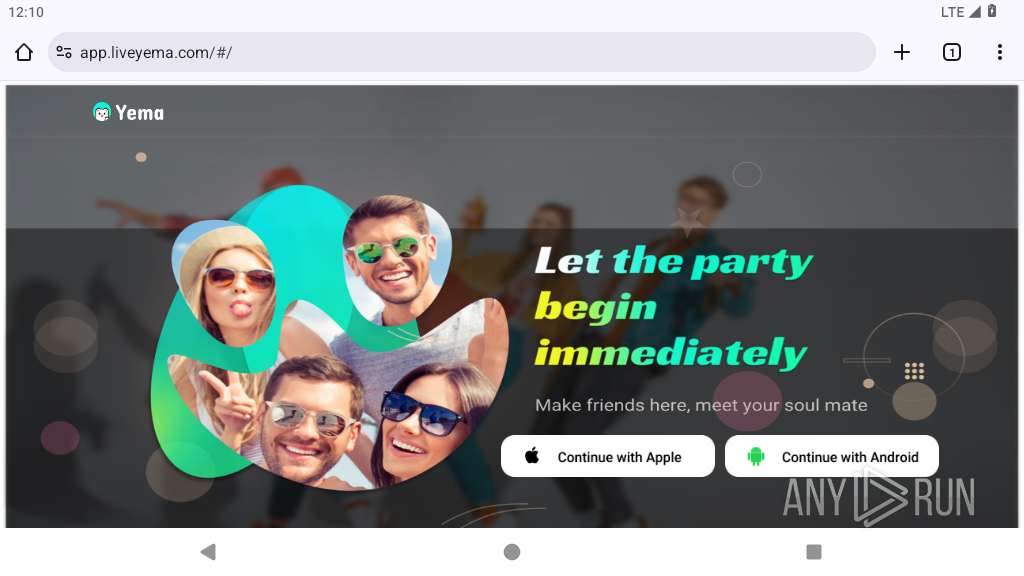
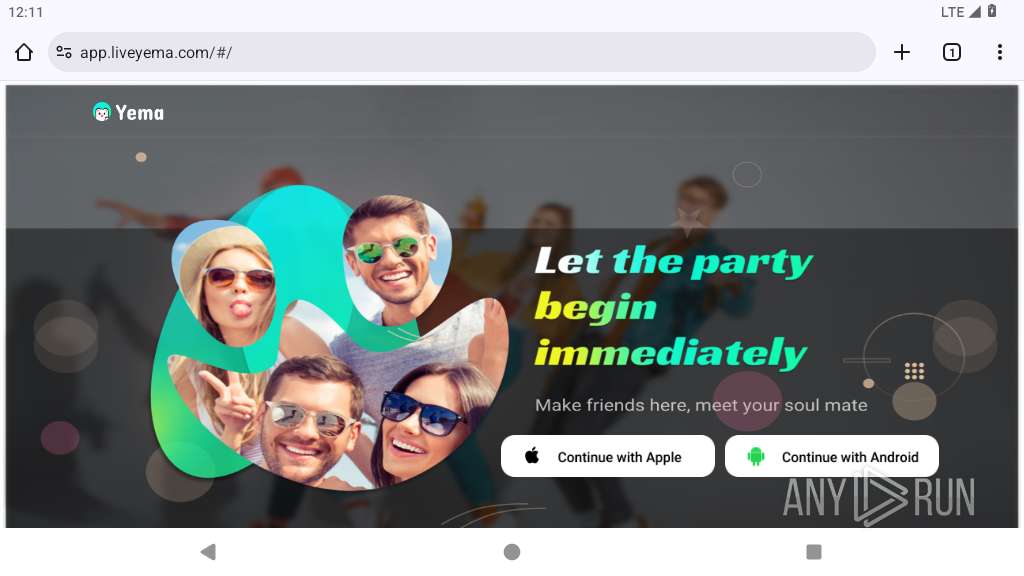
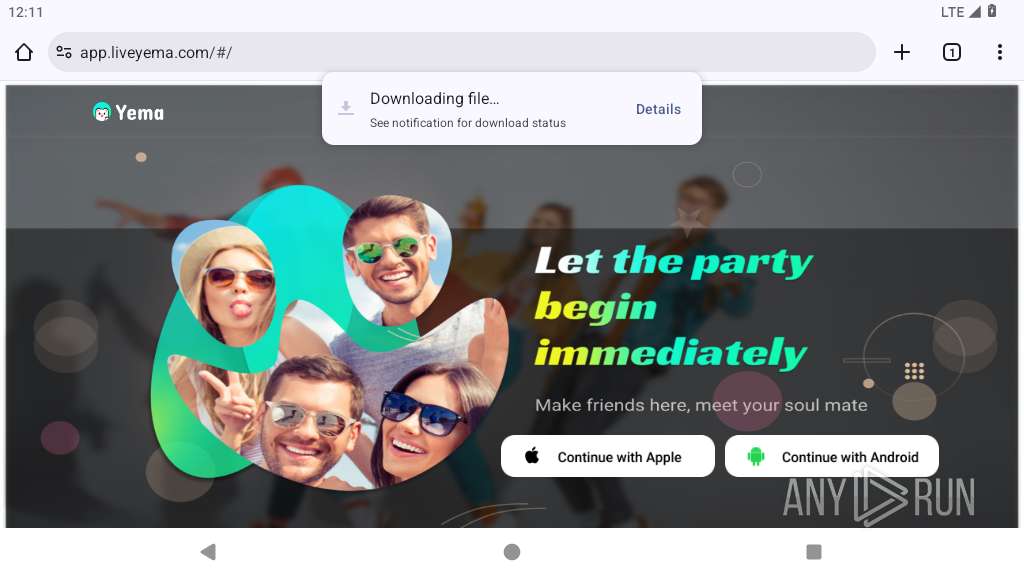
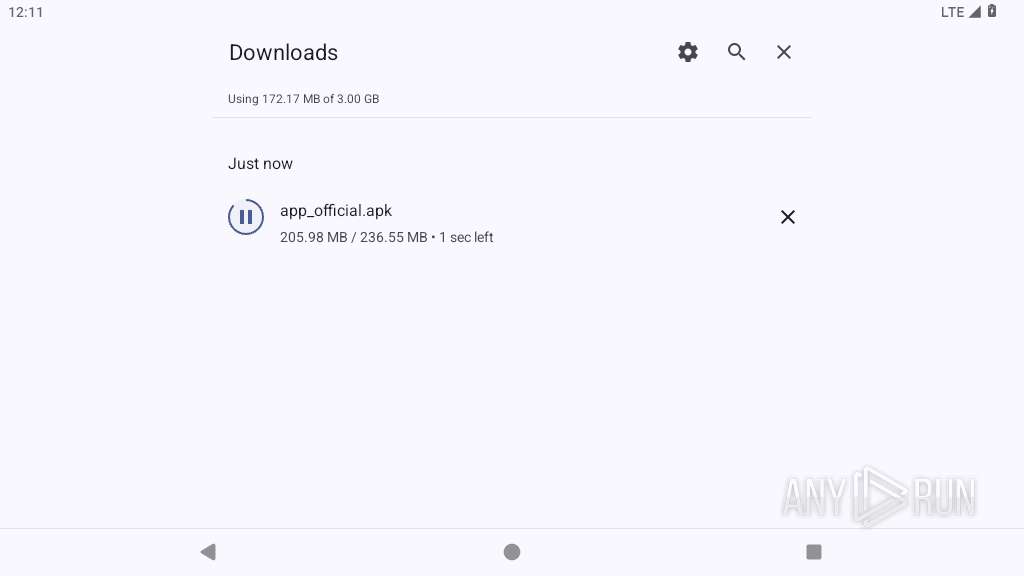
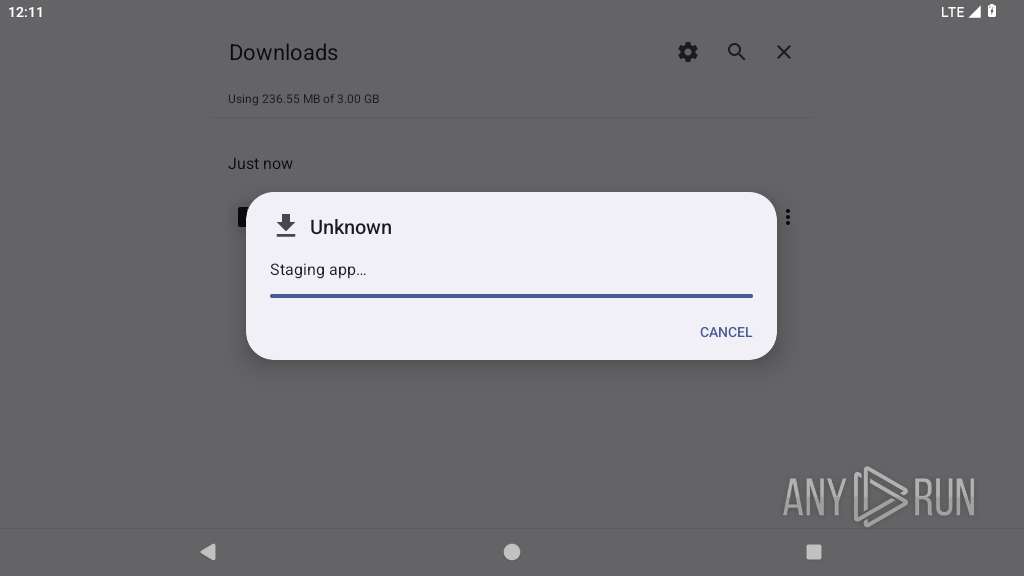
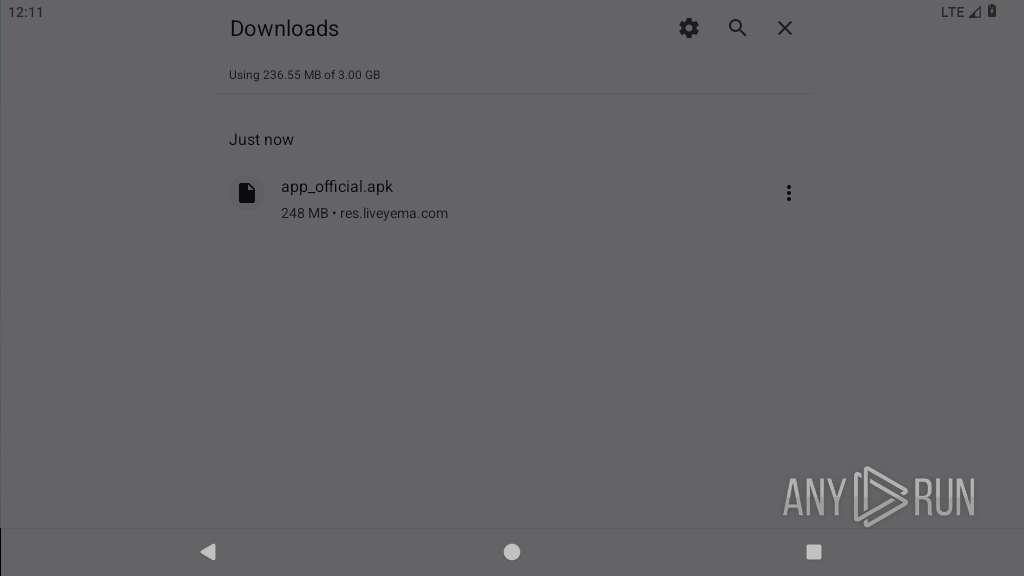
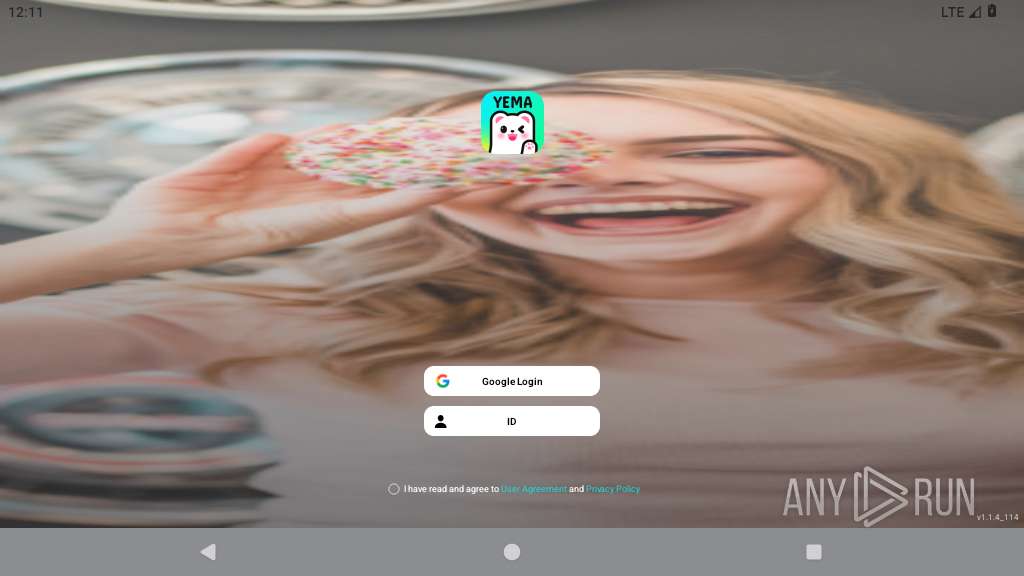
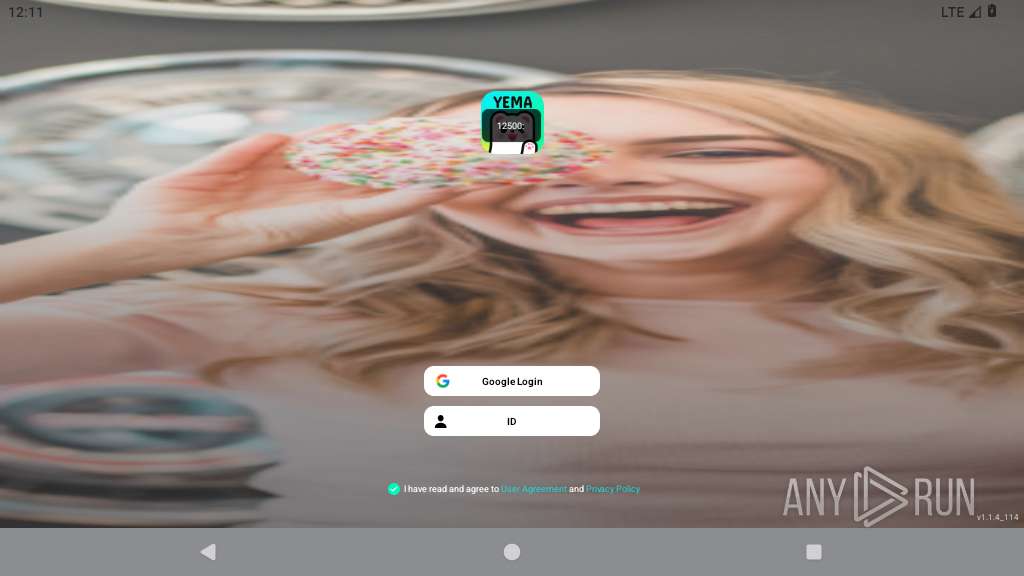
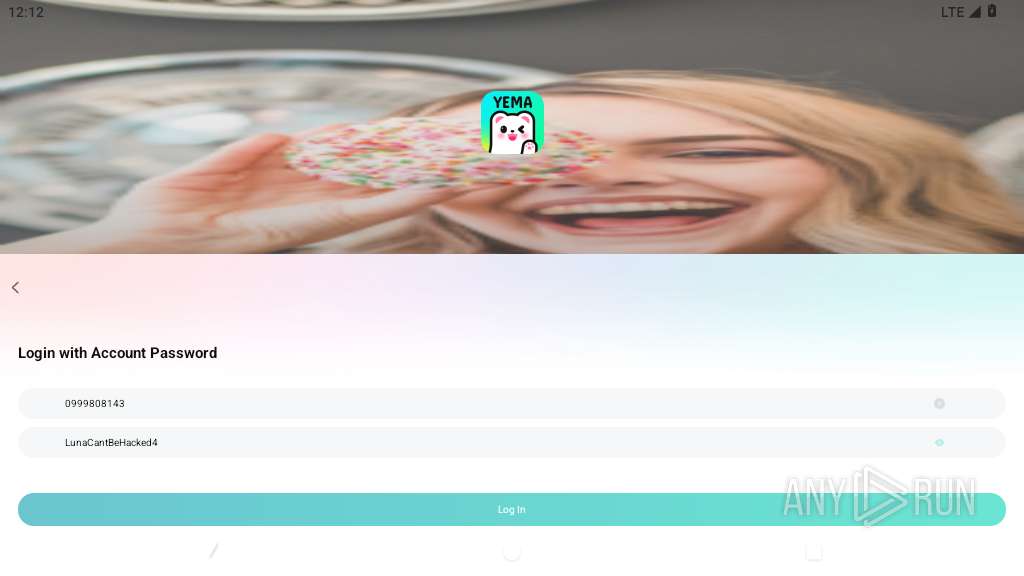
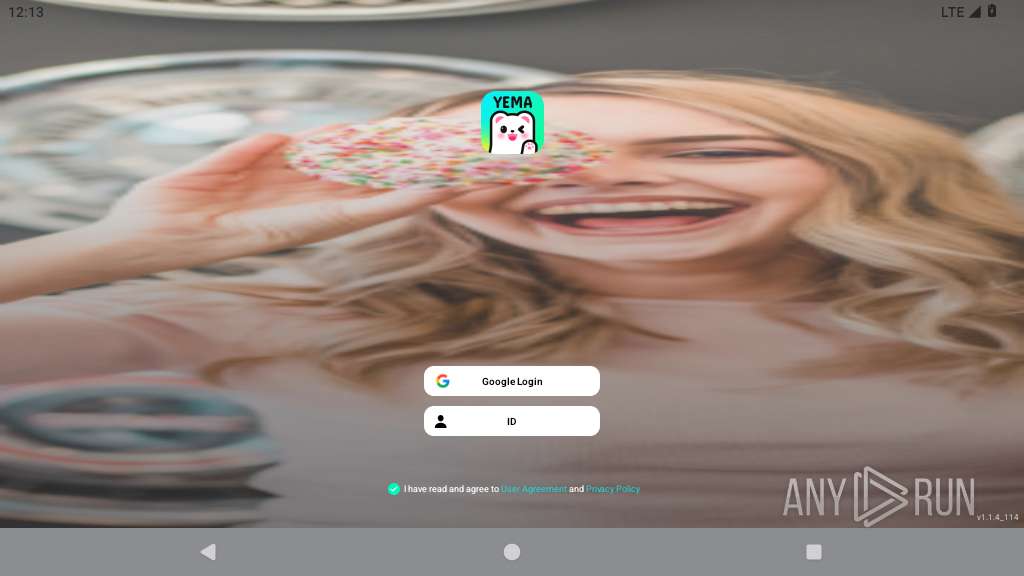
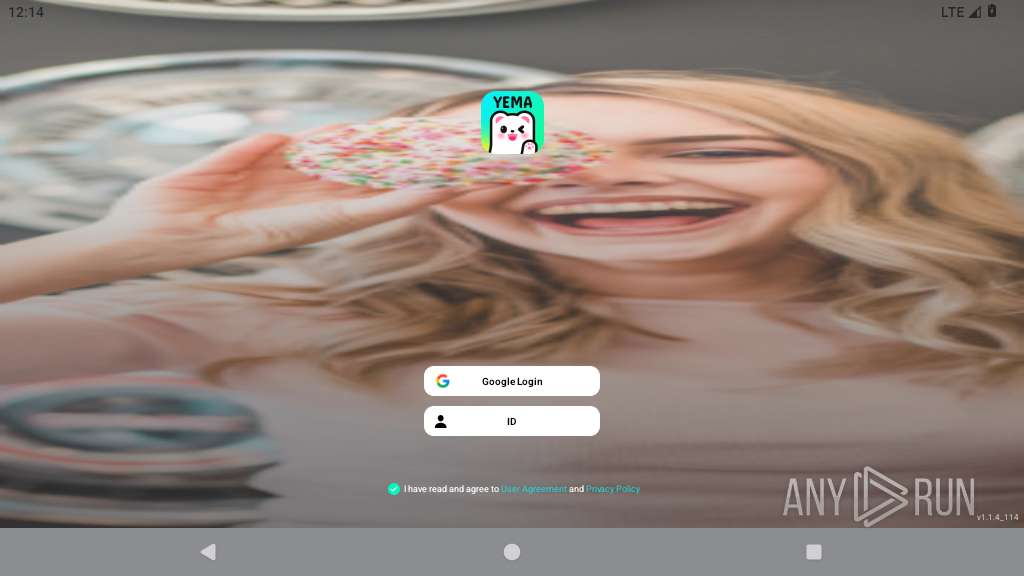
| URL: | https://app.liveyema.com/ |
| Full analysis: | https://app.any.run/tasks/d9de8923-2d3d-4af2-9f7c-0549d9cdda0b |
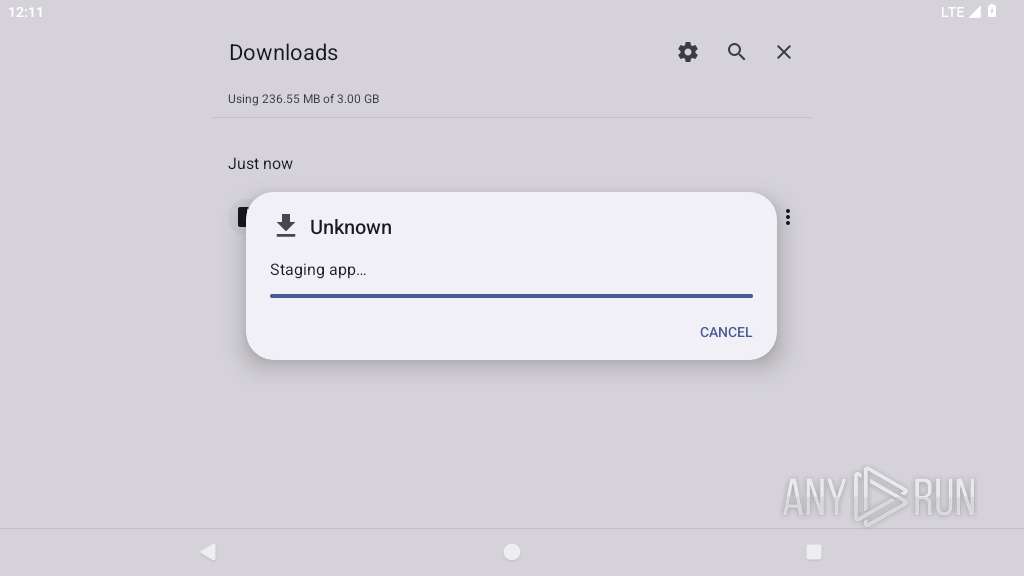
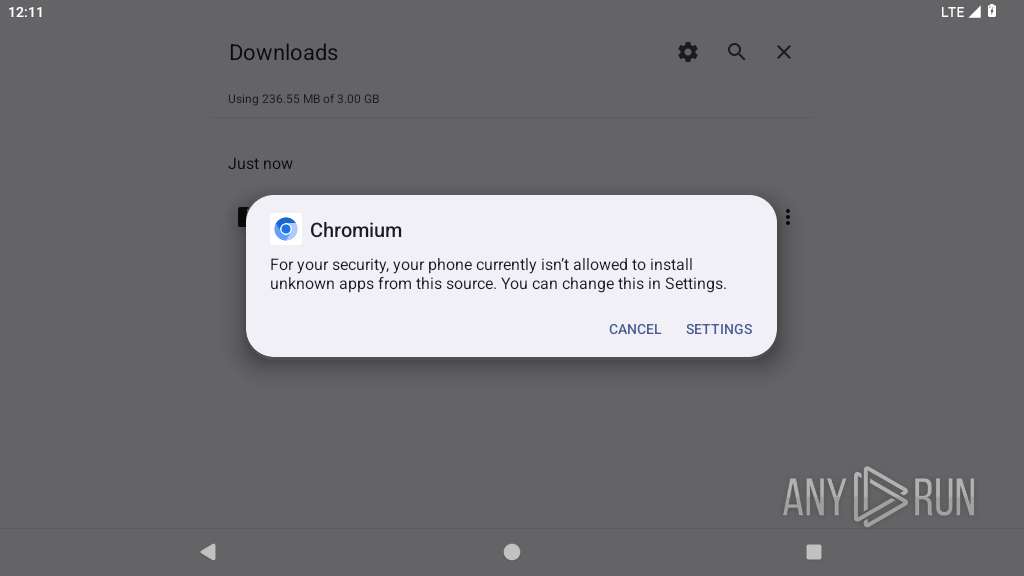
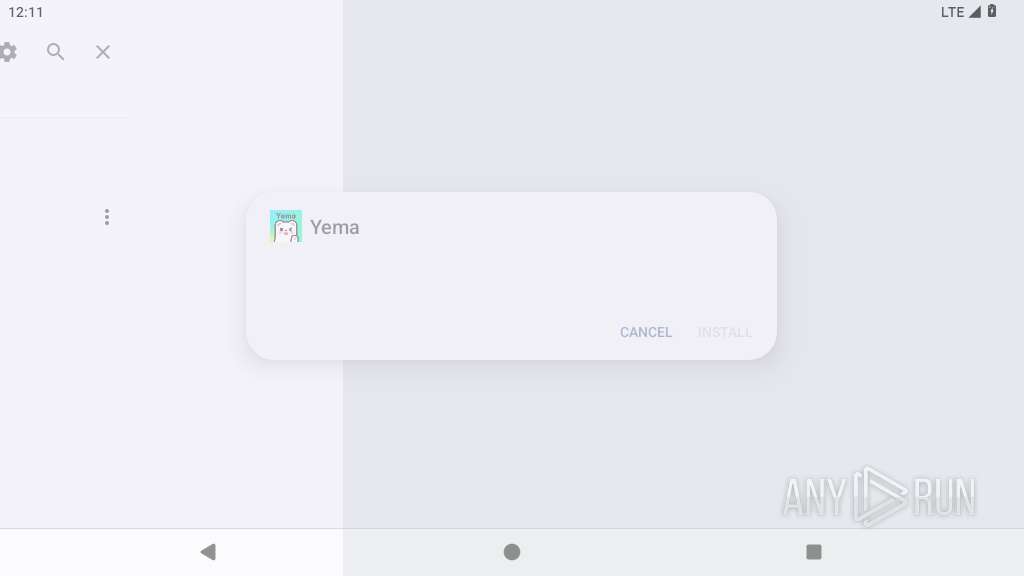
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 12:10:39 |
| OS: | Android 14 |
| Indicators: | |
| MD5: | F076D3F92AC5E521836CF68D2B12A7DD |
| SHA1: | C2F416AE5DC9D6815F6E811EE03EB2BC41199B99 |
| SHA256: | A3832C57E1641979C504F5DE05F88C3E4E5ED11B518951A38143EABF40898E76 |
| SSDEEP: | 3:N8auCIiRn:2ahR |
MALICIOUS
No malicious indicators.SUSPICIOUS
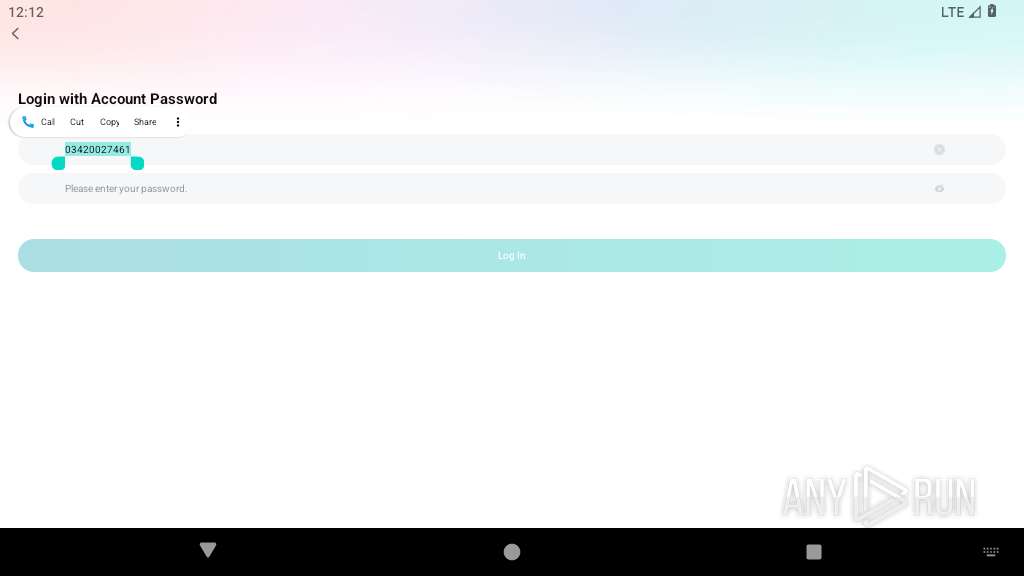
Scans for popular installed apps
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Accesses system-level resources
- app_process64 (PID: 2572)
Establishing a connection
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 2572)
Uses encryption API functions
- app_process64 (PID: 2572)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Accesses external device storage files
- app_process64 (PID: 2572)
Starts a service
- app_process64 (PID: 2572)
Launches a new activity
- app_process64 (PID: 2572)
Overlays content on other applications
- app_process64 (PID: 2572)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2572)
INFO
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Loads a native library into the application
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2572)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Retrieves the value of a secure system setting
- app_process64 (PID: 2572)
Returns elapsed time since boot
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Stores data using SQLite database
- app_process64 (PID: 2572)
Creates and writes local files
- app_process64 (PID: 2572)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Queries preferred Access Point Name
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Checks system memory usage details
- app_process64 (PID: 2572)
Dynamically loads a class in Java
- app_process64 (PID: 2572)
- app_process64 (PID: 2644)
Listens for connection changes
- app_process64 (PID: 2572)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
43
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2211 | <pre-initialized> | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2252 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2267 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2302 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2337 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2392 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2411 | zygote64 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2437 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2438 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2439 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
22
Suspicious files
321
Text files
339
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | app_process64 | /data/data/com.vcopper.chat/shared_prefs/Utils.xml | xml | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/shared_prefs/locale_prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/shared_prefs/crashrecord.xml | xml | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/app_crashrecord/1004 | binary | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/files/bugly_last_us_up_tm | text | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/shared_prefs/BUGLY_COMMON_VALUES.xml | xml | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/1450341e6cf30c3c655cc538de1c927b/nim_device2 | text | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/cache/nim/log/nim_sdk.log | text | |
MD5:— | SHA256:— | |||
| 2572 | app_process64 | /data/data/com.vcopper.chat/shared_prefs/NIMSDK_GLOBAL_CONFIG.xml | xml | |
MD5:— | SHA256:— | |||
| 2644 | app_process64 | /data/data/com.vcopper.chat/shared_prefs/locale_prefs.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
32
DNS requests
37
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.185.131:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acmmwq7dser4xm5sepzjv74g65vq_2023.7.28.10/cffplpkejcbdpfnfabnjikeicbedmifn_2023.07.28.10_all_acgbwixmcanakp2bkoppyszsbkrq.crx3 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwmiglbaq6quecjufmamfsqupsa_2025.5.21.0/niikhdgajlphfehepabhhblakbdgeefj_2025.05.21.00_all_msqewqxesfaohilvaerhlfagai.crx3 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 142.250.186.78:80 | http://clients2.google.com/time/1/current?cup2key=9:265I37lSRrdlpHFIu99CYPwWqxWo2YP349d-pthNkcI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/obedbbhbpmojnkanicioggnmelmoomoc/46aa4b4e34cfc311dbd61b35e64b658c48ee348f8763d0c15933e0d49c73305c | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k6aguqdkide4bh2fpta6vjk2eu_516/lmelglejhemejginpboagddgdfbepgmp_516_all_ZZ_acq26o44oyobumwxuztua66r7dlq.crx3 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acdvcifl2ztime6bsz3eijtcfeaq_2025.5.15.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.05.15.01_all_ehum5zzx5qnqq3vyyhyi6ytrfq.crx3 | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kgdbnmlfakkebekbaceapiaenjgmlhan/e41131c999e82c36dd1a380288d4af2f5decfed1ab6077c8c0aece3d05e1d0ea | unknown | — | — | whitelisted |
2211 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pcbw6tyw7x3rtjiemkmpb6yn2m_2025.6.9.0/kgdbnmlfakkebekbaceapiaenjgmlhan_2025.06.09.0_all_bvkcqje4h2s3xof6azs7f4xfba.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
446 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
— | — | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 74.125.206.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2211 | app_process64 | 142.250.186.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
2211 | app_process64 | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2211 | app_process64 | 18.66.122.125:443 | app.liveyema.com | AMAZON-02 | US | unknown |
2211 | app_process64 | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
2211 | app_process64 | 151.101.129.229:443 | cdn.jsdelivr.net | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
app.liveyema.com |
| unknown |
cdn.jsdelivr.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2211 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |