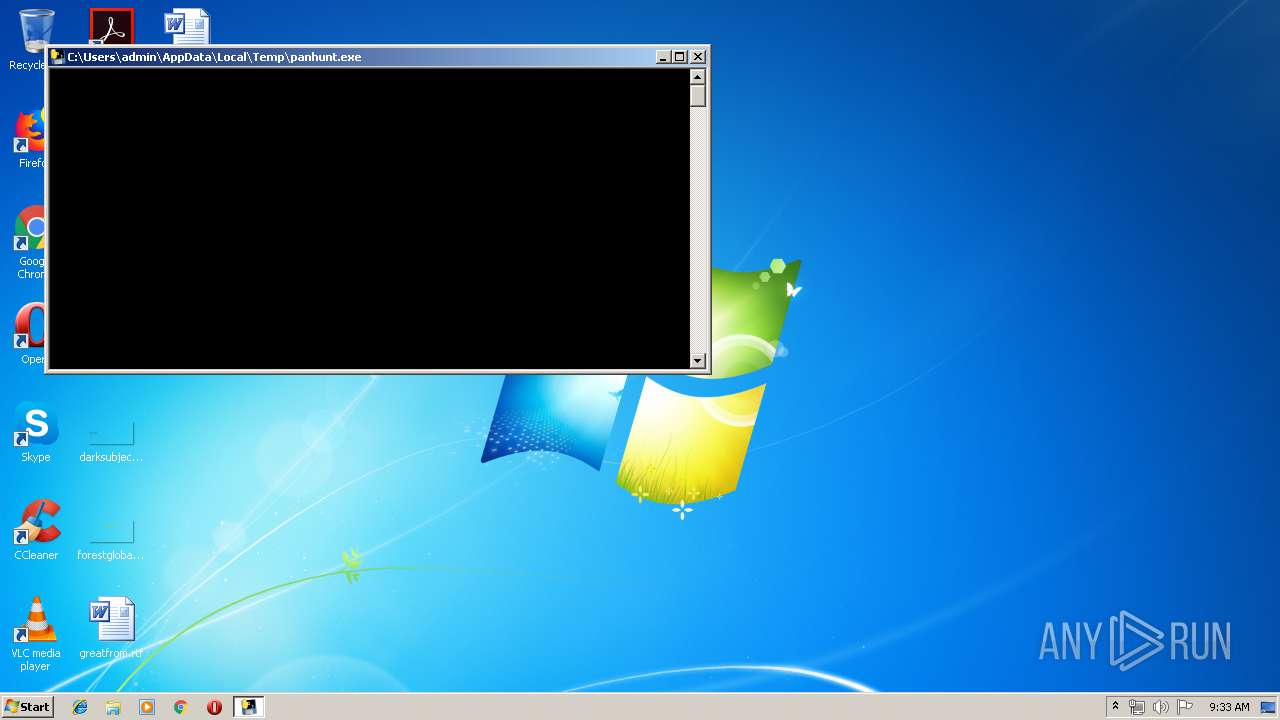
| File name: | panhunt.exe |
| Full analysis: | https://app.any.run/tasks/08ae47f6-9420-47e2-b90c-5d33741ff55c |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 08:32:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 16BBD59A99553E10CFEE6494DE25DF30 |
| SHA1: | 04F1171091B3FAA340C4EA15CA3DC3AC8D3659D4 |
| SHA256: | A3495519FF7160E4EE89868E7C69DC276C83490FC435798E0CFD2A6C3E370D83 |
| SSDEEP: | 98304:4cM96QF33YiVuCsaLgXYRY2zluD4bl5RPtYQeIXyehmbuJJ:NE6G3YeupaPRY2zluDsp1PXFmbuJ |
MALICIOUS
Loads dropped or rewritten executable
- panhunt.exe (PID: 3952)
Actions looks like stealing of personal data
- panhunt.exe (PID: 3952)
SUSPICIOUS
Application launched itself
- panhunt.exe (PID: 1012)
Loads Python modules
- panhunt.exe (PID: 3952)
Executable content was dropped or overwritten
- panhunt.exe (PID: 1012)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40960 |
| InitializedDataSize: | 127488 |
| UninitializedDataSize: | 51200 |
| EntryPoint: | 0x14f0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00009FF4 | 0x0000A000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.21798 |
.data | 0x0000B000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.541159 |
.rdata | 0x0000C000 | 0x00004EA8 | 0x00005000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.97064 |
.bss | 0x00011000 | 0x0000C6A4 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000C2C | 0x00000E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.84633 |
.CRT | 0x0001F000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.267208 |
.tls | 0x00020000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.175526 |
.rsrc | 0x00021000 | 0x0000EC4C | 0x0000EE00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.30073 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95053 | 443 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
msvcr100.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Users\admin\AppData\Local\Temp\panhunt.exe" | C:\Users\admin\AppData\Local\Temp\panhunt.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Local\Temp\panhunt.exe" | C:\Users\admin\AppData\Local\Temp\panhunt.exe | panhunt.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
14
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\Microsoft.VC90.CRT.manifest | xml | |
MD5:241A0EC0580005E5FEE986AFC78F6864 | SHA256:3993E65E8BCD38CAA3DD1CB8CC6507B4D98558A3FEAD96671FD00BFB3985CEE7 | |||
| 3952 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\panhunt_2019-05-15-093309.txt | text | |
MD5:— | SHA256:— | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\_ctypes.pyd | executable | |
MD5:D4E63D37BD2E2E4C8D411F213D1A0E03 | SHA256:00BB1BA68511D690024A76FAD1770A13CF74E4552AAABF80384A07ABA680D8D4 | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\msvcm90.dll | executable | |
MD5:96C7B7470ABE61BBC6F6E39FA06427DB | SHA256:B6691A3FEF03C385641D2FFD56BEBDBC19950750571C31C01383FA78C637DC57 | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\Include\pyconfig.h | text | |
MD5:BC185DE8B2437963368A85FDD9852951 | SHA256:8B130D901E0F83B55699D565F103F2F8F1B3A51712EBB4B9646EA517CC1F04D6 | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\select.pyd | executable | |
MD5:36E15944667B148005F41EFD28144D46 | SHA256:D4B43FF835CE0B42019D1D2722C44678D223837483D2D62455232B6C211274D0 | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\win32pipe.pyd | executable | |
MD5:0D4A1785AA8F949CFA2A19278CBE3C81 | SHA256:2EFC1764B23E02B2E91016EA331E68207CB5C2579166CA305A196FE343719D4D | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\pyexpat.pyd | executable | |
MD5:8AF50A8478A1512A0876B8F14AE0B0B3 | SHA256:9AC61BEA4CF0E80BBFB22A71F97080D292539F93696D52B97DEF069A0F4CAFED | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\msvcr90.dll | executable | |
MD5:5BC75D03ABF8EBAF9C5EA4E354DFB840 | SHA256:92281334CF905C35E7C93DD526B5C199EA9823CD52922F55F14E3008F98CD4E1 | |||
| 1012 | panhunt.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\_socket.pyd | executable | |
MD5:36DF5C04156580D8114E902FE7701D9F | SHA256:A7F11EF22074D69409EDDF7BDE7E8D533C31A6F8C1711F768173371004A64299 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report