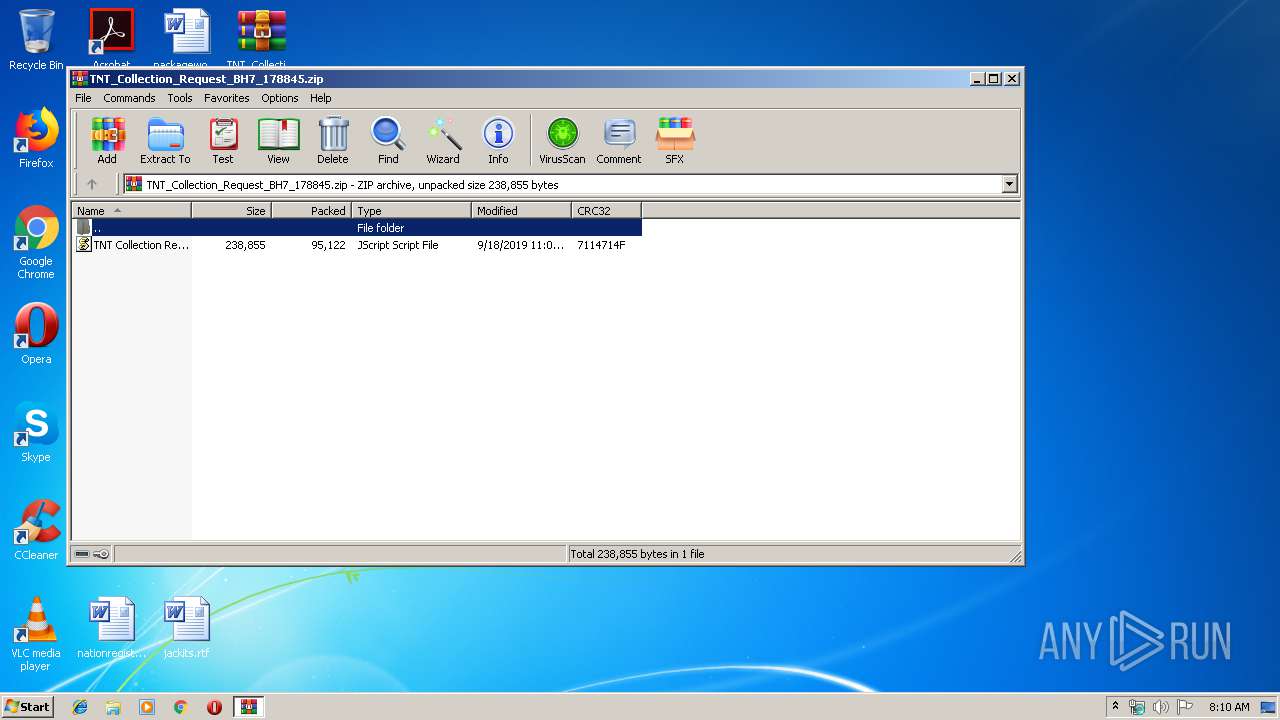
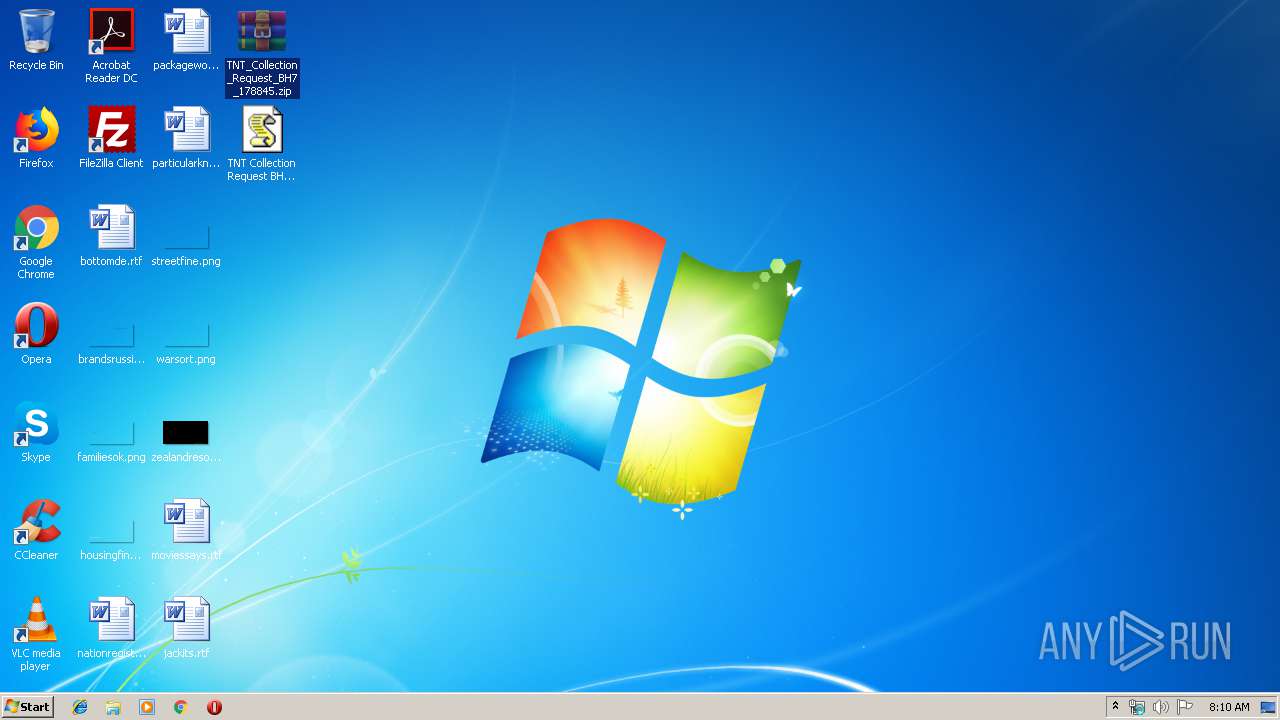
| File name: | TNT_Collection_Request_BH7_178845.zip |
| Full analysis: | https://app.any.run/tasks/0d1becea-e9ee-4c56-b0df-c2a4aea9da9b |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 07:09:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 62D4932BBA98708223CB31987DF59390 |
| SHA1: | F0E54C1998FBB34F9BBD9971DE80D17CA57E6FD6 |
| SHA256: | A34435D2621A56F97738527F1E86C49E50C558F593B8192DC032E2ED0D887C6F |
| SSDEEP: | 1536:pSa/Id/5/dh1o89V9ozmMJQn0yD8k8n2MOLWSc9mFLCi1WqCDb35suGLUVXn7LkZ:pSgIrVjb5MSnl8nQp7Wz35suGZ/EA/ |
MALICIOUS
Writes to a start menu file
- wscript.exe (PID: 2368)
- WScript.exe (PID: 3020)
- wscript.exe (PID: 3928)
Changes the autorun value in the registry
- wscript.exe (PID: 2368)
- wscript.exe (PID: 3928)
- WScript.exe (PID: 3020)
SUSPICIOUS
Application launched itself
- WScript.exe (PID: 3020)
- wscript.exe (PID: 3928)
Executes scripts
- WScript.exe (PID: 3020)
- wscript.exe (PID: 3928)
Creates files in the user directory
- WScript.exe (PID: 3020)
- wscript.exe (PID: 3928)
- wscript.exe (PID: 2368)
INFO
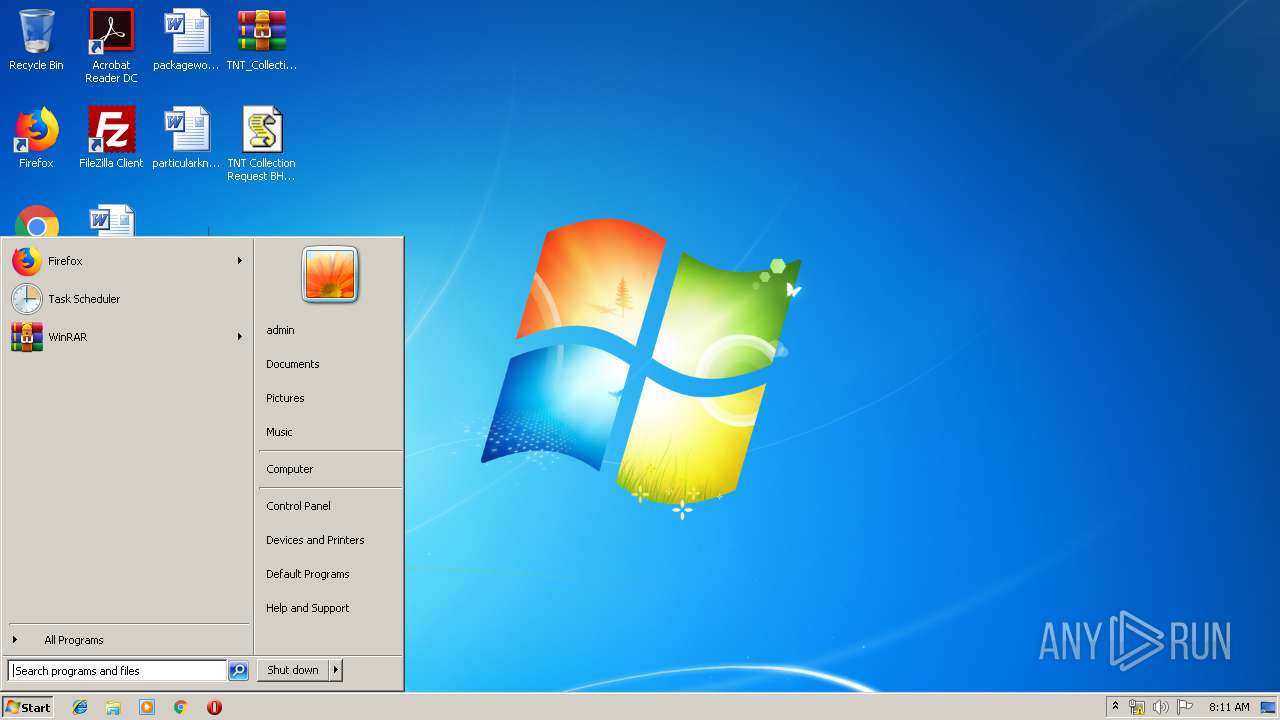
Manual execution by user
- WScript.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
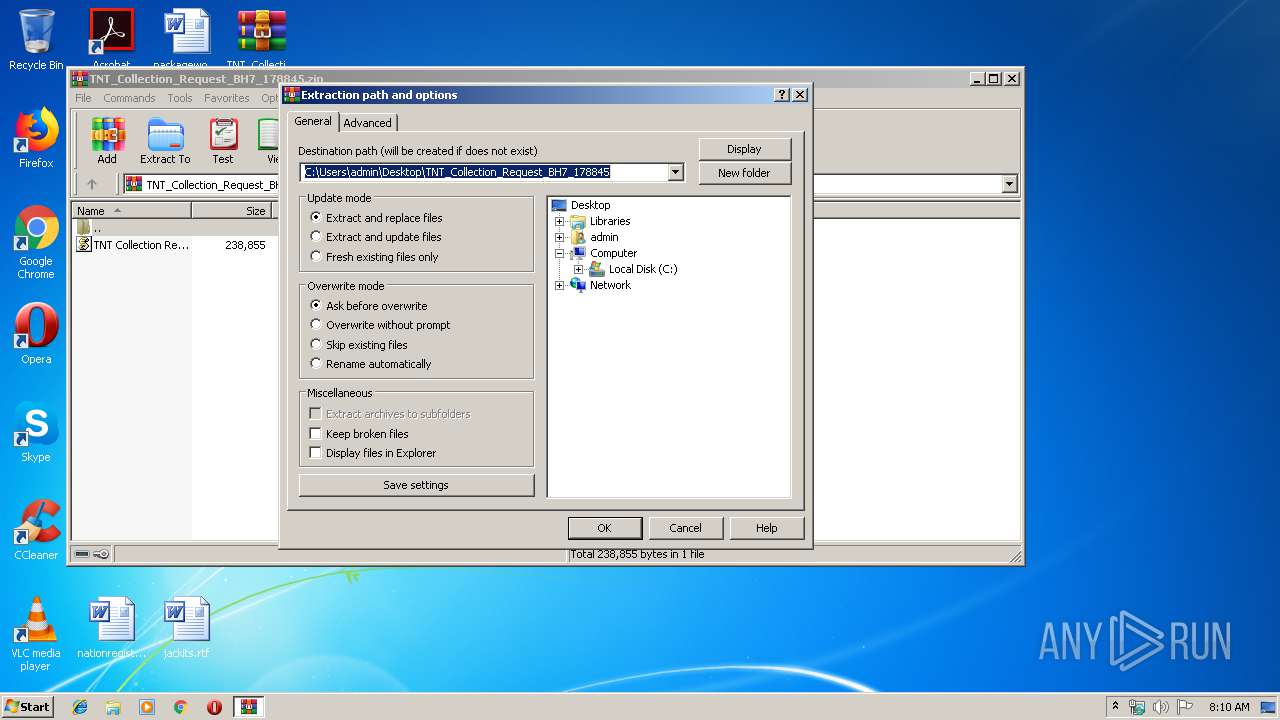
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:18 23:02:08 |
| ZipCRC: | 0x7114714f |
| ZipCompressedSize: | 95122 |
| ZipUncompressedSize: | 238855 |
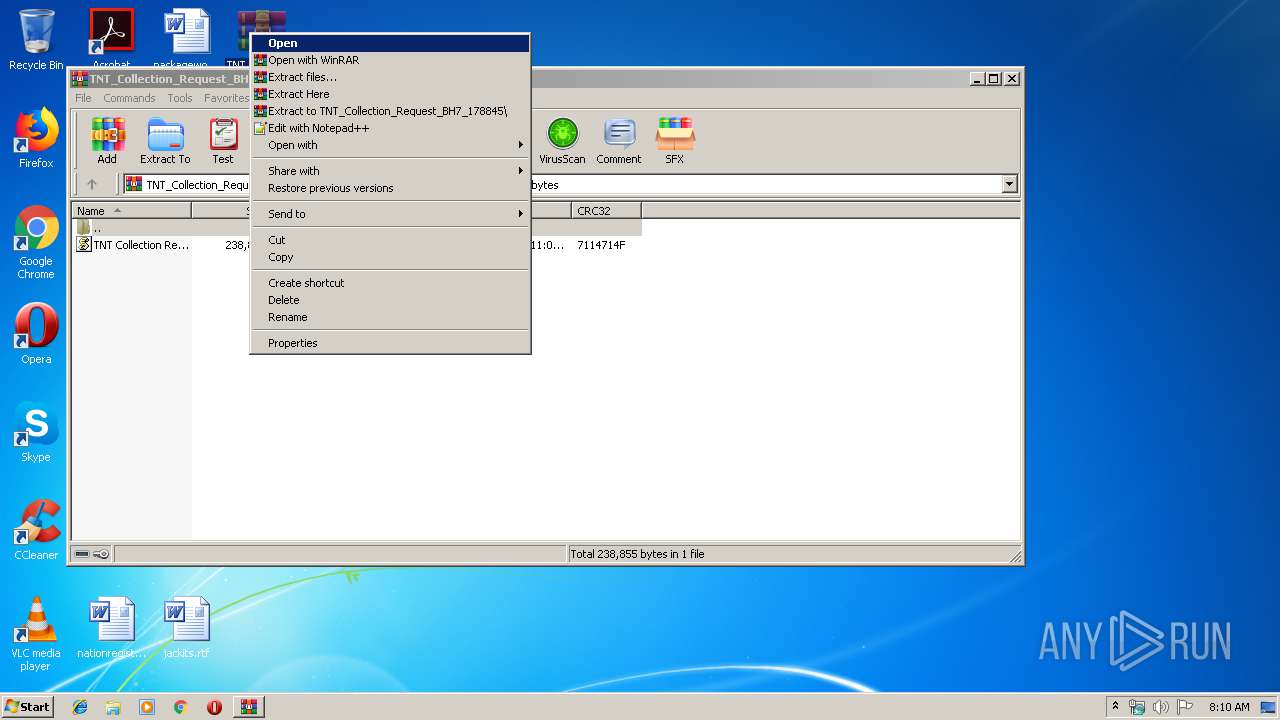
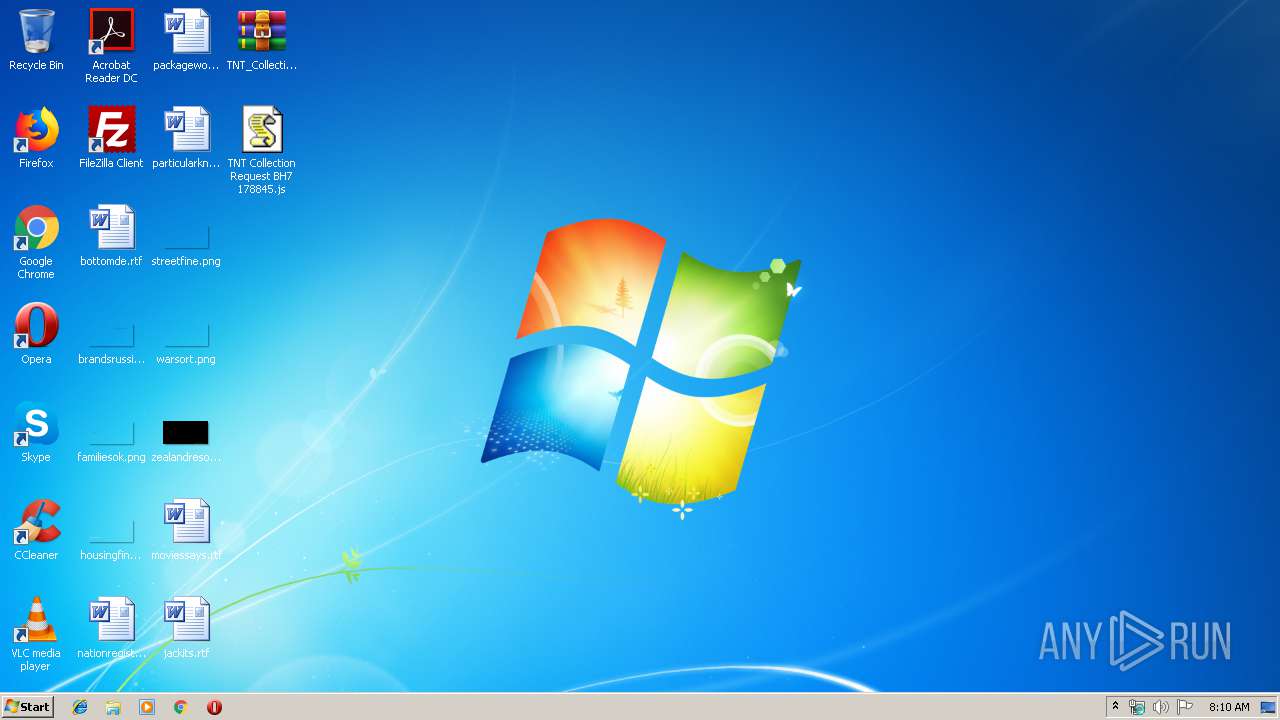
| ZipFileName: | TNT Collection Request BH7 178845.js |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2368 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\YLFuizCVuT.js" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\TNT_Collection_Request_BH7_178845.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3020 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\TNT Collection Request BH7 178845.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3336 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\YLFuizCVuT.js" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3928 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Local\Temp\TNT Collection Request BH7 178845.js" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
812
Read events
713
Write events
99
Delete events
0
Modification events
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\TNT_Collection_Request_BH7_178845.zip | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (2908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\TNT Collection Request BH7 178845.js | text | |
MD5:— | SHA256:— | |||
| 3020 | WScript.exe | C:\Users\admin\AppData\Roaming\YLFuizCVuT.js | text | |
MD5:— | SHA256:— | |||
| 2368 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\YLFuizCVuT.js | text | |
MD5:— | SHA256:— | |||
| 3020 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\TNT Collection Request BH7 178845.js | text | |
MD5:— | SHA256:— | |||
| 3928 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 2908 | WinRAR.exe | C:\Users\admin\Desktop\TNT Collection Request BH7 178845.js | text | |
MD5:— | SHA256:— | |||
| 3020 | WScript.exe | C:\Users\admin\AppData\Local\Temp\TNT Collection Request BH7 178845.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
21
DNS requests
5
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | wscript.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
2368 | wscript.exe | 45.79.48.200:7757 | pluginsrv1.duckdns.org | Linode, LLC | US | malicious |
3928 | wscript.exe | 43.252.213.38:2813 | 2813.noip.me | Exa Bytes Network Sdn.Bhd. | MY | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pluginsrv1.duckdns.org |
| malicious |
ip-api.com |
| malicious |
2813.noip.me |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |