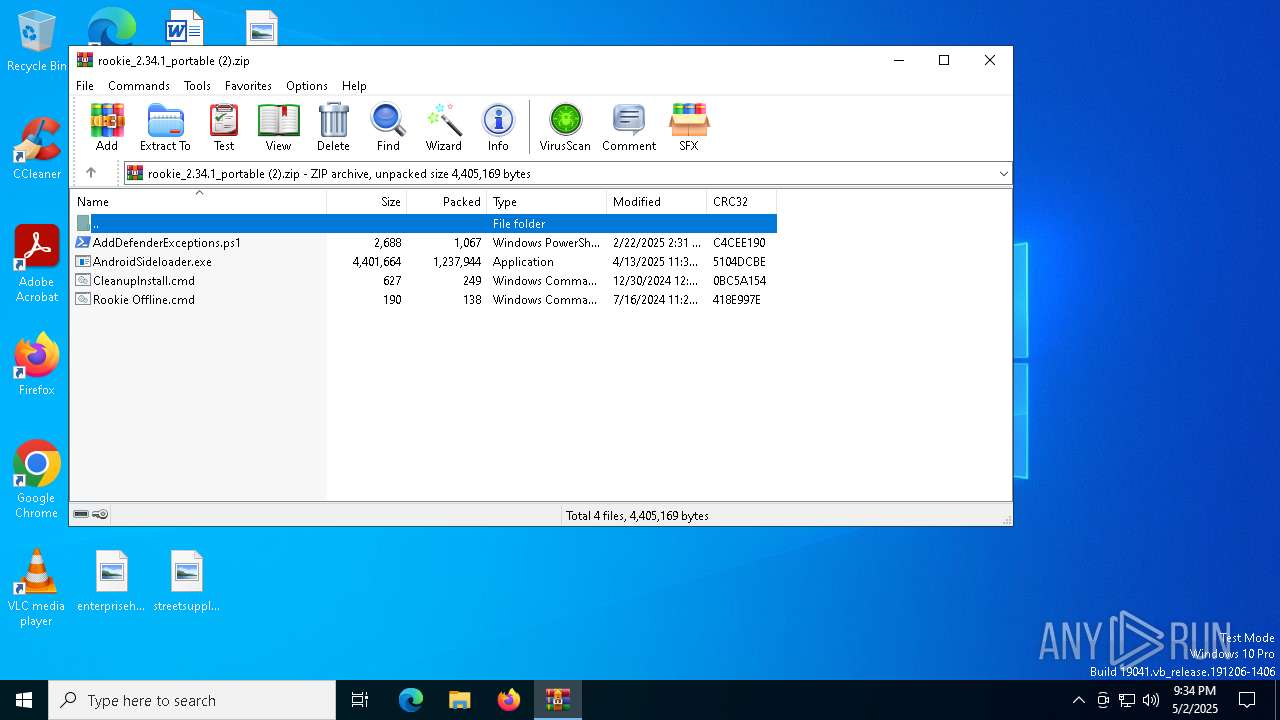
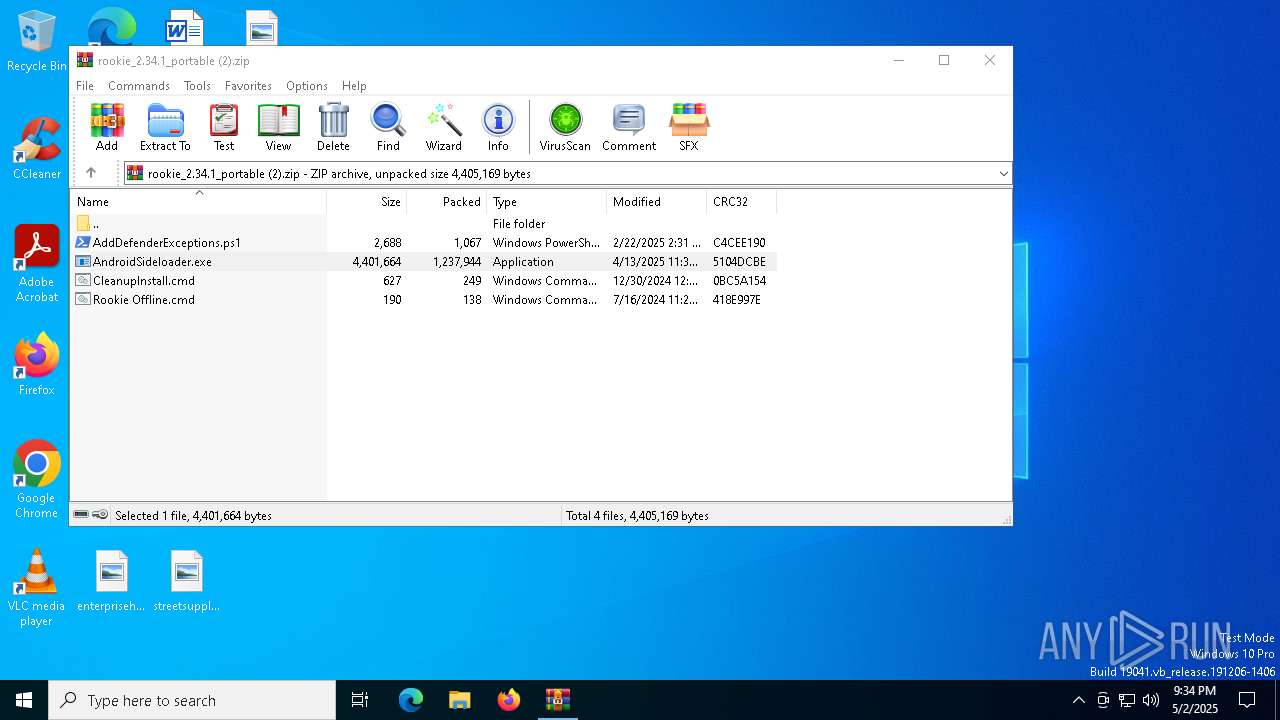
| File name: | rookie_2.34.1_portable (2).zip |
| Full analysis: | https://app.any.run/tasks/fd445776-546d-451c-abf4-346ce5770e57 |
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2025, 21:34:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | F036FCDB20B031D103DDC48A7D4E3FDE |
| SHA1: | 1122163C4DF062887A6943826ED5213242200306 |
| SHA256: | A329B31B2FDA9F72C907B2688F6EE6D64B2E1A9A0D8EFD186B3D64B930550800 |
| SSDEEP: | 49152:9dfIxtxcItUxnyKtzSdEkuexaVDsBVZ4hCsgLUUK/JfCVODmXZw9xBjMnfqd7tLk:7fcTRKsdEtexaVIBVZ4h5gYUK/JfCVOS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1132)
- AndroidSideloader.exe (PID: 7636)
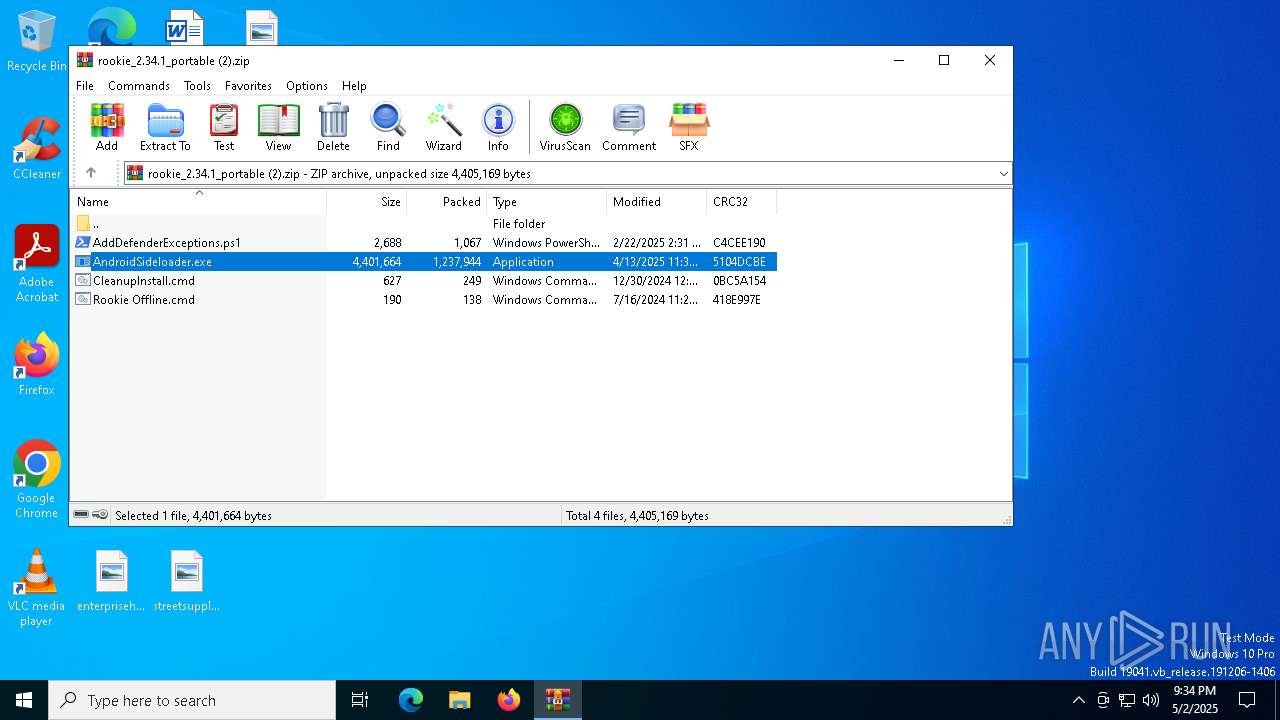
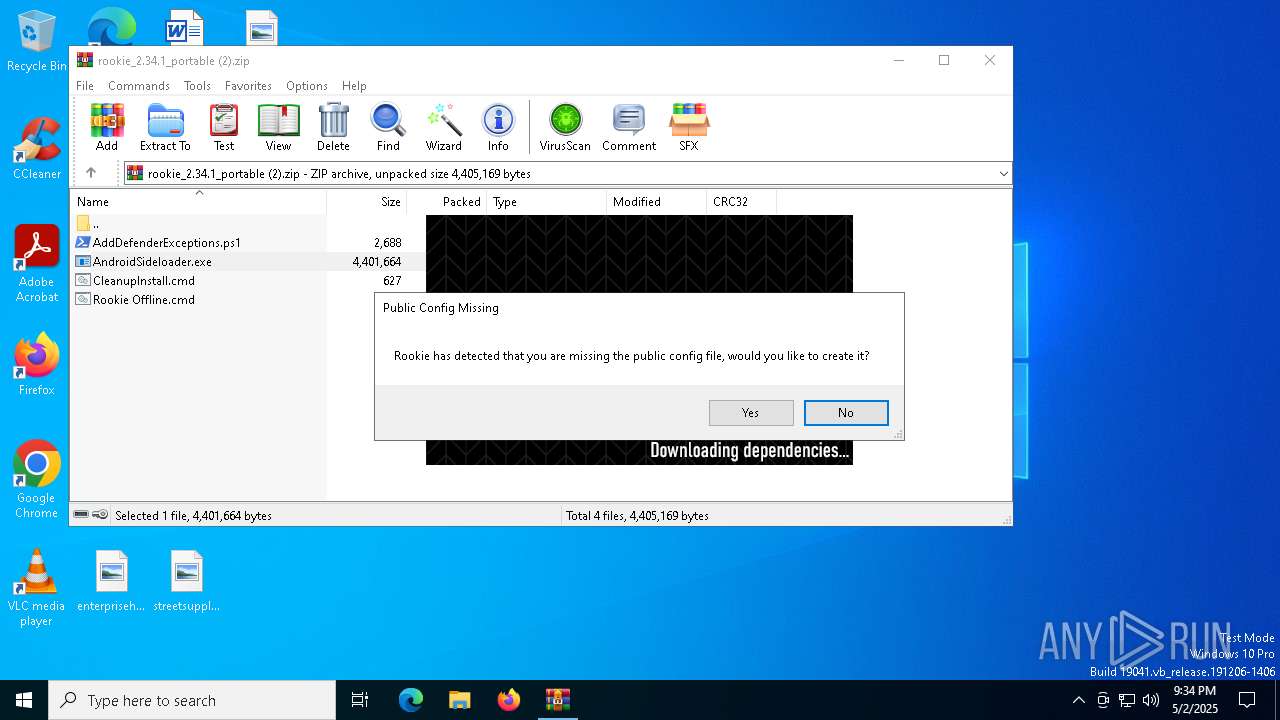
Executable content was dropped or overwritten
- AndroidSideloader.exe (PID: 7636)
- 7z.exe (PID: 7728)
Drops 7-zip archiver for unpacking
- AndroidSideloader.exe (PID: 7636)
Application launched itself
- adb.exe (PID: 8028)
RCLONE has been detected
- rclone.exe (PID: 300)
- rclone.exe (PID: 3888)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1132)
Checks supported languages
- AndroidSideloader.exe (PID: 7636)
- 7z.exe (PID: 7728)
- 7z.exe (PID: 7908)
- adb.exe (PID: 8028)
- adb.exe (PID: 7964)
- adb.exe (PID: 8148)
- rclone.exe (PID: 3888)
- 7z.exe (PID: 2692)
- rclone.exe (PID: 300)
Reads the computer name
- AndroidSideloader.exe (PID: 7636)
- 7z.exe (PID: 7728)
- 7z.exe (PID: 7908)
- rclone.exe (PID: 300)
- rclone.exe (PID: 3888)
- adb.exe (PID: 8148)
- 7z.exe (PID: 2692)
Reads the machine GUID from the registry
- AndroidSideloader.exe (PID: 7636)
- rclone.exe (PID: 300)
Create files in a temporary directory
- AndroidSideloader.exe (PID: 7636)
- 7z.exe (PID: 7908)
- rclone.exe (PID: 300)
- adb.exe (PID: 8148)
- 7z.exe (PID: 2692)
Disables trace logs
- AndroidSideloader.exe (PID: 7636)
Checks proxy server information
- AndroidSideloader.exe (PID: 7636)
Reads the software policy settings
- AndroidSideloader.exe (PID: 7636)
- rclone.exe (PID: 300)
- slui.exe (PID: 7256)
The sample compiled with english language support
- AndroidSideloader.exe (PID: 7636)
- 7z.exe (PID: 7728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:16 13:27:44 |
| ZipCRC: | 0x418e997e |
| ZipCompressedSize: | 138 |
| ZipUncompressedSize: | 190 |
| ZipFileName: | Rookie Offline.cmd |
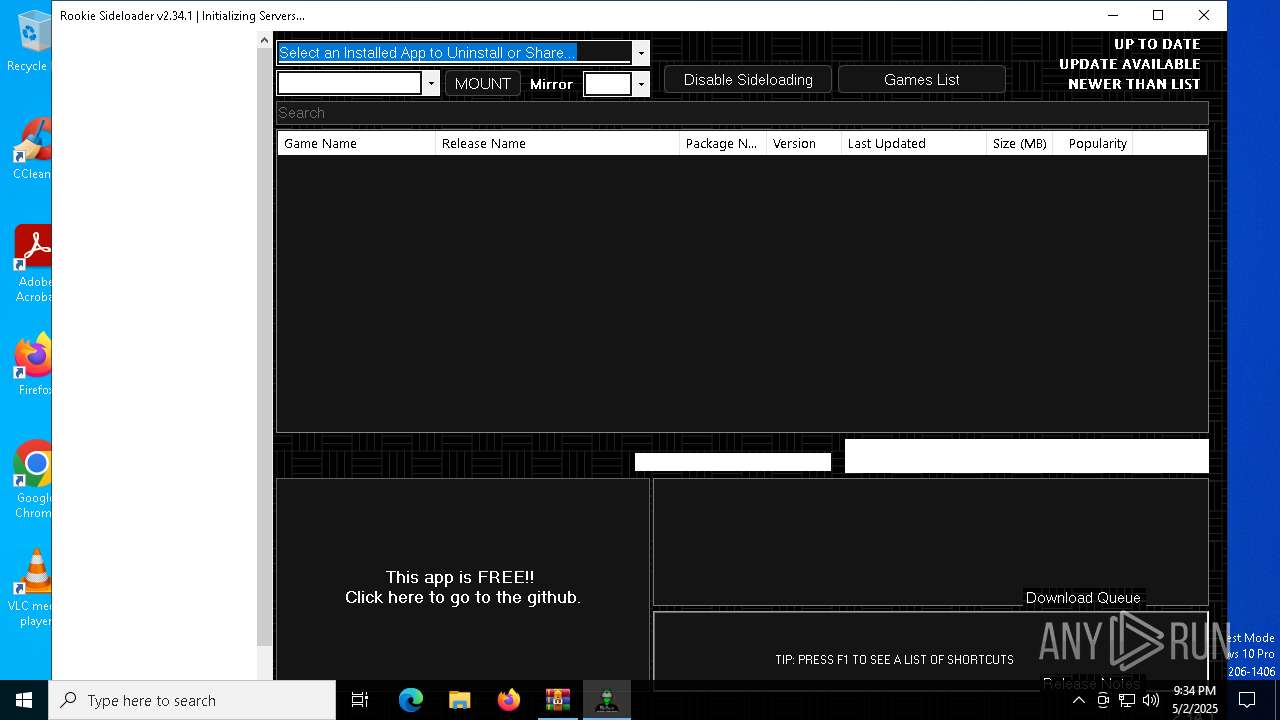
Total processes
146
Monitored processes
20
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\rclone\rclone.exe" sync ":http:/meta.7z" "C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986" --inplace --http-url https://go.vrpyourself.online/ --tpslimit 1.0 --tpslimit-burst 3 | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\rclone\rclone.exe | AndroidSideloader.exe | ||||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rclone Exit code: 0 Version: 1.68.2 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\rookie_2.34.1_portable (2).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "7z.exe" x "C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\meta.7z" -y -o"C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\meta" -p"gL59VfgPxoHR" -bsp1 | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\7z.exe | — | AndroidSideloader.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Version: 24.09 Modules
| |||||||||||||||
| 3888 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\rclone\rclone.exe" listremotes --config vrp.download.config --inplace | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\rclone\rclone.exe | AndroidSideloader.exe | ||||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rclone Exit code: 0 Version: 1.68.2 Modules
| |||||||||||||||
| 4408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7224 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7256 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 115
Read events
11 093
Write events
22
Delete events
0
Modification events
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\rookie_2.34.1_portable (2).zip | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7636) AndroidSideloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7636) AndroidSideloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
17
Suspicious files
3
Text files
748
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7636 | AndroidSideloader.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\dependencies.7z | — | |
MD5:— | SHA256:— | |||
| 1132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\CleanupInstall.cmd | text | |
MD5:9AE44CEBBDE4F44C27801BBF93494C1D | SHA256:57FC69317DE4E7B75A6D45C6037572738F6B48766A6C0D8A47A4F4A4CC533281 | |||
| 7636 | AndroidSideloader.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\debuglog.txt | text | |
MD5:9D4833F113B38ECFE7C6DE7A9EB9F10D | SHA256:8DD67284E50FA3A8F1E7580D7CD01951FEAA1FFE104C68F1ACF79BBBC997138F | |||
| 1132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\Rookie Offline.cmd | text | |
MD5:83B85F3A19C77666117DB1DFBBFD782B | SHA256:5286FC09CBBC098A5DA63096676B180BD7FD28DCD96A79F41F4D92784CC262D1 | |||
| 7636 | AndroidSideloader.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\7z.exe | executable | |
MD5:B6D5860F368B28CAA9DD14A51666A5CD | SHA256:E2CA3EC168AE9C0B4115CD4FE220145EA9B2DC4B6FC79D765E91F415B34D00DE | |||
| 7636 | AndroidSideloader.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\settings.json | binary | |
MD5:DB04BC3DC66695FE59BA6ACBB87E5F6F | SHA256:F384FFBD5D92527325EEBF05F4EFEFF8556BA234C0C4C554126CCA221B2D6936 | |||
| 1132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\AndroidSideloader.exe | executable | |
MD5:552E9C39473CA27A5DE66AB0C87ACEAA | SHA256:5FBEC60B550076E3436AB83683211F3DB39EEE46BD14139A18A36B79F929F67E | |||
| 1132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1132.46986\AddDefenderExceptions.ps1 | text | |
MD5:598164F06F8ABD143A91D20C0562EB93 | SHA256:A8CDB6D8B436DDCA50FCB94F6A6118E6D3B7F01288F15C676D941EBFFDE76C37 | |||
| 7728 | 7z.exe | C:\RSL\platform-tools\etc1tool.exe | executable | |
MD5:7E69E9643C14F5D64BF55407C77E58A1 | SHA256:DCAA07F97F357564847D2375FD15C4E39CADB5DB0FC70C6BC971049B65AC646F | |||
| 7728 | 7z.exe | C:\RSL\platform-tools\aapt.exe | executable | |
MD5:0DD164F26A0485592B34F302D7631493 | SHA256:DB0BA2050B8F6B37185D2BA458D6E25B565AEFA3F3B96040ADF0A82C3469CE3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7636 | AndroidSideloader.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
downloads.rclone.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7636 | AndroidSideloader.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |