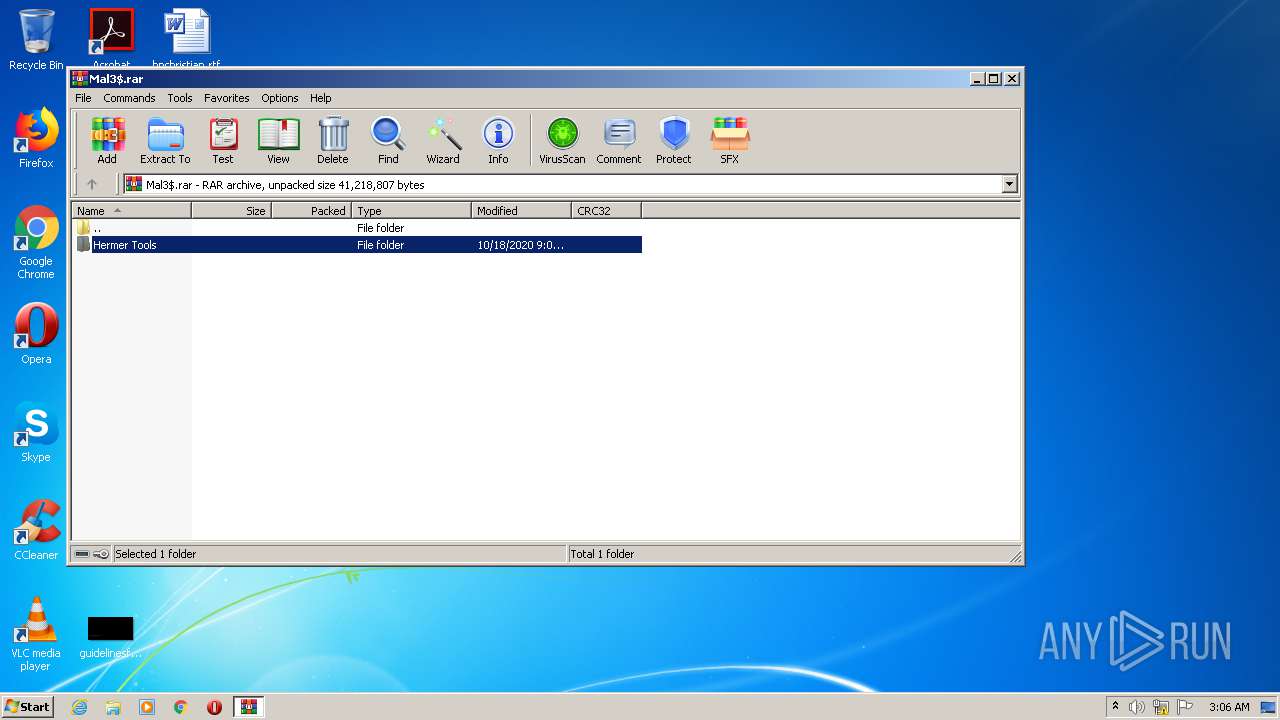
| File name: | Mal3$.rar |
| Full analysis: | https://app.any.run/tasks/bc7d7722-db22-4fc6-afdc-220d485a52da |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 02:06:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
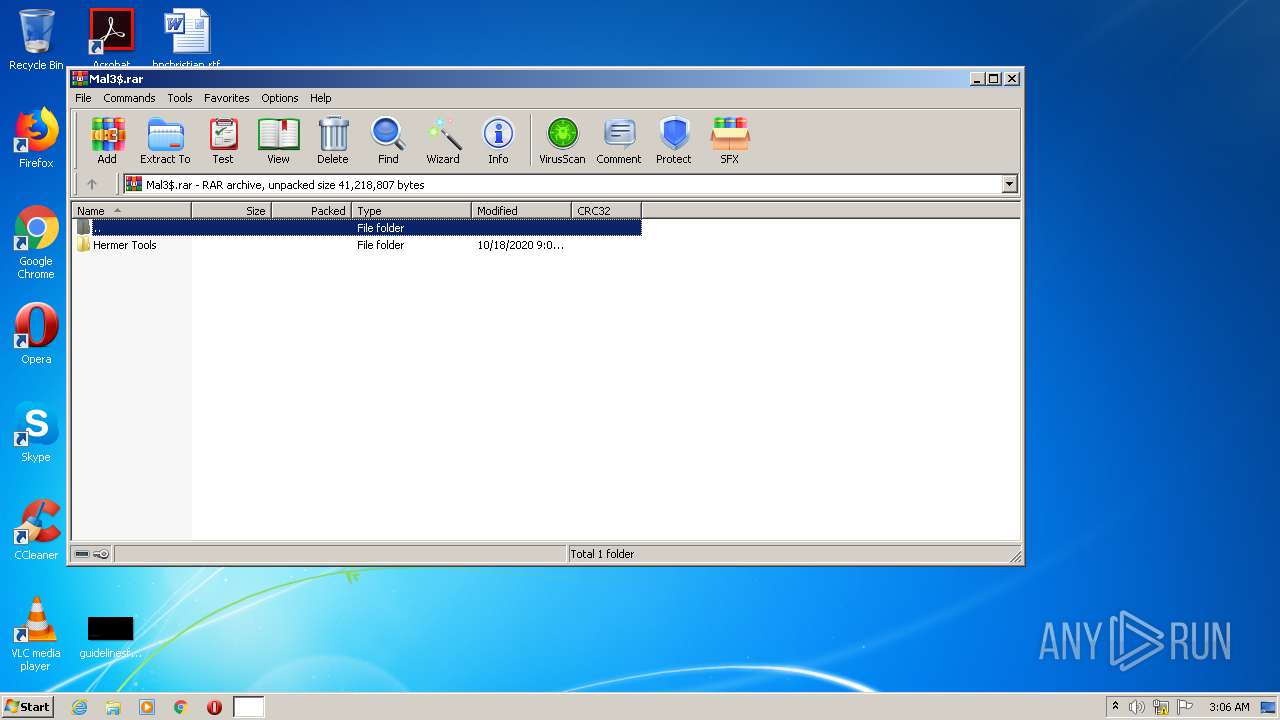
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | EF2181C3E6B686FFBE308CBC9C4974F6 |
| SHA1: | 973FDB6D8EDFF4353AFA3F877260D2D19CC8E9A1 |
| SHA256: | A361D02CBDED00DF80272895B681F3677A5427AA2B843CD9D7A9DDD14155E30A |
| SSDEEP: | 393216:ViCpCJQw+VNi9aEIs5EvK0rxVuaTZFoWt+8BC/Eveo:wDB909xV9TjLciCqeo |
MALICIOUS
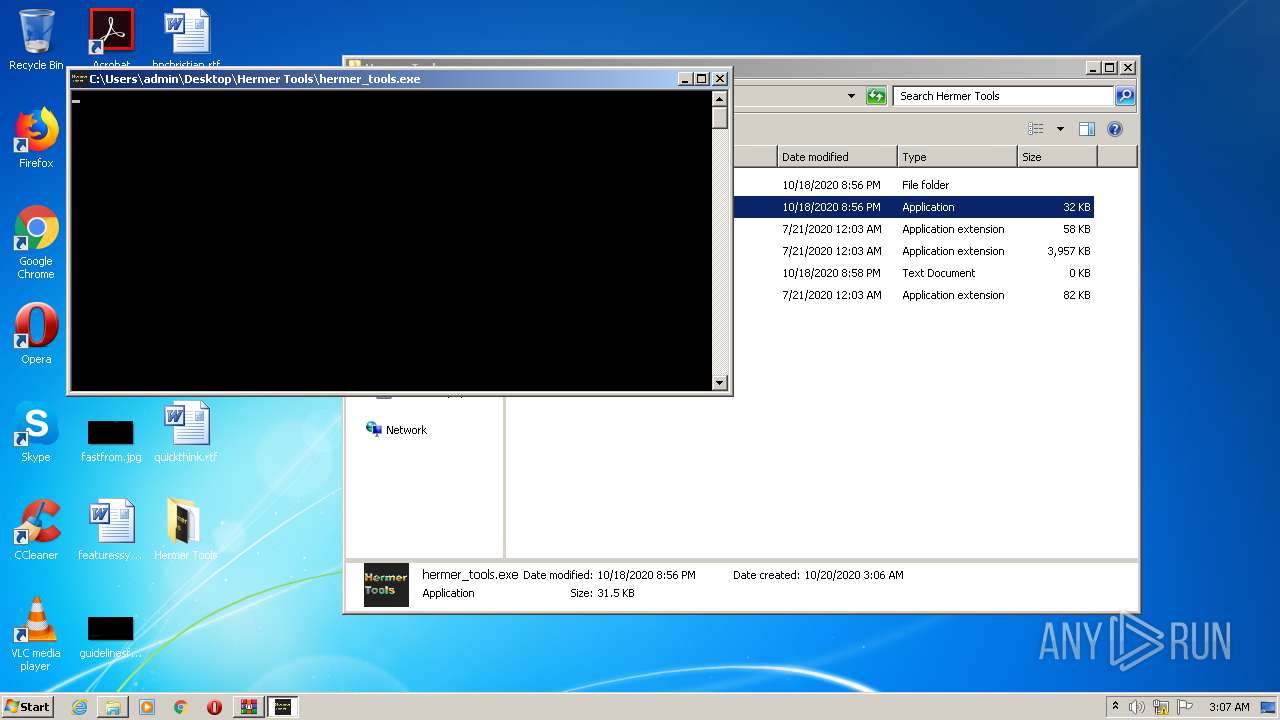
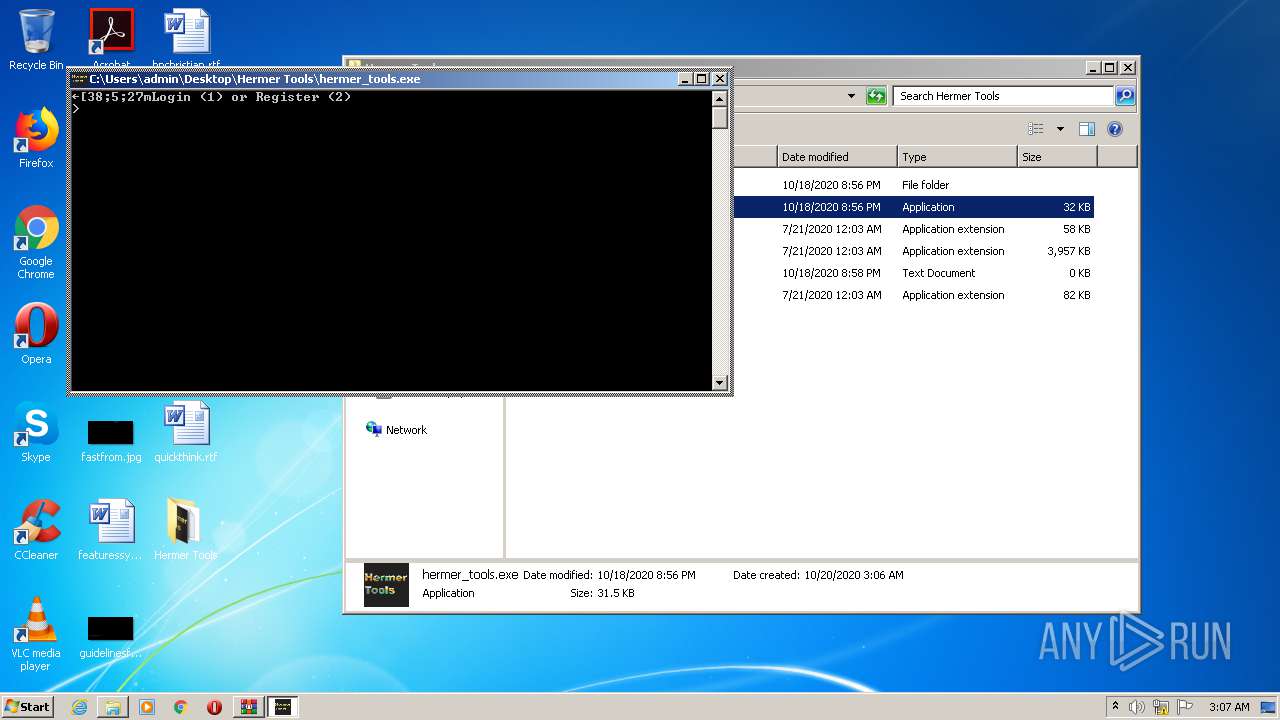
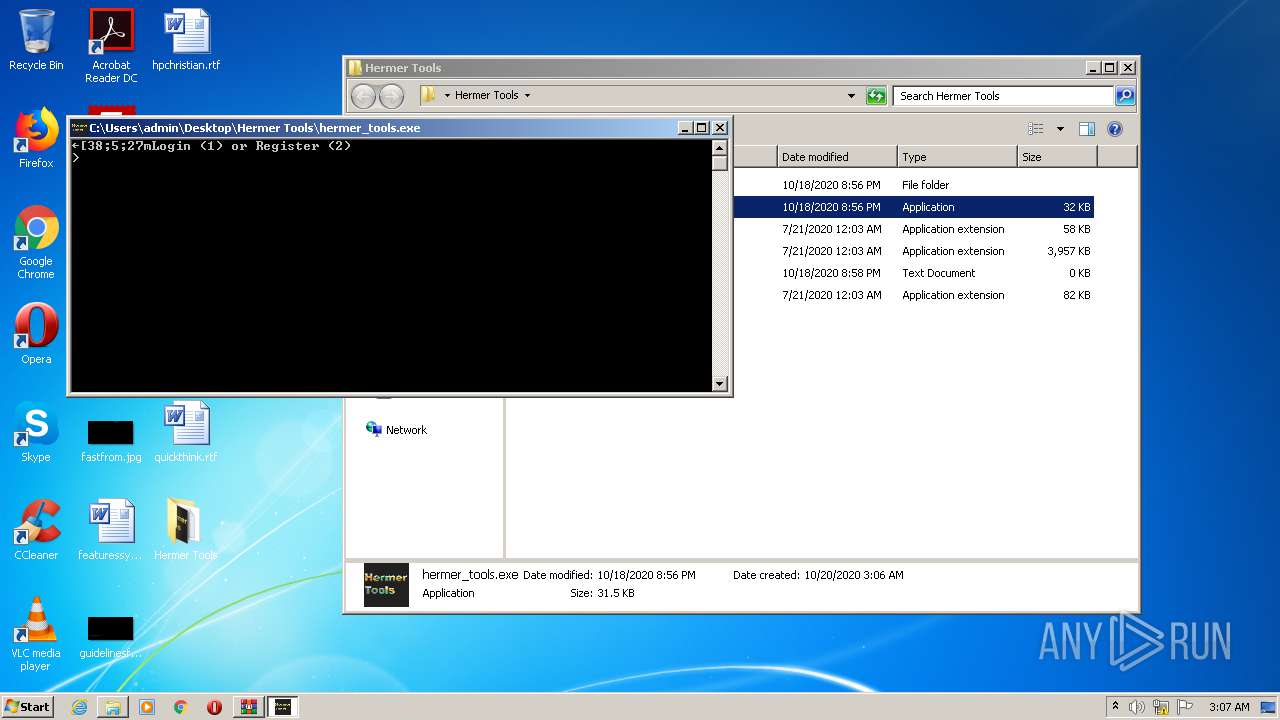
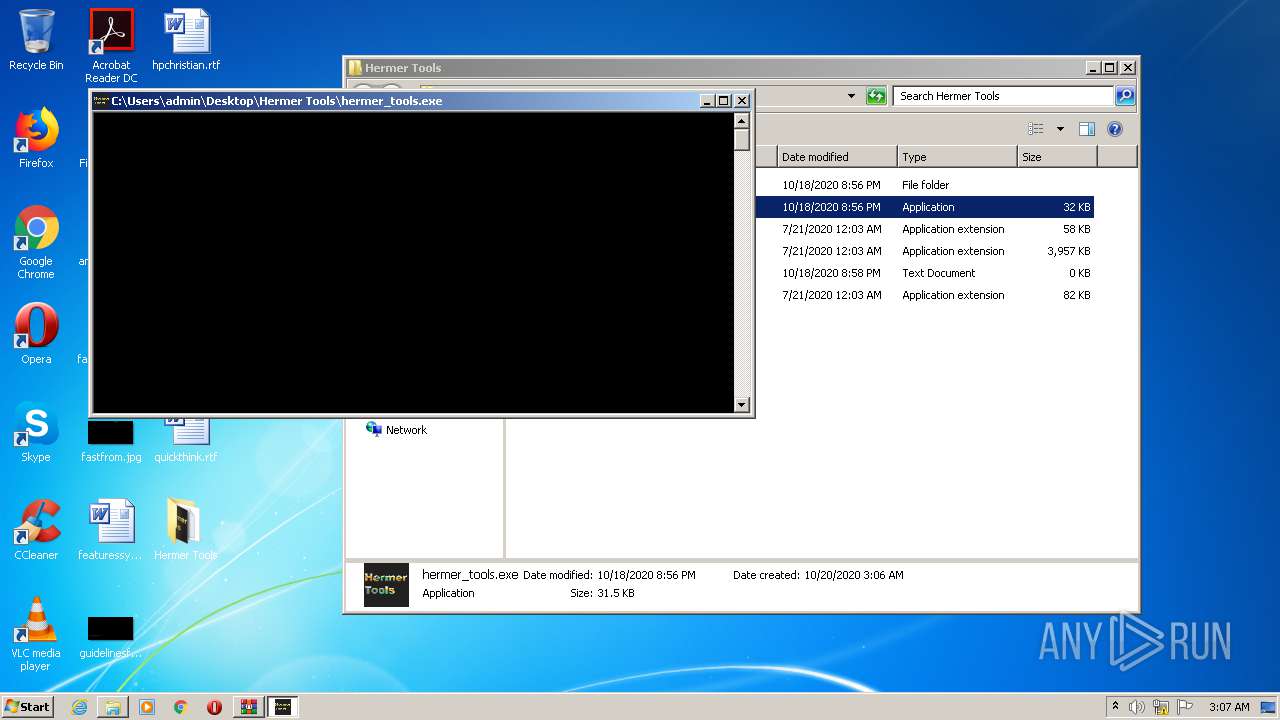
Application was dropped or rewritten from another process
- hermer_tools.exe (PID: 2728)
- hermer_tools.exe (PID: 3652)
Loads dropped or rewritten executable
- hermer_tools.exe (PID: 2728)
- SearchProtocolHost.exe (PID: 2500)
- hermer_tools.exe (PID: 3652)
SUSPICIOUS
Loads Python modules
- hermer_tools.exe (PID: 2728)
- hermer_tools.exe (PID: 3652)
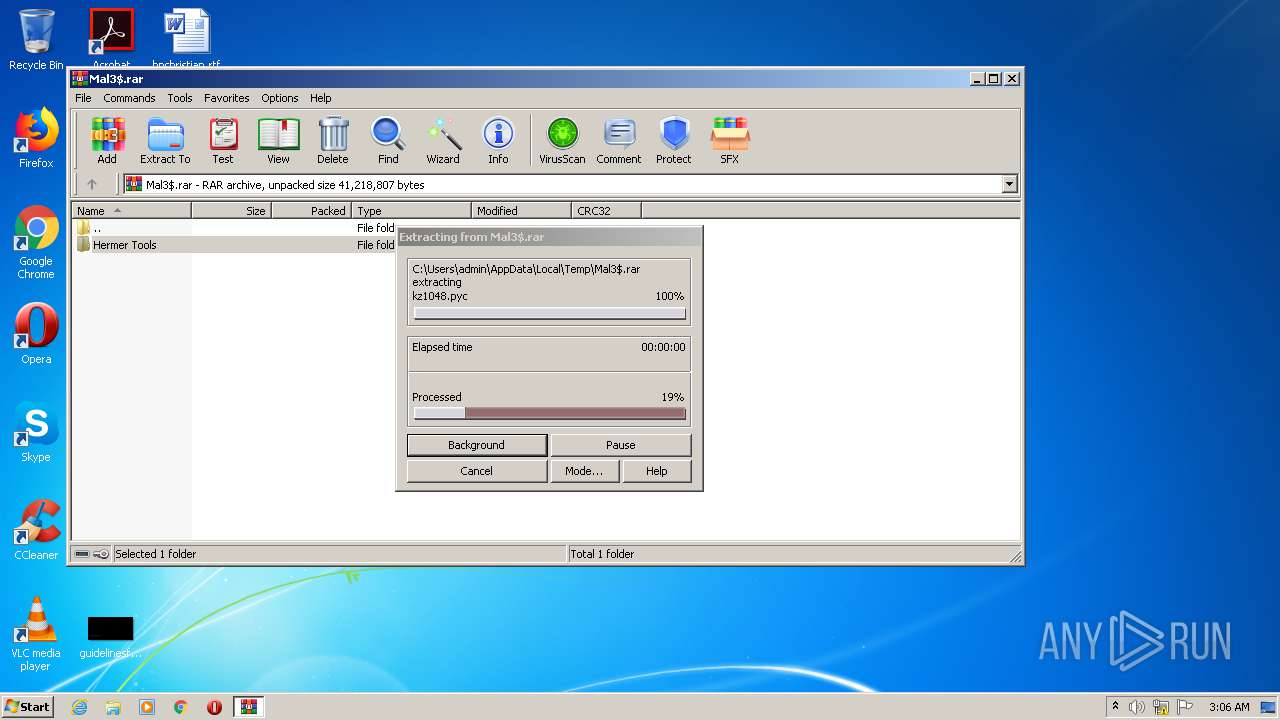
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2476)
Uses WMIC.EXE to obtain a system information
- hermer_tools.exe (PID: 2728)
- hermer_tools.exe (PID: 3652)
Starts CMD.EXE for commands execution
- hermer_tools.exe (PID: 2728)
- hermer_tools.exe (PID: 3652)
INFO
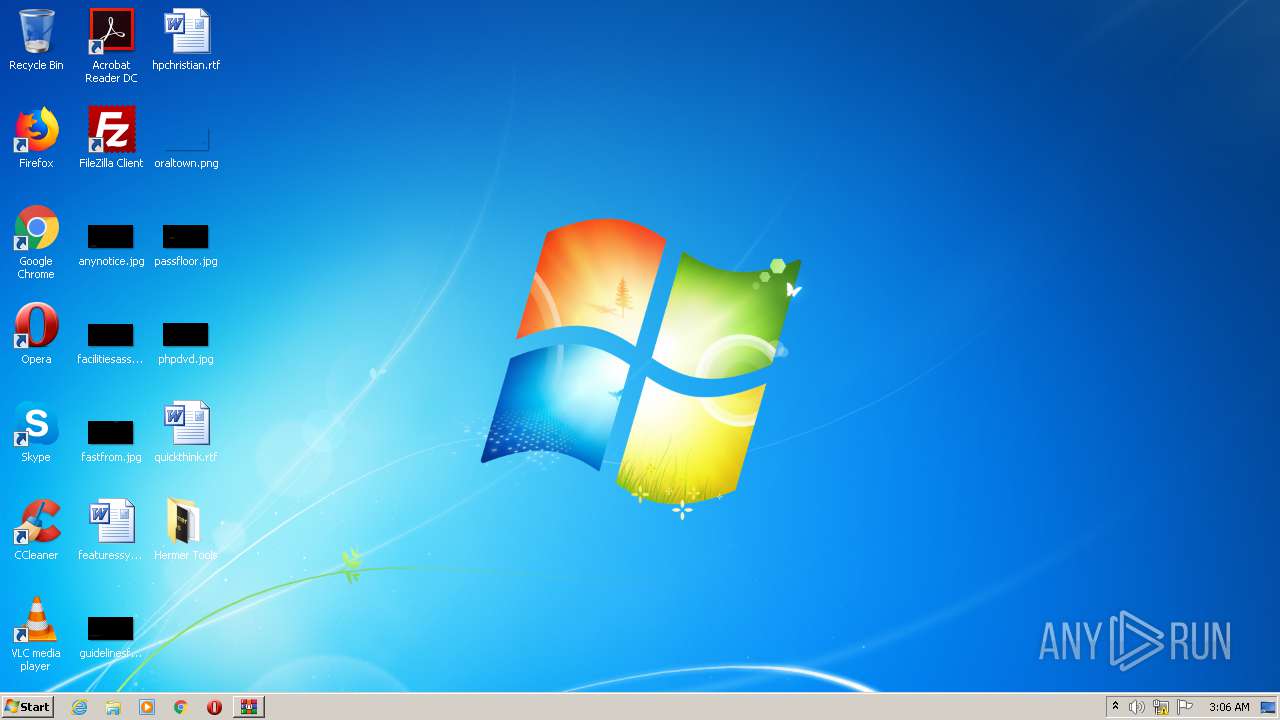
Manual execution by user
- hermer_tools.exe (PID: 2728)
- hermer_tools.exe (PID: 3652)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
47
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | wmic csproduct get uuid | C:\Windows\System32\Wbem\wmic.exe | — | hermer_tools.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2352 | wmic csproduct get uuid | C:\Windows\System32\Wbem\wmic.exe | — | hermer_tools.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2356 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | hermer_tools.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2372 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | hermer_tools.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Mal3$.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2500 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\Desktop\Hermer Tools\hermer_tools.exe" | C:\Users\admin\Desktop\Hermer Tools\hermer_tools.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\Desktop\Hermer Tools\hermer_tools.exe" | C:\Users\admin\Desktop\Hermer Tools\hermer_tools.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
833
Read events
820
Write events
13
Delete events
0
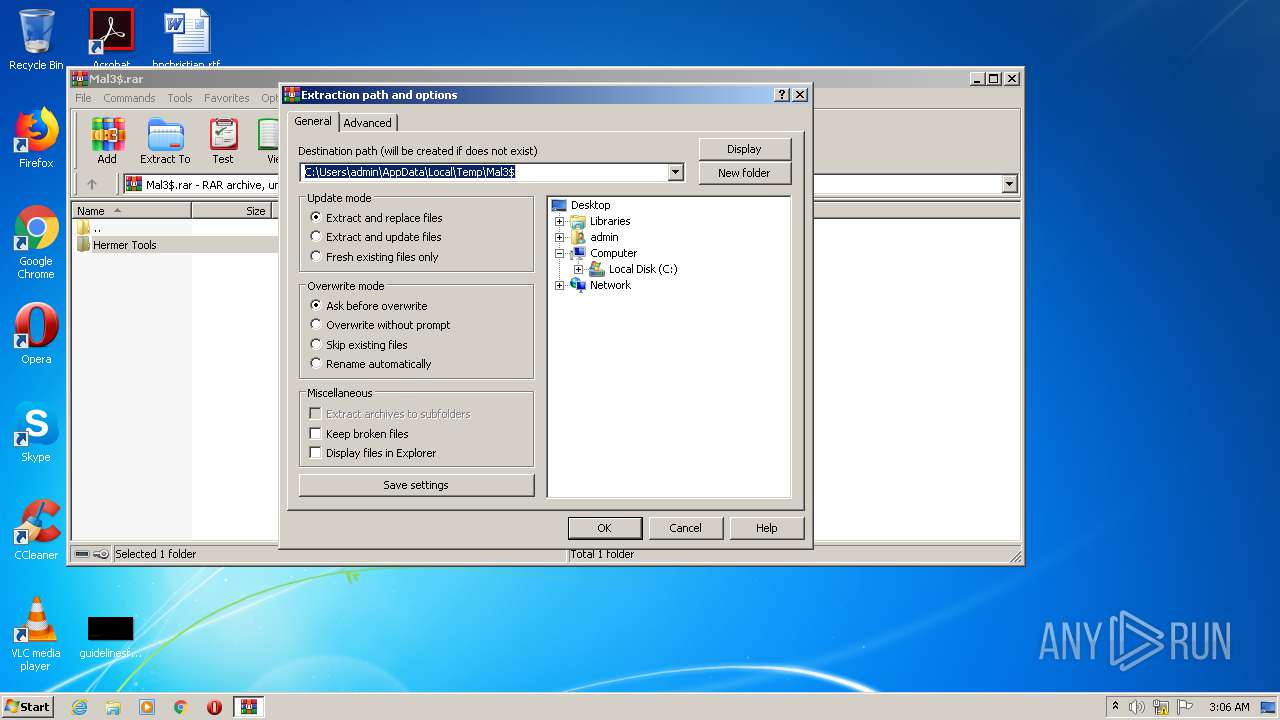
Modification events
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Mal3$.rar | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2500) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
46
Suspicious files
544
Text files
1 423
Unknown types
47
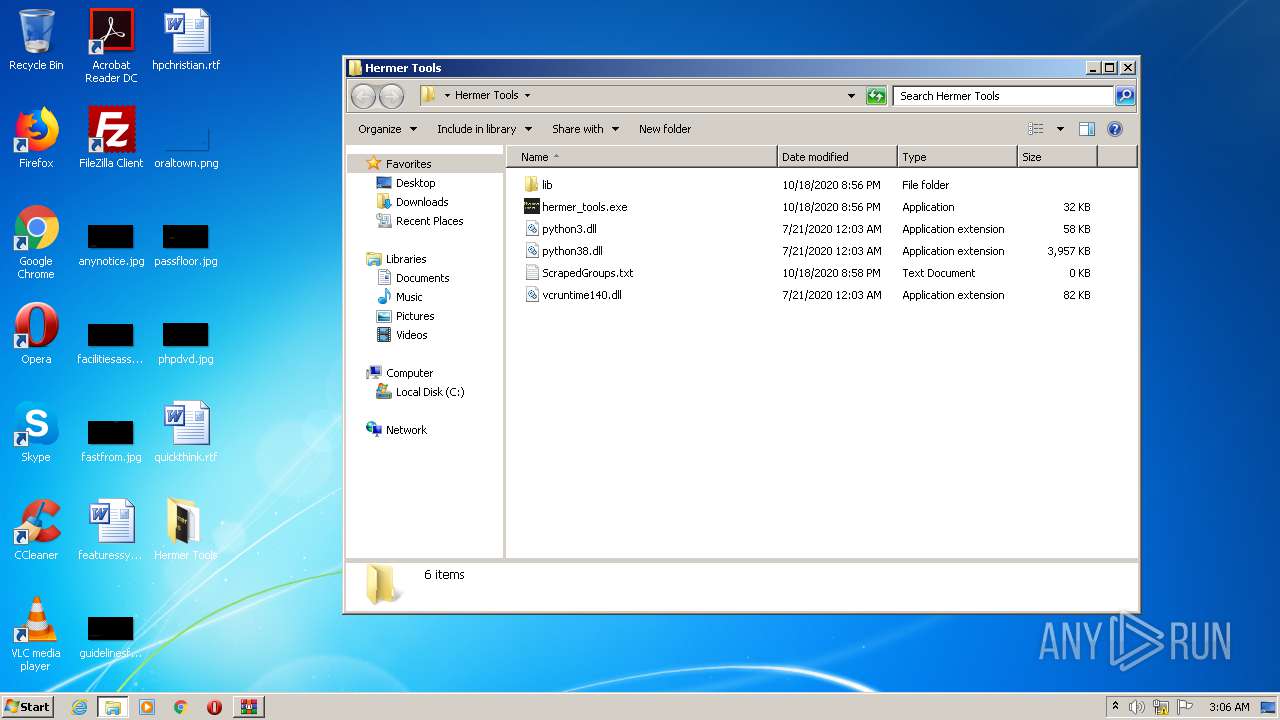
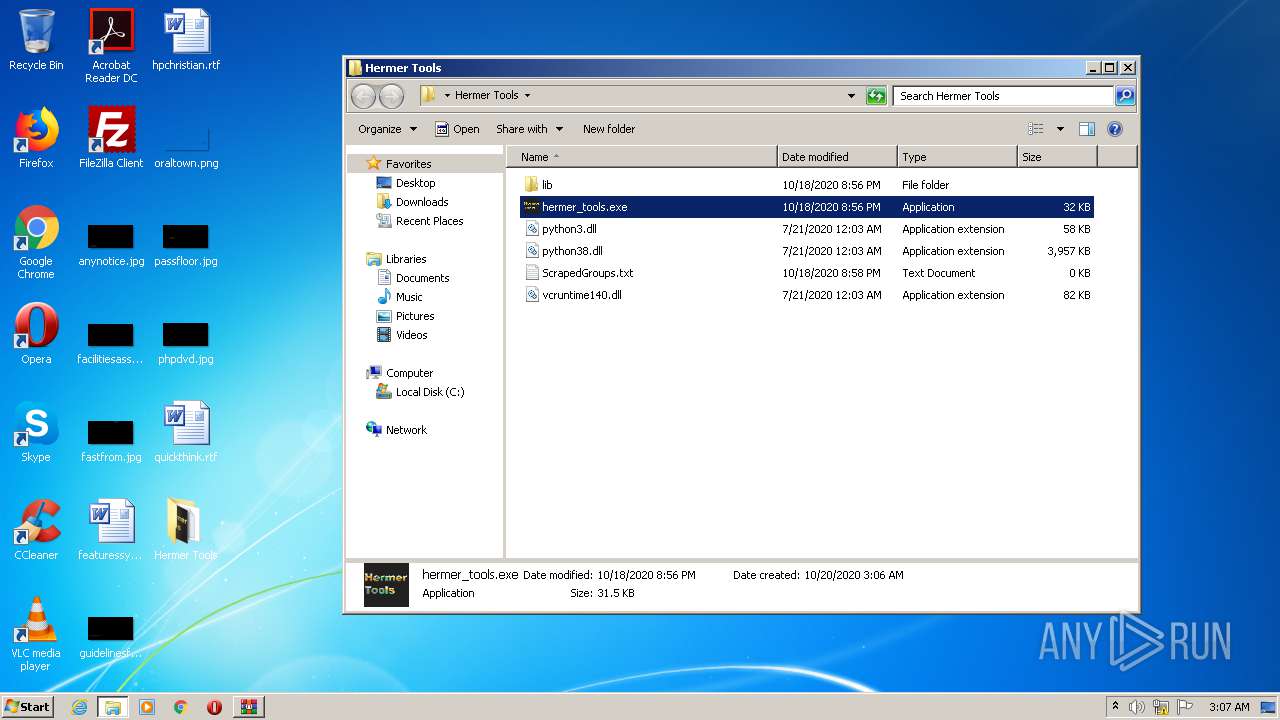
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\hermer_tools.exe | executable | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\constants.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\base_tasks.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\format_helpers.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\base_events.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\base_subprocess.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\base_futures.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\exceptions.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\locks.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\Desktop\Hermer Tools\lib\asyncio\futures.pyc | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report