| File name: | roy_sample_actor_119.doc |
| Full analysis: | https://app.any.run/tasks/243a2cb6-10b4-4efb-ba4c-485b7cb4661c |
| Verdict: | No threats detected |
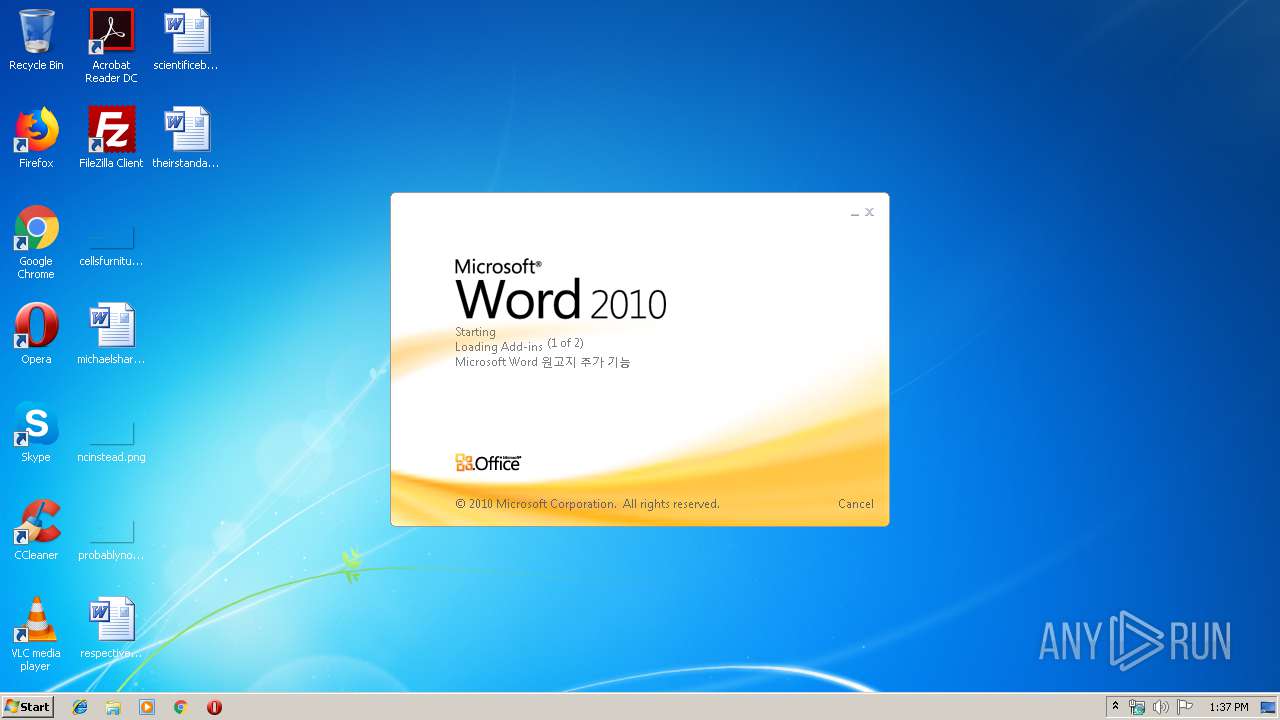
| Analysis date: | December 16, 2019, 13:37:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/CDFV2 |
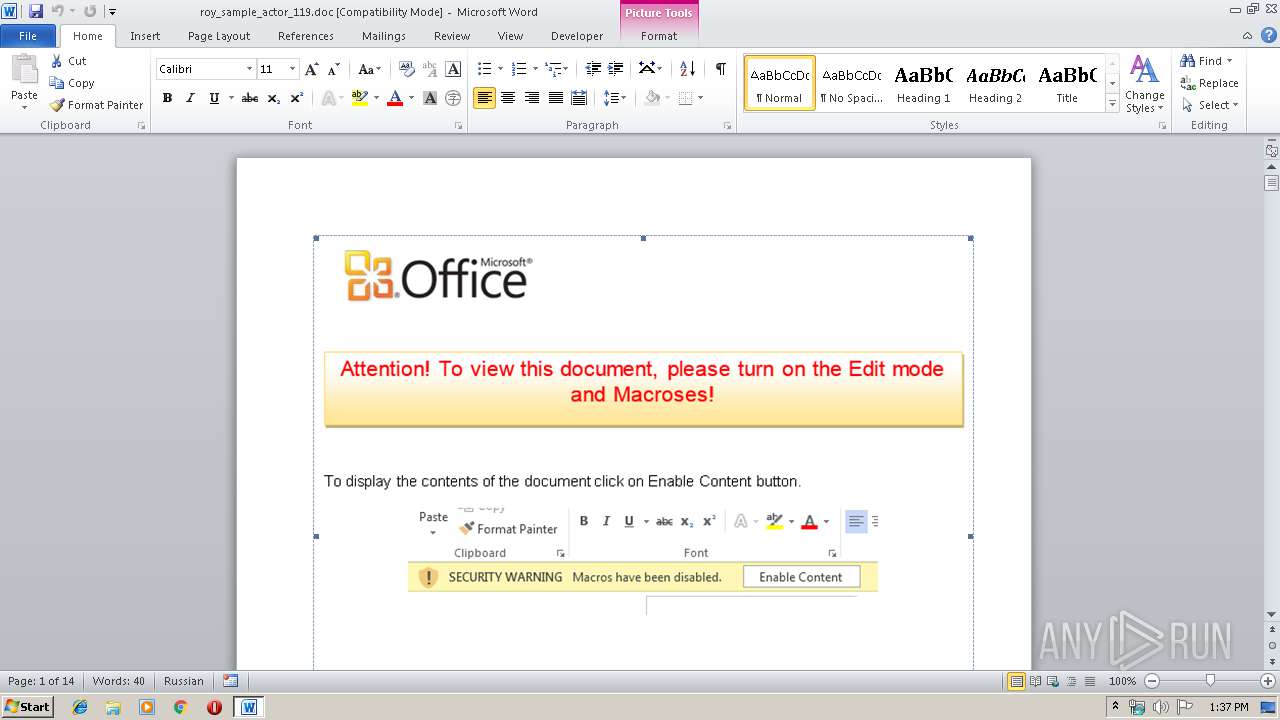
| File info: | Composite Document File V2 Document, Cannot read short stream |
| MD5: | 9A7B17A740407A9FC0299B5B8E7717FE |
| SHA1: | 06A5ED8DDC82810F5DE7E3311A08577F3535A08D |
| SHA256: | A33B86A8AD0961086D1AA7A71F937736D1BB6C24E932C241E5523D04A836F5CB |
| SSDEEP: | 3072:G+I8DQ16m6UvLeRspw7uzeJq+oqZSqf/NU5uWI:G+fQ1iUvCRawDJhoeSuNDj |
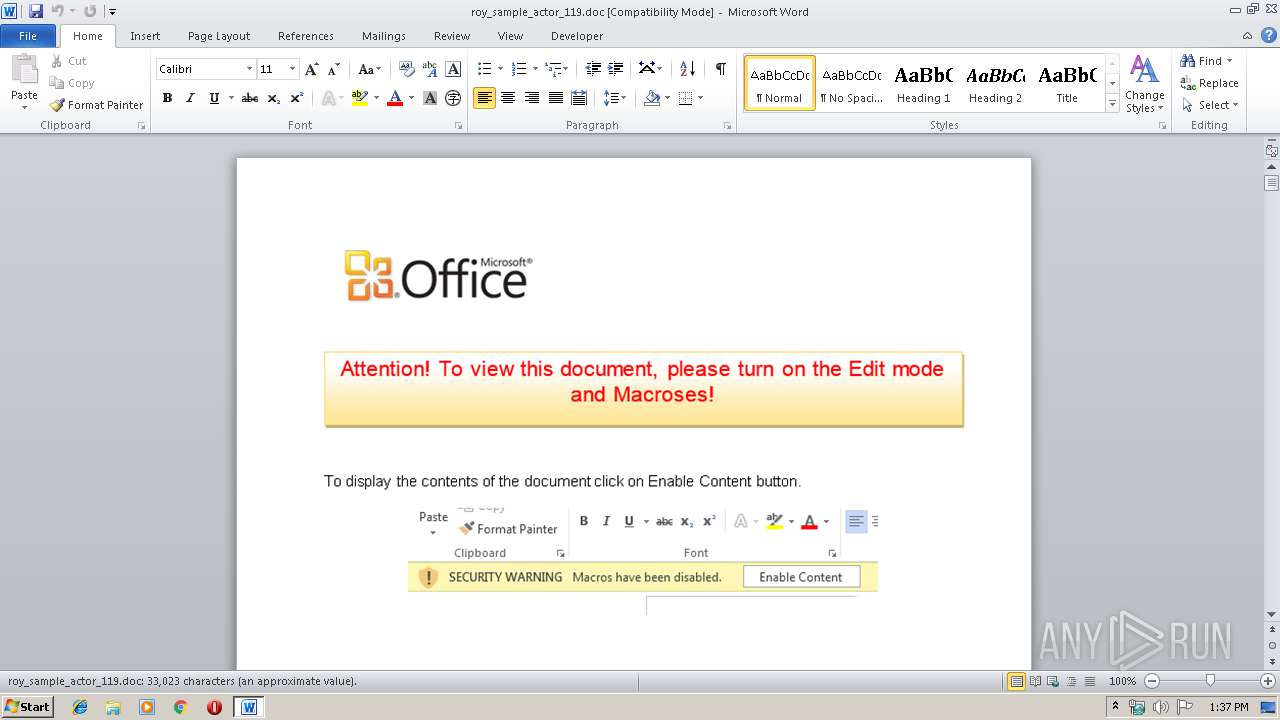
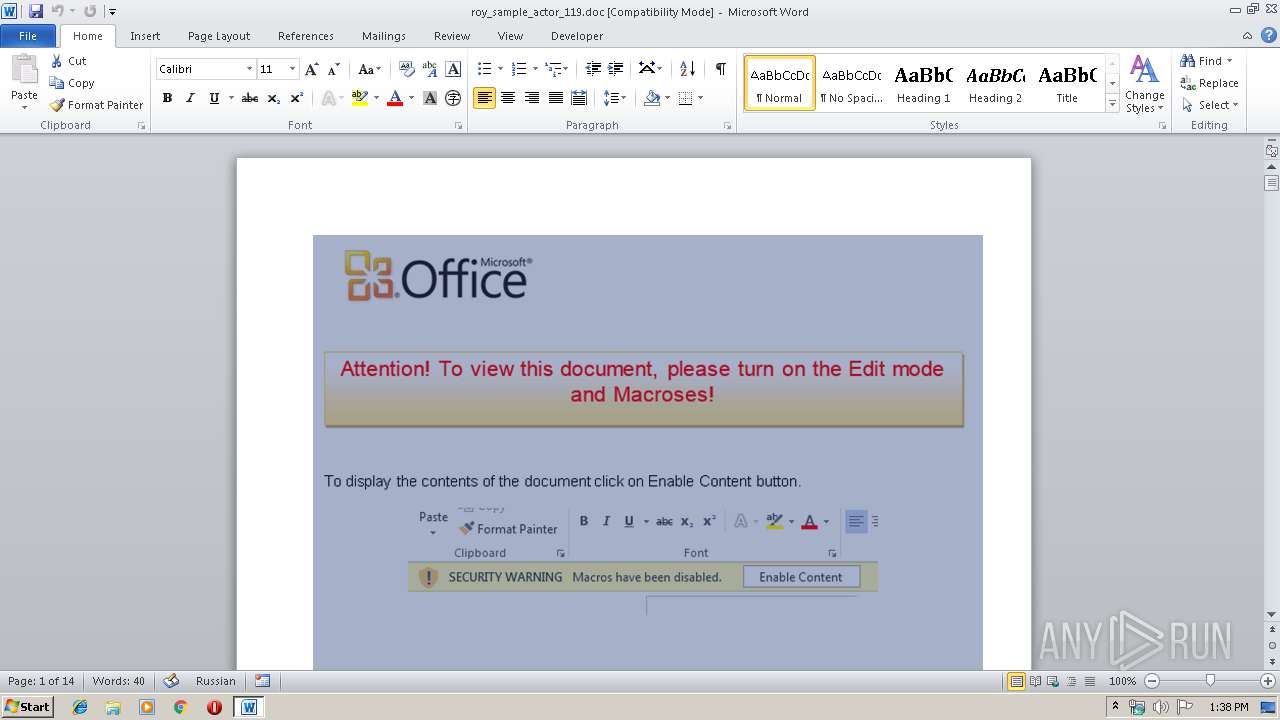
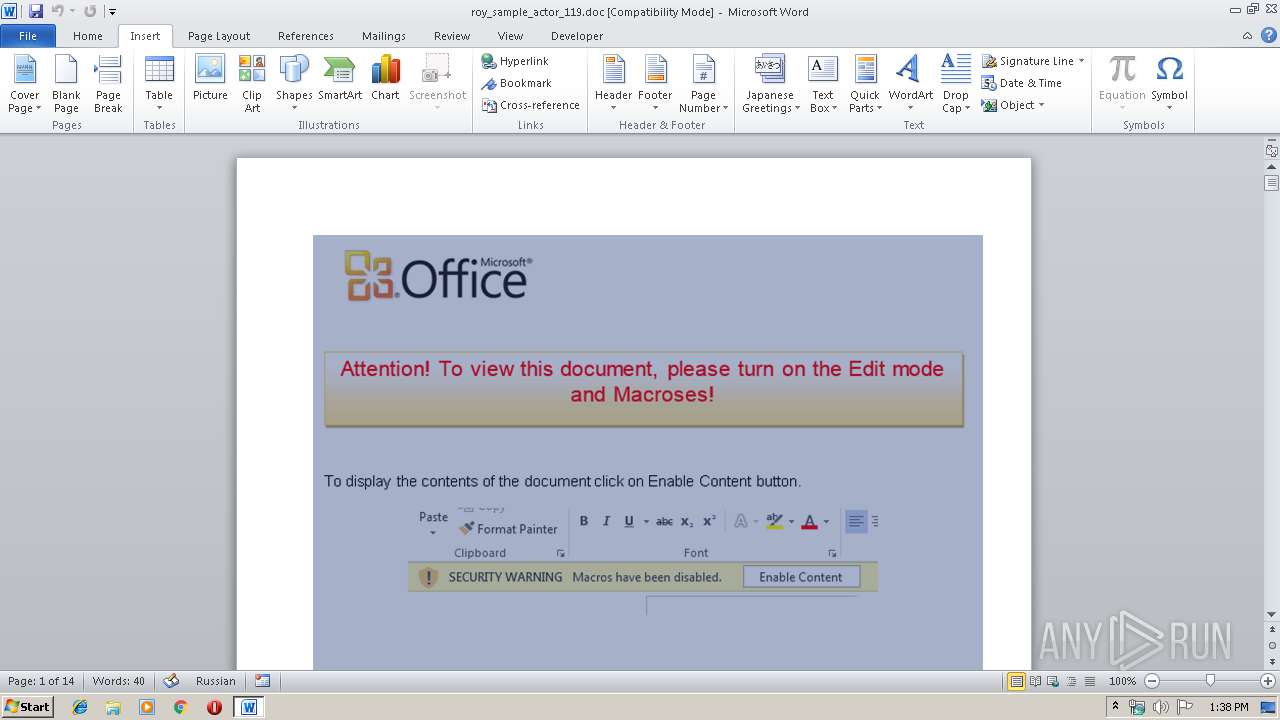
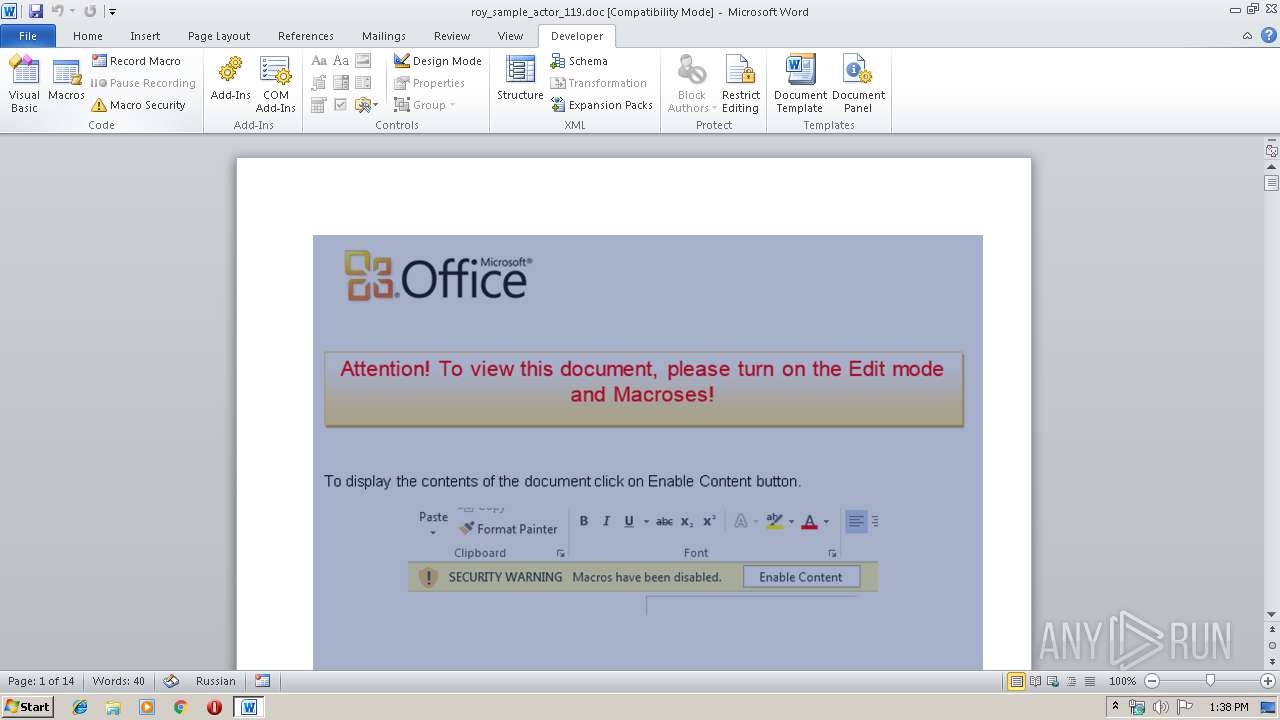
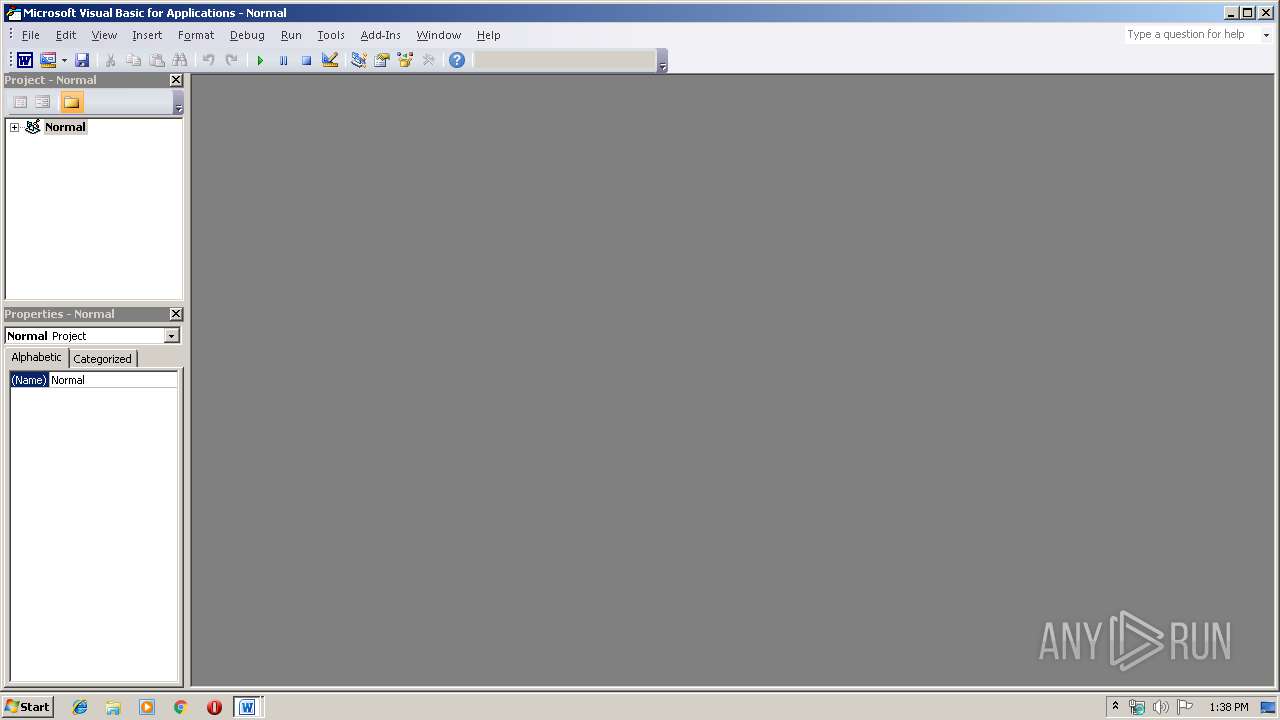
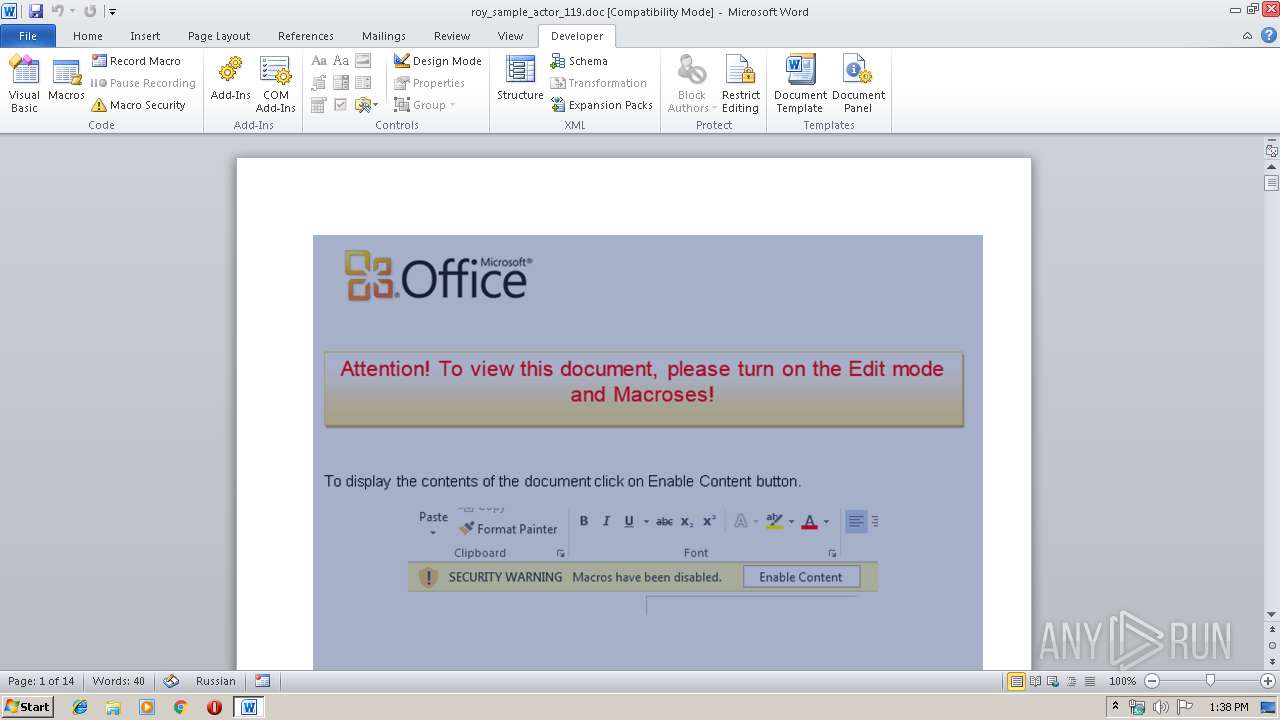
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
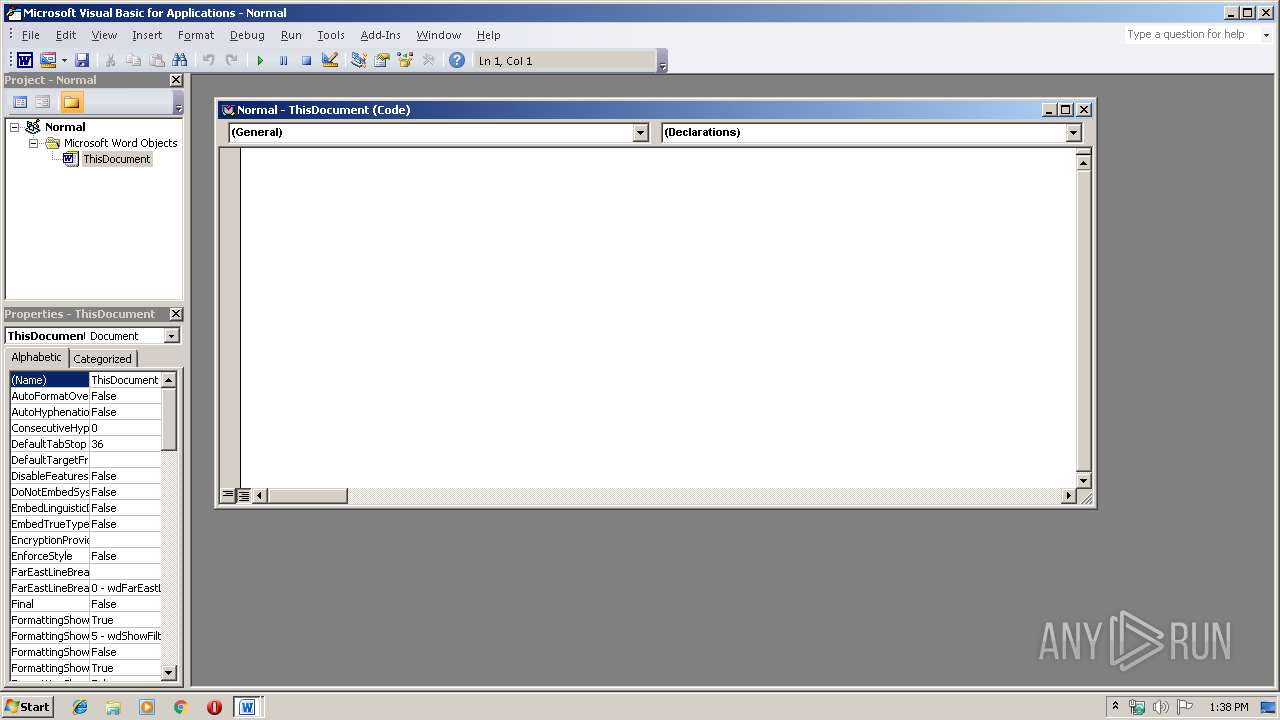
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 944)
Creates files in the user directory
- WINWORD.EXE (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (45.7) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (42.8) |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\roy_sample_actor_119.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 859
Read events
1 076
Write events
588
Delete events
195
Modification events
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (7> |
Value: 28373E00B0030000010000000000000000000000 | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (944) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334837310 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA708.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD7991B7EA9F3C7BA.TMP | — | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{ABC25AFB-3FF6-4626-9CF9-952631751234}.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{53A4EE63-149B-4CE5-A0E4-CE3DE828625E}.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$y_sample_actor_119.doc | pgc | |
MD5:— | SHA256:— | |||
| 944 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report