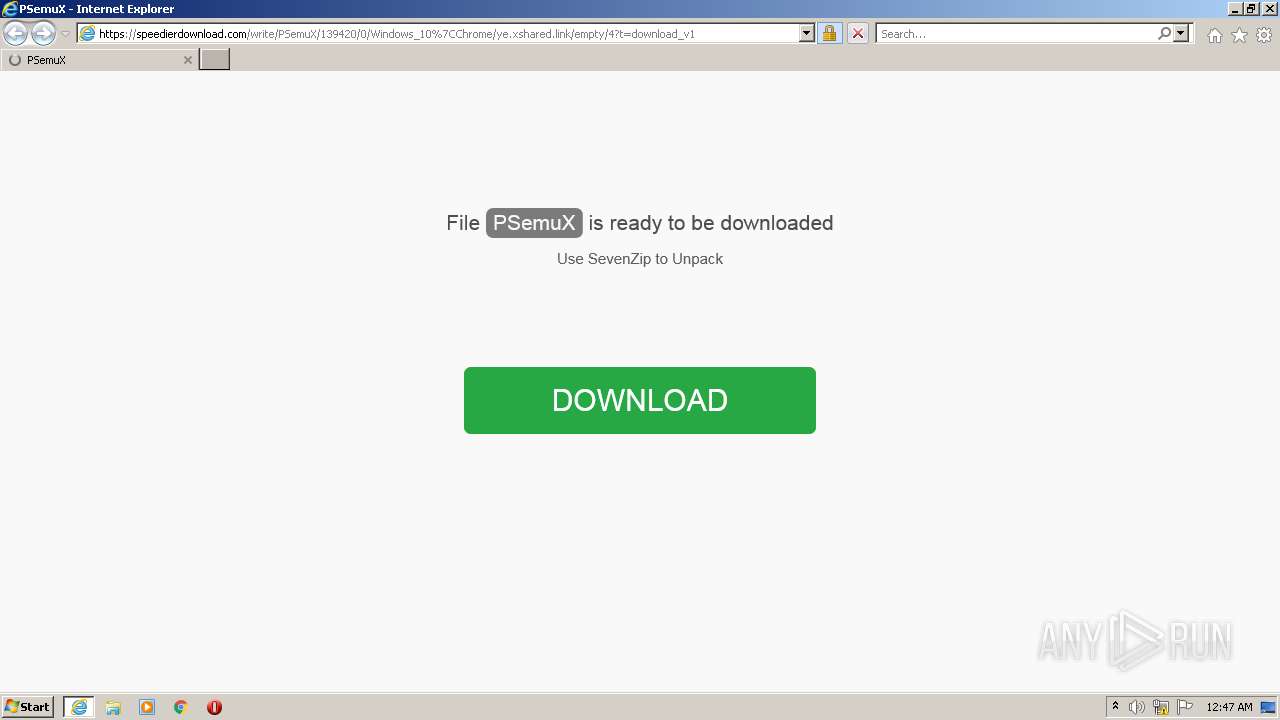
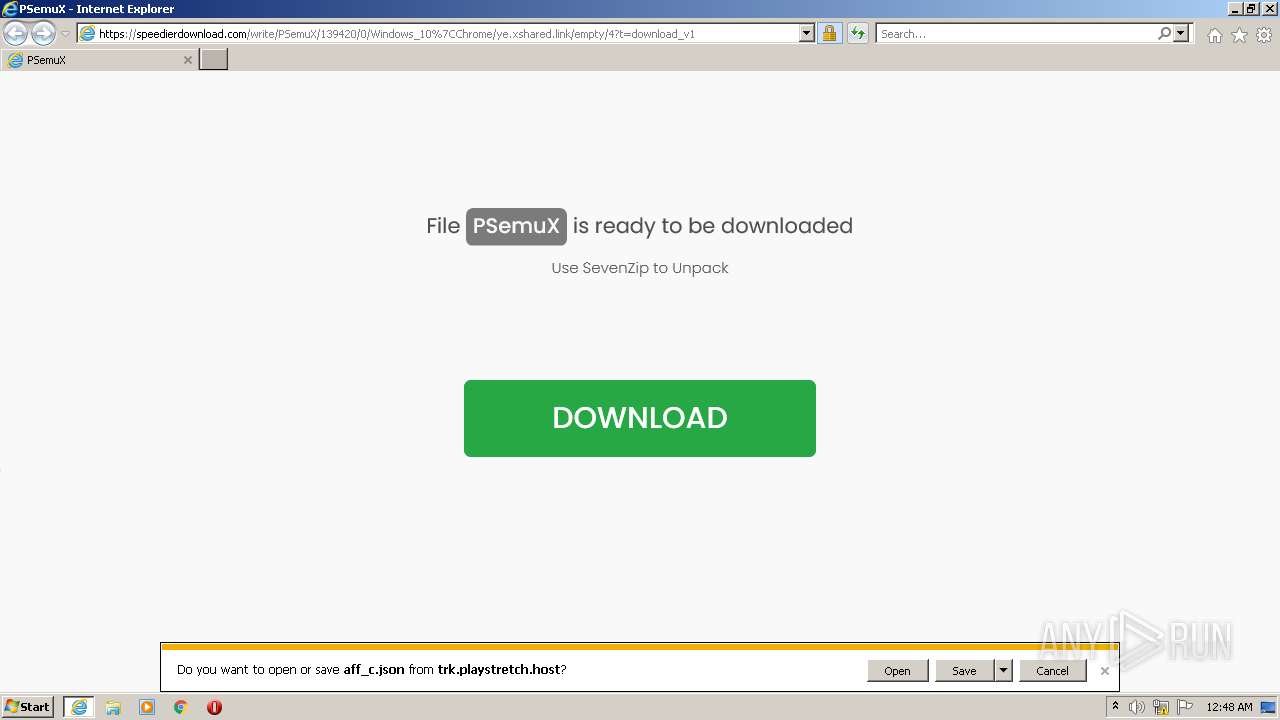
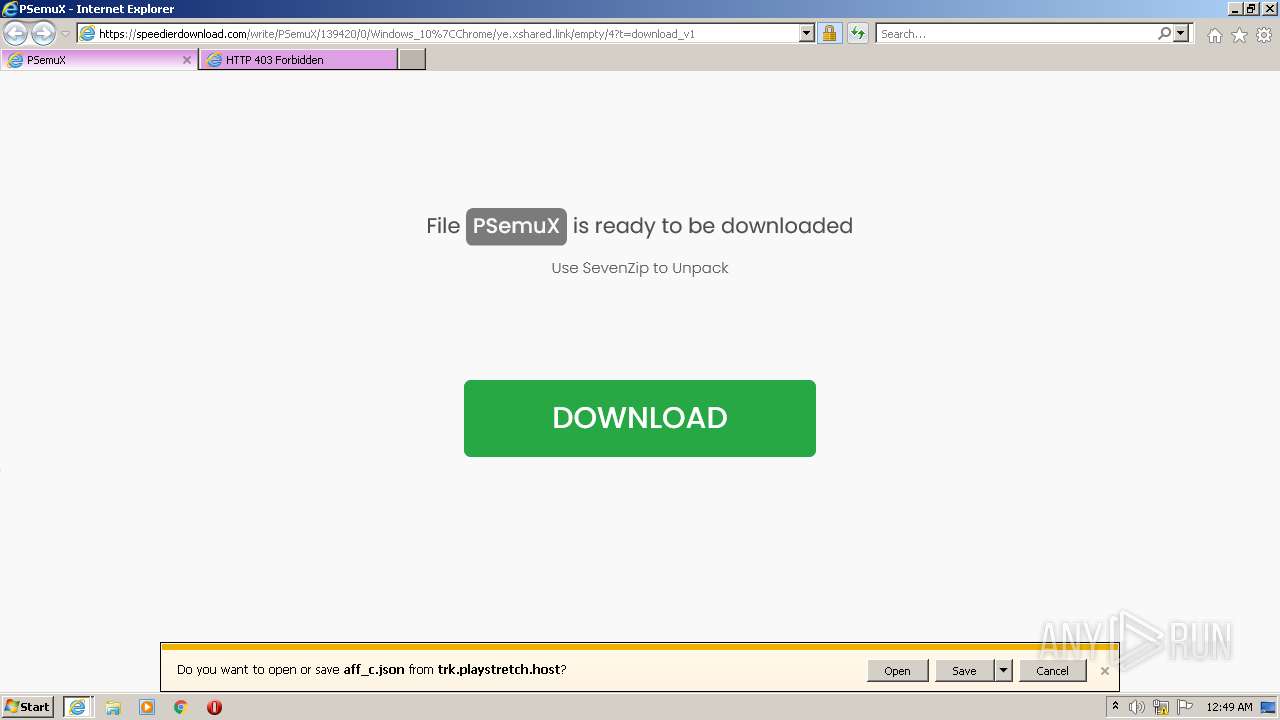
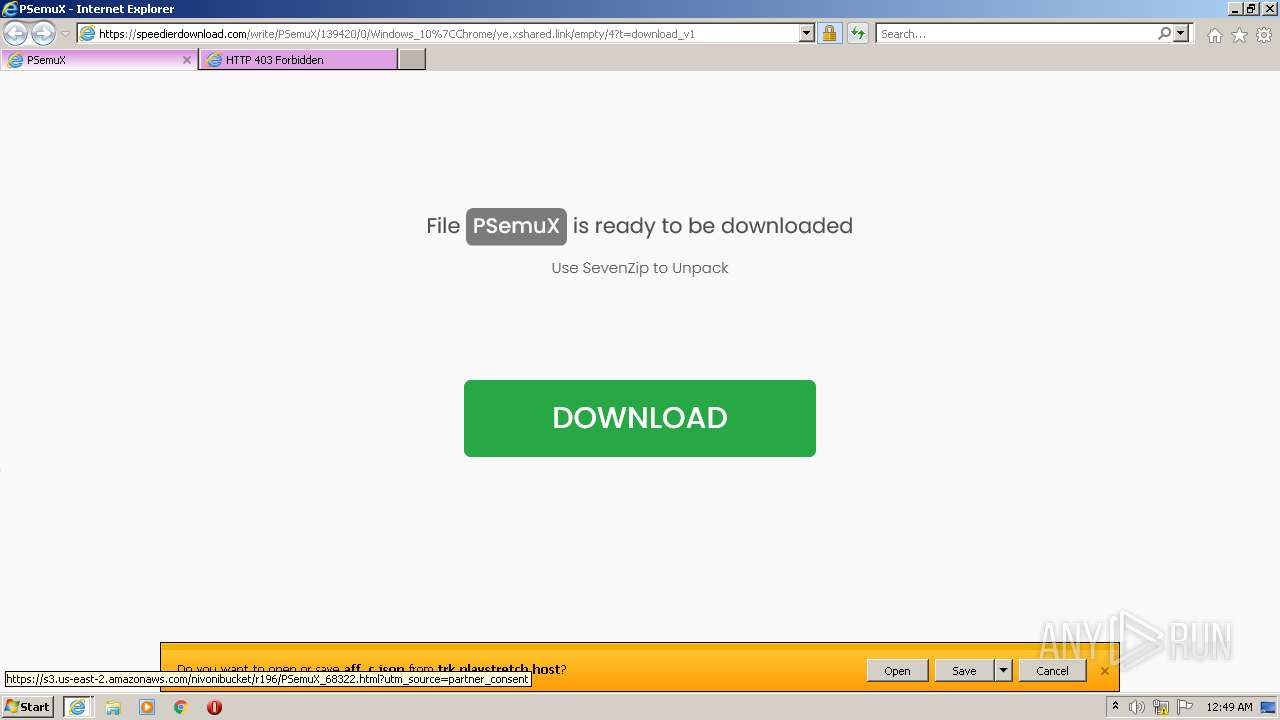
| URL: | https://speedierdownload.com/write/PSemuX/139420/0/Windows_10%7CChrome/ye.xshared.link/empty/4?t=download_v1 |
| Full analysis: | https://app.any.run/tasks/7ece1553-8f83-4e9a-ba7b-55d83193576f |
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2022, 00:47:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4F6764FC9737D3BD0D055C56B115A7C7 |
| SHA1: | 78633C9EFF3E6B718A257D911604E24A4D03FF0E |
| SHA256: | A396E99CC27F1449487EC33E834398D7035332DA3505BA5C36799D0410D6E274 |
| SSDEEP: | 3:N8YbhBJLnKZMRAYTRXfyK8S2qSDolQX6ZY84WY:2YNDKZMR/yK8S2qjla6t4N |
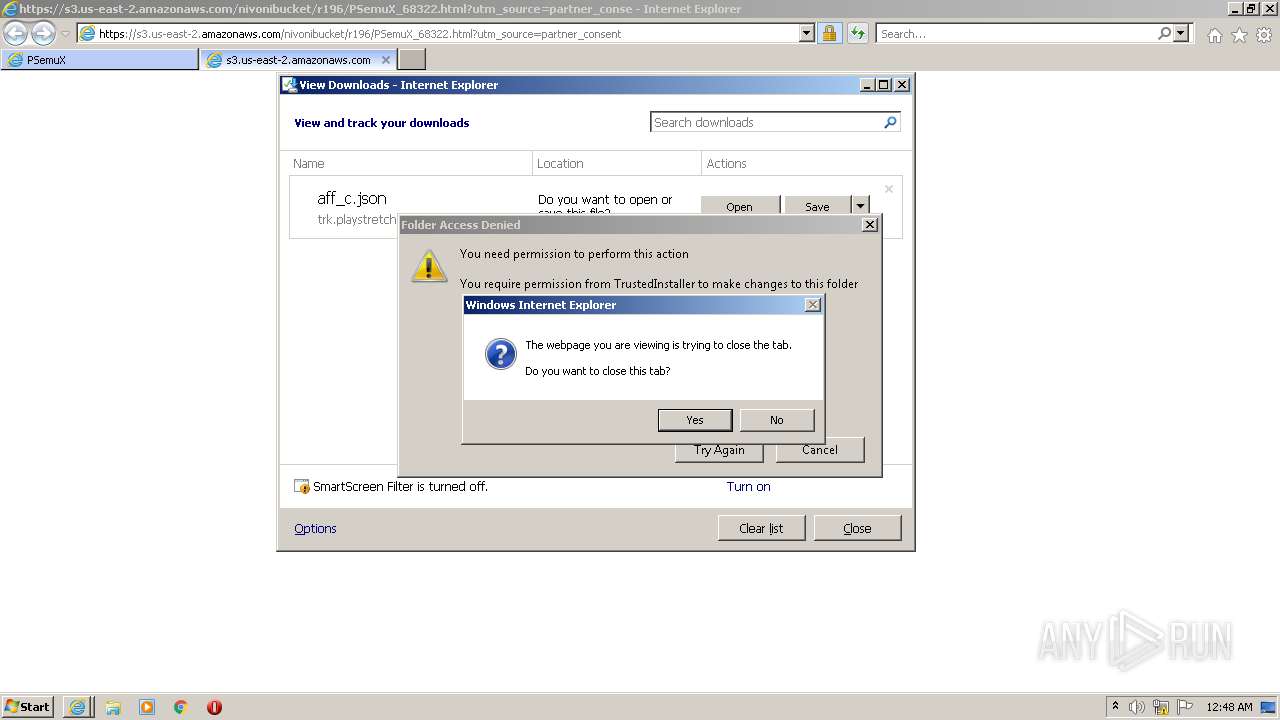
MALICIOUS
Application was dropped or rewritten from another process
- PSemuX_68322.exe (PID: 4080)
SUSPICIOUS
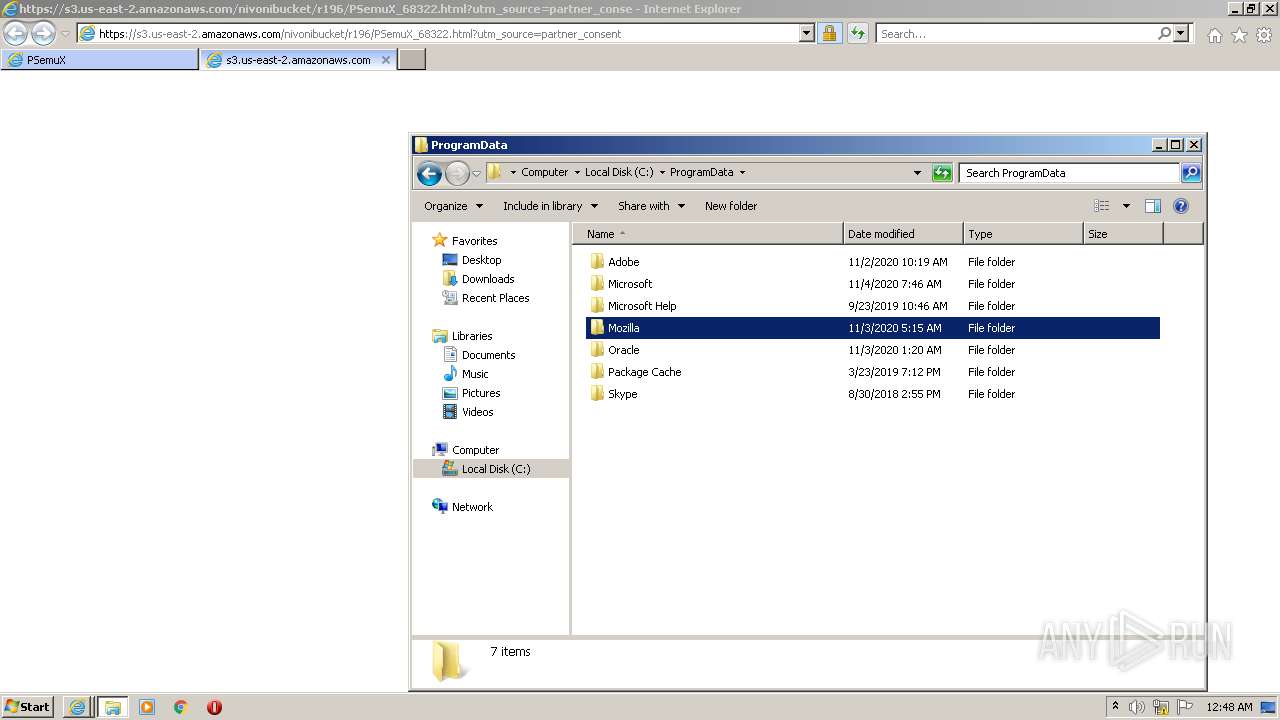
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 2188)
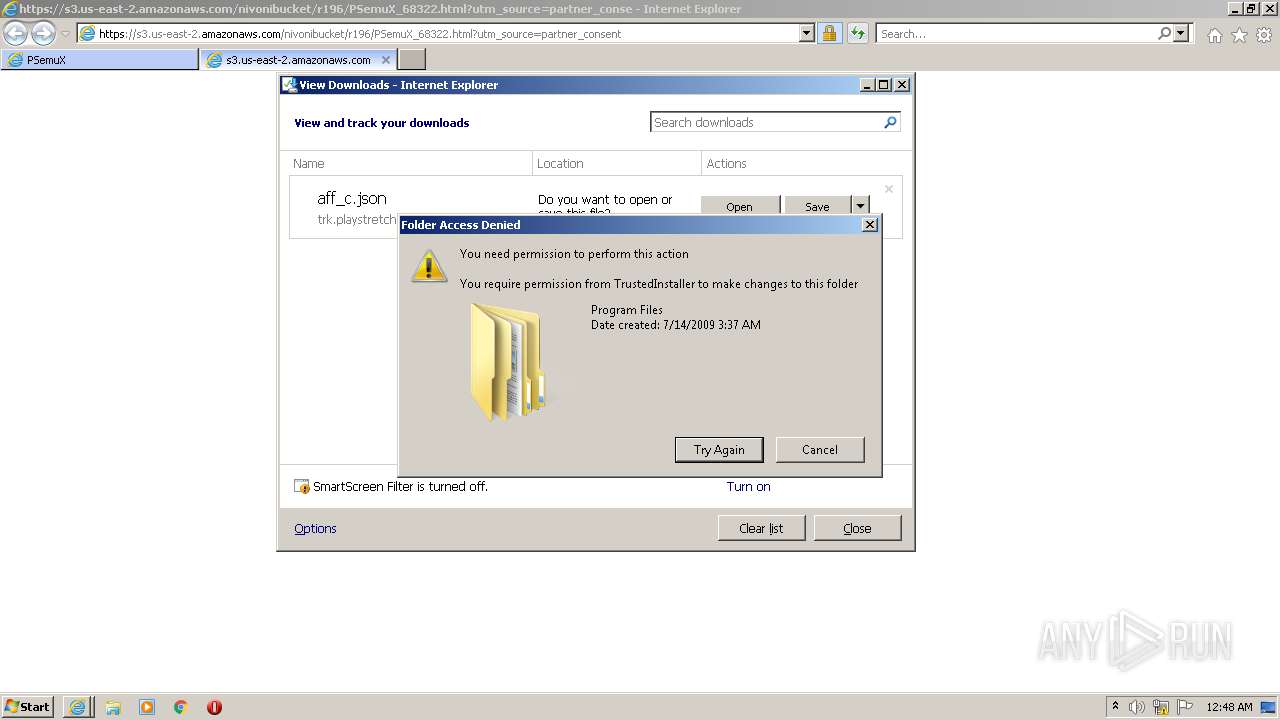
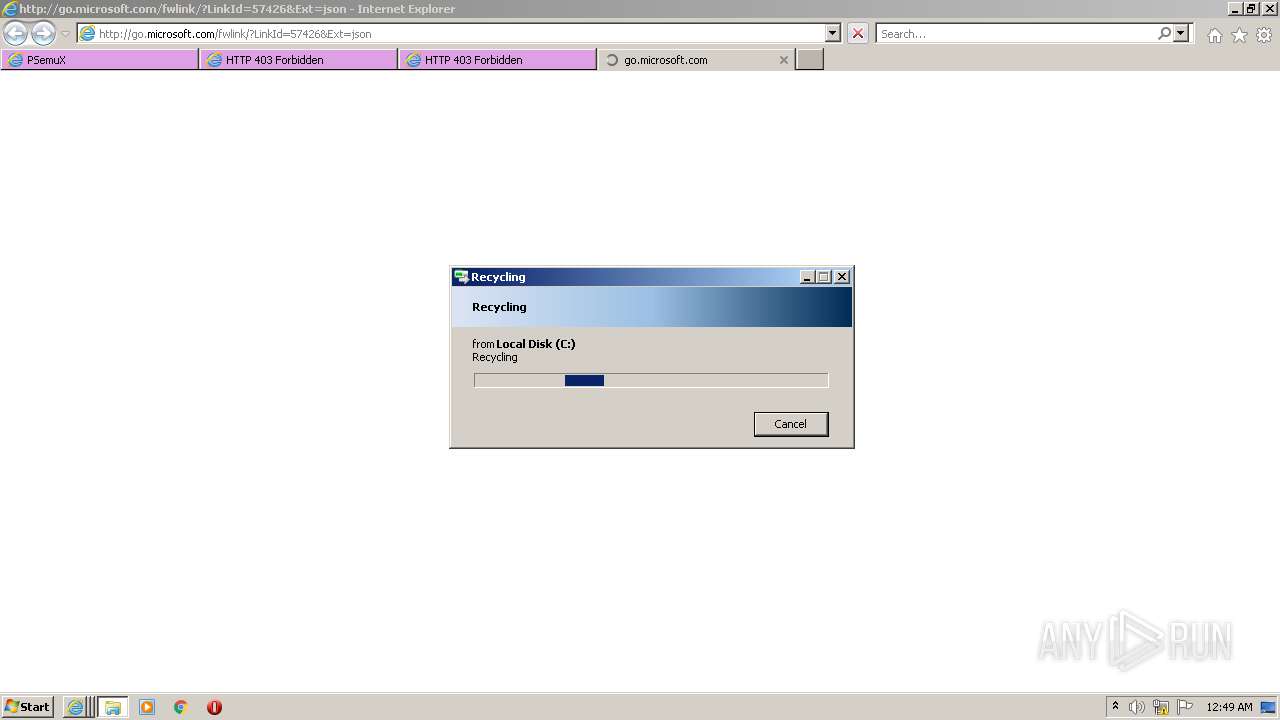
Executable content was dropped or overwritten
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 3724)
Checks supported languages
- PSemuX_68322.exe (PID: 4080)
Reads the computer name
- PSemuX_68322.exe (PID: 4080)
Executed via COM
- DllHost.exe (PID: 3668)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3724)
INFO
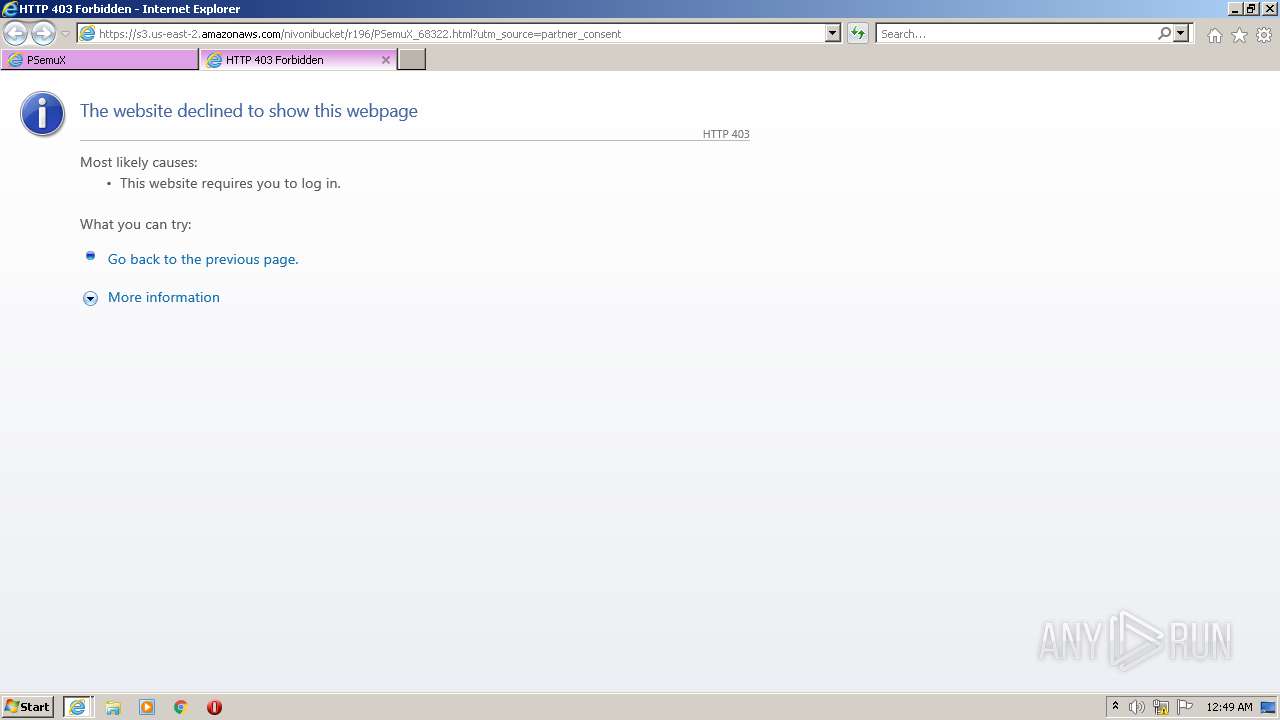
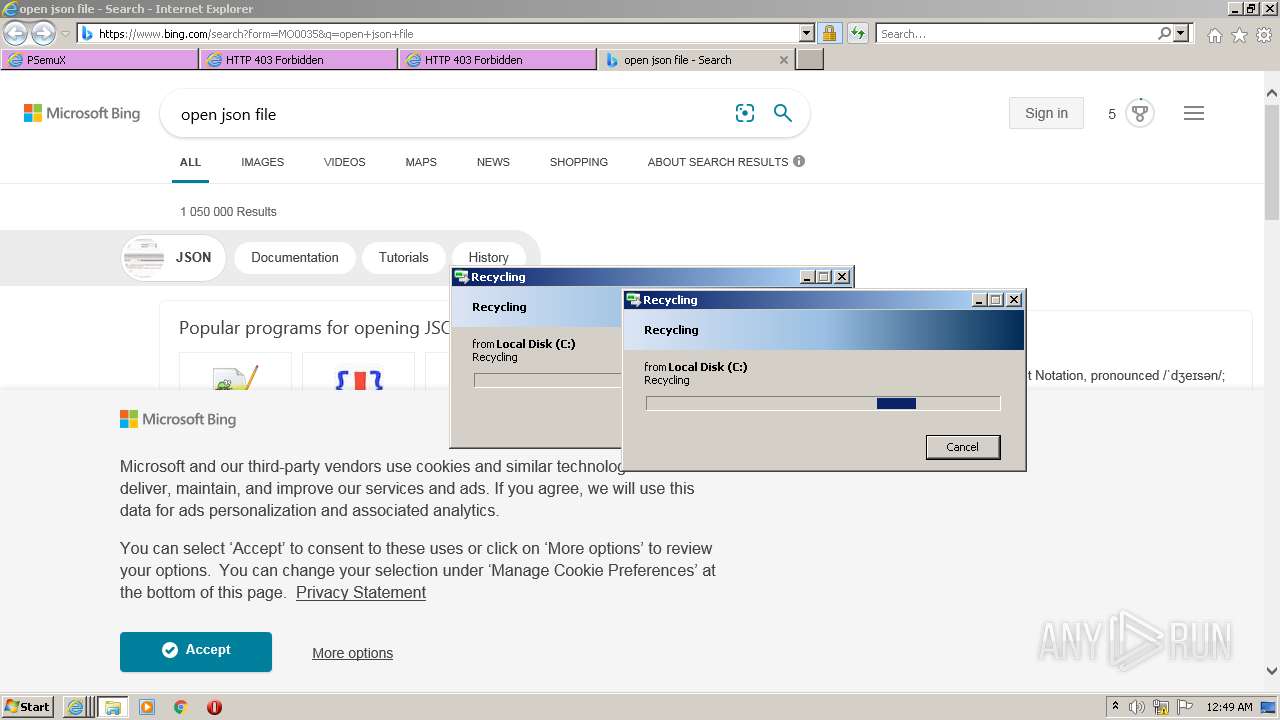
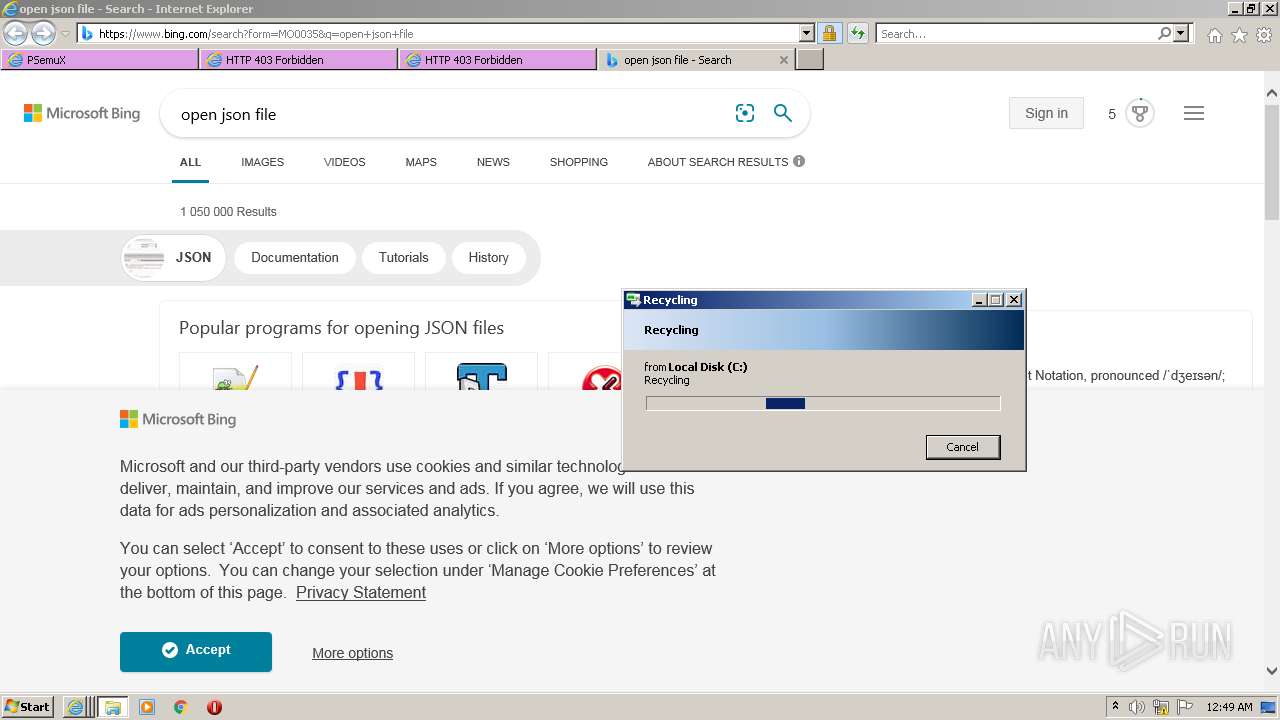
Application launched itself
- iexplore.exe (PID: 3724)
Checks Windows Trust Settings
- iexplore.exe (PID: 3724)
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 2188)
Reads the computer name
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 3724)
- explorer.exe (PID: 3372)
- DllHost.exe (PID: 3668)
Changes internet zones settings
- iexplore.exe (PID: 3724)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3724)
Reads settings of System Certificates
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 3724)
- iexplore.exe (PID: 572)
Checks supported languages
- iexplore.exe (PID: 3724)
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 572)
- DllHost.exe (PID: 3668)
- explorer.exe (PID: 3372)
Reads internet explorer settings
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 2188)
Changes settings of System certificates
- iexplore.exe (PID: 3724)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3724)
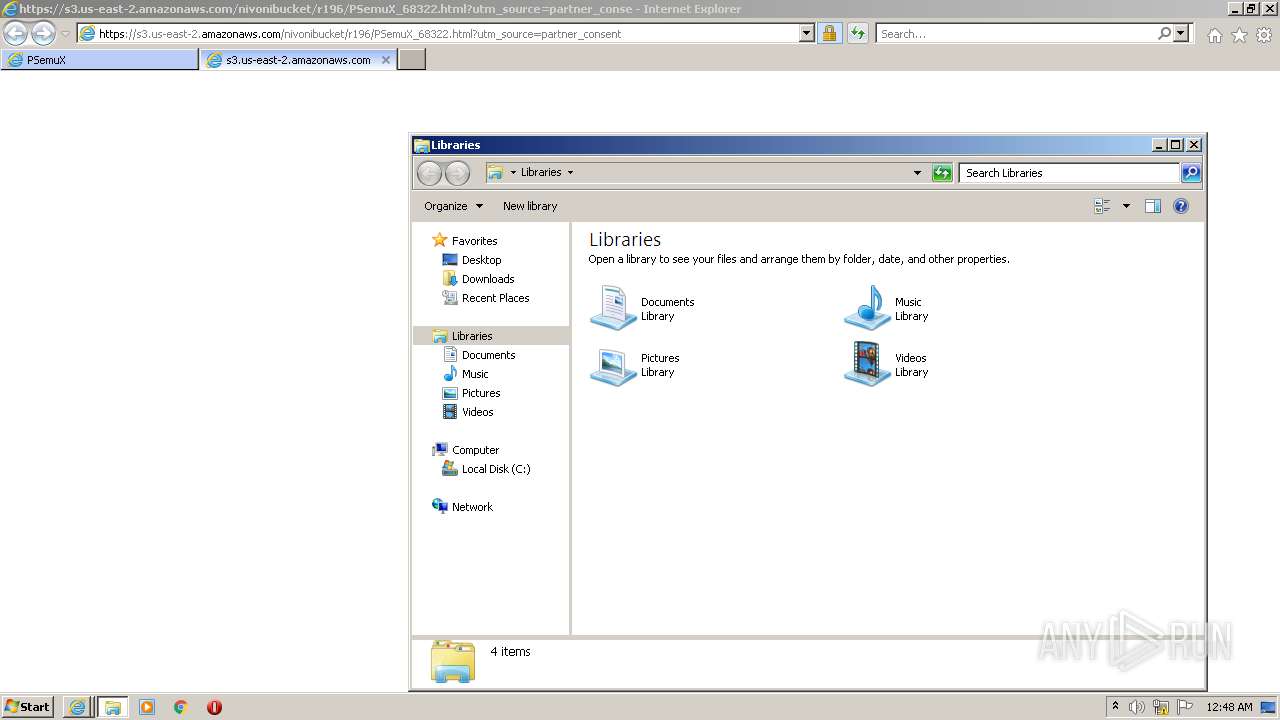
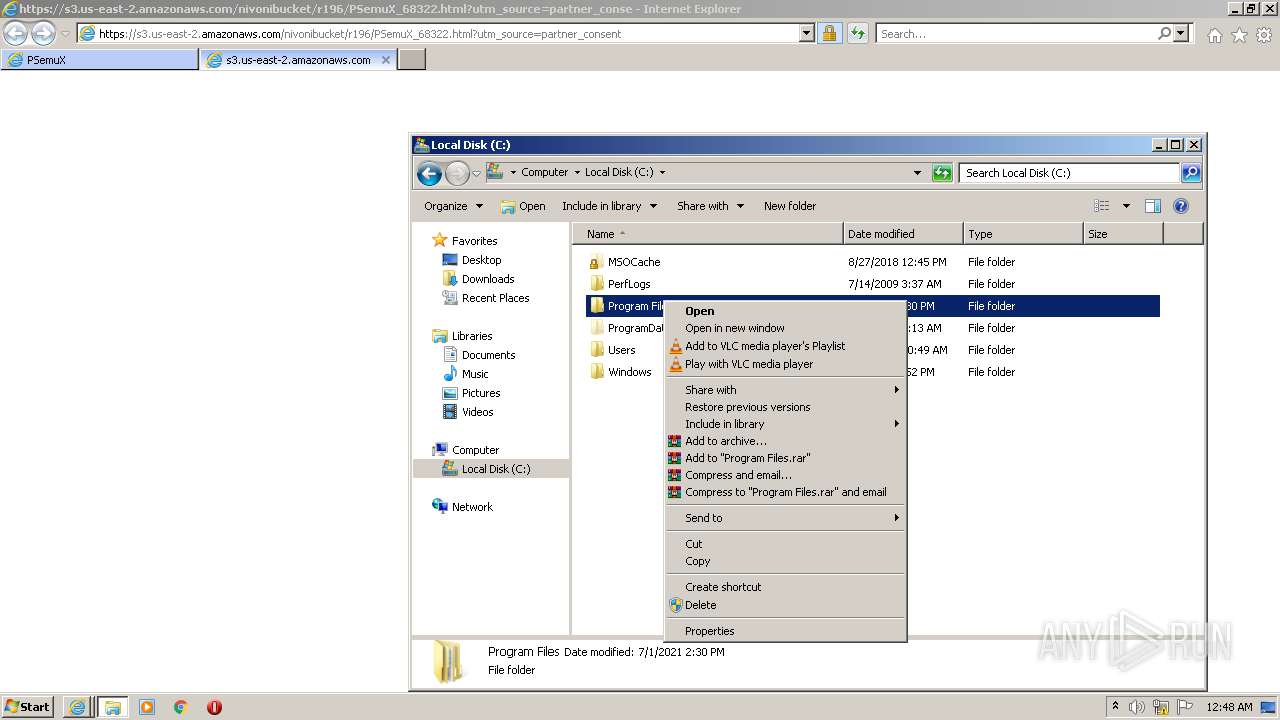
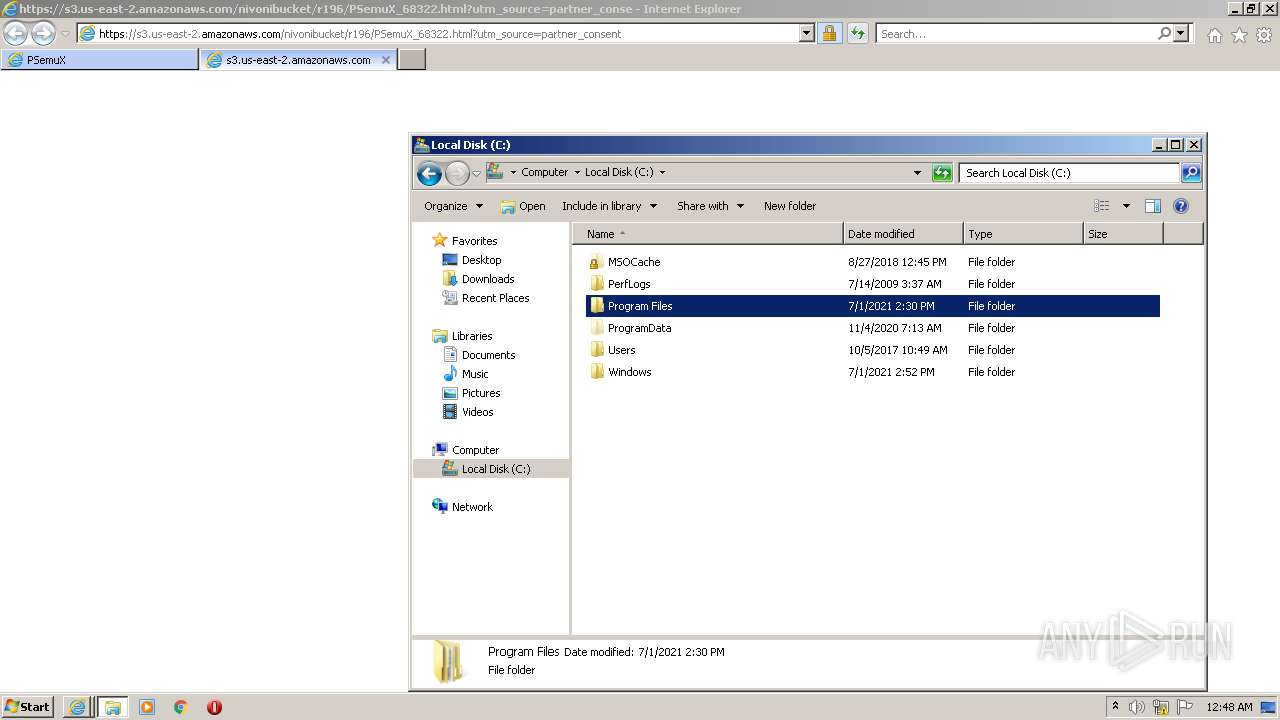
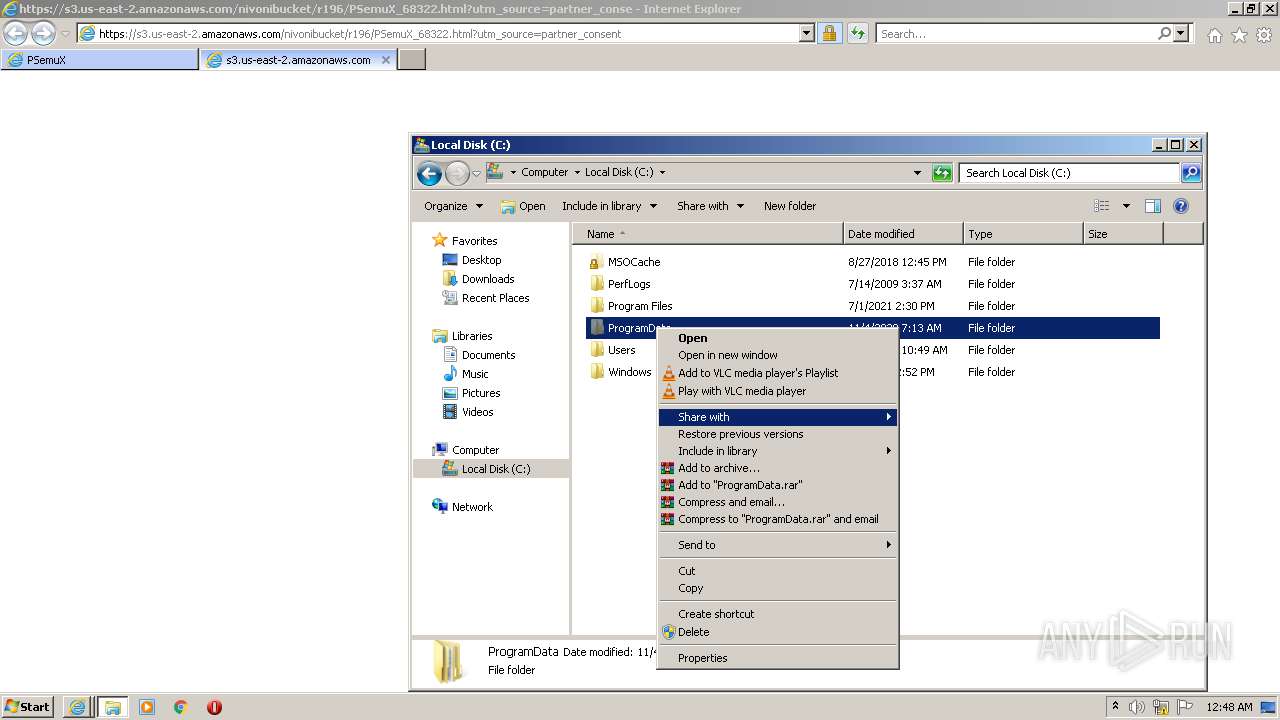
Manual execution by user
- explorer.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3724 CREDAT:464146 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 912 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3724 CREDAT:1381685 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3724 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
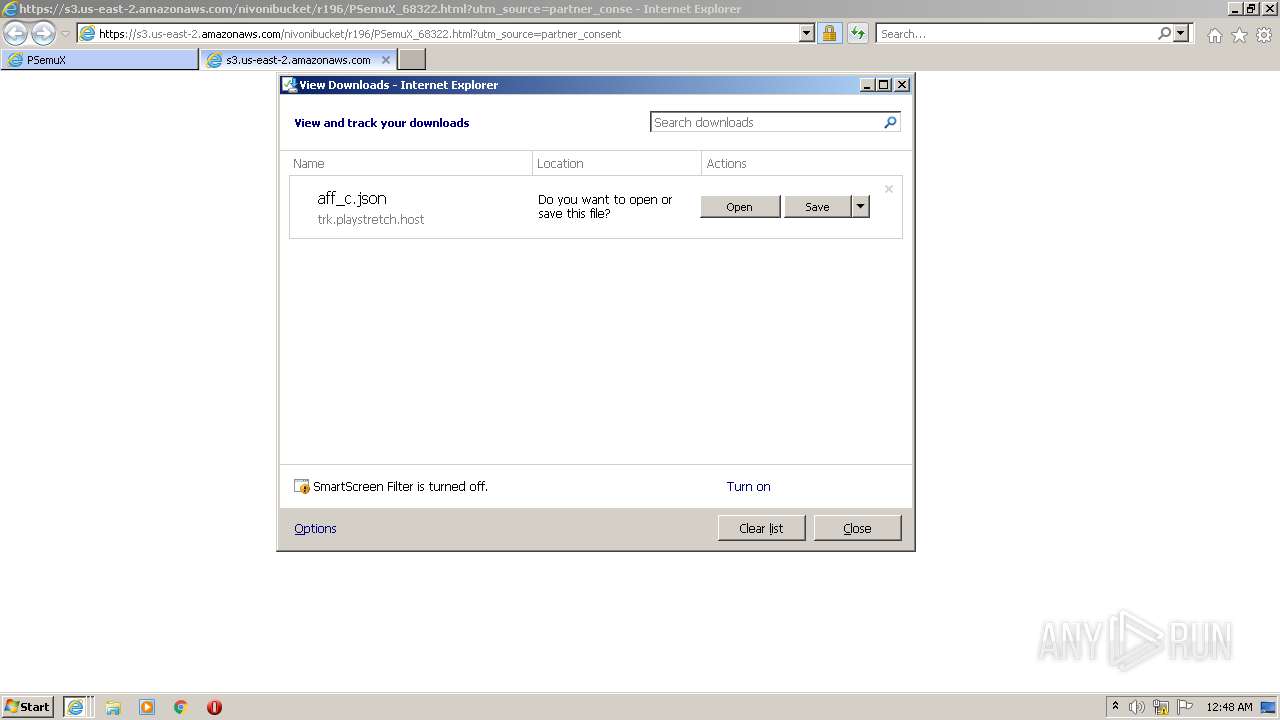
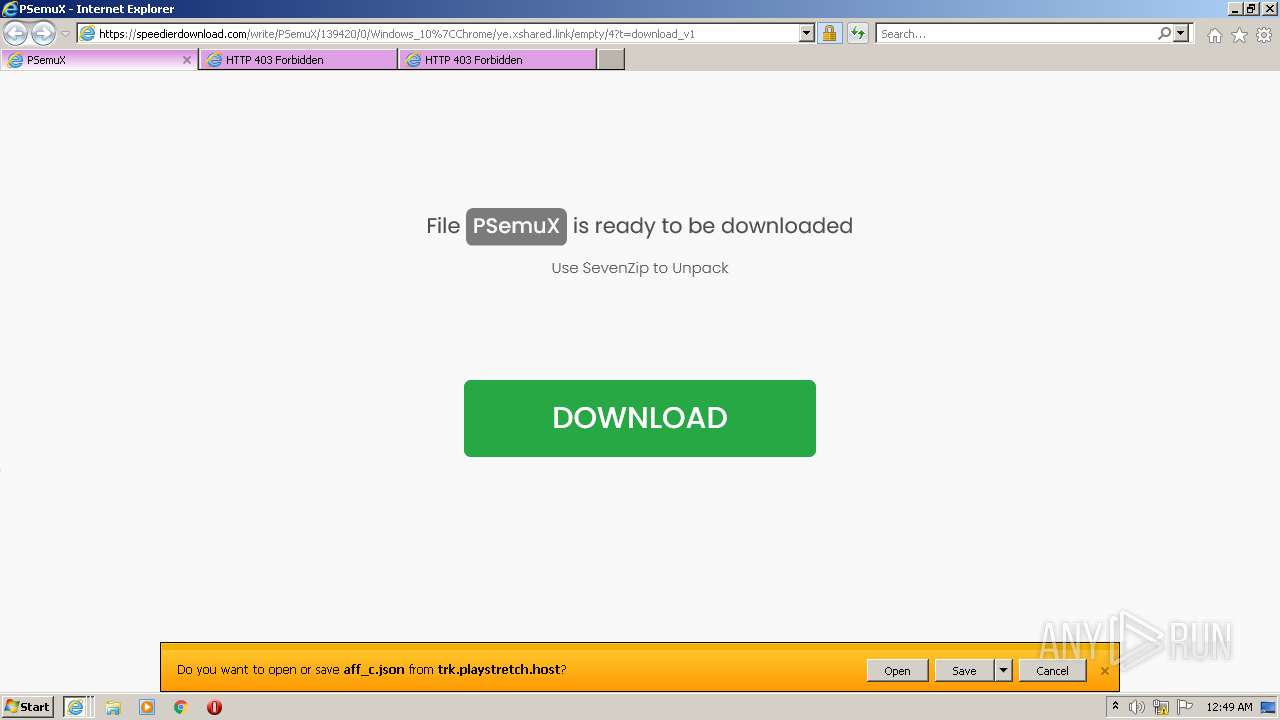
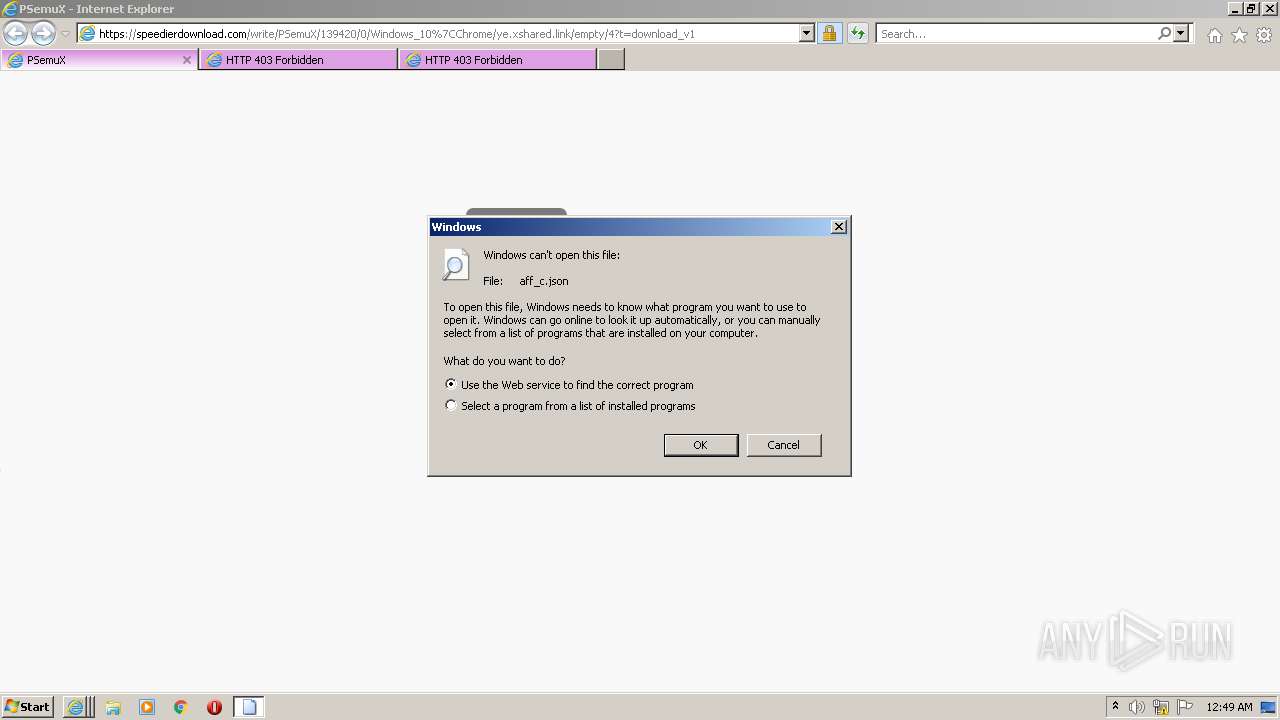
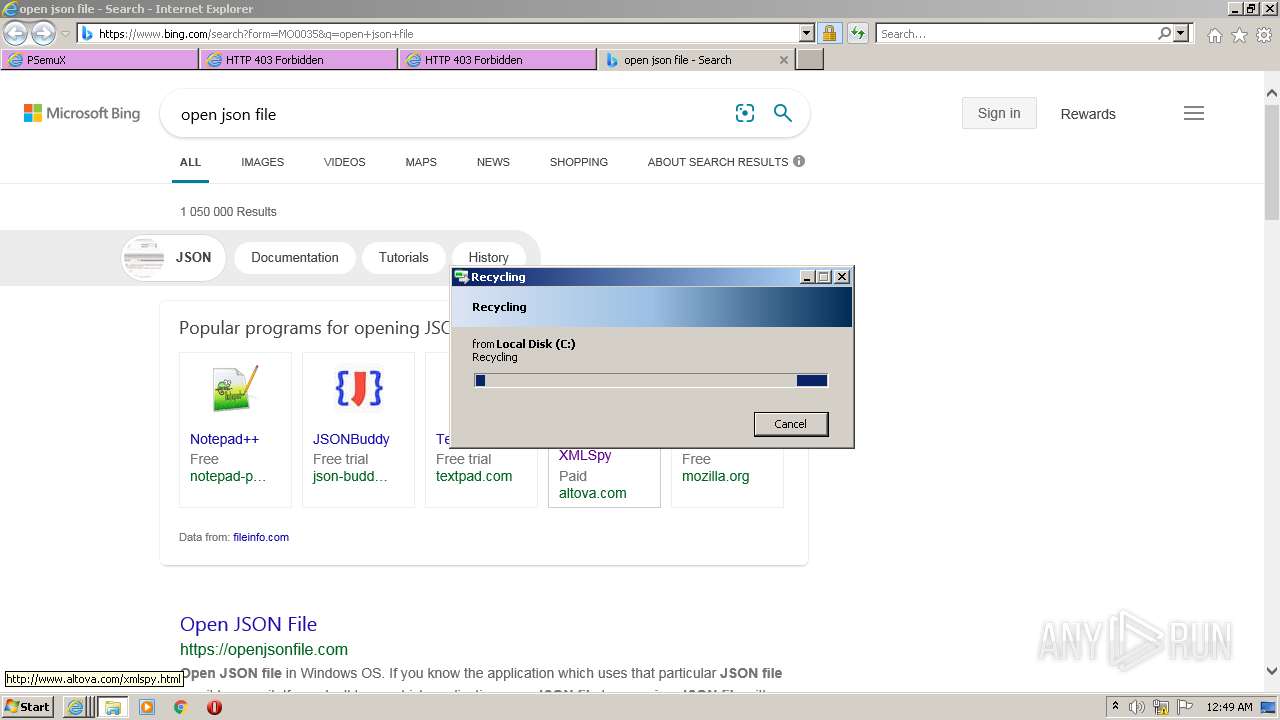
| 2696 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\aff_c.json | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3724 CREDAT:1643804 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3372 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3668 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
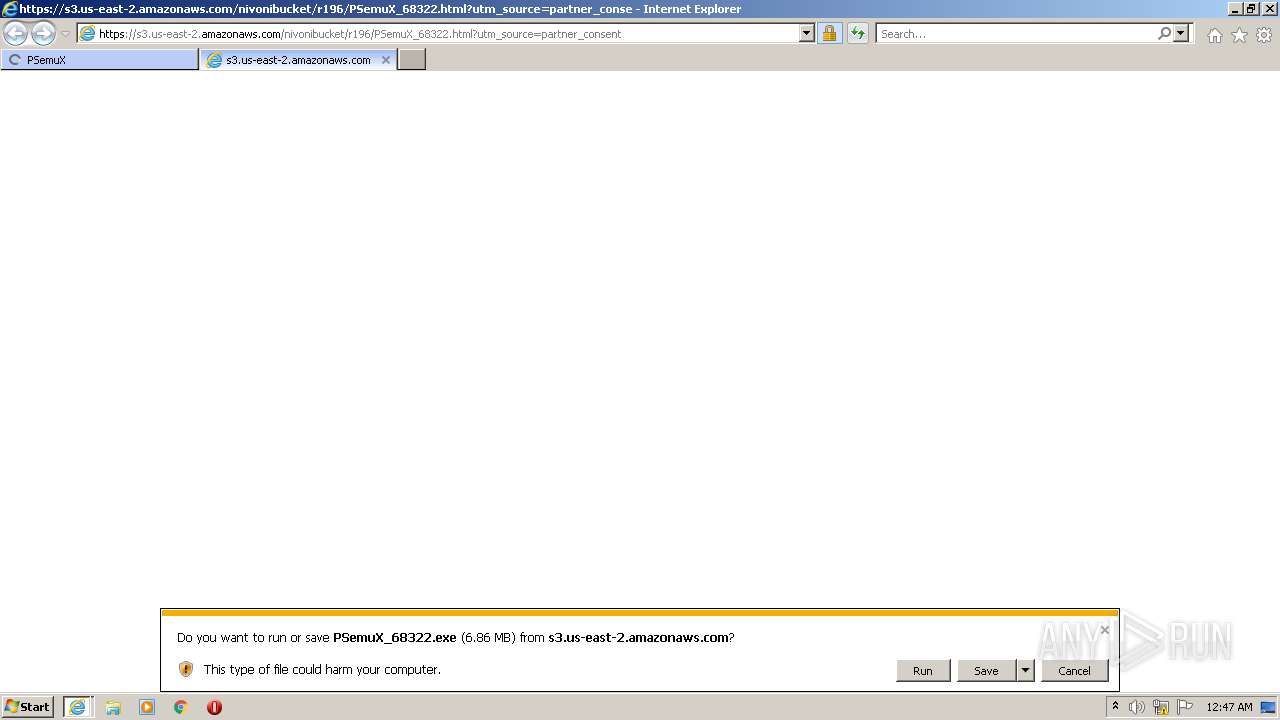
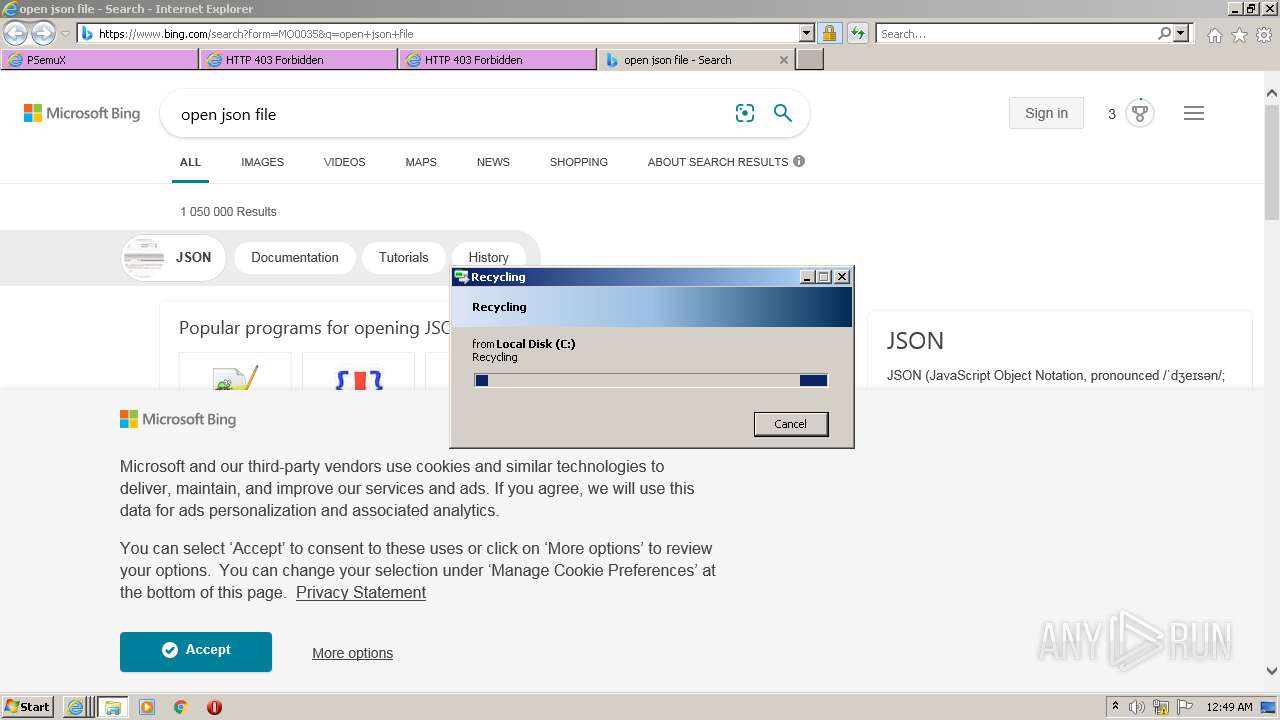
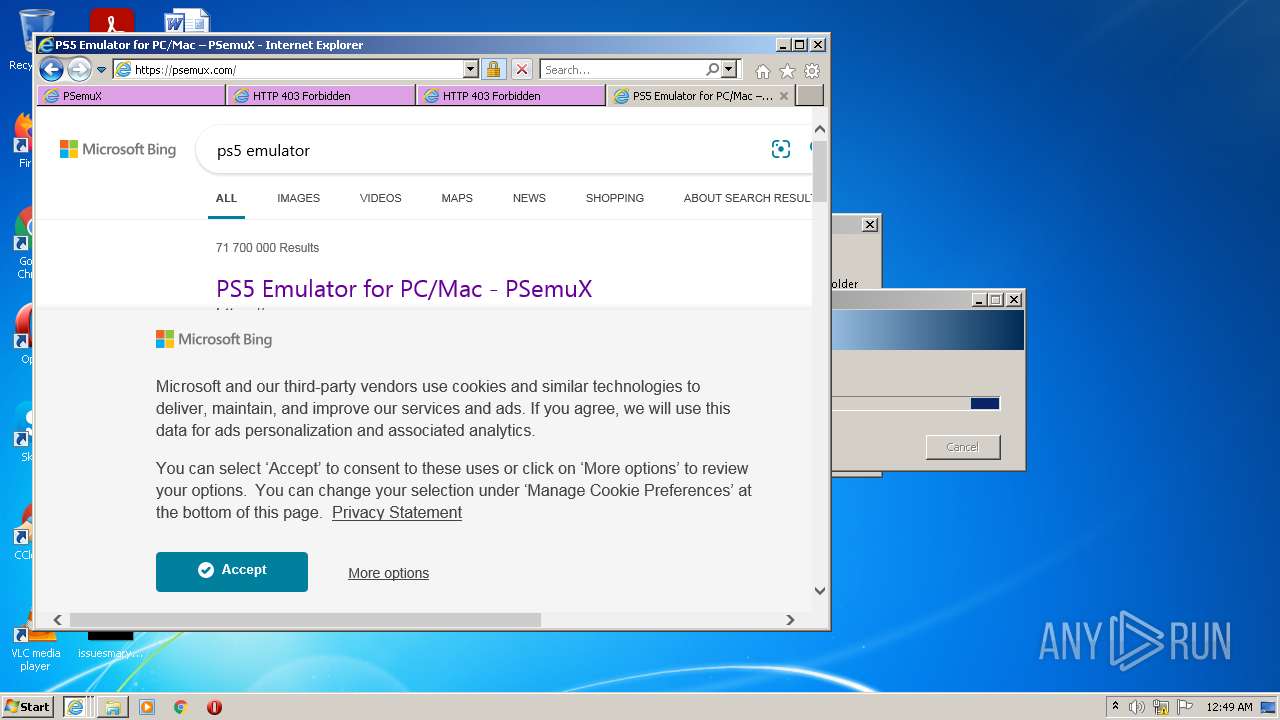
| 3724 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://speedierdownload.com/write/PSemuX/139420/0/Windows_10%7CChrome/ye.xshared.link/empty/4?t=download_v1" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\PSemuX_68322.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\PSemuX_68322.exe | iexplore.exe | ||||||||||||
User: admin Company: Increase Omniscient Integrity Level: MEDIUM Description: Increase Omniscient Flight Exit code: 0 Version: 1.0.2.01 Modules
| |||||||||||||||
Total events
36 577
Read events
36 301
Write events
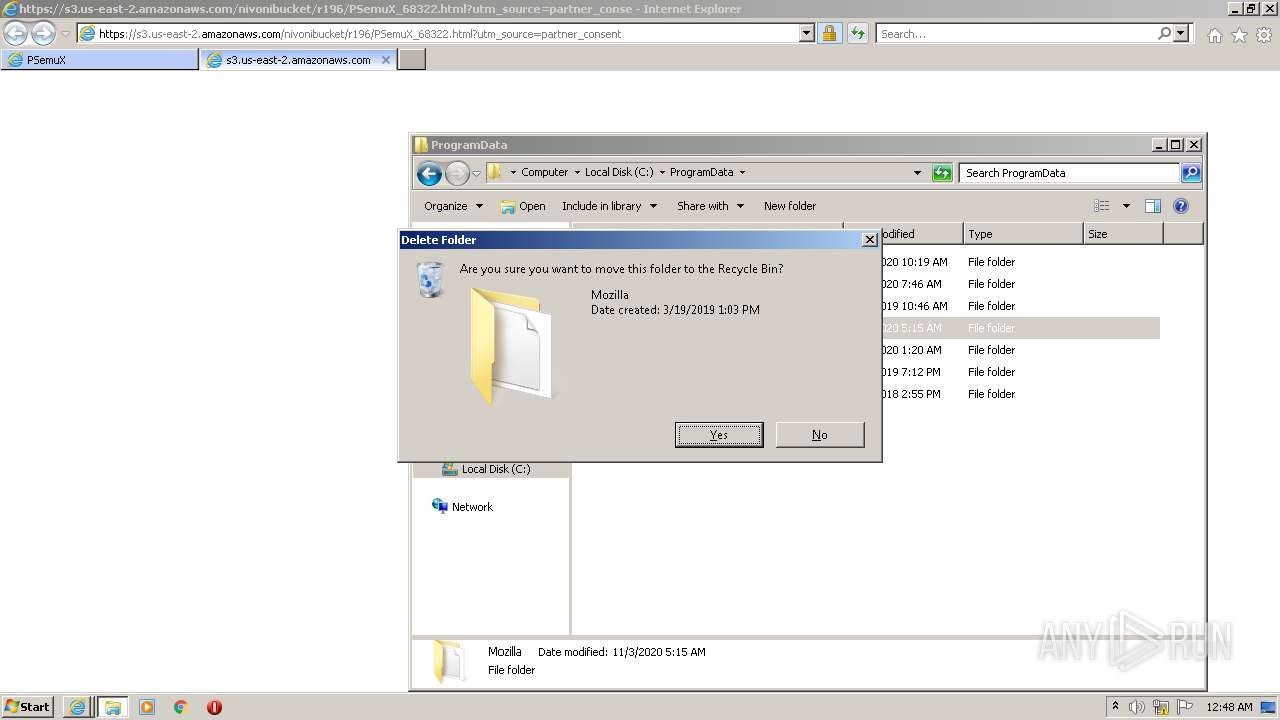
272
Delete events
4
Modification events
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940494 | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940494 | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
38
Text files
51
Unknown types
26
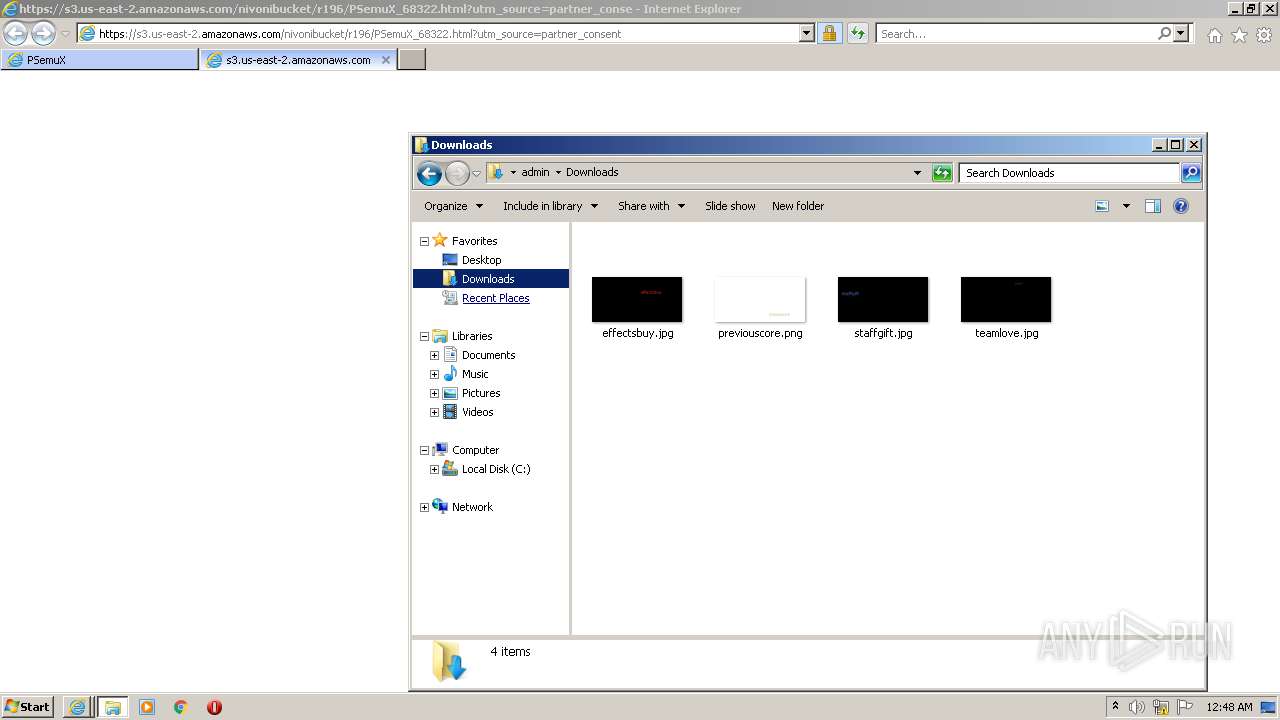
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:72CFA68ECDB0DE3C622DE9CE616A28FF | SHA256:539A729569ECB95308FD6C0DDC12DF441F7E427022EAEAFD5AC8149C31FAECD4 | |||
| 3724 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:473590396FF973CB5ADAFF4417CEEB43 | SHA256:6639DE206B0F60EB5BB2919388867BC7D37E781121BA61E0F847E19271354887 | |||
| 3724 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:1B6532B85D4C173BB7F60DD1BAC38CC7 | SHA256:E8A4DEE05C6075B3E1ABC097B51EAF5515198DE2ABD3DA81814EB72B4C7D625A | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:BA0DE697964517CF5A22A2DA2A0040FA | SHA256:DF9F88A1DABA79EC86C079656DB3CC6F60CA9989008C85FFB0E933F1A59F74D5 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:AE62EB74D831AE6C516212F44150AA3D | SHA256:C901CBA586A96AD5A77F73E5789CAEE8618EA6A2D538872290DB0D0100FD6AF5 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | der | |
MD5:409F38C1AD293CD48512C6464B5140D6 | SHA256:DA55C2761C254823E0B905D8231267FED0DB5BB8183881205DAAFA84939AAEBE | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\4[1].htm | html | |
MD5:0A41D82ED30331F7F4ADB6685BFF11FD | SHA256:5031DC3A4304940A4B4F0A6A7A63AEFA40A1FEC99D334A5223724360A759D580 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:5A1D021326BFF6F09AD45858FD430CF0 | SHA256:F714FE0B0D682CBD73431C92748539860E8844BF5561F43486D720DDE18E258D | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F03AA576202F35F6DDE46695C0BDD72F | der | |
MD5:881EFDC8695AEAB055054C4D220B1BF5 | SHA256:4E48CCAEBD2AF1955C32D7D80A4CF8A07EB981122C9D1068B9DF17C36B88B391 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F03AA576202F35F6DDE46695C0BDD72F | binary | |
MD5:ADDB29B8C6619F711D0194DF459AD531 | SHA256:BE57093C315830DF0E6CC04C7F581034C1BE150C965C63D452F6DEEFC6E46AD3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
112
DNS requests
48
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2188 | iexplore.exe | GET | 200 | 195.138.255.16:80 | http://e1.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBTvkAFw3ViPKmUeIVEf3NC7b1ErqwQUWvPtK%2Fw2wjd5uVIw6lRvz1XLLqwCEgP%2B7jJ9Wz4RMX%2FtFc3tKY84HQ%3D%3D | DE | der | 345 b | whitelisted |
3724 | iexplore.exe | GET | 200 | 8.248.119.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?896009c89a192b0d | US | compressed | 4.70 Kb | whitelisted |
2188 | iexplore.exe | GET | 200 | 104.117.200.9:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 8.248.119.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e0ecba08ce7e3400 | US | compressed | 59.9 Kb | whitelisted |
3724 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2188 | iexplore.exe | GET | 200 | 104.117.200.9:80 | http://x2.c.lencr.org/ | US | der | 299 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2188 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIRy5Lqyj5dAoAAAABLgV%2F | US | der | 472 b | whitelisted |
2188 | iexplore.exe | GET | 200 | 13.225.84.49:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2188 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2188 | iexplore.exe | 54.155.11.60:443 | trk.playstretch.host | Amazon.com, Inc. | IE | unknown |
2188 | iexplore.exe | 13.225.84.49:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2188 | iexplore.exe | 172.67.148.20:443 | speedierdownload.com | — | US | unknown |
— | — | 8.248.119.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
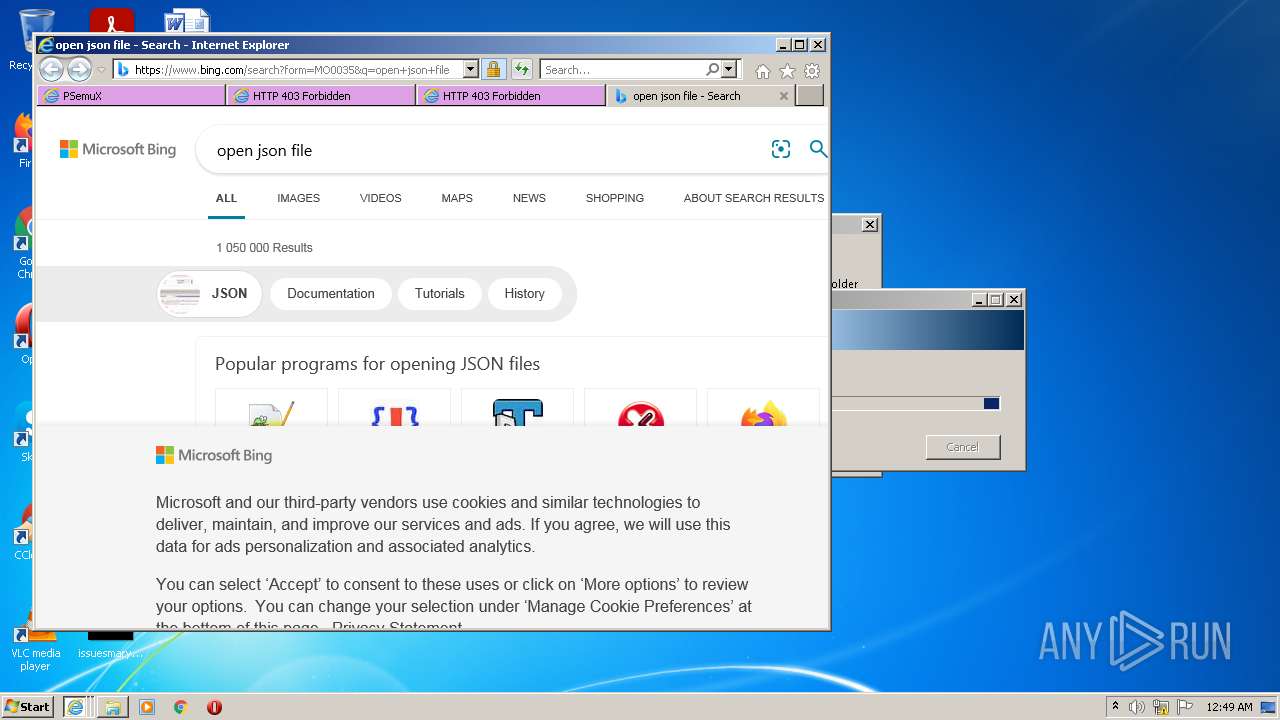
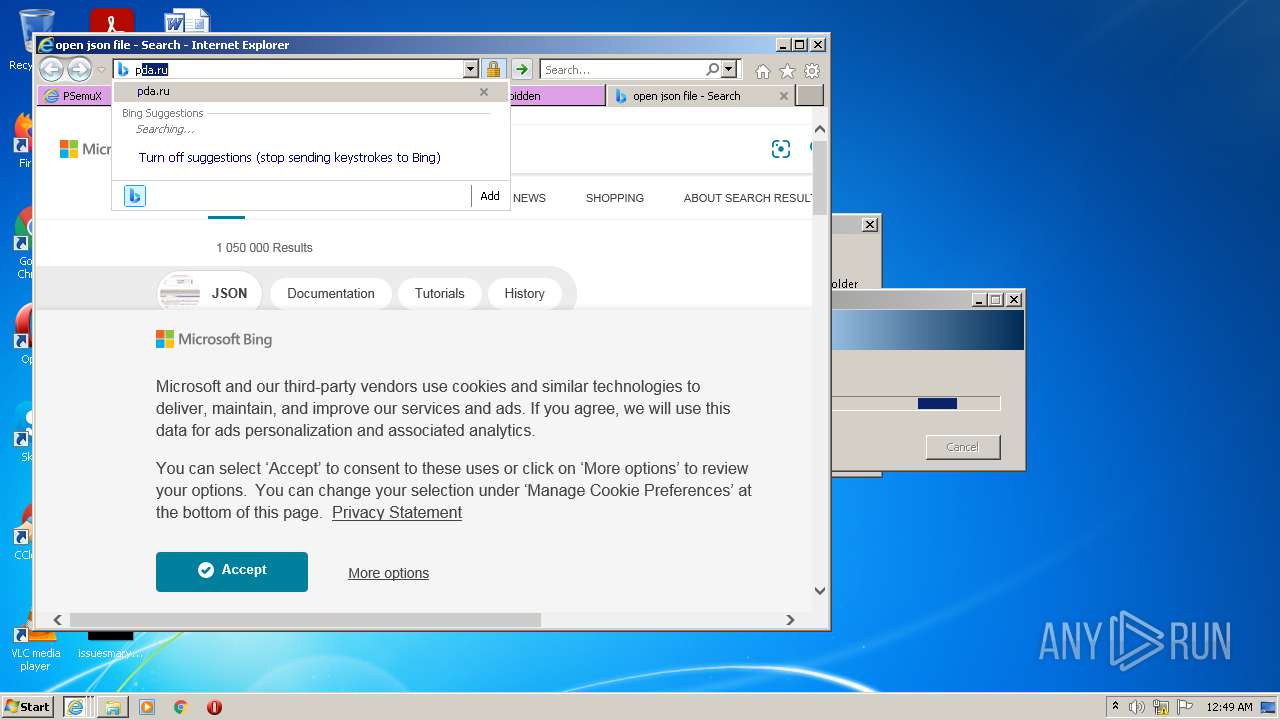
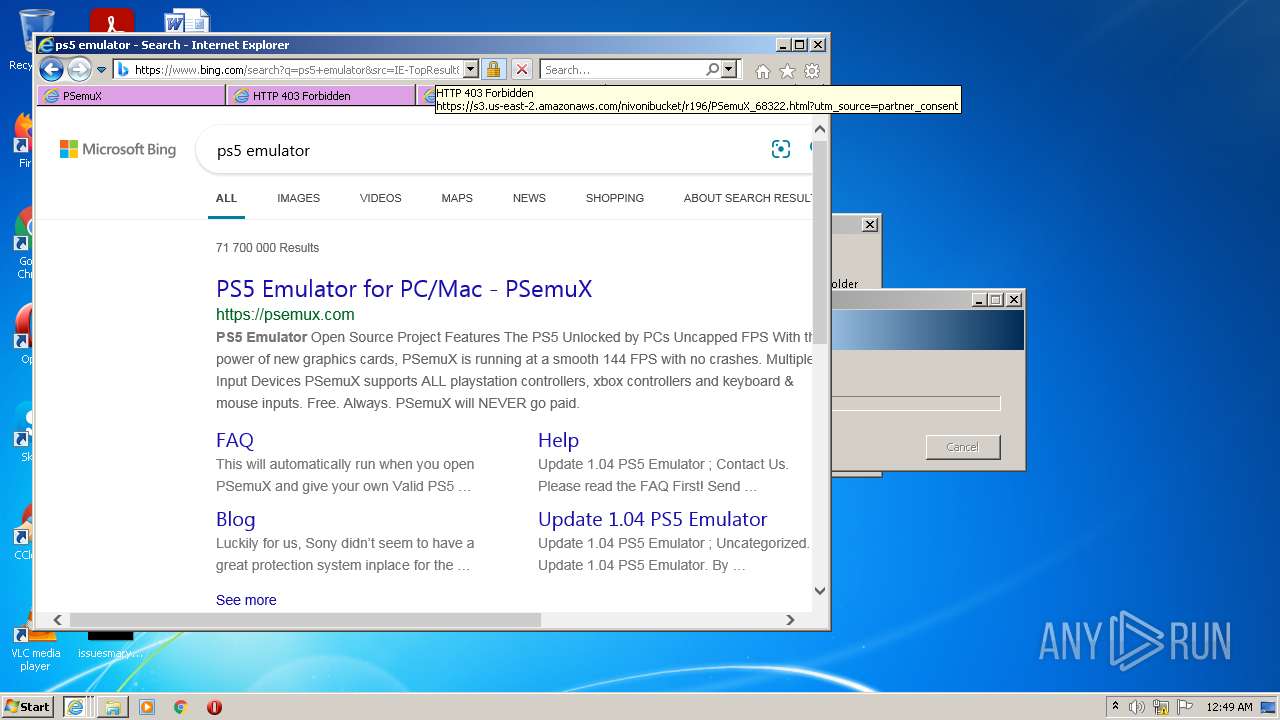
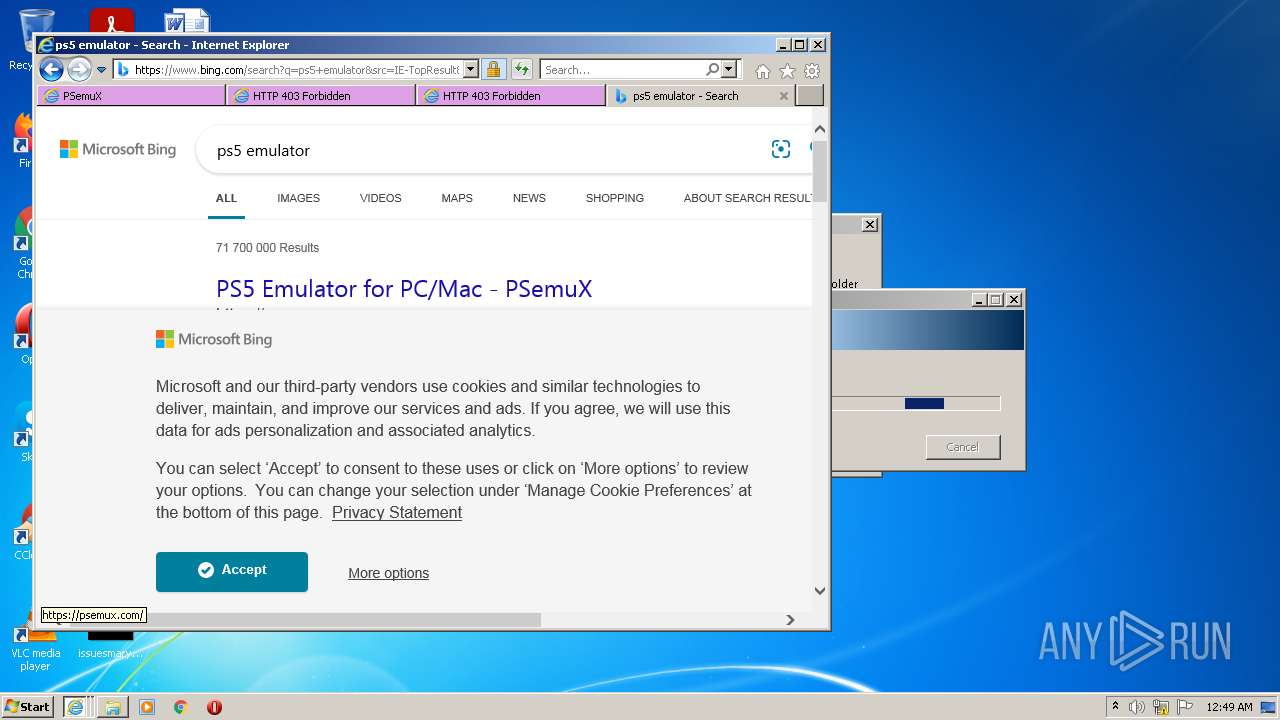
3724 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2188 | iexplore.exe | 8.248.119.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3724 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3724 | iexplore.exe | 8.248.119.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2188 | iexplore.exe | 104.117.200.9:80 | x1.c.lencr.org | TPG Telecom Limited | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
speedierdownload.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
e1.o.lencr.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
allcdnjs.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
912 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |