine GUID from the registry
- updater.exe (PID: 2216)
- ace.exe (PID: 4544)
Reads the software policy settings
- updater.exe (PID: 4920)
- updater.exe (PID: 2216)
Creates files or folders in the user directory
- updater.exe (PID: 2216)
- ace.exe (PID: 4544)
- ace.exe (PID: 6012)
- chrmstp.exe (PID: 1520)
Launching a file from a Registry key
- setup.exe (PID: 1356)
- ace.exe (PID: 4544)
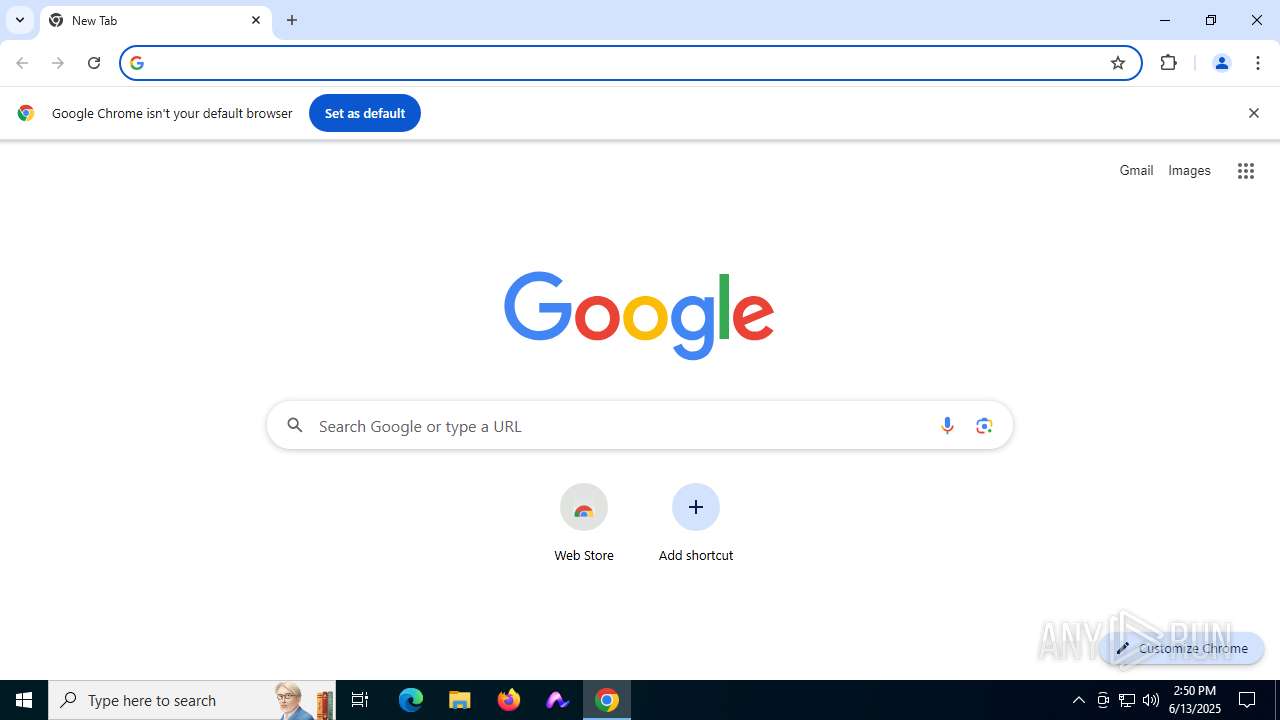
Manual execution by a user
- ace.exe (PID: 4544)
- ace.exe (PID: 7500)
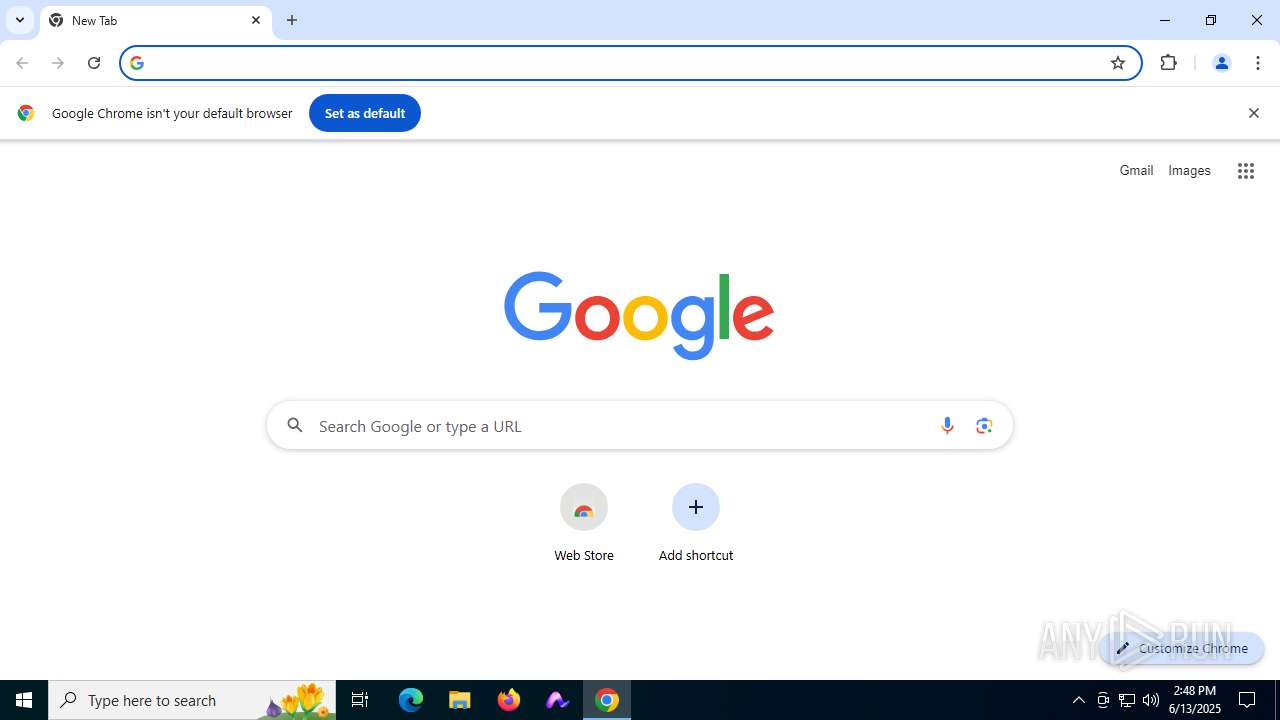
- chrome.exe (PID: 8108)
- firefox.exe (PID: 1964)
- chrmstp.exe (PID: 4612)
- ace.exe (PID: 7156)
- chrome.exe (PID: 7868)
Create files in a temporary directory
- ace.exe (PID: 4544)
Application launched itself
- chrome.exe (PID: 8108)
- firefox.exe (PID: 1964)
- firefox.exe (PID: 3620)
- chrome.exe (PID: 7868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 3994624 |
| InitializedDataSize: | 8067072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x392960 |
| OSVersion: | 10 |
| ImageVersion: | - |
| SubsystemVersion: | 10 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 132.0.6855.0 |
| ProductVersionNumber: | 132.0.6855.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
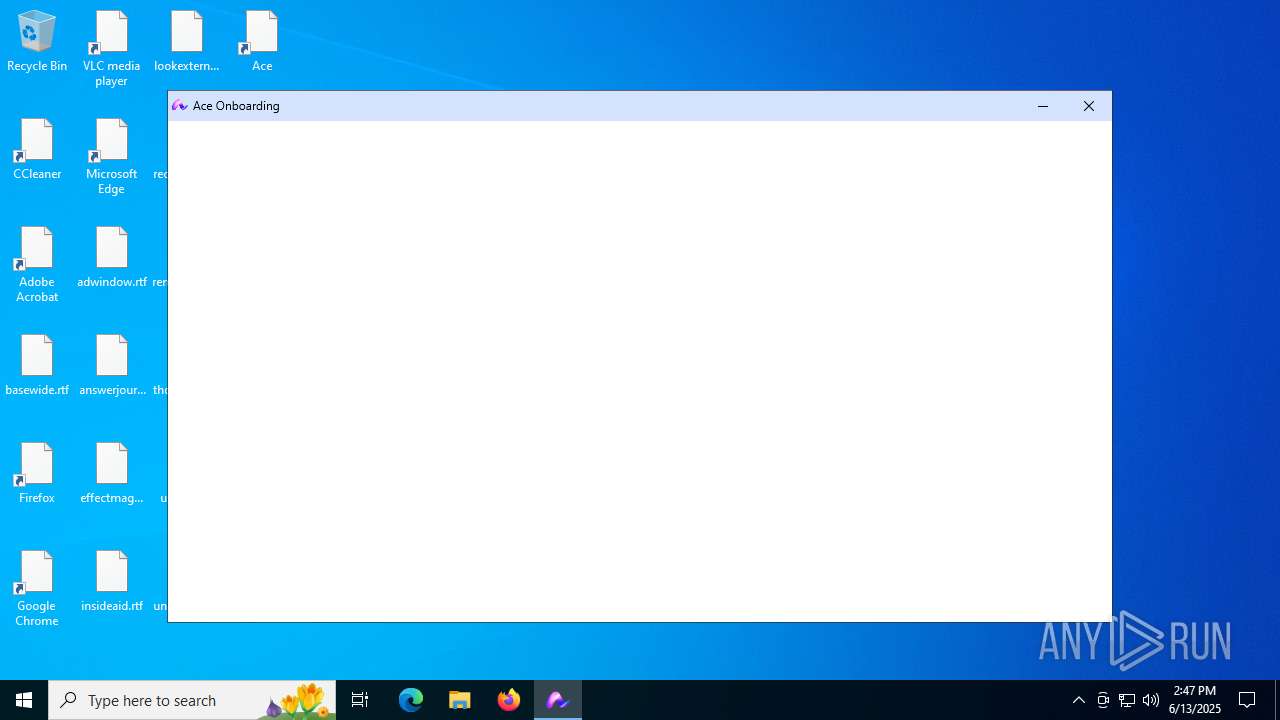
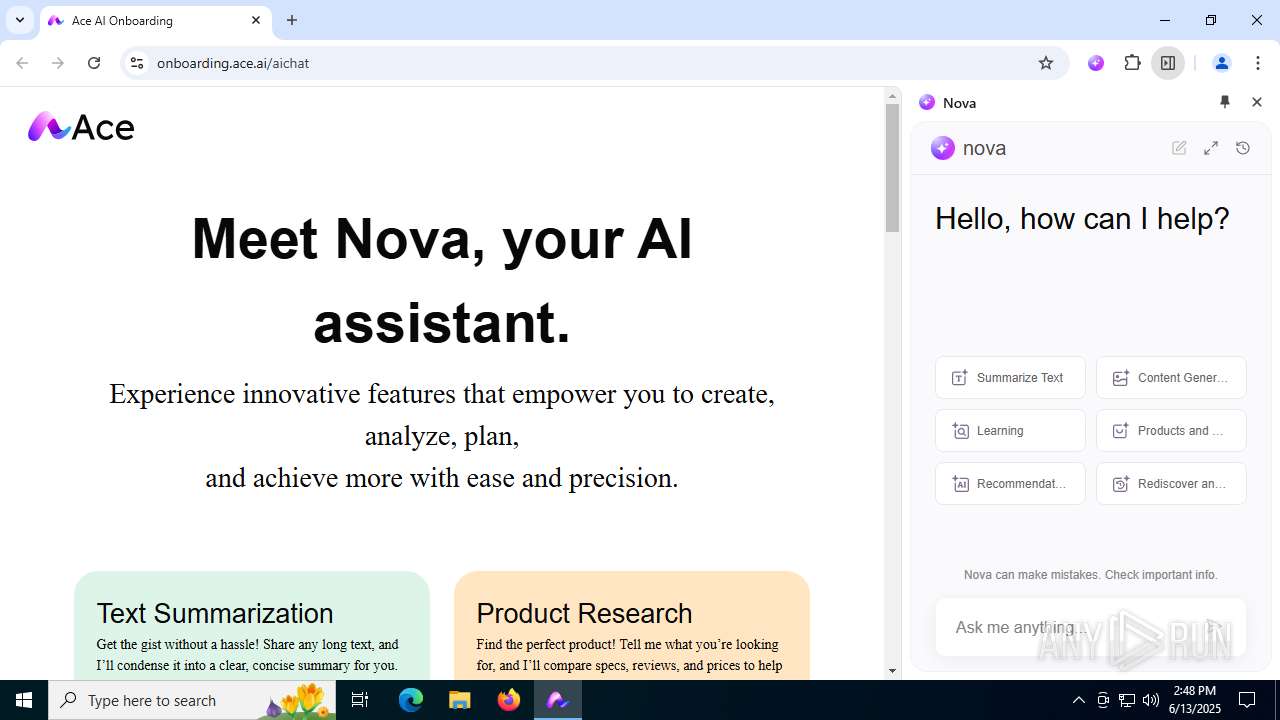
| CompanyName: | BrowseAI LLC |
| FileDescription: | Ace Installer |
| FileVersion: | 132.0.6855.0 |
| InternalName: | Ace Installer (x64) |
| LegalCopyright: | Copyright 1970 The BrowseAI LLC Authors. All rights reserved. |
| OriginalFileName: | UpdaterSetup.exe |
| ProductName: | Ace Installer |
| ProductVersion: | 132.0.6855.0 |
| CompanyShortName: | BrowseAI LLC |
| ProductShortName: | AceUpdater |
| LastChange: | 0000000000000000000000000000000000000000 |
| OfficialBuild: | 1 |
Total processes
389
Monitored processes
109
Malicious processes
18
Suspicious processes
49
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Ace\Ace\Application\ace.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Ace\Ace\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Ace\Ace\User Data\Crashpad" --annotation=plat=Win64 --annotation=prod=Ace --annotation=ver=132.0.6855.0 --initial-client-data=0x124,0x128,0x12c,0x100,0x130,0x7ffc45d6e7b8,0x7ffc45d6e7c4,0x7ffc45d6e7d0 | C:\Program Files\Ace\Ace\Application\ace.exe | — | ace.exe | |||||||||||
User: admin Company: BrowseAI LLC Integrity Level: MEDIUM Description: Ace Exit code: 0 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\AppData\Local\Temp\AceSetup.exe" | C:\Users\admin\AppData\Local\Temp\AceSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: BrowseAI LLC Integrity Level: MEDIUM Description: Ace Installer Exit code: 0 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1356 | "C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\CR_C17AC.tmp\setup.exe" --install-archive="C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\CR_C17AC.tmp\CHROME.PACKED.7Z" --do-not-launch-chrome | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\CR_C17AC.tmp\setup.exe | mini_installer.exe | ||||||||||||
User: SYSTEM Company: BrowseAI LLC Integrity Level: SYSTEM Description: Ace Installer Exit code: 0 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Ace\Ace\Application\132.0.6855.0\Installer\chrmstp.exe" --system-level --verbose-logging --installerdata="C:\Program Files\Ace\Ace\Application\master_preferences" --create-shortcuts=1 --install-level=0 | C:\Program Files\Ace\Ace\Application\132.0.6855.0\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: admin Company: BrowseAI LLC Integrity Level: MEDIUM Description: Ace Installer Exit code: 73 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Ace\Ace\Application\ace.exe" --type=renderer --string-annotations --start-stack-profiler --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3124,i,7682421411978712177,6666209489985857058,262144 --variations-seed-version --mojo-platform-channel-handle=3136 /prefetch:1 | C:\Program Files\Ace\Ace\Application\ace.exe | — | ace.exe | |||||||||||
User: admin Company: BrowseAI LLC Integrity Level: LOW Description: Ace Exit code: 0 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Ace\AceUpdater\132.0.6855.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Ace\AceUpdater\132.0.6855.0\Crashpad" --url=https://clients2.google.com/cr/staging_report --annotation=prod=AceUpdater --annotation=ver=132.0.6855.0 "--attachment=C:\Program Files (x86)\Ace\AceUpdater\updater.log" --initial-client-data=0x258,0x25c,0x260,0x234,0x264,0x7ff640854094,0x7ff6408540a0,0x7ff6408540b0 | C:\Program Files (x86)\Ace\AceUpdater\132.0.6855.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: BrowseAI LLC Integrity Level: SYSTEM Description: Ace Updater Exit code: 0 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1932 | "C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\CR_C17AC.tmp\setup.exe" --system-level --verbose-logging --create-shortcuts=0 --install-level=1 | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\CR_C17AC.tmp\setup.exe | — | setup.exe | |||||||||||
User: SYSTEM Company: BrowseAI LLC Integrity Level: SYSTEM Description: Ace Installer Exit code: 73 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Ace\Ace\Application\ace.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --string-annotations --start-stack-profiler --field-trial-handle=2256,i,7682421411978712177,6666209489985857058,262144 --variations-seed-version --mojo-platform-channel-handle=2272 /prefetch:3 | C:\Program Files\Ace\Ace\Application\ace.exe | ace.exe | ||||||||||||
User: admin Company: BrowseAI LLC Integrity Level: MEDIUM Description: Ace Exit code: 0 Version: 132.0.6855.0 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 1520 -prefsLen 39068 -prefMapHandle 1556 -prefMapSize 272997 -jsInitHandle 2280 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4152 -initialChannelId {9c6f9e08-3c74-43fd-9732-8ca017fccb9c} -parentPid 3620 -crashReporter "\\.\pipe\gecko-crash-server-pipe.3620" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
Total events
27 937
Read events
27 577
Write events
340
Delete events
20
Modification events
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ace\Update |
| Operation: | write | Name: | iid |
Value: 2b7de892-4865-11f0-b9f3-ba1e7b944c2b@8ccafd84-47c9-11f0-9972-3e790454ca80@ | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ace\Update\Clients\{ccb30364-74c7-4a6e-9b50-bc5471c59a9b} |
| Operation: | write | Name: | pv |
Value: 132.0.6855.0 | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ace\Update\Clients\{ccb30364-74c7-4a6e-9b50-bc5471c59a9b} |
| Operation: | write | Name: | name |
Value: AceUpdater | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ace\Update\ClientState\{ccb30364-74c7-4a6e-9b50-bc5471c59a9b} |
| Operation: | write | Name: | pv |
Value: 132.0.6855.0 | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ace\Update\ClientState\{ccb30364-74c7-4a6e-9b50-bc5471c59a9b} |
| Operation: | write | Name: | name |
Value: AceUpdater | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B41A39A6-7CFC-5948-8625-E54B6B18DF6F} |
| Operation: | write | Name: | AppID |
Value: {B41A39A6-7CFC-5948-8625-E54B6B18DF6F} | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{B41A39A6-7CFC-5948-8625-E54B6B18DF6F} |
| Operation: | write | Name: | LocalService |
Value: AceUpdaterInternalService132.0.6855.0 | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{B41A39A6-7CFC-5948-8625-E54B6B18DF6F} |
| Operation: | write | Name: | ServiceParameters |
Value: --com-service | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{5F43CC9F-3A58-591C-A125-BC822F6692AB}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (2216) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{5F43CC9F-3A58-591C-A125-BC822F6692AB}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
Executable files
7
Suspicious files
407
Text files
205
Unknown types
334
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3732 | AceSetup.exe | C:\Windows\SystemTemp\Ace3732_2098864898\UPDATER.PACKED.7Z | — | |
MD5:— | SHA256:— | |||
| 4920 | updater.exe | C:\Windows\SystemTemp\chrome_url_fetcher_4920_1377325825\browser-builds_new-version-v132.0.6855.0_x64_2025-06-08T06-36-42Z__signed__j0x98NR.crx3 | — | |
MD5:— | SHA256:— | |||
| 4920 | updater.exe | C:\Program Files (x86)\Ace\AceUpdater\crx_cache\{908aaf3d-6daa-4f36-a9b0-538d90bec8c1}_1.a09ff05e7b2cf8383127a5ddf54db2ce9511296fe63baa205e0d27a98d5e16a5 | — | |
MD5:— | SHA256:— | |||
| 4920 | updater.exe | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\mini_installer.exe | — | |
MD5:— | SHA256:— | |||
| 2216 | updater.exe | C:\Program Files (x86)\Ace\AceUpdater\132.0.6855.0\updater.exe | executable | |
MD5:03D5CAE439B411BD70C3D7CE7B3A5818 | SHA256:B4F893592A2910986FEE91E2B6A956F03380025C68971F0A767C416499B0DE60 | |||
| 3588 | updater.exe | C:\Program Files (x86)\Ace\Update\AceUpdate.exe | executable | |
MD5:03D5CAE439B411BD70C3D7CE7B3A5818 | SHA256:B4F893592A2910986FEE91E2B6A956F03380025C68971F0A767C416499B0DE60 | |||
| 4192 | mini_installer.exe | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping4920_967090947\CR_C17AC.tmp\CHROME.PACKED.7Z | — | |
MD5:— | SHA256:— | |||
| 3588 | updater.exe | C:\Program Files (x86)\Ace\AceUpdater\132.0.6855.0\08665b7d-a0bf-4468-b0bd-8c5392ebb143.tmp | binary | |
MD5:AA2D0C0C72BB528CF4168EA91C1C9A56 | SHA256:E03E9D262CA3B7D19E37C3A69C7D8B46BD3F5542AA555A17D864071C28257B2C | |||
| 2216 | updater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | der | |
MD5:1FBB37F79B317A9A248E7C4CE4F5BAC5 | SHA256:9BF639C595FE335B6F694EE35990BEFD2123F5E07FD1973FF619E3FC88F5F49F | |||
| 3588 | updater.exe | C:\Program Files (x86)\Ace\AceUpdater\prefs.json~RF176b0e.TMP | binary | |
MD5:E5A96940AA6911B29D172B20CD0EF9E0 | SHA256:1929773751D626A5DA39016FBE2E49C4C1DBFCE8486D61900AF1A34E938C0B85 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
156
DNS requests
175
Threats
83
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2216 | updater.exe | GET | 200 | 142.250.185.67:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
2216 | updater.exe | GET | 200 | 142.250.185.67:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
2216 | updater.exe | GET | 200 | 172.217.18.3:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCECICm33H9sWHCv79w8Zjw%2BM%3D | US | binary | 280 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6700 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
6700 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
7212 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:WzO4FWsrH_6626CjJnEPLiunUkvnD-JeM7TVFccwZVc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
5848 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3572 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4920 | updater.exe | 104.22.33.172:443 | update.ace.ai | CLOUDFLARENET | — | unknown |
2216 | updater.exe | 216.58.206.78:443 | dl.google.com | GOOGLE | US | whitelisted |
2216 | updater.exe | 142.250.185.67:80 | c.pki.goog | GOOGLE | US | whitelisted |
2216 | updater.exe | 172.217.18.3:80 | o.pki.goog | GOOGLE | US | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
update.ace.ai |
| unknown |
dl.google.com |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6012 | ace.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
Process | Message |
|---|---|
ace.exe | [0613/144746.256:ERROR:crash_report_database_win.cc(613)] CreateDirectory C:\Users\admin\AppData\Local\Ace\Ace\User Data\Crashpad: The system cannot find the path specified. (0x3)
|