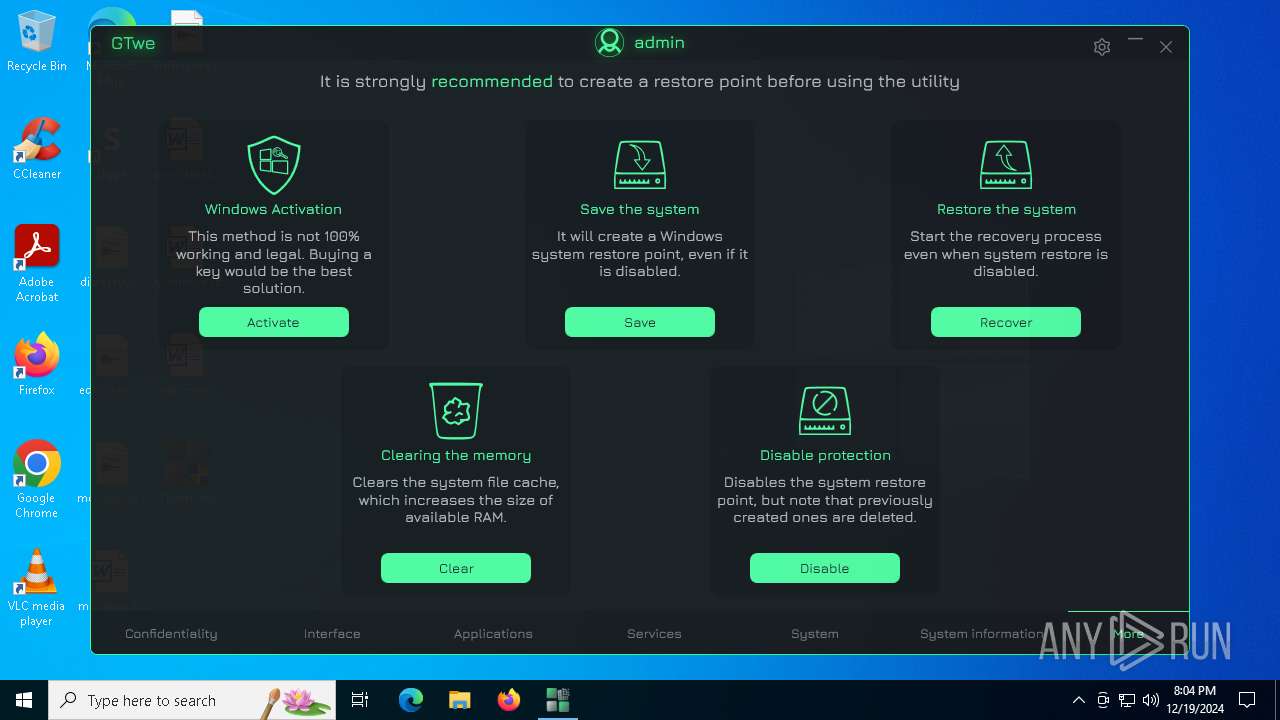
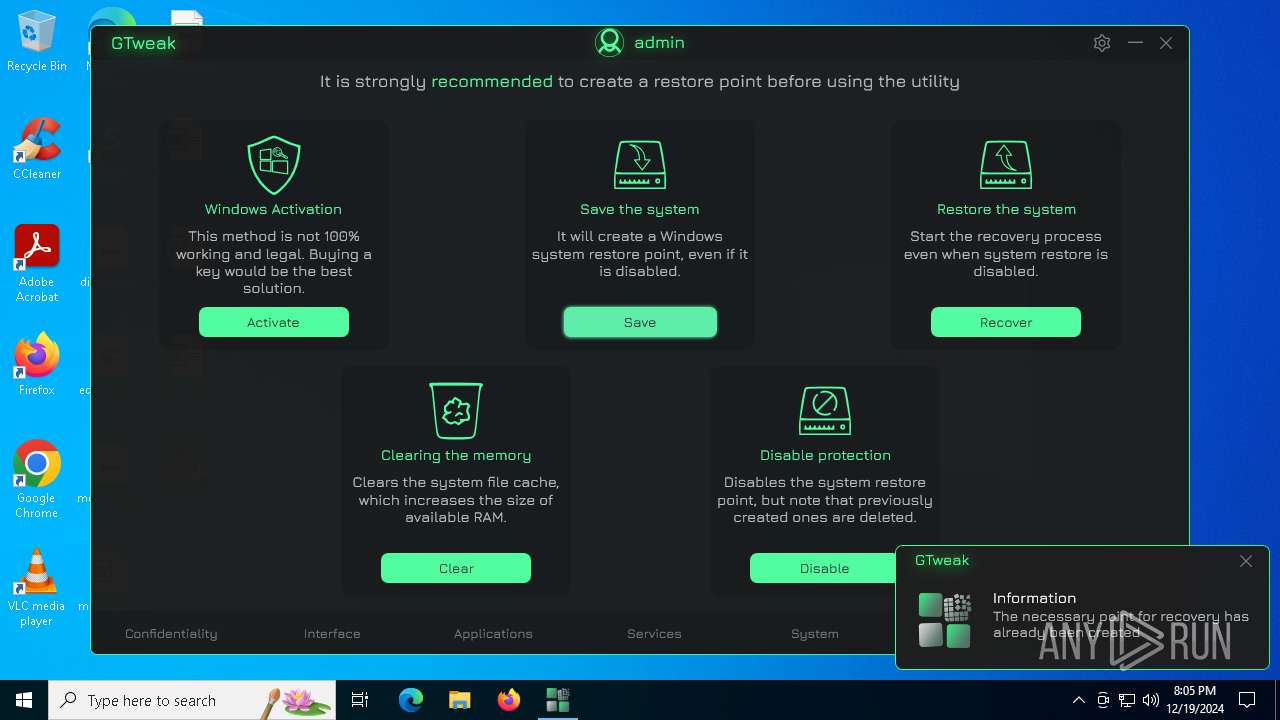
| File name: | GTweak.exe |
| Full analysis: | https://app.any.run/tasks/535725ff-56d4-4f41-b92c-f691b5607d37 |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2024, 20:03:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 4FB7FFD49EB96188C1C39BE0B0602881 |
| SHA1: | 802BFFAFE1D53EA0F9FD1C237B8C0564787B5D33 |
| SHA256: | A361D7C0A5EAEC150BCEF9CB223328087ECE98C5F871C0D4E3FE86DE999BDAE3 |
| SSDEEP: | 98304:e5a6zUWrpljUCzsmeX2y8JBi1B39u8WflB2bz14b8Msb8kN7NXKhF:qrip |
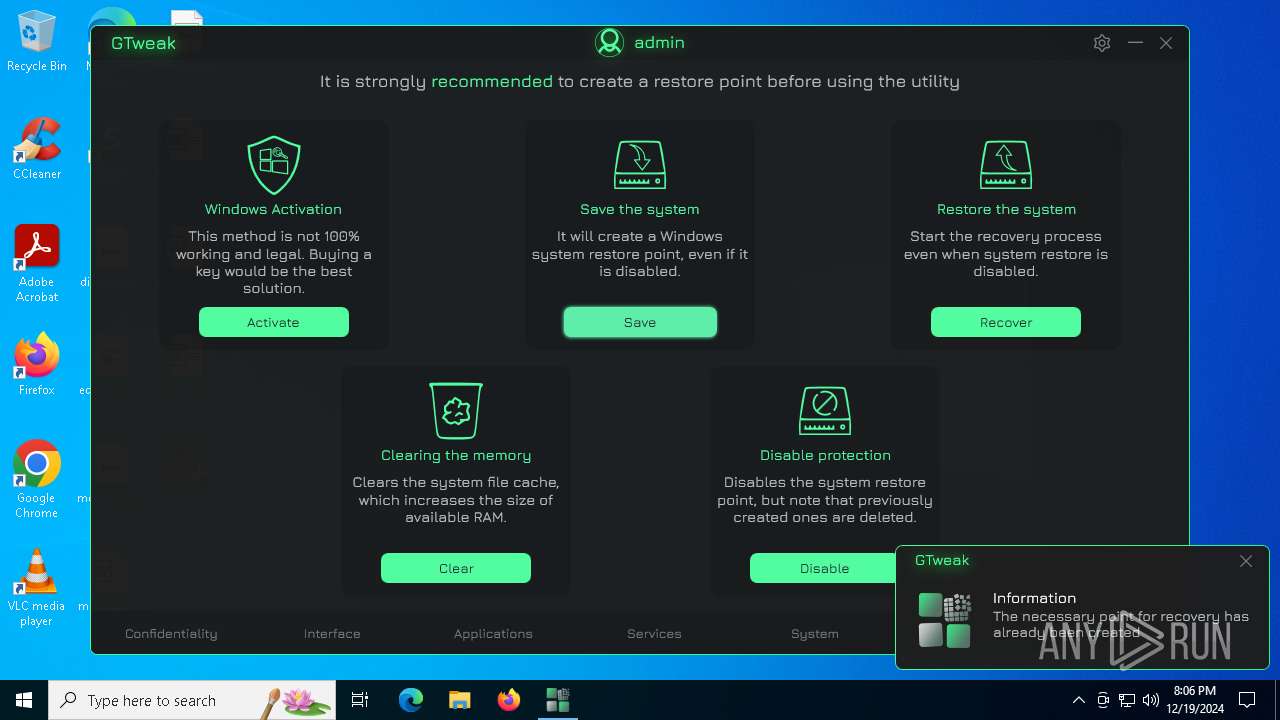
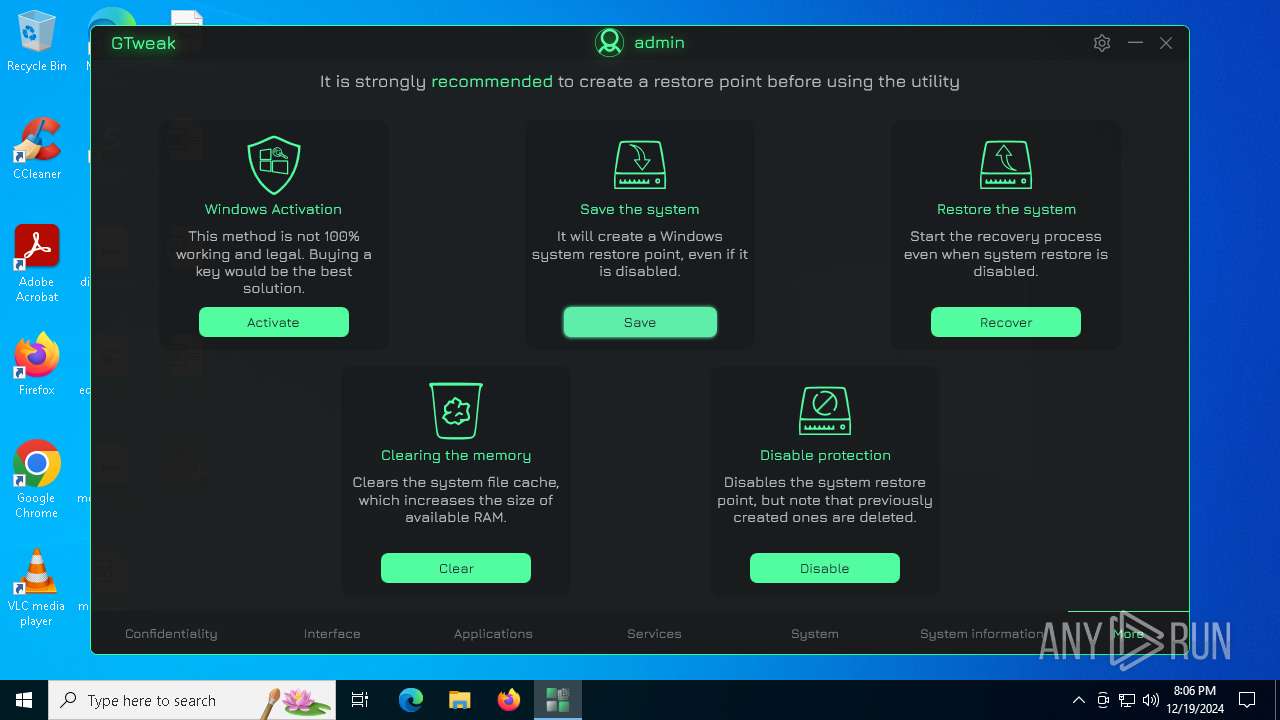
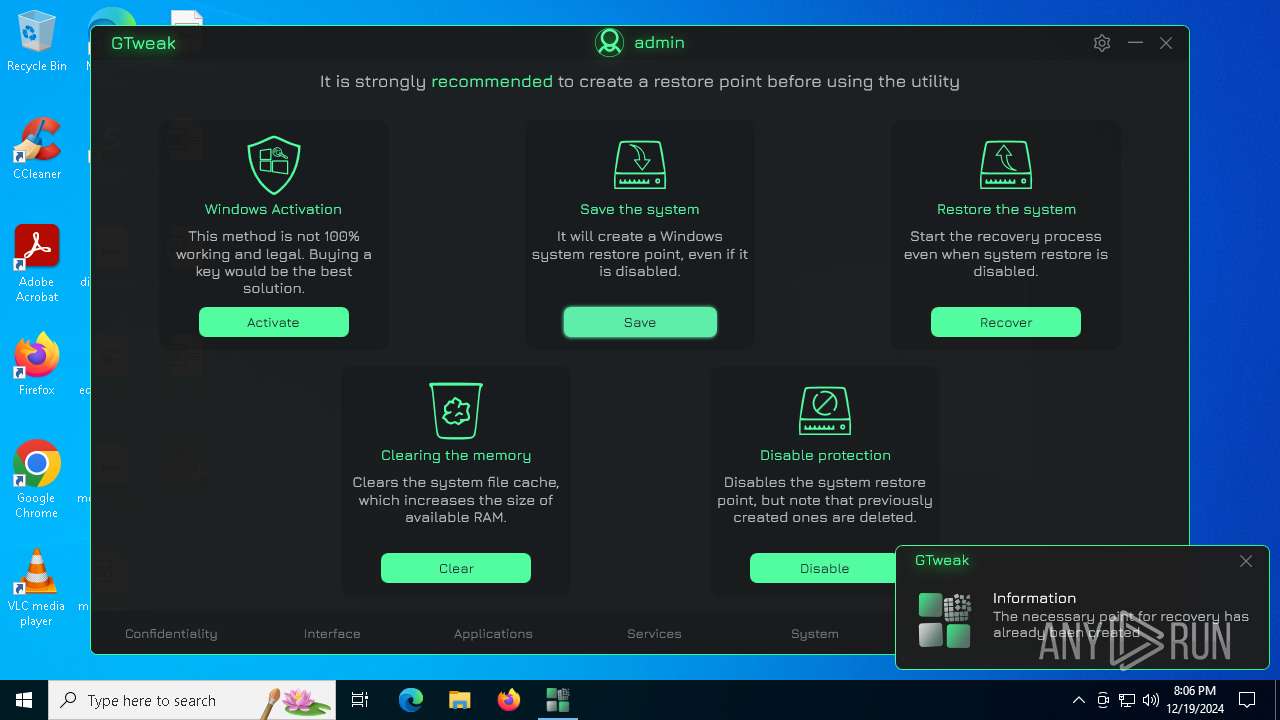
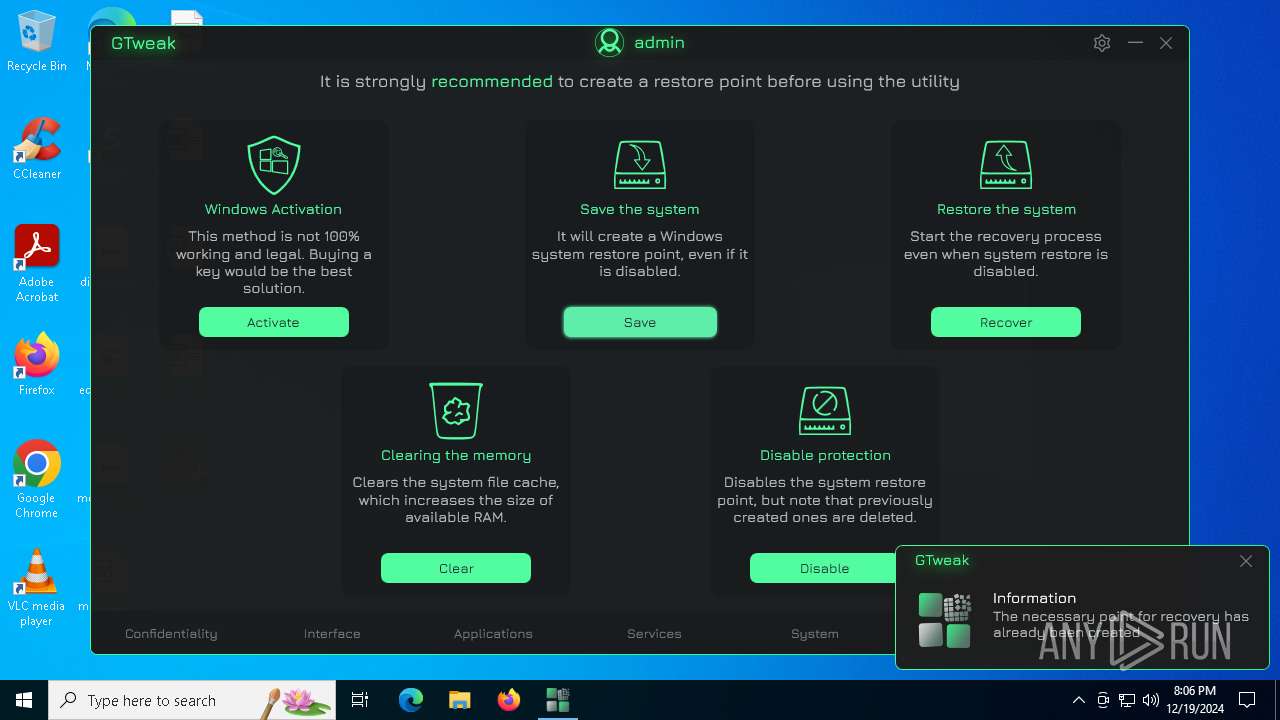
MALICIOUS
Starts CMD.EXE for self-deleting
- GTweak.exe (PID: 6724)
SUSPICIOUS
Starts CMD.EXE for commands execution
- GTweak.exe (PID: 6724)
Starts application with an unusual extension
- cmd.exe (PID: 5388)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6852)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 5388)
Starts POWERSHELL.EXE for commands execution
- GTweak.exe (PID: 6724)
Checks for external IP
- GTweak.exe (PID: 6724)
- svchost.exe (PID: 2192)
Executes as Windows Service
- VSSVC.exe (PID: 6388)
Reads security settings of Internet Explorer
- GTweak.exe (PID: 6724)
INFO
Checks supported languages
- GTweak.exe (PID: 6724)
- chcp.com (PID: 2828)
Creates files or folders in the user directory
- GTweak.exe (PID: 6724)
Reads Environment values
- GTweak.exe (PID: 6724)
Reads the machine GUID from the registry
- GTweak.exe (PID: 6724)
Disables trace logs
- GTweak.exe (PID: 6724)
- netsh.exe (PID: 1296)
- netsh.exe (PID: 396)
- netsh.exe (PID: 2972)
- netsh.exe (PID: 1512)
Reads the computer name
- GTweak.exe (PID: 6724)
Checks proxy server information
- GTweak.exe (PID: 6724)
Changes the display of characters in the console
- cmd.exe (PID: 5388)
Reads the software policy settings
- GTweak.exe (PID: 6724)
Creates files in the program directory
- GTweak.exe (PID: 6724)
The process uses the downloaded file
- powershell.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:12:09 13:10:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 1993216 |
| InitializedDataSize: | 218624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.35.603 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Perfect setup of Windows 10 & Windows 11 with the choice of options you need for better convenience and performance |
| FileDescription: | GTweak |
| FileVersion: | 5.0.35.603 |
| InternalName: | GTweak.exe |
| LegalCopyright: | Copyright © Greedeks 2024 |
| LegalTrademarks: | Greedeks |
| OriginalFileName: | GTweak.exe |
| ProductName: | GTweak |
| ProductVersion: | Build: 5.0.3 |
| AssemblyVersion: | 5.0.35.603 |
Total processes
170
Monitored processes
51
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | netsh int ipv6 6to4 show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 520 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | netsh int teredo show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1416 | "powershell.exe" Get-ComputerRestorePoint | Where-Object {$_.Description -ne 'Точка созданная с помощью GTweak' -and $_.Description -ne 'A point created with a GTweak'} | Select-Object EventType | ft -hide | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | GTweak.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | "powershell.exe" Get-LocalUser | Where-Object { $_.Enabled -match 'True'} | Select-Object PrincipalSource | ft -hide | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | GTweak.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
70 967
Read events
70 792
Write events
174
Delete events
1
Modification events
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Notification |
Value: True | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Sound |
Value: True | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Volume |
Value: 50 | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | TopMost |
Value: False | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Update |
Value: True | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | HiddenIP |
Value: False | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Theme |
Value: Dark | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Language |
Value: en | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\GTweak_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6724) GTweak.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\GTweak_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6724 | GTweak.exe | C:\Users\admin\AppData\Local\GTweak\resource\GTweak.ico | image | |
MD5:66B70CDF1E3AC3AABFD6A04FD585E153 | SHA256:1C6FBF4479B892AE5CC03FCD0945E33D86BA51B5248C63681DF4A5215DC0317F | |||
| 3140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z2sfp5ux.eeo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qjenv2wr.2r1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6724 | GTweak.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML.bak | text | |
MD5:7050D5AE8ACFBE560FA11073FEF8185D | SHA256:CB87767C4A384C24E4A0F88455F59101B1AE7B4FB8DE8A5ADB4136C5F7EE545B | |||
| 6724 | GTweak.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | xml | |
MD5:90BE2701C8112BEBC6BD58A7DE19846E | SHA256:644FBCDC20086E16D57F31C5BAD98BE68D02B1C061938D2F5F91CBE88C871FBF | |||
| 6724 | GTweak.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:5433EAB10C6B5C6D55B7CBD302426A39 | SHA256:23DBF7014E99E93AF5F2760F18EE1370274F06A453145C8D539B66D798DAD131 | |||
| 1876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nsh1wvzp.g4u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6724 | GTweak.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\CurrentDatabase_400.wmdb | binary | |
MD5:CAF15722EE937A480F0BB2484A6E7805 | SHA256:BCDF195F522AB1F5D9A83D48B1A2674754765EE2174698C5C8BA54326D436E1B | |||
| 6192 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dkazlyeg.rf2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6228 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kmyzt4n2.byw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
19
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 140.82.121.6:443 | https://api.github.com/repos/greedeks/gtweak/releases/latest | unknown | — | — | unknown |
6724 | GTweak.exe | GET | — | 208.95.112.1:80 | http://ip-api.com/json/?fields=61439 | unknown | — | — | shared |
6724 | GTweak.exe | GET | — | 208.95.112.1:80 | http://ip-api.com/json/?fields=61439 | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6724 | GTweak.exe | 140.82.121.6:443 | api.github.com | GITHUB | US | whitelisted |
6724 | GTweak.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.github.com |
| whitelisted |
ip-api.com |
| shared |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6724 | GTweak.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6724 | GTweak.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |