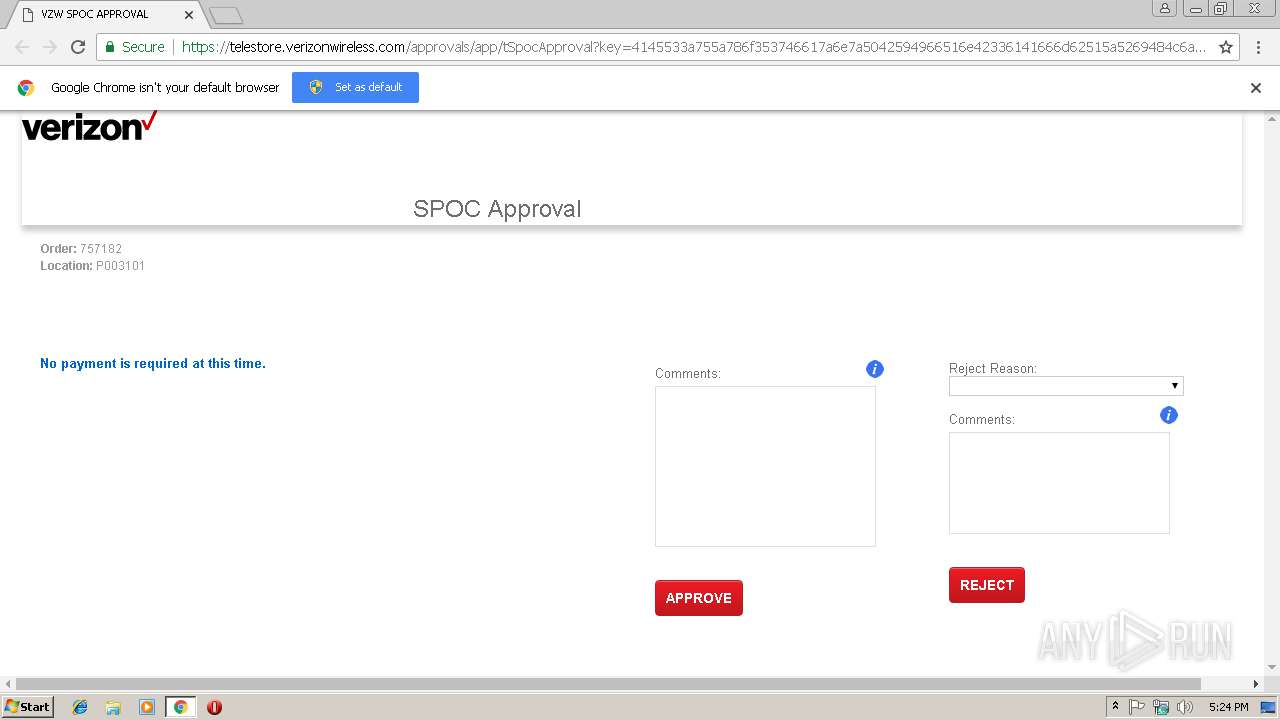
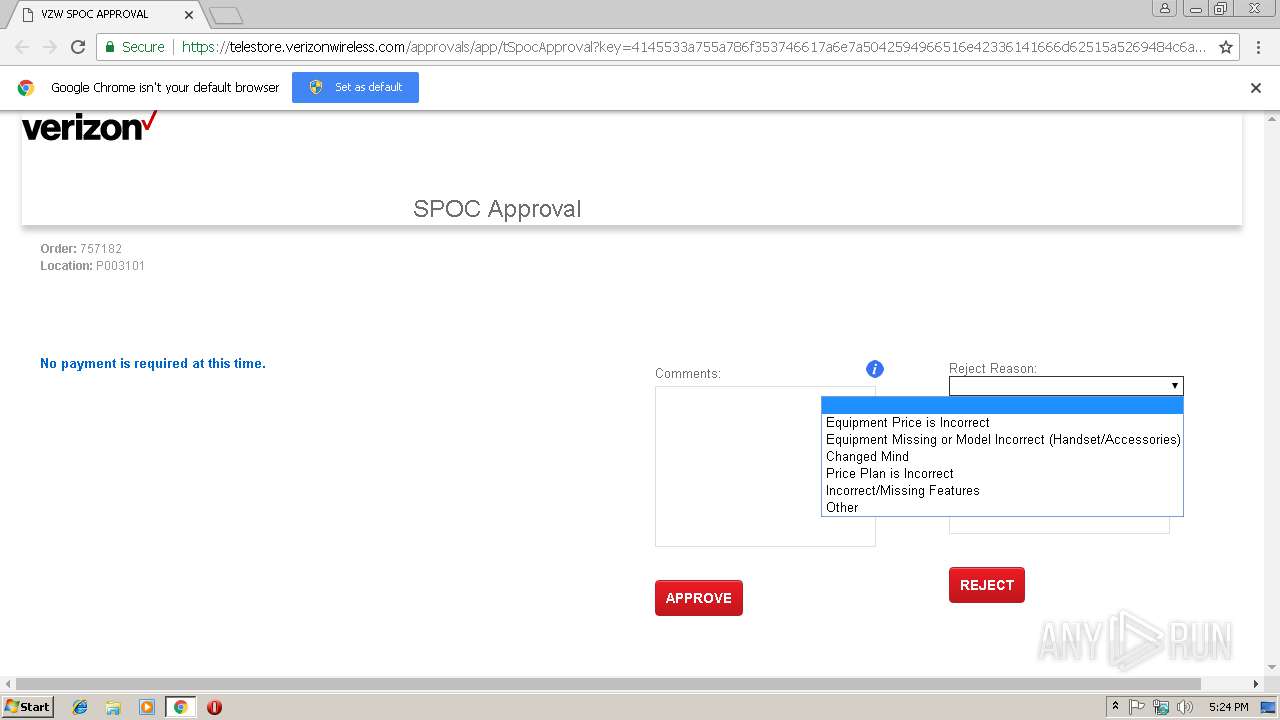
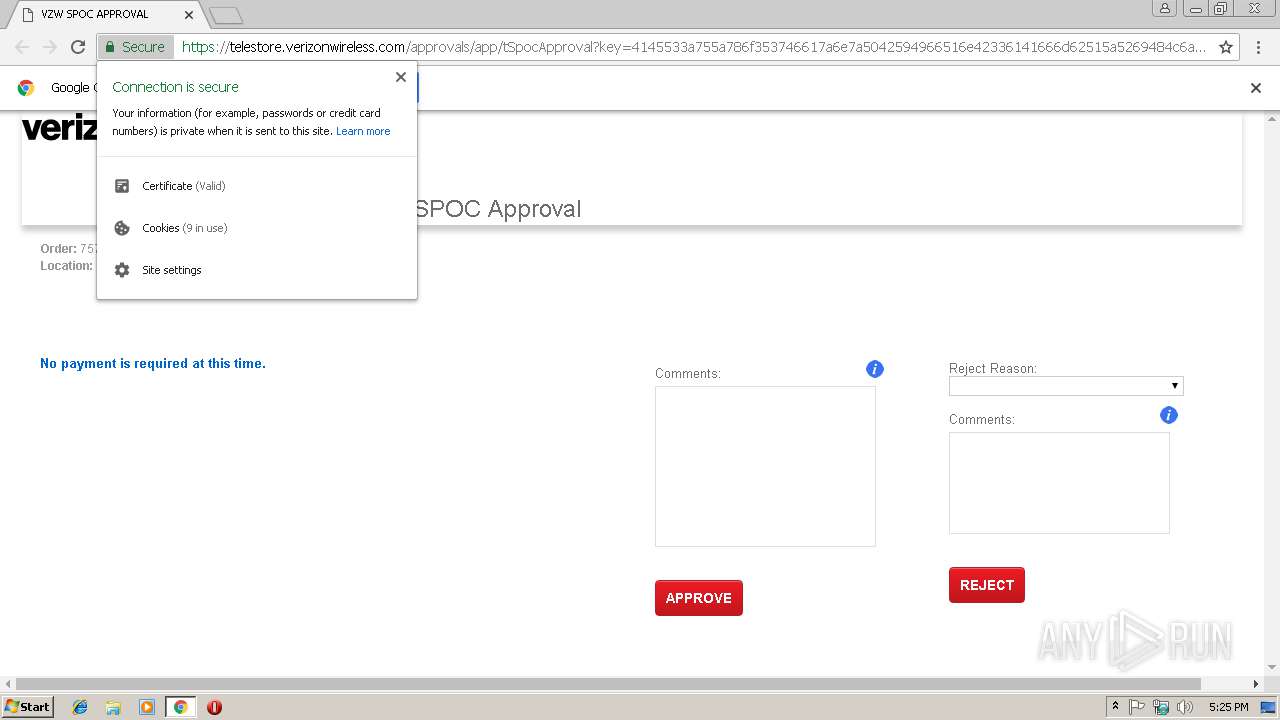
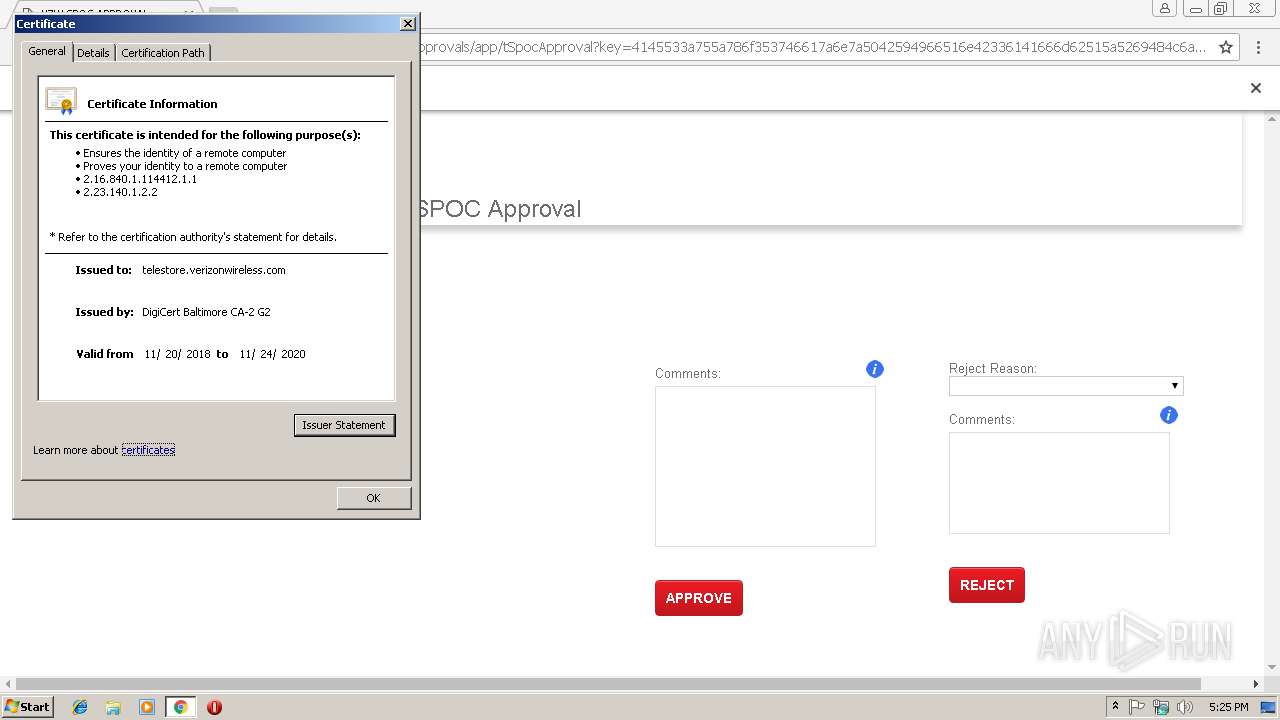
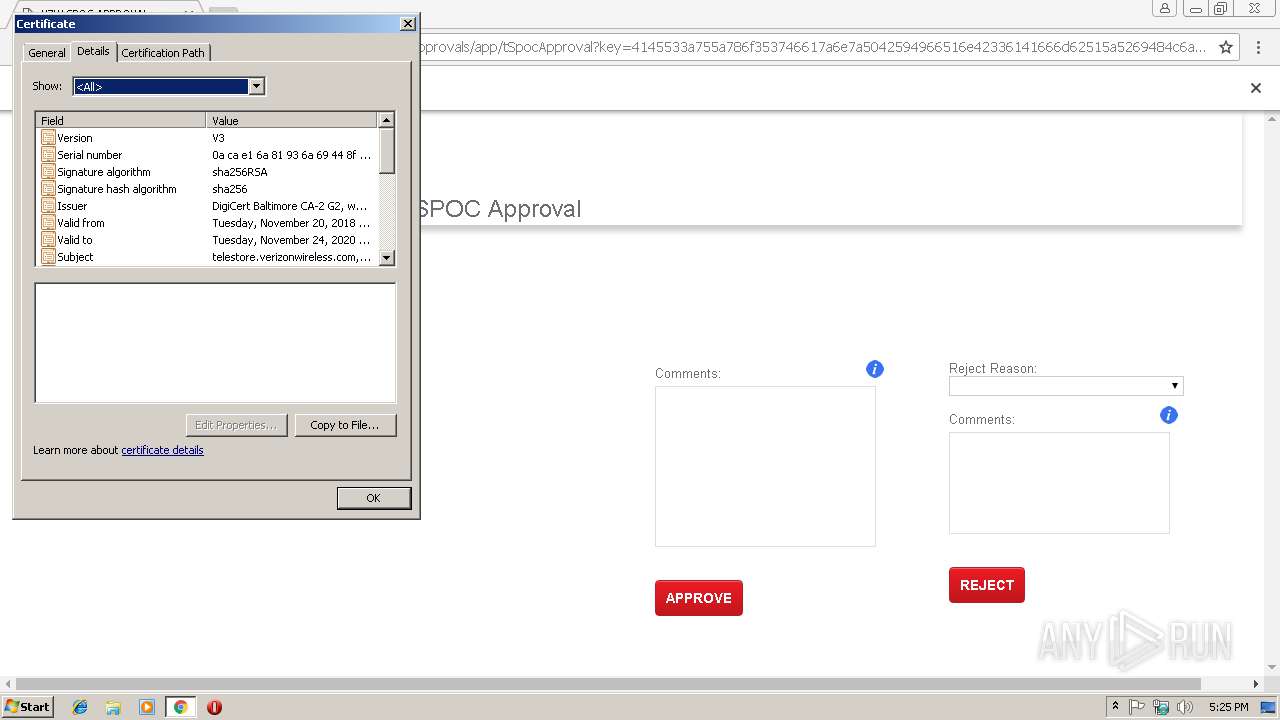
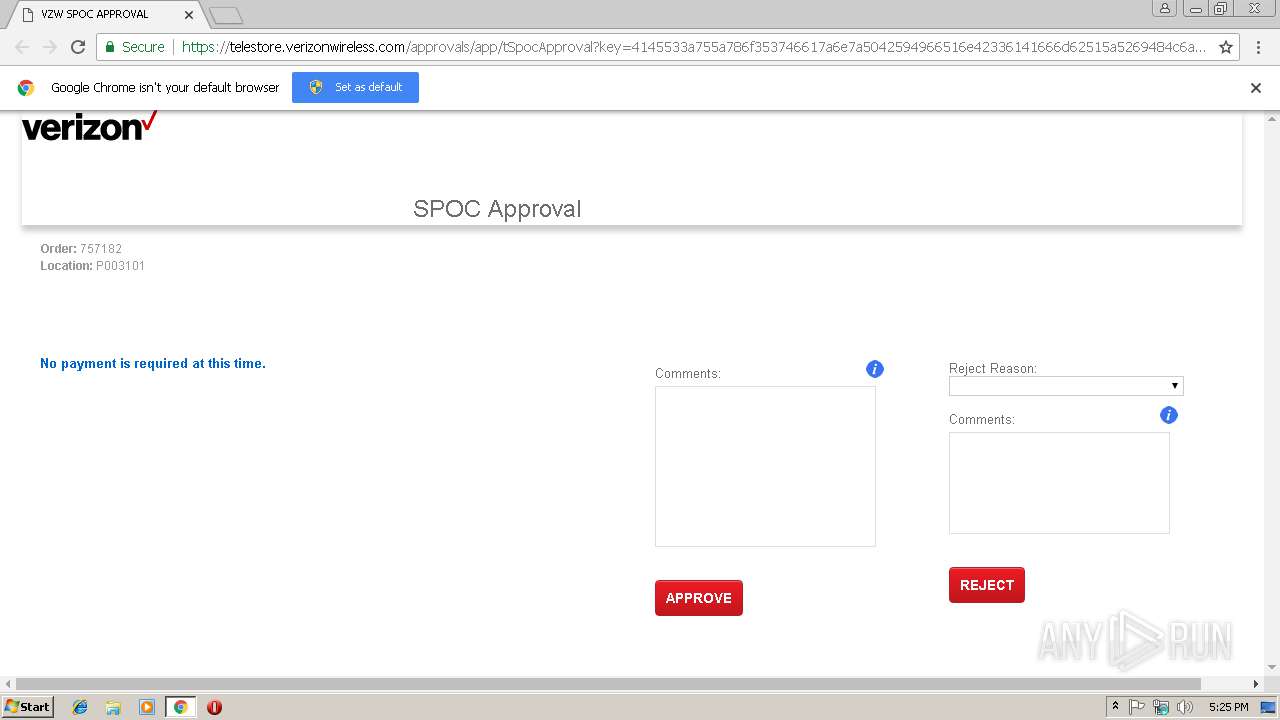
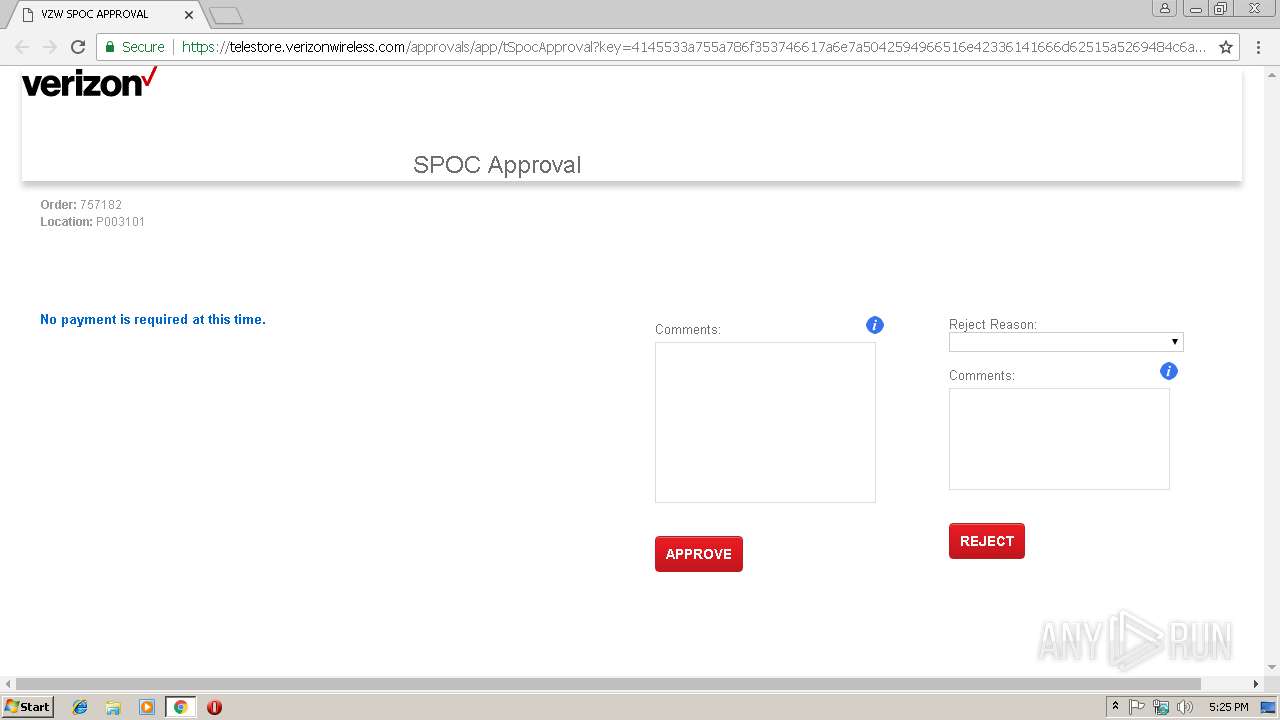
| URL: | https://telestore.verizonwireless.com/approvals/app/tSpocApproval?key=4145533a755a786f353746617a6e7a5042594966516e42336141666d62515a5269484c6a74325661645a75574f47445f364a334c4c564b634750366f4458465a7863783431574d51784e394742492d63774667416c6462344850683841776938754c4b3363495751345f5f4132534c6c4b32626263344e314b5674466b5f366b2d3639527649314a61486a562d57435a744e794c6569546369376f6e456d34745a5630535a773566793339364b6e4b514a6b4a657573397450774f504855757a414a6e555a756b3337587a574c4e77516c69724759356e32425f7538754b4166487551443272694d5f66356c686a733858767343365349337a61772d557431635957696e4e563469712d624a536f6351526d424e4335786b4b784558795a4c465f53504972514d4c766f595353445576766155664e3730484d503847573747565a3146774f37665f59744648596b446741347645393332714a72766d366e4154654a367765733473346c2d42774669504667784b6941525f6839754c504f6362503239507549456c787369666b58376f33484c386679736a642d596e73386d37394e75524e7351505f2d4b764c6f4c30366965546861457443733877346b393846534d69746f7268746f35664e567a6e55466935584739416d50366844416c6564343162716a505f7861354f553277&spocKey=P0031010007571820000000000000000300000000000000003 |
| Full analysis: | https://app.any.run/tasks/5da74c66-5db8-41be-a23f-8094e229bcaa |
| Verdict: | No threats detected |
| Analysis date: | January 28, 2019, 17:24:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7009C5A2E07E1A48AB49EED028679D3D |
| SHA1: | 477131FDC7BFAAC0DFEBA66E30E67880C4BFB91E |
| SHA256: | A339AE28E933F0FA66E50F0E38E0A1656BA6F6C247216B7851DA3171FB143619 |
| SSDEEP: | 24:2Ik+qow11pCQbvpDFVl+d6dFlYH9vX7KtBVCTlShKwZLWdKM:7klo8pCQNBVl+d6/OdvX7SBVCUhj4EM |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3000)
Reads settings of System Certificates
- chrome.exe (PID: 3000)
Modifies the open verb of a shell class
- chrome.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DE6EEE7CE3CE2DA9989B0EF80C04E438 --mojo-platform-channel-handle=3592 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --service-pipe-token=199BA151892DFACE2F2EA4ADA53A00DC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=199BA151892DFACE2F2EA4ADA53A00DC --renderer-client-id=4 --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=B4B3851B1A4AB88E28A8EFAFF15187F9 --mojo-platform-channel-handle=3248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3004 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://telestore.verizonwireless.com/approvals/app/tSpocApproval?key=4145533a755a786f353746617a6e7a5042594966516e42336141666d62515a5269484c6a74325661645a75574f47445f364a334c4c564b634750366f4458465a7863783431574d51784e394742492d63774667416c6462344850683841776938754c4b3363495751345f5f4132534c6c4b32626263344e314b5674466b5f366b2d3639527649314a61486a562d57435a744e794c6569546369376f6e456d34745a5630535a773566793339364b6e4b514a6b4a657573397450774f504855757a414a6e555a756b3337587a574c4e77516c69724759356e32425f7538754b4166487551443272694d5f66356c686a733858767343365349337a61772d557431635957696e4e563469712d624a536f6351526d424e4335786b4b784558795a4c465f53504972514d4c766f595353445576766155664e3730484d503847573747565a3146774f37665f59744648596b446741347645393332714a72766d366e4154654a367765733473346c2d42774669504667784b6941525f6839754c504f6362503239507549456c787369666b58376f33484c386679736a642d596e73386d37394e75524e7351505f2d4b764c6f4c30366965546861457443733877346b393846534d69746f7268746f35664e567a6e55466935584739416d50366844416c6564343162716a505f7861354f553277&spocKey=P0031010007571820000000000000000300000000000000003 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --service-pipe-token=A44D40E9F2ECB00B565096DA5B2F7516 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A44D40E9F2ECB00B565096DA5B2F7516 --renderer-client-id=3 --mojo-platform-channel-handle=2136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701500b0,0x701500c0,0x701500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=6575CC42F0B4E16380B6B08EDDB17655 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
549
Read events
474
Write events
71
Delete events
4
Modification events
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3000-13193169877550875 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3000-13193169877550875 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
10
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bd934b17-1d78-4454-a8a8-ed7e0e46278c.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e0124232-21eb-445f-becb-43d4732f94cf.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e8ae.TMP | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e8dd.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
12
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3000 | chrome.exe | 162.115.32.53:443 | telestore.verizonwireless.com | Cellco Partnership DBA Verizon Wireless | US | unknown |
3000 | chrome.exe | 104.20.42.93:443 | cdn.datatables.net | Cloudflare Inc | US | shared |
3000 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 104.19.198.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3000 | chrome.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3000 | chrome.exe | 162.115.227.4:443 | pie.prod.verizon.com | Cellco Partnership DBA Verizon Wireless | US | unknown |
3000 | chrome.exe | 162.115.227.199:443 | websso.verizonwireless.com | Cellco Partnership DBA Verizon Wireless | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
telestore.verizonwireless.com |
| unknown |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.datatables.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
code.jquery.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
pie.prod.verizon.com |
| unknown |
websso.verizonwireless.com |
| unknown |
Threats
Process | Message |
|---|---|
chrome.exe | Too long ^ |
chrome.exe | Too long restart command line passed |
chrome.exe |