| File name: | p.exe |
| Full analysis: | https://app.any.run/tasks/885dc951-d657-40d1-a39c-6c7346af7d27 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2020, 10:57:35 |
| OS: | Windows 10 Professional (build: 16299, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | AFEACC939AA01ED4CECBF85209371C32 |
| SHA1: | D9069BC3731396BEAE6D329DBB3EB2B4DFB8C182 |
| SHA256: | A39D375B4498174CA49F07D6BC5A152D34BBB3B7681B209125F2A1C7A8B01185 |
| SSDEEP: | 12288:79l7Z89NK3QMI+hJIUJ1BO6ENJDm7NEu1bMrjasSH6h+IwyE1U1Q4RB:N823++hJIC1BG5mxbgZHhW1U |
MALICIOUS
Uses Task Scheduler to run other applications
- p.exe (PID: 3592)
- p.exe (PID: 3496)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2372)
- schtasks.exe (PID: 3692)
Application was dropped or rewritten from another process
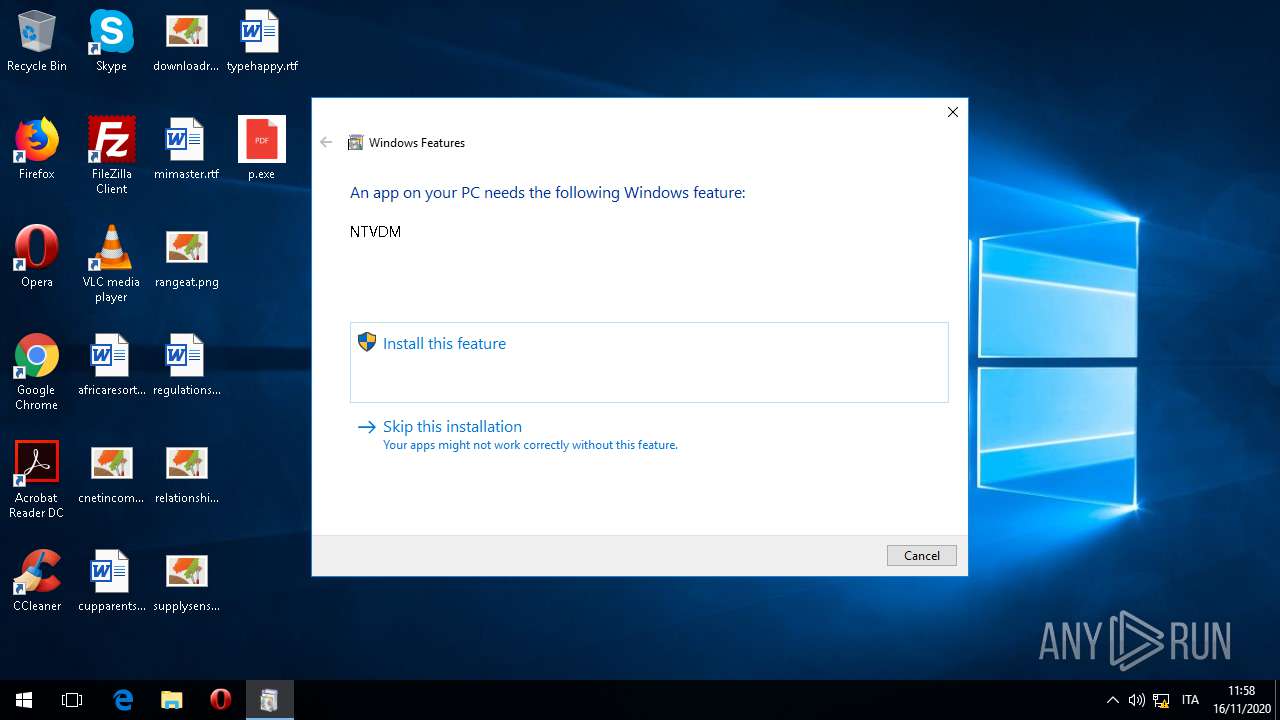
- ntvdm.exe (PID: 1672)
- ntvdm.exe (PID: 3912)
Loads dropped or rewritten executable
- ntvdm.exe (PID: 1672)
- ntvdm.exe (PID: 3912)
SUSPICIOUS
Executable content was dropped or overwritten
- p.exe (PID: 3592)
- p.exe (PID: 1280)
- TiWorker.exe (PID: 2564)
Creates files in the user directory
- p.exe (PID: 3592)
Application launched itself
- p.exe (PID: 3592)
- p.exe (PID: 3496)
Executed via COM
- TiWorker.exe (PID: 2564)
Uses RUNDLL32.EXE to load library
- p.exe (PID: 1280)
Executes application which crashes
- p.exe (PID: 1280)
- p.exe (PID: 1472)
Creates files in the Windows directory
- TiWorker.exe (PID: 2564)
Removes files from Windows directory
- TiWorker.exe (PID: 2564)
INFO
Reads the software policy settings
- TiWorker.exe (PID: 2564)
Manual execution by user
- p.exe (PID: 3496)
Dropped object may contain Bitcoin addresses
- TiWorker.exe (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:16 10:46:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 726528 |
| InitializedDataSize: | 107008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb34c2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Russian Roulette Game |
| FileVersion: | 1.0.0.0 |
| InternalName: | sIwA.exe |
| LegalCopyright: | Copyright © 2016 - 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | sIwA.exe |
| ProductName: | Russian Roulette Game |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Nov-2020 09:46:16 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Russian Roulette Game |
| FileVersion: | 1.0.0.0 |
| InternalName: | sIwA.exe |
| LegalCopyright: | Copyright © 2016 - 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | sIwA.exe |
| ProductName: | Russian Roulette Game |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Nov-2020 09:46:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000B14C8 | 0x000B1600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.52743 |
.rsrc | 0x000B4000 | 0x00019FFC | 0x0001A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.88202 |
.reloc | 0x000CE000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.2201 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.2865 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.52387 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.54785 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.12219 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
69
Monitored processes
17
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | "C:\Users\admin\Desktop\p.exe" | C:\Users\admin\Desktop\p.exe | p.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Russian Roulette Game Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1472 | "C:\Users\admin\Desktop\p.exe" | C:\Users\admin\Desktop\p.exe | — | p.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Russian Roulette Game Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
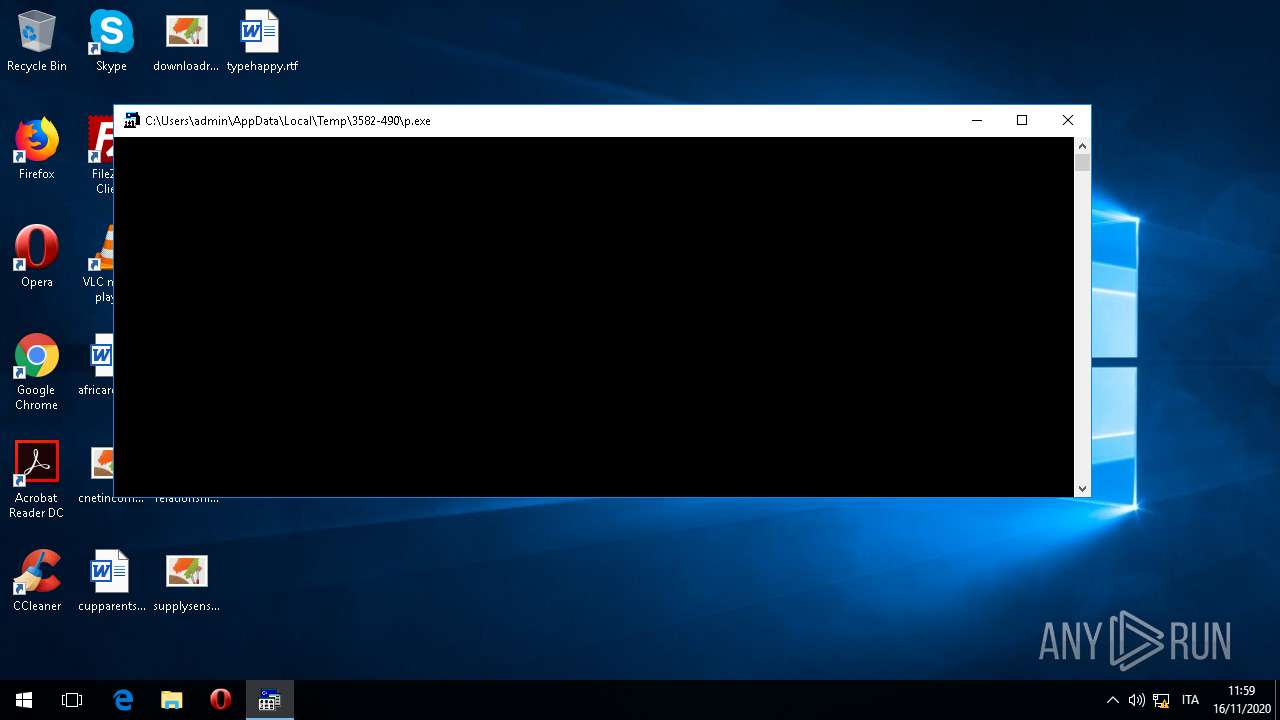
| 1672 | "C:\WINDOWS\system32\ntvdm.exe" -i1 | C:\WINDOWS\system32\ntvdm.exe | — | p.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
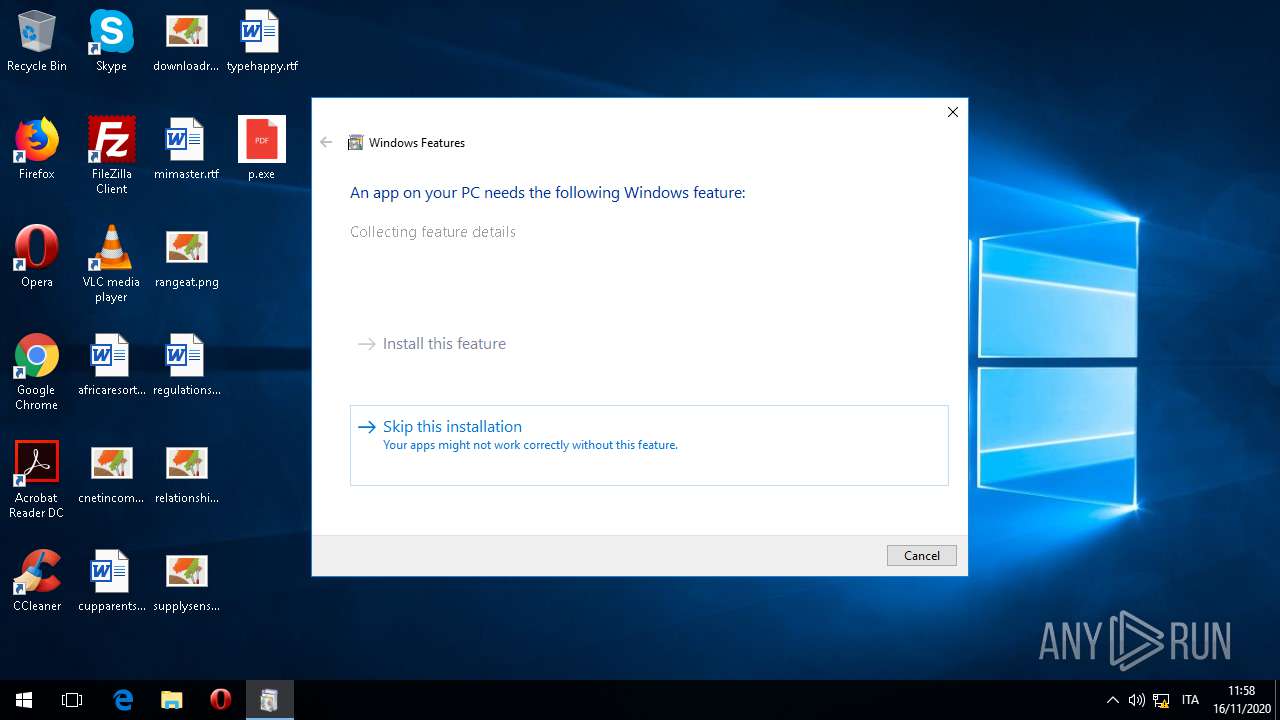
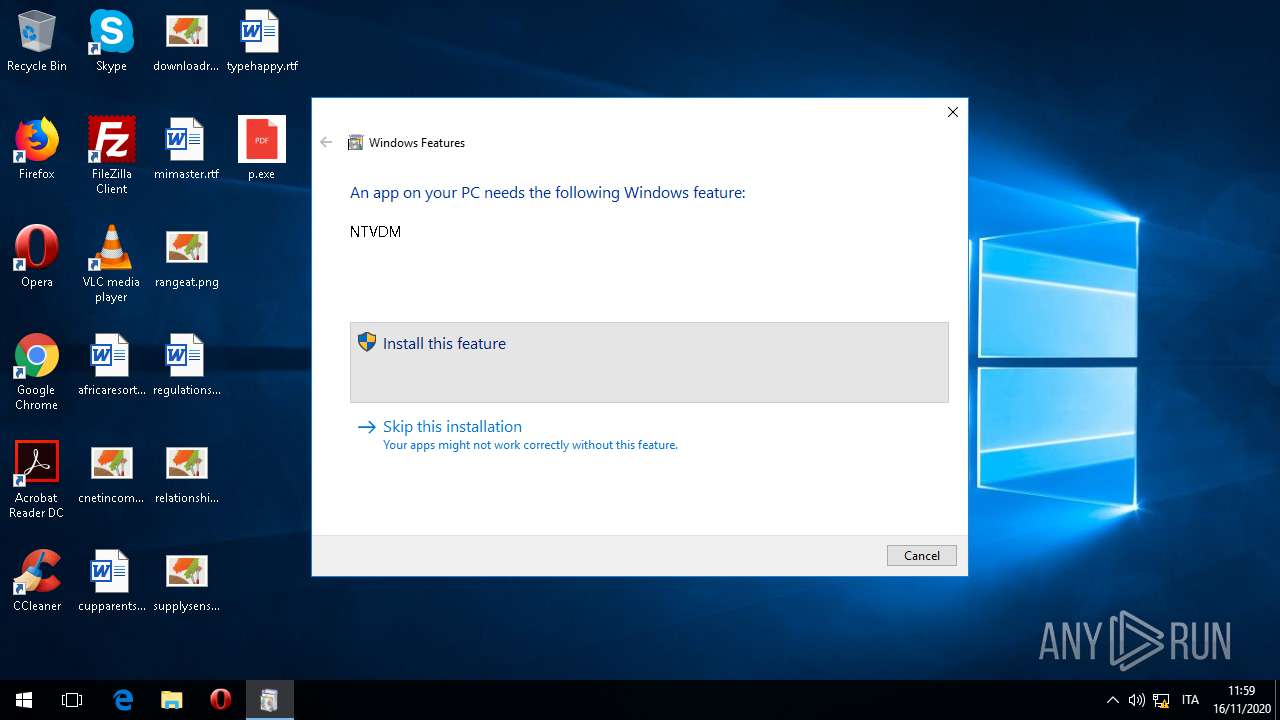
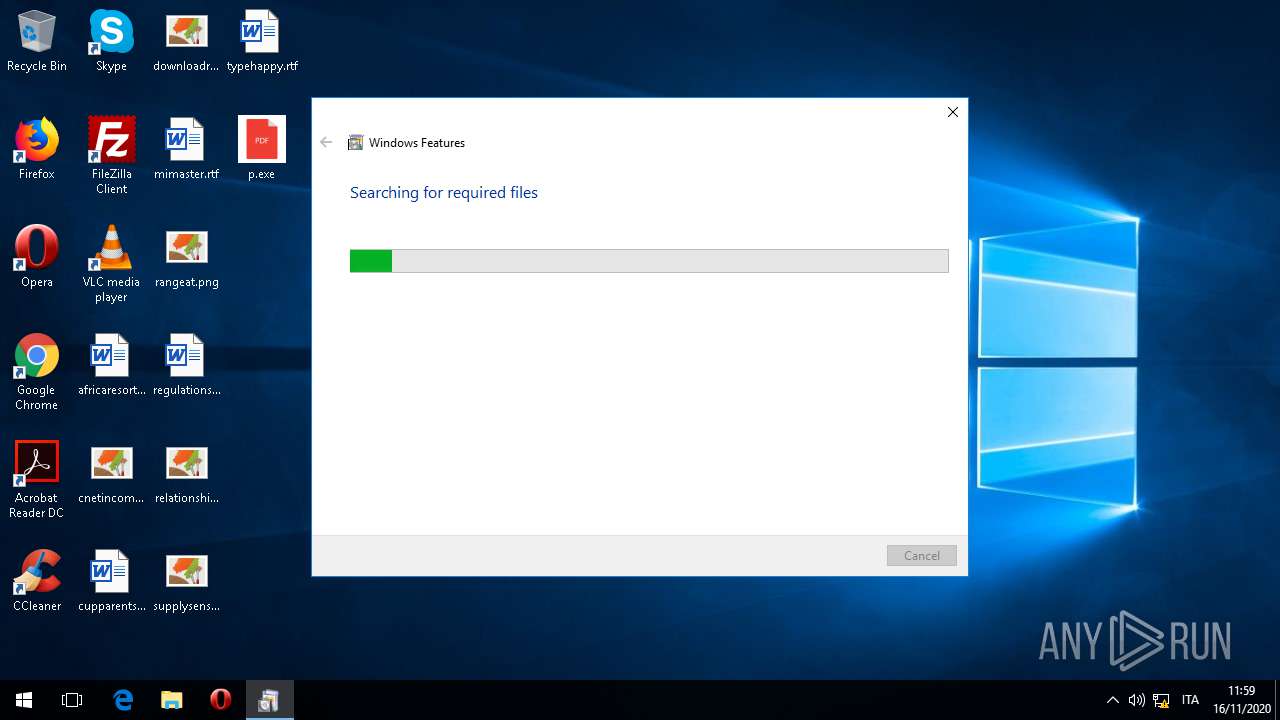
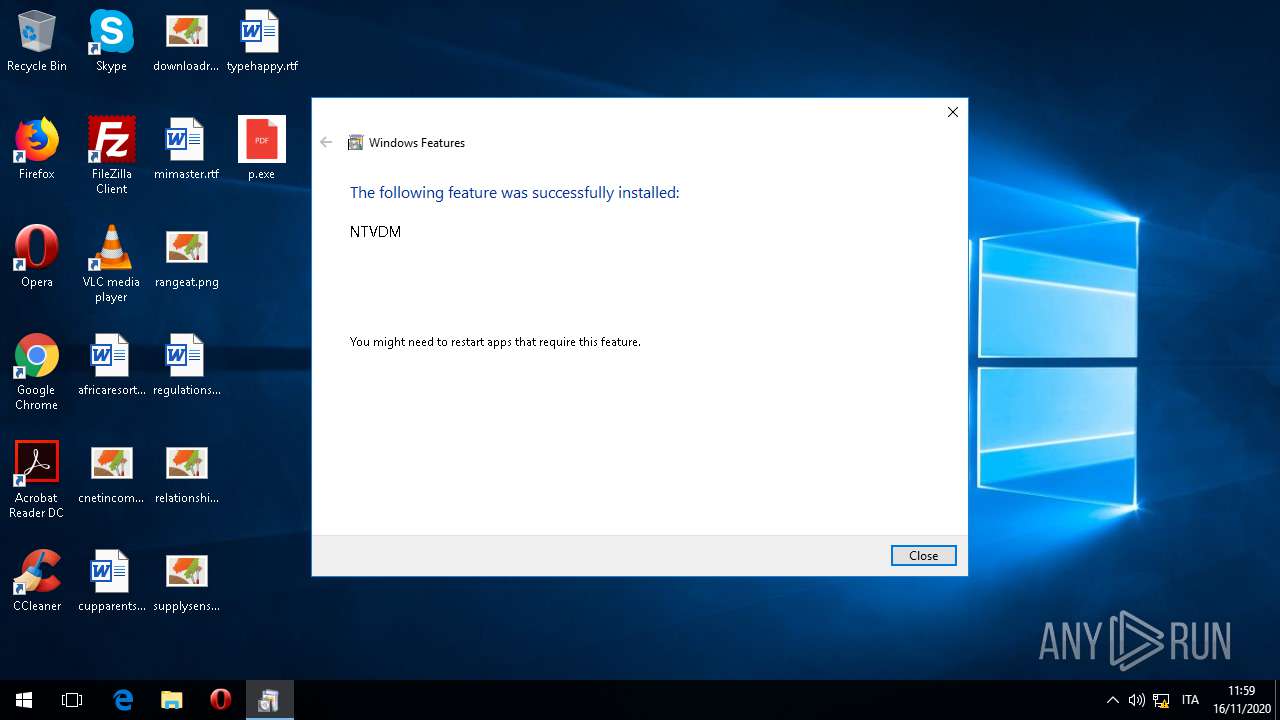
| 1748 | Fondue.exe /enable-feature:NTVDM /caller-name:"C:\Users\admin\AppData\Local\Temp\3582-490\p.exe" | C:\WINDOWS\system32\Fondue.exe | — | RunDll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Features on Demand UX Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2372 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\NOhvjlxDGIQgy" /XML "C:\Users\admin\AppData\Local\Temp\tmp3C75.tmp" | C:\Windows\System32\schtasks.exe | — | p.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | C:\WINDOWS\winsxs\x86_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.16299.245_none_bacd821279b53501\TiWorker.exe -Embedding | C:\WINDOWS\winsxs\x86_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.16299.245_none_bacd821279b53501\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2676 | C:\WINDOWS\system32\RunDll32.exe shell32.dll,Control_RunDLL ntvdmcpl.dll,,/originalapp:"C:\Users\admin\AppData\Local\Temp\3582-490\p.exe" | C:\WINDOWS\system32\RunDll32.exe | — | p.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | — | ntvdm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | — | ntvdm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\Desktop\p.exe" | C:\Users\admin\Desktop\p.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Russian Roulette Game Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 789
Read events
2 058
Write events
340
Delete events
391
Modification events
| (PID) Process: | (3592) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3592) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3592) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3592) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1280) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1280) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1280) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1280) p.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2564) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide |
| Operation: | write | Name: | LastScavengingStarvationReport |
Value: 14736E7507BCD601 | |||
| (PID) Process: | (2564) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 30850055 | |||
Executable files
95
Suspicious files
38
Text files
19
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\WFWNET.DRV | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\olecli.dll | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\MMSYSTEM.DLL | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\COMMDLG.DLL | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\SHELL.DLL | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\stdole.tlb | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\ver.dll | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\lzexpand.dll | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | C:\WINDOWS\WinSxS\Temp\InFlight\dd0a378207bcd60105000000040a5407\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\OLESVR.DLL | — | |
MD5:— | SHA256:— | |||
| 2564 | TiWorker.exe | \SystemRoot\WinSxS\x86_microsoft-windows-ntvdm-system-payload_31bf3856ad364e35_10.0.16299.15_none_0e1f6378cb96cf9e\WFWNET.DRV | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |